Page 1

QNAP Turbo NAS
TS- ECx80 Series Hardware User Manual
© 2014. QNAP Systems, Inc. All Rights Reserved.
Page 2
Thank you for choosing QNAP produ cts! T his user manual provid es description of the
hardware of the Turbo NAS and relevant guideline of certain functions. Please read
carefully and strictly adhere to the instructions of the manual.
This user manual is applicable to the following Turbo NAS mode ls:
TS-EC880 Pro, TS-EC1080 Pro, TS-EC2480U-RP, TS-EC1680U-RP, TS-EC1280U-RP,
TS-EC880U-RP
NOTE
• The “Turbo NAS” is hereafter referred to as “NAS”.
• The product you purchased may not support certain functions dedicated to specific
models.
• All features, functionality, and other product specifications are subject to change
without p rior notice or obligation.
• Information presented is subject to change without notice.
• No part of this publication may be reproduced, stored in a retrieval system, or
transmit ted , in a ny form or by any means, mechanical, electronic, photocopying,
recording, or otherwise , without prior written permission of QNAP Systems, Inc.
• QNAP and the QNAP logo are registered trademarks of QNAP Systems, Inc. Other
products and company names mentioned herein may be the trademarks of their
respective companies.
2
Page 3
DISCLAIMER
In no ev en t sha ll QN AP S ys tem s, Inc . (Q N AP) lia bil i ty e xce ed t he p ri ce pa id fo r the pro d uc t
from direct, indirect, special, incidental, or consequential damages resulting from the use
of the pr odu ct, its accompanying software, or its documentation . QNAP makes no
warr anty or repre se ntatio n, e xpres sed, imp lied, or stat utory, wit h resp ect to i ts pr od ucts or
the co n tents or us e o f this doc umentatio n and all acc o mp anying softwar e, a nd specific ally
disclaims its quality, performan ce, merchantability, or fitness for any particular purpose.
QNAP reserv e s the right to revise or update its products, software, or documentation
without obligation to notify any individual or entity.
Note:
Back up your sys tem perio dica ll y to avoid any potential data loss. QNAP disclaims
any resp onsibility of all sorts of data loss or recove ry.
Should you return any components of the NAS package for refund or maintenance,
make sure they are carefully packed for shipping. Any form of damages due to
improper packaging will not be compensated.
3
Page 4
Regulatory Notice
FCC Notice
The QNAP NAS complies w it h di ffer e n t F CC compliance c lasse s. Please refer to Appendix A
for de tai ls. Onc e the c lass o f th e d ev ice is d e ter mine d, re fe r to the f ol low ing co rre spo nd ing
statement.
=======================================================
FCC Class A Notice
This device complie s with P art 15 of th e FCC R ules. Opera tion is s ubjec t to the follow ing two
conditions:
1. This device may not cause harmful interference.
2. This device must accept any interference received, including interference that may
cause undesired operation.
Note: This equipment has been tested and found to comply with the limits for a Class A
digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to provide
reasonable protection against harmful interference when the equipment is operated in a
commer cia l e nviron me nt. T his eq uipm en t gener a tes, uses, and ca n ra dia te r adio freq uenc y
energy, a nd if not ins tal led and used i n a cco rda n ce w it h t he ins tr uctio n ma n ual, m ay ca use
harmfu l inter fere nce to rad io comm unica tions . Op eratio n of th is equ ipmen t i n a res ide nt ial
area is likely to cause harmful interference, in which case the user will be required to
correct the interference at his own expense.
Modifications: Any modifications made to this device that are not approved by QNAP
Systems, Inc. may void the authority granted to the user by the FCC to operate this
equipment.
4
Page 5

FCC Class B Notice
This de vice co mplie s with P art 15 of the FCC R ules. Op eratio n is sub ject to the fo llowing two
conditions:
1. This device may not cause harmful interference.
2. This device must accept any interference received, including interference that may
cause undesired operation.
Note: This equipment has been tested and found to comply with the limits for a Class B
digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to provi de
reasonable protection against harmful interference in a residential installation. This
equipment generates, uses, and can radiate radio frequency energy and, if not installed
and used in accordance with the instructions, may cause harmful interference to radio
communications. However, there is no guarantee that interference will not occur in a
particular installation. If this equipment does cause harmful interferenc e to radio or
television reception, which can be determined by turning the equipment off and on, the
user is encouraged to try to corr ect the interference by one or more of the following
measures:
Reorient or relocate the receiving antenna.
Increase the separation between the equipment and receiver.
Connec t the equipment into an outlet on a circuit different from that to which the
receiver is connected.
Consult the dealer or an experienced radio/television technician for help.
Modifications: Any modifications made to this device that are not approved by QNAP
Systems, Inc. may void the authority granted to the user by the FCC to operate this
equipment.
CE NOTICE
The QNAP NAS complies with different CE compliance classes. Please refer to A ppendix A
for det ail s.
5
Page 6
Symbols in thi s d ocument
Warning
This icon indicates the instructions must be strictly followed.
failure to follow the instructions could result in data damage, disk
Failure to do so coul d result in injury to huma n body or death.
This icon indicates the action may lead to disk clearance or loss OR
Caution
damage, or product damage.
6
Page 7

Table of Contents
Safety Warnings ................................................................................................. 8
Chapter 1. CPU and Memory Specifications ..................................................... 9
Chapter 2. Power Button and Reset Button Behavior .................................... 11
Chapter 3. USB One Touch C op y .................................................................... 13
Chapter 4. LED and Alarm Buzzer Specificati ons ........................................... 14
Chapter 5. Upgrade Memory on QNAP Turbo NAS (RAM Modul e I nstallation) 17
5.1 TS-EC2480U-RP, TS-EC1680U-RP, TS-EC1280U-RP, TS-EC880U-RP ............... 17
5.2 TS-EC880 PRO, TS-EC1080 PRO ................................................................ 20
Chapter 6. Network Expansi on Card Installatio n ........................................... 23
6.1 TS-EC880 PRO, TS-EC1080 PRO ................................................................ 23
6.2 TS-EC2480U-RP, TS-EC1680U-RP, TS-EC1280U-RP, TS-EC880U-RP ............... 27
Chapter 7. Install an mSATA Flash module to the NA S. ................................. 29
7.1 TS-EC2480U-RP, TS-EC1680U-RP, TS-EC1280U-RP, TS-EC880U-RP ............... 29
7.2 TS-EC880 PRO, TS-EC1080 PRO ................................................................ 33
Chapter 8. Hot-swap Hard Drives .................................................................. 36
Chapter 9. RAID Recovery ............................................................................. 38
Chapter 10. Use the LCD Panel ........................................................................ 40
Chapter 11. Install Power Supply Unit ............................................................. 46
Technical Supp ort ............................................................................................ 49
Appendix A. Product Compliance Class ............................................................. 50
GNU GENERAL PUBLIC LICENSE ....................................................................... 51
7
Page 8
Safety Warnings
1. The NAS can operate normally in temperatures of 0ºC–40ºC (32ºF -104ºF) and
relati ve h um idi ty of 5%–95%. Please make sur e the e n vi ronm en t is w el l-ventilated.
2. The power cord and de vices co nnected to the NA S must pro vide correct supply voltage
(100W, 90–264V).
3. Do not pla ce the N AS in d irect s unligh t or ne ar che micals. Mak e sure the tem pera ture
and humidity of the environment are in optimized level.
4. Unplug the power cord and a ll con nec ted cab le s befo re c leani ng. Wipe the NAS with
a dry tow el. Do not us e c h e m ic a l or ae r o sol to clean the NAS.
5. Do not place any objects on the NAS for the server’s normal operation and to avoid
overheat.
6. Use the flat head screw s in the prod uct package t o lock the hard di sks in the NAS when
installing hard disks for proper operation.
7. Do not place the NAS near any liquid.
8. Do not place the NAS on any uneven su rface to avoid falling off and damage.
9. Make sure the voltage is correct in the location where the NAS is installed. Contact
th e distributor or the local power supply company for the information.
10. Do not place any object on the power cord.
11. Do not attempt to repair the NAS in any occasions. Improper disassembly of the
product may expose the users to electric shock or other risks. For any enquiries,
please contact the distributor.
12. The c hass is NA S mo dels sho uld o nly be i nstal led in th e ser ver roo m and ma inta ined b y
the authorized server manager or IT administrator. The server room is locked by key
or keycard access and only certified staff is allowed to enter the server room.
Warning:
Danger of explosion if battery is incorrectly replaced. Replace only with the same or
equivalent type reco mme nded by the man ufac t urer. Dispose of used batteries
accord i ng to the manufac turer’s ins tructions.
Do NOT touch the fan inside the system to avoid serious injuries.
8
Page 9

