Page 1

Red Hat Directory
Server 8.1
Configuration and
Command Reference
Ella Deon Lackey
Publication date: April 28, 2009, updated on February 11, 2010
Page 2

Configuration and Command Reference
Red Hat Directory Server 8.1 Configuration and Command
Reference
Edition 8.1.10
Author Ella Deon Lackey
Copyright © 2009 Red Hat, Inc.
Copyright © 2009 Red Hat, Inc..
The text of and illustrations in this document are licensed by Red Hat under a Creative Commons
Attribution–Share Alike 3.0 Unported license ("CC-BY-SA"). An explanation of CC-BY-SA is available
at http://creativecommons.org/licenses/by-sa/3.0/. In accordance with CC-BY-SA, if you distribute this
document or an adaptation of it, you must provide the URL for the original version.
Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert,
Section 4d of CC-BY-SA to the fullest extent permitted by applicable law.
Red Hat, Red Hat Enterprise Linux, the Shadowman logo, JBoss, MetaMatrix, Fedora, the Infinity
Logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries.
Linux® is the registered trademark of Linus Torvalds in the United States and other countries.
Java® is a registered trademark of Oracle and/or its affiliates.
XFS® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States
and/or other countries.
MySQL® is a registered trademark of MySQL AB in the United States, the European Union and other
countries.
All other trademarks are the property of their respective owners.
1801 Varsity Drive
Raleigh, NC 27606-2072 USA
Phone: +1 919 754 3700
Phone: 888 733 4281
Fax: +1 919 754 3701
Page 3

About This Reference ix
1. Directory Server Overview .............................................................................................. ix
2. Examples and Formatting ............................................................................................... ix
2.1. Command and File Examples ............................................................................... ix
2.2. Tool Locations ..................................................................................................... ix
2.3. LDAP Locations ................................................................................................... ix
2.4. Text Formatting and Styles ................................................................................... x
3. Additional Reading ......................................................................................................... xi
4. Giving Feedback ............................................................................................................ xii
5. Documentation History ................................................................................................... xii
1. Introduction 1
1.1. Directory Server Configuration ...................................................................................... 1
1.2. Directory Server Instance File Reference ....................................................................... 1
1.3. Using Directory Server Command-Line Utilities .............................................................. 1
1.4. Using Directory Server Command-Line Scripts ............................................................... 1
2. Core Server Configuration Reference 3
2.1. Overview of the Directory Server Configuration .............................................................. 3
2.1.1. LDIF and Schema Configuration Files ................................................................. 3
2.1.2. How the Server Configuration Is Organized ......................................................... 6
2.2. Accessing and Modifying Server Configuration ............................................................... 7
2.2.1. Access Control for Configuration Entries ............................................................. 7
2.2.2. Changing Configuration Attributes ...................................................................... 8
2.3. Core Server Configuration Attributes Reference ........................................................... 10
2.3.1. cn=config ........................................................................................................ 10
2.3.2. cn=changelog5 ................................................................................................ 71
2.3.3. cn=encryption .................................................................................................. 75
2.3.4. cn=features ..................................................................................................... 77
2.3.5. cn=mapping tree .............................................................................................. 78
2.3.6. Suffix Configuration Attributes under cn="suffixName" ........................................ 78
2.3.7. Replication Attributes under cn=replica, cn="suffixDN", cn=mapping tree,
cn=config .................................................................................................................. 79
2.3.8. Replication Attributes under cn=ReplicationAgreementName, cn=replica,
cn="suffixName", cn=mapping tree, cn=config ............................................................. 85
2.3.9. Synchronization Attributes under cn=syncAgreementName,
cn=WindowsReplica,cn="suffixName", cn=mapping tree, cn=config .............................. 94
2.3.10. cn=monitor .................................................................................................... 97
2.3.11. cn=replication ................................................................................................. 99
2.3.12. cn=sasl ......................................................................................................... 99
2.3.13. cn=SNMP .................................................................................................... 100
2.3.14. SNMP Statistic Attributes .............................................................................. 102
2.3.15. cn=tasks ...................................................................................................... 104
2.3.16. cn=uniqueid generator .................................................................................. 120
2.4. Configuration Object Classes .................................................................................... 120
2.4.1. changeLogEntry (Object Class) ...................................................................... 120
2.4.2. directoryServerFeature (Object Class) ............................................................. 121
2.4.3. nsBackendInstance (Object Class) .................................................................. 122
2.4.4. nsChangelog4Config (Object Class) ................................................................ 122
2.4.5. nsContainer (Object Class) ............................................................................. 123
2.4.6. nsDS5Replica (Object Class) .......................................................................... 123
2.4.7. nsDS5ReplicationAgreement (Object Class) .................................................... 124
iii
Page 4
Configuration and Command Reference
2.4.8. nsDSWindowsReplicationAgreement (Object Class) ......................................... 126
2.4.9. nsMappingTree (Object Class) ........................................................................ 128
2.4.10. nsSaslMapping (Object Class) ...................................................................... 128
2.4.11. nsslapdConfig (Object Class) ........................................................................ 129
2.4.12. passwordpolicy (Object Class) ...................................................................... 129
2.5. Legacy Attributes ...................................................................................................... 131
2.5.1. Legacy Server Attributes ................................................................................ 132
2.5.2. Legacy Replication Attributes .......................................................................... 134
3. Plug-in Implemented Server Functionality Reference 143
3.1. Server Plug-in Functionality Reference ...................................................................... 143
3.1.1. 7-bit Check Plug-in ........................................................................................ 143
3.1.2. ACL Plug-in ................................................................................................... 144
3.1.3. ACL Preoperation Plug-in ............................................................................... 144
3.1.4. Attribute Uniqueness Plug-in .......................................................................... 145
3.1.5. Binary Syntax Plug-in ..................................................................................... 145
3.1.6. Boolean Syntax Plug-in .................................................................................. 146
3.1.7. Case Exact String Syntax Plug-in ................................................................... 146
3.1.8. Case Ignore String Syntax Plug-in .................................................................. 147
3.1.9. Chaining Database Plug-in ............................................................................. 147
3.1.10. Class of Service Plug-in ............................................................................... 147
3.1.11. Country String Syntax Plug-in ....................................................................... 148
3.1.12. Distinguished Name Syntax Plug-in ............................................................... 148
3.1.13. Distributed Numeric Assignment Plug-in ........................................................ 149
3.1.14. Generalized Time Syntax Plug-in .................................................................. 149
3.1.15. HTTP Client Plug-in ..................................................................................... 150
3.1.16. Integer Syntax Plug-in .................................................................................. 150
3.1.17. Internationalization Plug-in ............................................................................ 150
3.1.18. JPEG Syntax Plug-in .................................................................................... 151
3.1.19. ldbm database Plug-in .................................................................................. 151
3.1.20. Legacy Replication Plug-in ........................................................................... 152
3.1.21. MemberOf Plug-in ........................................................................................ 152
3.1.22. Multi-master Replication Plug-in .................................................................... 153
3.1.23. Octet String Syntax Plug-in ........................................................................... 153
3.1.24. OID Syntax Plug-in ...................................................................................... 153
3.1.25. Password Storage Schemes ......................................................................... 154
3.1.26. Postal Address String Syntax Plug-in ............................................................ 155
3.1.27. PTA Plug-in ................................................................................................. 156
3.1.28. Referential Integrity Postoperation Plug-in ..................................................... 156
3.1.29. Retro Changelog Plug-in .............................................................................. 157
3.1.30. Roles Plug-in ............................................................................................... 158
3.1.31. Schema Reload Plug-in ................................................................................ 158
3.1.32. Space Insensitive String Syntax Plug-in ......................................................... 159
3.1.33. State Change Plug-in ................................................................................... 159
3.1.34. Telephone Syntax Plug-in ............................................................................. 160
3.1.35. URI Syntax Plug-in ...................................................................................... 160
3.1.36. Views Plug-in ............................................................................................... 160
3.2. List of Attributes Common to All Plug-ins ................................................................... 161
3.2.1. nsSlapdPlugin ................................................................................................ 161
3.2.2. nsslapd-pluginPath ......................................................................................... 162
3.2.3. nsslapd-pluginInitfunc ..................................................................................... 162
3.2.4. nsslapd-pluginType ........................................................................................ 162
iv
Page 5

3.2.5. nsslapd-pluginEnabled ................................................................................... 162
3.2.6. nsslapd-pluginId ............................................................................................. 163
3.2.7. nsslapd-pluginVersion ..................................................................................... 163
3.2.8. nsslapd-pluginVendor ..................................................................................... 163
3.2.9. nsslapd-pluginDescription ............................................................................... 163
3.3. Attributes Allowed by Certain Plug-ins ....................................................................... 164
3.3.1. nsslapd-pluginLoadNow .................................................................................. 164
3.3.2. nsslapd-pluginLoadGlobal ............................................................................... 164
3.3.3. nsslapd-plugin-depends-on-type ...................................................................... 164
3.3.4. nsslapd-plugin-depends-on-named .................................................................. 165
3.4. Database Plug-in Attributes ....................................................................................... 165
3.4.1. Database Attributes under cn=config, cn=ldbm database, cn=plugins, cn=config
................................................................................................................................ 165
3.4.2. Database Attributes under cn=monitor, cn=ldbm database, cn=plugins,
cn=config ................................................................................................................ 178
3.4.3. Database Attributes under cn=NetscapeRoot, cn=ldbm database, cn=plugins,
cn=config and cn=userRoot, cn=ldbm database, cn=plugins, cn=config ....................... 179
3.4.4. Database Attributes under cn=database, cn=monitor, cn=ldbm database,
cn=plugins, cn=config .............................................................................................. 186
3.4.5. Database Attributes under cn=default indexes, cn=config, cn=ldbm database,
cn=plugins, cn=config .............................................................................................. 188
3.4.6. Database Attributes under cn=monitor, cn=NetscapeRoot, cn=ldbm database,
cn=plugins, cn=config .............................................................................................. 191
3.4.7. Database Attributes under cn=index, cn=NetscapeRoot, cn=ldbm database,
cn=plugins, cn=config and cn=index, cn=UserRoot, cn=ldbm database, cn=plugins,
cn=config ................................................................................................................ 192
3.4.8. Database Attributes under cn=attributeName, cn=encrypted attributes,
cn=database_name, cn=ldbm database, cn=plugins, cn=config .................................. 194
3.5. Database Link Plug-in Attributes (Chaining Attributes) ................................................. 195
3.5.1. Database Link Attributes under cn=config, cn=chaining database, cn=plugins,
cn=config ................................................................................................................ 196
3.5.2. Database Link Attributes under cn=default instance config, cn=chaining
database, cn=plugins, cn=config .............................................................................. 198
3.5.3. Database Link Attributes under cn=database_link_name, cn=chaining
database, cn=plugins, cn=config .............................................................................. 202
3.5.4. Database Link Attributes under cn=monitor, cn=database instance name,
cn=chaining database, cn=plugins, cn=config ............................................................ 204
3.6. Retro Changelog Plug-in Attributes ............................................................................ 205
3.6.1. nsslapd-changelogdir ..................................................................................... 206
3.6.2. nsslapd-changelogmaxage (Max Changelog Age) ............................................ 206
3.7. Distributed Numeric Assignment Plug-in Attributes ...................................................... 207
3.7.1. dnaFilter ........................................................................................................ 207
3.7.2. dnaMagicRegen ............................................................................................. 207
3.7.3. dnaMaxValue ................................................................................................. 208
3.7.4. dnaNextRange ............................................................................................... 208
3.7.5. dnaNextValue ................................................................................................ 209
3.7.6. dnaPrefix ....................................................................................................... 209
3.7.7. dnaRangeRequestTimeout ............................................................................. 209
3.7.8. dnaScope ...................................................................................................... 210
3.7.9. dnaSharedCfgDN ........................................................................................... 210
3.7.10. dnaThreshold ............................................................................................... 211
v
Page 6

Configuration and Command Reference
3.7.11. dnaType ....................................................................................................... 211
3.8. MemberOf Plug-in Attributes ..................................................................................... 211
3.8.1. memberofattr ................................................................................................. 212
3.8.2. memberofgroupattr ......................................................................................... 212
4. Server Instance File Reference 213
4.1. Overview of Directory Server Files ............................................................................ 213
4.2. Backup Files ............................................................................................................ 214
4.3. Configuration Files .................................................................................................... 214
4.4. Database Files ......................................................................................................... 214
4.5. LDIF Files ................................................................................................................ 216
4.6. Lock Files ................................................................................................................ 216
4.7. Log Files .................................................................................................................. 217
4.8. PID Files .................................................................................................................. 217
4.9. Tools ........................................................................................................................ 217
4.10. Scripts .................................................................................................................... 218
5. Log File Reference 219
5.1. Access Log Reference .............................................................................................. 219
5.1.1. Access Logging Levels .................................................................................. 220
5.1.2. Default Access Logging Content ..................................................................... 220
5.1.3. Access Log Content for Additional Access Logging Levels ................................ 227
5.1.4. Common Connection Codes ........................................................................... 229
5.2. Error Log Reference ................................................................................................. 229
5.2.1. Error Log Logging Levels ............................................................................... 230
5.2.2. Error Log Content .......................................................................................... 231
5.2.3. Error Log Content for Other Log Levels ........................................................... 232
5.3. Audit Log Reference ................................................................................................. 235
5.4. LDAP Result Codes .................................................................................................. 237
6. Command-Line Utilities 239
6.1. Finding and Executing Command-Line Utilities ........................................................... 239
6.2. Using Special Characters .......................................................................................... 239
6.3. Command-Line Utilities Quick Reference ................................................................... 240
6.4. ldapsearch ............................................................................................................... 240
6.5. ldapmodify ................................................................................................................ 256
6.6. ldapdelete ................................................................................................................ 262
6.7. ldappasswd .............................................................................................................. 267
6.8. ldif ........................................................................................................................... 273
6.9. dbscan ..................................................................................................................... 274
7. Command-Line Scripts 277
7.1. Finding and Executing Command-Line Scripts ............................................................ 277
7.2. Command-Line Scripts Quick Reference .................................................................... 277
7.3. Shell Scripts ............................................................................................................. 279
7.3.1. bak2db (Restores a Database from Backup) .................................................... 280
7.3.2. cl-dump (Dumps and Decodes the Changelog) ................................................ 281
7.3.3. db2bak (Creates a Backup of a Database) ...................................................... 282
7.3.4. db2ldif (Exports Database Contents to LDIF) ................................................... 282
7.3.5. db2index (Reindexes Database Index Files) .................................................... 283
7.3.6. dbverify (Checks for Corrupt Databases) ......................................................... 284
7.3.7. ds_removal .................................................................................................... 285
7.3.8. ldif2db (Import) .............................................................................................. 286
vi
Page 7

7.3.9. ldif2ldap (Performs Import Operation over LDAP) ............................................. 287
7.3.10. monitor (Retrieves Monitoring Information) ..................................................... 288
7.3.11. repl-monitor (Monitors Replication Status) ...................................................... 288
7.3.12. pwdhash (Prints Encrypted Passwords) ......................................................... 291
7.3.13. restart-slapd (Restarts the Directory Server) .................................................. 291
7.3.14. restoreconfig (Restores Administration Server Configuration) .......................... 292
7.3.15. saveconfig (Saves Administration Server Configuration) .................................. 292
7.3.16. start-slapd (Starts the Directory Server) ......................................................... 292
7.3.17. stop-slapd (Stops the Directory Server) ......................................................... 293
7.3.18. suffix2instance (Maps a Suffix to a Backend Name) ....................................... 293
7.3.19. vlvindex (Creates Virtual List View Indexes) ................................................... 294
7.4. Perl Scripts .............................................................................................................. 294
7.4.1. bak2db.pl (Restores a Database from Backup) ................................................ 295
7.4.2. cl-dump.pl (Dumps and Decodes the Changelog) ............................................. 296
7.4.3. db2bak.pl (Creates a Backup of a Database) ................................................... 297
7.4.4. db2index.pl (Creates and Generates Indexes) ................................................. 298
7.4.5. db2ldif.pl (Exports Database Contents to LDIF) ................................................ 298
7.4.6. fixup-memberof.pl (Regenerate memberOf Attributes) ...................................... 300
7.4.7. ldif2db.pl (Import) ........................................................................................... 300
7.4.8. logconv.pl (Log Converter) .............................................................................. 302
7.4.9. migrate-ds.pl .................................................................................................. 305
7.4.10. migrate-ds-admin.pl ...................................................................................... 308
7.4.11. ns-accountstatus.pl (Establishes Account Status) ........................................... 310
7.4.12. ns-activate.pl (Activates an Entry or Group of Entries) .................................... 310
7.4.13. ns-inactivate.pl (Inactivates an Entry or Group of Entries) ............................... 311
7.4.14. ns-newpwpolicy.pl (Adds Attributes for Fine-Grained Password Policy) ............. 312
7.4.15. register-ds-admin.pl ...................................................................................... 313
7.4.16. remove-ds.pl ................................................................................................ 313
7.4.17. repl-monitor.pl (Monitors Replication Status) .................................................. 314
7.4.18. schema-reload.pl (Reload Schema Files Dynamically) .................................... 317
7.4.19. setup-ds.pl ................................................................................................... 317
7.4.20. setup-ds-admin.pl ......................................................................................... 319
7.4.21. verify-db.pl (Check for Corrupt Databases) .................................................... 321
A. Using the ns-slapd Command-Line Utilities 323
A.1. Overview of ns-slapd ................................................................................................ 323
A.2. Finding and Executing the ns-slapd Command-Line Utilities ........................................ 323
A.3. Utilities for Exporting Databases: db2ldif .................................................................... 323
A.4. Utilities for Restoring and Backing up Databases: ldif2db ............................................ 325
A.5. Utilities for Restoring and Backing up Databases: archive2db ...................................... 326
A.6. Utilities for Restoring and Backing up Databases: db2archive ...................................... 327
A.7. Utilities for Creating and Regenerating Indexes: db2index ........................................... 327
Glossary 329
Index 343
vii
Page 8

viii
Page 9

About This Reference
Red Hat Directory Server (Directory Server) is a powerful and scalable distributed directory server
based on the industry-standard Lightweight Directory Access Protocol (LDAP). Directory Server is the
cornerstone for building a centralized and distributed data repository that can be used in an intranet,
over an extranet with trading partners, or over the public Internet to reach customers.
This reference covers the server configuration and the command-line utilities. It is designed primarily
for directory administrators and experienced directory users who want to use the command-line to
access the directory. After configuring the server, use this reference to help maintain it.
The Directory Server can also be managed through the Directory Server Console, a graphical user
interface. The Red Hat Directory Server Administrator's Guide describes how to do this and explains
individual administration tasks more fully.
1. Directory Server Overview
The major components of Directory Server include:
• An LDAP server – The LDAP v3-compliant network daemon.
• Directory Server Console – A graphical management console that dramatically reduces the effort of
setting up and maintaining your directory service.
• SNMP agent – Can monitor the Directory Server using the Simple Network Management Protocol
(SNMP).
2. Examples and Formatting
Each of the examples used in this guide, such as file locations and commands, have certain defined
conventions.
2.1. Command and File Examples
All of the examples for Red Hat Directory Server commands, file locations, and other usage are given
for Red Hat Enterprise Linux 5 (32-bit) systems. Be certain to use the appropriate commands and files
for your platform.
To start the Red Hat Directory Server:
service dirsv start
Example 1. Example Command
2.2. Tool Locations
The tools for Red Hat Directory Server are located in the /usr/bin and the /usr/sbin directories.
These tools can be run from any location without specifying the tool location.
2.3. LDAP Locations
There is another important consideration with the Red Hat Directory Server tools. The LDAP tools
referenced in this guide are Mozilla LDAP, installed with Red Hat Directory Server in the /usr/lib/
ix
Page 10
About This Reference
mozldap directory on Red Hat Enterprise Linux 5 (32-bit) (or /usr/lib64/mozldap for 64-bit
systems).
However, Red Hat Enterprise Linux systems also include LDAP tools from OpenLDAP in the /usr/
bin directory. It is possible to use the OpenLDAP commands as shown in the examples, but you must
use the -x argument to disable SASL, which OpenLDAP tools use by default.
2.4. Text Formatting and Styles
Certain words are represented in different fonts, styles, and weights. Different character formatting is
used to indicate the function or purpose of the phrase being highlighted.
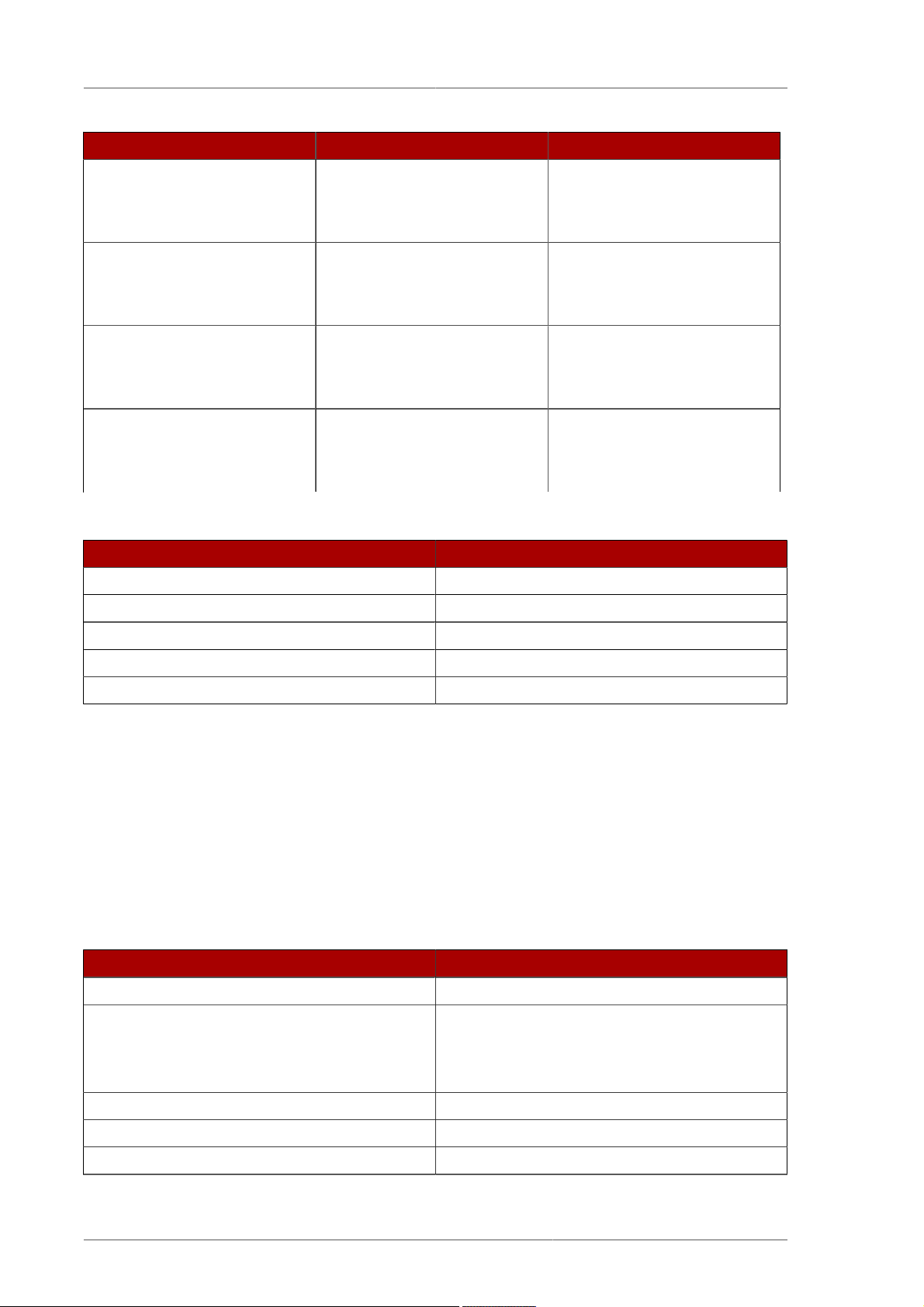
Formatting Style Purpose
Monospace font Monospace is used for commands, package
names, files and directory paths, and any text
displayed in a prompt.
Monospace
with a
background
Italicized text Any text which is italicized is a variable, such
Bolded text Most phrases which are in bold are application
Other formatting styles draw attention to important text.
This type of formatting is used for anything
entered or returned in a command prompt.
as instance_name or hostname. Occasionally,
this is also used to emphasize a new term or
other phrase.
names, such as Cygwin, or are fields or
options in a user interface, such as a User
Name Here: field or Save button.
NOTE
A note provides additional information that can help illustrate the behavior of the
system or provide more detail for a specific issue.
IMPORTANT
Important information is necessary, but possibly unexpected, such as a configuration
change that will not persist after a reboot.
WARNING
A warning indicates potential data loss, as may happen when tuning hardware for
maximum performance.
x
Page 11

