Page 1
Prestige 652
ADSL Security Router
User's Guide
Version 3.40
August 2002
Page 2

Prestige 652 ADSL Security Router
Copyright
Copyright © 2002 by ZyXEL Communications Corporation.
The contents of this publication may not be reproduced in any part or as a whole, transcribed, stored in a
retrieval system, translated into any language, or transmitted in any form or by any means, electronic,
mechanical, magnetic, optical, chemical, photocopying, manual, or otherwise, without the prior written
permission of ZyXEL Communications Corporation.
Published by ZyXEL Communications Corporation. All rights reserved.
Disclaimer
ZyXEL does not assume any liability arising out of the application or use of any products, or software
described herein. Neither does it convey any license under its patent rights nor the patent rights of others.
ZyXEL further reserves the right to make changes in any products described herein without notice. This
publication is subject to change without notice.
Trademarks
ZyNOS (ZyXEL Network Operating System) is a registered trademark of ZyXEL Communications, Inc.
Other trademarks mentioned in this publication are used for identification purposes only and may be
properties of their respective owners.
ii Copyright
Page 3

Prestige 652 ADSL Security Router
Federal Communications Commission
(FCC) Interference Statement
This device complies with Part 15 of FCC rules. Operation is subject to the following two conditions:
• This device may not cause harmful interference.
• This device must accept any interference received, including interference that may cause undesired
operations.
This equipment has been tested and found to comply with the limits for a Class B digital device pursuant to
Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful
interference in a commercial environment. This equipment generates, uses, and can radiate radio frequency
energy, and if not installed and used in accordance with the instructions, may cause harmful interference to
radio communications.
If this equipment does cause harmful interference to radio/television reception, which can be determined by
turning the equipment off and on, the user is encouraged to try to correct the interference by one or more of
the following measures:
1. Reorient or relocate the receiving antenna.
2. Increase the separation between the equipment and the receiver.
3. Connect the equipment into an outlet on a circuit different from that to which the receiver is connected.
4. Consult the dealer or an experienced radio/TV technician for help.
Notice 1
Changes or modifications not expressly approved by the party responsible for compliance could void the
user's authority to operate the equipment.
Certifications
Refer to the product page at www.zyxel.com.
FCC Statement iii
Page 4

Prestige 652 ADSL Security Router
Information for Canadian Users
The Industry Canada label identifies certified equipment. This certification means that the equipment meets
certain telecommunications network protective operation and safety requirements. The Industry Canada
label does not guarantee that the equipment will operate to a user's satisfaction.
Before installing this equipment, users should ensure that it is permissible to be connected to the facilities of
the local telecommunications company. The equipment must also be installed using an acceptable method
of connection. In some cases, the company's inside wiring associated with a single line individual service
may be extended by means of a certified connector assembly. The customer should be aware that
compliance with the above conditions may not prevent degradation of service in some situations.
Repairs to certified equipment should be made by an authorized Canadian maintenance facility
designated by the supplier. Any repairs or alterations made by the user to this equipment, or
equipment malfunctions, may give the telecommunications company cause to request the user to
disconnect the equipment.
For their own protection, users should ensure that the electrical ground connections of the power utility,
telephone lines, and internal metallic water pipe system, if present, are connected together. This precaution
may be particularly important in rural areas.
Caution
Users should not attempt to make such connections themselves, but should contact the
appropriate electrical inspection authority, or electrician, as appropriate.
Note
This digital apparatus does not exceed the Class A limits for radio noise emissions from digital apparatus
set out in the radio interference regulations of Industry Canada.
iv Information for Canadian Users
Page 5

Prestige 652 ADSL Security Router
ZyXEL Limited Warranty
ZyXEL warrants to the original end user (purchaser) that this product is free from any defects in materials
or workmanship for a period of up to two years from the date of purchase. During the warranty period, and
upon proof of purchase, should the product have indications of failure due to faulty workmanship and/or
materials, ZyXEL will, at its discretion, repair or replace the defective products or components without
charge for either parts or labor, and to whatever extent it shall deem necessary to restore the product or
components to proper operating condition. Any replacement will consist of a new or re-manufactured
functionally equivalent product of equal value, and will be solely at the discretion of ZyXEL. This warranty
shall not apply if the product is modified, misused, tampered with, damaged by an act of God, or subjected
to abnormal working conditions.
Note
Repair or replacement, as provided under this warranty, is the exclusive remedy of the purchaser. This
warranty is in lieu of all other warranties, express or implied, including any implied warranty of
merchantability or fitness for a particular use or purpose. ZyXEL shall in no event be held liable for indirect
or consequential damages of any kind of character to the purchaser.
To obtain the services of this warranty, contact ZyXEL's Service Center for your Return Material
Authorization number (RMA). Products must be returned Postage Prepaid. It is recommended that the unit
be insured when shipped. Any returned products without proof of purchase or those with an out-dated
warranty will be repaired or replaced (at the discretion of ZyXEL) and the customer will be billed for parts
and labor. All repaired or replaced products will be shipped by ZyXEL to the corresponding return address,
Postage Paid. This warranty gives you specific legal rights, and you may also have other rights that vary
from country to country.
Safety Warnings
1. To reduce the risk of fire, use only No. 26 AWG or larger telephone wire.
2. Do not use this product near water, for example, in a wet basement or near a swimming pool.
3. Avoid using this product during an electrical storm. There may be a remote risk of electric shock from
lightening.
ZyXEL Limited Waranty v
Page 6
Prestige 652 ADSL Security Router
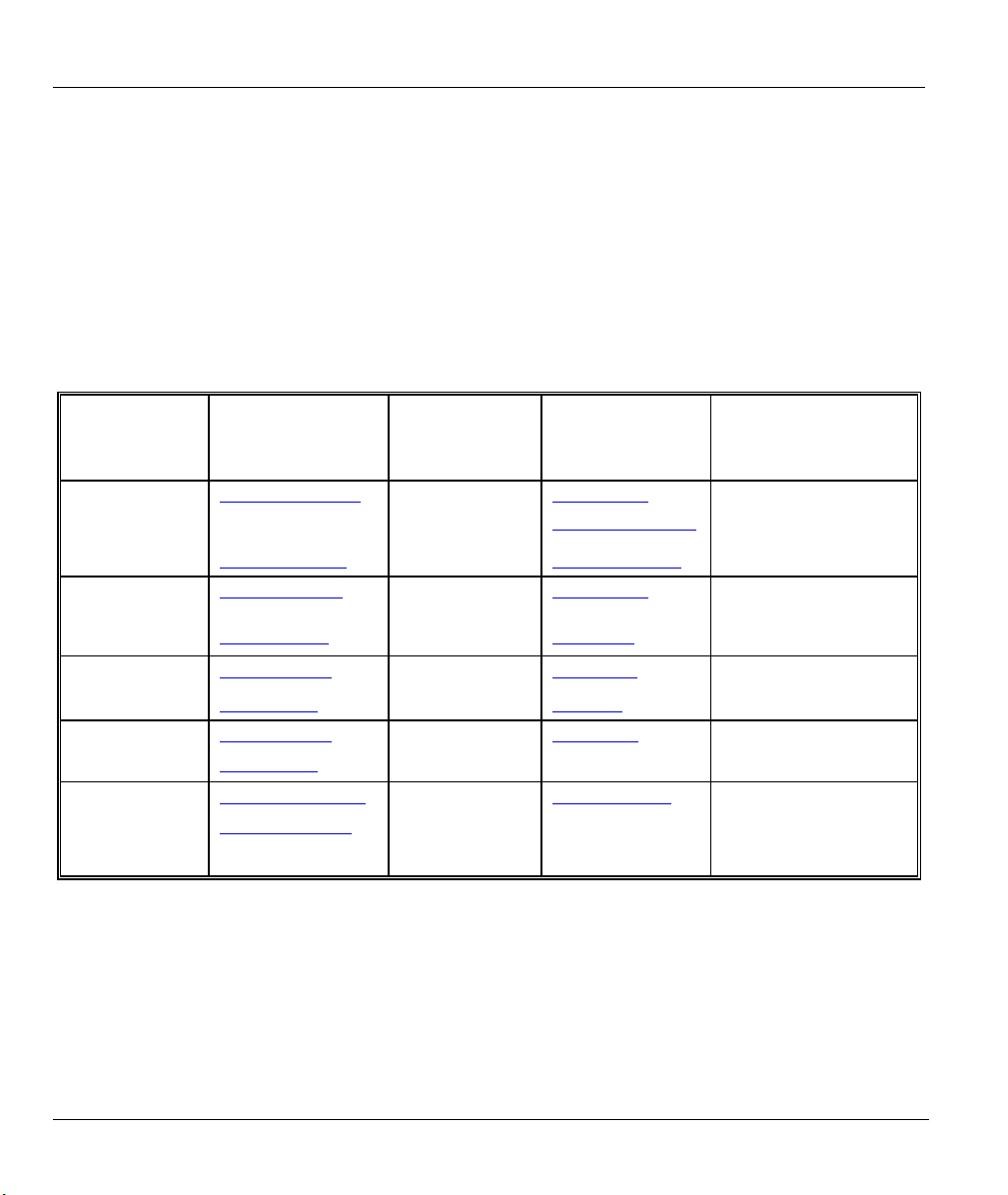
Customer Support
Please have the following information ready when you contact customer support.
• Product model and serial number.
• Information in Menu 24.2.1 – System Information.
• Warranty Information.
• Date that you received your device.
• Brief description of the problem and the steps you took to solve it.
METHOD
LOCATION
WORLDWIDE
E-MAIL
SUPPORT/SALES
support@zyxel.com.tw +886-3-578-3942 www.zyxel.com
sales@zyxel.com.tw
support@zyxel.com +1-714-632-0882
sales@zyxel.com
support@zyxel.dk +45-3955-0700 www.zyxel.dk SCANDINAVIA
sales@zyxel.dk
support@zyxel.de +49-2405-6909-0 www.zyxel.de GERMANY
sales@zyxel.de
support@zyxel.com.my +603-795-44-688 www.zyxel.com.my MALAYSIA
sales@zyxel.com.my
+886-3-578-2439 ftp.europe.zyxel.com
+1-714-632-0858 ftp.zyxel.com
+45-3955-0707 ftp.zyxel.dk
+49-2405-6909-99
TELEPHONE/FAX WEB SITE/ FTP SITE REGULAR MAIL
www.europe.zyxel.com
www.zyxel.com NORTH AMERICA
800-255-4101
+603-795-34-407
ZyXEL Communications
Corp., 6 Innovation Road II,
Science-Based Industrial
Park, Hsinchu, Taiwan 300,
R.O.C.
ZyXEL Communications Inc.,
1650 Miraloma Avenue,
Placentia, CA 92870, U.S.A.
ZyXEL Communications A/S,
Columbusvej 5, 2860
Soeborg, Denmark.
ZyXEL Deutschland GmbH.
Adenauerstr. 20/A4 D-52146
Wuerselen, Germany
Lot B2-06, PJ Industrial Park,
Section 13, Jalan Kemajuan,
46200 Petaling Jaya
Selangor Darul Ehasn,
Malaysia
vi Customer Support
Page 7

Prestige 652 ADSL Security Router
Table of Contents
GETTING STARTED........................................................................................................................................I
Chapter 1 Getting To Know Your Prestige.................................................................................................1-1
1.1 Prestige 652 ADSL Security Router ..........................................................................................1-1
1.2 Features ......................................................................................................................................1-1
1.3 Applications for the Prestige 652 ...............................................................................................1-6
Chapter 2 Hardware Installation and Initial Setup..................................................................................2-1
2.1 Front Panel LEDs of the P652....................................................................................................2-1
2.2 Rear Panel and Connections.......................................................................................................2-2
2.3 Additional Installation Requirements.........................................................................................2-3
2.4 P652 with POTS.........................................................................................................................2-4
2.5 P652 with ISDN .........................................................................................................................2-6
2.6 Turning On Your Prestige..........................................................................................................2-7
2.7 Configuring Your Prestige For Internet Access.........................................................................2-7
2.8 Resetting the Prestige.................................................................................................................2-8
2.9 Navigating the SMT Interface..................................................................................................2-10
2.10 Changing the System Password ...............................................................................................2-13
Chapter 3 General Setup.............................................................................................................................3-1
3.1 System Name .............................................................................................................................3-1
3.2 Dynamic DNS ............................................................................................................................3-1
3.3 General Setup.............................................................................................................................3-2
3.4 LAN Setup .................................................................................................................................3-4
3.5 Protocol Dependent Ethernet Setup ...........................................................................................3-5
Chapter 4 Internet Access ...........................................................................................................................4-1
4.1 Factory Ethernet Defaults...........................................................................................................4-1
4.2 LANs and WANs .......................................................................................................................4-1
4.3 TCP/IP Parameters.....................................................................................................................4-2
4.4 IP Multicast ................................................................................................................................4-5
4.5 IP Policies ..................................................................................................................................4-5
4.6 IP Alias.......................................................................................................................................4-5
4.7 Route IP Setup............................................................................................................................4-8
4.8 TCP/IP Ethernet Setup and DHCP.............................................................................................4-8
4.9 VPI and VCI.............................................................................................................................4-11
4.10 Multiplexing.............................................................................................................................4-11
4.11 Encapsulation...........................................................................................................................4-11
4.12 IP Address Assignment............................................................................................................4-12
4.13 Internet Access Configuration..................................................................................................4-13
Advanced Applications .................................................................................................................................... II
Table of Contents vii
Page 8

Prestige 652 ADSL Security Router
Chapter 5 Remote Node Configuration ..................................................................................................... 5-1
5.1 Remote Node Setup ...................................................................................................................5-1
5.2 Remote Node Setup ...................................................................................................................5-6
5.3 Remote Node Filter.................................................................................................................... 5-8
Chapter 6 Remote Node TCP/IP Configuration........................................................................................6-1
6.1 TCP/IP Configuration ................................................................................................................6-1
Chapter 7 Bridging Setup ...........................................................................................................................7-1
7.1 Bridging in General....................................................................................................................7-1
7.2 Bridge Ethernet Setup................................................................................................................7-1
Chapter 8 Network Address Translation (NAT)........................................................................................8-1
8.1 Introduction................................................................................................................................8-1
8.2 Using NAT.................................................................................................................................8-6
8.3 NAT Setup ................................................................................................................................. 8-8
8.4 NAT Server Sets – Port Forwarding........................................................................................8-16
8.5 General NAT Examples...........................................................................................................8-20
FIREWALL AND CONTENT FILTERS........................................................................................................ III
Chapter 9 Firewalls......................................................................................................................................9-1
9.1 What Is a Firewall?.................................................................................................................... 9-1
9.2 Types of Firewalls......................................................................................................................9-1
9.3 Introduction to ZyXEL’s Firewall ............................................................................................. 9-2
9.4 Denial of Service .......................................................................................................................9-3
9.5 Stateful Inspection .....................................................................................................................9-7
9.6 Guidelines For Enhancing Security With Your Firewall......................................................... 9-11
9.7 Packet Filtering Vs Firewall ....................................................................................................9-12
Chapter 10 Introducing the Prestige Firewall.........................................................................................10-1
10.1 Remote Management and the Firewall ....................................................................................10-1
10.2 Access Methods....................................................................................................................... 10-1
10.3 Using Prestige SMT Menus.....................................................................................................10-1
Chapter 11 Using the Prestige Web Configurator................................................................................... 11-1
11.1 Web Configurator Login and Main Menu Screens ..................................................................11-1
11.2 Enabling the Firewall............................................................................................................... 11-2
11.3 E-mail ......................................................................................................................................11-2
11.4 Attack Alert..............................................................................................................................11-6
Chapter 12 Creating Custom Rules .........................................................................................................12-1
12.1 Rules Overview........................................................................................................................12-1
12.2 Rule Logic Overview............................................................................................................... 12-1
12.3 Connection Direction...............................................................................................................12-3
12.4 Rule Summary .........................................................................................................................12-4
12.5 Predefined Services..................................................................................................................12-6
12.6 Timeout.................................................................................................................................. 12-13
Chapter 13 Customized Services .............................................................................................................. 13-1
viii Table of Contents
Page 9

Prestige 652 ADSL Security Router
13.1 Introduction..............................................................................................................................13-1
13.2 Creating/Editing A Customized Service ..................................................................................13-3
13.3 Example DHCP Negotiation and Syslog Connection from the Internet ..................................13-4
Chapter 14 Logs .........................................................................................................................................14-1
14.1 Log Screen ...............................................................................................................................14-1
Chapter 15 Content Filtering....................................................................................................................15-1
15.1 Keyword...................................................................................................................................15-1
15.2 Schedule...................................................................................................................................15-1
15.3 Trusted .....................................................................................................................................15-1
15.4 Logs..........................................................................................................................................15-1
Advanced Management...................................................................................................................................IV
Chapter 16 Filter Configuration...............................................................................................................16-1
16.1 About Filtering.........................................................................................................................16-1
16.2 Configuring a Filter Set............................................................................................................16-4
16.3 Configuring a Filter Rule .........................................................................................................16-9
16.4 Filter Types and NAT ............................................................................................................16-16
16.5 Example Filter........................................................................................................................16-16
16.6 Applying Filters and Factory Defaults...................................................................................16-19
Chapter 17 SNMP Configuration .............................................................................................................17-1
17.1 About SNMP............................................................................................................................17-1
17.2 Supported MIBs .......................................................................................................................17-2
17.3 SNMP Configuration ...............................................................................................................17-2
17.4 SNMP Traps.............................................................................................................................17-4
Chapter 18 System Information and Diagnosis.......................................................................................18-1
18.1 System Status ...........................................................................................................................18-1
18.2 System Information and Console Port Speed...........................................................................18-3
18.3 Log and Trace ..........................................................................................................................18-5
18.4 Diagnostic ................................................................................................................................18-8
18.5 Command Interpreter Mode .....................................................................................................18-9
Chapter 19 Firmware and Configuration File Maintenance..................................................................19-1
19.1 Filename Conventions..............................................................................................................19-1
19.2 Backup Configuration ..............................................................................................................19-2
19.3 Restore Configuration ..............................................................................................................19-7
19.4 Uploading Firmware and Configuration Files........................................................................19-10
Chapter 20 System Maintenance and Information .................................................................................20-1
20.1 Command Interpreter Mode .....................................................................................................20-1
20.2 Call Control Support ................................................................................................................20-2
20.3 Time and Date Setting..............................................................................................................20-4
Chapter 21 Remote Management.............................................................................................................21-1
21.1 About Telnet Configuration .....................................................................................................21-1
21.2 Telnet Under NAT ...................................................................................................................21-1
Table of Contents ix
Page 10

