Watchguard Firebox V10, Firebox V100, Firebox V200, Firebox V60, Firebox V60L Installation Manual
...
1install_guide.book Page i Friday, June 7, 2002 1:10 PM
Firebox® Vclass
Installation Guide
Vcontoller™ 3.2
Notice to Users
1install_guide.book Page ii Friday, June 7, 2002 1:10 PM
Notice to Users
Information in this guide is subject to change without notice. Companies, names, and data used in examples herein are
fictitious unless otherwise noted. No part of this guide may be reproduced or transmitted in any form or by any means,
electronic or mechanical, for any purpose, without the express written permission of WatchGuard Technologies, Inc.
Copyright, Trademark, and Patent Information
Copyright© 1998 - 2002 WatchGuard Technologies, Inc. All rights reserved.
Firebox, Firebox 1000, Firebox 2500, Firebox 4500, Firebox II, Firebox II Plus, Firebox II FastVPN, Firebox III,
Firebox SOHO, Firebox SOHO|tc, Firebox V100, Firebox V80, Firebox V60, Firebox V10, LiveSecurity,
RapidStream, RapidCore, WatchGuard, WatchGuard Technologies, Inc., AppLock, AppLock/Web, Designing peace of
mind, DVCP technology, Enforcer/MUVPN, FireChip, HackAdmin, HostWatch, LockSolid, RapidCare, SchoolMate,
ServerLock, ServiceWatch, Smart Security. Simply Done., SpamScreen, Vcontroller are either registered trademarks
or trademarks of WatchGuard Technologies, Inc. in the United States and/or other courtries.
© Hi/fn, Inc. 1993, including one or more U.S. Patents: 4701745, 5016009, 5126739, and 5146221 and other
patents pending.
Microsoft®, Internet Explorer®, Windows® 95, Windows® 98, Windows NT® and Windows® 2000 are either
registered trademarks or trademarks of Microsoft Corporation in the United States and/or other countries.
Netscape and Netscape Navigator are registered trademarks of Netscape Communications Corporation in the United
States and other countries.
RC2 Symmetric Block Cipher, RC4 Symmetric Stream Cipher, RC5 Symmetric Block Cipher, BSAFE, TIPEM, RSA
Public Key Cryptosystem, MD, MD2, MD4, and MD5 are either trademarks or registered trademarks of RSA Data
Security, Inc. Certain materials herein are Copyright © 1992-1999 RSA Data Security, Inc. All rights reserved.
RealNetworks, RealAudio, and RealVideo are either a registered trademark or trademark of RealNetworks, Inc. in the
United States and/or other countries.
Java and all Jave-based marks are trademarks or registered trademarks of Sun Microsystems, Inc. in the United
States and other countries. All right reserved.
© 1995-1998 Eric Young (eay@cryptsoft). All rights reserved.
© 1998-2000 The OpenSSL Project. All rights reserved. Redistribution and use in source and binary forms, with or
without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following
disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following
disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following acknowledgment:
"This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit. (http://
www.openssl.org/)"
4. The names "OpenSSL Toolkit" and "OpenSSL Project" must not be used to endorse or promote products derived from
this software without prior written permission. For written permission, please contact openssl-core@openssl.org.
5. Products derived from this software may not be called "OpenSSL" nor may "OpenSSL" appear in their names without
prior written permission of the OpenSSL Project.
6. Redistributions of any form whatsoever must retain the following acknowledgment: "This product includes software
developed by the OpenSSL Project for use in the OpenSSL Toolkit (http://www.openssl.org/)"
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT ``AS IS'' AND ANY EXPRESSED OR IMPLIED
WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY
AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL
PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL,
EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young
(eay@cryptsoft.com). This product includes software written by Tim
Hudson (tjh@cryptsoft.com).
ii Vcontroller 3.2

1install_guide.book Page iii Friday, June 7, 2002 1:10 PM
© 1995-1998 Eric Young (eay@cryptsoft.com)
All rights reserved.
This package is an SSL implementation written by Eric Young (eay@cryptsoft.com).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as the following conditions are aheared to. The
following conditions apply to all code found in this distribution, be it the RC4, RSA, lhash, DES, etc., code; not just the
SSL code. The SSL documentation included with this distribution is covered by the same copyright terms except that
the holder is Tim Hudson (tjh@cryptsoft.com).
Copyright remains Eric Young's, and as such any Copyright notices in the code are not to be removed. If this package is
used in a product, Eric Young should be given attribution as the author of the parts of the library used. This can be in
the form of a textual message at program startup or in documentation (online or textual) provided with the package.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the
following conditions are met:
1. Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following
disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following acknowledgement:
"This product includes cryptographic software written by Eric Young (eay@cryptsoft.com)" The word 'cryptographic'
can be left out if the routines from the library being used are not cryptographic related :-).
4. If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you
must include an acknowledgement: "This product includes software written by Tim Hudson (tjh@cryptsoft.com)"
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG ``AS IS'' AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS
FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS
BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES;
LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY
THEORY OF LIABILITY,
WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF
SUCH DAMAGE.
The licence and distribution terms for any publicly available version or derivative of this code cannot be changed. i.e.
this code cannot simply be copied and put under another distribution licence [including the GNU Public Licence.]
The mod_ssl package falls under the Open-Source Software label because it's distributed under a BSD-style license. The
detailed license information follows.
Copyright (c) 1998-2001 Ralf S. Engelschall. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the
following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following
disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following
disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following acknowledgment:
"This product includes software developed by Ralf S. Engelschall <rse@engelschall.com> for use in the mod_ssl
project (http://www.modssl.org/)."
4. The names "mod_ssl" must not be used to endorse or promote products derived from this software without prior
written permission. For written permission, please contact rse@engelschall.com.
5. Products derived from this software may not be called "mod_ssl" nor may "mod_ssl" appear in their names without
prior written permission of Ralf S. Engelschall.
6. Redistributions of any form whatsoever must retain the following acknowledgment: "This product includes software
developed by Ralf S. Engelschall <rse@engelschall.com> for use in the mod_ssl project (http://www.modssl.org/)."
THIS SOFTWARE IS PROVIDED BY RALF S. ENGELSCHALL ``AS IS'' AND ANY EXPRESSED OR IMPLIED
WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY
AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL RALF S.
ENGELSCHALL OR HIS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL,
Installation Guide iii
1install_guide.book Page iv Friday, June 7, 2002 1:10 PM
EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The Apache Software License, Version 1.1
Copyright (c) 2000 The Apache Software Foundation. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the
following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following
disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following
disclaimer in the documentation and/or other materials provided with the distribution.
3. The end-user documentation included with the redistribution, if any, must include the following acknowledgment:
"This product includes software developed by the Apache Software Foundation (http://www.apache.org/)." Alternately,
this acknowledgment may appear in the software itself, if and wherever such third-party acknowledgments normally
appear.
4. The names "Apache" and "Apache Software Foundation" must not be used to endorse or promote products derived
from this software without prior written permission. For written permission, please contact apache@apache.org.
5. Products derived from this software may not be called "Apache", nor may "Apache" appear in their name, without
prior written permission of the Apache Software Foundation.
THIS SOFTWARE IS PROVIDED ``AS IS'' AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING,
BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A
PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE APACHE SOFTWARE FOUNDATION
OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY,
OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT
(INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE,
EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This software consists of voluntary contributions made by many individuals on behalf of the Apache Software
Foundation. For more information on the Apache Software Foundation, please see <http://www.apache.org/>.
Portions of this software are based upon public domain software originally written at the National Center for
Supercomputing Applications, University of Illinois, Urbana-Champaign.
PLEASE NOTE: Some components of the WatchGuard Vclass software incorporate source code covered under the
GNU General Public License (GPL). To obtian the source code covered under the GPL, please contact WatchGuard
Technical Support at:
877.232.3531 in the United States and Canada
+1.360.482.1083 from all other countries
This source code is free to download. There is a $35 charge to ship a CD.
GNU GENERAL PUBLIC LICENSE
Version 2, June 1991
Copyright (C) 1989, 1991 Free Software Foundation, Inc.
59 Temple Place, Suite 330, Boston, MA 02111-1307 USA
Everyone is permitted to copy and distribute verbatim copies
of this license document, but changing it is not allowed.
iv Vcontroller 3.2
1install_guide.book Page v Friday, June 7, 2002 1:10 PM
Preamble
The licenses for most software are designed to take away your
freedom to share and change it. By contrast, the GNU General Public
License is intended to guarantee your freedom to share and change free
software--to make sure the software is free for all its users. This
General Public License applies to most of the Free Software
Foundation's software and to any other program whose authors commit to
using it. (Some other Free Software Foundation software is covered by
the GNU Library General Public License instead.) You can apply it to
your programs, too.
