Page 1
WatchGuard
®
Firebox
®
X Edge
User Guide
Firebox X Edge - Firmware Version 7.1
Page 2
Certifications and Notices
FCC Certification
This appliance has been tested and found to comply with limits
for a Class A digital appliance, pursuant to Part 15 of the FCC
Rules. Operation is subject to the following two conditions:
- This appliance may not cause harmful interference.
- This appliance must accept any interference received, including
interference that may cause undesired operation.
Changes or modifications not expressly approved by the party
responsible for compliance could void the user's authority to
operate the equipment.
This equipment has been tested and found to comply with the
limits for a Class A digital device, pursuant to Part 15 of the FCC
Rules. These limits are designed to provide reasonable
protection against harmful interference when the equipment is
operated in a commercial environment. This equipment
generates, uses, and can radiate radio frequency energy and, if
not installed and used in accordance with the instruction
manual, may cause harmful interference to radio
communications. Operation of this equipment in a residential
area is likely to cause harmful interference in which case the
user will be required to correct the interference at his own
expense.
CE Notice
The CE symbol on your WatchGuard Technologies equipment
indicates that it is in compliance with the Electromagnetic
Compatibility (EMC) directive and the Low Voltage Directive
(LVD) of the European Union (EU).
Industry Canada
This Class A digital apparatus meets all requirements of the
Canadian Interference-Causing Equipment Regulations.
Cet appareil numerique de la classe A respecte toutes les
exigences du Reglement sur le materiel broulleur du Canada.
ii WatchGuard Firebox X Edge
Page 3
Certifications and Notices
CANADA RSS-210
The term “IC:” before the radio certification number only
signifies that Industry of Canada technical specifications were
met.
Operation is subject to the following two conditions: (1) this
device may not cause interference, and (2) this device must
accept any interference, including interference that may cause
undesired operation of the device.
VCCI Notice Class A ITE
User Guide iii
Page 4
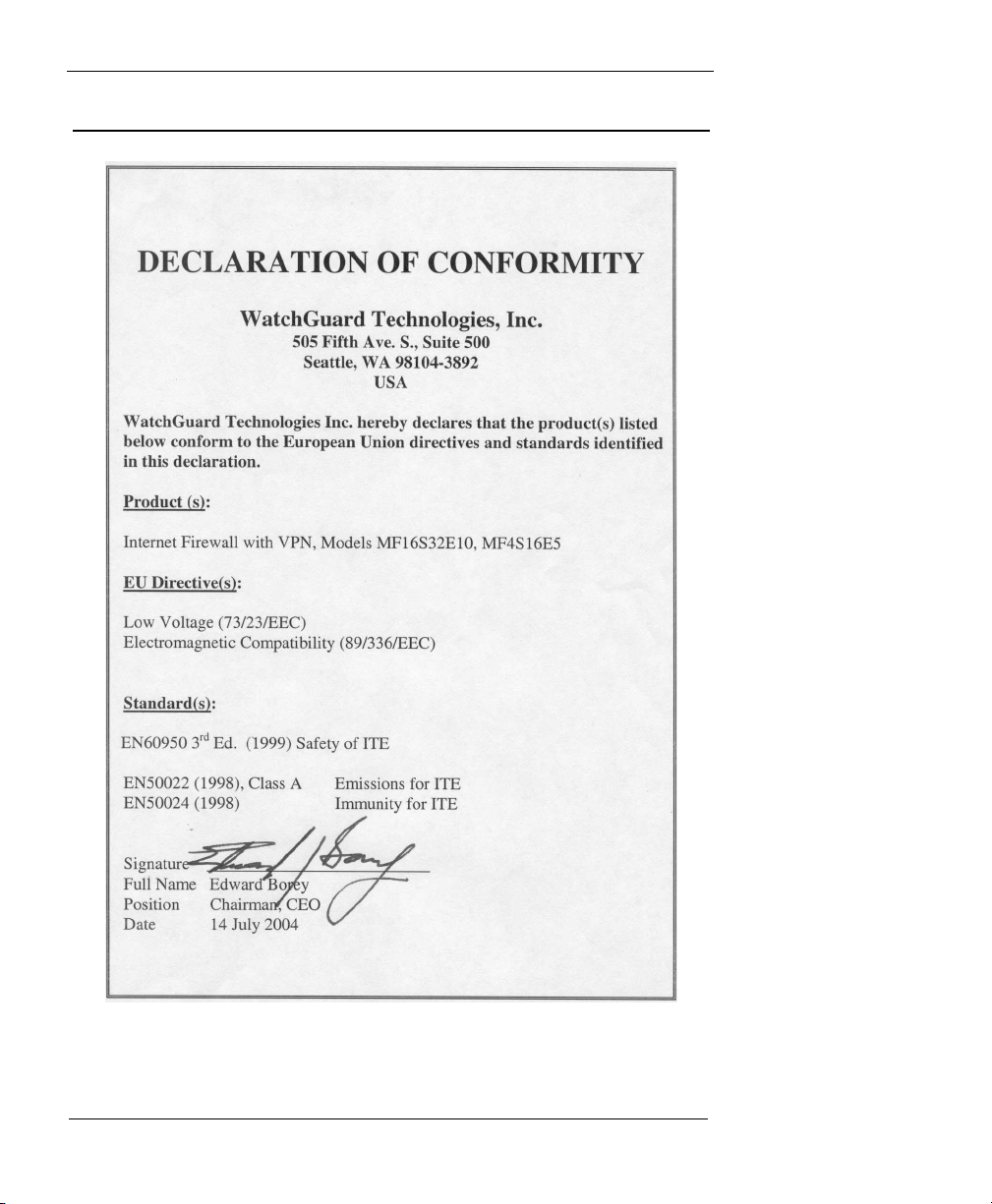
Declaration of Conformity
iv WatchGuard Firebox X Edge
Page 5
Notice to Users
Notice to Users
Information in this guide is subject to change without notice. Companies, names, and data used in
examples herein are fictitious unless otherwise noted. No part of this guide may be reproduced or
transmitted in any form or by any means, electronic or mechanical, for any purpose, without the express
written permission of WatchGuard Technologies, Inc.
WatchGuard Firebox Software
End-User License Agreement
IMPORTANT - READ CAREFULLY BEFORE ACCESSING WATCHGUARD SOFTWARE:
This Firebox Software End-User License Agreement (“AGREEMENT”) is a legal agreement between you
(either an individual or a single entity) and WatchGuard Technologies, Inc. (“WATCHGUARD”) for the
WATCHGUARD Firebox software product, which includes computer software components (whether
installed separately on a computer workstation or on the WATCHGUARD hardware product or included on
the WATCHGUARD hardware product) and may include associated media, printed materials, and on-line or
electronic documentation, and any updates or modifications thereto, including those received through the
WatchGuard LiveSecurity Service (or its equivalent), (the “SOFTWARE PRODUCT”). WATCHGUARD is willing
to license the SOFTWARE PRODUCT to you only on the condition that you accept all of the terms contained
in this Agreement. Please read this Agreement carefully. By installing or using the SOFTWARE PRODUCT
you agree to be bound by the terms of this Agreement. If you do not agree to the terms of this
AGREEMENT, WATCHGUARD will not license the SOFTWARE PRODUCT to you, and you will not have any
rights in the SOFTWARE PRODUCT. In that case, promptly return the SOFTWARE PRODUCT, along with
proof of payment, to the authorized dealer from whom you obtained the SOFTWARE PRODUCT for a full
refund of the price you paid. The WATCHGUARD hardware product is subject to a separate agreement and
limited hardware warranty included with the WATCHGUARD hardware product packaging and/or in the
associated user documentation.
1. Ownership and License. The SOFTWARE PRODUCT is protected by copyright laws and international
copyright treaties, as well as other intellectual property laws and treaties. This is a license agreement and
NOT an agreement for sale. All title and copyrights in and to the SOFTWARE PRODUCT (including but not
limited to any images, photographs, animations, video, audio, music, text, and applets incorporated into
the SOFTWARE PRODUCT), the accompanying printed materials, and any copies of the SOFTWARE
PRODUCT are owned by WATCHGUARD or its licensors. Your rights to use the SOFTWARE PRODUCT are as
specified in this AGREEMENT, and WATCHGUARD retains all rights not expressly granted to you in this
AGREEMENT. Nothing in this AGREEMENT constitutes a waiver of our rights under U.S. copyright law or
any other law or treaty.
2. Permitted Uses. You are granted the following rights to the SOFTWARE PRODUCT:
(A) You may install and use the SOFTWARE PRODUCT on any single WATCHGUARD hardware product at
any single location and may install and use the SOFTWARE PRODUCT on multiple workstation computers.
(B) To use the SOFTWARE PRODUCT on more than one WATCHGUARD hardware product at once, you
must purchase an additional copy of the SOFTWARE PRODUCT for each additional WATCHGUARD
hardware product on which you want to use it. To the extent that you install copies of the SOFTWARE
PRODUCT on additional WATCHGUARD hardware products in accordance with the prior sentence without
installing the additional copies of the SOFTWARE PRODUCT included with such WATCHGUARD hardware
products, you agree that use of any software provided with or included on the additional WATCHGUARD
hardware products that does not require installation will be subject to the terms and conditions of this
AGREEMENT. You must also maintain a current subscription to the WatchGuard LiveSecurity Service (or its
equivalent) for each additional WATCHGUARD hardware product on which you will use a copy of an
updated or modified version of the SOFTWARE PRODUCT received through the WatchGuard LiveSecurity
Service (or its equivalent).
User Guide v
Page 6

(C) In addition to the copies described in Section 2(A), you may make a single copy of the SOFTWARE
PRODUCT for backup or archival purposes only.
3. Prohibited Uses. You may not, without express written permission from WATCHGUARD:
(A) Use, copy, modify, merge or transfer copies of the SOFTWARE PRODUCT or printed materials except
as provided in this AGREEMENT;
(B) Use any backup or archival copy of the SOFTWARE PRODUCT (or allow someone else to use such a
copy) for any purpose other than to replace the original copy in the event it is destroyed or becomes
defective;
(C) Sublicense, lend, lease or rent the SOFTWARE PRODUCT;
(D) Transfer this license to another party unless
(i) the transfer is permanent,
(ii) the third party recipient agrees to the terms of this AGREEMENT, and
(iii) you do not retain any copies of the SOFTWARE PRODUCT; or
(E) Reverse engineer, disassemble or decompile the SOFTWARE PRODUCT.
4. Limited Warranty. WATCHGUARD makes the following limited warranties for a period of ninety (90) days
from the date you obtained the SOFTWARE PRODUCT from WATCHGUARD or an authorized dealer:
(A) Media. The disks and documentation will be free from defects in materials and workmanship under
normal use. If the disks or documentation fail to conform to this warranty, you may, as your sole and
exclusive remedy, obtain a replacement free of charge if you return the defective disk or documentation to
WATCHGUARD with a dated proof of purchase.
(B) SOFTWARE PRODUCT. The SOFTWARE PRODUCT will materially conform to the documentation that
accompanies it. If the SOFTWARE PRODUCT fails to operate in accordance with this warranty, you may, as
your sole and exclusive remedy, return all of the SOFTWARE PRODUCT and the documentation to the
authorized dealer from whom you obtained it, along with a dated proof of purchase, specifying the
problems, and they will provide you with a new version of the SOFTWARE PRODUCT or a full refund, at their
election.
Disclaimer and Release. THE WARRANTIES, OBLIGATIONS AND LIABILITIES OF WATCHGUARD, AND YOUR
REMEDIES, SET FORTH IN PARAGRAPHS 4, 4(A) AND 4(B) ABOVE ARE EXCLUSIVE AND IN SUBSTITUTION
FOR, AND YOU HEREBY WAIVE, DISCLAIM AND RELEASE ANY AND ALL OTHER WARRANTIES, OBLIGATIONS
AND LIABILITIES OF WATCHGUARD AND ITS LICENSORS AND ALL OTHER RIGHTS, CLAIMS AND REMEDIES
YOU MAY HAVE AGAINST WATCHGUARD AND ITS LICENSORS, EXPRESS OR IMPLIED, ARISING BY LAW OR
OTHERWISE, WITH RESPECT TO ANY NONCONFORMANCE OR DEFECT IN THE SOFTWARE PRODUCT
(INCLUDING, BUT NOT LIMITED TO, ANY IMPLIED WARRANTY OF MERCHANTABILITY OR FITNESS FOR A
PARTICULAR PURPOSE, ANY IMPLIED WARRANTY ARISING FROM COURSE OF PERFORMANCE, COURSE OF
DEALING, OR USAGE OF TRADE, ANY WARRANTY OF NONINFRINGEMENT, ANY WARRANTY THAT THE
SOFTWARE PRODUCT WILL MEET YOUR REQUIREMENTS, ANY WARRANTY OF UNINTERRUPTED OR ERRORFREE OPERATION, ANY OBLIGATION, LIABILITY, RIGHT, CLAIM OR REMEDY IN TORT, WHETHER OR NOT
ARISING FROM THE NEGLIGENCE (WHETHER ACTIVE, PASSIVE OR IMPUTED) OR FAULT OF WATCHGUARD
AND ITS LICENSORS AND ANY OBLIGATION, LIABILITY, RIGHT, CLAIM OR REMEDY FOR LOSS OR DAMAGE TO,
OR CAUSED BY OR CONTRIBUTED TO BY, THE SOFTWARE PRODUCT).
Limitation of Liability. WATCHGUARD'S LIABILITY (WHETHER IN CONTRACT, TORT, OR OTHERWISE; AND
NOTWITHSTANDING ANY FAULT, NEGLIGENCE, STRICT LIABILITY OR PRODUCT LIABILITY) WITH REGARD TO
THE SOFTWARE PRODUCT WILL IN NO EVENT EXCEED THE PURCHASE PRICE PAID BY YOU FOR SUCH
PRODUCT. THIS SHALL BE TRUE EVEN IN THE EVENT OF THE FAILURE OF AN AGREED REMEDY. IN NO EVENT
WILL WATCHGUARD BE LIABLE TO YOU OR ANY THIRD PARTY, WHETHER ARISING IN CONTRACT
(INCLUDING WARRANTY), TORT (INCLUDING ACTIVE, PASSIVE OR IMPUTED NEGLIGENCE AND STRICT
LIABILITY AND FAULT), FOR ANY INDIRECT, SPECIAL, INCIDENTAL, OR CONSEQUENTIAL DAMAGES
(INCLUDING WITHOUT LIMITATION LOSS OF BUSINESS PROFITS, BUSINESS INTERRUPTION, OR LOSS OF
BUSINESS INFORMATION) ARISING OUT OF OR IN CONNECTION WITH THIS WARRANTY OR THE USE OF OR
vi WatchGuard Firebox X Edge
Page 7

Copyright, Trademark, and Patent Information
INABILITY TO USE THE SOFTWARE PRODUCT, EVEN IF WATCHGUARD HAS BEEN ADVISED OF THE
POSSIBILITY OF SUCH DAMAGES. THIS SHALL BE TRUE EVEN IN THE EVENT OF THE FAILURE OF AN AGREED
REMEDY.
5. United States Government Restricted Rights. The SOFTWARE PRODUCT is provided with Restricted
Rights. Use, duplication or disclosure by the U.S. Government or any agency or instrumentality thereof is
subject to restrictions as set forth in subdivision (c)(1)(ii) of the Rights in Technical Data and Computer
Software clause at DFARS 252.227-7013, or in subdivision (c)(1) and (2) of the Commercial Computer
Software -- Restricted Rights Clause at 48 C.F.R. 52.227-19, as applicable. Manufacturer is WatchGuard
Technologies, Inc., 505 5th Ave. South, Suite 500, Seattle, WA 98104.
6. Export Controls. You agree not to directly or indirectly transfer the SOFTWARE PRODUCT or
documentation to any country to which such transfer would be prohibited by the U.S. Export
Administration Act and the regulations issued thereunder.
7. Termination. This license and your right to use the SOFTWARE PRODUCT will automatically terminate if
you fail to comply with any provisions of this AGREEMENT, destroy all copies of the SOFTWARE PRODUCT
in your possession, or voluntarily return the SOFTWARE PRODUCT to WATCHGUARD. Upon termination
you will destroy all copies of the SOFTWARE PRODUCT and documentation remaining in your control or
possession.
8. Miscellaneous Provisions. This AGREEMENT will be governed by and construed in accordance with the
substantive laws of Washington excluding the 1980 United National Convention on Contracts for the
International Sale of Goods, as amended. This is the entire AGREEMENT between us relating to the
SOFTWARE PRODUCT, and supersedes any prior purchase order, communications, advertising or
representations concerning the SOFTWARE PRODUCT AND BY USING THE SOFTWARE PRODUCT YOU AGREE
TO THESE TERMS. IF THE SOFTWARE PRODUCT IS BEING USED BY AN ENTITY, THE INDIVIDUAL INDICATING
AGREEMENT TO THESE TERMS REPRESENTS AND WARRANTS THAT (A) SUCH INDIVIDUAL IS DULY
AUTHORIZED TO ACCEPT THIS AGREEMENT ON BEHALF OF THE ENTITY AND TO BIND THE ENTITY TO THE
TERMS OF THIS AGREEMENT; (B) THE ENTITY HAS THE FULL POWER, CORPORATE OR OTHERWISE, TO ENTER
INTO THIS AGREEMENT AND PERFORM ITS OBLIGATIONS UNDER THIS AGREEMENT AND; (C) THIS
AGREEMENT AND THE PERFORMANCE OF THE ENTITY’S OBLIGATIONS UNDER THIS AGREEMENT DO NOT
VIOLATE ANY THIRD-PARTY AGREEMENT TO WHICH THE ENTITY IS A PARTY. No change or modification of
this AGREEMENT will be valid unless it is in writing and is signed by WATCHGUARD.
Version: 040226
Copyright, Trademark, and Patent Information
Copyright© 1998 - 2004 WatchGuard Technologies, Inc. All rights reserved.
WatchGuard, the WatchGuard logo, Firebox, LiveSecurity, and any other mark listed as a trademark in the
“Terms of Use” portion of the WatchGuard Web site that is used herein are either registered trademarks or
trademarks of WatchGuard Technologies, Inc. and/or its subsidiaries in the United States and/or other
countries. All other trademarks are the property of their respective owners.
Printed in the United States of America.
© Hi/fn, Inc. 1993, including one or more U.S. Patents: 4701745, 5016009, 5126739, and 5146221 and other
patents pending.
Microsoft®, Internet Explorer®, Windows® 95, Windows® 98, Windows NT®, Windows® 2000 and Windows
XP are either registered trademarks or trademarks of Microsoft Corporation in the United States and/or
other countries.
Netscape and Netscape Navigator are registered trademarks of Netscape Communications Corporation in
the United States and other countries.
User Guide vii
Page 8