Additional Reading
3. Additional Reading
The Directory Server Administrator's Guide describes how to set up, configure, and administer Red
Hat Directory Server and its contents. this manual does not describe many of the basic directory and
architectural concepts that you need to deploy, install, and administer a directory service successfully.
Those concepts are contained in the Red Hat Directory Server Deployment Guide. You should read
that book before continuing with this manual.
When you are familiar with Directory Server concepts and have done some preliminary planning for
your directory service, install the Directory Server. The instructions for installing the various Directory
Server components are contained in the Red Hat Directory Server Installation Guide. Many of the
scripts and commands used to install and administer the Directory Server are explained in detail in the
Red Hat Directory Server Configuration, Command, and File Reference.
Also, Managing Servers with Red Hat Console contains general background information on how to
use the Red Hat Console. You should read and understand the concepts in that book before you
attempt to administer Directory Server.
The document set for Directory Server contains the following guides:
• Red Hat Directory Server Release Notes contain important information on new features, fixed bugs,
known issues and workarounds, and other important deployment information for this specific version
of Directory Server.
• Red Hat Directory Server Deployment Guide provides an overview for planning a deployment of the
Directory Server.
• Red Hat Directory Server Administrator's Guide contains procedures for the day-to-day maintenance
of the directory service. Includes information on configuring server-side plug-ins.
• Red Hat Directory Server Configuration, Command, and File Reference provides reference
information on the command-line scripts, configuration attributes, and log files shipped with
Directory Server.
• Red Hat Directory Server Installation Guide contains procedures for installing your Directory Server
as well as procedures for migrating from a previous installation of Directory Server.
• Red Hat Directory Server Schema Reference provides reference information about the Directory
Server schema.
• Red Hat Directory Server Plug-in Programmer's Guide describes how to write server plug-ins in
order to customize and extend the capabilities of Directory Server.
• Using Red Hat Console gives an overview of the primary user interface and how it interacts with
the Directory Server and Administration Server, as well as how to perform basic management tasks
through the main Console window.
• Using the Admin Server describes the different tasks and tools associated with the Administration
Server and how to use the Administration Server with the Configuration and User Directory Server
instances.
For the latest information about Directory Server, including current release notes, complete product
documentation, technical notes, and deployment information, see the Red Hat Directory Server
documentation site at http://www.redhat.com/docs/manuals/dir-server/.
xi
Page 12

About This Reference
4. Giving Feedback
If there is any error in this Configuration, Command, and File Reference or there is any way to improve
the documentation, please let us know. Bugs can be filed against the documentation for Red Hat
Directory Server through Bugzilla, http://bugzilla.redhat.com/bugzilla. Make the bug report as specific
as possible, so we can be more effective in correcting any issues:
• Select the Red Hat Directory Server product.
• Set the component to Doc - cli-guide.
• Set the version number to 8.1.
• For errors, give the page number (for the PDF) or URL (for the HTML), and give a succinct
description of the problem, such as incorrect procedure or typo.
For enhancements, put in what information needs to be added and why.
• Give a clear title for the bug. For example, "Incorrect command example for setup
script options" is better than "Bad example".
We appreciate receiving any feedback — requests for new sections, corrections, improvements,
enhancements, even new ways of delivering the documentation or new styles of docs. You are
welcome to contact Red Hat Content Services directly at mailto:docs@redhat.com.
5. Documentation History
Revision
8.1.10
Adding information about setting an idle timeout period for large databases for the replication user,
per Bugzilla #618055.
Revision 8.1.9 February 11, 2010 Ella Deon Lackey
Clarifying how passwordUnlock works, per Bugzilla #552377.
Changing thensDirectoryServerTask object class to extensibleObject, per Bugzilla #555787.
Adding extra reference to the 64-bit tools directory, per Bugzilla #554972.
Revision 8.1.8 January 11, 2010 Ella Deon Lackey
Adding section on nsslapd-cachememsize and the import buffer size, per Bugzilla #531043.
July 29, 2010 Ella Deon Lackey
Revision 8.1.7 October 10, 2009 Ella Deon Lackey
Fixing two plug-in descriptions.
Revision 8.1.6 September 19, 2009 Ella Deon Lackey
Removing the silent configuration parameters for the register-ds-admin.pl script, per Bugzilla
#514231.
xii
Page 13

Documentation History
Revision 8.1.5 September 9, 2009 Ella Deon Lackey
Removing any references to the Directory Server Gateway or Org Chart.
Revision 8.1.4 September 4, 2009 Ella Deon Lackey
Correcting the directory paths for configuration LDIF files, per Bugzilla #521139.
Revision 8.1.3 August 26, 2009 Ella Deon Lackey
Adding information about setting database and entry cache memory sizes and clarifying the units
of measurement for the attributes, per Bugzilla #503615.
Revision 8.1.2 August 4, 2009 Ella Deon Lackey
Changed the default on the nsslapd-cache-autosize parameter to 0, per Bugzilla #514282.
Revision 8.1.1 July 19, 2009 Ella Deon Lackey
Expanding the description of dnaNextRange, Bugzilla #512557.
Revision 8.1.0 April 28, 2009 Ella Deon Lackey dlackey@redhat.com
Initial draft for version 8.1.
xiii
Page 14

xiv
Page 15

Chapter 1.
Introduction
Directory Server is based on an open-systems server protocol called the Lightweight Directory Access
Protocol (LDAP). The Directory Server is a robust, scalable server designed to manage large scale
directories to support an enterprise-wide directory of users and resources, extranets, and e-commerce
applications over the Internet. The Directory Server runs as the ns-slapd process or service on the
machine. The server manages the directory databases and responds to client requests.
This reference deals with the other methods of managing the Directory Server by altering the server
configuration attributes using the command line and using command-line utilities and scripts.
1.1. Directory Server Configuration
The format and method for storing configuration information for Directory Server and a listing for all
server attributes are found in two chapters, Chapter 2, Core Server Configuration Reference and
Chapter 3, Plug-in Implemented Server Functionality Reference.
1.2. Directory Server Instance File Reference
Chapter 4, Server Instance File Reference has an overview of the files and configuration information
stored in each instance of Directory Server. This is useful reference to helps administrators understand
the changes or absence of changes in the course of directory activity. From a security standpoint, this
also helps users detect errors and intrusion by highlighting normal changes and abnormal behavior.
1.3. Using Directory Server Command-Line Utilities
Directory Server comes with a set of configurable command-line utilities that can search and modify
entries in the directory and administer the server. Chapter 6, Command-Line Utilities describes these
command-line utilities and contains information on where the utilities are stored and how to access
them. In addition to these command-line utilities, Directory Server also provides ns-slapd commandline utilities for performing directory operations, as described in Appendix A, Using the ns-slapd
Command-Line Utilities.
1.4. Using Directory Server Command-Line Scripts
In addition to command-line utilities, several non-configurable scripts are provided with the Directory
Server that make it quick and easy to perform routine server administration tasks from the commandline. Chapter 7, Command-Line Scripts lists the most frequently used scripts and contains information
on where the scripts are stored and how to access them.
1
Page 16

2
Page 17
Chapter 2.
Core Server Configuration Reference
The configuration information for Red Hat Directory Server is stored as LDAP entries within the
directory itself. Therefore, changes to the server configuration must be implemented through the
use of the server itself rather than by simply editing configuration files. The principal advantage
of this method of configuration storage is that it allows a directory administrator to reconfigure the
server using LDAP while it is still running, thus avoiding the need to shut the server down for most
configuration changes.
This chapter gives details on how the configuration is organized and how to alter it. The chapter also
provides an alphabetical reference for all attributes.
2.1. Overview of the Directory Server Configuration
When the Directory Server is set up, its default configuration is stored as a series of LDAP entries
within the directory, under the subtree cn=config. When the server is started, the contents of the
cn=config subtree are read from a file (dse.ldif) in LDIF format. This dse.ldif file contains
all of the server configuration information. The latest version of this file is called dse.ldif, the
version prior to the last modification is called dse.ldif.bak, and the latest file with which the server
successfully started is called dse.ldif.startOK.
Many of the features of the Directory Server are designed as discrete modules that plug into the core
server. The details of the internal configuration for each plug-in are contained in separate entries
under cn=plugins,cn=config. For example, the configuration of the Telephone Syntax Plug-in is
contained in this entry:
cn=Telephone Syntax,cn=plugins,cn=config
Similarly, database-specific configuration is stored under
cn=ldbm database,cn=plugins,cn=config for local databases and cn=chaining
database,cn=plugins,cn=config for database links.
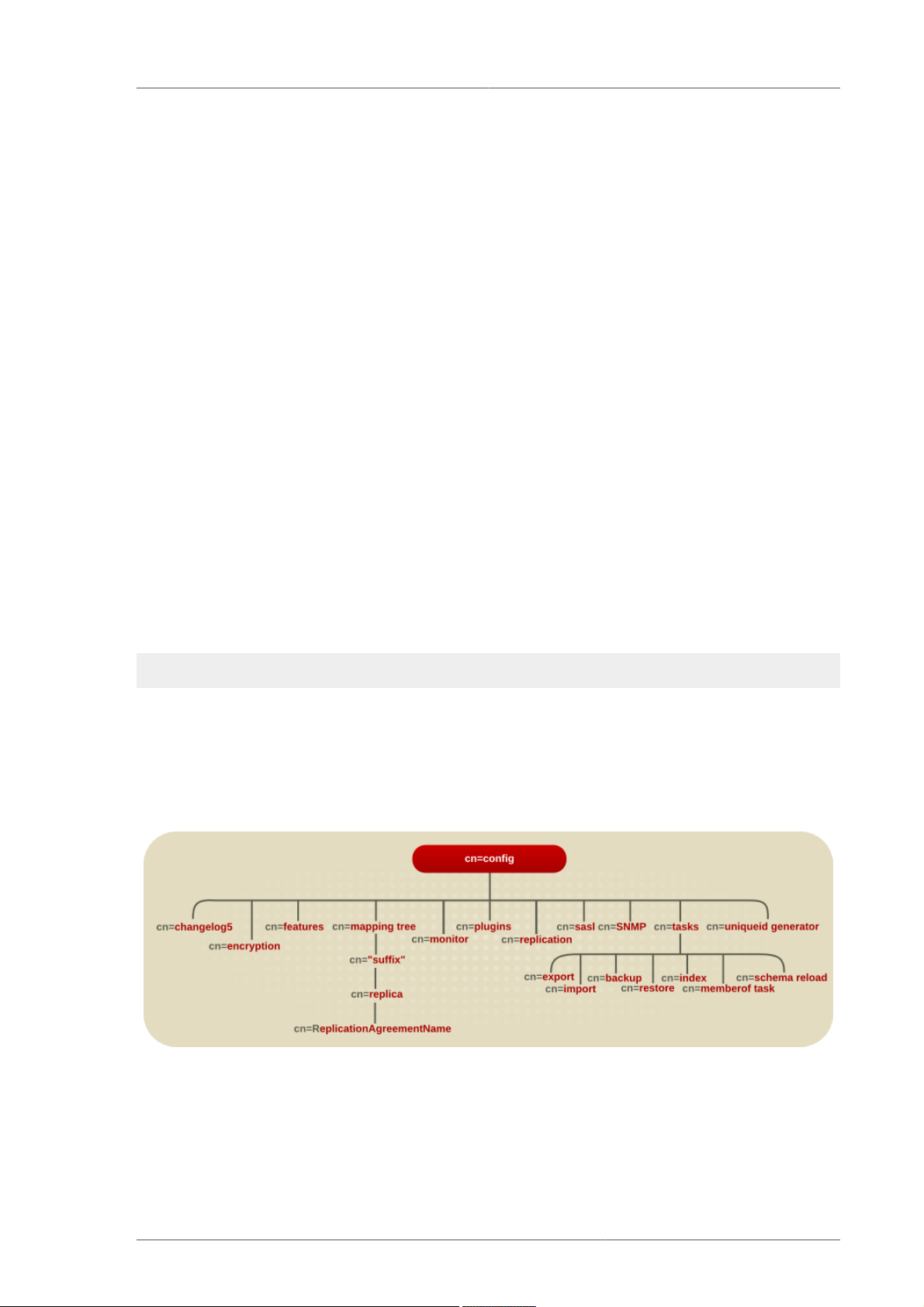
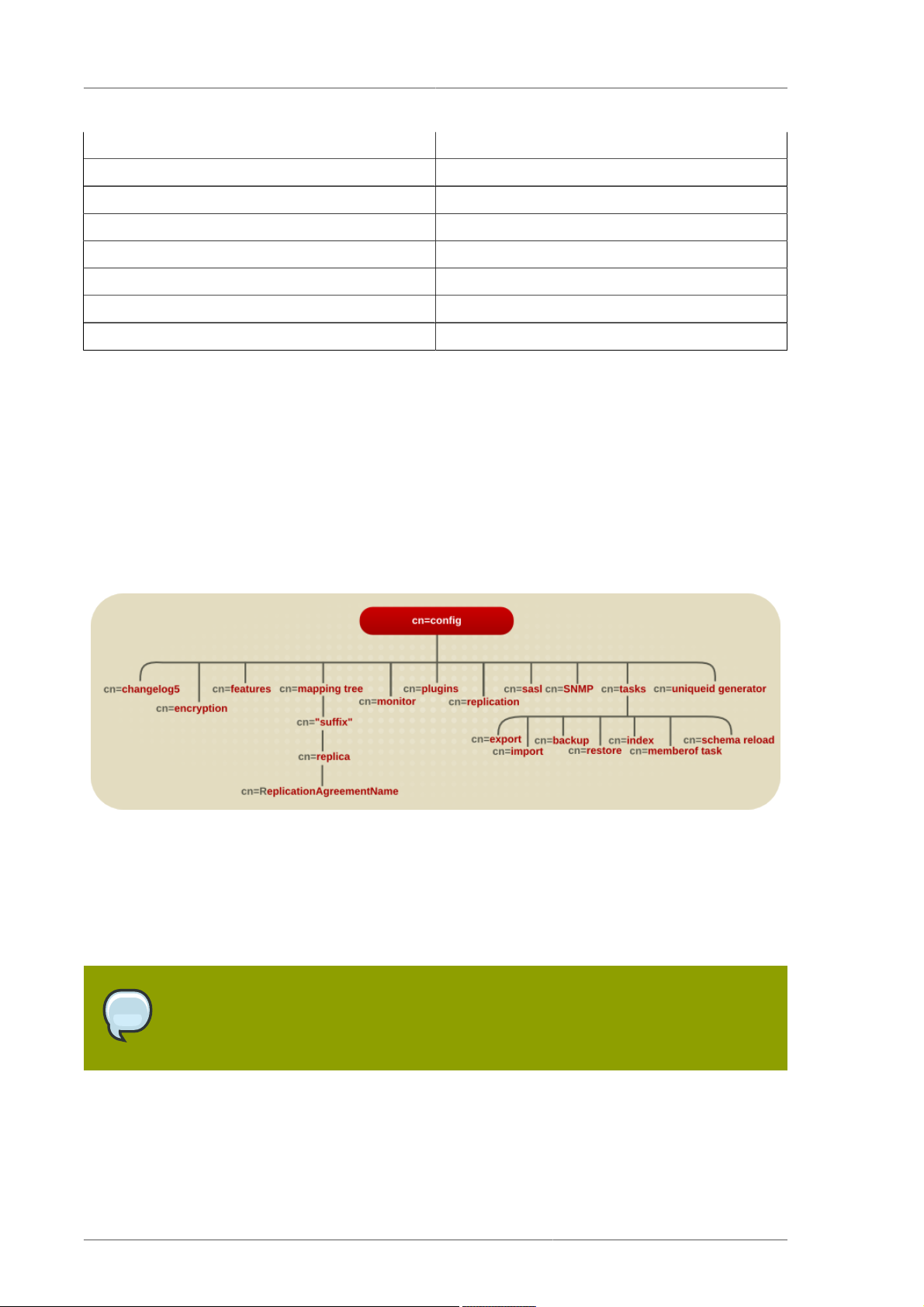
The following diagram illustrates how the configuration data fits within the cn=config directory
information tree.
Figure 2.1. Directory Information Tree Showing Configuration Data
2.1.1. LDIF and Schema Configuration Files
The Directory Server configuration data are stored in LDIF files in the /etc/dirsrv/
slapd-instance_name directory (/etc/opt/dirsrv/slapd-instance_name on HP-UX). Thus,
3
Page 18

Chapter 2. Core Server Configuration Reference
if a server identifier is phonebook, then for a Directory Server on Red Hat Enterprise Linux 5 (32-bit),
the configuration LDIF files are all stored under /etc/dirsrv/slapd-phonebook.
This directory also contains other server instance-specific configuration files.
Schema configuration is also stored in LDIF format, and these files are located in the /etc/dirsrv/
slapd-instance_name/schema directory (/etc/opt/dirsrv/slapd->instance_name on HP-
UX).
The following table lists all of the configuration files that are supplied with the Directory Server,
including those for the schema of other compatible servers. Each file is preceded by a number which
indicates the order in which they should be loaded (in ascending numerical and then alphabetical
order).
Configuration Filename Purpose
dse.ldif Contains front-end Directory Specific Entries
created by the directory at server startup. These
include the Root DSE ("") and the contents of
cn=config and cn=monitor (ACIs only).
00core.ldif Contains only those schema definitions
necessary for starting the server with the bare
minimum feature set (no user schema, no
schema for any non-core features). The rest
of the schema used by users, features, and
applications is found in 01common.ldif and the
other schema files. Do not modify this file.
01common.ldif Contains LDAPv3 standard operational schema,
such as subschemaSubentry, LDAPv3
standard user and organization schema
defined in RFC 2256 (based on X.520/X.521),
inetOrgPerson and other widely-used
attributes, and the operational attributes used by
Directory Server configuration. Modifying this file
causes interoperability problems. User-defined
attributes should be added through the Directory
Server Console.
05rfc2247.ldif Schema from RFC 2247 and related pilot
schema, from "Using Domains in LDAP/X500
Distinguished Names."
05rfc2927.ldif Schema from RFC 2927, "MIME Directory Profile
for LDAP Schema." Contains the ldapSchemas
operational attribute required for the attribute to
show up in the subschema subentry.
10presence.ldif Legacy. Schema for instant messaging presence
(online) information; the file lists the default
object classes with the allowed attributes that
must be added to a user's entry in order for
instant-messaging presence information to be
available for that user.
4
Page 19
LDIF and Schema Configuration Files
Configuration Filename Purpose
10rfc2307.ldif Schema from RFC 2307, "An Approach for Using
LDAP as a Network Information Service." This
may be superseded by 10rfc2307bis, the new
version of rfc2307, when that schema becomes
available.
20subscriber.ldif Contains new schema elements and the Nortel
subscriber interoperability specification. Also
contains the adminRole and memberOf
attributes and inetAdmin object class,
previously stored in the 50ns-delegated-
admin.ldif file.
25java-object.ldif Schema from RFC 2713, "Schema for
Representing Java® Objects in an LDAP
Directory."
28pilot.ldif Contains pilot directory schema from RFC
1274, which is no longer recommended for
new deployments. Future RFCs which succeed
RFC 1274 may deprecate some or all of
28pilot.ldif attribute types and classes.
30ns-common.ldif Schema that contains objects classes and
attributes common to the Directory Server
Console framework.
50ns-admin.ldif Schema used by Red Hat Administration Server.
50ns-certificate.ldif Schema for Red Hat Certificate Management
System.
50ns-directory.ldif Contains additional configuration schema used
by Directory Server 4.12 and earlier versions
of the directory, which is no longer applicable
to current releases of Directory Server. This
schema is required for replicating between
Directory Server 4.12 and current releases.
50ns-mail.ldif Schema used by Netscape Messaging Server to
define mail users and mail groups.
50ns-value.ldif Schema for servers' value item attributes.
50ns-web.ldif Schema for Netscape Web Server.
60pam-plugin.ldif Reserved for future use.
99user.ldif User-defined schema maintained by Directory
Server replication consumers which contains the
attributes and object classes from the suppliers.
Table 2.1. Directory Server LDIF Configuration Files
5
Page 20
Chapter 2. Core Server Configuration Reference
2.1.2. How the Server Configuration Is Organized
The dse.ldif file contains all configuration information including directory-specific entries created
by the directory at server startup, such as entries related to the database. The file includes the root
Directory Server entry (or DSE, named by "") and the contents of cn=config and cn=monitor.
When the server generates the dse.ldif file, it lists the entries in hierarchical order in the order that
the entries appear in the directory under cn=config, which is usually the same order in which an
LDAP search of subtree scope for base cn=config returns the entries.
dse.ldif also contains the cn=monitor entry, which is mostly read-only, but can have ACIs set on
it.
NOTE
The dse.ldif file does not contain every attribute in cn=config. If the attribute has
not been set by the administrator and has a default value, the server will not write it to
dse.ldif. To see every attribute in cn=config, use ldapsearch.
2.1.2.1. Configuration Attributes
Within a configuration entry, each attribute is represented as an attribute name. The value of the
attribute corresponds to the attribute's configuration.
The following code sample is an example of part of the dse.ldif file for a Directory Server. The
example shows, among other things, that schema checking has been enabled; this is represented by
the attribute nsslapd-schemacheck, which takes the value on.
dn: cn=config
objectclass: top
objectclass: extensibleObject
objectclass: nsslapdConfig
nsslapd-accesslog-logging-enabled: on
nsslapd-enquote-sup-oc: off
nsslapd-localhost: phonebook.example.com
nsslapd-schemacheck: on
nsslapd-port: 389
nsslapd-localuser: nobody
...
2.1.2.2. Configuration of Plug-in Functionality
The configuration for each part of Directory Server plug-in functionality has its own separate entry
and set of attributes under the subtree cn=plugins,cn=config. The following code sample is an
example of the configuration entry for an example plug-in, the Telephone Syntax plug-in.
dn: cn=Telephone Syntax,cn=plugins,cn=config
objectclass: top
objectclass: nsSlapdPlugin
objectclass: extensibleObject
cn: Telephone Syntax
nsslapd-pluginType: syntax
nsslapd-pluginEnabled: on
6
Page 21

