Page 1

ADMINISTRATION
Cisco Small Business
RV 120W Wireless-N VPN Firewall
GUIDE
Page 2

CCDE, CCENT, CCSI, Cisco Eos, Cisco HealthPresence, Cisco IronPort, the Cisco logo, Cisco Nurse Connect, Cisco Pulse, Cisco SensorBase, Cisco StackPower,
Cisco StadiumVision, Cisco TelePresence, Cisco Unified Computing System, Cisco WebEx, DCE, Flip Channels, Flip for Good, Flip Mino, Flipshare (Design), Flip
Ultra, Flip Video, Flip Video (Design), Instant Broadband, and Welcome to the Human Network are trademarks; Changing the Way We Work, Live, Play, and Learn,
Cisco Capital, Cisco Capital (Design), Cisco:Financed (Stylized), Cisco Store, Flip Gift Card, and One Million Acts of Green are service marks; and Access
Registrar, Aironet, AllTouch, AsyncOS, Bringing the Meeting To You, Catalyst, CCDA, CCDP, CCIE, CCIP, CCNA, CCNP, CCSP, CCVP, Cisco, the Cisco Certified
Internetwork Expert logo, Cisco IOS, Cisco Lumin, Cisco Nexus, Cisco Press, Cisco Systems, Cisco Systems Capital, the Cisco Systems logo, Cisco Unity,
Collaboration Without Limitation, Continuum, EtherFast, EtherSwitch, Event Center, Explorer, Follow Me Browsing, GainMaker, iLYNX, IOS, iPhone, IronPort, the
IronPort logo, Laser Link, LightStream, Linksys, MeetingPlace, MeetingPlace Chime Sound, MGX, Networkers, Networking Academy, PCNow, PIX, PowerKEY,
PowerPanels, PowerTV, PowerTV (Design), PowerVu, Prisma, ProConnect, ROSA, SenderBase, SMARTnet, Spectrum Expert, StackWise, WebEx, and the WebEx
logo are registered trademarks of Cisco Systems, Inc. and/or its affiliates in the United States and certain other countries.
All other trademarks mentioned in this document or website are the property of their respective owners. The use of the word partner does not imply a
partnership relationship between Cisco and any other company. (0910R)
© 2009 Cisco Systems, Inc. All rights reserved. 78-19307-01
Page 3
Contents
Chapter 1: Introduction 1
Product Overview 1
Getting to Know the Cisco RV 120W 3
Front Panel 3
Back Panel 4
Mounting the Cisco RV 120W 5
Installation Guidelines 5
Wall Mounting 5
Connecting the Equipment 7
Using the Setup Wizard 8
Starting the Wizard 8
Connecting Your Hardware 9
Entering Login and Internet Connection Information 13
Configuring Security 14
Manually Connecting Your System 16
Verifying the Hardware Installation 17
Connecting to Your Wireless Network 17
Getting Started in the Cisco RV 120W Device Manager 18
Logging In 18
Using the Getting Started Page 19
Navigating through the Pages 20
Saving Your Changes 21
Viewing the Help Files 22
Viewing Device Statistics 22
Viewing the System Summary 22
Viewing the Wireless Status 25
Viewing the IPsec Connection Status 26
Viewing the QuickVPN Connection Status 27
Viewing Logs 27
Viewing Available LAN Hosts 28
Viewing the Port Triggering Status 28
Viewing Port Statistics 28
Cisco RV 120W Administration Guide 1
Page 4

Contents
Chapter 2: Configuring Networking 30
Configuring the Wide Area Network (WAN) 30
Configuring the WAN for an IPv4 Network 30
Configuring the Internet Connection Type 30
Configuring Internet Address Information 32
Configuring Domain Name System (DNS) Server Information 33
Configuring Maximum Transmit Unit (MTU) 33
Configuring the Cisco RV 120W Media Access Control (MAC) Address 33
Configuring the WAN for an IPv6 Network 34
Configuring a Static IP Address 34
Configuring DHCPv6 35
Creating PPPoE Profiles 35
Configuring the Local Area Network (LAN) 36
Changing the Default Cisco RV 120W IP Address 37
Configuring DHCP 37
Configuring the LAN DNS Proxy 38
Configuring Virtual LANs (VLANs) 39
Enabling VLANs 39
Creating a VLAN 39
Configuring Port VLANs 40
Associating the Wireless Port to VLANs 41
Configuring Multiple VLAN Subnets 42
Configuring IPv6 LAN Properties 43
Configuring IPv6 Address Pools 44
Configuring LAN Groups 45
Adding a Static IP Address for a Device on the LAN 45
Viewing DHCP Leased Clients 46
Configuring a DMZ Host 46
Configuring Internet Group Management Protocol (IGMP) 47
Configuring Routing 48
Choosing the Routing Mode 48
Viewing Routing Information 48
Configuring Static Routing 49
Configuring Dynamic Routing 50
Cisco RV 120W Administration Guide 2
Page 5
Contents
Configuring Port Management 52
Configuring Dynamic DNS (DDNS) 53
Configuring IPv6 54
Configuring the Routing Mode 54
Configuring IPv6 Static Routing 54
Configuring RIP next generation (RIPng) 55
Configuring IPv6 to IPv4 Tunneling 56
Configuring 6to4 Tunneling 56
Configuring Intra-Site Automatic Tunnel Addressing Protocol Tunnels 56
Viewing IPv6 Tunnel Information 57
Configuring Router Advertisement 57
Chapter 3: Configuring the Wireless Network 60
A Note About Wireless Security 60
Wireless Security Tips 60
General Network Security Guidelines 62
Understanding the Cisco RV 120W’s Wireless Networks 63
Configuring Wireless Profiles 63
Configuring the Group Key Refresh Interval 65
Configuring RADIUS Authentication Parameters 66
Configuring Access Points 66
Enabling or Disabling APs 66
Editing an AP’s Properties 67
Using MAC Filtering 68
Viewing AP Status 68
Configuring the Wireless Radio Properties 70
Configuring Basic Wireless Radio Settings 70
Configuring Advanced Wireless Radio Settings 71
Configuring Wi-Fi Protected Setup 72
Configuring a Wireless Distribution System (WDS) 73
Cisco RV 120W Administration Guide 3
Page 6

Contents
Chapter 4: Configuring the Firewall 74
Cisco RV 120W Firewall Features 74
Configuring Basic Firewall Settings 76
Protecting from Attacks 76
Configuring Universal Plug and Play (UPnP) 77
Viewing UPnP Information 78
Enabling Session Initiation Protocol Application-Level Gateway (SIP ALG) 78
Configuring the Default Outbound Policy 79
Configuring Firewall Rules 79
Creating a Firewall Rule 80
Managing Firewall Rules 84
Creating Custom Services 84
Creating Firewall Schedules 85
Blocking and Filtering Content and Applications 85
Blocking Web Applications and Components 86
Adding Trusted Domains 87
Adding Blocked Keywords 87
Configuring MAC Address Filtering 88
Configuring IP/MAC Address Binding 89
Firewall Rule Examples 90
Configuring Port Triggering 92
Configuring Port Forwarding 94
Restricting Sessions 97
Configuring Remote Management 98
Configuring One-to-One Network Address Translation (NAT) 99
Chapter 5: Configuring Virtual Private Networks (VPNs) and Security 101
Configuring VPNs 102
Creating Cisco QuickVPN Client Users 102
Using the VPN Wizard 102
Viewing the Default Values 104
Cisco RV 120W Administration Guide 4
Page 7
Configuring IP Security Policies 105
Configuring IKE Policies 105
Configuring VPN Policies 108
Configuring VPN Clients 113
Monitoring VPN Tunnel Status 113
Configuring IPsec Users 114
Configuring VPN Passthrough 115
Contents
Configuring Security 115
Using Certificates for Authentication 115
Uploading CA Certificates 117
Uploading Self Certificates 117
Generating a Self Certificate Request 117
Downloading the Router’s Current Certificate 118
Using the Cisco RV 120W With a RADIUS Server 118
Configuring 802.1x Port-Based Authentication 119
Chapter 6: Configuring Quality of Service (QoS) 120
Configuring Bandwidth Profiles 120
Configuring Traffic Flows 121
Configuring Traffic Metering 122
Configuring 802.1p 124
Configuring 802.1p to Queue Mapping 125
Configuring 802.1p CoS to DSCP Remarking 125
Chapter 7: Administering Your Cisco RV 120W 126
Setting Password Complexity 126
Configuring User Accounts 127
Setting the Timeout Value 128
Configuring Simple Network Management (SNMP) 128
Editing SNMPv3 Users 128
Adding SNMP Traps 129
Configuring Access Control Rules 129
Configuring Additional SNMP Information 130
Cisco RV 120W Administration Guide 5
Page 8

Contents
Using Diagnostic Tools 130
Using PING 131
Using Trace Route 131
Performing a DNS Lookup 131
Capturing and Tracing Packets 131
Configuring Logging 131
Configuring Local Logging 132
Configuring Remote Logging 133
Configuring the Logging Type and Notification 134
Configuring E-Mailing of Log Events 135
Configuring Discovery (Bonjour) 135
Configuring VLAN Associations 136
Configuring Date and Time Settings 136
Backing Up and Restoring the System 137
Upgrading Firmware 138
Rebooting the Cisco RV 120W 138
Restoring the Factory Defaults 138
Appendix A: Using Cisco QuickVPN for Windows 2000, XP, or Vista 139
Overview 139
Before You Begin 139
Installing the Cisco QuickVPN Software 140
Installing from the CD-ROM 140
Downloading and Installing from the Internet 142
Using the Cisco QuickVPN Software 142
Appendix B: Where to Go From Here 146
Cisco RV 120W Administration Guide 6
Page 9

Introduction
This chapter provides information to familiarize you with the product features,
guide you through the installation process, and get started using the browserbased Device Manager. It contains the following sections:
1
• Product Overview, page 1
• Getting to Know the Cisco RV 120W, page 3
• Mounting the Cisco RV 120W, page 5
• Connecting the Equipment, page 7
• Verifying the Hardware Installation, page 17
• Getting Started in the Cisco RV 120W Device Manager, page 18
Product Overview
Thank you for choosing the Cisco Small Business RV 120W Wireless-N VPN
Firewall. The Cisco RV 120W is an advanced Internet-sharing network solution for
your small business needs. It allows multiple computers in your office to share an
Internet connection through both wired and wireless connections.
The Cisco RV 120W provides a Wireless-N access point, combined with support
for Virtual Private Networks (VPNs) to make your network more secure. Its 10/100
Ethernet WAN interface connects directly to your broadband DSL or Cable
modem. There are four full-duplex 10/100 Ethernet LAN interfaces that can
connect up to four devices. The wireless access point supports the 802.11n
standard with MIMO technology, which multiplies the effective data rate. This
technology results in better throughput and coverage than provided by 802.11g
networks.
Cisco RV 120W Administration Guide 1
Page 10

Introduction
Product Overview
1
The Cisco RV 120W incorporates a Stateful Packet Inspection (SPI)-based firewall
with Denial of Service (DoS) prevention and a Virtual Private Network (VPN)
engine for secure communication between mobile or remote workers and branch
offices. The Cisco RV 120W supports up to ten gateway-to-gateway IP Security
(IPsec) tunnels to facilitate branch office connectivity through encrypted virtual
links. Users connecting through a VPN tunnel are attached to your company’s
network with secure access to files, e-mail, and your intranet as if they were in the
building. You can also use the VPN capability to allow users on your small office
network to securely connect out to a corporate network
The Cisco RV 120W’s wireless access point supports Wireless Distribution
System (WDS), which allows the wireless coverage to be expanded without wires.
It also supports multiple SSIDs for the use of virtual networks (up to 4 separate
virtual networks), with 802.1Q-based VLAN support for traffic separation. The
Cisco RV 120W implements WPA2-PSK, WPA2-ENT, and WEP encryption, along
with other security features including the disabling of SSID broadcasts, MACbased filtering, and allowing or denying “time of day” access per SSID. The Cisco
RV 120W supports Wi-Fi Multimedia (WMM) and Wi-Fi Multimedia Power Save
(WMM-PS) for wireless Quality of Service (QoS). It supports 802.1p, Differentiated
Services Code Point (DSCP), and Type of Service (ToS) for wired QoS, which can
improve the quality of your network when using delay-sensitive Voice over IP
(VoIP) applications and bandwidth-intensive video streaming applications.
With the Cisco RV 120W’s embedded web server, its settings can be configured
using the browser-based Device Manager. The Cisco RV 120W supports Internet
Explorer, Firefox, and Safari web browsers. The Cisco RV 120W also provides a
setup wizard and VPN wizard. The setup wizard allows you to easily configure the
Cisco RV 120W’s basic settings. You can use the VPN wizard to easily configure
VPN tunnels.
Cisco RV 120W Administration Guide 2
Page 11
Introduction
Getting to Know the Cisco RV 120W
Getting to Know the Cisco RV 120W
Front Panel
1
POWER—The Power LED lights up green to indicate the device is powered on.
Flashes green when the power is coming on or software is being upgraded.
WAN LED—The WAN (Internet) LED lights up green when the device is connected
to your cable or DSL modem. The LED flashes green when the device is sending
or receiving data over the WAN port.
WIRELESS—The Wireless LED lights up green when the wireless module is
enabled. The LED is off when the wireless module is disabled. The LED flashes
green when the device is transmitting or receiving data on the wireless module.
LAN—These four LEDs correspond to the four LAN (Ethernet) ports of the Cisco
RV 120W. If the LED is continuously lit green, the Cisco RV 120W is connected to a
device through the corresponding port (1, 2, 3, or 4). The LED for a port flashes
green when the Cisco RV 120W is actively sending or receiving data over that
port.
Cisco RV 120W Administration Guide 3
Page 12

Introduction
Getting to Know the Cisco RV 120W
Back Panel
1
RESET Button—The Reset button has two functions:
• If the Cisco RV 120W is having problems connecting to the Internet, press
the RESET button for less than five seconds with a paper clip or a pencil tip.
This is similar to pressing the reset button on your PC to reboot it.
• If you are experiencing extreme problems with the Cisco RV 120W and
have tried all other troubleshooting measures, press and hold in the RESET
button for 10 seconds. This will restore the factory defaults and clear all of
the Cisco RV 120W settings.
LAN Ports (1-4)—These ports provide a LAN connection to network devices,
such as PCs, print servers, or additional switches.
WAN Por t—The WAN port is connected to your Internet device, such as a cable or
DSL modem.
ON/OFF Power Switch—Press this button to turn the Cisco RV 120W on and off.
When the button is pushed in, power is on.
Power Port—The power port is where you connect the AC power cable.
Cisco RV 120W Administration Guide 4
Page 13
Introduction
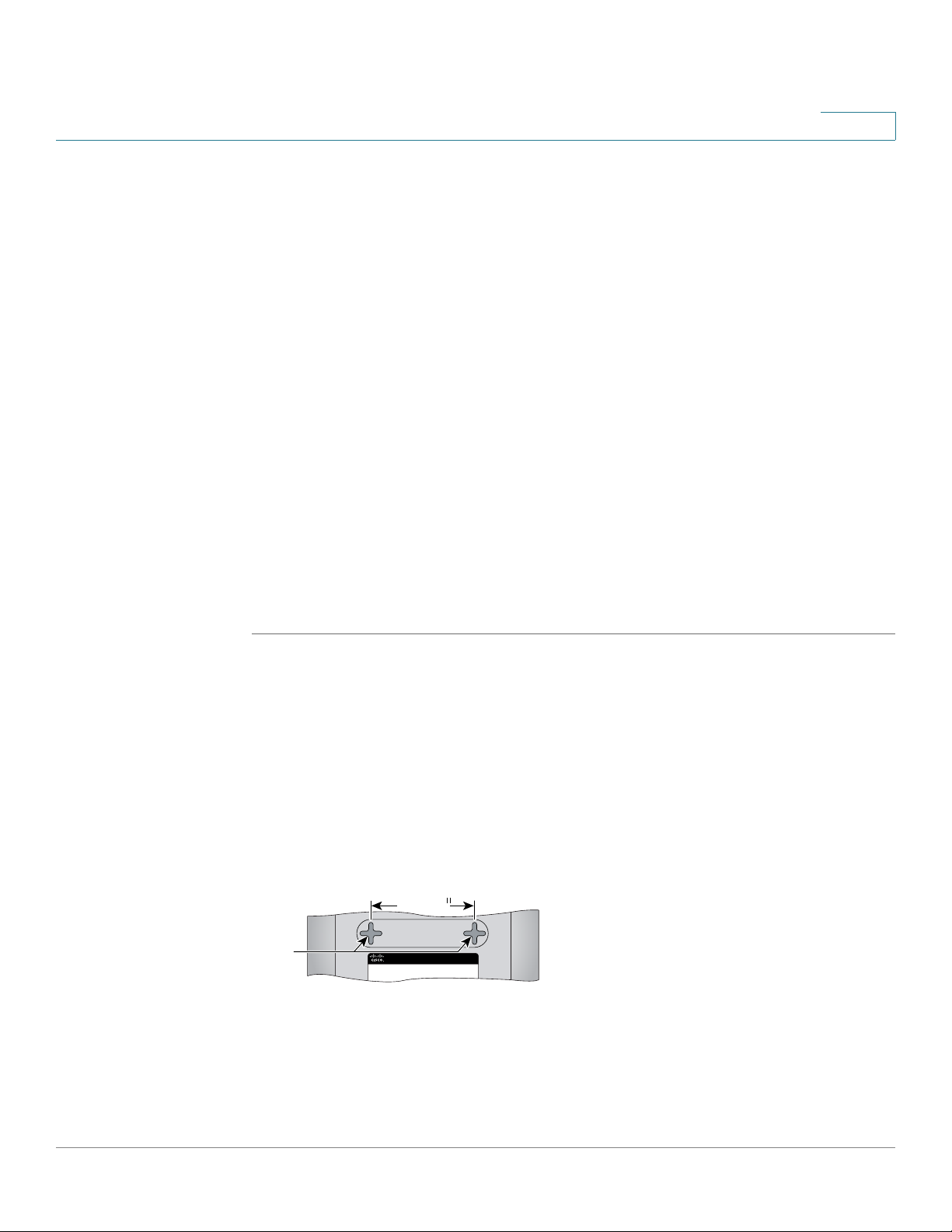
195114
Wall
mount
slots
2-7/16
Mounting the Cisco RV 120W
Mounting the Cisco RV 120W
You can place your Cisco RV 120W on a desktop or mount it on a wall.
Installation Guidelines
• Ambient Temperature—To prevent the device from overheating, do not
operate it in an area that exceeds an ambient temperature of
104°F (40°C).
• Air Flow—Be sure that there is adequate air flow around the device.
• Mechanical Loading—Be sure that the device is level and stable to avoid
any hazardous conditions.
For desktop placement, place the Cisco RV 120W device horizontally on a flat
surface so that it sits on its four rubber feet.
1
Wall Mounting
STEP 1 Determine where you want to mount the device and install two screws (not
supplied) that are 2-7/16 in. apart (approximately 61 mm). Mounting screws should
have a head that is approximately 5.5 mm in diameter and 2 mm deep, with a shaft
that is at least15.5 mm long and approximately 3.5 mm wide. (Your wall may
require shorter or longer screws, or drywall anchors.)
Do not mount the screw heads flush with the wall; the screw heads must fit inside
the back of the device.
STEP 2 With the back panel pointing up (if installing vertically), line up the device so that
the wall-mount slots on the bottom of the device line up with the two screws.
Cisco RV 120W Administration Guide 5
Page 14

