
WLAN 802.11G USB ADAPTER
User’s Guide
Version: 1.0 — Sep 2004

Copyright Statement
No part of this publication may be reproduced, stored in a retrieval system, or
transmitted in any form or by any means, whether electronic, mechanical,
photocopying, recording or otherwise without the prior writing of the publisher.
Windows™ 2000/XP are trademarks of Microsoft® Corp.
Atheros is a registered trademark of Atheros Communications, Inc.
All copyright reserved.
1

Regulatory Information
Federal Communication Commission Interference Statement
This equipment has been tested and found to comply with the limits for a Class B digital device,
pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable
protection against harmful interference in a residential installation. This equipment generates,
uses and can radiate radio frequency energy and, if not installed and used in accordance with
the instructions, may cause harmful interference to radio communications. However, there is
no guarantee that interference will not occur in a particular installation. If this equipment does
cause harmful interference to radio or television reception, which can be determined by turning
the equipment off and on, the user is encouraged to try to correct the interference by one of the
following measures:
- Reorient or relocate the receiving antenna.
- Increase the separation between the equipment and receiver.
- Connect the equipment into an outlet on a circuit different from that
to which the receiver is connected.
- Consult the dealer or an experienced radio/TV technician for help.
This device complies with Part 15 of the FCC Rules. Operation is subject to the following two
conditions: (1) This device may not cause harmful interference, and (2) this device must
accept any interference received, including interference that may cause undesired operation.
FCC Caution: Any changes or modifications not expressly approved by the party responsible
for compliance could void the user's authority to operate this equipment.
IMPORTANT NOTE: FCC Radiation Exposure Statement:
This equipment complies with FCC radiation exposure limits set forth for an uncontrolled
environment. End users must follow the specific operating instructions for satisfying RF
exposure compliance. To maintain compliance with FCC RF exposure compliance
requirements, please avoid direct contact to the transmitting antenna during transmitting.
This transmitter must not be co-located or operating in conjunction with any other antenna or
transmitter.
We declare that the product is limited in CH1~CH11 by specified firmware controlled in the
USA
2

Table of Contents
REGULATORY INFORMATION.............................................................................................................2
1. WELCOME...............................................................................................................................................5
1.1 KIT CONTENTS......................................................................................................................................5
1.2 MAIN FEATURES OF 802.11G USB 2.0 ADAPTER................................................................................5
1.3 WIRELESS NETWORKING SCENARIOS..................................................................................................6
2. QUICK START TO WIRELESS NETWORKING............................................................................8
2.1 INSTALLATION.......................................................................................................................................8
2.2 CONNECTING TO AN EXISTING NETWORK...........................................................................................9
3. STEP-BY-STEP INSTRUCTIONS......................................................................................................10
3.1 INSTALLATION.....................................................................................................................................10
3.2 CONNECTING TO A NETWORK.............................................................................................................15
3.3 CREATING AN AD HOC NETWORK .....................................................................................................19
3.4 REMOVING YOUR 802.11G USB 2.0 ADAPTER..................................................................................21
3.5 UNINSTALLATION................................................................................................................................22
4. USING THE UTILITY..........................................................................................................................24
4.1 CURRENT STATUS ...............................................................................................................................24
4.2 DIAGNOSTICS ......................................................................................................................................25
4.3 PROFILE MANAGEMENT.....................................................................................................................28
4.3.1 Creating or Modifying a Configuration Profile......................................................................28
4.3.2 Removing a Profile....................................................................................................................32
4.3.3 Profile Auto Selection................................................................................................................32
4.3.4 Switching Profiles......................................................................................................................33
4.4 SECURITY............................................................................................................................................34
4.4.1 Using EAP-TLS Security...........................................................................................................34
4.4.2 Enabling EAP-TLS Security......................................................................................................34
4.4.3 Using EAP-TTLS Security.........................................................................................................34
4.4.4 Enabling EAP-TTLS Security...................................................................................................35
4.4.5 Using PEAP(EAP-GTC) Security.............................................................................................36
4.4.6 Enabling PEAP(EAP-GTC) Security.......................................................................................36
4.4.7 Using PEAP-MSCHAP V2 Security.........................................................................................37
4.4.8 Enabling PEAP- MSCHAP V2 Security...................................................................................37
4.4.9 Using LEAP Security.................................................................................................................38
4.4.10 Configuring LEAP...................................................................................................................39
3

