Page 1
SpeedTouch™608(WL)/620
(Wireless) Business DSL Router
IPSec Configuration Guide
SpeedTouch™608WL and
SpeedTouch™620 only
Power
Ethernet
N
LA
N
W
Plug-in
ISD
Internet
Page 2

Page 3
SpeedTouch™
608(WL)/620
IPSec Configuration Guide
Page 4
Copyright
Copyright ©1999-2006 THOMSON. All rights reserved.
Distribution and copying of this document, use and communication of its contents is not permitted without written authorization
from THOMSON. The content of this document is furnished for informational use only, may be subject to change without notice,
and should not be construed as a commitment by THOMSON. THOMSON assumes no responsibility or liability for any errors or
inaccuracies that may appear in this document.
Thomson Telecom Belgium
Prins Boudewijnlaan, 47
B-2650 Edegem
Belgium
www.speedtouch.com
Trademarks
The following trademarks are used in this document:
SpeedTouch™ is a trademark of THOMSON.
Bluetooth® word mark and logos are owned by the Bluetooth SIG, Inc.
Ethernet™ is a trademark of Xerox Corporation.
Wi-Fi® and the Wi-Fi logo are registered trademarks of the Wi-Fi Alliance. "Wi-Fi CERTIFIED", "Wi-Fi ZONE", "Wi-Fi Alli-
ance", their respective logos and "Wi-Fi Protected Access" are trademarks of the Wi-Fi Alliance.
UPnP™ is a certification mark of the UPnP™ Implementers Corporation.
Microsoft®, MS-DOS®, Windows® and Windows NT® are either registered trademarks or trademarks of Microsoft Corpo-
ration in the United States and/or other countries.
Apple® and Mac OS® are registered trademarks of Apple Computer, Incorporated, registered in the United States and
other countries.
UNIX® is a registered trademark of UNIX System Laboratories, Incorporated.
Adobe®, the Adobe logo, Acrobat and Acrobat Reader are trademarks or registered trademarks of Adobe Systems, Incor-
porated, registered in the United States and/or other countries.
Netscape® and Netscape Navigator® are registered trademarks of Netscape Communications Corporation.
Other brands and product names may be trademarks or registered trademarks of their respective holders.
Document Information
Status: v1.0 (January 2006)
Reference: E-DOC-CTC-20051017-0169
Short Title: IPSec Configuration Guide ST608(WL)/620 R5.4
Page 5
Contents
Contents
About this IPSec Configuration Guide ....................... 9
1 IPSec: Concept for secure IP connections................. 11
1.1 IPSec Concepts ............................................................................ 12
2 SpeedTouch™ IPSec terminology............................. 15
2.1 Policy ........................................................................................... 16
2.2 Security Descriptor ...................................................................... 17
2.3 Authentication Attribute ............................................................. 18
2.4 Peer (Phase 1) .............................................................................. 19
2.5 Connection (Phase 2) ................................................................... 20
2.6 Network descriptor ...................................................................... 21
3 Configuration via Local Pages ...................................23
3.1 LAN to LAN Application............................................................... 25
3.1.1 Remote Gateway Address Known Page ...................................................................... 27
3.1.2 Remote Gateway Address Unknown Page..................................................................35
3.1.3 Connections Page .......................................................................................................... 47
E-DOC-CTC-20051017-0169 v0.1
3.2 VPN Client.................................................................................... 51
3.2.1 VPN Client Page ............................................................................................................. 52
3.2.2 Starting the VPN Client Connection ............................................................................. 59
3.2.3 Closing a Connection..................................................................................................... 62
3
Page 6
Contents
3.3 VPN Server ................................................................................... 63
3.3.1 VPN Server Page............................................................................................................64
3.4 Certificates .................................................................................. 73
3.5 Advanced VPN Menu ................................................................... 75
3.5.1 Peer Profiles Page.......................................................................................................... 78
3.5.2 Authentication Page ......................................................................................................82
3.5.3 Peer Descriptors Page ................................................................................................... 83
3.5.4 Peer Options Page ......................................................................................................... 85
3.5.5 VPN-Client Page.............................................................................................................86
3.5.6 VPN-Server Page............................................................................................................88
3.5.7 VPN-Server-XAuth Page................................................................................................90
3.5.8 Connection Profiles Page .............................................................................................. 91
3.5.9 Networks Page ...............................................................................................................94
3.5.10 Connection Descriptors Page........................................................................................ 96
3.5.11 Connection Options Page..............................................................................................99
3.5.12 Client Page....................................................................................................................100
4 Configuration via the Command Line Interface ..... 101
4.1 Basic IPSec configuration procedure ......................................... 102
4.2 Peer: Authentication Attribute .................................................. 104
4.2.1 Authentication Attribute Parameters ......................................................................... 105
4.2.2 List all Authentication Attributes................................................................................ 106
4.2.3 Create a New Authentication Attribute ...................................................................... 107
4.2.4 Set or Modify the Authentication Attribute Parameters........................................... 108
4.2.5 Delete an Authentication attribute .............................................................................109
4.3 Peer Security Descriptor ............................................................ 110
4.3.1 Peer Security Descriptor Parameters ......................................................................... 111
4.3.2 List all Peer Security Descriptors................................................................................114
4.3.3 Create a New Peer Security Descriptor......................................................................115
4.3.4 Set or Modify the Peer Descriptor Parameters..........................................................116
4.3.5 Delete a Peer Descriptor..............................................................................................117
4
E-DOC-CTC-20051017-0169 v0.1
Page 7
Contents
4.4 Peer ............................................................................................ 118
4.4.1 Peer parameters........................................................................................................... 119
4.4.2 List all peer entities...................................................................................................... 123
4.4.3 Create a new peer entity ............................................................................................. 124
4.4.4 Set or modify the peer parameters ............................................................................125
4.4.5 Delete a Peer entity...................................................................................................... 126
4.5 Connection Security Descriptor................................................. 127
4.5.1 Connection Security Descriptor parameters .............................................................128
4.5.2 List all Connection Security Descriptors....................................................................131
4.5.3 Create a new Connection Security Descriptor...........................................................132
4.5.4 Set the Connection Security Descriptor Parameters ................................................133
4.5.5 Delete a Connection Security Descriptor ................................................................... 134
4.6 Network Descriptor ................................................................... 135
4.6.1 Network Descriptor Parameters ................................................................................. 136
4.6.2 Create a New Network Descriptor..............................................................................138
4.6.3 Set the Network Descriptor Parameters ....................................................................139
4.6.4 Delete a Network Descriptor.......................................................................................140
4.7 Connection ................................................................................. 141
4.7.1 Connection Parameters...............................................................................................142
4.7.2 List all Connections...................................................................................................... 145
4.7.3 Create a New Connection............................................................................................146
4.7.4 Set or Modify the Connection Parameters ................................................................ 147
4.7.5 Delete a Connection..................................................................................................... 148
4.7.6 Start a Connection ....................................................................................................... 149
4.7.7 Stop a connection........................................................................................................150
4.8 Auxiliary Commands .................................................................. 151
4.8.1 Config Command.........................................................................................................152
4.8.2 Flush Command...........................................................................................................155
4.8.3 Clear Command Group ...............................................................................................156
4.9 Organisation of the IPSec Command Group .............................. 157
E-DOC-CTC-20051017-0169 v0.1
5 Troubleshooting SpeedTouch™ IPSec ...................161
5.1 Via the Debug Web pages .......................................................... 162
5.2 Via the CLI: Show command group............................................ 165
5
Page 8
Contents
5.3 Via the CLI: Debug command group ......................................... 167
5.4 Via SNMP ................................................................................... 170
5.5 Pinging from the SpeedTouch™ to the remote private network 171
6 Advanced Features ................................................... 173
6.1 IPSec and the Stateful Inspection Firewall ................................ 174
6.2 Surfing through the VPN tunnel ................................................ 175
6.3 Extended Authentication (XAuth) .............................................. 176
6.4 VPN Client.................................................................................. 177
6.4.1 VPN Client parameters ................................................................................................178
6.4.2 Create a new vpnclient................................................................................................179
6.4.3 Set or modify the vpnclient parameters .................................................................... 180
6.4.4 Attach the vpnclient entity to the peer entity ............................................................ 181
6.5 VPN Server ................................................................................. 182
6.5.1 VPN Server parameters............................................................................................... 183
6.5.2 Create a new VPN server.............................................................................................185
6.5.3 Set or modify the vpnserver parameters................................................................... 186
6.5.4 Attach the vpnserver entity to the peer entity........................................................... 187
6.6 XAuth Users Pool....................................................................... 188
6.6.1 XAuth Pool parameters...............................................................................................189
6.6.2 Create a new XAuth pool ............................................................................................190
6.6.3 Modify the xauthpool type..........................................................................................191
6.6.4 Attach the xauthpool entity to the vpnserver entity .................................................192
6.6.5 Delete an xauthpool entity..........................................................................................193
6.6.6 XAuth User parameters............................................................................................... 194
6.6.7 Create a new XAuth user ............................................................................................ 195
6.6.8 Set or modify the password of an XAuth user.......................................................... 196
6.6.9 Delete an xauthuser entity ..........................................................................................197
6.7 The Default Peer Concept .......................................................... 198
6.8 One Peer - Multiple Connections ............................................... 200
6
E-DOC-CTC-20051017-0169 v0.1
Page 9

Contents
6.9 Peer Options .............................................................................. 201
6.9.1 List all Peer Options lists............................................................................................. 203
6.9.2 Create a Peer Options list............................................................................................ 204
6.9.3 Set or modify the Peer Option list parameters......................................................... 205
6.9.4 Delete a Peer Options list............................................................................................ 206
6.10 Connection Options ................................................................... 207
6.10.1 List all Connection Options lists ................................................................................. 209
6.10.2 Create a Connection Options list................................................................................210
6.10.3 Set or modify the Connection Option list parameters............................................. 211
6.10.4 Delete an Options list .................................................................................................. 212
6.11 Advanced Connection ................................................................ 213
E-DOC-CTC-20051017-0169 v0.1
7
Page 10

Contents
8
E-DOC-CTC-20051017-0169 v0.1
Page 11
About this IPSec Configuration Guide
About this IPSec Configuration Guide
Abstract This document explains the IPSec functionality of the SpeedTouch™ Release R5.4
and higher. A brief theoretical explanation is provided where needed, but the main
goal of this document is to be a practical guide.
Applicability This configuration guide applies to the following SpeedTouch™ products:
The SpeedTouch™608/608WL (Wireless) Business DSL Routers Release R5.4
and higher.
The SpeedTouch™620 Wireless Business DSL Routers Release R5.4 and
higher.
In some SpeedTouch™ products, the IPSec VPN features are bundled in an
optional VPN software module. An optional VPN module is activated with a
VPN software activation key. By default, this key is not installed. If you want
to use the SpeedTouch™ VPN features, and the VPN software module is not
activated on your SpeedTouch™, please contact your local dealer.
Activating the VPN software module is described in the SpeedTouch™
Operator’s Guide.
Used Symbols The following symbols are used in this IPSec Configuration Guide:
A note provides additional information about a topic.
A tip provides an alternative method or shortcut to perform an action.
A caution warns you about potential problems or specific precautions that
!
need to be taken.
Terminology Generally, the SpeedTouch™ 608(WL) or SpeedTouch™620 will be referred to as
SpeedTouch™ in this IPSec Configuration Guide.
Documentation and
software updates
THOMSON continuously develops new solutions, but is also committed to improve
its existing products.
For suggestions regarding this document, please contact
documentation.speedtouch@thomson.net
For more information on THOMSON's latest technological innovations, documents
and software releases, visit us at:
www.speedtouch.com
.
E-DOC-CTC-20051017-0169 v1.0
9
Page 12