Introduction
Mounting the Cisco RV 120W
STEP 3 Place the wall-mount slots over the screws and slide the device down until the
1
screws fit snugly into the wall-mount slots.
Cisco RV 120W Administration Guide 6
Page 15
Introduction
Connecting the Equipment
Connecting the Equipment
Before you begin the installation, make sure that you have the following equipment
and services:
Required
• Functional Internet Connection (Broadband DSL or cable modem).
• Ethernet cable for WAN (Internet) connection.
• PC with functional network adapter (Ethernet connection) to run the Setup
Wizard or the Device Manager. The Setup Wizard is supported on Microsoft
Windows 2000, Windows XP, Windows Vista, and Windows 7. You must
have Microsoft Core XML Services (MSXML) software installed on the PC to
run the Setup Wizard. MSXML is available from the following location:
1
http://www.microsoft.com/windows/downloads/
The Device Manager is supported on the following web browsers:
- Microsoft Internet Explorer 6.0 and later
- Mozilla Firefox 3.0 and later
- Apple Safari 3.0 or later.
• Ethernet cable (provided) to connect the PC to the router for configuration.
• Software CD containing Setup Wizard (provided).
Optional
• Uninterruptible Power Supply (UPS) to provide backup power to essential
devices (strongly recommended).
• Ethernet cables for LAN interfaces, if you want to connect additional
devices.
Cisco recommends that you use the Setup Wizard to connect and configure your
Cisco RV 120W. If you do not want to use the setup wizard, skip to the “Manually
Connecting Your System” section on page16.
Cisco RV 120W Administration Guide 7
Page 16
Introduction
Connecting the Equipment
NOTE You must connect one PC with an Ethernet cable for the purpose of the initial
STEP 1 Make sure that all of the network hardware is powered off, including the
1
Using the Setup Wizard
Follow these steps to use the Cisco RV 120W Setup Wizard. The Setup Wizard
displays on-screen instructions that guide you through the installation, but you may
find it useful to refer to this document during installation.
configuration. After you complete the initial configuration, administrative tasks can
be performed using a wireless connection.
Starting the Wizard
Cisco RV 120W and cable or DSL modem.
STEP 2 Insert the CD that shipped with the Cisco RV 120W into the PC you are using to
configure the Cisco RV 120W. The Setup Wizard automatically begins.
STEP 3 Click Start to begin the installation.
STEP 4 Click the check box to accept the software license agreement and click Next.
STEP 5 The Setup Wizard verifies the network adapter on your PC is functional. If you
receive an error, view your PC’s network connections to make sure the network
adapter is working and click Back to test the connection again.
Next:
• If your network adapter is functional and you have not yet connected your
hardware, the Install Router window appears. (See Connecting Your
Hardware, page 9.)
• If your network adapter is functional, you have already connected your
hardware, and your Internet connection has been detected, the Secure Your
Router Settings window appears. (See Configuring Security, page 14.)
Cisco RV 120W Administration Guide 8
Page 17

Introduction
Connecting the Equipment
STEP 1 You should have an Ethernet cable connecting your PC to the cable or DSL
1
Connecting Your Hardware
modem. Unplug one end of the cable from your PC and plug it into the port marked
“WAN” on the device. Click Next.
Cisco RV 120W Administration Guide 9
Page 18

Introduction
Connecting the Equipment
STEP 2 Connect one end of a different Ethernet cable to one of the LAN (Ethernet) ports on
1
the back of the device. (In this example, the LAN 2 port is used.) Connect the other
end to an Ethernet port on the PC that is running the Setup Wizard. Click Next.
STEP 3 Power on the cable or DSL modem and wait until the connection is active.
Cisco RV 120W Administration Guide 10
Page 19
Introduction
!
Connecting the Equipment
STEP 4 Connect the power adapter to the Cisco RV 120W power port. Click Next.
CAUTION Use only the power adapter that is supplied with the device. Using a different
1
power adapter could damage the device.
STEP 5 Plug the other end of the adapter into an electrical outlet.
Cisco RV 120W Administration Guide 11
Page 20
Introduction
Connecting the Equipment
STEP 6 On the Cisco RV 120W, push in the ON/OFF POWER SWITCH button. The Setup
1
Wizard searches for the Cisco RV 120W.
The POWER LED on the front panel lights up green when the power adapter is
connected properly and the device is turned on.
Next:
• If your hardware connection is successful, but the Setup Wizard needs
more information about your Internet connection, the Enter Username and
Password window appears. (See Entering Login and Internet Connection
Information, page 13.)
• If your hardware connection is successful and the Setup Wizard
successfully detects your Internet connection, the Configure Router
window displays. (See Configuring Security, page 14.)
Cisco RV 120W Administration Guide 12
Page 21
Introduction
Connecting the Equipment
STEP 1 Enter the username and password for your Cisco RV 120W. The default username
STEP 2 Choose your Internet connection type:
STEP 3 The Setup Wizard confirms your Internet connection settings. If it cannot detect or
1
Entering Login and Internet Connection Information
and password are both admin. Click Next.
• Telephone (DSL)
• Cable broadband
• I don’t know
Click Next.
confirm your settings, you might need to provide information about your Internet
connection type. You can get this information from your ISP.
The types of Internet connections are:
• Dynamic (DHCP)—Your PC receives its IP address from your cable or DSL
modem. This address can change.
• Static IP Connection—Your Internet Service Provider (ISP) has assigned
you an IP address that does not change. You will need this address and
some additional information (see Step 4) to proceed with installation.
• PPPoE—You have a point-to-point connection to the Internet (used mainly
with asymmetric DSL).
• PPTP—Your provider uses point-to-point tunneling protocol (used in
Europe).
• LT 2 P —Your provider uses layer 2 tunneling protocol (used in Europe).
After selecting your connection type, click Next.
STEP 4 If you chose:
• Dynamic (DHCP)—Proceed to Step 5.
• Static IP Connection—Provide your Static IP Address, Subnet Mask,
Gateway IP, DNS, and secondary DNS (optional). This information comes
from your ISP. Click Next after entering the information.
• PPPoE—Provide your account name (for example,
password. Click Next after entering the information.
Cisco RV 120W Administration Guide 13
john@ISPname.net
), and
Page 22
Introduction
Connecting the Equipment
STEP 5 The Setup Wizard configures your connection, verifies the router settings, and
STEP 6 To configure your home network, click Next.
• PPTP (Europe)—Provide your account name (for example,
john@ISPname.net
entering the information.
• L2TP (Europe)—Provide your account name (for example,
john@ISPname.net), password, and server IP address. Click Next after
entering the information.
checks the network connection. Click Next.
), password, and server IP address. Click Next after
Configuring Security
1
STEP 1 Enter a new Cisco RV 120W administration password and click Next. For security
reasons, you should not use the default password. Follow these password
guidelines:
• Passwords should not contain dictionary words from any language or the
default password.
• Passwords should contain a mix of letters (both upper- and lowercase),
numbers, and symbols.
• Passwords must be at least 8 but no more than 30 characters.
• Password security ratings are shown to the right of the password you enter,
and are rated from weak to secure. Cisco recommends using a password
rated as secure.
STEP 2 Enter a name (SSID) for your wireless network and click Next. You should change
the default SSID to a unique name. The SSID is case-sensitive.
NOTE For added security, disable broadcasting of the SSID. You can disable SSID
broadcast using the Device Manager; see Editing an AP’s Properties, page 67.
Cisco RV 120W Administration Guide 14
Page 23
Introduction
Connecting the Equipment
STEP 3 Select the type of security to use:
1
Best Security (WPA2)
Strong wireless security that uses a password (security key) to protect your
network. Recommended for most networks. The devices you connect to your
wireless network must support WPA2; see the support information for your device
if you have questions.
a. Enter a security key (must be at least 8 and no more than 63 characters) or use
the randomly-generated one provided by the Cisco RV 120W. Keys should
contain a mix of letters (both upper- and lowercase), numbers, and symbols.
Security key ratings are shown to the right of the password you enter, and are
rated from weak to secure. Cisco recommends using a password rated as
secure.
b. Click Next.
Better Security (WPA)
Wireless security that uses a password (security key) to protect your network. It is
less secure than WPA2, but it is supported by older devices. If the devices you are
connecting to your wireless network do not support WPA2, choose this option.
a. Enter a security key (must be at least 8 and no more than 63 characters) or use
the randomly-generated one provided by the Cisco RV 120W. Keys should
contain a mix of letters (both upper- and lowercase), numbers, and symbols.
Security key ratings are shown to the right of the password you enter, and are
rated from weak to secure. Cisco recommends using a password rated as
secure.
b. Click Next.
No Security
This option is not recommended; it allows devices to connect to your wireless
network if the network name is known.
a. Click Next.
b. Click Ye s when the warning message is displayed.
Cisco RV 120W Administration Guide 15
Page 24
Introduction
Connecting the Equipment
STEP 4 The security settings for your network are shown. To save these settings in a text
NOTE You must enter this security information on each device that connects to your
STEP 5 The Cisco RV 120W configures your connection and displays a status message if
STEP 6 The Cisco RV 120W displays a message if it has been configured and is
1
file on your PC, check the box provided. To print, click Print these settings. Click
Next to confirm these settings. (If you chose to save these settings to your
desktop, then click OK.)
network. Save this information!
the configuration is successful. Click Next.
successfully connected to the Internet. Click Finish.
Manually Connecting Your System
Use these procedures if you do not want to use the Setup Wizard.
NOTE You must connect one PC with an Ethernet cable for the purpose of the initial
configuration. After you complete the initial configuration, administrative tasks can
be performed using a wireless connection.
STEP 1 Connect your equipment as described in “Connecting Your Hardware” section
on page 9.
STEP 2 Connect to the Device Manager to view and configure your Cisco RV 120W
settings. When you connect to the Device Manager, the Getting Started page
shows links that you can click to perform basic tasks. At a minimum, we
recommend that you:
• Change the Cisco RV 120W password (see Configuring User Accounts,
page 127.)
• Review wireless profile and set security settings (see Configuring the
Wireless Radio Properties, page 70.)
Cisco RV 120W Administration Guide 16
Page 25

Introduction
Verifying the Hardware Installation
See the “Getting Started in the Cisco RV 120W Device Manager” section on
page18 for more information.
Verifying the Hardware Installation
To verify the hardware installation, complete the following tasks:
• Check the LED states, as described in Getting to Know the Cisco RV
120W, page 3.
• Connect a PC to an available LAN port and verify that you can connect to a
website on the Internet, such as www.cisco.com.
1
• Configure a device to connect to your wireless network and verify the
wireless network is functional. See Connecting to Your Wireless Net work,
page17.
Connecting to Your Wireless Network
To connect a device (such as a PC) to your wireless network, you must configure
the wireless connection with the security information you entered when you used
the Setup Wizard or that you configured using the Device Manager.
The following steps are provided as an example; you may need to configure your
device differently. For instructions that are specific to your device, consult the user
documentation for your device.
STEP 1 Open the wireless connection settings window or program for your device. Your
PC may have special software installed to manage wireless connections, or you
may find wireless connections under the Control Panel in the Network
Connections or Network and Internet window. (The location depends on your
operating system.)
STEP 2 Enter the network name (SSID) you chose for your network when you configured
the Cisco RV 120W.
Cisco RV 120W Administration Guide 17
Page 26

Introduction
Getting Started in the Cisco RV 120W Device Manager
STEP 3 Choose the type of encryption and enter the security key that you chose when
setting up the Cisco RV 120W. If you did not enable security (not recommended),
leave these fields blank.
STEP 4 Verify your wireless connection and save your settings.
Getting Started in the Cisco RV 120W Device Manager
The Device Manager allows you to configure and manage your Cisco RV 120W,
including the following tasks:
• View system status information
1
• Configure local and wide-area network settings
• Configure wireless security, firewall, and VPN settings
• Configure quality of service
• Perform software upgrades
Logging In
To use the Device Manager:
STEP 1 On a PC connected to a LAN port on the back panel of the Cisco RV 120W, start
your web browser. (If you have performed the initial configuration using the Setup
Wizard, you can connect using the Cisco RV 120W’s wireless connection.)
STEP 2 To connect to the Device Manager, enter
http://192.168.1.1 in your browser’s address field, and press Enter. A password
request page appears.
NOTE The default IP address is 192.168.1.1. If there is another device connected to
the network that is acting as a DHCP server, that device may assign a
different address to the Cisco RV 120W. You must use the assigned IP
address to connect to the Cisco RV 120W.
Cisco RV 120W Administration Guide 18
Page 27
Introduction
Getting Started in the Cisco RV 120W Device Manager
STEP 3 In the Username and Password fields, enter the default user name (which is admin)
and password (which is also admin), in lowercase letters. Then click Log In.
Using the Getting Started Page
The Getting Started page displays some of the most common configuration tasks.
Click these underlined tasks to view the configuration windows. You can access
the following tasks from the Getting Started page:
Initial Settings
• Change Default Administrator Password—See Configuring User
Accounts, page 127.
• Configure WAN Settings—See Configuring the WAN for an IPv4
Network, page 30.
1
• Configure LAN Settings—See Configuring the Local Area Network (LAN),
page 36.
• Review Wireless Profile and Set Security Settings—See Configuring
Access Points, page 66.
• Add VPN Clients—See Configuring IPsec Users, page 114.
Quick Access
• Upgrade Device Software—See Upgrading Firmware, page 138.
• Configure Site to Site VPN—See Using the VPN Wizard, page 102.
• Configure Remote Management Access—See Configuring Remote
Management, page 98.
Device Status
• System Summary—See Viewing Device Statistics, page 22.
• Wireless Status—See Viewing the Wireless Status, page 25.
• VPN Status—See Viewing the IPsec Connection Status, page 26.
To get support for your device, click the Support link at the bottom of the page. To
visit the online support forums, click Forums.
To prevent the Getting Started page from showing when the Device Manager is
started, check the Don’t show this on start-up box.
Cisco RV 120W Administration Guide 19
Page 28

Introduction
Getting Started in the Cisco RV 120W Device Manager
Navigating through the Pages
Use the navigation tree in the left pane to open the configuration pages. Click a
menu item on the left panel to expand it. Click the menu names displayed
underneath to perform an action or view a sub-menu.
1
Cisco RV 120W Administration Guide 20
Page 29
Introduction
Getting Started in the Cisco RV 120W Device Manager
Saving Your Changes
When you finish making changes on a configuration page, click Save to save the
changes, or click Cancel to undo your changes.
1
Cisco RV 120W Administration Guide 21
Page 30
Introduction
Viewing Device Statistics
1
Viewing the Help Files
To view more information about a configuration page, click the Help link near the
top right corner of the page.
Viewing Device Statistics
The Cisco RV 120W provides real-time statistics for the device. To access
statistics, in the Device Manager, choose Status.
Viewing the System Summary
To view the system summary, choose Status > System Summary. Click Refresh to
refresh the information and obtain the latest information.
The system summary page displays the following:
• System Name—Name of the device.
• Firmware Version—Current software version the device is running.
Cisco RV 120W Administration Guide 22
Page 31