4.4.11 Using WPA Passphrase Security.............................................................................................40
4.4.12 Using Pre-Shared Key (Static WEP) Security.......................................................................40
4.5 DISPLAY SETTINGS .............................................................................................................................41
4.6 ACTIONS TOOLS..................................................................................................................................42
4.7 ABOUT UTILITY VERSION ..................................................................................................................42
5. RIGHT CLICKING THE TRAY ICON .............................................................................................43
6. NETWORK APPLICATION................................................................................................................44
6.1 SURVEYING THE NETWORK NEIGHBORHOOD....................................................................................44
6.2 FILE SHARING.....................................................................................................................................45
6.3 USING THE SHARED FOLDER..............................................................................................................46
7. Product Specifications……………………………………………………………47
4

1. Welcome
Thank you for purchasing our 802.11g USB 2.0 Adapter, and welcome to Wireless
LAN— the easy way to wireless networking.
This user’s guide introduces to you the 802.11g USB 2.0 Adapter and describes the
most common configurations, which will help you connect to your network easily.
Please read this manual to get familiar with the IEEE802.11g Wireless LAN. This
manual contains detailed instructions in operation of this product. Please keep this
manual for future reference.
1.1 Kit Contents
n One 802.11g USB 2.0 Adapter
n One Software CD:
(1) Utility & Driver Installation Software
(2) User Manual PDF File
n Quick Start Guide
1.2 Main Features of 802.11g USB 2.0 Adapter
Status LED
n Off: Power Off.
