Page 1

HP A-U200
A
Unified Threat Management Products
ccess Control Command Reference
Part number: 5998-2676
Software version: R5116P20
Document version: 6PW100-20111216
Page 2

Legal and notice information
© Copyright 2011 Hewlett-Packard Development Company, L.P.
No part of this documentation may be reproduced or transmitted in any form or by any means without
prior written consent of Hewlett-Packard Development Company, L.P.
The information contained herein is subject to change without notice.
HEWLETT-PACKARD COMPANY MAKES NO WARRANTY OF ANY KIND WITH REGARD TO THIS
MATERIAL, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY
AND FITNESS FOR A PARTICULAR PURPOSE. Hewlett-Packard shall not be liable for errors contained
herein or for incidental or consequential damages in connection with the furnishing, performance, or
use of this material.
The only warranties for HP products and services are set forth in the express warranty statements
accompanying such products and services. Nothing herein should be construed as constituting an
additional warranty. HP shall not be liable for technical or editorial errors or omissions contained
herein.
Page 3

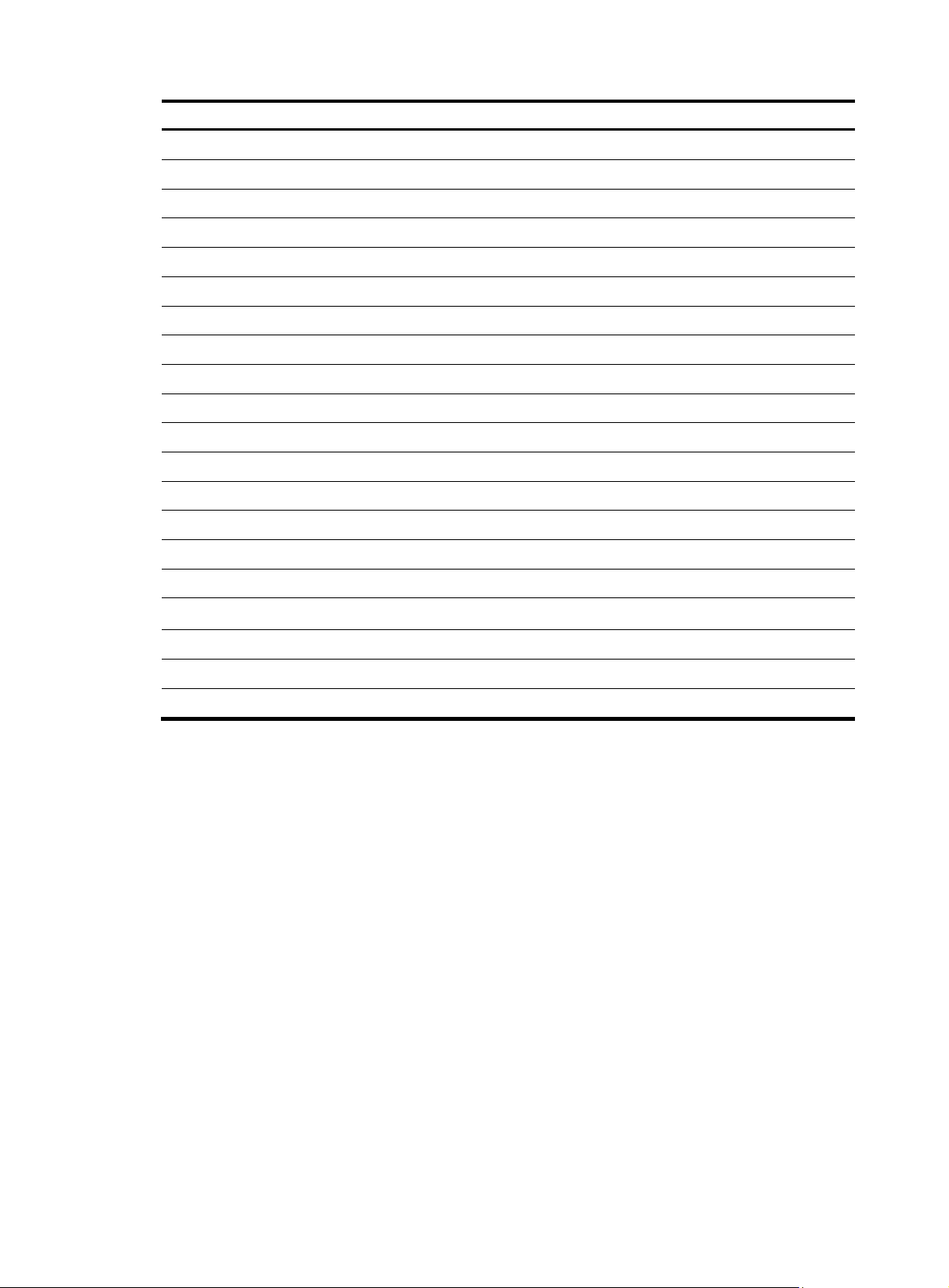
Contents
ACL configuration commands ····································································································································· 1
acl ·············································································································································································· 1
acl copy ····································································································································································· 2
acl name ···································································································································································· 3
description ································································································································································· 3
display acl ································································································································································· 4
display time-range ···················································································································································· 5
reset acl counter ······················································································································································· 6
rule (Ethernet frame header ACL view) ·················································································································· 6
rule (IPv4 advanced ACL view) ······························································································································· 8
rule (IPv4 basic ACL view) ···································································································································· 11
rule comment ·························································································································································· 13
step ·········································································································································································· 13
time-range ······························································································································································ 14
Session management commands ······························································································································ 17
application aging-time ·········································································································································· 17
display session relation-table ······························································································································· 17
display session statistics ········································································································································ 18
display session table ············································································································································· 20
reset session ··························································································································································· 23
reset session statistics ············································································································································ 23
session aging-time ················································································································································· 24
session checksum ··················································································································································· 25
session persist acl ·················································································································································· 25
Connection limit configuration commands ··············································································································· 27
connection-limit apply policy ································································································································ 27
connection-limit policy ··········································································································································· 27
display connection-limit policy ····························································································································· 28
limit ········································································································································································· 29
Portal configuration commands ································································································································· 31
display portal acl ··················································································································································· 31
display portal connection statistics ······················································································································ 33
display portal free-rule ·········································································································································· 36
display portal interface ········································································································································· 37
display portal server ············································································································································· 38
display portal server statistics ······························································································································ 38
display portal tcp-cheat statistics ························································································································· 40
display portal user ················································································································································· 41
portal auth-network ················································································································································ 43
portal delete-user ··················································································································································· 43
portal domain ························································································································································ 44
portal free-rule ························································································································································ 44
portal max-user ······················································································································································ 45
portal nas-id ··························································································································································· 46
portal nas-id-profile ··············································································································································· 47
portal nas-ip ··························································································································································· 47
portal server ··························································································································································· 48
i
Page 4

portal server method ············································································································································· 49
reset portal connection statistics ·························································································································· 50
reset portal server statistics ··································································································································· 50
reset portal tcp-cheat statistics ······························································································································ 50
web-redirect ··························································································································································· 51
AAA configuration commands ·································································································································· 53
AAA configuration commands ····································································································································· 53
aaa nas-id profile ·················································································································································· 53
access-limit enable ················································································································································ 53
accounting command ············································································································································ 54
accounting default ················································································································································· 55
accounting lan-access ··········································································································································· 55
accounting login ···················································································································································· 56
accounting optional ·············································································································································· 57
accounting portal ·················································································································································· 58
accounting ppp ······················································································································································ 59
authentication default ············································································································································ 59
authentication lan-access ······································································································································ 60
authentication login ··············································································································································· 61
authentication portal ············································································································································· 62
authentication ppp ················································································································································ 63
authorization command ········································································································································ 63
authorization default ············································································································································· 64
authorization lan-access ······································································································································· 65
authorization login ················································································································································ 66
authorization portal ··············································································································································· 67
authorization ppp ·················································································································································· 68
authorization-attribute user-profile ······················································································································· 69
cut connection ························································································································································ 69
display connection ················································································································································ 71
display domain ······················································································································································ 73
domain ··································································································································································· 75
domain default enable ·········································································································································· 76
idle-cut enable ························································································································································ 76
ip pool ···································································································································································· 77
nas-id bind vlan ····················································································································································· 78
self-service-url enable ············································································································································ 78
state (ISP domain view) ········································································································································· 79
Local user configuration commands ····························································································································· 80
access-limit ····························································································································································· 80
authorization-attribute (local user view/user group view) ················································································ 80
bind-attribute ·························································································································································· 82
display local-user ··················································································································································· 83
display user-group ················································································································································· 85
expiration-date (local user view) ·························································································································· 85
group ······································································································································································ 86
local-user ································································································································································ 87
local-user password-display-mode ······················································································································· 87
password ································································································································································ 88
service-type ····························································································································································· 89
state (local user view) ············································································································································ 90
user-group ······························································································································································ 90
RADIUS configuration commands ································································································································ 91
accounting-on enable ············································································································································ 91
ii
Page 5

attribute 25 car ······················································································································································ 92
data-flow-format (RADIUS scheme view) ············································································································· 93
display radius scheme ·········································································································································· 93
display radius statistics ········································································································································· 96
display stop-accounting-buffer (for RADIUS) ······································································································· 99
key (RADIUS scheme view)································································································································· 100
nas-ip (RADIUS scheme view) ···························································································································· 100
primary accounting (RADIUS scheme view) ····································································································· 101
primary authentication (RADIUS scheme view) ································································································ 102
radius client ·························································································································································· 103
radius nas-ip ························································································································································· 104
radius scheme ······················································································································································ 105
radius trap ···························································································································································· 105
reset radius statistics ············································································································································ 106
reset stop-accounting-buffer (for RADIUS) ········································································································· 106
retry ······································································································································································· 107
retry realtime-accounting ···································································································································· 108
retry stop-accounting (RADIUS scheme view) ··································································································· 109
secondary accounting (RADIUS scheme view) ································································································· 110
secondary authentication (RADIUS scheme view) ··························································································· 111
security-policy-server ··········································································································································· 112
server-type ···························································································································································· 113
state primary ························································································································································ 114
state secondary ···················································································································································· 114
stop-accounting-buffer enable (RADIUS scheme view) ···················································································· 115
timer quiet (RADIUS scheme view) ···················································································································· 116
timer realtime-accounting (RADIUS scheme view) ··························································································· 117
timer response-timeout (RADIUS scheme view) ································································································ 118
user-name-format (RADIUS scheme view) ········································································································· 118
HWTACACS configuration commands ····················································································································· 119
data-flow-format (HWTACACS scheme view) ·································································································· 119
display hwtacacs ················································································································································· 120
display stop-accounting-buffer (for HWTACACS) ···························································································· 123
hwtacacs nas-ip ··················································································································································· 123
hwtacacs scheme················································································································································· 124
key (HWTACACS scheme view) ························································································································ 125
nas-ip (HWTACACS scheme view) ··················································································································· 125
primary accounting (HWTACACS scheme view) ···························································································· 126
primary authentication (HWTACACS scheme view) ······················································································· 127
primary authorization ········································································································································· 128
reset hwtacacs statistics ······································································································································ 129
reset stop-accounting-buffer (for HWTACACS) ································································································ 129
retry stop-accounting (HWTACACS scheme view) ·························································································· 130
secondary accounting (HWTACACS scheme view) ························································································ 130
secondary authentication (HWTACACS scheme view) ··················································································· 131
secondary authorization ····································································································································· 132
stop-accounting-buffer enable (HWTACACS scheme view) ··········································································· 133
timer quiet (HWTACACS scheme view) ··········································································································· 134
timer realtime-accounting (HWTACACS scheme view) ··················································································· 134
timer response-timeout (HWTACACS scheme view) ······················································································· 135
user-name-format (HWTACACS scheme view) ································································································ 136
Support and other resources ·································································································································· 137
Contacting HP ······························································································································································ 137
Subscription service ············································································································································ 137
iii
Page 6

Related information ······················································································································································ 137
Documents ···························································································································································· 137
Websites ······························································································································································· 137
Conventions ·································································································································································· 138
Index ········································································································································································ 140
iv
Page 7

ACL configuration commands
acl
Syntax
acl number acl-number [ name acl-name ] [ match-order { auto | config } ]
undo acl { all | name acl-name | number acl-number }
View
System view
Default level
2: System level
Parameters
number acl-number: Specifies the number of an IPv4 access control list (ACL):
• 2000 to 2999 for IPv4 basic ACLs
• 3000 to 3999 for IPv4 advanced ACLs
• 4000 to 4999 for Ethernet frame header ACLs
name acl-name: Assigns a name to the ACL for easy identification. The acl-name argument takes a
case-insensitive string of 1 to 32 characters. It must start with an English letter and to avoid confusion, it
cannot be all..
match-order: Sets the order in which ACL rules are compared against packets:
• auto—Compares ACL rules in depth-first order. The depth-first order differs with ACL categories. For
• config—Compares ACL rules in ascending order of rule ID. The rule with a smaller ID has higher
all: Deletes all IPv4 ACLs.
Description
Use the acl command to create an IPv4 ACL and enter its view. If the ACL has been created, you enter its
view directly.
Use the undo acl command to delete the specified IPv4 ACL or all IPv4 ACLs.
By default, no ACL exists.
You can assign a name to an I Pv4 ACL only when you cre ate it. After an ACL is created with a name, you
cannot rename it or remove its name.
You can change match order only for ACLs that do not contain any rules.
To display any ACLs you have created, use the display acl command.
more information, see ACL and QoS Configuration Guide.
priority. If no match order is specified, the config order applies by default.
Examples
# Create IPv4 basic ACL 2000, and enter its view.
<Sysname> system-view
[Sysname] acl number 2000
1
Page 8

[Sysname-acl-basic-2000]
# Create IPv4 basic ACL 2001 with the name flow, and enter its view.
<Sysname> system-view
[Sysname] acl number 2001 name flow
[Sysname-acl-basic-2001-flow]
acl copy
Syntax
acl copy { source-acl-number | name source-acl-name } to { dest-acl-number | name dest-acl-name }
View
System view
Default level
2: System level
Parameters
source-acl-number: Specifies a source existing IPv4 ACL by its number:
• 2000 to 2999 for IPv4 basic ACLs
• 3000 to 3999 for IPv4 advanced ACLs
• 4000 to 4999 for Ethernet frame header ACLs
name source-acl-name: Specifies a source exiting IPv4 ACL by its name. The source-acl-name argument
takes a case-insensitive string of 1 to 32 characters.
dest-acl-number: Assigns a unique number to the IPv4 ACL you are creating. This number must be from
the same ACL category as the source ACL. Available value ranges include:
• 2000 to 2999 for IPv4 basic ACLs
• 3000 to 3999 for IPv4 advanced ACLs
• 4000 to 4999 for Ethernet frame header ACLs
name dest-acl-name: Assigns a unique name to the IPv4 ACL you are creating. The dest-acl-name takes
a case-insensitive string of 1 to 32 characters. It must start with an English letter and to avoid confusion,
it cannot be all. For this ACL, the system automatically picks the smallest number from all available
numbers in the same ACL category as the source ACL.
Description
Use the acl copy command to create an IPv4 ACL by copying an IPv4 ACL that already exists. The new
ACL has the same properties and content as the source ACL, but not the same ACL number and name.
You can assign a name to an IPv4 ACL only when you create it. After an IPv4 ACL is created with a name,
you cannot rename it or remove its name.
Examples
# Create IPv4 basic ACL 2002 by copying IPv4 basic ACL 2001.
<Sysname> system-view
[Sysname] acl copy 2001 to 2002
2
Page 9

acl name
Syntax
acl name acl-name
View
System view
Default level
2: System level
Parameters
acl-name: Specifies an IPv4 ACL name, a case-insensitive string of 1 to 32 characters. It must start with
an English letter. The IPv4 ACL must already exist.
Description
Use the acl name command to enter the view of an IPv4 ACL that has a name.
Related commands: acl.
Examples
# Enter the view of IPv4 ACL flow.
<Sysname> system-view
[Sysname] acl name flow
[Sysname-acl-basic-2001-flow]
description
Syntax
description text
undo description
View
IPv4 basic/advanced ACL view, Ethernet frame header ACL view
Default level
2: System level
Parameters
text: ACL description, a case-sensitive string of 1 to 127 characters.
Description
Use the description command to configure a description for an ACL.
Use the undo description command to remove the ACL description.
By default, an ACL has no ACL description.
Related commands: display acl.
Examples
# Configure a description for IPv4 basic ACL 2000.
<Sysname> system-view
3
Page 10

[Sysname] acl number 2000
p
[Sysname-acl-basic-2000] description This is an IPv4 basic ACL.
display acl
Syntax
display acl { acl-number | all | name acl-name }
View
Any view
Default level
1: Monitor level
Parameters
acl-number: Specifies an ACL by its number:
• 2000 to 2999 for IPv4 basic ACLs
• 3000 to 3999 for IPv4 advanced ACLs
• 4000 to 4999 for Ethernet frame header ACLs
all: Displays information for all IPv4 ACLs.
name acl-name: Specifies an ACL by its name. The acl-name argument takes a case-insensitive string of
1 to 32 characters. It must start with an English letter.
Description
Use the display acl command to display the IPv4 ACL configuration and match statistics.
This command displays ACL rules in config or depth-first order, whichever is configured.
Examples
# Display all IPv4 configuration and match statistics.
<Sysname> display acl all
Basic ACL 2000, named flow, 3 rules,
ACL's step is 5
rule 0 permit
rule 5 permit source 1.1.1.1 0 (2 times matched)
rule 10 permit vpn-instance mk
Basic ACL 2001, named -none-, 3 rules, match-order is auto,
ACL's step is 5
rule 10 permit vpn-instance rd
rule 10 comment This rule is used in VPN rd.
rule 5 permit source 2.2.2.2 0
rule 0 permit
Table 1 Output description
Field
Descri
Basic ACL 2000
Category and number of the ACL. The following field information is about IPv4
basic ACL 2000.
tion
4
Page 11

Field Description
named flow The name of the ACL is flow. "-none-" means the ACL is not named.
3 rules
match-order is auto
ACL's step is 5 The rule numbering step is 5.
rule 0 permit Content of rule 0
2 times matched
Uncompleted
rule 10 comment This rule is
used in VPN rd.
display time-range
Syntax
display time-range { time-range-name | all }
View
The ACL contains three rules.
The match order for the ACL is auto, which sorts ACL rules in depth-first order.
This field is not present when the match order is config.
There have been two matches for the rule. The statistic counts only ACL
matches performed in software.
This field is not displayed when no packets have matched the rule.
Applying the rule to hardware failed because no sufficient resources were
available or the hardware does not support the rule. This event might occur
when you modify a rule in an ACL that has been applied.
The description of ACL rule 10 is "This rule is used in VPN rd."
Any view
Default level
1: Monitor level
Parameters
time-range-name: Specifies a time range name, a case-insensitive string of 1 to 32 characters. It must
start with an English letter.
all: Displays the configuration and status of all existing time ranges.
Description
Use the display time-range command to display the configuration and status of the specified time range
or all time ranges.
Examples
# Display the configuration and status of time range t4.
<Sysname> display time-range t4
Current time is 17:12:34 4/13/2010 Tuesday
Time-range : t4 ( Inactive )
10:00 to 12:00 Mon
14:00 to 16:00 Wed
from 00:00 1/1/2010 to 23:59 1/31/2010
from 00:00 6/1/2010 to 23:59 6/30/2010
5
Page 12

Table 2 Output description
p
Field
Descri
tion
Current time Current system time
Time-range
reset acl counter
Syntax
reset acl counter { acl-number | all | name acl-name }
View
User view
Default level
2: System level
Parameters
acl-number: Specifies an IPv4 ACL by its number:
• 2000 to 2999 for IPv4 basic ACLs
• 3000 to 3999 for IPv4 advanced ACLs
• 4000 to 4999 for Ethernet frame header ACLs
Configuration and status of the time range, including its name,
status (active or inactive), and start time and end time.
all: Clears statistics for all IPv4 ACLs.
name acl-name: Specifies an IPv4 ACL by its name. The acl-name argument takes a case-insensitive
string of 1 to 32 characters. It must start with an English letter.
Description
Use the reset acl counter command to clear IPv4 ACL statistics.
Related commands: display acl.
Examples
# Clear statistics for IPv4 basic ACL 2001.
<Sysname> reset acl counter 2001
# Clear statistics for IPv4 ACL flow.
<Sysname> reset acl counter name flow
rule (Ethernet frame header ACL view)
Syntax
rule [ rule-id ] { deny | permit } [ cos vlan-pri | dest-mac dest-addr dest-mask | { lsap lsap-type
lsap-type-mask | type protocol-type protocol-type-mask } | source-mac sour-addr source-mask |
time-range time-range-name ] *
undo rule rule-id [ counting | time-range ] *
View
Ethernet frame header ACL view
6
Page 13