Prestige 652 ADSL Security Router
21.3 Telnet Capabilities ................................................................................................................... 21-1
21.4 FTP ..........................................................................................................................................21-2
21.5 Web..........................................................................................................................................21-2
21.6 Remote Management...............................................................................................................21-2
21.7 Remote Management and NAT ...............................................................................................21-4
21.8 System Timeout.......................................................................................................................21-4
Chapter 22 IP Policy Routing ...................................................................................................................22-1
22.1 Introduction..............................................................................................................................22-1
22.2 Benefits.................................................................................................................................... 22-1
22.3 Routing Policy ......................................................................................................................... 22-1
22.4 IP Routing Policy Setup...........................................................................................................22-2
22.5 Applying an IP Policy.............................................................................................................. 22-5
22.6 IP Policy Routing Example......................................................................................................22-7
CALL SCHEDULING, VPN/IPSEC AND INTERNAL SPTGEN ................................................................. V
Chapter 23 Call Scheduling ...................................................................................................................... 23-1
23.1 Introduction..............................................................................................................................23-1
Chapter 24 Introduction to IPSec.............................................................................................................24-1
24.1 Introduction..............................................................................................................................24-1
24.2 IPSec Architecture................................................................................................................... 24-3
24.3 Encapsulation........................................................................................................................... 24-5
24.4 IPSec and NAT........................................................................................................................ 24-5
Chapter 25 VPN/IPSec Setup....................................................................................................................25-1
25.1 VPN/IPSec Setup..................................................................................................................... 25-1
25.2 IPSec Algorithms..................................................................................................................... 25-2
25.3 IPSec Summary........................................................................................................................25-3
25.4 IPSec Setup..............................................................................................................................25-8
25.5 IKE Setup...............................................................................................................................25-12
25.6 Manual Setup ......................................................................................................................... 25-17
Chapter 26 SA Monitor .............................................................................................................................26-1
1.1. Introduction..............................................................................................................................26-1
Chapter 27 IPSec Log................................................................................................................................27-1
27.1 IPSec Logs...............................................................................................................................27-1
Chapter 28 Internal SPTGEN ..................................................................................................................28-1
28.1 The Configuration Text File Format........................................................................................ 28-1
28.2 Internal SPTGEN FTP Download Example ............................................................................28-3
28.3 Internal SPTGEN FTP Upload Example .................................................................................28-4
ADDITIONAL INFORMATION ...................................................................................................................VI
Chapter 29 Troubleshooting......................................................................................................................29-1
29.1 Problems Starting Up the Prestige ........................................................................................... 29-1
29.2 Problems with the LAN LED...................................................................................................29-1
29.3 Problems with the DSL LED ................................................................................................... 29-2
x Table of Contents
Page 11

Prestige 652 ADSL Security Router
29.4 Problems with the LAN Interface ............................................................................................29-2
29.5 Problems with the WAN Interface ...........................................................................................29-2
29.6 Problems with Internet Access.................................................................................................29-3
29.7 Problems with the Password ....................................................................................................29-3
29.8 Problems with the Web Configurator.......................................................................................29-4
29.9 Problems with Remote Management .......................................................................................29-4
Table of Contents xi
Page 12

Prestige 652 ADSL Security Router
List of Figures
Figure 1-1 Internet Access Application...........................................................................................................1-7
Figure 1-2 Firewall Application......................................................................................................................1-8
Figure 1-3 LAN-to-LAN Application.............................................................................................................1-8
Figure 1-4 VPN Application...........................................................................................................................1-9
Figure 2-1 Front Panel ....................................................................................................................................2-1
Figure 2-2 Rear Panel .....................................................................................................................................2-2
Figure 2-3 Connecting a POTS Splitter .......................................................................................................... 2-5
Figure 2-4 Connecting a Microfilter ...............................................................................................................2-6
Figure 2-5 P652 with ISDN............................................................................................................................2-6
Figure 2-6 Power-On Display.........................................................................................................................2-7
Figure 2-7 Login Screen .................................................................................................................................2-8
Figure 2-8 SMT Menu Overview .................................................................................................................2-10
Figure 2-9 SMT Main Menu.........................................................................................................................2-12
Figure 2-10 Menu 23 — System Password ..................................................................................................2-13
Figure 3-1 Menu 1 — General Setup..............................................................................................................3-2
Figure 3-2 Configure Dynamic DNS..............................................................................................................3-3
Figure 3-3 Menu 3 — Ethernet Setup.............................................................................................................3-5
Figure 3-4 Menu 3.1 — LAN Port Filter Setup..............................................................................................3-5
Figure 4-1 LAN & WAN IPs ..........................................................................................................................4-2
Figure 4-2 Physical Network .......................................................................................................................... 4-6
Figure 4-3 Partitioned Logical Networks .......................................................................................................4-6
Figure 4-4 Menu 3.2 — TCP/IP and DHCP Ethernet Setup ..........................................................................4-6
Figure 4-5 Menu 3.2.1 — IP Alias Setup........................................................................................................4-7
Figure 4-6 Menu 1 — General Setup..............................................................................................................4-8
Figure 4-7 Menu 3.2 — TCP/IP and DHCP Ethernet Setup ...........................................................................4-9
List of Figures xii
Page 13

Prestige 652 ADSL Security Router
Figure 4-8 Example of Traffic Shaping........................................................................................................ 4-15
Figure 4-9 Internet Access Setup ................................................................................................................. 4-15
Figure 5-1 Menu 11 — Remote Node Setup.................................................................................................. 5-2
Figure 5-2 Menu 11.1 — Remote Node Profile............................................................................................. 5-4
Figure 5-3 Remote Node Network Layer Options ......................................................................................... 5-7
Figure 5-4 Menu 11.5 — Remote Node Filter ............................................................................................... 5-9
Figure 5-5 Menu 11.5 — Remote Node Filter (PPPoE or PPPoA Encapsulation) ....................................... 5-9
Figure 6-1 Menu 11.6 for RFC-1483 or ENET ENCAP with VC-based Multiplexing.................................. 6-2
Figure 6-2 Menu 11.6 for LLC-based Multiplexing or PPPoA or PPPoE Encapsulation.............................. 6-2
Figure 6-3 Sample IP Addresses for a TCP/IP LAN-to-LAN Connection..................................................... 6-3
Figure 6-4 Remote Node Network Layer Options ......................................................................................... 6-5
Figure 6-5 Sample Static Routing Topology .................................................................................................. 6-7
Figure 6-6 Menu 12 — Static Route Setup.................................................................................................... 6-8
Figure 6-7 Menu 12.1 — IP Static Route Setup............................................................................................. 6-8
Figure 6-8 Edit IP Static Route ...................................................................................................................... 6-9
Figure 7-1 Menu 11.3 — Remote Node Bridging Options ............................................................................ 7-2
Figure 7-2 Menu 12.3.1 — Edit Bridge Static Route..................................................................................... 7-3
Figure 8-1 How NAT Works .......................................................................................................................... 8-3
Figure 8-2 NAT Application With IP Alias .................................................................................................... 8-4
Figure 8-3 Menu 4 — Applying NAT for Internet Access ............................................................................. 8-7
Figure 8-4 Menu 11.3 — Applying NAT to the Remote Node ...................................................................... 8-8
Figure 8-5 Menu 15 — NAT Setup................................................................................................................ 8-9
Figure 8-6 Menu 15.1 — Address Mapping Sets ........................................................................................... 8-9
Figure 8-7 Menu 15.1.255 — SUA Address Mapping Rules ........................................................................8-11
Figure 8-8 Menu 15.1.1 — First Set ............................................................................................................ 8-12
Figure 8-9 Menu 15.1.1.1 — Editing/Configuring an Individual Rule in a Set........................................... 8-15
Figure 8-10 Menu 15.2 — NAT Server Setup.............................................................................................. 8-18
xiii List of Figures
Page 14

Prestige 652 ADSL Security Router
Figure 8-11 Menu 15.2.1 — NAT Server Setup ...........................................................................................8-18
Figure 8-12 Multiple Servers Behind NAT Example....................................................................................8-19
Figure 8-13 NAT Example 1......................................................................................................................... 8-20
Figure 8-14 Menu 4 — Internet Access & NAT Example ............................................................................8-21
Figure 8-15 NAT Example 2......................................................................................................................... 8-22
Figure 8-16 Menu 15.2.1 — Specifying an Inside Server ............................................................................8-23
Figure 8-17 NAT Example 3......................................................................................................................... 8-25
Figure 8-18 Example 3: Menu 11.3 ..............................................................................................................8-26
Figure 8-19 Example 3: Menu 15.1.1.1........................................................................................................8-26
Figure 8-20 Example 3: Final Menu 15.1.1..................................................................................................8-27
Figure 8-21 NAT Example 4......................................................................................................................... 8-29
Figure 8-22 Example 4: Menu 15.1.1.1 — Address Mapping Rule.............................................................. 8-29
Figure 8-23 Example 4: Menu 15.1.1 — Address Mapping Rules ..............................................................8-30
Figure 9-1 Prestige Firewall Application........................................................................................................9-3
Figure 9-2 Three-Way Handshake ..................................................................................................................9-5
Figure 9-3 SYN Flood ....................................................................................................................................9-5
Figure 9-4 Smurf Attack .................................................................................................................................9-6
Figure 9-5 Stateful Inspection.........................................................................................................................9-8
Figure 10-1 Menu 21 — Filter and Firewall Setup.......................................................................................10-1
Figure 10-2 Menu 21.2 — Firewall Setup....................................................................................................10-2
Figure 10-3 Example Firewall Log...............................................................................................................10-2
Figure 11-1 Enabling the Firewall ................................................................................................................ 11-2
Figure 11-2 E-mail Screen............................................................................................................................ 11-3
Figure 11-3 E-mail Log ................................................................................................................................ 11-6
Figure 11-4 Attack Alert ............................................................................................................................... 11-8
Figure 12-1 LAN to WAN Traffic.................................................................................................................12-3
Figure 12-2 WAN to LAN Traffic.................................................................................................................12-4
List of Figures xiv
Page 15

Prestige 652 ADSL Security Router
Figure 12-3 Firewall Rules Summary — First Screen................................................................................. 12-5
Figure 12-4 Creating/Editing A Firewall Rule ........................................................................................... 12-10
Figure 12-5 Adding/Editing Source and Destination Addresses ................................................................ 12-12
Figure 12-6 Timeout Screen....................................................................................................................... 12-13
Figure 13-1 Customized Services ................................................................................................................ 13-1
Figure 13-2 Creating/Editing A Customized Service ................................................................................... 13-3
Figure 13-3 Configure Source IP................................................................................................................. 13-5
Figure 13-4 Customized Service for Syslog................................................................................................. 13-6
Figure 13-5 Syslog Rule Configuration ....................................................................................................... 13-7
Figure 13-6 Example Rule Summary........................................................................................................... 13-8
Figure 14-1 Log Screen................................................................................................................................ 14-1
Figure 16-1 Outgoing Packet Filtering Process ........................................................................................... 16-2
Figure 16-2 Filter Rule Process.................................................................................................................... 16-3
Figure 16-4 Menu 21 — Filter and Firewall Setup...................................................................................... 16-4
Figure 16-5 Menu 21.1 — Filter Set Configuration..................................................................................... 16-5
Figure 16-6 NetBIOS_WAN Filter Rules Summary ....................................................................................16-6
Figure 16-7 NetBIOS _LAN Filter Rules Summary.................................................................................... 16-6
Figure 16-8 PPPoE Filter Rules Summary................................................................................................... 16-7
Figure 16-9 TEL_FTP_WEB_SNM Filter Rules Summary ........................................................................ 16-7
Figure 16-10 Menu 21.1.7.1 — TCP/IP Filter Rule................................................................................... 16-10
Figure 16-11 Executing an IP Filter ........................................................................................................... 16-13
Figure 16-12 Menu 21.1.5.1 — Generic Filter Rule .................................................................................. 16-14
Figure 16-13 Protocol and Device Filter Sets ............................................................................................ 16-16
Figure 16-14 Sample Telnet Filter.............................................................................................................. 16-17
Figure 16-15 Sample Filter — Menu 21.1.9.1 ........................................................................................... 16-18
Figure 16-16 Sample Filter Rules Summary — Menu 21.1.9.................................................................... 16-19
Figure 16-17 Filtering Ethernet Traffic...................................................................................................... 16-20
xv List of Figures
Page 16

Prestige 652 ADSL Security Router
Figure 16-18 Filtering Remote Node Traffic ..............................................................................................16-22
Figure 16-19 Filtering Remote Node Traffic with PPPoE ..........................................................................16-22
Figure 17-1 SNMP Management Model.......................................................................................................17-1
Figure 17-2 Menu 22 — SNMP Configuration ............................................................................................17-3
Figure 18-1 Menu 24 — System Maintenance.............................................................................................18-1
Figure 18-2 Menu 24.1 — System Maintenance — Status...........................................................................18-2
Figure 18-3 Menu 24.2 — System Information and Console Port Speed.....................................................18-3
Figure 18-4 Menu 24.2.1 — System Maintenance — Information .............................................................. 18-4
Figure 18-5 Menu 24.2.2 — System Maintenance — Change Console Port Speed..................................... 18-5
Figure 18-6 Menu 24.3 — System Maintenance — Log and Trace .............................................................18-5
Figure 18-7 Sample Error and Information Messages..................................................................................18-6
Figure 18-8 Menu 24.3.2 — System Maintenance — Syslog and Accounting ............................................18-6
Figure 18-9 Menu 24.4 — System Maintenance — Diagnostic ................................................................... 18-8
Figure 18-10 Command Mode......................................................................................................................18-9
Figure 19-1 Telnet in Menu 24.5 .................................................................................................................. 19-3
Figure 19-2 FTP Session Example................................................................................................................19-4
Figure 19-3 System Maintenance — Backup Configuration........................................................................19-6
Figure 19-4 System Maintenance — Starting Xmodem Download Screen..................................................19-7
Figure 19-5 Backup Configuration Example................................................................................................19-7
Figure 19-6 Successful Backup Confirmation Screen .................................................................................. 19-7
Figure 19-7 Telnet into Menu 24.6 ...............................................................................................................19-8
Figure 19-8 Restore Using FTP Session Example........................................................................................19-9
Figure 19-9 System Maintenance — Restore Configuration........................................................................ 19-9
Figure 19-10 System Maintenance — Starting Xmodem Download Screen................................................19-9
Figure 19-11 Restore Configuration Example ............................................................................................19-10
Figure 19-12 Successful Restoration Confirmation Screen........................................................................19-10
Figure 19-13 Telnet Into Menu 24.7.1 — Upload System Firmware .........................................................19-11
List of Figures xvi
Page 17

Prestige 652 ADSL Security Router
Figure 19-14 Telnet Into Menu 24.7.2 — System Maintenance .................................................................19-11
Figure 19-15 FTP Session Example of Firmware File Upload .................................................................. 19-12
Figure 19-16 Menu 24.7.1 as seen using the Console Port ........................................................................ 19-14
Figure 19-17 Example Xmodem Upload ................................................................................................... 19-14
Figure 19-18 Menu 24.7.2 as seen using the Console Port ........................................................................ 19-15
Figure 19-19 Example Xmodem Upload ................................................................................................... 19-16
Figure 20-1 Command Mode in Menu 24.................................................................................................... 20-1
Figure 20-2 Valid Commands ...................................................................................................................... 20-2
Figure 20-3 Call Control.............................................................................................................................. 20-2
Figure 20-4 Budget Management................................................................................................................. 20-3
Figure 20-5 Menu 24 — System Maintenance ............................................................................................ 20-4
Figure 20-6 Menu 24.10 System Maintenance — Time and Date Setting ................................................... 20-4
Figure 21-1 Telnet Configuration on a TCP/IP Network ............................................................................. 21-1
Figure 21-2 Menu 24.11 – Remote Management Control............................................................................ 21-3
Figure 22-1 IP Routing Policy Setup ........................................................................................................... 22-2
Figure 22-2 Menu 25.1 — Sample IP Routing Policy Setup ....................................................................... 22-3
Figure 22-3 IP Routing Policy ..................................................................................................................... 22-4
Figure 22-4 Menu 3.2 — TCP/IP and DHCP Ethernet Setup ...................................................................... 22-6
Figure 22-5 Menu 11.3 — Remote Node Network Layer Options.............................................................. 22-6
Figure 22-6 Example of IP Policy Routing.................................................................................................. 22-7
Figure 22-7 IP Routing Policy Example ...................................................................................................... 22-8
Figure 22-8 IP Routing Policy ..................................................................................................................... 22-9
Figure 22-9 Applying IP Policies................................................................................................................. 22-9
Figure 23-1 Menu 26 - Schedule Setup........................................................................................................ 23-1
Figure 23-2 Schedule Set Setup ................................................................................................................... 23-2
Figure 23-3 Applying Schedule Set(s) to a Remote Node (PPPoE)............................................................. 23-4
Figure 24-1 Encryption and Decryption....................................................................................................... 24-2
xvii List of Figures
Page 18