Introduction
Viewing Device Statistics
1
• Firmware MD5 Checksum—The message-digest algorithm used to verify
the integrity of files.
• PID VID—Product ID and vendor ID of the device.
• CPU Usage—Percentage of CPU currently used.
• Memory Usage—Percentage of memory currently used.
LAN Information
• MAC Address—Hardware address.
• IPv4 Address—Address and subnet mask of the device.
• IPv6 Address—Address and subnet mask of the device (shown only if IPv6
is enabled).
• DHCP Server—Indicates if the device’s DHCP server is enabled or
disabled. If it is enabled, DHCP client machines connected to the LAN port
receive their IP address dynamically.
• DHCP Relay—Indicates if the device is acting as a DHCP relay (DHCP relay
must be enabled).
• DHCPv6 Server: Indicates if the device’s DHCPv6 server is enabled or
disabled. If it is enabled, DHCPv6 client machines connected to the LAN
port receive their IP address dynamically.
• DHCPv6 Server—Indicates if the device’s DHCPv6 server is enabled or
disabled. If it is enabled, DHCP client machines connected to the LAN port
receive their IP address dynamically.
WAN Information
The WAN Information provides the current status of the WAN interfaces. It
provides details about WAN interface and also provides actions that can be taken
on that particular WAN interface. The actions that can be taken differ with the
connection type. If WAN is configured using DHCP, the DHCP release renew
options are available, other connection types offer other options. The Dedicated
WAN Info displays information about the WAN port.
• MAC Address—MAC Address of the WAN port.
• Connection Time—Displays the time duration for which the connection is
up.
Cisco RV 120W Administration Guide 23
Page 32

Introduction
Viewing Device Statistics
1
• Connection Type—Indicates if the WAN IPv4 address is obtained
dynamically through a DHCP server, assigned statically by the user, or
obtained through a PPPoE/PPTP/L2TP ISP connection.
• Connection State—Indicates if the WAN port is connected to the Internet
Service Provider.
• IP Address—IP address of the WAN port.
• Subnet Mask—Subnet Mask for the WAN port.
• NAT—Indicates if the security appliance is in NAT mode (enabled) or routing
mode (disabled).
• Gateway—Gateway IP address of the WAN port.
• Primary DNS—Primary DNS server IP address of the WAN port.
• Secondary DNS—Secondary DNS server IP address of the WAN port.
• NAT (IPv4 Only Mode)—Indicates if the security appliance is in NAT mode
(enabled) or routing mode (disabled).
If connection is DHCP Enabled:
• DHCP Server—Indicates the IP address of the DHCP server to which WAN
port is connected.
• Lease Obtained—Indicates the time at which lease is obtained from the
DHCP server.
• Lease Duration—Indicates the duration for which the lease would remain
active.
Click Renew to release the current IP address and obtain a new one, or Release to
release the current IP address only.
Wireless Information
This section displays information about the Wireless Radio settings.
• Country—Displays the country for which the radio is configured.
• Operating Frequency—Displays the operational frequency band.
• Wireless Network Mode—Displays the Wi-Fi™ mode of the radio (for
example, N or N/G,).
• Channel—Displays the current channel in use by the radio.
Cisco RV 120W Administration Guide 24
Page 33

Introduction
Viewing Device Statistics
1
Available Access Points Table
The table displays the list of Access Points currently enabled in the device. The
table also displays information related to the Access Point, such as Security and
Encryption methods used by the Access Point.
• SSID—This is the Service Set Identifier (SSID) that clients use to connect to
the AP that has this profile. It is referenced in the AP tables and statistics.
• BSSID—The 48 bit unique identifier of the Basic Service Set (BSS) to which
the Access Point belongs.
• Profile Name—This is the unique (alphanumeric) identifier of the wireless
profile attached to the Access Point.
• Security—This field displays the type of wireless security (if any) assigned
to this profile.
• Encryption—This field displays the encryption type that is assigned to the
profile: TKIP, AES, TKIP + AES.
• Authentication—This field displays the client authentication method that is
configured in the profile: PSK, RADIUS, PSK + RADIUS.
Viewing the Wireless Status
This page shows a cumulative total of relevant wireless statistics for the radio and
APs configured on the device. The counters are reset when the device is
rebooted.
Radio Statistics
A given radio can have multiple virtual APs (VAPs) configured and active
concurrently. This table indicates cumulative statistics for the available radio(s).
• Packets—The number of transmitted/received (tx/rx) wireless packets
reported to the radio, over all configured APs.
• Bytes—The number of transmitted/received (tx/rx) bytes of information
reported to the radio, over all configured APs.
• Errors—The number of transmitted/received (tx/rx) packet errors reported
to the radio, over all configured APs.
• Dropped—The number of transmitted/received (tx/rx) packets dropped by
the radio, over all configured APs.
Cisco RV 120W Administration Guide 25
Page 34

Introduction
Viewing Device Statistics
1
• Multicast—The number of multicast packets sent over this radio.
• Collisions—The number of packet collisions reported to the AP.
AP Statistics
This table displays transmit/receive data for a given AP.
• AP Name—The name of the AP.
• Packets—The number of transmitted/received (tx/rx) wireless packets on
the AP.
• Bytes—The number of transmitted/received (tx/rx) bytes of information on
the AP.
• Errors—The number of transmitted/received (tx/rx) packet errors reported
to the AP.
• Dropped—The number of transmitted/received (tx/rx) packets dropped by
the AP.
• Multicast—The number of multicast packets sent over this AP.
• Collisions—The number of packet collisions reported to the AP.
• Poll Interval—Enter a value in seconds for the poll interval. This causes the
page to re-read the statistics from the router and refresh the page
automatically. To modify the poll interval, click the Stop button and then click
Start to restart automatic refresh.
Viewing the IPsec Connection Status
This page displays the status of IPSec connections. You can change the status of a
connection to either establish or disconnect the configured SAs (Security
Associations).
• Policy Name—The name of the IKE or VPN policy associated with this SA.
• Endpoint—Displays the IP address of the remote VPN gateway or client.
• Tx K B —The data transmitted (in KB) over this SA.
• Tx P a ck e ts —The number of IP packets transmitted over this SA.
• State—The current status of the SA for IKE policies. The status can be Not
Connected or IPsec SA Established.
Cisco RV 120W Administration Guide 26
Page 35

Introduction
Viewing Device Statistics
1
Click Connect to establish an inactive SA (connection) or Drop to terminate an
active SA (connection).
The page refreshes automatically to display the most current status for an SA. To
change the refresh settings, in the Poll Interval field, enter a value in seconds for
the poll interval. This causes the page to re-read the statistics from the router and
refresh the page automatically. To modify the poll interval, click the Stop button
and click Start to restart automatic refresh.
Viewing the QuickVPN Connection Status
This page displays the status of QuickVPN connections and allows you to DROP
any existing active (ONLINE) connections.
• Username—The name of the IPSec User associated with the QuickVPN
tunnel.
• Remote IP—Displays the IP address of the remote QuickVPN client. This
could be NAT/Public IP if the client is behind the NAT router.
• Status—Displays the current status of QuickVPN client. OFFLINE means
that QuickVPN tunnel is NOT initiated/established by the IPSec user.
ONLINE means that QuickVPN Tunnel, initiated/established by the IPSec
user, is active.
Click Drop to terminate an active/ONLINE connection and change the status of
QuickVPN client to OFFLINE.
The page refreshes automatically to display the most current status for QuickVPN
users. To change the refresh settings, in the Poll Interval field, enter a value in
seconds for the poll interval. This causes the page to re-read the statistics from
the router and refresh the page automatically. To modify the poll interval, click the
Stop button and click Start to restart automatic refresh.
Viewing Logs
This window displays the system event log, which can be configured to log login
attempts, DHCP server messages, reboots, firewall messages and other
information.
• Facility—From the drop-down list, select the type of logs to display: All,
Kernel, System, IPSec VPN, Local0-Wireless.
- Kernel logs are those that are a part of the kernel code (for example,
firewall).
Cisco RV 120W Administration Guide 27
Page 36

Introduction
Viewing Device Statistics
1
- System logs are those that are a part of user-space applications (for
example, NTP, Session, DHCP).
- IPSec VPN logs are those related to ipsec negotiations. These are
related user space logs. Local0-Wireless are those related to wireless
connection and negotiation.
Click Refresh Logs to view the entries added after the page was opened. Click
Clear Logs to delete all entries in the log window.
Click Send Logs to e-mail the log messages currently displayed in the log window.
Before clicking Send Log, ensure that the e-mail address and server information
are configured on the Administration > Logging > Remote Logging page.
Viewing Available LAN Hosts
This page shows available LAN hosts.
Viewing the Port Triggering Status
The Port Triggering Status page provides information on the ports that have been
opened per the port triggering configuration rules. The ports are opened
dynamically whenever traffic that matches the port triggering rules flows through
them. The table displays the following fields:
• LAN IP Address—Displays the LAN IP address of the device which caused
the ports to be opened.
• Open Ports—Displays the ports that have been opened so that traffic from
WAN destined to the LAN IP address can flow through the router.
• Time Remaining Seconds—This field displays the time for which the port
will remain open when there is no activity on that port. The time is reset
when there is activity on the port.
Click Refresh to refresh the current page and obtain the latest statistics.
Viewing Port Statistics
This table displays the data transfer statistics for the Dedicated WAN, LAN, and
WLAN ports, including the duration for which they were enabled. The following
data is displayed:
Cisco RV 120W Administration Guide 28
Page 37

Introduction
Viewing Device Statistics
1
• Tx P a ck e ts —The number of IP packets going out of the port.
• Rx Packets—The number of packets received by the port.
• Collisions—The number of signal collisions that have occurred on this port.
A collision occurs when the port tries to send data at the same time as a
port on another router or computer that is connected to this port.
• Tx B /s —The number of bytes going out of the port per second.
• Rx B/s—The number of bytes received by the port per second.
• Uptime—The duration for which the port has been active. The uptime is
reset to zero when the router or the port is restarted.
Poll Interval—Enter a value in seconds for the poll interval. This causes the page to
re-read the statistics from the router and refresh the page automatically. To modify
the poll interval, click the Stop button and then Start to restart automatic refresh.
Cisco RV 120W Administration Guide 29
Page 38

Configuring Networking
The networking page allows you to configure networking settings. This chapter
contains the following sections:
• Configuring the Wide Area Network (WAN), page 30
• Configuring the Local Area Network (LAN), page 36
• Configuring Routing, page 48
2
• Configuring Routing, page 48
• Configuring Dynamic DNS (DDNS), page 53
• Configuring IPv6, page 54
Configuring the Wide Area Network (WAN)
Wide area network configuration properties are configurable for both IPv4 and
IPv6 networks. You can enter information about your Internet connection type and
other parameters in these pages.
Configuring the WAN for an IPv4 Network
Configuring WAN properties for an IPv4 network differs depending on which type
of Internet connection you have. See the sections below for detailed instructions.
Configuring the Internet Connection Type
NOTE If your Internet connection does not require a login, you do not need to configure the
ISP Connection Type fields.
Cisco RV 120W Administration Guide 30
Page 39

Configuring Networking
Configuring the Wide Area Network (WAN)
STEP 1 Choose Networking > WAN > IPv4 WAN Configuration.
STEP 2 If you connect to the Internet using one of the following connection types, check
the Internet Connection Requires a Login box:
• Point-to-Point Protocol over Ethernet (PPPoE)—used mainly with
asymmetric DSL.
• Point-to-Point Tunneling Protocol (used in Europe).
• Layer 2 Tunneling Protocol (used in Europe).
STEP 3 Choose your ISP Connection Type:
PPPoE
a. First, create a PPPoE Profile. See “Creating PPPoE Profiles” on page 35.
2
b. Under PPPoE Profile Name, select the profile you created on the WAN > PPPoE
Profiles page. The username, password, and other fields are entered
automatically.
c. Go to “Configuring Maximum Transmit Unit (MTU)” on page 33.
PPTP
a. Provide your username and password. These are assigned to you by the ISP to
access your account.
b. If your ISP supports Microsoft Point-to-Point encryption, check the MPPE
Encryption box.
c. Choose the connectivity type:
• Keep connected—The Internet connection is always on.
• Connect on demand—The Internet connection is on only when traffic is
present. If the connection is idle—that is, no traffic is occurring—the
connection is closed. You might want to choose this if your ISP charges
based on the amount of time that you are connected.
If you choose this connection type, enter the number of minutes after which
the connection shuts off in the Idle Time field.
d. Enter the IP address assigned to you by your ISP in the My IP Address field.
e. Enter the IP address of your ISP’s server in the Server IP Address field.
f. Go to “Configuring Maximum Transmit Unit (MTU)” on page 33.
Cisco RV 120W Administration Guide 31
Page 40

Configuring Networking
Configuring the Wide Area Network (WAN)
L2TP
a. Provide your username and password. These are assigned to you by the ISP to
access your account.
b. Enter your secret phrase. This phrase is known to you and your ISP for use in
authenticating your logon.
c. Choose the connectivity type:
• Keep connected—The Internet connection is always on.
• Connect on demand—The Internet connection is on only when traffic is
present. If the connection is idle—that is, no traffic is occurring—the
connection is closed. You might want to choose this if your ISP charges
based on the amount of time that you are connected.
If you choose this connection type, enter the number of minutes after which
the connection shuts off in the Idle Time field.
2
d. Enter the IP address assigned to you by your ISP in the My IP Address field.
e. Enter the IP address of your ISP’s server in the Server IP Address field.
f. Click Save. If applicable, go to “Configuring Maximum Transmit Unit (MTU)”
on page 33.
Configuring Internet Address Information
STEP 1 If your ISP uses Dynamic Host Control Protocol (DHCP) to assign you an IP
address, you receive a dynamic IP address that is newly generated each time you
log in. In the IP Address Source field, choose Get Dynamically From ISP.
If your ISP has assigned you a static (non-changing) IP address, in the IP Address
Source Field, choose Use Static IP Address and enter the following:
• IP address assigned to you by your ISP.
• IPv4 subnet mask assigned to you by your ISP.
• ISP gateway's IP address.
STEP 2 Click Save.
Cisco RV 120W Administration Guide 32
Page 41

Configuring Networking
Configuring the Wide Area Network (WAN)
Configuring Domain Name System (DNS) Server Information
DNS servers map Internet domain names (for example, www.cisco.com) to IP
addresses. Under DNS Server Source, you can choose whether to get DNS server
addresses automatically from your ISP or to use ISP-specified DNS server
addresses.
STEP 1 If your ISP provides DNS servers, under DNS Server Source, choose Get
Dynamically from ISP.
If your ISP instructs you to use specific DNS server addresses, under DNS Server
Source, choose Use These DNS Servers. Enter the IP address of the primary and
secondary DNS servers.
STEP 2 Click Save.
2
Configuring Maximum Transmit Unit (MTU)
The MTU (Maximum Transmit Unit) is the size of the largest packet that can be sent
over the network. The standard MTU value for Ethernet networks is usually 1500
bytes and for PPPoE connections, it is 1492 bytes.
STEP 1 Unless a change is required by your ISP, Cisco recommends that you choose
Default in the MTU Type field. The default MTU size is 1500 bytes. If your ISP
requires a custom MTU setting, choose Custom and enter the MTU Size.
STEP 2 Click Save.
Configuring the Cisco RV 120W Media Access Control (MAC) Address
The router has a unique 48-bit local Ethernet hardware address. In most cases, the
default MAC address is used to identify your Cisco RV 120W to your ISP. However,
you can change this setting if required by your ISP.
STEP 1 In the MAC Address Source field, choose one of the following:
• Use Default Address (recommended).
• Use this computer's MAC—Choose this option to assign the MAC address
of the computer that you are using to configure the router.
Cisco RV 120W Administration Guide 33
Page 42

Configuring Networking
Configuring the Wide Area Network (WAN)
• Use This MAC Address—Choose this option if you want to manually enter a
MAC Address that is expected by your ISP.
STEP 2 If you chose not to use the default MAC address, in the MAC Address field, enter a
MAC address in the format of XX:XX:XX:XX:XX:XX, where X is a number from 0
through 9 or a letter from A through F.
STEP 3 Click Save.
Configuring the WAN for an IPv6 Network
Configuring WAN properties for an IPv6 network differs depending on which type
of Internet connection you have. See the sections below for detailed instructions.
2
NOTE Before configuring any WAN properties for an IPv6 network, you must configure the
routing mode. Choose Networking > IPv6 > Routing Mode and select IPv4 / IPv6
mode. Click Save.
The Cisco RV 120W can be configured to be a DHCPv6 client of the ISP for this
WAN or a static IPv6 address provided by the ISP can be assigned.
Configuring a Static IP Address
If your ISP assigns you a fixed address to access the Internet, choose this option.
The information needed for configuring a static IP address can be obtained from
your ISP.
STEP 1 In the Internet Address field, choose Static IPv6.
STEP 2 Enter the IPv6 IP address assigned to your router.
STEP 3 Enter the IPv6 prefix length defined by the ISP. The IPv6 network (subnet) is
identified by the initial bits of the address which are called the prefix (for example,
in the IP address 2001:0DB8:AC10:FE01::, 2001 is the prefix). All hosts in the
network have identical initial bits for their IPv6 address; the number of common
initial bits in the network’s addresses is set in this field.
STEP 4 Enter the default IPv6 gateway address, or the IP address of the server at the ISP
that this router will connect to for accessing the internet.
Cisco RV 120W Administration Guide 34
Page 43

