Redhat LVS FOR ENTERPRISE LINUX 5.2 User Manual

Linux Virtual Server Administration
Linux Virtual Server (LVS)
for Red Hat Enterprise
Linux
5.2
Virtual_Server_Administration
ISBN: N/A
Publication date: May 2008

Linux Virtual Server Administration
Building a Linux Virtual Server (LVS) system offers highly-available and scalable solution for
production services using specialized routing and load-balancing techniques configured through
the PIRANHA. This book discusses the configuration of high-performance systems and services
with Red Hat Enterprise Linux and LVS for Red Hat Enterprise Linux 5.2.

Linux Virtual Server Administration: Linux Virtual Server
(LVS) for Red Hat Enterprise Linux
Copyright © 2008 Red Hat, Inc.
Copyright © 2008 Red Hat, Inc. This material may only be distributed subject to the terms and conditions set forth in the
Open Publication License, V1.0 or later with the restrictions noted below (the latest version of the OPL is presently
available at http://www.opencontent.org/openpub/).
Distribution of substantively modified versions of this document is prohibited without the explicit permission of the
copyright holder.
Distribution of the work or derivative of the work in any standard (paper) book form for commercial purposes is
prohibited unless prior permission is obtained from the copyright holder.
Red Hat and the Red Hat "Shadow Man" logo are registered trademarks of Red Hat, Inc. in the United States and other
countries.
All other trademarks referenced herein are the property of their respective owners.
The GPG fingerprint of the security@redhat.com key is:
CA 20 86 86 2B D6 9D FC 65 F6 EC C4 21 91 80 CD DB 42 A6 0E
1801 Varsity Drive
Raleigh, NC 27606-2072
USA
Phone: +1 919 754 3700
Phone: 888 733 4281
Fax: +1 919 754 3701
PO Box 13588
Research Triangle Park, NC 27709
USA

Linux Virtual Server Administration

Introduction .............................................................................................................. vii
1. Document Conventions ................................................................................ viii
2. Feedback ......................................................................................................ix
1. Linux Virtual Server Overview ................................................................................. 1
1. A Basic LVS Configuration .............................................................................. 1
1.1. Data Replication and Data Sharing Between Real Servers ..................... 3
2. A Three-Tier LVS Configuration ...................................................................... 3
3. LVS Scheduling Overview .............................................................................. 5
3.1. Scheduling Algorithms ......................................................................... 5
3.2. Server Weight and Scheduling ............................................................. 7
4. Routing Methods ............................................................................................ 7
4.1. NAT Routing ....................................................................................... 7
4.2. Direct Routing ..................................................................................... 9
5. Persistence and Firewall Marks ......................................................................11
5.1. Persistence ........................................................................................11
5.2. Firewall Marks ....................................................................................12
6. LVS — A Block Diagram ................................................................................12
6.1. LVS Components ...............................................................................14
2. Initial LVS Configuration ........................................................................................17
1. Configuring Services on the LVS Routers .......................................................17
2. Setting a Password for the Piranha Configuration Tool .................................18
3. Starting the Piranha Configuration Tool Service ...........................................18
3.1. Configuring the Piranha Configuration Tool Web Server Port .............19
4. Limiting Access To the Piranha Configuration Tool ......................................20
5. Turning on Packet Forwarding .......................................................................21
6. Configuring Services on the Real Servers .......................................................21
3. Setting Up LVS .....................................................................................................23
1. The NAT LVS Network ..................................................................................23
1.1. Configuring Network Interfaces for LVS with NAT .................................23
1.2. Routing on the Real Servers ...............................................................25
1.3. Enabling NAT Routing on the LVS Routers ..........................................25
2. LVS via Direct Routing ..................................................................................26
2.1. Direct Routing and arptables_jf .......................................................27
2.2. Direct Routing and iptables ..............................................................28
3. Putting the Configuration Together .................................................................29
3.1. General LVS Networking Tips .............................................................30
4. Multi-port Services and LVS ...........................................................................30
4.1. Assigning Firewall Marks ....................................................................31
5. Configuring FTP ............................................................................................32
5.1. How FTP Works .................................................................................32
5.2. How This Affects LVS Routing ............................................................33
5.3. Creating Network Packet Filter Rules ..................................................33
6. Saving Network Packet Filter Settings ............................................................35
4. Configuring the LVS Routers with Piranha Configuration Tool ...............................37
1. Necessary Software ......................................................................................37
2. Logging Into the Piranha Configuration Tool ................................................37
v