Prestige 652 ADSL Security Router
Figure 24-2 VPN Application.......................................................................................................................24-3
Figure 24-3 IPSec Architecture.....................................................................................................................24-4
Figure 24-4 Transport and Tunnel Mode IPSec Encapsulation.....................................................................24-5
Figure 25-1 VPN SMT Menu Tree ...............................................................................................................25-1
Figure 25-2 Menu 27 — VPN/IPSec Setup..................................................................................................25-2
Figure 25-3 IPSec Summary Fields..............................................................................................................25-3
Figure 25-4 Telecommuter’s Prestige Configuration....................................................................................25-5
Figure 25-5 Headquarters Prestige Configuration ........................................................................................25-5
Figure 25-6 Menu 27.1 — IPSec Summary..................................................................................................25-6
Figure 25-7 Menu 27.1.1 — IPSec Setup.....................................................................................................25-9
Figure 25-8 Two Phases to set up the IPSec SA ......................................................................................... 25-13
Figure 25-9 Menu 27.1.1.1 — IKE Setup...................................................................................................25-15
Figure 25-10 Menu 27.1.1.2 — Manual Setup ...........................................................................................25-18
Figure 26-1 Menu 27.2 — SA Monitor ........................................................................................................26-1
Figure 27-1 Example VPN Initiator IPSec Log ............................................................................................27-1
Figure 27-2 Example VPN Responder IPSec Log........................................................................................27-2
Figure 28-1 Configuration Text File Format — Column Descriptions.........................................................28-2
Figure 28-2 Invalid Parameter Entered — Command Line Example...........................................................28-3
Figure 28-3 Valid Parameter Entered — Command Line Example..............................................................28-3
Figure 28-4 Internal SPTGEN FTP Download Example.............................................................................. 28-3
Figure 28-5 Internal SPTGEN FTP Upload Example...................................................................................28-4
List of Diagrams
Diagram 1 Single-PC per Router Hardware Configuration .............................................................................. A
Diagram 2 Prestige as a PPPoE Client.............................................................................................................. B
Diagram 3 Virtual Circuit Topology ................................................................................................................. C
Diagram 4 Option to Enter Debug Mode.......................................................................................................... D
List of Figures xviii
Page 19

Prestige 652 ADSL Security Router
Diagram 5 Boot Module Commands ................................................................................................................ E
xix List of Figures
Page 20

Prestige 652 ADSL Security Router
List of Tables
Table 2-1 Front Panel LED Description......................................................................................................... 2-1
Table 2-2 Main Menu Commands................................................................................................................ 2-11
Table 2-3 Main Menu Summary .................................................................................................................. 2-12
Table 3-1 General Setup Menu Fields............................................................................................................ 3-2
Table 3-2 Configure Dynamic DNS Menu Fields.......................................................................................... 3-4
Table 4-1 IP Alias Setup Menu Fields ............................................................................................................ 4-7
Table 4-2 DHCP Ethernet Setup Menu Fields................................................................................................ 4-9
Table 4-3 TCP/IP Ethernet Setup Menu Fields ............................................................................................ 4-10
Table 4-4 Internet Account Information....................................................................................................... 4-13
Table 4-5 Internet Access Setup Menu Fields.............................................................................................. 4-16
Table 5-1 Remote Node Profile Menu Fields................................................................................................. 5-4
Table 5-2 Remote Node Network Layer Options........................................................................................... 5-7
Table 6-1 TCP/IP-Related Fields in Menu 11.1 — Remote Node Profile......................................................6-3
Table 6-2 TCP/IP Remote Node Configuration .............................................................................................6-5
Table 6-3 Edit IP Static Route Menu Fields................................................................................................... 6-9
Table 7-1 Remote Node Bridge Options........................................................................................................ 7-2
Table 7-2 Edit Bridge Static Route Menu Fields............................................................................................7-3
Table 8-1 NAT Definitions............................................................................................................................. 8-1
Table 8-2 NAT Mapping Types ...................................................................................................................... 8-5
Table 8-3 Applying NAT in Menus 4 & 11.3 ................................................................................................. 8-8
Table 8-4 SUA Address Mapping Rules....................................................................................................... 8-11
Table 8-5 Fields in Menu 15.1.1 ..................................................................................................................8-13
Table 8-6 Menu 15.1.1.1 — Editing/Configuring an Individual Rule in a Set.............................................8-15
Table 8-7 Services & Port Numbers............................................................................................................. 8-16
Table 9-1 Common IP Ports........................................................................................................................... 9-4
Table 9-2 ICMP Commands That Trigger Alerts ...........................................................................................9-6
xx List of Tables
Page 21

Prestige 652 ADSL Security Router
Table 9-3 Legal NetBIOS Commands............................................................................................................9-7
Table 9-4 Legal SMTP Commands ................................................................................................................9-7
Table 10-1 View Firewall Log......................................................................................................................10-3
Table 11-1 E-mail ......................................................................................................................................... 11-4
Table 11-2 SMTP Error Messages................................................................................................................ 11-5
Table 11-3 Attack Alert................................................................................................................................. 11-9
Table 12-1 Firewall Rules Summary — First Screen................................................................................... 12-5
Table 12-2 Predefined Services....................................................................................................................12-7
Table 12-3 Creating/Editing A Firewall Rule ............................................................................................. 12-10
Table 12-4 Adding/Editing Source and Destination Addresses..................................................................12-12
Table 12-5 Timeout Menu ..........................................................................................................................12-14
Table 13-1 Customized Services ..................................................................................................................13-2
Table 13-2 Creating/Editing A Custom Port................................................................................................. 13-3
Table 14-1 Log Screen .................................................................................................................................14-2
Table 16-1 Filter Rules Summary Menu Abbreviations ...............................................................................16-8
Table 16-2 Rule Abbreviations Used............................................................................................................16-8
Table 16-3 TCP/IP Filter Rule Menu Fields...............................................................................................16-10
Table 16-4 Generic Filter Rule Menu Fields .............................................................................................. 16-15
Table 16-5 Filter Sets Table........................................................................................................................ 16-20
Table 17-1 SNMP Configuration Menu Fields............................................................................................. 17-3
Table 17-2 SNMP Traps ...............................................................................................................................17-4
Table 17-3 Ports and Permanent Virtual Circuits .........................................................................................17-4
Table 18-1 System Maintenance — Status Menu Fields..............................................................................18-2
Table 18-2 Fields in System Maintenance....................................................................................................18-4
Table 18-3 System Maintenance Menu — Syslog Parameters.....................................................................18-7
Table 18-4 System Maintenance Menu — Diagnostic.................................................................................18-9
Table 19-1 Filename Conventions................................................................................................................19-2
Table 19-2 General Commands for GUI-based FTP Clients........................................................................19-4
List of Diagrams xxi
Page 22

Prestige 652 ADSL Security Router
Table 19-3 General Commands for GUI-based TFTP Clients .....................................................................19-6
Table 20-1 Budget Management .................................................................................................................. 20-3
Table 20-2 Time and Date Setting Fields..................................................................................................... 20-5
Table 21-1 Menu 24.11 – Remote Management Control ............................................................................. 21-3
Table 22-1 IP Routing Policy Setup............................................................................................................. 22-3
Table 22-2 IP Routing Policy....................................................................................................................... 22-4
Table 23-1 Schedule Set Setup Fields.......................................................................................................... 23-2
Table 24-1 VPN and NAT ............................................................................................................................ 24-6
Table 25-1 AH and ESP ............................................................................................................................... 25-3
Table 25-2 Telecommuter and Headquarters Configuration Example ......................................................... 25-4
Table 25-3 Menu 27.1 — IPSec Summary................................................................................................... 25-6
Table 25-4 Menu 27.1.1 — IPSec Setup...................................................................................................... 25-9
Table 25-5 Menu 27.1.1.1 — IKE Setup.................................................................................................... 25-15
Table 25-6 Active Protocol — Encapsulation and Security Protocol......................................................... 25-17
Table 25-7 Menu 27.1.1.2 — Manual Setup .............................................................................................. 25-18
Table 26-1 Menu 27.2 — SA Monitor ......................................................................................................... 26-1
Table 27-1 Sample IKE Key Exchange Logs............................................................................................... 27-2
Table 27-2 Sample IPSec Logs During Packet Transmission ...................................................................... 27-4
Table 27-3 RFC-2408 ISAKMP Payload Types........................................................................................... 27-4
Table 29-1 Troubleshooting the LAN LED.................................................................................................. 29-1
Table 29-2 Troubleshooting the DSL LED .................................................................................................. 29-2
Table 29-3 Troubleshooting the LAN Interface ........................................................................................... 29-2
Table 29-4 Troubleshooting the WAN Interface .......................................................................................... 29-2
Table 29-5 Troubleshooting Internet Access................................................................................................ 29-3
Table 29-6 Troubleshooting the Password ................................................................................................... 29-3
Table 29-7 Troubleshooting the Web Configurator...................................................................................... 29-4
Table 29-8 Troubleshooting Remote Management ...................................................................................... 29-4
xxii List of Tables
Page 23
Prestige 652 ADSL Security Router
Preface
Congratulations on your purchase of the Prestige 652 ADSL Router with VPN and Firewall.
There are two Prestige 652 models, one for ADSL over POTS (Plain Old Telephone System) and one for
ADSL over ISDN (Integrated Synchronous Digital System). Both models are discussed together in this
guide.
The Prestige 652 is an ADSL router used for Internet/LAN access via an ADSL line. The P652 can run
maximum upstream transmission rates of up to 832Kbps and maximum downstream transmission rates of
8Mbps. The actual rate depends on the copper category of your telephone wire, distance from the central
office and the type of ADSL service subscribed to. See the What is DSL section for more background
information on DSL and ADSL.
The P652's 10/100M auto-negotiating LAN interface enables fast data transfer of either 10Mbps or
100Mbps in either half-duplex or full-duplex mode depending on your Ethernet network.
Your Prestige is easy to install and configure. All functions of the Prestige are software configurable via the
SMT (System Management Terminal) and web configurator. Advanced users may configure the Prestige
using CLI (Command Line Interface) commands.
Register your Prestige online at www.zyxel.com for free future product updates
and information.
About This User's Guide
This User's Guide covers all aspects of the Prestige 652 operations and shows you how to use the SMT to
get the best out of its multiple advanced features. It is designed to guide you through the correct
configuration of your Prestige 652 for various applications.
Related Documentation
Supporting Disk
More detailed information and examples can be found in our included disk (as well as on the
zyxel.com web site). This disk contains information on configuring your Prestige for Internet
Access, general and advanced FAQs, Application Notes, Troubleshooting, a reference for CI
Commands and bundled software.
Read Me First
Our Read Me First is designed to help you get up and running right away. It contains a detailed
easy-to-follow connection diagram, default settings, handy checklists and information on setting
up your network and configuring for Internet access.
ZyXEL Web Site and Glossary
Preface xxiii
Page 24
Prestige 652 ADSL Security Router
Please refer to www.zyxel.com for an online glossary of networking terms and additional support
documentation
Syntax Conventions
• “Enter” means for you to type one or more characters and press the carriage return. “Select” or
“Choose” means for you to select one from the predefined choices.
• The SMT menu titles and labels are in Bold Times New Roman font. Predefined field choices are in
Bold Arial font. Command and arrow keys are enclosed in square brackets. [ENTER] means the
Enter, or carriage return key; [ESC] means the Escape key and [SPACE BAR] means the Space Bar.
• For brevity’s sake, we will use “e.g.,” as a shorthand for “for instance”, and “i.e.,” for “that is” or “in
other words” throughout this manual.
• The Prestige 652 ADSL Router with VPN and Firewall may be referred to as the P652 or the Prestige
in this User’s Guide.
The following section offers some background information on DSL. Skip it if you
wish to begin working with your router right away.
xxiv Preface
Page 25

Prestige 652 ADSL Security Router
What is DSL?
DSL (Digital Subscriber Line) technology enhances the data capacity of the existing twisted-pair wire that
runs between the local telephone company switching offices and most homes and offices. While the wire
itself can handle higher frequencies, the telephone switching equipment is designed to cut off signals above
4,000 Hz to filter noise off the voice line, but now everybody is searching for ways to get more bandwidth
to improve access to the Web - hence DSL technologies.
There are actually seven types of DSL service, ranging in speeds from 16 Kbits/sec to 52 Mbits/sec. The
services are either symmetrical (traffic flows at the same speed in both directions), or asymmetrical (the
downstream capacity is higher than the upstream capacity). Asymmetrical services (ADSL) are suitable for
Internet users because more information is usually downloaded than uploaded. For example, a simple
button click in a web browser can start an extended download that includes graphics and text.
As data rates increase, the carrying distance decreases. That means that users who are beyond a certain
distance from the telephone company’s central office may not be able to obtain the higher speeds.
A DSL connection is a point-to-point dedicated circuit, meaning that the link is always up and there is no
dialing required.
What is ADSL?
It is an asymmetrical technology, meaning that the downstream data rate is much higher than the upstream
data rate. As mentioned, this works well for a typical Internet session in which more information is
downloaded, for example, from Web servers, than is uploaded. ADSL operates in a frequency range that is
above the frequency range of voice services, so the two systems can operate over the same cable.
What is DSL? xxv
Page 26

Page 27
Getting Started
PPaarrtt II::
GETTING STARTED
This part is structured as a step-by-step guide to help you connect, install and set up your
Prestige to operate on your network and to access the Internet. Described are Key Features and
Applications, Hardware Installation, Initial Setup and Internet Access.
I
Page 28

Page 29

Prestige 652 ADSL Security Router
Chapter 1
Getting To Know Your Prestige
This chapter describes the key features and applications of your Prestige
1.1 Prestige 652 ADSL Security Router
Your Prestige integrates a high-speed 10/100Mbps auto-negotiating LAN interface and a high-speed ADSL
port into a single package. The Prestige is ideal for high-speed Internet browsing and making LAN-to-LAN
connections to remote networks.
The Prestige provides not only ease of installation and high-speed Internet access, but also a complete
security solution. The Prestige 652 combines an ADSL router with a robust firewall and VPN capability.
The web browser-based Graphical User Interface provides easy management and is totally independent of
the operating system platform you use.
1.2 Features
Your Prestige is packed with a number of features that give it the flexibility to provide a complete
networking solution for almost any user.
z High Speed Internet Access
Your Prestige can support downstream transmission rates of up to 8Mbps and upstream transmission rates
of 832 Kbps. Your Prestige also supports rate management; rate management allows ADSL subscribers to
select an Internet access speed that best suits their needs and budgets.
z IPSec VPN Capability
Establish a Virtual Private Network (VPN) to connect with business partners and branch offices using data
encryption and the Internet to provide secure communications without the expense of leased site-to-site
lines. The Prestige’s VPN is based on the IPSec standard and is fully interoperable with other IPSec-based
VPN products.
.
Firewall
•
The Prestige is a stateful inspection firewall with DoS (Denial of Service) protection. By default, when the
firewall is activated, all incoming traffic from the WAN to the LAN is blocked unless it is initiated from the
LAN. The Prestige firewall supports TCP/UDP inspection, DoS detection and prevention, real time alerts,
reports and logs.
Getting To Know Your Prestige 1-1
Page 30
Prestige 652 ADSL Security Router
You can configure most features of the Prestige via SMT but we recommend you
configure the firewall and content filters using the Prestige Web Configurator.
Content Filtering
•
The Prestige can block specific URLs by using the keyword blocking feature.
z Internal SPTGEN
Internal SPTGEN (System Parameter Table Generator) lets you configure, save and upload multiple menus
at the same time using just one configuration text file - eliminating the need to navigate and configure
individual SMT menus for each Prestige.
Dynamic DNS Support
•
With Dynamic DNS support, you can have a static hostname alias for a dynamic IP address, allowing the
host to be more easily accessible from various locations on the Internet. You must register for this service
with a Dynamic DNS client to use this service.
Packet Filtering
•
The Packet Filtering mechanism blocks unwanted traffic from entering/leaving your network.
z PPPoE Support (RFC2516)
PPPoE (Point-to-Point Protocol over Ethernet) emulates a dial-up connection. It allows your ISP to use their
existing network configuration with newer broadband technologies such as ADSL. The PPPoE driver on the
Prestige is transparent to the computers on the LAN, which see only Ethernet and are not aware of PPPoE
thus saving you from having to manage PPPoE clients on individual computers.
z Network Address Translation (NAT)
NAT (Network Address Translation - NAT, RFC 1631) allows the translation of multiple IP addresses used
within one network to different IP addresses known within another network. This feature allows multipleuser Internet access for the cost of a single IP account. NAT supports popular Internet applications such as
MS traceroute, CuSeeMe, IRC, RealPlayer, VDOLive, Quake, and PPTP. No configuration is needed to
support these applications.
z 10/100M Auto-negotiation Ethernet/Fast Ethernet Interface
This auto-negotiation feature allows the Prestige to detect the speed of incoming transmissions and adjust
appropriately without manual intervention. It allows data transfer of either 10 Mbps or 100 Mbps in either
half-duplex or full-duplex mode depending on your Ethernet network.
z Multiple PVC (Permanent Virtual Circuits) Support
Your Prestige supports up to 8 PVCs.
1-2 Getting To Know Your Prestige
Page 31

Prestige 652 ADSL Security Router
z ADSL Transmission Rate Standards
♦ Full-Rate (ANSI T1.413, Issue 2; G.dmt (G.992.1) with line rate support of up to 8 Mbps
downstream and 832 Kbps upstream.
♦ G.lite (G.992.2) with line rate support of up to 1.5Mbps downstream and 512Kbps upstream.
♦ Supports Multi-Mode standard (ANSI T1.413, Issue 2; G.dmt (G.992.1); G.lite (G992.2)).
♦ TCP/IP (Transmission Control Protocol/Internet Protocol) network layer protocol.
♦ ATM Forum UNI 3.1 PVC.
♦ Supports up to 8 PVCs (UBR, CBR).
♦ Multiple Protocol over AAL5 (RFC 1483).
♦ PPP over AAL5 (RFC 2364).
♦ PPP over Ethernet over AAL5 (RFC 2516).
Protocol Support
•
♦ DHCP Support
DHCP (Dynamic Host Configuration Protocol) allows the individual clients (computers) to obtain
the TCP/IP configuration at start-up from a centralized DHCP server. The Prestige has built-in
DHCP server capability enabled by default. It can assign IP addresses, an IP default gateway and
DNS servers to DHCP clients. The Prestige can also act as a surrogate DHCP server (DHCP Relay)
where it relays IP address assignments from the actual DHCP server to the clients.
♦ IP Alias
IP Alias allows you to partition a physical network into logical networks over the same Ethernet
interface. The Prestige supports three logical LAN interfaces via its single physical Ethernet
interface with the Prestige itself as the gateway for each LAN network.
♦ IP Policy Routing (IPPR)
Traditionally, routing is based on the destination address only and the router takes the shortest path
to forward a packet. IP Policy Routing (IPPR) provides a mechanism to override the default routing
behavior and alter the packet forwarding based on the policy defined by the network administrator.
♦ PPP (Point-to-Point Protocol) link layer protocol.
♦ Transparent bridging for unsupported network layer protocols.
♦ RIP I/RIP II
♦ IGMP Proxy
Getting To Know Your Prestige 1-3
Page 32