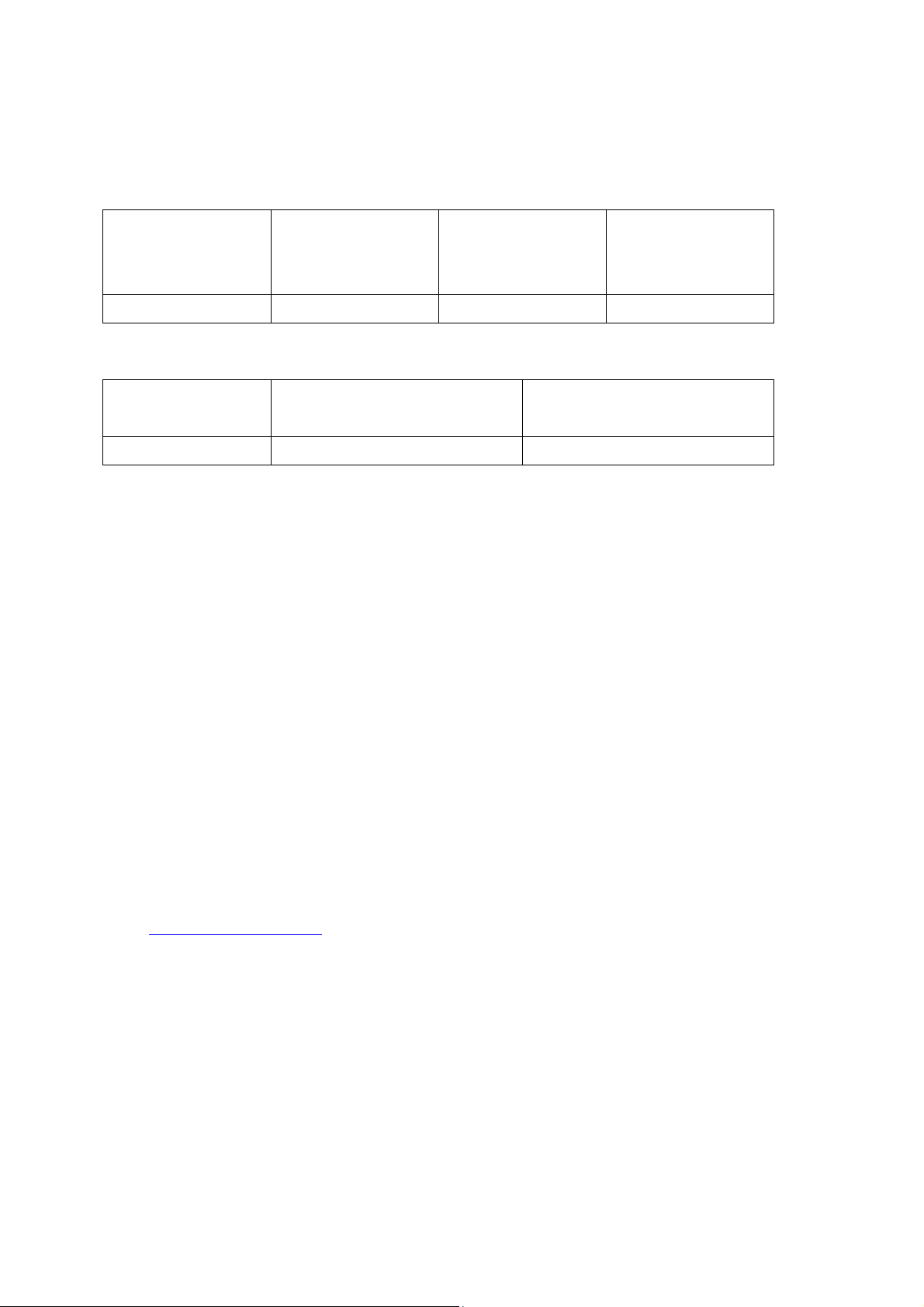
Chapter 1. CPU and Memory Specifications
n
1200 v3
n
1200 v3
n
1200 v3
Caution: Modifying the hardwa re, software, or firmware of the QNAP product s will
void the warranty . QNAP is not responsible for any form of damage or loss of data caused
by modding the QNAP products. Us ers should bear their own risks of all sorts of poss ib le
data loss o r s yst em in stab il itie s d ue to cha ng ing the hard w are p a rts, mo di fy ing the de fau lt
system f ir mwa r e or insta l ling any una ut hor ized t hird p a rty app lica tio ns o n QN AP pro duc ts.
System TS-EC880 Pro
Quad-Core Intel Xeo
CPU
Memory 2GB DDR3 ECC RAM 2GB DDR3 ECC RAM 4GB DDR3 ECC RAM
Flash 512MB (USB DOM) 512MB (USB DOM) 512MB (USB DOM)
CPU replaceable No No No
Memory
replaceable
Number of
LONG-DIMM slots
Number of hard
drive slots
Number of PCIe
slots
Processor E3Family
Yes Yes Yes
4 4 4
8 10 8
1 1 2
TS-EC1080 Pro TS-EC880U-RP
Quad-Core Intel Xeo
Processor E3Family
Quad-Core Intel Xeo
Processor E3Family
Number of internal
cache ports
9
2 2 2
Page 10

System TS-EC1280U-RP TS-EC1680U-RP TS-EC2480U-RP
n
1200 v3
n
1200 v3
n
1200 v3
Quad-Core Intel Xe o
CPU
Memory 4GB DDR3 ECC RAM 4GB DDR3 ECC RAM 4GB DDR3 ECC RAM
Flash 512MB (USB DOM) 512MB (USB DOM) 512MB (USB DOM)
CPU replaceable No No No
Memory
replaceable
Number of
LONG-DIMM slots
Number of hard
drive slots
Number of PCIe
slots
Number of internal
cache ports
Processor E3Family
Yes Yes Yes
4 4 4
12 16 24
2 2 2
2 2 2
Quad-Core Intel Xeo
Processor E3Family
Quad-Core Intel Xeo
Processor E3Family
10
Page 11
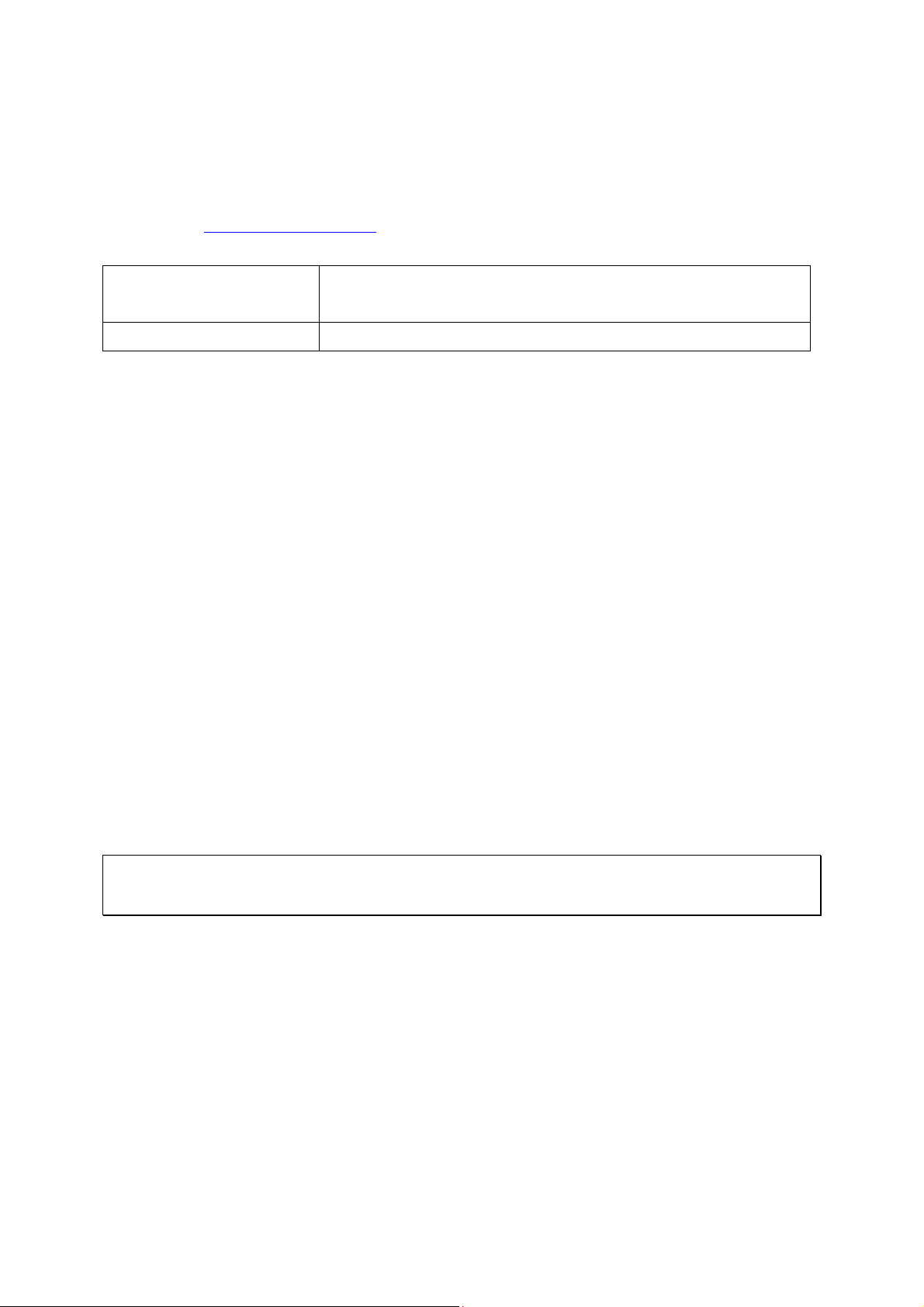
Chapter 2. Power Button and Reset Button Behavior
Power button: Press to turn on or turn off.
Power button
System
Power button
(Hardware turn
(Turn on)
Power button
(Force turn off)
off)
All models Press once 1.5 sec 5 sec
Reset button: Press to reset the system settings.
Basic system reset
Advanced system reset
System
(1 beep)
(2 beeps)
All models 3 sec 10 sec
Basic system reset (3 sec)
Press the reset button for 3 seconds, a beep sound will be heard. The following sett ings
are reset to default:
System administration password: admin
TCP/IP configuration: Obtain the IP address settings automatically via DHCP
TCP/IP configuration: Disable Jumbo Frame
TCP/IP configuration: If port trunking is enabled (dual LAN models only), the port
trunking mode will be reset to “Active Backup (Failover)”.
System Port: 8080 (system service port)
Security Lev el: Low (Allow all c onnections)
LCD panel password: ( bla nk ) *
VLAN will be disabled.
Service binding: All the NAS s ervices run on all available network interfaces.
*This feature is only provided by the NAS models with LCD panels. Please
http://www.qnap.com for details.
visit
11
Page 12