RealNetworks, RealAudio, and RealVideo are either a registered trademark or trademark of RealNetworks,
Inc. in the United States and/or other countries.
Java and all Java-based marks are trademarks or registered trademarks of Sun Microsystems, Inc. in the
United States and other countries. All right reserved.
© 1995-1998 Eric Young (eay@cryptsoft). All rights reserved.
© 1998-2003 The OpenSSL Project. All rights reserved. Redistribution and use in source and binary forms,
with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following
acknowledgment: "This product includes software developed by the OpenSSL Project for use in the
OpenSSL Toolkit. (http://www.openssl.org/)"
4. The names "OpenSSL Toolkit" and "OpenSSL Project" must not be used to endorse or promote products
derived from this software without prior written permission. For written permission, please contact
openssl-core@openssl.org.
5. Products derived from this software may not be called "OpenSSL" nor may "OpenSSL" appear in their
names without prior written permission of the OpenSSL Project.
6. Redistributions of any form whatsoever must retain the following acknowledgment: "This product
includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit (http://
www.openssl.org/)"
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT ``AS IS'' AND ANY EXPRESSED OR IMPLIED
WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND
FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR ITS
CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY
THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR
OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com). This product
includes software written by Tim Hudson (tjh@cryptsoft.com).
© 1995-2003 Eric Young (eay@cryptsoft.com)
All rights reserved.
This package is an SSL implementation written by Eric Young (eay@cryptsoft.com).
The implementation was written so as to conform with Netscapes’ SSL.
This library is free for commercial and non-commercial use as long as the following conditions are adhered
to. The following conditions apply to all code found in this distribution, be it the RC4, RSA, lhash, DES, etc.,
code; not just the SSL code. The SSL documentation included with this distribution is covered by the same
copyright terms except that the holder is Tim Hudson (tjh@cryptsoft.com).
Copyright remains Eric Young's, and as such any Copyright notices in the code are not to be removed. If
this package is used in a product, Eric Young should be given attribution as the author of the parts of the
library used. This can be in the form of a textual message at program startup or in documentation (online
or textual) provided with the package. Redistribution and use in source and binary forms, with or without
modification, are permitted provided that the following conditions are met:
viii WatchGuard Firebox X Edge
Page 9

Copyright, Trademark, and Patent Information
1. Redistributions of source code must retain the copyright notice, this list of conditions and the following
disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following
acknowledgement: "This product includes cryptographic software written by Eric Young
(eay@cryptsoft.com)" The word 'cryptographic' can be left out if the routines from the library being used
are not cryptographic related.
4. If you include any Windows specific code (or a derivative thereof) from the apps directory (application
code) you must include an acknowledgement: "This product includes software written by Tim Hudson
(tjh@cryptsoft.com)"
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG ``AS IS'' AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A
PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE
FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES
(INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE,
DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY,
WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN
ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The license and distribution terms for any publicly available version or derivative of this code cannot be
changed. i.e. this code cannot simply be copied and put under another distribution license [including the
GNU Public License.]
The mod_ssl package falls under the Open-Source Software label because it's distributed under a BSD-style
license. The detailed license information follows.
Copyright (c) 1998-2003 Ralf S. Engelschall. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided
that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following
acknowledgment:
This product includes software developed by Ralf S. Engelschall <rse@engelschall.com> for use in the
mod_ssl project (http://www.modssl.org/)."
4. The names "mod_ssl" must not be used to endorse or promote products derived from this software
without prior written permission. For written permission, please contact rse@engelschall.com.
5. Products derived from this software may not be called "mod_ssl" nor may "mod_ssl" appear in their
names without prior written permission of Ralf S. Engelschall.
6. Redistributions of any form whatsoever must retain the following acknowledgment: "This product
includes software developed by Ralf S. Engelschall <rse@engelschall.com> for use in the mod_ssl project
(http://www.modssl.org/)."
THIS SOFTWARE IS PROVIDED BY RALF S. ENGELSCHALL ``AS IS'' AND ANY EXPRESSED OR IMPLIED
WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND
FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL RALF S. ENGELSCHALL OR HIS
CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY
User Guide ix
Page 10

THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR
OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
POSSIBILITY OF SUCH DAMAGE.
The Apache Software License, Version 1.1
Copyright (c) 2000-2004 The Apache Software Foundation. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided
that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
3. The end-user documentation included with the redistribution, if any, must include the following
acknowledgment:
"This product includes software developed by the Apache Software Foundation (http://www.apache.org/)."
Alternately, this acknowledgment may appear in the software itself, if and wherever such third-party
acknowledgments normally appear.
4. The names "Apache" and "Apache Software Foundation" must not be used to endorse or promote
products derived from this software without prior written permission. For written permission, please
contact apache@apache.org.
5. Products derived from this software may not be called "Apache", nor may "Apache" appear in their name,
without prior written permission of the Apache Software Foundation.
THIS SOFTWARE IS PROVIDED ``AS IS'' AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT
NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE APACHE SOFTWARE FOUNDATION OR ITS
CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY
THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR
OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
POSSIBILITY OF SUCH DAMAGE.
This software consists of voluntary contributions made by many individuals on behalf of the Apache
Software Foundation. For more information on the Apache Software Foundation, please see <http://
www.apache.org/>.
Portions of this software are based upon public domain software originally written at the National Center
for Supercomputing Applications, University of Illinois, Urbana-Champaign.
PCRE LICENSE
------------
PCRE is a library of functions to support regular expressions whose syntax and semantics are as close as
possible to those of the Perl 5 language.
Written by: Philip Hazel <ph10@cam.ac.uk>
University of Cambridge Computing Service,
Cambridge, England. Phone: +44 1223 334714.
Copyright (c) 1997-2003 University of Cambridge
Permission is granted to anyone to use this software for any purpose on any computer system, and to
redistribute it freely, subject to the following restrictions:
x WatchGuard Firebox X Edge
Page 11

Copyright, Trademark, and Patent Information
1. This software is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without
even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
2. The origin of this software must not be misrepresented, either by explicit claim or by omission. In
practice, this means that if you use PCRE in software that you distribute to others, commercially or
otherwise, you must put a sentence like this:
Regular expression support is provided by the PCRE library package, which is open source software, written
by Philip Hazel, and copyright by the University of Cambridge, England.
somewhere reasonably visible in your documentation and in any relevant files or online help data or
similar. A reference to the ftp site for the source, that is, to:
ftp://ftp.csx.cam.ac.uk/pub/software/programming/pcre/
should also be given in the documentation. However, this condition is not intended to apply to whole
chains of software. If package A includes
PCRE, it must acknowledge it, but if package B is software that includes
package A, the condition is not imposed on package B (unless it uses
PCRE independently).
3. Altered versions must be plainly marked as such, and must not be misrepresented as being the original
software.
4. If PCRE is embedded in any software that is released under the GNU General Purpose License (GPL), or
Lesser General Purpose License (LGPL), then the terms of that license shall supersede any condition above
with which it is incompatible.
The documentation for PCRE, supplied in the "doc" directory, is distributed under the same terms as the
software itself.
PLEASE NOTE: Some components of the WatchGuard WFS software incorporate source code covered
under the GNU Lesser General Public License (LGPL). To obtain the source code covered under the LGPL,
please contact WatchGuard Technical Support at:
877.232.3531 in the United States and Canada
+1.360.482.1083 from all other countries
This source code is free to download. There is a $35 charge to ship the CD.
This product includes software covered by the LGPL.
GNU LESSER GENERAL PUBLIC LICENSE
Version 2.1, February 1999
Copyright (C) 1991, 1999 Free Software Foundation, Inc.59 Temple Place, Suite 330, Boston, MA 021111307 USA
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is
not allowed.
[This is the first released version of the Lesser GPL. It also counts as the successor of the GNU Library
Public License, version 2, hence the version number 2.1.]
Preamble
The licenses for most software are designed to take away your freedom to share and change it. By
contrast, the GNU General Public Licenses are intended to guarantee your freedom to share and change
free software--to make sure the software is free for all its users.
This license, the Lesser General Public License, applies to some specially designated software packages-typically libraries--of the Free Software Foundation and other authors who decide to use it. You can use it
User Guide xi
Page 12

too, but we suggest you first think carefully about whether this license or the ordinary General Public
License is the better strategy to use in any particular case, based on the explanations below.
When we speak of free software, we are referring to freedom of use, not price. Our General Public Licenses
are designed to make sure that you have the freedom to distribute copies of free software (and charge for
this service if you wish); that you receive source code or can get it if you want it; that you can change the
software and use pieces of
it in new free programs; and that you are informed that you can do these things.
To protect your rights, we need to make restrictions that forbid distributors to deny you these rights or to
ask you to surrender these rights. These restrictions translate to certain responsibilities for you if you
distribute copies of the library or if you modify it.
For example, if you distribute copies of the library, whether gratis or for a fee, you must give the recipients
all the rights that we gave you. You must make sure that they, too, receive or can get the source code. If
you link other code with the library, you must provide complete object files to the recipients, so that they
can relink them with the library after making changes to the library and recompiling it. And you must
show them these terms so they know their rights.
We protect your rights with a two-step method: (1) we copyright the library, and (2) we offer you this
license, which gives you legal permission to copy, distribute and/or modify the library.
To protect each distributor, we want to make it very clear that there is no warranty for the free library.
Also, if the library is modified by someone else and passed on, the recipients should know that what they
have is not the original version, so that the original author's reputation will not be affected by problems
that might be introduced by others.
Finally, software patents pose a constant threat to the existence of any free program. We wish to make
sure that a company cannot effectively restrict the users of a free program by obtaining a restrictive license
from a patent holder. Therefore, we insist that any patent license obtained for a version of the library must
be consistent with the full freedom of use specified in this license.
Most GNU software, including some libraries, is covered by the ordinary GNU General Public License. This
license, the GNU Lesser General Public License, applies to certain designated libraries, and is quite different
from the ordinary General Public License. We use this license for certain libraries in order to permit linking
those libraries into non-free programs.
When a program is linked with a library, whether statically or using a shared library, the combination of the
two is legally speaking a combined work, a derivative of the original library. The ordinary General Public
License therefore permits such linking only if the entire combination fits its criteria of freedom. The Lesser
General Public License permits more lax criteria for linking other code with the library.
We call this license the "Lesser" General Public License because it does Less to protect the user's freedom
than the ordinary General Public License. It also provides other free software developers Less of an
advantage over competing non-free programs. These disadvantages are the reason we use the ordinary
General Public License for many libraries. However, the Lesser license provides advantages in certain
special circumstances.
For example, on rare occasions, there may be a special need to encourage the widest possible use of a
certain library, so that it becomes a de-facto standard. To achieve this, non-free programs must be allowed
to use the library. A more frequent case is that a free library does the same job as widely used non-free
libraries. In this case, there is little to gain by limiting the free library to free software only, so we use the
Lesser General Public License.
In other cases, permission to use a particular library in non-free programs enables a greater number of
people to use a large body of free software. For example, permission to use the GNU C Library in non-free
programs enables many more people to use the whole GNU operating system, as well as its variant, the
GNU/Linux operating system.
Although the Lesser General Public License is Less protective of the users' freedom, it does ensure that the
user of a program that is linked with the Library has the freedom and the wherewithal to run that program
using a modified version of the Library.
xii WatchGuard Firebox X Edge
Page 13

Copyright, Trademark, and Patent Information
The precise terms and conditions for copying, distribution and modification follow. Pay close attention to
the difference between a "work based on the library" and a "work that uses the library". The former
contains code derived from the library, whereas the latter must be combined with the library in order to
run.
GNU LESSER GENERAL PUBLIC LICENSE
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
0. This License Agreement applies to any software library or other program which contains a notice placed
by the copyright holder or other authorized party saying it may be distributed under the terms of this
Lesser General Public License (also called "this License"). Each licensee is addressed as "you".
A "library" means a collection of software functions and/or data prepared so as to be conveniently linked
with application programs (which use some of those functions and data) to form executables.
The "Library", below, refers to any such software library or work which has been distributed under these
terms. A "work based on the Library" means either the Library or any derivative work under copyright law:
that is to say, a work containing the Library or a portion of it, either verbatim or with modifications and/or
translated straightforwardly into another language. (Hereinafter, translation is included without limitation
in the term "modification".)
"Source code" for a work means the preferred form of the work for making modifications to it. For a
library, complete source code means all the source code for all modules it contains, plus any associated
interface definition files, plus the scripts used to control compilation and installation of the library.
Activities other than copying, distribution and modification are not covered by this License; they are
outside its scope. The act of running a program using the Library is not restricted, and output from such a
program is covered only if its contents constitute a work based on the Library (independent of the use of
the Library in a tool for writing it). Whether that is true depends on what the Library does and what the
program that uses the Library does.
1. You may copy and distribute verbatim copies of the Library's complete source code as you receive it, in
any medium, provided that you conspicuously and appropriately publish on each copy an appropriate
copyright notice and disclaimer of warranty; keep intact all the notices that refer to this License and to the
absence of any warranty; and distribute a copy of this License along with the Library.
You may charge a fee for the physical act of transferring a copy, and you may at your option offer
warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Library or any portion of it, thus forming a work based on the
Library, and copy and distribute such modifications or work under the terms of Section 1 above, provided
that you also meet all of these conditions:
a) The modified work must itself be a software library.
b) You must cause the files modified to carry prominent notices stating that you changed the files and the
date of any change.
c) You must cause the whole of the work to be licensed at no charge to all third parties under the terms of
this License.
d) If a facility in the modified Library refers to a function or a table of data to be supplied by an application
program that uses the facility, other than as an argument passed when the facility is invoked, then you
must make a good faith effort to ensure that, in the event an application does not supply such function or
table, the facility still operates, and performs whatever part of its purpose remains meaningful.
(For example, a function in a library to compute square roots has a purpose that is entirely well-defined
independent of the application. Therefore, Subsection 2d requires that any application-supplied function
or table used by this function must be optional: if the application does not supply it, the square root
function must still compute square roots.)
These requirements apply to the modified work as a whole. If identifiable sections of that work are not
derived from the Library, and can be reasonably considered independent and separate works in themselves,
User Guide xiii
Page 14

then this License, and its terms, do not apply to those sections when you distribute them as separate works.
But when you distribute the same sections as part of a whole which is a work based on the Library, the
distribution of the whole must be on the terms of this License, whose permissions for other licensees
extend to the entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest your rights to work written entirely by
you; rather, the intent is to exercise the right to control the distribution of derivative or collective works
based on the Library.
In addition, mere aggregation of another work not based on the Library with the Library (or with a work
based on the Library) on a volume of a storage or distribution medium does not bring the other work under
the scope of this License.
3. You may opt to apply the terms of the ordinary GNU General Public License instead of this License to a
given copy of the Library. To do this, you must alter all the notices that refer to this License, so that they
refer to the ordinary GNU General Public License, version 2, instead of to this License. (If a newer version
than version 2 of the ordinary GNU General Public License has appeared, then you can specify that version
instead if you wish.) Do not make any other change in these notices.
Once this change is made in a given copy, it is irreversible for that copy, so the ordinary GNU General Public
License applies to all subsequent copies and derivative works made from that copy.
This option is useful when you wish to copy part of the code of the Library into a program that is not a
library.
4. You may copy and distribute the Library (or a portion or derivative of it, under Section 2) in object code
or executable form under the terms of Sections 1 and 2 above provided that you accompany it with the
complete corresponding machine-readable source code, which must be distributed under the terms of
Sections 1 and 2 above on a medium customarily used for software interchange.
If distribution of object code is made by offering access to copy from a designated place, then offering
equivalent access to copy the source code from the same place satisfies the requirement to distribute the
source code, even though third parties are not compelled to copy the source along with the object code.
5. A program that contains no derivative of any portion of the Library, but is designed to work with the
Library by being compiled or linked with it, is called a "work that uses the Library". Such a work, in
isolation, is not a derivative work of the Library, and therefore falls outside the scope of this License.
However, linking a "work that uses the Library" with the Library creates an executable that is a derivative of
the Library (because it contains portions of the Library), rather than a "work that uses the library". The
executable is therefore covered by this License. Section 6 states terms for distribution of such executables.
When a "work that uses the Library" uses material from a header file that is part of the Library, the object
code for the work may be a derivative work of the Library even though the source code is not. Whether this
is true is especially significant if the work can be linked without the Library, or if the work is itself a library.
The threshold for this to be true is not precisely defined by law.
If such an object file uses only numerical parameters, data structure layouts and accessors, and small
macros and small inline functions (ten lines or less in length), then the use of the object file is unrestricted,
regardless of whether it is legally a derivative work. (Executables containing this object code plus portions
of the Library will still fall under Section 6.)
Otherwise, if the work is a derivative of the Library, you may distribute the object code for the work under
the terms of Section 6. Any executables containing that work also fall under Section 6, whether or not they
are linked directly with the Library itself.
6. As an exception to the Sections above, you may also combine or link a "work that uses the Library" with
the Library to produce a work containing portions of the Library, and distribute that work under terms of
your choice, provided that the terms permit modification of the work for the customer's own use and
reverse engineering for debugging such modifications.
You must give prominent notice with each copy of the work that the Library is used in it and that the
Library and its use are covered by this License. You must supply a copy of this License. If the work during
xiv WatchGuard Firebox X Edge
Page 15