Linux Virtual Server Administration
3. CONTROL/MONITORING .............................................................................38
4. GLOBAL SETTINGS ....................................................................................40
5. REDUNDANCY ............................................................................................42
6. VIRTUAL SERVERS .....................................................................................44
6.1. The VIRTUAL SERVER Subsection ....................................................45
6.2. REAL SERVER Subsection ................................................................49
6.3. EDIT MONITORING SCRIPTS Subsection ..........................................51
7. Synchronizing Configuration Files ..................................................................53
7.1. Synchronizing lvs.cf ........................................................................54
7.2. Synchronizing sysctl ........................................................................54
7.3. Synchronizing Network Packet Filtering Rules ......................................55
8. Starting LVS .................................................................................................55
A. Using LVS with Red Hat Cluster ............................................................................57
Index .......................................................................................................................61
vi

Introduction
This document provides information about installing, configuring, and managing Red Hat Virtual
Linux Server (LVS) components. LVS provides load balancing through specialized routing
techniques that dispatch traffic to a pool of servers. This document does not include information
about installing, configuring, and managing Red Hat Cluster software. Information about that is
in a separate document.
The audience of this document should have advanced working knowledge of Red Hat
Enterprise Linux and understand the concepts of clusters, storage, and server computing.
This document is organized as follows:
• Chapter 1, Linux Virtual Server Overview
• Chapter 2, Initial LVS Configuration
• Chapter 3, Setting Up LVS
• Chapter 4, Configuring the LVS Routers with Piranha Configuration Tool
• Appendix A, Using LVS with Red Hat Cluster
For more information about Red Hat Enterprise Linux 5, refer to the following resources:
• Red Hat Enterprise Linux Installation Guide — Provides information regarding installation of
Red Hat Enterprise Linux 5.
• Red Hat Enterprise Linux Deployment Guide — Provides information regarding the
deployment, configuration and administration of Red Hat Enterprise Linux 5.
For more information about Red Hat Cluster Suite for Red Hat Enterprise Linux 5, refer to the
following resources:
• Red Hat Cluster Suite Overview — Provides a high level overview of the Red Hat Cluster
Suite.
• Configuring and Managing a Red Hat Cluster — Provides information about installing,
configuring and managing Red Hat Cluster components.
• LVM Administrator's Guide: Configuration and Administration — Provides a description of the
Logical Volume Manager (LVM), including information on running LVM in a clustered
environment.
• Global File System: Configuration and Administration — Provides information about installing,
configuring, and maintaining Red Hat GFS (Red Hat Global File System).
• Using Device-Mapper Multipath — Provides information about using the Device-Mapper
vii

Introduction
Multipath feature of Red Hat Enterprise Linux 5.
• Using GNBD with Global File System — Provides an overview on using Global Network Block
Device (GNBD) with Red Hat GFS.
• Red Hat Cluster Suite Release Notes — Provides information about the current release of
Red Hat Cluster Suite.
Red Hat Cluster Suite documentation and other Red Hat documents are available in HTML,
PDF, and RPM versions on the Red Hat Enterprise Linux Documentation CD and online at
http://www.redhat.com/docs/.
1. Document Conventions
Certain words in this manual are represented in different fonts, styles, and weights. This
highlighting indicates that the word is part of a specific category. The categories include the
following:
Courier font
Courier font represents commands, file names and paths, and prompts .
When shown as below, it indicates computer output:
Desktop about.html logs paulwesterberg.png
Mail backupfiles mail reports
bold Courier font
Bold Courier font represents text that you are to type, such as: service jonas start
If you have to run a command as root, the root prompt (#) precedes the command:
# gconftool-2
italic Courier font
Italic Courier font represents a variable, such as an installation directory:
install_dir/bin/
bold font
Bold font represents application programs and text found on a graphical interface.
When shown like this: OK , it indicates a button on a graphical application interface.
viii

Feedback
Additionally, the manual uses different strategies to draw your attention to pieces of information.
In order of how critical the information is to you, these items are marked as follows:
Note
A note is typically information that you need to understand the behavior of the
system.
Tip
A tip is typically an alternative way of performing a task.
Important
Important information is necessary, but possibly unexpected, such as a
configuration change that will not persist after a reboot.
Caution
A caution indicates an act that would violate your support agreement, such as
recompiling the kernel.
Warning
A warning indicates potential data loss, as may happen when tuning hardware
for maximum performance.
2. Feedback
If you spot a typo, or if you have thought of a way to make this manual better, we would love to
hear from you. Please submit a report in Bugzilla (http://bugzilla.redhat.com/bugzilla/) against
the component Documentation-cluster.
Be sure to mention the manual's identifier:
ix