Advanced syst em reset (10 sec)
Press the reset button for 10 seconds; you will hear two beeps at the third and the tenth
seconds. The NAS will reset all the system settings to default as it does by web-based
system reset in “Control Panel” > “System Settings” > “Backup / Restore” > “Restore to
Factory Default” except all the data are reserved. The settings such as the users, user
groups, and the network share folders previously created will be cleared. To retrieve the
old data after the advanced system reset, create the same network share folders on the
NAS and the data will be accessible again.
12
Page 13
Chapter 3. USB One Touch Copy
This feature is only provided by the NAS models with a USB One Touch Copy button.
Please visit
System
All NAS models 0.5 sec
Data Copy by the Front USB Port
The NA S sup por ts i nstan t da ta cop y ba ckup fro m the exte rna l USB dev ice to the NA S or t he
other wa y ro und b y t he fro nt on e tou ch cop y bu tton. To u se th is fun ctio n, follo w the step s
below:
1. Make sure a hard drive is installed and formatted on the NAS. The default network
share Qusb or Usb is created.
2. Turn on the NAS.
3. Configure the be ha vior o f the Co py b u tton o n “Backup Station” > “External Backup” >
“USB one touch copy” page.
http://www.qnap.com for details.
Number of seco nds (press the one touch copy button
to trigger data copy)
4. Connect the USB storage device to the front USB port of the NAS.
5. Press the Copy button. The USB LED will flash. The data will be copied to or from
the USB device according to the NAS settings.
Note: Thi s f eature adopts incr e m ental bac kup. After the first tim e d ata bac kup, the N A S
only copies the changed files since the last backup.
13
Page 14
Chapter 4. LED and Alarm Buzzer Specifications
Online RAID leve l migr atio n is in pro cess.
(2 membe r drives fa il in a RAID 5 or RAID
All the hard drives on the NAS are in standby
The disk data is being accessed from the
network and a read/write error occurs during
the process.
The LED ind ica to rs o f t he N AS i ndic at e the sys te m s tat us a nd inf orma tio n. When the NAS
is turne d on, c h e ck the follow ing items to make sure the s ystem stat us is normal. Note
that th e fo llowi ng L ED in forma tio n is a ppl icab le o nly w hen u sers hav e pro perly ins talle d th e
hard drive, and connected the NAS to the network and the power supply.
LED Color LED Status Description
1. The hard drive on the NAS is being
formatted.
2. The NAS is be i ng in itialized .
3. The system firmware is being updated.
4. RAID rebuilding is in process.
5. Online RAID capacity expansion is in
process.
6.
1. The hard drive is invalid.
2. The disk volume has reached its full
capacity.
3. The disk volume is goin g to b e full.
4. The system fan is out of function.
5. An error occurs when accessing
(read/write) the disk data.
6. A bad sector is detected on the hard
drive.
7. The NAS is in degraded read-only mode
6 configuration, the disk data can still be
read).
8. Hardware self-test error.
System
Status
Flashes green
and red
alternately
every 0.5 sec
Red
Red/
Green
Flashes red
every 0.5 sec
Flashes green
every 0.5 sec
Green The NAS is ready.
Deep flashes
of orange
Off
LAN Orange Orange
14
The NAS is in degraded mode (one member
drive fails in RAID 1, RAID 5 or RAID 6
configuration).
1. The NAS is sta r ting up.
2. The NAS is not configured.
3. A hard disk drive is not fo rm atted.
The NAS is in sleep mode.
mode.
Page 15

LED Color LED Status Description
installed.
No 10Gb E netwo rk expa nsio n card is i nsta lled.
The NAS ha s fi nis hed cop ying the da ta to
10 GbE Green
HDD
Red/
Green
USB Blue
Flashes
orange
Green
The NAS is connec ted to the ne two rk.
The 10GbE network expansion card is
Off
Flashes red The NAS is being accessed from the network.
Red A hard drive read/write error occurs.
Flashes green The disk data is being accessed.
Green The hard drive can be accessed.
1. A USB device (connected to the front USB
port) is being detected.
2. A USB device (connected to the front USB
Flashes blue
every 0.5 sec
port) is being removed from the NAS.
3. The USB device (connected to the front
USB port of the NAS) is being accessed.
4. The data is being copied to or from the
external USB or eSATA device.
Blue
A front USB device is detected (after the
device is mounted).
eSATA Orange
Storage
Expansion
Orange
Port
1
Status
1. No USB device is detected.
Off
2.
or from the USB d ev ice connected to th e
front USB port.
Flashes
orange
The eSATA device is being accessed.
Off No eSATA device can be detected.
Off No expansion enclosures are detected.
Orange Expansion enclosures are detected.
1
The sto r age exp ansio n port st atu s LED i s onl y s up por te d by the TS-EC2480U-RP, TS-EC1680U-RP,
TS-EC1280U-RP, TS-EC880U-RP.
15
Page 16

Beep alarm: All NAS models
1. The NAS is sta r ting up.
updated.
The disk volume has reached its full
The NAS has been turned on and is
The beep alarm can be disabled in “Control Panel” > “System Settings” > “Hardware”.
Beep sound Number of Times Description
2. The NAS is being shut down
(softw are shutdown).
Short beep (0.5 sec) 1
Short beep (0.5 sec) 3
Long beep (1.5 sec) 3, every 5 min The system fan is out of function.
2
Long beep (1.5 sec)
3. The user presses the reset butto n to
reset the NAS.
4. The system firmware has been
The NAS data cannot be copied to the
external storage device from the front
USB po rt.
1. The disk volume is goin g to b e full.
2.
capacity.
3. T he hard driv es on th e NAS are in
degraded mode.
4. The user starts the hard drive
rebuilding process.
5. A hard drive is plugged in or out.
1
1. The NAS is turned off by force
shutdown (hardware shutdown).
2.
ready.
16
Page 17

Chapter 5. Upgrade Memory on QNAP Turbo NAS (RAM Module
Installation)
Warning:
The following instructions should only be performed by an authorized and trained
technician.
Strictly adhere to the instructions to install a RAM module on the NAS. Failure to do
so could r es ult in injury to human body or death.
QNAP provi des RAM module (optional purchase) for users to upgrade the memory of the
NAS. Insert an extra RAM mo dule on the mother board of the NAS to upgr ade the memory .
The total memory will be shown in “System Information” of the administration page.
5.1 TS-EC2480U-RP, TS-EC1680U-RP, TS-EC1280U-RP, TS-EC880U-RP
17
Page 18

1. Turn off the NAS. Disconnect the power adaptor, network cable(s), and any other
connectors or cables from the NAS.
2. Be fore installing the network expansion card, put on an antistatic wrist strap to
prevent electrostatic discharge. The crocodile clip should be connected to the ground.
3. Loosen the 2 screws on the rear of the NAS as shown in the illustration.
4. Hold the handle pulled backwards to remove the Motherboard Drawer.
18
Page 19

5. Release the ejector clips gently by pulling them out of the sides of the RAM slot.
6. Grasp the edge of the RAM module. A lign the notch on the gold edge of the RAM
module with the notch in the RAM slot. Insert the RAM module to the RAM slot until
it cannot go any further.
7. Insert the Motherboard Drawer, push the handle, locking NAS rear two screws.
19
Page 20

5.2 TS-EC880 Pro, TS-EC1080 Pro
1. Turn off the NAS. Disconnect the power a daptor, network cable(s), and any other
connectors or cables from the NAS.
2. Before installing the network expansion card, put on an antistatic wrist strap to
prevent electrostatic discharge. The crocodile clip should be connected to the
ground.
3. Loosen the seven screws on the rear of the NAS.
20
Page 21

4. Remove the case cover of the NAS gently.
5. Loosen the cable
21
Page 22

6. Release the ejector clips gently by pulling them out of the sides of the RAM slot.
7. Grasp the edge of the RAM module. Align the notch on the gold edge of the RAM
module with the notch in the RAM slot. Insert the RAM module to the RAM slot until
it cannot go any further.
8. Installed on the NAS enclosure, locking rear of the seven screws NAS.
22
Page 23