About this IPSec Configuration Guide
10
E-DOC-CTC-20051017-0169 v1.0
Page 13
1 IPSec: Concept for secure IP connections
Policies The introduction of network security mainly involves the application of traffic
policies. Firstly, the policies need to be defined, then it should be whether the
policies are correctly applied.
Security policies can apply to various levels. The IPSec protocol (Internet Protocol
Security) applies to the IP layer. This location of the IPSec protocol within the
layered network model makes it a generic solution for a wide range of applications.
Types of policies supported in the IPSec protocol:
user/entity authentication
level of encryption
validity time of the keys
...
The Target of IPSec The main goals for using the IPSec protocol suite are:
Integrity of data
It ensures that data has not been modified in transit.
Confidentiality of data
On non-trusted network sections, the data is encrypted. When this data is
intercepted, it cannot be interpreted by the eavesdropper.
User authentication
Ensures that you know the party you are communicating with, and that they
are who they say they are.
Chapter 1
IPSec: Concept for secure IP connections
In this section The following items are discussed in this section:
Topic Page
1.1 IPSec Concepts 12
E-DOC-CTC-20051017-0169 v1.0
11
Page 14
Chapter 1
IPSec: Concept for secure IP connections
1.1 IPSec Concepts
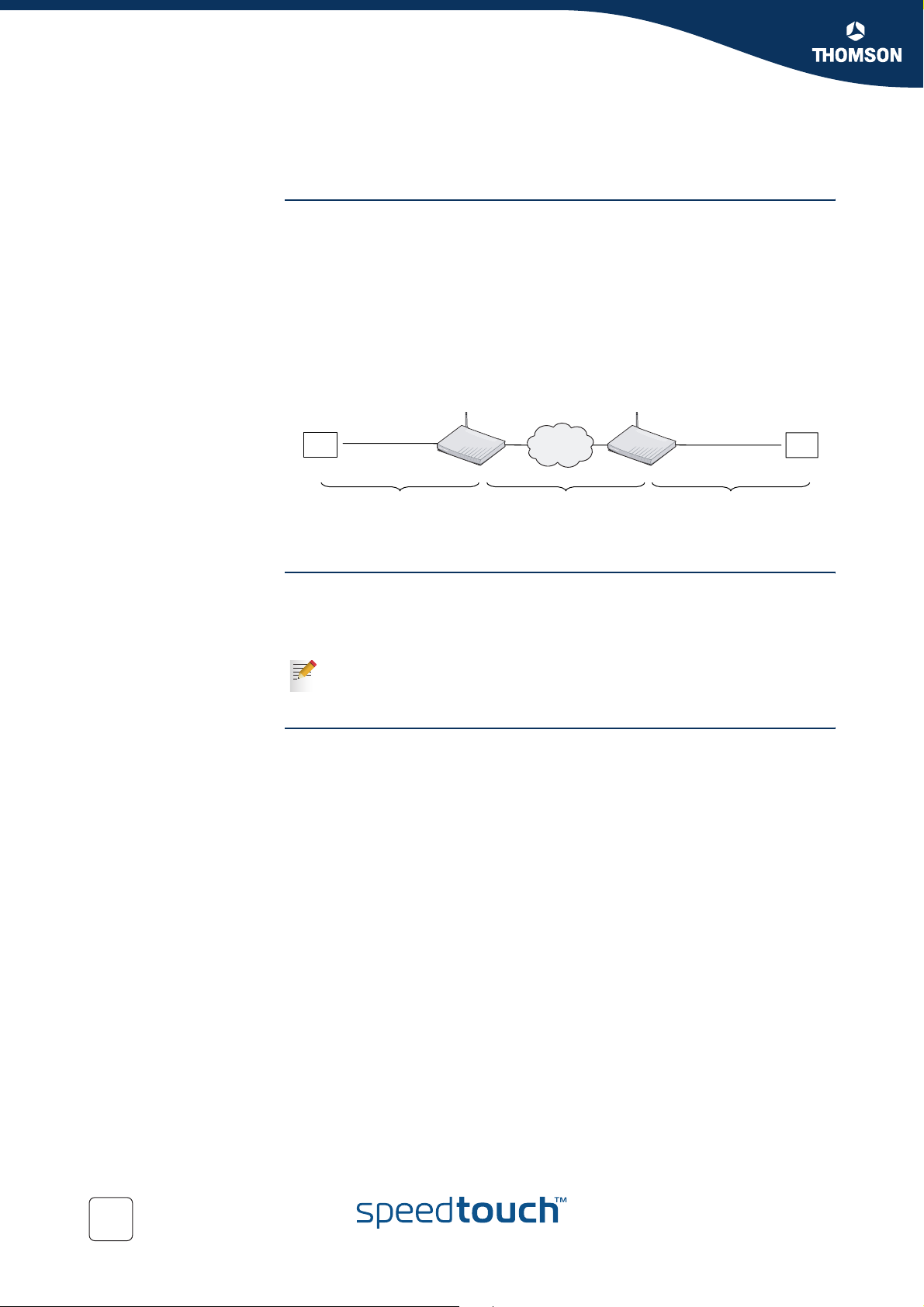
Red and Black Network Following nomenclature will be used throughout this document:
The SpeedTouch™
The IPSec capable DSL router
The Red network
Private or trusted side of the SpeedTouch™.
The Black network
Public or non-trusted side of the SpeedTouch™. The black network is
frequently referred to as the WAN side, being the connection towards the
Internet.
Red network
node
SpeedTouch 620 [1] Red network
SpeedTouch 620 [2]
node
Red LAN
Trusted network side
Black network
Non-trusted network side
Red LAN
Trusted network side
Authentication Header The Authentication Header (AH) protocol allows to check the integrity of a data
packet. A digital signature (=hash) is computed over the entire packet, with the
exception of the mutable fields (fields that change during the transmission of the
packet - e.g. TTL counter).
As the use of the Authentication Header is deprecated, the SpeedTouch™
from Release onwards only supports the ESP protocol. Authentication
without encryption can be achieved by selecting ESP with NULL encryption.
Encapsulated Security
Payload
The Encapsulated Security Payload (ESP) protocol provides data confidentiality and
ensures data integrity (message authentication). ESP supports various encryption
algorithms, thus making the data unreadable for an eavesdropper. A Security
Association (SA) consists of a set of parameters, negotiated between two peers:
authentication type
compression, hashing or encryption algorithms
key size
key lifetime
...
12
E-DOC-CTC-20051017-0169 v1.0
Page 15
Chapter 1
IPSec: Concept for secure IP connections
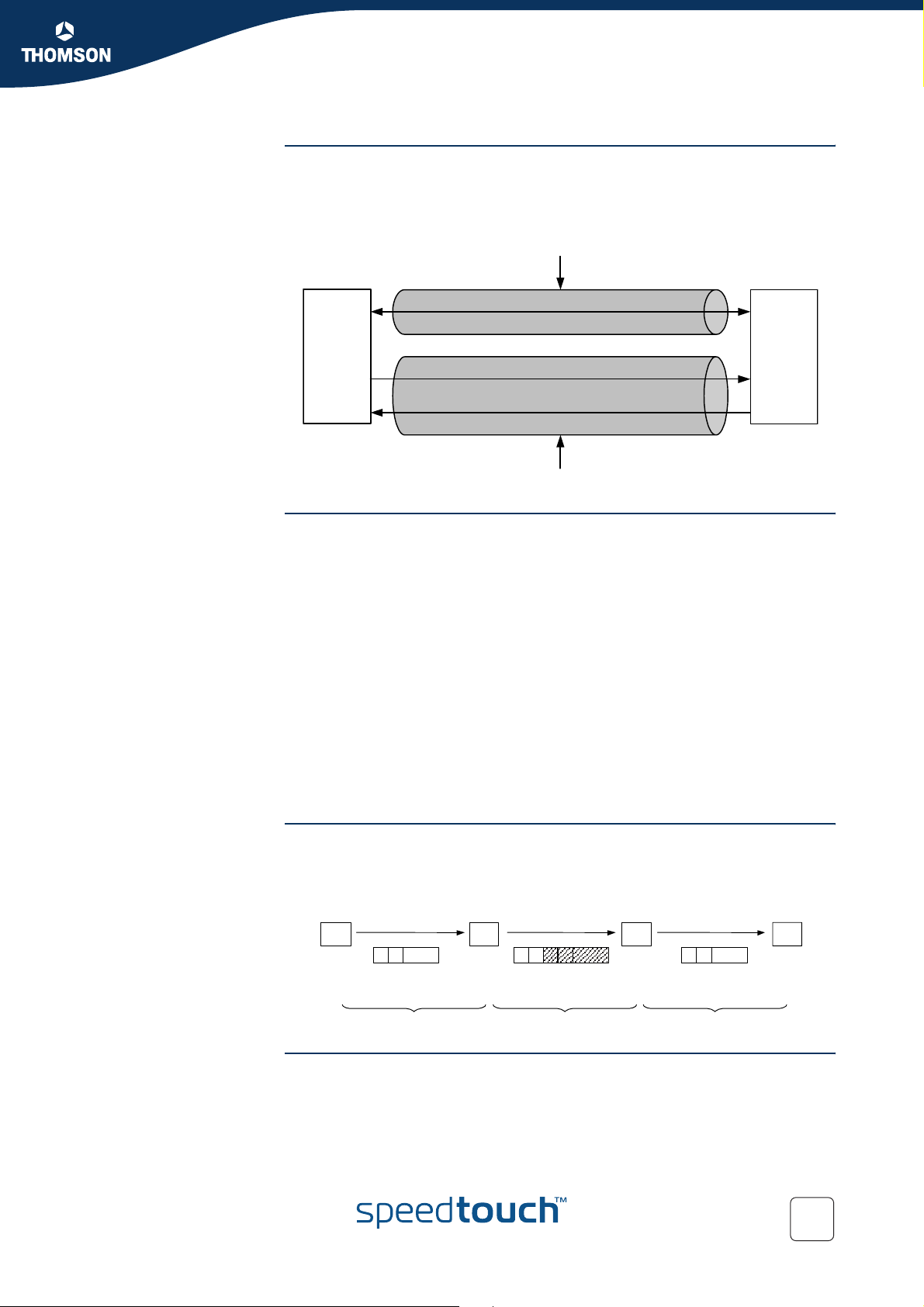
Internet Key Exchange The Internet Key Exchange (IKE) protocol is the negotiation protocol used to establish
an SA by negotiating security protocols and exchanging keys. First the IKE SA is set
up, then the IKE channel acts as a signalling channel to negotiate a general purpose
SA.
Phase 1
Phase 1 (IKE) SA
SA (ESP/AH)
SA (ESP/AH)
Phase 2 tunnel
Security Associations Within the IKE protocol, two phases are distinguished to set up a tunnel between
two peers:
Phase 1: negotiate a bi-directional IKE SA functioning as a signalling channel to
negotiate the Phase 2 SAs.
Phase 2: negotiate unidirectional IPSec Security Associations that will carry
general purpose traffic.
The IKE SA is bidirectional, whereas the Phase 2 SA is unidirectional: one Security
Association must be set up in each direction. The initiator and responder cookies
uniquely identify an IKE SA while each PH2 SA is uniquely identified by a SPI
(Security Parameter Index) value.
Per convention, throughout this document the IKE SA is referred to as the Phase 1
SA and the ESP SAs are referred to as the Phase 2 SA:
Phase 1 SA = IKE SA = secure Phase 1 tunnel
A pair of Phase 2 SAs = a secure Phase 2 tunnel
Tunnel Mode Using tunnel mode, the complete IP packet (including its IP header) is encapsulated
Transport Mode In transport mode, the IP header is transported unmodified. The use of transport
E-DOC-CTC-20051017-0169 v1.0
and a new IP header is attached. This allows for the original source and destination IP
addresses to be hidden from the outside world.
Red network
node
AB C D
AB AB
SpeedTouch620 [1] SpeedTouch620 [2]
CDAB
Red LAN Black LAN Red LAN
Red network
node
mode is limited to connections where the security gateway is acting as a host, e.g.,
for network management applications. When the SpeedTouch™ is managed from a
remote location via a VPN connection, transport mode can be used, because in this
case the SpeedTouch™ is the end user of this information stream.
13
Page 16
Chapter 1
IPSec: Concept for secure IP connections
14
E-DOC-CTC-20051017-0169 v1.0
Page 17
SpeedTouch™ IPSec terminology
2 SpeedTouch™ IPSec terminology
Introduction In order to understand the IPSec configuration of the SpeedTouch™, a number of
concepts and definitions are introduced in this section. The Graphical User Interface
(GUI) and the Command Line Interface (CLI) provide two alternative methods to
configure the IPSec functions. The GUI contains some scenario-driven pages, which
means that the configuration pages are grouped according to the intended network
application. The advanced GUI pages and the CLI are component-driven, which
means that network components are configured independently of each other. It is
up to the user to combine the configuration of various components in order to build
an operational node in the intended network environment.
The majority of IPSec configurations can be built with the Graphical User Interface.
Only in particular situations, it may be required to access some advanced functions
via the Command Line Interface. The terminology used in the CLI and GUI is similar.
The clarification of the concepts and terms refers to the command structure of the
CLI. The IPSec command group comprises a number of underlying command
groups, each containing a number of commands in a hierarchical way.
Chapter 2
In this section The following topics are discussed in this section:
Topic Page
2.1 Policy 16
2.2 Security Descriptor 17
2.3 Authentication Attribute 18
2.4 Peer (Phase 1) 19
2.5 Connection (Phase 2) 20
2.6 Network descriptor 21
E-DOC-CTC-20051017-0169 v1.0
15
Page 18
Chapter 2
SpeedTouch™ IPSec terminology
2.1 Policy
What is ... Security is all about traffic policies and these can be configured using the IPSec
Static policy In a static network environment with fixed IP addresses, the policy can be
Dynamic policy In a more dynamic network environment, where IP addresses are dynamically
policy commands. By default, policy rules are automatically generated when the
IPSec connection is created and the user does not need to execute extra commands.
A set of rules defines whether a packet has to pass through a secure tunnel or not.
These rules are expressed in terms of IP addresses, protocols and/or ports that have
access to the secure connections. The user specifies and configures a general policy
in function of his overall security policy and the VPN network topology.
completely defined, and specific rules can be expressed in the configuration.
assigned, or where terminals may connect from various unknown locations, it may
be impossible to express a specific policy in the router configuration. In order to
cope with this situation, the SpeedTouch™ allows expressing a general policy in the
configuration. This general policy may include some placeholders for information
that becomes available only during the Security Association negotiations. The
specific policy rules are automatically derived from the general policy and the
outcome of the negotiations.
16
E-DOC-CTC-20051017-0169 v1.0
Page 19
2.2 Security Descriptor
What is ... All security parameters required to establish a secure tunnel are grouped into a
string called Security Descriptor or simply descriptor. Two different sets of
descriptors are defined:
IKE session descriptors
IPSec descriptors
A Descriptor contains the methods for message authentication, encryption and
hashing, and the lifetime of the Security Association. A number of descriptors are
pre-configured in the SpeedTouch™. The user can modify these descriptors, or
define additional descriptors to fit his requirements.
IKE session Descriptor The IKE descriptor contains the following parameters:
Encryption method
Message integrity method (also called message authentication)
Diffie-Hellman group used for key generation
Lifetime of the Security Association.
Chapter 2
SpeedTouch™ IPSec terminology
IPSec Descriptor The IPSec descriptor contains the following parameters:
Encryption method
Message integrity method (also called message authentication)
Selection to use Perfect Forward Secrecy, or not
Lifetime of the Security Association
Encapsulation method.
E-DOC-CTC-20051017-0169 v1.0
17
Page 20
Chapter 2
SpeedTouch™ IPSec terminology
2.3 Authentication Attribute
What is ... Two main methods for authentication are supported in the SpeedTouch™:
pre-shared key
certificates
The authentication parameters used for the IKE negotiations are bundled in the
SpeedTouch™ in a descriptor with a symbolic name.
This symbolic descriptor is called the Authentication Attribute, and is encountered
when you configure the SpeedTouch™ via the Command Line Interface.
For pre-shared key authentication, this attribute holds the pre-shared key. For
authentication with certificates it simply indicates the authentication method.
18
E-DOC-CTC-20051017-0169 v1.0
Page 21
SpeedTouch™ IPSec terminology
2.4 Peer (Phase 1)
What is ... The Peer is a term that refers to the remote Security Gateway to which the IPSec
secure tunnel(s) will be established. In a first phase, an IKE Security Association is
negotiated between the SpeedTouch™ and a remote Security Gateway (peer). In
the configuration of the SpeedTouch™, the Peer bundles all the parameters
required to negotiate an IKE Security Association (Phase 1 SA), such as:
Address
The public IP address of the remote IPSec peer. Eventually a backup address
can be defined.
Local ID
The identity of the local peer, which is presented to the remote peer during the
Phase 1 negotiation. Various identity types are supported, such as: IP address,
Distinguished Name. FQDN, etc.
Remote ID
Similar to the Local ID, this parameter identifies the remote peer during the
Phase 1 negotiation. Various identity types are supported, such as: IP address,
Distinguished Name. FQDN, etc.
Authtype
Authentication method used: preshared key or with certificates.
XAuth user and password
Allows for a secondary authentication based on a legacy authentication
system
Descriptor
Refers to the Phase 1 security descriptor
The complete list of parameters is found in section “4.4 Peer” on page 118 and in
the CLI Reference Guide.
Chapter 2
E-DOC-CTC-20051017-0169 v1.0
19
Page 22
Chapter 2
SpeedTouch™ IPSec terminology
2.5 Connection (Phase 2)
What is ... Bundles all the parameters required for the Phase 2 SA (IPSec) negotiation:
Peer
Reference, pointing to the peer configuration to be used. In fact, this refers to
the IKE channel used for the Phase 2 negotiations.
Local/remote range
Range of red IP addresses to which the IPSec policy applies.
Reference to the Network Descriptors.
Descriptor
Reference to the Phase 2 Security Descriptor grouping the security
parameters.
20
E-DOC-CTC-20051017-0169 v1.0
Page 23
SpeedTouch™ IPSec terminology
2.6 Network descriptor
What is ... The concept of Network Descriptors is introduced for the first time in the
SpeedTouch™ R5.3. Not only the classical idea of an IP network or subnet is
comprised in this concept, but also the protocol and port number of the messages
can be specified, such that access to the VPN can be restricted to certain hosts,
protocols and port numbers.
Both the origin and destination traffic policies are expressed by referring to a
Network Descriptor. To this end, a symbolic name is attributed to a Network
Descriptor.
The definition of relevant Network Descriptors is linked with the topology of the VPN
that is constructed with the IPSec configuration. The Network Descriptors determine
the type of messages that will trigger the IPSec module.
Chapter 2
E-DOC-CTC-20051017-0169 v1.0
21
Page 24