Configuring Networking
Configuring the Wide Area Network (WAN)
STEP 5 Enter the primary and secondary DNS server IP addresses on the ISP's IPv6
network. DNS servers map Internet domain names (for example, www.cisco.com)
to IP addresses.
STEP 6 Choose the method by which the router obtains an IP address:
STEP 7 Click Save.
Configuring DHCPv6
When the ISP allows you to obtain the WAN IP settings via DHCP, you need to
provide details for the DHCPv6 client configuration.
STEP 1 In the Internet Address field, choose DHCPv6.
2
STEP 2 Choose if the DHCPv6 client on the gateway is stateless or stateful. If a stateful
client is selected, the gateway connects to the ISP's DHCPv6 server for a leased
address. For stateless DHCP, it is not necessary to have a DHCPv6 server
available at the ISP. Instead, a ICMPv6 discover messages will originate from the
Cisco RV 120W and is used for auto-configuration.
STEP 3 Click Save.
Creating PPPoE Profiles
You can create profiles for multiple PPPoE accounts, which can be useful if you
connect to the Internet using different service provider accounts.
STEP 1 Choose Networking > WAN > PPPoE Profiles. Click Add to create a new profile.
STEP 2 Enter the profile name. This is a label that you choose to identify the profile (for
example, “ISPOne”).
STEP 3 Enter the username and password. These are assigned to you by the ISP to
access your account.
STEP 4 Choose the authentication type:
• Auto-negotiate—The server sends a configuration request specifying the
security algorithm set on it. The router then sends back authentication
credentials with the security type sent earlier by the server.
Cisco RV 120W Administration Guide 35
Page 44

Configuring Networking
Configuring the Local Area Network (LAN)
• PA P—The Cisco RV 120W uses Password Authentication Protocol when
connecting with the ISP.
• CHAP—The Cisco RV 120W uses Challenge Handshake Authentication
Protocol when connecting with the ISP.
• MS-CHAP or MS-CHAPv2—The Cisco RV 120W uses Microsoft Challenge
Handshake Authentication Protocol when connecting with the ISP.
STEP 5 Choose the connectivity type:
• Keep connected—The Internet connection is always on.
• Idle Time—The Internet connection is on only when traffic is present. If the
connection is idle—that is, no traffic is occurring—the connection is closed.
You might want to choose this if your ISP charges based on the amount of
time that you are connected.
2
If you choose this connection type, enter the number of minutes after which
the connection shuts off in the Idle Time field.
STEP 6 Click Save. Your new profile is added to the list.
Configuring the Local Area Network (LAN)
For most applications, the default DHCP and TCP/IP settings are satisfactory. If you
want another PC on your network to be the DHCP server, or if you are manually
configuring the network settings of all of your PCs, disable DHCP.
Instead of using a DNS server, you can use a Windows Internet Naming Service
(WINS) server. A WINS server is the equivalent of a DNS server but uses the
NetBIOS protocol to resolve hostnames. The router includes the WINS server IP
address in the DHCP configuration when acknowledging a DHCP request from a
DHCP client.
You can also enable a DNS proxy. When enabled, the router then acts as a proxy
for all DNS requests and communicates with the ISP's DNS servers. When
disabled, all DHCP clients receive the DNS IP addresses of the ISP.
Cisco RV 120W Administration Guide 36
Page 45

Configuring Networking
Configuring the Local Area Network (LAN)
If machines on your LAN use different IP address ranges (for example, 172.16.2.0
or 10.0.0.0), you can add aliases to the LAN port to give PCs on those networks
access to the Internet. This allows the firewall to act as a gateway to additional
logical subnets on your LAN. You can assign the firewall an IP address on each
additional logical subnet.
NOTE If you have IPv6 configured, see “Configuring IPv6 LAN Properties” on page 43.
Changing the Default Cisco RV 120W IP Address
STEP 1 Choose Networking > LAN > LAN Configuration.
STEP 2 In the IP address field, enter the new IP address for your Cisco RV 120W. The
default IP address is 192.168.1.1. You might want to change the default IP address if
that address is assigned to another piece of equipment in your network.
2
STEP 3 Enter the Subnet Mask for the new IP address.
STEP 4 Click Save. After changing the IP address, you are no longer connected to the
Cisco RV 120W. You must do one of the following:
• Release and renew the IP address on the PC that you are using to access
the Cisco RV 120W (if DHCP is configured on the router).
• Manually assign an IP address to your PC that is in the same subnet as the
Cisco RV 120W. For example, if you change the Cisco RV 120W IP address
to 10.0.0.1, you would assign an IP address in the 10.0.0.0 subnet to your PC.
STEP 5 Open a new browser window and enter the new IP address of the Cisco RV 120W
to re-connect.
Configuring DHCP
By default, the Cisco RV 120W functions as a DHCP server to the hosts on the
Wireless LAN (WLAN) or LAN network and assigns IP and DNS server addresses.
With DHCP enabled, the router's IP address serves as the gateway address to
your LAN. The PCs in the LAN are assigned IP addresses from a pool of
addresses. Each address is tested before it is assigned to avoid duplicate
addresses on the LAN.
Cisco RV 120W Administration Guide 37
Page 46

Configuring Networking
Configuring the Local Area Network (LAN)
STEP 1 Choose Networking > LAN > LAN Configuration.
STEP 2 In the DHCP Section, in the DHCP Mode field, choose one of the following:
• DHCP Server—Choose this to allow the Cisco RV 120W to act as the DHCP
server in the network. Enter the following information:
- Domain Name—Enter the domain name for your network (optional).
- Starting and Ending IP Address—Enter the first and last of the
contiguous addresses in the IP address pool. Any new DHCP client
joining the LAN is assigned an IP address in this range. You can save part
of the range for PCs with fixed addresses. These addresses should be
in the same IP address subnet as the router's LAN IP address.
- Primary and Secondary DNS Server—DNS servers map Internet
domain names (for example, www.cisco.com) to IP addresses. Enter the
server IP addresses in these fields if you want to use different DNS
servers than are specified in your WAN settings.
2
- Lease time—Enter the duration (in hours) for which IP addresses are
leased to clients.
• DHCP Relay—If you chose DHCP Relay as the DHCP mode, enter the
address of the relay gateway in the Relay Gateway field. The relay gateway
transmits DHCP messages between multiple subnets.
• None—Use this to disable DHCP on the Cisco RV 120W. If you want another
PC on your network to be the DHCP server, or if you are manually
configuring the network settings of all of your PCs, disable DHCP.
STEP 3 Click Save.
Configuring the LAN DNS Proxy
STEP 1 Choose Networking > LAN > LAN Configuration.
STEP 2 In the LAN Proxy section, to enable the Cisco RV 120W to act as a proxy for all
DNS requests and communicate with the ISP's DNS servers, check Enable DNS
Proxy. When this feature is enabled, the router acts as a proxy for all DNS requests
and communicates with the ISP's DNS servers (as configured in the WAN settings
page). All DHCP clients receive the Primary/Secondary DNS IP and the IP of the
router where DHCP is running. All DHCP clients receive the DNS IP addresses of
Cisco RV 120W Administration Guide 38
Page 47

Configuring Networking
Configuring the Local Area Network (LAN)
the ISP, excluding the DNS Proxy IP address when it is disabled. The feature is
useful for an “auto rollover” configuration. For example, if the DNS servers for each
connection are different, then a link failure can render the DNS servers
inaccessible. However, when the DNS proxy is enabled, then clients can make
requests to the router and the router, in turn, sends those requests to the DNS
servers of the active connection.
STEP 3 Click Save.
Configuring Virtual LANs (VLANs)
A VLAN is a group of endpoints in a network that are associated by function or
other shared characteristics. Unlike LANs, which are usually geographically based,
VLANs can group endpoints without regard to the physical location of the
equipment or users.
2
Enabling VLANs
STEP 1 Choose Networking > LAN > VLAN Configuration.
STEP 2 Check the Enable box.
STEP 3 Click Save.
Underneath the Enable VLAN field, a list of available VLANs is shown, including the
name, ID, and whether inter-VLAN routing is enabled or not for each configured
VLAN.
Creating a VLAN
STEP 1 Choose Networking > LAN > VLAN Configuration.
STEP 2 Click Add.
STEP 3 Enter a name to identify the VLAN.
STEP 4 Enter a numerical VLAN ID that will be assigned to endpoints in the VLAN
membership. The VLAN ID can range from 2 to 4094. VLAN ID 1 is reserved for the
default VLAN, which is used for untagged frames received on the interface, and
VLAN ID 4092 is reserved and cannot be used.
Cisco RV 120W Administration Guide 39
Page 48

Configuring Networking
Configuring the Local Area Network (LAN)
STEP 5 To enable routing between this and other VLANS, check the Inter VLAN Routing
Enable box.
STEP 6 Click Save.
Configuring Port VLANs
You can associate VLANS on the Cisco RV 120W to the LAN ports on the device.
By default, all 4 ports belong to VLAN1. You can edit these ports to associate them
with other VLANS.
To associate a LAN port to a VLAN:
STEP 1 Choose Networking > LAN > Port VLAN.
2
STEP 2 In the Port VLANs table, check the box in the row of the LAN port that you want to
configure and press Edit.
STEP 3 Select the mode for the VLAN port:
• General—In general mode, the port is a member of a user-defined set of
VLANs. The port sends and receives both tagged and untagged data.
Untagged data coming into the port is assigned to a PVID by the user. Data
being sent out of the port from the same PVID is untagged. All other data is
tagged.
This mode is typically used with IP phones that have dual Ethernet ports.
Data coming from the phone to the LAN port on the Cisco RV 120W is
tagged. Data passing through the phone from a connected device is
untagged.
• Access (default)—In access mode, the port is a member of a single VLAN.
All data going into and out of the port is untagged.
• Trunk mode—In trunk mode, the port is a member of a user-defined set of
VLANs. All data going into and out of the port is tagged. Untagged data
coming into the port is not forwarded.
STEP 4 If you selected General or Access mode, enter the default Port VLAN ID (PVID).
This ID is used to tag untagged packets that come into the port.
STEP 5 Click Save.
Cisco RV 120W Administration Guide 40
Page 49

Configuring Networking
Configuring the Local Area Network (LAN)
NOTE If you have changed the port mode, you must save the change and return to the Port
VLAN list before configuring the VLAN membership. Check the box next to the port
and click Edit.
STEP 6 If you selected General or Tr un k mode, you can assign the LAN port to one or more
VLANs by checking the box next to the VLAN.
STEP 7 Click Save.
Associating the Wireless Port to VLANs
You can associate wireless VLANS on the Cisco RV 120W to the wireless port on
the device. To associate the wireless port to a VLAN:
2
STEP 1 Choose Networking > LAN > Port VLAN.
STEP 2 In the Wireless VLANs Table, check the box in the row of the wireless port that you
want to configure and press Edit.
STEP 3 Select the mode for the wireless port:
• General—In general mode, the port is a member of a user-defined set of
VLANs. The port sends and receives both tagged and untagged data.
Untagged data coming into the port is assigned to a PVID by the user. Data
being sent out of the port from the same PVID is untagged. All other data is
tagged.
This mode is typically used with IP phones that have dual Ethernet ports.
Data coming from the phone to the LAN port on the Cisco RV 120W is
tagged. Data passing through the phone from a connected device is
untagged.
• Access (default)—In access mode, the port is a member of a single VLAN.
All data going into and out of the port is untagged.
• Trunk mode—In trunk mode, the port is a member of a user-defined set of
VLANs. All data going into and out of the port is tagged. Untagged data
coming into the port is not forwarded.
STEP 4 If you selected General or Access mode, enter the default Port VLAN ID (PVID).
This ID is used to tag untagged packets that come into the port.
STEP 5 Click Save.
Cisco RV 120W Administration Guide 41
Page 50

Configuring Networking
Configuring the Local Area Network (LAN)
NOTE If you have changed the port mode, you must save the change and return to the Port
VLAN list before configuring the VLAN membership. Check the box next to the port
and click Edit.
STEP 6 If you selected General or Tr un k mode, you can assign the LAN port to one or more
VLANs by checking the box next to the VLAN.
STEP 7 Click Save.
Configuring Multiple VLAN Subnets
When you create a VLAN, a subnet is created automatically for the VLAN. You can
then further configure the VLAN properties, such as the IP address and DHCP
behavior.
2
To e di t a V L A N:
STEP 1 Choose Networking > LAN > Multiple VLAN Subnets. The list of subnets appears.
STEP 2 Check the box next to the VLAN you want to edit and click Edit.
STEP 3 If you want to edit the IP address of this VLAN:
a. In the IP address field, enter the new IP address.
b. Enter the Subnet Mask for the new IP address.
c. Click Save. If you are connected to the Cisco RV 120W by the LAN port that is a
member of this VLAN, you might have to release and renew the IP address on
the PC connected to the LAN port, or manually assign an IP address to your PC
that is in the same subnet as the VLAN. Open a new browser window and reconnect to the Cisco RV 120W.
If you want to edit the DHCP behavior of this VLAN:
a. In the DHCP Section, in the DHCP Mode field, choose one of the following:
• DHCP Server—Choose this to allow the VLAN to act as the DHCP server in
the network. Enter the following information:
- Domain Name—Enter the domain name for your network (optional).
Cisco RV 120W Administration Guide 42
Page 51

Configuring Networking
Configuring the Local Area Network (LAN)
- Starting and Ending IP Address—Enter the first and last of the
contiguous addresses in the IP address pool. Any new DHCP client
joining the LAN is assigned an IP address in this range. You can save part
of the range for PCs with fixed addresses. These addresses should be
in the same IP address subnet as the VLAN’s IP address.
- Primary and Secondary DNS Server—DNS servers map Internet
domain names (for example, www.cisco.com) to IP addresses. Enter the
server IP addresses in these fields if you want to use different DNS
servers than are specified in your WAN settings.
- Lease time—Enter the duration (in hours) for which IP addresses are
leased to clients.
• DHCP Relay—Choose this if you are using a DHCP relay gateway. The relay
gateway transmits DHCP messages between multiple subnets. Enter the
address of the relay gateway in the Relay Gateway field.
2
• None—Use this to disable DHCP on the VLAN.
In the LAN Proxy section, to enable the VLAN to act as a proxy for all DNS requests
and communicate with the ISP's DNS servers, check the Enable box.
STEP 4 Click Save.
Configuring IPv6 LAN Properties
In IPv6 mode, the LAN DHCP server is enabled by default (similar to IPv4 mode).
The DHCPv6 server assigns IPv6 addresses from configured address pools with
the IPv6 Prefix Length assigned to the LAN.
To configure IPv6 LAN properties:
STEP 1 Choose Networking > LAN > IPv6 LAN Configuration.
STEP 2 Under LAN TCP/IP Setup, in the IPv6 address field, enter the IP address of the
Cisco RV 120W. The default IPv6 address for the gateway is fec0::1. You can
change this 128 bit IPv6 address based on your network requirements.
STEP 3 Enter the IPv6 prefix length. The IPv6 network (subnet) is identified by the initial
bits of the address called the prefix. By default, the prefix is 64 bits long. All hosts
in the network have the identical initial bits for their IPv6 address; the number of
common initial bits in the network's addresses is set by the prefix length field.
Cisco RV 120W Administration Guide 43
Page 52

Configuring Networking
Configuring the Local Area Network (LAN)
STEP 4 In the DHCPv6 field, choose to disable or enable the DHCPv6 server. If enabled,
the Cisco RV 120W assigns an IP address within the specified range plus
additional specified information to any LAN endpoint that requests DHCP-served
addresses.
STEP 5 Choose the DHCP mode. If stateless is selected, an external IPv6 DHCP server is
not required as the IPv6 LAN hosts are auto-configured by the Cisco RV 120W. In
this case, the router advertisement daemon (RADVD) must be configured on this
device and ICMPv6 router discovery messages are used by the host for autoconfiguration. There are no managed addresses to serve the LAN nodes.
If stateful is selected, the IPv6 LAN host will rely on an external DHCPv6 server to
provide required configuration settings.
STEP 6 (Optional) Enter the domain name of the DHCPv6 server.
STEP 7 Enter the server preference. This field is used to indicate the preference level of
this DHCP server. DHCP advertise messages with the highest server preference
value to a LAN host are preferred over other DHCP server advertise messages.
The default is 255.
2
STEP 8 Choose the DNS proxy behavior:
• Use DNS Proxy—Check this box to enable DNS proxy on this LAN, or
uncheck this box to disable this proxy. When this feature is enabled, the
router acts as a proxy for all DNS requests and communicate with the ISP’s
DNS servers (as configured in the WAN settings page).
• Use DNS from ISP—This option allows the ISP to define the DNS servers
(primary/secondary) for the LAN DHCP client.
• Use below—If selected, the primary/secondary DNS servers configured
are used. If you chose this option, enter the IP address of the primary and
secondary DNS servers.
STEP 9 Enter the lease/rebind time. Enter the duration (in seconds) for which IP addresses
will be leased to endpoints on the LAN.
STEP 10 Click Save.
Configuring IPv6 Address Pools
This feature allows you to define the IPv6 delegation prefix for a range of IP
addresses to be served by the Cisco RV 120W’s DHCPv6 server. Using a
delegation prefix, you can automate the process of informing other networking
equipment on the LAN of DHCP information specific for the assigned prefix.
Cisco RV 120W Administration Guide 44
Page 53

Configuring Networking
Configuring the Local Area Network (LAN)
STEP 1 Choose Networking > LAN > IPv6 LAN Configuration.
STEP 2 In the List of Address Pools field, click Add.
STEP 3 Enter the starting IP address and ending IP address of the pool.
STEP 4 Enter the prefix length. The number of common initial bits in the network’s
addresses is set by the prefix length field.
STEP 5 Click Save.
Configuring LAN Groups
You can create LAN groups, which are groups of endpoints that are identified by
their IP address. After creating a group, you can then configure actions, such as
blocked keywords in a firewall rule, that apply to the group. (See Adding Blocked
Keywords, page 87.)
2
To create a LAN Group:
STEP 1 Choose Networking > LAN > LAN Groups.
STEP 2 Click Add.
STEP 3 Enter the group name; spaces and quotes are not supported. Click Save.
STEP 4 In the LAN Groups page, click the box next to the group you just created and click
Host List.
STEP 5 To add endpoints to the group, click Add.
STEP 6 Enter the IP address of the endpoint and click Save. Repeat steps 4 through 6 for
each endpoint you want to add to the group.
Adding a Static IP Address for a Device on the LAN
You can configure an IP Address and MAC Address for a known computer or
device on the LAN network from the LAN Interface menu.
Cisco RV 120W Administration Guide 45
Page 54