Accessing and Modifying Server Configuration
Some of these attributes are common to all plug-ins, and some may be particular to a specific plug-in.
Check which attributes are currently being used by a given plug-in by performing an ldapsearch on
the cn=config subtree.
For a list of plug-ins supported by Directory Server, general plug-in configuration information, the plugin configuration attribute reference, and a list of plug-ins requiring restart for configuration changes,
see Chapter 3, Plug-in Implemented Server Functionality Reference.
2.1.2.3. Configuration of Databases
The o=NetscapeRoot and cn=UserRoot subtrees under the database plug-in entry contain
configuration data for the databases containing the o=NetscapeRoot suffix and the default suffix
created during setup, such as dc=example,dc=com.
These entries and their children have many attributes used to configure different database settings,
like the cache sizes, the paths to the index files and transaction logs, entries and attributes for
monitoring and statistics; and database indexes.
2.1.2.4. Configuration of Indexes
Configuration information for indexing is stored as entries in the Directory Server under the following
information-tree nodes:
• cn=index,o=NetscapeRoot,cn=ldbm database,cn=plugins,cn=config
• cn=index,cn=UserRoot,cn=ldbm database,cn=plugins,cn=config
• cn=default indexes,cn=config,cn=ldbm database,cn=plugins,cn=config
For more information about indexes in general, see the Directory Server Administrator's Guide. For
information about the index configuration attributes, see Section 3.4.1, “Database Attributes under
cn=config, cn=ldbm database, cn=plugins, cn=config”.
2.2. Accessing and Modifying Server Configuration
This section discusses access control for configuration entries and describes the various ways in
which the server configuration can be viewed and modified. It also covers restrictions to the kinds
of modification that can be made and discusses attributes that require the server to be restarted for
changes to take effect.
2.2.1. Access Control for Configuration Entries
When the Directory Server is installed, a default set of access control instructions (ACIs) is
implemented for all entries under cn=config. The following code sample is an example of these
default ACIs.
aci: (targetattr = "*")(version 3.0; acl "Configuration Administrators Group"; allow (all)
groupdn = "ldap:///cn=Configuration Administrators,u=Groups, ou=TopologyManagement,
o=NetscapeRoot";)
aci: (targetattr = "*")(version 3.0; acl "Configuration Administrator"; allow (all)
userdn = "ldap:///uid=admin, ou=Administrators, ou=TopologyManagement, o=NetscapeRoot";)
aci: (targetattr = "*")(version 3.0; acl "Local Directory Administrators Group"; allow (all)
groupdn = "ldap:///ou=Directory Administrators, dc=example,dc=com";)
7
Page 22

Chapter 2. Core Server Configuration Reference
aci: (targetattr = "*")(version 3.0; acl "SIE Group"; allow(all)
groupdn = "ldap:///cn=slapd-phonebook, cn=Red Hat Directory Server,
cn=Server Group, cn=phonebook.example.com, dc=example,dc=com, o=NetscapeRoot";)
These default ACIs allow all LDAP operations to be carried out on all configuration attributes by the
following users:
• Members of the Configuration Administrators group.
• The user acting as the administrator, the admin account that was configured at setup. By default,
this is the same user account which is logged into the Console.
• Members of local Directory Administrators group.
• The SIE (Server Instance Entry) group, usually assigned using the Set Access Permissions
process the main console.
For more information on access control, see the Directory Server Administrator's Guide.
2.2.2. Changing Configuration Attributes
Server attributes can be viewed and changed in one of three ways: through the Directory Server
Console, by performing ldapsearch and ldapmodify commands, or by manually editing the
dse.ldif file.
NOTE
Before editing the dse.ldif file, the server must be stopped; otherwise, the
changes are lost. Editing the dse.ldif file is recommended only for changes to
attributes which cannot be altered dynamically. See Section 2.2.2.3, “Configuration
Changes Requiring Server Restart” for further information.
The following sections describe how to modify entries using LDAP (both by using Directory Server
Console and by using the command line), the restrictions that apply to modifying entries, the
restrictions that apply to modifying attributes, and the configuration changes requiring restart.
2.2.2.1. Modifying Configuration Entries Using LDAP
The configuration entries in the directory can be searched and modified using LDAP either via the
Directory Server Console or by performing ldapsearch and ldapmodify operations in the same
way as other directory entries. The advantage of using LDAP to modify entries is changes can be
made while the server is running.
For further information, see the "Creating Directory Entries" chapter in the Directory Server
Administrator's Guide. However, certain changes do require the server to be restarted before they are
taken into account. See Section 2.2.2.3, “Configuration Changes Requiring Server Restart” for further
information.
NOTE
As with any set of configuration files, care should be taken when changing or deleting
nodes in the cn=config subtree as this risks affecting Directory Server functionality.
8
Page 23

Changing Configuration Attributes
The entire configuration, including attributes that always take default values, can be viewed by
performing an ldapsearch operation on the cn=config subtree:
ldapsearch -b cn=config -D bindDN -w password
• bindDN is the DN chosen for the Directory Manager when the server was installed (cn=Directory
Manager by default).
• password is the password chosen for the Directory Manager.
For more information on using ldapsearch, see Section 6.4, “ldapsearch”.
To disable a plug-in, use ldapmodify to edit the nsslapd-pluginEnabled attribute:
ldapmodify -D cn="directory manager" -w password
dn: cn=Telephone Syntax,cn=plugins,cn=config
changetype: modify
replace: nsslapd-pluginEnabled
nsslapd-pluginEnabled: off
2.2.2.2. Restrictions to Modifying Configuration Entries and Attributes
Certain restrictions apply when modifying server entries and attributes:
• The cn=monitor entry and its child entries are read-only and cannot be modified, except to
manage ACIs.
• If an attribute is added to cn=config, the server ignores it.
• If an invalid value is entered for an attribute, the server ignores it.
• Because ldapdelete is used for deleting an entire entry, use ldapmodify to remove an attribute
from an entry.
2.2.2.3. Configuration Changes Requiring Server Restart
Some configuration attributes cannot be altered while the server is running. In these cases, for the
changes to take effect, the server needs to be shut down and restarted. The modifications should
be made either through the Directory Server Console or by manually editing the dse.ldif file.
Some of the attributes that require a server restart for any changes to take effect are listed below.
This list is not exhaustive; to see a complete list, run ldapsearch and search for the nsslapd-
requiresrestart attribute. For example:
ldapsearch -p 389 -D "cn=directory manager" -w password -s sub -b "cn=config"
"(objectclass=*)" | grep nsslapd-requiresrestart
nsslapd-cachesize nsslapd-certdir
nsslapd-dbcachesize nsslapd-dbncache
nsslapd-plugin nsslapd-changelogdir
nsslapd-changelogmaxage nsslapd-changelogmaxentries
nsslapd-port nsslapd-schemadir
nsslapd-saslpath nsslapd-secureport
9
Page 24
Chapter 2. Core Server Configuration Reference
nsslapd-tmpdir nsSSL2
nsSSL3 nsSSLclientauth
nsSSLSessionTimeout nsslapd-conntablesize
nsslapd-lockdir nsslapd-maxdescriptors
nsslapd-reservedescriptors nsslapd-listenhost
nsslapd-schema-ignore-trailing-spaces nsslapd-securelistenhost
nsslapd-workingdir nsslapd-return-exact-case
nsslapd-maxbersize
2.3. Core Server Configuration Attributes Reference
This section contains reference information on the configuration attributes that are relevant to the core
server functionality. For information on changing server configuration, see Section 2.2, “Accessing
and Modifying Server Configuration”. For a list of server features that are implemented as plug-ins,
see Section 3.1, “Server Plug-in Functionality Reference”. For help with implementing custom server
functionality, contact Directory Server support.
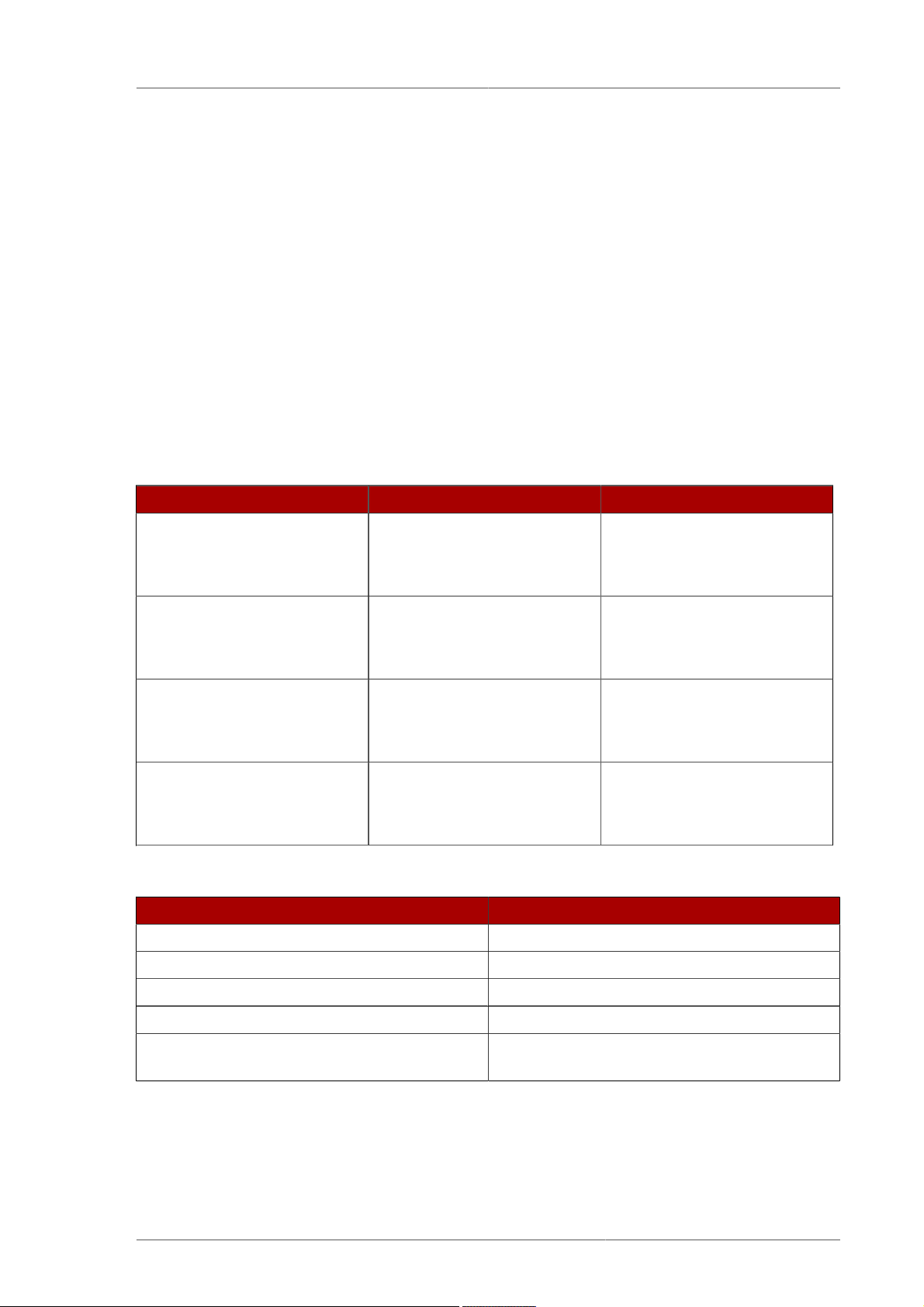
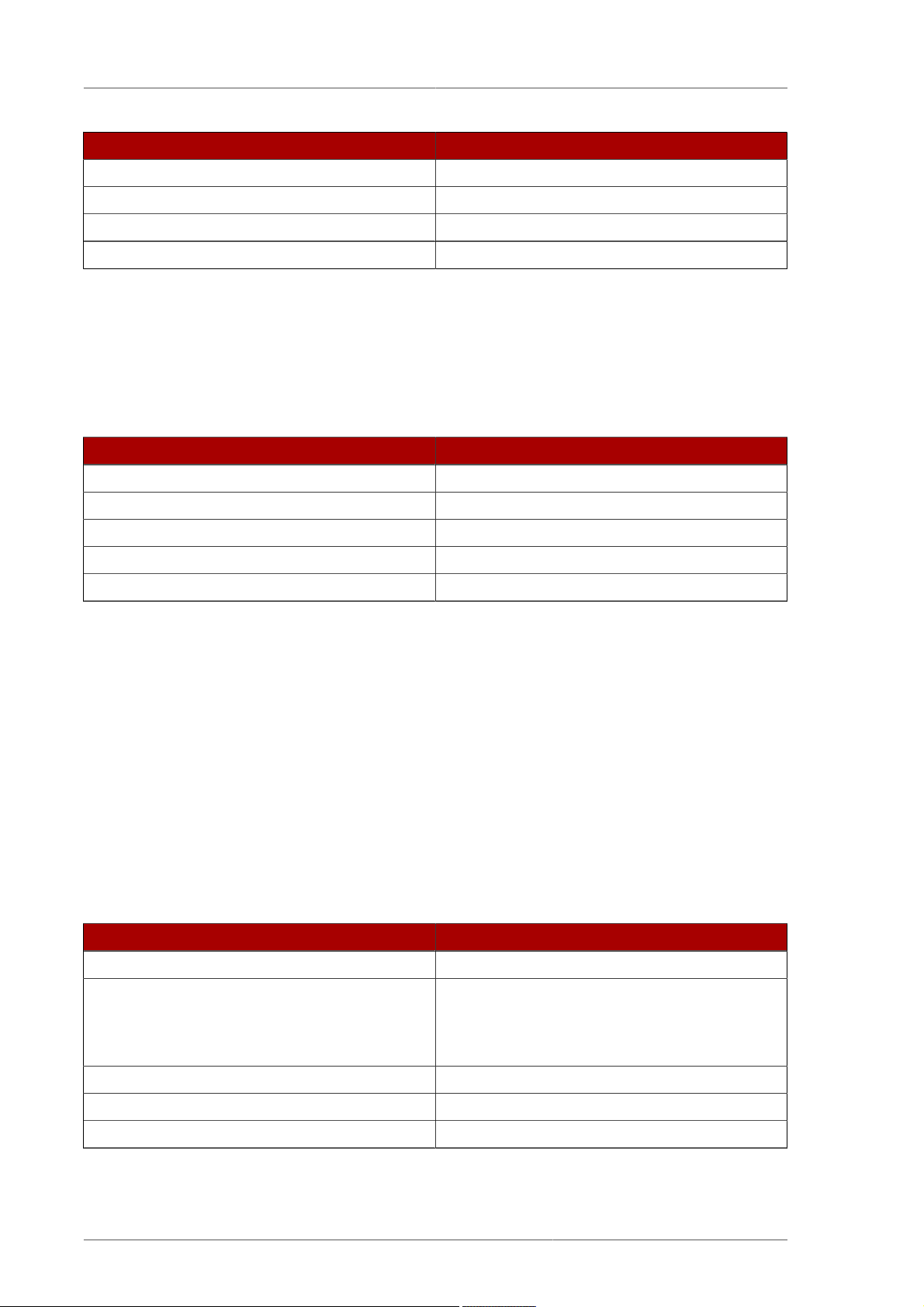
The configuration information stored in the dse.ldif file is organized as an information tree under
the general configuration entry cn=config, as shown in the following diagram.
Figure 2.2. Directory Information Tree Showing Configuration Data
Most of these configuration tree nodes are covered in the following sections.
The cn=plugins node is covered in Chapter 3, Plug-in Implemented Server Functionality Reference.
The description of each attribute contains details such as the DN of its directory entry, its default value,
the valid range of values, and an example of its use.
NOTE
Some of the entries and attributes described in this chapter may change in future
releases of the product.
2.3.1. cn=config
General configuration entries are stored in the cn=config entry. The cn=config entry is an instance
of the nsslapdConfig object class, which in turn inherits from extensibleObject object class.
10
Page 25
cn=config
2.3.1.1. nsslapd-accesslog (Access Log)
This attribute specifies the path and filename of the log used to record each LDAP access. The
following information is recorded by default in the log file:
• IP address of the client machine that accessed the database.
• Operations performed (for example, search, add, and modify).
• Result of the access (for example, the number of entries returned or an error code).
For more information on turning access logging off, see the "Monitoring Server and Database Activity"
chapter in the Directory Server Administrator's Guide.
For access logging to be enabled, this attribute must have a valid path and parameter, and the
nsslapd-accesslog-logging-enabled configuration attribute must be switched to on. The table
lists the four possible combinations of values for these two configuration attributes and their outcome
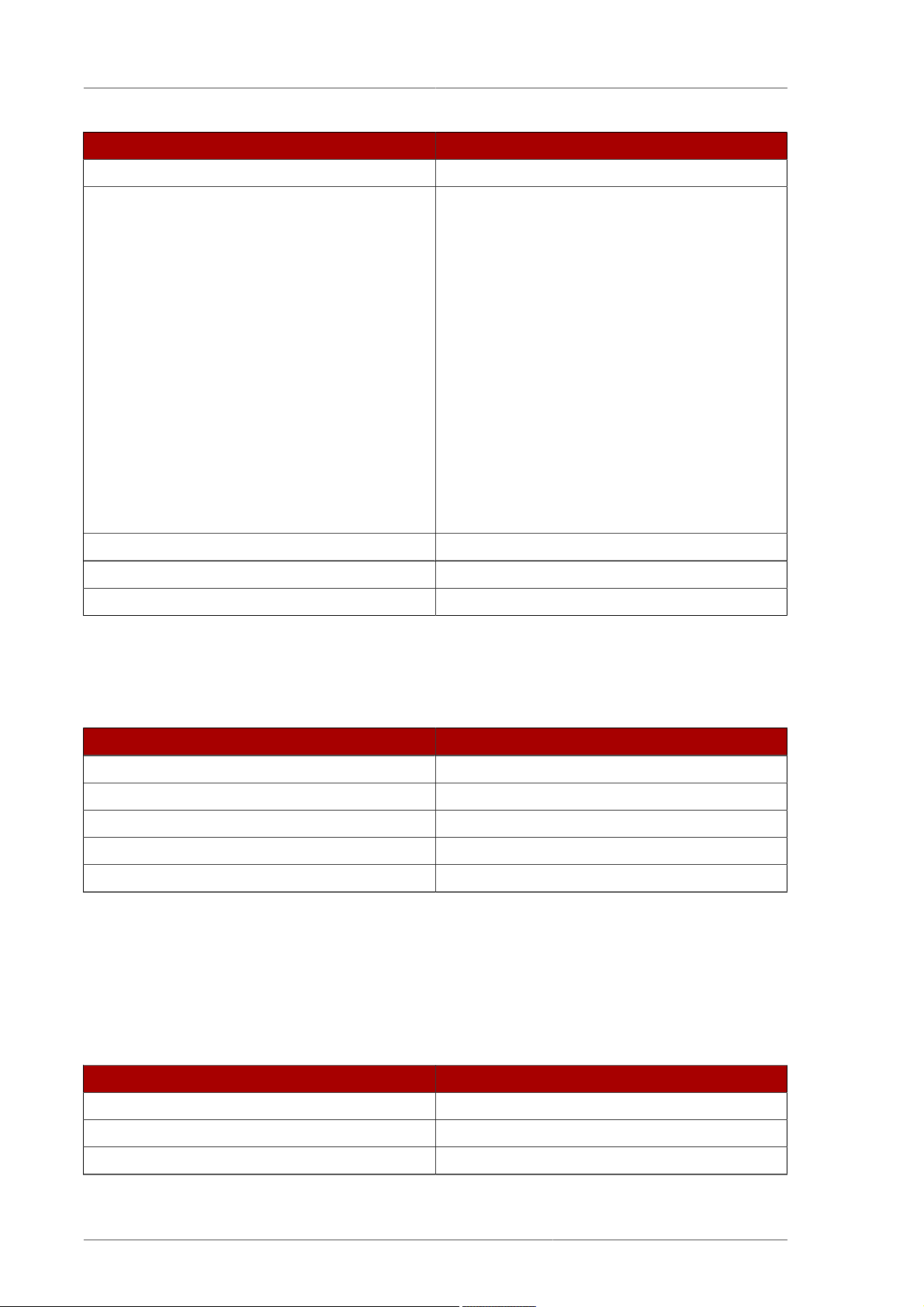
in terms of disabling or enabling of access logging.
Attribute Value Logging enabled or disabled
nsslapd-accesslog-loggingenabled
nsslapd-accesslog
nsslapd-accesslog-loggingenabled
nsslapd-accesslog
nsslapd-accesslog-loggingenabled
nsslapd-accesslog
nsslapd-accesslog-loggingenabled
nsslapd-accesslog
Table 2.2. dse.ldif File Attributes
Parameter Description
Entry DN cn=config
Valid Values Any valid filename.
on
empty string
on
filename
off
empty string
off
filename
Disabled
Enabled
Disabled
Disabled
Default Value /var/log/dirsrv/slapd-instance_name/access
Syntax DirectoryString
Example nsslapd-accesslog: /var/log/dirsrv/
slapd-instance_name/access
2.3.1.2. nsslapd-accesslog-level (Access Log Level)
This attribute controls what is logged to the access log.
11
Page 26
Chapter 2. Core Server Configuration Reference
Parameter Description
Entry DN cn=config
Valid Values • 0 - No access logging
• 4 - Logging for internal access operations
• 256 - Logging for connections, operations, and
results
• 512 - Logging for access to an entry and
referrals
• 131072 - Provides microsecond operation
timing
• These values can be added together to
provide the exact type of logging required;
for example, 516 (4 + 512) to obtain internal
access operation, entry access, and referral
logging.
Default Value 256
Syntax Integer
Example nsslapd-accesslog-level: 256
2.3.1.3. nsslapd-accesslog-list (List of Access Log Files)
This read-only attribute, which cannot be set, provides a list of access log files used in access log
rotation.
Parameter Description
Entry DN cn=config
Valid Values
Default Value None
Syntax DirectoryString
Example nsslapd-accesslog-list: accesslog2,accesslog3
2.3.1.4. nsslapd-accesslog-logbuffering (Log Buffering)
When set to off, the server writes all access log entries directly to disk. Buffering allows the server
to use access logging even when under a heavy load without impacting performance. However, when
debugging, it is sometimes useful to disable buffering in order to see the operations and their results
right away instead of having to wait for the log entries to be flushed to the file. Disabling log buffering
can severely impact performance in heavily loaded servers.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
12
Page 27