Chapter 2
SpeedTouch™ IPSec terminology
22
E-DOC-CTC-20051017-0169 v1.0
Page 25
Configuration via Local Pages
3 Configuration via Local Pages
Prerequisites In order to use the VPN features in the SpeedTouch™608(WL)/620, you should
enable the VPN software module.
To activate this VPN module, you have to acquire the optional software activation
key. To check whether the software activation key is present, browse to the
SpeedTouch™ Web pages and go to Expert Mode > SpeedTouch > Add-On. This
page shows which keys are enabled. For more information , see the SpeedTouch™
Operator’s Guide.
IPSec Web Pages All IPSec configurations can be built by means of the SpeedTouch™ local Web
pages.
Application-oriented configuration pages gives you direct access to all relevant
parameters. Getting your IPSec configuration up and running is as easy as selecting
your application and filling out a few Web pages. The application-oriented pages
cover the most common application scenarios.
Additional Web pages are component-oriented and allow to control advanced
settings, such as certificates management and debugging options. The Advanced
Web pages allow you to build an operational IPSec configuration by combining
configuration components in a similar way as the underlying CLI commands.
Chapter 3
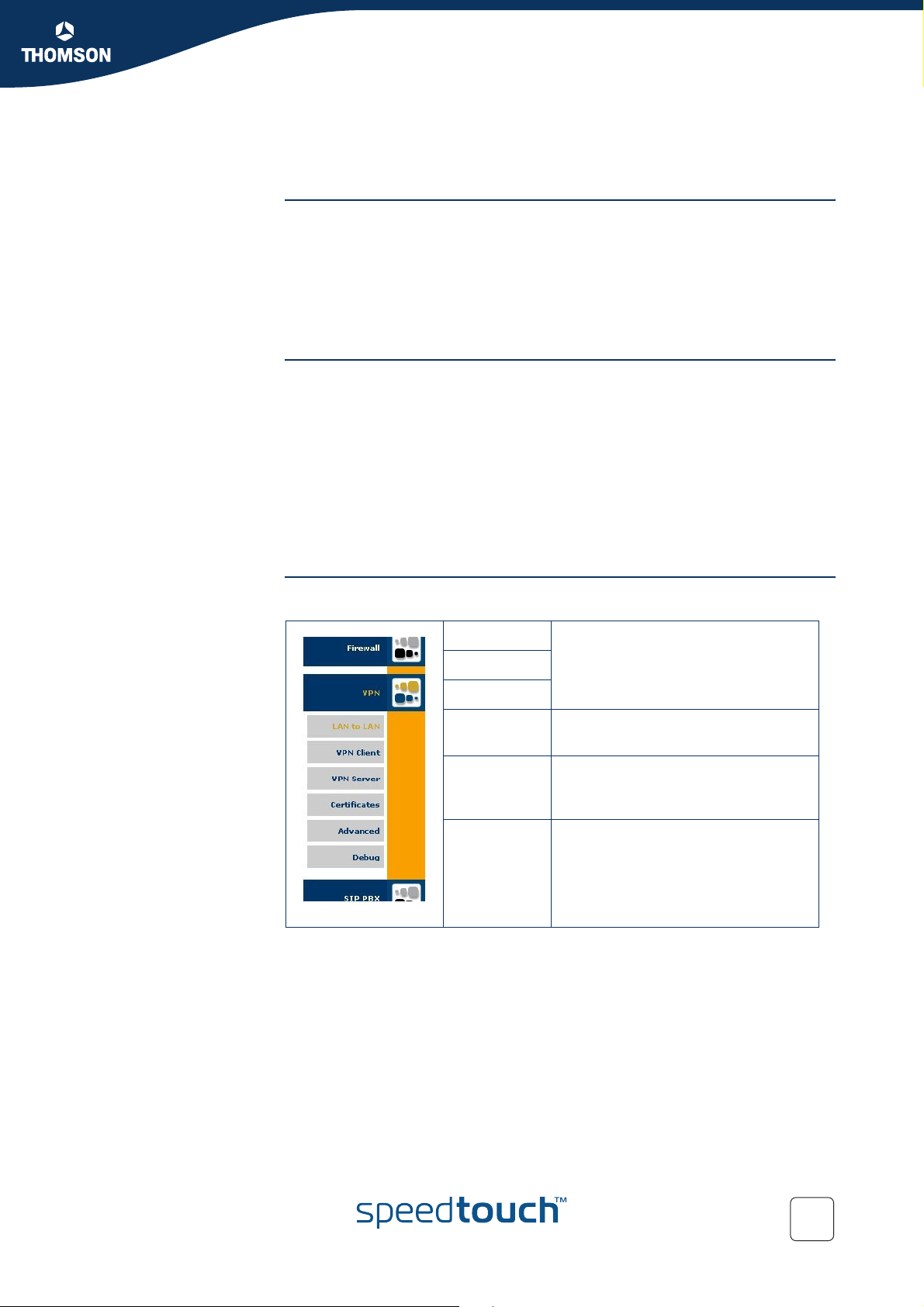
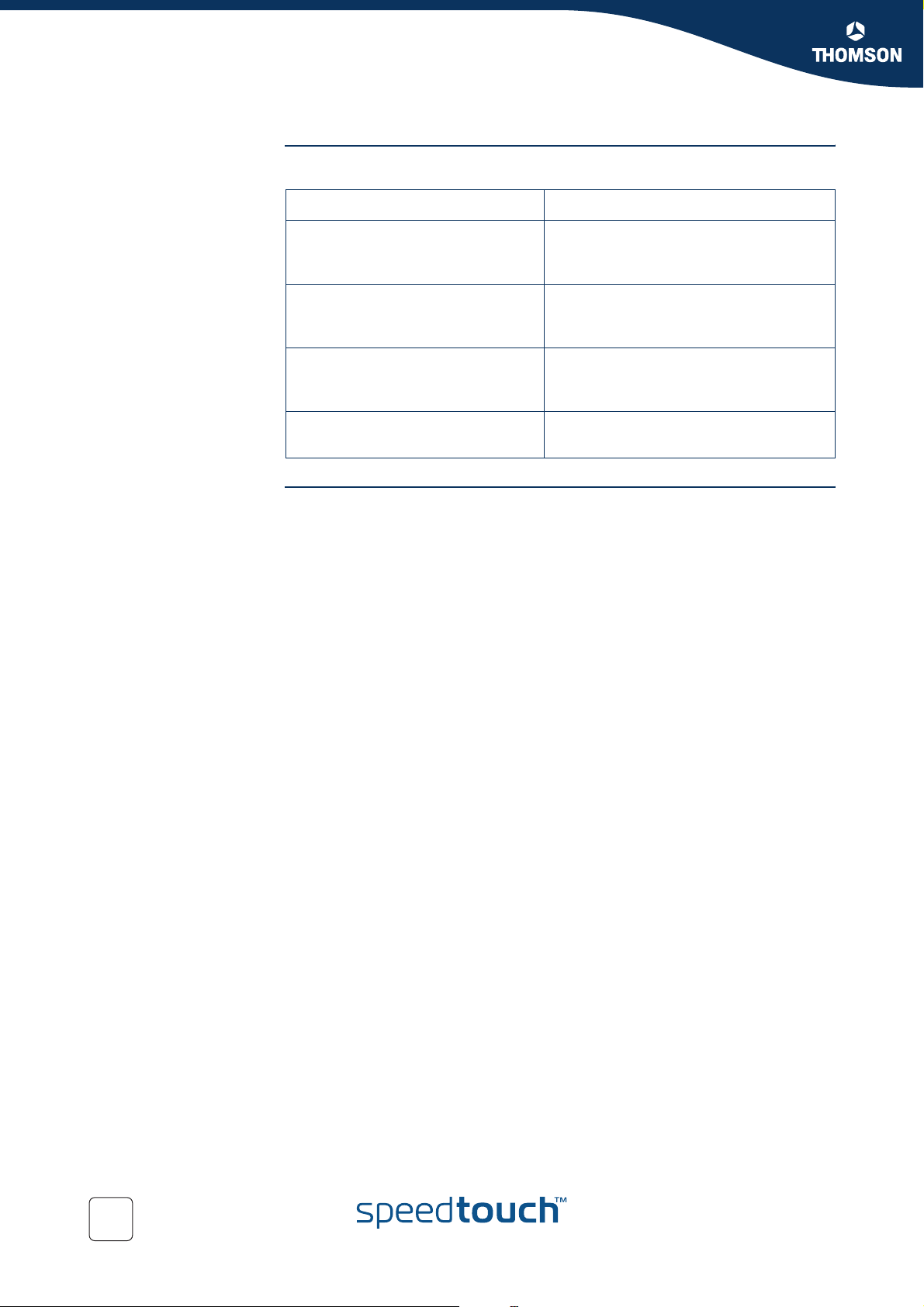
VPN Menu All IPSec related configuration pages are accessed via Expert Mode > VPN.
LAN to LAN
VPN Client
VPN Server
Certificates Access to the Certificate configuration
Advanced Access to the Advanced configuration
Debug Debugging pages, allowing you to
Access to user-friendly configuration
pages for these specific application
scenarios.
pages.
pages, reflecting the commands and
command groups of the CLI.
diagnose VPN connection problems.
E-DOC-CTC-20051017-0169 v0.1
23
Page 26
Chapter 3
Configuration via Local Pages
In this section The following topics are discussed in this section:
Topic Page
3.1 LAN to LAN Application 25
3.2 VPN Client 51
3.3 VPN Server 63
3.4 Certificates 73
3.5 Advanced VPN Menu 75
24
E-DOC-CTC-20051017-0169 v0.1
Page 27
3.1 LAN to LAN Application
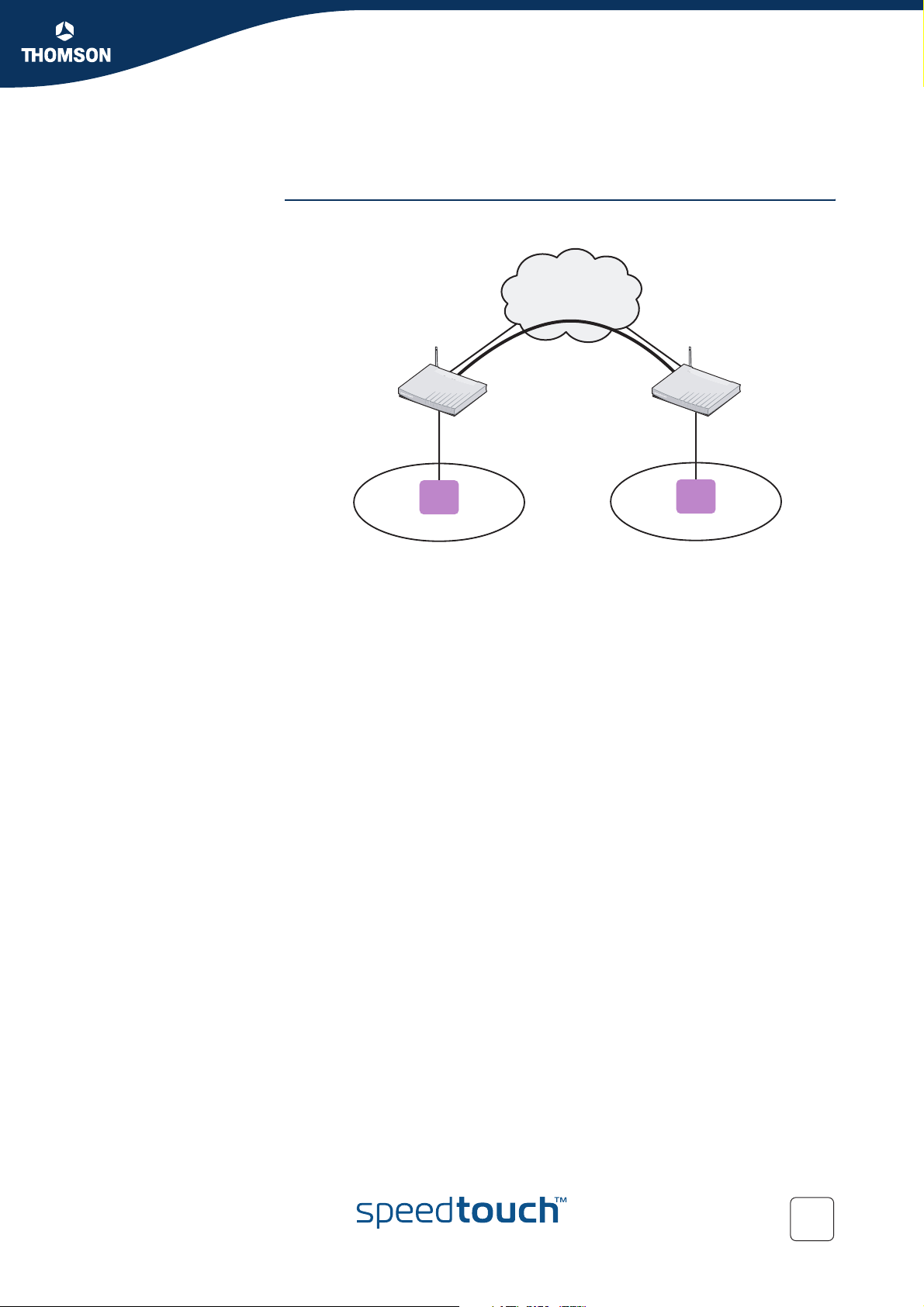
Reference network A simple LAN-to-LAN network configuration is shown here.
Internet
Chapter 3
Configuration via Local Pages
SpeedTouch A SpeedTouch B
10.0.0.254 20.0.0.254
Host
10.0.0.1
100.100.0.1 200.200.0.1
Host
20.0.0.5
Network 10.0.0.0/24 Network 20.0.0.0/24
The figure shows two LAN networks connected via a SpeedTouch™ to the public
Internet. In each LAN segment, the IP addresses of the terminals are typically
managed by a DHCP server, which may be the built-in DHCP server of the
SpeedTouch™.
Making use of the VPN capabilities of the SpeedTouch™, it is possible to connect
the two LAN segments via a secure VPN tunnel over the public Internet. At each
peer the SpeedTouch™ serves as an IPSec Security Gateway.
A dedicated set of user-friendly configuration pages allows you to quickly and easily
implement this scenario. Selections are made in accordance to the data known to
the user, and the VPN layout.
The GUI pages are organized along two main alternative paths.
Path 1: You know exactly to which Remote Gateway you want to establish a
VPN connection. You know its location in the public Internet (either the IP
address or the domain name). This generally is the case in a symmetrical LANto-LAN scenario.
Path 2: Your SpeedTouch™ is located in a central facility where services are
provided to remote locations that require a secure connection. For the
moment, you have no idea which Remote Gateway may want to establish a
secure connection. In this case, your SpeedTouch™ always has the role of
responder in the VPN connection establishment negotiations. It can not initiate
the establishment of a VPN connection. This leads to an asymmetrical LAN-toLAN scenario, where one peer is always the responder, while the remote
peer(s) is/are the initiator. You can think of a corporate head quarter that
constructs a hub and spoke VPN network with its branch offices. It is
convenient to configure the SpeedTouch™ at the head quarter in such a way
that it will accept new branch offices in the VPN without requiring any
adaptation to its configuration.
E-DOC-CTC-20051017-0169 v0.1
25
Page 28
Chapter 3
Configuration via Local Pages
Selecting the LAN to
LAN application
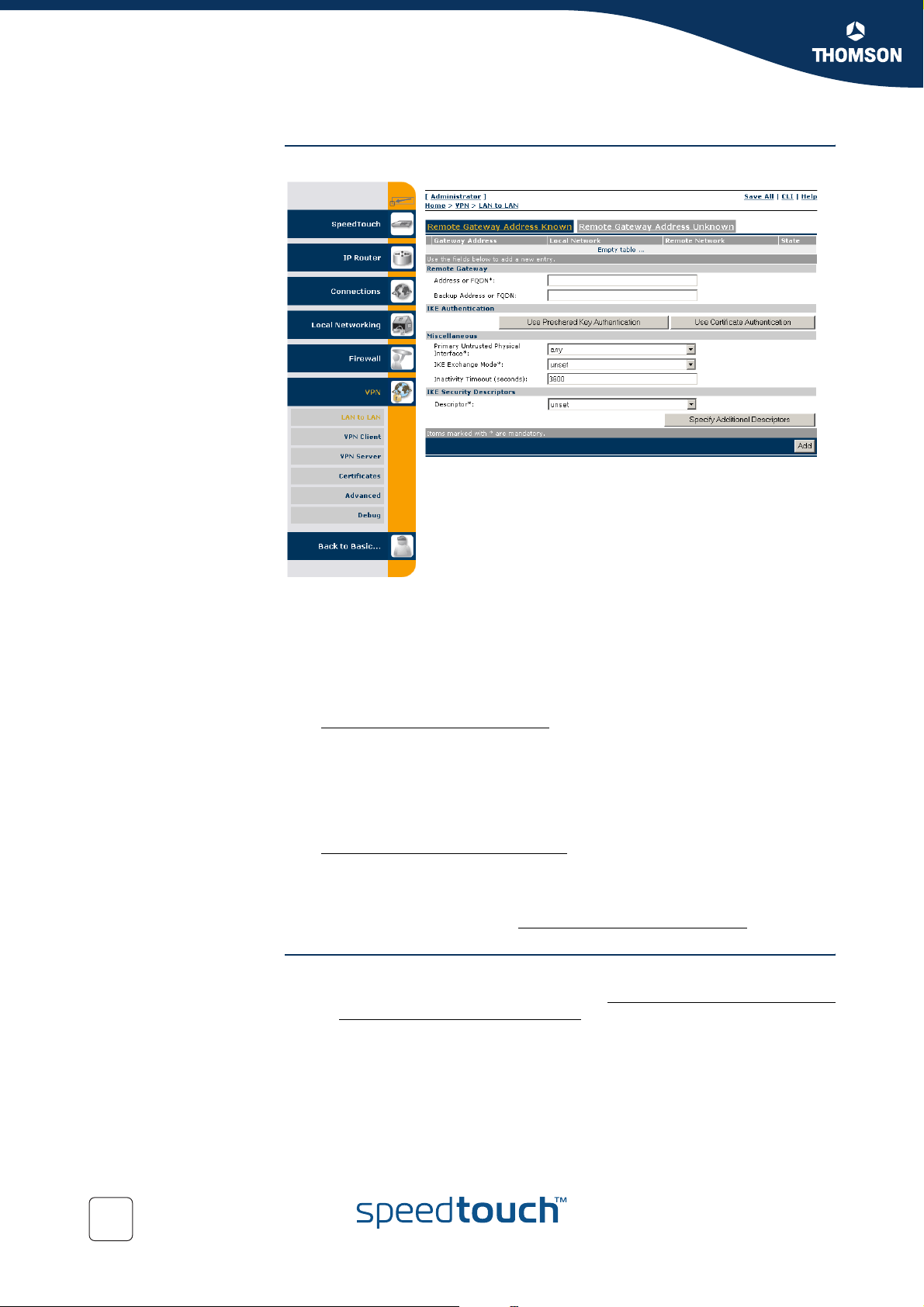
In Expert Mode, click VPN > LAN to LAN. As a result, the following page is shown
This page contains two main tab pages. Select one of the alternative pages,
according to which VPN context best describes your situation.
When you know the network address or domain name of the remote Security
Gateway, your SpeedTouch™ can either take the initiative to set up an IPSec
tunnel to that remote Gateway, or it can wait until the remote gateway
requests to set up a tunnel.
If this is the VPN context that best describes you situation, then select
Remote Gateway Address Known.
and proceed with section “3.1.1 Remote Gateway Address Known Page” on
page 27.
Alternatively, there may be no need to take the initiative to set up a VPN
tunnel. In your situation you rather wait until a remote Gateway requests you
to set up a tunnel. In this situation you may not even know the location of the
Remote Gateway. In this case, select
Remote Gateway Address Unknown.
and proceed with section “3.1.2 Remote Gateway Address Unknown Page” on
page 35.
In a simple LAN to LAN connection where two peers are connected, at least one of
the peers should be configured via Remote Gateway Address Known.
Outline of a
configuration procedure
26
Perform the following steps to configure your LAN to LAN application:
1 On the LAN to LAN Web page, select either Remote Gateway Address Known
or Remote Gateway Address Unknown.
2 Configure the Remote Gateway parameters.
3 Define the Connection parameters.
4 Save the configuration.
The configuration pages you encounter during this procedure are described in more
detail below.
E-DOC-CTC-20051017-0169 v0.1
Page 29
Chapter 3
Configuration via Local Pages
3.1.1 Remote Gateway Address Known Page
VPN context You know the location of the Remote Gateway in the public Internet, either by its IP
address or its FQDN. In this case, the SpeedTouch™ can connect either as an
initiator or as a responder. As an initiator of a connection you are capable of starting
a secure connection from your SpeedTouch™. As a responder, a connection will be
started when the remote Security Gateway initiates the negotiations.
When this description fits best your VPN context, then the Remote Gateway
Address Known page is your starting page for the configuration of your LAN to LAN
scenario.
Initial page When you click Remote Gateway Address Known, the following page is displayed:
The page contains a number of buttons and fields to complete.
It is recommended to fill out the page from top to bottom, starting with the Remote
Gateway address parameters.
When you click a button, the page layout changes, revealing other fields and
buttons. More information about the various fields and buttons is found below.
E-DOC-CTC-20051017-0169 v0.1
27
Page 30
Chapter 3
Configuration via Local Pages
Buttons You can use one of the following buttons:
Click ... To ...
Use Preshared Key Authentication Reveal additional parameter fields
required for the configuration of
Preshared Key Authentication.
Use Certificate Authentication Reveal additional parameter fields
required for the configuration of
Certificate Authentication.
Specify Additional Descriptors Reveal additional fields where you can
specify alternative IKE Security
Descriptors.
Add Add a completely configured peer to the
configuration
Remote Gateway The Remote Gateway parameters identify the peer Security Gateway in the IP
network.
Address or FQDN:
Fill out the publicly known network location of the remote Gateway. You can
specify the public IP address, if it is invariable and known. More often, the
publicly known FQDN (such as vpn.corporate.com) will be used.
Backup Address or FQDN:
This field can optionally be filled out in a configuration with a backup remote
Security Gateway. If no backup gateway is available, you leave this field open.
28
E-DOC-CTC-20051017-0169 v0.1
Page 31