Configuring Networking
Configuring the Local Area Network (LAN)
STEP 1 Choose Networking > LAN > Static DHCP (LAN).
STEP 2 Click Add.
STEP 3 Enter the IP address of the device.
STEP 4 Enter the MAC address of the device. The format for the MAC Address is
XX:XX:XX:XX:XX:XX where X is a number from 0 to 9 (inclusive) or an alphabetical
letter between A and F (inclusive).
NOTE The IP Address assigned should be outside the pool of the DHCP addresses
configured. The DHCP pool is treated as generic pool and all reserved IP's should
be outside this pool. The DHCP server will then serve the reserved IP address
when the device using the corresponding MAC address requests an IP address.
2
Viewing DHCP Leased Clients
You can view a list of endpoints on the network (identified by MAC address) and
see the IP address assigned to them by the DHCP server. The VLAN of the
endpoint is also displayed.
STEP 1 Choose Networking > LAN > DHCP Leased Clients (LAN).
STEP 2 The list of endpoints is displayed; you cannot edit this list.
Configuring a DMZ Host
The Cisco RV 120W supports DMZ options. A DMZ is a sub-network that is open
to the public but behind the firewall. DMZ allows you to redirect packets going to
your WAN port IP address to a particular IP address in your LAN. It is
recommended that hosts that must be exposed to the WAN (such as web or e-mail
servers) be placed in the DMZ network. Firewall rules can be allowed to permit
access to specific services and ports to the DMZ from both the LAN or WAN. In
the event of an attack on any of the DMZ nodes, the LAN is not necessarily
vulnerable as well.
Cisco RV 120W Administration Guide 46
Page 55

Configuring Networking
Configuring the Local Area Network (LAN)
You must configure a fixed (static) IP address for the endpoint that will be
designated as the DMZ host. The DMZ host should be given an IP address in the
same subnet as the router's LAN IP address but it cannot be identical to the IP
address given to the LAN interface of this gateway.
STEP 1 Choose Networking > LAN > DMZ Host.
STEP 2 Check the Enable box to enable DMZ on the network.
STEP 3 Enter the IP address for the endpoint that will receive the redirected packets. This
is the DMZ host.
STEP 4 Click Save. You must then configure firewall rules for the zone. See Configuring
Firewall Rules, page 79.
2
Configuring Internet Group Management Protocol (IGMP)
Internet Group Management Protocol (IGMP) is an exchange protocol for routers.
Hosts that want to receive multicast messages need to inform their neighboring
routers of their status. In some networks, each node in a network becomes a
member of a multicast group and receives multicast packets. In these situations,
hosts exchange information with their local routers using IGMP. Routers use IGMP
periodically to check if the known group members are active. IGMP provides a
method called dynamic membership by which a host can join or leave a multicast
group at any time.
To configure IGMP:
STEP 1 Choose Networking > LAN > IGMP Configuration.
STEP 2 Check the Enable box to allow IGMP communication between the router and other
nodes in the network.
STEP 3 Click Save.
Cisco RV 120W Administration Guide 47
Page 56

Configuring Networking
Configuring Routing
Configuring Routing
Choosing the Routing Mode
The Cisco RV 120W provides two different routing modes. Network Address
Translation (NAT) is a technique that allows several endpoints on a LAN to share an
Internet connection. The computers on the LAN use a “private” IP address range
while the WAN port on the router is configured with a single “public” IP address.
The Cisco RV 120W translates the internal private addresses into a public
address, hiding internal IP addresses from computers on the Internet. If your ISP
has assigned you a single IP address, you want to use NAT so that the computers
that connect through the Cisco RV 120W are assigned IP addresses from a private
subnet (for example, 192.168.10.0).
The other routing mode, “classical routing,” is used if your ISP has assigned you
multiple IP addresses so that you have an IP address for each endpoint on your
network. You must configure either static or dynamic routes if you use this type of
routing. See Configuring Static Routing, page 49, or Configuring Dynamic
Routing, page 50.
2
To choose your routing mode:
STEP 1 Select Networking > Routing > Routing Mode.
STEP 2 Click the box next to the type of routing to configure (“NAT” or “Routing”) and click
Save.
NOTE If you have already configured DMZ or firewall settings on your router in NAT mode,
selecting “router” changes those settings back to the default.
Viewing Routing Information
To view routing information your network, choose Networking > Routing > Routing
Ta b l e . Information about your network routing is displayed, including the following:
• Destination—Destination host/network IP address for which this route is
added.
• Gateway—The gateway used for this route.
Cisco RV 120W Administration Guide 48
Page 57

Configuring Networking
Configuring Routing
2
• Genmask—The netmask for the destination network.
• Flags—For debugging purpose only; possible flags include:
- U—Route is up.
- H—Target is a host.
- G—Use gateway.
- R—Reinstate route for dynamic routing.
- D—Dynamically installed by daemon or redirect.
- M—Modified from routing daemon or redirect.
- A—Installed by
- C—Cache entry.
- !—Reject route.
• Metric—The distance to the target (usually counted in hops).
• Ref—Number of references to this route.
• Use—Count of lookups for the route. Depending on the use of -F and -C, this
is either route cache misses (-F) or hits (-C).
• Iface—Interface to which packets for this route will be sent.
addrconf
.
Configuring Static Routing
You can configure static routes to direct packets to the destination network. A
static route is a pre-determined pathway that a packet must travel to reach a
specific host or network. Some ISPs require static routes to build your routing
table instead of using dynamic routing protocols. Static routes do not require CPU
resources to exchange routing information with a peer router. You can also use
static routes to reach peer routers that do not support dynamic routing protocols.
Static routes can be used together with dynamic routes. Be careful not to
introduce routing loops in your network.
To create a static route:
STEP 1 Select Networking > Routing > Static Routing.
STEP 2 In the list of static routes, click Add.
Cisco RV 120W Administration Guide 49
Page 58

Configuring Networking
Configuring Routing
STEP 3 Enter the route name.
STEP 4 If a route is to be immediately active, check the Active box. When a route is added
STEP 5 Check the Private box to mark this route as private, which means that it will not be
STEP 6 In the destination IP address field, enter the IP address of the destination host or
2
in an inactive state, it will be listed in the routing table, but will not be used by the
router. The route can be enabled later. This feature is useful if the network that the
route connects to is not available when you added the route. When the network
becomes available, the route can be enabled.
shared in a Routing Information Protocol (RIP) broadcast or multicast. Uncheck this
box if the route can be shared with other routers when RIP is enabled.
network to which the route leads. For a standard Class C IP domain, the network
address is the first three fields of the Destination LAN IP; the last field should be
zero.
STEP 7 In the IP subnet mask field, enter the IPv4 Subnet Mask for the destination host or
network. For Class C IP domains, the Subnet Mask is 255.255.255.0.
STEP 8 Choose the physical network interface through which this route is accessible
(WAN or LAN).
STEP 9 In the gateway IP address field, enter the IP Address of the gateway through which
the destination host or network can be reached. If this router is used to connect
your network to the Internet, then your gateway IP is the router's IP address. If you
have another router handling your network's Internet connection, enter the IP
address of that router instead.
STEP 10 In the metric field, enter a value between 2 and 15 to define the priority of the
route. If multiple routes to the same destination exist, the route with the lowest
metric is chosen.
STEP 11 Click Save.
Configuring Dynamic Routing
RIP (Routing Information Protocol, RFC 2453) is an Interior Gateway Protocol (IGP)
that is commonly used in internal networks. It allows the router to exchange its
routing information automatically with other routers, and allows it to dynamically
adjust its routing tables and adapt to changes in the network.
Cisco RV 120W Administration Guide 50
Page 59

Configuring Networking
Configuring Routing
NOTE RIP is disabled by default on the Cisco RV 120W.
STEP 1 Choose Networking > Routing > Dynamic Routing.
STEP 2 To configure how the router sends and receives RIP packets, choose the RIP
2
To configure dynamic routing:
direction:
• Both—The router both broadcasts its routing table and also processes RIP
information received from other routers.
• Out Only—The router broadcasts its routing table periodically but does not
accept RIP information from other routers.
• In Only—The router accepts RIP information from other router, but does not
broadcast its routing table.
• None—The router neither broadcasts its route table nor does it accept any
RIP packets from other routers. This option disables RIP.
STEP 3 Choose the RIP version:
• Disabled.
• RIP-1—This is a class-based routing version that does not include subnet
information. RIP-1 is the most commonly supported version.
• RIP-2B—This version broadcasts data in the entire subnet.
• RIP-2M—This version sends data to multicast addresses.
STEP 4 RIP v2 authentication forces authentication of RIP packets before routes are
exchanged with other routers. It acts as a security feature because routes are
exchanged only with trusted routers in the network. RIP authentication is disabled
by default. You can enter two key parameters so that routes can be exchanged
with multiple routers present in the network. The second key also acts as a failsafe
when authorization with first key fails.
To enable authentication for RIP-2B or RIP-2M, check the Enable box. (You must
also choose the direction as explained in Step 1.)
If you enabled RIP v2 authentication, enter the following first and second key
parameters:
Cisco RV 120W Administration Guide 51
Page 60

Configuring Networking
Configuring Port Management
STEP 5 Click Save.
2
• MD5 Key ID—Input the unique MD-5 key ID used to create the
Authentication Data for this RIP v2 message.
• MD5 Auth Key—Input the auth key for this MD5 key, the auth key that is
encrypted and sent along with the RIP-V2 message.
• Not Valid Before—Enter the start date when the auth key is valid for
authentication.
• Not Valid After—Enter the end date when the auth key is valid for
authentication.
Configuring Port Management
The Cisco RV 120W has four LAN ports. You can enable or disable ports,
configure if the port is half- or full-duplex, and set the port speed.
To configure LAN ports:
STEP 1 Choose Networking > Port Management.
STEP 2 To enable a port, check the Enable box. To disable the port, uncheck the Enable
box. By default, all ports are enabled.
STEP 3 Check the Auto box to let the router and network determine the optimal port
settings. By default, automatic mode is enabled. This setting is available only when
the Enable box is checked.
STEP 4 (Optional) Choose either half- or full-duplex based on the port support. The default
is full-duplex for all ports. This setting is available only when the Auto check box is
unchecked.
STEP 5 (Optional) Select one of the following port speeds: 10 Mbps or 100 Mbps. The
default setting is 100 Mbps for all ports. This setting is available only when the
Auto check box is unchecked. You can change the port speed if a network is
designed to run at a particular speed, such as 10 Mbps mode. In this case, the
endpoint also uses 10 Mbps mode either by auto-negotiation or manual setting.
STEP 6 Click Save.
Cisco RV 120W Administration Guide 52
Page 61

Configuring Networking
Configuring Dynamic DNS (DDNS)
Configuring Dynamic DNS (DDNS)
DDNS is an Internet service that allows routers with varying public IP addresses to
be located using Internet domain names. To use DDNS, you must set up an account
with a DDNS provider such as DynDNS.com or TZO.com.
The router will notify dynamic DNS servers of changes in the WAN IP address, so
that any public services on your network can be accessed by using the domain
name.
To configure DDNS:
2
STEP 1 Choose Networking > Dynamic DNS.
STEP 2 Select the Dynamic DNS Service you are using. Selecting None disables this
service.
STEP 3 If you selected DynDNS.com:
a. Specify the complete Host Name and Domain Name for the DDNS service.
b. Enter the DynDNS account username.
c. Enter the password for the DynDNS account.
d. Check the Use Wildcards box to enable the wildcards feature, which allows all
subdomains of your DynDNS Host Name to share the same public IP as the
Host Name. This option can be enabled here if not done on the DynDNS Web
site.
e. Check the Update Every 30 Days box to configure the router to update the host
information on DynDNS and keep the subscription active after the 30-day trial.
If you selected TZO.com:
a. Specify the complete Host Name and Domain Name for the DDNS service.
b. Enter the user e-mail address for the TZO account.
c. Enter the user key for the TZO account.
d. Check the Update Every 30 Days box to configure the router to update the host
information on TZO.com and keep the subscription active after the 30-day trial.
Cisco RV 120W Administration Guide 53
Page 62

Configuring Networking
Configuring IPv6
STEP 4 Click Save.
Configuring IPv6
The IPv6 configuration information for your router is performed in several sections
on your Cisco RV 120W. Make sure you do the following:
2
• Configure IPv6 WAN properties—See Configuring the WAN for an IPv6
Network, page 34.
• Set the Routing Mode to IPv4/IPv6 mode. See Configuring the Routing
Mode, page 54.
Configuring the Routing Mode
To configure IPv6 properties on the Cisco RV 120W, set the routing mode to IPv6:
STEP 1 Choose Networking > IPv6 > Routing Mode.
STEP 2 Select IPv4/IPv6 and click Save.
Configuring IPv6 Static Routing
You can configure static routes to direct packets to the destination network. A
static route is a pre-determined pathway that a packet must travel to reach a
specific host or network. Some ISPs require static routes to build your routing
table instead of using dynamic routing protocols. Static routes do not require CPU
resources to exchange routing information with a peer router. You can also use
static routes to reach peer routers that do not support dynamic routing protocols.
Static routes can be used together with dynamic routes. Be careful not to
introduce routing loops in your network.
Cisco RV 120W Administration Guide 54
Page 63

Configuring Networking
Configuring IPv6
STEP 1 Select Networking > Routing > Static Routing.
STEP 2 In the list of static routes, click Add.
STEP 3 Enter the route name.
STEP 4 If a route is to be immediately active, check the Active box. When a route is added
STEP 5 In the IPv6 destination field, enter the IPv6 address of the destination host or
2
To create a static route:
in an inactive state, it will be listed in the routing table, but will not be used by the
router. The route can be enabled later. This feature is useful if the network that the
route connects to is not available when you added the route. When the network
becomes available, the route can be enabled.
network for this route.
STEP 6 In the IPv6 prefix length field, enter the number of prefix bits in the IPv6 address
that define the destination subnet.
STEP 7 Choose the physical network interface through which this route is accessible
(WAN, LAN, or sit0 tunnel). (The Simple Internet Transition [SIT] is a set of protocol
mechanisms implemented in hosts and routers, along with some operational
guidelines for addressing and deployment, designed to make the transition from
the Internet to IPv6 work with as little disruption as possible. The SIT0 tunnel is a
point-to-point tunnel.)
STEP 8 Enter the IP Address of the gateway through which the destination host or network
can be reached.
STEP 9 In the metric field, specify the priority of the route by choosing a value between 2
and 15. If multiple routes to the same destination exist, the route with the lowest
metric is used.
STEP 10 Click Save.
Configuring RIP next generation (RIPng)
RIPng (RFC 2080) is a routing protocol based on the distance vector (D-V)
algorithm. RIPng uses UDP packets to exchange routing information through port
521. RIPng uses a hop count to measure the distance to a destination. The hop
count is referred to as metric, or cost. The hop count from a router to a directlyconnected network is 0. The hop count between two directly-connected routers is
1. When the hop count is greater than or equal to 16, the destination network or
Cisco RV 120W Administration Guide 55
Page 64

Configuring Networking
Configuring IPv6
STEP 1 Select Networking > IPv6 > Routing (RIPng).
STEP 2 Check the Enable RIPng box.
STEP 3 Click Save.
2
host is unreachable. By default, the routing update is sent every 30 seconds. If the
router receives no routing updates from a neighbor after 180 seconds, the routes
learned from the neighbor are considered as unreachable. After another 240
seconds, if no routing update is received, the router will remove these routes from
the routing table.
On the Cisco RV 120W, RIPng is disabled by default.
To configure RIPng:
Configuring IPv6 to IPv4 Tunneling
The Cisco RV 120W provides several IPv6 tunneling methods.
Configuring 6to4 Tunneling
6to4 tunneling allows IPv6 packets to be transmitted over an IPv4 network. 6to4
tunneling is typically used when a site or end user wants to connect to the IPv6
Internet using the existing IPv4 network.
To configure 6to4 Tunneling:
STEP 1 Select Networking > IPv6 > 6to4 Tunneling.
STEP 2 Check the Enable Automatic Tunneling box.
STEP 3 Click Save.
Configuring Intra-Site Automatic Tunnel Addressing Protocol Tunnels
Intra-site automatic tunnel addressing protocol is a method to transmit IPv6
packets between dual-stack nodes over an IPv4 network. The Cisco RV 120W is
one endpoint (a node) for the tunnel. You must also set a local endpoint, as well as
the ISATAP Subnet Prefix that defines the logical ISATAP subnet to configure a
tunnel.
Cisco RV 120W Administration Guide 56
Page 65

