Page 1

TM
Alteon OS
Application Guide
Nortel 10Gb Ethernet Switch Module for IBM BladeCenter®
Version 1.0
Part Number: 42C4911, January 2007
2350 Mission College Blvd.
Santa Clara, CA 95054
www.bladenetwork.net
Suite 600
Page 2

Alteon OS Application Guide
Copyright © 2007 Blade Network T echnologies, Inc., 2350 Mission College Blvd., Suite 600, Santa Clara,
California, 95054, USA. All rights reserved. Part Number: 42C4911.
This document is protected by copyright and distributed under licenses restricting its use, copying,
distribution, and decompilation. No part of this document may be reproduced in any form by any means
without prior written authorization of Blade Network T echnologies, Inc. Documentation is provided “as
is” without warranty of any kind, either express or implied, including any kind of implied or express
warranty of non-infringement or the implied warranties of merchantability or fitness for a particular
purpose.
U.S. Government End Users: This document is provided with a “commercial item” as defined by F AR
2.101 (Oct. 1995) and contains “commercial technical data” and “commercial software documentation” as
those terms are used in F AR 12.211-12.212 (Oct. 1995). Govern ment End Users are authorized to use this
documentation only in accordance with those rights and restrictions set forth herein, consistent with F AR
12.211- 12.212 (Oct. 1995), DF ARS 227.7202 ( JUN 1995) and DF ARS 252.227-7015 (Nov . 1995).
Blade Network Techn ologies, Inc. reserves the right to change any products described herein at any time,
and without notice. Blade Network T echnologies, Inc. assumes no responsibility or liability arisin g from
the use of products described herein, except as expressly agreed to in writing by Blade Network
Technologies, Inc. The use and purchase of this produc t does not convey a license under any patent rights,
trademark rights, or any other intellectual property rights of Blade Network T echnologies, Inc.
Originated in the USA.
Alteon OS, and Alteon are trademarks of Nortel Networks, Inc. in the United States and certain other
countries. Cisco
®
and EtherChannel® are registered trademarks of Cisco Syst ems, Inc. in the United S tates
and certain other countries. Any other trademarks appearing in this manual are owned by their respective
companies.
2 42C4911, January 2007
Page 3
Contents
Preface 15
Who Should Use This Guide 15
What You’ll Find in This Guide 16
Typographic Conventions 18
How to Get Help 19
Part 1: Basic Switching 21
Chapter 1: Accessing the Switch 23
Management module setup 24
Factory-Default vs. MM assigned IP Addresses 24
Default Gateway 25
Configuring management module for switch access 25
External management port setup 28
Configuring the external management interface 28
Using Telnet 29
Connect to the Switch via SSH 29
BOOTP Relay Agent 29
DHCP Relay Agent 31
Using the Browser-Based Interface 33
Configuring BBI Access via HTTP 33
Configuring BBI Access via HTTPS 33
Using SNMP 36
SNMP v1.0 36
SNMP v3.0 36
Configuring SNMP Trap Hosts 39
Securing Access to the Switch 43
RADIUS Authentication and Authorization 44
TACACS+ Authentication 48
42C4911, January 2007 3
Page 4

Alteon OS Application Guide
LDAP Authentication and Authorization 53
Secure Shell and Secure Copy 55
End User Access Control 61
Chapter 2: Port-based Network Access Control 67
Extensible Authentication Protocol over LAN 68
802.1x Authentication Process 69
802.1x Port States 71
Supported RADIUS Attributes 72
Configuration Guidelines 73
Chapter 3: VLANs 75
Overview 76
VLANs and Port VLAN ID Numbers 77
VLAN Numbers 77
PVID Numbers 77
VLAN Tagging 80
VLAN Topologies and Design Considerations 84
VLAN configuration rules 84
Example 1: Multiple VLANs with Tagging Adapters 85
Protocol-based VLANs 87
Port-based vs. Protocol-based VLANs 88
PVLAN Priority Levels 88
PVLAN Tagging 88
PVLAN Configuration Guidelines 89
Configuring PVLAN 89
Chapter 4: Ports and Trunking 93
Overview 94
Statistical Load Distribution 95
Built-In Fault Tolerance 95
Before you configure static trunks 95
Trunk group configuration rules 96
Port Trunking Example 97
Configurable Trunk Hash Algorithm 100
Link Aggregation Control Protocol 101
Configuring LACP 103
4 42C4911, January 2007
Page 5