Miscellaneous Comprises the following settings:
Primary Untrusted Physical Interface:
This field shows a list of your SpeedTouch™ interfaces. You select the
preferred Primary Untrusted Physical Interface. This interface is used as the
primary carrier for your VPN connection. In general, the primary untrusted
interface is your DSL connection to the public Internet.
In the SpeedTouch™ the routing engine determines which interface is used for
the VPN connection (your DSL connection to the Internet in most cases). So,
what is the relevance to select a physical interface?
First of all, for incoming VPN connections where your SpeedTouch™ is the
responder in the IKE negotiations, the interface is part of the matching process
for accepting the connection. Selecting any has the effect of removing this
matching criterion. If you select a specific interface as Primary Untrusted
Physical Interface, then a new incoming VPN connection on a backup interface
is not accepted.
Secondly, if your SpeedTouch™ is equipped with a backup physical interface,
for example an ISDN backup interface, then this field determines the preferred
interface for your VPN connection. This interface is used whenever it is
available. When this interface fails, the active VPN connections are re-routed
via the backup interface. When the primary interface becomes available again,
the VPN connections are re-routed to the primary interface. On the other hand,
when you select any as the Primary Untrusted Physical Interface and this
interface fails, the active VPN connections are also re-routed to the backup
interface. But when the DSL connection becomes available again, the VPN
connections are not re-routed as long as the backup connection is available.
IKE Exchange Mode:
IKE specifies two modes of operation for the Phase 1 negotiations: main mode
and aggressive mode. Main mode is more secure while aggressive mode is
quicker.
Inactivity Timeout:
When no traffic is detected at the peer for a certain period, it is decided that the
tunnel is not used any more, and the IKE session is terminated. All IPSec
connections supported by the IKE session are terminated as well.
This option sets the value of the inactivity timer.
Chapter 3
Configuration via Local Pages
E-DOC-CTC-20051017-0169 v0.1
Inactivity Timeout default value
seconds 3600
29
Page 32

Chapter 3
Configuration via Local Pages
IKE Security Descriptors
Page layout with
additional Descriptors
The IKE Security Descriptor bundles the security parameters used for the IKE
Security Association (Phase1).
A number of IKE Security Descriptors are pre-configured in the SpeedTouch™, and
can be selected from a list. Select a Security Descriptor in compliance with the IKE
security parameters configured in the remote Security Gateway.
For example, the pre-configured IKE Security Descriptor AES_MD5, used in various
examples throughout this document, contains the following settings:
Parameter Value for AES_MD5
Cryptographic function AES
Hash function HMAC-MD5
Diffie-Hellman group MODP768 (= group 1)
IKE SA lifetime in seconds. 3600 seconds (= 1 hour)
The contents of the IKE Security Descriptors can be verified via
Advanced > Peers > Security Descriptors.
It is recommended to use AES as preferred encryption method. AES is more
advanced, compared to DES or 3DES. It is faster for comparable key
lengths, and provides better security.
When you click Specify Additional Descriptors, the IKE Security Descriptors area of
the page is updated and shows additional fields where you can specify up to four
alternative IKE Security Descriptors:
30
These will be used as alternative valid proposals in the IKE negotiations.
E-DOC-CTC-20051017-0169 v0.1
Page 33

Chapter 3
Configuration via Local Pages
Page layout for pre-
shared key
authentication
When you click Use Preshared Key Authentication, the initial page is updated in the
following way:
E-DOC-CTC-20051017-0169 v0.1
31
Page 34

Chapter 3
Configuration via Local Pages
IKE Authentication with
Preshared Key
When you select Use Preshared Key Authentication, the following fields have to be
completed:
Preshared Secret:
A string to be used as a secret password for the VPN connection. This secret
needs to be identically configured at both peers (local and remote peer).
Confirm Secret:
The Preshared Secret value is not shown in clear text in the SpeedTouch™
Web page. In order to protect from typing errors, you have to type the key
twice, in order to confirm your original entry.
Local ID Type and Local ID:
The Local ID identifies the local SpeedTouch™ during the Phase 1 negotiation
with the remote Security Gateway. This identity must match the settings in the
remote Security Gateway in order to successfully set up the IKE Security
Association. The identity types supported in the SpeedTouch™ are listed in
the table below.
Remote ID Type and Remote ID:
The Remote ID identifies the remote Security Gateway during the Phase 1
negotiation. This identity must match the settings in the remote Security
Gateway in order to successfully set up the IKE Security Association. The
identity types supported in the SpeedTouch™ are listed in the table below.
Identity type Keyword Examples
IP address addr 10.0.0.1
Fully qualified domain name fqdn sales.corporate.net
Page layout for
certificate
authentication
IKE Authentication:
Certificate parameters
User fully qualified domain
name
Distinguished name dn dc=corpor,uid=user
Key identity keyid myid
If you encounter problems during the IKE negotiations, use the Debug >
Logging page to verify that the Identity Type and Identity of the two peer
Security Gateways correspond with each other.
When you click Use Certificate Authentication, the IKE Authentication area of the
page is updated in the following way:
When you select Use Certificate Authentication, you have to fill out the
Distinguished Name of the local and remote Certificates.
userfqdn
john.doe@corporate
.net
32
E-DOC-CTC-20051017-0169 v0.1
Page 35

Chapter 3
Configuration via Local Pages
Example of a completed
page
The illustration below shows a completed page. The data in the various fields
correspond with the VPN layout shown on page 25:
Pre-shared key was selected as authentication method.
keyid was selected for the local and remote identity.
After the page was completed, the remote gateway settings were added to the
configuration by clicking Add.
At the bottom of the screen additional buttons appear, which are explained below.
E-DOC-CTC-20051017-0169 v0.1
33
Page 36

Chapter 3
Configuration via Local Pages
Buttons You can use one of the following buttons:
Click ... To ...
Stop All Connections to this
Gateway
Apply Apply modifications made to the settings
Delete Delete the selected remote Security
New Gateway Start defining a new remote Security
New Connection to this Gateway Start defining a new connection to the
Status Show the operational status of the
Statistics Show the traffic carried by the VPN
Stop all VPN connections to the selected
remote Security Gateway.
of the selected remote Security Gateway.
Gateway from the configuration.
Gateway.
selected remote Security Gateway.
connections to the selected remote
Security Gateway. The status is shown at
the bottom of the page.
connections to the selected remote
Security Gateway. The data are shown at
the bottom of the page.
34
E-DOC-CTC-20051017-0169 v0.1
Page 37

Configuration via Local Pages
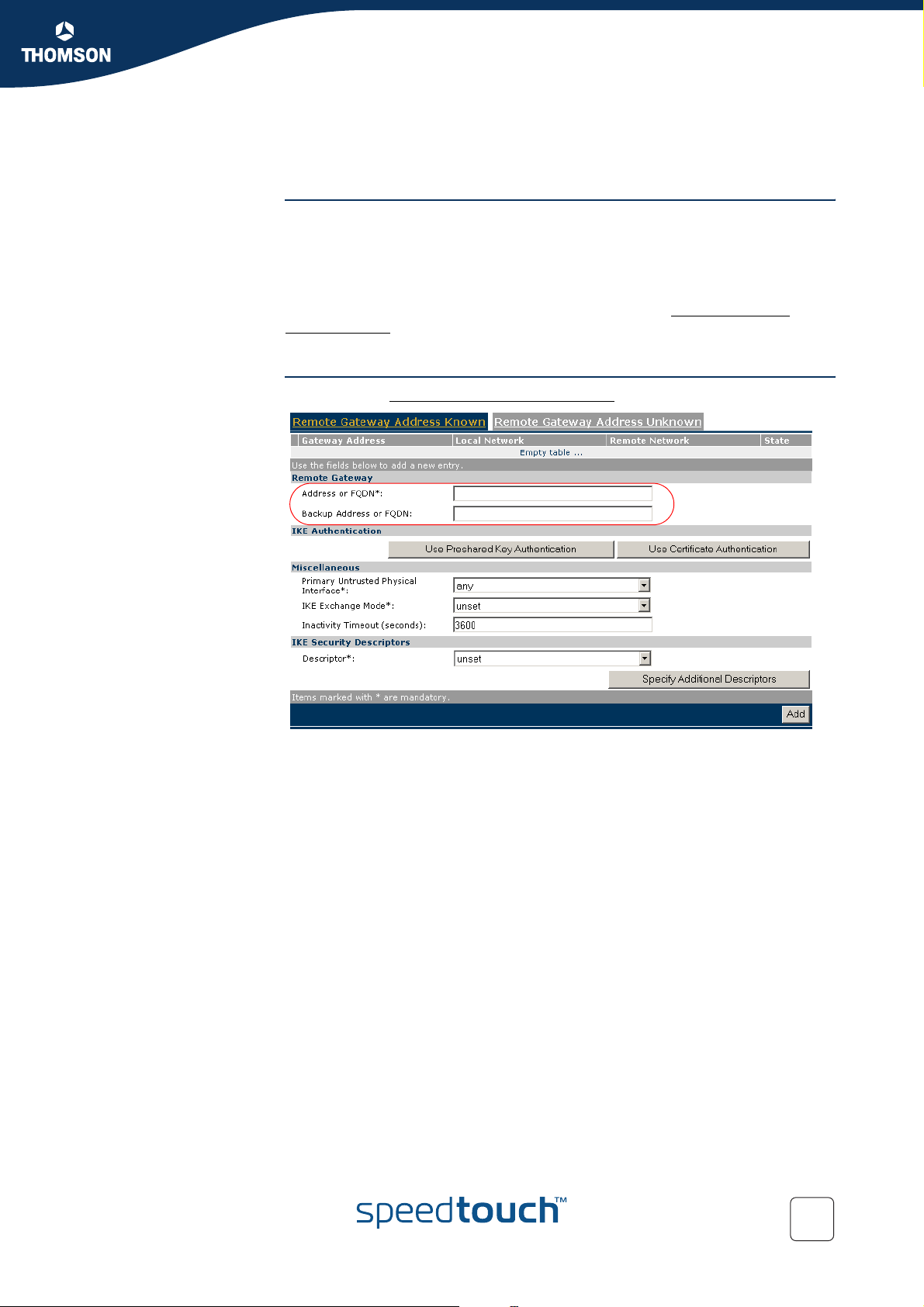
3.1.2 Remote Gateway Address Unknown Page
VPN context Your SpeedTouch™ may have to set up (simultaneous) VPN connections with
various remote Security Gateways. At the time you configure your SpeedTouch™,
you have no clear idea about the location of the Remote Gateway(s) in the network.
This may be the case in a central location of a large network, where remote
locations may be added as time passes. It is an asset if you can configure the
SpeedTouch™ at the central location in such a way that the addition of new remote
sites requires no intervention at the central site.
In this case, the SpeedTouch™ is obviously not able to take the initiative to contact
the Remote Gateway. So, the role of initiator is excluded. Your SpeedTouch™ can
only act as a responder for a Remote Gateway that request a VPN connection. Of
course, both peers need to know and agree on the security parameters in order to
have access to the VPN.A secure connection will be established with any Remote
Gateway that meets your SpeedTouch™ VPN settings, regardless its location in the
public network.
When this description fits best your VPN context, then the Remote Gateway
Address Unknown page is your starting page for the configuration of your LAN to
LAN scenario.
Chapter 3
Example As an example, this context may be encountered at the head office of a company
Aggressive Mode initial
page
that is constructing a VPN with its remote offices. New remote locations may join
the VPN without the need of any reconfiguration actions at the head office.
When you click Remote Gateway Address Unknown, the following page is
displayed:
At the top of the page, you find a main selection between Aggressive Mode and
Main Mode. Furthermore, the page contains a number of buttons and fields to
complete. By clicking a button, the page layout changes, revealing other fields and
buttons. More information about the various fields and buttons is found below.
E-DOC-CTC-20051017-0169 v0.1
35
Page 38

Chapter 3
Configuration via Local Pages
Aggressive Mode
versus Main Mode
Buttons You can use one of the following buttons:
IKE specifies two modes of operation for the Phase 1 negotiations: main mode and
aggressive mode. Main mode is more secure while aggressive mode is quicker.
Click ... To ...
Aggressive mode Switch to the Aggressive Mode
configuration page. This page is shown
by default when you click Remote
Gateway Address Unknown.
Main mode Switch to the Main Mode configuration
page.
Use Preshared Key Authentication Reveal additional parameter fields
required for the configuration of
Preshared Key Authentication.
Use Certificate Authentication Reveal additional parameter fields
required for the configuration of
Certificate Authentication.
Specify Additional Descriptors Reveal additional fields where you can
specify alternative IKE Security
Descriptors.
Add Add a completely configured peer to the
configuration.
36
E-DOC-CTC-20051017-0169 v0.1
Page 39

Miscellaneous Comprises the following settings:
Primary Untrusted Physical Interface:
This field shows a list of your SpeedTouch™ interfaces. You select the
preferred Primary Untrusted Physical Interface. This interface is used as the
primary carrier for your VPN connection. In general, the primary untrusted
interface is your DSL connection to the public Internet.
In the SpeedTouch™ the routing engine determines which interface is used for
the VPN connection (your DSL connection to the Internet in most cases). So,
what is the relevance to select a physical interface?
First of all, for incoming VPN connections where your SpeedTouch™ is the
responder in the IKE negotiations, the interface is part of the matching process
for accepting the connection. Selecting any has the effect of removing this
matching criterion. If you select a specific interface as Primary Untrusted
Physical Interface, then a new incoming VPN connection on a backup interface
is not accepted.
Secondly, if your SpeedTouch™ is equipped with a backup physical interface,
for example an ISDN backup interface, then this field determines the preferred
interface for your VPN connection. This interface is used whenever it is
available. When this interface fails, the active VPN connections are re-routed
via the backup interface. When the primary interface becomes available again,
the VPN connections are re-routed to the primary interface. On the other hand,
when you select any as the Primary Untrusted Physical Interface and this
interface fails, the active VPN connections are also re-routed to the backup
interface. But when the DSL connection becomes available again, the VPN
connections are not re-routed as long as the backup connection is available.
Inactivity Timeout:
When no traffic is detected at the peer for a certain period, it is decided that the
tunnel is not used any more, and the IKE session is terminated. All IPSec
connections supported by the IKE session are terminated as well.
This option sets the value of the inactivity timer.
Chapter 3
Configuration via Local Pages
Inactivity Timeout default value
seconds 3600
E-DOC-CTC-20051017-0169 v0.1
37
Page 40

Chapter 3
Configuration via Local Pages
IKE Security Descriptors
Page layout with
additional Descriptors
The IKE Security Descriptor bundles the security parameters used for the IKE
Security Association (Phase1).
A number of IKE Security Descriptors are pre-configured in the SpeedTouch™, and
can be selected from a list. Select a Security Descriptor in compliance with the IKE
security parameters configured in the remote Security Gateway.
For example, the pre-configured IKE Security Descriptor AES_MD5, used in various
examples throughout this document, contains the following settings:
Parameter Value for AES_MD5
Cryptographic function AES
Hash function HMAC-MD5
Diffie-Hellman group MODP768 (= group 1)
IKE SA lifetime in seconds. 3600 seconds (= 1 hour)
The contents of the IKE Security Descriptors can be verified via
Advanced > Peers > Security Descriptors.
It is recommended to use AES as preferred encryption method. AES is more
advanced, compared to DES or 3DES. It is faster for comparable key
lengths, and provides better security.
When you click Specify Additional Descriptors, the IKE Security Descriptors area of
the page is updated and shows additional fields where you can specify up to four
alternative IKE Security Descriptors:
38
These will be used as alternative valid proposals in the IKE negotiations.
E-DOC-CTC-20051017-0169 v0.1
Page 41

Chapter 3
Configuration via Local Pages
Page layout for pre-
shared key
authentication
When you click Use Preshared Key Authentication, the initial page is updated in the
following way:
E-DOC-CTC-20051017-0169 v0.1
39
Page 42