Configuring Networking
Configuring IPv6
STEP 1 Choose Networking > IPv6 > ISATAP Tunnels.
STEP 2 Click Add.
STEP 3 Enter the ISATAP subnet prefix. This is the 64-bit subnet prefix that is assigned to
STEP 4 Choose the local endpoint address, or the endpoint address for the tunnel that
STEP 5 If you chose an endpoint other than the LAN interface in Step 4, enter the IPv4
2
To add an ISATAP tunnel:
the logical ISATAP subnet for this intranet. This can be obtained from your ISP or
internet registry, or derived from RFC 4193.
starts with the Cisco RV 120W. The endpoint can be the LAN interface (if the LAN
is configured as an IPv4 network), or a specific LAN IPv4 address.
address of the endpoint.
STEP 6 Click Save.
Viewing IPv6 Tunnel Information
To view IPv6 tunnel information, choose Networking > IPv6 > IPv6 Tunnels Status.
The page displays information about the automatic tunnel set up through the
dedicated WAN interface. The table shows the name of tunnel and the IPv6
address that is created on the device.
Configuring Router Advertisement
The Router Advertisement Daemon (RADVD) on the Cisco RV 120W listens for
router solicitations in the IPv6 LAN and responds with router advertisements as
required. This is stateless IPv6 auto configuration, and the Cisco RV 120W
distributes IPv6 prefixes to all nodes on the network.
To configure the RADVD:
STEP 1 Choose Networking > IPv6 > Router Advertisement.
STEP 2 Under RADVD Status, choose Enable.
STEP 3 Under Advertise Mode, choose one of the following:
• Unsolicited Multicast—Select this option to send router advertisements
(RAs) to all interfaces belonging to the multicast group.
Cisco RV 120W Administration Guide 57
Page 66

Configuring Networking
Configuring IPv6
STEP 4 If you chose Unsolicited Multicast in Step 3, enter the advertise interval. The
STEP 5 Under RA Flags, check Managed to use the administered/stateful protocol for
STEP 6 Under router preference, choose low, medium, or high. The router preference
2
• Unicast only—Select this option to restrict advertisements to well-known
IPv6 addresses only (router advertisements [RAs] are sent to the interface
belonging to the known address only).
advertise interval is a random value between the Minimum Router Advertisement
Interval and Maximum Router Advertisement Interval. (MinRtrAdvInterval = 0.33 *
MaxRtrAdvInterval.) The default is 30 seconds.
address auto configuration. Check Other to use the administered/stateful protocol
of other, non-address information auto configuration.
provides a preference metric for default routers. The low, medium and high values
are signaled in unused bits in Router Advertisement messages. This extension is
backward compatible, both for routers (setting the router preference value) and
hosts (interpreting the router preference value). These values are ignored by hosts
that do not implement router preference. This feature is useful if there are other
RADVD-enabled devices on the LAN. The default is high.
STEP 7 Enter the MTU size. The MTU is the size of the largest packet that can be sent over
the network. The MTU is used in RAs to ensure all nodes on the network use the
same MTU value when the LAN MTU is not well-known. The default is 1500 bytes.
STEP 8 Enter the router lifetime value, or the time in seconds that the advertisement
messages will exist on the route. The default is 3600 seconds.
STEP 9 Click Save.
To configure the RADVD available prefixes:
STEP 1 Choose Networking > IPv6 > Advertisement Prefixes.
STEP 2 Click Add.
STEP 3 Choose the IPv6 Prefix Type:
• 6to4—6to4 is a system that allows IPv6 packets to be transmitted over an
IPv4 network. It is used when an end user wants to connect to the IPv6
Internet using their existing IPv4 connection
• Global/ISATAP—By using ISATAP, you can integrate IPv6 traffic into a IPv4
network environment. ISATAP uses a locally assigned IPv4 address to
create a 64-bit interface identifier for IPv6.
Cisco RV 120W Administration Guide 58
Page 67

Configuring Networking
Configuring IPv6
STEP 4 If you chose 6to4 in Step 3, enter the Site-level aggregation identifier (SLA ID.) The
STEP 5 Enter the prefix lifetime, or the length of time over which the requesting router is
STEP 6 Click Save.
2
SLA ID in the 6to4 address prefix is set to the interface ID of the interface on which
the advertisements are sent.
If you chose Global/Local/ISATAP in Step 3, enter the IPv6 prefix and prefix length.
The IPv6 prefix specifies the IPv6 network address. The prefix length variable is a
decimal value that indicates the number of contiguous, higher-order bits of the
address that make up the network portion of the address.
allowed to use the prefix.
Cisco RV 120W Administration Guide 59
Page 68

Configuring the Wireless Network
This chapter describes how to configure your wireless network and includes the
following sections:
• A Note About Wireless Security, page 60
• Understanding the Cisco RV 120W’s Wireless Networks, page 63
• Configuring Access Points, page 66
3
• Configuring the Wireless Radio Properties, page 70
• Configuring the Wireless Radio Properties, page 70
• Configuring Wi-Fi Protected Setup, page 72
• Configuring a Wireless Distribution System (WDS), page 73
A Note About Wireless Security
Wireless networks are convenient and easy to install, so homes with high-speed
Internet access are adopting them at a rapid pace. Because wireless networking
operates by sending information over radio waves, it can be more vulnerable to
intruders than a traditional wired network. Like signals from your cellular or
cordless phones, signals from your wireless network can also be intercepted. The
following information will help you to improve your security:
• Wireless Security Tips, page 60
• General Network Security Guidelines, page 62
Wireless Security Tips
Since you cannot physically prevent someone from connecting to your wireless
network, you need to take some additional steps to keep your network secure:
Cisco RV 120W Administration Guide 60
Page 69

Configuring the Wireless Network
A Note About Wireless Security
• Change the default wireless network name or SSID
Wireless devices have a default wireless network name or Service Set
Identifier (SSID) set by the factory. This is the name of your wireless
network, and can be up to 32 characters in length.
You should change the wireless network name to something unique to
distinguish your wireless network from other wireless networks that may
exist around you, but do not use personal information (such as your Social
Security number) because this information may be available for anyone to
see when browsing for wireless networks.
• Change the default password
For wireless products such as access points, routers, and gateways, you
will be asked for a password when you want to change their settings. These
devices have a default password set by the factory. The default password
is often admin. Hackers know these defaults and may try to use them to
access your wireless device and change your network settings. To thwart
any unauthorized changes, customize the device’s password so it will be
hard to guess.
3
• Enable MAC address filtering
Cisco routers and gateways give you the ability to enable Media Access
Control (MAC) address filtering. The MAC address is a unique series of
numbers and letters assigned to every networking device. With MAC
address filtering enabled, wireless network access is provided solely for
wireless devices with specific MAC addresses. For example, you can
specify the MAC address of each computer in your network so that only
those computers can access your wireless network.
• Enable encryption
Encryption protects data transmitted over a wireless network. Wi-Fi
Protected Access (WPA/WPA2) and Wired Equivalency Privacy (WEP) offer
different levels of security for wireless communication. Currently, devices
that are Wi-Fi certified are required to support WPA2, but are not required
to support WEP.
A network encrypted with WPA/WPA2 is more secure than a network
encrypted with WEP, because WPA/WPA2 uses dynamic key encryption.
To protect the information as it passes over the airwaves, you should enable
the highest level of encryption supported by your network equipment.
WEP is an older encryption standard and may be the only option available
on some older devices that do not support WPA.
Cisco RV 120W Administration Guide 61
Page 70

Configuring the Wireless Network
Understanding the Cisco RV 120W’s Wireless Networks
• Keep wireless routers, access points, or gateways away from exterior walls
and windows.
• Turn wireless routers, access points, or gateways off when they are not
being used (at night, during vacations).
• Use strong passphrases that are at least eight characters in length.
Combine letters and numbers to avoid using standard words that can be
found in the dictionary.
General Network Security Guidelines
Wireless network security is useless if the underlying network is not secure. Cisco
recommends that you take the following precautions:
• Password protect all computers on the network and individually password
protect sensitive files.
3
• Change passwords on a regular basis.
• Install anti-virus software and personal firewall software.
• Disable file sharing (peer-to-peer). Some applications may open file sharing
without your consent and/or knowledge.
Understanding the Cisco RV 120W’s Wireless Networks
The Cisco Small Business RV 120W Wireless-N VPN Firewall provides four
Wireless Access Points (APs), or virtual wireless networks. These networks can
be configured and enabled with individual settings. You can set up multiple
networks to segment the network traffic, to allow different levels of access, such
as guest access, or to allow access for different functions such as accounting,
billing, and so on.
You can further customize wireless access by creating profiles. A profile is a set of
generic wireless settings that can be shared across multiple APs. Profiles allow
you to easily duplicate SSIDs, security settings, encryption methods, and client
authentication for multiple APs.
Cisco RV 120W Administration Guide 62
Page 71

Configuring the Wireless Network
Configuring Wireless Profiles
Configuring Wireless Profiles
A profile is a set of generic wireless settings that can be shared across multiple
APs. You can create multiple profiles on the Cisco RV 120W, but only one profile is
assigned to each AP at a time.
The Cisco RV 120W provides four default wireless profiles. Even if you are not
going to create custom profiles, at a minimum, you should edit the default profiles
to enable wireless security. See A Note About Wireless Security, page 60.
To configure wireless profiles:
STEP 1 Choose Wireless > AP Profiles.
STEP 2 In the Profiles Table, either click Add to add a new profile, or check the box in the
row of an existing profile and click Edit.
3
STEP 3 If creating a new profile, enter a unique name to identify the profile.
STEP 4 In the SSID field, enter a unique name for this wireless network. Include up to 32
characters, using any of the characters on the keyboard. For added security, you
should change the default value to a unique name.
STEP 5 Check the Broadcast SSID box if you want to allow all wireless clients within range
to be able to detect this wireless network when they are scanning the local area
for available networks. Disable this feature if you do not want to make the SSID
known. When this feature is disabled, wireless users can connect to your wireless
network only if they know the SSID (and provide the required security credentials).
STEP 6 In the Security field, select the type of security. All devices on your network must
use the same security mode and settings to work correctly. Cisco recommends
using the highest level of security that is supported by the devices in your
network.
• Disabled—Any device can connect to the network. Not recommended.
• Wired Equivalent Privacy (WEP)— Weak security with a basic encryption
method that is not as secure as WPA. WEP may be required if your network
devices do not support WPA; however, it is not recommended.
• Wi-Fi Protected Access (WPA) Personal—WPA is part of the wireless
security standard (802.11i) standardized by the Wi-Fi Alliance and was
intended as an intermediate measure to take the place of WEP while the
802.11i standard was being prepared. It supports TKIP/AES encryption. The
personal authentication is the preshared key (PSK) that is an alphanumeric
passphrase shared with the wireless peer.
Cisco RV 120W Administration Guide 63
Page 72

Configuring the Wireless Network
Configuring Wireless Profiles
• WPA Enterprise—Allows you to use WPA with RADIUS server
authentication.
• WPA2 Personal—WPA2 is the implementation of security standard
specified in the final 802.11i standard. It supports AES encryption and this
option uses preshared key (PSK) based authentication.
• WPA2 Personal Mixed—Allows both WPA and WPA2 clients to connect
simultaneously using PSK authentication.
• WPA2 Enterprise—Allows you to use WPA2 with RADIUS server
authentication.
• WPA2 Enterprise Mixed—Allows both WPA and WPA2 clients to connect
simultaneously using RADIUS authentication.
STEP 7 Perform the following steps based on the type of encryption you chose in Step 6:
3
WPA/WPA2
a. Select the encryption method to be used: TKIP, AES, or TKIP+AES.
b. Select the authentication method to be used: RADIUS, PSK, or PSK + RADIUS.
c. WPA Password—Enter the pre-shared key for WPA/WPA2 PSK authentication.
The clients also need to be configured with the same password.
d. (Optional) Check the Enable Pre-Authentication box to enable pre-
authentication for this profile. Pre-authentication allows wireless clients to
quickly switch between connected Access Points sharing the same security
configuration. This is mainly used when APs are configured with WPA/WPA2
security. In event of wireless client disconnecting from an AP, a notification is
sent to the AP, which then sends the pre-authentication info to other APs in the
network.
WEP
In the WEP Index and Keys section:
a. In the Authentication field, choose Open System or Shared Key. If you choose
open system, a wireless client doesn't need to provide a shared key in order to
access the wireless network. Any client can associate to the router. If you
choose shared key, a wireless client must provide the correct shared key
(password) in order to access the wireless network.
b. Select the encryption type (64- or 128-bit). The larger size keys provide
stronger encryption, making the key more difficult to crack (for example, 64-bit
Cisco RV 120W Administration Guide 64
Page 73

Configuring the Wireless Network
Configuring Wireless Profiles
WEP has a 40-bit key which is less secure than the 128-bit WEP, which has a
104-bit key).
c. (Optional) In the passphrase field, enter an alphanumeric phrase (longer than
eight characters for optimal security) and click Generate Key to generate four
unique WEP keys in the WEP Key fields below.
d. Select one of the four to use as the shared key that devices must have in order
to use the wireless network. If you did not generate a key in Step C, enter a key
directly into the WEP Key field. The length of the key should be 5 ASCII
characters (or 10 hexadecimal characters) for 64-bit WEP and 13 ASCII
characters (or 26 hexadecimal characters) for 128-bit WEP. Valid hexadecimal
characters are “0” to “9” and “A” to “F”.
STEP 8 Click Save.
3
Configuring the Group Key Refresh Interval
If you configure WPA or WPA2 security, you can specify the timeout interval after
which group keys are generated:
STEP 1 Choose Wireless > AP Profile.
STEP 2 Check the box in the row of the profile you want to configure and click Advanced
Configuration.
STEP 3 Enter the group key refresh interval, in seconds.
STEP 4 Click Save.
Configuring RADIUS Authentication Parameters
In WPA2 security, Pairwise Master Key Security Association (PMKSA) caching is
used to store the master keys derived from successful RADIUS authentication. A
client reconnecting within this interval (after successful RADIUS authentication)
can skip the RADIUS authentication. This feature prevents a long RADIUS
authentication process every time a client connects.
To configure:
Cisco RV 120W Administration Guide 65
Page 74

Configuring the Wireless Network
Configuring Access Points
STEP 1 Choose Wireless > AP Profile.
STEP 2 Check the box in the row of the profile you want to configure and click Advanced
Configuration.
STEP 3 Specify the number of seconds that the master keys are stored in the AP.
STEP 4 In the 802.1X re-authentication interval field, enter the timeout interval (in seconds)
after which the AP should re-authenticate with the RADIUS server.
STEP 5 Click Save.
Configuring Access Points
3
To configure the APs, choose Wireless > AP Profiles. The four APs are displayed in
the Access Points Table.
Enabling or Disabling APs
An AP can be disabled if not in use and enabled when needed. Disabling an AP
does not delete the configuration, but removes it from availability. Enabling the AP
creates a wireless network, where computers and other devices can join and
communicate with the devices connected to the AP or other devices on the Local
Area Network (LAN).
Cisco RV 120W Administration Guide 66
Page 75

Configuring the Wireless Network
Configuring Access Points
To enable or disable an AP:
STEP 1 Choose Wireless > AP Profiles.
STEP 2 In the Access Points Table, click the check box in the row of the AP and click
Enable or Disable. You can enable or disable multiple APs at one time by checking
multiple boxes.
Editing an AP’s Properties
You can edit properties for an AP to make it only available at certain times of the
day, restrict the number of endpoints that can use the AP, or separate the AP from
the other wireless networks in the Cisco RV 120W.
3
To edit the properties of an access point:
STEP 1 Choose Wireless > AP Profiles.
STEP 2 Check the box in the row of the AP that you want to edit.
STEP 3 Associate a profile with this AP by choosing the profile from the Profile Name list.
The profile controls the name and security settings for the AP. See Configuring
the Wireless Radio Properties, page 70.
STEP 4 (Optional) To configure the AP to be active only during a certain time of day, check
the Active Time box. Enter the start and stop times (hours, minutes, and AM/PM).
STEP 5 In the Max Associated Clients field, enter the maximum number of endpoints that
can use this AP. The default value is 8. You can change this number if you want to
restrict traffic on the network to prevent it from being overloaded, for example.
STEP 6 (Optional) Check the AP Isolation box to separate this AP into its own network.
When this feature is enabled, the AP can communicate with the Cisco RV 120W,
but not with any other AP on the network.
STEP 7 Click Save.
Cisco RV 120W Administration Guide 67
Page 76

Configuring the Wireless Network
Configuring Access Points
Using MAC Filtering
You can use MAC filtering to permit or deny access to the wireless network based
on the MAC (hardware) address of the requesting device. For example, you can
enter the MAC addresses of a set of PCs and only allow those PCs to access the
network. MAC filtering is configured for each AP.
To configure MAC filtering:
STEP 1 Choose Wireless > AP Profiles.
STEP 2 Check the box in the row of the AP for which you want to configure MAC filtering
and click MAC Filter.
STEP 3 In the AP Policy Status field, choose the type of access to the AP:
• Open—Access to the network is open to all endpoints and is not allowed or
denied based on the endpoint’s MAC address. This is the default setting.
3
• Allow—Access to the network is only allowed to endpoints with specified
MAC addresses.
• Deny—Access to the network is denied to endpoints with specified MAC
addresses, but open to all others.
STEP 4 If you chose Allow or Deny in Step 3, click Save.
STEP 5 In the MAC Address Table, check the box next to MAC Address and click Add.
STEP 6 Enter the MAC Address of the endpoint to allow or deny and click Save. The
address is added to the table. Repeat this step for all the endpoints you want to
allow or deny.
STEP 7 Click Save again.
Viewing AP Status
You can view statistics about each AP, including connected clients (endpoints),
data transmitted and received, errors, and other information.
Cisco RV 120W Administration Guide 68
Page 77