When we speak of free software, we are referring to freedom, not
price. Our General Public Licenses are designed to make sure that you
have the freedom to distribute copies of free software (and charge for
this service if you wish), that you receive source code or can get it
if you want it, that you can change the software or use pieces of it
in new free programs; and that you know you can do these things.
To protect your rights, we need to make restrictions that forbid
anyone to deny you these rights or to ask you to surrender the rights.
These restrictions translate to certain responsibilities for you if you
distribute copies of the software, or if you modify it.
For example, if you distribute copies of such a program, whether
gratis or for a fee, you must give the recipients all the rights that
you have. You must make sure that they, too, receive or can get the
source code. And you must show them these terms so they know their
rights.
We protect your rights with two steps: (1) copyright the software, and
(2) offer you this license which gives you legal permission to copy,
distribute and/or modify the software.
Also, for each author's protection and ours, we want to make certain
that everyone understands that there is no warranty for this free
software. If the software is modified by someone else and passed on, we
want its recipients to know that what they have is not the original, so
that any problems introduced by others will not reflect on the original
authors' reputations.
Finally, any free program is threatened constantly by software
patents. We wish to avoid the danger that redistributors of a free
program will individually obtain patent licenses, in effect making the
program proprietary. To prevent this, we have made it clear that any
patent must be licensed for everyone's free use or not licensed at all.
The precise terms and conditions for copying, distribution and
modification follow.
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
GNU GENERAL PUBLIC LICENSE
0. This License applies to any program or other work which contains
a notice placed by the copyright holder saying it may be distributed
under the terms of this General Public License. The "Program", below,
refers to any such program or work, and a "work based on the Program"
means either the Program or any derivative work under copyright law:
that is to say, a work containing the Program or a portion of it,
either verbatim or with modifications and/or translated into another
Installation Guide v

1install_guide.book Page vi Friday, June 7, 2002 1:10 PM
language. (Hereinafter, translation is included without limitation in
the term "modification".) Each licensee is addressed as "you".
Activities other than copying, distribution and modification are not
covered by this License; they are outside its scope. The act of
running the Program is not restricted, and the output from the Program
is covered only if its contents constitute a work based on the
Program (independent of having been made by running the Program).
Whether that is true depends on what the Program does.
1. You may copy and distribute verbatim copies of the Program's
source code as you receive it, in any medium, provided that you
conspicuously and appropriately publish on each copy an appropriate
copyright notice and disclaimer of warranty; keep intact all the
notices that refer to this License and to the absence of any warranty;
and give any other recipients of the Program a copy of this License
along with the Program.
You may charge a fee for the physical act of transferring a copy, and
you may at your option offer warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Program or any portion
of it, thus forming a work based on the Program, and copy and
distribute such modifications or work under the terms of Section 1
above, provided that you also meet all of these conditions:
a) You must cause the modified files to carry prominent notices
stating that you changed the files and the date of any change.
b) You must cause any work that you distribute or publish, that in
whole or in part contains or is derived from the Program or any
part thereof, to be licensed as a whole at no charge to all third
parties under the terms of this License.
c) If the modified program normally reads commands interactively
when run, you must cause it, when started running for such
interactive use in the most ordinary way, to print or display an
announcement including an appropriate copyright notice and a
notice that there is no warranty (or else, saying that you provide
a warranty) and that users may redistribute the program under
these conditions, and telling the user how to view a copy of this
License. (Exception: if the Program itself is interactive but
does not normally print such an announcement, your work based on
the Program is not required to print an announcement.)
These requirements apply to the modified work as a whole. If
identifiable sections of that work are not derived from the Program,
and can be reasonably considered independent and separate works in
themselves, then this License, and its terms, do not apply to those
sections when you distribute them as separate works. But when you
distribute the same sections as part of a whole which is a work based
on the Program, the distribution of the whole must be on the terms of
this License, whose permissions for other licensees extend to the
entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest
your rights to work written entirely by you; rather, the intent is to
exercise the right to control the distribution of derivative or
collective works based on the Program.
vi Vcontroller 3.2
1install_guide.book Page vii Friday, June 7, 2002 1:10 PM
In addition, mere aggregation of another work not based on the Program
with the Program (or with a work based on the Program) on a volume of
a storage or distribution medium does not bring the other work under
the scope of this License.
3. You may copy and distribute the Program (or a work based on it,
under Section 2) in object code or executable form under the terms of
Sections 1 and 2 above provided that you also do one of the following:
a) Accompany it with the complete corresponding machine-readable
source code, which must be distributed under the terms of Sections
1 and 2 above on a medium customarily used for software interchange; or,
b) Accompany it with a written offer, valid for at least three
years, to give any third party, for a charge no more than your
cost of physically performing source distribution, a complete
machine-readable copy of the corresponding source code, to be
distributed under the terms of Sections 1 and 2 above on a medium
customarily used for software interchange; or,
c) Accompany it with the information you received as to the offer
to distribute corresponding source code. (This alternative is
allowed only for noncommercial distribution and only if you
received the program in object code or executable form with such
an offer, in accord with Subsection b above.)
The source code for a work means the preferred form of the work for
making modifications to it. For an executable work, complete source
code means all the source code for all modules it contains, plus any
associated interface definition files, plus the scripts used to
control compilation and installation of the executable. However, as a
special exception, the source code distributed need not include
anything that is normally distributed (in either source or binary
form) with the major components (compiler, kernel, and so on) of the
operating system on which the executable runs, unless that component
itself accompanies the executable.
If distribution of executable or object code is made by offering
access to copy from a designated place, then offering equivalent
access to copy the source code from the same place counts as
distribution of the source code, even though third parties are not
compelled to copy the source along with the object code.
4. You may not copy, modify, sublicense, or distribute the Program
except as expressly provided under this License. Any attempt
otherwise to copy, modify, sublicense or distribute the Program is
void, and will automatically terminate your rights under this License.
However, parties who have received copies, or rights, from you under
this License will not have their licenses terminated so long as such
parties remain in full compliance.
5. You are not required to accept this License, since you have not
signed it. However, nothing else grants you permission to modify or
distribute the Program or its derivative works. These actions are
prohibited by law if you do not accept this License. Therefore, by
modifying or distributing the Program (or any work based on the
Program), you indicate your acceptance of this License to do so, and
all its terms and conditions for copying, distributing or modifying
the Program or works based on it.
Installation Guide vii
1install_guide.book Page viii Friday, June 7, 2002 1:10 PM
6. Each time you redistribute the Program (or any work based on the
Program), the recipient automatically receives a license from the
original licensor to copy, distribute or modify the Program subject to
these terms and conditions. You may not impose any further
restrictions on the recipients' exercise of the rights granted herein.
You are not responsible for enforcing compliance by third parties to
this License.
7. If, as a consequence of a court judgment or allegation of patent
infringement or for any other reason (not limited to patent issues),
conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not
excuse you from the conditions of this License. If you cannot
distribute so as to satisfy simultaneously your obligations under this
License and any other pertinent obligations, then as a consequence you
may not distribute the Program at all. For example, if a patent
license would not permit royalty-free redistribution of the Program by
all those who receive copies directly or indirectly through you, then
the only way you could satisfy both it and this License would be to
refrain entirely from distribution of the Program.
If any portion of this section is held invalid or unenforceable under
any particular circumstance, the balance of the section is intended to
apply and the section as a whole is intended to apply in other
circumstances.
It is not the purpose of this section to induce you to infringe any
patents or other property right claims or to contest validity of any
such claims; this section has the sole purpose of protecting the
integrity of the free software distribution system, which is
implemented by public license practices. Many people have made
generous contributions to the wide range of software distributed
through that system in reliance on consistent application of that
system; it is up to the author/donor to decide if he or she is willing
to distribute software through any other system and a licensee cannot
impose that choice.
This section is intended to make thoroughly clear what is believed to
be a consequence of the rest of this License.
8. If the distribution and/or use of the Program is restricted in
certain countries either by patents or by copyrighted interfaces, the
original copyright holder who places the Program under this License
may add an explicit geographical distribution limitation excluding
those countries, so that distribution is permitted only in or among
countries not thus excluded. In such case, this License incorporates
the limitation as if written in the body of this License.
9. The Free Software Foundation may publish revised and/or new versions
of the General Public License from time to time. Such new versions will
be similar in spirit to the present version, but may differ in detail to
address new problems or concerns.