Copyright, Trademark, and Patent Information
execution displays copyright notices, you must include the copyright notice for the Library among them, as
well as a reference directing the user to the copy of this License. Also, you must do one of these things:
a) Accompany the work with the complete corresponding machine-readable source code for the Library
including whatever changes were used in the work (which must be distributed under Sections 1 and 2
above); and, if the work is an executable linked with the Library, with the complete machine-readable
"work that uses the Library", as object code and/or source code, so that the user can modify the Library and
then relink to produce a modified executable containing the modified Library. (It is understood that the
user who changes the contents of definitions files in the Library will not necessarily be able to recompile
the application to use the modified definitions.)
b) Use a suitable shared library mechanism for linking with the Library. A suitable mechanism is one that
(1) uses at run time a copy of the library already present on the user's computer system rather than
copying library functions into the executable, and (2) operate properly with a modified version of the
library, if the user installs one, as long as the modified version is interface-compatible with the version that
the work was made with.
c) Accompany the work with a written offer, valid for at least three years, to give the same user the
materials specified in Subsection 6a, above, for a charge no more than the cost of performing this
distribution.
d) If distribution of the work is made by offering access to copy from a designated place, offer equivalent
access to copy the above specified materials from the same place.
e) Verify that the user has already received a copy of these materials or that you have already sent this user
a copy.
For an executable, the required form of the "work that uses the Library" must include any data and utility
programs needed for reproducing the executable from it. However, as a special exception, the materials to
be distributed need not include anything that is normally distributed (in either source or binary form) with
the major components (compiler, kernel, and so on) of the operating system on which the executable runs,
unless that component itself accompanies the executable.
It may happen that this requirement contradicts the license restrictions of other proprietary libraries that
do not normally accompany the operating system. Such a contradiction means you cannot use both them
and the Library together in an executable that you distribute.
7. You may place library facilities that are a work based on the Library side-by-side in a single library
together with other library facilities not covered by this License, and distribute such a combined library,
provided that the separate distribution of the work based on the Library and of the other library facilities is
otherwise permitted, and provided that you do these two things:
a) Accompany the combined library with a copy of the same work based on the Library, uncombined with
any other library facilities. This must be distributed under the terms of the Sections above.
b) Give prominent notice with the combined library of the fact that part of it is a work based on the Library,
and explaining where to find the accompanying uncombined form of the same work.
8. You may not copy, modify, sublicense, link with, or distribute the Library except as expressly provided
under this License. Any attempt otherwise to copy, modify, sublicense, link with, or distribute the Library is
void, and will automatically terminate your rights under this License. However, parties who have received
copies, or rights, from you under this License will not have their licenses terminated so long as such parties
remain in full compliance.
9. You are not required to accept this License, since you have not signed it. However, nothing else grants
you permission to modify or distribute the Library or its derivative works. These actions are prohibited by
law if you do not accept this License. Therefore, by modifying or distributing the Library (or any work based
on the Library), you indicate your acceptance of this License to do so, and all its terms and conditions for
copying, distributing or modifying the Library or works based on it.
10. Each time you redistribute the Library (or any work based on the Library), the recipient automatically
receives a license from the original licensor to copy, distribute, link with or modify the Library subject to
User Guide xv
Page 16
these terms and conditions. You may not impose any further restrictions on the recipients' exercise of the
rights granted herein. You are not responsible for enforcing compliance by third parties with this License.
11. If, as a consequence of a court judgment or allegation of patent infringement or for any other reason
(not limited to patent issues), conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of
this License. If you cannot distribute so as to satisfy simultaneously your obligations under this License
and any other pertinent obligations, then as a consequence you may not distribute the Library at all. For
example, if a patent license would not permit royalty-free redistribution of the Library by all those who
receive copies directly or indirectly through you, then the only way you could satisfy both it and this
License would be to refrain entirely from distribution of the Library.
If any portion of this section is held invalid or unenforceable under any particular circumstance, the
balance of the section is intended to apply, and the section as a whole is intended to apply in other
circumstances.
It is not the purpose of this section to induce you to infringe any patents or other property right claims or
to contest validity of any such claims; this section has the sole purpose of protecting the integrity of the
free software distribution system which is implemented by public license practices. Many people have
made generous contributions to the wide range of software distributed through that system in reliance on
consistent application of that system; it is up to the author/donor to decide if he or she is willing to
distribute software through any other system and a licensee cannot impose that choice.
This section is intended to make thoroughly clear what is believed to be a consequence of the rest of this
License.
12. If the distribution and/or use of the Library is restricted in certain countries either by patents or by
copyrighted interfaces, the original copyright holder who places the Library under this License may add an
explicit geographical distribution limitation excluding those countries, so that distribution is permitted
only in or among countries not thus excluded. In such case, this License incorporates the limitation as if
written in the body of this License.
13. The Free Software Foundation may publish revised and/or new versions of the Lesser General Public
License from time to time. Such new versions will be similar in spirit to the present version, but may differ
in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Library specifies a version number of this
License which applies to it and "any later version", you have the option of following the terms and
conditions either of that version or of any later version published by the Free Software Foundation. If the
Library does not specify a license version number, you may choose any version ever published by the Free
Software Foundation.
14. If you wish to incorporate parts of the Library into other free programs whose distribution conditions
are incompatible with these, write to the author to ask for permission. For software which is copyrighted
by the Free Software Foundation, write to the Free Software Foundation; we sometimes make exceptions
for this. Our decision will be guided by the two goals of preserving the free status of all derivatives of our
free software and of promoting the sharing and reuse of software generally.
PLEASE NOTE: Some components of the WatchGuard WFS software incorporate source code covered under
the GNU General Public License (GPL). To obtain the source code covered under the GPL, please contact
WatchGuard Technical Support at:
877.232.3531 in the United States and Canada
+1.360.482.1083 from all other countries
This source code is free to download. There is a $35 charge to ship the CD.
This product includes software covered by the GPL.
GNU GENERAL PUBLIC LICENSE
Version 2, June 1991
xvi WatchGuard Firebox X Edge
Page 17

Copyright, Trademark, and Patent Information
Copyright (C) 1989, 1991 Free Software Foundation, Inc.
59 Temple Place - Suite 330, Boston, MA 02111-1307, USA
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is
not allowed.
Preamble
The licenses for most software are designed to take away your freedom to share and change it. By contrast,
the GNU General Public License is intended to guarantee your freedom to share and change free software-
-to make sure the software is free for all its users. This General Public License applies to most of the Free
Software Foundation's software and to any other program whose authors commit to using it. (Some other
Free Software Foundation software is covered by the GNU Library General Public License instead.) You can
apply it to your programs, too.
When we speak of free software, we are referring to freedom, not price. Our General Public Licenses are
designed to make sure that you have the freedom to distribute copies of free software (and charge for this
service if you wish), that you receive source code or can get it if you want it, that you can change the
software or use pieces of it in new free programs; and that you know you can do these things.
To protect your rights, we need to make restrictions that forbid anyone to deny you these rights or to ask
you to surrender the rights. These restrictions translate to certain responsibilities for you if you distribute
copies of the software, or if you modify it.
For example, if you distribute copies of such a program, whether gratis or for a fee, you must give the
recipients all the rights that you have. You must make sure that they, too, receive or can get the source
code. And you must show them these terms so they know their rights.
We protect your rights with two steps: (1) copyright the software, and (2) offer you this license which gives
you legal permission to copy, distribute and/or modify the software.
Also, for each author's protection and ours, we want to make certain that everyone understands that there
is no warranty for this free software. If the software is modified by someone else and passed on, we want
its recipients to know that what they have is not the original, so that any problems introduced by others
will not reflect on the original authors' reputations.
Finally, any free program is threatened constantly by software patents. We wish to avoid the danger that
redistributors of a free program will individually obtain patent licenses, in effect making the program
proprietary. To prevent this, we have made it clear that any patent must be licensed for everyone's free use
or not licensed at all.
The precise terms and conditions for copying, distribution and modification follow.
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
0. This License applies to any program or other work which contains a notice placed by the copyright
holder saying it may be distributed under the terms of this General Public License. The "Program", below,
refers to any such program or work, and a "work based on the Program" means either the Program or any
derivative work under copyright law: that is to say, a work containing the Program or a portion of it, either
verbatim or with modifications and/or translated into another language. (Hereinafter, translation is
included without limitation in the term "modification".) Each licensee is addressed as "you".
Activities other than copying, distribution and modification are not covered by this License; they are
outside its scope. The act of running the Program is not restricted, and the output from the Program is
covered only if its contents constitute a work based on the Program (independent of having been made by
running the Program). Whether that is true depends on what the Program does.
1. You may copy and distribute verbatim copies of the Program's source code as you receive it, in any
medium, provided that you conspicuously and appropriately publish on each copy an appropriate
copyright notice and disclaimer of warranty; keep intact all the notices that refer to this License and to the
absence of any warranty; and give any other recipients of the Program a copy of this License along with
the Program.
User Guide xvii
Page 18

You may charge a fee for the physical act of transferring a copy, and you may at your option offer
warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Program or any portion of it, thus forming a work based on
the Program, and copy and distribute such modifications or work under the terms of Section 1 above,
provided that you also meet all of these conditions:
a) You must cause the modified files to carry prominent notices stating that you changed the files and the
date of any change.
b) You must cause any work that you distribute or publish, that in whole or in part contains or is derived
from the Program or any part thereof, to be licensed as a whole at no charge to all third parties under the
terms of this License.
c) If the modified program normally reads commands interactively when run, you must cause it, when
started running for such interactive use in the most ordinary way, to print or display an announcement
including an appropriate copyright notice and a notice that there is no warranty (or else, saying that you
provide a warranty) and that users may redistribute the program under these conditions, and telling the
user how to view a copy of this License. (Exception: if the Program itself is interactive but does not
normally print such an announcement, your work based on the Program is not required to print an
announcement.)
These requirements apply to the modified work as a whole. If identifiable sections of that work are not
derived from the Program, and can be reasonably considered independent and separate works in
themselves, then this License, and its terms, do not apply to those sections when you distribute them as
separate works. But when you distribute the same sections as part of a whole which is a work based on the
Program, the distribution of the whole must be on the terms of this License, whose permissions for other
licensees extend to the entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest your rights to work written entirely by
you; rather, the intent is to exercise the right to control the distribution of derivative or collective works
based on the Program.
In addition, mere aggregation of another work not based on the Program with the Program (or with a work
based on the Program) on a volume of a storage or distribution medium does not bring the other work
under the scope of this License.
3. You may copy and distribute the Program (or a work based on it, under Section 2) in object code or
executable form under the terms of Sections 1 and 2 above provided that you also do one of the following:
a) Accompany it with the complete corresponding machine-readable source code, which must be
distributed under the terms of Sections 1 and 2 above on a medium customarily used for software
interchange; or,
b) Accompany it with a written offer, valid for at least three years, to give any third party, for a charge no
more than your cost of physically performing source distribution, a complete machine-readable copy of
the corresponding source code, to be distributed under the terms of Sections 1 and 2 above on a medium
customarily used for software interchange; or,
c) Accompany it with the information you received as to the offer to distribute corresponding source code.
(This alternative is allowed only for noncommercial distribution and only if you received the program in
object code or executable form with such an offer, in accord with Subsection b above.)
The source code for a work means the preferred form of the work for making modifications to it. For an
executable work, complete source code means all the source code for all modules it contains, plus any
associated interface definition files, plus the scripts used to control compilation and installation of the
executable. However, as a special exception, the source code distributed need not include anything that is
normally distributed (in either source or binary form) with the major components (compiler, kernel, and so
on) of the operating system on which the executable runs, unless that component itself accompanies the
executable.
xviii WatchGuard Firebox X Edge
Page 19

Copyright, Trademark, and Patent Information
If distribution of executable or object code is made by offering access to copy from a designated place,
then offering equivalent access to copy the source code from the same place counts as distribution of the
source code, even though third parties are not compelled to copy the source along with the object code.
4. You may not copy, modify, sublicense, or distribute the Program except as expressly provided under this
License. Any attempt otherwise to copy, modify, sublicense or distribute the Program is void, and will
automatically terminate your rights under this License. However, parties who have received copies, or
rights, from you under this License will not have their licenses terminated so long as such parties remain in
full compliance.
5. You are not required to accept this License, since you have not signed it. However, nothing else grants
you permission to modify or distribute the Program or its derivative works. These actions are prohibited by
law if you do not accept this License. Therefore, by modifying or distributing the Program (or any work
based on the Program), you indicate your acceptance of this License to do so, and all its terms and
conditions for copying, distributing or modifying the Program or works based on it.
6. Each time you redistribute the Program (or any work based on the Program), the recipient automatically
receives a license from the original licensor to copy, distribute or modify the Program subject to these
terms and conditions. You may not impose any further restrictions on the recipients' exercise of the rights
granted herein. You are not responsible for enforcing compliance by third parties to this License.
7. If, as a consequence of a court judgment or allegation of patent infringement or for any other reason
(not limited to patent issues), conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of
this License. If you cannot distribute so as to satisfy simultaneously your obligations under this License and
any other pertinent obligations, then as a consequence you may not distribute the Program at all. For
example, if a patent license would not permit royalty-free redistribution of the Program by all those who
receive copies directly or indirectly through you, then the only way you could satisfy both it and this
License would be to refrain entirely from distribution of the Program.
If any portion of this section is held invalid or unenforceable under any particular circumstance, the
balance of the section is intended to apply and the section as a whole is intended to apply in other
circumstances.
It is not the purpose of this section to induce you to infringe any patents or other property right claims or
to contest validity of any such claims; this section has the sole purpose of protecting the integrity of the
free software distribution system, which is implemented by public license practices. Many people have
made generous contributions to the wide range of software distributed through that system in reliance on
consistent application of that system; it is up to the author/donor to decide if he or she is willing to
distribute software through any other system and a licensee cannot impose that choice.
This section is intended to make thoroughly clear what is believed to be a consequence of the rest of this
License.
8. If the distribution and/or use of the Program is restricted in certain countries either by patents or by
copyrighted interfaces, the original copyright holder who places the Program under this License may add
an explicit geographical distribution limitation excluding those countries, so that distribution is permitted
only in or among countries not thus excluded. In such case, this License incorporates the limitation as if
written in the body of this License.
9. The Free Software Foundation may publish revised and/or new versions of the General Public License
from time to time. Such new versions will be similar in spirit to the present version, but may differ in detail
to address new problems or concerns.
Each version is given a distinguishing version number. If the Program specifies a version number of this
License which applies to it and "any later version", you have the option of following the terms and
conditions either of that version or of any later version published by the Free Software Foundation. If the
Program does not specify a version number of this License, you may choose any version ever published by
the Free Software Foundation.
10. If you wish to incorporate parts of the Program into other free programs whose distribution conditions
are different, write to the author to ask for permission. For software which is copyrighted by the Free
Software Foundation, write to the Free Software Foundation; we sometimes make exceptions for this. Our
User Guide xix
Page 20
decision will be guided by the two goals of preserving the free status of all derivatives of our free software
and of promoting the sharing and reuse of software generally.
NO WARRANTY
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY FOR THE PROGRAM,
TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE
COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY OF
ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES
OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY
AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU
ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT
HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR REDISTRIBUTE THE PROGRAM AS PERMITTED
ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR
CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING
BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY
YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN
IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
END OF TERMS AND CONDITIONS
All other trademarks or trade names mentioned herein, if any, are the property of their respective owners.
Limited Hardware Warranty
This Limited Hardware Warranty (the "Warranty") applies to the enclosed Firebox hardware product, not
including any associated software which is licensed pursuant to a separate end-user license agreement and
warranty (the "Product"). BY USING THE PRODUCT, YOU (either an individual or a single entity) AGREE TO
THE TERMS HEREOF. If you do not agree to these terms, please return this package, along with proof of
purchase, to the authorized dealer from which you purchased it for a full refund. WatchGuard
Technologies, Inc. ("WatchGuard") and you agree as set forth below or on the reverse side of this card, as
applicable:
1. LIMITED WARRANTY. WatchGuard warrants that upon delivery and for one (1) year thereafter (the
"Warranty Period"): (a) the Product will be free from material defects in materials and workmanship, and (b)
the Product, when properly installed and used for its intended purpose and in its intended operating
environment, will perform substantially in accordance with WatchGuard applicable specifications.
This warranty does not apply to any Product that has been: (i) altered, repaired or modified by any party
other than WatchGuard except for the replacement or inclusion of specified components authorized in and
performed in strict accordance with documentation provided by WatchGuard; or (ii) damaged or destroyed
by accidents, power spikes or similar events or by any intentional, reckless or negligent acts or omissions of
any party. You may have additional warranties with respect to the Product from the manufacturers of
Product components. However, you agree not to look to WatchGuard for, and hereby release WatchGuard
from any liability for, performance of, enforcement of, or damages or other relief on account of, any such
warranties or any breach thereof.
2. REMEDIES. If any Product does not comply with the WatchGuard warranties set forth in Section 1 above,
WatchGuard will, following receipt of the product you claim is defective and at its option, either (a) repair
the Product, or (b) replace the Product; provided, that you will be responsible for returning the Product and
for all costs of shipping and handling. Repair or replacement of the Product shall not extend the Warranty
Period. Any Product, component, part or other item replaced by WatchGuard becomes the property of
WatchGuard. WatchGuard shall not be responsible for return of or damage to any software, firmware,
information or data contained in, stored on, or integrated with any returned Products.
3. DISCLAIMER AND RELEASE. THE WARRANTIES, OBLIGATIONS AND LIABILITIES OF WATCHGUARD, AND
YOUR REMEDIES, SET FORTH IN PARAGRAPHS 1 AND 2 ABOVE ARE EXCLUSIVE AND IN SUBSTITUTION FOR,
xx WatchGuard Firebox X Edge
Page 21