cn=config
Parameter Description
Syntax DirectoryString
Example nsslapd-accesslog-logbuffering: off
2.3.1.5. nsslapd-accesslog-logexpirationtime (Access Log Expiration Time)
This attribute specifies the maximum age that a log file is allowed to reach before it is deleted. This
attribute supplies only the number of units. The units are provided by the nsslapd-accesslog-
logexpirationtimeunit attribute.
Parameter Description
Entry DN cn=config
Valid Range -1 to the maximum 32 bit integer value
(2147483647)
A value of -1 or 0 means that the log never
expires.
Default Value -1
Syntax Integer
Example nsslapd-accesslog-logexpirationtime: 2
2.3.1.6. nsslapd-accesslog-logexpirationtimeunit (Access Log Expiration Time Unit)
This attribute specifies the units for nsslapd-accesslog-logexpirationtime attribute. If the unit
is unknown by the server, then the log never expires.
Parameter Description
Entry DN cn=config
Valid Values month | week | day
Default Value month
Syntax DirectoryString
Example nsslapd-accesslog-logexpirationtimeunit: week
2.3.1.7. nsslapd-accesslog-logging-enabled (Access Log Enable Logging)
Disables and enables accesslog logging but only in conjunction with the nsslapd-accesslog
attribute that specifies the path and parameter of the log used to record each database access.
For access logging to be enabled, this attribute must be switched to on, and the nsslapd-
accesslog configuration attribute must have a valid path and parameter. The table lists the four
possible combinations of values for these two configuration attributes and their outcome in terms of
disabling or enabling of access logging.
13
Page 28
Chapter 2. Core Server Configuration Reference
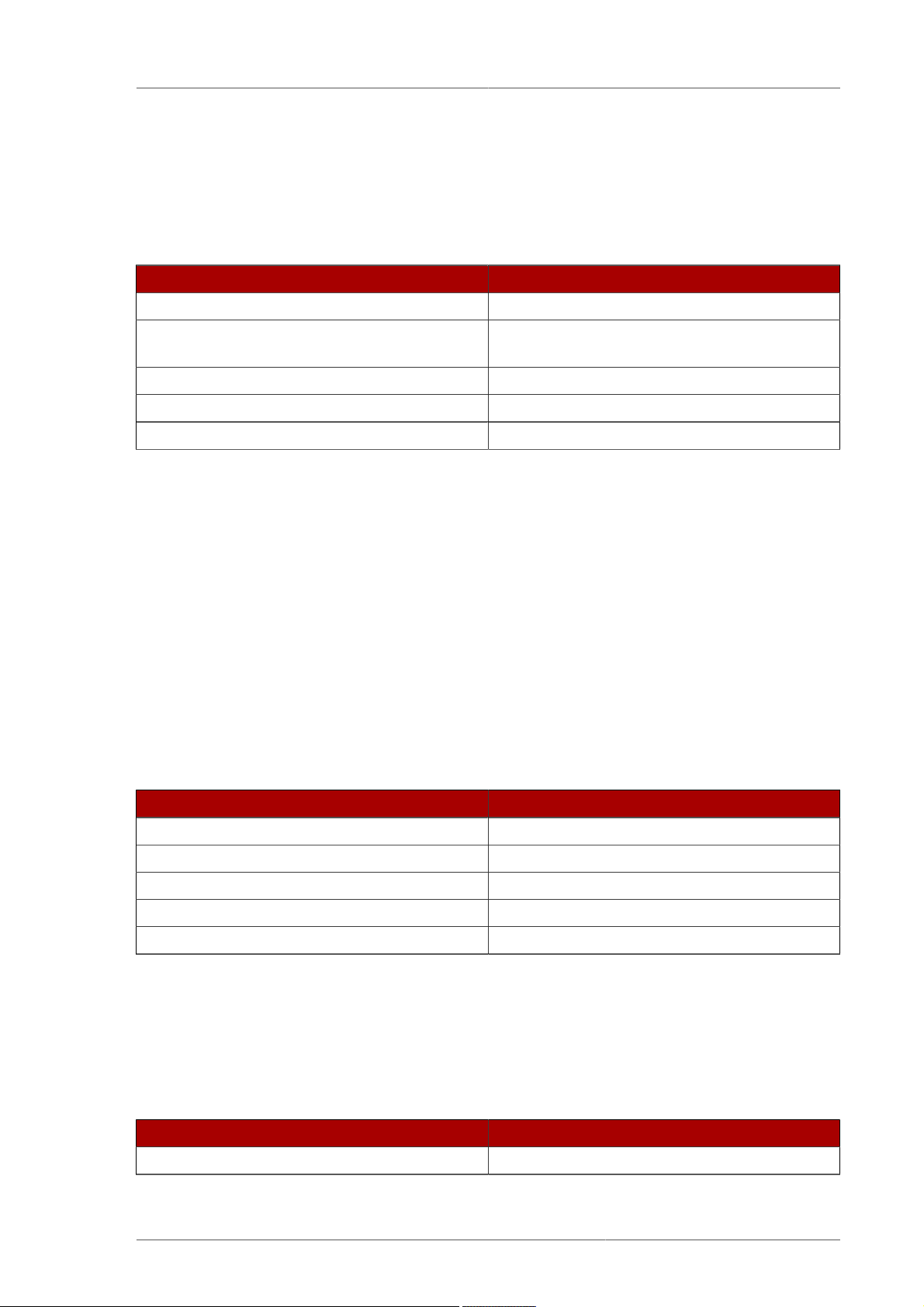
Attribute Value Logging Enabled or Disabled
nsslapd-accesslog-loggingenabled
nsslapd-accesslog
nsslapd-accesslog-loggingenabled
nsslapd-accesslog
nsslapd-accesslog-loggingenabled
nsslapd-accesslog
nsslapd-accesslog-loggingenabled
nsslapd-accesslog
Table 2.3. dse.ldif Attributes
Parameter Description
Entry DN cn=config
Valid Values on | off
on
empty string
on
filename
off
empty string
off
filename
Disabled
Enabled
Disabled
Disabled
Default Value on
Syntax DirectoryString
Example nsslapd-accesslog-logging-enabled: off
2.3.1.8. nsslapd-accesslog-logmaxdiskspace (Access Log Maximum Disk Space)
This attribute specifies the maximum amount of disk space in megabytes that the access logs are
allowed to consume. If this value is exceeded, the oldest access log is deleted.
When setting a maximum disk space, consider the total number of log files that can be created due
to log file rotation. Also, remember that there are three different log files (access log, audit log, and
error log) maintained by the Directory Server, each of which consumes disk space. Compare these
considerations to the total amount of disk space for the access log.
Parameter Description
Entry DN cn=config
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647), where a value of -1 means that
the disk space allowed to the access log is
unlimited in size.
Default Value -1
Syntax Integer
Example nsslapd-accesslog-logmaxdiskspace: 100000
14
Page 29
cn=config
2.3.1.9. nsslapd-accesslog-logminfreediskspace (Access Log Minimum Free Disk Space)
This attribute sets the minimum allowed free disk space in megabytes. When the amount of free disk
space falls below the value specified on this attribute, the oldest access logs are deleted until enough
disk space is freed to satisfy this attribute.
Parameter Description
Entry DN cn=config
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647)
Default Value -1
Syntax Integer
Example nsslapd-accesslog-logminfreediskspace: -1
2.3.1.10. nsslapd-accesslog-logrotationsync-enabled (Access Log Rotation Sync Enabled)
This attribute sets whether access log rotation is to be synchronized with a particular time of the day.
Synchronizing log rotation this way can generate log files at a specified time during a day, such as
midnight to midnight every day. This makes analysis of the log files much easier because they then
map directly to the calendar.
For access log rotation to be synchronized with time-of-day, this attribute must be enabled
with the nsslapd-accesslog-logrotationsynchour and nsslapd-accesslog-
logrotationsyncmin attribute values set to the hour and minute of the day for rotating log files.
For example, to rotate access log files every day at midnight, enable this attribute by setting its
value to on, and then set the values of the nsslapd-accesslog-logrotationsynchour and
nsslapd-accesslog-logrotationsyncmin attributes to 0.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-accesslog-logrotationsync-enabled: on
2.3.1.11. nsslapd-accesslog-logrotationsynchour (Access Log Rotation Sync Hour)
This attribute sets the hour of the day for rotating access logs. This attribute must be used in
conjunction with nsslapd-accesslog-logrotationsync-enabled and nsslapd-accesslog-
logrotationsyncmin attributes.
Parameter Description
Entry DN cn=config
15
Page 30
Chapter 2. Core Server Configuration Reference
Parameter Description
Valid Range 0 through 23
Default Value 0
Syntax Integer
Example nsslapd-accesslog-logrotationsynchour: 23
2.3.1.12. nsslapd-accesslog-logrotationsyncmin (Access Log Rotation Sync Minute)
This attribute sets the minute of the day for rotating access logs. This attribute must be used in
conjunction with nsslapd-accesslog-logrotationsync-enabled and nsslapd-accesslog-
logrotationsynchour attributes.
Parameter Description
Entry DN cn=config
Valid Range 0 through 59
Default Value 0
Syntax Integer
Example nsslapd-accesslog-logrotationsyncmin: 30
2.3.1.13. nsslapd-accesslog-logrotationtime (Access Log Rotation Time)
This attribute sets the time between access log file rotations. The access log is rotated when this
time interval is up, regardless of the current size of the access log. This attribute supplies only the
number of units. The units (day, week, month, and so forth) are given by the nsslapd-accesslog-
logrotationtimeunit attribute.
Although it is not recommended for performance reasons to specify no log rotation since the log
grows indefinitely, there are two ways of specifying this. Either set the nsslapd-accesslog-
maxlogsperdir attribute value to 1 or set the nsslapd-accesslog-logrotationtime
attribute to -1. The server checks the nsslapd-accesslog-maxlogsperdir attribute first,
and, if this attribute value is larger than 1, the server then checks the nsslapd-accesslog-
logrotationtime attribute. See Section 2.3.1.16, “nsslapd-accesslog-maxlogsperdir (Access Log
Maximum Number of Log Files)” for more information.
Parameter Description
Entry DN cn=config
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647), where a value of -1 means that
the time between access log file rotation is
unlimited.
Default Value 1
Syntax Integer
Example nsslapd-accesslog-logrotationtime: 100
16
Page 31

cn=config
2.3.1.14. nsslapd-accesslog-logrotationtimeunit (Access Log Rotation Time Unit)
This attribute sets the units for the nsslapd-accesslog-logrotationtime attribute.
Parameter Description
Entry DN cn=config
Valid Values month | week | day | hour | minute
Default Value day
Syntax DirectoryString
Example nsslapd-accesslog-logrotationtimeunit: week
2.3.1.15. nsslapd-accesslog-maxlogsize (Access Log Maximum Log Size)
This attribute sets the maximum access log size in megabytes. When this value is reached, the access
log is rotated. That means the server starts writing log information to a new log file. If the nsslapd-
accesslog-maxlogsperdir attribute is set to 1, the server ignores this attribute.
When setting a maximum log size, consider the total number of log files that can be created due
to log file rotation. Also, remember that there are three different log files (access log, audit log, and
error log) maintained by the Directory Server, each of which consumes disk space. Compare these
considerations to the total amount of disk space for the access log.
Parameter Description
Entry DN cn=config
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647), where a value of -1 means the
log file is unlimited in size.
Default Value 100
Syntax Integer
Example nsslapd-accesslog-maxlogsize: 100
2.3.1.16. nsslapd-accesslog-maxlogsperdir (Access Log Maximum Number of Log Files)
This attribute sets the total number of access logs that can be contained in the directory where the
access log is stored. Each time the access log is rotated, a new log file is created. When the number
of files contained in the access log directory exceeds the value stored in this attribute, then the oldest
version of the log file is deleted. For performance reasons, Red Hat recommends not setting this value
to 1 because the server does not rotate the log, and it grows indefinitely.
If the value for this attribute is higher than 1, then check the nsslapd-accesslog-
logrotationtime attribute to establish whether log rotation is specified. If the nsslapdaccesslog-logrotationtime attribute has a value of -1, then there is no log rotation. See
Section 2.3.1.13, “nsslapd-accesslog-logrotationtime (Access Log Rotation Time)” for more
information.
17
Page 32

Chapter 2. Core Server Configuration Reference
Parameter Description
Entry DN cn=config
Valid Range 1 to the maximum 32 bit integer value
(2147483647)
Default Value 10
Syntax Integer
Example nsslapd-accesslog-maxlogsperdir: 10
2.3.1.17. nsslapd-accesslog-mode (Access Log File Permission)
This attribute sets the access mode or file permission with which access log files are to be created.
The valid values are any combination of 000 to 777 (these mirror the numbered or absolute UNIX file
permissions). The value must be a 3-digit number, the digits varying from 0 through 7:
• 0 - None
• 1 - Execute only
• 2 - Write only
• 3 - Write and execute
• 4 - Read only
• 5 - Read and execute
• 6 - Read and write
• 7 - Read, write, and execute
In the 3-digit number, the first digit represents the owner's permissions, the second digit represents the
group's permissions, and the third digit represents everyone's permissions. When changing the default
value, remember that 000 does not allow access to the logs and that allowing write permissions to
everyone can result in the logs being overwritten or deleted by anyone.
The newly configured access mode only affects new logs that are created; the mode is set when the
log rotates to a new file.
Parameter Description
Entry DN cn=config
Valid Range 000 through 777
Default Value 600
Syntax Integer
Example nsslapd-accesslog-mode: 600
2.3.1.18. nsslapd-allow-unauthenticated-binds
An unauthenticated bind is a bind where the user supplies a username but not a password. For
example, running an ldapsearch without supplying a password option:
18
Page 33

cn=config
/usr/lib/mozldap/ldapsearch -D "cn=directory manager" -b "dc=example,dc=com" -s sub
"(objectclass=*)"
When unauthenticated binds are allowed, the bind attempt goes through as an anonymous bind
(assuming anonymous access is allowed).
The nsslapd-allow-unauthenticated-binds attribute sets whether to allow an unauthenticated
bind to succeed as an anonymous bind. By default, unauthenticated binds are disabled.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-allow-unauthenticated-binds: on
2.3.1.19. nsslapd-attribute-name-exceptions
This attribute allows non-standard characters in attribute names to be used for backwards
compatibility with older servers, such as "_" in schema-defined attributes.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-attribute-name-exceptions: on
2.3.1.20. nsslapd-auditlog (Audit Log)
This attribute sets the path and filename of the log used to record changes made to each database.
Parameter Description
Entry DN cn=config
Valid Values Any valid filename
Default Value /var/log/dirsrv/slapd-instance_name/audit
Syntax DirectoryString
Example nsslapd-auditlog: /var/log/dirsrv/
slapd-instance_name/audit
For audit logging to be enabled, this attribute must have a valid path and parameter, and the
nsslapd-auditlog-logging-enabled configuration attribute must be switched to on. The table
lists the four possible combinations of values for these two configuration attributes and their outcome
in terms of disabling or enabling of audit logging.
19
Page 34

Chapter 2. Core Server Configuration Reference
Attributes in dse.ldif Value Logging enabled or disabled
nsslapd-auditlog-loggingenabled
nsslapd-auditlog
nsslapd-auditlog-loggingenabled
nsslapd-auditlog
nsslapd-auditlog-loggingenabled
nsslapd-auditlog
nsslapd-auditlog-loggingenabled
nsslapd-auditlog
Table 2.4. Possible Combinations for nsslapd-auditlog
on
empty string
on
filename
off
empty string
off
filename
2.3.1.21. nsslapd-auditlog-list
Provides a list of audit log files.
Disabled
Enabled
Disabled
Disabled
Parameter Description
Entry DN cn=config
Valid Values
Default Value None
Syntax DirectoryString
Example nsslapd-auditlog-list: auditlog2,auditlog3
2.3.1.22. nsslapd-auditlog-logexpirationtime (Audit Log Expiration Time)
This attribute sets the maximum age that a log file is allowed to be before it is deleted. This attribute
supplies only the number of units. The units (day, week, month, and so forth) are given by the
nsslapd-auditlog-logexpirationtimeunit attribute.
Parameter Description
Entry DN cn=config
Valid Range -1 to the maximum 32 bit integer value
(2147483647)
A value of -1 or 0 means that the log never
expires.
Default Value -1
Syntax Integer
Example nsslapd-auditlog-logexpirationtime: 1
20
Page 35

cn=config
2.3.1.23. nsslapd-auditlog-logexpirationtimeunit (Audit Log Expiration Time Unit)
This attribute sets the units for the nsslapd-auditlog-logexpirationtime attribute. If the unit is
unknown by the server, then the log never expires.
Parameter Description
Entry DN cn=config
Valid Values month | week | day
Default Value week
Syntax DirectoryString
Example nsslapd-auditlog-logexpirationtimeunit: day
2.3.1.24. nsslapd-auditlog-logging-enabled (Audit Log Enable Logging)
Turns audit logging on and off.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-auditlog-logging-enabled: off
For audit logging to be enabled, this attribute must have a valid path and parameter and the
nsslapd-auditlog-logging-enabled configuration attribute must be switched to on. The table
lists the four possible combinations of values for these two configuration attributes and their outcome
in terms of disabling or enabling of audit logging.
Attribute Value Logging enabled or disabled
nsslapd-auditlog-loggingenabled
nsslapd-auditlog
nsslapd-auditlog-loggingenabled
nsslapd-auditlog
on
empty string
on
filename
Disabled
Enabled
nsslapd-auditlog-loggingenabled
nsslapd-auditlog
nsslapd-auditlog-loggingenabled
nsslapd-auditlog
Table 2.5. Possible combinations for nsslapd-auditlog and nsslapd-auditlog-logging-enabled
off
empty string
off
filename
Disabled
Disabled
21
Page 36

Chapter 2. Core Server Configuration Reference
2.3.1.25. nsslapd-auditlog-logmaxdiskspace (Audit Log Maximum Disk Space)
This attribute sets the maximum amount of disk space in megabytes that the audit logs are allowed to
consume. If this value is exceeded, the oldest audit log is deleted.
When setting a maximum disk space, consider the total number of log files that can be created due
to log file rotation. Also remember that there are three different log files (access log, audit log, and
error log) maintained by the Directory Server, each of which consumes disk space. Compare these
considerations with the total amount of disk space for the audit log.
Parameter Description
Entry DN cn=config
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647), where a value of -1 means
that the disk space allowed to the audit log is
unlimited in size.
Default Value -1
Syntax Integer
Example nsslapd-auditlog-logmaxdiskspace: 10000
2.3.1.26. nsslapd-auditlog-logminfreediskspace (Audit Log Minimum Free Disk Space)
This attribute sets the minimum permissible free disk space in megabytes. When the amount of free
disk space falls below the value specified by this attribute, the oldest audit logs are deleted until
enough disk space is freed to satisfy this attribute.
Parameter Description
Entry DN cn=config
Valid Range -1 (unlimited) | 1 to the maximum 32 bit integer
value (2147483647)
Default Value -1
Syntax Integer
Example nsslapd-auditlog-logminfreediskspace: -1
2.3.1.27. nsslapd-auditlog-logrotationsync-enabled (Audit Log Rotation Sync Enabled)
This attribute sets whether audit log rotation is to be synchronized with a particular time of the day.
Synchronizing log rotation this way can generate log files at a specified time during a day, such as
midnight to midnight every day. This makes analysis of the log files much easier because they then
map directly to the calendar.
For audit log rotation to be synchronized with time-of-day, this attribute must be enabled with the
nsslapd-auditlog-logrotationsynchour and nsslapd-auditlog-logrotationsyncmin
attribute values set to the hour and minute of the day for rotating log files.
22
Page 37

cn=config
For example, to rotate audit log files every day at midnight, enable this attribute by setting its value to
on, and then set the values of the nsslapd-auditlog-logrotationsynchour and nsslapd-
auditlog-logrotationsyncmin attributes to 0.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-auditlog-logrotationsync-enabled: on
2.3.1.28. nsslapd-auditlog-logrotationsynchour (Audit Log Rotation Sync Hour)
This attribute sets the hour of the day for rotating audit logs. This attribute must be used in
conjunction with nsslapd-auditlog-logrotationsync-enabled and nsslapd-auditlog-
logrotationsyncmin attributes.
Parameter Description
Entry DN cn=config
Valid Range 0 through 23
Default Value None (because nsslapd-auditlog-
logrotationsync-enabled is off)
Syntax Integer
Example nsslapd-auditlog-logrotationsynchour: 23
2.3.1.29. nsslapd-auditlog-logrotationsyncmin (Audit Log Rotation Sync Minute)
This attribute sets the minute of the day for rotating audit logs. This attribute must be used in
conjunction with nsslapd-auditlog-logrotationsync-enabled and nsslapd-auditlog-
logrotationsynchour attributes.
Parameter Description
Entry DN cn=config
Valid Range 0 through 59
Default Value None (because nsslapd-auditlog-
logrotationsync-enabled is off)
Syntax Integer
Example nsslapd-auditlog-logrotationsyncmin: 30
2.3.1.30. nsslapd-auditlog-logrotationtime (Audit Log Rotation Time)
This attribute sets the time between audit log file rotations. The audit log is rotated when this
time interval is up, regardless of the current size of the audit log. This attribute supplies only the
23
Page 38

Chapter 2. Core Server Configuration Reference
number of units. The units (day, week, month, and so forth) are given by the nsslapd-auditloglogrotationtimeunit attribute. If the nsslapd-auditlog-maxlogsperdir attribute is set to 1,
the server ignores this attribute.
Although it is not recommended for performance reasons to specify no log rotation, as the log
grows indefinitely, there are two ways of specifying this. Either set the nsslapd-auditlog-
maxlogsperdir attribute value to 1 or set the nsslapd-auditlog-logrotationtime attribute to
-1. The server checks the nsslapd-auditlog-maxlogsperdir attribute first, and, if this attribute
value is larger than 1, the server then checks the nsslapd-auditlog-logrotationtime attribute.
See Section 2.3.1.33, “nsslapd-auditlog-maxlogsperdir (Audit Log Maximum Number of Log Files)” for
more information.
Parameter Description
Entry DN cn=config
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647), where a value of -1 means
that the time between audit log file rotation is
unlimited.
Default Value 1
Syntax Integer
Example nsslapd-auditlog-logrotationtime: 100
2.3.1.31. nsslapd-auditlog-logrotationtimeunit (Audit Log Rotation Time Unit)
This attribute sets the units for the nsslapd-auditlog-logrotationtime attribute.
Parameter Description
Entry DN cn=config
Valid Values month | week | day | hour | minute
Default Value week
Syntax DirectoryString
Example nsslapd-auditlog-logrotationtimeunit: day
2.3.1.32. nsslapd-auditlog-maxlogsize (Audit Log Maximum Log Size)
This attribute sets the maximum audit log size in megabytes. When this value is reached, the audit
log is rotated. That means the server starts writing log information to a new log file. If nsslapd-
auditlog-maxlogsperdir to 1, the server ignores this attribute.
When setting a maximum log size, consider the total number of log files that can be created due
to log file rotation. Also, remember that there are three different log files (access log, audit log, and
error log) maintained by the Directory Server, each of which consumes disk space. Compare these
considerations to the total amount of disk space for the audit log.
Parameter Description
Entry DN cn=config
24
Page 39

cn=config
Parameter Description
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647), where a value of -1 means the
log file is unlimited in size.
Default Value 100
Syntax Integer
Example nsslapd-auditlog-maxlogsize: 50
2.3.1.33. nsslapd-auditlog-maxlogsperdir (Audit Log Maximum Number of Log Files)
This attribute sets the total number of audit logs that can be contained in the directory where the audit
log is stored. Each time the audit log is rotated, a new log file is created. When the number of files
contained in the audit log directory exceeds the value stored on this attribute, then the oldest version
of the log file is deleted. The default is 1 log. If this default is accepted, the server will not rotate the
log, and it grows indefinitely.
If the value for this attribute is higher than 1, then check the nsslapd-auditlog-
logrotationtime attribute to establish whether log rotation is specified. If the nsslapdauditlog-logrotationtime attribute has a value of -1, then there is no log rotation. See
Section 2.3.1.30, “nsslapd-auditlog-logrotationtime (Audit Log Rotation Time)” for more information.
Parameter Description
Entry DN cn=config
Valid Range 1 to the maximum 32 bit integer value
(2147483647)
Default Value 1
Syntax Integer
Example nsslapd-auditlog-maxlogsperdir: 10
2.3.1.34. nsslapd-auditlog-mode (Audit Log File Permission)
This attribute sets the access mode or file permissions with which audit log files are to be created.
The valid values are any combination of 000 to 777 since they mirror numbered or absolute UNIX file
permissions. The value must be a combination of a 3-digit number, the digits varying from 0 through 7:
• 0 - None
• 1 - Execute only
• 2 - Write only
• 3 - Write and execute
• 4 - Read only
• 5 - Read and execute
• 6 - Read and write
25
Page 40