Default level
2: System level
Parameters
rule-id: Specifies a rule ID, in the range of 0 to 65534. If no rule ID is provided when you create an ACL
rule, the system automatically assigns it a rule ID. This rule ID takes the nearest higher multiple of the
numbering step to the current highest rule ID, starting from 0. For example, if the rule numbering step is
5 and the current highest rule ID is 28, the rule is numbered 30.
deny: Denies matching packets.
permit: Allows matching packets to pass.
cos vlan-pri: Matches an 802.1p priority. The vlan-pri argument can be a number in the range of 0 to 7,
or in words, best-effort (0), background (1), spare (2), excellent-effort (3), controlled-load (4), video (5),
voice (6), or network-management (7).
dest-mac dest-addr dest-mask: Matches a destination MAC address range. The dest-addr and dest-mask
arguments represent a destination MAC address and mask in H-H-H format.
lsap lsap-type lsap-type-mask: Matches the DSAP and SSAP fields in LLC encapsulation. The lsap-type
argument is a 16-bit hexadecimal number that represents the encapsulation format. The lsap-type-mask
argument is a 16-bit hexadecimal number that represents the LSAP mask.
type protocol-type protocol-type-mask: Matches one or more protocols in the Ethernet frame header. The
protocol-type argument is a 16-bit hexadecimal number that represents a protocol type in Ethernet_II and
Ethernet_SNAP frames. The protocol-type-mask argument is a 16-bit hexadecimal number that represents
a protocol type mask.
source-mac sour-addr source-mask: Matches a source MAC address range. The sour-addr argument
represents a source MAC address, and the sour-mask argument represents a mask in H-H-H format.
time-range time-range-name: Specifies a time range for the rule. The time-range-name argument is a
case-insensitive string of 1 to 32 characters. It must start with an English letter. If the time range is not
configured, the system creates the rule; however, the rule using the time range can take effect only after
you configure the timer range.
Description
Use the rule command to create or edit an Ethernet frame header ACL rule. You can edit ACL rules only
when the match order is config.
Use the undo rule command to delete an Ethernet frame header ACL rule or some attributes in the rule.
If no optional keywords are provided, you delete the entire rule. If optional keywords or arguments are
provided, you delete the specified attributes.
By default, an Ethernet frame header ACL does not contain any rule.
Wit hin an ACL, the permit or deny statement of each rule must be unique. If the ACL rule you are creati ng
or editing has the same deny or permit statement as another rule in the ACL, your creation or editing
attempt fails.
To view rules in an ACL and their rule IDs, use the display acl all command.
Related commands: acl, display acl, step, and time-range.
Examples
# Create a rule in ACL 4000 to permit ARP packets and deny RARP packets.
<Sysname> system-view
[Sysname] acl number 4000
7
Page 14

[Sysname-acl-ethernetframe-4000] rule permit type 0806 ffff
p
[Sysname-acl-ethernetframe-4000] rule deny type 8035 ffff
rule (IPv4 advanced ACL view)
Syntax
rule [ rule-id ] { deny | permit } protocol [ { { ack ack-value | fin fin-value | psh psh-value | rst rst-value
| syn syn-value | urg urg-value } * } | destination { dest-addr dest-wildcard | any } | destination-port
operator port1 [ port2 ] | dscp dscp | fragment | icmp-type { icmp-type [ icmp-code ] | icmp-message }
| logging | precedence precedence | reflective | source { sour-addr sour-wildcard | any } | source-port
operator port1 [ port2 ] | time-range time-range-name | tos tos | vpn-instance vpn-instance-name ] *
undo rule rule-id [ { { ack | fin | psh | rst | sy
fragment | icmp-type | logging | precedence | reflective | source | source-port | time-range | tos |
vpn-instance ] *
View
IPv4 advanced ACL view
Default level
2: System level
Parameters
rule-id: Specifies a rule ID, in the range of 0 to 65534. If no rule ID is provided when you create an ACL
rule, the system automatically assigns it a rule ID. This rule ID takes the nearest higher multiple of the
numbering step to the current highest rule ID, starting from 0. For example, if the rule numbering step is
5 and the current highest rule ID is 28, the rule is numbered 30.
deny: Denies matching packets.
permit: Allows matching packets to pass.
protocol: Protocol carried by IPv4. It can be a number in the range of 0 to 255, or in words, gre (47),
icmp (1) , igmp (2), ip, ipinip (4), ospf (89), tcp (6), or udp (17) . Table 3 de
can specify regardless of the value that the protocol argument takes.
Table 3 Match criteria and other rule information for IPv4 advanced ACL rules
n | urg } * } | destination | destination-port | dscp |
scribes the parameters that you
Parameters Function Descri
source
{ sour-addr
sour-wildcard |
any }
destination
{ dest-addr
dest-wildcard |
any }
precedence
precedence
tos tos
Specifies a source
address
Specifies a
destination
address
Specifies an IP
precedence value
Specifies a ToS
preference
The sour-addr sour-wildcard arguments represent a source IP address
and wildcard mask in dotted decimal notation. An all-zero wildcard
specifies a host address.
The any keyword specifies any source IP address.
The dest-addr dest-wildcard arguments represent a destination IP
address and wildcard mask in dotted decimal notation. An all-zero
wildcard specifies a host address.
The any keyword represents any destination IP address.
The precedence argument can be a number in the range of 0 to 7, or
in words, routine (0), priority (1), immediate (2), flash (3),
flash-override (4), critical (5), internet (6), or network (7).
The tos argument can be a number in the range of 0 to 15, or in
words, max-reliability (2), max-throughput (4), min-delay (8),
min-monetary-cost (1), or normal (0).
tion
8
Page 15

Parameters Function Description
p
The dscp argument can be a number in the range of 0 to 63, or in
words, af11 (10), af12 (12), af13 (14), af21 (18), af22 (20), af23
(22), af31 (26), af32 (28), af33 (30), af41 (34), af42 (36), af43 (38),
cs1 (8), cs2 (16), cs3 (24), cs4 (32), cs5 (40), cs6 (48), cs7 (56),
default (0), or ef (46).
dscp dscp
Specifies a DSCP
priority
logging
reflective
vpn-instance
vpn-instance-na
me
fragment
time-range
time-range-nam
e
Logs matching
packets
Specifies that the
rule be reflective
Applies the rule to
packets in a VPN
instance
Applies the rule to
only non-first
fragments
Specifies a time
range for the rule
This function requires that the module that uses the ACL supports
logging.
A rule with the reflective keyword can be defined only for TCP, UDP,
or ICMP packets and can only be a permit statement.
The vpn-instance-name argument takes a case-sensitive string of 1 to
31 characters.
If no VPN instance is specified, the rule applies only to non-VPN
packets.
Without this keyword, the rule applies to all fragments and
non-fragments.
The time-range-name argument takes a case-insensitive string of 1 to
32 characters. It must start with an English letter. If the time range is not
configured, the system creates the rule; however, the rule using the
time range can take effect only after you configure the timer range.
NOTE:
If you provide the precedence or tos keyword in addition to the dscp keyword, only the dscp keyword
takes effect.
If the protocol argument takes tcp (6) or udp (7), set the parameters shown in Table 4.
Table 4 TCP/UDP-specific parameters for IPv4 advanced ACL rules
Parameters Function Descri
source-port
operator port1
[ port2 ]
destination-port
operator port1
[ port2 ]
Specifies one or
more UDP or TCP
source ports
Specifies one or
more UDP or TCP
destination ports
The operator argument can be lt (lower than), gt (greater than),
eq (equal to), neq (not equal to), or range (inclusive range).
The port1 and port2 arguments are TCP or UDP port numbers in
the range of 0 to 65535. port2 is needed only when the operator
argument is range.
TCP port numbers can be represented as: chargen (19), bgp
(179), cmd (514), daytime (13), discard (9), domain (53), echo
(7), exec (512), finger (79), ftp (21), ftp-data (20), gopher (70),
hostname (101), irc (194), klogin (543), kshell (544), login
(513), lpd (515), nntp (119), pop2 (109), pop3 (110), smtp
(25), sunrpc (111), tacacs (49), talk (517), telnet (23), time (37),
uucp (540), whois (43), and www (80).
UDP
bootps (67), discard (9), dns (53), dnsix (90), echo (7),
mobilip-ag (434), mobilip-mn (435), nameserver (42),
netbios-dgm (138), netbios-ns (137), netbios-ssn (139), ntp
(123), rip (520), snmp (161), snmptrap (162), sunrpc (111),
syslog (514), tacacs-ds (65), talk (517), tftp (69), time (37), who
(513), and xdmcp (177).
tion
port numbers can be represented as: biff (512), bootpc (68),
9
Page 16

Parameters Function Description
p
g
{ ack ack-value |
fin fin-value | psh
psh-value | rst
rst-value | syn
syn-value | urg
urg-value } *
Specifies one or
more TCP flags
including ACK, FIN,
PSH, RST, SYN, and
URG
Parameters specific to TCP.
The value for each argument can be 0 (flag bit not set) or 1 (flag
bit set).
For example, a rule configured with ack 1 psh 0 may match
packets that have the ACK flag bit set or the PSH flag bit not set on
one device.
If the protocol argument takes icmp (1), set the parameters shown in Table 5.
Table 5 ICMP-specific parameters for IPv4 advanced ACL rules
Parameters Function Descri
The icmp-type argument is in the range of 0 to 255.
icmp-type { icmp-type
[ icmp-code ] |
icmp-message }
Specifies the ICMP
message type and
code
The icmp-code argument is in the range of 0 to 255.
The icmp-message argument specifies a message name.
Supported ICMP message names and their corresponding type
and code values are listed in Table 6.
tion
Table 6 ICMP message names supported in IPv4 advanced ACL rules
ICMP messa
echo 8 0
e name ICMP message type
ICMP message code
echo-reply 0 0
fragmentneed-DFset 3 4
host-redirect 5 1
host-tos-redirect 5 3
host-unreachable 3 1
information-reply 16 0
information-request 15 0
net-redirect 5 0
net-tos-redirect 5 2
net-unreachable 3 0
parameter-problem 12 0
port-unreachable 3 3
protocol-unreachable 3 2
reassembly-timeout 11 1
source-quench 4 0
source-route-failed 3 5
timestamp-reply 14 0
timestamp-request 13 0
ttl-exceeded 11 0
10
Page 17

Description
Use the rule command to create or edit an IPv4 advanced ACL rule. You can edit ACL rules only when
the match order is config.
Use the undo rule command to delete an entire IPv4 advanced ACL rule or some attributes in the rule. If
no optional keywords are provided, you delete the entire rule. If optional keywords or arguments are
provided, you delete the specified attributes.
By default, an IPv4 advanced ACL does not contain any rule.
Wit hin an ACL, the permit or deny statement of each rule must be unique. If the ACL rule you are creati ng
or editing has the same deny or permit statement as another rule in the ACL, your creation or editing
attempt fails.
To view rules in an ACL and their rule IDs, use the display acl all command.
Related commands: acl, display acl, step, and time-range.
Examples
# Create an IPv4 advanced ACL rule to permit TCP packets with the destination port 80 from
129.9.0.0/16 to 202.38.160.0/24, and enable logging matching packets.
<Sysname> system-view
[Sysname] acl number 3000
[Sysname-acl-adv-3000] rule permit tcp source 129.9.0.0 0.0.255.255 destination
202.38.160.0 0.0.0.255 destination-port eq 80 logging
# Create IPv4 advanced ACL rules to permit all IP packets but the ICMP packets destined for
192.168.1.0/24.
<Sysname> system-view
[Sysname] acl number 3001
[Sysname-acl-adv-3001] rule permit ip
[Sysname-acl-adv-3001] rule deny icmp destination 192.168.1.0 0.0.0.255
# Create IPv4 advanced ACL rules to permit inbound and outbound FTP packets.
<Sysname> system-view
[Sysname] acl number 3002
[Sysname-acl-adv-3002] rule permit tcp source-port eq ftp
[Sysname-acl-adv-3002] rule permit tcp source-port eq ftp-data
[Sysname-acl-adv-3002] rule permit tcp destination-port eq ftp
[Sysname-acl-adv-3002] rule permit tcp destination-port eq ftp-data
# Create IPv4 advanced ACL rules to permit inbound and outbound SNMP and SNMP trap packets.
<Sysname> system-view
[Sysname] acl number 3003
[Sysname-acl-adv-3003] rule permit udp source-port eq snmp
[Sysname-acl-adv-3003] rule permit udp source-port eq snmptrap
[Sysname-acl-adv-3003] rule permit udp destination-port eq snmp
[Sysname-acl-adv-3003] rule permit udp destination-port eq snmptrap
rule (IPv4 basic ACL view)
Syntax
rule [ rule-id ] { deny | permit } [ fragment | logging | source { sour-addr sour-wildcard | any } |
time-range time-range-name | vpn-instance vpn-instance-name ] *
11
Page 18

undo rule rule-id [ fragment | logging | source | time-range | vpn-instance ] *
View
IPv4 basic ACL view
Default level
2: System level
Parameters
rule-id: Specifies a rule ID, in the range of 0 to 65534. If no rule ID is provided when you create an ACL
rule, the system automatically assigns it a rule ID. This rule ID takes the nearest higher multiple of the
numbering step to the current highest rule ID, starting from 0. For example, if the rule numbering step is
5 and the current highest rule ID is 28, the rule is numbered 30.
deny: Denies matching packets.
permit: Allows matching packets to pass.
fragment: Applies the rule only to non-first fragments. A rule without this keyword applies to both
fragments and non-fragments.
logging: Logs matching packets. This function is available only when the application module that uses the
ACL supports the logging function.
source { sour-addr sour-wildcard | any }: Matches a source address. The sour-addr sour-wildcard
arguments represent a source IP address and wildcard mask in dotted decimal notation. A wildcard
mask of zeros specifies a host address. The any keyword represents any source IP address.
time-range time-range-name: Specifies a time range for the rule. The time-range-name argument is a
case-insensitive string of 1 to 32 characters. It must start with an English letter. If the time range is not
configured, the system creates the rule; however, the rule using the time range can take effect only after
you configure the timer range.
vpn-instance vpn-instance-name: Applies the rule to packets in a VPN instance. The vpn-instance-name
argument takes a case-sensitive string of 1 to 31 characters. If no VPN instance is specified, the rule
applies only to non-VPN packets.
Description
Use the rule command to create or edit an IPv4 basic ACL rule. You can edit ACL rules only when the
match order is config.
Use the undo rule command to delete an entire IPv4 basic ACL rule or some attributes in the rule. If no
optional keywords are provided, you delete the entire rule. If optional keywords or arguments are
provided, you delete the specified attributes.
By default, an IPv4 basic ACL does not contain any rule.
Wit hin an ACL, the permit or deny statement of each rule must be unique. If the ACL rule you are creati ng
or editing has the same deny or permit statement as another rule in the ACL, your creation or editing
attempt fails.
To view rules in an ACL and their rule IDs, use the display acl all command.
Related commands: acl, display acl, step, and time-range.
Examples
# Create a rule in IPv4 basic ACL 2000 to deny the packets from any source IP segment but 10.0.0.0/8,
172.17.0.0/16, or 192.168.1.0/24.
<Sysname> system-view
12
Page 19

[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.0.0.0 0.255.255.255
[Sysname-acl-basic-2000] rule permit source 172.17.0.0 0.0.255.255
[Sysname-acl-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Sysname-acl-basic-2000] rule deny source any
rule comment
Syntax
rule rule-id comment text
undo rule rule-id comment
View
IPv4 basic/advanced ACL view, Ethernet frame header ACL view
Default level
2: System level
Parameters
rule-id: Specifies an ACL rule ID, in the range of 0 to 65534. The ACL rule must already exist.
text: Specifies a comment about the ACL rule, a case-sensitive string of 1 to 127 characters.
Description
Use the rule comment command to add a comment about an existing ACL rule or edit its comment to
make the rule easy to understand.
Use the undo rule comment command to delete the ACL rule comment.
By default, an IPv4 ACL rule has no rule comment.
Related commands: display acl.
Examples
# Create a rule in IPv4 basic ACL 2000 and add a comment about the rule.
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule 0 deny source 1.1.1.1 0
[Sysname-acl-basic-2000] rule 0 comment This rule is used on GigabitEthernet 0/1.
step
Syntax
step step-value
undo step
View
IPv4 basic/advanced ACL view, Ethernet frame header ACL view
Default level
2: System level
13
Page 20

Parameters
step-value: ACL rule numbering step, in the range of 1 to 20.
Description
Use the step command to set a rule numbering step for an ACL. The rule numbering step sets the
increment by which the system numbers rules automatically. For example, the default ACL rule numbering
step is 5. If you do not assign IDs to rules you are creating, they are numbered 0, 5, 10, 15, and so on.
The wider the numbering step, the more rules you can insert between two rules. Whenever the step
changes, the rules are renumbered, starting from 0. For example, if there are five rules numbered 5, 10,
13, 15, and 20, changing the step from 5 to 2 causes the rules to be renumbered 0, 2, 4, 6 and 8.
Use the undo step command to restore the default.
The default rule numbering step is 5. After you restore the default numbering step by the undo step
command, the rules are renumbered in steps of 5.
Related commands: display acl.
Examples
# Set the rule numbering step to 2 for IPv4 basic ACL 2000.
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] step 2
time-range
Syntax
time-range time-range-name { start-time to end-time days [ from time1 date1 ] [ to time2 date2 ] | from
time1 date1 [ to time2 date2 ] | to time2 date2 }
undo time-range time-range-name [ start-time to end-time days [ from time1 date1 ] [ to time2 date2 ]
| from time1 date1 [ to time2 date2 ] | to time2 date2 ]
View
System view
Default level
2: System level
Parameters
time-range-name: Specifies a time range name. The name is a case-insensitive string of 1 to 32
characters. It must start with an English letter and to avoid confusion, it cannot be all.
start-time to end-time: Specifies a periodic statement. Both start-time and end-time are in hh:mm format
(24-hour clock), and each value is in the range of 00:00 to 23:59. The end time must be greater than the
start time.
days: Specifies the day or days of the week (in words or digits) on which the periodic statement is valid.
If you specify multiple values, separate each value with a space, and be sure that they do not overlap.
These values can take one of the following forms:
• A digit in the range of 0 to 6, respectively for Sunday, Monday, Tuesday, Wednesday, Thursday,
Friday, and Saturday.
• A day of a week in abbreviated words, sun, mon, tue, wed, thu, fri, and sat.
• working-day for Monday through Friday.
14
Page 21

• off-day for Saturday and Sunday.
• daily for the whole week.
from time1 date1: Specifies the start time and date of an absolute statement. The time1 argument
specifies the time of the day in hh:mm format (24-hour clock). Its value is in the range of 00:00 to 23:59.
The date1 argument specifies a date in MM/DD/YYYY or YYYY/MM/DD format, where MM is the
month of the year in the range of 1 to 12, DD is the day of the month with the range depending on MM,
and YYYY is the year in the calendar in the range of 1970 to 2100. If not specified, the start time is
01/01/1970 00:00 AM, the earliest time available in the system.
to time2 date2: Specifies the end time and date of the absolute time statement. The time2 argument has
the same format as the time1 argument, but its value is in the range of 00:00 to 24:00. The date2
argument has the same format and value range as the date1 argument. The end time must be greater
than the start time. If not specified, the end time is 12/31/2100 24:00 PM, the maximum time available
in the system.
Description
Use the time-range command to configure a time range.
Use the undo time-range command to delete a time range or a statement in the time range.
By default, no time range exists.
You can create multiple statements in a time range. Each time statement can take one of the following
forms:
Examples
• Periodic statement in the start-time to end-time days format. A periodic statement recurs periodically
on a day or days of the week.
• Absolute statement in the from time1 date1 to time2 date2 format. An absolute statement does not
recur.
• Compound statement in the start-time to end-time days from time1 date1 to time2 date2 format. A
compound statement recurs on a day or days of the week only within the specified period. For
example, to create a time range that is active from 08:00 to 12:00 on Monday between January
1, 2010 00:00 and December 31, 2010 23:59, use the time-range test 08:00 to 12:00 mon from
00:00 01/01/2010 to 23:59 12/31/2010 command.
The active period of a time range is calculated as follows:
1. Combining all periodic statements
2. Combining all absolute statements
3. Taking the intersection of the two statement sets as the active period of the time range
You can create a maximum of 256 time ranges, each with a maximum of 32 periodic statements and 12
absolute statements.
Related commands: display time-range.
# Create a periodic time range t1, setting it to be active between 8:00 to 18:00 during working days.
<Sysname> system-view
[Sysname] time-range t1 8:0 to 18:0 working-day
# Create an absolute time range t2, setting it to be active in the whole year of 2010.
<Sysname> system-view
[Sysname] time-range t2 from 0:0 1/1/2010 to 23:59 12/31/2010
15
Page 22

# Create a compound time range t3, setting it to be active from 08:00 to 12:00 on Saturdays and
Sundays of the year 2010.
<Sysname> system-view
[Sysname] time-range t3 8:0 to 12:0 off-day from 0:0 1/1/2010 to 23:59 12/31/2010
# Create a compound time range t4, setting it to be active from 10:00 to 12:00 on Mondays and from
14:00 to 16:00 on Wednesdays in the period of January through June of the year 2010.
<Sysname> system-view
[Sysname] time-range t4 10:0 to 12:0 1 from 0:0 1/1/2010 to 23:59 1/31/2010
[Sysname] time-range t4 14:0 to 16:0 3 from 0:0 6/1/2010 to 23:59 6/30/2010
16
Page 23