Prestige 652 ADSL Security Router
♦ ICMP support
♦ IP QoS support
♦ MIB II support (RFC 1213)
z Networking Compatibility
Your Prestige is compatible with the major ADSL DSLAM (Digital Subscriber Line Access Multiplexer)
providers, making configuration as simple as possible for you.
z Multiplexing
The Prestige supports VC-based and LLC-based multiplexing.
z Encapsulation
The Prestige supports PPPoA (RFC 2364 - PPP over ATM Adaptation Layer 5), RFC 1483 encapsulation over
ATM, MAC encapsulated routing as well as PPP over Ethernet (RFC 2516).
Network Management
♦ Menu driven SMT (System Management Terminal) management
♦ Embedded Web Configurator
♦ CLI (Command Line Interpreter)
♦ Remote SMT session via Telnet
♦ SNMP manageable
♦ Local SMT session via console port
♦ DHCP Server/Client
♦ Built-in Diagnostic Tools
♦ Syslog
♦ Telnet Support (Password-protected telnet access to internal configuration manager)
♦ TFTP/FTP server, firmware upgrade and configuration backup/support supported
♦ Supports OAM F4/F5 loop-back, AIS and RDI OAM cells
Other PPPoE Features
•
♦ PPPoE idle time out
♦ PPPoE Dial on Demand
1-4 Getting To Know Your Prestige
Page 33

Prestige 652 ADSL Security Router
Diagnostics Capabilities
•
♦ The Prestige can perform self-diagnostic tests. These tests check the integrity of the following
circuitry:
♦ FLASH memory
♦ ADSL circuitry
♦ RAM
♦ LAN port
z Ease of Installation
Your Prestige is designed for quick, intuitive and easy installation.
z Housing
Your Prestige's all new compact and ventilated housing minimizes space requirements making it easy to
position anywhere in your busy office.
1.3 Applications for the Prestige 652
1.3.1 Internet Access
The Prestige is the ideal high-speed Internet access solution. Your Prestige supports the TCP/IP protocol,
which the Internet uses exclusively. It is compatible with all major ADSL DSLAM (Digital Subscriber
Line Access Multiplexer) providers. A DSLAM is a rack of ADSL line cards with data multiplexed into a
backbone network interface/connection (for example, T1, OC3, DS3, ATM or Frame Relay). Think of it as
the equivalent of a modem rack for ADSL. A typical Internet Access application is shown below.
Getting To Know Your Prestige 1-5
Page 34

Prestige 652 ADSL Security Router
Figure 1-1 Internet Access Application
Internet Single User Account
For a SOHO (Small Office/Home Office) environment, your Prestige offers the Network Address
Translation (NAT) feature that allows multiple users on the LAN (Local Area Network) to access the
Internet concurrently for the cost of a single IP address.
1.3.2 Firewall for Secure Broadband Internet Access
The Prestige provides protection from attacks by Internet hackers. By default, the firewall blocks all
incoming traffic from the WAN. The firewall supports TCP/UDP inspection and DoS (Denial of Services)
detection and prevention, as well as real time alerts, reports and logs.
Figure 1-2 Firewall Application
1-6 Getting To Know Your Prestige
Page 35

1.3.3 LAN to LAN Application
Prestige 652 ADSL Security Router
You can use the Prestige to connect two geogr
LAN-to-LAN application for your Prestige is shown as follows.
Figure 1-3 LAN-to-LAN Application
aphical
ly dispersed networks over the ADSL line. A typical
1.3.4 VPN Application
The Prestige’s VPN feature makes it an ideal cost-effective way to connect branch offices and business
partners over the Internet without the need (and expense) for leased lines between sites. VPN ensures the
privacy and integrity of your data transmissions.
Getting To Know Your Prestige 1-7
Page 36

Prestige 652 ADSL Security Router
Figure 1-4 VPN Application
1-8 Getting To Know Your Prestige
Page 37

Prestige 652 ADSL Security Router
Chapter 2
Hardware Installation and Initial Setup
This chapter describes the physical features of the Prestige and how to make cable connections
2.1 Front Panel LEDs of the P652
The LEDs on the front panel indicate the operational status of your Prestige
Figure 2-1 Front Panel
Table 2-1 Front Panel LED Description
LED COLOR
PWR Green
SYS
Green
Red On The Prestige is not receiving enough power.
STATUS
On The Prestige is receiving power.
Blinking The Prestige is performing a self-test.
Off The Prestige is not receiving power.
On The Prestige is functioning properly.
Blinking The Prestige is rebooting.
Off The Prestige is not ready or has malfunctioned.
On The Prestige is connected to the PPPoE server.PPPoE Green
Off There is no connection to the PPPoE server.
DESCRIPTION
.
Hardware Installation and Initial Setup 2-1
Page 38

Prestige 652 ADSL Security Router
LED COLOR
LAN 10M Green
LAN 100M Orange
AUX This LED is reserved for a feature to be available in the future.
xDSL Green
ACT Green
STATUS
On The Prestige has a successful 10Mb Ethernet connection.
Blinking The Prestige is sending/receiving data.
Off The Prestige does not have a 10Mb Ethernet connection.
On The Prestige has a successful 100Mb Ethernet connection.
Blinking The Prestige is sending/receiving data.
Off The Prestige does not have a 100Mb Ethernet connection.
On The Prestige is linked successfully to a DSLAM.
Blinking The Prestige is initializing or sending/receiving data.
Off The DSL link is down.
On The Prestige has a successful Ethernet connection.
Blinking The Prestige is sending/receiving data.
Off The system is not ready or has malfunctioned.
DESCRIPTION
2.2 Rear Panel and Connections
The following figure shows the rear panel of your Prestige.
Figure 2-2 Rear Panel
2-2 Hardware Installation and Initial Setup
Page 39

Prestige 652 ADSL Security Router
2.2.1 xDSL Port
Connect the Prestige directly to the wall jack using a DSL cable (telephone wire). Connect a microfilter(s)
between the wall jack and your telephone(s). A microfilter acts as low-pass filter (voice transmission takes
place in the 0 to 4KHz bandwidth) and is an optional purchase.
2.2.2 Console Port
Use terminal emulator software on a computer for configuring your Prestige via console port. Connect the
9-pin end of the console cable to the console port of the Prestige and the other end (choice of 9-pin or 25pin, depending on your computer) end to a serial port (COM1, COM2 or other COM port) of your
computer. You can use an extension RS-232 cable if the enclosed one is too short. After the initial setup,
you can modify the configuration remotely through telnet connections.
2.2.3 LAN 10/100M Port
For a single computer, connect the 10/100M LAN port on the Prestige to the Network Adapter on the
computer using a crossover Ethernet cable with the UPLINK button “off” (out). Use a straight-through
cable if the UPLINK button is “on” (in).
If you have more than one computer, then you must use an external hub. Connect the 10/100M LAN port
on the Prestige to a port on the hub using a straight-through Ethernet cable and make sure the Uplink button
is "on".
The corresponding LAN LED on the front panel turns on when the Prestige is on
and properly connected to a computer or hub.
2.2.4 Power Port
Connect the power adapter to the port labeled POWER on the rear panel of your Prestige.
Make sure you use the correct power adapter to avoid damage to the Prestige.
Refer to the Power Adapter Specification Appendix for this information.
2.2.5 Reset Button
Refer to section 2.8 for information on the RESET button.
2.3 Additional Installation Requirements
z A computer with an Ethernet 10Base-T/100Base-T NIC (Network Interface Card).
Hardware Installation and Initial Setup 2-3
Page 40

Prestige 652 ADSL Security Router
A computer equipped with communications software (for example, Hyper Terminal in Windows 95)
configured to the following parameters:
VT100 terminal emulation.
9600 baud rate.
Parity set to none, 8 data bits, 1 stop bit.
Flow control set to none.
After the Prestige has been successfully connected to your network, you can make future changes to the
configuration via Telnet.
2.4 P652 with POTS
2.4.1 Connecting a POTS Splitter
One major difference between Full Rate (G.dmt) ADSL and dial-up modems is the optional telephone
splitter. This device keeps the telephone and ADSL signals separated, giving them the capability to provide
simultaneous Internet access and telephone service on the same line. Splitters also eliminate the destructive
interference conditions caused by telephone sets. The purchase of a POTS splitter is optional.
Noise generated from a telephone in the same frequency range, as the ADSL signal can be disruptive to the
ADSL signal. In addition the impedance of a telephone when off-hook may be so low that it shunts the
strength of the ADSL signal. When a POTS splitter is installed at the entry point, where the line comes into
the home, it will filter the telephone signals before combining the ADSL and telephone signals transmitted
and received. The issues of noise and impedance are eliminated with a single POTS splitter installation.
A telephone splitter is easy to install as shown in the following figure.
2-4 Hardware Installation and Initial Setup
Page 41

Prestige 652 ADSL Security Router
Figure 2-3 Connecting a POTS Splitter
Step 1. Connect the side labeled “Phone” to your telephone.
Step 2. Connect the side labeled “Modem” to your Prestige.
Step 3. Connect the side labeled “Line” to the telephone wall jack.
2.4.2 Telephone Microfilters
Telephone voice transmissions take place in the lower frequency range, 0 - 4KHz, while ADSL
transmissions take place in the higher bandwidth range, above 4KHz. A microfilter acts as a low-pass filter,
for your telephone, to ensure that ADSL transmissions do not interfere with your telephone voice
transmissions. The purchase of a telephone microfilter is optional.
Step 1. Connect a phone cable from the wall jack to the single jack end of the Y- Connector.
Step 2. Connect a cable from the double jack end of the Y-Connector to the “wall side” of the
microfilter.
Step 3. Connect another cable from the double jack end of the Y-Connector to the Prestige.
Step 4. Connect the “phone side” of the microfilter to your telephone as shown in the following figure.
Hardware Installation and Initial Setup 2-5
Page 42

Prestige 652 ADSL Security Router
Figure 2-4 Connecting a Microfilter
2.5 P652 with ISDN
This section relates to people who use their P652 with ADSL over ISDN (digital telephone service) only.
The following is an example installation for the P652 with ISDN.
Figure 2-5 P652 with ISDN
2-6 Hardware Installation and Initial Setup
Page 43

Prestige 652 ADSL Security Router
2.6 Turning On Your Prestige
At this point, you should have connected the DSL, LAN 10/100M, console and power ports to the
appropriate devices. Make sure the power adapter is plugged into an appropriate power source and the
power button (located on the back of your Prestige) is “on” (pushed in).
2.7 Configuring Your Prestige For Internet Access
Configure your Prestige for Internet access using:
Web configurator (refer to the Read Me First for access instructions)
SMT (System Management Terminal). Access the SMT via:
o LAN or WAN using Telnet
o Console port using terminal emulation software
The remainder of this User’s Guide shows you how to configure the Prestige using SMT screens.
2.7.1 Initial Screen
When you turn on your Prestige, it performs several internal tests as well as line initialization. After the
initialization, the Prestige asks you to press [ENTER] to continue, as shown.
Copyright (c) 1994 - 2002 ZyXEL Communications Corp.
initialize ch = 0, ethernet address: 00:a0:c5:01:23:45
Wan Channel init ........ done
Loading ADSL modem F/W
......................................................... done
Press ENTER to continue...
Figure 2-6 Power-On Display
2.7.2 Entering Password
The login screen appears after you press [ENTER], prompting you to enter the password, as shown next.
For your first login, enter the default password “1234”. As you type the password, the screen displays an
“X” for each character you type.
Please note that if there is no activity for longer than five minutes after you log in, your Prestige
automatically logs you out and displays a blank screen. If you see a blank screen, press [ENTER] to
display the login screen again.
Hardware Installation and Initial Setup 2-7
Page 44

Prestige 652 ADSL Security Router
Enter Password : XXXX
Figure 2-7 Login Screen
2.8 Resetting the Prestige
If you forget your password or cannot access the Prestige, you will need to reload the factory-default
configuration file. Uploading this configuration file replaces the current configuration file with the factorydefault configuration file. This means that you will lose all configurations that you had previously and the
speed of the console port will be reset to the default of 9600bps with 8 data bit, no parity, one stop bit and
flow control set to none. The password will be reset to “1234” and the LAN IP address to 192.168.1.1also.
To obtain the default configuration file, download it from the ZyXEL FTP site, unzip it and save it in a
folder. Turn the Prestige off and then on to begin a session. When you turn on the Prestige again you will
see the initial screen. When you see the message “Press any key to enter Debug Mode within 3 seconds”
press any key to enter debug mode.
To upload the configuration file, do the following:
1. Type atlc after the Enter Debug Mode message.
2. Wait for the Starting XMODEM upload message before activating XMODEM upload on your
terminal.
3. After a successful firmware upload, type atgo to restart the Prestige.
The Prestige is now reinitialized with a default configuration file including the default password of “1234”.
2.8.1 Methods of Restoring Factory-Defaults
You can erase the current configuration and restore factory defaults in three ways:
a. Upload the default configuration file via the console port as described above. See later in
this User’s Guide for more information on how to transfer the configuration file to your
Prestige using the SMT menus.
b. Use the RESET button on the rear panel of the Prestige (see the next section). Use this
method for cases when the password or IP address of the Prestige is not known.
c. Use the web configurator to restore defaults (see the web configurator HTML help).
2-8 Hardware Installation and Initial Setup
Page 45

Prestige 652 ADSL Security Router
2.8.2 Procedure To Use The Reset Button
Make sure the SYS led is on (not blinking) before you begin this procedure.
1. Press the RESET button for ten seconds, then release it. If the SYS LED begins to blink, the
defaults have been restored and the Prestige restarts. Otherwise, go to step 2.
2. Turn the Prestige off.
3. While pressing the RESET button, turn the Prestige on.
4. Continue to hold the RESET button. The SYS LED will begin to blink and flicker very quickly
after about 10 or 15 seconds. This indicates that the defaults have been restored and the Prestige is
now restarting.
Release the RESET button and wait for the Prestige to finish restarting.
Hardware Installation and Initial Setup 2-9
Page 46

Prestige 652 ADSL Security Router
2.8.3 Prestige 652 SMT Menu Overview
The following figure gives you an overview of the various SMT menu screens of your Prestige.
Figure 2-8 SMT Menu Overview
2.9 Navigating the SMT Interface
The SMT (System Management Terminal) is the interface that you use to configure your Prestige.
2-10 Hardware Installation and Initial Setup
Page 47

Prestige 652 ADSL Security Router
Several operations that you should be familiar with before you attempt to modify the configuration are
listed in the table below.
Table 2-2 Main Menu Commands
OPERATION KEYSTROKE DESCRIPTION
Move down to
another menu
Move up to a
previous menu
Move to a “hidden”
menu
Move the cursor [ENTER] or
Entering
information
Required fields
N/A fields <N/A> Some of the fields in the SMT will show a <N/A>. This symbol
Save your
configuration
Exit the SMT Type 99, then press
[ENTER] To move forward to a submenu, type in the number of the desired
submenu and press [ENTER].
[ESC] Press [ESC] to move back to the previous menu.
Press [SPACE
BAR] to change No
to Yes then press
[ENTER].
[UP]/[DOWN] arrow
keys.
Type in or press
[SPACE BAR], then
press [ENTER].
?>
<
[ENTER] Save your configuration by pressing [ENTER] at the message
[ENTER].
Fields beginning with “Edit” lead to hidden menus and have a
default setting of No. Press [SPACE BAR] once to change No to
Yes, then press [ENTER] to go to the “hidden” menu.
Within a menu, press [ENTER] to move to the next field. You can
also use the [UP]/[DOWN] arrow keys to move to the previous
and the next field, respectively.
You need to fill in two types of fields. The first requires you to type
in the appropriate information. The second allows you to cycle
through the available choices by pressing [SPACE BAR].
All fields with the symbol <?> must be filled in order to be able to
save the new configuration.
refers to an option that is Not Applicable.
“Press ENTER to confirm or ESC to cancel”. Saving the data on
the screen will take you, in most cases to the previous menu.
Type 99 at the main menu prompt and press [ENTER] to exit the
SMT interface.
After you enter the password, the SMT displays the main menu, as shown next.
Hardware Installation and Initial Setup 2-11
Page 48

Prestige 652 ADSL Security Router
Prestige 652 Main Menu
Getting Started
1. General Setup
3. LAN Setup
4. Internet Access Setup
Advanced Applications
11. Remote Node Setup
12. Static Routing Setup
15. NAT Setup
Copyright (c) 1994 - 2002 ZyXEL Communications Corp.
Advanced Management
21. Filter and Firewall Setup
22. SNMP Configuration
23. System Password
24. System Maintenance
25. IP Routing Policy Setup
26. Schedule Setup
27. VPN/IPSec Setup
99. Exit
Enter Menu Selection Number:_
Figure 2-9 SMT Main Menu
2.9.1 System Management Terminal Interface Summary
Table 2-3 Main Menu Summary
# MENU TITLE DESCRIPTION
1 General Setup Use this menu to set up your general information.
3 LAN Setup Use this menu to set up your LAN connection.
4 Internet Access Setup A quick and easy way to set up an Internet connection.
11 Remote Node Setup Use this menu to set up the Remote Node for LAN-to-LAN connection,
including Internet connection.
12 Static Routing Setup Use this menu to set up static routes.
15 NAT Setup Use this menu to specify inside servers when NAT is enabled.
21 Filter and Firewall Setup Use this menu to configure filters, activate/deactivate the firewall and
view the firewall log.
22 SNMP Configuration Use this menu to set up SNMP related parameters.
23 System Password Use this menu to change your password.
24 System Maintenance This menu provides system status, diagnostics, software upload, etc.
25 IP Routing Policy Setup Use this menu to configure your IP routing policy.
2-12 Hardware Installation and Initial Setup
Page 49

Prestige 652 ADSL Security Router
# MENU TITLE DESCRIPTION
26 Schedule Setup Use this menu to schedule outgoing calls.
27 VPN/ IPSec Setup Use this menu to configure VPN connections.
99 Exit Use this to exit from SMT and return to a blank screen.
2.10 Changing the System Password
Change the Prestige default password by following the steps shown next.
Step 1. Enter 23 in the main menu to display Menu 23 - System Password as shown next.
Step 2. Type your existing system password in the Old Password field, for example “1234”, and press
[ENTER].
Menu 23 – System Password
Old Password= ****
New Password= ?
Retype to confirm= ?
Enter here to CONFIRM or ESC to CANCEL:
Figure 2-10 Menu 23 — System Password
Step 3. Type your new system password in the New Password field (up to 30 characters), and press
[ENTER].
Step 4. Re-type your new system password in the Retype to confirm field for confirmation and press
[ENTER].
Note that as you type a password, the screen displays an “X” for each character you type.
Hardware Installation and Initial Setup 2-13
Page 50