Introduction
Virtual_Server_Administration(EN)-5.2 (2008-05-15T16:07)
By mentioning this manual's identifier, we know exactly which version of the guide you have.
If you have a suggestion for improving the documentation, try to be as specific as possible. If
you have found an error, please include the section number and some of the surrounding text
so we can find it easily.
x

Chapter 1.
Linux Virtual Server Overview
Linux Virtual Server (LVS) is a set of integrated software components for balancing the IP load
across a set of real servers. LVS runs on a pair of equally configured computers: one that is an
active LVS router and one that is a backup LVS router. The active LVS router serves two roles:
• To balance the load across the real servers.
• To check the integrity of the services on each real server.
The backup LVS router monitors the active LVS router and takes over from it in case the active
LVS router fails.
This chapter provides an overview of LVS components and functions, and consists of the
following sections:
• Section 1, “A Basic LVS Configuration”
• Section 2, “A Three-Tier LVS Configuration”
• Section 3, “LVS Scheduling Overview”
• Section 4, “Routing Methods”
• Section 5, “Persistence and Firewall Marks”
• Section 6, “LVS — A Block Diagram”
1. A Basic LVS Configuration
Figure 1.1, “A Basic LVS Configuration” shows a simple LVS configuration consisting of two
layers. On the first layer are two LVS routers — one active and one backup. Each of the LVS
routers has two network interfaces, one interface on the Internet and one on the private
network, enabling them to regulate traffic between the two networks. For this example the active
router is using Network Address Translation or NAT to direct traffic from the Internet to a
variable number of real servers on the second layer, which in turn provide the necessary
services. Therefore, the real servers in this example are connected to a dedicated private
network segment and pass all public traffic back and forth through the active LVS router. To the
outside world, the servers appears as one entity.
1

Chapter 1. Linux Virtual Server Overview
Figure 1.1. A Basic LVS Configuration
Service requests arriving at the LVS routers are addressed to a virtual IP address, or VIP. This
is a publicly-routable address the administrator of the site associates with a fully-qualified
domain name, such as www.example.com, and is assigned to one or more virtual servers. A
virtual server is a service configured to listen on a specific virtual IP. Refer to Section 6,
“VIRTUAL SERVERS” for more information on configuring a virtual server using the Piranha
Configuration Tool. A VIP address migrates from one LVS router to the other during a failover,
thus maintaining a presence at that IP address (also known as floating IP addresses).
VIP addresses may be aliased to the same device which connects the LVS router to the
Internet. For instance, if eth0 is connected to the Internet, than multiple virtual servers can be
aliased to eth0:1. Alternatively, each virtual server can be associated with a separate device
per service. For example, HTTP traffic can be handled on eth0:1, and FTP traffic can be
handled on eth0:2.
Only one LVS router is active at a time. The role of the active router is to redirect service
requests from virtual IP addresses to the real servers. The redirection is based on one of eight
supported load-balancing algorithms described further in Section 3, “LVS Scheduling Overview”.
2