Session management commands
application aging-time
Syntax
application aging-time { dns | ftp | msn | qq | sip } time-value
undo application aging-time [ dns | ftp | msn | qq | sip ]
View
System view
Default level
2: System level
Parameters
dns: Specifies the aging time for DNS sessions.
ftp: Specifies the aging time for FTP sessions.
msn: Specifies the aging time for MSN sessions.
qq: Specifies the aging time for QQ sessions.
sip: Specifies the aging time for SIP sessions.
time-value: Aging time, which ranges from 5 seconds to 100000 seconds.
Description
Use the application aging-time command to set the aging time for sessions of an application layer
protocol.
Use the undo application aging-time command to restore the default. If no application layer protocol
type is specified, the command restores the session aging times for all the application layer protocols to
the defaults.
The default session aging times for the application layer protocols is 60 seconds.
Examples
# Set the aging time for FTP sessions to 1800 seconds.
<Sysname> system-view
[Sysname] application aging-time ftp 1800
display session relation-table
Syntax
display session relation-table [ vd-name vd-name ]
View
Any view
17
Page 24

p
Default level
2: System level
Parameters
vd-name vd-name: Displays the relationship table entries of the specified virtual device. The vd-name
argument specifies the name of a virtual device. It is a case-insensitive string of 1 to 20 characters, which
can be numerals, letters and underlines.
Description
Use the display session relation-table command to display relationship table entries.
With no virtual device specified, the command displays the relationship table entries of all virtual
devices.
Examples
# Displays all relationship table entries.
<Sysname> display session relation-table
Local IP/Port Global IP/Port MatchMode
192.168.1.22/99 10.153.2.22/99 Local
APP:QQ Pro:UDP TTL:2000s AllowConn:10
Local IP/Port Global IP/Port MatchMode
192.168.1.100/99 10.153.2.100/99 Local
APP:FTP Pro:TCP TTL:2000s AllowConn:10
Total find: 2
Table 7 Output description
Field Descri
Local IP/Port
Global IP/Port
IP address/port number of the inside network
IP address/ port number of the outside network
Match mode from session table to relationship table, including Local, Global,
and Either.
• Local: Indicates that the source IP address/source port of a new session are
MatchMode
• Global: Indicates that the destination IP address/destination port of a new
• Either: Indicates that the IP/port of a new session are matched against Local
App
Pro
TTL
AllowConn
Total find
Application layer protocol, FTP, MSN, or QQ
Transport layer protocol, TCP, or UDP
Remaining lifetime of the relationship table entry, in seconds.
Number of sessions allowed by the relationship table entry
Total number of found relationship table entries
tion
matched against Local IP/Port in the relation table.
session are matched against Global IP/Port in the relation table.
IP/Port or Global IP/Port in the relation table.
display session statistics
Syntax
display session statistics [ vd-name vd-name ]
18
Page 25

p
View
Any view
Default level
2: System level
Parameters
vd-name vd-name: Displays the session statistics of the specified virtual device. The vd-name argument
specifies the name of a virtual device. It is a case-insensitive string of 1 to 20 characters, which can be
numerals, letters and underlines.
Description
Use the display session statistics command to display statistics about sessions.
With no virtual device specified, the command displays the session statistics of all virtual devices. With
no keyword specified, the command displays all session statistics information. If you specify to display
session statistics on a specified virtual device, the output information does not contain the number of
dropped packets.
Examples
# Display statistics about all sessions.
<Sysname> display session statistics
Current session(s):593951
Current TCP session(s): 0
Half-Open: 0 Half-Close: 0
Current UDP session(s): 593951
Current ICMP session(s): 0
Current RAWIP session(s): 0
Current relation table(s): 50000
Session establishment rate: 184503/s
TCP Session establishment rate: 0/s
UDP Session establishment rate: 184503/s
ICMP Session establishment rate: 0/s
RAWIP Session establishment rate: 0/s
Received TCP: 1538 packet(s) 337567 byte(s)
Received UDP: 86810494849 packet(s) 4340524910260 byte(s)
Received ICMP: 307232 packet(s) 17206268 byte(s)
Received RAWIP: 0 packet(s) 0 byte(s)
Dropped TCP: 0 packet(s) 0 byte(s)
Dropped UDP: 0 packet(s) 0 byte(s)
Dropped ICMP: 0 packet(s) 0 byte(s)
Dropped RAWIP: 0 packet(s) 0 byte(s)
Table 8 Output description
Field Descri
Current session(s) Total number of sessions
19
tion
Page 26
Field Description
Current TCP session(s) Number of TCP sessions
Half-Open Number of TCP sessions in the half-open state
Half-Close Number of TCP sessions in the half-close state
Current UDP session(s) Number of UDP sessions
Current ICMP session(s) Number of ICMP sessions
Current RAWIP session(s) Number of Raw IP sessions
Current relation table(s) Total number of relationship table entries
Session establishment rate Session establishment rate
TCP Session establishment rate Establishment rate of TCP sessions
UDP Session establishment rate Establishment rate of UDP sessions
ICMP Session establishment rate Establishment rate of ICMP sessions
RAWIP Session establishment rate Establishment rate of Raw IP sessions
Received TCP Counts of received TCP packets and bytes
Received UDP Counts of received UDP packets and bytes
Received ICMP Counts of received ICMP packets and bytes
Received RAWIP Counts of received Raw IP packets and bytes
Dropped TCP Counts of dropped TCP packets and bytes
Dropped UDP Counts of dropped UDP packets and bytes
Dropped ICMP Counts of dropped ICMP packets and bytes
Dropped RAWIP Counts of dropped Raw IP packets and bytes
display session table
Syntax
display session table [ vd-name vd-name ] [ source-ip source-ip ] [ destination-ip destination-ip ]
[ verbose ]
View
Any view
Default level
2: System level
Parameters
vd-name vd-name: Displays the sessions of the specified virtual device. The vd-name argument specifies
the name of a virtual device. It is a case-insensitive string of 1 to 20 characters, which can be numerals,
letters and underlines.
source-ip source-ip: Displays the sessions with the specified source IP address.
destination-ip destination-ip: Displays sessions with the specified destination IP address.
20
Page 27

verbose: Displays detailed information about sessions. Without this keyword, the command displays
brief information about the specified sessions.
Description
Use the display session table command to display information about sessions.
• If no argument is specified, the command displays all sessions.
• If no virtual device is specified, the command displays the sessions on all virtual devices.
• If both the source-ip and destination-ip keywords are specified, the command displays only the
Examples
# Display brief information about all sessions.
<Sysname> display session table
Initiator:
Source IP/Port : 192.168.1.18/2048
Dest IP/Port : 192.168.1.55/768
Pro : ICMP(ICMP(1))
VPN-Instance/VLAN ID/VLL ID:
Initiator:
Source IP/Port : 192.168.1.18/1212
Dest IP/Port : 192.168.1.55/23
Pro : TCP(TCP(6))
VPN-Instance/VLAN ID/VLL ID:
Total find: 2
sessions with the specified source and destination IP addresses.
# Display detailed information about all sessions.
<Sysname> display session table verbose
Initiator:
Source IP/Port : 192.168.1.19/137
Dest IP/Port : 192.168.1.255/137
VPN-Instance/VLAN ID/VLL ID:
Responder:
Source IP/Port : 192.168.1.255/137
Dest IP/Port : 192.168.1.19/137
VPN-Instance/VLAN ID/VLL ID:
Pro: UDP(17) App: NBT-name State: UDP-OPEN
Start time: 2009-03-17 10:39:43 TTL: 2s
Root Zone(in): Management
Zone(out): Local
Received packet(s)(Init): 6 packet(s) 468 byte(s)
Received packet(s)(Reply): 0 packet(s) 0 byte(s)
Initiator:
Source IP/Port : 192.168.1.18/1212
Dest IP/Port : 192.168.1.55/23
VPN-Instance/VLAN ID/VLL ID:
Responder:
Source IP/Port : 192.168.1.55/23
Dest IP/Port : 192.168.1.18/1212
VPN-Instance/VLAN ID/VLL ID:
21
Page 28

p
Pro: TCP(6) App: TELNET State: TCP-EST
Start time: 2009-03-17 09:30:33 TTL: 3600s
Root Zone(in): Management
Zone(out): Local
Received packet(s)(Init): 1173 packet(s) 47458 byte(s)
Received packet(s)(Reply): 1168 packet(s) 61845 byte(s)
Total find: 2
Table 9 Output description
Field Descri
Initiator: Session information of the initiator
Responder: Session information of the responder
Pro Transport layer protocol, TCP, UDP, ICMP, or Raw IP
VPN-Instance/VLAN ID/VLL ID
App
VPN that the session belongs to and the VLAN and INLINE that the
session belongs to during Layer 2 forwarding
Application layer protocol, FTP, DNS, MSN or QQ
Unknown indicates protocol type of a non-well-known port
Session status. Possible values are:
tion
• Accelerate
• SYN
• TCP-EST
• FIN
State
• UDP-OPEN
• UDP-READY
• ICMP-OPEN
• ICMP-CLOSED
• RAWIP-OPEN
• RAWIP-READY
Start Time Session establishment time
TTL Remaining lifetime of the session, in seconds.
VD-name Name of virtual device
Zone(in) Security zone (in)
Zone(out) Security zone (out)
Received packet(s)(Init) Counts of packets and bytes from the initiator to the responder
Received packet(s)(Reply) Counts of packets and bytes from the responder to the initiator
Total find Total number of sessions currently found
22
Page 29

reset session
Syntax
reset session [ vd-name vd-name ] [ source-ip source-ip ] [ destination-ip destination-ip ] [ protocol-type
{ icmp | raw-ip | tcp | udp } ] [ source-port source-port ] [ destination-port destination-port ]
[ vpn-instance vpn-instance-name ]
View
User view
Default level
2: System level
Parameters
vd-name vd-name: Clears the sessions on the specified virtual device. The vd-name argument specifies
the name of a virtual device. It is a case-insensitive string of 1 to 20 characters, which can be only
numerals, letters and underlines.
source-ip source-ip: Clears the sessions with the specified source IP address of the initiator.
destination-ip destination-ip: Clears the sessions with the specified destination IP address of the initiator.
protocol-type { icmp | raw-ip | tcp | udp }: Clears the sessions of the specified protocol type. The
protocol types include ICMP, Raw IP, TCP, and UDP.
source-port source-port: Clears the sessions with the specified source port of the initiator.
destination-port destination-port: Clears the sessions with the specified destination port of the initiator.
vpn-instance vpn-instance-name: Clears the sessions of the specified VPN. The vpn-instance-name
argument is a case-sensitive string of 1 to 31 characters.
Description
Use the reset session command to clear sessions.
• If no virtual device is specified, the command clears the sessions on all virtual devices.
• If no VPN instance is specified, the command clears the sessions on the public network.
• If no parameter is specified, the command clears all sessions.
Examples
# Clear all sessions.
<Sysname> reset session
# Clear all sessions with the source IP address as 10.10.10.10 of the initiator.
<Sysname> reset session source-ip 10.10.10.10
reset session statistics
Syntax
reset session statistics [ vd-name vd-name ]
View
User view
23
Page 30

Default level
2: System level
Parameters
vd-name vd-name: Clears the session statistics of the specified virtual device. The vd-name argument
specifies the name of a virtual device. It is a case-insensitive string of 1 to 20 characters, which can be
numerals, letters and underlines.
Description
Use the reset session statistics command to clear session statistics.
If no virtual device is specified, the command clears the session statistics on all virtual devices.
Examples
# Clear all session statistics.
<Sysname> reset session statistics
session aging-time
Syntax
session aging-time { accelerate | fin | icmp-closed | icmp-open | rawip-open | rawip-ready | syn |
tcp-est | udp-open | udp-ready } time-value
undo session aging-time [ accelerate | fin | icmp-closed | icmp-open | rawip-open | rawip-ready |
syn | tcp-est | udp-open | udp-ready ]
View
System view
Default level
2: System level
Parameters
accelerate: Specifies the aging time for the sessions in the accelerate queue.
fin: Specifies the aging time for the TCP sessions in the FIN_WAIT state.
icmp-closed: Specifies the aging time for the ICMP sessions in the CLOSED state.
icmp-open: Specifies the aging time for the ICMP sessions in the OPEN state.
rawip-open: Specifies the aging time for the sessions in the RAWIP_OPEN state.
rawip-ready: Specifies the aging time for the sessions in the RAWIP_READY state.
syn: Specifies the aging time for the TCP sessions in the SYN_SENT or SYN_RCV state.
tcp-est: Specifies the aging time for the TCP sessions in the ESTABLISHED state.
udp-open: Specifies the aging time for the UDP sessions in the OPEN state.
udp-ready: Specifies the aging time for the UDP sessions in the READY state.
time-value: Aging time, in seconds in the range of 5 to 10000.
Description
Use the session aging-time command to set the aging time for sessions of a specified protocol that are
in a specified state.
24
Page 31

Use the undo session aging-time command to restore the default. If no keyword is specified, the
command restores the session aging times for all protocol states to the defaults.
The defaults value is 30 seconds.
Examples
# Set the aging time for TCP sessions in the SYN_SENT or SYN_RCV state to 60 seconds.
<Sysname> system-view
[Sysname] session aging-time syn 60
session checksum
Syntax
session checksum { all | { icmp | tcp | udp } * }
undo session checksum { all | { icmp | tcp | udp } * }
View
System view
Default level
2: System level
Parameters
all: Enables checksum verification for TCP, UDP, and ICMP packets.
icmp: Enables checksum verification for ICMP packets.
tcp: Enables checksum verification for TCP packets.
udp: Enables checksum verification for UDP packets.
Description
Use the session checksum command to enable checksum verification for protocol packets.
Use the undo session checksum command to disable checksum verification.
By default, checksum verification is disabled.
Examples
# Enable checksum verification for UDP packets.
<Sysname> system-view
[Sysname] session checksum udp
session persist acl
Syntax
session persist acl acl-number [ aging-time time-value ]
undo session persist
View
System view
Default level
2: System level
25
Page 32

Parameters
acl-number: ACL number, in the range 2000 to 3999.
aging-time time-value: Specifies the aging time for persistent sessions, in hours. The value of the
time-value argument is in the range of 0 to 360 and defaults to 24. A value of 0 means the persistent
sessions are never aged.
Description
Use the session persist acl command to specify the persistent session rule. All sessions permitted by the
specified ACL are considered persistent sessions.
Use the undo session persist command to remove the configuration.
By default, no persistent session rule is specified.
Persistent sessions will not be removed because they are not matched with any packets within the aging
time. You can manually remove such sessions when necessary.
A persistent session rule can reference only one ACL.
Related commands: reset session.
Examples
# Configure all sessions matching ACL 2000 as persistent sessions, setting the aging time of the sessions
to 72 hours.
<Sysname> system-view
[Sysname] session persist acl 2000 aging-time 72
26
Page 33

Connection limit configuration commands
connection-limit apply policy
Syntax
connection-limit apply policy policy-number
undo connection-limit apply policy policy-number
View
System view
Default level
2: System level
Parameters
policy-number: Number for an existing connection limit policy, which can only be 0.
Description
Use the connection-limit apply policy command to apply a connection limit policy.
Use the undo connection-limit apply policy command to remove the application.
If a connection limit policy is applied, you cannot add, remove, or modify the conneciton limit rules in the
connection limit policy view.
A conneciton limit policy to be applied must contain at least one limit rule.
Related commands: connection-limit policy.
Examples
# Apply connection limit policy 0.
<Sysname> system-view
[Sysname] connection-limit apply policy 0
connection-limit policy
Syntax
connection-limit policy policy-number
undo connection-limit policy { policy-number | all }
View
System view
Default level
2: System level
Parameters
policy-number: Connection limit policy number, which can only be 0.
all: Specifies all connection limit policies.
27
Page 34

Description
Use the connection-limit policy command to create a connection limit policy and enter connection limit
policy view.
Use the undo connection-limit policy command to delete a specific or all connection limit policies.
A connection limit policy contains a set of rules that limit the number of connections of a specific user. By
default, a connection limit policy uses the default connection limit settings.
When creating a connection limit policy, you must assign it a unique number. Polices are matched by
number in descending order.
After applying a connection limit policy in system view, you cannot modify, add, or remove connection
limit rules in the policy.
Examples
# Create a connection limit policy numbered 0 and enter its view.
<Sysname> system-view
[Sysname] connection-limit policy 0
[Sysname-connection-limit-policy-0]
display connection-limit policy
Syntax
display connection-limit policy { policy-number | all }
View
Any view
Default level
1: Monitor level
Parameters
policy-number: Connection limit policy number, which can only be 0.
all: Displays all connection limit policies.
Description
Use the display connection-limit policy command to display information about a specific or all
connection limit policies.
Related commands: limit.
Examples
# Display information about all connection limit policies.
<Sysname> display connection-limit policy all
There is 1 policy:
Connection-limit policy 0, refcount 0 ,3 limits
limit 1 acl 2000 per-source amount 1111 10
limit 2 acl 2001 per-destination amount 300 20
limit 3 acl 2002 per-service amount 400 50
# Display information about all connection limit policies.
<Sysname> display connection-limit policy all
There are 1 policies:
28
Page 35
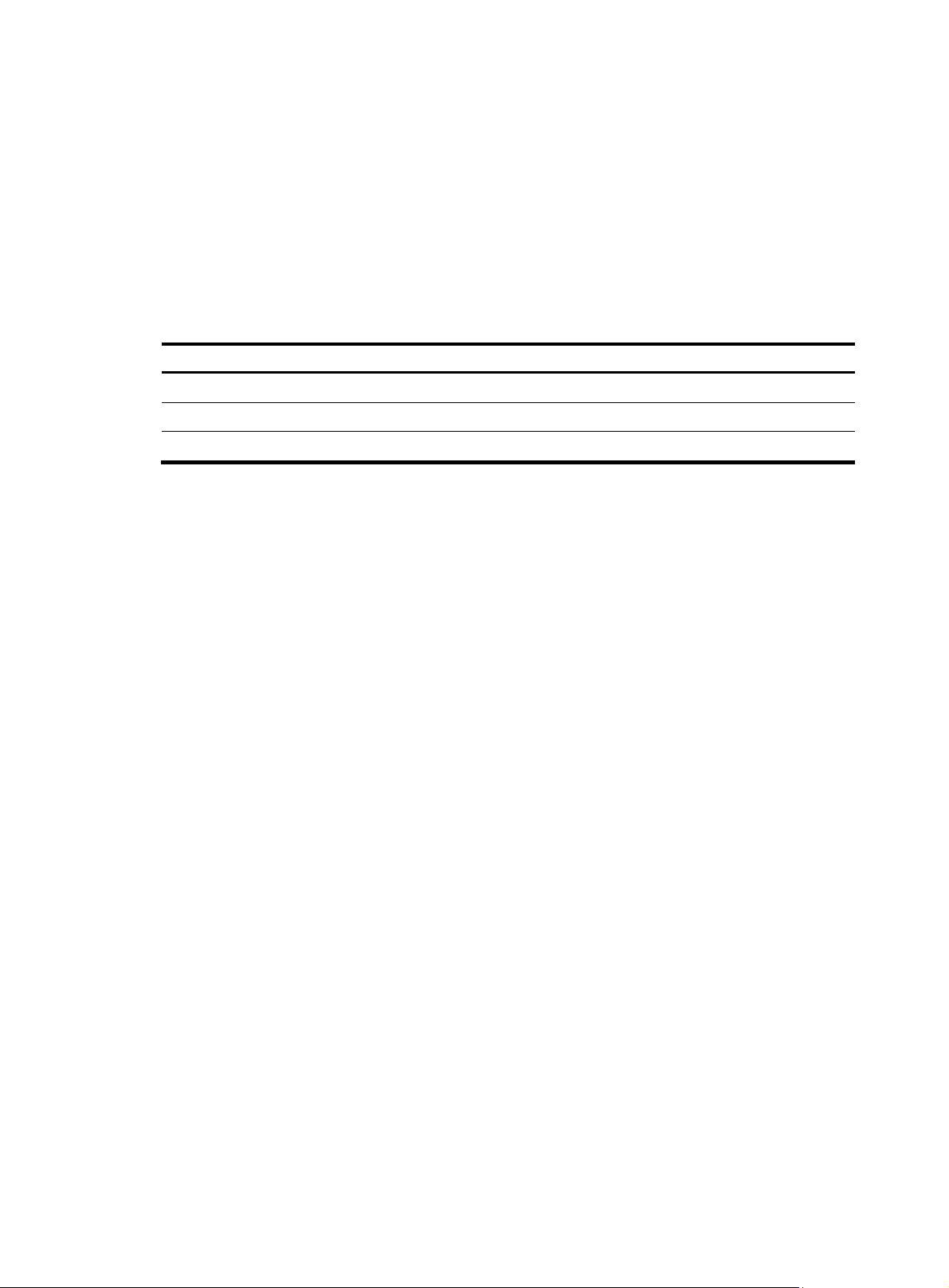
p
Connection-limit policy 0, refcount 1, 2 limits
limit 0 source any amount dns 100 http 200 tcp 300 other 400 rate 100 shared
limit 1 source 1.1.1.0 24 amount tcp 100 bandwidth 200 shared
# Display information about all connection limit policies.
<Sysname> display connection-limit policy all
There are 1 policies:
Connection-limit policy 0, refcount 0, 1 limit
limit 0 source ip 3.3.3.0 24 source-vpn vpn1 destination ip any protocol tcp
max-connections 200 per-source
Table 10 Output description
Field Descri
Connection-limit policy Number of the connection limit policy
refcount 1, 2 limits Number of times that the policy is applied and number of rules in the policy.
limit xxx Rule in the policy. Refer to the limit command for details.
limit
Syntax
limit limit-id { source ip { ip-address mask-length | any } [ source-vpn src-vpn-name ] | destination ip
{ ip-address mask-length | any } [ destination-vpn dst-vpn-name ] } * protocol { dns | http | ip | tcp |
udp } max-connections max-num [ per-destination | per-source | per-source-destination ]
undo limit limit-id
View
Connection limit policy view
Default level
2: System level
Parameters
tion
limit-id: ID of a rule in the connection limit policy, which can only be 0.
source ip: Specifies the source IP address of the connections to be limited.
ip-address mask-length: IP address and its mask length. The mask-length argument is in the range of 1 to
32.
any: Specifies all IP addresses on the specified network or the public network. For example, source ip any
specifies all hosts on the source network.
source-vpn src-vpn-name: Specifies a source MPLS VPN by its instance name a case-sensitive string of 1
to 31 characters. Absence of the option indicates the public network.
destination ip: Specifies the destination IP address of the connections to be limited.
destination-vpn dst-vpn-name: Specifies a destination MPLS VPN by its instance name, a case-sensitive
string of 1 to 31 characters. Absence of the option indicates the public network.
protocol: Specifies connections of a protocol.
• dns: Specifies connections of the DNS protocol.
29
Page 36