Chapter 2. Core Server Configuration Reference
• 7 - Read, write, and execute
In the 3-digit number, the first digit represents the owner's permissions, the second digit represents the
group's permissions, and the third digit represents everyone's permissions. When changing the default
value, remember that 000 does not allow access to the logs and that allowing write permissions to
everyone can result in the logs being overwritten or deleted by anyone.
The newly configured access mode only affects new logs that are created; the mode is set when the
log rotates to a new file.
Parameter Description
Entry DN cn=config
Valid Range 000 through 777
Default Value 600
Syntax Integer
Example nsslapd-auditlog-mode: 600
2.3.1.35. nsslapd-certdir (Certificate and Key Database Directory)
This is the full path to the directory holding the certificate and key databases for a Directory Server
instance. This directory must contain only the certificate and key databases for this instance and no
other instances. This directory must be owned and allow read-write access for the server user ID. No
other user should have read-right access to this directory. The default location is the configuration file
directory, /etc/dirsrv/slapd-instance_name.
Changes to this value will not take effect until the server is restarted.
Parameter Description
Entry DN cn=config
Valid Values Absolute path to any directory which is owned by
the server user ID and only allows read and write
access to the server user ID
Default Value /etc/dirsrv/slapd-instance_name
Syntax DirectoryString
Example /etc/dirsrv/slapd-phonebook
2.3.1.36. nsslapd-certmap-basedn (Certificate Map Search Base)
This attribute can be used when client authentication is performed using SSL certificates in order to
avoid limitations of the security subsystem certificate mapping, configured in the certmap.conf
file. Depending on the certmap.conf configuration, the certificate mapping may be done using
a directory subtree search based at the root DN. If the search is based at the root DN, then the
nsslapd-certmap-basedn attribute may force the search to be based at some entry other than the
root. The valid value for this attribute is the DN of the suffix or subtree to use for certificate mapping.
For further information on configuring for SSL, see the "Managing SSL" chapter in the Directory Server
Administrator's Guide.
26
Page 41

2.3.1.37. nsslapd-config
This read-only attribute is the config DN.
Parameter Description
Entry DN cn=config
Valid Values Any valid configuration DN
Default Value
Syntax DirectoryString
Example nsslapd-config: cn=config
2.3.1.38. nsslapd-conntablesize
This attribute sets the connection table size, which determines the total number of connections
supported by the server.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
cn=config
Entry DN cn=config
Valid Values Operating-system dependent
Default Value The default value is the system's max
descriptors, which can be configured using
the Section 2.3.1.77, “nsslapd-maxdescriptors
(Maximum File Descriptors)” attribute.
Syntax Integer
Example nsslapd-conntablesize: 4093
Increase the value of this attribute if Directory Server is refusing connections because it is out of
connection slots. When this occurs, the Directory Server's error log file records the message Not
listening for new connections -- too many fds open.
A server restart is required for the change to take effect.
It may be necessary to increase the operating system limits for the number of open files and number
of open files per process, and it may be necessary to increase the ulimit for the number of open
files (ulimit -n) in the shell that starts the Directory Server. See Section 2.3.1.77, “nsslapd-
maxdescriptors (Maximum File Descriptors)” for more information.
2.3.1.39. nsslapd-counters
The nsslapd-counters attribute enables and disables Directory Server database and server
performance counters.
There can be a performance impact by keeping track of the larger counters. Turning off 64-bit integers
for counters can have a minimal improvement on performance, although it negatively affects long term
statistics tracking.
This parameter is enabled by default. To disable counters, stop the Directory Server, edit the
dse.ldif file directly, and restart the server.
27
Page 42

Chapter 2. Core Server Configuration Reference
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example nsslapd-counters: on
2.3.1.40. nsslapd-csnlogging
This attribute sets whether change sequence numbers (CSNs), when available, are to be logged in the
access log. By default, CSN logging is turned on.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example nsslapd-csnlogging: on
2.3.1.41. nsslapd-ds4-compatible-schema
Makes the schema in cn=schema compatible with 4.x versions of Directory Server.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-ds4-compatible-schema: off
2.3.1.42. nsslapd-enquote-sup-oc (Enable Superior Object Class Enquoting)
This attribute is deprecated and will be removed in a future version of Directory Server.
This attribute controls whether quoting in the objectclass attributes contained in the cn=schema
entry conforms to the quoting specified by Internet draft RFC 2252. By default, the Directory Server
conforms to RFC 2252, which indicates that this value should not be quoted. Only very old clients
need this value set to on, so leave it off.
Turning this attribute on or off does not affect Directory Server Console.
Parameter Description
Entry DN cn=config
Valid Values on | off
28
Page 43

cn=config
Parameter Description
Default Value off
Syntax DirectoryString
Example nsslapd-enquote-sup-oc: off
2.3.1.43. nsslapd-errorlog (Error Log)
This attribute sets the path and filename of the log used to record error messages generated by
the Directory Server. These messages can describe error conditions, but more often they contain
informative conditions, such as:
• Server startup and shutdown times.
• The port number that the server uses.
This log contains differing amounts of information depending on the current setting of the Log Level
attribute. See Section 2.3.1.44, “nsslapd-errorlog-level (Error Log Level)” for more information.
Parameter Description
Entry DN cn=config
Valid Values Any valid filename
Default Value /var/log/dirsrv/slapd-instance_name/errors
Syntax DirectoryString
Example nsslapd-errorlog: /var/log/dirsrv/
slapd-instance_name/errors
For error logging to be enabled, this attribute must have a valid path and filename, and the nsslapd-
errorlog-logging-enabled configuration attribute must be switched to on. The table lists the four
possible combinations of values for these two configuration attributes and their outcome in terms of
disabling or enabling of error logging.
Attributes in dse.ldif Value Logging enabled or disabled
nsslapd-errorlog-loggingenabled
nsslapd-errorlog
nsslapd-errorlog-loggingenabled
nsslapd-errorlog
on
empty string
on
filename
Disabled
Enabled
nsslapd-errorlog-loggingenabled
nsslapd-errorlog
nsslapd-errorlog-loggingenabled
nsslapd-errorlog
Table 2.6. Possible Combinations for nsslapd-errorlog Configuration Attributes
off
empty string
off
filename
Disabled
Disabled
29
Page 44

Chapter 2. Core Server Configuration Reference
2.3.1.44. nsslapd-errorlog-level (Error Log Level)
This attribute sets the level of logging for the Directory Server. The log level is additive; that is,
specifying a value of 3 includes both levels 1 and 2.
The default value for nsslapd-errorlog-level is 16384.
Parameter Description
Entry DN cn=config
Valid Values • 1 — Trace function calls. Logs a message
when the server enters and exits a function.
• 2 — Debug packet handling.
• 4 — Heavy trace output debugging.
• 8 — Connection management.
• 16 — Print out packets sent/received.
• 32 — Search filter processing.
• 64 — Config file processing.
• 128 — Access control list processing.
• 1024 — Log communications with shell
databases.
• 2048 — Log entry parsing debugging.
• 4096 — Housekeeping thread debugging.
• 8192 — Replication debugging.
• 16384 — Default level of logging used for
critical errors and other messages that are
always written to the error log; for example,
server startup messages. Messages at this
level are always included in the error log,
regardless of the log level setting.
• 32768 — Database cache debugging.
• 65536 — Server plug-in debugging. It writes
an entry to the log file when a server plug-in
calls slapi-log-error.
30
• 131072 — Microsecond resolution for
timestamps instead of the default seconds.
• 262144 — Access control summary
information, much less verbose than level
128. This value is recommended for use when
a summary of access control processing is
Page 45

Parameter Description
needed. Use 128 for very detailed processing
messages.
Default Value 16384
Syntax Integer
Example nsslapd-errorlog-level: 8192
2.3.1.45. nsslapd-errorlog-list
This read-only attribute provides a list of error log files.
Parameter Description
Entry DN cn=config
Valid Values
Default Value None
Syntax DirectoryString
cn=config
Example nsslapd-errorlog-list: errorlog2,errorlog3
2.3.1.46. nsslapd-errorlog-logexpirationtime (Error Log Expiration Time)
This attribute sets the maximum age that a log file is allowed to reach before it is deleted. This
attribute supplies only the number of units. The units (day, week, month, and so forth) are given by the
nsslapd-errorlog-logexpirationtimeunit attribute.
Parameter Description
Entry DN cn=config
Valid Range -1 to the maximum 32 bit integer value
(2147483647)
A value of -1 or 0 means that the log never
expires.
Default Value -1
Syntax Integer
Example nsslapd-errorlog-logexpirationtime: 1
2.3.1.47. nsslapd-errorlog-logexpirationtimeunit (Error Log Expiration Time Unit)
This attribute sets the units for the nsslapd-errorlog-logexpirationtime attribute. If the unit is
unknown by the server, then the log never expires.
Parameter Description
Entry DN cn=config
Valid Values month | week | day
Default Value month
31
Page 46

Chapter 2. Core Server Configuration Reference
Parameter Description
Syntax DirectoryString
Example nsslapd-errorlog-logexpirationtimeunit: week
2.3.1.48. nsslapd-errorlog-logging-enabled (Enable Error Logging)
Turns error logging on and off.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example nsslapd-errorlog-logging-enabled: on
2.3.1.49. nsslapd-errorlog-logmaxdiskspace (Error Log Maximum Disk Space)
This attribute sets the maximum amount of disk space in megabytes that the error logs are allowed to
consume. If this value is exceeded, the oldest error log is deleted.
When setting a maximum disk space, consider the total number of log files that can be created due
to log file rotation. Also, remember that there are three different log files (access log, audit log, and
error log) maintained by the Directory Server, each of which consumes disk space. Compare these
considerations to the total amount of disk space for the error log.
Parameter Description
Entry DN cn=config
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647), where a value of -1 means
that the disk space allowed to the error log is
unlimited in size.
Default Value -1
Syntax Integer
Example nsslapd-errorlog-logmaxdiskspace: 10000
2.3.1.50. nsslapd-errorlog-logminfreediskspace (Error Log Minimum Free Disk Space)
This attribute sets the minimum allowed free disk space in megabytes. When the amount of free disk
space falls below the value specified on this attribute, the oldest error log is deleted until enough disk
space is freed to satisfy this attribute.
Parameter Description
Entry DN cn=config
32
Page 47

cn=config
Parameter Description
Valid Range -1 (unlimited) | 1 to the maximum 32 bit integer
value (2147483647)
Default Value -1
Syntax Integer
Example nsslapd-errorlog-logminfreediskspace: -1
2.3.1.51. nsslapd-errorlog-logrotationsync-enabled (Error Log Rotation Sync Enabled)
This attribute sets whether error log rotation is to be synchronized with a particular time of the day.
Synchronizing log rotation this way can generate log files at a specified time during a day, such as
midnight to midnight every day. This makes analysis of the log files much easier because they then
map directly to the calendar.
For error log rotation to be synchronized with time-of-day, this attribute must be enabled with the
nsslapd-errorlog-logrotationsynchour and nsslapd-errorlog-logrotationsyncmin
attribute values set to the hour and minute of the day for rotating log files.
For example, to rotate error log files every day at midnight, enable this attribute by setting its value to
on, and then set the values of the nsslapd-errorlog-logrotationsynchour and nsslapd-
errorlog-logrotationsyncmin attributes to 0.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-errorlog-logrotationsync-enabled: on
2.3.1.52. nsslapd-errorlog-logrotationsynchour (Error Log Rotation Sync Hour)
This attribute sets the hour of the day for rotating error logs. This attribute must be used in
conjunction with nsslapd-errorlog-logrotationsync-enabled and nsslapd-errorlog-
logrotationsyncmin attributes.
Parameter Description
Entry DN cn=config
Valid Range 0 through 23
Default Value 0
Syntax Integer
Example nsslapd-errorlog-logrotationsynchour: 23
33
Page 48

Chapter 2. Core Server Configuration Reference
2.3.1.53. nsslapd-errorlog-logrotationsyncmin (Error Log Rotation Sync Minute)
This attribute sets the minute of the day for rotating error logs. This attribute must be used in
conjunction with nsslapd-errorlog-logrotationsync-enabled and nsslapd-errorlog-
logrotationsynchour attributes.
Parameter Description
Entry DN cn=config
Valid Range 0 through 59
Default Value 0
Syntax Integer
Example nsslapd-errorlog-logrotationsyncmin: 30
2.3.1.54. nsslapd-errorlog-logrotationtime (Error Log Rotation Time)
This attribute sets the time between error log file rotations. The error log is rotated when this
time interval is up, regardless of the current size of the error log. This attribute supplies only the
number of units. The units (day, week, month, and so forth) are given by the nsslapd-errorlog-
logrotationtimeunit (Error Log Rotation Time Unit) attribute.
Although it is not recommended for performance reasons to specify no log rotation, as the log
grows indefinitely, there are two ways of specifying this. Either set the nsslapd-errorlog-
maxlogsperdir attribute value to 1 or set the nsslapd-errorlog-logrotationtime attribute to
-1. The server checks the nsslapd-errorlog-maxlogsperdir attribute first, and, if this attribute
value is larger than 1, the server then checks the nsslapd-errorlog-logrotationtime attribute.
See Section 2.3.1.57, “nsslapd-errorlog-maxlogsperdir (Maximum Number of Error Log Files)” for
more information.
Parameter Description
Entry DN cn=config
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647), where a value of -1 means
that the time between error log file rotation is
unlimited).
Default Value 1
Syntax Integer
Example nsslapd-errorlog-logrotationtime: 100
2.3.1.55. nsslapd-errorlog-logrotationtimeunit (Error Log Rotation Time Unit)
This attribute sets the units for nsslapd-errorlog-logrotationtime (Error Log Rotation Time).
If the unit is unknown by the server, then the log never expires.
Parameter Description
Entry DN cn=config
34
Page 49

cn=config
Parameter Description
Valid Values month | week | day | hour | minute
Default Value week
Syntax DirectoryString
Example nsslapd-errorlog-logrotationtimeunit: day
2.3.1.56. nsslapd-errorlog-maxlogsize (Maximum Error Log Size)
This attribute sets the maximum error log size in megabytes. When this value is reached, the error
log is rotated, and the server starts writing log information to a new log file. If nsslapd-errorlog-
maxlogsperdir is set to 1, the server ignores this attribute.
When setting a maximum log size, consider the total number of log files that can be created due
to log file rotation. Also, remember that there are three different log files (access log, audit log, and
error log) maintained by the Directory Server, each of which consumes disk space. Compare these
considerations to the total amount of disk space for the error log.
Parameter Description
Entry DN cn=config
Valid Range -1 | 1 to the maximum 32 bit integer value
(2147483647) where a value of -1 means the log
file is unlimited in size.
Default Value 100
Syntax Integer
Example nsslapd-errorlog-maxlogsize: 100
2.3.1.57. nsslapd-errorlog-maxlogsperdir (Maximum Number of Error Log Files)
This attribute sets the total number of error logs that can be contained in the directory where the error
log is stored. Each time the error log is rotated, a new log file is created. When the number of files
contained in the error log directory exceeds the value stored on this attribute, then the oldest version
of the log file is deleted. The default is 1 log. If this default is accepted, the server does not rotate the
log, and it grows indefinitely.
If the value for this attribute is higher than 1, then check the nsslapd-errorlog-
logrotationtime attribute to establish whether log rotation is specified. If the nsslapderrorlog-logrotationtime attribute has a value of -1, then there is no log rotation. See
Section 2.3.1.54, “nsslapd-errorlog-logrotationtime (Error Log Rotation Time)” for more information.
Parameter Description
Entry DN cn=config
Valid Range 1 to the maximum 32 bit integer value
(2147483647)
Default Value 1
Syntax Integer
Example nsslapd-errorlog-maxlogsperdir: 10
35
Page 50

Chapter 2. Core Server Configuration Reference
2.3.1.58. nsslapd-errorlog-mode (Error Log File Permission)
This attribute sets the access mode or file permissions with which error log files are to be created.
The valid values are any combination of 000 to 777 since they mirror numbered or absolute UNIX file
permissions. That is, the value must be a combination of a 3-digit number, the digits varying from 0
through 7:
• 0 - None
• 1 - Execute only
• 2 - Write only
• 3 - Write and execute
• 4 - Read only
• 5 - Read and execute
• 6 - Read and write
• 7 - Read, write, and execute
In the 3-digit number, the first digit represents the owner's permissions, the second digit represents the
group's permissions, and the third digit represents everyone's permissions. When changing the default
value, remember that 000 does not allow access to the logs and that allowing write permissions to
everyone can result in the logs being overwritten or deleted by anyone.
The newly configured access mode only affects new logs that are created; the mode is set when the
log rotates to a new file.
Parameter Description
Entry DN cn=config
Valid Range 000 through 777
Default Value 600
Syntax Integer
Example nsslapd-errorlog-mode: 600
2.3.1.59. nsslapd-groupevalnestlevel
This attribute is deprecated, and documented here only for historical purposes.
The Access Control Plug-in does not use the value specified by the nsslapd-
groupevalnestlevel attribute to set the number of levels of nesting that access control performs
for group evaluation. Instead, the number of levels of nesting is hard-coded as 5.
Parameter Description
Entry DN cn=config
Valid Range 0 to 5
Default Value 5
Syntax Integer
36
Page 51

cn=config
Parameter Description
Example nsslapd-groupevalnestlevel: 5
2.3.1.60. nsslapd-idletimeout (Default Idle Timeout)
This attribute sets the amount of time in seconds after which an idle LDAP client connection is closed
by the server. A value of 0 means that the server never closes idle connections. This setting applies
to all connections and all users. Idle timeout is enforced when the connection table is walked, when
poll() does not return zero. Therefore, a server with a single connection never enforces the idle
timeout.
Use the nsIdleTimeout operational attribute, which can be added to user entries, to override the
value assigned to this attribute. For details, see the "Setting Resource Limits Based on the Bind DN"
section in the Directory Server Administrator's Guide.
NOTE
For very large databases, with millions of entries, this attribute must have a high
enough value that the online initialization process can complete or replication will
fail when the connection to the server times out. Alternatively, the nsIdleTimeout
attribute can be set to a high value on the entry used as the supplier bind DN.
Parameter Description
Entry DN cn=config
Valid Range 0 to the maximum 32 bit integer value
(2147483647)
Default Value 0
Syntax Integer
Example nsslapd-idletimeout: 0
2.3.1.61. nsslapd-instancedir (Instance Directory)
This attribute is deprecated. There are now separate configuration parameters for instance-specific
paths, such as nsslapd-certdir and nsslapd-lockdir. See the documentation for the specific
directory path that is set.
2.3.1.62. nsslapd-ioblocktimeout (IO Block Time Out)
This attribute sets the amount of time in milliseconds after which the connection to a stalled LDAP
client is closed. An LDAP client is considered to be stalled when it has not made any I/O progress for
read or write operations.
Parameter Description
Entry DN cn=config
Valid Range 0 to the maximum 32 bit integer value
(2147483647) in ticks
Default Value 1800000
37
Page 52

Chapter 2. Core Server Configuration Reference
Parameter Description
Syntax Integer
Example nsslapd-ioblocktimeout: 1800000
2.3.1.63. nsslapd-lastmod (Track Modification Time)
This attribute sets whether the Directory Server maintains the modification attributes for Directory
Server entries. These are operational attributes. These attributes include:
• modifiersName - The distinguished name of the person who last modified the entry.
• modifyTimestamp - The timestamp, in GMT format, for when the entry was last modified.
• creatorsName - The distinguished name of the person who initially created the entry.
• createTimestamp - The timestamp for when the entry was created in GMT format.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example nsslapd-lastmod: on
WARNING
This attribute should never be turned off. If the nsslapd-lastmod is set to off,
then generating nsUniqueIDs is also disabled, replication does not work, and other
issues may arise.
If for some reason this attribute were set to off, the solution is to export the database
to ldif (db2ldif or db2ldif.pl or from the console), set the value to on, and import
the data. The import process assigns each entry a unique id.
2.3.1.64. nsslapd-ldapiautobind (Enable Autobind)
The nsslapd-ldapiautobind sets whether the server will allow users to autobind to Directory
Server using LDAPI. Autobind maps the UID or GUID number of a system user to a Directory Server
user, and automatically authenticates the user to Directory Server based on those credentials. The
Directory Server connection occurs over UNIX socket.
Along with enabling autobind, configuring autobind requires configuring mapping entries. The
nsslapd-ldapimaprootdn maps a root user on the system to the Directory Manager. The
nsslapd-ldapimaptoentries maps regular users to Directory Server users, based on the
parameters defined in the nsslapd-ldapiuidnumbertype, nsslapd-ldapigidnumbertype,
and nsslapd-ldapientrysearchbase attributes.
Autobind can only be enabled if LDAPI is enabled, meaning the nsslapd-ldapilisten is on and
the nsslapd-ldapifilepath attribute is set to an LDAPI socket.
38
Page 53

cn=config
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-ldapiautobind: off
2.3.1.65. nsslapd-ldapientrysearchbase (Search Base for LDAPI Authentication Entries)
With autobind, it is possible to map system users to Directory Server user entries, based on the
system user's UID and GUID numbers. This requires setting Directory Server parameters for
which attribute to use for the UID number (nsslapd-ldapiuidnumbertype) and GUID number
(nsslapd-ldapigidnumbertype) and setting the search base to use to search for matching user
entries.
The nsslapd-ldapientrysearchbase gives the subtree to search for user entries to use for
autobind.
Parameter Description
Entry DN cn=config
Valid Values DN
Default Value The suffix created when the server instance was
created, such as dc=example,dc=com
Syntax DN
Example nsslapd-ldapientrysearchbase:
ou=people,dc=example,dc=om
2.3.1.66. nsslapd-ldapifilepath (File Location for LDAPI Socket)
LDAPI connects a user to an LDAP server over a UNIX socket rather than TCP. In order to configure
LDAPI, the server must be configured to communicate over a UNIX socket. The UNIX socket to use is
set in the nsslapd-ldapifilepath attribute.
Parameter Description
Entry DN cn=config
Valid Values Any directory path
Default Value /var/run/dirsrv/slapd-example.socket
Syntax Case-exact string
Example nsslapd-ldapifilepath: /var/run/slapd-
example.socket
39
Page 54