Limited Hardware Warranty
AND YOU HEREBY WAIVE, DISCLAIM AND RELEASE ANY AND ALL OTHER WARRANTIES, OBLIGATIONS AND
LIABILITIES OF WATCHGUARD AND ALL OTHER RIGHTS, CLAIMS AND REMEDIES YOU MAY HAVE AGAINST
WATCHGUARD, EXPRESS OR IMPLIED, ARISING BY LAW OR OTHERWISE, WITH RESPECT TO ANY
NONCONFORMANCE OR DEFECT IN THE PRODUCT (INCLUDING, BUT NOT LIMITED TO, ANY IMPLIED
WARRANTY OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE, ANY IMPLIED WARRANTY
ARISING FROM COURSE OF PERFORMANCE, COURSE OF DEALING, OR USAGE OF TRADE, ANY WARRANTY
OF NONINFRINGEMENT, ANY WARRANTY OF UNINTERRUPTED OR ERROR-FREE OPERATION, ANY
OBLIGATION, LIABILITY, RIGHT, CLAIM OR REMEDY IN TORT, WHETHER OR NOT ARISING FROM THE
NEGLIGENCE (WHETHER ACTIVE, PASSIVE OR IMPUTED) OR FAULT OF WATCHGUARD OR FROM PRODUCT
LIABILITY, STRICT LIABILITY OR OTHER THEORY, AND ANY OBLIGATION, LIABILITY, RIGHT, CLAIM OR REMEDY
FOR LOSS OR DAMAGE TO, OR CAUSED BY OR CONTRIBUTED TO BY, THE PRODUCT).
4. LIMITATION AND LIABILITY. WATCHGUARD’S LIABILITY (WHETHER ARISING IN CONTRACT (INCLUDING
WARRANTY), TORT (INCLUDING ACTIVE, PASSIVE OR IMPUTED NEGLIGENCE AND STRICT LIABILITY AND
FAULT) OR OTHER THEORY) WITH REGARD TO ANY PRODUCT WILL IN NO EVENT EXCEED THE PURCHASE
PRICE PAID BY YOU FOR SUCH PRODUCT. THIS SHALL BE TRUE EVEN IN THE EVENT OF THE FAILURE OF ANY
AGREED REMEDY. IN NO EVENT WILL WATCHGUARD BE LIABLE TO YOU OR ANY THIRD PARTY (WHETHER
ARISING IN CONTRACT (INCLUDING WARRANTY), TORT (INCLUDING ACTIVE, PASSIVE OR IMPUTED
NEGLIGENCE AND STRICT LIABILITY AND FAULT) OR OTHER THEORY) FOR COST OF COVER OR FOR ANY
INDIRECT, SPECIAL, INCIDENTAL, OR CONSEQUENTIAL DAMAGES (INCLUDING WITHOUT LIMITATION LOSS
OF PROFITS, BUSINESS, OR DATA) ARISING OUT OF OR IN CONNECTION WITH THIS WARRANTY OR THE USE
OF OR INABILITY TO USE THE PRODUCT, EVEN IF WATCHGUARD HAS BEEN ADVISED OF THE POSSIBILITY OF
SUCH DAMAGES. THIS SHALL BE TRUE EVEN IN THE EVENT OF THE FAILURE OF ANY AGREED REMEDY.
5. MISCELLANEOUS PROVISIONS. This Warranty will be governed by the laws of the state of Washington,
U.S.A., without reference to its choice of law rules. The provisions of the 1980 United Nations Convention
on Contracts for the International Sales of Goods, as amended, shall not apply. You agree not to directly or
indirectly transfer the Product or associated documentation to any country to which such transfer would
be prohibited by the U.S. Export laws and regulations. If any provision of this Warranty is found to be
invalid or unenforceable, then the remainder shall have full force and effect and the invalid provision shall
be modified or partially enforced to the maximum extent permitted by law to effectuate the purpose of
this Warranty. This is the entire agreement between WatchGuard and you relating to the Product, and
supersedes any prior purchase order, communications, advertising or representations concerning the
Product AND BY USING THE PRODUCT YOU AGREE TO THESE TERMS. IF THE PRODUCT IS BEING USED BY AN
ENTITY, THE INDIVIDUAL INDICATING AGREEMENT TO THESE TERMS BY USING THE PRODUCT REPRESENTS
AND WARRANTS THAT (A) SUCH INDIVIDUAL IS DULY AUTHORIZED TO ACCEPT THE WARRANTY ON BEHALF
OF THE ENTITY AND TO BIND THE ENTITY TO THE TERMS OF THIS WARRANTY; (B) THE ENTITY HAS THE FULL
POWER, CORPORATE OR OTHERWISE, TO ENTER INTO THE WARRANTY AND PERFORM ITS OBLIGATIONS
UNDER THE WARRANTY AND; (C) THE WARRANTY AND THE PERFORMANCE OF THE ENTITY’S OBLIGATIONS
UNDER THE WARRANTY DO NOT VIOLATE ANY THIRD-PARTY AGREEMENT TO WHICH THE ENTITY IS A
PARTY. No change or modification of the Warranty will be valid unless it is in writing and is signed by
WatchGuard.
Firmware Version: 7.1
Part Number: 1776-0000
Guide Version: 7.1-beta1
User Guide xxi
Page 22
Abbreviations Used in this Guide
3DES Triple Data Encryption Standard
BOVPN Branch Office Virtual Private Network
DES Data Encryption Standard
DNS Domain Name Service
DHCP Dynamic Host Configurationl Protocol
DSL Digital Subscriber Line
IP Internet Protocol
IPSec Internet Protocol Security
ISDN Integrated Services Digital Network
ISP Internet Service Provider
MAC Media Access Control
MUVPN Mobile User Virtual Private Network
NAT Network Address Translation
PPP Point-to-Point Protocol
PPPoE Point-to-Point Protocol over Ethernet
TCP Transfer Control Protocol
UDP User Datagram Protocol
URL Universal Resource Locator
VPN Virtual Private Network
WAN Wide Area Network
WSEP WatchGuard Security Event Processor
xxii WatchGuard Firebox X Edge
Page 23
Contents
CHAPTER 1 Introduction to Network Security ........................1
Network Security .....................................................................1
About Networks .......................................................................2
Clients and servers ...............................................................2
Connecting to the Internet .......................................................2
Protocols .................................................................................3
How Information Travels on the Internet ...................................3
IP Addresses ...........................................................................5
Network addressing ..............................................................5
About DHCP .........................................................................5
About PPPoE ........................................................................6
Domain Name Service (DNS) ...................................................6
Services ..................................................................................6
Ports .......................................................................................7
Firewalls ..................................................................................8
Firebox® X Edge and Your Network ..........................................9
CHAPTER 2
Installing the
Firebox® X Edge11
Package Contents .................................................................12
Installation Requirements ......................................................12
Identifying Your Network Settings ...........................................13
Finding your TCP/IP properties ............................................13
User Guide xxiii
Page 24

Disabling the HTTP Proxy Setting ...........................................15
Connecting the Firebox X Edge ...............................................17
Cabling the Firebox X Edge for more than seven devices .........18
Connecting to the System Configuration Pages ......................20
Setting your computer to use DHCP ......................................20
Setting your computer with a static IP address ......................21
Browsing to the System Status page .....................................22
Configuring the External Interface ..........................................23
Setting the Edge to use DHCP ..............................................23
Setting a Static IP Address ..................................................24
Entering PPPoE settings ......................................................24
Registering Your Edge and Activating LiveSecurity Service ......26
CHAPTER 3
Configuration and Management Basics ............29
Navigating the Configuration Pages ........................................29
Using the navigation bar ......................................................31
Logging in and setting a password .......................................31
Configuration Overview ..........................................................32
Firebox System Status Page .................................................32
Network Page .....................................................................33
Firebox Users Page .............................................................34
Administration Page ............................................................35
Firewall Page .....................................................................36
Logging Page .....................................................................37
WebBlocker Page ................................................................38
VPN Page ..........................................................................39
Wizards Page .....................................................................39
Updating Firebox X Edge Software ..........................................40
Factory Default Settings ........................................................41
Resetting the Firebox to the factory default settings ...............42
Rebooting the Firebox ............................................................42
Local reboot ......................................................................43
Remote reboot ...................................................................43
CHAPTER 4
Changing Your Network Settings ......................45
Using the Network Setup Wizard ............................................45
Configuring the External Network ...........................................46
If your ISP uses DHCP .........................................................47
If your ISP uses static IP addresses ......................................48
If your ISP uses PPPoE ........................................................48
Configuring the Trusted Network ............................................50
xxiv WatchGuard Firebox X Edge
Page 25

Changing the IP address of the trusted network .....................51
Using DHCP on the trusted network ......................................51
Setting trusted network DHCP address reservations ...............53
Configuring the trusted network for DHCP relay .....................53
Using static IP addresses for trusted computers ....................54
Adding computers to the trusted network ..............................54
Configuring the Optional Network ...........................................55
Enabling the optional network ..............................................55
Changing the IP address of the optional network ...................55
Using DHCP on the optional network ....................................56
Setting optional network DHCP address reservations ..............58
Configuring the optional network for DHCP relay ....................58
Using static IP addresses for optional computers ...................59
Adding computers to the optional network ............................59
Requiring encrypted connections .........................................60
Making Static Routes ............................................................60
Viewing Network Statistics ....................................................62
Registering with the Dynamic DNS Service ............................62
Enabling the WAN Failover Option ..........................................64
Enabling External Modem Failover ..........................................66
DNS settings ......................................................................67
Dialup settings ...................................................................68
CHAPTER 5
Setting up the Firebox X Edge Wireless ............69
How Wireless Networking Works ............................................70
Connecting to the Firebox X Edge Wireless ............................70
Cabling the Firebox X Edge Wireless for one to seven devices ..70
Cabling the Firebox X Edge Wireless for more than seven devices
71
Using the Wireless Network Wizard ........................................73
Setting up the Wireless Access Point .....................................73
Configuring the Wireless Card on Your Computer ...................73
Wireless Security Options ......................................................74
Changing basic settings ......................................................75
Configuring security ............................................................76
Configuring advanced settings .............................................77
Configuring Static Routes ......................................................78
CHAPTER 6
Configuring Firewall Settings ...........................79
Configuring Incoming and Outgoing Policies ...........................79
Standard policies ...............................................................80
User Guide xxv
Page 26

Adding a custom policy using the wizard ...............................81
Adding a custom policy .......................................................82
Adding a Policy for the Optional Interface ...............................83
Blocking External Sites ..........................................................84
Configuring Firewall Options ...................................................85
Responding to ping requests ...............................................86
Denying FTP access to the trusted network interface ..............86
SOCKS implementation for the Firebox X Edge .......................86
Logging all allowed outbound traffic .....................................88
Stop using the current MAC address .....................................88
CHAPTER 7
Configuring Logging ........................................91
Viewing Log Messages ..........................................................91
Logging to a WatchGuard Security Event Processor Log Host .92
Logging to a Syslog Host .......................................................93
Setting the System Time .......................................................94
Setting time using NTP ........................................................96
Setting time manually .........................................................96
CHAPTER 8
Configuring WebBlocker ..................................97
How WebBlocker Works .........................................................98
Configuring Global WebBlocker Settings .................................98
Creating WebBlocker Profiles .................................................99
WebBlocker Categories ........................................................101
Allowing Certain Sites to Bypass WebBlocker .......................103
Blocking Additional Web Sites ..............................................104
Allowing Internal Hosts to Bypass WebBlocker .....................106
CHAPTER 9
Configuring Virtual Private Networks ..............107
What You Need to Create a VPN ..........................................107
VPN requirements ............................................................109
Using a DVCP server to create your VPN tunnels ..................111
Setting up management for a dynamic Edge device ..............111
Setting up management for a static Edge device ..................112
Setting Up Manual VPN Tunnels ...........................................113
Phase 1 settings ..............................................................114
Phase 2 settings ..............................................................116
VPN Keep Alive ....................................................................117
Viewing VPN Statistics .........................................................118
Frequently Asked Questions .................................................118
xxvi WatchGuard Firebox X Edge
Page 27

CHAPTER 10 Configuring the MUVPN Client .......................121
Preparing Remote Computers to Use the MUVPN Client .......122
System requirements ........................................................122
Windows 98/ME setup ......................................................122
Windows NT setup ............................................................125
Windows 2000 setup ........................................................126
Windows XP setup ............................................................128
Installing and Configuring the MUVPN Client ........................131
Installing the MUVPN client ................................................131
Importing the .wgx file ......................................................132
Uninstalling the MUVPN client ............................................132
Enabling MUVPN for Edge Users ..........................................133
Configuring MUVPN client settings ......................................134
Enabling MUVPN access for an Edge user account ...............134
Configuring the Firebox for MUVPN Clients Using Pocket PC ..135
Connecting and Disconnecting the MUVPN Client .................135
Connecting the MUVPN client ............................................135
The MUVPN client icon ......................................................136
Allowing the MUVPN client through a personal firewall ..........137
Disconnecting the MUVPN client ........................................138
Monitoring the MUVPN Client Connection ............................138
Using Log Viewer ..............................................................138
Using Connection Monitor .................................................139
The ZoneAlarm Personal Firewall .........................................140
Allowing traffic through ZoneAlarm .....................................140
Shutting down ZoneAlarm .................................................141
Uninstalling ZoneAlarm .....................................................141
Troubleshooting Tips ............................................................142
CHAPTER 11
Managing the Firebox® X Edge ......................145
Viewing Current Sessions and Users ...................................145
Firebox User Settings ........................................................146
Active Sessions ................................................................146
Local User Accounts .........................................................147
About User Authentication ...................................................148
......................................................Authenticating to the Firebox 149
Changing authentication options for all users ......................149
Configuring MUVPN client settings ......................................151
Adding or Editing a User Account .........................................152
Creating a read only administrative account ........................153
User Guide xxvii
Page 28
Setting a WebBlocker profile for a user ...............................154
Enabling MUVPN for a user ...............................................154
The Administrator account .................................................154
Terminating a session .......................................................155
Changing a user account name or password .......................155
About Seat Licenses ...........................................................156
Selecting HTTP or HTTPS for Firebox Management ...............157
Changing the HTTP Server Port ............................................158
Setting up VPN Manager Access ..........................................158
Updating the Firmware .........................................................159
Method 1 ........................................................................160
Method 2 ........................................................................160
Activating Upgrade Options ..................................................161
Enabling the Model Upgrade Option .....................................162
Configuring Additional Options .............................................163
Viewing the Configuration File ..............................................164
Firebox®X Edge Hardware 165
Package Contents ...............................................................165
Specifications .....................................................................167
Hardware Description ..........................................................167
Front panel ......................................................................167
Back view ........................................................................169
Side panels .....................................................................169
Index............................................................................171
xxviii WatchGuard Firebox X Edge
Page 29
CHAPTER 1 Introduction to
Network Security
Congratulations on your purchase of the WatchGuard Firebox® X Edge.
Your new security device provides peace of mind when countering
today’s network security threats.
To provide context for the many features described throughout this
user guide, this chapter explains basic concepts of networking and
network security.
Network Security
Although the Internet puts a tremendous volume of information at
your fingertips, it also presents risks by exposing your network to
attackers. Network security is the process of preventing and detecting
unauthorized use of your computer or network. Prevention measures
help you to stop intruders from accessing any part of your computer
system.
Although you may not consider anything on your computer “top
secret," you should still be very concerned about security. If you aren’t
careful, intruders can take malicious actions such as use your computer
to attack other computer systems, send forged e-mail from your computer, or steal your financial information. They can also damage your
computer by reformatting your hard drive or changing your data.
User Guide 1
Page 30
Introduction to Network Security
Computer security must always be kept up-to-date. Intruders are
always discovering new vulnerabilities to exploit in computer software.
About Networks
A network is a connected group of computers and other devices. It
can consist of anything from two computers connected by a serial
cable to thousands of computers connected by high-speed data
communication links located throughout the world.
A
Local Area Network
ically to form a common work environment. This facilitates the sharing of applications and data, and is especially important when a
group of people need to work together on one project.
A
Wide Area Network
icant distances, such as those located in different buildings.
Clients and servers
The terms
ers that are part of a network. A server is a computer that makes its
resources available to the network and responds to the commands
of a client. Examples of a server’s shared resources are files (a file
server), printers (a print server), and processing power (an application server). A client is a computer that uses the resources made
available by the server.
client
(LAN) is a group of computers linked electron-
(WAN) involves computers separated by signif-
and
server
are used to describe individual comput-
Connecting to the Internet
You have a number of options for connecting to the Internet. Highspeed Internet connections, such as cable modem or Digital Subscriber Line (DSL), are referred to as broadband connections.
width
describes the relative speed of an Internet connection, such as
1 Megabit per second (Mbps).
You can use a cable modem to connect to the Internet via the cable
TV network. The cable modem usually has an Ethernet LAN connection to the computer, and it is capable of speeds in excess of 5
Mbps.
Typical speeds tend to be lower than the maximum, however,
because cable providers turn entire neighborhoods into LANs that
2 WatchGuard Firebox X Edge
Band-
Page 31

share the same bandwidth. Because of this "shared-medium" topology, cable modem users might experience somewhat slower network
access during periods of peak demand, and can be more susceptible
to certain types of attacks more than users with other types of connectivity.
Digital Subscriber Line (DSL) Internet connectivity, unlike cable
modem-based service, provides the user with dedicated bandwidth.
However, the maximum bandwidth available to DSL users is usually
lower than the maximum cable modem rate because of differences
in their respective network technologies. Also, the "dedicated bandwidth" is dedicated only between your home or office and the DSL
provider's central office. The provider offers little or no guarantee of
bandwidth across the Internet.
Internet Service Providers
the Internet.
Protocols
Protocols
(ISP) are companies that provide access to
You will often hear the term protocol. A
that allows computers to communicate across a network. In a way,
protocols define the grammar that computers use to communicate
with each other.
The standard protocol whenever you connect to the Internet is
called Internet Protocol (IP). This protocol can be thought of as the
common language of computers on the Internet.
A protocol also defines how data is assembled and transmitted
through a network. The most frequently used protocols are TCP
(Transmission Control Protocol) and UDP (User Datagram Protocol).
Other IP protocols are less commonly used.
TCP/IP is the basic protocol used by computers connected to the
Internet. TCP/IP involves certain settings that you need to know
when setting up your Firebox X Edge. For more information on TCP/
IP, see “Finding your TCP/IP properties” on page 13.
protocol
is a specification
How Information Travels on the Internet
The data that is sent through the Internet is divided into units called
packets. When you send a file from one place to another on the
User Guide 3
Page 32