Data Replication and Data Sharing Between
The active router also dynamically monitors the overall health of the specific services on the real
servers through simple send/expect scripts. To aid in detecting the health of services that
require dynamic data, such as HTTPS or SSL, the administrator can also call external
executables. If a service on a real server malfunctions, the active router stops sending jobs to
that server until it returns to normal operation.
The backup router performs the role of a standby system. Periodically, the LVS routers
exchange heartbeat messages through the primary external public interface and, in a failover
situation, the private interface. Should the backup node fail to receive a heartbeat message
within an expected interval, it initiates a failover and assumes the role of the active router.
During failover, the backup router takes over the VIP addresses serviced by the failed router
using a technique known as ARP spoofing — where the backup LVS router announces itself as
the destination for IP packets addressed to the failed node. When the failed node returns to
active service, the backup node assumes its hot-backup role again.
The simple, two-layered configuration used in Figure 1.1, “A Basic LVS Configuration” is best for
serving data which does not change very frequently — such as static webpages — because the
individual real servers do not automatically sync data between each node.
1.1. Data Replication and Data Sharing Between Real Servers
Since there is no built-in component in LVS to share the same data between the real servers,
the administrator has two basic options:
• Synchronize the data across the real server pool
• Add a third layer to the topology for shared data access
The first option is preferred for servers that do not allow large numbers of users to upload or
change data on the real servers. If the configuration allows large numbers of users to modify
data, such as an e-commerce website, adding a third layer is preferable.
1.1.1. Configuring Real Servers to Synchronize Data
There are many ways an administrator can choose to synchronize data across the pool of real
servers. For instance, shell scripts can be employed so that if a Web engineer updates a page,
the page is posted to all of the servers simultaneously. Also, the system administrator can use
programs such as rsync to replicate changed data across all nodes at a set interval.
However, this type of data synchronization does not optimally function if the configuration is
overloaded with users constantly uploading files or issuing database transactions. For a
configuration with a high load, a three-tier topology is the ideal solution.
2. A Three-Tier LVS Configuration
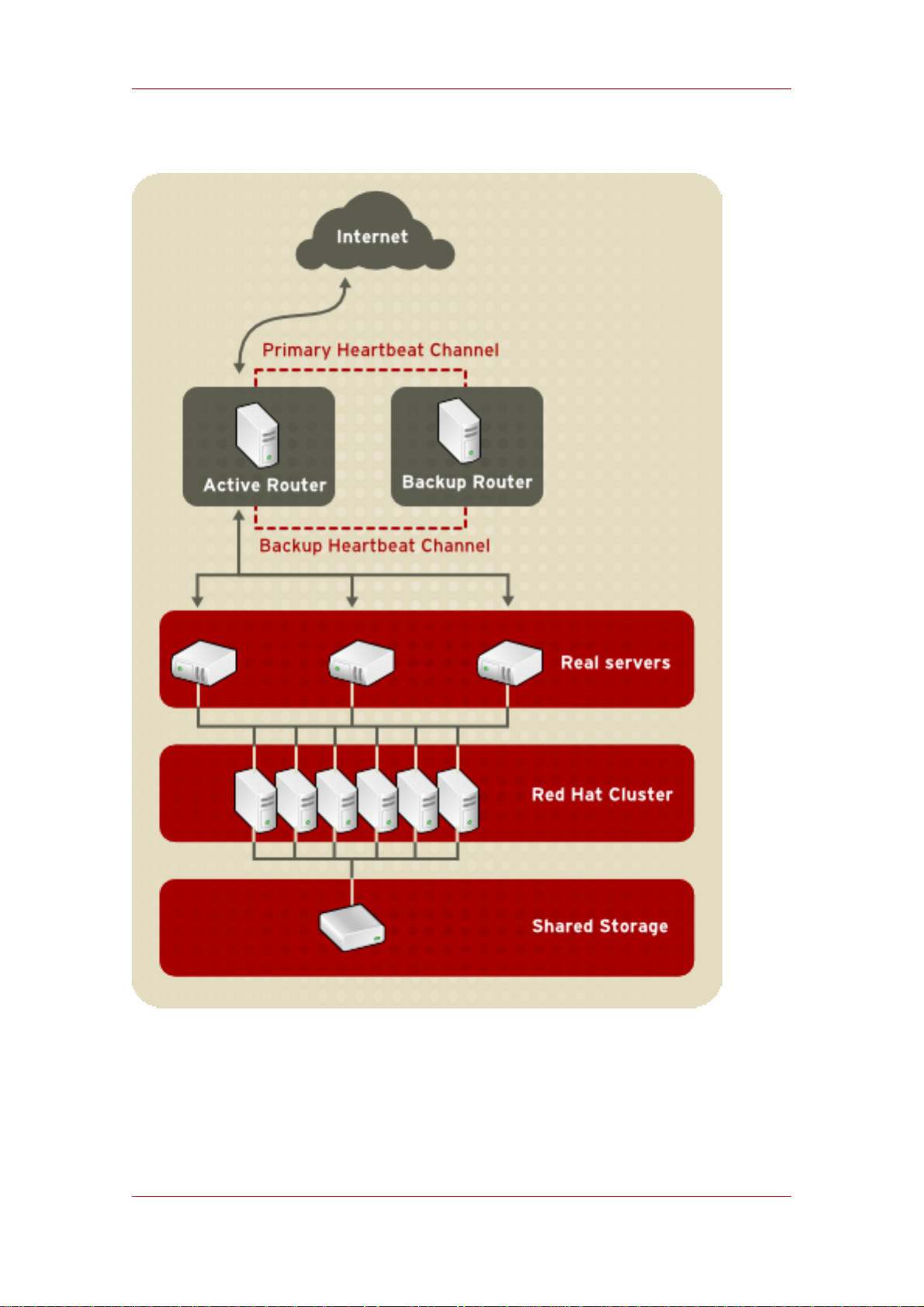
Figure 1.2, “A Three-Tier LVS Configuration” shows a typical three-tier LVS topology. In this
example, the active LVS router routes the requests from the Internet to the pool of real servers.
3
Chapter 1. Linux Virtual Server Overview
Each of the real servers then accesses a shared data source over the network.
Figure 1.2. A Three-Tier LVS Configuration
This configuration is ideal for busy FTP servers, where accessible data is stored on a central,
highly available server and accessed by each real server via an exported NFS directory or
Samba share. This topology is also recommended for websites that access a central, highly
4