Each version is given a distinguishing version number. If the Program
specifies a version number of this License which applies to it and "any
later version", you have the option of following the terms and conditions
either of that version or of any later version published by the Free
Software Foundation. If the Program does not specify a version number of
this License, you may choose any version ever published by the Free Software
Foundation.
viii Vcontroller 3.2
1install_guide.book Page ix Friday, June 7, 2002 1:10 PM
10. If you wish to incorporate parts of the Program into other free
programs whose distribution conditions are different, write to the author
to ask for permission. For software which is copyrighted by the Free
Software Foundation, write to the Free Software Foundation; we sometimes
make exceptions for this. Our decision will be guided by the two goals
of preserving the free status of all derivatives of our free software and
of promoting the sharing and reuse of software generally.
NO WARRANTY
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY
FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN
OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES
PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED
OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS
TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE
PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING,
REPAIR OR CORRECTION.
12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR
REDISTRIBUTE THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES,
INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING
OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED
TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY
YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER
PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE
POSSIBILITY OF SUCH DAMAGES.
All other trademarks or trade names mentioned herein, if any, are the property of their respective owners.
Part No: 0774-000
WatchGuard Technologies, Inc.
Firebox Vclass Software
End-User License Agreement
IMPORTANT - READ CAREFULLY BEFORE ACCESSING WATCHGUARD SOFTWARE:
This Firebox Vclass Software End-User License Agreement (‘AGREEMENT’) is a legal agreement between you (either
an individual or a single entity) and WatchGuard Technologies, Inc. (‘WATCHGUARD’) for the WATCHGUARD
Firebox Vclass software product, which includes computer software components (whether installed separately on a
computer workstation or on the WATCHGUARD hardware product or included on the WATCHGUARD hardware
product) and may include associated media, printed materials, and on-line or electronic documentation, and any
updates or modifications thereto, including those received through the WatchGuard LiveSecurity Service (or its
equivalent), (the ‘SOFTWARE PRODUCT’). WATCHGUARD is willing to license the SOFTWARE PRODUCT to you
only on the condition that you accept all of the terms contained in this Agreement. Please read this Agreement
carefully. By installing or using the SOFTWARE PRODUCT you agree to be bound by the terms of this Agreement. If
you do not agree to the terms of this AGREEMENT, WATCHGUARD will not license the SOFTWARE PRODUCT to
you, and you will not have any rights in the SOFTWARE PRODUCT. In that case, promptly return the SOFTWARE
PRODUCT, along with proof of payment, to the authorized dealer from whom you obtained the SOFTWARE PRODUCT
for a full refund of the price you paid.
1. Ownership and License. The SOFTWARE PRODUCT is protected by copyright laws and international copyright
treaties, as well as other intellectual property laws and treaties. This is a license agreement and NOT an agreement for
sale. All title and copyrights in and to the SOFTWARE PRODUCT (including but not limited to any images,
END OF TERMS AND CONDITIONS
Installation Guide ix

1install_guide.book Page x Friday, June 7, 2002 1:10 PM
photographs, animations, video, audio, music, text, and applets incorporated into the SOFTWARE PRODUCT), the
accompanying printed materials, and any copies of the SOFTWARE PRODUCT are owned by WATCHGUARD or its
licensors. Your rights to use the SOFTWARE PRODUCT are as specified in this AGREEMENT, and WATCHGUARD
retains all rights not expressly granted to you in this AGREEMENT. Nothing in this AGREEMENT constitutes a
waiver of our rights under U.S. copyright law or any other law or treaty.
2. Permitted Uses. You are granted the following rights to the SOFTWARE PRODUCT:
(A) You may install and use the SOFTWARE PRODUCT on any single WATCHGUARD hardware product at any
single location and may install and use the SOFTWARE PRODUCT on multiple workstation computers.
(B) To use the SOFTWARE PRODUCT on more than one WATCHGUARD hardware product at once, you must
purchase an additional copy of the SOFTWARE PRODUCT for each additional WATCHGUARD hardware product on
which you want to use it. To the extent that you install copies of the SOFTWARE PRODUCT on additional
WATCHGUARD hardware products in accordance with the prior sentence without installing the additional copies of
the SOFTWARE PRODUCT included with such WATCHGUARD hardware products, you agree that use of any software
provided with or included on the additional WATCHGUARD hardware products that does not require installation will
be subject to the terms and conditions of this AGREEMENT. You must also maintain a current subscription to the
WatchGuard LiveSecurity Service (or its equivalent) for each additional WATCHGUARD hardware product on which
you will use a copy of an updated or modified version of the SOFTWARE PRODUCT received through the WatchGuard
LiveSecurity Service (or its equivalent).
(C) In addition to the copies described in Section 2(A), you may make a single copy of the SOFTWARE PRODUCT
for backup or archival purposes only.
3. Prohibited Uses. You may not, without express written permission from WATCHGUARD:
(A) Use, copy, modify, merge or transfer copies of the SOFTWARE PRODUCT or printed materials except as
provided in this AGREEMENT;
(B) Use any backup or archival copy of the SOFTWARE PRODUCT (or allow someone else to use such a copy) for
any purpose other than to replace the original copy in the event it is destroyed or becomes defective;
(C) Sublicense, lend, lease or rent the SOFTWARE PRODUCT;
(D) Transfer this license to another party unless
(i) the transfer is permanent,
(ii) the third party recipient agrees to the terms of this AGREEMENT, and
(iii) you do not retain any copies of the SOFTWARE PRODUCT; or
(E) Reverse engineer, disassemble or decompile the SOFTWARE PRODUCT.
4. Limited Warranty. WATCHGUARD makes the following limited warranties for a period of ninety (90) days from
the date you obtained the SOFTWARE PRODUCT from WATCHGUARD or an authorized dealer:
(A) Media. The disks and documentation will be free from defects in materials and workmanship under normal use. If
the disks or documentation fail to conform to this warranty, you may, as your sole and exclusive remedy, obtain a
replacement free of charge if you return the defective disk or documentation to WATCHGUARD with a dated proof of
purchase.
(B) SOFTWARE PRODUCT. The SOFTWARE PRODUCT will materially conform to the documentation that
accompanies it. If the SOFTWARE PRODUCT fails to operate in accordance with this warranty, you may, as your sole
and exclusive remedy, return all of the SOFTWARE PRODUCT and the documentation to the authorized dealer from
whom you obtained it, along with a dated proof of purchase, specifying the problems, and they will provide you with a
new version of the SOFTWARE PRODUCT or a full refund, at their election.
Disclaimer and Release. THE WARRANTIES, OBLIGATIONS AND LIABILITIES OF WATCHGUARD, AND YOUR
REMEDIES, SET FORTH IN PARAGRAPHS 4, 4(A) AND 4(B) ABOVE ARE EXCLUSIVE AND IN
SUBSTITUTION FOR, AND YOU HEREBY WAIVE, DISCLAIM AND RELEASE ANY AND ALL OTHER
WARRANTIES, OBLIGATIONS AND LIABILITIES OF WATCHGUARD AND ITS LICENSORS AND ALL OTHER
RIGHTS, CLAIMS AND REMEDIES YOU MAY HAVE AGAINST WATCHGUARD AND ITS LICENSORS,
EXPRESS OR IMPLIED, ARISING BY LAW OR OTHERWISE, WITH RESPECT TO ANY NONCONFORMANCE
OR DEFECT IN THE SOFTWARE PRODUCT (INCLUDING, BUT NOT LIMITED TO, ANY IMPLIED WARRANTY
OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE, ANY IMPLIED WARRANTY ARISING
FROM COURSE OF PERFORMANCE, COURSE OF DEALING, OR USAGE OF TRADE, ANY WARRANTY OF
NONINFRINGEMENT, ANY WARRANTY THAT THE SOFTWARE PRODUCT WILL MEET YOUR
REQUIREMENTS, ANY WARRANTY OF UNINTERRUPTED OR ERROR-FREE OPERATION, ANY OBLIGATION,
LIABILITY, RIGHT, CLAIM OR REMEDY IN TORT, WHETHER OR NOT ARISING FROM THE NEGLIGENCE
x Vcontroller 3.2

1install_guide.book Page xi Friday, June 7, 2002 1:10 PM
(WHETHER ACTIVE, PASSIVE OR IMPUTED) OR FAULT OF WATCHGUARD AND ITS LICENSORS AND ANY
OBLIGATION, LIABILITY, RIGHT, CLAIM OR REMEDY FOR LOSS OR DAMAGE TO, OR CAUSED BY OR
CONTRIBUTED TO BY, THE SOFTWARE PRODUCT).