Introduction to Network Security
Internet, the file is divided into chunks of data. Each chunk, or
packet, is separately numbered and includes the Internet address of
the destination. The individual packets for a given file may travel
different routes through the Internet. When they have all arrived,
they are reassembled into the original file. To make sure that the
packets are received at the destination, information is added to the
packets.
The TCP and IP protocols are used for sending and receiving these
packets. TCP disassembles and reassembles the data; for example,
data that may consist of an e-mail message or a program file. IP
adds information to the packets that includes the destination and
the handling requirements.
Data packet
Packets traveling on the Internet
4 WatchGuard Firebox X Edge
Page 33

IP Addresses
IP addresses are like street addresses—when you want to send some
information to someone, you must first know his or her address.
Similarly, when a computer connected to the Internet needs to send
data to another computer, it must first know its IP address.
Each computer on the Internet has its own unique IP address. An IP
address consists of four sets of numbers separated by decimal
points. Examples of IP addresses are:
• 192.168.0.11
• 10.1.20.18
• 208.15.15.15
A firewall device such as the Firebox® X Edge is also a computer and
therefore has its own IP address.
Network addressing
Your ISP assigns IP addresses, which are a requirement to connect to
the Internet. The assignment of IP addresses is
Static IP addressing occurs when an ISP permanently assigns one or
more IP addresses for each user. These addresses do not change over
time. However, if a static address is assigned but not in use, it is
effectively wasted. Because ISPs have a limited number of addresses
allocated to them, they sometimes need to make more efficient use
of their addresses.
Dynamic IP addressing allows the ISP to use their address space
more efficiently. Using dynamic IP addressing, the IP addresses of
individual user computers may change over time. If a dynamic
address is not in use (the user is not connected to the network), it
can be automatically reassigned to another computer as needed.
Your ISP can tell you how their system assigns IP addresses.
dynamic
IP Addresses
or
static
.
About DHCP
Most ISPs make dynamic IP address assignments through (Dynamic
Host Configuration Protocol (DHCP). When a computer connects to
the network, a DHCP server at the ISP assigns that computer an IP
address. The manual assignment of IP addresses is not necessary
when using DHCP.
User Guide 5
Page 34

Introduction to Network Security
About PPPoE
Some ISPs assign the IP addresses through Point-to-Point Protocol
over Ethernet (PPPoE). PPPoE emulates a standard dial-up connection to provide some of the features of Ethernet and PPP. This system allows the ISP to use the billing, authentication, and security
systems designed for dial-up, DSL modem, and cable modem service.
Domain Name Service (DNS)
If you don’t know a person’s street address, you can look it up in the
telephone directory. On the Internet, the equivalent to a telephone
directory is the Domain Name Service, or DNS. You probably use
DNS all the time without knowing it. Whenever you use a “.com”
address such as www.mysite.com (which is actually the site’s
) to visit an Internet site, you are using DNS. When you type
name
the .com address into your Internet browser (such as Internet
Explorer or Netscape), your computer asks its DNS server for the
actual IP address of the site.
A URL (Uniform Resource Locator) identifies each IP address on the
Internet. An example of a URL is:
http://www.watchguard.com/
domain
Services
As the name implies, a service provides some kind of useful function
for you on the computer, such as exchanging e-mail or transferring
files from one computer to another through the network. These services are based on specific protocols. Commonly used Internet services are:
• World Wide Web access uses Hypertext Transfer Protocol (HTTP)
• E-mail uses Simple Mail Transfer Protocol (SMTP)
• File transfer uses File Transfer Protocol (FTP)
• Resolving a domain name into an Internet address uses Domain
Name Service (DNS)
• Remote terminal access uses Telnet or Secure Shell
6 WatchGuard Firebox X Edge
Page 35

Ports
Ports
Although some services are essential, they can also be a security risk.
To send and receive data, you must “open a door” in your computer,
which makes your network vulnerable. One of the most common
ways networks are broken into is by intruders exploiting services.
On computers and other telecommunication devices, a port is a specific place for physically connecting another device, usually with a
socket and plug. A computer usually has one or more serial ports
and one parallel port. The serial port supports sequential, one bitat-a-time transmission to devices such as scanners, and the parallel
port supports multiple-bit-at-a-time transmission to devices such as
printers.
Computers also have ports that are not physical locations. These
ports are “logical connection places” for programs or applications on
a computer in a network. Some applications, such as HTTP, have
ports with preassigned numbers. These are known as “well-known
ports.” Other application processes are assigned port numbers
dynamically for each connection. When a service is initially started,
it is said to “bind” to its designated port number.
Every Internet service using TCP is identified by a unique port number. When a client initiates a connection to a server, it chooses to
connect to, say, port 25 on the remote machine. Port 25 is assigned
to the SMTP protocol which is the service of delivering electronic
mail.
Most services are assigned a port number in the range from 0 to
1024, but the valid port numbers range from 0 to 65535.
User Guide 7
Page 36

Introduction to Network Security
Firewalls
A
firewall
this danger. The computers on the “trusted” (internal) side of a firewall are protected. The illustration below shows how a firewall physically divides the trusted network (your computers) from the
Internet.
divides your internal network from the Internet to reduce
Firewalls allow the user to define access policies for the Internet
traffic going to the computers they are protecting. Many also provide the ability to control what services or ports the protected computers are able to access on the Internet (outbound access). Most
firewalls intended for home use come with pre-configured security
policies from which the user chooses, and some—such as the Firebox
X Edge—allow the user to customize these policies for their specific
8 WatchGuard Firebox X Edge
Page 37

Firebox® X Edge and Your Network
needs.
Firewalls are implemented in both hardware and software, or a combination of both. Firewalls are frequently used to prevent unauthorized Internet users from accessing private networks connected to
the Internet. All messages entering or leaving the intranet pass
through the firewall, which examines each message and blocks those
that do not meet the specified security criteria.
Firebox® X Edge and Your Network
The Firebox® X Edge controls all traffic between the external network (the Internet) and the trusted network. The Edge also supports
an optional network to extend the protection of the firewall to
include telecommuters on a separate network. All suspicious traffic
is stopped. The rules and policies that identify the suspicious traffic
are described in Chapter 5, “Configuring Firewall Settings.”
Designed for small and remote offices with modest in-house security
expertise, the Firebox X Edge is a high-performance security device
that simply plugs in between your cable, DSL, or ISDN router and
your network.
The Web-based user interface of the Firebox X Edge intuitive and
straight-forward. You don't need additional security expertise to
install and manage your firewall. Because you can manage your network securely from anywhere, at any time, you have more time and
resources to focus on your business.
User Guide 9
Page 38

Introduction to Network Security
10 WatchGuard Firebox X Edge
Page 39

CHAPTER 2 Installing the
Firebox® X Edge
To install the WatchGuard® Firebox® X Edge in your network, you must
complete these steps:
• Identify and record the TCP/IP properties for your Internet
connection.
• Disable the HTTP proxy properties of your Web browser.
• Connect the Firebox X Edge to your network.
• Enable your computer for DHCP.
• Activate the LiveSecurity® Service.
User Guide 11
Page 40

Installing the Firebox® X Edge
Package Contents
Make sure that the package for your Firebox® X Edge includes this
User Guide and these items:
• The Firebox X Edge
• A LiveSecurity® Service activation card
• A Hardware Warranty Card
• An AC adapter (12 V)
• Power cable clip, to attach to the cable and connect to the side
of the Edge. This releases tension on the power cable.
• One straight-through Ethernet cable
QuickStart Guide
Installation Requirements
The other installation requirements are:
• A computer with a 10/100BaseT Ethernet I/O network interface
card.
• A Web browser. You must use Netscape 7.0 (or later), Internet
Explorer 6.0 (or later), or an equivalent browser.
• The serial number of the Firebox X Edge you see on the bottom
of the device.
You use the serial number to register the Edge.
12 WatchGuard Firebox X Edge
Page 41

Identifying Your Network Settings
• An Internet connection that operates.
The external network connection can be a cable or DSL modem with a
10/100BaseT port, an ISDN router, or a direct LAN connection. If the
Internet connection does not operate, speak to your Internet Service
Provider (ISP).
Identifying Your Network Settings
You use an Internet Service Provider (ISP) to connect to the Internet.
These ISPs give all computers an Internet Protocol (IP) address. An
ISP can give you a static or dynamic IP address. A static address is an
address that stays the same. A dynamic address is an address that
can change each time you connect to the Internet. When you close a
dynamic Internet connection, the dynamic address goes to the list of
available addresses.
Your ISP gives you an IP address using one of these:
• Static: Web servers, FTP Web sites, and other Internet resources
that must have an address that cannot change get static a IP
addresses.
• DHCP: ISPs use the Dynamic Host Configuration Protocol
(DHCP) to give you a dynamic IP address. Each time you
connect to the ISP, a DHCP server can give you a different IP
address.
• PPPoE: ISPs use Point-to-Point Protocol over Ethernet (PPPoE)
to give you a dynamic IP address or a static IP address. A user
name and passphrase are necessary for PPPoE.
An ISP can also give a network mask (netmask) to a computer. A
netmask is a string of bits that "mask" one part of an IP address.
You use a netmask to divide your network into smaller units, and
creating added destinations to which you can send routed traffic.
Read your DSL or cable modem instructions or speak to your ISP to
learn if you have a dynamic IP address or a static IP address.
Finding your TCP/IP properties
Transmission Control Protocol/Internet Protocol (TCP/IP) is the primary protocol computers use to connect to the Internet. To use
TCP/IP, your computer must have an IP address and information
about the computer network of your ISP. You must have this information to install your Firebox X Edge.
User Guide 13
Page 42

Installing the Firebox® X Edge
N
OTE
N
OTE
If your ISP gives your computer an IP address of 10.0.0.0/8 or one
that starts with 192.168 or 172.16 to 172.31, then your ISP uses
network address translation (NAT). You must get a public IP
address and disable NAT on your intranet router for full
functionality. Get instructions from your ISP.
Your TCP/IP Properties Table
TCP/IP Proper ty Value
IP Address
Subnet Mask
Default Gateway
DHCP Enabled Yes No
DNS Server(s) Primary
Secondary
. . .
. . .
. . .
. . .
. . .
To find your TCP/IP properties, use the instructions for your computer operating system.
Microsoft Windows 2000 and Windows XP
1 Click Start > Programs > Accessories > Command Prompt.
2 At the MS-DOS prompt, type ipconfig /all and then press
Enter.
3 Record the values in the Your TCP/IP Properties Table on
page 14.
4 Close the window.
Microsoft Windows NT
1 Click Start > Programs > Command Prompt.
2 At the MS-DOS prompt, type ipconfig /all and then press
Enter.
14 WatchGuard Firebox X Edge
Page 43

Disabling the HTTP Proxy Setting
3 Record the values in the Your TCP/IP Properties Table on
page 14.
4 Close the window.
Microsoft Windows 98 or ME
1 Click Start > Run.
2 At the MS-DOS prompt, type winipcfg and then press Enter.
3 Click OK.
4 Select the Ethernet Adapter.
5 Record the values in the Your TCP/IP Properties Table on
page 14.
6 Click Cancel.
Macintosh
1 Click the Apple menu > Control Panels > TCP/IP.
2 Record the values in the Your TCP/IP Properties Table on
page 14.
3 Close the window.
Other operating systems (Unix, Linux)
1 Read your operating system guide to locate the TCP/IP settings.
2 Record the values in the Your TCP/IP Properties Table on
page 14.
3 Exit the TCP/IP configuration screen.
Disabling the HTTP Proxy Setting
A proxy is a computer procedure that receives and examines packet
headers and packet content. If the proxy finds packet headers or
packet contents that do not obey the proxy rules, those packets are
denied, blocked, or stripped. The proxy policy monitors and controls
traffic to protect your network from the Internet.
Many Web browsers use the HTTP proxy to monitor incoming Internet traffic. When this proxy is enabled, you can see Web pages on
the Internet, but you cannot see Web pages in other locations.
Because you must see pages that are stored or saved on the Firebox
X Edge to complete the installation procedure, you must disable this
proxy temporarily.
User Guide 15
Page 44

Installing the Firebox® X Edge
You can use the instructions below to disable the HTTP proxy in
Netscape or Internet Explorer. If you are using a different browser,
try using the browser Help system to find the necessary information.
Many opensource browsers automatically disable the HTTP proxy
feature.
Netscape
1 Open Netscape.
2 Click Edit > Preferences.
The Preferences window appears.
3 A list of options appears at the left side of the window. Click the
arrow symbol to the left of the Advanced heading to expand
the list.
4 Click Proxies.
5 Make sure the Direct Connection to the Internet option is
selected.
6 Click OK.
Internet Explorer
1 Open Internet Explorer.
2 Click Tools > Internet Options.
The Internet Options window appears.
3 Click the Advanced tab.
4 Scroll down the page to HTTP 1.1 Settings.
5 Clear all of the checkboxes.
6 Click OK.
16 WatchGuard Firebox X Edge
Page 45

Connecting the Firebox X Edge
Use this procedure to connect your Firebox® X Edge Ethernet and
power cables:
1 Shut down your computer.
2 If you use a DSL or cable modem to connect to the Internet,
disconnect its power supply.
3 Find the Ethernet cable between the modem and your
computer. Disconnect this cable from your computer and
connect it to the Edge external interface (WAN 1).
Connecting the Firebox X Edge
4 Find the Ethernet cable supplied with your Edge. Connect this
cable to a trusted interface (0-6) on the Edge. Connect the
other end of this cable to the Ethernet interface of your
computer.
5 If you use a DSL or cable modem, connect its power supply.
User Guide 17
Page 46

Installing the Firebox® X Edge
6 Find the AC adapter supplied with your Edge. Connect the AC
adapter to the Edge and to a power source.
The Edge power indicator light comes on and the external interface
indicator lights flash and then come on. The Edge is ready.
N
OTE
N
OTE
Use only the Firebox X Edge AC adapter.
7 When the Edge is ready, start your computer.
Cabling the Firebox X Edge for more than seven devices
Although the Firebox X Edge has only seven numbered Ethernet
ports (labeled 0-6), you can connect more than seven devices. Use
one or more network hubs to make more connections.
The maximum number of devices that can connect to the Internet
at the same time is set by model. For example, the Firebox X5 has a
five-session license. There can be more than five devices on the
trusted network, but the Edge allows only five Internet connections
at the same time.
The Edge uses a session when it makes a connection between a
computer on the trusted interface and a computer on the external
interface. The Edge releases the session when:
• The session reaches the idle timeout limit
• The session reaches the maximum time limit
• The Edge administrator uses the Firebox Users page to end the
session
• The user ends the session by closing all browser windows
• The Edge restarts.
For more information, see the FAQ:
https://www.watchguard.com/support/AdvancedFaqs/
sogen_seatlimit.asp
License upgrades are available from your reseller or from the WatchGuard Web site:
http://www.watchguard.com/sales/buyonline.asp
To connect more than seven devices to the Edge, you need:
• An Ethernet 10/100Base TX hub or switch
• A straight-through Ethernet cable, with RJ-45 connectors, for
each computer
18 WatchGuard Firebox X Edge
Page 47