• http: Specifies connections of the HTTP protocol.
• ip: Specifies connections of the IP protocol.
• tcp: Specifies connections of the TCP protocol.
• udp: Specifies connections of the UDP protocol.
max-connections max-num: Maximum number of the connections in the range of 0 to 1000000. .
per-destination: Limits connections by destination address.
per-source: Limits connections by source address.
per-source-destination: Limits connections by source-desitnation address pair.
Description
Use the limit command to configure an IP address-based conneciton limit policy rule.
Use the undo limit command to remove a conneciton limit policy rule.
Any two rules of one policy must have different rule criteria.
The connection limit rules become invalid if the VPN instance with which the rules are associated are
removed.
The connection limit rules in a policy are matched in ascending order of rule ID. If the source addresses,
destination addresses, or protocols in two rules are overlapped, the first matched rule takes effect.
Therefore, take the match order into consideration when assigning the rules IDs. HP recommends
arranging the rule by limit granularity and limit range in ascending order.
Examples
Related commands: connection-limit policy, display connection-limit policy.
# Configure connection limit rule 1 for policy 1 to li m i t T C P c o n n e c t i o n s s o u r c e d f r o m 1.1.1.1 w i t h t h e
upper connection limit of 200.
<Sysname> system-view
[Sysname] connection-limit policy 0
[Sysname-connection-limit-policy-0] limit 1 source ip 1.1.1.1 32 protocol tcp
max-connections 200
# Configure connection limit rule 2 to limit UDP connections destined to 2.2.2.2 with the upper
connection limit of 200.
[Sysname-connection-limit-policy-0] limit 2 destination ip 2.2.2.2 32 protocol udp
max-connections 200
# Configure connection limit rule 3 to limit IP connections sourced from the segment 1.1.1.0/24 with the
upper connection limit of 200.
[Sysname-connection-limit-policy-1] limit 3 source ip 1.1.1.0 24 protocol ip
max-connections 200 per-source
# Configure connection limit rule 4 to limit IP connections destined to the segment 2.2.2.0/24 with the
upper connection limit of 200.
[Sysname-connection-limit-policy-0] limit 4 destination ip 2.2.2.0 24 protocol ip
max-connections 200 per-destination
# Configure connection limit rule 5 to limit IP connections from vpn1 to vpn2 with the upper connection
limit of 200.
[Sysname-connection-limit-policy-0] limit 5 source ip any source-vpn vpn1 destination ip
any destination-vpn vpn2 protocol ip max-connections 200
30
Page 37

Portal configuration commands
display portal acl
Syntax
display portal acl { all | dynamic | static } interface interface-type interface-number
View
Any view
Default level
1: Monitor level
Parameters
all: Displays all portal access control lists (ACLs), including dynamic ones and static ones.
dynamic: Displays dynamic portal ACLs, namely, ACLs generated after a user passes portal
authentication.
static: Displays static portal ACLs, namely, ACLs generated by related configurations.
interface interface-type interface-number: Displays the ACLs on the specified interface.
Description
Use the display portal acl command to display the ACLs on a specific interface.
Examples
# Display all ACLs on interface GigabitEthernet 0/0.
<Sysname> display portal acl all interface gigabitethernet 0/0
GigabitEthernet0/0 portal ACL rule:
Rule 0
Inbound interface : GigabitEthernet0/0
Type : static
Action : permit
Source:
IP : 0.0.0.0
Mask : 0.0.0.0
MAC : 0000-0000-0000
Interface : any
VLAN : 0
Protocol : 0
Destination:
IP : 192.168.0.111
Mask : 255.255.255.255
Rule 1
Inbound interface : GigabitEthernet0/0
Type : static
Action : redirect
31
Page 38
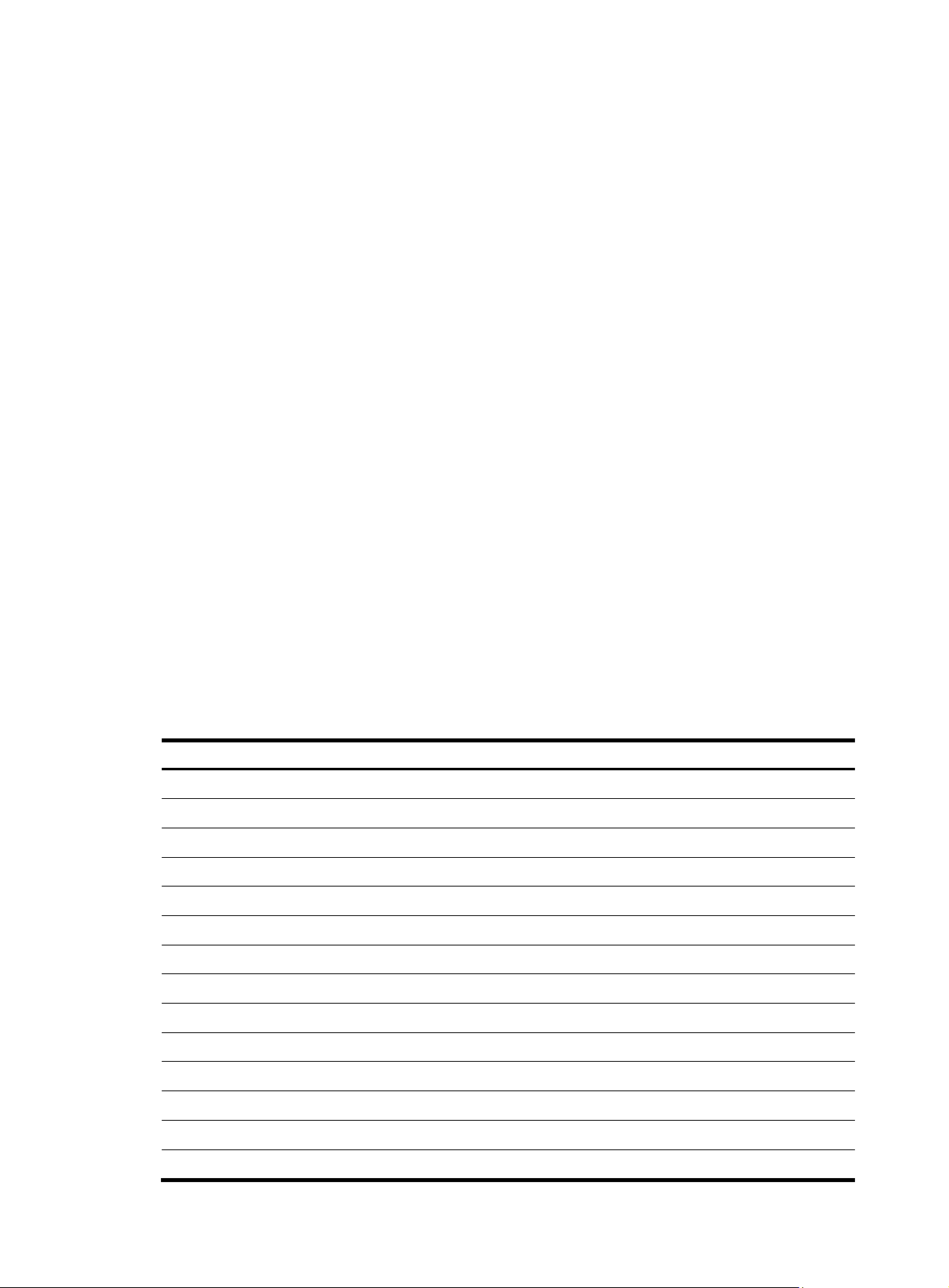
p
Source:
IP : 0.0.0.0
Mask : 0.0.0.0
MAC : 0000-0000-0000
Interface : any
VLAN : 2
Protocol : 6
Destination:
IP : 0.0.0.0
Mask : 0.0.0.0
Rule 2
Inbound interface : GigabitEthernet0/0
Type : dynamic
Action : permit
Source:
IP : 2.2.2.2
Mask : 255.255.255.255
MAC : 000d-88f8-0eab
Interface : GigabitEthernet0/0
VLAN : 0
Protocol : 0
Destination:
IP : 0.0.0.0
Mask : 0.0.0.0
Author ACL:
Number : 3001
Table 11 Output description
Field Descri
Rule Sequence number of the generated ACL, which is numbered from 0 in ascending order
Inbound interface Interface to which portal ACLs are bound
Type Type of the portal ACL
Action Match action in the portal ACL
Source Source information in the portal ACL
IP Source IP address in the portal ACL
Mask Subnet mask of the source IP address in the portal ACL
MAC Source MAC address in the portal ACL
Interface Source interface in the portal ACL
VLAN Source VLAN in the portal ACL
Protocol Protocol type in the portal ACL
Destination Destination information in the portal ACL
IP Destination IP address in the portal ACL
Mask Subnet mask of the destination IP address in the portal ACL
tion
32
Page 39
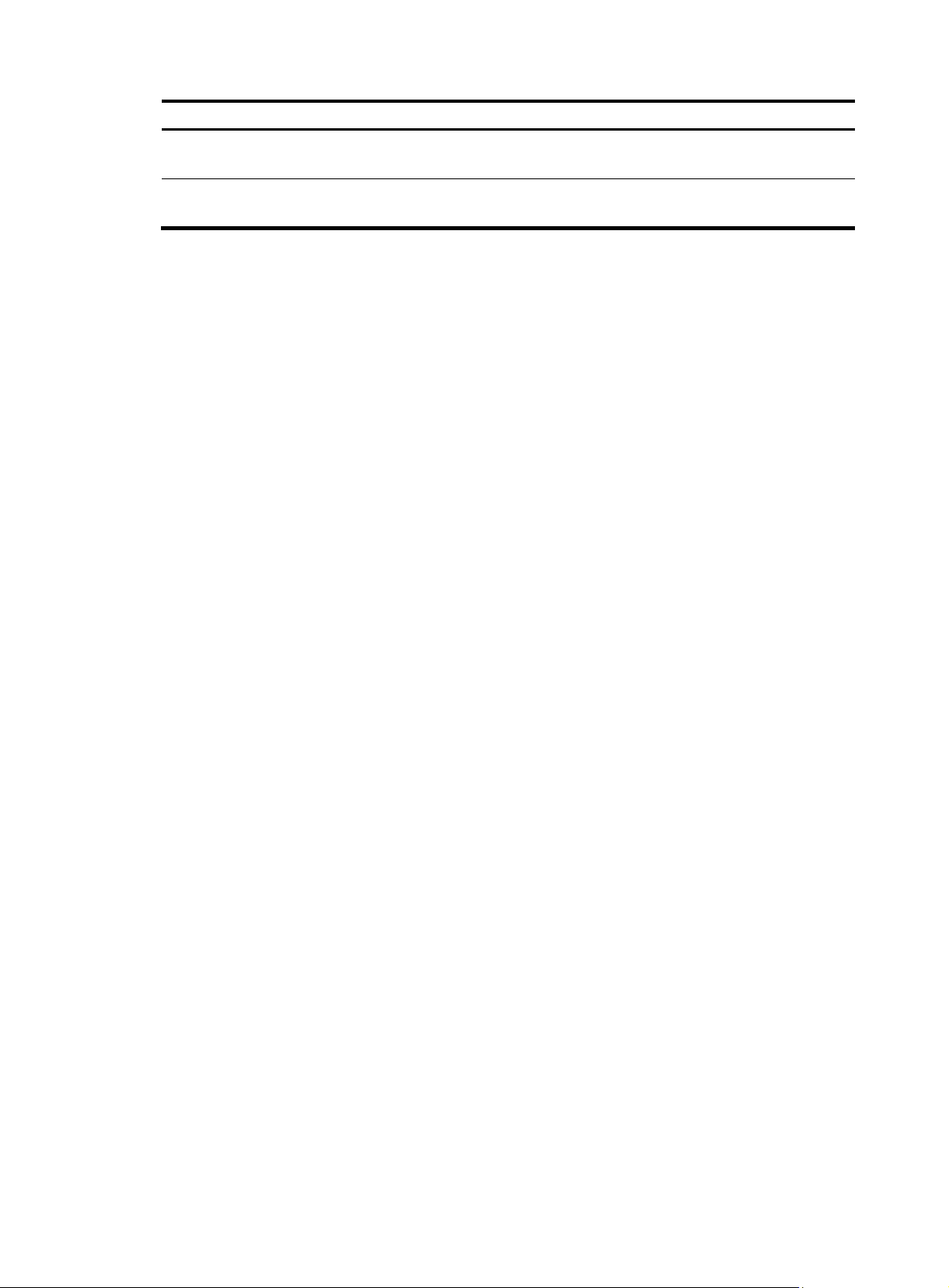
Field Description
Author ACL
Number
Authorization ACL of portal ACL. It is displayed only when the Type field has a value of
dynamic.
Authorization ACL number assigned by the server. None indicates that the server did not
assign any ACL.
display portal connection statistics
Syntax
display portal connection statistics { all | interface interface-type interface-number }
View
Any view
Default level
1: Monitor level
Parameters
all: Specifies all interfaces.
interface interface-type interface-number: Specifies an interface by its type and number.
Description
Examples
Use the display portal connection statistics command to display portal connection statistics on a specific
interface or all interfaces.
# Display portal connection statistics on interface GigabitEthernet 0/0.
<Sysname> display portal connection statistics interface GigabitEthernet0/0
---------------Interface: GigabitEthernet0/0---------------------- User state statistics:
State-Name User-Num
VOID 0
DISCOVERED 0
WAIT_AUTHEN_ACK 0
WAIT_AUTHOR_ACK 0
WAIT_LOGIN_ACK 0
WAIT_ACL_ACK 0
WAIT_NEW_IP 0
WAIT_USERIPCHANGE_ACK 0
ONLINE 1
WAIT_LOGOUT_ACK 0
WAIT_LEAVING_ACK 0
Message statistics:
Msg-Name Total Err Discard
MSG_AUTHEN_ACK 3 0 0
MSG_AUTHOR_ACK 3 0 0
MSG_LOGIN_ACK 3 0 0
33
Page 40
p
MSG_LOGOUT_ACK 2 0 0
MSG_LEAVING_ACK 0 0 0
MSG_CUT_REQ 0 0 0
MSG_AUTH_REQ 3 0 0
MSG_LOGIN_REQ 3 0 0
MSG_LOGOUT_REQ 2 0 0
MSG_LEAVING_REQ 0 0 0
MSG_ARPPKT 0 0 0
MSG_TMR_REQAUTH 1 0 0
MSG_TMR_AUTHEN 0 0 0
MSG_TMR_AUTHOR 0 0 0
MSG_TMR_LOGIN 0 0 0
MSG_TMR_LOGOUT 0 0 0
MSG_TMR_LEAVING 0 0 0
MSG_TMR_NEWIP 0 0 0
MSG_TMR_USERIPCHANGE 0 0 0
MSG_PORT_REMOVE 0 0 0
MSG_VLAN_REMOVE 0 0 0
MSG_IF_REMOVE 6 0 0
MSG_L3IF_SHUT 0 0 0
MSG_IP_REMOVE 0 0 0
MSG_ALL_REMOVE 1 0 0
MSG_IFIPADDR_CHANGE 0 0 0
MSG_SOCKET_CHANGE 8 0 0
MSG_NOTIFY 0 0 0
MSG_SETPOLICY 0 0 0
MSG_SETPOLICY_RESULT 0 0 0
Table 12 Output description
Field Descri
User state statistics Statistics on portal users
State-Name Name of a user state
User-Num Number of users
VOID Number of users in void state
DISCOVERED Number of users in discovered state
WAIT_AUTHEN_ACK Number of users in wait_authen_ack state
WAIT_AUTHOR_ACK Number of users in wait_author_ack state
WAIT_LOGIN_ACK Number of users in wait_login_ack state
WAIT_ACL_ACK Number of users in wait_acl_ack state
WAIT_NEW_IP Number of users in wait_new_ip state
WAIT_USERIPCHANGE_ACK Number of users wait_useripchange_ack state
ONLINE Number of users in online state
WAIT_LOGOUT_ACK Number of users in wait_logout_ack state
WAIT_LEAVING_ACK Number of users in wait_leaving_ack state
tion
34
Page 41
Field Description
Message statistics Statistics on messages
Msg-Name Message type
Total Total number of messages
Err Number of erroneous messages
Discard Number of discarded messages
MSG_AUTHEN_ACK Authentication acknowledgment message
MSG_AUTHOR_ACK Authorization acknowledgment message
MSG_LOGIN_ACK Accounting acknowledgment message
MSG_LOGOUT_ACK Accounting-stop acknowledgment message
MSG_LEAVING_ACK Leaving acknowledgment message
MSG_CUT_REQ Cut request message
MSG_AUTH_REQ Authentication request message
MSG_LOGIN_REQ Accounting request message
MSG_LOGOUT_REQ Accounting-stop request message
MSG_LEAVING_REQ Leaving request message
MSG_ARPPKT ARP message
MSG_TMR_REQAUTH Authentication request timeout message
MSG_TMR_AUTHEN Authentication timeout message
MSG_TMR_AUTHOR Authorization timeout message
MSG_TMR_LOGIN Accounting-start timeout message
MSG_TMR_LOGOUT Accounting-stop timeout message
MSG_TMR_LEAVING Leaving timeout message
MSG_TMR_NEWIP Public IP update timeout message
MSG_TMR_USERIPCHANGE User IP change timeout message
MSG_PORT_REMOVE Users-of-a-Layer-2-port-removed message
MSG_VLAN_REMOVE VLAN user removed message
MSG_IF_REMOVE Users-of-a-Layer-3-interface-removed message
MSG_L3IF_SHUT Layer 3 interface shutdown message
MSG_IP_REMOVE User-with-an-IP-removed message
MSG_ALL_REMOVE All-users-removed message
MSG_IFIPADDR_CHANGE Interface IP address change message
MSG_SOCKET_CHANGE Socket change message
MSG_NOTIFY Notification message
MSG_SETPOLICY Set policy message for assigning security ACL
MSG_SETPOLICY_RESULT Set policy response message
35
Page 42

p
display portal free-rule
Syntax
display portal free-rule [ rule-number ]
View
Any view
Default level
1: Monitor level
Parameters
rule-number: Number of a portal-free rule, in the range of 0 to 15.
Description
Use the display portal free-rule command to display information about a specific portal-free rule or all
portal-free rules.
Related commands: portal free-rule.
Examples
# Display information about portal-free rule 1.
<Sysname> display portal free-rule 1
Rule-Number 1:
Source:
IP : 2.2.2.0
Mask : 255.255.255.0
MAC : 0000-0000-0000
Interface : any
Vlan : 0
Destination:
IP : 0.0.0.0
Mask : 0.0.0.0
Table 13 Output description
Field Descri
Rule-Number Number of the portal-free rule
Source Source information in the portal-free rule
IP Source IP address in the portal-free rule
Mask Subnet mask of the source IP address in the portal-free rule
MAC Source MAC address in the portal-free rule
Interface Source interface in the portal-free rule
Vlan Source VLAN in the portal-free rule
Destination Destination information in the portal-free rule
IP Destination IP address in the portal-free rule
Mask Subnet mask of the destination IP address in the portal-free rule
tion
36
Page 43

p
display portal interface
Syntax
display portal interface interface-type interface-number
View
Any view
Default level
1: Monitor level
Parameters
interface-type interface-number: Specifies an interface by its type and number.
Description
Use the display portal interface command to display the portal configuration of an interface.
Examples
# Display the portal configuration of interface GigabitEthernet 0/0.
<Sysname> display portal interface gigabitethernet0/0
Interface portal configuration:
GigabitEthernet0/0: Portal running
Portal server: servername
Authentication type: Direct
Portal backup-group: 1
Authentication domain: my-domain
Authentication network:
address : 0.0.0.0 mask : 0.0.0.0
Table 14 Output description
Field Descri
Interface portal configuration Portal configuration on the interface
GigabitEthernet0/0 Status of the portal feature on the interface, disabled, enabled, or running.
Portal server Portal server referenced by the interface
Authentication type Authentication mode enabled on the interface
Number of the portal group to which the interface belongs.
Portal backup-group
Authentication domain Mandatory authentication domain of the interface
Authentication network Information of the portal authentication subnet
address IP address of the portal authentication subnet
mask Subnet mask of the IP address of the portal authentication subnet
If the interface does not belong to any portal group, None will be
displayed.
tion
37
Page 44

p
display portal server
Syntax
display portal server [ server-name ]
View
Any view
Default level
1: Monitor level
Parameters
server-name: Name of a portal server, a case-sensitive string of 1 to 32 characters.
Description
Use the display portal server command to display information about a specific portal server or all portal
servers.
Related commands: portal server.
Examples
# Display information about portal server aaa.
<Sysname> display portal server aaa
Portal server:
1)aaa:
IP : 192.168.0.111
Key : portal
Port : 50100
URL : http://192.168.0.111
Table 15 Output description
Field Descri
1) Number of the portal server
aaa Name of the portal server
IP IP address of the portal server
Key
Port Listening port on the portal server
URL
Key for portal authentication
Not configured will be displayed if no key is configured.
Address the packets are to be redirected to
Not configured will be displayed if no address is configured.
tion
display portal server statistics
Syntax
display portal server statistics { all | interface interface-type interface-number }
View
Any view
38
Page 45

p
Default level
1: Monitor level
Parameters
all: Specifies all interfaces.
interface interface-type interface-number: Specifies an interface by its type and name.
Description
Use the display portal server statistics command to display portal server statistics on a specific interface
or all interfaces.
Note that with the all keyword specified, the command displays portal server statistics by interface and
therefore statistics about a portal server referenced by more than one interface may be displayed
repeatedly.
Examples
# Display portal server statistics on GigabitEthernet 0/0.
<Sysname> display portal server statistics interface gigabitethernet 0/0
---------------Interface: GigabitEthernet0/0--------------------- Server name: st
Invalid packets: 0
Pkt-Name Total Discard Checkerr
REQ_CHALLENGE 3 0 0
ACK_CHALLENGE 3 0 0
REQ_AUTH 3 0 0
ACK_AUTH 3 0 0
REQ_LOGOUT 1 0 0
ACK_LOGOUT 1 0 0
AFF_ACK_AUTH 3 0 0
NTF_LOGOUT 1 0 0
REQ_INFO 6 0 0
ACK_INFO 6 0 0
NTF_USERDISCOVER 0 0 0
NTF_USERIPCHANGE 0 0 0
AFF_NTF_USERIPCHANGE 0 0 0
ACK_NTF_LOGOUT 1 0 0
Table 16 Output description
Field Descri
Interface Interface referencing the portal server
Server name Name of the portal server
Invalid packets Number of invalid packets
Pkt-Name Packet type
Total Total number of packets
Discard Number of discarded packets
Checkerr Number of erroneous packets
REQ_CHALLENGE Challenge request message the portal server sends to the access device
tion
39
Page 46