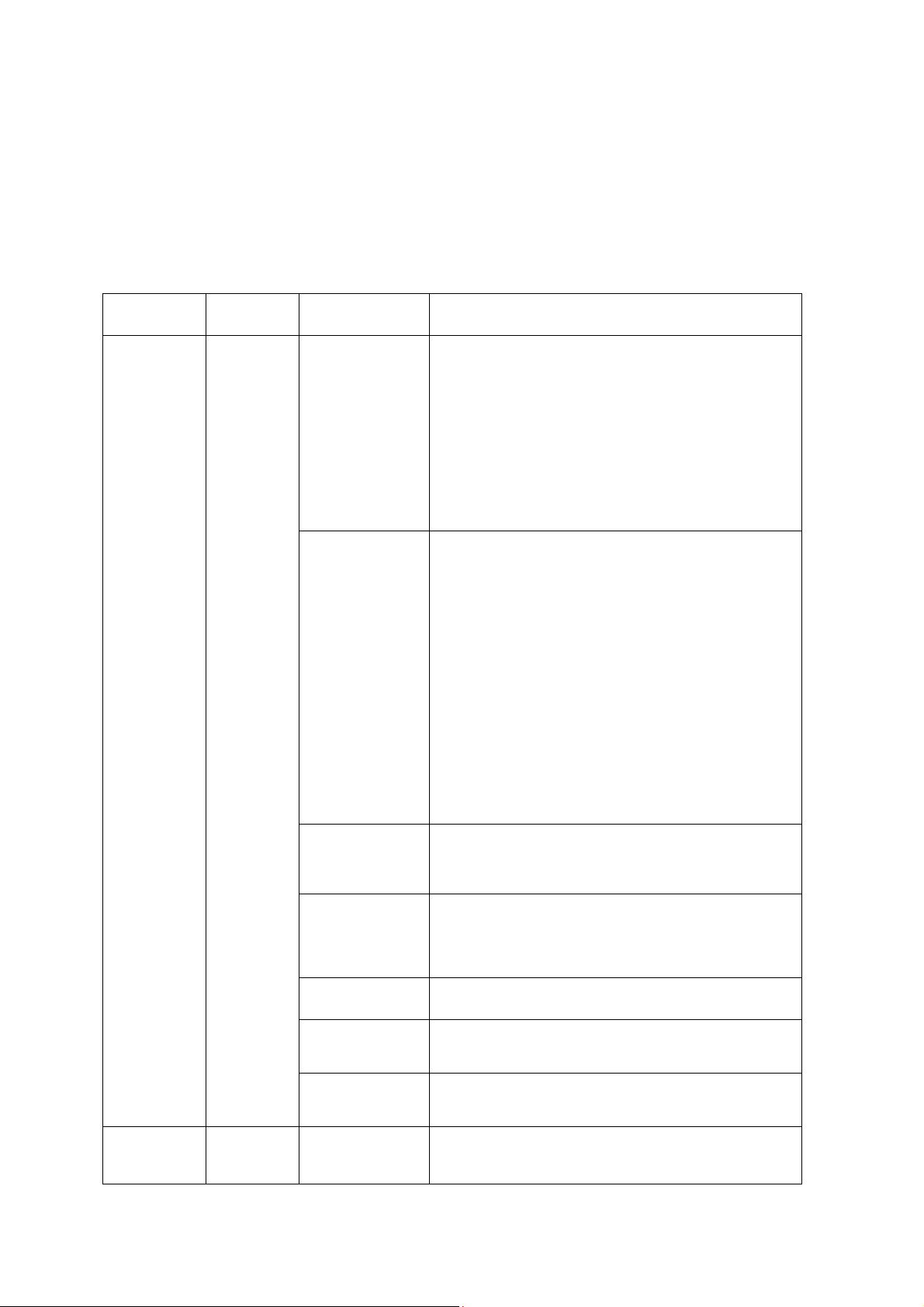
Chapter 6. Network Expansion Card Installation
Warning:
The following instructions should only be performed by an authorized and trained
technician.
Strictly adhere to the instructions to install a network expansion card on the NAS.
Failure to do so could result in inju ry to human body or death.
The TS-x80 series provides expansion slots for network expansion. Insert an extra
network expansion card (optional purchase) to the motherboard of the NAS to increase the
network bandwidth.
6.1 TS-EC880 Pro, TS-EC1080 Pro
Please refer to the compatibility table below and replace a proper bracket for the network
expansion card.
Brac ket A Bracket B Bracket C
23
Page 24

Network Expansion Card Compatibility
Bracket A (X520-T2) Intel® Ether net Ser ver Adapter X520-T2 (E10G42B)
Brac ket B
(X520-SR2/X520-DA2)
Bracket C (Emulex) 1. Emulex OneConnect 10GbE Network Adapters, SFP+
1. Turn off the NAS. Disconnect the power adaptor, network cable(s), and any other
connectors or cables from the NAS.
2. Before installing the network expansion card, put on an antistatic wrist strap to
1. Intel® Ethernet Server Adapter X520-SR2
(E10G42BFSR)
2. Intel® Ethernet Server Adapter X520-DA2
(E10G42BTDA)
Direct attach copper (OCe11102-NX)
2. Emulex OneConnect 10GbE Network Adapters, Short
reach o ptical (OCe11102-NM)
3. Emulex OneConnect 10GbE Network Adapters, SFP+
Direct attach copper (OCe11102-IX)
4. Emulex OneConnect 10GbE Network Adapters, Short
reach o ptical (OCe11102-IM)
prevent electrostatic discharge. The crocodile clip should be con ne cted to the
ground.
3. Loosen the seven screws on the rear of the NAS.
24
Page 25

4. Remove the case cover of the NAS g en tly.
5. Loosen the screws and remove the expansion slot cover.
25
Page 26

6. Grasp the edge of the network expansion card. Align the notch on the gold edge of
the card with the notch in the PCIe slot. Insert the network expansion card to the
PCIe slot until it cannot g o any further.
7. Fasten th e screw s.
8. Close the case co ver and fa sten the s crews. Connect the p ower adaptor and cables to
th e NAS.
9. T o c hec k tha t the n etwo rk exp a nsio n is re cog ni ze d by th e N AS, p owe r up the N AS a nd
login the web interface as an administrator . Go to “Control Panel” > “System Settings”
> “Network” > “TCP/I P ” an d check the total number of network interfaces.
26
Page 27

6.2 TS-EC2480U-RP, TS-EC1680U-RP, TS-EC1280U-RP, TS-EC880U-RP
1. Turn off the NAS. Disconnect the power adaptor, network cable(s), and any other
connectors or cables from the NAS.
2. Before installing the network expansion card, put on an antistatic wrist strap to
prevent electrostatic discharge. The crocodile clip should be connected to the ground.
3. Loosen the 2 screws on the rear of the NAS as shown in the illustration.
4. Hold the handle pulled backwards to remove the Motherboard Drawer.
27
Page 28

5. Loosen the screw and remove the expansion slot cover.
6. Insert the ne tw ork ex pan sio n c ard to th e P CIe sl ot u nti l i t ca nno t go a ny fur th er. The n
fasten the screw.
7. Push back Motherboard Drawer. Then fasten the screw.
8. Con nect the power adaptor and cables to th e NAS.
9. To c hec k tha t the ne two rk e xp an sio n is re cog nize d by the N A S, pow er up the N AS a nd
login the web interface as an administrator . Go to “Contro l Pane l” > “System Settings”
> “Network” > “TCP/IP” and check the total number of network interfaces.
28
Page 29

Chapter 7. Install an mSATA Flash module to the NAS.
Warning:
The following instructions should only be performed by an authorized and trained
technician.
Stric tl y adhere to the in s tructions to install a mSATA module on the NAS. Failure to
do so could result in injury to human body or death.
7.1 TS-EC2480U-RP, TS-EC1680U-RP, TS-EC1280U-RP, TS-EC880U-RP
1. Turn off the NAS. Disconnect the power adaptor, network cable(s), and any other
connectors or cables from the NAS.
29
Page 30

2. Loosen the 2 screws on the rear of the NAS as shown in the illustration.
3. Hold the hand le and pull backwards to remove the Moth erboard Drawer.
30
Page 31

4. Carefully g rasp the edge of the mSATA Flash Modul e. Align t he no tch on the gold
edge of the m SA T A module wit h the notch in t he mSA T A slot. Inser t the mSATA Flash
Module to the mSATA slot until it cannot go any further.
5. Insert the module fixing
6. Return the Motherboard Drawer to its normal position.
31
Page 32

7. Con nect the power adaptor and cables to th e NAS.
8. To c he c k that the mSATA Flash Module is recognized by the NAS, power up the NAS
and login to the web interface as an administrator. Go to “Control Panel” > “Storage
Manager” > “Disk” and check the “Internal Cache Port”.
32
Page 33

7.2 TS-EC880 Pro, TS-EC1080 Pro
1. Turn off the NAS. Disconnect the power adaptor, network cable(s), and any other
connectors or cables from th e NAS.
2. Before installing the network expansion card, put on an antistatic wrist strap to
preve nt elec trosta tic dis charge . The croco dile clip sho uld b e conne cted to a grounded
surface.
3. Loosen the seven screws on the rear of the NAS.
4. Remove the case cover of the NAS gently.
33
Page 34

5. Carefully g rasp the edge of the mSATA Flash Modul e. Align t he no tch on the gold
edge of the mSATA Flash Module with the notch in the mSATA slot. Insert the mSATA
Flash Module to the mSATA slot until it cannot go any further.
6. Insert and fasten screws in place as indicated.
34
Page 35

7. Close the case cover and fas ten the screws. Connect the power adap tor and cables to
th e NAS.
8. To c he c k that the mSATA Flas h Module is recognized by the NA S, power up the NAS
and login to the web interface as an administrator. Go to “Control Panel” > “Storage
Manager” > “Disk” and check the Internal Cache Port.
35
Page 36

Chapter 8. Hot-swap Hard Drives
System
Supports
Supports
Supports
Supports
only)
The QNAP NAS is compatible with 2.5-inch/3.5-inc h SATA hard drives from majo r hard
drive brands. For the upd a ted hard drive comp a tibility list, please
http://www.qnap.com.
visit
Caution:
QNAP disclaims any responsi bility for product damage/malfunction or data
loss/recovery due to misuse or improp er installati on of hard disks in any occasions for
any reasons.
Note that if a hard drive (new or used) which has never been installed on the NAS
before is insta lled, the hard drive will be f orm atte d and pa rtitio ned auto mat ically an d al l
the disk data will be cleared.
TS-EC880 Pro, TS-EC1080 Pro,
TS-EC2480U-RP, TS-EC1680U-RP,
TS-EC1280U-RP, TS-EC880U-RP
3.5-inch
SATA
Hard
Drives
2.5-inch
SATA
Hard
Drives
SSD
Hot-swap
ping
Hard
Drives
(RAID 1
or above
Yes Yes Yes Yes
36
Page 37