Alteon OS Application Guide
Chapter 5: Spanning Tree Group 105
Overview 106
Bridge Protocol Data Units (BPDUs) 107
Determining the Path for Forwarding BPDUs 107
Spanning Tree Group configuration guidelines 108
Multiple Spanning Trees 110
Default Spanning Tree configuration 110
Why Do We Need Multiple Spanning Trees? 111
Switch-Centric Spanning Tree Group 111
VLAN Participation in Spanning Tree Groups 112
Configuring Multiple Spanning Tree Groups 113
Port Fast Forwarding 115
Configuring Port Fast Forwarding 115
Fast Uplink Convergence 116
Configuration Guidelines 116
Configuring Fast Uplink Convergence 116
Chapter 6: Rapid Spanning Tree Protocol/Multiple Spanning Tree
Protocol 117
Rapid Spanning Tree Protocol 118
Port State Changes 118
Port Type and Link Type 119
RSTP Configuration Guidelines 119
RSTP Configuration Example 120
Multiple Spanning Tree Protocol 121
MSTP Region 121
Common Internal Spanning Tree 121
MSTP Configuration Guidelines 122
MSTP Configuration Example 122
Chapter 7: Quality of Service 123
Overview 124
Using ACL Filters 126
Summary of packet classifiers 126
Summary of ACL Actions 128
Understanding ACL Precedence 128
Using ACL Groups 129
ACL Metering and Re-marking 130
542C4911, January 2007
Page 6
Alteon OS Application Guide
Viewing ACL Statistics 131
ACL Configuration Examples 132
Using DSCP Values to Provide QoS 134
Differentiated Services Concepts 134
Using 802.1p Priorities to Provide QoS 139
802.1p Configuration Example 140
Queuing and Scheduling 140
Part 2: IP Routing 141
Chapter 8: Basic IP Routing 143
IP Routing Benefits 144
Routing Between IP Subnets 145
Example of Subnet Routing 148
Dynamic Host Configuration Protocol 152
DHCP Relay Agent 153
DHCP Relay Agent Configuration 154
Chapter 9: Routing Information Protocol 155
Distance Vector Protocol 155
Stability 155
Routing Updates 156
RIPv1 156
RIPv2 156
RIPv2 in RIPv1 compatibility mode 157
RIP Features 157
RIP Configuration Example 158
Chapter 10: IGMP 161
IGMP Snooping 162
IGMP Snooping Configuration Example 163
Static Multicast Router 164
IGMP Relay 165
Configuration Guidelines 165
Configure IGMP Relay 166
Additional IGMP Features 168
FastLeave 168
IGMP Filtering 168
6 42C4911, January 2007
Page 7

Chapter 11: Border Gateway Protocol 171
Internal Routing Versus External Routing 172
Forming BGP Peer Routers 173
What is a Route Map? 174
Incoming and Outgoing Route Maps 175
Precedence 176
Configuration Overview 176
Aggregating Routes 178
Redistributing Routes 179
BGP Attributes 180
Local Preference Attribute 180
Metric (Multi-Exit Discriminator) Attribute 180
Selecting Route Paths in BGP 181
BGP Failover Configuration 182
Default Redistribution and Route Aggregation Example 185
Chapter 12: OSPF 187
OSPF Overview 188
Types of OSPF Areas 188
Types of OSPF Routing Devices 190
Neighbors and Adjacencies 191
The Link-State Database 191
The Shortest Path First Tree 192
Internal Versus External Routing 192
OSPF Implementation in Alteon OS 193
Configurable Parameters 193
Defining Areas 194
Interface Cost 196
Electing the Designated Router and Backup 196
Summarizing Routes 196
Default Routes 197
Virtual Links 198
Router ID 199
Authentication 199
Host Routes for Load Balancing 202
OSPF Features Not Supported in This Release 203
Alteon OS Application Guide
742C4911, January 2007
Page 8