Page 51

Prestige 652 ADSL Security Router
Chapter 3
General Setup
Menu 1 - General Setup contains administrative and system-related information.
3.1 System Name
System Name is for identification purposes. ZyXEL recommends you enter your computer’s “Computer
name”.
• In Windows 95/98 click Start -> Settings -> Control Panel and then double-click Network. Click the
Identification tab, note the entry for the Computer name field and enter it as the Prestige System
Name.
• In Windows 2000 click Start->Settings->Control Panel and then double-click System. Click the
Network Identification tab and then the Properties button. Note the entry for the Computer name
field and enter it as the Prestige System Name.
• In Windows XP, click start -> My Computer -> View system information and then click the
Computer Name tab. Note the entry in the Full computer name field and enter it as the Prestige
System Name.
The Domain Name entry is what is propagated to the DHCP clients on the LAN. If you leave this field
blank, the domain name obtained by DHCP from the ISP is used. While you must enter the host name
(System Name) on each individual computer, the domain name can be assigned from the Prestige via
DHCP.
3.2 Dynamic DNS
Dynamic DNS (Domain Name System) allows you to update your current dynamic IP address with one or
many dynamic DNS services so that anyone can contact you (in NetMeeting, CU-SeeMe or other services).
You can also access your FTP server or Web site on your own computer using a DNS-like address (for
example, myhost.dhs.org, where myhost is a name of your choice) that will never change instead of using an
IP address that changes each time you reconnect. Your friends or relatives will always be able to call you
even if they don’t know your IP address.
First of all, you need to have registered a dynamic DNS account with www.dyndns.org. This is for people
with a dynamic IP from their ISP or DHCP server that would still like to have a DNS name.
General Setup 3-1
Page 52

Prestige 652 ADSL Security Router
To use this service, you must register with the Dynamic DNS service provider. The Dynamic DNS service
provider will give you a password or key. The Prestige supports www.dyndns.org. You can apply to this
service provider for Dynamic DNS service.
3.2.1 DYNDNS Wildcard
Enabling the wildcard feature for your host causes *.yourhost.dyndns.org to be aliased to the same IP
address as yourhost.dyndns.org. This feature is useful if you want to be able to use for example,
www.yourhost.dyndns.org and still reach your hostname.
3.3 General Setup
To enter menu 1 and fill in the required information, follow these steps:
Step 1. Enter 1 in main menu to display Menu 1 – General Setup.
Step 2. The Menu 1 - General Setup screen appears, as shown next. Fill in the fields, as explained in
the following table.
Menu 1 - General Setup
System Name= ?
Location=
Contact Person's Name=
Domain Name=
Edit Dynamic DNS= No
Route IP= Yes
Bridge= No
Press ENTER to Confirm or ESC to Cancel:
Figure 3-1 Menu 1 — General Setup
Table 3-1 General Setup Menu Fields
FIELD DESCRIPTION EXAMPLE
System Name
(required)
Location (optional) Enter the geographic location (up to 31 characters) of your Prestige. MyHouse
Contact Person's
Name (optional)
Choose a descriptive name for identification purposes. This name can
be up to 30 alphanumeric characters long. Spaces are not allowed, but
dashes “-” and underscores "_" are accepted.
Enter the name (up to 30 characters) of the person in charge of this
Prestige.
P652
JohnDoe
3-2 General Setup
Page 53

Prestige 652 ADSL Security Router
Domain Name Enter your domain name here (if you have one). If you leave this field
zyxel.com.tw
blank, the ISP may assign a domain name via DHCP. You can go to
menu 24.8 and type "sys domain name" to see the current domain
name used by your router.
If you want to clear this field just press [SPACE BAR] and then
[ENTER]. The domain name entered by you is given priority over the
ISP assigned domain name.
Edit Dynamic DNS
Press [SPACE BAR] and then [ENTER] to select
Select
to configure
Yes
Menu 1.1 — Configure Dynamic DNS
Yes
or
No
(default).
No
(default)
discussed next.
Route IP
Set this field to
to enable or No to disable IP routing. You must
Yes
Yes
enable IP routing for Internet access.
Bridge Turn on/off bridging for protocols not supported (for example, SNA) or
not turned on in the previous
Route IP
field. Select
Yes
to turn
No
bridging on; select No to turn bridging off.
3.3.1 Configuring Dynamic DNS
To configure Dynamic DNS, go to Menu 1 — General Setup and press [SPACE BAR] to select Yes in
the Edit Dynamic DNS field. Press [ENTER] to display Menu 1.1— Configure Dynamic DNS (shown
next).
Menu 1.1 - Configure Dynamic DNS
Service Provider= WWW.DynDNS.ORG
Active= Yes
Host=
EMAIL=
USER=
Password= ********
Enable Wildcard= No
Press ENTER to confirm or ESC to cancel:
Figure 3-2 Configure Dynamic DNS
General Setup 3-3
Page 54

Prestige 652 ADSL Security Router
Follow the instructions in the next table to configure Dynamic DNS parameters.
Table 3-2 Configure Dynamic DNS Menu Fields
FIELD DESCRIPTION EXAMPLE
Service Provider This is the name of your Dynamic DNS service provider. WWW.DynDNS.ORG
(default)
Active
Host Enter the domain name assigned to your Prestige by your
EMAIL Enter your e-mail address. mail@mailserver
USER Enter your user name.
Password Enter the password assigned to you.
Enable Wildcard Your Prestige supports DYNDNS Wildcard. Press [SPACE BAR]
When you have completed this menu, press [ENTER] at the prompt “Press ENTER to Confirm…” to save
your configuration, or press [ESC] at any time to cancel.
Press [SPACE BAR] to select
enable dynamic DNS.
Dynamic DNS provider.
and then [ENTER] to select
you choose DDNS client as your service provider.
and then press [ENTER] to
Yes
or
Yes
This field is
No
N/A
Yes
me.dyndns.org
No
when
The IP address will be updated when you reconfigure menu 1 or perform DHCP client renewal.
If you have a private WAN IP address, then you cannot use Dynamic DNS.
3.4 LAN Setup
This section describes how to configure the Ethernet using Menu 3 – LAN Setup. From the main menu,
enter 3 to display menu 3.
3-4 General Setup
Page 55

Prestige 652 ADSL Security Router
Menu 3 - Ethernet Setup
1. LAN Port Filter Setup
2. TCP/IP and DHCP Setup
Enter Menu Selection Number:
Figure 3-3 Menu 3 — Ethernet Setup
3.4.1 LAN Port Filter Setup
This menu allows you to specify filter set(s) that you wish to apply to the Ethernet traffic. You seldom
need to filter Ethernet traffic; however, the filter sets may be useful to block certain packets, reduce traffic
and prevent security breaches.
Menu 3.1 - LAN Port Filter Setup
Input Filter Sets:
protocol filters=
device filters=
Output Filter Sets:
protocol filters=
device filters=
Press ENTER to Confirm or ESC to Cancel:
Figure 3-4 Menu 3.1 — LAN Port Filter Setup
If you need to define filters, please read the Filter Set Configuration chapter first, then return to this menu
to define the filter sets.
3.5 Protocol Dependent Ethernet Setup
Depending on the protocols for your applications, you need to configure the respective Ethernet Setup, as
outlined next.
z For TCP/IP Ethernet setup refer to Internet Access Application.
z For bridging Ethernet setup refer to Bridging Setup.
General Setup 3-5
Page 56

Page 57

Prestige 652 ADSL Security Router
Chapter 4
Internet Access
This chapter shows you how to configure the LAN and WAN of your Prestige for Internet access.
4.1 Factory Ethernet Defaults
The Ethernet parameters of the Prestige are preset in the factory with the following values:
1. IP address of 192.168.1.1 with subnet mask of 255.255.255.0 (24 bits).
2. DHCP server enabled with 32 client IP addresses starting from 192.168.1.33.
These parameters should work for the majority of installations. If the parameters are satisfactory, you can
skip to TCP/IP Ethernet Setup and DHCP to enter the DNS server address(es) if your ISP gives you explicit
DNS server address(es). Please read on if you wish to change the factory defaults or to learn more about
TCP/IP.
4.2 LANs and WANs
A LAN (Local Area Network) is a computer network limited to the immediate area, usually the same
building or floor of a building. A WAN (Wide Area Network), on the other hand, is an outside connection
to another network or the Internet.
4.2.1 LANs, WANs and the Prestige
The actual physical connection determines whether the Prestige ports are LAN or WAN ports. There are
two separate IP networks, one inside, the LAN network; the other outside: the WAN network as shown
next:
Internet Access 4-1
Page 58

Prestige 652 ADSL Security Router
Figure 4-1 LAN & WAN IPs
4.3 TCP/IP Parameters
4.3.1 IP Address and Subnet Mask
Like houses on a street that share a common street name, the computers on a LAN share one common
network number.
Where you obtain your network number depends on your particular situation. If the ISP or your network
administrator assigns you a block of registered IP addresses, follow their instructions in selecting the IP
addresses and the subnet mask.
If the ISP did not explicitly give you an IP network number, then most likely you have a single user account
and the ISP will assign you a dynamic IP address when the connection is established. If this is the case, it is
recommended that you select a network number from 192.168.0.0 to 192.168.255.0 (ignoring the trailing
zero) and you must enable the Single User Account feature of the Prestige. The Internet Assigned Number
Authority (IANA) reserved this block of addresses specifically for private use; please do not use any other
number unless you are told otherwise. Let’s say you select 192.168.1.0 as the network number; which
covers 254 individual addresses, from 192.168.1.1 to 192.168.1.254 (zero and 255 are reserved). In other
words, the first three numbers specify the network number while the last number identifies an individual
computer on that network.
The subnet mask specifies the network number portion of an IP address. Your Prestige will compute the
subnet mask automatically based on the IP address that you entered. You don’t need to change the subnet
mask computed by the Prestige unless you are instructed to do otherwise.
4-2 Internet Access
Page 59

Prestige 652 ADSL Security Router
4.3.2 Private IP Addresses
Every machine on the Internet must have a unique address. If your networks are isolated from the Internet,
for example, only between your two branch offices, you can assign any IP addresses to the hosts without
problems. However, the Internet Assigned Numbers Authority (IANA) has reserved the following three
blocks of IP addresses specifically for private networks:
10.0.0.0 - 10.255.255.255
172.16.0.0 - 172.31.255.255
192.168.0.0 - 192.168.255.255
You can obtain your IP address from the IANA, from an ISP or it can be assigned from a private network.
If you belong to a small organization and your Internet access is through an ISP, the ISP can provide you
with the Internet addresses for your local networks. On the other hand, if you are part of a much larger
organization, you should consult your network administrator for the appropriate IP addresses.
Note: Regardless of your particular situation, do not create an arbitrary IP
address; always follow the guidelines above. For more information on address
assignment, please refer to RFC 1597,
and RFC 1466,
Guidelines for Management of IP Address Space.
Address Allocation for Private Internets
4.3.3 RIP Setup
RIP (Routing Information Protocol) allows a router to exchange routing information with other routers.
The RIP Direction field controls the sending and receiving of RIP packets. When set to:
1. Both - the Prestige will broadcast its routing table periodically and incorporate the RIP information
that it receives.
2. In Only - the Prestige will not send any RIP packets but will accept all RIP packets received.
3. Out Only - the Prestige will send out RIP packets but will not accept any RIP packets received.
4. None - the Prestige will not send any RIP packets and will ignore any RIP packets received.
The Version field controls the format and the broadcasting method of the RIP packets that the Prestige
sends (it recognizes both formats when receiving). RIP-1 is universally supported; but RIP-2 carries more
information. RIP-1 is probably adequate for most networks, unless you have an unusual network topology.
Both RIP-2B and RIP-2M sends the routing data in RIP-2 format; the difference being that RIP-2B uses
subnet broadcasting while RIP-2M uses multicasting.
Internet Access 4-3
Page 60

Prestige 652 ADSL Security Router
4.3.4 DHCP Configuration
DHCP (Dynamic Host Configuration Protocol) allows the individual clients (computers) to obtain the
TCP/IP configuration at start-up from a centralized DHCP server. The Prestige has built-in DHCP server
capability, enabled by default, which means it can assign IP addresses, an IP default gateway and DNS
servers to Windows 95, Windows NT and other systems that support the DHCP client. The Prestige can
also act as a surrogate DHCP server where it relays IP address assignment from the actual DHCP server to
the clients.
IP Pool Setup
The Prestige is pre-configured with a pool of 32 IP addresses starting from 192.168.1.33 to 192.168.1.64 for
the client machines. This leaves 31 IP addresses, 192.168.1.2 to 192.168.1.32 (excluding the Prestige itself
which has a default IP of 192.168.1.1) for other server machines, for example, server for mail, FTP, telnet,
web, etc., that you may have.
DNS Server Address
DNS (Domain Name System) is for mapping a domain name to its corresponding IP address and vice versa,
for example, the IP address of www.zyxel.com is 204.217.0.2. The DNS server is extremely important
because without it, you must know the IP address of a machine before you can access it. The DNS server
addresses that you enter in the DHCP setup are passed to the client machines along with the assigned IP
address and subnet mask.
There are two ways that an ISP disseminates the DNS server addresses. The first is for an ISP to tell a
customer the DNS server addresses, usually in the form of an information sheet, when s/he signs up. If
your ISP does give you the DNS server addresses, enter them in the DNS Server fields in DHCP Setup,
otherwise, leave them blank.
Some ISP’s choose to pass the DNS servers using the DNS server extensions of PPP IPCP (IP Control
Protocol) after the connection is up. If your ISP did not give you explicit DNS servers, chances are the
DNS servers are conveyed through IPCP negotiation. The Prestige supports the IPCP DNS server
extensions through the DNS proxy feature.
If the Primary and Secondary DNS Server fields in DHCP Setup are not specified, for instance, left as
0.0.0.0, the Prestige tells the DHCP clients that it itself is the DNS server. When a computer sends a DNS
query to the Prestige, the Prestige forwards the query to the real DNS server learned through IPCP and
relays the response back to the computer.
Please note that DNS proxy works only when the ISP uses the IPCP DNS server extensions. It does not
mean you can leave the DNS servers out of the DHCP setup under all circumstances. If your ISP gives you
explicit DNS servers, make sure that you enter their IP addresses in the DHCP Setup menu. This way, the
Prestige can pass the DNS servers to the computers and the computers can query the DNS server directly
without the Prestige’s intervention.
4-4 Internet Access
Page 61

Prestige 652 ADSL Security Router
4.4 IP Multicast
Traditionally, IP packets are transmitted in one of either two ways - Unicast (1 sender – 1 recipient) or
Broadcast (1 sender – everybody on the network). Multicast is a third way to deliver IP packets to a group
of hosts on the network - not everybody.
IGMP (Internet Group Multicast Protocol) is a session-layer protocol used to establish membership in a
multicast group - it is not used to carry user data. IGMP version 2 (RFC 2236) is an improvement over
version 1 (RFC 1112) but IGMP version 1 is still in wide use. If you would like to read more detailed
information about interoperability between IGMP version 2 and version 1, please see sections 4 and 5 of
RFC 2236. The class D IP address is used to identify host groups and can be in the range 224.0.0.0 to
239.255.255.255. The address 224.0.0.0 is not assigned to any group and is used by IP multicast computers.
The address 224.0.0.1 is used for query messages and is assigned to the permanent group of all IP hosts
(including gateways). All hosts must join the 224.0.0.1 group in order to participate in IGMP. The address
224.0.0.2 is assigned to the multicast routers group.
The Prestige supports both IGMP version 1 (IGMP-v1) and version 2 (IGMP-v2). At start up, the Prestige
queries all directly connected networks to gather group membership. After that, the Prestige periodically
updates this information. IP Multicasting can be enabled/disabled on the Prestige LAN and/or WAN
interfaces using menus 3.2 (LAN) and 11.3 (WAN). Select None to disable IP Multicasting on these
interfaces.
4.5 IP Policies
Traditionally, routing is based on the destination address only and the router takes the shortest path to
forward a packet. IP Policy Routing (IPPR) provides a mechanism to override the default routing behavior
and alter the packet forwarding based on the policy defined by the network administrator. Policy-based
routing is applied to incoming packets on a per interface basis, prior to the normal routing. Create policies
using SMT menu 25 (see IP Policy Routing) and apply them on the Prestige LAN and/or WAN interfaces
using menus 3.2 (LAN) and 11.3 (WAN).
4.6 IP Alias
IP Alias allows you to partition a physical network into different logical networks over the same Ethernet
interface. The Prestige supports three logical LAN interfaces via its single physical Ethernet interface with
the Prestige itself as the gateway for each LAN network.
Internet Access 4-5
Page 62

Prestige 652 ADSL Security Router
Figure 4-2 Physical Network Figure 4-3 Partitioned Logical Networks
Use menu 3.2.1 to configure IP Alias on your Prestige.
4.6.1 IP Alias Setup
Use menu 3.2 to configure the first network. Move the cursor to Edit IP Alias field and press
[SPACEBAR] to choose Yes and press [ENTER] to configure the second and third network.
Menu 3.2 - TCP/IP and DHCP Ethernet Setup
DHCP Setup:
DHCP= Server
Client IP Pool Starting Addres= 192.168.1.33
Size of Client IP Pool= 32
Primary DNS Server= 0.0.0.0
Secondary DNS Server= 0.0.0.0
Remote DHCP Server= N/A
TCP/IP Setup:
IP Address= 192.168.1.1
IP Subnet Mask= 255.255.255.0
RIP Direction= None
Version= N/A
Multicast= None
IP Policies=
Edit IP Alias= No
Press ENTER to confirm or ESC to Cancel:
Press Space Bar to Toggle.
Figure 4-4 Menu 3.2 — TCP/IP and DHCP Ethernet Setup
4-6 Internet Access
Page 63