Chapter 2. Core Server Configuration Reference
2.3.1.67. nsslapd-ldapigidnumbertype (Attribute Mapping for System GUID Number)
Autobind can be used to authenticate system users to the server automatically and connect to the
server using a UNIX socket. To map the system user to a Directory Server user for authentication,
the system user's UID and GUID numbers should be mapped to be a Directory Server attribute. The
nsslapd-ldapigidnumbertype attribute points to the Directory Server attribute to map system
GUIDs to user entries.
Users can only connect to the server with autobind if LDAPI is enabled (nsslapd-ldapilisten
and nsslapd-ldapifilepath), autobind is enabled (nsslapd-ldapiautobind), and autobind
mapping is enabled for regular users (nsslapd-ldapimaptoentries).
Parameter Description
Entry DN cn=config
Valid Values Any Directory Server attribute
Default Value gidNumber
Syntax DirectoryString
Example nsslapd-ldapigidnumbertype: gidNumber
2.3.1.68. nsslapd-ldapilisten (Enable LDAPI)
The nsslapd-ldapilisten enables LDAPI connections to the Directory Server. LDAPI allows
users to connect to the Directory Server over a UNIX socket rather than a standard TCP port. Along
with enabling LDAPI by setting nsslapd-ldapilisten to on, there must also be a UNIX socket set
for LDAPI in the nsslapd-ldapifilepath attribute.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-ldapilisten: off
2.3.1.69. nsslapd-ldapimaprootdn (Autobind Mapping for Root User)
With autobind, a system user is mapped to a Directory Server user and then automatically
authenticated to the Directory Server over a UNIX socket.
The root system user (the user with a UID of 0) is mapped to whatever Directory Server entry is
specified in the nsslapd-ldapimaprootdn attribute.
Parameter Description
Entry DN cn=config
Valid Values Any DN
Default Value cn=Directory Manager
Syntax DN
40
Page 55

cn=config
Parameter Description
Example nsslapd-ldapimaprootdn: cn=Directory Manager
2.3.1.70. nsslapd-ldapimaptoentries (Enable Autobind Mapping for Regular Users)
With autobind, a system user is mapped to a Directory Server user and then automatically
authenticated to the Directory Server over a UNIX socket. This mapping is automatic for root users,
but it must be enabled for regular system users through the nsslapd-ldapimaptoentries
attribute. Setting this attribute to on enables mapping for regular system users to Directory Server
entries. If this attribute is not enabled, then only root users can use autobind to authenticate to the
Directory Server, and all other users connect anonymously.
The mappings themselves are configured through the nsslapd-ldapiuidnumbertype and
nsslapd-ldapigidnumbertype attributes, which map Directory Server attributes to the user's UID
and GUID numbers.
Users can only connect to the server with autobind if LDAPI is enabled (nsslapd-ldapilisten and
nsslapd-ldapifilepath) and autobind is enabled (nsslapd-ldapiautobind).
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-ldapimaptoentries: on
2.3.1.71. nsslapd-ldapiuidnumbertype
Autobind can be used to authenticate system users to the server automatically and connect to the
server using a UNIX socket. To map the system user to a Directory Server user for authentication,
the system user's UID and GUID numbers must be mapped to be a Directory Server attribute. The
nsslapd-ldapiuidnumbertype attribute points to the Directory Server attribute to map system
UIDs to user entries.
Users can only connect to the server with autobind if LDAPI is enabled (nsslapd-ldapilisten
and nsslapd-ldapifilepath), autobind is enabled (nsslapd-ldapiautobind), and autobind
mapping is enabled for regular users (nsslapd-ldapimaptoentries).
Parameter Description
Entry DN cn=config
Valid Values Any Directory Server attribute
Default Value uidNumber
Syntax DirectoryString
Example nsslapd-ldapiuidnumbertype: uidNumber
41
Page 56

Chapter 2. Core Server Configuration Reference
2.3.1.72. nsslapd-listenhost (Listen to IP Address)
This attribute allows multiple Directory Server instances to run on a multihomed machine (or makes
it possible to limit listening to one interface of a multihomed machine). There can be multiple IP
addresses associated with a single hostname, and these IP addresses can be a mix of both IPv4 and
IPv6. This parameter can be used to restrict the Directory Server instance to a single IP interface.
If a hostname is given as the nsslapd-listenhost value, then the Directory Server responds to
requests for every interface associated with the hostname. If a single IP interface (either IPv4 or IPv6)
is given as the nsslapd-listenhost value, Directory Server only responds to requests sent to that
specific interface. Either an IPv4 or IPv6 address can be used.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=config
Valid Values Any local hostname, IPv4 or IPv6 address
Default Value
Syntax DirectoryString
Example nsslapd-listenhost: ldap.example.com
NOTE
On HP-UX the hostname value can be a relocatable IP address.
2.3.1.73. nsslapd-localhost (Local Host)
This attribute specifies the host machine on which the Directory Server runs. This attribute is used to
create the referral URL that forms part of the MMR protocol. In a high-availability configuration with
failover nodes, that referral should point to the virtual name of the cluster, not the local hostname.
Parameter Description
Entry DN cn=config
Valid Values Any fully qualified hostname.
Default Value Hostname of installed machine.
Syntax DirectoryString
Example nsslapd-localhost: phonebook.example.com
2.3.1.74. nsslapd-localuser (Local User)
This attribute sets the user as whom the Directory Server runs. The group as which the user runs is
derived from this attribute by examining the user's primary group. Should the user change, then all of
the instance-specific files and directories for this instance need to be changed to be owned by the new
user, using a tool such as chown.
The value for the nsslapd-localuser is set initially when the server instance is configured.
42
Page 57

cn=config
Parameter Description
Entry DN cn=config
Valid Values Any valid user
Default Value
Syntax DirectoryString
Example nsslapd-localuser: nobody
2.3.1.75. nsslapd-lockdir (Server Lock File Directory)
This is the full path to the directory the server uses for lock files. The default value is /var/lock/
dirsrv/slapd-instance_name. Changes to this value will not take effect until the server is
restarted.
Parameter Description
Entry DN cn=config
Valid Values Absolute path to a directory owned by the server
user ID with write access to the server ID
Default Value /var/lock/dirsrv/slapd-instance_name
Syntax DirectoryString
Example nsslapd-lockdir: /var/lock/dirsrv/
slapd-instance_name
2.3.1.76. nsslapd-maxbersize (Maximum Message Size)
Defines the maximum size in bytes allowed for an incoming message. This limits the size of LDAP
requests that can be handled by the Directory Server. Limiting the size of requests prevents some
kinds of denial of service attacks.
The limit applies to the total size of the LDAP request. For example, if the request is to add an entry
and if the entry in the request is larger than two megabytes, then the add request is denied. Be
cautious before changing this attribute.
The server should be restarted for changes in this attribute to take effect.
Parameter Description
Entry DN cn=config
Valid Range 0 - 2 gigabytes (2,147,483,647 bytes)
Zero 0 means that the default value should be
used.
Default Value 2097152
Syntax Integer
Example nsslapd-maxbersize: 2097152
43
Page 58

Chapter 2. Core Server Configuration Reference
2.3.1.77. nsslapd-maxdescriptors (Maximum File Descriptors)
This attribute sets the maximum, platform-dependent number of file descriptors that the Directory
Server tries to use. A file descriptor is used whenever a client connects to the server and also for
some server activities, such as index maintenance. File descriptors are also used by access logs,
error logs, audit logs, database files (indexes and transaction logs), and as sockets for outgoing
connections to other servers for replication and chaining.
The number of descriptors available for TCP/IP to serve client connections is determined by
nsslapd-conntablesize, and is equal to the nsslapd-maxdescriptors attribute minus the
number of file descriptors used by the server as specified in the nsslapd-reservedescriptors
attribute for non-client connections, such as index management and managing replication. The
nsslapd-reservedescriptors attribute is the number of file descriptors available for other uses
as described above. See Section 2.3.1.89, “nsslapd-reservedescriptors (Reserved File Descriptors)”.
The number given here should not be greater than the total number of file descriptors that the
operating system allows the ns-slapd process to use. This number differs depending on the
operating system.
If this value is set too high, the Directory Server queries the operating system for the maximum
allowable value, and then use that value. It also issues a warning in the error log. If this value is set to
an invalid value remotely, by using the Directory Server Console or ldapmodify, the server rejects
the new value, keep the old value, and respond with an error.
Some operating systems let users configure the number of file descriptors available to a process.
See the operating system documentation for details on file descriptor limits and configuration. The
dsktune program (explained in the Directory Server Installation Guide) can be used to suggest
changes to the system kernel or TCP/IP tuning attributes, including increasing the number of file
descriptors if necessary. Increased the value on this attribute if the Directory Server is refusing
connections because it is out of file descriptors. When this occurs, the following message is written to
the Directory Server's error log file:
Not listening for new connections -- too many fds open
See Section 2.3.1.38, “nsslapd-conntablesize” for more information about increasing the number of
incoming connections.
NOTE
UNIX shells usually have configurable limits on the number of file descriptors. See the
operating system documentation for further information about limit and ulimit, as
these limits can often cause problems.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=config
Valid Range 1 to 65535
Default Value 1024
Syntax Integer
44
Page 59

cn=config
Parameter Description
Example nsslapd-maxdescriptors: 1024
2.3.1.78. nsslapd-maxsasliosize (Maximum SASL Packet Size)
When a user is authenticated to the Directory Server over SASL GSS-API, the server must allocate a
certain amount of memory to the client to perform LDAP operations, according to how much memory
the client requests. It is possible for an attacker to send such a large packet size that it crashes the
Directory Server or ties it up indefinitely as part of a denial of service attack.
The packet size which the Directory Server will allow for SASL clients can be limited using the
nsslapd-maxsasliosize attribute. This attribute sets the maximum allowed SASL IO packet size
that the server will accept.
When an incoming SASL IO packet is larger than the nsslapd-maxsasliosize limit, the server
immediately disconnects the client and logs a message to the error log, so that an administrator can
adjust the setting if necessary.
This attribute value is specified in bytes.
Parameter Description
Entry DN cn=config
Valid Range -1 (unlimited) to the maximum 32-bit integer
value (2147483647) on 32-bit systems
-1 (unlimited) to the maximum 64-bit integer
value (9223372036854775807) on 64-bit
systems
Default Value 2000000 (2MB)
Syntax Integer
Example nsslapd-maxsasliosize: 5000000
2.3.1.79. nsslapd-maxthreadsperconn (Maximum Threads per Connection)
Defines the maximum number of threads that a connection should use. For normal operations where
a client binds and only performs one or two operations before unbinding, use the default value. For
situations where a client binds and simultaneously issues many requests, increase this value to allow
each connection enough resources to perform all the operations. This attribute is not available from
the server console.
Parameter Description
Entry DN cn=config
Valid Range 1 to maximum threadnumber
Default Value 5
Syntax Integer
Example nsslapd-maxthreadsperconn: 5
45
Page 60

Chapter 2. Core Server Configuration Reference
2.3.1.80. nsslapd-nagle
When the value of this attribute is off, the TCP_NODELAY option is set so that LDAP responses (such
as entries or result messages) are sent back to a client immediately. When the attribute is turned
on, default TCP behavior applies; specifically, sending data is delayed so that additional data can be
grouped into one packet of the underlying network MTU size, typically 1500 bytes for Ethernet.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-nagle: off
2.3.1.81. nsslapd-outbound-ldap-io-timeout
This attribute limits the I/O wait time for all outbound LDAP connections. The default is 300000
milliseconds (5 minutes). A value of 0 means that the server does not impose a limit on I/O wait time.
Parameter Description
Entry DN cn=config
Valid Range 0 to the maximum 32-bit integer value
(2147483647)
Default Value 300000
Syntax DirectoryString
Example nsslapd-outbound-ldap-io-timeout: 300000
2.3.1.82. nsslapd-plug-in
This read-only attribute lists the DNs of the plug-in entries for the syntax and matching rule plug-ins
loaded by the server.
2.3.1.83. nsslapd-port (Port Number)
This attribute gives the TCP/IP port number used for standard LDAP communications. To run SSL/TLS
over this port, use the Start TLS extended operation. This selected port must be unique on the host
system; make sure no other application is attempting to use the same port number. Specifying a port
number of less than 1024 means the Directory Server has to be started as root.
The server sets its uid to the nsslapd-localuser value after startup. When changing the port
number for a configuration directory, the corresponding server instance entry in the configuration
directory must be updated.
The server has to be restarted for the port number change to be taken into account.
Parameter Description
Entry DN cn=config
Valid Range 1 to 65535
46
Page 61

cn=config
Parameter Description
Default Value 389
Syntax Integer
Example nsslapd-port: 389
NOTE
Set the port number to zero (0) to disable the LDAP port if the LDAPS port is enabled.
2.3.1.84. nsslapd-privatenamespaces
This read-only attribute contains the list of the private naming contexts cn=config, cn=schema, and
cn=monitor.
Parameter Description
Entry DN cn=config
Valid Values cn=config, cn=schema, and cn=monitor
Default Value
Syntax DirectoryString
Example nsslapd-privatenamespaces: cn=config
2.3.1.85. nsslapd-pwpolicy-local (Enable Subtree- and User-Level Password Policy)
Turns fine-grained (subtree- and user-level) password policy on and off.
If this attribute has a value of off, all entries (except for cn=Directory Manager) in the directory
is subjected to the global password policy; the server ignores any defined subtree/user level password
policy.
If this attribute has a value of on, the server checks for password policies at the subtree- and userlevel and enforce those policies.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-pwpolicy-local: off
2.3.1.86. nsslapd-readonly (Read Only)
This attribute sets whether the whole server is in read-only mode, meaning that neither data in the
databases nor configuration information can be modified. Any attempt to modify a database in readonly mode returns an error indicating that the server is unwilling to perform the operation.
47
Page 62

Chapter 2. Core Server Configuration Reference
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-readonly: off
2.3.1.87. nsslapd-referral (Referral)
This multi-valued attribute specifies the LDAP URLs to be returned by the suffix when the server
receives a request for an entry not belonging to the local tree; that is, an entry whose suffix does not
match the value specified on any of the suffix attributes. For example, assume the server contains only
entries:
ou=People,dc=example,dc=com
but the request is for this entry:
ou=Groups,dc=example,dc=com
In this case, the referral would be passed back to the client in an attempt to allow the LDAP client to
locate a server that contains the requested entry. Although only one referral is allowed per Directory
Server instance, this referral can have multiple values.
NOTE
To use SSL and TLS communications, the referral attribute should be in the form
ldaps://server-location.
Start TLS does not support referrals.
For more information on managing referrals, see the "Configuring Directory Databases" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values Any valid LDAP URL in the form ldap://server-
location
Default Value
Syntax DirectoryString
Example nsslapd-referral: ldap://ldap.example.com
2.3.1.88. nsslapd-referralmode (Referral Mode)
When set, this attribute sends back the referral for any request on any suffix.
48
Page 63

cn=config
Parameter Description
Entry DN cn=config
Valid Values Any valid LDAP URL in the form
>ldap://server-location
Default Value
Syntax DirectoryString
Example nsslapd-referralmode: ldap://ldap.example.com
2.3.1.89. nsslapd-reservedescriptors (Reserved File Descriptors)
This attribute specifies the number of file descriptors that Directory Server reserves for managing
non-client connections, such as index management and managing replication. The number of file
descriptors that the server reserves for this purpose subtracts from the total number of file descriptors
available for servicing LDAP client connections (See Section 2.3.1.77, “nsslapd-maxdescriptors
(Maximum File Descriptors)”).
Most installations of Directory Server should never need to change this attribute. However, consider
increasing the value on this attribute if all of the following are true:
• The server is replicating to a large number of consumer servers (more than 10), and/or the server is
maintaining a large number of index files (more than 30).
• The server is servicing a large number of LDAP connections.
• There are error messages reporting that the server is unable to open file descriptors (the actual
error message differs depending on the operation that the server is attempting to perform), but these
error messages are not related to managing client LDAP connections.
Increasing the value on this attribute may result in more LDAP clients being unable to access the
directory. Therefore, the value on this attribute is increased, also increase the value on the nsslapd-
maxdescriptors attribute. It may not be possible to increase the nsslapd-maxdescriptors
value if the server is already using the maximum number of file descriptors that the operating system
allows a process to use; see the operating system documentation for details. If this is the case, then
reduce the load on the server by causing LDAP clients to search alternative directory replicas. See
Section 2.3.1.38, “nsslapd-conntablesize” for information about file descriptor usage for incoming
connections.
To assist in computing the number of file descriptors set for this attribute, use the following formula:
nsslapd-reservedescriptor = 20 + (NldbmBackends * 4) + NglobalIndex +
ReplicationDescriptor + ChainingBackendDescriptors + PTADescriptors + SSLDescriptors
• NldbmBackends is the number of ldbm databases.
• NglobalIndex is the total number of configured indexes for all databases including system indexes.
(By default 8 system indexes and 17 additional indexes per database).
• ReplicationDescriptor is eight (8) plus the number of replicas in the server that can act as a supplier
or hub (NSupplierReplica).
49
Page 64

Chapter 2. Core Server Configuration Reference
• ChainingBackendDescriptors is NchainingBackend times the nsOperationConnectionsLimit (a
chaining or database link configuration attribute; 10 by default).
• PTADescriptors is 3 if PTA is configured and 0 if PTA is not configured.
• SSLDescriptors is 5 (4 files + 1 listensocket) if SSL is configured and 0 if SSL is not configured.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=config
Valid Range 1 to 65535
Default Value 64
Syntax Integer
Example nsslapd-reservedescriptors: 64
2.3.1.90. nsslapd-return-exact-case (Return Exact Case)
Returns the exact case of attribute type names as requested by the client. Although LDAPv3compliant clients must ignore the case of attribute names, some client applications require attribute
names to match exactly the case of the attribute as it is listed in the schema when the attribute is
returned by the Directory Server as the result of a search or modify operation. However, most client
applications ignore the case of attributes; therefore, by default, this attribute is disabled. Do not modify
it unless there are legacy clients that can check the case of attribute names in results returned from
the server.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example nsslapd-return-exact-case: off
2.3.1.91. nsslapd-rewrite-rfc1274
This attribute is deprecated and will be removed in a later version.
This attribute is used only for LDAPv2 clients that require attribute types to be returned with their RFC
1274 names. Set the value to on for those clients. The default is off.
2.3.1.92. nsslapd-rootdn (Manager DN)
This attribute sets the distinguished name (DN) of an entry that is not subject to access control
restrictions, administrative limit restrictions for operations on the directory, or resource limits in general.
There does not have to be an entry corresponding to this DN, and by default there is not an entry for
this DN, thus values like cn=Directory Manager are acceptable.
50
Page 65

cn=config
For information on changing the root DN, see the "Creating Directory Entries" chapter in the Directory
Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values Any valid distinguished name
Default Value
Syntax DN
Example nsslapd-rootdn: cn=Directory Manager
2.3.1.93. nsslapd-rootpw (Root Password)
This attribute sets the password associated with the Manager DN. When the root password
is provided, it is encrypted according to the encryption method selected for the nsslapd-
rootpwstoragescheme attribute. When viewed from the server console, this attribute shows the
value *****. When viewed from the dse.ldif file, this attribute shows the encryption method
followed by the encrypted string of the password. The example shows the password as displayed in
the dse.ldif file, not the actual password.
WARNING
When the root DN is configured at server setup, a root password is required.
However, it is possible for the root password to be deleted from dse.ldif by directly
editing the file. In this situation, the root DN can only obtain the same access to the
directory is allowed for anonymous access. Always make sure that a root password is
defined in dse.ldif when a root DN is configured for the database. The pwdhash
command-line utility can create a new root password. For more information, see
Section 7.3.12, “pwdhash (Prints Encrypted Passwords)”.
Parameter Description
Entry DN cn=config
Valid Values Any valid password encrypted by any one of
the encryption methods which are described in
Section 2.3.1.142, “passwordStorageScheme
(Password Storage Scheme)”.
Default Value
Syntax DirectoryString {encryption_method
}encrypted_Password
Example nsslapd-rootpw: {SSHA}9Eko69APCJfF
2.3.1.94. nsslapd-rootpwstoragescheme (Root Password Storage Scheme)
This attribute sets the encryption method used for the root password.
Parameter Description
Entry DN cn=config
51
Page 66

Chapter 2. Core Server Configuration Reference
Parameter Description
Valid Values Any encryption method as described in
Section 2.3.1.142, “passwordStorageScheme
(Password Storage Scheme)”.
Default Value SSHA
Syntax DirectoryString
Example nsslapd-rootpwstoragescheme: SSHA
2.3.1.95. nsslapd-saslpath
Sets the absolute path to the directory containing the Cyrus-SASL SASL2 plug-ins. On HP-UX
systems, the Directory Server cannot use the system SASL libraries because they are either not
provided or are not the correct version. Setting this attribute allows the server to use custom or nonstandard SASL plug-in libraries. This is usually set correctly during installation, and Red Hat strongly
recommends not changing this attribute. If the attribute is not present or the value is empty, this means
the Directory Server is using the system provided SASL plug-in libraries which are the correct version.
If this parameter is set, the server uses the specified path for loading SASL plugins. If this parameter
is not set, the server uses the SASL_PATH environment variable. If neither nsslapd-saslpath or
SASL_PATH are set, the server attempts to load SASL plugins from the default location, /usr/lib/
sasl2.
Changes made to this attribute will not take effect until the server is restarted.
Parameter Description
Entry DN cn=config
Valid Values Path to plugins directory.
Default Value Platform dependent
Syntax DirectoryString
Example nsslapd-saslpath: /usr/lib/sasl2
2.3.1.96. nsslapd-schema-ignore-trailing-spaces (Ignore Trailing Spaces
in Object Class Names)
Ignores trailing spaces in object class names. By default, the attribute is turned off. If the directory
contains entries with object class values that end in one or more spaces, turn this attribute on. It is
preferable to remove the trailing spaces because the LDAP standards do not allow them.
For performance reasons, server restart is required for changes to take effect.
An error is returned by default when object classes that include trailing spaces are added to an entry.
Additionally, during operations such as add, modify, and import (when object classes are expanded
and missing superiors are added) trailing spaces are ignored, if appropriate. This means that even
when nsslapd-schema-ignore-trailing-spaces is on, a value such as top is not added if
top is already there. An error message is logged and returned to the client if an object class is not
found and it contains trailing spaces.
Parameter Description
Entry DN cn=config
52
Page 67

cn=config
Parameter Description
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-schema-ignore-trailing-spaces: on
2.3.1.97. nsslapd-schemacheck (Schema Checking)
This attribute sets whether the database schema is enforced when entries are added or modified.
When this attribute has a value of on, Directory Server will not check the schema of existing entries
until they are modified. The database schema defines the type of information allowed in the database.
The default schema can be extended using the object classes and attribute types. For information
on how to extend the schema using the Directory Server Console, see the "Extending the Directory
Schema" chapter in the Directory Server Administrator's Guide.
WARNING
Red Hat strongly discourages turning off schema checking. This can lead to severe
interoperability problems. This is typically used for very old or non-standard LDAP
data that must be imported into the Directory Server. If there are not a lot of entries
that have this problem, consider using the extensibleObject object class in those
entries to disable schema checking on a per entry basis.
NOTE
Schema checking works by default when database modifications are made using
an LDAP client, such as ldapmodify or when importing a database from LDIF
using ldif2db. If schema checking is turned off, every entry has to be verified
manually to see that they conform to the schema. If schema checking is turned on,
the server sends an error message listing the entries which do not match the schema.
Ensure that the attributes and object classes created in the LDIF statements are both
spelled correctly and identified in dse.ldif. Either create an LDIF file in the schema
directory or add the elements to 99user.ldif.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example nsslapd-schemacheck: on
2.3.1.98. nsslapd-schemadir
This is the absolute path to the directory containing the Directory Server instance-specific schema
files. When the server starts up, it reads the schema files from this directory, and when the schema
is modified through LDAP tools, the schema files in this directory are updated. This directory must
53
Page 68