n Blinking: The USB adapter is powered on but no wireless connection is made
yet.
n Steady Green: Wireless connection is linked.
802.11g USB 2.0 Adapter features
n High-speed wireless connection, up to 54 Mbps
n IEEE802.11g (DSSS) standard for 2.4 GHz Wireless LAN
n Plug-and-Play installation
n Solid design with an integrated antenna
n Full mobility and seamless cell-to-cell roaming
n Automatic scale back at per packet level
n Super GTM (up to 108 Mbps data rate) and eXtended Range (XR) Technology
802.11g USB 2.0 Adapter supports
n Automatic load balancing for optimized bandwidth
5
n Advanced power management
n Windows® 2000 and XP
1.3 Wireless Networking Scenarios
As our 802.11g USB 2.0 Adapter is interoperable and compatible with other IEEE
802.11g compliant products from other manufacturers, it offers you the most freedom
to establish your ideal wireless network. Therefore, after installing 802.11g USB 2.0
Adapter, you can connect your computer to:
n A Peer-to-Peer Workgroup of 802.11g compliant wireless devices.
n A LAN (Local Area Network) constructed by Access Point(s) or other 802.11g
compliant systems.
n Share your Internet access by using just one connection, share printers and other
peripheral devices, share data and image files between networked PCs, play
multi-player games, and use other network enabled sharing resources.
Peer-to-Peer Networking:
An Ad Hoc Network could be easily set up with some PCs and this 802.11g USB
2.0 Adapter or our other WLAN devices. Therefore, it is very suitable to build a
network for temporary use, such as for demonstration in exhibition, for new sales
point/branch use and alike.
6
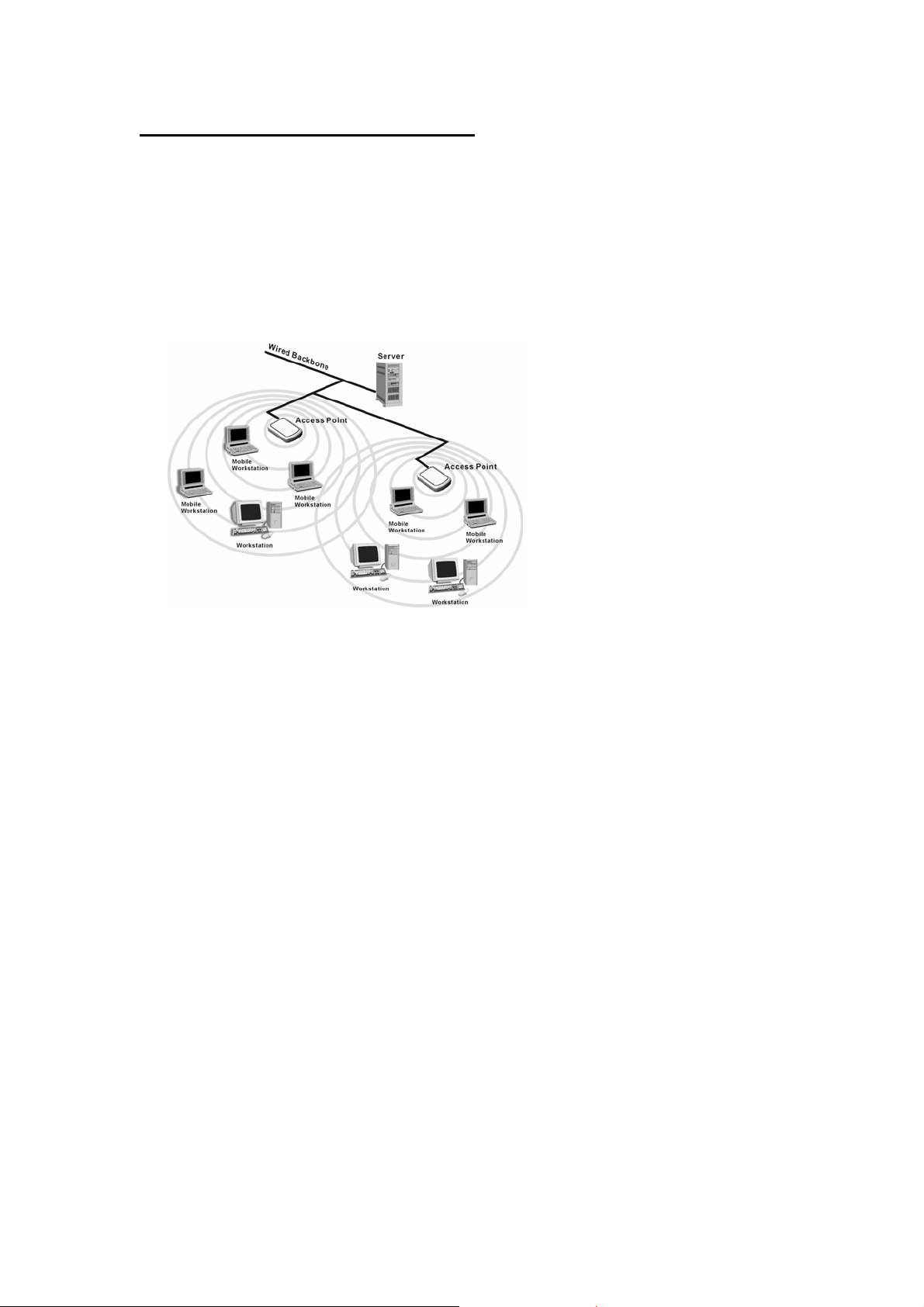
Cooperate LAN (Local Area Networking):
With some 802.11g USB 2.0 Adapters and Access Points, it is easy to construct a
LAN with access to Internet for enterprise use.
The construction is quite easy that the 802.11g USB 2.0 Adapter and Access Point
will automatically work at the most suitable frequency when Access Point is set
within the proper range.
In addition, commonly manufacturers will bundle the Site-Survey tool for users to
check the communication quality.
7
 Loading...
Loading...