Chapter 3
Configuration via Local Pages
IKE Authentication with
Preshared Key
When you select Use Preshared Key Authentication, the following fields have to be
completed:
Preshared Secret:
A string to be used as a secret password for the VPN connection. This secret
needs to be identically configured at both peers (local and remote peer).
Confirm Secret:
The Preshared Secret value is not shown in clear text in the SpeedTouch™
Web page. In order to protect from typing errors, you have to type the key
twice, in order to confirm your original entry.
Local ID Type and Local ID:
The Local ID identifies the local SpeedTouch™ during the Phase 1 negotiation
with the remote Security Gateway. This identity must match the settings in the
remote Security Gateway in order to successfully set up the IKE Security
Association. The identity types supported in the SpeedTouch™ are listed in
the table below.
Remote ID Type and Remote ID:
The Remote ID identifies the remote Security Gateway during the Phase 1
negotiation. This identity must match the settings in the remote Security
Gateway in order to successfully set up the IKE Security Association. The
identity types supported in the SpeedTouch™ are listed in the table below.
Identity type Keyword Examples
IP address addr 10.0.0.1
Fully qualified domain name fqdn sales.corporate.net
Page layout for
certificate
authentication
IKE Authentication:
Certificate parameters
User fully qualified domain
name
Distinguished name dn dc=corpor,uid=user
Key identity keyid myid
If you encounter problems during the IKE negotiations, use the Debug >
Logging page to verify that the Identity Type and Identity of the two peer
Security Gateways correspond with each other.
When you click Use Certificate Authentication, the IKE Authentication area of the
page is updated in the following way:
When you select Use Certificate Authentication, you have to fill out the
Distinguished Name of the local and remote Certificates.
userfqdn
john.doe@corporate
.net
40
E-DOC-CTC-20051017-0169 v0.1
Page 43

Main Mode initial page When you click Main Mode, the following page is displayed:
By clicking a button, the page layout changes, revealing other fields and buttons.
More information about the various fields and buttons is found below.
Chapter 3
Configuration via Local Pages
Buttons You can use one of the following buttons:
Click ... To ...
Use Preshared Key Authentication Reveal additional parameter fields
Use Certificate Authentication Reveal additional parameter fields
Specify Additional Descriptors Reveal additional fields where you can
Apply Confirm the IKE Authentication, IKE
IKE Security Descriptors
The IKE Security Descriptor bundles the security parameters used for the IKE
Security Association (Phase1).
A number of IKE Security Descriptors are pre-configured in the SpeedTouch™, and
can be selected from a list. Select a Security Descriptor in compliance with the IKE
security parameters configured in the remote Security Gateway.
The contents of the IKE Security Descriptors can be verified via
Advanced > Peers > Security Descriptors.
required for the configuration of
Preshared Key Authentication.
required for the configuration of
Certificate Authentication.
specify alternative IKE Security
Descriptors.
Security Descriptors and Miscellaneous
parameters and reveal additional
parameters to complete the remote
Security Gateway profile.
E-DOC-CTC-20051017-0169 v0.1
41
Page 44

Chapter 3
Configuration via Local Pages
Page layout with
additional Descriptors
Miscellaneous Comprises the following setting:
Page layout for pre-
shared key
authentication
When you click Specify Additional Descriptors, the IKE Security Descriptors area of
the page is updated and shows additional fields where you can specify up to four
alternative IKE Security Descriptors:
These will be used as alternative valid proposals in the IKE negotiations.
Inactivity Timeout:
When no traffic is detected at the peer for a certain period, it is decided that the
tunnel is not used any more, and the IKE session is terminated. All IPSec
connections supported by the IKE session are terminated as well.
This option sets the value of the inactivity timer.
Inactivity Timeout default value
seconds 3600
When you click Use Preshared Key Authentication, the initial page is updated in the
following way:
IKE Authentication with
Preshared Key
42
When you select Use Preshared Key Authentication, the following fields have to be
completed:
Preshared Secret:
A string to be used as a secret password for the VPN connection. This secret
needs to be identically configured at both peers (local and remote peer).
Confirm Secret:
The Preshared Secret value is not shown in clear text in the SpeedTouch™
Web page. In order to protect from typing errors, you have to type the key
twice, in order to confirm your original entry.
E-DOC-CTC-20051017-0169 v0.1
Page 45

Chapter 3
Configuration via Local Pages
Page layout for
certificate
authentication
IKE Authentication:
Certificate parameters
Main mode expanded
page
When you click Use Certificate Authentication, the IKE Authentication area of the
page is updated in the following way:
When you select Use Certificate Authentication, you have to fill out the
Distinguished Name of the local and remote Certificates.
When you click Apply after you fill out the IKE Authentication, IKE Security
Descriptors and Miscellaneous parameters, the following page is displayed:
E-DOC-CTC-20051017-0169 v0.1
The Identification & Interface parameters are described below.
43
Page 46

Chapter 3
Configuration via Local Pages
Identification &
Interface
The Identification & Interface fields have to be filled out with the following information:
Local ID Type and Local ID:
The Local ID identifies the local SpeedTouch™ during the Phase 1 negotiation
with the remote Security Gateway. This identity must match the settings in the
remote Security Gateway in order to successfully set up the IKE Security
Association. The identity types supported in the SpeedTouch™ are listed in
the table below.
Remote ID Type and Remote ID:
The Remote ID identifies the remote Security Gateway during the Phase 1
negotiation. This identity must match the settings in the remote Security
Gateway in order to successfully set up the IKE Security Association. The
identity types supported in the SpeedTouch™ are listed in the table below.
Identity type Keyword Examples
IP address addr 10.0.0.1
Fully qualified domain
name
User fully qualified domain
name
Distinguished name dn dc=corpor,uid=user
Key identity keyid myid
fqdn sales.corporate.net
userfqdn john.doe@corporate.net
If you encounter problems during the IKE negotiations, use the Debug >
Logging page to verify that the Identity Type and Identity of the two peer
Security Gateways correspond with each other.
44
E-DOC-CTC-20051017-0169 v0.1
Page 47

Chapter 3
Configuration via Local Pages
Example of a completed
page
The illustration below shows a completed page. The data in the various fields
correspond with the VPN layout shown on page 25:
Pre-shared key was selected as authentication method.
keyid was selected for the local and remote identity.
After the page was completed, the remote gateway settings were added to the
configuration by clicking Add. At the bottom of the screen additional buttons
appear, which are explained below.
E-DOC-CTC-20051017-0169 v0.1
45
Page 48

Chapter 3
Configuration via Local Pages
Buttons You can use one of the following buttons:
Click ... To ...
Stop All Connections to this
Gateway
Apply Apply modifications made to the settings
Delete Delete the selected remote Security
New Gateway Start defining a new remote Security
New Connection to this Gateway Start defining a new connection to the
Status Show the operational status of the
Statistics Show the traffic carried by the VPN
Stop all VPN connections to the selected
remote Security Gateway.
of the selected remote Security Gateway.
Gateway.
Gateway.
selected remote Security Gateway.
connections to the selected remote
Security Gateway. The status is shown at
the bottom of the page.
connections to the selected remote
Security Gateway. The data are shown at
the bottom of the page.
46
E-DOC-CTC-20051017-0169 v0.1
Page 49

Chapter 3
Configuration via Local Pages
3.1.3 Connections Page
Page layout When you click New Connection to this Gateway, the following fields are revealed:
In this section of the page, you fill out the characteristics of the Virtual Private
Network you are building. Specify the local and remote private network parameters.
Specify the Security Descriptor you use for this IPSec connection. More information
about the various fields and buttons is found below.
To learn more about Security Descriptors, see section “3.5 Advanced VPN
Menu”.
Buttons You can use one of the following buttons:
Click ... To ...
Specify Additional Descriptors Reveal additional fields where you can
Add Confirm the connection parameters.
specify alternative IPSec Security
Descriptors.
E-DOC-CTC-20051017-0169 v0.1
47
Page 50

Chapter 3
Configuration via Local Pages
Trusted Network The Local and Remote Trusted Network parameters describe which terminals have
access to the secure connection at the local and remote peers, respectively. Two
fields must be completed for each peer: Trusted Network Type and Trusted Network
IP. The Trusted Network Type determines which type of value to use for the Trusted
Network IP field.
The following network types are supported.
Type IP
Valid network types are: Keyword: Examples:
a single IP address address
a single IP subnet subnet
a contiguous IP address
range
The Trusted Network IP values are used during the Phase 1 negotiations, and must
comply with the values configured at the remote Security Gateway.
In the example above, it is assumed that all the hosts in the private (sub)networks
communicate via the secure connection. The local and remote networks cover the
complete LAN segments (10.0.0.0/24 and 20.0.0.0/24, respectively).
range
10.0.0.15
10.0.0.0/24
10.0.0.5-10.0.0.56
10.0.0.[5-56]
Protocol In this field you can optionally restrict the IPSec connection to a single protocol.
Valid entries are listed in the following table.
Protocol
ah egp esp
ggp gre hmp
icmp igmp pup
rdp rsvp tcp
48
udp vines xns-idp
6to4
Select any if you do not want to restrict the connection to a specific protocol.
If you want to restrict the protocols on your secure VPN link, and you need
multiple protocols, then you define a new connection for every individual
protocol. Separate IPSec tunnels will be established for each protocol.
E-DOC-CTC-20051017-0169 v0.1
Page 51

Chapter 3
Configuration via Local Pages
Port If the tcp or udp protocol is selected for the protocol parameter, then the access to
the IPSec connection can be further restricted to a single port. Many well-known
port numbers can be selected from the pull-down menu.
Separate fields are foreseen for the local and remote ports. Typically, identical
values are selected for both fields. In almost all cases, the value any is the most
appropriate choice.
If you want to restrict the ports on your secure VPN link, and you need
multiple ports, then you define a new connection for every individual port.
Separate IPSec tunnels will be established for each port.
IPSec Security
Descriptors
The IPSec Security Descriptor bundles the security parameters used for the Phase 2
Security Association.
A number of IPSec Security Descriptors are pre-configured in the SpeedTouch™,
and can be selected from a list. Select a Security Descriptor in compliance with the
IPSec security parameters configured in the remote Gateway.
For example, the pre-configured IPSec Security Descriptor AES_MD5_TUN, used in
various examples throughout this document, contains the following settings:
Parameter Value for AES_MD5_TUN
Cryptographic function AES
Hash function HMAC-MD5
Use of Perfect Forward Secrecy no
IPSec SA lifetime in seconds. 86400 seconds (= 24 hours)
IPSec SA volume lifetime in kbytes. no volume limit
The ESP encapsulation mode tunnel
The contents of the IPSec Security Descriptors can be verified via the
Advanced menu.
Select Connections, and subsequently Security Descriptors.
Page layout with
additional Descriptors
E-DOC-CTC-20051017-0169 v0.1
When you click Specify Additional Descriptors, the IPSEC Security Descriptors area
of the page is updated and shows additional fields where you can specify up to four
alternative IPSec Security Descriptors:
These will be used as alternative valid proposals in the Phase 2 negotiations.
49
Page 52

Chapter 3
Configuration via Local Pages
Starting and stopping a
connection.
A VPN connection is started automatically when data is sent or received that
complies with the traffic policy.
Alternatively, you can manually start and stop a VPN connection by selecting it in
the table. At the bottom of the page, Start and Stop buttons appear, as shown
below.
50
E-DOC-CTC-20051017-0169 v0.1
Page 53

Chapter 3
Configuration via Local Pages
3.2 VPN Client
VPN context For a VPN client-server scenario a dedicated set of user-friendly configuration pages
is available. Separate pages exist for the client and server sides. In this section the
VPN client configuration page is described.
The VPN client in the SpeedTouch™ can replace a software VPN client installed on a
computer. You can use it for example to connect from your home to your
employer’s corporate network for teleworking. The VPN Client page allows you to
configure a VPN client that functions in Initiator mode. This means that the VPN
client takes the initiative to set up a secure connection to a remote VPN server.
Advantages of the
SpeedTouch™ VPN
Client
Selecting the VPN
Client application
Outline of a VPN Client
configuration procedure
Using the VPN client in the SpeedTouch™ has several advantages over the use of
VPN client software installed on the computer of the end user.
The administrator of the corporate network does not have to worry about
upgrades of the Operating System on the teleworker’s computer (Microsoft
Windows upgrades, new service packs,...). The operation of the VPN client in
the SpeedTouch™ is not affected by these upgrades because it is OS
independent.
Since the VPN client is fully integrated in the SpeedTouch™, it can not be
tampered with, and is probably more secure than software residing on a
computer.
Adverse interactions with computer software, such as firewalls, PPPoE clients,
wireless drivers, viruses and worms are avoided. This guarantees a better
stability and fewer functionality problems.
In Expert Mode, click VPN > VPN Client. The VPN Client Connection Configuration
page appears, which combines all VPN client settings on a single Web page.
Perform the following steps to configure your VPN client:
1 In Expert Mode, select the VPN Client Web page from the VPN menu.
2 Fill out the various parameter fields in the VPN Client Web page.
3 Select the IKE Authentication method. Either Preshared Key or Certificate
Authentication can be selected.
4 Select the Start Mechanism. Either manual dial-in or Automatic Start (Always
On) can be selected.
5 Click Add to confirm the data and Save All to save the configuration.
The configuration pages you encounter during this procedure are described in
detail below.
E-DOC-CTC-20051017-0169 v0.1
51
Page 54

Chapter 3
Configuration via Local Pages
3.2.1 VPN Client Page
Initial page When you click VPN > VPN Client, the following page is displayed:
The page contains a number of buttons and fields to complete.
It is recommended to fill out the page from top to bottom.
When you click a button, the page layout changes, revealing other fields and
buttons. More information about the various fields and buttons is found below.
Buttons You can use one of the following buttons:
Click ... To ...
Use Preshared Key Authentication Reveal additional parameter fields
Use Certificate Authentication Reveal additional parameter fields
Use Automatic Start(Always On) Select the Automatic Start mechanism.
Use Manual Dialup Select the Manual Start mechanism. You
required for the configuration of
Preshared Key Authentication.
required for the configuration of
Certificate Authentication.
The VPN connection is started without
any human intervention whenever the
SpeedTouch™ is active.
start and stop the VPN connection via the
SpeedTouch™ Web pages.
52
Add Add a completely configured peer to the
configuration.
E-DOC-CTC-20051017-0169 v0.1
Page 55

Chapter 3
Configuration via Local Pages
Server IP Address or
FQDN
Backup Server IP
Address or FQDN
Fill out the publicly known network location of the remote Gateway. You can specify
the public IP address, if it is invariable and known. More often, the publicly known
FQDN (such as vpn.corporate.com) will be used.
When you specify an IP address, the SpeedTouch™ expects the VPN server
!
to use an IP address as identifier during the IKE negotiations. When an
FQDN is specified, the SpeedTouch™ expects the VPN server to use an
FQDN as well. If you encounter problems during the IKE negotiations, a
possible cause may be that different identity types are used by client and
server. You can check this via the VPN > Debug > Logging page.
This field can optionally be filled out in a configuration with a backup VPN server. If
no backup VPN server is available, you leave this field open.
IKE Security Descriptor The IKE Security Descriptor bundles the security parameters used for the IKE
Security Association (Phase1).
A number of IKE Security Descriptors are pre-configured in the SpeedTouch™, and
can be selected from a list. Select a Security Descriptor in compliance with the IKE
security parameters configured in the remote VPN server.
For example, the pre-configured IKE Security Descriptor AES_MD5, used in various
examples throughout this document, contains the following settings:
Parameter Value for AES_MD5
Cryptographic function AES
Hash function HMAC-MD5
Diffie-Hellman group MODP768 (= group 1)
IKE SA lifetime in seconds. 3600 seconds (= 1 hour)
The contents of the IKE Security Descriptors can be verified via
Advanced > Peers > Security Descriptors.
It is recommended to use AES as preferred encryption method. AES is more
advanced, compared to DES or 3DES. It is faster for comparable key
lengths, and provides better security.
E-DOC-CTC-20051017-0169 v0.1
53
Page 56

Chapter 3
Configuration via Local Pages
IPSec Security
Descriptor
The IPSec Security Descriptor bundles the security parameters used for the Phase 2
Security Association.
A number of IPSec Security Descriptors are pre-configured in the SpeedTouch™,
and can be selected from a list. Select a Security Descriptor in compliance with the
IPSec security parameters configured in the remote VPN server.
For example, the pre-configured IPSec Security Descriptor AES_MD5_TUN, used in
various examples throughout this document, contains the following settings:
Parameter Value for AES_MD5_TUN
Cryptographic function AES
Hash function HMAC-MD5
Use of Perfect Forward Secrecy no
IPSec SA lifetime in seconds. 86400 seconds (= 24 hours)
IPSec SA volume lifetime in kbytes. no volume limit
The ESP encapsulation mode tunnel
The contents of the IPSec Security Descriptors can be verified via
Advanced > Connections > Security Descriptors.
Exchange Mode IKE specifies two modes of operation for the Phase 1 negotiations: main mode and
aggressive mode. Main mode is more secure while aggressive mode is quicker.
Server Vendor The SpeedTouch™ can interact with VPN servers of various vendors. Because some
vendors implement proprietary features, it is required to select the server vendor.
The vendor specific features are reflected in the parameters required to dial in to the
VPN server. This is explained in more detail below.
Following vendors can be selected:
Select ... when ...
generic the VPN server is either a SpeedTouch™ or is unknown.
You need to specify your e-mail address for the dial-in
procedure (see “ Set of Server Vendor specific
parameters” on page 58).
Cisco you connect to a Cisco VPN server. Cisco requires a
Group ID to be specified for the VPN clients (see “Set of
Server Vendor specific parameters” on page 58).
Nortel you connect to a Nortel VPN server.
54
E-DOC-CTC-20051017-0169 v0.1
Page 57