Chapter 2. Core Server Configuration Reference
be owned by the server user ID, and that user must have read and write permissions to the directory.
The default value is the schema subdirectory of the Directory Server instance-specific configuration
directory, /etc/dirsrv/slapd-instance_name/schema.
Changes made to this attribute will not take effect until the server is restarted.
2.3.1.99. nsslapd-schemareplace
Determines whether modify operations that replace attribute values are allowed on the cn=schema
entry.
Parameter Description
Entry DN cn=config
Valid Values on | off | replication-only
Default Value replication-only
Syntax DirectoryString
Example nsslapd-schemareplace: replication-only
2.3.1.100. nsslapd-securelistenhost
This attribute allows multiple Directory Server instances to run on a multihomed machine (or makes
it possible to limit listening to one interface of a multihomed machine). There can be multiple IP
addresses associated with a single hostname, and these IP addresses can be a mix of both IPv4 and
IPv6. This parameter can be used to restrict the Directory Server instance to a single IP interface; this
parameter also specifically sets what interface to use for SSL/TLS traffic rather than regular LDAP
connections.
If a hostname is given as the nsslapd-securelistenhost value, then the Directory Server
responds to requests for every interface associated with the hostname. If a single IP interface (either
IPv4 or IPv6) is given as the nsslapd-securelistenhost value, Directory Server only responds to
requests sent to that specific interface. Either an IPv4 or IPv6 address can be used.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=config
Valid Values Any secure hostname, IPv4 or IPv6 address
Default Value
Syntax DirectoryString
Example nsslapd-securelistenhost: ldaps.example.com
2.3.1.101. nsslapd-securePort (Encrypted Port Number)
This attribute sets the TCP/IP port number used for SSL/TLS communications. This selected port
must be unique on the host system; make sure no other application is attempting to use the same
port number. Specifying a port number of less than 1024 requires that Directory Server be started as
root. The server sets its uid to the nsslapd-localuser value after startup.
The server only listens to this port if it has been configured with a private key and a certificate, and
nsslapd-security is set to on; otherwise, it does not listen on this port.
54
Page 69

cn=config
The server has to be restarted for the port number change to be taken into account.
Parameter Description
Entry DN cn=config
Valid Range 1 to 65535
Default Value 636
Syntax Integer
Example nsslapd-securePort: 636
2.3.1.102. nsslapd-security (Security)
This attribute sets whether the Directory Server is to accept SSL/TLS communications on its encrypted
port. This attribute should be set to on for secure connections. To run with security on, the server must
be configured with a private key and server certificate in addition to the other SSL/TLS configuration.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsslapd-security: off
2.3.1.103. nsslapd-sizelimit (Size Limit)
This attribute sets the maximum number of entries to return from a search operation. If this limit is
reached, ns-slapd returns any entries it has located that match the search request, as well as an
exceeded size limit error.
When no limit is set, ns-slapd returns every matching entry to the client regardless of the number
found. To set a no limit value whereby the Directory Server waits indefinitely for the search to
complete, specify a value of -1 for this attribute in the dse.ldif file.
This limit applies to everyone, regardless of their organization.
NOTE
A value of -1 on this attribute in dse.ldif file is the same as leaving the attribute
blank in the server console, in that it causes no limit to be used. This cannot have
a null value in dse.ldif file, as it is not a valid integer. It is possible to set it to 0,
which returns size limit exceeded for every search.
Parameter Description
Entry DN cn=config
Valid Range -1 to the maximum 32 bit integer value
(2147483647)
Default Value 2000
Syntax Integer
55
Page 70

Chapter 2. Core Server Configuration Reference
Parameter Description
Example nsslapd-sizelimit: 2000
2.3.1.104. nsslapd-ssl-check-hostname (Verify Hostname for Outbound
Connections)
This attribute sets whether an SSL-enabled Directory Server should verify authenticity of a request by
matching the hostname against the value assigned to the common name (cn) attribute of the subject
name (subjectDN field) in the certificate being presented. By default, the attribute is set to on. If it is
on and if the hostname does not match the cn attribute of the certificate, appropriate error and audit
messages are logged.
For example, in a replicated environment, messages similar to the following are logged in the supplier
server's log files if it finds that the peer server's hostname does not match the name specified in its
certificate:
[DATE] - SSL alert: ldap_sasl_bind("",LDAP_SASL_EXTERNAL) 81 (Netscape runtime error -12276 Unable to communicate securely with peer: requested domain name does not
match the server's certificate.)
[DATE] NSMMReplicationPlugin - agmt="cn=SSL Replication Agreement to
host1" (host1.example.com:636):
Replication bind with SSL client authentication failed:
LDAP error 81 (Can't contact LDAP server)
Red Hat recommends turning this attribute on to protect Directory Server's outbound SSL connections
against a man in the middle (MITM) attack.
NOTE>
DNS and reverse DNS must be set up correctly in order for this to work; otherwise,
the server cannot resolve the peer IP address to the hostname in the subject DN in
the certificate.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example nsslapd-ssl-check-hostname: on
2.3.1.105. nsslapd-threadnumber (Thread Number)
Defines the number of operation threads that the Directory Server creates at startup. The nsslapdthreadnumber value should be increased if there are many directory clients performing time-
consuming operations such as add or modify, as this ensures that there are other threads available for
servicing short-lived operations such as simple searches. This value may also need increased if there
are many replication agreements or chained backends (database links). This attribute is not available
from the server console.
56
Page 71

cn=config
Parameter Description
Entry DN cn=config
Valid Range 1 to the maximum number of threads supported
by the system
Default Value 30
Syntax Integer
Example nsslapd-threadnumber: 60
2.3.1.106. nsslapd-timelimit (Time Limit)
This attribute sets the maximum number of seconds allocated for a search request. If this limit is
reached, Directory Server returns any entries it has located that match the search request, as well as
an exceeded time limit error.
When no limit is set, ns-slapd returns every matching entry to the client regardless of the time it
takes. To set a no limit value whereby Directory Server waits indefinitely for the search to complete,
specify a value of -1 for this attribute in the dse.ldif file. A value of zero (0) causes no time to be
allowed for searches. The smallest time limit is 1 second.
NOTE
A value of -1 on this attribute in thedse.ldif is the same as leaving the attribute
blank in the server console in that it causes no limit to be used. However, a negative
integer cannot be set in this field in the server console, and a null value cannot be
used in the dse.ldif entry, as it is not a valid integer.
Parameter Description
Entry DN cn=config
Valid Range -1 to the maximum 32 bit integer value
(2147483647) in seconds
Default Value 3600
Syntax Integer
Example nsslapd-timelimit: 3600
2.3.1.107. nsslapd-tmpdir
This is the absolute path of the directory the server uses for temporary files. The directory must be
owned by the server user ID and the user must have read and write access. No other user ID should
have read or write access to the directory. The default value is /tmp.
Changes made to this attribute will not take effect until the server is restarted.
2.3.1.108. nsslapd-versionstring
This attribute sets the server version number. The build data is automatically appended when the
version string is displayed.
57
Page 72

Chapter 2. Core Server Configuration Reference
Parameter Description
Entry DN cn=config
Valid Values Any valid server version number.
Default Value
Syntax DirectoryString
Example nsslapd-versionstring: Red Hat-Directory/8.1
2.3.1.109. nsslapd-workingdir
This is the absolute path of the directory that the server uses as its current working directory after
startup. This is the value that the server would return as the value of the getcwd() function, and the
value that the system process table shows as its current working directory. This is the directory a core
file is generated in. The server user ID must have read and write access to the directory, and no other
user ID should have read or write access to it. The default value for this attribute is the same directory
containing the error log, which is usually /var/log/dirsrv/slapd-instance_name.
Changes made to this attribute will not take effect until the server is restarted.
2.3.1.110. nsSSLclientauth (Client Authentication)
This attribute sets whether client authentication (also called certificate-based authentication) is allowed
to the Directory Server. If this attribute is set to required, then the Console cannot be set to require
SSL because certificate-based authentication is not supported in the Console.
Parameter Description
Entry DN cn=config
Valid Values off | allowed | required
Default Value off
Syntax DirectoryString
Example nsSSLclientauth: allowed
2.3.1.111. passwordAllowChangeTime
This attribute specifies the length of time that must pass before the user is allowed to change his
password.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values Any integer
Default Value
Syntax DirectoryString
Example passwordAllowChangeTime: 5h
58
Page 73

cn=config
2.3.1.112. passwordChange (Password Change)
Indicates whether users may change their passwords.
This can be abbreviated to pwdAllowUserChange.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example passwordChange: on
2.3.1.113. passwordCheckSyntax (Check Password Syntax)
This attribute sets whether the password syntax is checked before the password is saved. The
password syntax checking mechanism checks that the password meets or exceeds the password
minimum length requirement and that the string does not contain any trivial words, such as the user's
name or user ID or any attribute value stored in the uid, cn, sn, givenname, ou, or mail attributes
of the user's directory entry.
Password syntax includes several different categories for checking:
• Minimum number of digit characters (0-9)
• Minimum number of ASCII alphabetic characters, both upper- and lower-case
• Minimum number of uppercase ASCII alphabetic characters
• Minimum number of lowercase ASCII alphabetic characters
• Minimum number of special ASCII characters, such as !@#$
• Minimum number of 8-bit characters
• Maximum number of times that the same character can be immediately repeated, such as aaabbb
• Minimum number of character categories required per password; a category can be upper- or lowercase letters, special characters, digits, or 8-bit characters
This can be abbreviated to pwdCheckSyntax.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
59
Page 74

Chapter 2. Core Server Configuration Reference
Parameter Description
Syntax DirectoryString
Example passwordCheckSyntax off
2.3.1.114. passwordExp (Password Expiration)
Indicates whether user passwords expire after a given number of seconds. By default, user passwords
do not expire. Once password expiration is enabled, set the number of seconds after which the
password expires using the passwordMaxAge attribute.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example passwordExp: on
2.3.1.115. passwordExpirationTime
This attribute specifies the length of time that passes before the user’s password expires.
Parameter Description
Entry DN cn=config
Valid Values Any date, in integers
Default Value none
Syntax GeneralizedTime
Example passwordExpirationTime: 200909011953
2.3.1.116. passwordExpWarned
This attribute is used to indicate that a password expiration warning has been sent to the user.
Parameter Description
Entry DN cn=config
Valid Values true | false
Default Value none
Syntax DirectoryString
Example passwordExpWarned: true
2.3.1.117. passwordGraceLimit (Password Expiration)
This attribute is only applicable if password expiration is enabled. After the user's password has
expired, the server allows the user to connect for the purpose of changing the password. This is called
60
Page 75

cn=config
a grace login. The server allows only a certain number of attempts before completely locking out the
user. This attribute is the number of grace logins allowed. A value of 0 means the server does not
allow grace logins.
Parameter Description
Entry DN cn=config
Valid Values 0 (off) to any reasonable integer
Default Value 0
Syntax Integer
Example passwordGraceLimit: 3
2.3.1.118. passwordGraceUserTime
This attribute counts the number of attempts the user has made with the expired password.
This is an operational attribute, meaning its value is managed by the server and the attribute is not
returned in default searches.
Parameter Description
Entry DN cn=config
Valid Values none to any reasonable integer
Default Value none
Syntax Integer
Example passwordGraceUserTime: 1
2.3.1.119. passwordHistory (Password History)
Enables password history. Password history refers to whether users are allowed to reuse passwords.
By default, password history is disabled, and users can reuse passwords. If this attribute is set to
on, the directory stores a given number of old passwords and prevents users from reusing any
of the stored passwords. Set the number of old passwords the Directory Server stores using the
passwordInHistory attribute.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example passwordHistory: on
2.3.1.120. passwordInHistory (Number of Passwords to Remember)
Indicates the number of passwords the Directory Server stores in history. Passwords that are stored in
history cannot be reused by users. By default, the password history feature is disabled, meaning that
61
Page 76

Chapter 2. Core Server Configuration Reference
the Directory Server does not store any old passwords, and so users can reuse passwords. Enable
password history using the passwordHistory attribute.
To prevent users from rapidly cycling through the number of passwords that are tracked, use the
passwordMinAge attribute.
This can be abbreviated to pwdInHistory.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Range 2 to 24 passwords
Default Value 6
Syntax Integer
Example passwordInHistory: 7
2.3.1.121. passwordIsGlobalPolicy (Password Policy and Replication)
This attribute controls whether password policy attributes are replicated.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example passwordIsGlobalPolicy: off
2.3.1.122. passwordKeepHistory
This attribute sets whether a password history is maintained for users.
Parameter Description
Entry DN cn=config
Valid Values 0 (no history) or 1 (keep history)
Default Value 0
Syntax DirectoryString
Example passwordKeepHistory: 1
2.3.1.123. passwordLockout (Account Lockout)
Indicates whether users are locked out of the directory after a given number of failed bind attempts.
By default, users are not locked out of the directory after a series of failed bind attempts. If account
lockout is enabled, set the number of failed bind attempts after which the user is locked out using the
passwordMaxFailure attribute.
62
Page 77

cn=config
This can be abbreviated to pwdLockOut.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example passwordLockout: off
2.3.1.124. passwordLockoutDuration (Lockout Duration)
Indicates the amount of time in seconds during which users are locked out of the directory after
an account lockout. The account lockout feature protects against hackers who try to break into the
directory by repeatedly trying to guess a user's password. Enable and disable the account lockout
feature using the passwordLockout attribute.
This can be abbreviated to pwdLockoutDuration.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Range 1 to the maximum 32 bit integer value
(2147483647) in seconds
Default Value 3600
Syntax Integer
Example passwordLockoutDuration: 3600
2.3.1.125. passwordMaxAge (Password Maximum Age)
Indicates the number of seconds after which user passwords expire. To use this attribute, password
expiration has to be enabled using the passwordExp attribute.
This can be abbreviated to pwdMaxAge.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Range 1 to the maximum 32 bit integer value
(2147483647) in seconds
Default Value 8640000 (100 days)
Syntax Integer
63
Page 78

Chapter 2. Core Server Configuration Reference
Parameter Description
Example passwordMaxAge: 100
2.3.1.126. passwordMaxFailure (Maximum Password Failures)
Indicates the number of failed bind attempts after which a user is locked out of the directory. By
default, account lockout is disabled. Enable account lockout by modifying the passwordLockout
attribute.
This can be abbreviated to pwdMaxFailure.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Range 1 to maximum integer bind failures
Default Value 3
Syntax Integer
Example passwordMaxFailure: 3
2.3.1.127. passwordMaxRepeats (Password Syntax)
Maximum number of times the same character can appear sequentially in the password. Zero (0) is
off. Integer values reject any password which used a character more than that number of times; for
example, 1 rejects characters that are used more than once (aa) and 2 rejects characters used more
than twice (aaa).
Parameter Description
Entry DN cn=config
Valid Range 0 to 64
Default Value 0
Syntax Integer
Example passwordMaxRepeats: 1
2.3.1.128. passwordMin8Bit (Password Syntax)
This sets the minimum number of 8-bit characters the password must contain.
NOTE
The 7-bit checking for userPassword must be disabled to use this.
Parameter Description
Entry DN cn=config
Valid Range 0 to 64
64
Page 79

cn=config
Parameter Description
Default Value 0
Syntax Integer
Example passwordMin8Bit: 0
2.3.1.129. passwordMinAge (Password Minimum Age)
Indicates the number of seconds that must pass before a user can change their password. Use this
attribute in conjunction with the passwordInHistory (number of passwords to remember) attribute
to prevent users from quickly cycling through passwords so that they can use their old password
again. A value of zero (0) means that the user can change the password immediately.
This can be abbreviated to pwdMaxFailure.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Range 0 to valid maximum integer
Default Value 0
Syntax Integer
Example passwordMinAge: 150
2.3.1.130. passwordMinAlphas (Password Syntax)
This attribute sets the minimum number of alphabetic characters password must contain.
Parameter Description
Entry DN cn=config
Valid Range 0 to 64
Default Value 0
Syntax Integer
Example passwordMinAlphas: 4
2.3.1.131. passwordMinCategories (Password Syntax)
This sets the minimum number of character categories that are represented in the password. The
categories are lower, upper, digit, special, and 8-bit. For example, if the value of this attribute were
set to 2, and the user tried to change the password to aaaaa, the server would reject the password
because it contains only lower case characters, and therefore contains characters from only one
category. A password of aAaAaA would pass because it contains characters from two categories,
uppercase and lowercase. The default is 3, which means that if password syntax checking is enabled,
valid passwords have to have three categories of characters.
Parameter Description
Entry DN cn=config
65
Page 80

Chapter 2. Core Server Configuration Reference
Parameter Description
Valid Range 0 to 5
Default Value 0
Syntax Integer
Example passwordMinCategories: 2
2.3.1.132. PasswordMinDigits (Password Syntax)
This sets the minimum number of digits a password must contain.
Parameter Description
Entry DN cn=config
Valid Range 0 to 64
Default Value 0
Syntax Integer
Example passwordMinDigits: 3
2.3.1.133. passwordMinLength (Password Minimum Length)
This attribute specifies the minimum number of characters that must be used in Directory Server user
password attributes. In general, shorter passwords are easier to crack. Directory Server enforces a
minimum password of eight characters. This is long enough to be difficult to crack but short enough
that users can remember the password without writing it down.
This can be abbreviated to pwdMinLength.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Range 2 to 512 characters
Default Value 6
Syntax Integer
Example passwordMinLength: 6
2.3.1.134. PasswordMinLowers (Password Syntax)
This attribute sets the minimum number of lower case letters password must contain.
Parameter Description
Entry DN cn=config
Valid Range 0 to 64
Default Value 0
Syntax Integer
66
Page 81

cn=config
Parameter Description
Example passwordMinLowers: 1
2.3.1.135. PasswordMinSpecials (Password Syntax)
This attribute sets the minimum number of special, or not alphanumeric, characters a password must
contain.
Parameter Description
Entry DN cn=config
Valid Range 0 to 64
Default Value 0
Syntax Integer
Example passwordMinSpecials: 1
2.3.1.136. PasswordMinTokenLength (Password Syntax)
This attribute sets the smallest attribute value length that is used for trivial words checking. For
example, if the PasswordMinTokenLength is set to 3, then a givenname of DJ does not result in
a policy that rejects DJ from being in the password, but the policy rejects a password containing the
givenname of Bob.
Parameter Description
Entry DN cn=config
Valid Range 1 to 64
Default Value 3
Syntax Integer
Example passwordMinTokenLength: 3
2.3.1.137. PasswordMinUppers (Password Syntax)
This sets the minimum number of uppercase letters password must contain.
Parameter Description
Entry DN cn=config
Valid Range 0 to 64
Default Value 0
Syntax Integer
Example passwordMinUppers: 2
2.3.1.138. passwordMustChange (Password Must Change)
Indicates whether users must change their passwords when they first bind to the Directory Server or
when the password has been reset by the Manager DN.
This can be abbreviated to pwdMustChange.
67
Page 82

Chapter 2. Core Server Configuration Reference
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example passwordMustChange: off
2.3.1.139. passwordResetDuration
This attribute sets the amount of time that must pass after login failures before the server resets the
password retry count to zero.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Range 0 to the maximum 32 bit integer value
(2147483647) in seconds
Default Value 600
Syntax Integer
Example passwordResetDuration: 600
2.3.1.140. passwordResetFailureCount (Reset Password Failure Count After)
Indicates the amount of time in seconds after which the password failure counter resets. Each time
an invalid password is sent from the user's account, the password failure counter is incremented. If
the passwordLockout attribute is set to on, users are locked out of the directory when the counter
reaches the number of failures specified by the passwordMaxFailure attribute (within 600 seconds
by default). After the amount of time specified by the passwordLockoutDuration attribute, the
failure counter is reset to zero (0).
This can be abbreviated to pwdFailureCountInterval.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Range 1 to the maximum 32 bit integer value
(2147483647) in seconds
Default Value 600
Syntax Integer
68
Page 83

cn=config
Parameter Description
Example passwordResetFailureCount: 600
2.3.1.141. passwordRetryCount
This attribute counts the number of consecutive failed attempts at entering the correct password.
This is an operational attribute, meaning its value is managed by the server and the attribute is not
returned in default searches.
Parameter Description
Entry DN cn=config
Valid Range 0 to the maximum 32 bit integer value
(2147483647)
Default Value 0
Syntax Integer
Example passwordRetryCount: 3
2.3.1.142. passwordStorageScheme (Password Storage Scheme)
This attribute sets the type of encryption used to store Directory Server passwords.
The following encryption types are supported by the Directory Server:
• CLEAR means the password is stored in cleartext, with no hashing or encryption. This scheme must
be used in order to use SASL DIGEST-MD5.
• SSHA (Salted Secure Hash Algorithm), the default, is the recommended method because it is the
most secure. There are several bit sizes available: 140 bits (the default), 256, 384, and 512.
• SHA (Secure Hash Algorithm) is included only for backward compatibility with 4.x Directory Servers;
do not use this algorithm.
• MD5 (Message Digest algorithm 5) is a commonly used standard hashing algorithm.
• CRYPT, the UNIX crypt algorithm, is provided for compatibility with UNIX passwords.
NOTE
Passwords cannot be encrypted using the NS-MTA-MD5 password storage scheme.
The storage scheme is still present but only for reasons of backward compatibility.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
2.3.1.143. passwordUnlock (Unlock Account)
Indicates whether users are locked out of the directory for a specified amount of time or until the
administrator resets the password after an account lockout. The account lockout feature protects
69
Page 84

Chapter 2. Core Server Configuration Reference
against hackers who try to break into the directory by repeatedly trying to guess a user's password. If
this passwordUnlock attribute is set to off and the operational attribute accountUnlockTime has
a value of 0, then the account is locked indefinitely.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example passwordUnlock: off
2.3.1.144. passwordWarning (Send Warning)
Indicates the number of seconds before a user's password is due to expire that the user receives a
password expiration warning control on their next LDAP operation. Depending on the LDAP client, the
user may also be prompted to change their password at the time the warning is sent.
This can be abbreviated to pwdExpireWarning.
For more information on password policies, see the "Managing Users and Passwords" chapter in the
Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=config
Valid Range 1 to the maximum 32 bit integer value
(2147483647) in seconds
Default Value 86400 (1 day)
Syntax Integer
Example passwordWarning: 86400
2.3.1.145. retryCountResetTime
This attribute specifies the length of time that passes before the passwordRetryCount attribute is
reset.
Parameter Description
Entry DN cn=config
Valid Range 1 to any reasonable integer
Default Value none
Syntax Integer
Example retryCountResetTime: 15
70
Page 85

cn=changelog5
2.3.2. cn=changelog5
Multi-master replication changelog configuration entries are stored under the cn=changelog5 entry.
The changelog behaves much like a database, and it has many of attributes also used by the ldbm
databases.
The primary cache-related memory attribute, nsslapd-cachememsize, has a default value of
10485760 bytes, which is 10 MB. This parameter is tuned for a single backend replicated to a single
consumer.
When more backends are replicated or when one backend is replicated to more than one consumer,
tune the nsslapd-cachememsize so that its value is 5000000 times the number of replication
agreements initiated from the server (5000000 * no_of_repl_agreements).
The relationship between the values assigned to the nsslapd-dbcachesize and nsslapd-
cachememsize parameters should be the same as the relationship that is described in the database
tuning section.
The cn=changelog5,cn=config entry is an instance of the extensibleObject object class.
NOTE
Two different types of changelogs are maintained by Directory Server. The first
type, which is stored here and referred to as the changelog, is used by multimaster replication; the second changelog, which is actually a plug-in and referred
to as the retro changelog, is for compatibility with some legacy applications. See
Section 3.1.29, “Retro Changelog Plug-in” for further information about the Retro
Changelog Plug-in.
2.3.2.1. nsslapd-changelogdir
This required attribute specifies the name of the directory in which the changelog database is created.
Whenever a changelog configuration entry is created, it must contain a valid directory; otherwise,
the operation is rejected. The GUI proposes by default that this database be stored in /var/lib/
dirsrv/slapd-instance_name/changelogdb.
WARNING
If the cn=changelog5 entry is removed, the directory specified in the nsslapdchangelogdir parameter, including any subdirectories, are removed, with all of
their contents.
NOTE
For performance reasons, store this database on a different physical disk.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=changelog5,cn=config
71
Page 86