The NA S sup por ts hot -swapping t he hard drives when 1 me mber drive crashe s in RAID 1 or
1–2 member drives crash in RAID 5 or RAID 6. Follow the steps below to hot-swap the
hard drive when a member drive fails in a RAID configuration.
1. Login the NAS and c heck the storage pool status in “Storage Manager” > “Storage
Pools”.
2. The storage pool status shoul d be “Warning” and RAID group status should be
“Degraded”.
3. Prepare a new hard drive to replace the failed one. The capacity of the new hard drive
should be the same as or larger than the failed hard drive.
4. Unplug the failed drive from the NAS. Wait for about 20 s econds or until the s erver
beeps twice.
5. Remove the failed drive from the drive tray.
6. Install the ne w har d drive on the dr i v e tray. Insert it to the NAS.
7. The server should beep 1.5 seconds twice.
8. Check the volume status on the web admini stration page. The volume should be
rebuilding.
Warning: Users are strongly re commende d to turn OFF the serv er before rep lacing
the hard drive to reduce the risk of elec tric shock.
37
Page 38

Chapter 9. RAID Recovery
The QNAP NAS suppor ts recovery of a failed RAID group from unintentional disconnection
or removal of the hard drives from the system. Users can recover an inactive RAID 1,
RAID 5, or RAID 6 group to degraded mode, or an inactive RAID 0 and JBOD configuration
to normal.
Disk volume Supports RAID recov ery Maximum numbe r of disk
removal allowed
Single No JBOD Yes 1 or more
RAID 0 Yes 1 or more
RAID 1 Yes 1 or 2
RAID 5 Yes 2 or more
RAID 6 Yes 3 or more
RAID 10 No -
Follow the steps below to recover an inactive RAID group on the NAS:
1. Make sure the volume status of the RAID group is “Not active”.
2. Install the same hard drives, which have been formerly removed from the NAS, back
to the same hard drive slots.
3. Go to “Storage Manager” > “Storage Pools”. Select the degraded or inactive RAID
group. Click “Manage” > “Recover”.
4. Wait for about 1 minute for the process to complete. When finished, the NAS data
can be accessed.
Note:
• After re covering a RAID 1, RAID 5, or RAID 6 RAID group from “not active” to degraded
mode by RAID r ecove ry, users c an rea d or write the volume norm a lly. The volume
status will be recovered to normal after synchronization.
• If the disconnected drive member is damaged, the RAID recovery function will not
work.
38
Page 39

Standard
QNAP RAID 5 Standard
QNAP RAID 6
RAID 5
Degraded mode N-1 N-1 N-1 & N-2 N-1 & N-2
Read only
protection (for
immediate data
backup & hard
drive
replacement)
RAID recove ry
(RAID status: Not
active)
N/A N-1, bad blocks
found in the
surviving drives of
the array.
N/A If re-inserting all
the orig i na l ha rd
disk drives to the
NAS and they can
be spun up,
identified,
accessed, and the
hard drive
superblock is not
RAID 6
N/A N-2, bad blocks
found i n the
surviving drives of
the array.
N/A If re-inserting all
the orig i na l ha rd
disk drives to the
NAS and they can
be spun up,
identified,
accessed, and the
hard drive
superblock is not
damaged.
RAID crash N-2 N-2 failed hard
drive and any of
the rema ining hard
drives cannot be
spun up or
identified or
accessed.
N = Number of ha rd d isk drives in the array
damaged).
N-3 N-3 and any of the
remaining hard
drives cannot be
spun up or
identified or
accessed.
39
Page 40

Chapter 10. Use the LCD Panel
This feature is only provided by the NAS models with LCD panels. Please
http://www.qnap.com for details.
visit
The NAS pr ovides a handy LCD p anel for us e r s to perform disk config uration a nd v ie w t he
system in formation.
When the NAS has started up, the server name and IP address will be shown.
N A S 5 F 4 D E 3
1 6 9 . 2 5 4 . 1 0 0 . 1 0 0
For the first time ins ta lla tio n, the LCD panel s how s the numb er of har d dr iv es de tec ted and
the IP address. Configure the hard drives.
Number of hard
drives detected
1 Single Single
2 RAID 1 Single -> JBOD ->RAID 0 -> RAID 1
3 RAID 5 Single -> JBOD -> RAID 0 -> RAID 5
4 or ab ove RAID 5
*Press the “Select” button to choose the option, and press the “Enter” button to confirm.
Default disk
configuration
Available disk configuration options*
Single ->JBOD -> RAID 0 -> RAI D 5
-> RAID 6
40
Page 41

For example, when 5 hard dri v es installe d are a vailable o n the NAS, the LC D p anel shows:
C o n f i g . D i s k s ?
→
R A I D 5
Press the “Select” button to browse more options, for example, RAID 6.
Press the “Enter” button and the following message shows. Press the “Select” button to
select “Yes” to confirm.
C h o o s e R A I D 5 ?
→
Y e s N o
When RAID 1, RAID 5, or RAID 6 configuration is executed, the system will initialize the
hard drives, create t he RAID dev ice, format the RAID device, a nd mount it as a vo lume on
the NAS. The progress will be shown on the LCD panel. When it reaches 100%, the RAID
volume can be ac cesse d. Users ca n cre ate s hare folders a nd uplo ad file s to t he fo lders o n
the NAS . In the meant ime, to ma ke sure t he stripes and block s in all th e RAID co mponen t
devices are ready, the NAS will execute RAID synchronization and the progress will be
shown o n “ Storage Ma nager” > “Storage Pools” page. The synchronization rate is around
30–60 MB/s (vary by hard drive models, system resource usage, etc.).
Note: If a member drive of a RA ID co nf ig ura tion we re lo s t du ring the sy nch ro niz at ion, th e
RAID device will en ter degrad ed mo de. The volume data is still ac cess ib le. When a new
member drive is added, the NAS will start to rebuild. The status can be checked on the
“Volume Management” page.
To encrypt a disk volume*, select “Yes” when the LCD panel shows <Encrypt Volume?>.
The default encryption password is “admin”. To change the password, please login the
web-based administration interface as an adminis trator and change the settings in
“Storage Manag e r” > “Storage” > “Encryption” > “Change”.
E n c r y p t V o l u m e ?
→
Y e s N o
When the c onfiguration is finished, the se rver name and IP addres s will be shown. If the
NAS fails to create the disk volume, the following message will be shown.
C r e a t i n g . . .
R A I D 5 F a i l e d
41
Page 42

Note: The data encryption functions may not be available in accordance to the legislative
restrictions of some countries.
View system information by the LCD panel
When the LCD panel shows the server name and IP address, press the “Enter” button to
enter the Ma in Menu. The Main Menu consists of the following items:
1. TCP/IP
2. Physical disk
3. Volume
4. System
5. Shut down
6. Reboot
7. Password
8. B ack
1. TCP/IP
The follow ing options are av a ilable:
LAN1 IP Add re ss
LAN1 Sub ne t Mask
LAN1 Gateway
LAN 1 PRI. DNS
LAN 1 SEC. DNS
Enter Network Settings
Network Settings – DHCP
Network Settings – Static IP*
Network Settings – BACK
Back to Main Menu
* In Network Setti ngs – Static IP, users can configure the IP address, subnet mask,
gateway, and DNS of LAN 1 and LAN 2.
42
Page 43

2. Physical disk
The follow ing options are av a ilable:
Disk Info
Back to Main Menu
The disk info shows the temperature and the capacity of the hard drive.
D i s k : 1 T e m p : 5 0 ° C
S i z e : 2 3 2 G B
3. Volume
This section shows the disk configuration of the NAS. The first line shows the RAID
configurat ion and stora ge capacity; the second line sho ws t he me mber drive number
of the configuration.
R A I D 5 7 5 0 G B
D r i v e 1 2 3 4
If there is m ore than one volume, pr ess the “Select” button to view the inform a tion.
The follow ing table shows the description of th e LCD messages for RAI D 5
configuration.
LCD Display Drive configuration
RAID5+S RAID5+spare
RAID5 (D) RAID 5 degraded mode
RAID 5 (B) R AID 5 reb u ilding
RAID 5 (S) RAID 5 re-synchronizing
RAID 5 (U) RAID 5 is unmounted
RAID 5 (X) RAID 5 non-activated
4. System
This section s hows t he sys tem te mpera ture and the ro tation speed of the sys tem fa n.
C P U T e m p : 5 0 ° C
S y s T e m p : 5 5 ° C
S y s F a n : 8 6 5 R P M
5. Shut down
Use this option to turn off the NAS. Press the “Select” button to select “Yes”. Then
press the “Enter” button to confirm.
43
Page 44

→
6. Reboot
Use this option to restart the NAS. Press the “Select” button to select “Yes”. Then
press t he “ En te r” button to confirm.
7. Password
The default password of the LCD panel is blank. Enter this option to change the
password of the LCD panel. Select “Yes” to continue.
C h a n g e P a s s w o r d
Y e s
Enter a pa ssword o f maximum 8 numeric char acters (0-9). When the cursor moves
to “OK”, press the “Enter” button. Verify the password to confirm the changes.
N e w P a s s w o r d :
O K
8. Back
Select this option to re turn to the main menu.
N o
44
Page 45

System Messages
When the NAS encounters a syste m error, an erro r message will be s hown on the LCD p anel.
Press the “Enter” button to view the message. Press the “Enter” button again to view the
next message.
S y s t e m E r r o r !
P l s . C h e c k L o g s
System Message Description
Sy s. Fan Failed The system fan fails
Sys. Overhea t The system overheats
HDD Overheat The hard drive overheats
CPU Overheat The CPU ov erheats
Network Lost Both LAN 1 and LAN 2 are disconnected in failover or
load-balancing mode
LAN1 Lost LAN 1 is disconnect ed
LAN2 Lost LAN 2 is disconnect ed
HDD Failure The hard drive fails
Vol1 Full The volume is full
HDD Ejected The hard drive is ejected
Vol1 Degraded The volume is in degraded mode
Vol1 Unmounted The volume is unmounted
Vol1 Nona ctivate The volume is not activated
45
Page 46