Chapter 3
Configuration via Local Pages
Primary Untrusted
Physical Interface
This field shows a list of your SpeedTouch™ interfaces. You select the preferred Primary Untrusted Physical Interface. This interface is used as the primary carrier for your VPN connection. In general, the primary untrusted interface is your DSL connection to the public Internet.
In the SpeedTouch™ the routing engine determines which interface is used for the
VPN connection (your DSL connection to the Internet in most cases). So, what is the
relevance to select a physical interface?
In a VPN client the selection is relevant only when your SpeedTouch™ is equipped
with a backup physical interface, for example an ISDN backup interface. This field
determines the preferred interface for your VPN connection. This interface is used
whenever it is available. When this interface fails, the active VPN connections are
re-routed via the backup interface. When the primary interface becomes available
again, the VPN connections are re-routed to the primary interface. On the other
hand, when you select any as the Primary Untrusted Physical Interface and this
interface fails, the active VPN connections are also re-routed to the backup interface.
But when the DSL connection becomes available again, the VPN connections are
not re-routed as long as the backup connection is available.
Virtual IP mapping Either dhcp or nat can be selected.
Selecting dhcp as virtual IP address mapping has the effect that the virtual IP
address attributed by the VPN server to the SpeedTouch™ VPN client is
effectively assigned to the terminal. The SpeedTouch™ creates a new IP
address pool, called a spoofing address pool. The SpeedTouch™will use this
pool to provide a new IP address to the terminal that starts the secure
connection. Simultaneous access to the VPN of multiple terminals in the LAN
is not possible. The VPN server attributes a single virtual IP address.
The spoofing address pool inherits the lease time for IP addresses
from the originally used address pool. In order to have a swift renewal
of IP addresses, it is recommended to set a conveniently low lease
time in the original dhcp address pool. A value of 60 seconds is
suggested.
Selecting nat as virtual IP address mapping has the effect that the VPN server
attributes a virtual IP address to the SpeedTouch™ VPN client. This virtual IP
address is stored in the SpeedTouch™. The SpeedTouch™ will automatically
create a new NAT entry to map the virtual IP address to the IP addresses used
on the local network. Simultaneous access to the VPN of multiple terminals is
supported.
Optional Remote
network
E-DOC-CTC-20051017-0169 v0.1
These settings allow you to limit the accessible area on the remote network.
Normally the VPN server sets this parameter during the tunnel negotiations.
55
Page 58

Chapter 3
Configuration via Local Pages
Page layout for pre-
shared key
authentication
When you click Use Preshared Key Authentication, the initial page is updated in the
following way:
IKE Authentication with
Preshared Key
Page layout for
certificate
authentication
IKE Authentication:
Certificate parameters
When you select Use Preshared Key Authentication, the following fields have to be
completed:
Preshared Secret:
A string to be used as a secret password for the VPN connection. This secret
needs to be identically configured at both peers (local and remote peer).
Confirm Secret:
The Preshared Secret value is not shown in clear text in the SpeedTouch™
Web page. In order to protect from typing errors, you have to type the key
twice, in order to confirm your original entry.
When you click Use Certificate Authentication, the IKE Authentication area of the
page is updated in the following way:
When you select Use Certificate Authentication, you have to fill out the
Distinguished Name of the local and remote Certificates.
56
E-DOC-CTC-20051017-0169 v0.1
Page 59

Chapter 3
Configuration via Local Pages
Starting and stopping a
VPN client connection
Page layout for
Automatic Start
Two start mechanisms are defined:
Manual Dialup
Automatic Start.
When you use pre-shared key authentication, both start mechanisms require a
number of parameters to be set. The set of parameters depends on which Server
Vendor you selected.
Selecting the Manual Dialup method, no further parameters have to be configured.
You have to dial in to the VPN server each time you need the secure connection.
Whenever you dial in, you have to enter a set of parameters to join the VPN.
Select the Automatic Start method when multiple terminals in your LAN have
access to the secure connection, and individual users do not need to authenticate.
The set of parameters required to access the VPN server are stored in the
SpeedTouch™ configuration. Furthermore. you specify the range of local terminals
that may access the secure VPN connection. Once configured, the automatic start
procedure provides permanent access to the secure connection for the authorized
terminals, without further user interaction.
When you use pre-shared key authentication and you click Use Automatic
Start(Always On), an additional set of parameters is shown in the VPN Client
Connection Configuration page.
The set of parameters depends on the selected Server Vendor.
When you selected generic, the following set of parameters is shown:
E-DOC-CTC-20051017-0169 v0.1
When you selected cisco, the following set of parameters is shown:
When you selected nortel, the following set of parameters is shown:
Interworking with a Nortel VPN server is possible only when IKE
!
Authentication is done via Certificates. Pre-shared key authentication can
not be used on an IPSec connection between a SpeedTouch™ VPN client
and a Nortel VPN server.
57
Page 60

Chapter 3
Configuration via Local Pages
Local LAN IP Range In this field you have to configure the local access policy. In other words, you define
which IP range of local terminals has access to the VPN. You can specify either a
single IP address, a subnet, or a range.
Local LAN IP range: Examples:
Set of Server Vendor
specific parameters
a single IP address
a single IP subnet
a contiguous IP address range
When for the IKE Authentication method the Preshared Key method was selected,
some Server Vendor specific fields must be filled out for the Automatic Start
mechanism.
For a generic VPN server:
You have to fill out your e-mail address. This e-mail address (User FQDN) is used as
the local identity of the VPN client.
When building a VPN with multiple SpeedTouch™ devices configured as
!
VPN client at different locations, you must take care to configure a unique email address in each VPN client. The e-mail address is used by the VPN
server as an identifier to bind an IP address to the VPN client.
For a Cisco VPN server:
You have to fill out the Group ID. The value should correspond with the groupname,
as configured on the Cisco VPN server with the command:
10.0.0.15
10.0.0.0/24
10.0.0.5-10.0.0.56
10.0.0.[5-56]
crypto isakmp client configuration group groupname
For a Nortel VPN server:
Interworking with a Nortel VPN server is possible only when IKE
!
Authentication is done via Certificates. Pre-shared key authentication can
not be used on an IPSec connection between a SpeedTouch™ VPN client
and a Nortel VPN server.
Configuring XAuth Optionally, you can use the Extended Authentication protocol in combination with
the Automatic Start mechanism. Simply fill out a Username and Password in the
optional fields, and XAuth is used when the connection is established. The
Username and Password in this case act as a group key for all local terminals
authorized to use the VPN connection.
58
E-DOC-CTC-20051017-0169 v0.1
Page 61

3.2.2 Starting the VPN Client Connection
Chapter 3
Configuration via Local Pages
Method 1:
Automatic Start
Method 2:
Manual Start
In section “ Starting and stopping a VPN client connection” on page 57, the
configuration of the Automatic Start mechanism is explained. All parameters
required for starting the connection are stored in the SpeedTouch™ configuration
file, and no further user interaction is required to start the VPN connection. With
XAuth configured, the authentication parameters are stored in the SpeedTouch™
and can be regarded as a group authentication for all terminals that have access to
the VPN. In case of nat virtual IP mapping multiple terminals may simultaneously
access the VPN. In case of dhcp virtual IP mapping, a single terminal at a time is
allowed to access the VPN.
If the Manual Start mechanism is selected, no connection startup parameters are
configured in the SpeedTouch™. Each time you want access to the VPN, you have
to manually dial in and enter the login parameters. A manual dial-in page is
available in the SpeedTouch™ Web pages.
The manual start mechanism is most suited in a teleworker scenario, where a single
user makes use of the VPN connection.
E-DOC-CTC-20051017-0169 v0.1
59
Page 62

Chapter 3
Configuration via Local Pages
Dialling in 1 Select the VPN server from the table and click Dial-In at the bottom of the
screen.
VPN Client Connect
Page
As a result, the VPN Client Connect
page is shown.
2 Fill out the login parameters and click Continue.
The SpeedTouch™ starts the negotiations to set up the secure VPN
connection. The outcome of the dial-up procedure is shown on the screen.
All active VPN connections are shown at the bottom of the VPN Client Connection
Configuration page.
When you encounter problems to set up the VPN connection, you can use
the Debug page to diagnose the problem. See “5.1 Via the Debug Web
pages” on page 162
The layout of the VPN Client Connect page depends on the IKE Authentication
method and Server Vendor you selected in the VPN Client Connection
Configuration page.
The Client Identification parameter is Server Vendor specific.
Below, an example is shown for a connection to a Cisco VPN server.
60
E-DOC-CTC-20051017-0169 v0.1
Page 63

Chapter 3
Configuration via Local Pages
Client Identification When for the IKE Authentication method the Preshared Key method was selected,
some Server Vendor specific fields must be filled out. See “ Set of Server Vendor
specific parameters” on page 58
Using XAuth When the VPN server uses the Extended Authentication protocol, you fill out your
Username and Password in the optional fields:
E-DOC-CTC-20051017-0169 v0.1
61
Page 64

Chapter 3
Configuration via Local Pages
3.2.3 Closing a Connection
Disconnect procedure At the bottom of the VPN Client Connection Configuration page, all active VPN
connections are shown.
Select the connection you want to terminate and click Disconnect.
The secure connection is closed and is removed from the list of active connections.
62
E-DOC-CTC-20051017-0169 v0.1
Page 65

Chapter 3
Configuration via Local Pages
3.3 VPN Server
VPN context In a VPN client-server scenario, the VPN server is always the responder in the IKE
negotiations. Various VPN clients can dial in to a VPN server, since it supports
multiple simultaneous VPN connections. A VPN server does not know a priori which
remote Security Gateway will attempt to set up a VPN connection. In time, new
users may join the VPN. It is an advantage that the SpeedTouch™ VPN server
requires no modifications to its configuration when new clients are added to the
VPN. The SpeedTouch™ can establish a secure connection with any Remote
Gateway that meets the VPN settings, regardless its location in the public network.
The use of the Extended Authentication protocol can optionally be configured. In
this case, a list of authorized users is composed and stored in the SpeedTouch™.
Selecting the VPN
Server application
Outline of a VPN server
configuration procedure
In Expert Mode, click VPN > VPN Server. The VPN Server Configuration page
appears, which combines all VPN server settings on a single Web page.
Perform the following steps to configure your VPN server:
1 In Expert Mode, select the VPN Server Web page from the VPN menu.
2 Fill out the various parameter fields in the VPN Server Web page.
3 Select the IKE Authentication method. Either Preshared Key or Certificate
Authentication can be selected.
4 Click Apply to confirm the data and Save All to make the configuration
permanent.
5 Optional: If you use the Extended Authentication protocol, you have to
compose an authorized users list.
The configuration pages you encounter during this procedure are described in
detail below.
E-DOC-CTC-20051017-0169 v0.1
63
Page 66

Chapter 3
Configuration via Local Pages
3.3.1 VPN Server Page
Initial page When you click VPN > VPN Server, the following page is displayed:
The page contains a number of buttons and fields to complete.
It is recommended to fill out the page from top to bottom.
When you click a button, the page layout changes, revealing other fields and
buttons. More information about the various fields and buttons is found below.
64
E-DOC-CTC-20051017-0169 v0.1
Page 67

Buttons You can use one of the following buttons:
Click ... To ...
Specify Additional Networks Reveal additional fields where you can
Use Preshared Key Authentication Reveal additional parameter fields
Use Certificate Authentication Reveal additional parameter fields
Specify Additional Descriptors Reveal additional fields where you can
Apply Confirm the VPN server settings.
Chapter 3
Configuration via Local Pages
specify additional descriptors for the
local network open to remote terminals
via a VPN connection.
required for the configuration of
Preshared Key Authentication.
required for the configuration of
Certificate Authentication.
specify alternative Security Descriptors.
Clear All Clear all VPN server settings.
Local Trusted Network The Local Trusted Network open to Remote Clients describes which part of the local
network you want to make accessible for remote VPN clients. Two fields must be
completed: Trusted Network Type and Trusted Network IP. The Trusted Network
Type determines which type of value to use for the Trusted Network IP field.
The following network types are supported.
Type IP
Valid network types are: Keyword: Examples:
a single IP address address
a single IP subnet subnet
The Trusted Network IP values are used during the Phase 1 negotiations, and must
comply with the values configured in the remote VPN client.
10.0.0.15
10.0.0.0/24
E-DOC-CTC-20051017-0169 v0.1
65
Page 68

Chapter 3
Configuration via Local Pages
Page layout with
additional Networks
Clicking Specify Additional Networks allows you to designate up to four addresses/
subnets in case the Local Trusted Network can not be described by a single address/
subnet.
IKE Security Descriptor The IKE Security Descriptor bundles the security parameters used for the IKE
Security Association (Phase1).
A number of IKE Security Descriptors are pre-configured in the SpeedTouch™, and
can be selected from a list. Select a Security Descriptor in function of your security
requirements. The remote VPN clients must comply with the IKE security
parameters configured in the VPN server.
For example, the pre-configured IKE Security Descriptor AES_MD5, used in various
examples throughout this document, contains the following settings:
Parameter Value for AES_MD5
Cryptographic function AES
Hash function HMAC-MD5
Diffie-Hellman group MODP768 (= group 1)
IKE SA lifetime in seconds. 3600 seconds (= 1 hour)
The contents of the IKE Security Descriptors can be verified via
Advanced > Peers > Security Descriptors.
It is recommended to use AES as preferred encryption method. AES is more
advanced, compared to DES or 3DES. It is faster for comparable key
lengths, and provides better security.
The IKE Security Descriptor bundles the security parameters used for the IKE
Security Association (Phase1).
66
E-DOC-CTC-20051017-0169 v0.1
Page 69

Chapter 3
Configuration via Local Pages
Page layout with
additional Descriptors
IPSec Security
Descriptor
When you click Specify Additional Descriptors, the IKE Security Descriptors area of
the page is updated and shows additional fields where you can specify up to four
alternative IKE Security Descriptors:
These will be used as alternative valid proposals in the IKE negotiations.
The IPSec Security Descriptor bundles the security parameters used for the Phase 2
Security Association.
A number of IPSec Security Descriptors are pre-configured in the SpeedTouch™,
and can be selected from the pull-down menu. Select a Security Descriptor in
function of your security requirements. The remote VPN clients must comply with
the security parameters configured in the VPN server.
In the example shown above, the pre-configured IPSec Security Descriptor, called
DES_MD5_TUN is selected.
This descriptor contains following settings:
Parameter Example: DES_MD5_TUN
Cryptographic function DES
Page layout with
additional Descriptors
Hash function HMAC-MD5
Use of Perfect Forward Secrecy no
IPSec SA lifetime in seconds. 86400 seconds (= 24 hours)
IPSec SA volume lifetime in kbytes. no volume limit
The ESP encapsulation mode tunnel
The contents of the IPSec Security Descriptors can be verified via
Advanced > Connections > Security Descriptors.
When you click Specify Additional Descriptors, the IPSEC Security Descriptors area
of the page is updated and shows additional fields where you can specify up to four
alternative IPSec Security Descriptors:
These will be used as alternative valid proposals in the Phase 2 negotiations.
E-DOC-CTC-20051017-0169 v0.1
67
Page 70

Chapter 3
Configuration via Local Pages
Miscellaneous Comprises the following settings:
IKE Exchange Mode:
IKE specifies two modes of operation for the Phase 1 negotiations: main mode
and aggressive mode. Main mode is more secure while aggressive mode is
quicker.
Primary Untrusted Physical Interface:
This field shows a list of your SpeedTouch™ interfaces. You select the
preferred Primary Untrusted Physical Interface. This interface is used as the
primary carrier for your VPN connection. In general, the primary untrusted
interface is your DSL connection to the public Internet.
In the SpeedTouch™ the routing engine determines which interface is used for
the VPN connection (your DSL connection to the Internet in most cases). So,
what is the relevance to select a physical interface?
The VPN server handles incoming VPN connections only. For this kind of
connections, where your SpeedTouch™ is the responder in the IKE
negotiations, the interface is part of the matching process for accepting the
connection. Using the default setting (any) has the effect of removing this
matching criterion. For a VPN server configuration, this is the most convenient
setting. If you select a specific interface as Primary Untrusted Physical
Interface, then a new incoming VPN connection on a backup interface is not
accepted.
The SpeedTouch™ VPN server has no mechanism for re-routing active VPN
connections to a backup physical interface. Even if your SpeedTouch™ is
equipped with an ISDN backup interface, all active VPN connections are lost
when the primary interface of the VPN server fails. The overall network
topology determines whether a VPN client is capable of reaching the backup
interface of the SpeedTouch™ VPN server. It is the responsibility of the VPN
client to set up a new VPN connection.
Inactivity Timeout:
When no traffic is detected at the peer for a certain period, it is decided that the
tunnel is not used any more, and the IKE session is terminated. All IPSec
connections supported by the IKE session are terminated as well.
This option sets the value of the inactivity timer.
68
Inactivity Timeout default value
seconds 3600
E-DOC-CTC-20051017-0169 v0.1
Page 71