Alteon OS Application Guide
OSPF Configuration Examples 204
Example 1: Simple OSPF Domain 205
Example 2: Virtual Links 207
Example 3: Summarizing Routes 211
Verifying OSPF Configuration 213
Part 3: High Availability
Fundamentals 215
Chapter 13: High Availability 217
Layer 2 Failover 218
VLAN Monitor 218
Setting the Failover Limit 219
L2 Failover with Other Features 219
Configuration Guidelines 220
L2 Failover Configurations 220
Configuring Trunk Failover 223
VRRP Overview 224
VRRP Components 224
VRRP Operation 226
Selecting the Master VRRP Router 226
Failover Methods 227
Active-Active Redundancy 228
Hot-Standby Redundancy 229
Alteon OS extensions to VRRP 230
Tracking VRRP Router Priority 230
Virtual Router Deployment Considerations 231
Assigning VRRP Virtual Router ID 231
Configuring the Switch for Tracking 231
High Availability Configurations 233
Active-Active Configuration 233
Hot-Standby Configuration 238
8 42C4911, January 2007
Page 9
Part 4: Appendices 243
Appendix A: Troubleshooting 245
Monitoring Ports 246
Port Mirroring behavior 247
Configuring Port Mirroring 251
Appendix B: RADIUS Server Configuration Notes 253
Glossary 255
Index 257
Alteon OS Application Guide
942C4911, January 2007
Page 10

Alteon OS Application Guide
10 42C4911, January 2007
Page 11
Figures
Figure 1-1:Switch management on the BladeCenter management module 26
Figure 1-2:BOOTP Relay Agent Configuration 30
Figure 1-3:DHCP Relay Agent Configuration 31
Figure 2-1:Authenticating a Port Using EAPoL 69
Figure 3-1:Default VLAN settings 81
Figure 3-2:Port-based VLAN assignment 82
Figure 3-3:802.1Q tagging (after port-based VLAN assignment) 82
Figure 3-4:802.1Q tag assignment 83
Figure 3-5:802.1Q tagging (after 802.1Q tag assignment) 83
Figure 3-6:Example 1: Multiple VLANs with VLAN-Tagged Gigabit Adapters 85
Figure 4-1:Port Trunk Group 94
Figure 4-2:Port Trunk Group Configuration Example 97
Figure 5-1:Using Multiple Instances of Spanning Tree Group 111
Figure 5-2:Implementing Multiple Spanning Tree Groups 112
Figure 7-1:QoS Model 124
Figure 7-2:Layer 3 IPv4 packet 134
Figure 7-3:Layer 2 802.1q/802.1p VLAN tagged packet 139
Figure 8-1:The Router Legacy Network 145
Figure 8-2:Switch-Based Routing Topology 146
Figure 8-3:DHCP Relay Agent Configuration 154
Figure 11-1:iBGP and eBGP 172
Figure 11-2:Distributing Network Filters in Access Lists and Route Maps 175
Figure 11-3:BGP Failover Configuration Example 182
Figure 11-4:Route Aggregation and Default Route Redistribution 185
Figure 12-1:OSPF Area Types 189
Figure 12-2:OSPF Domain and an Autonomous System 190
Figure 12-3:Injecting Default Routes 197
Figure 12-4:OSPF Authentication 200
Figure 12-5:A Simple OSPF Domain 205
Figure 12-6:Configuring a Virtual Link 207
Figure 12-7:Summarizing Routes 211
Figure 13-1:Basic Layer 2 Failover 220
Figure 13-2:Two trunks, each in a different Failover Trigger 221
42C4911, January 2007 11
Page 12