Limitation of Liability. WATCHGUARD'S LIABILITY (WHETHER IN CONTRACT, TORT, OR OTHERWISE; AND
NOTWITHSTANDING ANY FAULT, NEGLIGENCE, STRICT LIABILITY OR PRODUCT LIABILITY) WITH
REGARD TO THE SOFTWARE PRODUCT WILL IN NO EVENT EXCEED THE PURCHASE PRICE PAID BY YOU
FOR SUCH PRODUCT. THIS SHALL BE TRUE EVEN IN THE EVENT OF THE FAILURE OF AN AGREED
REMEDY. IN NO EVENT WILL WATCHGUARD BE LIABLE TO YOU OR ANY THIRD PARTY, WHETHER
ARISING IN CONTRACT (INCLUDING WARRANTY), TORT (INCLUDING ACTIVE, PASSIVE OR IMPUTED
NEGLIGENCE AND STRICT LIABILITY AND FAULT), FOR ANY INDIRECT, SPECIAL, INCIDENTAL, OR
CONSEQUENTIAL DAMAGES (INCLUDING WITHOUT LIMITATION LOSS OF BUSINESS PROFITS,
BUSINESS INTERRUPTION, OR LOSS OF BUSINESS INFORMATION) ARISING OUT OF OR IN CONNECTION
WITH THIS WARRANTY OR THE USE OF OR INABILITY TO USE THE SOFTWARE PRODUCT, EVEN IF
WATCHGUARD HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. THIS SHALL BE TRUE
EVEN IN THE EVENT OF THE FAILURE OF AN AGREED REMEDY.
5.United States Government Restricted Rights. The SOFTWARE PRODUCT is provided with Restricted Rights. Use,
duplication or disclosure by the U.S. Government or any agency or instrumentality thereof is subject to restrictions as
set forth in subdivision (c)(1)(ii) of the Rights in Technical Data and Computer Software clause at DFARS 252.2277013, or in subdivision (c)(1) and (2) of the Commercial Computer Software -- Restricted Rights Clause at 48 C.F.R.
52.227-19, as applicable. Manufacturer is WatchGuard Technologies, Inc., 505 5th Ave. South, Suite 500, Seattle,
WA 98104.
6.Export Controls. You agree not to directly or indirectly transfer the SOFTWARE PRODUCT or documentation to
any country to which such transfer would be prohibited by the U.S. Export Administration Act and the regulations
issued thereunder.
7.Termination. This license and your right to use the SOFTWARE PRODUCT will automatically terminate if you fail
to comply with any provisions of this AGREEMENT, destroy all copies of the SOFTWARE PRODUCT in your
possession, or voluntarily return the SOFTWARE PRODUCT to WATCHGUARD. Upon termination you will destroy
all copies of the SOFTWARE PRODUCT and documentation remaining in your control or possession.
8.Miscellaneous Provisions. This AGREEMENT will be governed by and construed in accordance with the substantive
laws of Washington excluding the 1980 United National Convention on Contracts for the International Sale of Goods,
as amended. This is the entire AGREEMENT between us relating to the SOFTWARE PRODUCT, and supersedes any
prior purchase order, communications, advertising or representations concerning the SOFTWARE PRODUCT AND BY
USING THE SOFTWARE PRODUCT YOU AGREE TO THESE TERMS. IF THE SOFTWARE PRODUCT IS BEING
USED BY AN ENTITY, THE INDIVIDUAL INDICATING AGREEMENT TO THESE TERMS REPRESENTS AND
WARRANTS THAT (A) SUCH INDIVIDUAL IS DULY AUTHORIZED TO ACCEPT THIS AGREEMENT ON
BEHALF OF THE ENTITY AND TO BIND THE ENTITY TO THE TERMS OF THIS AGREEMENT; (B) THE
ENTITY HAS THE FULL POWER, CORPORATE OR OTHERWISE, TO ENTER INTO THIS AGREEMENT AND
PERFORM ITS OBLIGATIONS UNDER THIS AGREEMENT AND; (C) THIS AGREEMENT AND THE
PERFORMANCE OF THE ENTITY’S OBLIGATIONS UNDER THIS AGREEMENT DO NOT VIOLATE ANY THIRDPARTY AGREEMENT TO WHICH THE ENTITY IS A PARTY. No change or modification of this AGREEMENT will
be valid unless it is in writing and is signed by WATCHGUARD.
Installation Guide xi
1install_guide.book Page xii Friday, June 7, 2002 1:10 PM
xii Vcontroller 3.2
1install_guide.book Page xiii Friday, June 7, 2002 1:10 PM
Contents
CHAPTER 1 A Tour of the WatchGuard Firebox Vclass
Security Appliances ................................... 1
What’s inside a Firebox Vclass security appliance ............... 1
The RapidCore™ hardware ensemble ............................... 1
The WatchGuard Firebox Vclass Operating System™ (OS) .... 2
The WatchGuard Firebox Vclass administrative client
applications ......................................................................
What’s inside the carton ................................................... 2
WatchGuard Firebox V10 security appliance ....................... 3
WatchGuard Firebox V60 and V80 security appliance ........... 3
WatchGuard Firebox V100 security appliance ..................... 3
After unpacking the security appliance .............................. 4
Key features of the Firebox V10 security appliance ............. 5
What you should know about these features ...................... 5
Features of the appliance’s back panel .............................. 6
Key features of the Firebox V60 and V80 appliances .......... 8
What you should know about these features ...................... 8
Features of the appliance’s back panel ............................ 10
2
Key features of the Firebox Vclass 100 appliance ............. 12
What you should know about these features .................... 13
Installation Guide xiii

1install_guide.book Page xiv Friday, June 7, 2002 1:10 PM
Features of the appliance’s back panel ............................ 15
Connecting to a UPS device ........................................... 16
What’s next .................................................................... 17
CHAPTER 2 Installing a Firebox Vclass Security
Appliance ...................................................19
What you’ll be doing ...................................................... 20
Considering the location options .................................... 21
Protecting one region of the network from unauthorized
internal access ...............................................................
Protecting the whole network from external access ............ 22
An extremely short Vcontroller/WatchGuard Glossary ....... 23
Connecting the appliance for setup and software
installation ...................................................................
21
24
CHAPTER 3 Starting the Firebox Vclass Appliance
Setup ........................................................ 27
Configuring more than one security appliance .................. 27
Turning on a Firebox Vclass security appliance ................. 28
If problems occur ........................................................ 28
An overview of Vcontroller hardware and software
requirements ..............................................................
What’s next .................................................................... 31
Installing the Vcontroller (Windows) ................................. 31
Installing the Vcontroller (Solaris) ..................................... 33
Installing the Vcontroller (Linux) ...................................... 35
Discovering a new Firebox Vclass appliance ..................... 38
If no appliance is found ................................................40
If an appliance is found ................................................ 41
Changing the IP address of an appliance’s Private interface 42
Extra: Using the WatchGuard CLI to record an IP address 44
CHAPTER 4 Completing the Vcontroller Installation
Wizard ....................................................... 47
Before you begin ........................................................... 47
29
Starting the process ....................................................... 48
When the Installation Wizard appears .............................. 48
xiv Vcontroller 3.2

1install_guide.book Page xv Friday, June 7, 2002 1:10 PM
Completing interface 1 (Public) entries ............................ 53
Completing interface 2 (DMZ) entries. ............................ 55
Completing the Wizard Interface tab entries .................... 56
Concluding the installation ............................................. 66
Relocating the appliance to a permanent network setting 67
After relocation .......................................................... 69
CHAPTER 5 Importing a Profile into a New Appliance 71
Requirements ............................................................. 71
Exporting a profile from an existing security appliance ..... 72
EXTRA: Editing the profile ............................................ 73
Getting started .............................................................. 74
Importing a profile ......................................................... 76
Index ........................................................................... 79
Installation Guide xv

1install_guide.book Page xvi Friday, June 7, 2002 1:10 PM
xvi Vcontroller 3.2
1install_guide.book Page 1 Friday, June 7, 2002 1:10 PM
CHAPTER 1 A Tour of the WatchGuard
Firebox Vclass Security
Appliances
This chapter provides a visual tour of the external hardware features of
the WatchGuard® Firebox® Vclass security appliances, focusing on the
buttons, LEDs, interfaces, ports and outlets for the following models:
•Firebox V10
•Firebox V60
•Firebox V80
•Firebox V100
What’s inside a Firebox Vclass security appliance
Every Firebox Vclass appliance has three important sets of components
that we want to highlight, before proceeding with installation and setup
instructions:
The RapidCore™ hardware ensemble
A well-integrated chip set and memory system powers every Firebox
Vclass appliance in its primary duties: protecting your network and
efficiently managing all legitimate data streams. This proprietary set of
Installation Guide 1
1install_guide.book Page 2 Friday, June 7, 2002 1:10 PM
CHAPTER 1: A Tour of the WatchGuard Firebox Vclass Security Appliances
hardware features rely wholly on the next two component sets for
operational guidance.
The WatchGuard Firebox Vclass Operating System™ (OS)
Every Firebox Vclass security appliance is pre-installed with the latest
version of the Firebox Vclass Operating System–which is identified on the
packaging by a version number. This operating system includes all the
software resources that make the appliance fully functional, including a
complex database that stores the settings you assemble with the following
software application.