Real Servers
available database for transactions. Additionally, using an active-active configuration with Red
Hat Cluster Manager, administrators can configure one high-availability cluster to serve both of
these roles simultaneously.
The third tier in the above example does not have to use Red Hat Cluster Manager, but failing
to use a highly available solution would introduce a critical single point of failure.
3. LVS Scheduling Overview
One of the advantages of using LVS is its ability to perform flexible, IP-level load balancing on
the real server pool. This flexibility is due to the variety of scheduling algorithms an administrator
can choose from when configuring LVS. LVS load balancing is superior to less flexible methods,
such as Round-Robin DNS where the hierarchical nature of DNS and the caching by client
machines can lead to load imbalances. Additionally, the low-level filtering employed by the LVS
router has advantages over application-level request forwarding because balancing loads at the
network packet level causes minimal computational overhead and allows for greater scalability.
Using scheduling, the active router can take into account the real servers' activity and,
optionally, an administrator-assigned weight factor when routing service requests. Using
assigned weights gives arbitrary priorities to individual machines. Using this form of scheduling,
it is possible to create a group of real servers using a variety of hardware and software
combinations and the active router can evenly load each real server.
The scheduling mechanism for LVS is provided by a collection of kernel patches called IP
Virtual Server or IPVS modules. These modules enable layer 4 (L4) transport layer switching,
which is designed to work well with multiple servers on a single IP address.
To track and route packets to the real servers efficiently, IPVS builds an IPVS table in the
kernel. This table is used by the active LVS router to redirect requests from a virtual server
address to and returning from real servers in the pool. The IPVS table is constantly updated by
a utility called ipvsadm — adding and removing cluster members depending on their availability.
3.1. Scheduling Algorithms
The structure that the IPVS table takes depends on the scheduling algorithm that the
administrator chooses for any given virtual server. To allow for maximum flexibility in the types
of services you can cluster and how these services are scheduled, Red Hat Enterprise Linux
provides the following scheduling algorithms listed below. For instructions on how to assign
scheduling algorithms refer to Section 6.1, “The VIRTUAL SERVER Subsection”.
Round-Robin Scheduling
Distributes each request sequentially around the pool of real servers. Using this algorithm,
all the real servers are treated as equals without regard to capacity or load. This scheduling
model resembles round-robin DNS but is more granular due to the fact that it is
network-connection based and not host-based. LVS round-robin scheduling also does not
suffer the imbalances caused by cached DNS queries.
5