Alteon OS Application Guide
Figure 13-3:Two trunks, one Failover Trigger 222
Figure 13-4:A Non-VRRP, Hot-Standby Configuration 227
Figure 13-5:Active-Active Redundancy 228
Figure 13-6:Hot-Standby Redundancy 229
Figure 13-7:Active-Active High-Availability Configuration 233
Figure 13-8:Hot-Standby Configuration 239
12 42C4911, January 2007
Page 13
Tables
Table 1-1: GbESM IP addresses, based on switch-module bay numbers 24
Table 1-2: User Access Levels 47
Table 1-3: Alteon OS-proprietary Attributes for RADIUS 47
Table 1-4: Default TACACS+ Authorization Levels 49
Table 1-5: Alternate TACACS+ Authorization Levels 49
Table 4-1: Actor vs. Partner LACP configuration 101
Table 5-1: Ports, Trunk Groups, and VLANs 106
Table 7-1: Well-Known Protocol Types 126
Table 7-2: Well-Known Application Ports 127
Table 7-3: Well-Known TCP flag values 127
Table 7-4: ACL Precedence Groups 128
Table 7-5: Default QoS Service Levels 136
Table 8-1: Subnet Routing Example: IP Address Assignments 148
Table 8-2: Subnet Routing Example: IP Interface Assignments 148
Table 8-3: Subnet Routing Example: Optional VLAN Ports 150
Table 13-1: VRRP Tracking Parameters 230
42C4911, January 2007 13
Page 14

Alteon OS Application Guide
14 42C4911, January 2007
Page 15
Preface
The Alteon OS Application Guide describes how to configure and use the Alteon OS software
on the 10Gb Ethernet Switch Module for IBM BladeCenter. For documentation on installing
the switch physically, see the Installation Guide for your GbE Switch Module (GbESM).
Who Should Use This Guide
This Application Guide is intended for network installers and system administrators engaged in
configuring and maintaining a network. The administrator should be familiar with Et hernet
concepts, IP addressing, Spanning Tree Protocol, and SNMP configuration parameters.
42C4911, January 2007 15
Page 16
Alteon OS Application Guide
What You’ll Find in This Guide
This guide will help you plan, implement, and administer Alteon OS software. Where possible,
each section provides feature overviews, usage examples, and configuration instructions.
Part 1: Basic Switching
Chapter 1, “Accessing the Switch,” describes how to access the GbE Switch Module to
configure, view information and run statistics on the switch. This chapter also discusses
different methods to manage the switch for remote administrators using specific IP
addresses, authentication, Secure Shell (SSH), and Secure Copy (SCP).
Chapter 2, “Port-based Network Access Control ,” describes how to authenticate devices
attached to a LAN port that has point-to-point connection characteristics. It prevents
access to ports that fail authentication and authorization. This feature provides security to
ports of the GbESM that connect to blade servers.
Chapter 3, “VLANs,” describes how to configure Virtual Local Area Networks (VLANs)
for creating separate network segments, including how to use VLAN tagging for devices
that use multiple VLANs. This chapter also describes Protocol-based VLANs, Private
VLANs, and Generic VLAN Registration Protocol (GVRP).
Chapter 4, “Ports and Trunking,” describes how to group multiple physical ports together
to aggregate the bandwidth between large-scale network devices.
Chapter 5, “Spanning Tree Group,” discusses how Spanning T rees configure the network
so that the switch uses the most efficient path when multiple paths exist.
Chapter 6, “R apid Spanning Tree Protocol/Multiple Spanning Tree Protocol,” describes
Rapid Spanning Tree and Multiple Spanning Tree configurations.
Chapter 7, “Quality of Service,” discusses Quality of Servi ce features, including IP filter-
ing using Access Control Lists, Differentiated Services, and IEEE 802.1p priority values.
Part 2: IP Routing
Chapter 8, “Basic IP Routing,” describes how to configure the GbE Switch Module for IP
routing using IP subnets, and DHCP Relay.
Chap ter 9, “Routing Information Protocol,” describes how the Alteon OS software imple-
ments standard RIP for exchanging TCP/IP route information with other routers.
Chapter 10, “IGMP,” describes how the Alteon OS software implements IGMP Snooping
or IGMP Relay to handle multicast traffic efficiently.
Preface 42C4911, January 2007
16
Page 17