Configuring the Wireless Network
Configuring Access Points
To view the AP status:
STEP 1 Choose Wireless > AP Profiles.
STEP 2 In the List of Available Access Points, check the box in the row of the AP for which
you want to view statistics and click Status.
STEP 3 The following statistics are displayed:
• AP Name—Name of the AP whose statistics are being displayed.
• Radio—Wireless radio number on which the AP is configured.
• Packets—Number of wireless packets transmitted and received.
• Bytes—Number of bytes of information transmitted and received.
• Errors—Number of transmitted and received packet errors reported to the
AP.
3
• Dropped—Number of transmitted and received packets dropped by the
AP.
• Multicast—Number of multicast packets sent over this AP.
• Collisions—Number of packet collisions reported to the AP.
• Connected Clients—Lists clients currently connected to the selected AP.
- MAC Address—The unique identifier of the client connected to the AP.
- Radio—Wireless radio number on which AP is configured and to which
the client is associated.
- Security—Security method employed by the client to connect to this AP.
- Encryption—Encryption method employed by the client to connect to
this AP.
- Authentication—Authentication mechanism employed by this
connection.
- Time Connected—Time (in minutes) since the connection was
established between the AP and client.
STEP 4 The Poll Seconds displays the interval at which statistics are shown if the page is
on “automatic refresh.” The default is 10 seconds, which can be changed from 1 to
Cisco RV 120W Administration Guide 69
Page 78

Configuring the Wireless Network
Configuring the Wireless Radio Properties
60 seconds. To cause the page to automatically refresh, click Start. To stop the
page from refreshing, click Stop.
Configuring the Wireless Radio Properties
You can configure radio card properties, including the wireless standard (for
example, 802.11n or 802.11g) on the Cisco RV 120W.
Configuring Basic Wireless Radio Settings
STEP 1 Choose Wireless > Radio Settings > Radio Settings.
3
STEP 2 Select the Wireless Network Mode:
• B/G Mixed—Select this mode if you have devices in the network that
support 802.11b.
• G Only—Select this mode if all devices in the wireless network only
support 802.11g.
• N/G Mixed—Select this mode if you have devices in the network that
support 802.11g and 802.11n.
• N Only—Select this mode if all devices in the wireless network support
802.11n.
STEP 3 Select the channel bandwidth. Available choices depend on the wireless network
mode chosen in Step 2.
STEP 4 The control sideband field defines the sideband which is used for the secondary
or extension channel when the AP is operating in 40 Mhz channel width. Choose
lower or upper. This field is only available when channel spacing is set to auto. The
signal components above the carrier frequency constitute the upper sideband
(USB) and those below the carrier frequency constitute the lower sideband (LSB).
STEP 5 The channel field specifies the frequency that the radio uses to transmit wireless
frames. Select a channel from the list of channels or choose auto to let the Cisco
RV 120W determine the best channel to use based on the environment noise
levels for the available channels.
STEP 6 Click Save.
.
Cisco RV 120W Administration Guide 70
Page 79

Configuring the Wireless Network
Configuring the Wireless Radio Properties
Configuring Advanced Wireless Radio Settings
STEP 1 Choose Wireless > Radio Settings > Radio Settings.
STEP 2 In the beacon interval field, enter the time in milliseconds between beacon
transmissions. The default interval is 100 milliseconds.
STEP 3 In the DTIM interval field, enter the interval at which the delivery traffic indication
message should be sent. A DTIM field is a countdown field informing clients of the
next window for listening to broadcast and multicast messages. When the Cisco
RV 120W has buffered broadcast or multicast messages for associated clients, it
sends the next DTIM with a DTIM Interval value. Its clients hear the beacons and
awaken to receive the broadcast and multicast messages.The default interval is 2
beacon intervals.
STEP 4 The Request to Send (RTS) threshold is the packet size, in bytes, that requires the
AP to check the transmitting frames to determine if an RTS/Clear to Send (CTS)
handshake is required with the receiving client. Using a small value causes RTS
packets to be sent more often, consuming more of the available bandwidth,
reducing the apparent throughput of the network packets. The default value is
2346, which effectively disables RTS.
3
STEP 5 The fragmentation threshold is the maximum length of the frame, in bytes, beyond
which packets must be fragmented into two or more frames. Collisions occur
more often for long frames because while sending them, they occupy the channel
for a longer time. The default value is 2346, which effectively disables
fragmentation. If you experience a high packet error rate, you can slightly increase
the fragmentation threshold; setting the fragmentation threshold too low may
result in poor network performance. Only minor reduction of the default value is
recommended.
STEP 6 Choose the preamble mode. The 802.11b standard requires that a preamble be
appended to every frame before it is transmitted through the air. The preamble
may be either the traditional “long” preamble, which requires 192 μs for
transmission, or it may be an optional “short” preamble that requires only 96 μs. A
long preamble is needed for compatibility with the legacy 802.11 systems
operating at 1 and 2 Mbps. The default selection is long.
STEP 7 Choose the protection mode. Select none (the default) to turn off CTS. The CTS-
to-Self Protection option enables the CTS-to-Self protection mechanism, which is
used to minimize collisions among stations in a mixed 802.11b and 802.11g
environment. This function boosts the Cisco RV 120W’s ability to catch all wireless
transmissions but severely decreases performance.
Cisco RV 120W Administration Guide 71
Page 80

Configuring the Wireless Network
Configuring Wi-Fi Protected Setup
STEP 8 (Optional) Check the U-APSD box to enable the Unscheduled Automatic Power
Save Delivery (also referred to as WMM Power Save) feature that allows the radio
to conserve power.
STEP 9 The short retry limit and long retry limit fields determine the number of times the
AP will reattempt a frame transmission that fails. The limit applies to both long and
short frames of a size less than or equal to the RTS threshold.
STEP 10 Click Save.
Configuring Wi-Fi Protected Setup
You can configure Wi-Fi Protected Setup (WPS) on the Cisco RV 120W to allow
WPS-enabled devices to more easily connect to the wireless network.
3
STEP 1 Choose Wireless > WPS.
STEP 2 Select the AP on which you want to enable WPS. The AP must use WPA, WPA2, or
WPA+WPA2 security.
STEP 3 Under WPS status, choose Enable. By default, WPS is disabled.
STEP 4 Click Save.
To set up a WPS-enabled device in the network:
STEP 1 Choose Wireless > WPS.
STEP 2 In the WPS Setup Method section, in the Station PIN field, enter the personal
identification number (PIN) of the device to connect to the network. You must log in
to that device to obtain its WPS PIN.
STEP 3 Click Configure via PIN to initiate the WPS session. On the WPS-enabled device,
select the necessary option to begin WPS. The device should begin
communication with the Cisco RV 120W.
STEP 4 Click Save.
Cisco RV 120W Administration Guide 72
Page 81

Configuring the Wireless Network
Configuring a Wireless Distribution System (WDS)
Configuring a Wireless Distribution System (WDS)
A Wireless Distribution System (WDS) is a system that enables the wireless
interconnection of access points in a network. It allows a wireless network to be
expanded using multiple access points without the need for a wired backbone to
link them.
WDS peers are other access points in the network connected in the WDS. All
base stations in a WDS must be configured to use the same radio channel, method
of encryption (none, WEP, or WPA) and encryption keys
To configure a WDS:
STEP 1 Choose Wireless > WDS.
STEP 2 Check the Enable WDS box to enable WDS in the Cisco RV 120W.
3
STEP 3 Enter a WPA password for authentication.
STEP 4 Click Save.
You can manually add WDS peers that can connect to the Cisco RV 120W:
STEP 1 In the WDS Peers Table, click Add.
STEP 2 Enter the MAC (hardware) address of the WDS peer and click Save.
Cisco RV 120W Administration Guide 73
Page 82

Configuring the Firewall
This chapter contains information about configuring the firewall properties of the
Cisco RV 120W and includes the following sections:
• Cisco RV 120W Firewall Features, page 74
• Configuring Basic Firewall Settings, page 76
• Configuring Firewall Rules, page 79
4
• Creating Firewall Schedules, page 85
• Blocking and Filtering Content and Applications, page 85
• Firewall Rule Examples, page 90
• Configuring Port Triggering, page 92
• Configuring Port Forwarding, page 94
• Configuring Remote Management, page 98
• Configuring One-to-One Network Address Translation (NAT), page 99
Cisco RV 120W Firewall Features
You can secure your network by creating and applying rules that the Cisco RV
120W uses to selectively block and allow inbound and outbound Internet traffic.
You then specify how and to what devices the rules apply. To do so, you must
define the following:
• Services or traffic types (examples: web browsing, VoIP, other standard
services and also custom services that you define) that the router should
allow or block.
• Direction for the traffic by specifying the source and destination of traffic;
this is done by specifying the “From Zone” (LAN/WAN/DMZ) and “To Zone”
(LAN/WAN/DMZ).
Cisco RV 120W Administration Guide 74
Page 83

Configuring the Firewall
Cisco RV 120W Firewall Features
You can, for example, establish restricted-access policies based on time-of-day,
web addresses, and web address keywords. You can block Internet access by
applications and services on the LAN, such as chat rooms or games. You can block
just certain groups of PCs on your network from being accessed by the WAN or
public DMZ network.
4
• Schedules as to when the router should apply rules.
• Keywords (in a domain name or on a URL of a web page) that the router
should allow or block.
• Rules for allowing or blocking inbound and outbound Internet traffic for
specified services on specified schedules.
• MAC addresses of devices whose inbound access to your network the
router should block.
• Port triggers that signal the router to allow or block access to specified
services as defined by port number.
• Reports and alerts that you want the router to send to you.
Inbound (WAN to LAN/DMZ) rules restrict access to traffic entering your network,
selectively allowing only specific outside users to access specific local resources.
By default, all access from the insecure WAN side is blocked from accessing the
secure LAN, except in response to requests from the LAN or DMZ. To allow
outside devices to access services on the secure LAN, you must create a firewall
rule for each service.
If you want to allow incoming traffic, you must make the router's WAN port IP
address known to the public. This is called “exposing your host.” How you make
your address known depends on how the WAN ports are configured; for the Cisco
RV 120W, you may use the IP address if a static address is assigned to the WAN
port, or if your WAN address is dynamic, a DDNS (Dynamic DNS) name can be
used.
Outbound (LAN/DMZ to WAN) rules restrict access to traffic leaving your network,
selectively allowing only specific local users to access specific outside resources.
The default outbound rule is to allow access from the secure zone (LAN) to either
the public DMZ or insecure WAN. To block hosts on the secure LAN from
accessing services on the outside (insecure WAN), you must create a firewall rule
for each service.
Cisco RV 120W Administration Guide 75
Page 84

Configuring the Firewall
Configuring Basic Firewall Settings
Configuring Basic Firewall Settings
To configure basic firewall settings, choose Firewall > Basic Settings. You can
configure the following:
Protecting from Attacks
Attacks are malicious security breeches or unintentional network issues that
render the Cisco RV 120W unusable. Attack checks allow you to manage WAN
security threats such as continual ping requests and discovery via ARP scans.
TCP and UDP flood attack checks can be enabled to manage extreme usage of
WAN re sourc es .
As well, certain Denial-of-Service (DoS) attacks can be blocked. These attacks, if
uninhibited, can use up processing power and bandwidth and prevent regular
network services from running normally. ICMP packet flooding, SYN traffic
flooding, and Echo storm thresholds can be configured to temporarily suspect
traffic from the offending source.
4
STEP 1 Choose Firewall > Basic Settings > Attack Checks.
STEP 2 Check the boxes to enable the following functions:
WAN Security
• Respond to Ping on the Internet—To configure the Cisco RV 120W to allow
a response to an Internet Control Message Protocol (ICMP) Echo (ping)
request on the WAN interface, check this box. This setting is used as a
diagnostic tool for connectivity problems. Not enabled by default.
• Enable Stealth Mode—If Stealth Mode is enabled, the router will not
respond to port scans from the WAN. This feature makes the network less
susceptible to discovery and attacks. Enabled by default.
• Block TCP Flood— If this option is enabled, the router will drop all invalid
TCP packets. This feature protects the network from a SYN flood attack.
Enabled by default.
LAN Security
• Block UDP Flood—If this option is enabled, the router will not accept more
than 25 simultaneous, active UDP connections from a single computer on
the LAN. Enabled by default.
Cisco RV 120W Administration Guide 76
Page 85

Configuring the Firewall
Configuring Basic Firewall Settings
International Computer Security Association (ICSA) Settings
• Block ICMP Notification—ICSA requires the firewall to silently block without
• Block Fragmented Packets—ICSA requires the firewall to block fragmented
• Block Multicast Packets—ICSA requires the firewall to block multicast
STEP 3 Click Save.
4
sending an ICMP notification to the sender. Some protocols, such as MTU
Path Discovery, require ICMP notifications. Enable this setting to operate in
“stealth” mode. Enabled by default.
packets from ANY to ANY. Enabled by default.
packets. Enabled by default.
Configuring Universal Plug and Play (UPnP)
UPnP is a feature that allows for automatic discovery of devices that can
communicate with the Cisco RV 120W.
To e na bl e U P n P :
STEP 1 Choose Firewall > Basic Settings > UPnP.
STEP 2 Check the Enable box. If disabled, the Cisco RV 120W does not allow automatic
device configuration.
STEP 3 Select the interface on which you want to allow UPnP.
STEP 4 In the Advertisement Period field, enter the period (in seconds) to specify how
often the Cisco RV 120W will broadcast its UPnP information to all devices within
range.
STEP 5 In the Advertisement Time to Live field, enter the number of hops to allow for each
UPnP packet. This setting determines how long a packet is allowed to propagate
before being discarded. Small values will limit the UPnP broadcast range.
STEP 6 Click Save.
Cisco RV 120W Administration Guide 77
Page 86

Configuring the Firewall
Configuring Basic Firewall Settings
Viewing UPnP Information
To view UPnP information:
STEP 1 Choose Firewall > Basic Settings > UPnP.
STEP 2 The UPnP Portmap Table shows IP addresses and other settings of UPnP devices
that have accessed the Cisco RV 120W. It includes the following fields:
• Active—Indicates whether or not the port of the UPnP device that
• Protocol—The network protocol (i.e. HTTP, FTP, etc.) that the device is using
• Internal Port—Indicates which, if any, internal ports are opened by the UPnP
4
established a connection is currently active: Yes or No.
to connect to the Cisco RV 120W.
device.
• External Port—Indicates which, if any, external ports are opened by the
UPnP device.
• IP Address—The IP address of the UPnP device that is accessing the Cisco
RV 120W.
STEP 3 Click Refresh to refresh the portmap table and search for any new UPnP devices.
Enabling Session Initiation Protocol Application-Level Gateway (SIP ALG)
SIP ALG can rewrite information within SIP messages (SIP headers and SDP body)
making signaling and audio traffic possible between a client behind Network
Address Translation (NAT) and the SIP endpoint.
To e na bl e S I P A LG :
STEP 1 Choose Firewall > Basic Settings > SIP ALG.
STEP 2 Check the Enable box to enable SIP ALG support. If disabled, the router will not
allow incoming calls to the UAC (User Agent Client) behind the Cisco RV 120W.
STEP 3 Click Save.
Cisco RV 120W Administration Guide 78
Page 87

Configuring the Firewall
Configuring Firewall Rules
STEP 1 Choose Firewall > Access Control > Default Outbound Policy.
STEP 2 Under the IPv4 or IPv6 fields, select one of the following:
4
Configuring the Default Outbound Policy
The Firewall Settings page allows the user to configure the default outbound
policy for the traffic that is directed from the secure network (LAN) to the nonsecure network (dedicated WAN/optional). The default inbound policy for traffic
flowing from the non-secure zone to the secure zone is always blocked and
cannot be changed.
To configure the default outbound policy:
• Always Allow—Always allow traffic from the secure to the non-secure
network.
• Always Block—Always block traffic from the secure to the non-secure
network.
NOTE Ensure that IPv6 support is enabled on the Cisco RV 120W to configure an IPv6
firewall. See Configuring IPv6, page 54.
STEP 3 Click Save.
Configuring Firewall Rules
All configured firewall rules on the Cisco RV 120W are displayed in the Firewall
Rules list. This list also indicates whether the rule is enabled (active), and gives a
summary of the “from/to” zone as well as the services and users the rule affects.
If you plan to apply a rule to a specific group of devices on your LAN, define the
group by selecting Networking > LAN Settings > LAN Groups. See Configuring
LAN Groups, page 45.
Cisco RV 120W Administration Guide 79
Page 88

Configuring the Firewall
Configuring Firewall Rules
STEP 1 Choose Firewall > Access Control > IPv4 Rules.
STEP 2 Click Add.
STEP 3 In the From Zone field, choose the source of originating traffic:
STEP 4 Choose the To Z o n e to configure the destination of traffic covered by this rule. If
4
Creating a Firewall Rule
To create firewall rules:
• Tru st ed (L A N) —Choose if traffic will originate from the secure LAN.
• Untrusted (WAN)—Choose this option to create an inbound rule.
the From Zone is the WAN, the To Zone can be the public DMZ or secure LAN. If
the From Zone is the LAN, then the To Zone can be only the insecure WAN.
STEP 5 Choose the service to allow or block for this rule. Choose Any to allow the rule to
apply to all applications and services, or you can choose a single application to
block:
• AIM (AOL Instant Messenger)
• BGP (Border Gateway Control)
• BOOT_P (Bootstrap Protocol) client
• BOOT_P Server
• CU-SeeMe (videoconferencing) UDP or TCP
• Domain Name System (DNS), UDP or TCP
• Finger
• File Transfer Protocol (FTP)
• Hyptertext Transfer Protocol (HTTP)
• Secure Hypertext Transfer Protocol (HTTPS)
• Internet Control Message Protocol (ICMP) type 3 through 11 or 13
• ICQ (chat)
• Internet Message Access Protocol (IMAP) 2 or 3
• Internet Relay Chat (IRC)
Cisco RV 120W Administration Guide 80
Page 89