Connecting the Firebox X Edge
• A straight-through Ethernet cable to connect each hub to the
Firebox X Edge.
To connect more than seven devices to the Firebox X Edge:
1 Shut down your computer. If you connect to the Internet
through a DSL modem or cable modem, disconnect the power
supply from this device.
2 Disconnect the Ethernet cable that runs from your DSL modem,
cable modem, or other Internet connection to your computer.
Connect the Ethernet cable to the WAN port on the Firebox X
Edge.
The Firebox X Edge is connected directly to the modem or other Internet
connection.
3 Connect one end of the straight-through Ethernet cable
supplied with your Firebox X Edge to one of the seven
numbered Ethernet ports (labeled 0-6) on the Edge. Connect
the other end to the uplink port of the Ethernet hub or switch.
The Firebox X Edge is connected to the Internet and your Ethernet hub
or switch.
4 Connect an Ethernet cable between each of the computers and
an uplink port on the Ethernet hub, and make sure the link
lights are lit on both devices when powered back on.
5 If you connect to the Internet through a DSL modem or cable
modem, reconnect the power supply to this device. The
indicator lights flash and then stop. The modem is ready for use.
6 Attach the AC adapter to the Firebox X Edge. Connect the AC
adapter to a power supply.
7 Restart your computer.
If you get a message that says your operating system has no network
connection, shut down all equipment and make sure all devices are
connected properly.
8 Start your Internet browser.
9 Type https://192.168.111.1/ into the URL entry field of your
browser and press Enter.
10 Follow the steps in the QuickSetup Wizard to configure your
Firebox X Edge.
User Guide 19
Page 48

Installing the Firebox® X Edge
If your ISP uses static IP addressing, or uses PPPoE, then do the following additional steps:
1 From your Web browser, select File > Open Location, type
https://192.168.111.1/ into the URL entry field of your browser,
and press Enter. Log on using the default user name (admin)
and password (admin).
2 From the navigation bar, expand Network (click the plus sign)
and select External.
3 From the Configuration Mode drop-down list, select either
Manual Configuration (for static IP addressing) or PPPoE
Client.
Connecting to the System Configuration Pages
Use a Web browser to connect to the Firebox® X Edge system configuration pages. The first time you connect to the Edge configuration pages, the End User License Agreement (EULA) appears. To
continue, you must accept the agreement. You must also set the
administrator password.
A factory default Edge allows HTTP traffic on port 80. After you set
the administrator password, the Edge uses only secure HTTP
(HTTPS) on port 443 for system configuration.
For your computer to connect to the Edge, you must choose one of
these options:
• Get a dynamic IP address from the Edge using DCHP
• Set a static IP address within the default trusted interface
address range
The default trusted interface IP address is 192.168.111.1/24.
For more information on network addressing, see “IP Addresses” on
page 5.
Setting your computer to use DHCP
This procedure sets a computer with the Windows XP operating system to use DHCP. If your computer does not use Windows XP, read
20 WatchGuard Firebox X Edge
Page 49

Connecting to the System Configuration Pages
the documentation for instructions to set your computer to use
DHCP.
1 Click Start > Control Panel.
The Control Panel window appears.
2 Double-click the Network Connections icon.
3 Double-click the Local Area Connection icon.
4 Double-click the Internet Protocol (TCP/IP) item.
The Internet Protocol (TCP/IP) Properties dialog box appears.
5 Select the Obtain an IP address automatically and the Obtain
DNS server address automatically options.
6 Click OK to close the Internet Protocol (TCP/IP) Properties
dialog box.
7 Click OK to close the Local Area Network Connection
Properties dialog box. Close the Network Connections and
Control Panel windows.
Your computer is now connected to the Firebox X Edge.
Setting your computer with a static IP address
This procedure sets a computer with the Windows XP operating system to a static IP address. If your computer does not use Windows
XP, read the documentation for instructions to set your computer to
use DHCP. You must use an IP address on the same network as the
Firebox X Edge trusted interface.
1 Click Start > Control Panel.
The Control Panel window appears.
2 Double-click the Network Connections icon.
3 Double-click the Local Area Connection icon.
4 Double-click the Internet Protocol (TCP/IP) item.
The Internet Protocol (TCP/IP) Properties dialog box appears.
5 Select the Use the following IP address option.
6 In the IP address field, type an IP address on the same network
as the Edge trusted interface. We recommend 192.168.111.2.
The default trusted interface network is 192.168.111.0/24. The last
number can be between 2 and 254.
7 In the Subnet Mask field, type 255.255.255.0.
User Guide 21
Page 50

Installing the Firebox® X Edge
8 In the Default Gateway field, type the IP address of the Edge
trusted interface.
The default Edge trusted interface address is 192.168.111.1.
9 Click OK to close the Internet Protocol (TCP/IP) Properties
dialog box.
10 Click OK to close the Local Area Network Connection
Properties dialog box. Close the Network Connections and
Control Panel windows.
Your computer is now connected to the Firebox X Edge.
Browsing to the System Status page
Use a Web browser to connect to the Edge and then change the
network settings.
1 Open your Web browser.
If this is the first connection to the Edge, the End User License
Agreements appears. You must accept the agreement and set your
administrator password to continue.
2 In the Address bar, type the Edge trusted interface IP address
which is https://192.168.111.1 for a new Edge. Press the Enter
key.
22 WatchGuard Firebox X Edge
Page 51

Configuring the External Interface
Configuring the External Interface
Your Internet Service Provider (ISP) uses DHCP, PPPoE, or static IP
addressing to identify your computer on their network. After you
connect the Edge, you must configure the external interface with
the information from your ISP.
Setting the Edge to use DHCP
A new Edge uses DHCP to get an IP address for the external interface. If your ISP uses DHCP addressing to identify your computer on
their network, it is not necessary to make a configuration change
unless the ISP gives you a DHCP ID or name. If necessary, use this
procedure to set the DHCP ID or name:
1 Open your Web browser. Browse to the System Status page at
https://192.168.111.1.
Type the URL in the Address bar of your browser and press the [Enter]
key.
2 From the navigation bar on the left side, click the + symbol to
the left of Network. Click External.
3 Use the Configuration mode drop-down list to select DHCP
Client.
4 In the Optional DHCP Identifier field, type the DHCP name or
ID you got from your ISP.
5 Click Submit.
User Guide 23
Page 52

Installing the Firebox® X Edge
Setting a Static IP Address
If your ISP uses static IP addressing, you must set the Edge external
interface address. Use the information in the Your TCP/IP Properties
Table on page 14 to do this procedure.
1 Open your Web browser. Browse to the System Status page at
https://192.168.111.1.
Type the URL in the Address bar of your browser and press the [Enter]
key.
2 From the navigation bar on the left side, click the plus sign (+)
to the left of Network. Click External.
3 Use the Configuration mode drop-down list to select Manual
Configuration.
4 Type the IP address, subnet mask, and default gateway.
5 Type the IP addresses of the primary and secondary DNS servers.
6 Type the DNS domain suffix.
7 Click Submit.
Entering PPPoE settings
Many ISPs use Point to Point Protocol over Ethernet (PPPoE)
because it is easy to merge with dial-up infrastructure. If your ISP
uses PPPoE to give IP addresses, you must get more setup information.
24 WatchGuard Firebox X Edge
Page 53

PPPoE Address Settings
PPPoE Setting Value
Login Name
Domain
Password
For more information in PPPoE, see “About PPPoE” on page 6. To
configure the Edge for PPPoE:
1 Open your Web browser and click Stop.
Because the Internet connection is not configured, the browser cannot
show your home page from the Internet. The browser can only open the
configuration pages saved on the Edge.
2 Type the IP address of the trusted network in your browser
window to connect to the System Status page of the Firebox X
Edge.
The default IP address is: https://192.168.111.1
3 From the navigation bar at left, select Network > External.
The External Network Configuration page opens.
4 From the Configuration Mode drop-down list, select PPPoE
Client.
Configuring the External Interface
User Guide 25
Page 54

Installing the Firebox® X Edge
5 Type the PPPoE login name and domain as well as the PPPoE
password supplied by your service provide in the applicable
fields.
6 Type the time delay before inactive TCP connections are
disconnected.
7 If appropriate, select the Automatically restore lost
connections checkbox.
This option keeps a constant traffic flow between the Edge and the
PPPoE server. Thus the Edge keeps the PPPoE connection open during a
period of frequent packet loss. If the traffic flow stops, the Edge reboots,
which frequently activates the connection. The ISP sees this constant
traffic flow as a continuous connection. The ISP rules and billing policy
control if you can use this option.
8 Select the Enable PPPoE debug trace checkbox to activate
PPPoE debug trace.
This can assist WatchGuard Technical Support in troubleshooting PPPoE
problems.
9 Click Submit.
Registering Your Edge and Activating LiveSecurity Service
After you install the Firebox® X Edge, you can register the Edge and
activate your LiveSecurity® Service subscription. The LiveSecurity
Service gives you threat alert notifications, security advice, free virus
protection, software updates, technical support by Web or telephone, and access to online help resources and the WatchGuard user
forum.
You must have a subscription to the LiveSecurity Service before you
can get license keys for the upgrades that you purchase. To apply
upgrades, you must log into LiveSecurity Service and enter your
upgrade key. You get a
feature key
to activate the features on your
Firebox X Edge.
You must have the serial number of your Firebox X Edge to register.
The Edge serial number is on the bottom of the device. Record the
serial number in the table below:
1 Register your Firebox X Edge with the LiveSecurity Service at the
WatchGuard Web site:
http://www.watchguard.com/activate
26 WatchGuard Firebox X Edge
Page 55

Registering Your Edge and Activating LiveSecurity Service
To activate the LiveSecurity Service, your browser must have
JavaScript enabled.
2 If you have a user profile on the WatchGuard Web site, enter
your user name and password. If you have not registered before,
you must create a user profile. To do this, follow the
instructions on the Web site.
3 Record your LiveSecurity Service user profile information in the
table below. Keep this information confidential.
WatchGuard User Profile
User name:
Password:
Serial Number:
4 If a model upgrade key is included with your model, activate it
by going to:
http://www.watchguard.com/upgrade
5 Select your product and follow the instructions for product
activation.
N
OTE
N
OTE
User Guide 27
Page 56

Installing the Firebox® X Edge
28 WatchGuard Firebox X Edge
Page 57

CHAPTER 3 Configuration and
Management Basics
When you
Edge appropriate for the specific security needs of your organization.
This is your main task after you install your Firebox. You use Web
pages inthe Firebox to create the configuration of the Firebox X Edge.
You connect to these configuration pages with your Web browser.
You can also use the Firebox Web pages to create accounts, look at
network statistics, and see the current configuration of the Firebox.
Read this chapter to learn basic information about the Firebox X Edge
Web pages. Sections in later chapters have more detailed intructions.
This chapter contains cross-references to those later sections.
configure
a Firebox, you make the WatchGuard® Firebox® X
Navigating the Configuration Pages
To configure your Firebox® X Edge, you use a Web browser such as
Internet Explorer, Mozilla Firefox, or NetScape Navigator. You must
first disable the HTTP Proxy feature. For more information, see “Disabling the HTTP Proxy Setting” on page 15.
In this User Guide, every procedure starts with a step to:
“Type the IP address of the trusted network in your browser window to
connect to the System Status page of the Firebox X Edge. The default
IP address is https://192.168.111.1.”
User Guide 29
Page 58

Configuration and Management Basics
The purpose of the step is to open your Firebox system configuration pages. Your computer must be connected to the Firebox with
an Ethernet cable. You can change the IP address of the trusted network from https://192.168.111.1 to an IP address of your choice. For
more information, see “Configuring the Trusted Network” on
page 50.
For example, if you use Internet Explorer to configure your Firebox:
1 Start Internet Explorer.
2 Click File > Open, type https://192.168.111.1 in the text box
next to the word Open, and then click OK.
You can also type the URL directly into the Address bar and press the
Enter key.
30 WatchGuard Firebox X Edge
Page 59

Navigating the Configuration Pages
Using the navigation bar
On the left side of the System Status page is a navigation bar that
you use to see other Firebox X Edge configuration and status pages.
To see the main page for each area, click the appropriate menu item
on the navigation bar. For example, to see how logging is currently
configured for your Firebox and to see the current event log, click
Logging.
Each area contains submenus that you use to configure various settings within that area. To see these submenus, click the plus sign (+)
to the left of the area. For example, if you click the plus sign next to
WebBlocker, the following submenu items appear: Settings, Profiles,
Allowed Sites, Denied Sites, and Trusted Hosts.
This guide uses a series of arrow (>) symbols to show menu items
that you expand or click. The menu names are in bold. For example,
the command to open the Denied Sites page appears in the text as
WebBlocker > Denied Sites.
Logging in and setting a password
The Firebox X Edge has no administrative password until you set
one. To connect to the Firebox before it has a password:
1 Start your Internet browser.
2 Click File > Open, type https://192.168.111.1 in the text box
next to the word Open, and then click OK.
3 The End User License Agreement (EULA) appears. Read through
it, and if you agree, accept the EULA.
4 Type your administrative password on the screen that appears.
Type it again to confirm.
User Guide 31
Page 60

Configuration and Management Basics
Configuration Overview
You use the Firebox X Edge system configuration pages to set up
your Edge and make it work for your network and security requirements. This section gives a brief introduction to each category of
pages and tells you which chapters in this
detailed information about each feature.
Firebox System Status Page
The System Status page is the main configuration page of the Firebox X Edge. The center panel of the page shows information about
the current settings. It also contains buttons so you can change
these settings. This guide gives more detail on each setting in kater
chapters.
Basic information on this page includes the following:
• Firebox components and their current versions
• The serial number of the device
• The status of key Firebox X Edge features
• The status of upgrade options
• Network configuration information
• Which external network (external or failover) is currently active.
A green triangle appears next to the active network.
• Firewall configuration information
• A button to reboot the Firebox
User Guide
contain
32 WatchGuard Firebox X Edge
Page 61

Configuration Over view
Network Page
The Network page shows the configuration of each network interface. It also shows any configured routes and has buttons you can
to change configurations and to see network statistics. For more
information, see Chapter 4, “Changing Your Network Settings.”
User Guide 33
Page 62

Configuration and Management Basics
Firebox Users Page
The Firebox Users page shows statistics on the active sessions and
local user accounts. It also has buttons to close current sessions and
to add, edit, and delete user accounts.
This page also shows the MUVPN client configuration files that are
available for download. If you cannot yet use your Firebox for
MUVPN clients, the page has a button for you to make your Firebox
have MUVPN client support. For more information, see Chapter 11,
“Managing the Firebox X Edge.”
34 WatchGuard Firebox X Edge
Page 63

Configuration Over view
Administration Page
The Administration page shows whether the Firebox uses HTTP or
HTTPS for its configuration pages, whether VPN Manager access is
enabled, and which upgrades are enabled. It has buttons to change
configurations, add upgrades, and view the configuration file. For
more information, see Chapter 11, “Managing the Firebox X Edge.”
User Guide 35
Page 64

Configuration and Management Basics
Firewall Page
The Firewall page shows the incoming and outgoing services,
blocked sites, as well as other firewell settings. This page also has
buttons to change these settings. For more information, see Chapter
6, “Configuring Firewall Settings.”
36 WatchGuard Firebox X Edge
Page 65

Configuration Over view
Logging Page
The Logging page shows the current event log, status of WSEP and
Syslog logging, and the system time. It also has buttons to change
these settings and to set your system time so that it is the same as
your local computer. For more information, see Chapter 7, “Configuring Logging.”
User Guide 37
Page 66

Configuration and Management Basics
WebBlocker Page
The WebBlocker page shows the WebBlocker settings, profiles,
allowed sites, and denied sites. It also has buttons to change the
current settings. For more information, see Chapter 8, “Configuring
WebBlocker.”
38 WatchGuard Firebox X Edge
Page 67

Configuration Over view
VPN Page
The VPN page shows information on managed VPNs, manual VPN
gateways, and echo hosts along with buttons to change the configuration of VPN tunnels. It also has a button for you to see statistics
on active tunnels. For more information, see Chapter 9, “Configuring VPNs.
Wizards Page
The Wizards page shows the wizards available to help you quickly
and easily set up key Firebox X Edge features:
• Network Interface Wizard
Configure all interfaces, including WAN failover. For more information,
see “Using the Network Setup Wizard” on page 45.
• Service Configuration Wizard
Create a rule to filter network traffic between interfaces. For more
information, see “Adding a custom policy using the wizard” on page 81.
•QuickSetup Wizard
Set up your Firebox X Edge.
•Failover Setup Wizard
Set up the failover network.
• Wireless Setup Wizard
Set up the wireless interface.
User Guide 39
Page 68

Configuration and Management Basics
Updating Firebox X Edge Software
One benefit of your LiveSecurity® Service is ongoing software
updates. As new threats appear and WatchGuard adds product
enhancements, you receive alerts to let you know about new versions of your Firebox® X Edge software.
When you receive the alert, WatchGuard gives you instructions on
how to download the software to your personal computer. After this
download is complete, use the following instructions to update your
Firebox software:
1 Type the IP address of the trusted network in your browser
window to connect to the System Status page of the Firebox X
Edge.
The default IP address is https://192.168.111.1.
2 At the bottom of the System Status page, click Update.
The Administration Page appears with the End User License Agreement
(EULA). You can also go to this page by selecting Administration >
Update from the navigation bar at left.
40 WatchGuard Firebox X Edge
Page 69