Alteon OS Application Guide
Chapter 11, “Border Gateway Protocol,” describes BGP concepts and BGP features sup-
ported in Alteon OS.
Chapter 12, “OSPF,” describes OSPF concepts, how OSPF is implemented in Alteon OS,
and examples of how to configure your switch for OSPF support.
Part 3: High Availability Fundamentals
Chapter 13, “High A vailability,” describes how to use the Virtual Router Redundancy Pro-
tocol (VRRP) to ensure that network resources remain available if one GbE Switch Module is removed for service.
Part 4: Appendices
Appendix A, “Troubleshooting,” discusses two tools for troubleshooting your switch—
monitoring ports and filtering session dumps.
Appe ndi x B, “RADIUS Server Con figuration Notes,” discusses how to modify RADIUS
configuration files for the Nortel Networks BaySecure Access Control RADIUS server, to
provide authentication for users of the GbE Switch Module.
Preface
1742C4911, January 2007
Page 18
Alteon OS Application Guide
Typographic Conventions
The following table describes the typographic styles used in this book.
Table 1 Typographic Conventions
Typeface or
Symbol
AaBbCc123 This type is used for names of commands,
AaBbCc123 This bold type appears in command exam-
<AaBbCc123> This italicized type appears in command
[ ] Command items shown inside brackets are
Meaning Example
files, and directories used within the text.
It also depicts on-screen computer output and
prompts.
ples. It shows text that must be typed in
exactly as shown.
examples as a parameter placeholder. Replace
the indicated text with the appropriate real
name or value when using the command. Do
not type the brackets.
This also shows book titles, special terms, or
words to be emphasized.
optional and can be used or excluded as the
situation demands. Do not type the brackets.
View the readme.txt file.
Main#
Main# sys
To establish a Telnet session, enter:
host# telnet <IP address>
Read your User’ s Guide thoroughly.
host# ls [-a]
Preface 42C4911, January 2007
18
Page 19
Alteon OS Application Guide
How to Get Help
If you need help, service, or technical assistance, see the "Getting help and
technical assistance" appendix in the Nortel 10Gb Ethernet Switch Module for
IBM BladeCenter Installation Guide.
Preface
1942C4911, January 2007
Page 20

Alteon OS Application Guide
Preface 42C4911, January 2007
20
Page 21

Part 1: Basic Switching
This section discusses basic switching functions. This includes how to access and manage the
switch:
Accessing the switch
Po rt -Based Network Access Control
VLANs
Port Trunking
Spanning Tree Protocol
Rapid Spanning Tree and Protocol and Multiple Spanning Tree Protocol
Quality of Service
42C4911, January 2007
Page 22

Alteon OS Application Guide
22 42C4911, January 2007
Page 23

CHAPTER 1
Accessing the Switch
The Alteon OS software provides means for accessing, configuring, and viewing information
and statistics about the GbE Switch Module. This chapter discusses different methods of
accessing the switch and ways to secure the switch for remote administrators:
“Management module setup” on page 24
“External mana gement port setup” on page 28
“Using Telnet” on page 29
“Using the Browser-Based Interface” on page 33
“Using SNMP” on page 36
“Securing Access to the Switch” on page 43
“RADIUS Authentication and Authorization” on page 44
“TACACS+ Authentication” on page 48
“LDAP Authentication and Authorization” on page 53
“Secure Shell and Secure Copy” on page 55
42C4911, January 2007 23
Page 24
Alteon OS Application Guide
Management module setup
The BladeCenter GbE Switch Module is an integral subsystem within the overall BladeCenter
system. The BladeCenter chassis includes a management module as the central element for
overall chassis management and control.
You can use the management mod ule to configure and manage the GbE Switch Module. The
GbE Switch Module communicates with the management module(s) through its internal port
15 (MG T1) and port 16 (MGT2), which you can access through the 100 Mbps Ethernet port on
each management module. The factory default settings permit management and control access
to the switch module only through the management module, or the built-in serial port. Y ou can
use the external Ethernet ports (EXT1-EXT7) on the switch module for management and control of the switch, by selecting this mode as an option through the management module configuration utility program (see the applicable BladeCenter Installation and User’ s Guide
publications for more information).
NOTE – Support for each management module is provided by a separate management port
(MGT1 and MGT2). One port is active, and the other port is used as a backup.
Factory-Default vs. MM assigned IP Addresses
Each GbE Switch Module must be assigned its own Internet Protocol address, which is used
for communication with an SNMP network manager or other transmission control protocol /
Internet Protocol (TCP/IP) applications (for example, BootP or TFTP). The factory-default IP
address is 10.90.90.8x, where x corresponds to the number of the bay into which the GbE
Switch Module is installed. For additional information, see the Installation Guide. The management module assigns an IP address of 192.168.70.1xx, where xx corresponds to the number
of the bay into which each GbE Switch Module is installed, as shown in the following table:
Table 1-1 GbESM IP addresses, based on switch-module bay numbers
Bay number Factory-default IP address IP address assigned by MM
Bay 7 10.90.90.80 192.168.70.133
Bay 8 10.90.90.82 192.168.70.134
Bay 9 10.90.90.81 192.168.70.135
Bay 10 10.90.90.83 192.168.70.136
Chapter 1: Accessing the Switch 42C4911, January 2007
24
Page 25