Chapter 1. Linux Virtual Server Overview
Weighted Round-Robin Scheduling
Distributes each request sequentially around the pool of real servers but gives more jobs to
servers with greater capacity. Capacity is indicated by a user-assigned weight factor, which
is then adjusted upward or downward by dynamic load information. Refer to Section 3.2,
“Server Weight and Scheduling” for more on weighting real servers.
Weighted round-robin scheduling is a preferred choice if there are significant differences in
the capacity of real servers in the pool. However, if the request load varies dramatically, the
more heavily weighted server may answer more than its share of requests.
Least-Connection
Distributes more requests to real servers with fewer active connections. Because it keeps
track of live connections to the real servers through the IPVS table, least-connection is a
type of dynamic scheduling algorithm, making it a better choice if there is a high degree of
variation in the request load. It is best suited for a real server pool where each member
node has roughly the same capacity. If a group of servers have different capabilities,
weighted least-connection scheduling is a better choice.
Weighted Least-Connections (default)
Distributes more requests to servers with fewer active connections relative to their
capacities. Capacity is indicated by a user-assigned weight, which is then adjusted upward
or downward by dynamic load information. The addition of weighting makes this algorithm
ideal when the real server pool contains hardware of varying capacity. Refer to Section 3.2,
“Server Weight and Scheduling” for more on weighting real servers.
Locality-Based Least-Connection Scheduling
Distributes more requests to servers with fewer active connections relative to their
destination IPs. This algorithm is designed for use in a proxy-cache server cluster. It routes
the packets for an IP address to the server for that address unless that server is above its
capacity and has a server in its half load, in which case it assigns the IP address to the least
loaded real server.
Locality-Based Least-Connection Scheduling with Replication Scheduling
Distributes more requests to servers with fewer active connections relative to their
destination IPs. This algorithm is also designed for use in a proxy-cache server cluster. It
differs from Locality-Based Least-Connection Scheduling by mapping the target IP address
to a subset of real server nodes. Requests are then routed to the server in this subset with
the lowest number of connections. If all the nodes for the destination IP are above capacity,
it replicates a new server for that destination IP address by adding the real server with the
least connections from the overall pool of real servers to the subset of real servers for that
destination IP. The most loaded node is then dropped from the real server subset to prevent
over-replication.
Destination Hash Scheduling
Distributes requests to the pool of real servers by looking up the destination IP in a static
hash table. This algorithm is designed for use in a proxy-cache server cluster.
Source Hash Scheduling
6

Server Weight and Scheduling
Distributes requests to the pool of real servers by looking up the source IP in a static hash
table. This algorithm is designed for LVS routers with multiple firewalls.
3.2. Server Weight and Scheduling
The administrator of LVS can assign a weight to each node in the real server pool. This weight
is an integer value which is factored into any weight-aware scheduling algorithms (such as
weighted least-connections) and helps the LVS router more evenly load hardware with different
capabilities.
Weights work as a ratio relative to one another. For instance, if one real server has a weight of 1
and the other server has a weight of 5, then the server with a weight of 5 gets 5 connections for
every 1 connection the other server gets. The default value for a real server weight is 1.
Although adding weight to varying hardware configurations in a real server pool can help
load-balance the cluster more efficiently, it can cause temporary imbalances when a real server
is introduced to the real server pool and the virtual server is scheduled using weighted
least-connections. For example, suppose there are three servers in the real server pool. Servers
A and B are weighted at 1 and the third, server C, is weighted at 2. If server C goes down for
any reason, servers A and B evenly distributes the abandoned load. However, once server C
comes back online, the LVS router sees it has zero connections and floods the server with all
incoming requests until it is on par with servers A and B.
To prevent this phenomenon, administrators can make the virtual server a quiesce server —
anytime a new real server node comes online, the least-connections table is reset to zero and
the LVS router routes requests as if all the real servers were newly added to the cluster.
4. Routing Methods
Red Hat Enterprise Linux uses Network Address Translation or NAT routing for LVS, which
allows the administrator tremendous flexibility when utilizing available hardware and integrating
the LVS into an existing network.
4.1. NAT Routing
Figure 1.3, “LVS Implemented with NAT Routing”, illustrates LVS utilizing NAT routing to move
requests between the Internet and a private network.
7

Chapter 1. Linux Virtual Server Overview
Figure 1.3. LVS Implemented with NAT Routing
In the example, there are two NICs in the active LVS router. The NIC for the Internet has a real
IP address on eth0 and has a floating IP address aliased to eth0:1. The NIC for the private
network interface has a real IP address on eth1 and has a floating IP address aliased to eth1:1.
In the event of failover, the virtual interface facing the Internet and the private facing virtual
interface are taken-over by the backup LVS router simultaneously. All of the real servers located
on the private network use the floating IP for the NAT router as their default route to
communicate with the active LVS router so that their abilities to respond to requests from the
Internet is not impaired.
In this example, the LVS router's public LVS floating IP address and private NAT floating IP
address are aliased to two physical NICs. While it is possible to associate each floating IP
address to its own physical device on the LVS router nodes, having more than two NICs is not a
requirement.
Using this topology, the active LVS router receives the request and routes it to the appropriate
server. The real server then processes the request and returns the packets to the LVS router
8