The WatchGuard Firebox Vclass administrative client
applications
Using the WatchGuard Vcontroller (or the companion WatchGuard CPM
client software) gives you full control of all the customizable operating
system parameters, including basic system configurations, security
policies, maintenance and activity logging. You can use a more recent
version of a client management application to maintain the operations of
an appliance with an older version of the OS, however, you should not
use an older client to manage a recently upgraded-OS appliance.
This is important, as a careful upgrade strategy is crucial in keeping your
security appliances at optimum levels. As fully detailed in a separate
chapter in the System Administration Guide, you will need to occasionally
upgrade both operating system software and the WatchGuard
administrative application. This will ensure that you can utilize the most
complete set of features in your Firebox Vclass appliances.
What’s inside the carton
Different Firebox Vclass appliance models are packaged with differing
contents, as catalogued in this section.
2 Vcontroller 3.2
1install_guide.book Page 3 Friday, June 7, 2002 1:10 PM
WatchGuard Firebox V10 security appliance
• One 12V 1.25A power supply
• Two 6-foot straight-through 10/100 BaseT Ethernet cables (TAN)
• A CD containing the WatchGuard Vcontroller application software
for use with three different operating systems: Windows 9x/2000/XP,
Sun Solaris, and Linux. The CD also provides electronic versions of
the complete user guide documentation, including this Installation
Guide, a System Administration Guide, a Policy Configuration Guide and
the CLI Guide.
WatchGuard Firebox V60 and V80 security appliance
•One power cord
What’s inside the carton
• One 6-foot crossover 10/100 BaseT Ethernet cable (RED)
• Three 6-foot straight-through 10/100 BaseT Ethernet cables (GREEN)
• One 6-foot console RJ-45-to-RJ 45 serial cable and DB-9 adapter
• One APC-manufactured appliance-to-UPS device cable
• A kit containing rack-mounting hardware for this appliance
• A CD containing the WatchGuard Vcontroller application software
for use with three different operating systems: Windows 9x/2000/XP,
Sun Solaris, and Linux. The CD also provides electronic versions of
the complete user guide documentation, including this Installation
Guide, a System Administration Guide, a Policy Configuration Guide and
the CLI Guide.
N
OTE
Rack-mounting hardware has also been included in the package for these
models. If you are mounting your appliance in a rack, please note that
both Firebox V60 and V80 appliances are 1U high.
WatchGuard Firebox V100 security appliance
•One power cord
• One 6-foot crossover (RED) 10/100 BaseT Ethernet cable
• One 6-foot straight-through (GREEN) 10/100 BaseT Ethernet cable
• Two optical data cables
Installation Guide 3

1install_guide.book Page 4 Friday, June 7, 2002 1:10 PM
CHAPTER 1: A Tour of the WatchGuard Firebox Vclass Security Appliances
• One APC-manufactured appliance-to-UPS device cable
• One 6-foot console RJ-45-to-RJ 45 serial cable and DB-9 adapter
• A kit containing rack-mounting hardware for this appliance
• A CD containing the WatchGuard Vcontroller application software
for use with three different operating systems: Windows 9x/2000/XP,
Sun Solaris, and Linux. The CD also provides electronic versions of
the complete user guide documentation, including this Installation
Guide, a System Administration Guide, a Policy Configuration Guide and
the CLI Guide.
• Rack-mounting hardware has been included in this WatchGuard
Firebox package. If you are mounting the appliance in a rack, please
note that the Firebox V100 is also 1 U high.
After unpacking the security appliance
Once you have unpacked the contents of the Firebox Vclass security
appliance package, you may want to take a quick look at the front and
back of the appliance itself to acquaint yourself with all the features. The
remainder of this chapter offers model-specific descriptions of the
external features, which you can review by turning to one of the following
pages:
• Key features of the Firebox V10 appliances page 5
• Key features of the Firebox V60 and V80 appliances page 8