Alteon OS Application Guide
NOTE – Before you install the GbESM in Bay 8 or Bay 10, confirm that your blade
I/O Expansion adapter supports communication to these I/O bays.
Default Gateway
The default Gateway IP address determines where packets with a destination address outside
the current subnet should be sent. Usually, the default Gateway is a router or host acting as an
IP gateway to handle connections to other subnets of other TCP/IP networks. If you want to
access the GbE Switch Module from outside your local network, use the management module
to assign a default Gateway address to the GbE Switch Module. Choose I/O Module Tasks >
Configuration from the navigation pane on the left, and enter the default Gateway IP address
(for example, 192.168.70.125). Click Save.
Configuring management module for switch access
Complete the following initial configuration steps:
1. Connect the Ethernet port of the management module to a 10/100 Mbps network (with
access to a management station) or directly to a management station.
2. Access and log on to the management module, as described in the BladeCenter Manage-
ment Module User’s Guide. The management module provides the appropriate IP
addresses for network access (see the applicable BladeCenter Installation and User’s
Guide publications for more information).
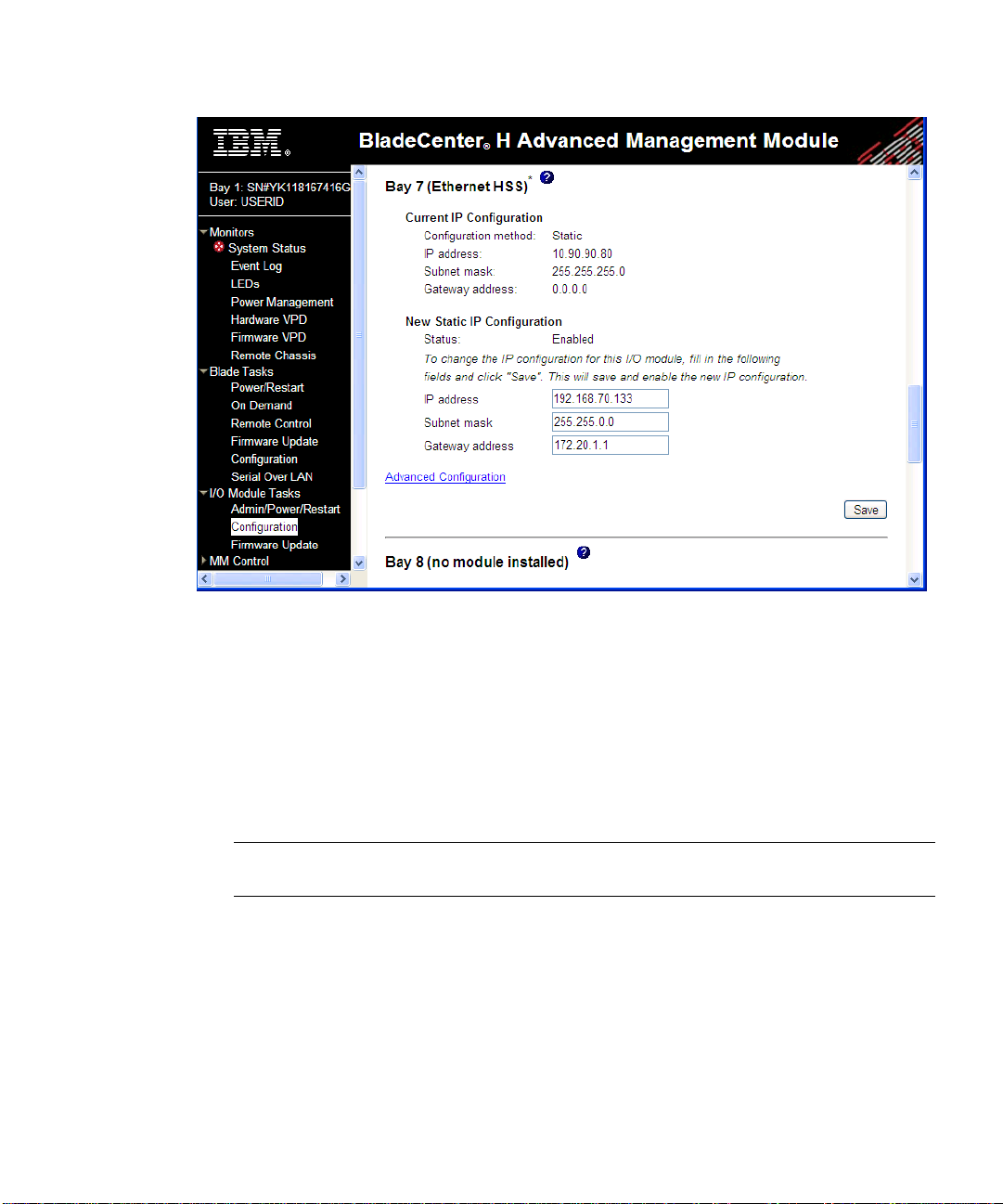
3. Select Configuration on the I/O Module Tasks menu on the left side of the BladeCenter
Management Module window. See Figure 1-1.
Chapter 1: Accessing the Switch
2542C4911, January 2007
Page 26
Alteon OS Application Guide
Figure 1-1 Switch management on the BladeCenter management module
4. You can use the default IP addresses provided by the management module, or you can
assign a new IP address to the switch module through the management module. You can
assign this IP address through one of the following methods:
Manually through the BladeCenter management module
Autom a ticall y through the IBM Director Configuration Wizard (available in