Chapter 11. Install Power Supply Unit
Note: The following instructions should only be performed by an authorized and trained
technician.
To repl a ce a failed power su pply unit on the TS-EC2480U-RP, TS-EC1680U-RP,
TS-EC1280U-RP, TS-EC880U-RP Turb o NAS Turbo NAS, follow the step s below.
1. Turn off the NAS. Disconnect the power adaptor, network cable(s), and any other
connectors or cables from the NAS.
2. Hold the black handler and press and hold the green button firmly.
46
Page 47

3. Unplug the failed power supply.
4. Plug in a new power supply to the NAS.
5. Turn on the NAS.
6. Connect the power adaptor and cables to the NAS.
47
Page 48

Enable warni ng alert for redundant power supply on t he w eb -based interface:
If two power s upply units (P SU) ha ve bee n insta lled o n the NA S and co nnecte d to t he powe r
socke ts, bo th PS U w ill s up ply t he po we r to the N AS ( app lie d to 1U a nd 2 U mo de ls) . Users
can enable redundant power supply mode in “Control Panel” > “System Settings” >
“Hardware” to receive warning alert for the redundant power supply. The NAS will beep
and record the error messages in “System Logs” when the PSU is plugged out or fails.
If only one PSU is installed on the NAS, users are suggested NOT to enable this option.
* This function is disabled by default.
48
Page 49

Technical Support
QNAP provides dedicated online support and customer service via instant messenger.
Online Support:
Forum: http://forum.qnap.com
Technical Supp ort i n t he USA and Canada:
Email: q_supportus@qnap.com
TEL: +1-909-595-2782
Address: 168 University Parkway, Pomona CA 91768
Service Hours: 08:00-17:00 (GMT- 08:00 Pacific Time, Monday to Friday)
http://www.qnap.com
49
Page 50

Appendix A. Product Compliance Class
NAS Models FCC CE
TS-EC2480U-RP Class A Class A
TS-EC1680U-RP Class A Class A
TS-EC1280U-RP Class A Class A
TS-EC880U-RP Class A Class A
TS-EC1080 Pro Class B Class B
TS-EC880 Pro Class B Class B
50
Page 51

GNU GENERAL PUBLIC LICENSE
Version 3, 29 June 2007
Copyright © 2007 Free Software Foundation, Inc. <http://fsf.org/>
Everyo n e is pe rm itte d to co py a nd d istr ib ute v er b ati m cop ie s of th is li ce nse doc um en t, but
changing it is not allowed.
Preamble
The GNU General Public License is a free, copyleft license for software and other kinds of
works.
The licenses for most software and other practical works are designed to take away your
freedom to share and change the works. By contrast, the GNU General Public License is
intended to guarantee your free d om to share and change all ver sions of a program--to
make sure it rema ins free softw are for a ll its user s. W e, the Free So ftwa re Fo undatio n, use
the GNU Ge ner al Pub lic License for most of our software; it applies also to any other work
release d this way by its authors . You can apply it to your programs, too.
When we speak of free software, we a re referring to freedom, not pric e. Our Genera l Public
Licenses are desig ne d to m ake sure t ha t you ha ve the freedo m to distribu te c o pies of free
software (and charge for them if you wish), that you receive source code or can get it if you
want i t, tha t yo u ca n cha nge the so ftwar e or use piece s of it in new free progr ams, and that
you know you ca n do these t hi ngs.
T o protect your rights, we need to prevent others from denying you these rights or asking
you to surrender the rights. Therefore, you have certain responsibilities if you distribute
copies of the software, or if you modify it: responsibilities to respect the freedom of others.
For example, if y ou di stribute copie s of such a program, whether gratis or for a fee, you
must pass on to th e recipients the same freedoms tha t yo u rece i ved . You must make sur e
that th ey, too, re ceive o r can get the source code . And yo u must sho w them these ter ms so
they know their rights.
Developers t hat us e the GNU GPL prot ect yo ur rig hts wit h two steps: ( 1) asse r t cop yr igh t
on the software, and (2) offer you this License giving you legal permission to copy,
51
Page 52

distribute and/o r modify it.
For the developers' and authors' protection, the GPL clearly explains that there is no
warranty for this free software. For both users' and authors' sake, the GPL requires that
modified versions be marked as changed, so that their problems will not be attributed
errone ously to authors of previous versions.
Some devices are designed to deny users access to install or run modified versions of the
software inside them, although the manufacturer can do so. This is fundamentally
incompatible with the aim of protecting user s' freedom to chang e th e software. The
systematic p attern of s uch abuse o ccurs in the area of prod ucts for indi viduals to u se, which
is precisely where it is most unacceptable. Therefore, we have designe d t his ve rs ion o f t he
GPL to pro hibit the p rac tice for thos e pro duc ts. If suc h pro blems aris e s ubstan tial ly i n othe r
domain s, we s tand read y to exte nd this prov isio n to tho se do ma ins i n f uture vers ion s of the
GPL, as needed to protect the freedom of users.
Finally, every program is threatened constantly by software patents. States should not
allow patents to restrict development and use of software on general-purpose computers,
but in those that do, we wish to avoid the special danger that patents applied to a free
program could make it effectively proprietary. T o prevent this, the GPL assures that patents
cannot be used to render the program non-free.
The precise terms and conditions for copying, distribution and modification follow.
TERMS AND CONDITIONS
0. Definitions.
“This License” refers to version 3 of the GNU General Public License.
“Copyri ght” also means cop yright-like laws that apply to other kinds of works, such as
semiconduc tor ma sks.
“The Program” refers to a ny co pyrightable work l ice nsed under this Li ce nse. Eac h li cen see
is addressed as “you”. “Licensees” and “recipients” may be individuals or organizations.
T o “modify” a work means to copy from or adapt all or part of the work in a fashion requiring
copyright per m is sion, oth e r than the m a k ing of a n exact cop y. The re s ulting wo rk is called
a “modified version” of the e arlier work or a work “base d on” the earlier work.
52
Page 53

A “covered work” means either th e un modified Program or a work based on the Program.
T o “propagate” a work means to do a nything with it that, wi thout perm ission, w o ul d m ake
you directly or secondarily liable for infringement under applicable copyright law, except
executin g it on a computer or modif ying a private copy. Propagation include s copying,
distribution (with or without modification), making available to the public, and in some
countries other activities as well.
To “convey ” a work means any kind of prop a g at ion that enables other parties to make or
receive co pie s. Mer e i nter action with a u ser th ro ugh a co mputer netwo rk, wit h no tra nsfe r
of a copy, is not conveying.
An interactive user interface displays “Appropriate Legal Notices” to the extent that it
includes a convenient and prominently visible feature that (1) displays an appropriate
copyright no tice, a nd (2) tells the user that t here is no warr anty for the wor k (excep t to the
extent that warranties are provided), that licensees may convey the work under this
License, and how to view a copy of this License. If the interface presents a list of user
commands or options, such as a menu, a prominent item in the list meets this criterion.
1. Source Code.
The “sourc e code” for a work means the preferred form of the work for making
modifications to it. “Object code” means any non-source form of a w ork.
A “Sta n dard Interface” means an interface that either is an official standard defined by a
recognized standards body, or, in the case of interfaces specified for a particular
programming language, one tha t is widely used among developers working in that
language.
The “System Libraries” of an executable work include anything, other than the work as a
whole, that (a) is included in the normal form of packaging a Major Component, but which
is not part of that Major Component, and (b) serves only to enable use of the work with that
Major Compon ent, or to implem ent a Standard Interface for which an imple mentation is
available to the public in source code form. A “Major Component”, in this context, means a
major essential component (kernel, window system, and so on) of the specific operating
system (if a ny) on which the e xecutable work runs, or a compiler used to produce the wo rk,
or an object code interpret er used to run it.
The “Corre sponding Source” for a work in object code form means all the source code
53
Page 54

needed to generate, install, and (for an executable work) run the object code and to modify
the work, including scripts to control those activities. However, it does not include the
work's System Libraries, or general-pur p ose tools or generall y available free programs
which a re use d un modified in per form ing tho se ac tivitie s but w hich ar e not p art o f the w ork.
For example, C orresponding Sour ce includes interface definiti on files associat ed with
source files for the work, and the source code for shared libraries and dynamically lin ked
subprograms that the work is specifically designed to require, such as by intimate data
communication or control flow between those subp rograms and other parts of the work.
The Corr e sp o nding Sourc e nee d no t include any t hi ng that users can regenerate
automati cally from other parts of the Correspond ing Source.
The Corre sponding Source for a work in source code form is that same work.
2. B asic Permissions.
All rig hts gr a nted und er th is Li cen se a re g ra nt ed fo r th e te rm o f co p yrig ht o n t he Program,
and are irrevocable provided the stated conditions are met. This License explicitly affirms
your unlimited permission to run the unmodified Program. The output from running a
covered work is covered by this License only if the output, given its content , constitutes a
covered work. This License acknowledges your rights of fair use or other equivalent, as
provided by copyright law.
You may make, run and propagate covered works that you do not convey, without
conditions so long as your license otherwise remains in force. You may convey covered
works to othe rs for the so le purpose o f having t hem make mo difications e xclusively for you,
or provide you with facilities for running those work s, provided that you comply with the
terms of this L icense in con veying all mate rial fo r which you do no t contro l copy right. Those
thus makin g or running the covere d works for you must do so exclusively on your behalf,
under your direction and control, on terms that prohibit them from making any copies of
your copyrighted material outside their relationship with you.
Conveying under any other circumstances is permitted solely under the conditions stated
below. Sublic ensing is no t al lo w e d ; s e c tion 10 make s it unnecess a r y.
3. Protecting Users' Legal Rights From Anti-Circumvention Law.
No covered work shall be deemed part of an effective technological measure under any
applica ble la w fulf illing o bliga tions under ar ticle 11 of the WIPO copyrig ht tr eaty ad opted on
20 December 1996, or similar laws prohibiting or restricting circumvention of such
54
Page 55