Field Description
ACK_CHALLENGE
REQ_AUTH Authentication request message the portal server sends to the access device
ACK_AUTH
REQ_LOGOUT Logout request message the portal server sends to the access device
ACK_LOGOUT Logout acknowledgment message the access device sends to the portal server
AFF_ACK_AUTH
NTF_LOGOUT Forced logout notification message the access device sends to the portal server
REQ_INFO Information request message
ACK_INFO Information acknowledgment message
NTF_USERDISCOVER
NTF_USERIPCHANGE
AFF_NTF_USERIPCHANGE
Challenge acknowledgment message the access device sends to the portal
server
Authentication acknowledgment message the access device sends to the portal
server
Affirmation message the portal server sends to the access device after
receiving an authentication acknowledgement message
User discovery notification message the portal server sends to the access
device
User IP change notification message the access device sends to the portal
server
User IP change success notification message the portal server sends to the
access device
ACK_NTF_LOGOUT Forced logout acknowledgment message from the portal server
display portal tcp-cheat statistics
Syntax
display portal tcp-cheat statistics
View
Any view
Default level
1: Monitor level
Parameters
None
Description
Use the display portal tcp-cheat statistics command to display TCP spoofing statistics.
Examples
# Display TCP spoofing statistics.
<Sysname> display portal tcp-cheat statistics
TCP Cheat Statistic:
Total Opens: 0
Resets Connections: 0
Current Opens: 0
Packets Received: 0
40
Page 47

p
Packets Sent: 0
Packets Retransmitted: 0
Packets Dropped: 0
HTTP Packets Sent: 0
Connection State:
SYN_RECVD: 0
ESTABLISHED: 0
CLOSE_WAIT: 0
LAST_ACK: 0
FIN_WAIT_1: 0
FIN_WAIT_2: 0
CLOSING: 0
Table 17 Output description
Field Descri
TCP Cheat Statistic TCP spoofing statistics
Total Opens Total number of opened connections
Resets Connections Number of connections reset through RST packets
Current Opens Number of connections currently being setting up
Packets Received Number of received packets
Packets Sent Number of sent packets
Packets Retransmitted Number of retransmitted packets
Packets Dropped Number of dropped packets
HTTP Packets Sent Number of HTTP packets sent
Connection State Statistics of connections in various state
ESTABLISHED Number of connections in ESTABLISHED state
CLOSE_WAIT Number of connections in CLOSE_WAIT state
LAST_ACK Number of connections in LAST-ACK state
FIN_WAIT_1 Number of connections in FIN_WAIT_1 state
FIN_WAIT_2 Number of connections in FIN_WAIT_2 state
tion
CLOSING Number of connections in CLOSING state
display portal user
Syntax
display portal user { all | interface interface-type interface-number }
View
Any view
Default level
1: Monitor level
41
Page 48
p
Parameters
all: Specifies all interfaces.
interface interface-type interface-number: Specifies an interface by its type and name.
Description
Use the display portal user command to display information about portal users on a specific interface or
all interfaces.
Examples
# Display information about portal users on all interfaces.
<Sysname> display portal user all
Index:2
State:ONLINE
SubState:INVALID
ACL:NONE
Work-mode:Stand-alone
MAC IP Vlan Interface
-------------------------------------------------------------------- 000d-88f8-0eab 2.2.2.2 0 GigabitEthernet0/0
Index:3
State:ONLINE
SubState:INVALID
ACL:3000
Work-mode:Primary
MAC IP Vlan Interface
-------------------------------------------------------------------- 000d-88f8-0eac 2.2.2.3 0 GigabitEthernet0/0
Total 2 user(s) matched, 2 listed.
Table 18 Output description
Field Descri
Index Index of the portal user
State Current status of the portal user
SubState Current sub-status of the portal user
ACL Authorization ACL of the portal user
Working mode of the portal user, which can be:
Work-mode
• Primary
tion
• Secondary
• Stand-alone
MAC MAC address of the portal user
IP IP address of the portal user
Vlan VLAN to which the portal user belongs
Interface Interface to which the portal user is attached
Total 2 user(s) matched, 2 listed Total number of portal users
42
Page 49

portal auth-network
Syntax
portal auth-network network-address { mask-length | mask }
undo portal auth-network { network-address | all }
View
Interface view
Default level
2: System level
Parameters
network-address: IP address of the authentication subnet.
mask-length: Length of the subnet mask, in the range of 0 to 32.
mask: Subnet mask, in dotted decimal notation.
all: Specifies all authentication subnets.
Description
Use the portal auth-network command to configure a portal authentication subnet.
Use the undo portal auth-network command to remove a specific portal authentication subnet or all
portal authentication subnets.
This command is only applicable for Layer 3 authentication. The portal authentication subnet for direct
authentication is any source IP address, and the portal authentication subnet for re-DHCP authentication
is the one determined by the private IP address of the interface.
By default, the portal authentication subnet is 0.0.0.0/0, meaning that users in all subnets are to be
authenticated.
Examples
# Configure a portal authentication subnet of 10.10.10.0/24.
<Sysname> system-view
[Sysname] interface gigabitethernet0/0
[Sysname-GigabitEthernet0/0] portal auth-network 10.10.10.0 24
portal delete-user
Syntax
portal delete-user { ip-address | all | interface interface-type interface-number }
View
System view
Default level
2: System level
Parameters
ip-address: IP address of a user.
all: Logs out all users.
43
Page 50

interface interface-type interface-number: Logs out all users on the specified interface.
Description
Use the portal delete-user command to log out users.
Related commands: display portal user.
Examples
# L o g o u t u s e r 1.1.1.1.
<Sysname> system-view
[Sysname] portal delete-user 1.1.1.1
portal domain
Syntax
portal domain domain-name
undo portal domain
View
Interface view
Default level
2: System level
Parameters
domain-name: ISP domain name, a case-insensitive string of 1 to 24 characters. The domain specified by
this argument must already exist.
Description
Use the portal domain command to specify an authentication domain for portal users on an interface.
Then, the device uses the specified authentication domain for authentication, authorization and
accounting (AAA) of the portal users on the interface.
Use the undo portal domain command to restore the default.
By default, no authentication domain is specified for an interface.
Related commands: display portal interface.
Examples
# Configure the authentication domain for portal users on GigabitEthernet 0/0 as my-domain.
<Sysname> system-view
[Sysname] interface gigabitethernet0/0
[Sysname-GigabitEthernet0/0] portal domain my-domain
portal free-rule
Syntax
portal free-rule rule-number { destination { any | ip { ip-address mask { mask-length | netmask } | any } }
| source { any | [ interface interface-type interface-number | ip { ip-address mask { mask-length |
netmask } | any } | mac mac-address | vlan vlan-id ] * } } *
undo portal free-rule { rule-number | all }
44
Page 51

View
System view
Default level
2: System level
Parameters
rule-number: Number for the portal-free rule, in the range of 0 to 15.
any: Imposes no limitation on the previous keyword.
ip ip-address: Specifies an IP address.
mask { mask-length | netmask }: Specifies the mask of the IP address, which can be in dotted decimal
notation or an integer in the range of 0 to 32.
interface interface-type interface-number: Specifies a source interface.
mac mac-address: Specifies a source MAC address in the format of H-H-H.
vlan vlan-id: Specifies a source VLAN ID.
all: Specifies all portal-free rules.
Description
Examples
Use the portal free-rule command to configure a portal-free rule and specify the source filtering condition
and/or destination filtering condition.
Use the undo portal free-rule command to remove a specific portal-free rule or all portal-free rules.
When you use the command, follow these guidelines:
• If you specify both a source IP address and a source MAC address in a portal-free rule, the IP
address must be a host address with a 32-bit mask. Otherwise, the specified MAC address does not
take effect.
• If you specify both a VLAN and an interface in a portal-free rule, the interface must belong to the
VLAN.
• You cannot configure a portal-free rule to have the same filtering criteria as that of an existing one.
When attempted, the system prompts that the rule already exists.
• No matter whether portal authentication is enabled on an interface, you can only add or remove a
portal-free rule. You cannot modify a portal-free rule.
Related commands: display portal free-rule.
# Configure a portal-free rule, allowing any packet whose source IP address is 10.10.10.1/24 and source
interface is GigabitEthernet 0/0 to bypass portal authentication.
<Sysname> system-view
[Sysname] portal free-rule 15 source ip 10.10.10.1 mask 24 interface gigabitethernet0/0
destination ip any
portal max-user
Syntax
portal max-user max-number
undo portal max-user
45
Page 52

View
System view
Default level
2: System level
Parameters
max-number: Maximum number of online portal users allowed in the system.
Description
Use the portal max-user command to set the maximum number of online portal users allowed in the
system.
Use the undo portal max-user command to restore the default.
By default, the maximum number of portal users allowed on the device is 512.
If the maximum number of portal users specified in the command is less than that of the current online
portal users, the command can be executed successfully and does not impact the online portal users, but
the system does not allow new portal users to log in until the number drops down below the limit.
Examples
# Set the maximum number of portal users allowed in the system to 100.
<Sysname> system-view
[Sysname] portal max-user 100
portal nas-id
Syntax
portal nas-id nas-identifier
undo portal nas-id
View
Interface view
Default level
2: System level
Parameters
nas-identifier: NAS ID, a case-sensitive string of 1 to 16 characters. This value is used as the value of the
NAS -Identifier attribute in the RAD IUS request to be sent to the RADIUS server when a portal user logs on
from the interface.
Description
Use the portal nas-id command to specify the NAS ID value carried in a RADIUS request.
Use the undo portal nas-id command to restore the default.
By default, the device name specified by the sysname command is used as the NAS ID in a RADIUS
request. For information about the sysname command, see Getting Started Command Reference.
Examples
# Specify the NAS ID value carried in a RADIUS request sent by GigabitEthernet 0/0 as
0002053110000460.
46
Page 53

<Sysname> system-view
[Sysname] interface gigabitethernet 0/0
[Sysname-GigabitEthernet0/0] portal nas-id 0002053110000460
portal nas-id-profile
Syntax
portal nas-id-profile profile-name
undo portal nas-id-profile
View
Interface
Default level
2: System level
Parameters
profile-name: Name of the profile that defines the binding relationship between VLANs and NAS IDs.
The profile can be configured by using the aaa nas-id profile command.
Description
Use the portal nas-id-profile command to specify a NAS ID profile for the interface.
Use the undo portal nas-id-profile command to cancel the configuration.
By default, an interface is not specified with any NAS ID profile.
If an interface is specified with a NAS ID profile, the interface prefers to use the binding defined in the
profile. If no NAS ID profile is specified for an interface or no matching binding is found in the specified
profile:
• If a NAS ID is configured using the portal nas-id command, the device uses the configured NAS ID
as that of the interface.
• If the interface has no NAS ID configured, the device uses the device name as the interface NAS ID.
Examples
# Specify NAS ID profile aaa for VLAN-interface 2.
<Sysname> system-view
[Sysname] interface vlan-interface 2
[Sysname-Vlan-interface2] portal nas-id-profile aaa
portal nas-ip
Syntax
portal nas-ip ip-address
undo portal nas-ip
View
Interface view
Default level
2: System level
47
Page 54

Parameters
ip-address: Source IP address to be specified for portal packets. This IP address must be a local IP
address, and cannot be 0.0.0.0, 255.255.255.255, a class D address, a class E address, or a loopback
address.
Description
Use the portal nas-ip command to configure the source IP address for portal packets to be sent.
Use the undo portal nas-ip command to restore the default.
By default, no source IP address is specified, and the IP address of the user access interface will be used
as the source IP address of the portal packets.
Examples
# Configure the source IP address for portal packets to be sent on GigabitEthernet 0/0 as 2.2.2.2.
<Sysname> system-view
[Sysname] interface gigabitethernet0/0
[Sysname-GigabitEthernet0/0] portal nas-ip 2.2.2.2
portal server
Syntax
portal server server-name ip ip-address [ key key-string | port port-id | url url-string ] *
undo portal server server-name [ key | port | url ]
View
System view
Default level
2: System level
Parameters
server-name: Name of the portal server, a case-sensitive string of 1 to 32 characters.
ip-address: IP address of the portal server.
key-string: Shared key for communication with the portal server, a case-sensitive string of 1 to 16
characters.
port-id: Destination port number used when the device sends unsolicited messages to the portal server,
in the range of 1 to 65534. The default is 50100.
url-string: Uniform resource locator (URL) to which HTTP packets are to be redirected. The default URL is
in the http://ip-address format, where ip-address is the IP address of the portal server. You can also
specify the domain name of the portal server, in which case you must use the portal free-rule command
to configure the IP address of the DNS server as a portal authentication-free IP address.
Description
Use the portal server command to configure a portal server.
Use the undo portal server command to remove a portal server, restore the default destination port
number or URL, or delete the shared key.
By default, no portal server is configured.
48
Page 55

Using the undo portal server server-name command, you remove the specified portal server if the
specified portal server exists and there is no user on the interfaces referencing the portal server.
The configured portal server and its parameters can be removed or modified only when the portal server
is not referenced by an interface. To remove or modify the settings of a portal server that has been
referenced by an interface, you must remove the portal configuration on the interface using the undo
portal command.
Related commands: display portal server.
Examples
# Configure portal server pts, setting the IP address to 192.168.0.111, t h e k e y t o portal, and the
redirection URL to h t t p : / / 1 9 2 .16 8 . 0 .111 / p o r t a l .
<Sysname> system-view
[Sysname] portal server pts ip 192.168.0.111 key portal url http://192.168.0.111/portal
portal server method
Syntax
portal server server-name method { direct | layer3 | redhcp }
undo portal
View
Interface view
Default level
2: System level
Parameters
server-name: Name of the portal server, a case-sensitive string of 1 to 32 characters.
method: Specifies the authentication mode to be used.
direct: Direct authentication.
layer3: Layer 3 authentication.
redhcp: Re-DHCP authentication.
Description
Use the portal server command to enable portal authentication on an interface, and specify the portal
server to be referenced and the authentication mode.
Use the undo portal command to disable portal authentication on an interface.
By default, portal authentication is disabled on an interface.
Note that the portal server to be referenced must exist.
Examples
Related commands: display portal server.
# Enable portal authentication on interface GigabitEthernet 0/0, setting the portal server to pts, and the
authentication mode to direct.
<Sysname> system-view
[Sysname] interface gigabitethernet0/0
[Sysname-GigabitEthernet0/0] portal server pts method direct
49
Page 56

reset portal connection statistics
Syntax
reset portal connection statistics { all | interface interface-type interface-number }
View
User view
Default level
1: Monitor level
Parameters
all: Specifies all interfaces.
interface interface-type interface-number: Specifies an interface by its type and number.
Description
Use the reset portal connection statistics command to clear portal connection statistics on a specific
interface or all interfaces.
Examples
# Clear portal connection statistics on interface GigabitEthernet 0/0.
<Sysname> reset portal connection statistics interface gigabitethernet0/0
reset portal server statistics
Syntax
reset portal server statistics { all | interface interface-type interface-number }
View
User view
Default level
1: M o n i t o r l e v e l
Parameters
all: Specifies all interfaces.
interface interface-type interface-number: Specifies an interface by its type and number.
Description
Use the reset portal server statistics command to clear portal server statistics on a specific interface or all
interfaces.
Examples
# Clear portal server statistics on interface GigabitEthernet 0/0.
<Sysname> reset portal server statistics interface gigabitethernet0/0
reset portal tcp-cheat statistics
Syntax
reset portal tcp-cheat statistics
50
Page 57

View
User view
Default level
1: Monitor level
Parameters
None
Description
Use the reset portal tcp-cheat statistics command to clear TCP spoofing statistics.
Examples
# Clear TCP spoofing statistics.
<Sysname> reset portal tcp-cheat statistics
web-redirect
Syntax
web-redirect url url-string [ interval interval ]
undo web-redirect
View
Interface view
Default level
2: System level
Parameters
url-string: URL address to which a Web access request is to be redirected.
Interval: Redirection interval in seconds, in the range of 60 to 86400. The default is 86400.
Description
Use the web-redirect command to configure the mandatory Web page pushing function on an interface.
After you configure this function on an interface and set the redirection interval, a user on the interface
will be forced to access a specific Web page when the user accesses network resources through Web for
the first time. After a specific period of time, namely, the redirection interval, if the user sends a Web
access request again, the system will push the specified Web page to the user again.
Use the undo web-redirect command to restore the default.
By default, this function is not configured on an interface.
You cannot configure both the portal function and the mandatory Web page pushing function on an
interface. If you do so, the function configured later does not take effect.
Examples
If you execute this command repeatedly, the last configuration takes effect.
# Configure the mandatory Web page pushing function on GigabitEthernet 0/0, setting the redirection
URL address to http://192.0.0.1 and the interval to 3600 seconds.
<Sysname> system-view
[Sysname] interface gigabitethernet0/0
51
Page 58

[Sysname-GigabitEthernet0/0] web-redirect url http://192.0.0.1 interval 3600
52
Page 59

AAA configuration commands
AAA configuration commands
aaa nas-id profile
Syntax
aaa nas-id profile profile-name
undo aaa nas-id profile profile-name
View
System view
Default level
2: System level
Parameters
profile-name: Name of the NAS ID profile, a case-insensitive string of 1 to 16 characters.
Description
Use the aaa nas-id profile command to create a NAS ID profile and enter its view. A NAS ID profile
maintains the bindings between NAS IDs and VLANs.
Use the undo aaa nas-id profile command to remove a NAS ID profile.
Related commands: nas-id bind vlan.
Examples
# Create a NAS ID profile named aaa.
<Sysname> system-view
[Sysname] aaa nas-id profile aaa
[Sysname-nas-id-prof-aaa]
access-limit enable
Syntax
access-limit enable max-user-number
undo access-limit enable
View
ISP domain view
Default level
2: System level
53
Page 60

Parameters
max-user-number: Maximum number of online users that the ISP domain can accommodate, in the range
of 1 to 2147483646.
Description
Use the access-limit enable command to set the maximum number of online users in an ISP domain. After
the number of online users reaches the allowed maximum number, no more users will be accepted.
Use the undo access-limit enable command to restore the default.
By default, there is no limit to the number of online users in an ISP domain.
System resources are limited, and user connections may compete for network resources when there are
many users. Setting a proper limit to the number of online users helps provide reliable system
performance.
Related commands: display domain.
Examples
# Set a limit of 500 user connections for ISP domain test.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] access-limit enable 500
accounting command
Syntax
accounting command hwtacacs-scheme hwtacacs-scheme-name
undo accounting command
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
Description
Use the accounting command command to specify the command line accounting method.
Use the undo accounting command command to restore the default.
By default, the default accounting method for the ISP domain is used for command line accounting.
The specified HWTACACS scheme must have been configured.
Examples
Command line accounting can use only a HWTACACS scheme.
Related commands: accounting default and hwtacacs scheme.
# Configure ISP domain test to use HWTACACS scheme hwtac for command line accounting.
<Sysname> system-view
54
Page 61