Prestige 652 ADSL Security Router
Pressing [ENTER] displays Menu 3.2.1 - IP Alias Setup, as shown next.
Menu 3.2.1 - IP Alias Setup
IP Alias 1= No
IP Address= N/A
IP Subnet Mask= N/A
RIP Direction= N/A
Version= N/A
Incoming protocol filters= N/A
Outgoing protocol filters= N/A
IP Alias 2= No
IP Address= N/A
IP Subnet Mask= N/A
RIP Direction= N/A
Version= N/A
Incoming protocol filters= N/A
Outgoing protocol filters= N/A
Enter here to CONFIRM or ESC to CANCEL:
Press Space Bar to Toggle.
Figure 4-5 Menu 3.2.1 — IP Alias Setup
Follow the instructions in the following table to configure IP Alias parameters.
Table 4-1 IP Alias Setup Menu Fields
FIELD DESCRIPTION EXAMPLE
IP Alias (1 or 2)
Choose
IP Address Enter the IP address of your Prestige in dotted decimal notation 192.168.2.1
IP Subnet Mask Your Prestige will automatically calculate the subnet mask based on
the IP address that you assign. Unless you are implementing
subnetting, use the subnet mask computed by the Prestige
RIP Direction
Press [SPACE BAR] to select the RIP direction. Choices are
Both, In Only
Version
Press [
RIP-2B
Incoming
Protocol Filters
Outgoing
Protocol Filters
Enter the filter set(s) you wish to apply to the incoming traffic
between this node and the Prestige.
Enter the filter set(s) you wish to apply to the outgoing traffic between
this node and the Prestige.
to configure the LAN network for the Prestige.
Yes
or
Out Only
.
SPACE BAR] to select the RIP version. Choices are
or
RIP-2M
.
None
RIP-1
255.255.255.0
,
,
Yes
None
RIP-1
When you have completed this menu, press [ENTER] at the prompt “Press ENTER to Confirm…” to
save your configuration, or press [
ESC] at any time to cancel.
Internet Access 4-7
Page 64

Prestige 652 ADSL Security Router
4.7 Route IP Setup
The first step is to enable the IP routing in Menu 1 - General Setup.
To edit menu 1, type in 1 in the main menu and press [ENTER]. Set the Route IP field to Yes by pressing
[SPACE BAR].
Menu 1 - General Setup
System Name= ?
Location=
Contact Person's Name=
Domain Name=
Edit Dynamic DNS= No
Route IP= Yes
Bridge= No
Press ENTER to Confirm or ESC to Cancel:
Figure 4-6 Menu 1 — General Setup
4.8 TCP/IP Ethernet Setup and DHCP
Use menu 3.2 to configure your Prestige for TCP/IP.
To edit menu 3.2, enter 3 from the main menu to display Menu 3 - Ethernet Setup. When menu 3 appears,
enter 2 to display Menu 3.2 - TCP/IP and DHCP Ethernet Setup, as shown next
:
4-8 Internet Access
Page 65

Prestige 652 ADSL Security Router
Menu 3.2 - TCP/IP and DHCP Ethernet Setup
DHCP Setup:
DHCP= Server
Client IP Pool Starting Address= 192.168.1.33
Size of Client IP Pool= 32
Primary DNS Server= 0.0.0.0
Secondary DNS Server= 0.0.0.0
Remote DHCP Server= N/A
TCP/IP Setup:
IP Address= 192.168.1.1
IP Subnet Mask= 255.255.255.0
RIP Direction= Both
Version= RIP-1
Multicast= None
IP Policies=
Edit IP Alias= No
Press ENTER to Confirm or ESC to Cancel:
Press Space Bar to Toggle.
First address
in the IP Pool
Size of the IP
Pool
IP addresses
of the DNS
servers
This is the IP
address of the
Prestige
Figure 4-7 Menu 3.2 — TCP/IP and DHCP Ethernet Setup
Follow the instructions in the following table on how to configure the DHCP fields.
Table 4-2 DHCP Ethernet Setup Menu Fields
FIELD DESCRIPTION EXAMPLE
DHCP Setup
If set to
DHCP
default gateway and DNS servers to Windows 95, Windows NT
and other systems that support the DHCP client.
If set to
If set to
relays DHCP requests and responses between the remote server
and the clients. Enter the IP address of the actual, remote DHCP
server in the Remote DHCP Server in this case.
When DHCP is used, the following items need to be set:
Client IP Pool Starting
Address
This field specifies the first of the contiguous addresses in the IP
address pool.
Size of Client IP Pool This field specifies the size or count of the IP address pool. 32
, your Prestige can assign IP addresses, an IP
Server
, the DHCP server will be disabled.
None
, the Prestige acts as a surrogate DHCP server and
Relay
Server
(default)
192.168.1.33
Internet Access 4-9
Page 66

Prestige 652 ADSL Security Router
FIELD DESCRIPTION EXAMPLE
Primary DNS Server
Secondary DNS Server
Remote DHCP Server
Enter the IP addresses of the DNS servers. The DNS servers
are passed to the DHCP clients along with the IP address and
the subnet mask.
If
address of the actual remote DHCP server here.
is selected in the
Relay
field above then enter the IP
DHCP
Follow the instructions in the following table to configure TCP/IP parameters for the Ethernet port.
Table 4-3 TCP/IP Ethernet Setup Menu Fields
FIELD DESCRIPTION EXAMPLE
TCP/IP Setup
IP Address Enter the (LAN) IP address of your Prestige in dotted decimal
notation
IP Subnet Mask Your Prestige will automatically calculate the subnet mask based on
the IP address that you assign. Unless you are implementing
subnetting, use the subnet mask computed by the Prestige.
RIP Direction
Version
Multicast IGMP (Internet Group Multicast Protocol) is a session-layer protocol
IP Policies Create policies using SMT menu 25 (see the IP Policy Routing
Edit IP Alias The Prestige supports three logical LAN interfaces via its single
SPACE BAR] to select the RIP direction. Choices are
Press [
Both, In Only, Out Only or None
Press [SPACE BAR] to select the RIP version. Choices are
RIP-2B or RIP-2M
used to establish membership in a Multicast group. The Prestige
supports both IGMP version 1 (
Press the [
to disable it.
chapter) and apply them on the Prestige LAN interface here. You
can apply up to four IP Policy sets (from twelve) by entering their
numbers separated by commas.
physical Ethernet interface with the Prestige itself as the gateway for
each LAN network. Press [SPACE BAR] to change
press [ENTER] to for menu 3.2.1
SPACE BAR] to enable IP Multicasting or select
.
.
IGMP-v1
) and version 2 (
No
RIP-1
IGMP-v2
None
to
Yes
and
192.168.1.1
255.255.255.0
(default)
,
(default)
(default)
).
(default)
RIP-1
None
2,4,7,9
Both
No
When you have completed this menu, press [ENTER] at the prompt “Press ENTER to Confirm…” to save
your configuration, or press [
ESC] at any time to cancel.
4-10 Internet Access
Page 67

Prestige 652 ADSL Security Router
4.9 VPI and VCI
Be sure to use the correct Virtual Path Identifier (VPI) and Virtual Channel Identifier (VCI) numbers
supplied by your telephone company. The valid range for the VPI is 0 to 255 and for the VCI is 32 to
65535 (0 to 31 is reserved for local management of ATM traffic). Please see the Appendices for more
information.
4.10 Multiplexing
There are two conventions to identify what protocols the virtual circuit (VC) is carrying. Be sure to use the
multiplexing method required by your ISP.
4.10.1 VC-based Multiplexing
In this case, by prior mutual agreement, each protocol is assigned to a specific virtual circuit, for example,
VC1 carries IP, etc. VC-based multiplexing may be dominant in environments where dynamic creation of
large numbers of ATM VCs is fast and economical.
4.10.2 LLC-based Multiplexing
In this case one VC carries multiple protocols with protocol identifying information being contained in each
packet header. Despite the extra bandwidth and processing overhead, this method may be advantageous if it
is not practical to have a separate VC for each carried protocol, for example, if charging heavily depends on
the number of simultaneous VCs.
4.11 Encapsulation
Be sure to use the encapsulation method required by your ISP. The Prestige supports the following
methods.
4.11.1 ENET ENCAP
The MAC Encapsulated Routing Link Protocol (ENET ENCAP) is only implemented with the IP network
protocol. IP packets are routed between the Ethernet interface and the WAN interface and then formatted so
that they can be understood in a bridged environment for instance, it encapsulates routed Ethernet frames
into bridged ATM cells. ENET ENCAP requires that you specify a gateway IP address in the Ethernet
Encapsulation Gateway field in menu 4 and in the Rem IP Addr field in menu 11.1. You can get this
information from your ISP.
Internet Access 4-11
Page 68

Prestige 652 ADSL Security Router
4.11.2 PPP over Ethernet
PPPoE provides access control and billing functionality in a manner similar to dial-up services using PPP.
The Prestige bridges a PPP session over Ethernet (PPP over Ethernet, RFC 2516) from your computer to an
ATM PVC (Permanent Virtual Circuit) which connects to a xDSL Access Concentrator where the PPP
session terminates. One PVC can support any number of PPP sessions from your LAN. For more
information on PPPoE, see the Appendices.
4.11.3 PPPoA
Please refer to RFC 2364 for more information on PPP over ATM Adaptation Layer 5 (AAL5). Refer to
RFC 1661 for more information on PPP.
4.11.4 RFC 1483
RFC 1483 describes two methods for Multiprotocol Encapsulation over ATM Adaptation Layer 5 (AAL5).
The first method allows multiplexing of multiple protocols over a single ATM virtual circuit (LLC-based
multiplexing) and the second method assumes that each protocol is carried over a separate ATM virtual
circuit (VC-based multiplexing). Please refer to the RFC for more detailed information.
4.12 IP Address Assignment
A static IP is a fixed IP that your ISP gives you. A dynamic IP is not fixed; the ISP assigns you a different
one each time. The Single User Account feature can be enabled or disabled if you have either a dynamic or
static IP. However the encapsulation method assigned influences your choices for IP Address and ENET
ENCAP Gateway.
4.12.1 Using PPPoA or PPPoE Encapsulation
If you have a dynamic IP, then the IP Address and ENET ENCAP Gateway fields are not applicable (N/A).
If you have a static IP, then you only need to fill in the IP Address field and not the ENET ENCAP
Gateway field.
4.12.2 Using RFC 1483 Encapsulation
In this case the IP Address Assignment must be static with the same requirements for the IP Address and
ENET ENCAP Gateway fields as stated above.
4.12.3 Using ENET ENCAP Encapsulation
In this case you can have either a static or dynamic IP. For a static IP you must fill in all the IP Address and
ENET ENCAP Gateway fields as supplied by your ISP. However for a dynamic IP, the Prestige acts as a
4-12 Internet Access
Page 69

Prestige 652 ADSL Security Router
DHCP client on the WAN port and so the IP Address and ENET ENCAP Gateway fields are not applicable
(N/A) as they are assigned to the Prestige by the DHCP server.
4.13 Internet Access Configuration
Menu 4 allows you to enter the Internet Access information in one screen. Menu 4 is actually a simplified
setup for one of the remote nodes that you can access in menu 11. Before you configure your Prestige for
Internet access, you need to collect your Internet account information from your ISP and telephone
company.
Use the following table to record your Internet Account Information. Note that if you are using PPPoA or
PPPoE encapsulation, then the only ISP information you need is a login name and password. You only need
to know the Ethernet Encapsulation Gateway IP address if you are using ENET ENCAP encapsulation.
Table 4-4 Internet Account Information
FIELD DESCRIPTION YOUR INFO
System Name Name of the Prestige (optional).
Service Name
(PPPoE
Encapsulation)
Encapsulation PPPoE, RFC1483, PPPoA or ENET ENCAP.
Multiplexing LLC-based or VC-based. If this information is not
VPI Enter your Virtual Path Identifier here.
VCI Enter your Virtual Channel Identifier here.
My Login Enter the login name assigned by your ISP (for
My Password Enter the password associated with your ISP assigned
Idle Timeout
(PPPoE or PPP)
IP Address Enter if your IP address if it is not dynamically
Network Address
Translation
Enter the PPPoE service name if the ISP supplies one.
Enter “any” if the ISP does not assign you one.
given, use the default.
PPP/PPPoE only).
My Login (for PPPoA/PPPoE only).
Enter the time lapse, in seconds, before you
automatically disconnect from the PPPoE or PPP
server.
assigned.
Full Feature, SUA Only or None.
Internet Access 4-13
Page 70

Prestige 652 ADSL Security Router
FIELD DESCRIPTION YOUR INFO
DNS Server
Address
Assignment
ENET ENCAP
Gateway
Primary DNS server
Secondary DNS server
Enter when using RFC 1483 Encapsulation or a static
IP address.
IP Address
Gateway IP Address
Enter when using ENET ENCAP Encapsulation.
4.13.1 Traffic Shaping
Traffic Shaping is an agreement between the carrier and the subscriber to regulate the average rate and
“burstiness” or fluctuation of data transmission over an ATM network. This agreement helps eliminate
congestion, which is important for transmission of real time data such as audio and video connections.
Peak Cell Rate (PCR) is the maximum rate at which the sender can send cells. This parameter may be lower
(but not higher) than the maximum line speed. 1 ATM cell is 53 bytes (424 bits), so a maximum speed of
832 Kbps gives a maximum PCR of 1962 cells/sec. This rate is not guaranteed because it is dependent on
the line speed.
Sustained Cell Rate (SCR) is the mean cell rate of a bursty, on-off traffic source that can be sent at the peak
rate, and a parameter for burst-type traffic. SCR may not be greater than the PCR; the system default is 0
cells/sec.
Maximum Burst Size (MBS) is the maximum number of cells that can be sent at the PCR. After MBS is
reached, cell rates fall below SCR until cell rate averages to the SCR again. At this time, more cells (up to
the MBS) can be sent at the PCR again.
If the PCR, SCR or MBS is set to the default of “0”, the system will assign a
maximum value that correlates to your upstream line rate.
The following figure illustrates the relationship between PCR, SCR and MBS.
4-14 Internet Access
Page 71

Prestige 652 ADSL Security Router
Figure 4-8 Example of Traffic Shaping
From the main menu, enter 4 to display Menu 4 - Internet Access Setup, (shown next).
Menu 4 - Internet Access Setup
ISP's Name= ChangeMe
Encapsulation= RFC 1483
Multiplexing= VC-based
VPI #= 8
VCI #= 35
ATM QoS Type= CBR
Peak Cell Rate (PCR)= 0
Sustain Cell Rate (SCR)= 0
Maximum Burst Size (MBS)= 0
My Login= N/A
My Password= N/A
ENET ENCAP Gateway= N/A
IP Address Assignment= Static
IP Address= 0.0.0.0
Network Address Translation= SUA Only
Address Mapping Set= N/A
Press ENTER to Confirm or ESC to Cancel:
Figure 4-9 Internet Access Setup
The following table contains instructions on how to configure your Prestige for Internet access.
Internet Access 4-15
Page 72

Prestige 652 ADSL Security Router
Table 4-5 Internet Access Setup Menu Fields
FIELD DESCRIPTION EXAMPLE
ISP’s Name Enter the name of your Internet Service Provider. This
information is for identification purposes only.
Encapsulation
Multiplexing
VPI # Enter the Virtual Path Identifier (VPI) that the telephone
VCI # Enter the Virtual Channel Identifier (VCI) that the telephone
ATM QoS Type
Peak Cell Rate (PCR) This is the maximum rate at which the sender can send cells.
Sustain Cell Rate
(SCR)= 0
Maximum Burst Size
(MBS)= 0
My Login Configure the My Login and My Password fields for PPP and
My Password Enter the password associated with the login name above. N/A
ENET ENCAP
Gateway
IP Address
Assignment
IP Address Enter the IP address supplied by your ISP if applicable. 0.0.0.0
Press [SPACE BAR] to select the method of encapsulation
used by your ISP. Choices are
ENET ENCAP
Press [SPACE BAR] to select the method of multiplexing
used by your ISP. Choices are
company gives you.
company gives you.
Press [SPACE BAR] and select
specify fixed (always-on) bandwidth. Select
Bit Rate) for applications that are non-time sensitive, such as
e-mail.
Type the PCR.
Sustained Cell Rate is the mean cell rate of a bursty, on-off
traffic source that can be sent at the peak rate, and a
parameter for burst-type traffic. Type the SCR; it must be less
than the PCR.
Refers to the maximum number of cells that can be sent at the
peak rate. Type the MBS. The MBS must be less than 65535.
PPPoE encapsulation only. Enter the login name that your ISP
gives you. If you are using
field must be of the form user@domain where domain
identifies your PPPoE service name.
Enter the gateway IP address supplied by your ISP when you
are using
Press [SPACE BAR] to select
assignment.
.
ENET ENCAP
PPPoE, PPP
VC-based
CBR
PPPoE
encapsulation.
encapsulation, then this
Static
oA,
RFC 1483
or
LLC-based
(Continuous Bit Rate) to
(Unspecified
UBR
or
Dynamic
address
or
.
ChangeMe
RFC 1483
VC-based
8
35
UBR
0
0
0
N/A
N/A
Static
4-16 Internet Access
Page 73

Prestige 652 ADSL Security Router
FIELD DESCRIPTION EXAMPLE
Network Address
Translation
Address Mapping Set Type the numbers of mapping sets (1-8) to use with NAT. See
When you have completed this menu, press [ENTER] at the prompt “Press ENTER to Confirm…” to save
your configuration, or press [ESC] at any time to cancel.
Press [SPACE BAR] to select
Feature
SUA (Single User Account) feature.
the NAT chapter for details.
. Please see the NAT Chapter for more details on the
None, SUA Only
or
Full
SUA Only
N/A
If all your settings are correct your Prestige should connect automatically to the Internet. If the connection
fails, note the error message that you receive on the screen and take the appropriate troubleshooting steps.
Internet Access 4-17
Page 74

Advanced Applications
PPaarrtt IIII::
ADVANCED APPLICATIONS
This part shows how to configure Remote Nodes, Remote Node TCP/IP and NAT.
II
Page 75