3 Read the text of the EULA. If you agree, select the I accept the
above license agreement checkbox.
4 Type the name of the file containing the new Firebox X Edge
software in the Select file box or click Browse to find the file
on your local computer.
5 Click Update.
The Firebox makes sure the software package is a legimate software
upgrade. It then copies the new software to the system and reboots. This
can take 15 to 45 seconds. When the update is complete, the System
Status page appears and shows the new version number.
Factory Default Settings
Factory Default Settings
The term
factory default settings
refers to how the Firebox® X Edge
is configured when you first receive it—before you have made any
changes of your own to the configuration. The default network and
configuration settings for the Firebox X Edge are as follows:
Trusted network
- The default IP address for the trusted network is 192.168.111.1.
The subnet mask for the trusted network is 255.255.255.0.
- The Firebox X Edge is configured to give IP addresses to
computers on the trusted network through DHCP. You can also
give static addresses to computers in the trusted network with
IP addresses in the 192.168.111.2–192.168.111.254 range.
External network
- The external network settings use DHCP.
Optional network
- The optional network is disabled.
Firewall settings
- All incoming services are blocked.
- An outgoing service allows all outbound traffic.
- All of the options on the Firewall Options page are disabled.
System Security
- The System Security is disabled. The system administrator name
and system administrator passphrase are not set. All computers
on the trusted network can see the configuration pages.
- Remote Management is disabled.
User Guide 41
Page 70

Configuration and Management Basics
- VPN Manager Access is disabled.
- Remote logging is not configured.
WebBlocker
- The WebBlocker feature is disabled and the settings are not
configured.
Upgrade Options
- The upgrade options are disabled until you type the license
keys into the configuration page.
Resetting the Firebox to the factory default settings
You might have a reason to set the Firebox to the factory default
settings. For example, you might be unable to correct a configuration problem and just want to “start over.” Sometimes, a reset is
your only choice: such as if the system security passphrase is
unknown or the firmware of the Firebox X Edge is damaged by a
power interruption.
You should have a copy of the most recent Firebox X Edge software
on your local computer before you try to return to factory default
settings.
Follow these steps to set the Firebox to the factory default settings:
1 Disconnect the power supply.
2 Hold down the Reset button, located on the front of the
Firebox.
3 Connect the power supply while you continue to hold down the
Reset button.
4 Continue to hold down the button until the red light on the
front of the Firebox blinks in a steady pattern (about 15
seconds).
5 Disconnect the power supply.
6 Reconnect the power supply.
The Power indicator is on and the reset is complete.
Rebooting the Firebox
You can reboot the Firebox® X Edge from a computer on the trusted
network. You can also reboot the Firebox from a computer with the
Internet to connect to the Firebox external interface.
42 WatchGuard Firebox X Edge
Page 71

Rebooting the Firebox
The Firebox reboot cycle is up to 30 seconds. During the reboot
cycle, the mode light on the front of the Firebox turns off and then
turns on again.
Local reboot
You can locally reboot the Firebox X Edge either with the Web
browser or by disconnecting the power supply.
Using the Web browser
1 Type the IP address of the trusted network in your browser
window to connect to the System Status page of the Firebox X
Edge.
The default IP address is: https://192.168.111.1
2 Click Reboot.
Disconnecting the power supply
Disconnect the Firebox power supply. After a minimum of 10 seconds, connect the power supply.
Remote reboot
You must configure the remote Firebox X Edge to send incoming
HTTP (Web) or FTP traffic to the Firebox’s trusted interface IP
address if you want to use the following method to reboot it. For
more information on how to configure the Firebox to receive incoming traffic, see “Configuring Incoming and Outgoing Policies” on
page 65. Also, see the following FAQ for more information on configuring a Firebox X Edge to receive incoming traffic:
User Guide 43
Page 72

Configuration and Management Basics
https://www.watchguard.com/support/tutorials/
stepsoho_remotemanage.asp
1 Type the external network IP address of the remote Firebox X
Edge in your browser window to connect to its System Status
page.
2 Click Reboot.
44 WatchGuard Firebox X Edge
Page 73

CHAPTER 4 Changing Your
Network Settings
A primary task to set up your WatchGuard® Firebox® X Edge is to configure the network IP addresses. At a minimum, you must configure
the external network and the trusted network to let traffic flow
through the Edge. You can also set up the optional interface. Many
customers use the optional network for public servers. An example of a
public server is a Web server.
You can use the Quick Setup Wizard to set up your network IP
addresses. You can also manually set up or change your network IP
addresses on the Network page.
Using the Network Setup Wizard
The easiest procedure to set up your network IP addresses is with the
Network Setup Wizard.
1 To connect to the System Status page, type the IP address of the
trusted network in the browser.
The default IP address is: https://192.168.111.1.
2 From the navigation bar, select Wizards.
3 Next to Setup the primary network interfaces of the Firebox X
Edge, click Go.
User Guide 45
Page 74

Changing Your Network Settings
4 Work through the wizard, following the instructions on the
screens. Steps associated with optional functionality you decide
not to enable are automatically skipped by the wizard.
The Network Setup Wizard consists of the following steps:
Step 1: Welcome
The first screen describes the purpose of the wizard.
Step 2: Configure the External Interface of your Firebox
The next screen asks the method your ISP uses to set your IP
address. For more information, see the next section in this guide,
“Configuring the External Network.”
Step 3a: Configure the External Interface for DHCP
On the next screen, type in your DHCP identification as provided
by your ISP. For more information, see “If your ISP uses DHCP”
on page 47.
Step 3b: Configure the External Interface for PPPoE
On the next screen, type in your PPPoE information as provided
by your ISP. For more information, see “If your ISP uses PPPoE”
on page 48.
Step 3c: Configure the External Interface with a static IP
address
On the next screen, type in your static IP address information as
provided by your ISP. For more information, see “If your ISP uses
static IP addresses” on page 48.
Step 4: Configure the Trusted Interface of the Firebox
On the next screen, type the IP address of the trusted interface.
For more information, see “Configuring the Trusted Network” on
page 50.
Step 5: Change the User Name and Passphrase
The next screen enables you to set a username and passphrase
for the Edge.
Step 6: The Network Setup Wizard is complete
Configuring the External Network
You must configure your external network manually if you choose
not to use the Network Setup wizard.
46 WatchGuard Firebox X Edge
Page 75

Configuring the External Network
When you configure the external network, set how your Internet
Service Provider (ISP) gives an IP address to your Firebox. There are
three methods to give IP addresses:
• DHCP - Network administrators use the Dynamic Host
Configuration Protocol (DHCP) to give IP addresses to
computers on their network automatically. With DHCP, your
Firebox can receive a new external address each time it connects
to the ISP network.
• Static IP address - Network administrators use static IP
addresses to manually give an IP address to each computer on
their network. Because more work is necessary with this
procedure, an ISP frequently charges more for a static IP
address. Static IP addresses are also known as manual addresses.
• PPPoE - Many ISPs use the Point to Point Protocol over
Ethernet (PPPoE) to give IP addresses to each computer on their
network. Frequently they use PPPoE with a dial-up network
infrastructure.
To configure your Firebox® X Edge, you must know how it gets the
IP address for the external interface. If you do not know the
method, get the information from your ISP or corporate network
administrator.
If your ISP uses DHCP
The default configuration sets the Firebox X Edge to get the external address information through DHCP. If your ISP uses DHCP, your
Edge gets a new external IP address when it starts and connects to
the ISP network.
For more information about DHCP, see “About DHCP” on page 5.
To manually set your Firebox to use DHCP on the external interface:
1 To connect to the System Status page, type the IP address of
the trusted network in the browser.
The default IP address is: https://192.168.111.1
2 From the navigation bar, select Network > External.
The External Network Configuration page appears.
3 From the Configuration Mode drop-down list,
select DHCP Client.
4 Click Submit.
User Guide 47
Page 76

Changing Your Network Settings
If your ISP uses static IP addresses
If your ISP uses static IP addresses, you must enter the address information into your Edge before it can send traffic through the external interface.
To set your Edge to use a static IP address for the external interface:
1 Use your browser to connect to the System Status page. From
the navigation bar, select Network > External.
The External Network Configuration page appears.
2 From the Configuration Mode drop-down list, select
Manual Configuration.
3 Type the IP address, Subnet Mask, Default Gateway, Primary
DNS, Secondary DNS and DNS Domain Suffix into the related
Get this information from your ISP or corporate network
fields.
administrator.
If you completed the table on page 14, type the information from the
table.
4 Click Submit.
If your ISP uses PPPoE
If your ISP uses PPPoE, you must enter the PPPoE information into
your Firebox before it can send traffic through the external interface. For more information in PPPoE, see “About PPPoE” on page 6.
48 WatchGuard Firebox X Edge
Page 77

Configuring the External Network
To set your Firebox to use PPPoE on the external interface:
1 Use your browser to connect to the System Status page. From
the navigation bar, select Network > External.
The External Network Configuration page appears.
2 From the Configuration Mode drop-down list,
select PPPoE Client.
3 Type the Name and Password in the related fields. Get this
information from your ISP. If your ISP gives you a domain
name, type it into the Domain field.
Most ISPs make the domain name section of the PPPoE name (e.g.
myname@ispdomain). If you have a PPPoE name with this format, type
the myname section in the Name field. Type the ispdomain section in
the Domain field. Do not type the @ symbol. Some ISPs do not use the
Domain.
4 Type the time before the Firebox disconnects inactive TCP
connections.
We recommend a value of 20.
5 If necessary, select the Automatically restore lost connections
check box.
The Firebox can keep a constant traffic flow to the PPPoE server. This
flow keeps the PPPoE connection open when there is frequent packet
loss. If the traffic flow stops, the Firebox restarts to make the connection
again. The PPPoE server reads the constant traffic flow as a continuous
connection. Many ISPs charge more if you use this option.
6 WatchGuard Technical Support uses the Enable PPPoE debug
trace check box to troubleshoot PPPoE problems. With this
User Guide 49
Page 78

Changing Your Network Settings
option on, the Firebox makes a file which you can send to
Technical Support. Only use this option when Technical Support
tells you. This option decreases Firebox performance.
7 Click Submit.
Configuring the Trusted Network
You must configure your trusted network manually if you choose
not to use the Network Setup wizard.
You can use static IP addresses or DHCP for your trusted network.
The Firebox® X Edge has a DHCP server to give IP addresses to computers on your trusted and optional networks. You can also change
the IP address of the trusted network.
With a factory default Firebox, its DHCP server automatically gives
IP addresses to computers on the trusted network. The trusted network starts with IP address 192.168.111.1. It is a “class C” network
with a subnet mask of 255.255.255.0. The Firebox can give an IP
address from 192.168.111.2 to 192.168.111.252. The factory default
configuration uses the same DNS and domain name as it uses for
the external interface. For more information, see “IP Addresses” on
page 5.
If necessary, you can disable the Firebox DHCP server. The Firebox
can forward the DHCP requests to a DHCP server on a different network. You can also use static IP addresses for the computers on your
trusted network.
N
OTE
N
OTE
You can make one or more changes to the trusted network,
Submit each change, then Reboot only once to enable all of the
changes. You must Reboot the Firebox to enable a change to the
trusted network configuration.
u can make many changes and click Submit. Any change to the
Yo
trusted network configuration All changes to the Trusted Network
Configuration page require that you click Submit and then reboot
the Firebox before they take effect.But you can make all the
changes you want to make and then reboot just once when you are
done.
50 WatchGuard Firebox X Edge
Page 79

Configuring the Trusted Network
Changing the IP address of the trusted network
If necessary, you can change the trusted network address. For example, if you connect two or more Firebox devices in a virtual private
network, each Firebox must use a different trusted network address.
For more information, see “What You Need to Create a VPN” on
page 107.
To change the IP address of the trusted network:
1 To connect to the System Status page, type the IP address of
the trusted network in the browser.
The default IP address is: https://192.168.111.1
2 From the navigation bar, select Network > Trusted.
The Trusted Network Configuration page appears.
3 Type the first address of the new network address range in the
IP Address text field.
4 If necessary, type the new subnet mask.
Most networks use 255.255.255.0 which includes 252 addresses.
Using DHCP on the trusted network
The DHCP Server option sets the Firebox X Edge to give IP addresses
to the computers on the trusted network. When the Firebox receives
a DHCP request from a computer on the trusted network, it gives
the computer an IP address. A factory default Firebox has the DHCP
Server option for the trusted interface on.
User Guide 51
Page 80

Changing Your Network Settings
To use DHCP on the trusted network:
1 Use your browser to connect to the System Status page. From
the navigation bar, select Network > Trusted.
The Trusted Network Configuration page appears.
2 Select the Enable DHCP Server on the Trusted Network check
box.
3 Type the first available IP address for the trusted network. Type
last IP address.
The IP addresses must be on the same network as the trusted IP address.
For example, if your trusted IP address is 192.168.200.1, the IP addresses
can be from 192.168.200.2 to 192.168.200.252.
4 Type the WINS Server Address, DNS Server Primary Address,
DNS Server Secondary Address, and DNS Domain Suffix in the
related fields.
Use these field if you have a WINS or DNS server. If you do not enter a
value, the Firebox uses the same values as those used for the external
network.
5 Click Submit.
52 WatchGuard Firebox X Edge
Page 81

Configuring the Trusted Network
Setting trusted network DHCP address reservations
You can manually give an IP address to a specified computer on
your trusted network. The Firebox identifies the computer by its
MAC address.
1 Use your browser to connect to the System Status page. From
the navigation bar, select Network > Trusted.
The Trusted Network Configuration page appears.
2 Click the DHCP Reservations button.
The DHCP Address Reservations page appears.
3 Type a static IP address in the IP Address field. The IP address
must be on the trusted network.
For example, if the trusted network starts with 192.168.111.1, you can
enter 192.168.111.2 to 192.168.111.251.
4 Type the MAC address of the computer on the trusted network
in the MAC Address field. Click Add.
5 Click Submit.
Configuring the trusted network for DHCP relay
One method to get IP addresses for the computers on the Firebox
trusted network is to use a DHCP server on a different network. The
Firebox can send a DHCP request to a DHCP server at a different
location. It gives the reply to the computers on the Firebox trusted
User Guide 53
Page 82

Changing Your Network Settings
network. This option lets computers in more than one office use the
same network address range. This procedure makes the Firebox a
DHCP relay agent
.
To configure the Firebox as a DHCP relay agent for the trusted
interface:
1 Use your browser to connect to the System Status page. From
the navigation bar, select Network > Trusted.
The Trusted Network Configuration page appears.
2 Select the Enable DHCP Relay check box.
3 Type the IP address of the DHCP server in the related field.
4 Click Submit.
The Firebox restarts. If the Firebox can not connect to the DHCP server in
30 seconds, it uses its DHCP server to give IP addresses to computers on
the trusted network.
Using static IP addresses for trusted computers
You can use static IP addresses for some or all of the computers on
your trusted network. If you disable the DHCP server, you must
manually configure the IP address and subnet mask of each computer. You can also configure specified computers with a static IP
address. For example, this is necessary when a client server software
application must use a static IP address for the server. Static IP
addresses must be on the same network as the Firebox trusted interface.
To disable the Firebox DHCP server, clear the Enable DHCP Server
on the Trusted Network check box on the Trusted Network Configuration page.
Adding computers to the trusted network
The Firebox X Edge can connect to one to seven trusted computers.
You can use 10/100 BaseT Ethernet hubs or switches with RJ-45
connectors to connect more than seven computers. It is not necessary that the computers on the trusted network use the same operating system.
To add more than seven computers to the trusted network:
1 Make sure that each computer has a functional Ethernet card.
2 Set each computer to use DHCP. For more information, see
“Setting your computer to use DHCP,” on page 20.
54 WatchGuard Firebox X Edge
Page 83

Configuring the Optional Network
3 Connect each computer to the network. Use the procedure
“Cabling the Firebox X Edge for more than seven devices” on
page 18.
4 Restart each computer.
Configuring the Optional Network
The optional network is an isolated network for less secure public
resources. Many customers use the optional network for public computers such as a Web, e-mail, or FTP server. A factory default Firebox does not connect the trusted network to the optional network.
While you can enable traffic between these networks, this procedure
decreases security for the trusted network. For more information,
see “Adding a Policy for the Optional Interface” on page 83.
You can use the Firebox® X Edge DHCP server or you can use static
IP addresses for computers on the optional network. You can also
change the IP address range of the optional network.
Many public servers must have a static IP address. For increased
security, we recommend that you disable DHCP on the optional network. If it is necessary to protect your servers from Internet traffic,
you can put your user computers on the optional network and your
servers on the more secure trusted network.
N
OTE
N
OTE
You can make one or more changes to the optional network,
Submit each change, then Reboot only once to enable all of the
changes. You must Reboot the Firebox to enable a change to the
optional network configuration.
Enabling the optional network
1 To connect to the System Status page, type the IP address of
the trusted network in the browser.
The default IP address is: https://192.168.111.1
2 From the navigation bar, select Network > Optional.
The Optional Network Configuration page appears.
3 Select the Enable Optional Network check box.
Changing the IP address of the optional network
If necessary, you can change the optional network address. For
example, you can isolate a wireless network from the trusted net-
User Guide 55
Page 84

Changing Your Network Settings
work. A factory default Firebox has the trusted network and the
optional network on 2 different subnets.
To change the IP address of the optional network:
1 To connect to the System Status page, type the IP address of
the trusted network in the browser.
The default IP address is: https://192.168.111.1
2 From the navigation bar, select Network > Optional.
The Optional Network Configuration page appears.
3 Type the first address of the new network address range in the
IP Address text field.
4 If necessary, type the new subnet mask.
Most networks use 255.255.255.0 which includes 252 addresses.
Using DHCP on the optional network
The DHCP Server option sets the Firebox X Edge to give IP addresses
to the computers on the optional network. When the Firebox
receives a DHCP request from a computer on the optional network,
it gives the computer an IP address. A factory default Firebox has
the DHCP Server option for the optional interface off.
56 WatchGuard Firebox X Edge
Page 85