[Sysname] domain test
[Sysname-isp-test] accounting command hwtacacs-scheme hwtac
accounting default
Syntax
accounting default { hwtacacs-scheme hwtacacs-scheme-name [ local ] | local | none | radius-scheme
radius-scheme-name [ local ] }
undo accounting default
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
local: Performs local accounting.
none: Does not perform any accounting.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the accounting default command to configure the default accounting method for an ISP domain.
Use the undo accounting default command to restore the default.
By default, the default accounting method of an ISP domain is local.
The specified RADIUS or HWTACACS scheme must have been configured.
The default accounting method will be used for all users that support the specified accounting method
and have no specific accounting method configured.
Local accounting is only for monitoring and controlling the number of local user connections; it does not
provide the statistics function that the accounting feature generally provides.
Related commands: local-user, hwtacacs scheme, and radius scheme.
Examples
# Configure the default accounting method for ISP domain test to use RADI US accou nting scheme rd and
use local accounting as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] accounting default radius-scheme rd local
accounting lan-access
Syntax
accounting lan-access { local | none | radius-scheme radius-scheme-name [ local | none ] }
55
Page 62

undo accounting lan-access
View
ISP domain view
Default level
2: System level
Parameters
local: Performs local accounting.
none: Does not perform any accounting.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the accounting lan-access command to configure the accounting method for LAN users.
Use the undo accounting lan-access command to restore the default.
By default, the default accounting method for the ISP domain is used for LAN users.
The specified RADIUS scheme must have been configured.
Related commands: local-user, accounting default, and radius scheme.
Examples
# Configure ISP domain test to use local accounting for LAN users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] accounting lan-access local
# Configure ISP domain test to use RADIUS accounting scheme rd for LAN users and use local
accounting as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] accounting lan-access radius-scheme rd local
accounting login
Syntax
accounting login { hwtacacs-scheme hwtacacs-scheme-name [ local ] | local | none | radius-scheme
radius-scheme-name [ local ] }
undo accounting login
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
56
Page 63

local: Performs local accounting.
none: Does not perform any accounting.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the accounting login command to configure the accounting method for login users (users logging in
through the console, AUX, or Asyn port or accessing through Telnet).
Use the undo accounting login command to restore the default.
By default, the default accounting method for the ISP domain is used for login users.
The specified RADIUS or HWTACACS scheme must have been configured.
Accounting is not supported for login users that use FTP.
Related commands: local-user, accounting default, hwtacacs scheme, and radius scheme.
Examples
# Configure ISP domain test to use local accounting for login users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] accounting login local
# Configure ISP domain test to use RADIUS accounting scheme rd for login users and use local
accounting as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] accounting login radius-scheme rd local
accounting optional
Syntax
accounting optional
undo accounting optional
View
ISP domain view
Default level
2: System level
Parameters
None
Description
Use the accounting optional command to enable the accounting optional feature.
Use the undo accounting optional command to disable the feature.
By default, the feature is disabled.
After you configure the accounting optional command for a domain, a user that will be disconnected
otherwise can continue to use the network resources when no accounting server is available or the
57
Page 64

A
communication with the current accounting server fails. However, the device will not send real-time
accounting updates for the user anymore. The accounting optional feature applies to scenarios where
accounting is not important.
NOTE:
fter you configure the accounting optional command, the setting configured by the access-limit
command in local user view is not effective.
Examples
# Enable the accounting optional feature for users in domain test.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] accounting optional
accounting portal
Syntax
accounting portal { local | none | radius-scheme radius-scheme-name [ local ] }
undo accounting portal
View
ISP domain view
Default level
2: System level
Parameters
local: Performs local accounting.
none: Does not perform any accounting.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the accounting portal command to configure the accounting method for portal users.
Use the undo accounting portal command to restore the default.
By default, the default accounting method for the ISP domain is used for portal users.
The specified RADIUS scheme must have been configured.
Related commands: local-user, accounting default, and radius scheme.
Examples
# Configure ISP domain test to use local accounting for portal users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] accounting portal local
# Configure ISP domain test to use RADIUS scheme rd for accounting on portal users and use local
accounting as the backup.
<Sysname> system-view
58
Page 65

[Sysname] domain test
[Sysname-isp-test] accounting portal radius-scheme rd local
accounting ppp
Syntax
accounting ppp { hwtacacs-scheme hwtacacs-scheme-name [ local ] | local | none | radius-scheme
radius-scheme-name [ local ] }
undo accounting ppp
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
local: Performs local accounting.
none: Does not perform any accounting.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the accounting ppp command to configure the accounting method for PPP users.
Use the undo accounting ppp command to restore the default.
By default, the default accounting method for the ISP domain is used for PPP users.
The specified RADIUS or HWTACACS scheme must have been configured.
Related commands: local-user, accounting default, hwtacacs scheme, and radius scheme.
Examples
# Configure ISP domain test to use local accounting for PPP users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] accounting ppp local
# Configure ISP domain test to use RADIUS accounting scheme rd for PPP users and use local accounting
as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] accounting ppp radius-scheme rd local
authentication default
Syntax
authentication default { hwtacacs-scheme hwtacacs-scheme-name [ local ] | local | none |
radius-scheme radius-scheme-name [ local ] }
59
Page 66

undo authentication default
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
local: Performs local authentication.
none: Does not perform any authentication.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the authentication default command to configure the default authentication method for an ISP
domain.
Use the undo authentication default command to restore the default.
By default, the default authentication method of an ISP domain is local.
The specified RADIUS or HWTACACS scheme must have been configured.
The default authentication method will be used for all users that support the specified authentication
method and have no specific authentication method configured.
Related commands: local-user, hwtacacs scheme, and radius scheme.
Examples
# Configure the default authentication method for ISP domain test to use RADIUS authentication scheme
rd and use local authentication as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authentication default radius-scheme rd local
authentication lan-access
Syntax
authentication lan-access { local | none | radius-scheme radius-scheme-name [ local | none ] }
undo authentication lan-access
View
ISP domain view
Default level
2: System level
Parameters
local: Performs local authentication.
none: Does not perform any authentication.
60
Page 67
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the authentication lan-access command to configure the authentication method for LAN users.
Use the undo authentication lan-access command to restore the default.
By default, the default authentication method for the ISP domain is used for LAN users.
The specified RADIUS scheme must have been configured.
Related commands: local-user, authentication default, and radius scheme.
Examples
# Configure ISP domain test to use local authentication for LAN users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authentication lan-access local
# Configure ISP domain test to use RADIUS authentication scheme rd for LAN users and use local
authentication as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authentication lan-access radius-scheme rd local
authentication login
Syntax
authentication login { hwtacacs-scheme hwtacacs-scheme-name [ local ] | local | none | radius-scheme
radius-scheme-name [ local ] }
undo authentication login
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
local: Performs local authentication.
none: Does not perform any authentication.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the authentication login command to configure the authentication method for login users (users
logging in through the console, AUX port or accessing through Telnet or FTP).
Use the undo authentication login command to restore the default.
By default, the default authentication method for the ISP domain is used for login users.
61
Page 68

The specified RADIUS or HWTACACS scheme must have been configured.
Related commands: local-user, authentication default, hwtacacs scheme, and radius scheme.
Examples
# Configure ISP domain test to use local authentication for login users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authentication login local
# Configure ISP domain test to use RADIUS authentication scheme rd for login users and use local
authentication as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authentication login radius-scheme rd local
authentication portal
Syntax
authentication portal { local | none | radius-scheme radius-scheme-name [ local ] }
undo authentication portal
View
ISP domain view
Default level
2: System level
Parameters
local: Performs local authentication.
none: Does not perform any authentication.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the authentication portal command to configure the authentication method for portal users.
Use the undo authentication portal command to restore the default.
By default, the default authentication method for the ISP domain is used for portal users.
The specified RADIUS scheme must have been configured.
Related commands: local-user, authentication default, and radius scheme.
Examples
# Configure ISP domain test to use local authentication for portal users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authentication portal local
# Configure ISP domain test to use RADIUS scheme rd for authentication of portal users and use local
authentication as the backup.
<Sysname> system-view
62
Page 69

[Sysname] domain test
[Sysname-isp-test] authentication portal radius-scheme rd local
authentication ppp
Syntax
authentication ppp { hwtacacs-scheme hwtacacs-scheme-name [ local ] | local | none | radius-scheme
radius-scheme-name [ local ] }
undo authentication ppp
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
local: Performs local authentication.
none: Does not perform any authentication.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the authentication ppp command to configure the authentication method for PPP users.
Use the undo authentication ppp command to restore the default.
By default, the default authentication method for the ISP domain is used for PPP users.
The specified RADIUS or HWTACACS scheme must have been configured.
Related commands: local-user, authentication default, hwtacacs scheme, and radius scheme.
Examples
# Configure ISP domain test to use local authentication for PPP users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authentication ppp local
# Configure ISP domain test to use RADIUS authentication scheme rd for PPP users and use local
authentication as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authentication ppp radius-scheme rd local
authorization command
Syntax
authorization command { hwtacacs-scheme hwtacacs-scheme-name [ local | none ] | local | none }
63
Page 70

undo authorization command
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
local: Performs local authorization.
none: Does not perform any authorization exchange. In this case, an authenticated user can access only
commands of Level 0.
Description
Use the authorization command command to configure the command line authorization method.
Use the undo authorization command command to restore the default.
By default, the default authorization method for the ISP domain is used for command line authorization.
The specified HWTACACS scheme must have been configured.
With command line authorization configured, a user who has logged in to the device can execute only
the commands with a level lower than or equal to that of the local user.
Related commands: local-user, authorization default, and hwtacacs scheme.
Examples
# Configure ISP domain test to use local command line authorization.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization command local
# Configure ISP domain test to use HWTACACS scheme hwtac for command line authorization and use
local authorization as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization command hwtacacs-scheme hwtac local
authorization default
Syntax
authorization default { hwtacacs-scheme hwtacacs-scheme-name [ local ] | local | none |
radius-scheme radius-scheme-name [ local ] }
undo authorization default
View
ISP domain view
Default level
2: System level
64
Page 71

Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
local: Performs local authorization.
none: Does not perform any authorization exchange. After passing authentication, non-login users can
access the network, FTP users can access the root directory of the device, and other login users can
access only the commands of Level 0.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the authorization default command to configure the default authorization method for an ISP domain.
Use the undo authorization default command to restore the default.
By default, the default authorization method for the ISP domain of an ISP domain is local.
The specified RADIUS or HWTACACS scheme must have been configured.
The default authorization method will be used for all users that support the specified authorization
method and have no specific authorization method are configured.
The RADIUS authorization configuration takes effect only when the authentication method and
authorization method of the ISP domain use the same RADIUS scheme.
Related commands: local-user, hwtacacs scheme, and radius scheme.
Examples
# Configure the default authorization method for ISP domain test to use RADIUS authorization scheme rd
and use local authorization as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization default radius-scheme rd local
authorization lan-access
Syntax
authorization lan-access { local | none | radius-scheme radius-scheme-name [ local | none ] }
undo authorization lan-access
View
ISP domain view
Default level
2: System level
Parameters
local: Performs local authorization.
none: Does not perform any authorization exchange. In this case, an authenticated LAN user can access
the network directly.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
65
Page 72

Description
Use the authorization lan-access command to configure the authorization method for LAN users.
Use the undo authorization lan-access command to restore the default.
By default, the default authorization method for the ISP domain is used for LAN users.
The specified RADIUS scheme must have been configured.
The RADIUS authorization configuration takes effect only when the authentication method and
authorization method of the ISP domain use the same RADIUS scheme.
Related commands: local-user, authorization default, and radius scheme.
Examples
# Configure ISP domain test to use local authorization for LAN users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization lan-access local
# Configure ISP domain test to use RADIUS authorization scheme rd for LAN users and use local
authorization as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization lan-access radius-scheme rd local
authorization login
Syntax
authorization login { hwtacacs-scheme hwtacacs-scheme-name [ local ] | local | none | radius-scheme
radius-scheme-name [ local ] }
undo authorization login
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
local: Performs local authorization.
none: Does not perform any authorization exchange. After passing authentication, FTP users can access
the root directory of the device, and other login users can access only the commands of Level 0.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the authorization login command to configure the authorization method for login users (users
logging in through the console, AUX, or Asyn port or accessing through Telnet or FTP).
Use the undo authorization login command to restore the default.
66
Page 73

By default, the default authorization method for the ISP domain is used for login users.
The specified RADIUS or HWTACACS scheme must have been configured.
The RADIUS authorization configuration takes effect only when the authentication method and
authorization method of the ISP domain use the same RADIUS scheme.
Related commands: local-user, authorization default, hwtacacs scheme, and radius scheme.
Examples
# Configure ISP domain test to use local authorization for login users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization login local
# Configure ISP domain test to use RADIUS authorization scheme rd for login users and use local
authorization as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization login radius-scheme rd local
authorization portal
Syntax
authorization portal { local | none | radius-scheme radius-scheme-name [ local ] }
undo authorization portal
View
ISP domain view
Default level
2: System level
Parameters
local: Performs local authorization.
none: Does not perform any authorization exchange. In this case, an authenticated portal user can
access the network directly.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the authorization portal command to configure the authorization method for portal users.
Use the undo authorization portal command to restore the default.
By default, the default authorization method for the ISP domain is used for portal users.
The specified RADIUS scheme must have been configured.
The RADIUS authorization configuration takes effect only when the authentication method and
authorization method of the ISP domain use the same RADIUS scheme.
Related commands: local-user, authorization default, and radius scheme.
67
Page 74

Examples
# Configure ISP domain test to use local authorization for portal users.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization portal local
# Configure ISP domain test to use RADIUS scheme rd for authorization of portal users and use local
authorization as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization portal radius-scheme rd local
authorization ppp
Syntax
authorization ppp { hwtacacs-scheme hwtacacs-scheme-name [ local ] | local | none | radius-scheme
radius-scheme-name [ local ] }
undo authorization ppp
View
ISP domain view
Default level
2: System level
Parameters
hwtacacs-scheme hwtacacs-scheme-name: Specifies an HWTACACS scheme by its name, which is a
case-insensitive string of 1 to 32 characters.
local: Performs local authorization.
none: Does not perform any authorization exchange. In this case, an authenticated PPP user can access
the network directly.
radius-scheme radius-scheme-name: Specifies a RADIUS scheme by its name, which is a case-insensitive
string of 1 to 32 characters.
Description
Use the authorization ppp command to configure the authorization method for PPP users.
Use the undo authorization ppp command to restore the default.
By default, the default authorization method for the ISP domain is used for PPP users.
The specified RADIUS or HWTACACS scheme must have been configured.
The RADIUS authorization configuration takes effect only when the authentication method and
authorization method of the ISP domain use the same RADIUS scheme.
Examples
Related commands: local-user, authorization default, hwtacacs scheme, and radius scheme.
# Configure ISP domain test to use local authorization for PPP users.
<Sysname> system-view
[Sysname] domain test
68
Page 75

[Sysname-isp-test] authorization ppp local
# Configure ISP domain test to use RADIUS authorization scheme rd for PPP users and use local
authorization as the backup.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization ppp radius-scheme rd local
authorization-attribute user-profile
Syntax
authorization-attribute user-profile profile-name
undo authorization-attribute user-profile
View
ISP domain view
Default level
3: Manage level
Parameters
profile-name: Name of the user profile, a case-sensitive string of 1 to 31 characters. For more information
about user profile configuration, see Security Configuration Guide.
Description
Use the authorization-attribute user-profile command to specify the default authorization user profile for
an ISP domain.
Use the undo authorization-attribute user-profile command to restore the default.
By default, an ISP domain has no default authorization user profile.
After a user of an ISP domain passes authentication, if the server (or the access device in the case of local
authentication) does not authorize any user profile to the ISP domain, the system uses the user profile
specified by the authorization-attribute user-profile command as that of the ISP domain.
If you configure the authorization-attribute user-profile command repeatedly, only the last one takes
effect
Examples
# Specify the default authorization user profile for domain test as profile1.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] authorization-attribute user-profile profile1
cut connection
Syntax
cut connection { access-type { dot1x | mac-authentication | portal } | all | domain isp-name | interface
interface-type interface-number | ip ip-address | mac mac-address | ucibindex ucib-index | user-name
user-name | vlan vlan-id }
69
Page 76

View
System view
Default level
2: System level
Parameters
access-type: Specifies the user connections of the specified access type.
• dot1x: Indicates 802.1X authentication.
• mac-authentication: Indicates MAC address authentication.
• portal: Indicates portal authentication.
all: Specifies all user connections.
domain isp-name: Specifies the user connections of an ISP domain. The isp-name argument represents
the name of an existing ISP domain and is a string of 1 to 24 characters.
interface interface-type interface-number: Specifies the user connections on an interface. Only Layer 2
Ethernet interfaces is supported.
ip ip-address: Specifies the user connections for an IP address.
mac mac-address: Specifies the user connections for a MAC address, with mac-address in the format
H-H-H.
ucibindex ucib-index: Specifies the user connection that uses the connection index, in the range of 0 to
4294967295..
user-name user-name: Specifies the user connections that use the username. The user-name argument is
a case-sensitive string of 1 to 80 characters. For a username entered without a domain name, the system
assumes that the user is in the default domain or the mandatory authentication domain.
vlan vlan-id: Specifies the user connections of a VLAN. vlan-id is in the range 1 to 4094.
Description
Use the cut connection command to tear down the specified user connections forcibly.
This command applies to only LAN access, portal, and PPP user connections.
For 802.1X users whose usernames carry the version number or contain spaces, you cannot cut the
connections by username.
For 802.1X users whose usernames use a forward slash (/) or backward slash (\) as the domain name
delimiter, you cannot cut their connections by username. For example, the cut connection user-name
aaa\bbb command cannot cut the connections of the user aaa\bbb.
An interface that is configured with a mandatory authentication domain treats users of the corresponding
access type as users in the mandatory authentication domain. For example, if you configure an 802.1X
mandatory authentication domain on an interface, the interface uses the domain’s AAA methods for all
its 802.1X users. To cut connections of such users, use the cut connection domain isp-name command and
specify the mandatory authentication domain.
Examples
Related commands: display connection and service-type.
# Tear down all connections of ISP domain test.
<Sysname> system-view
[Sysname] cut connection domain test
70
Page 77

display connection
Syntax
display connection [ access-type { dot1x | mac-authentication | portal } | domain isp-name | interface
interface-type interface-number | ip ip-address | mac mac-address | ucibindex ucib-index | user-name
user-name | vlan vlan-id ]
View
Any view
Default level
1: Monitor level
Parameters
access-type: Specifies the user connections of the specified access type.
• dot1x: Indicates 802.1X authentication.
• mac-authentication: Indicates MAC address authentication.
• portal: Indicates portal authentication.
domain isp-name: Specifies the user connections of an ISP domain. The isp-name argument represents
the name of an existing ISP domain and is a case-insensitive string of 1 to 24 characters.
interface interface-type interface-number: Specifies the user connections on an interface. Only Layer 2
Ethernet interfaces is supported.
ip ip-address: Specifies the user connections of an IP address.
mac mac-address: Specifies the user connections of a MAC address, with mac-address in the format
H-H-H.
ucibindex ucib-index: Specifies the user connection that uses the connection index, in the range of 0 to
4294967295.
user-name user-name: Specifies the user connections that use the username. The user-name argument is
a case-sensitive string of 1 to 80 characters. For a username entered without a domain name, the system
assumes that the user is in the default domain name or the mandatory authentication domain.
vlan vlan-id: Specifies the user connections of a VLAN. vlan-id is in the range 1 to 4094.
Description
Use the display connection command to display information about AAA user connections.
This command does not display information about FTP user connections.
With no parameter specified, this command displays brief information about all AAA user connections.
If you specify the ucibindex ucib-index option, this command displays detailed information; otherwise,
this command displays brief information.
If an interface is configured with a mandatory authentication domain (for example, an 802.1X
mandatory authentication domain), the device uses the mandatory authentication domain to perform
authentication, authorization, and accounting for users who access the interface through the specified
access type. To display connections of such users, use the display connection domain isp-name
command and specify the mandatory authentication domain.
How the device displays the username of a user on an interface configured with a mandatory
authentication domain depends on the format of the username entered by the user at login:
71
Page 78