Prestige 652 ADSL Security Router
Chapter 5
Remote Node Configuration
This chapter covers the parameters that are protocol-independent. Protocol-dependent
configuration (TCP/IP and Bridging) is covered in the following chapters.
A remote node is required for placing calls to a remote gateway. A remote node represents both the remote
gateway and the network behind it across a WAN connection. When you use menu 4 to set up Internet
access, you are configuring one of the remote nodes.
5.1 Remote Node Setup
This section describes the protocol-independent parameters for a remote node.
5.1.1 Remote Node Profile
To configure a remote node, follow these steps:
Step 1. From the main menu, enter 11 to display Menu 11 - Remote Node Setup.
Step 2. When menu 11 appears, as shown in the following figure, enter the number of the remote node
that you want to configure.
Menu 11 - Remote Node Setup
1. ChangeMe (ISP, SUA)
2. ________
3. ________
4. ________
5. ________
6. ________
7. ________
8. ________
Enter Node # to Edit:
Figure 5-1 Menu 11 — Remote Node Setup
Remote Node Configuration 5-1
Page 76

Prestige 652 ADSL Security Router
5.1.2 Encapsulation and Multiplexing Scenarios
For Internet access you should use the encapsulation and multiplexing methods used by your ISP. Consult
your telephone company for information on encapsulation and multiplexing methods for LAN-to-LAN
applications, for example between a branch office and corporate headquarters. There must be prior
agreement on encapsulation and multiplexing methods because they cannot be automatically determined.
What method(s) you use also depends on how many VCs you have and how many different network
protocols you need. The extra overhead that ENET ENCAP encapsulation entails makes it a poor choice in
a LAN-to-LAN application. Here are some examples of more suitable combinations in such an application.
Scenario 1. One VC, Multiple Protocols
PPPoA (RFC-2364) encapsulation with VC-based multiplexing is the best combination because no extra
protocol identifying headers are needed. The PPP protocol already contains this information.
Scenario 2. One VC, One Protocol (IP)
Selecting RFC-1483 encapsulation with VC-based multiplexing requires the least amount of overhead (0
octets). However, if there is a potential need for multiple protocol support in the future, it may be safer to
select PPPoA encapsulation instead of RFC-1483, so you do not need to reconfigure either computer later.
Scenario 3. Multiple VCs
If you have an equal number (or more) of VCs than the number of protocols, then select RFC-1483
encapsulation and VC-based multiplexing.
Nailed-Up Connection (PPPoA)
A nailed-up connection is a dial-up line where the connection is always up regardless of traffic demand.
The Prestige does two things when you specify a nailed-up connection. The first is that idle timeout is
disabled. The second is that the Prestige will try to bring up the connection when turned on and whenever
the connection is down. A nailed-up connection can be very expensive.
Do not specify a nailed-up connection unless your telephone company offers flat-rate service or you need a
constant connection and the cost is of no concern.
5-2 Remote Node Configuration
Page 77

Prestige 652 ADSL Security Router
Menu 11.1 - Remote Node Profile
Rem Node Name= ChangeMe
Active= Yes
Encapsulation= PPP
Multiplexing= LLC-based
Service Name= N/A
Incoming:
Rem Login=
Rem Password= ********
Outgoing:
My Login=
My Password= ********
Authen= CHAP/PAP
Press ENTER to Confirm or ESC to Cancel:
Route= IP
Bridge= No
Edit IP/Bridge= No
Edit ATM Options= No
Telco Option:
Allocated Budget(min)= 0
Period (hr)= 0
Schedule Sets= N/A
Nailed-Up Connection= N/A
Session Options:
Edit Filter Sets= No
Idle Timeout (sec)= 0
Figure 5-2 Menu 11.1 — Remote Node Profile
In Menu 11.1 – Remote Node Profile, fill in the fields as described in the following table.
Table 5-1 Remote Node Profile Menu Fields
FIELD DESCRIPTION EXAMPLE
Rem Node Name Type a unique, descriptive name of up to eight characters for this
node.
Active
Press [SPACE BAR] and then [ENTER] to select
to deactivate this node. Inactive nodes are displayed with a
No
minus sign “–“.
Encapsulation
RFC-1483
then [ENTER] to select either
is the default configuration, press [SPACE BAR] and
PPPoE, PPP
oA (RFC-2364, PPP
Encapsulation over ATM Adaptation Layer 5) or
oA refers to RFC-2364 (PPP Encapsulation over ATM Adaptation
PPP
Layer 5).
refers to RFC-2364 (Point-to-Point Protocol over Ethernet).
PPPoE
If
RFC-1483
Layer 5) or
Password, My Login, My Password
Timeout
(Multiprotocol Encapsulation over ATM Adaptation
ENET ENCAP
is selected, then the
, Telco Options and
fields are not applicable (
N/A
).
Multiplexing Press [SPACE BAR] and then [ENTER] to select the method of
multiplexing that your ISP uses, either
VC-based
to activate or
Yes
ENET ENCAP.
Rem Login, Rem
Idle
or
LLC-based
.
ChangeMe
Yes
PPPoA
LLC-based
Remote Node Configuration 5-3
Page 78

Prestige 652 ADSL Security Router
FIELD DESCRIPTION EXAMPLE
Service Name When using PPPoE encapsulation, type the name of your PPPoE
service here.
Incoming:
Rem Login
Rem Password Type the password used when this remote node calls your
Outgoing:
My Login
My Password Type the password assigned by your ISP when the Prestige calls
Authen
Route
Bridge When bridging is enabled, your Prestige will forward any packet
Edit IP/Bridge
Edit ATM Options
Telco Option
Allocated Budget
(min)
Period (hr) This field is the time period that the budget should be reset. For
Type the login name that this remote node will use to call your
Prestige. The login name and the
authenticate this node.
Prestige.
Type the login name assigned by your ISP when the Prestige calls
this remote node.
this remote node.
This field sets the authentication protocol used for outgoing calls.
Options for this field are:
CHAP/PAP
requested by this remote node.
CHAP
Protocol) only.
PAP
This field determines the protocol used in routing. Options are
and
None.
that it does not route to this remote node; otherwise, the packets
are discarded. Select
Press [SPACE BAR] to select
Menu 11.3 – Remote Node Network Layer Options
Press [SPACE BAR] to select
Menu 11.6 – Remote Node ATM Layer Options
This sets a ceiling for outgoing call time for this remote node. The
default for this field is 0 meaning no budget control.
example, if we are allowed to call this remote node for a maximum
of 10 minutes every hour, then the
minutes) and the
– Your Prestige will accept either
– accept
– accept PAP (Password Authentication Protocol) only.
(Challenge Handshake Authentication
CHAP
to enable and No to disable.
Yes
Period (hr)
Rem Password
and press [ENTER] to display
Yes
and press [ENTER] to display
Yes
Allocated Budget
is 1 (hour).
will be used to
or
CHAP
.
.
is (10
PAP
when
IP
N/A
PAP
IP
No
No
No
0
(default)
0
(default)
5-4 Remote Node Configuration
Page 79

Prestige 652 ADSL Security Router
FIELD DESCRIPTION EXAMPLE
Schedule Sets You can apply up to four schedule sets here. For more details
please refer to the Call Schedule Setup chapter.
Nailed up
Connection
Session Options
Edit Filter Sets
Idle Timeout (sec) Type the number of seconds (0-9999) that can elapse when the
When you have completed this menu, press [ENTER] at the prompt “Press [ENTER] to confirm or [ESC]
to cancel” to save your configuration or press [ESC] to cancel and go back to the previous screen.
This field specifies if you want to make the connection to this
remote node a nailed-up connection. More details are given earlier
in this section.
Use [SPACE BAR] to choose
menu 11.5 to edit the filter sets. See the Remote Node Filter
section for more details.
Prestige is idle (there is no traffic going to the remote node), before
the Prestige automatically disconnects the remote node. 0 means
that the session will not timeout.
and press [ENTER] to open
Yes
No
(default)
0
(default)
5.1.3 Outgoing Authentication Protocol
For obvious reasons, you should employ the strongest authentication protocol possible. However, some
vendors’ implementation includes specific authentication protocol in the user profile. It will disconnect if
the negotiated protocol is different from that in the user profile, even when the negotiated protocol is
stronger than specified. If the peer disconnects right after a successful authentication, make sure that you
specify the correct authentication protocol when connecting to such an implementation.
5.2 Remote Node Setup
For the TCP/IP parameters, perform the following steps to edit Menu 11.3 – Remote Node Network
Layer Options as shown next.
Step 1. In menu 11.1, make sure IP is among the protocols in the Route field.
Step 2. Move the cursor to the Edit IP/Bridge field, press [SPACE BAR] to select Yes, then press
[ENTER] to display Menu 11.3 – Remote Node Network Layer Options.
Remote Node Configuration 5-5
Page 80

Prestige 652 ADSL Security Router
Menu 11.3 - Remote Node Network Layer Options
IP Options: Bridge Options:
IP Address Assignment= Static Ethernet Addr Timeout(min)= 0
Rem IP Addr: 0.0.0.0
Rem Subnet Mask= 0.0.0.0
My WAN Addr= 0.0.0.0
NAT= SUA Only
Address Mapping Set=2
Metric= 2
Private= No
RIP Direction= None
Version= RIP-1
Multicast= None
IP Policies= 3,4,5,6
Press ENTER to Confirm or ESC to Cancel:
Figure 5-3 Remote Node Network Layer Options
The next table explains fields in Menu 11.3
Remote Node Network Layer Options.
–
Table 5-2 Remote Node Network Layer Options
FIELD DESCRIPTION EXAMPLE
IP Address
Assignment
Press [SPACE BAR] and then [ENTER] to select
node is using a dynamically assigned IP address, or
Dynamic
a static (fixed) IP address. You will only be able to configure this in the
ISP node (also the one you configure in menu 4), all other nodes are
set to
Static
.
Rem IP Addr This is the IP address you entered in the previous menu.
Rem Subnet
Type the subnet mask assigned to the remote node.
Mask
My WAN Addr Some implementations, especially UNIX derivatives, require separate
IP network numbers for the WAN and LAN links and each end to have a
unique address within the WAN network number. In that case, type the
IP address assigned to the WAN port of your Prestige.
NOTE: Refers to local Prestige address, not the remote router address.
NAT
(Network
Address
Translation)
Address
Press [SPACE BAR] and then [ENTER] to select
have multiple public WAN IP addresses for your Prestige. Select
if you have just one public WAN IP address for your Prestige. The
Only
SMT uses Address Mapping Set 255 (menu 15.1 - see section 8.3.1).
Select
When
to disable NAT.
None
Full Feature
is selected in the
NAT
Full Feature
field, configure address
Static
if the remote
if it is using
if you
SUA
Static
SUA
Only
2
5-6 Remote Node Configuration
Page 81

Prestige 652 ADSL Security Router
FIELD DESCRIPTION EXAMPLE
Mapping Set mapping sets in menu 15.1. Select one of the NAT server sets (2-10) in
menu 15.2 (see the NAT chapter for details) and type that number here.
When
SUA Only
set 1 in menu 15.2 (see the NAT chapter for details).
Metric The metric represents the “cost” of transmission for routing purposes.
IP routing uses hop count as the cost measurement, with a minimum of
1 for directly connected networks. Type a number that approximates the
cost for this link. The number need not be precise, but it must be
between 1 and 15. In practice, 2 or 3 is usually a good number.
Private This determines if the Prestige will include the route to this remote node
in its RIP broadcasts. If set to
included in RIP broadcast. If No, the route to this remote node will be
propagated to other hosts through RIP broadcasts.
RIP Direction Press [SPACE BAR] and then [ENTER] to select the RIP Direction.
Options are
Version Press [SPACE BAR] and then [ENTER] to select the RIP version.
Options are
Multicast
IP Policies You can apply up to four IP Policy sets (from 12) by typing in their
When you have completed this menu, press [ENTER] at the prompt “Press [ENTER] to confirm or [ESC]
to cancel” to save your configuration or press [ESC] to cancel and go back to the previous screen.
IGMP-v1
disables IGMP.
None
numbers separated by commas. Configure the filter sets in menu 25
first (see the IP Policy Routing chapter) and then apply them here.
is selected in the NAT field, the SMT uses NAT server
, this route is kept private and not
Yes
Both, In Only, Out Only
RIP-1, RIP-2B or RIP-2M
sets IGMP to version 1,
or
.
IGMP-v2
.
None
sets IGMP to version 2 and
2
No
None
RIP-1
None
3, 4, 5, 6
5.3 Remote Node Filter
Move the cursor to the Edit Filter Sets field in menu 11.1, then press [SPACE BAR] to select Yes. Press
[ENTER] to display Menu 11.5 – Remote Node Filter.
Use Menu 11.5 – Remote Node Filter to specify the filter set(s) to apply to the incoming and outgoing
traffic between this remote node and the Prestige and also to prevent certain packets from triggering calls.
You can specify up to 4 filter sets separated by comma, for example, 1, 5, 9, 12, in each filter field.
Note that spaces are accepted in this field. The Prestige has a prepackaged filter set, NetBIOS_WAN, that
blocks NetBIOS packets. Include this in the call filter sets (call protocol filter = 1) when using PPPoE if you
want to prevent NetBIOS packets from triggering calls to a remote node.
Remote Node Configuration 5-7
Page 82

Prestige 652 ADSL Security Router
Input Filter Sets:
protocol filters=
device filters=
Output Filter Sets:
protocol filters=
device filters=
Enter here to CONFIRM or ESC to CANCEL:
Figure 5-4 Menu 11.5 — Remote Node Filter
Menu 11.5 - Remote Node Filter
Menu 11.5 - Remote Node Filter
Input Filter Sets:
protocol filters=
Device filters=
Output Filter Sets:
protocol filters=
device filters=
Call Filter Sets:
protocol filters=
Device filters=
Enter here to CONFIRM or ESC to CANCEL:
Figure 5-5 Menu 11.5 — Remote Node Filter (PPPoE or PPP Encapsulation)
5-8 Remote Node Configuration
Page 83

Prestige 652 ADSL Security Router
p
Chapter 6
Remote Node TCP/IP Configuration
This chapter shows a sample LAN-to-LAN application and how to configure TCP/IP remote node.
6.1 TCP/IP Configuration
The following sections describe how to configure the TCP/IP parameters of a remote node.
6.1.1 Editing TCP/IP Options
Follow the steps shown next to edit Menu 11.6 – Remote Node ATM Layer Options.
In menu 11.1, move the cursor to the Edit ATM Options field and then press [SPACE BAR] to select
Yes. Press [ENTER] to display Menu 11.6 – Remote Node ATM Layer Options.
There are two versions of menu 11.6 for the Prestige, depending on which encapsulation type you use and
whether you chose VC-based or LLC-based multiplexing in menu 11.1.
VC-based Multiplexing
For RFC-1483 or ENET ENCAP encapsulation with VC-based multiplexing, by prior agreement, a
protocol is assigned a specific virtual circuit, for example, VC1 will carry IP. Separate VPI and VCI
numbers must be specified for each protocol.
Menu 11.6 - Remote Node ATM Layer Options
VC Options for IP:
VPI #= 8
VCI #= 35
ATM QoS Type= UBR
Peak Cell Rate (PCR)= 0
Sustain Cell Rate (SCR)= 0
Maximum Burst Size (MBS)= 0
Press ENTER to Confirm or ESC to Cancel:
VPI/VCI (VC-Multiplexing)
VC Options for Bridge:
VPI #= 8
VCI #= 35
ATM QoS Type= 0
Peak Cell Rate (PCR)= 0
Sustain Cell Rate (SCR)= 0
Maximum Burst Size (MBR)= 0
Separate VPI and
VCI numbers
must be specified
for each
rotocol.
Figure 6-1 Menu 11.6 for RFC-1483 or ENET ENCAP with VC-based Multiplexing
Remote Node TCP/IP Configuration 6-1
Page 84

Prestige 652 ADSL Security Router
LLC-based Multiplexing or PPPoA or PPPoE Encapsulation
For LLC-based multiplexing or PPP or PPPoE encapsulation, one VC carries multiple protocols with
protocol identifying information being contained in each packet header.
Menu 11.6 - Remote Node ATM Layer Options
VPI/VCI (LLC-Multiplexing or PPP-Encapsulation)
VPI #= 8
VCI #= 35
ATM QoS Type= UBR
Peak Cell Rate (PCR)= 5400
Sustain Cell Rate (SCR)= 0
Maximum Burst Size (MBS)= 0
.
ENTER here to CONFIRM or ESC to CANCEL:
Only one set of
VPI and VCI
numbers needs to
be specified.
Figure 6-2 Menu 11.6 for LLC-based Multiplexing or PPPoA or PPPoE Encapsulation
In this case, only one set of VPI and VCI numbers need be specified for all protocols. The valid range for
the VPI is 0 to 255 and for the VCI is 32 to 65535 (1 to 31 is reserved for local management of ATM
traffic).
The following figure uses sample IP addresses to help you understand the field of My Wan Addr in menu
11.3. Refer to the previous figure LAN and WAN IPs for a brief review of what a WAN IP is. My WAN
Addr indicates the local Prestige WAN IP while Rem IP Addr indicates the peer WAN IP.
6-2 Remote Node TCP/IP Configuration
Page 85

Prestige 652 ADSL Security Router
Figure 6-3 Sample IP Addresses for a TCP/IP LAN-to-LAN Connection
To configure the TCP/IP parameters of a remote node, first configure fields in Menu 11.1 – Remote Node
Profile, as shown in the following table. For more details on the IP Option fields, refer to Internet Access.
Table 6-1 TCP/IP-Related Fields in Menu 11.1 — Remote Node Profile
FIELD DESCRIPTION EXAMPLE
Route
Edit
IP/Bridge
Make sure IP is among the protocols in the
Remote Node Profile
Press [SPACE BAR] to select
.
and press [ENTER] to display menu.
Yes
Route
field in
Menu 11.1 –
IP
Yes
Remote Node TCP/IP Configuration 6-3
Page 86