measures.
When you convey a covered work, you waive any legal power to forbid circumvention of
technological measures to the extent such circumvention is effected by exercising rights
under this License wi th respect to the co vered work , and you d iscla im a ny in tentio n to limit
operation or modification of the work as a means of enforcing, against the work's users,
your or third parties' legal rights to forbid circumvention of technological measures.
4. Conveying Ver b at im Copies.
You may convey verbatim copies of the Program's source code as you receive it, in any
medium, provided that you conspicuously and appropriately publish on each copy an
appropriate copyright notice; keep intact all notices stating that this License and any
non-permissive terms added in accord with section 7 apply to the code; keep intact all
notice s of the a b sence of any war r anty; a nd give a ll recipients a c o p y o f this L icense a lo ng
with the Pro g ram.
You may charge any price or no price for each copy that you convey, and you may offer
support or warranty protection for a fee.
5. Conveying Modified Source Versions.
You may convey a work based on the Program, or the modifications to produce it from the
Program, in the form of source code un der the terms of section 4, provided that you also
meet all of these conditions:
a) The work must carry prominent notices stating that you modified it, and giving a
relevant date.
b) The wo rk mus t ca r ry pro min en t n ot ices s tat in g t hat it is re lease d und er th is L ice nse a nd
any conditions added under section 7. This requirement modifies the requirement in
section 4 to “keep intact all notices”.
c) You must license the entire work, as a whole, under this License to anyone who comes
into possession of a copy. This License will therefore apply, along with any applicable
section 7 additional terms, to the whole of the work, and all its parts, regardless of how
they are pa ckage d. Th is L icense gives no permission to license t he wo rk i n any other way,
but it does not invalidate such permission if you have separately received it.
d) If the work has in teractive user interfaces, ea ch must displa y Appropriate Lega l Notices;
however, if the Program has interactive interfaces that do not display Appropriate Legal
Notices, your work need not make them do so.
A comp ilatio n of a cove red wo rk w ith ot her sep ara te and indep enden t wor ks, w hich ar e no t
55
Page 56

by the ir nat ure e xten sions o f th e co vered work, and whic h are not co mbin ed wi th it s uch as
to form a larger program, in or on a volume of a storage or distributio n medi um, is ca lled an
“aggr egate” if the co mpi latio n and its r esul ting c opy righ t are not u sed to lim it th e acc ess o r
legal r ights o f the co mpila tion's users b eyond what the indiv idual w orks pe rmit. Inclus ion of
a covered work in an aggregate does not cause this License to apply to the other parts of
the aggregate.
6. Conveying Non-Source Forms.
You may convey a covered work in object code form under the terms of sections 4 and 5,
provided tha t you a lso co n ve y the mac hine -readable Corresponding Source under the
terms of this License, in one of these ways:
a) Convey the ob ject code in, or embodied in, a physical product (including a physical
distribution medium), accompanied by the Cor responding Sou rc e fixed on a durable
physical med ium cus to marily used for software interchange.
b) Convey the object code in, or emb odi ed in, a physical product (including a physical
distribution medium), accompanied by a written offer, valid for at least three years and
valid for as long as you offer spare par ts or customer supp ort for that product m od el, to
give anyone who possesses the object code either (1) a copy of the Corresponding Source
for all the software in the product that is covered by this License, on a durable physical
medium customarily used for software interch ange, for a price no more than your
reasonable co st of p hysical ly perfor ming this conve ying of source, o r (2) a ccess to co py the
Correspondin g Source from a network server at no charge.
c) Convey individual copies of the object code with a copy of the written offer to provide the
Corresponding Source. This alternative is al lowed only occasionally and noncom mercially,
and only if you received the object code with such an offer, in ac cord with subsecti on 6b.
d) Convey the object code by offering access from a designated place (gratis or for a
charge) , and offe r equ ivale nt a ccess to t he Corr es pondi ng So urce i n the same way thro ugh
the same place at no further charge. You need not require recipients to copy the
Corresponding Source along with the object code. If the p lace to copy the obj ect co de is a
network server, the Correspond ing Source may be on a dif ferent server (opera ted by you or
a third party) that supports equivalent copying facilities, provided you maintain clear
direc tions next to th e ob j e ct code saying where to find the Correspon din g Source.
Regardless of what serv er hosts the C orresponding Source, yo u remain obliga ted to ensur e
that it is available for as long as needed to satisfy these requirements.
e) Convey the object code using peer-to-peer transmission, provided you inform other
peers where the object code and Corresponding Source of the work are being offered to the
general public at no charge under subsection 6d.
56
Page 57

A separable portion of the object code, whose sourc e code is excluded from the
Corresponding Source as a System Library, need not b e included in conveyin g the object
code work.
A “User Product” is either (1) a “consumer product”, which means any tangible personal
property which is normally used for personal, famil y, or household purposes, or (2)
anything d es igned or sold for inc orporation into a dwelling. In determining whether a
product is a consumer product, doubtful cases shall be resolved in favor of coverage. For a
particular product received by a particular user, “normally used” refers to a typical or
common use of that clas s of pro duct, re gardle ss of t he stat us of the partic ular use r or of t he
way in wh ich the par ticular user a ctually u ses, or expe cts or is exp ected to u se, the prod uct.
A product is a consumer product regardless of whether the product has substantial
commercial, industrial or non-consumer uses, unless such uses represent the only
significant mode of use of the product.
“Insta llation Information” for a User Prod uct means any methods, p rocedures,
authorization keys, or other information required to install and execute modified versions
of a covered work in that User Product from a modified version of its Corresponding Source.
The information must suffice to ensure that the continued functioning of the modified
object code is in no case prevented or interfered with solely because modification has been
made.
If you convey an obj ect code work under this section in, or with, or specifica lly for use in,
a User Product, and the conveying occurs as part of a transaction in which the right of
posses sio n a nd us e o f t he U ser P ro du ct is tr ans fe rr ed to the re cip ie nt in p er pe tui ty o r fo r a
fixed term (regard less of how the tr a nsa ct ion is char ac ter ized), the Corresponding Source
conveyed u nder this se ctio n m ust b e acco mp anie d by the Insta lla tion Inform at ion. B ut this
requirement does not apply if neither you nor any third party retains the ability to install
modified object code on the Us er Product (for example, the work has been installed in
ROM).
The requirement to provide Insta llation Inf o rm ation doe s no t in c l ud e a requiremen t to
contin ue to pr ovide suppor t serv ice, wa rran ty , or update s for a w ork t hat has been mo dified
or installed by the recipient, or for the User Product in which it has been modified or
installed. Access to a network may be denied when the modification itself materially and
adversely affects the operation of the network or violates the rules and protocols for
communication across the network.
57
Page 58

Corre spo nd ing So urce co n ve ye d, a nd In sta lla tio n Inf orma tion pro vid ed, in acc ord w it h this
section must be in a format that is publicly documented (and with an implementation
available to the public in source code form), and must require no special password or key
for unpack ing, reading or copying.
7. Additional Terms.
“Additional permissions” are terms that supplement the terms of this License by making
excep tions from one o r mor e of its co nditio ns. Addit iona l per missio ns that ar e app lica ble to
the entire Program shall be treated as though they were included in this License, to the
exten t tha t t he y ar e va lid un der app li cab le la w . I f a dd itio na l pe rm iss ion s ap pl y on ly to p a rt
of the Program, that part may be used separately under those perm issions, but the entire
Program remains governed by this License without regard to the additional permissions.
When yo u con vey a co py of a co vered work, yo u ma y at yo ur op tion re mo ve a ny add itiona l
permissions from that copy, or from any part of it. (Additional permissions may be written
to require their own removal in certain cases when you modify the work.) You may place
addit iona l pe r miss io ns on ma ter ial, add e d b y you to a co ver ed wo rk, for w hic h you ha ve or
can give appropriate copyright permission .
Notwithstanding any other provision of this License, for material you add to a covered work,
you ma y (if authorized by the copyrigh t ho ld ers of t ha t m a t e rial) supp le ment the terms of
this License with terms:
a) Disclaiming warranty or limiting liability differently from the terms of sections 15 and 16
of this Lic ense; or
b) R equir ing p rese rv atio n of spec ified reas ona ble legal not ices or a uthor a ttrib utions in tha t
material or in the Appropriate Legal Notices displayed by works containing it; or
c) Prohibiting misrepresentation of the origin of that material, or requiring that modified
versions of such material be marked in reasonable ways as different from the original
version; or
d) Limiting the use for publicity purposes of names of licensors or authors of the material;
or
e) Decli ning to gr ant right s under tr ademar k law for use of some trade names, tr ademarks,
or service marks; or
f) Requiring indemnification of licensors and authors of that material by anyone who
conve ys t he ma teria l (or m od ified v ers ions o f it) with contr ac tual as sum ption s of l iabi lity to
the recipient, for any liability that these contractual assumptions directly impose on those
licensors and authors.
58
Page 59