Direct Routing
which uses network address translation to replace the address of the real server in the packets
with the LVS routers public VIP address. This process is called IP masquerading because the
actual IP addresses of the real servers is hidden from the requesting clients.
Using this NAT routing, the real servers may be any kind of machine running various operating
systems. The main disadvantage is that the LVS router may become a bottleneck in large
cluster deployments because it must process outgoing as well as incoming requests.
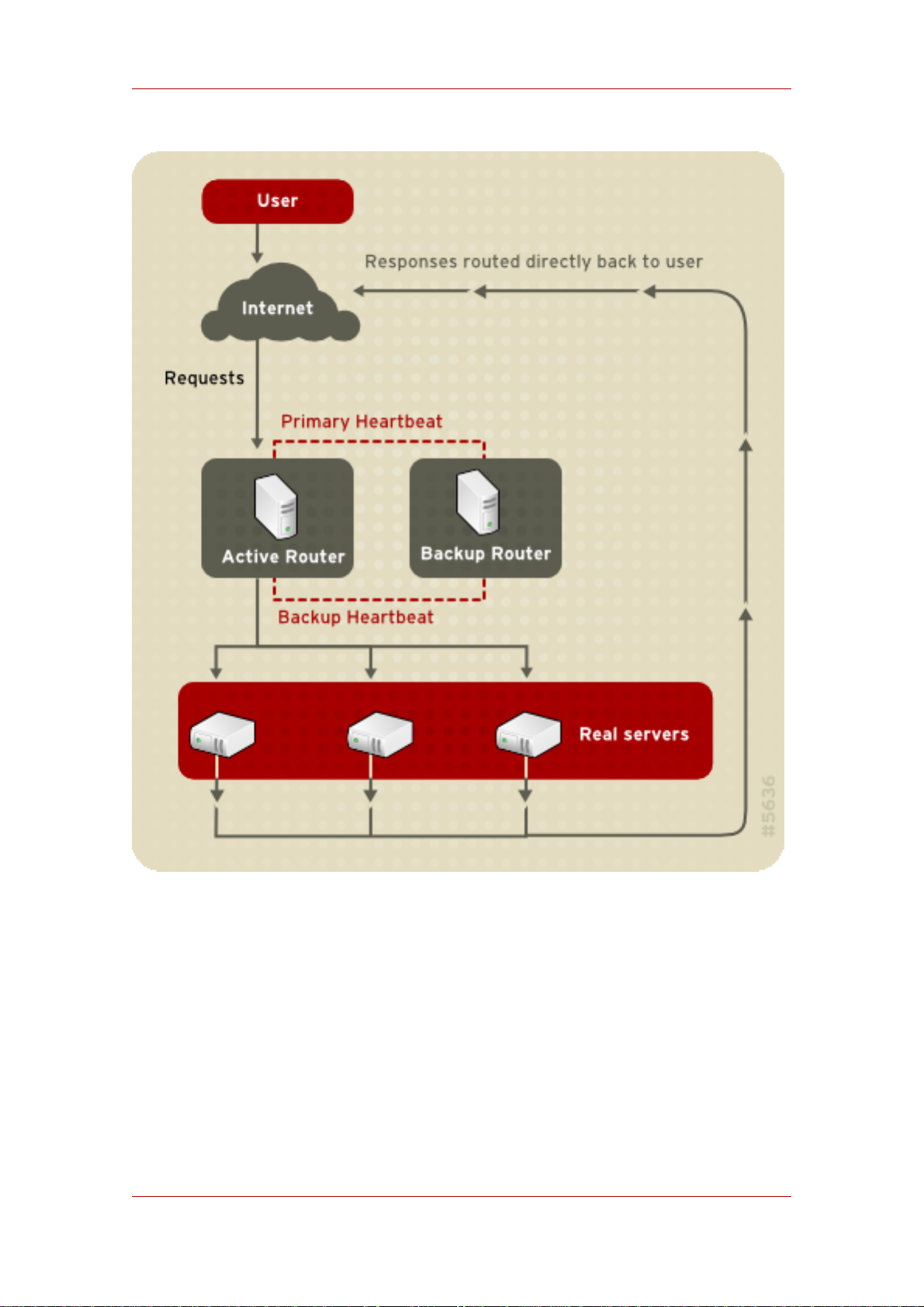
4.2. Direct Routing
Building an LVS setup that uses direct routing provides increased performance benefits
compared to other LVS networking topologies. Direct routing allows the real servers to process
and route packets directly to a requesting user rather than passing all outgoing packets through
the LVS router. Direct routing reduces the possibility of network performance issues by
relegating the job of the LVS router to processing incoming packets only.
9
Chapter 1. Linux Virtual Server Overview
Figure 1.4. LVS Implemented with Direct Routing
In the typical direct routing LVS setup, the LVS router receives incoming server requests
through the virtual IP (VIP) and uses a scheduling algorithm to route the request to the real
servers. The real server processes the request and sends the response directly to the client,
bypassing the LVS routers. This method of routing allows for scalability in that real servers can
be added without the added burden on the LVS router to route outgoing packets from the real
server to the client, which can become a bottleneck under heavy network load.
4.2.1. Direct Routing and the ARP Limitation
10