Examples
• If the username does not contain the character @, the device displays the username in the format
username @mandatory authentication domain name.
• If the username contains the character @, the device displays the entered username. For example,
if a user entered the username aaa@123 at login and the name of the mandatory authentication
domain is dom, the device displays the username aaa@123, rather than aaa@123@dom.
For 802.1X users whose usernames use a forward slash (/) or backward slash (\) as the domain name
delimiter, you cannot query the connections by username. For example, the display connection
user-name aaa\bbb command cannot display the connections of the user aaa\bbb.
Related commands: cut connection.
# Display information about all AAA user connections.
<Sysname> display connection
Index=1 ,Username=telnet@system
IP=10.0.0.1
Total 1 connection(s) matched.
# Display information about AAA user connections using the index of 0.
<Sysname> display connection ucibindex 0
Index=0 , Username=telnet@system
IP=10.0.0.1
Access=Admin ,AuthMethod=PAP
Port Type=Virtual ,Port Name=N/A
Initial VLAN=999, Authorized VLAN=20
ACL Group=Disable
User Profile=N/A
CAR=Disable
Priority=Disable
Start=2009-07-16 10:53:03 ,Current=2009-07-16 10:57:06 ,Online=00h04m03s
Total 1 connection matched.
# Display information about AAA user connections using the index of 0.
<Sysname> display connection ucibindex 0
Slot: 0
Index=0 , Username=telnet@system
IP=10.0.0.1
Access=Admin ,AuthMethod=PAP
Port Type=Virtual ,Port Name=N/A
Initial VLAN=999, Authorized VLAN=20
ACL Group=Disable
User Profile=N/A
CAR=Disable
Priority=Disable
Start=2009-07-16 10:53:03 ,Current=2009-07-16 10:57:06 ,Online=00h04m03s
Total 1 connection matched.
Slot: 1
Total 0 connection matched.
Slot: 2
72
Page 79

p
Total 0 connection matched.
Table 19 Output description
Field Descri
Username Username of the connection, in the format username@domain
MAC MAC address of the user
IP IPv4 address of the user
Access User access type
ACL Group Authorization ACL group. Disable means no authorization ACL group is assigned.
User Profile Authorization user profile
CAR(kbps) Authorized CAR parameters
UpPeakRate Uplink peak rate
DnPeakRate Downlink peak rate
UpAverageRate Uplink average rate
DnAverageRate Downlink average rate
display domain
Syntax
display domain [ isp-name ]
tion
View
Any view
Default level
1: Monitor level
Parameters
isp-name: Name of an existing ISP domain, a string of 1 to 24 characters.
Description
Use the display domain command to display the configuration information of ISP domains.
If you do not specify any ISP domain, the command displays the configuration information of all ISP
domains.
Related commands: access-limit enable, domain, and state.
Examples
# Display the configuration information of all ISP domains.
<Sysname> display domain
0 Domain : system
State : Active
Access-limit : Disabled
Accounting method : Required
Default authentication scheme : local
Default authorization scheme : local
73
Page 80
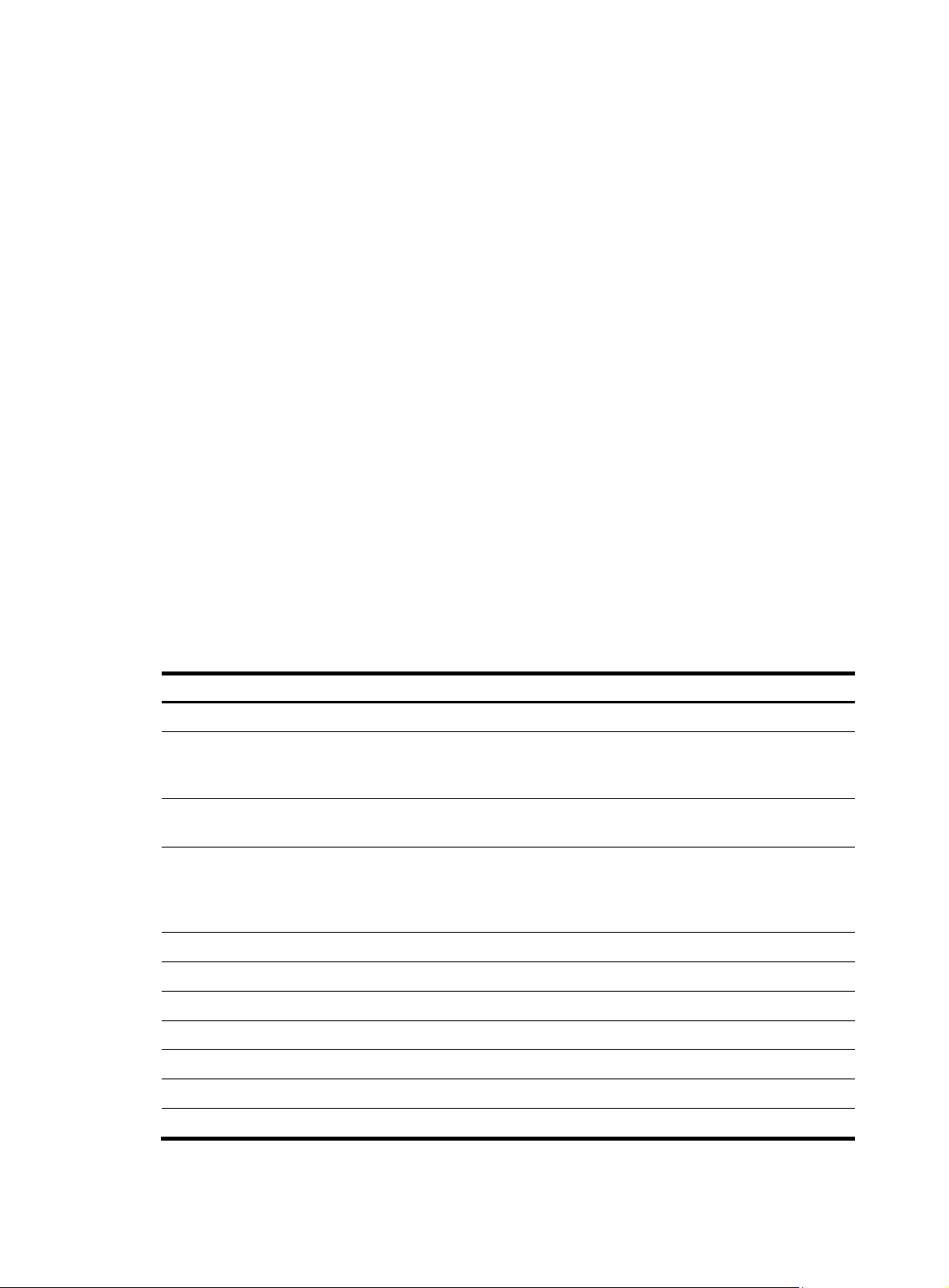
p
Default accounting scheme : local
Domain User Template:
Idle-cut : Disabled
Self-service : Disabled
Authorization attributes :
1 Domain : test
State : Active
Access-limit : Disabled
Accounting method : Required
Default authentication scheme : local
Default authorization scheme : local
Default accounting scheme : local
Lan-access authentication scheme : radius:test, local
Lan-access authorization scheme : hwtacacs:hw, local
Lan-access accounting scheme : local
Domain User Template:
Idle-cut : Disabled
Self-service : Disabled
Authorization attributes :
User-profile : profile1
Default Domain Name: system
Total 2 domain(s).
Table 20 Output description
Field Descri
Domain ISP domain name.
Status of the ISP domain, active or blocked. Users in an active ISP
State
Access-limit
Accounting method
Default authentication scheme Default authentication method.
Default authorization scheme Default authorization method.
Default accounting scheme Default accounting method.
Lan-access authentication scheme Authentication method for LAN users.
Lan-access authorization scheme Authorization method for LAN users.
Lan-access accounting scheme Accounting method for LAN users.
domain can request network services, and users in a blocked ISP
domain cannot.
Limit on the number of user connections. If there is no limit on the
number, the value of this field is Disabled.
Indicates whether accounting is required. If accounting is required,
when no accounting server is available or communication with the
accounting server fails, user connections will be torn down.
Otherwise, users can continue to use network services.
tion
Domain User Template Indicates some functions and attributes set for users in the domain.
74
Page 81
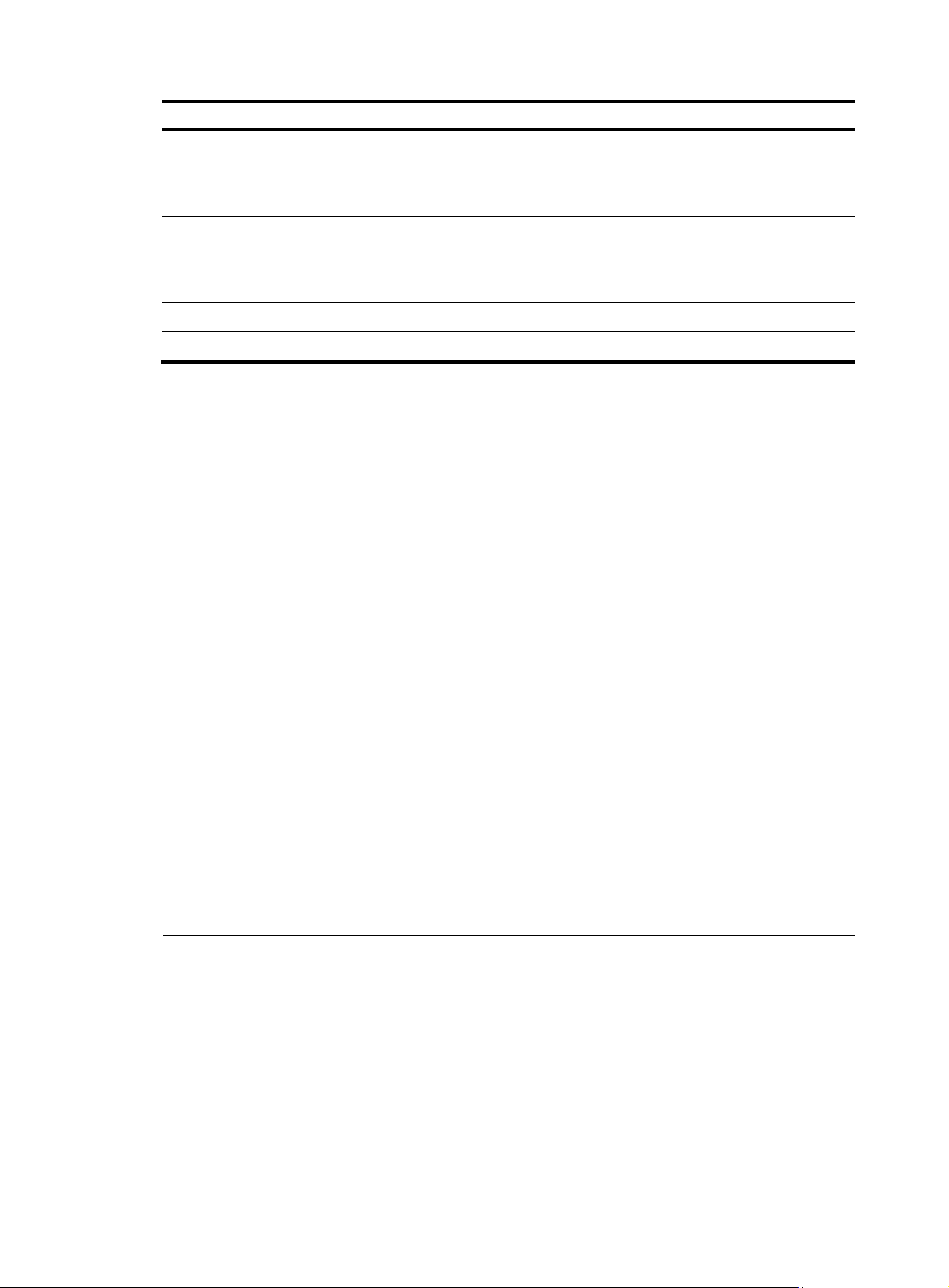
Field Description
Idle-cut
Self-service
Authorization attributes Default authorization attributes for the ISP domain.
User-profile Default authorization user profile.
domain
Syntax
domain isp-name
undo domain isp-name
View
Indicates whether the idle cut function is enabled. With the idle cut
function enabled for a domain, the system logs out any user in the
domain whose traffic is less than the specified minimum traffic
during the idle timeout period.
Indicates whether the self service function is enabled. With the self
service function enabled, users can launch a browser and enter the
self service URL in the address bar to access the self service pages
and perform self service operations.
System view
Default level
3: Manage level
Parameters
isp-name: ISP domain name, a case-insensitive string of 1 to 24 characters that contains no forward slash
(/), backward slash (\), colon (:), asterisk (*), question mark (?), less-than sign (<), greater-than sign (>),
or the @ sign.
Description
Use the domain isp-name command to create an ISP domain and enter ISP domain view.
Use the undo domain command to remove an ISP domain.
By default, there is a system predefined ISP domain named system in the system.
All ISP domains are in active state when they are created.
The system predefined ISP domain system cannot be deleted; you can only modify its configuration.
NOTE:
To delete the ISP domain that is used as the default ISP domain, you must change it to a non-default ISP
domain first by using the undo domain default enable command.
Related commands: state and display domain.
Examples
# Create ISP domain test, and enter ISP domain view.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test]
75
Page 82

domain default enable
Syntax
domain default enable isp-name
undo domain default enable
View
System view
Default level
3: Manage level
Parameters
isp-name: Name of the ISP domain, a case-insensitive string of 1 to 24 characters.
Description
Use the domain default enable command to specify the default ISP domain. Users without any domain
name carried in the usernames are considered to be in the default domain.
Use the undo domain default enable command to restore the default.
By default, the default ISP domain is the system predefined ISP domain system.
There can be only one default ISP domain.
The specified domain must already exist; otherwise, users without a domain name in the username
cannot pass authentication.
To delete the ISP domain that is used as the default ISP domain, you must change it to a non-default ISP
domain first by using the domain default disable command.
Related commands: domain, state, and display domain.
Examples
# Create a new ISP domain named test, and configure it as the default ISP domain.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] quit
[Sysname] domain default enable test
idle-cut enable
Syntax
idle-cut enable minute [ flow ]
undo idle-cut enable
View
ISP domain view
Default level
2: System level
Parameters
minute: Idle timeout period, in the range 1 to 120 minutes.
76
Page 83

flow: Minimum traffic during the idle timeout period in bytes. It ranges from 1 to 10240000 and defaults
to 10240.
Description
Use the idle-cut enable command to enable the idle cut function and set the relevant parameters. With
the idle cut function enabled for a domain, the device checks the traffic of each online user in the domain
at the idle timeout interval, and logs out any user in the domain whose traffic during the idle timeout
period is less than the specified minimum traffic.
Use the undo idle-cut enable command to restore the default.
By default, the function is disabled.
You can also set the idle timeout period on the server to make the server log out users whose traffic during
the idle timeout period is less than 10240 bytes, but your setting on the server takes effect only when you
disable the idle cut function on the device.
Related commands: domain.
Examples
# Enable the idle cut function and set the idle timeout period to 50 minutes and the traffic threshold to
1024 byt es for IS P d om ai n test.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] idle-cut enable 50 1024
ip pool
Syntax
ip pool pool-number low-ip-address [ high-ip-address ]
undo ip pool pool-number
View
ISP domain view
Default level
2: System level
Parameters
pool-number: Address pool number, in the range 0 to 99.
low-ip-address and high-ip-address: Start and end IP addresses of the address pool. Up to 1024
addresses are allowed for an address pool. If you do not specify the end IP address, there is only one IP
address in the pool, which is the start IP address.
Description
Use the ip pool command to configure an address pool for assigning addresses to PPP users.
Use the undo ip pool command to delete an address pool.
Examples
By default, no IP address pool is configured for PPP users.
Related commands: ip pool.
# Configure the IP address pool 0 with the address range of 129.102.0.1 to 129.102.0.10.
77
Page 84

<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] ip pool 0 129.102.0.1 129.102.0.10
nas-id bind vlan
Syntax
nas-id nas-identifier bind vlan vlan-id
undo nas-id nas-identifier bind vlan vlan-id
View
NAS ID profile view
Default level
2: System level
Parameters
nas-identifier: NAS ID, a case-sensitive string of 1 to 20 characters
vlan-id: ID of the VLAN to be bound with the NAS ID, in the range 1 to 4094.
Description
Use the nas-id bind vlan command to bind a NAS ID with a VLAN.
Use the undo nas-id bind vlan command to remove a NAS ID-VLAN binding.
By default, no NAS ID-VLAN binding exists.
In a NAS ID profile view, you can configure multiple NAS ID–VLAN bindings.
A NAS ID can be bound with more than one VLAN, but one VLAN can be bound with only one NAS ID.
If you bind a VLAN with different NAS IDs, only the last binding takes effect.
Related commands: aaa nas-id profile.
Examples
# Bind NAS ID 222 with VLAN 2.
<Sysname> system-view
[Sysname] aaa nas-id profile aaa
[Sysname-nas-id-prof-aaa] nas-id 222 bind vlan 2
self-service-url enable
Syntax
self-service-url enable url-string
undo self-service-url enable
View
ISP domain view
Default level
2: System level
78
Page 85
Parameters
url-string: URL of the self-service server, a string of 1 to 64 characters that starts with http:// and contains
no question mark. This URL was specified by the RADIUS server administrator during RADIUS server
installation.
Description
Use the self-service-url enable command to enable the self-service server location function and specify
the URL of the self-service server.
Use the undo self-service-url enable command to restore the default.
By default, the self-service server location function is disabled.
With the self-service function, users can manage and control their accounts and passwords. Only the
RADIUS server systems provided by the Intelligent Management Center (IMC) support the self-service
function.
Examples
# For ISP domain test, enable the self-service server location function and specify the URL of the
self-service server for changing user password to http://10.153.89.94/selfservice.
<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] self-service-url enable http://10.153.89.94/selfservice
state (ISP domain view)
Syntax
state { active | block }
undo state
View
ISP domain view
Default level
2: System level
Parameters
active: Places the ISP domain in active state to allow the users in the ISP domain to request network
services.
block: Places the ISP domain in blocked state to prevent users in the ISP domain from requesting network
services.
Description
Use the state command to set the status of an ISP domain.
Use the undo state command to restore the default.
Examples
By default, an ISP domain is in active state.
By blocking an ISP domain, you disable users of the domain that are offline from requesting network
services. The online users are not affected.
# Place the current ISP domain test to the state of blocked.
79
Page 86

<Sysname> system-view
[Sysname] domain test
[Sysname-isp-test] state block
Local user configuration commands
access-limit
Syntax
access-limit max-user-number
undo access-limit
View
Local user view
Default level
3: Manage level
Parameters
max-user-number: Maximum number of concurrent users of the current local user account, in the range 1
to 1024.
Description
Use the access-limit command to limit the number of concurrent users of a local user account.
Use the undo access-limit command to remove the limitation.
By default, there is no limit to the number of users who concurrently use the same local user account.
This command takes effect only when local accounting is used for the user account.
This limit is not effective for FTP users because accounting is not available for FTP users.
Related commands: display local-user.
Examples
# Limit the maximum number of concurrent users of local user account abc to 5.
<Sysname> system-view
[Sysname] local-user abc
[Sysname-luser-abc] access-limit 5
authorization-attribute (local user view/user group view)
Syntax
authorization-attribute { acl acl-number | callback-number callback-number | idle-cut minute | level
level | user-profile profile-name |vlan vlan-id | work-directory directory-name } *
View
undo authorization-attribute { acl | callback-number | idle-cut | level | user-profile | vlan |
work-directory } *
Local user view, user group view
80
Page 87

Default level
3: Manage level
Parameters
acl acl-number: Specifies the authorization ACL. The ACL number must be in the range 2000 to 5999.
After passing authentication, a local user is authorized to access the network resources specified by this
ACL.
callback-number callback-number: Specifies the authorization PPP callback number. callback-number is
a case-sensitive string of 1 to 64 characters. After a local user passes authentication, the device uses this
number to call the user.
idle-cut minute: Sets the idle timeout period. With the idle cut funct ion en able d, an onli ne us er whos e idl e
period exceeds the specified idle timeout period will be logged out. minute indicates the idle timeout
period, in the range 1 to 120 minutes.
level level: Specifies the user level, which can be 0 for visit level, 1 for monitor level, 2 for system level,
and 3 for manage level. A smaller number means a lower level. If the user interfaces’ authentication
mode is scheme, which commands users can use after login in depends on this argument. By default, the
user level is 0, and users can use only commands of level 0 after login.
user-profile profile-name: Specifies the authorization user profile. profile-name is a case-sensitive string
of 1 to 32 characters. It can consist of English letters, digits, and underlines and must start with an English
letter. After a user passes authentication and gets online, the device uses the settings in the user profile
to restrict the access behavior of the user. For more information about user profiles, see Security
Configuration Guide. Support for the user-profile keyword depends on the device model.
vlan vlan-id: Specifies the authorized VLAN. vlan-id is in the range 1 to 4094. After passing
authentication, a local user can access the resources in this VLAN.
work-directory directory-name: Specifies the work directory, if the user or users use the FTP or SFTP
service. directory-name is a case -i nsen sitive strin g of 1 to 135 ch aracters. The directory must already exist.
By default, an FTP or SFTP user can access the root directory of the device.
Description
Use the authorization-attribute command to configure authorization attributes for the local user or user
group. After the local user or a local user of the user group passes authentication, the device will assign
these attributes to the user.
Use the undo authorization-attribute command to remove authorization attributes and restore the
defaults.
By default, no authorization attribute is configured for a local user or user group.
Every configurable authorization attribute has its definite application environments and purposes.
Consider the service types of users when assigning authorization attributes.
Authorization attributes configured for a user group are effective for all local users in the group. You can
group local users to improve configuration and management efficiency.
An authorization attribute configured in local user view takes precedence over the same attribute
configured in user group view. If an authorization attribute is configured in user group view but not in
local user view, the setting in user group view takes effect.
If only one user is playing the role of security log administrator in the system, you cannot delete the user
account, or remove or change the user’s role, unless you configure another user as a security log
administrator first.
81
Page 88

A local user can play only one role at a moment. If you perform the role configuration repeatedly, only
the last role configuration takes effect.
Examples
# Configure the authorized VLAN of local user abc as VLAN 2.
<Sysname> system-view
[Sysname] local-user abc
[Sysname-luser-abc] authorization-attribute vlan 2
# Configure the authorized VLAN of user group abc as VLAN 3.
<Sysname> system-view
[Sysname] user-group abc
[Sysname-ugroup-abc] authorization-attribute vlan 3
bind-attribute
Syntax
bind-attribute { call-number call-number [ : subcall-number ] | ip ip-address | location port slot-number
subslot-number port-number | mac mac-address | vlan vlan-id } *
undo bind-attribute { call-number | ip | location | mac | vlan } *
View
Local user view
Default level
3: Manage level
Parameters
call-number call-number: Specifies a calling number for ISDN user authentication. The call-number
argument is a string of 1 to 64 characters. This option is applicable to only PPP users.
subcall-number: Specifies the sub-calling number. The total length of the calling number and the
sub-calling number cannot be more than 62 characters.
ip ip-address: Specifies the IP address of the user. This option is applicable to only 802.1X users.
location port slot-number subslot-number port-number: Specifies the port to which the user is bound. The
slot-number argument is in the range 0 to 255, the subslot-number argument is in the range 0 to 15, and
the port-number argument is in the range 0 to 255. This option is applicable to only LAN users.
mac mac-address: Specifies the MAC address of the user in the format H-H-H. This option is applicable
to only LAN users.
vlan vlan-id: Specifies the VLAN to which the user belongs. The vlan-id argument is in the range 1 to
4094. This option is applicable to only LAN users.
Description
Use the bind-attribute command to configure binding attributes for a local user.
Use the undo bind-attribute command to remove binding attributes of a local user.
By default, no binding attribute is configured for a local user.
Binding attributes are checked upon authentication of a local user. If the binding attributes of a local user
do not match the configured ones, the user fails the checking and the authentication.
82
Page 89