• Key features of the Firebox V100 appliance page 12
• Connecting to a Uninterruptable Power Supply (UPS) device page 16
4 Vcontroller 3.2
1install_guide.book Page 5 Friday, June 7, 2002 1:10 PM
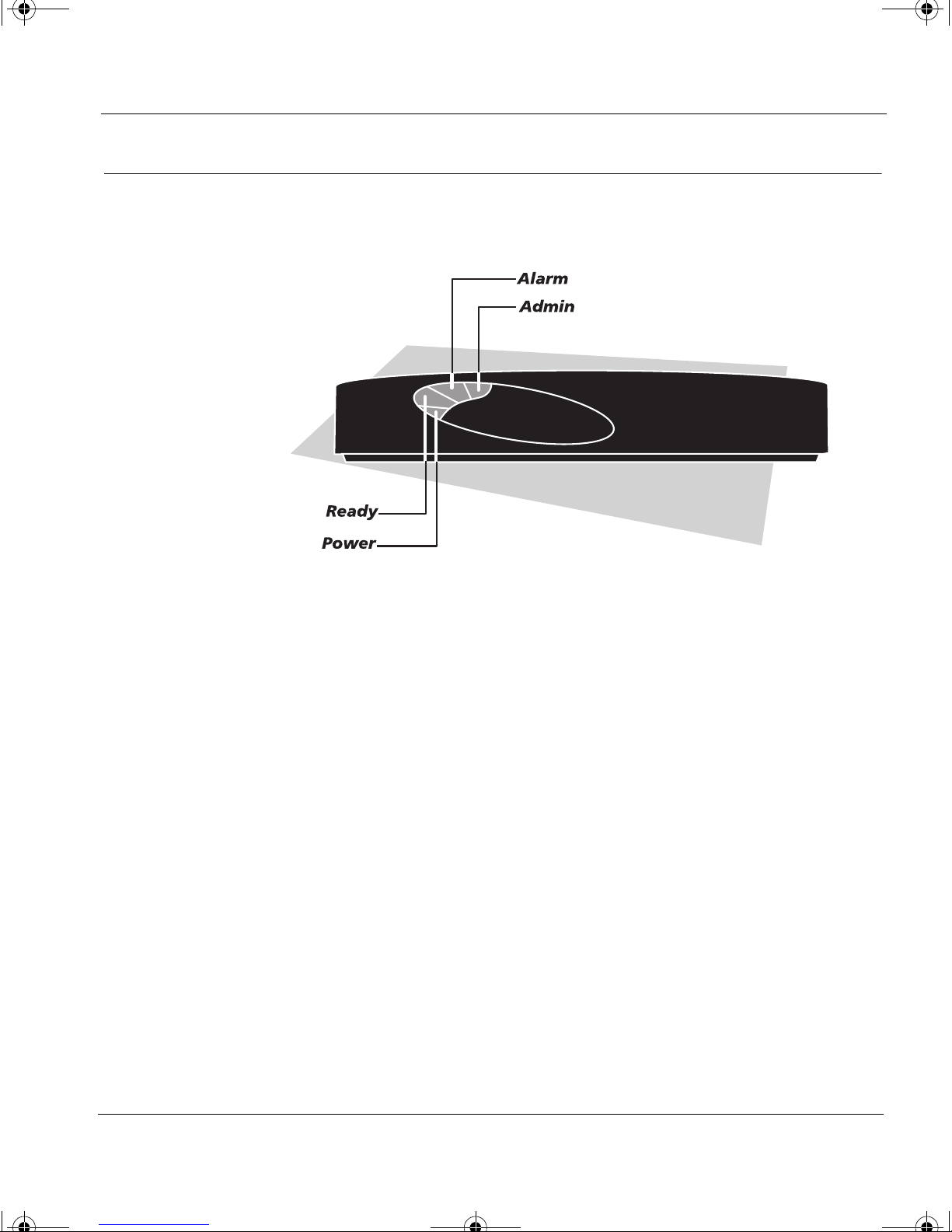
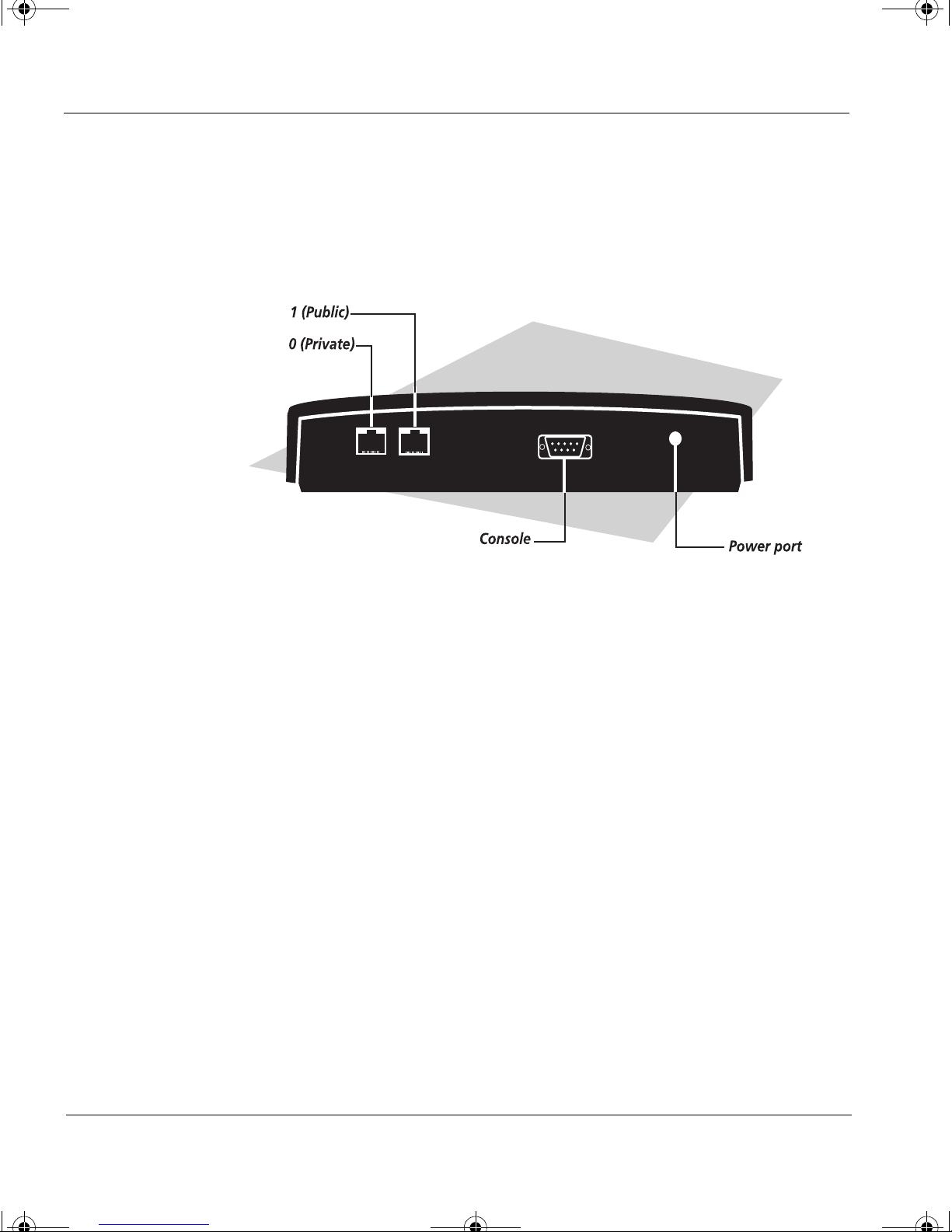
Key features of the Firebox V10 security appliance
The front panel of a Firebox V10 appliance contains the features shown in
the following illustration.
Key features of the Firebox V10 security appliance
Three LED’s Labeled Alarm, Admin and Ready
One Power LED Located in the lower right corner
What you should know about these features
Power The Power LED indicates that the appliance has
been turned on; however, the Ready LED
(described below) is the best indicator of the
appliance’s readiness for use.
Alarm The Alarm LED will be lit when certain severe
alarms have been triggered. The Firebox Vclass
appliances support multiple types of alarm
notification including Alarm LED activation,
page/e-mail messaging, and the Alarm Manager
feature of the WatchGuard Vcontroller, which are
discussed in the System Administration Guide.
Admin The Admin LED will be lit whenever a system
administrator is currently connected to the
appliance by means of the Vcontroller or the
WatchGuard CLI.
Installation Guide 5
1install_guide.book Page 6 Friday, June 7, 2002 1:10 PM
CHAPTER 1: A Tour of the WatchGuard Firebox Vclass Security Appliances
Ready The Ready LED will blink when the appliance is
powering up. It will be steadily lit when the
appliance is ready for network traffic.
Features of the appliance’s back panel
Data interfaces Two Ethernet interfaces (RJ-45 connectors)
labeled 0 and 1, act as the primary data
interfaces.
Incorporated into each Ethernet interface
are two indicator lights labeled 10 and 100.
These LEDs indicate (1) a connection to a
hub or direct-connect workstation is
active, (2) the speed of the link (10 Mbps or
100 Mbps Ethernet), and (3) that traffic is
being transmitted.
When a cable is first plugged into an RJ-45
interface, either the 10 or the 100 LED
should be lit. This indicates that there is a
successful link between the Firebox V10
appliance and the network or a computer.
If either light doesn't turn on, check that
the cable is securely connected to the
proper interface on each end.
6 Vcontroller 3.2
1install_guide.book Page 7 Friday, June 7, 2002 1:10 PM
Console interface A single DB-9 interface, labeled Console,
Key features of the Firebox V10 security appliance
Make sure, too, that the cable is the correct
type for the connection. If connecting the
Firebox V10 appliance to a hub or switch, a
straight-through cable is needed (two 3-ft.
10/100 cables are provided). If connecting
directly to a computer, a crossover cable is
required (a 6-ft. 10/100 crossover cable is
provided).
permits a direct workstation-to-appliance
connection, at which time you can use the
WatchGuard command line interface
(CLI) to configure and administer this
appliance. To learn more about this
administrative option, open and review
the WatchGuard CLI User Guide (included
on the installer CD).
5Vdc3.0A power interface This interface serves as the connection to a
100VAC-to-240VAC (50/60Hz) source.
Use the power cord supplied in the
package to connect this appliance to a UPS
device or to a power outlet.
N
OTE
The power supply can auto-detect 110/220 voltage.
Appliance reset This opening allows you to insert a straight pin or
paperclip and press an internal Reset switch that
restarts the appliance. This is an option to
unplugging and replugging the power cord.
N
OTE
IN THE EVENT OF A POWER FAILURE… this security appliance, if
left connected to the power source, will automatically restart itself once
electrical power has been restored. You do not have to unplug and then
reconnect the appliance to the power source.
Installation Guide 7
1install_guide.book Page 8 Friday, June 7, 2002 1:10 PM
CHAPTER 1: A Tour of the WatchGuard Firebox Vclass Security Appliances
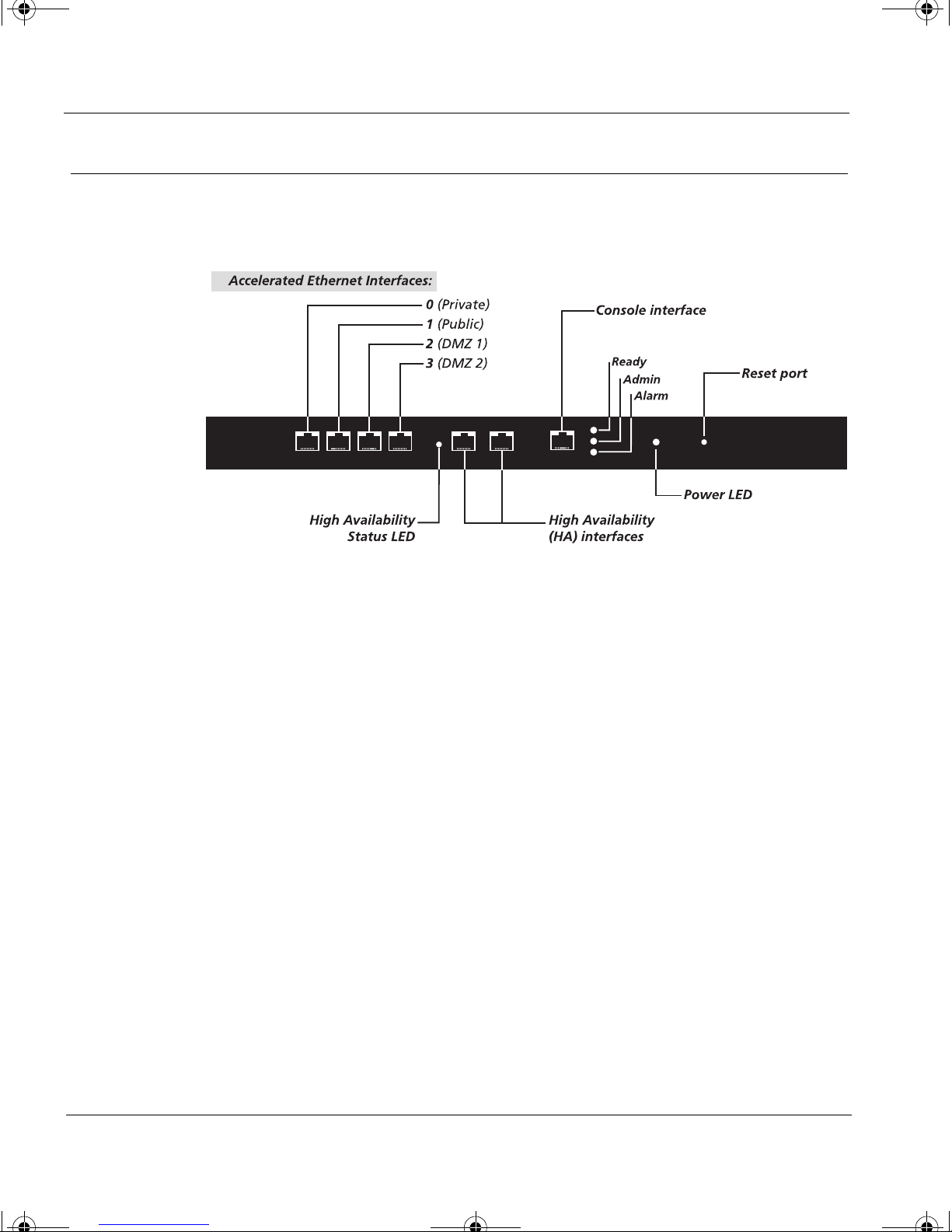
Key features of the Firebox V60 and V80 appliances
The front panels of both Firebox V60 and V80 security appliances contain
the features shown in the following illustration.