VPN Server settings Comprises the following settings:
Virtual IP Range:
Specifies the range of IP addresses from which the VPN client addresses are
selected. An address range or a subnet can be entered for this parameter.
Examples:
10.20.30.[5-50]
10.20.30.*
Netmask
Specifies the netmask provided to the VPN client. Use the dotted decimal
format.
For example: 255.255.255.0
Push IP
Select this check box when you want the VPN server to take the initiative for
assigning an IP address to the VPN clients via IKE Mode Config.
When the check box is not selected, the VPN clients will request an IP address
from the VPN server.
Domain name
The domain name provided to the VPN clients via IKE Mode Config.
Primary DNS IP Address
The IP address of the primary DNS server, provided to the VPN clients via IKE
Mode Config. This is the primary DNS server in the local network that is open
to VPN clients.
Secondary DNS IP Address
The IP address of the secondary DNS server, provided to the VPN clients via
IKE Mode Config. This is the secondary DNS server in the local network that is
open to VPN clients.
Primary WINS IP Address
The IP address of the primary WINS server, provided to the VPN clients via IKE
Mode Config. This is the primary WINS server in the local network that is open
to VPN clients. A WINS server maps NETBIOS names to IP addresses.
Secondary WINS IP Address
The IP address of the secondary WINS server, provided to the VPN clients via
IKE Mode Config. This is the secondary WINS server in the local network that
is open to VPN clients.
XAuth
The SpeedTouch™ VPN server allows the use of the Extended Authorization
protocol with an internal user list. Two different types of Authentication
protocols can be selected: generic and chap. When the use of XAuth is
selected, a list of authorized users is to be composed. This is explained in
“ Authorized Users List” on page 72.
Chapter 3
Configuration via Local Pages
E-DOC-CTC-20051017-0169 v0.1
69
Page 72

Chapter 3
Configuration via Local Pages
Page layout for pre-
shared key
authentication
IKE Authentication with
Preshared Key
When you click Use Preshared Key Authentication, the initial page is updated in the
following way:
When you select Use Preshared Key Authentication, the following fields have to be
completed:
Preshared Secret:
A string to be used as a secret password for the VPN connection. This secret
needs to be identically configured at both peers (local and remote peer).
Confirm Secret:
The Preshared Secret value is not shown in clear text in the SpeedTouch™
Web page. In order to protect from typing errors, you have to type the key
twice, in order to confirm your original entry.
Local ID Type and Local ID:
The Local ID identifies the VPN server during the Phase 1 negotiation with the
remote VPN client. This identity must match the settings in the VPN client in
order to successfully set up the IKE Security Association. The identity types
supported in the SpeedTouch™ are listed in the table below (wildcards not
allowed).
70
Identity type Keyword Examples
IP address addr 10.0.0.1
Fully qualified domain
name
User fully qualified domain
name
Distinguished name dn dc=corpor,uid=user
Key identity keyid myid
For more information about matching the settings of the built-in VPN client of
the SpeedTouch™, see “ Server IP Address or FQDN” on page 53.
fqdn sales.corporate.net
userfqdn john.doe@corporate.net
E-DOC-CTC-20051017-0169 v0.1
Page 73

Configuration via Local Pages
Remote ID (Filter) Type and Remote ID Filter:
The Remote ID Filter identifies the VPN client during the Phase 1 negotiation.
This identity is used as a filter for VPN clients when they join the VPN. Its value
must match the settings in the VPN client in order to successfully set up the
IKE Security Association. The identity types supported in the SpeedTouch™
are listed in the table below.
Identity type Keyword Examples
10.0.0.1
IP address addr
Fully qualified domain name fqdn sales.corporate.net
0.0.0.0 (any address
accepted)
Chapter 3
Page layout for
certificate
authentication
User fully qualified domain
name
Distinguished name dn dc=corpor,uid=user
Key identity keyid myid
Any ID type accepted any -
A SpeedTouch™ VPN client identifies itself with a userfqdn in the form of a
unique e-mail address, when generic is selected for the Server Vendor. In
order to make the configuration of the VPN server independent of the number
of VPN clients, wildcards can be used, as shown in the table above. For
example, *.corporate.net will match with any e-mail address in the domain
corporate.net.
If you encounter problems during the IKE negotiations, use the Debug >
Logging page to verify that the Identity Type and Identity of VPN client and
server correspond with each other.
When you click Use Certificate Authentication, the IKE Authentication area of the
page is updated in the following way:
userfqdn *@
corporate.net
IKE Authentication:
Certificate parameters
E-DOC-CTC-20051017-0169 v0.1
When you select Use Certificate Authentication, you have to fill out the
Distinguished Name of the local and remote Certificates.
71
Page 74

Chapter 3
Configuration via Local Pages
Authorized Users List When you selected the use of XAuth (either generic or chap) in the VPN Server
Configuration page, then clicking Apply reveals an additional section at the top of
the page.
Compose a list of authorized users for the VPN:
1 Enter a User name and corresponding Password.
2 Click Add User.
3 Repeat the previous steps for each individual VPN client you want to grant
access to the VPN.
72
E-DOC-CTC-20051017-0169 v0.1
Page 75

Configuration via Local Pages
3.4 Certificates
Introduction The Certificates Navigation tab gives access to four main pages for certificates
management.
Secure Storage page This page shows the list of certificates stored in the SpeedTouch™.
Request Import page This page allows importing new certificates from a Certificate Authority into the
SpeedTouch™.
Chapter 3
CRL page This page allows managing the use of Certificates Revocation Lists.
CRL Distribution Point This field indicates the URL/URI location a CRL should be retrieved from. The values
must be in the form of a URI and the supported protocols include LDAP and HTTP.
The server name portion of the distribution point should be in the form of an IP
address. Refer to RFCs 1738, 1779 and 1957 for further details on URIs, DNs and
LDAP URIs respectively.
E-DOC-CTC-20051017-0169 v0.1
73
Page 76

Chapter 3
Configuration via Local Pages
CEP page This page allows configuring the Certificates Enrollment Protocol settings.
Enrollment URL This URL point to the location of the CEP script on the Certificate Authority server.
Usually, it has the following form: “http://<host>[:<port>]/<path>”.
<host> is a numeric address, do not use a DNS name
<port> is the port number (by default port 80 is assumed)
<path> is the path to the script, e.g. cgi-bin/pkiclient.exe.
Subject DN See RFC1779. This is the Distinguished Name for the certificate. The value must be a
valid distinguished name in string representation. It can include a common name
(cn=), organization unit (ou=), organization name (o=), locality (l=), province or state
(st=) and country (c=). Use commas to separate the items.
74
E-DOC-CTC-20051017-0169 v0.1
Page 77

Configuration via Local Pages
3.5 Advanced VPN Menu
When to use The Advanced VPN menu gives access to two main pages where the complete
IPSec configuration can be done. These pages are component-oriented, as opposed
to the application-oriented pages described in sections 3.1, 3.2 and 3.3. Componentoriented means that a number of components are constructed and subsequently
combined.
It is highly recommended to use the application-oriented Web pages for
VPN configurations. Only in exceptional cases, these pages will not be
sufficiently flexible to fulfil your requirements. Only in these cases, the
Advanced VPN menu should be used.
Configuring an operational IPSec connection basically consists of the definition of a
Peer Profile and a Connection Profile. The Peer represents the remote Security
Gateway and all the parameters required to set up an IKE Security Association to
this Security Gateway. A Connection represents the IPSec connection and all its
associated parameters.
All parameters of an IPSec configuration can be adjusted, so the functionality of
these Web pages corresponds to the Command Line Interface (CLI). Choices have to
be made in accordance to the data known to the user, and the VPN layout.
The Advanced VPN menu should be used by skilled persons only, as these
!
pages allow you to manually adjust configuration components that are in
general automatically generated by the SpeedTouch™. Therefore, take care
when altering settings in the Advanced VPN menu.
Chapter 3
E-DOC-CTC-20051017-0169 v0.1
75
Page 78

Chapter 3
Configuration via Local Pages
Peer Profiles page When you click VPN > Advanced > Peers, the Peer Profiles page is displayed.
The Peers page gives access to the following sub-pages:
Advanced > Peers sub-pages See
Peer Profiles “3.5.1 Peer Profiles Page” on page 78
Authentication “3.5.2 Authentication Page” on page 82
Descriptors “3.5.3 Peer Descriptors Page” on page 83
Options “3.5.4 Peer Options Page” on page 85
VPN-Client “3.5.5 VPN-Client Page” on page 86
VPN-Server “3.5.6 VPN-Server Page” on page 88
VPN-Server-XAuth “3.5.7 VPN-Server-XAuth Page” on page 90
All peer parameters explained in the CLI configuration method can be filled out in
these pages. The parameters of the various sub-pages are combined in a Peer
Profile, which completely defines a Peer entity.
Enter the Connections page to configure a connection to a peer.
76
E-DOC-CTC-20051017-0169 v0.1
Page 79

Chapter 3
Configuration via Local Pages
Connection Profiles
page
When you click VPN > Advanced > Connections, the Connection Profiles page is
displayed.
The Connections page gives access to the following sub-pages:
Advanced > Connections
See
sub-pages
Connection Profiles “3.5.8 Connection Profiles Page” on page 91
Networks “3.5.9 Networks Page” on page 94
Descriptors “3.5.10 Connection Descriptors Page” on page 96
Options “3.5.11 Connection Options Page” on page 99
Client “3.5.12 Client Page” on page 100
All connection parameters explained in the CLI configuration method can be filled
out in these pages. The parameters of the various sub-pages are combined in a
Connection Profile, which completely defines a connection.
E-DOC-CTC-20051017-0169 v0.1
77
Page 80

Chapter 3
Configuration via Local Pages
3.5.1 Peer Profiles Page
Peer Profiles
page layout
The Peer Profiles page bundles all parameters that define a Peer.
A number of parameters makes use of symbolic descriptors that are defined and
managed on other sub-pages. On the Profiles page, these descriptors are selected
by their symbolic name from a list. Therefore, you need to prepare the descriptors
in other Peers sub-pages, before a complete Peer Profile can be composed in the
Peer Profiles page.
Peer name Give the peer a symbolic name. This name only has local significance inside the
SpeedTouch™. This parameter is not used in the IKE negotiations with the remote
Security Gateway.
Remote address This address localizes the remote Security Gateway in the IP network. Either the
public IP address or the Fully Qualified Domain Name can be used as an identifier.
Backup remote address When a redundant remote Security Gateway is available, its public IP address or
domain name can be specified here. In a basic IPSec configuration, you leave this
field open.
78
E-DOC-CTC-20051017-0169 v0.1
Page 81

Chapter 3
Configuration via Local Pages
Local ID The Local ID identifies the local SpeedTouch™ during the Phase 1 negotiation with
the remote Security Gateway. This identity must match the settings in the remote
Security Gateway in order to successfully set up the IKE Security Association. The
Local ID types supported in the SpeedTouch™ are listed in the following table.
Local ID type Keyword Examples
IP address addr 10.0.0.1
Fully qualified domain name fqdn sales.corporate.net
User fully qualified domain
name
Distinguished name dn dc=corpor,uid=user
Key identity keyid cisid
any any
For a VPN client/server connection between a SpeedTouch™ VPN client and
a Cisco IOS VPN server, select keyid as Local ID type. As Local ID value you
type the user group name used in the Cisco configuration.
userfqdn john.doe@corporate.net
Remote ID The Remote ID identifies the remote Security Gateway during the Phase 1
negotiation. This identity must match the settings in the remote Security Gateway in
order to successfully set up the IKE Security Association. The Remote ID types
supported in the SpeedTouch™ are listed in the following table.
Remote ID type Keyword Examples
IP address addr 10.0.0.1
Fully qualified domain name fqdn sales.corporate.net
User fully qualified domain
name
userfqdn john.doe@corporate.net
E-DOC-CTC-20051017-0169 v0.1
Distinguished name dn dc=corpor,uid=user
Key identity keyid cisid
any any
79
Page 82

Chapter 3
Configuration via Local Pages
Primary Untrusted
Physical Interface
This field shows a list of your SpeedTouch™ interfaces. You select the preferred Primary Untrusted Physical Interface. This interface is used as the primary carrier for your VPN connection. In general, the primary untrusted interface is your DSL connection to the public Internet. On the DSL line, various logical connections can be defined, eventually using different protocol stacks (IpoA, PPPoE, PPPoA,…). The peer entity has to be tied to the correct IP connection.
In the SpeedTouch™ the routing engine determines which interface is used for the
VPN connection (your DSL connection to the Internet in most cases). So, what is the
relevance to select a physical interface?
First of all, for incoming VPN connections where your SpeedTouch™ is the
responder in the IKE negotiations, the interface is part of the matching process for
accepting the connection. Selecting the default value any has the effect of removing
this matching criterion. If you select a specific interface as Primary Untrusted
Physical Interface, then a new incoming VPN connection on a backup interface is
not accepted.
Secondly, if your SpeedTouch™ is equipped with a backup physical interface, for
example an ISDN backup interface, then this field determines the preferred
interface for your VPN connection. This interface is used whenever it is available.
When this interface fails, the active VPN connections are re-routed via the backup
interface. When the primary interface becomes available again, the VPN
connections are re-routed to the primary interface. On the other hand, when you
select any as the Primary Untrusted Physical Interface and this interface fails, the
active VPN connections are also re-routed to the backup interface. But when the
DSL connection becomes available again, the VPN connections are not re-routed as
long as the backup connection is available.
The IPSec peer can also be tied to the LAN interface (eth0). This could be
useful to set up a secure connection with a local host within the local LAN
for testing purposes, or when a redundant gateway to the public Internet,
other than the SpeedTouch™, is present in the LAN.
Exchange mode Select the exchange mode used during the Phase 1 negotiation. The SpeedTouch™
supports both main mode and aggressive mode.
Authentication Select from the list the symbolic name of the applicable Authentication Attribute.
Either pre-shared key or certificates can be used for authentication. Authentication
Attributes are defined on the Authentication sub-page. See “3.5.2 Authentication
Page” on page 82.
Peer Descriptor Select from the list the symbolic name of a Peer Security Descriptor to be used for
the IKE negotiation. Up to four Descriptors can be selected in the Profiles page.
These Descriptors are presented as alternative proposals during the IKE
negotiations. Peer Security Descriptors are managed on the Peer Descriptors subpage. See “3.5.3 Peer Descriptors Page” on page 83.
Client/Server This optional parameter refers to a dialup VPN Client/Server descriptor. Client/
Server parameters are managed on separate sub-pages. See “3.5.5 VPN-Client
Page” on page 86 for the VPN client configuration. See “3.5.6 VPN-Server Page” on
page 88 for the VPN server configuration.
80
E-DOC-CTC-20051017-0169 v0.1
Page 83

Chapter 3
Configuration via Local Pages
Peer Options This optional parameter refers to the symbolic name of a peer options list. The peer
options modify the VPN behaviour. The peer options lists are defined on the Peers
Options sub-page, see “3.5.4 Peer Options Page” on page 85. For a basic IPSec
configuration, no options list is selected.
E-DOC-CTC-20051017-0169 v0.1
81
Page 84

Chapter 3
Configuration via Local Pages
3.5.2 Authentication Page
Authentication
The Authentication page allows you to define Authentication Attributes.
page layout
Two main methods for user authentication are supported in the SpeedTouch™:
pre-shared key
certificates
The user authentication parameters used for IKE negotiations are bundled in a
descriptor with a symbolic name.This is called the Authentication Attribute. For
pre-shared key authentication, this attribute holds the pre-shared key. For
authentication with certificates it simply indicates the authentication method.
Parameter table The authentication attribute is a named descriptor, bundling the authentication
parameters. The following data need to be provided:
Parameter Possible values Description
Authentication
name
Type
Secret A text string
The Preshared Secret has to be entered twice in order to protect against
typing errors.
A text string
preshared
cert Authentication with certificates.
The symbolic name of the
authentication attribute. This name is
used in the Peer Profile.
Pre-shared key authentication method
is used.
When pre-shared key authentication
is used, enter the pre-shared key
(password) here.
Irrelevant in case of authentication
with certificates. In this case, leave
this parameter unset.
82
E-DOC-CTC-20051017-0169 v0.1
Page 85

3.5.3 Peer Descriptors Page
Chapter 3
Configuration via Local Pages
Descriptors
page layout
A Peer Security Descriptor contains the methods for message authentication,
encryption and hashing, and the lifetime of the IKE Security Association.
The Peer Descriptors page allows you to manage Peer Security Descriptors.
A number of Peer Security Descriptors are pre-configured in the SpeedTouch™.
You can verify and modify the contents of the pre-defined Security Descriptors or
define your own Security Descriptors.
Parameter table The following table summarizes the parameters comprised in the peer security
descriptor:
Parameter Description
Descriptor name Symbolic name to identify the Descriptor.
Crypto
Integrity Hashing function used for message authentication
Group Diffie-Hellman group for key exchange
Lifetime-secs
Cryptographic function used for encrypting the IKE
messages.
The lifetime of the IKE Security Association. At
expiration of this period re-keying occurs.
Peer Descriptor name This name is used internally to identify the Peer Security Descriptor. This name
appears in the Descriptor lists on the Peer Profiles page.
E-DOC-CTC-20051017-0169 v0.1
83
Page 86