All other non-permissive additional terms are considered “further restrictions” within the
meaning of section 10. If the Program as you received it, or any part o f i t, con tains a no tice
stati ng tha t it is go verne d by this Lice nse a long wit h a ter m tha t is a fur ther r est rict ion, you
may remove that term. If a license document contains a further restriction but permits
relicensing or conveying under this License, you may add to a covered work material
gover ned by the te rms o f th at l ic ens e do cu me nt, pro vid ed tha t the fur t her re s tric tio n d oes
not survive such relicensing or conveying.
If you add terms to a covered work in accord with this section, you must place, in the
relevant source files, a statement of the additional terms that apply to those files, or a
notice indicating where to find the applicable terms.
Additional terms, permissive or non-permissive, may be sta ted in the for m o f a sep ar at el y
written license, or stated as exceptions; the above requirements apply either way.
8. Termination.
Yo u may not propagate or modify a co vered wo rk except as expressly provided under this
License. Any attempt otherwise to propagate or modify it is void, and will automatically
termi na te your right s under this License (incl ud i ng a ny patent lice n s es granted under the
third paragraph of section 11).
However, if you cea se all violati on of this License, then your license from a part icular
copyright holder is reinsta te d ( a) provisionally, unles s a nd until the cop y r ig ht holder
explicitly and finally terminates your license, and (b) permanently, if the copyright holder
fails to notify you of the violation by some reasonable means prior to 60 days after the
cessation.
Moreover, your license from a particular copyright holder is reinstated permanently if the
copyright holder notifies you of the vio la t io n by s o m e reasonab le m e ans, this is t he f i rs t
time you have received notice of violation of this License (for any work) from that copyright
holder, and you cure the violation prior to 30 days after your receipt of the notice.
T ermination of your rights under this section does not terminate the licenses of parties who
have received copies or rights from you under this License. If your rights have been
termi na te d and not permanen t ly r einstated , y o u d o no t q ualify to r ec eive new l ic enses for
the same material under section 10.
9. Acceptance Not Required for Having Copies.
59
Page 60

Y ou are not req uired to ac cep t this L ice nse i n ord er to r ece ive or run a copy of the Program.
Ancillary propagation of a covered work occurring solely as a consequence of using
peer-to-peer transmiss ion to receive a cop y likew ise does not requ ire acceptance. However,
nothing other than this License grants you permission to propagate or modify any covered
work. These actions infringe copyright if you do not accept this License. Therefore, by
modifying or propagating a covered work, you indicate your acceptance of this License to
do so.
10. Automatic Licensing of Downstream Recipients.
Each time you convey a covered work, the recipient automatically receives a license from
the original licensors, to run, modify and propagate that work, subject to this License. You
are not responsible for enforcing compliance by third parties with this License.
An “entity transaction” is a transaction transferring control of an organization, or
substa nt ial ly a ll as se ts o f o ne, o r s ubd ivid ing a n o rga niza tio n, o r me rg ing or gan iza tio ns. If
propagation of a covered work resu lts from an entity transaction, each party to that
transact ion who receiv es a copy of the w ork a lso rece ives w hatever license s to the wor k the
party's predecessor in interest had or could give under the previous par agraph, plus a right
to possession of the Corresponding Source of the work from the predecesso r in interest, if
the predecessor has it or can get it with reasonable efforts.
You may not impose any further restrictions on the exercise of the rights granted or
affirmed under this License. For example, you may not impose a license fee, royalty , or
other charge for exercise of rights granted under this License, and you may not initiate
litigation (including a cross-claim or counterclaim in a lawsuit) alleging that any patent
claim is infringed b y maki ng, us ing, selling, offering for sale, or importing the Program or
any portion of it.
11. Patents.
A “co nt r ibutor” is a copyright holde r who a ut ho r i z es use u nde r this L ic e nse of th e P ro g ram
or a work on which the Program is based. The work thus licensed is called the contributor's
“contr ibutor ver sion”.
A contributor's “essential patent claims” are all patent claims owned or controlled by the
contributor, whether already acquired or hereafter acquired, that would be infringed by
some manner, permitted by this License, of making, using, or selling its contributor version,
but do not include claims that would be infringed only as a consequence of further
modification of the contributor version. For purposes of this definition, “control” includes
60
Page 61

the right to grant patent sublicenses in a manner consistent with the requirements of this
License.
Each contributor grants you a non-exclusive, worldwide, royalty-free patent license un der
the contributor's essential patent claims, to make, use, sell, offer for sale, import and
other wi se run, modify and propag a te the contents of its contributor version.
In the following three paragraphs, a “patent license” is any express agreement or
commitment, however denominated, not to enforce a patent (such as an express
permission to practice a p a ten t or covena nt no t to sue fo r p ate nt in fring e me nt). To “grant”
such a pate nt l ice nse to a party means to make such an agreement or com mit me n t no t to
enforce a patent against the party.
If you co nvey a co vered wor k, knowing ly relying o n a patent l icense, a nd the Corr espond ing
Source o f the wor k is not available fo r anyone to copy, free of c ha r g e and under the terms
of this License, through a publicly available network server or other readily accessible
means, then you must either (1) cause the Corresponding Source to be so available, or (2)
arra nge to de pri ve yo urse lf o f t he be nefit of the pate nt l icense fo r th is pa rti cular wor k, o r (3)
arra nge, in a mann er co nsis tent w ith the re qu iremen ts o f this Lic ense, to e xtend the pat ent
licen se to do w nstream recipients. “Knowingly relying” means you have actual knowledge
that, but for the patent license, your conveying the covered work in a country, or your
recipi ent's use of the covered work in a country, would infringe one or more identifiable
paten ts in that country that you have reason to b e li ev e are valid .
If, pursuant to or in connection with a single transaction or arrangement, you convey, or
propagate by p roc uring co n veya nce of, a co vered work, and gr a nt a paten t lice nse to so me
of the parties receiving the covered work authorizing them to use, propaga te, modify or
convey a specific copy of the covered work, then the patent license you grant is
automatically extended to all recipients of the covered work and works based on it.
A paten t li c ense is “discriminatory” if it does not include wit hin the scope of its cove rag e ,
prohibits the exercise of , or is conditioned on the non-exercise of one or more of the rights
that a r e sp e cifically g ranted u nd er this License. You may no t c onvey a covered work if y ou
are a party to an arrangement with a third party that is in the business of distributing
software, under which you make payment to the third party based on the extent of your
activity of conve ying the w ork, a nd unde r which t he third party g rants, to an y of the parties
who would receive the covered wor k f rom you, a discriminat ory patent license (a) in
connection with copies of the covered work conveyed by you (or copies made from those
61
Page 62

copies), or (b) primaril y f or and in connection with specific products or compilations that
conta in the cove red work, unle ss yo u en tered into that a rra ngem ent, o r tha t pa tent licen se
was granted, prior to 28 March 2007.
Nothing in this License shall be construed as excluding or limiting any implied license or
other defenses to infringement that may otherwise be available to you under applicable
paten t la w.
12. No Surrender of Others' Freedom.
If conditions are imposed on you (whether by court order, agreement or otherwise) that
contra d ic t t he cond it ion s o f th is L ic ens e, th ey do not excuse you from the conditions of this
License. If you cannot convey a covered work so as to satisfy simultaneously your
obligations under this License and any other pertinent obligations, then as a consequence
you may not convey it at all. For example, if yo u agre e to term s tha t obliga te you to co llec t
a royalty for further conveying from those to whom you convey the Program, the only way
you could satisfy both those terms and this License would be to refrain entirely from
conveyi ng the Program.
13. Use with the GNU Affero General Public License.
Notwit hstand ing a ny othe r prov ision of this L icens e, you h ave p ermiss ion to link or combin e
any covered work with a work licensed under version 3 of the GNU Affero General Public
License into a single combined work, and to convey the resulting work. The terms of this
License will continue to apply to the part which is the covered work, but the special
requirements of the GN U Affero General Pub li c L icense, section 13, co nc erning inte raction
through a network will apply to the combination as such.
14. Revised Versions of this License.
The Free Softwa re Foundation may p ublish revised and/o r new versions of the GN U General
Public License from time to ti m e. S u ch new vers i o ns w il l be s imilar in spi ri t to the present
version, but may differ in detai l to address new proble ms or concerns.
Each version is given a distinguishing version number. If the Program specifies that a
certa in n u mb ered version of th e GN U General Public License “o r any later ve r s ion” applies
to it, you have the option of following the terms and conditions either of that numbered
version or of any later versio n published by the Free Softw are Foundation. If the Program
does not specify a version number of the GNU General Public License, you may choose any
version ever published by the Free Software Foundation.
62
Page 63

If the Program speci fies tha t a proxy can decide which futur e version s of the GNU Gener al
Public License can be used, that proxy's public statement of acceptance of a version
permanently authorizes you to choose that version for the Program.
Later license versions may give you additional or different permissions. However, no
additi onal obligations are imposed on any author or copyright holder as a result of your
choosing to follow a later version.
15. Disclaimer of Warranty.
THERE IS NO WAR RAN TY FO R THE P ROGR AM, TO THE EX TENT P ERM IT TED B Y APP LIC ABLE
LA W . E XCEP T W HEN O TH ERWIS E STATED IN WR ITIN G THE COPY RIG HT HOL DERS AND /OR
OTHER PARTIES PROVIDE THE PROGRAM “AS IS” WITHOUT WARRANTY OF ANY KIND,
EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE
ENTIRE RISK AS TO THE QU AL IT Y AN D PERFORMANC E OF THE PROGRAM IS WITH YO U.
SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY
SERVICING, REPAI R OR CORREC TION.
16. Limitation of Liability.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL
ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS THE
PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
DAT A OR DA T A BEING RENDERED INACCURA TE OR LOSSES SUSTAINED BY YOU OR THIRD
PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
SUCH DAMAGES.
17. Interpretation of Sections 15 and 16.
If the d iscla im er of wa rr a nty a nd lim ita tio n of lia bil ity p ro v ided above ca nno t b e g iv en loc a l
legal e ffect a ccordi ng to t heir ter ms, re viewing court s shal l apply lo cal la w that most clo sely
approximates an absolute waiver of all civil liability in connection with the Program, unless
a warranty or assumption of liability accompanies a copy of the Program in return for a fee.
END OF TERMS AND CONDITIONS
63
 Loading...
Loading...