Configuring the Optional Network
To use DHCP on the optional network:
1 Use your browser to connect to the System Status page. From
the navigation bar, select Network > Optional.
The Optional Network Configuration page appears.
2 Select the Enable DHCP Server on the Optional Network check
box.
3 Type the first available IP address for the optional network. Type
last IP address.
The IP addresses must be on the same network as the optional IP
address. For example, if your optional IP address is 192.168.112.1, the IP
addresses can be from 192.168.112.2 to 192.168.112.252.
4 Type the WINS Server Address, DNS Server Primary Address,
DNS Server Secondary Address, and DNS Domain Suffix in the
related fields.
Use these field if you have a WINS or DNS server. If you do not enter a
value, the Firebox uses the same values as those used for the external
network.
5 Click Submit.
User Guide 57
Page 86

Changing Your Network Settings
Setting optional network DHCP address reservations
You can manually give an IP address to a specified computer on
your optional network. The Firebox identifies the computer by its
MAC address.
1 Use your browser to connect to the System Status page. From
the navigation bar, select Network > Optional.
The Optional Network Configuration page appears.
2 Click the DHCP Reservations button.
The DHCP Address Reservations page appears.
3 Type a static IP address in the IP Address field. The IP address
must be on the optional network.
For example, if the optional network starts with 192.168.112.1, you can
enter 192.168.112.2 to 192.168.112.251.
4 Type the MAC address of the computer on the optional network
in the MAC Address field. Click Add.
5 Click Submit.
Configuring the optional network for DHCP relay
One method to get IP addresses for the computers on the Firebox
optional network is to use a DHCP server on a different network.
The Firebox can send a DHCP request to a DHCP server at a different
58 WatchGuard Firebox X Edge
Page 87

Configuring the Optional Network
location. It gives the reply to the computers on the Firebox optional
network. This option lets computers in more than one office use the
same network address range. This procedure makes the Firebox a
DHCP relay agent
.
To configure the Firebox as a DHCP relay agent for the optional
interface:
1 Use your browser to connect to the System Status page. From
the navigation bar, select Network > Optional.
The Optional Network Configuration page appears.
2 Select the Enable DHCP Relay on Optional Network check box.
3 Type the IP address of the DHCP server in the related field.
4 Click Submit.
The Firebox restarts. If the Firebox can not connect to the DHCP server in
30 seconds, it uses its DHCP server to give IP addresses to computers on
the optional network.
Using static IP addresses for optional computers
You can use static IP addresses for some or all of the computers on
your optional network. If you disable the DHCP server, you must
manually configure the IP address and subnet mask of each computer. You can also configure specified computers with a static IP
address. For example, this is necessary when a client server software
application must use a static IP address for the server. Static IP
addresses must be on the same network as the Firebox optional
interface.
To disable the Firebox DHCP server, clear the Enable DHCP Server
on the Optional Network check box on the Optional Network Configuration page.
Adding computers to the optional network
The Firebox X Edge can connect to 1 optional computer. You can
use 10/100 BaseT Ethernet hubs or switches with RJ-45 connectors
to connect more than 1 computer. It is not necessary that the computers on the optional network use the same operating system.
To add more than 1 computers to the optional network:
1 Make sure that each computer has a functional Ethernet card.
2 Set each computer to use DHCP. For more information, see
“Setting your computer to use DHCP,” on page 20.
User Guide 59
Page 88

Changing Your Network Settings
3 Connect each computer to the network. Use the procedure
“Cabling the Firebox X Edge for more than seven devices” on
page 18.
4 Restart each computer.
N
OTE
N
All changes to the Optional Network Configuration page require
that you click Submit and then reboot the Firebox before they
take effect. But you can make all the changes you want to make
and then reboot just once when you are done.
You can either enable or disable the DHCP server on the optional
network.
Requiring encrypted connections
You can set the optional interface to use only encrypted connections. Frequently a customer uses this option to make a secure wireless network. The wireless connections use the Mobile User VPN
client. The client encrypts all traffic from the optional interface to
the Firebox. A “drive-by” hacker can not read the encrypted traffic
on the wireless network.
Making Static Routes
OTE
You can configure the Firebox to send specified traffic to different
parts of the Firebox® X Edge trusted network connected by a router
or switch. Use the Routes page to make a static route:
1 To connect to the System Status page, type the IP address of
the trusted network in the browser.
The default IP address is: https://192.168.111.1
60 WatchGuard Firebox X Edge
Page 89

Making Static Routes
2 From the navigation bar, select Network > Routes.
The Routes page appears.
3 Click Add.
The Add Route page appears.
4 From the Type drop-down list, select either Host or Network.
A host is 1 computer. A network is more than one computer which use a
range of IP addresses.
5 Type the destination IP address and the gateway in the related
fields.
The Gateway is the ylocal interface of the router.
6 Click Submit.
To remove a static route, click the IP address and click Remove.
User Guide 61
Page 90

Changing Your Network Settings
Viewing Network Statistics
The Firebox® X Edge Network Statistics page shows information
about the performance. Network administrators frequently use this
page to troubleshoot a problem with the Firebox or network.
1 To connect to the System Status page, type the IP address of
the trusted network in the browser.
The default IP address is: https://192.168.111.1
2 From the navigation bar, select Network > Network Statistics.
The Network Statistics page appears.
Registering with the Dynamic DNS Service
You can register the external IP address of the Firebox® X Edge with
the dynamic Domain Name Server (DNS) service DynDNS.org. A
dynamic DNS service makes sure that the IP address attached to
your domain name changes when your ISP gives you a new IP
address. For more information, click Information about Dynamic
DNS available here.
You can also see these WatchGuard FAQs:
What is Dynamic DNS?
How do I set up Dynamic DNS?
https://www.watchguard.com/support/AdvancedFaqs/sogen_main.asp
62 WatchGuard Firebox X Edge
Page 91

Registering with the Dynamic DNS Service
After you click this link, log into your LiveSecurity Service account
to see the FAQ.
N
OTE
N
OTE
WatchGuard is not affiliated with DynDNS.org.
1 Create a dynamic DNS account.
For more information, see the Technical Support FAQ “How do I set up
Dynamic DNS?
1 To connect to the System Status page, type the IP address of
the trusted network in the browser.
The default IP address is: https://192.168.111.1
2 From the navigation bar, select Network > Dynamic DNS.
The Dynamic DNS client page appears.
3 Select the Enable Dynamic DNS client check box.
4 Type the Domain, Name, and Password in the related fields.
N
OTE
N
OTE
The Firebox gets the IP address of members.dyndns.org when it
connects to the time server.
5 System???
6 Options???
7 Click Submit.
User Guide 63
Page 92

Changing Your Network Settings
Enabling the WAN Failover Option
The WAN Failover option adds redundant support for the external
interface. With this option, the Firebox® X Edge starts a connection
through the WAN2 port when the primary external interface (WAN1)
can not send traffic. Companies use this option if they must have a
constant connection. You must get a second Internet connection to
use this option.
It is not necessary to configure new services to use this option. The
failover interface uses the same services and network properties as
the external interface.
The Firebox uses two methods to find out if the external interface is
functional:
• The status of the link to the nearest router
• A ping command to a specified location
The Firebox pings the default gateway or a computer specified by
the administrator. If there is no reply, the Firebox changes to the
secondary external network interface (WAN2).
When you enable the WAN Failover, the Firebox does the following:
• If the WAN1 interface connection stops, the Firebox starts to
use WAN2 interface.
• If the WAN2 interface connection stops, the Firebox starts to
use the WAN1 interface.
• If the WAN1 interface and the WAN2 interface stop, the Firebox
tries the 2 interfaces until it makes a connection.
When the WAN2 is in use, the Firebox does not switch back to the
WAN1 port unless PPPoE is used to assign IP addresses. After the
Firebox switches to the WAN2 port, the administrator must change
the configuration back to the WAN1 port when the connection is
restored.
If you use PPPoE, you can set an inactivity timeout that disables
inactive TCP connections during periods of inactivity. See “If your
ISP uses PPPoE” on page 48 for PPPoE configuration information. If
your external connection fails, the WAN2 port connection is started
and used. The WAN2 port is used until the TCP connection becomes
inactive (timeout). When the traffic continues, the Firebox connects
64 WatchGuard Firebox X Edge
Page 93

Enabling the WAN Failover Option
through the WAN1 port first. If a connection is made, the WAN1port
is used. If the WAN1 port is not available, the Firebox connects
through the WAN2 port.
To configure the WAN failover network:
1 Connect one end of a straight through Ethernet cable to the
WAN2 interface. Connect the other end to the source of the
secondary external network connection. This connection can be
a cable modem or a hub.
2 To connect to the System Status page, type the IP address of
the trusted network in the browser.
The default IP address is: https://192.168.111.1
3 From the navigation bar, select Network > WAN Failover.
The WAN Failover page appears.
4 Select the Enable failover using the Ethernet (WAN2)
interface check box.
User Guide 65
Page 94

Changing Your Network Settings
5 From the drop-down list, select the interface for the feature:
Ethernet or modem (see the next section for additional
information on using a modem).
6 Type the IP addresses of the hosts to ping for WAN1 and WAN2
interfaces in the applicable fields.
7 Type the number of seconds between pings and the number of
seconds to wait for a reply in the applicable fields.
8 Type the limit number of pings before timeout in the applicable
field.
9 Click Submit.
Enabling External Modem Failover
Using the Firebox X Edge, you can specify that upon failover the
Edge can contact a remote secondary host for routing traffic by way
of a modem. For a list of the types of modem supported, see [FAQ?]
1 From the drop-down list on the WAN Failover page, select
Modem (serial port).
2 Under Dial Up Account Settings, use the drop-down list to
select your ISP. The following ISPs are supported: Standard PPP,
AOL, AT&T Worldnet, CompuServe 4.0, EarthLink, MSN, and
Qwest.
3 Type the telephone number of your ISP. Optionally, you can also
type an alternate telephone number.
4 Type the account name used by your ISP for your modem.
5 (Optional) If you use the login to your account with a domain
name (such as aol.com), enter it in Account Domain.
6 Enter the account password.
7 If you want to enable automatically restoring lost connections,
select the corresponding checkbox.
8 If you want to enable modem and PPP debug trace, select the
corresponding checkbox.
66 WatchGuard Firebox X Edge
Page 95

Enabling External Modem Failover
DNS settings
If your server is not using DHCP and doesn’t specify the location of
the DNS server, you must manually enter IP addresses for your DNS
server:
1 Select the Manually configure DNS server IP addresses
checkbox.
2 In the Primary DNS Server text box, enter the IP address of the
primary DNS server.
3 (Optional) In the Secondary DNS Server text box, enter the IP
address of the secondary DNS server.
User Guide 67
Page 96

Changing Your Network Settings
Dialup settings
1 In the Dial up timeout field, enter the number of seconds
before timeout if your modem doesn’t connect.
2 In the Redial attempts field, enter the number of attempts
made if your modem doesn’t connect
3 In the Inactivity timeout field, enter the number of seconds
before timeout if no traffic passes through the modem.
4 In the Speaker volume field, set your modem speaker’s volume
to off, low, medium, or high.
68 WatchGuard Firebox X Edge
Page 97

CHAPTER 5 Setting up the Firebox
X Edge Wireless
The Firebox X Edge Wireless protects the computers that are connected
to your network. The Firebox X Edge Wireless also protects network
wireless connections. This chapter shows how to install the Firebox X
Edge Wireless and set up the wireless network.
WatchGuard is concerned about the security of your network so the
wireless feature of the Firebox X Edge Wireless is disabled until you are
ready to use it. Activate the wireless feature when you configure the
security of the wireless connections.
To install the Firebox X Edge Wireless:
• Identify and record your TCP/IP settings
• Disable the HTTP proxy setting of your Web browser
• Activate DHCP on your computer
• Make the physical connections between the Firebox X Edge
Wireless and your network
• Attach the two antennae to the Firebox X Edge Wireless
• Install the Firebox X Edge Wireless in a location more than 20
centimeters from all persons. Put the Firebox X Edge Wireless in a
location away from all other antennae or transmitters.
To set up the wireless network:
• Configure the wireless network
User Guide 69
Page 98

Setting up the Firebox X Edge Wireless
• Configure the Wireless Access Point (WAP)
• Configure the wireless card on your computer
How
Wireless Networking Works
Wireless networking uses radio-frequency signals to communicate
with computers and the Firebox X Edge Wireless. The Firebox X Edge
Wireless complies with 802.11b and 802.11g standards defined by
the Institute of Electrical and Electronics Engineers (IEEE).
You must protect a wireless network from unauthorized access.
Without this protection, unauthorized users compromise the security
of your network or make use of your Internet connection.
You increase the security of your corporate network by requiring
users to authenticate as MUVPN clients. A VPN creates a secure
IPSec tunnel from the wireless computer to the Firebox X Edge
Wireless. Another way to increase security is to separate the trusted
network from the optional network.
Connecting to the Firebox X Edge Wireless
The Firebox X Edge Wireless protects all the computers that connect
to your network through the Ethernet ports and wireless connections of the Firebox. This section shows how to connect computers
to the Firebox X Edge Wireless using Ethernet cables.
The Firebox X Edge Wireless protects one computer or all the computers on a network. The Firebox X Edge Wireless also operates as a
hub to connect other computers.
To set up a wireless network, you connect a computer to the Firebox
X Edge Wireless with an Ethernet cable. The computer (the management station) that is connected through an Ethernet cable is used to
configure the wireless network.
Cabling the Firebox X Edge Wireless for one to seven devices
A maximum of seven computers, printers, scanners or other devices
can connect directly to the Firebox X Edge Wireless. These connections use the seven Ethernet ports (labeled 0-6). There are also two
WAN ports (WAN1 and WAN2) you use to create dual ISP connections that provide uninterrupted connectivity. To connect a maxi-
70 WatchGuard Firebox X Edge
Page 99

Connecting to the Firebox X Edge Wireless
mum of seven devices, use the Firebox X Edge Wireless as a network
hub.
1 Shut down your computer.
2 If you connect to the Internet through a DSL modem or cable
modem, disconnect the power supply to this device.
3 Disconnect the Ethernet cable that connects your DSL modem,
cable modem or other Internet connection to your computer.
Connect this cable to the WAN port on the Firebox X Edge
Wireless.
The Firebox X Edge Wireless is connected directly to the modem or other
Internet connection.
4 Connect one end of the straight-through Ethernet cable
supplied with your Firebox X Edge Wireless to one of the seven
numbered Ethernet ports (labeled 0-6) on the Firebox X Edge
Wireless. Connect the other end to the Ethernet port of your
computer.
The Firebox X Edge Wireless is connected to the Internet and your
computer.
5 If you connect to the Internet through a DSL modem or cable
modem, reconnect the power supply to this device. The
indicator lights flash and then stop. The modem is available for
use.
6 Attach the AC adapter to the Firebox X Edge Wireless. Connect
the AC adapter to a power source.
7 Restart the computer.
See “Configuring the External Network” on page 46 and “Configuring the Trusted Network” on page 50 for special configurations.
Cabling the Firebox X Edge Wireless for more than seven devices
Although the Firebox X Edge Wireless has only seven Ethernet ports
(labeled 0-6), you can connect more than seven devices. Use one or
more network hubs to make more connections.
The base model Firebox X Edge Wireless includes a ten-seat license.
This license allows a maximum of ten devices on the trusted network to connect to the Internet at the same time. There can be more
than ten devices on the trusted network, but the Firebox X Edge
Wireless allows only ten Internet connections. A seat is in use when
User Guide 71
Page 100

Setting up the Firebox X Edge Wireless
a devices connects to the Internet and is free when the connection
ends. License upgrades are available from the WatchGuard Web site:
http://www.watchguard.com/sales/buyonline.asp
To connect more than seven devices to the Firebox X Edge Wireless,
you need:
• An Ethernet hub
• A straight-through Ethernet cable, with RJ-45 connectors, for
each computer
• A straight-through Ethernet cable to connect each hub to the
Firebox X Edge Wireless.
To connect more than seven devices to the Firebox X Edge:
1 Shut down your computer. If you connect to the Internet
through a DSL modem or cable modem, disconnect the power
supply from this device.
2 Disconnect the Ethernet cable that runs from your DSL modem,
cable modem, or other Internet connection to your computer.
Connect the Ethernet cable to the WAN port on the Firebox X
Edge Wireless.
The Firebox X Edge Wireless is connected directly to the modem or other
Internet connection.
3 Connect one end of the straight-through Ethernet cable
supplied with your Firebox X Edge Wireless to one of the seven
numbered Ethernet ports (labeled 0-6) on the Firebox X Edge
Wireless. Connect the other end to the uplink port of the
Ethernet hub.
The Firebox X Edge Wireless is connected to the Internet and your
Ethernet hub.
4 Connect an Ethernet cable between each of the computers and
an uplink port on the Ethernet hub.
5 If you connect to the Internet through a DSL modem or cable
modem, reconnect the power supply to this device. The
indicator lights flash and then stop. The modem is available for
use.
6 Attach the AC adapter to the Firebox X Edge Wireless. Connect
the AC adapter to a power supply.
7 Restart your computer.
72 WatchGuard Firebox X Edge
 Loading...
Loading...