Chapter 3
Configuration via Local Pages
Crypto The table below shows the encryption algorithms supported by the SpeedTouch™
along with their corresponding key size:
Algorithm Valid key lengths (bits)
DES 56
3DES 168
AES 128, 192, 256
DES is relatively slow and is the weakest of the algorithms, but it is the
industry standard.
3DES is a stronger version of DES, but is the slowest of the supported
algorithms (for a comparable key length).
AES is the new encryption standard selected by the American government to
replace DES/3DES. It is recommended to use AES since it is the most
advanced of the supported encryption methods.
Integrity The SpeedTouch™ supports two types of hashing algorithms:
Hashing algorithm
MD5
SHA1
HMAC is always used as integrity algorithm, combined with either MD5 or
SHA1.
SHA1 is stronger than MD5, but slightly slower.
Group The table below shows the supported Diffie-Hellman groups:
Diffie-Hellman group
number of bits Keyword
number
1 768 MODP768
2 1024 MODP1024
5 1536 MODP1536
Lifetime-secs The lifetime of a Security Association is specified in seconds:
84
Lifetime measured in: Minimum value Maximum value
seconds 240 (=4 minutes) 31536000 (=1 year)
E-DOC-CTC-20051017-0169 v0.1
Page 87

3.5.4 Peer Options Page
Chapter 3
Configuration via Local Pages
Options
page layout
The Options page allows you to define Options lists that you can later refer to in a
Peer Profile.
Peer options are described in section “6.9 Peer Options” on page 201.
E-DOC-CTC-20051017-0169 v0.1
85
Page 88

Chapter 3
Configuration via Local Pages
3.5.5 VPN-Client Page
VPN-Client
The VPN-Client page allows you to define VPN Client Descriptors.
page layout
The configuration of a VPN client scenario is described in detail in section
“3.2 VPN Client” on page 51 and following. The application-oriented VPN
Client Web page is the recommended way to configure a VPN client.
Client descriptor name This name is used internally to identify the VPN client Descriptor. This name
appears in the Client/Server list on the Peer Profiles page.
Configuring XAuth When you want to use Extended Authentication, you can fill out an XAuth
Username and Password in the optional fields. Storing these parameters in the VPN
Client Descriptor is required for always-on connections.
The XAuth Password is not shown in clear text. In order to protect from
typing errors, you have to confirm your entry.
The use of XAuth is further explained in section “6.3 Extended
Authentication (XAuth)” on page 176 and following.
Gateway Vendor The SpeedTouch™ can interact with VPN servers of various vendors. Because some
vendors implement proprietary features, it is required to select the Gateway
Vendor.
Following vendors can be selected:
Select ... when ...
generic the VPN server is either a SpeedTouch™ or the vendor is
unknown.
Cisco you connect to a Cisco VPN server. Cisco requires a
Group ID to be specified for the VPN clients (see “Set of
Server Vendor specific parameters” on page 58).
Nortel you connect to a Nortel VPN server. (Certificate
authentication only.)
86
E-DOC-CTC-20051017-0169 v0.1
Page 89

Chapter 3
Configuration via Local Pages
Type The Type parameter determines which Virtual IP Address Mapping type is selected.
Either dhcp or nat can be selected.
Selecting dhcp has the effect that the virtual IP address attributed by the VPN
server to the SpeedTouch™ VPN client is effectively assigned to the terminal.
The SpeedTouch™ creates a new IP address pool, called a spoofing address
pool. The SpeedTouch™will use this pool to provide a new IP address to the
terminal that starts the secure connection. Simultaneous access to the VPN of
multiple terminals in the LAN is not possible. The VPN server attributes a
single virtual IP address.
The spoofing address pool inherits the lease time for IP addresses
from the originally used address pool. In order to have a swift renewal
of IP addresses, it is recommended to set a conveniently low lease
time in the original dhcp address pool. A value of 60 seconds is
suggested.
Selecting nat has the effect that the VPN server attributes a virtual IP address to the
SpeedTouch™ VPN client. This virtual IP address is stored in the SpeedTouch™. The
SpeedTouch™ will automatically create a new NAT entry to map the virtual IP
address to the IP addresses used on the local network. Simultaneous access to the
VPN of multiple terminals is supported.
E-DOC-CTC-20051017-0169 v0.1
87
Page 90

Chapter 3
Configuration via Local Pages
3.5.6 VPN-Server Page
VPN-Server
The VPN-Server page allows you to define VPN Server Descriptors.
page layout
The configuration of a VPN server scenario is described in detail in section
“3.3 VPN Server” on page 63 and following. The application-oriented VPN
Server Web page is the recommended way to configure a VPN server.
Server descriptor name This name is used internally to identify the VPN Server Descriptor. This name
appears in the Client/Server list on the Peer Profiles page.
Virtual IP Range Specifies the range of IP addresses from which the VPN client addresses are
selected. An address range or a subnet can be entered for this parameter.
Netmask Specifies the netmask provided to the VPN client. Use the dotted decimal format.
For example: 255.255.255.0
Push IP Select this check box when you want the VPN server to take the initiative for
assigning an IP address to the VPN clients via IKE Mode Config.
When the check box is not selected, the VPN clients will request an IP address from
the VPN server.
Domain The domain name provided to the VPN clients via IKE Mode Config.
Primary DNS The IP address of the primary DNS server, provided to the VPN clients via IKE Mode
Config. This is the primary DNS server in the local network that is open to VPN
clients.
88
E-DOC-CTC-20051017-0169 v0.1
Page 91

Configuration via Local Pages
Secondary DNS The IP address of the secondary DNS server, provided to the VPN clients via IKE
Mode Config. This is the secondary DNS server in the local network that is open to
VPN clients.
Primary WINS The IP address of the primary WINS server, provided to the VPN clients via IKE
Mode Config. This is the primary WINS server in the local network that is open to
VPN clients. A WINS server maps NETBIOS names to IP addresses.
Secondary WINS The IP address of the secondary WINS server, provided to the VPN clients via IKE
Mode Config. This is the secondary WINS server in the local network that is open to
VPN clients.
XAuth Pool The SpeedTouch™ allows the optional use of the Extended Authorization protocol
with an internal list of authorized users. When you want to use XAuth, a list of
authorized users is to be composed. This is explained in section “3.5.7 VPN-Server-
XAuth Page” on page 90.
Once you have defined a named list or authorized users, select it from the XAuth
Pool list to activate the use of Xauth in the VPN server.
Chapter 3
E-DOC-CTC-20051017-0169 v0.1
89
Page 92

Chapter 3
Configuration via Local Pages
3.5.7 VPN-Server-XAuth Page
VPN-Server-XAuth
page layout
The VPN-Server-XAuth page allows you to define XAuth user pools and to add
authorized users to these pools.
An XAuth user pool is a named list of authorized users. Use Add User to define
additional user records.
The configuration of a VPN server scenario is described in detail in section
“3.3 VPN Server” on page 63 and following. The application-oriented VPN
Server Web page is the recommended way to configure a VPN server.
XAuth pool name This name is used internally to identify the XAuth pool. This name appears in the
XAuth Pool list on the VPN-Server page.
Type Two different types of user authentication protocols can be selected: generic and
Username and
Password
chap.
You define a new record for an authorized user by typing a Username and
Password.
Click Add User to add the user record to the XAuth pool.
90
E-DOC-CTC-20051017-0169 v0.1
Page 93

3.5.8 Connection Profiles Page
Chapter 3
Configuration via Local Pages
Connection Profiles
page layout
The Connection Profiles page bundles all parameters that define an IPSec
Connection to a Peer. In other words it bundles the Phase 2 parameters.
A number of parameters makes use of symbolic descriptors that are defined and
managed on other sub-pages. On the Profiles page, these descriptors are selected
by their symbolic name from a list. Therefore, you need to prepare the descriptors
in other Connections sub-pages, before a complete Connection Profile can be
composed in the Connection Profiles page.
Connection name Give the connection a symbolic name. This name only has local significance inside
the SpeedTouch™. This parameter is not used in the IPSec negotiations with the
remote Security Gateway.
Peer name Select from the list the name of the peer you want to connect to.
E-DOC-CTC-20051017-0169 v0.1
91
Page 94

Chapter 3
Configuration via Local Pages
Local network This parameter is used in the proposal presented to the remote Security Gateway
during the Phase 2 negotiation. It determines which messages have access to the
IPSec connection at the local side of the tunnel. This is the basic parameter for the
dynamic IPSec policy capabilities of the SpeedTouch™. As an outcome of the Phase
2 negotiations, a static IPSec policy is derived.
The valid settings are:
the keyword: retrieve_from_server
This setting can be used in an IPSec client/server configuration. It is only
relevant at the client side of the connection where the SpeedTouch™ acts as
an initiator for the IPSec Security Association.
the keyword: black_ip
This setting is used only for remote management scenarios where the IPSec
tunnel is used exclusively for information generated or terminated by the
SpeedTouch™.
a symbolic name of a network descriptor
This is the most common selection in a LAN-to-LAN application. In this case
the Local network field holds the symbolic name of the network descriptor
that refers to the local private network having access to the IPSec connection.
Remote network This parameter describes the remote network that may use the IPSec connection.
This parameter expresses a dynamic policy, which during the Phase 2 negotiation
results in a static policy.
The valid settings are:
the keyword: retrieve_from_server
This setting can be used in an IPSec client/server configuration. It is only
relevant at the client side of the connection where the SpeedTouch™ acts as
an initiator for the IPSec Security Association.
the keyword: allocated_virtual_ip
This setting can be used in an IPSec client/server configuration. It is only
relevant at the server side of the connection.
the keyword: black_ip
Designates the public IP address of the remote Security Gateway as the end
user of the secure connection. This setting is useful for a connection that
serves secure remote management of the remote Security Gateway.
a symbolic name of a network descriptor
This setting is used when the network environment at the remote side is
completely known. This is often the case in a site-to-site application where the
VPN structure and the use of specific ranges of IP addresses are under the
control of a network manager.
Always on Select this check box when you want a VPN connection that automatically starts
negotiations when the SpeedTouch™ is operational.
Connection Descriptor Select from the list the symbolic name of a Connection Security Descriptor to be
used for the IPSec connection. Up to four Descriptors can be selected in the Profiles
page. These Descriptors are presented as alternative proposals during the Phase 2
negotiations. Connection Security Descriptors are managed on the Connection
Descriptors sub-page. See “3.5.10 Connection Descriptors Page” on page 96.
92
E-DOC-CTC-20051017-0169 v0.1
Page 95

Configuration via Local Pages
Connection Options This optional parameter refers to the symbolic name of a connection options list.
The connection options modify the VPN behaviour. The connection options lists are
defined on the Connection Options sub-page, see “3.5.11 Connection Options
Page” on page 99. For a basic IPSec configuration, no options list is selected.
Connection enabled Select this box to enable the connection.
Chapter 3
E-DOC-CTC-20051017-0169 v0.1
93
Page 96

Chapter 3
Configuration via Local Pages
3.5.9 Networks Page
Networks
page layout
What is a Network
Descriptor?
The Networks page allows you to define Network Descriptors.
The concept of Network Descriptors is introduced for the first time in the
SpeedTouch™ R5.3. Not only the classical idea of an IP network or subnet is
comprised in this concept, but also the protocol and port number of the messages
can be specified, such that access to the VPN can be restricted to certain hosts,
protocols and port numbers.
Both the origin and destination traffic policies are expressed by referring to a
Network Descriptor. To this end, a symbolic name is attributed to a Network
Descriptor.
The definition of relevant Network Descriptors is linked with the topology of the
VPN that is constructed with the IPSec configuration. The Network Descriptors
determine the type of messages that will trigger the IPSec module.
How is it used? Network Descriptors can be used to express the origin and destination networks for
Network name Internal symbolic name to identify the Network Descriptor.
Type of network and IP
address
an IPSec Connection. In case a static IPSec policy is used, the local and remote
private networks are described by referring to a Network Descriptor. In this case,
relevant Network Descriptors have to be created prior to the definition of a
Connection Profile. A Connection Profile refers to a Network Descriptor by its
symbolic name.
The Type and IP parameters locate the network in the IP address space. In the IP
field, you enter a value corresponding to the network Type .
Type IP
Valid network types are: Keyword: Examples:
a single IP address address
a single IP subnet subnet
a contiguous IP address range range
10.0.0.15
10.0.0.0/24
10.0.0.5-10.0.0.56
10.0.0.[5-56]
94
E-DOC-CTC-20051017-0169 v0.1
Page 97

Configuration via Local Pages
Protocol Optionally, the access to an IPSec connection can be restricted to a specific
protocols by selecting a protocol from the list.
Select any if you do not want to restrict the connection to a specific protocol.
If you want to restrict the protocols on your secure VPN link, and you need
multiple protocols, then you define a new connection for every individual
protocol. Separate IPSec tunnels will be established for each protocol.
Port Optionally, if the tcp or udp protocol is selected for the protocol parameter, then the
access to the IPSec connection can be further restricted to a single port number.
Many well-known port numbers can be selected from the list.
Select any if you do not want to restrict the connection to a specific port.
Chapter 3
E-DOC-CTC-20051017-0169 v0.1
95
Page 98

Chapter 3
Configuration via Local Pages
3.5.10 Connection Descriptors Page
Descriptors
page layout
A Connection Security Descriptor contains the following security parameters for an
IPSec connection:
Encryption method
Message integrity method (also called message authentication)
Selection to use Perfect Forward Secrecy, or not
Lifetime of the IPSec (Phase 2) Security Association
Encapsulation method.
The Descriptors page allows you to manage Connection Security Descriptors.
96
A number of Connection Security Descriptors are pre-configured in the
SpeedTouch™. You can verify and modify the contents of the pre-defined Security
Descriptors or define your own Security Descriptors.
The Connection Profile refers to the Connection Security Descriptor by its symbolic
name.
E-DOC-CTC-20051017-0169 v0.1
Page 99

Configuration via Local Pages
Parameter table The following table summarizes the parameters comprised in the connection
security descriptor:
Parameter Description
Descriptor name Symbolic name to identify the Descriptor.
Chapter 3
Connection Descriptor
name
Crypto The table below shows the cryptographic functions supported by the SpeedTouch™
Crypto
Integrity Hashing function used for message authentication.
Encapsulation Selects the ESP encapsulation mode.
PFS Selects the use of Perfect Forward Secrecy
Lifetime-secs
Lifetime-kbytes
Internal symbolic name to identify the Connection Descriptor.
along with their corresponding key size:
Cryptographic function to be used for the IPSec Security
Association.
The lifetime of the IPSec Security Association. At
expiration of this period re-keying occurs.
The maximum data volume transported before re-keying
occurs.
Algorithm Valid key lengths (bits)
DES 56
3DES 168
AES 128, 192, 256
NULL -
DES is relatively slow and is the weakest of the algorithms, but it is the
industry standard.
3DES is a stronger version of DES, but is the slowest of the supported
algorithms (for a comparable key length).
AES is the new encryption standard selected by the American government to
replace DES/3DES. It is recommended to use AES since it is the most
advanced of the supported encryption methods.
NULL encryption: The message is not encrypted. Selecting NULL encryption
achieves authentication without encryption, being equivalent to the use of the
Authentication Header (AH) that is no longer supported from Release R5.3.0
onwards.
In addition, NULL encryption may be useful for testing purposes since the
messages on the communication link can be interpreted. Message
authentication remains active.
E-DOC-CTC-20051017-0169 v0.1
97
Page 100

Chapter 3
Configuration via Local Pages
Integrity The SpeedTouch™ supports two types of hashing algorithms:
Encapsulation Tunnel mode is used in all applications where the SpeedTouch™ is the IPSec
Hashing algorithm
MD5
SHA1
HMAC is always used as integrity algorithm, combined with either MD5 or
SHA1.
SHA1 is stronger than MD5, but slightly slower.
Security Gateway for the connected hosts.
Transport mode can be used only for information streams generated or terminated
by the SpeedTouch™ itself. For example, remote management applications may
use this setting.
PFS Enables or disables the use of Perfect Forward Secrecy. A lot of vendors have
Perfect Forward Secrecy (PFS) enabled by default for the Phase 2 negotiation. In
order to configure this on the SpeedTouch™, the use of PFS must be enabled in the
Connection Security Descriptor by selecting the PFS check box.
PFS provides better security, but increases the key calculation overhead.
With PFS enabled, the independence of Phase 2 keying material is
guaranteed. Each time the Phase 2 tunnel is rekeyed, a Diffie-Hellman
exchange is performed.
Not enabling PFS means that the new Phase 2 key is derived from keying
material present in the SpeedTouch™ as a result of the Diffie-Hellman
exchange during the Phase 1 negotiation.
Lifetime-secs The lifetime of an IPSec Security Association is specified in seconds:
lifetime measured in: Minimum value Maximum value
seconds 240 (=4 minutes) 31536000 (=1 year)
Lifetime-kbytes] The data volume limit of an IPSec Security Association before re-keying, expressed
in kilobytes:
lifetime measured in: Minimum value Maximum value
98
kilobytes 1 230 = 1 073 741 824
E-DOC-CTC-20051017-0169 v0.1
 Loading...
Loading...