Four Ethernet interfaces Labeled 0, 1, 2, and 3
Two HA interfaces Labeled HA1 and HA2
One HA status LED Labeled HA
Three status LED’s Labeled Alarm, Admin and Ready
One RJ-45 interface Labeled Console
One status LED Labeled Power
What you should know about these features
Power The Power LED indicates that the appliance has
been fully turned on and is ready for
administration and/or use.
Alarm The Alarm LED is lit when certain alarms have
been triggered.
The Firebox Vclass appliance supports multiple
types of alarm notification including Alarm LED
activation, page/e-mail messaging, and the Alarm
Manager feature of the WatchGuard Vcontroller,
8 Vcontroller 3.2

1install_guide.book Page 9 Friday, June 7, 2002 1:10 PM
Admin The Admin LED is lit whenever a system
Ready The Ready LED is steadily lit when the appliance is
Data interfaces Four accelerated Ethernet interfaces (RJ-45
Key features of the Firebox V60 and V80 appliances
which are discussed in the System Administration
Guide.
administrator is currently connected to the
appliance by means of the Vcontroller software or
by means of a terminal window and the
WatchGuard CLI.
ready for network traffic. (This LED will blink
when the appliance is powering up or powering
down.)
connectors) labeled 0 (Private), 1 (Public), 2
(DMZ1), and 3 (DMZ2) act as the primary
conduits through which passes all of the network
data traffic. Note that 3 is not currently active, and
should not be used for data traffic.
Incorporated into each Ethernet interface are two
indicator lights labeled 10 and 100. These LEDs
indicate (1) a connection to a hub or direct-connect
workstation is active, (2) the speed of the link (10
Mbps or 100 Mbps Ethernet), and (3) that traffic is
being transmitted.
When a cable is first plugged into a RJ-45 interface,
either the 10 or the 100 LED should be lit. This
indicates that there is a successful link between the
Firebox Vclass appliance and the network or a
computer. If the light doesn't turn on, check that
the cable is securely connected to the proper
interface on each end.
Make sure, too, that the cable is the correct type
for the connection. If connecting the Firebox
Vclass appliance to a hub or switch, a straight-
through cable is needed (two 3-ft. 10/100 cables are
provided). If connecting directly to a computer, a
crossover cable is required (a 6-ft. 10/100 crossover
cable is provided).
Installation Guide 9
1install_guide.book Page 10 Friday, June 7, 2002 1:10 PM
CHAPTER 1: A Tour of the WatchGuard Firebox Vclass Security Appliances
HA status LED This light reports on the current status of this
appliance, if it is one of two connected as a highavailability system. If this is the primary
appliance, and the light is on and steady, the
system is functional, and this appliance is on-line.
If this is the primary appliance and the LED is
blinking, a failover has occurred and the
secondary appliance is online. (That appliance’s
HA LED should be steadily lit, indicating that it is
now the primary appliance.)
Console interface A single RJ-45 interface, labeled Console, permits a
direct workstation-to-appliance connection, at
which time you can use the WatchGuard
Command Line Interface (CLI) to configure and
administer this appliance. To learn more about
this administrative option, see the CLI Guide
chapter in the System Administration Guide.
Reset port This opening allows you to insert a straight pin or
paperclip and press an internal Reset switch that
restarts the appliance. This is an alternative to
unplugging and replugging the power cord.
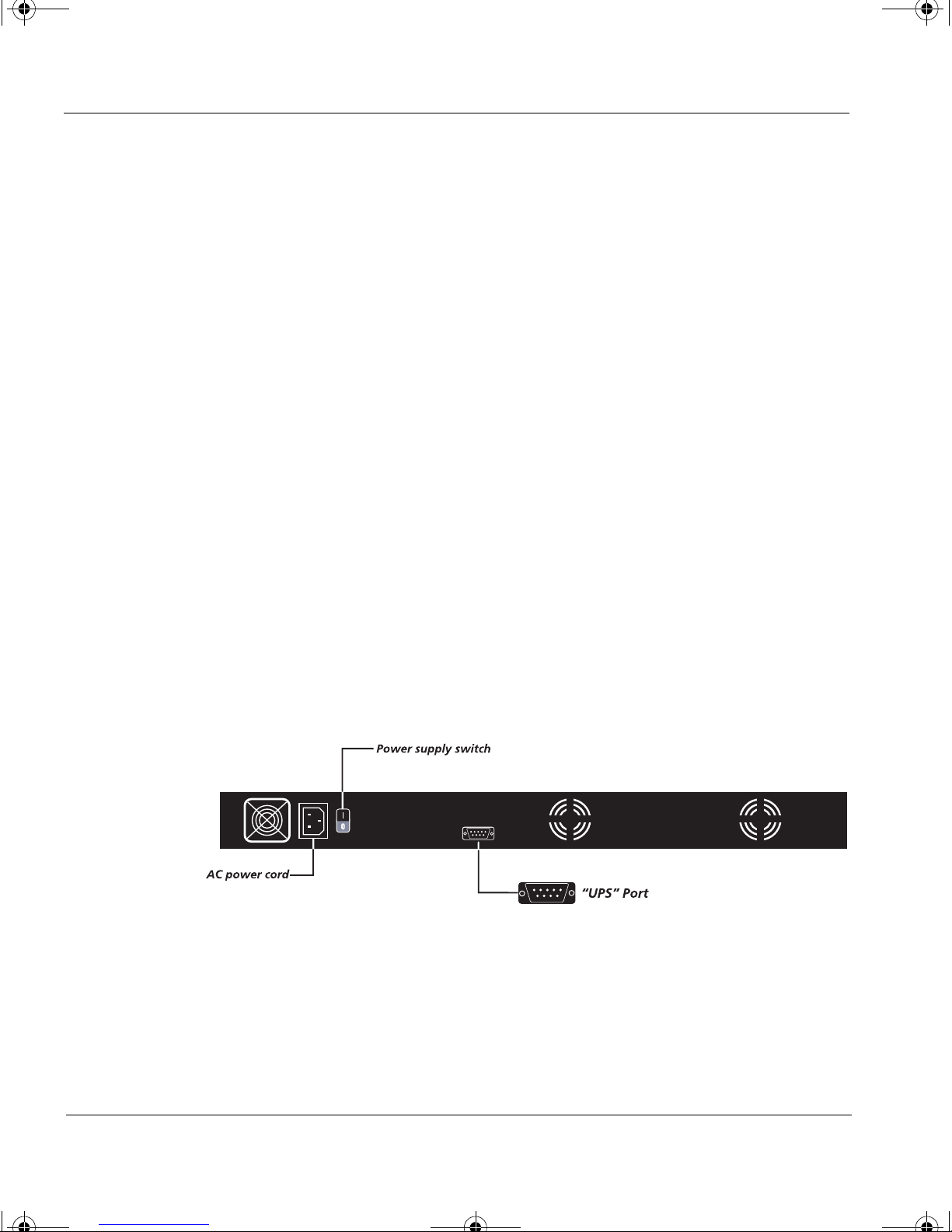
Features of the appliance’s back panel
AC power This interface enables you to connect the appliance
(using the supplied power cord) to a 100 to
240VAC (50/60Hz) power source.
10 Vcontroller 3.2
1install_guide.book Page 11 Friday, June 7, 2002 1:10 PM
Do not connect any Firebox Vclass appliance to a source of power that
supplies the wrong voltage. Doing so will damage the appliance and void
the warranty.