Persistence and Firewall Marks
While there are many advantages to using direct routing in LVS, there are limitations as well.
The most common issue with LVS via direct routing is with Address Resolution Protocol (ARP).
In typical situations, a client on the Internet sends a request to an IP address. Network routers
typically send requests to their destination by relating IP addresses to a machine's MAC
address with ARP. ARP requests are broadcast to all connected machines on a network, and
the machine with the correct IP/MAC address combination receives the packet. The IP/MAC
associations are stored in an ARP cache, which is cleared periodically (usually every 15
minutes) and refilled with IP/MAC associations.
The issue with ARP requests in a direct routing LVS setup is that because a client request to an
IP address must be associated with a MAC address for the request to be handled, the virtual IP
address of the LVS system must also be associated to a MAC as well. However, since both the
LVS router and the real servers all have the same VIP, the ARP request will be broadcast ed to
all the machines associated with the VIP. This can cause several problems, such as the VIP
being associated directly to one of the real servers and processing requests directly, bypassing
the LVS router completely and defeating the purpose of the LVS setup.
To solve this issue, ensure that the incoming requests are always sent to the LVS router rather
than one of the real servers. This can be done by using either the arptables_jf or the
iptables packet filtering tool for the following reasons:
• The arptables_jf prevents ARP from associating VIPs with real servers.
• The iptables method completely sidesteps the ARP problem by not configuring VIPs on real
servers in the first place.
For more information on using arptables or iptables in a direct routing LVS environment,
refer to Section 2.1, “Direct Routing and arptables_jf” or Section 2.2, “Direct Routing and
iptables”.
5. Persistence and Firewall Marks
In certain situations, it may be desirable for a client to reconnect repeatedly to the same real
server, rather than have an LVS load balancing algorithm send that request to the best available
server. Examples of such situations include multi-screen web forms, cookies, SSL, and FTP
connections. In these cases, a client may not work properly unless the transactions are being
handled by the same server to retain context. LVS provides two different features to handle this:
persistence and firewall marks.
5.1. Persistence
When enabled, persistence acts like a timer. When a client connects to a service, LVS
remembers the last connection for a specified period of time. If that same client IP address
connects again within that period, it is sent to the same server it connected to previously —
bypassing the load-balancing mechanisms. When a connection occurs outside the time window,
11

Chapter 1. Linux Virtual Server Overview
it is handled according to the scheduling rules in place.
Persistence also allows the administrator to specify a subnet mask to apply to the client IP
address test as a tool for controlling what addresses have a higher level of persistence, thereby
grouping connections to that subnet.
Grouping connections destined for different ports can be important for protocols which use more
than one port to communicate, such as FTP. However, persistence is not the most efficient way
to deal with the problem of grouping together connections destined for different ports. For these
situations, it is best to use firewall marks.
5.2. Firewall Marks
Firewall marks are an easy and efficient way to a group ports used for a protocol or group of
related protocols. For instance, if LVS is deployed to run an e-commerce site, firewall marks can
be used to bundle HTTP connections on port 80 and secure, HTTPS connections on port 443.
By assigning the same firewall mark to the virtual server for each protocol, state information for
the transaction can be preserved because the LVS router forwards all requests to the same real
server after a connection is opened.
Because of its efficiency and ease-of-use, administrators of LVS should use firewall marks
instead of persistence whenever possible for grouping connections. However, administrators
should still add persistence to the virtual servers in conjunction with firewall marks to ensure the
clients are reconnected to the same server for an adequate period of time.
6. LVS — A Block Diagram
LVS routers use a collection of programs to monitor cluster members and cluster services.
Figure 1.5, “LVS Components” illustrates how these various programs on both the active and
backup LVS routers work together to manage the cluster.
12
 Loading...
Loading...