Chapter 2. Core Server Configuration Reference
Parameter Description
Valid Values Any valid path to the directory storing the
changelog
Default Value None
Syntax DirectoryString
Example nsslapd-changelogdir: /var/lib/dirsrv/
slapd-instance_name/changelogdb
2.3.2.2. nsslapd-changelogmaxage (Max Changelog Age)
This attribute sets the maximum age of any entry in the changelog. The changelog contains a
record for each directory modification and is used when synchronizing consumer servers. Each
record contains a timestamp. Any record with a timestamp that is older than the value specified in
this attribute is removed. If this attribute is absent, there is no age limit on changelog records. For
information on the changelog, see Section 2.3.2.1, “nsslapd-changelogdir”.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=changelog5,cn=config
Valid Range 0 (meaning that entries are not removed
according to their age) to maximum 32-bit integer
(2147483647)
Default Value 0
Syntax DirectoryString IntegerAgeID where AgeID is
s for seconds, m for minutes, h for hours, d for
days, and w for weeks
Example nsslapd-changelogmaxage: 30d
2.3.2.3. nsslapd-changelogmaxentries (Max Changelog Records)
This attribute sets the maximum number of records the changelog may contain. If this attribute is
absent, there is no maximum number of records the changelog can contain. For information on the
changelog, see Section 2.3.2.1, “nsslapd-changelogdir”.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=changelog5,cn=config
Valid Range 0 (meaning that the only maximum limit is
the disk size) to maximum 32-bit integer
(2147483647)
Default Value 0
Syntax Integer
Example nsslapd-changelogmaxentries: 5000
72
Page 87

cn=changelog5
2.3.2.4. changes
This attribute contains the changes made to the entry for add and modify operations in LDIF format.
OID 2.16.840.1.113730.3.1.8
Syntax Binary
Multi- or Single-Valued Multi-valued
Defined in Changelog Internet Draft
2.3.2.5. changeLog
This attribute contains the distinguished name of the entry which contains the set of entries comprising
the server’s changelog.
OID 2.16.840.1.113730.3.1.35
Syntax DN
Multi- or Single-Valued Multi-valued
Defined in Changelog Internet Draft
2.3.2.6. changeNumber
This attribute is always present. It contains an integer which uniquely identifies each change made
to a directory entry. This number is related to the order in which the change occurred. The higher the
number, the later the change.
OID 2.16.840.1.113730.3.1.5
Syntax Integer
Multi- or Single-Valued Multi-valued
Defined in Changelog Internet Draft
2.3.2.7. changeTime
This attribute defines a time, in a YYMMDDHHMMSS format, when the entry was added.
OID 2.16.840.1.113730.3.1.77
Syntax DirectoryString
Multi- or Single-Valued Multi-valued
Defined in Directory Server
2.3.2.8. changeType
This attribute specifies the type of LDAP operation, add, delete, modify, or modrdn. For example:
changeType: modify
OID 2.16.840.1.113730.3.1.7
Syntax DirectoryString
73
Page 88

Chapter 2. Core Server Configuration Reference
Multi- or Single-Valued Multi-valued
Defined in Changelog Internet Draft
2.3.2.9. deleteOldRdn
In the case of modrdn operations, this attribute specifies whether the old RDN was deleted.
OID 2.16.840.1.113730.3.1.10
Syntax Boolean
Multi- or Single-Valued Multi-valued
Defined in Changelog Internet Draft
2.3.2.10. filterInfo
This is used by the changelog for processing replication.
OID 2.16.840.1.113730.3.1.206
Syntax DirectoryString
Multi- or Single-Valued Multi-valued
Defined in Directory Server
2.3.2.11. newRdn
In the case of modrdn operations, this attribute specifies the new RDN of the entry.
OID 2.16.840.1.113730.3.1.9
Syntax DN
Multi- or Single-Valued Multi-valued
Defined in Changelog Internet Draft
2.3.2.12. newSuperior
In the case of modrdn operations, this attribute specifies the newSuperior attribute of the entry.
OID 2.16.840.1.113730.3.1.11
Syntax DN
Multi- or Single-Valued Multi-valued
Defined in Changelog Internet Draft
2.3.2.13. targetDn
This attribute contains the DN of the entry that was affected by the LDAP operation. In the case of
a modrdn operation, the targetDn attribute contains the DN of the entry before it was modified or
moved.
OID 2.16.840.1.113730.3.1.6
Syntax DN
74
Page 89

cn=encryption
Multi- or Single-Valued Multi-valued
Defined in Changelog Internet Draft
2.3.3. cn=encryption
Encryption related attributes are stored under the cn=encryption,cn=config entry. The
cn=encryption,cn=config entry is an instance of the nsslapdEncryptionConfig object class.
2.3.3.1. nsSSLSessionTimeout
This attribute sets the lifetime duration of a TLS/SSL. The minimum timeout value is 5 seconds. If a
smaller value is set, then it is automatically replaced by 5 seconds. A value greater than the maximum
value in the valid range below is replaced by the maximum value in the range.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=encryption, cn=config
Valid Range 5 seconds to 24 hours
Default Value 0, which means use the maximum value in the
valid range above.
Syntax Integer
Example nsSSLSessionTimeout: 5
2.3.3.2. nsSSLclientauth
This attribute sets how clients may use certificates to authenticate to the Directory Server for SSL
connections.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=encryption, cn=config
Valid Values off | allowed | required
off means disallow certificate-based
authentication
allowed means clients may use certificates or
other forms of authentication
required means clients must use certificates for
authentication
Default Value allowed
Syntax DirectoryString
Example nsSSLclientauth: allowed
2.3.3.3. nsSSL2
Supports SSL version 2. SSLv2 is deprecated, and Red Hat strongly discourages using it.
The server has to be restarted for changes to this attribute to go into effect.
75
Page 90

Chapter 2. Core Server Configuration Reference
Parameter Description
Entry DN cn=encryption, cn=config
Valid Values on | off
Default Value off
Syntax DirectoryString
Example nsSSL2: off
2.3.3.4. nsSSL3
Supports SSL version 3.
The server has to be restarted for changes to this attribute to go into effect.
Parameter Description
Entry DN cn=encryption, cn=config
Valid Values on | off
Default Value on
Syntax DirectoryString
Example nsSSL3: on
2.3.3.5. nsSSL3ciphers
This multi-valued attribute specifies the set of encryption ciphers the Directory Server uses during
SSL communications. For more information on the ciphers supported by the Directory Server, see the
"Managing SSL" chapter in the Directory Server Administrator's Guide.
Parameter Description
Entry DN cn=encryption, cn=config
Valid Values For SSLv3:
• rsa_null_md5
• rsa_rc4_128_md5
• rsa_rc4_40_md5
• rsa_rc2_40_md5
76
• rsa_des_sha
• rsa_fips_des_sha
• rsa_3des_sha
• rsa_fips_3des_sha
For TLS:
• tls_rsa_export1024_with_rc4_56_sha
Page 91

cn=features
Parameter Description
• tls_rsa_export1024_with_des_cbc_sha
Default Value
Syntax DirectoryString
Use the plus (+) symbol to enable or minus (-)
symbol to disable, followed by the ciphers. Blank
spaces are not allowed in the list of ciphers.
To enable all ciphers — except rsa_null_md5,
which must be specifically called — specify
+all.
Example nsslapd-SSL3ciphers: +RSA_NULL_MD5,
+RC4_56_SHA,-RC4_56_SHA
For more information, see the "Managing SSL" chapter in the Directory Server Administrator's Guide
2.3.4. cn=features
There are not attributes for the cn=features entry itself. This entry is only used as a parent
container entry, with the nsContainer object class.
The child entries contain an oid attribute to identify the feature and the directoryServerFeature
object class, plus optional identifying information about the feature, such as specific ACLs. For
example:
dn: oid=2.16.840.1.113730.3.4.9,cn=features,cn=config
objectClass: top
objectClass: directoryServerFeature
oid: 2.16.840.1.113730.3.4.9
cn: VLV Request Control
aci: (targetattr != "aci")(version 3.0; acl "VLV Request Control"; allow( read, search,
compare, proxy ) userdn = "ldap:///all";)
creatorsName: cn=server,cn=plugins,cn=config
modifiersName: cn=server,cn=plugins,cn=config
createTimestamp: 20090129132357Z
modifyTimestamp: 20090129132357Z
2.3.4.1. oid
The oid attribute contains an object identifier assigned to a directory service feature. oid is used as
the naming attribute for these directory features.
OID 2.16.840.1.113730.3.1.215
Syntax DirectoryString
Multi- or Single-Valued Multi-valued
Defined in Directory Server
77
Page 92

Chapter 2. Core Server Configuration Reference
2.3.5. cn=mapping tree
• Configuration attributes for suffixes, replication, and Windows synchronization are stored under
cn=mapping tree,cn=config. Configuration attributes related to suffixes are found under the
suffix subentry cn=suffix, cn=mapping tree,cn=config.
For example, a suffix is the root entry in the directory tree, such as dc=example,dc=com.
• Replication configuration attributes are stored under cn=replica, cn=suffix, cn=mapping
tree,cn=config.
• Replication agreement attributes are stored under cn=replicationAgreementName, cn=replica,
cn=suffix,cn=mapping tree,cn=config.
• Windows synchronization agreement attributes are stored under cn=syncAgreementName,
cn=replica, cn=suffix,cn=mapping tree,cn=config.
2.3.6. Suffix Configuration Attributes under cn="suffixName"
Suffix configuration attributes are stored under the cn=suffix entry. The cn=suffix entry is an instance
of the nsMappingTree object class which inherits from the extensibleObject object class. For
suffix configuration attributes to be taken into account by the server, these object classes (in addition
to the top object class) must be present in the entry.
The suffix DN should be quoted because the suffix DN contains characters such as equals signs (=),
commas (,), and space characters that must be quoted or escaped to appear as a value in another
DN.
2.3.6.1. nsslapd-state
Determines how the suffix handles operations.
Parameter Description
Entry DN cn=suffix, cn=mapping tree, cn=config
Valid Values backend | disabled | referral | referral on update
backend means the backend (database) is used
to process all operations.
disabled means the database is not available for
processing operations. The server returns a "No
such search object" error in response to requests
made by client applications.
referral means a referral is returned for requests
made to this suffix.
referral on update means the database is used
for all operations except update requests, which
receive a referral.
Default Value backend
Syntax DirectoryString
78
Page 93

Replication Attributes under cn=replica, cn="suffixDN", cn=mapping tree, cn=config
Parameter Description
Example nsslapd-state: backend
2.3.6.2. nsslapd-backend
Gives the name of the database or database link used to process requests. This attribute can
be multi-valued, with one database or database link per value. This attribute is required when
the value of the nsslapd-state attribute is set to backend or referral on update.
The value should be the name of the backend database entry instance under cn=ldbm
database,cn=plugins,cn=config. For example:
o=NetscapeRoot,cn=ldbm database,cn=plugins,cn=config
Parameter Description
Entry DN cn=suffix, cn=mapping tree, cn=config
Valid Values Any valid partition name
Default Value None
Syntax DirectoryString
Example nsslapd-backend: userRoot
2.3.7. Replication Attributes under cn=replica, cn="suffixDN", cn=mapping tree, cn=config
Replication configuration attributes are stored under cn=replica, cn=suffix, cn=mapping
tree, cn=config. The cn=replica entry is an instance of the nsDS5Replica object class. For
replication configuration attributes to be taken into account by the server, this object class (in addition
to the top object class) must be present in the entry. For further information about replication, see the
"Managing Replication" chapter in the Directory Server Administrator's Guide.
2.3.7.1. nsDS5Flags
This attribute sets replica properties that were previously defined in flags. At present only one flag
exists, which sets whether the log changes.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Values 0 | 1
0 means no changes are logged
1 means changes are logged
Default Value 0
Syntax Integer
Example nsDS5Flags: 0
79
Page 94

Chapter 2. Core Server Configuration Reference
2.3.7.2. nsds5DebugReplicaTimeout
This attribute gives an alternate timeout period to use when the replication is run with debug logging.
This can set only the time or both the time and the debug level:
nsds5debugreplicatimeout: seconds[:debuglevel]
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Values Any numeric string
Default Value
Syntax DirectoryString
Example nsds5debugreplicatimeout: 60:8192
2.3.7.3. nsDS5ReplConflict
Although this attribute is not in the cn=replica entry, it is used in conjunction with replication.
This multi-valued attribute is included on entries that have a change conflict that cannot be resolved
automatically by the synchronization process. To check for replication conflicts requiring administrator
intervention, perform an LDAP search for (nsDS5ReplConflict=*). For example:
ldapsearch -D cn=directory manager -w password -s sub -b dc=example,dc=com
"(|(objectclass=nsTombstone)(nsDS5ReplConflict=*))" dn nsDS5ReplConflict nsUniqueID
Using the search filter "(objectclass=nsTombstone)" also shows tombstone (deleted) entries.
The value of the nsDS5ReplConflict contains more information about which entries are in conflict,
usually by referring to them by their nsUniqueID. It is possible to search for a tombstone entry by its
nsUniqueID. For example:
ldapsearch -D cn=directory manager -w password -s sub -b dc=example,dc=com "(|
(objectclass=nsTombstone)(nsUniqueID=66a2b699-1dd211b2-807fa9c3-a58714648))"
2.3.7.4. nsDS5ReplicaAutoReferral
This attribute sets whether the Directory Server follows configured referrals for the database.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Values on | off
Default Value
Syntax DirectoryString
Example nsDS5ReplicaAutoReferral: on
2.3.7.5. nsDS5ReplicaBindDN
This multi-valued attribute specifies the DN to use when binding. Although there can be more than one
value in this cn=replica entry, there can only be one supplier bind DN per replication agreement.
80
Page 95

Replication Attributes under cn=replica, cn="suffixDN", cn=mapping tree, cn=config
Each value should be the DN of a local entry on the consumer server. If replication suppliers are using
client certificate-based authentication to connect to the consumers, configure the certificate mapping
on the consumer to map the subjectDN in the certificate to a local entry.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Values Any valid DN
Default Value
Syntax DirectoryString
Example nsDS5ReplicaBindDN: cn=replication manager,
cn=config
2.3.7.6. nsDS5ReplicaChangeCount
This read-only attribute shows the total number of entries in the changelog and whether they still
remain to be replicated. When the changelog is purged, only the entries that are still to be replicated
remain.
See Section 2.3.7.10, “nsDS5ReplicaPurgeDelay” and Section 2.3.7.13,
“nsDS5ReplicaTombstonePurgeInterval” for more information about purge operation properties.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Range -1 to maximum 32-bit integer (2147483647)
Default Value
Syntax Integer
Example nsDS5ReplicaChangeCount: 675
2.3.7.7. nsDS5ReplicaId
This attribute sets the unique ID for suppliers in a given replication environment.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Range 0 to 65534
Default Value
Syntax Integer
Example nsDS5ReplicaId: 1
2.3.7.8. nsDS5ReplicaLegacyConsumer
If this attribute is absent or has a value of false, then it means that the replica is not a legacy
consumer.
81
Page 96

Chapter 2. Core Server Configuration Reference
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Values true | false
Default Value false
Syntax DirectoryString
Example nsDS5ReplicaLegacyConsumer: false
2.3.7.9. nsDS5ReplicaName
This attribute specifies the name of the replica with a unique identifier for internal operations. If it is not
specified, this unique identifier is allocated by the server when the replica is created.
NOTE
It is recommended that the server be permitted to generate this name. However, in
certain circumstances, for example, in replica role changes (master to hub etc.), this
value needs to be specified. Otherwise, the server will not use the correct changelog
database, and replication fails.
This attribute is destined for internal use only.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Values
Default Value
Syntax DirectoryString (a UID identifies the replica)
Example nsDS5ReplicaName:
66a2b699-1dd211b2-807fa9c3-a58714648
2.3.7.10. nsDS5ReplicaPurgeDelay
This attribute controls the maximum age of deleted entries (tombstone entries) and state information.
The Directory Server stores tombstone entries and state information so that when a conflict occurs in a
multi-master replication process, the server resolves the conflicts based on the timestamp and replica
ID stored in the change sequence numbers.
An internal Directory Server housekeeping operation periodically removes tombstone entries
which are older than the value of this attribute (in seconds). State information which is older than
the nsDS5ReplicaPurgeDelay value is removed when an entry which contains the the state
information is modified.
Not every tombstone and state information may be removed because, with multi-master replication,
the server may need to keep a small number of the latest updates to prime replication, even if they are
older than the value of the attribute.
82
Page 97

Replication Attributes under cn=replica, cn="suffixDN", cn=mapping tree, cn=config
This attribute specifies the interval, in seconds, to perform internal purge operations on an entry. When
setting this attribute, ensure that the purge delay is longer than the longest replication cycle in the
replication policy to preserve enough information to resolve replication conflicts and to prevent the
copies of data stored in different servers from diverging.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Range 0 (keep forever) to maximum 32-bit integer
(2147483647)
Default Value 604800 [1 week (60x60x24x7)]
Syntax Integer
Example nsDS5ReplicaPurgeDelay: 604800
2.3.7.11. nsDS5ReplicaReferral
This multi-valued attribute specifies the user-defined referrals. This should only be defined on a
consumer. User referrals are only returned when a client attempts to modify data on a read-only
consumer. This optional referral overrides the referral that is automatically configured by the consumer
by the replication protocol.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Values Any valid LDAP URL
Default Value
Syntax DirectoryString
Example nsDS5ReplicaReferral: ldap://ldap.example.com
2.3.7.12. nsDS5ReplicaRoot
This attribute sets the DN at the root of a replicated area. This attribute must have the same value as
the suffix of the database being replicated and cannot be modified.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Values Suffix of the database being replicated, which is
the suffix DN
Default Value
Syntax DirectoryString
Example nsDS5ReplicaRoot: "dc=example,dc=com"
2.3.7.13. nsDS5ReplicaTombstonePurgeInterval
This attribute specifies the time interval in seconds between purge operation cycles.
83
Page 98

Chapter 2. Core Server Configuration Reference
Periodically, the server runs an internal housekeeping operation to purge old update
and state information from the changelog and the main database. See Section 2.3.7.10,
“nsDS5ReplicaPurgeDelay”.
When setting this attribute, remember that the purge operation is time-consuming, especially if the
server handles many delete operations from clients and suppliers.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Range 0 to maximum 32-bit integer (2147483647) in
seconds
Default Value 86400 (1 day)
Syntax Integer
Example nsDS5ReplicaTombstonePurgeInterval: 86400
2.3.7.14. nsDS5ReplicaType
Defines the type of replication relationship that exists between this replica and the others.
Parameter Description
Entry DN cn=replica, cn=suffixDN, cn=mapping tree,
cn=config
Valid Values 0 | 1 | 2 | 3
0 means unknown
1 means primary (not yet used)
2 means consumer (read-only)
3 consumer/supplier (updatable)
Default Value
Syntax Integer
Example nsDS5ReplicaType: 2
2.3.7.15. nsDS5ReplicaReapActive
This read-only attribute specifies whether the background task that removes old tombstones (deleted
entries) from the database is active. See Section 2.3.7.13, “nsDS5ReplicaTombstonePurgeInterval” for
more information about this task. A value of 0 means that the task is inactive, and a value of 1 means
that the task is active. The server ignores the modify request if this value is set manually.
Parameter Description
Entry DN cn=replica,cn="suffixDN”,cn=mapping
tree,cn=config
Valid Values 0 | 1
Default Value
Syntax Integer
Example nsDS5ReplicaReapActive: 0
84
Page 99

Replication Attributes under cn=ReplicationAgreementName, cn=replica, cn="suffixName", cn=mapping tree, cn=config
2.3.7.16. nsds5Task
This attribute is used to launch a replication task, such as dumping the database contents to LDIF.
This is used internally by the Directory Server supplier.
2.3.7.17. nsState
This attribute stores information on the state of the clock. It is designed only for internal use to ensure
that the server cannot generate a change sequence number (csn) inferior to existing ones required for
detecting backward clock errors.
2.3.8. Replication Attributes under cn=ReplicationAgreementName, cn=replica, cn="suffixName", cn=mapping tree, cn=config
The replication attributes that concern the replication agreement are stored under
cn=ReplicationAgreementName, cn=replica, cn=suffixDN, cn=mapping tree, cn=config.
The cn=ReplicationAgreementName entry is an instance of the nsDS5ReplicationAgreement
object class. Replication agreements are configured only on supplier replicas.
2.3.8.1. cn
This attribute is used for naming. Once this attribute has been set, it cannot be modified. This attribute
is required for setting up a replication agreement.
Parameter Description
Entry DN cn=ReplicationAgreementName, cn=replica,
cn=suffixDN, cn=mapping tree, cn=config
Valid Values Any valid cn
Default Value
Syntax DirectoryString
Example cn: MasterAtoMasterB
2.3.8.2. description
Free form text description of the replication agreement. This attribute can be modified.
Parameter Description
Entry DN cn=ReplicationAgreementName, cn=replica,
cn=suffixDN, cn=mapping tree, cn=config
Valid Values Any string
Default Value
Syntax DirectoryString
Example description: Replication Agreement between
Server A and Server B.
2.3.8.3. nsDS5ReplicaBindDN
This attribute sets the DN to use when binding to the consumer during replication. The value of
this attribute must be the same as the one in cn=replica on the consumer replica. This may be
85
Page 100

Chapter 2. Core Server Configuration Reference
empty if certificate-based authentication is used, in which case the DN used is the subject DN of the
certificate, and the consumer must have appropriate client certificate mapping enabled. This can also
be modified.
Parameter Description
Entry DN cn=ReplicationAgreementName, cn=replica,
cn=suffixDN, cn=mapping tree, cn=config
Valid Values Any valid DN (can be empty if client certificates
are used)
Default Value
Syntax DirectoryString
Example nsDS5ReplicaBindDN: cn=replication manager,
cn=config
2.3.8.4. nsDS5ReplicaBindMethod
This attribute sets the method for the server to use to bind to the consumer server.
Parameter Description
Entry DN cn=ReplicationAgreementName, cn=replica,
cn=suffixDN, cn=mapping tree, cn=config
Valid Values SIMPLE | SSLCLIENTAUTH
The SIMPLE bind method requires a DN and
password.
Default Value SIMPLE
Syntax DirectoryString
Example nsDS5ReplicaBindMethod: SIMPLE
2.3.8.5. nsDS5ReplicaBusyWaitTime
This attribute sets the amount of time in seconds a supplier should wait after a consumer sends back
a busy response before making another attempt to acquire access. The default value is three (3)
seconds. If the attribute is set to a negative value, Directory Server sends the client a message and an
LDAP_UNWILLING_TO_PERFORM error code.
The nsDS5ReplicaBusyWaitTime attribute works in conjunction with the
nsDS5ReplicaSessionPauseTime attribute. The two attributes are designed so that the
nsDS5ReplicaSessionPauseTime interval is always at least one second longer than the interval
specified for nsDS5ReplicaBusyWaitTime. The longer interval gives waiting suppliers a better
chance to gain consumer access before the previous supplier can re-access the consumer.
Set the nsDS5ReplicaBusyWaitTime attribute at any time by using changetype:modify with the
replace operation. The change takes effect for the next update session if one is already in progress.
Parameter Description
Entry DN cn=ReplicationAgreementName, cn=replica,
cn=suffixDN, cn=mapping tree, cn=config
86
 Loading...
Loading...