Power switch Press this switch to power up or to power down
Key features of the Firebox V60 and V80 appliances
N
OTE
the appliance. To power up the appliance, press
this switch after connecting the appliance to a safe
power source. To power down the appliance,
perform a software shutdown, then wait for the
status LEDs on the front to dim. Wait 30 seconds
after the LEDs go dim. At that point it is safe to
press this switch to cut power.
Amperage switch This switch allows you to change the power
source between 115 and 230 volts, depending
upon your supply.
N
OTE
The power supply can auto-detect 110/220 voltage.
UPS interface This interface permits connection of the appliance
to an Uninterruptable Power Supply (UPS). You
should use the cable provided in the appliance
packaging for this connection. This type of
connection enables suitably configured UPS
devices to notify the appliance if the power goes
out, prompting the appliance to shut itself down
properly.
UPS devices from American Power Company (APC)
are currently supported by the Firebox Vclass
power management firmware. Check
WatchGuard's Web site (www.watchguard.com) for
updated information on complete UPS support.
Installation Guide 11
1install_guide.book Page 12 Friday, June 7, 2002 1:10 PM
CHAPTER 1: A Tour of the WatchGuard Firebox Vclass Security Appliances
N
OTE
IN THE EVENT OF A POWER FAILURE… This security appliance, if
left connected to the power source, will automatically restart itself once
electrical power has been restored. You do not have to press either the
Power button on the front or the power supply switch on the back of the
appliance.
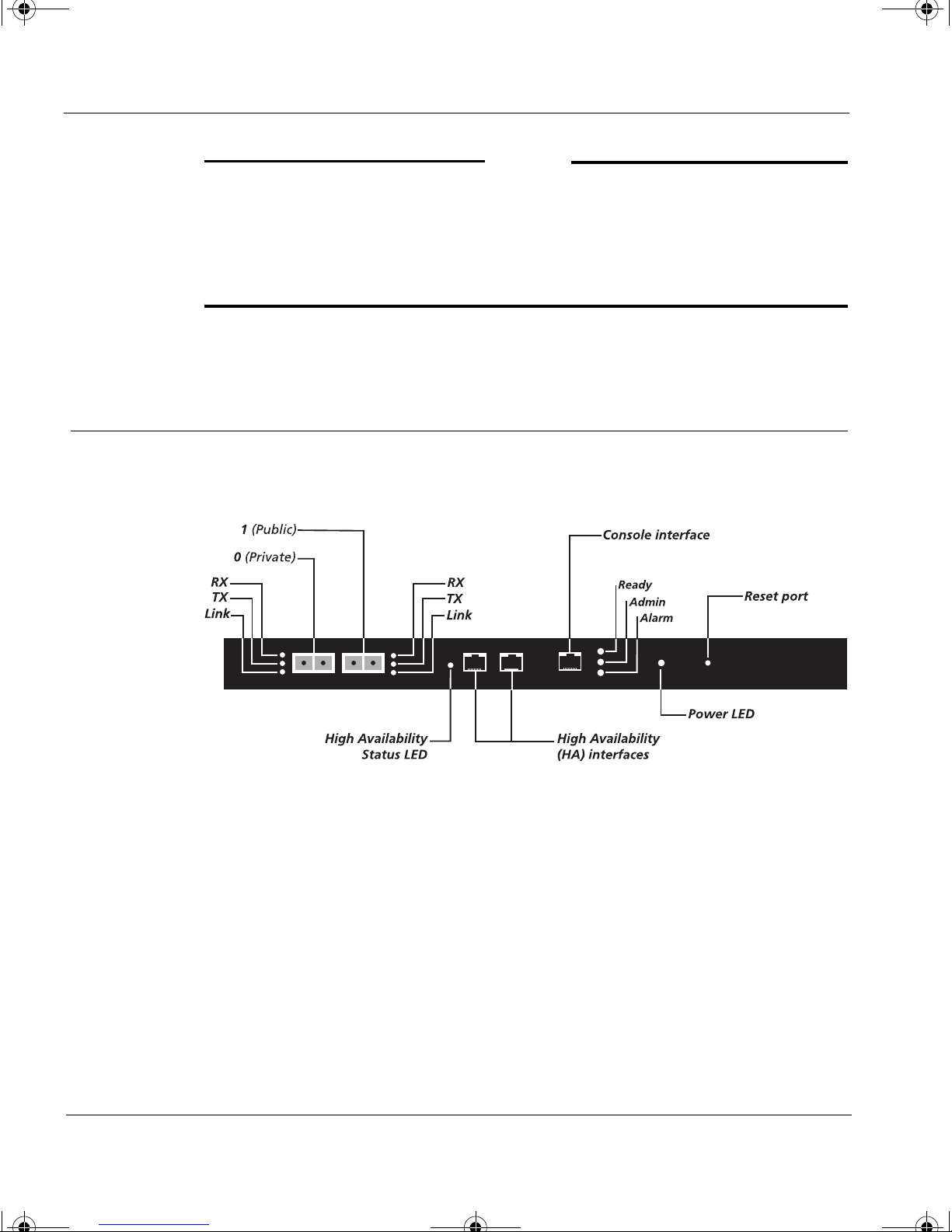
Key features of the Firebox Vclass 100 appliance
The front panel of the Firebox Vclass 100 security appliance contains the
features shown in the following illustration.
Two Gigabit Ethernet interfaces Labeled 0 and 1
Three LEDs per interface Labelled RX, TX and Link
Two Ethernet interfaces Labeled HA1 and HA2 (High
Three status LED’s Labeled Alarm, Admin and Ready
One RJ-45 interface Labeled Console
One LED Labeled Power
One pin-hole port Labeled Reset
12 Vcontroller 3.2
Availability)

1install_guide.book Page 13 Friday, June 7, 2002 1:10 PM
What you should know about these features
Power This LED indicates that the appliance has been
Alarm The Alarm LED is lit when an alarm is activated.
Admin The Admin LED is lit whenever a user or system
Key features of the Firebox Vclass 100 appliance
fully turned on and is ready for administration
and/or use.
The Firebox Vclass appliance supports multiple
types of alarm notification including LED
activation, page/e-mail message, and the Alarm
Manager feature of the WatchGuard Vcontroller,
which are discussed in the System Administration
Guide.
administrator is currently connected to the
Firebox Vclass appliance by means of the
Vcontroller software or by means of a terminal
window and the WatchGuard CLI.
Ready The Ready LED is lit when the Firebox Vclass
appliance is ready for network traffic. (This LED
will blink when the appliance is powering up or
powering down.)
Gigabit interfaces Two Gigabit Ethernet interfaces, labeled "0" and
"1" (corresponding to Private and Public), act as
the primary conduits through which passes all of
the network data traffic. These interfaces are
multi-mode, but they do not support 10/100
communications.
On each side of the two Gigabit interfaces are
three LEDs labeled RX, TX, and Link.
The Link LED is lit when a connection is active.
The RX LED will blink steadily when data packets
are being received by the appliance.
The TX LED will blink steadily when data packets
are being transmitted.
HA interfaces Two Ethernet interfaces, labelled HA1 and HA2
(for High Availability) enable you to connect with a
cross-over Ethernet cable to other HA-ready
Installation Guide 13

1install_guide.book Page 14 Friday, June 7, 2002 1:10 PM
CHAPTER 1: A Tour of the WatchGuard Firebox Vclass Security Appliances
Firebox Vclass appliances for failover (backup)
protection. Incorporated into the two highavailability Ethernet ports are two indicator lights
labeled 10 and 100.These LEDs indicate (1) a
connection to a hub or direct-connect workstation
is active, (2) the speed of the link (10 Mbps or 100
Mbps Ethernet), and (3) that traffic is being
transmitted.
HA status LED This light reports on the current status of this
appliance, if it is one of two connected as a highavailability system. If this is the primary
appliance, and the light is on and steady, the
system is functional, and this appliance is online.
If this is the primary appliance and the LED is
blinking, a failover has occurred and the
secondary appliance is on-line. (That appliance’s
HA LED should be steadily lit, indicating that it is
now the primary appliance.)
For more information on HA setup, see the System
Administration Guide.
Console interface A single RJ-45 interface, labelled Console, supports
a direct workstation-to-appliance connection, at
which time you can use the WatchGuard
Command Line Interface (CLI) to administer and
test this appliance. To learn more about this
administrative option, open and review the
WatchGuard CLI User Guide included on the
installer CD.
Reset port This opening allows you to insert a straight pin or
paperclip and press an internal Reset switch that
restarts the appliance. This is an alternative to
unplugging and replugging the power cord.
14 Vcontroller 3.2
 Loading...
Loading...