Configuring the Firewall
Configuring Firewall Rules
4
• News
• PING
• Post Office Protocol (POP3)
• Point-to-Point Tunneling Protocol (PPTP)
• RCMD (command)
• Real Audio
• Remote execution command (REXEC)
• Remote login commend (RLOGIN)
• Remote Telnet (RTELNET)
• Real-Time Streaming Protocol (RTSP) TCP or UDP
• Secure Shell File Transfer Protocol (SFTP)
• Simple Mail Transfer Protocol (SMTP)
• Simple Network Management Protocol (SNMP) TCP or UDP
• SNMP Traps (TCP or UDP)
• Structured Query Language (SQL)*Net (Oracle)
• SSH (TCP or UDP)
• STRMWORKS
• Terminal Access Controller Access-Control System (TACACS)
• Telnet (command)
• Trivial File Transfer Protocol (TFTP)
• Routing Information Protocol (RIP)
• IKE
• Simple HTTPD web server
• UDP Encapsulation of IPsec packets (IPSEC-UDP-ENCAP)
• IDENT protocol
• VDOLive (web video delivery)
Cisco RV 120W Administration Guide 81
Page 90

Configuring the Firewall
Configuring Firewall Rules
STEP 6 Choose the action:
STEP 7 In the Source Hosts field, select the users to which the firewall rule applies:
4
• SSH
• SIP-TCP
• Always Block—Always block the selected type of traffic.
• Always Allow—Never block the selected type of traffic.
• Block by schedule, otherwise allow—Blocks the selected type of traffic
according to a schedule. See Creating Firewall Schedules, page 85.
• Allow by schedule, otherwise block—Allows the selected type of traffic
according to a schedule. See Creating Firewall Schedules, page 85.
• Any—The rule applies to traffic originating on any host in the local network.
• Single Address—The rule applies to traffic originating on a single IP
address in the local network. Enter the address in the From field.
• Address Range—The rule applies to traffic originating from an IP address
located in a range of addresses. Enter the starting IP address in the From
field, and the ending IP address in the To field.
STEP 8 In the Log field, specify whether or not the packets for this rule should be logged.
To log details for all packets that match this rule, select Always. For example, if an
outbound rule for a schedule is selected as Block Always, then for every packet
that tries to make an outbound connection for that service, a message with the
packet’s source address and destination address (and other information) is
recorded in the log. Enabling logging may generate a significant volume of log
messages and is recommended for debugging purposes only. Select Never to
disable logging.
STEP 9 When traffic is going from the LAN or DMZ to the WAN, the system requires
rewriting the source or destination IP address of incoming IP packets as they pass
through the firewall. In the SNAT IP Type field, choose WAN I nterfa ce Ad dress or
choose Single Address and enter the Single IP Address in the SNAT IP field.
STEP 10 In the QoS Priority field, assign a priority to IP packets of this service. The priorities
are defined by “Type of Service (TOS) in the Internet Protocol Suite” standards,
RFC 1349. The gateway marks the Type Of Service (TOS) field as defined below:
• Normal-Service—No special priority is given to the traffic. The IP packets
for services with this priority are marked with a TOS value of 0.
Cisco RV 120W Administration Guide 82
Page 91

Configuring the Firewall
Configuring Firewall Rules
4
• Minimize-Cost—Choose this option when data must be transferred over a
link that has a lower “cost.” The IP packets for services with this priority are
marked with a TOS value of 2.
• Maximize-Reliability—Choose this option when data needs to travel to the
destination over a reliable link and with little or no retransmission. The IP
packets for services with this priority are marked with a TOS value of 4.
• Maximize-Throughput—Choose this option when the volume of data
transferred during an interval is important even if the latency over the link is
high. The IP packets for services with this priority are marked with a TOS
value of 8.
• Minimize-Delay—Choose this option when the time required (latency) for
the packet to reach the destination must be low. The IP packets for services
with this priority are marked with a TOS value of 16.
STEP 11 When the traffic is coming from the WAN to the DMZ or the LAN, Destination
Network Address Translation maps a public IP address (your Dedicated WAN
address, Optional WAN address, or another address) to an IP address on your
private network. Enter the following:
• Send to Local Server (DNAT IP)—Specify an IP address of a machine on the
Local Network which is hosting the server.
• (Optional) Check the Enable Port Forwarding box to enable port forwarding
to the port that you specify in the Translate Port Number field. This will allow
traffic from the Internet to reach the appropriate LAN port via a port
forwarding rule.
• Translate Port Number—Enter the port number to use for port forwarding.
For example, if a machine on the Local Network side is running a telnet
server on port 2000, then check the Enable Port Forwarding box and enter
2000 in the Translate Port Number field. If the server is listening on the
default port 23, then the box can be left unchecked.
• Internet Destination Address—Select the public IP address that is used for
this firewall rule: Dedicated WAN, Optional WAN, or Other. If you choose
Other, enter the WAN IP address that will map to the internal server in the
Other IP Address field.
Cisco RV 120W Administration Guide 83
Page 92

Configuring the Firewall
Configuring Firewall Rules
STEP 12 Click Save.
4
This gateway supports multi-NAT, and the Internet Destination IP address does
not necessarily have to be the WAN address. On a single WAN interface,
multiple public IP addresses are supported. If your ISP assigns you more than
one public IP address, one of these can be used as your primary IP address on
the WAN port, and the others can be assigned to servers on the LAN or DMZ.
In this way, the LAN/DMZ server can be accessed from the internet by its
aliased public IP address.
Managing Firewall Rules
Choose Firewall > Access Control > IPv4 Rules.
To enable or disable a rule, check the box next to the rule in the list of firewall rules
and choose Enable or Disable.
To delete a rule, check the box next to the rule and click Delete.
To reorder rules, check the box next to a rule and click Up or Down. The Cisco RV
120W applies rules in the order listed. As a general rule, you should move the
strictest rules (those with the most specific services or addresses) to the top of
the list.
Creating Custom Services
When you create a firewall rule, you can specify a service that is controlled by the
rule. Common types of services are available for selection, and you can create
your own custom services. This page allows creation of custom services against
which firewall rules can be defined. Once defined, the new service will appear in
the List of Available Custom Services table.
To create a custom service:
STEP 1 Choose Firewall > Access Control > Services.
STEP 2 Enter a service name for identification and management purposes.
STEP 3 Enter the service type, or layer 4 protocol that the service uses (TCP, UDP, ICMP, or
ICMPv6).
STEP 4 If you chose ICMP or ICMPv6 as the service type, enter the ICMP type. This is a
numeric value from 0 through 40 for ICMP and from 0 through 255 for ICMPv6.
Cisco RV 120W Administration Guide 84
Page 93

Configuring the Firewall
Creating Firewall Schedules
STEP 5 In the Start Port field, enter the first TCP or UDP port of the range that the service
uses.
STEP 6 In the Finish Port field, enter the last TCP or UDP port of the range that the service
uses.
STEP 7 Click Save.
Creating Firewall Schedules
You can create firewall schedules to apply firewall rules on specific days or at
specific times of the day.
4
To create a schedule:
STEP 1 Choose Firewall > Access Control > Schedules.
STEP 2 Enter a unique name to identify the schedule. This name is then available in the
Firewall Rule Configuration page in the “Select Schedule” list. (See Configuring
Firewall Rules, page 79.)
STEP 3 Under Scheduled Days, select whether you want the schedule to apply to all days
or specific days. If you choose Specific Days, check the box next to the days you
want to include in the schedule.
STEP 4 Under Scheduled Time of Day, select the time of day that you want the schedule to
apply. You can either choose All Day, or choose Specific Time. If you choose
Specific Time, enter the start and end times, selecting a.m. or p.m.
STEP 5 Click Save.
Blocking and Filtering Content and Applications
The Cisco RV 120W supports several content filtering options. You can block
certain web applications or components (such as ActiveX or Java). You can set up
trusted domains from which to always allow content. You can block access to
Internet sites by specifying keywords to block. If these keywords are found in the
site's name (for example, web site URL or newsgroup name), the site is blocked.
Cisco RV 120W Administration Guide 85
Page 94

Configuring the Firewall
Blocking and Filtering Content and Applications
You also need to turn on content filtering to set up trusted domains.
Blocking Web Applications and Components
STEP 1 Choose Firewall > Access Control > Content Filtering.
STEP 2 Check the Enable box.
STEP 3 Certain commonly-used web components can be blocked for increased security.
Some of these components can be used by malicious websites to infect
computers that access them. With content filtering enabled, select the check box
for each component you wish to block:
• Proxy—A proxy server (or simply, proxy) allows computers to route
connections to other computers through the proxy, thus circumventing
certain firewall rules. For example, if connections to a specific IP address
are blocked by a firewall rule, the requests can be routed through a proxy
that is not blocked by the rule, rendering the restriction ineffective. Enabling
this feature blocks proxy servers.
4
• Java—Blocks java applets from being downloaded from pages that contain
them. Java applets are small programs embedded in web pages that
enable dynamic functionality of the page. A malicious applet can be used to
compromise or infect computers. Enabling this setting blocks Java applets
from being downloaded.
• ActiveX—Similar to Java applets, ActiveX controls are installed on a
Windows computer while running Internet Explorer. A malicious ActiveX
control can be used to compromise or infect computers. Enabling this
setting blocks ActiveX applets from being downloaded.
Cisco RV 120W Administration Guide 86
Page 95

Configuring the Firewall
Blocking and Filtering Content and Applications
• Cookies—Cookies are used to store session information by websites that
usually require login. However, several websites use cookies to store
tracking information and browsing habits. Enabling this option filters out
cookies from being created by a website.
NOTE Many websites require that cookies be accepted in order for the site to be
accessed properly. Blocking cookies can cause many websites to not function
properly.
STEP 4 Click Save.
Adding Trusted Domains
4
You can add a list of trusted domains. These domains are bypassed during
keyword filtering. For example, if “yahoo” is added to the blocked keywords list
and www.yahoo.com is added to the trusted domain list, then www.yahoo.com
will be allowed, but mail.yahoo.com will not be allowed.
NOTE Before adding trusted domains, you must enable content filtering. See Blocking
Web Applications and Components, page 86.
To add trusted domains:
STEP 1 Choose Firewall > Access Control > Trusted Domains.
STEP 2 Enter the trusted domain.
STEP 3 Click Save.
Adding Blocked Keywords
NOTE Before adding blocked keywords, you must enable content filtering. See Blocking
Web Applications and Components, page 86.
Cisco RV 120W Administration Guide 87
Page 96

Configuring the Firewall
Blocking and Filtering Content and Applications
STEP 1 Choose Firewall > Access Control > Blocked Keywords.
STEP 2 Click Add.
STEP 3 Enter the keyword to block. Keywords prevent access to websites that contain the
specified characters in the URL or the page contents.
STEP 4 Select the group to which to apply the keyword blocking. (These groups are
configured in the Networking > LAN > LAN Groups page.)
STEP 5 Click Save.
Configuring MAC Address Filtering
4
MAC address filtering allows you to block traffic coming from certain known
machines or devices. The router uses the MAC address of a computer or device
on the network to identify it and block or permit the access. Traffic coming in from
a specified MAC address will be filtered depending upon the policy.
To enable MAC address filtering:
STEP 1 Choose Firewall > Access Control > MAC Filtering.
STEP 2 Check the Enable box to enable MAC Address Filtering for this device. Uncheck
the box to disable this feature.
If you enable MAC filtering, in the Policy for MAC Address listed below field,
choose one of the following options:
• Block and Permit the rest—Choose this option to block the traffic from the
specified MAC addresses and to allow traffic from all other addresses.
• Permit and Block the rest—Choose this option to permit the traffic from the
specified MAC addresses and to block traffic from all other machines on
the LAN side of the router.
For example, two computers are on the LAN with MAC addresses of
00:01:02:03:04:05 (host1), and 00:01:02:03:04:11 (host2). If the host1 MAC address
is added to the MAC filtering list and the “block and permit the rest” policy is
chosen, when this computer tries to connect to a website, the router will not allow
Cisco RV 120W Administration Guide 88
Page 97

Configuring the Firewall
Blocking and Filtering Content and Applications
it to connect. However, host2 is able to connect because its MAC address is not in
the list. If the policy is “permit and block the rest,” then host1 is able to connect to a
website, but host2 is blocked because its URL is not in the list. The MAC filtering
policy does not override a firewall rule that directs incoming traffic to a host.
STEP 3 Click Save.
STEP 4 In the MAC Addresses table, click Add.
STEP 5 Enter the MAC address to add to the table and click Save. Repeat for each address
to permit or block.
Configuring IP/MAC Address Binding
IP/MAC Binding allows you to bind IP addresses to MAC address. Some machines
are configured with static addresses. To prevent users from changing static IP
addresses, IP/MAC Binding should be enabled. If the Cisco RV 120W sees
packets with matching IP address but inconsistent MAC addresses, it drops those
packets.
4
To configure IP/MAC Address binding:
STEP 1 Choose Firewall > Access Control > IP/MAC Binding. The table lists all the
currently defined IP/MAC binding rules and allows several operations on the rules.
STEP 2 Click Add to add a new rule.
STEP 3 In the name field, enter the name for this rule.
STEP 4 In the MAC Addresses field, enter the MAC Addresses (the physical address of
the piece of hardware) for this rule.
STEP 5 In the IP Addresses field, enter the IP Addresses to assign to the piece of
hardware.
STEP 6 In the Log Dropped Packets field, choose if you want to log the dropped packets.
Choosing enable logs the dropped packets. Logs can be viewed in Status > View
All Logs page.
Cisco RV 120W Administration Guide 89
Page 98

Configuring the Firewall
Firewall Rule Examples
Firewall Rule Examples
Example 1: Allow inbound HTTP traffic to the DMZ
In this example, you host a public web server on your local DMZ network. You
want to allow inbound HTTP requests from any outside IP address to the IP
address of your web server at any time of day.
Create an inbound rule as follows:
Parameter Value
From Zone Insecure (WAN1/WAN2)
To Z o n e P u b l i c ( D M Z )
Service HTTP
4
Action Allow always
Send to Local Server (DNAT IP) 192.168.5.2 (web server IP address)
Destination Users Any
Log Never
Example 2: Allow videoconferencing from range of outside IP addresses.
In this example, you want to allow incoming videoconferencing to be initiated from
a restricted range of outside IP addresses (132.177.88.2 - 132.177.88.254), from a
branch office.
Create an inbound rule as follows. In the example, CUSeeMe connections are
allowed only from a specified range of external IP addresses.
Parameter Value
From Zone Insecure (WAN1/WAN2)
To Z o n e S e c u r e ( LA N )
Service CU-SEEME:UDP
Cisco RV 120W Administration Guide 90
Page 99

Configuring the Firewall
Firewall Rule Examples
4
Parameter Value
Action Allow always
Send to Local Server (DNAT IP) 192.168.1.11
Destination Users Address Range
From 132.177.88.2
To 134.177.88.254
Enable Port Forwarding Yes (enabled)
Example 3: Multi-NAT Configuration
In this example, you want to configure multi-NAT to support multiple public IP
addresses on one WAN port interface.
Create an inbound rule that configures the firewall to host an additional public IP
address. Associate this address with a web server on the DMZ. If you arrange with
your ISP to have more than one public IP address for your use, you can use the
additional public IP addresses to map to servers on your LAN. One of these public
IP addresses is used as the primary IP address of the router. This address is used
to provide Internet access to your LAN PCs through NAT. The other addresses are
available to map to your DMZ servers.
The following addressing scheme is used to illustrate this procedure:
• WAN IP address: 10.1.0.118
• LAN IP address: 192.168.1.1; subnet 255.255.255.0
• Web server PC in the DMZ, IP address: 192.168.1.2
• Access to Web server: (simulated) public IP address 10.1.0.52
Parameter Value
From Zone Insecure (WAN1/WAN2)
To Z o n e P u b l i c ( D M Z )
Service HTTP
Action Allow always
Cisco RV 120W Administration Guide 91
Page 100

Configuring the Firewall
Configuring Port Triggering
4
Parameter Value
Send to Local Server (DNAT IP) 192.168.1.2 (local IP address of your web server)
Destination Users Single Address
From 10.1.0.52
WAN Use r s Any
Log Never
Example 4: Block traffic by schedule if generated from specific range of
machines
In this example, you want to block all HTTP traffic on the weekends if the request
originates from a specific group of machines in the LAN having a known range of
IP addresses, and anyone coming in through the Network from the WAN (i.e. all
remote users).
STEP 1 Setup a schedule. Choose Firewall > Access Control > Schedules.
STEP 2 Enter Weekend in the Name field.
STEP 3 Under Scheduled Days, choose Specific Days.
STEP 4 Check the box next to Saturday and Sunday.
STEP 5 Under Scheduled Time of Day, select All Day. This applies the schedule from 12:00
a.m. to 11:59 p.m. of the selected days.
STEP 6 Click Save.
Configuring Port Triggering
Port triggering allows devices on the LAN or DMZ to request one or more ports to
be forwarded to them. Port triggering waits for an outbound request from the LAN/
DMZ on one of the defined outgoing ports, and then opens an incoming port for
that specified type of traffic. Port triggering is a form of dynamic port forwarding
while an application is transmitting data over the opened outgoing or incoming
ports.
Cisco RV 120W Administration Guide 92
 Loading...
Loading...