Prestige 652 ADSL Security Router
Menu 11.3 - Remote Node Network Layer Options
IP Options: Bridge Options:
IP Address Assignment= Static Ethernet Addr Timeout (min)= 0
Rem IP Addr: 0.0.0.0
Rem Subnet Mask= 0.0.0.0
My WAN Addr= 0.0.0.0
NAT= Full Feature
Address Mapping Set=2
Metric= 2
Private= No
RIP Direction= Both
Version= RIP-2B
Multicast= IGMP-v2
IP Policies=
Press ENTER to Confirm or ESC to Cancel:
Figure 6-4 Remote Node Network Layer Options
The following table shows the fields in Menu 11.3 – Remote Node Network Layer Options.
Table 6-2 TCP/IP Remote Node Configuration
FIELD DESCRIPTION EXAMPLE
IP Address
Assignment
Press [SPACE BAR] and then [ENTER] to select
node is using a dynamically assigned IP address or
Dynamic
static (fixed) IP address. You will only be able to configure this in the
ISP node (the first node); all other nodes are set to
Rem IP Addr
This is the IP address of the remote gateway. Type the remote
Prestige’s WAN IP address here (172.16.02 in the example Figure 6-3
shown previously). If the remote Prestige’s WAN IP address is 0.0.0.0,
then type 192.168.1.1 (its LAN IP address) here.
Rem Subnet
Type the subnet mask assigned to the remote node. 0.0.0.0
Mask
My WAN Addr Some implementations, especially UNIX derivatives, require separate
IP network numbers for the WAN and LAN links and each end to have a
unique address within the WAN network number. In that case, type the
IP address assigned to the WAN port of your Prestige.
NOTE: Refers to local Prestige address, not the remote router address.
NAT
Press [SPACE BAR] and then [ENTER] to select
Full Feature
have multiple public WAN IP addresses for your Prestige.
Static
Static
if the remote
if it is using a
.
if you
Static
0.0.0.0
(default)
(default)
Full
Feature
6-4 Remote Node TCP/IP Configuration
Page 87

Prestige 652 ADSL Security Router
FIELD DESCRIPTION EXAMPLE
(Network
Address
Translation)
Select
SUA Only
Prestige. The SMT uses Address Mapping Set 255 (menu 15.1 - see
section 8.3.1).
Select
None
if you have just one public WAN IP address for your
to disable NAT.
When
Address
Mapping Set
Metric The metric represents the “cost” of transmission for routing purposes.
Private This determines if the Prestige will include the route to this remote node
RIP Direction Press [SPACE BAR] and then [ENTER] to select the RIP Direction.
Version Press [SPACE BAR] and then [ENTER] to select the RIP version.
Multicast
IP Policies You can apply up to four IP Policy sets (from 12) by typing in their
When you have completed this menu, press [ENTER] at the prompt “Press [ENTER] to confirm or [ESC]
to cancel” to save your configuration or press [ESC] to cancel and go back to the previous screen.
Full Feature
mapping sets in menu 15.1. Select one of the NAT server sets (2-10) in
menu 15.2 (see the NAT chapter for details) and type that number here.
When
SUA Only
set 1 in menu 15.2 (see the NAT chapter for details).
IP routing uses hop count as the cost measurement, with a minimum of
1 for directly connected networks. Type a number that approximates the
cost for this link. The number need not be precise, but it must be
between 1 and 15. In practice, 2 or 3 is usually a good number.
in its RIP broadcasts. If set to
included in RIP broadcast. If No, the route to this remote node will be
propagated to other hosts through RIP broadcasts.
Options are
Options are
IGMP-v1
None
numbers separated by commas.
sets IGMP to version 1,
disables IGMP.
is selected in the
is selected in the NAT field, the SMT uses NAT server
, this route is kept private and not
Yes
Both, In Only, Out Only
RIP-1, RIP-2B
or
RIP-2M
IGMP-v2
field, configure address
NAT
or
.
.
None
sets IGMP to version 2 and
2
2
Yes
Both
RIP-2B
IGMP-v2
3, 4, 5, 6
6.1.2 IP Static Route Setup
Static routes tell the Prestige routing information that it cannot learn automatically through other means.
This can arise in cases where RIP is disabled on the LAN or a remote network is beyond the one that is
directly connected to a remote node.
Each remote node specifies only the network to which the gateway is directly connected and the Prestige
has no knowledge of the networks beyond. For instance, the Prestige knows about network N2 in the
following figure through remote node Router 1. However, the Prestige is unable to route a packet to
Remote Node TCP/IP Configuration 6-5
Page 88

Prestige 652 ADSL Security Router
network N3 because it does not know that there is a route through remote node Router 1 (via Router 2). The
static routes allow you to tell the Prestige about the networks beyond the remote nodes.
Figure 6-5 Sample Static Routing Topology
Configuration
Step 1. To configure an IP static route, use Menu 12 – Static Route Setup (shown next).
6-6 Remote Node TCP/IP Configuration
Page 89

Prestige 652 ADSL Security Router
Menu 12 - Static Route Setup
1. IP Static Route
3. Bridge Static Route
Please enter selection:
Figure 6-6 Menu 12 — Static Route Setup
Step 2. From menu 12, select 1 to open Menu 12.1 — IP Static Route Setup (shown next).
Menu 12.1 - IP Static Route Setup
1. ________
2. ________
3. ________
4. ________
5. ________
6. ________
7. ________
8. ________
Enter selection number:
Figure 6-7 Menu 12.1 — IP Static Route Setup
Step 3. Now, type the route number of a static route you want to configure.
Menu 12.1.1 - Edit IP Static Route
Route #: 1
Route Name= ?
Active= No
Destination IP Address= ?
IP Subnet Mask= ?
Gateway IP Address= ?
Metric= 2
Private= No
Press ENTER to Confirm or ESC to Cancel:
Figure 6-8 Edit IP Static Route
Remote Node TCP/IP Configuration 6-7
Page 90

Prestige 652 ADSL Security Router
The following table describes the fields for Menu 12.1.1 – Edit IP Static Route Setup.
Table 6-3 Edit IP Static Route Menu Fields
FIELD DESCRIPTION
Route # This is the index number of the static route that you chose in menu 12.1.
Route Name Type a descriptive name for this route. This is for identification purpose only.
Active This field allows you to activate/deactivate this static route.
Destination IP Address This parameter specifies the IP network address of the final destination.
Routing is always based on network number. If you need to specify a route to
a single host, use a subnet mask of 255.255.255.255 in the subnet mask field
to force the network number to be identical to the host ID.
IP Subnet Mask Type the subnet mask for this destination. Follow the discussion on IP Subnet
Mask in this manual.
Gateway IP Address Type the IP address of the gateway. The gateway is an immediate neighbor of
your Prestige that will forward the packet to the destination. On the LAN, the
gateway must be a router on the same segment as your Prestige; over WAN,
the gateway must be the IP address of one of the remote nodes.
Metric Metric represents the “cost” of transmission for routing purposes. IP routing
uses hop count as the measurement of cost, with a minimum of 1 for directly
connected networks. Type a number that approximates the cost for this link.
The number need not be precise, but it must be between 1 and 15. In practice,
2 or 3 is usually a good number.
Private This parameter determines if the Prestige will include the route to this remote
node in its RIP broadcasts. If set to
included in RIP broadcasts. If No, the route to this remote node will be
propagated to other hosts through RIP broadcasts.
When you have completed this menu, press [ENTER] at the prompt “Press [ENTER] to confirm or [ESC]
to cancel” to save your configuration or press [ESC] to cancel and go back to the previous screen.
, this route is kept private and is not
Yes
6-8 Remote Node TCP/IP Configuration
Page 91

Prestige 652 ADSL Security Router
Chapter 7
Bridging Setup
This chapter shows you how to configure the bridging parameters of your Prestige.
7.1 Bridging in General
Bridging bases the forwarding decision on the MAC (Media Access Control), or hardware address, while
routing does it on the network layer (IP) address. Bridging allows the Prestige to transport packets of
network layer protocols that it does not route, for example, SNA, from one network to another. The caveat
is that, compared to routing, bridging generates more traffic for the same network layer protocol and it also
demands more CPU cycles and memory.
For efficiency reasons, do not turn on bridging unless you need to support protocols other than IP on your
network. For IP, enable the routing if you need it; do not bridge what the Prestige can route.
7.2 Bridge Ethernet Setup
Basically, all non-local packets are bridged to the WAN. Your Prestige does not support IPX.
7.2.1 Remote Node Bridging Setup
Follow the procedure in another section to configure the protocol-independent parameters in Menu 11.1 –
Remote Node Profile. For bridging-related parameters, you need to configure Menu 11.3 – Remote Node
Network Layer Options.
To setup Menu 11.3 – Remote Node Network Layer Options shown in the next figure, follow these steps:
Step 1. In menu 11.1, make sure the Bridge field is set to Yes.
Step 2. Move the cursor to the Edit IP/Bridge field, then press [SPACE BAR] to set the value to Yes
and press [ENTER] to edit Menu 11.3 – Remote Node Network Layer Options.
Bridging Setup 7-1
Page 92

Prestige 652 ADSL Security Router
Menu 11.3 - Remote Node Network Layer Options
IP Options: Bridge Options:
IP Address Assignment= Static Ethernet Addr Timeout (min)= 0
Rem IP Addr: 0.0.0.0
Rem Subnet Mask= 0.0.0.0
My WAN Addr= 0.0.0.0
NAT= Full Feature
Address Mapping Set=2
Metric= 2
Private= No
RIP Direction= Both
Version= RIP-2B
Multicast= IGMP-v2
IP Policies=
Press ENTER to Confirm or ESC to Cancel:
Figure 7-1 Menu 11.3 — Remote Node Bridging Options
Table 7-1 Remote Node Bridge Options
FIELD DESCRIPTION
Bridge (menu 11.1)
Edit IP/Bridge (menu
Make sure this field is set to
Press [SPACE BAR] to select
11.1)
Ethernet Addr Timeout
(min.) (menu 11.3)
Type the time (in minutes) for the Prestige to retain the Ethernet Address
information in its internal tables while the line is down. If this information is
retained, your Prestige will not have to recompile the tables when the line
comes back up.
When you have completed this menu, press [ENTER] at the prompt “Press [ENTER] to confirm or [ESC]
to cancel” to save your configuration or press [ESC] to cancel and go back to the previous screen.
.
Yes
and press [ENTER] to display menu 11.3.
Yes
7.2.2 Bridge Static Route Setup
Similar to network layer static routes, a bridging static route tells the Prestige the route to a node before a
connection is established. You configure bridge static routes in menu 12.3.1 (go to menu 12, choose option
3, then choose a static route to edit) as shown next.
7-2 Bridging Setup
Page 93

Prestige 652 ADSL Security Router
Menu 12.3.1 - Edit Bridge Static Route
Route #: 1
Route Name=
Active= No
Ether Address= ?
IP Address=
Gateway Node= 1
Press ENTER to Confirm or ESC to Cancel:
Figure 7-2 Menu 12.3.1 — Edit Bridge Static Route
The following table describes the Edit Bridge Static Route menu.
Table 7-2 Edit Bridge Static Route Menu Fields
FIELD DESCRIPTION
Route #
This is the route index number you typed in
Route Name Type a name for the bridge static route for identification purposes.
Active
Indicates whether the static route is active (
Ether Address Type the MAC address of the destination computer that you want to bridge the
packets to.
IP Address If available, type the IP address of the destination computer that you want to bridge
the packets to.
Gateway Node Press [SPACE BAR] and then [ENTER] to select the number of the remote node (one
to eight) that is the gateway of this static route.
When you have completed this menu, press [ENTER] at the prompt “Press [ENTER] to confirm or [ESC]
to cancel” to save your configuration or press [ESC] to cancel and go back to the previous screen.
Menu 12.3 – Bridge Static Route Setup
) or not (No).
Yes
.
Bridging Setup 7-3
Page 94

Page 95

Prestige 652 ADSL Security Router
Chapter 8
Network Address Translation (NAT)
This chapter discusses how to configure NAT on the Prestige.
8.1 Introduction
NAT (Network Address Translation - NAT, RFC 1631) is the translation of the IP address of a host in a
packet, for example, the source address of an outgoing packet, used within one network to a different IP
address known within another network.
8.1.1 NAT Definitions
Inside/outside denotes where a host is located relative to the Prestige, for example, the computers of your
subscribers are the inside hosts, while the web servers on the Internet are the outside hosts.
Global/local denotes the IP address of a host in a packet as the packet traverses a router, for example, the
local address refers to the IP address of a host when the packet is in the local network, while the global
address refers to the IP address of the host when the same packet is travelling in the WAN side.
Note that inside/outside refers to the location of a host, while global/local refers to the IP address of a host
used in a packet. Thus, an inside local address (ILA) is the IP address of an inside host in a packet when
the packet is still in the local network, while an inside global address (IGA) is the IP address of the same
inside host when the packet is on the WAN side. The following table summarizes this information.
Table 8-1 NAT Definitions
TERM DESCRIPTION
Inside This refers to the host on the LAN.
Outside This refers to the host on the WAN.
Local This refers to the packet address (source or destination) as the packet travels on the LAN.
Global This refers to the packet address (source or destination) as the packet travels on the WAN.
NAT 8-1
Page 96

Prestige 652 ADSL Security Router
NAT never changes the IP address (either local or global) of an outside host.
8.1.2 What NAT Does
In the simplest form, NAT changes the source IP address in a packet received from a subscriber (the inside
local address) to another (the inside global address) before forwarding the packet to the WAN side. When
the response comes back, NAT translates the destination address (the inside global address) back to the
inside local address before forwarding it to the original inside host. Note that the IP address (either local or
global) of an outside host is never changed.
The global IP addresses for the inside hosts can be either static or dynamically assigned by the ISP. In
addition, you can designate servers, for example, a web server and a telnet server, on your local network
and make them accessible to the outside world. If you do not define any servers (for Many-to-One and
Many-to-Many Overload mapping – see Table 8-2), NAT offers the additional benefit of firewall
protection. With no servers defined, your Prestige filters out all incoming inquiries, thus preventing
intruders from probing your network. For more information on IP address translation, refer to RFC 1631,
The IP Network Address Translator (NAT).
8.1.3 How NAT Works
Each packet has two addresses – a source address and a destination address. For outgoing packets, the ILA
(Inside Local Address) is the source address on the LAN, and the IGA (Inside Global Address) is the source
address on the WAN. For incoming packets, the ILA is the destination address on the LAN, and the IGA is
the destination address on the WAN. NAT maps private (local) IP addresses to globally unique ones
required for communication with hosts on other networks. It replaces the original IP source address (and
TCP or UDP source port numbers for Many-to-One and Many-to-Many Overload NAT mapping) in each
packet and then forwards it to the Internet. The Prestige keeps track of the original addresses and port
numbers so incoming reply packets can have their original values restored. The following figure illustrates
this.
8-2 NAT
Page 97

8.1.4 NAT Application
Prestige 652 ADSL Security Router
Figure 8-1 How NAT Works
The following figure illustrates a possible NAT application, where three inside LANs (logical LANs using
IP Alias) behind the Prestige can communicate with three distinct WAN networks. More examples follow at
the end of this chapter.
NAT 8-3
Page 98

Prestige 652 ADSL Security Router
Figure 8-2 NAT Application With IP Alias
8.1.5 NAT Mapping Types
NAT supports five types of IP/port mapping. They are:
1. One to One: In One-to-One mode, the Prestige maps one local IP address to one global IP address.
2. Many to One: In Many-to-One mode, the Prestige maps multiple local IP addresses to one global IP
address. This is equivalent to SUA (for instance, PAT, port address translation), ZyXEL’s Single User
Account feature that previous ZyXEL routers supported (the SUA Only option in today’s routers).
3. Many to Many Overload: In Many-to-Many Overload mode, the Prestige maps the multiple local IP
addresses to shared global IP addresses.
4. Many-to-Many No Overload: In Many-to-Many No Overload mode, the Prestige maps each local IP
address to a unique global IP address.
5. Server: This type allows you to specify inside servers of different services behind the NAT to be
accessible to the outside world.
8-4 NAT
Page 99

Prestige 652 ADSL Security Router
Port numbers do not change for One-to-One and Many-to-Many No Overload NAT
mapping types.
The following table summarizes these types.
Table 8-2 NAT Mapping Types
TYPE IP MAPPING SMT ABBREVIATION
One-to-One ILA1ÅÆ IGA1 1:1
Many-to-One (SUA/PAT) ILA1ÅÆ IGA1
ILA2ÅÆ IGA1
…
Many-to-Many Overload ILA1ÅÆ IGA1
ILA2ÅÆ IGA2
ILA3ÅÆ IGA1
ILA4ÅÆ IGA2
…
Many-to-Many No Overload ILA1ÅÆ IGA1
ILA2ÅÆ IGA2
ILA3ÅÆ IGA3
…
Server Server 1 IPÅÆ IGA1
Server 2 IPÅÆ IGA1
Server 3 IPÅÆ IGA1
M:1
M:M Ov
M:M No OV
Server
8.2 Using NAT
In addition to setting up SUA/NAT, you must create a firewall rule to allow traffic
from the WAN to be forwarded through the Prestige.
8.2.1 SUA (Single User Account) Versus NAT
SUA (Single User Account) is a ZyNOS implementation of a subset of NAT that supports two types of
mapping, Many-to-One and Server. See section 8.3.1 for a detailed description of the NAT set for SUA.
NAT 8-5
Page 100

Prestige 652 ADSL Security Router
The Prestige also supports Full Feature NAT to map multiple global IP addresses to multiple private LAN
IP addresses of clients or servers using mapping types as outlined in Table 8-2.
1. Choose SUA Only if you have just one public WAN IP address for your Prestige.
2. Choose Full Feature if you have multiple public WAN IP addresses for your Prestige.
8.2.2 Applying NAT
You apply NAT via menus 4 or 11.3 as displayed next. The next figure shows you how to apply NAT for
Internet access in menu 4. Enter 4 from the main menu to go to Menu 4 - Internet Access Setup.
Menu 4 - Internet Access Setup
ISP's Name= ChangeMe
Encapsulation= RFC-1483
Multiplexing= LLC-based
VPI #= 0
VCI #= 35
ATM QoS Type= CBR
Peak Cell Rate (PCR)= 0
Sustain Cell Rate (SCR)= 0
Maximum Burst Size (MBS)= 0
My Login= N/A
My Password= N/A
ENET ENCAP Gateway= N/A
IP Address Assignment= Static
IP Address= 0.0.0.0
Network Address Translation= SUA Only
Address Mapping Set= N/A
Figure 8-3 Menu 4 — Applying NAT for Internet Access
The following figure shows how you apply NAT to the remote node in menu 11.1.
Step 1. Enter 11 from the main menu.
Step 2. Move the cursor to the Edit IP field, press [SPACE BAR] to select Yes and then press
[ENTER] to bring up Menu 11.3 - Remote Node Network Layer Options.
8-6 NAT
 Loading...
Loading...