Binding attribute checking does not take the service types of the users into account. A configured binding
attribute is effective for all types of users. Be cautious when deciding which binding attributes should be
configured for which type of local users. For example, an IP address binding is applicable to only 802.1X
authentication that supports IP address upload. If you configure an IP address binding for an
authentication method that does not support IP address upload, for example, MAC authentication, the
local authentication fails.
Examples
# Configure the bound IP of local user abc as 3.3.3.3.
<Sysname> system-view
[Sysname] local-user abc
[Sysname-luser-abc] bind-attribute ip 3.3.3.3
display local-user
Syntax
display local-user [ idle-cut { disable | enable } | service-type { ftp | lan-access | portal | ppp | ssh |
telnet | terminal } | state { active | block } | user-name user-name | vlan vlan-id ]
View
Any view
Default level
1: Monitor level
Parameters
idle-cut { disable | enable }: Specifies local users with the idle cut function disabled or enabled.
service-type: Specifies the local users that use a specified type of service.
• ftp—FTP users.
• lan-access—Users accessing the network through Ethernet, such as 802.1X users.
• portal—Portal users.
• ppp—PPP users.
• ssh—SSH users.
• telnet—Telnet users.
• terminal—Users logging in through the console port.
state { active | block }: Specifies local users in active state or blocked state. A local user in active state
can access network services, but a local user in blocked state cannot.
user-name user-name: Specifies all local users using the specified username. The username is a
case-sensitive string of 1 to 55 characters and does not contain the domain name.
vlan vlan-id: Specifies all local users in a VLAN. The VLAN ID ranges from 1 to 4094.
Description
Use the display local-user command to display configuration and statistics information about local users.
If you do not specify any parameter, the command displays information about all local users.
Related commands: local-user.
83
Page 90

p
Examples
# Display information about all local users.
<Sysname> display local-user
The contents of local user abc:
State: Active
ServiceType: telnet
Access-limit: Enabled Current AccessNum: 0
Max AccessNum: 300
User-group: system
Bind attributes:
IP address: 1.2.3.4
Bind location: 0/4/1 (SLOT/SUBSLOT/PORT)
MAC address: 0001-0002-0003
Vlan ID: 100
Authorization attributes:
Idle TimeOut: 10(min)
Work Directory: cfa0:/
User Privilege: 3
Acl ID: 2000
Vlan ID: 100
User Profile: prof1
Expiration date: 12:12:12-2018/09/16
Total 1 local user(s) matched.
Table 21 Output description
Field Descri
State Status of the local user, active or blocked
ServiceType
Access-limit Whether to limit the number of user connections that use the current username
Current AccessNum Current number of user connections that use the current username
Max AccessNum Maximum number of user connections that use the current username
Bind attributes Binding attributes of the local user
VLAN ID VLAN to which the user is bound
Calling Number Calling number bound for the ISDN user
Authorization attributes Authorization attributes of the local user
Idle TimeOut Idle timeout period of the user, in minutes
Callback-number Authorized PPP callback number of the local user
Work Directory Directory that the FTP user can access
VLAN ID Authorized VLAN of the local user
Service types that the local user can use, including FTP, LAN, PPP, Portal, SSH,
Telnet, and terminal
tion
User Profile User profile for local user authorization
Expiration date Expiration time of the local user
84
Page 91

display user-group
Syntax
display user-group [ group-name ]
View
Any view
Default level
2: System level
Parameters
group-name: User group name, a case-insensitive string of 1 to 32 characters.
Description
Use the display user-group command to display configuration information about one or all user groups.
If you do not specify any user group name, the command displays information about all users groups.
Related command: user-group.
Examples
# Display configuration information about user group abc.
<Sysname> display user-group abc
The contents of user group abc:
Authorization attributes:
Idle-cut: 120(min)
Work Directory: cfa0:
Level: 1
Acl Number: 2000
Vlan ID: 1
User-Profile: 1
Callback-number: 1
Total 1 user group(s) matched.
expiration-date (local user view)
Syntax
expiration-date time
undo expiration-date
View
Local user view
Default level
3: Manage level
Parameters
time: Expiration time of the local user, in the format HH:MM:SS-MM/DD/YYYY,
HH:MM:SS-YYYY/MM/DD, MM/DD/YYYY-HH:MM:SS, or YYYY/MM/DD-HH:MM:SS. HH:MM:SS
indicates the time, where HH ranges from 0 to 23, MM and SS range from 0 to 59. MM/DD/YYYY or
YYYY/MM/DD indicates the date, where YYYY ranges from 2000 to 2035, MM ranges from 1 to 12,
85
Page 92

and the range of DD depends on the month. Except for the zeros in 00:00:00, leading zeros can be
omitted. For example, 2:2:0-2008/2/2 equals to 02:02:00-2008/02/02.
Description
Use the expiration-date command to set the expiration time of a local user.
Use the undo expiration-date command to remove the configuration.
By default, a local user has no expiration time and no time validity checking is performed.
When some users need to access the network temporarily, create a guest account and specify a validity
time and an expiration time for the account to control the validity of the account. When a user uses the
guest account for local authentication and passes the authentication, the access device checks whether
the current system time is between the validity time and the expiration time. If so, it permits the user to
access the network. Otherwise, it denies the access request of the user.
Related commands: validity-date.
Examples
# Set the expiration time of user abc to 12:10:20 on May 31, 2008.
<Sysname> system-view
[Sysname] local-user abc
[Sysname-luser-abc] expiration-date 12:10:20-2008/05/31
group
Syntax
group group-name
undo group
View
Local user view
Default level
3: Manage level
Parameters
group-name: User group name, a case-insensitive string of 1 to 32 characters.
Description
Use the group command to assign a local user to a user group.
Use the undo group command to restore the default.
By default, a local user belongs to the system default user group system.
Examples
# Assign local user 111 to user group abc.
<Sysname> system-view
[Sysname] local-user 111
[Sysname-luser-111] group abc
86
Page 93

local-user
Syntax
local-user user-name
undo local-user { user-name | all [ service-type { ftp | lan-access | portal | ppp | ssh | telnet |
terminal } ] }
View
System view
Default level
3: Manage level
Parameters
user-name: Name for the local user, a case-sensitive string of 1 to 55 characters that does not contain the
domain name. It cannot contain any backward slash (\), forward slash (/), vertical line (|), colon (:),
asterisk (*), question mark (?) , less-than sign (<), greater-than sign (>), and the @ sign and cannot be a,
al, or all.
all: Specifies all users.
service-type: Specifies the users of a type.
• ftp—FTP users.
• lan-access—Users accessing the network through an Ethernet, such as 802.1X users.
• portal—Portal users.
• ppp—PPP users.
• ssh—SSH users.
• telnet—Telnet users.
• terminal—Users logging in through the console port or AUX port.
Description
Use the local-user command to add a local user and enter local user view.
Use the undo local-user command to remove the specified local users.
By default, no local user is configured.
Related commands: display local-user and service-type.
Examples
# Add a local user named user1.
<Sysname> system-view
[Sysname] local-user user1
[Sysname-luser-user1]
local-user password-display-mode
Syntax
local-user password-display-mode { auto | cipher-force }
undo local-user password-display-mode
87
Page 94

View
System view
Default level
2: System level
Parameters
auto: Displays the password of a local user in the mode that is specified for the user by using the
password command.
cipher-force: Displays the passwords of all local users in cipher text.
Description
Use the local-user password-display-mode command to set the password display mode for all local
users.
Use the undo local-user password-display-mode command to restore the default.
By default, the password display mode is auto.
If you configure the local-user password-display-mode cipher-force command, all existing local user
passwords will be displayed in cipher text, regardless of the configuration of the password command. If
you also save the configuration and restart the device, all existing local user passwords will always be
displayed in cipher text, no matter how you configure the local-user password-display-mode command
or the password command. The passwords configured after you restore the display mode to auto by
using the local-user password-display-mode auto command, however, are displayed as defined by the
password command.
Related commands: display local-user and password.
Examples
# Specify to display the passwords of all users in cipher text.
<Sysname> system-view
[Sysname] local-user password-display-mode cipher-force
password
Syntax
password [ { cipher | simple } password ]
undo password
View
Local user view
Default level
2: System level
Parameters
cipher: Displays the password in cipher text.
simple: Displays the password in plain text.
password: Password for the local user, case-sensitive. It must be in plain text if you specify the simple
keyword and can be in plain or cipher text if you specify the cipher keyword. A password in plain text
88
Page 95

must be a string of 1 to 63 characters that contains no blank space, for example, aabbcc. A password
in cipher text must be a string of 24 or 88 characters, for example, _(TT8F]Y\5SQ=^Q`MAF4<1!!.
Description
Use the password command to configure a password for a local user and specify whether to display the
password in cipher text or plain text.
Use the undo password command to delete the password of a local user.
With no keyword or argument specified, the command prompts you to provide a password, and the
password will be displayed in plain text. This interactive mode is supported only on devices that support
the password control feature. Support for the feature depends on the device model. For more information
about password control commands, see Security Command Reference.
With the cipher keyword specified, a password of up to 16 characters in plain text is encrypted into a
password of 24 characters in cipher text, and a password of 16 to 63 characters in plain text is encrypted
into a password of 88 characters in cipher text. For a password of 24 characters, if the system can
decrypt the password, the system treats it as a password in cipher text. Otherwise, the system treats it as
a password in plain text.
Related commands: display local-user and local-user password-display-mode.
Examples
# Set the password of local user user1 to 123456 and set the display mode to plain text.
<Sysname> system-view
[Sysname] local-user user1
[Sysname-luser-user1] password simple 123456
service-type
Syntax
service-type { ftp | lan-access | { ssh | telnet | terminal } * | portal | ppp }
undo service-type { ftp | lan-access | { ssh | telnet | terminal } * | portal | ppp }
View
Local user view
Default level
3: Manage level
Parameters
ftp: Authorizes the user to use the FTP service. The user can use the root directory of the FTP server by
default.
lan-access: Authorizes the user to use the LAN access service. Such users are mainly Ethernet users, for
example, 802.1X users.
ssh: Authorizes the user to use the SSH service..
telnet: Authorizes the user to use the Telnet service.
terminal: Authorizes the user to use the terminal service, allowing the user to login from the console or
AUX port.
portal: Authorizes the user to use the Portal service.
ppp: Authorizes the user to use the PPP service. .
89
Page 96

Description
Use the service-type command to specify the service types that a user can use.
Use the undo service-type command to delete one or all service types configured for a user.
By default, a user is authorized with no service.
You can execute the service-type command repeatedly to specify multiple service types for a user.
Examples
# Authorize user user1 to use the Telnet service.
<Sysname> system-view
[Sysname] local-user user1
[Sysname-luser-user1] service-type telnet
state (local user view)
Syntax
state { active | block }
undo state
View
Local user view
Default level
2: System level
Parameters
active: Places the local user in active state to allow the local user to request network services.
block: Places the local user in blocked state to prevent the local user from requesting network services.
Description
Use the state command to set the status of a local user.
Use the undo state command to restore the default.
By default, a local user is in active state.
By blocking a user, you disable the user from requesting network services. No other users are affected.
Related commands: local-user.
Examples
# Place local user user1 to the blocked state.
<Sysname> system-view
[Sysname] local-user user1
[Sysname-luser-user1] state block
user-group
Syntax
user-group group-name
undo user-group group-name
90
Page 97

View
System view
Default level
3: Manage level
Parameters
group-name: User group name, a case-insensitive string of 1 to 32 characters.
Description
Use the user-group command to create a user group and enter its view.
Use the undo user-group command to remove a user group.
A user group consists of a group of local users and has a set of local user attributes. You can configure
local user attributes for a user group to implement centralized management of user attributes for the local
users in the group.
A user group with one or more local users cannot be removed.
The system predefined user group system cannot be removed but you can change its configurations.
Related commands: display user-group.
Examples
# Create a user group named abc and enter its view.
<Sysname> system-view
[Sysname] user-group abc
[Sysname-ugroup-abc]
RADIUS configuration commands
accounting-on enable
Syntax
accounting-on enable [ interval seconds | send send-times ] *
undo accounting-on enable
View
RADIUS scheme view
Default level
2: System level
Parameters
seconds: Time interval for retransmitting an accounting-on packet in seconds, in the range 1 to 15. The
default is 3 seconds.
send-times: Maximum number of accounting-on packet transmission attempts, in the range 1 to 255. The
default is 50.
91
Page 98
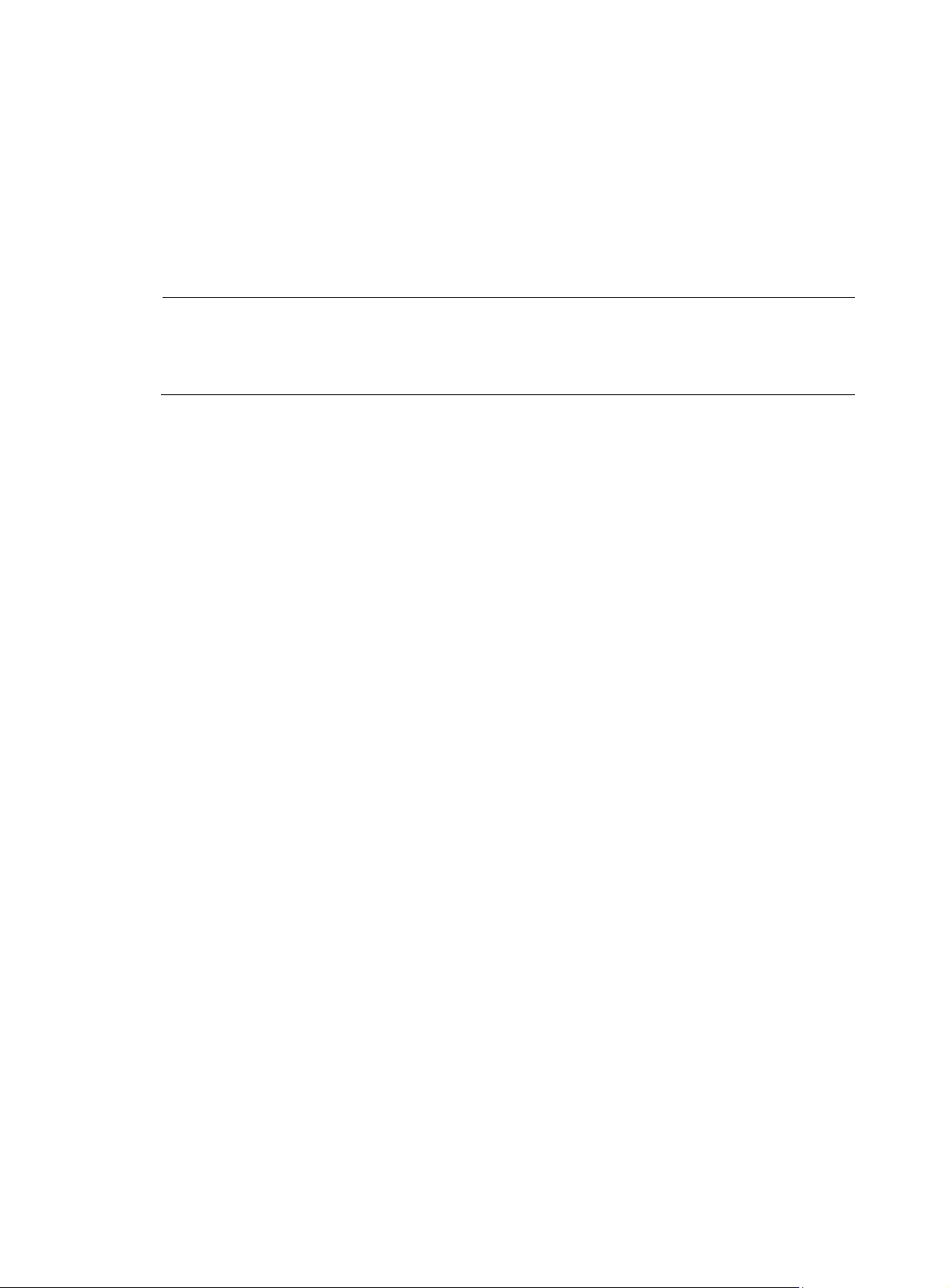
A
Description
Use the accounting-on enable command to configure the accounting-on feature. This feature enables the
device to, after rebooting, automatically send an accounting-on message to the RADIUS accounting
server stipulated by the RADIUS scheme to stop accounting for and log out online users.
Use the undo accounting-on enable command to disable the accounting-on feature.
By default, the accounting-on feature is disabled.
Parameters set with the accounting-on enable command take effect immediately.
NOTE:
command takes effect after the device reboots. For information about the save command, see
Fundamentals Command Reference
Related commands: radius scheme.
Examples
# Enable the accounting-on feature for RADIUS authentication scheme radius1, and set the
retransmission interval to 5 seconds and the transmission attempts to 15.
<Sysname> system-view
[Sysname] radius scheme radius1
[Sysname-radius-radius1] accounting-on enable interval 5 send 15
fter executing the accounting-on enable command, issue the save command to make sure that the
.
attribute 25 car
Syntax
attribute 25 car
undo attribute 25 car
View
RADIUS scheme view
Default level
2: System level
Parameters
None
Description
Use the attribute 25 car command to specify to interpret the RADIUS class attribute (attribute 25) as CAR
parameters.
Use the undo attribute 25 car command to restore the default.
By default, RADIUS attribute 25 is not interpreted as CAR parameters.
Related commands: display radius scheme and display connection.
Examples
# Specify to interpret RADIUS attribute 25 as CAR parameters.
<Sysname> system-view
[Sysname] radius scheme radius1
92
Page 99

[Sysname-radius-radius1] attribute 25 car
data-flow-format (RADIUS scheme view)
Syntax
data-flow-format { data { byte | giga-byte | kilo-byte | mega-byte } | packet { giga-packet |
kilo-packet | mega-packet | one-packet } } *
undo data-flow-format { data | packet }
View
RADIUS scheme view
Default level
2: System level
Parameters
data { byte | giga-byte | kilo-byte | mega-byte }: Specifies the unit for data flows, which can be byte,
kilobyte, megabyte, or gigabyte.
packet { giga-packet | kilo-packet | mega-packet | one-packet }: Specifies the unit for data packets,
which can be one-packet, kilo-packet, mega-packet, or giga-packet.
Description
Use the data-flow-format command to set the traffic statistics unit for data flows or packets.
Use the undo data-flow-format command to restore the default.
By default, the unit for data flows is byte and that for data packets is one-packet.
The unit for data flows and that for packets must be consistent with those on the RADIUS server.
Otherwise, accounting cannot be performed correctly.
Related commands: display radius scheme.
Examples
# Set the traffic statistics unit for data flows and that for packets to kilobytes and kilo-packets respectively
in RADIUS scheme radius1.
<Sysname> system-view
[Sysname] radius scheme radius1
[Sysname-radius-radius1] data-flow-format data kilo-byte packet kilo-packet
display radius scheme
Syntax
display radius scheme [ radius-scheme-name ]
View
Any view
Default level
2: System level
Parameters
radius-scheme-name: RADIUS scheme name.
93
Page 100
p
Description
Use the display radius scheme command to display the configuration information of RADIUS schemes.
If you do not specify any RADIUS scheme, the command displays the configuration information of all
RADIUS schemes.
Related commands: radius scheme.
Examples
# Display the configuration information of all RADIUS schemes.
<Sysname> display radius scheme
-----------------------------------------------------------------SchemeName : radius1
Index : 0 Type : extended
Primary Auth Server:
IP: 1.1.1.1 Port: 1812 State: active
Encryption Key : 345
Primary Acct Server:
IP: 1.1.1.1 Port: 1813 State: active
Encryption Key : 345
Second Auth Server:
IP: 1.1.2.1 Port: 1812 State: active
Encryption Key : N/A
IP: 1.1.3.1 Port: 1812 State: active
Encryption Key : N/A
Second Acct Server:
IP: 1.1.2.1 Port: 1813 State: block
Encryption Key : N/A
Auth Server Encryption Key : 123
Acct Server Encryption Key : N/A
Accounting-On packet disable, send times : 50 , interval : 3s
Interval for timeout(second) : 3
Retransmission times for timeout : 3
Interval for realtime accounting(minute) : 12
Retransmission times of realtime-accounting packet : 5
Retransmission times of stop-accounting packet : 500
Quiet-interval(min) : 5
Username format : without-domain
Data flow unit : Byte
Packet unit : one
NAS-IP address : 1.1.1.1
Attribute 25 : car
-----------------------------------------------------------------Total 1 RADIUS scheme(s).
Table 22 Output description
Field Descri
SchemeName Name of the RADIUS scheme.
Index Index number of the RADIUS scheme.
tion
94
 Loading...
Loading...