Director release 5.20.1)
NOTE – If you change the IP address of the GbE Switch Module, make sure that the switch
module and the management module both reside on the same subnet.
5. Enable the following features in the management module:
External Ports (I/O Module Tasks > Admin/Power/Restart > Advanced Setup)
External management over all ports (Configuration > Advanced Configuration)
This setting is required if you want to access the management network through the
external data ports (EXT1 - EXT6) and the external management port (EXT7) on the
GbE Switch Module.
Chapter 1: Accessing the Switch 42C4911, January 2007
26
Page 27
Alteon OS Application Guide
The default value is Disabled for both features. If these features are not already enabled,
change the value to Enabled, then Save.
NOTE – In Advanced Configuration > Advanced Setup, enable “Preserve new IP configura-
tion on all switch resets,” to retain the switch’s IP interface when you restore factory defaults.
This setting preserves the management port’s IP address in the management module’s memory,
so you maintain connectivity to the management module after a reset.
You can now start a Telnet session, Browser-Based Interface (Web) session, a Secure Shell session, or a secure HTTPS session to the GbE Switch Module.
Chapter 1: Accessing the Switch
2742C4911, January 2007
Page 28

Alteon OS Application Guide
External management port setup
In addition to the internal management ports (MGT1 and MGT2), the 10Gb Ethernet
Switch Module (GbESM) also has an external management port (EXT7) to support
out-of-band management traffic. Port EXT7 allows you to perform data transfers without
taxing the data ports (EXT1-EXT6). Some commands (for example, so ft ware image transfers
such as /boot/gtimg) that initiate data transfers provide an option for choosing the port
over which to perform the transfer.
To use the external management port, you must configure the external management interface
and gateway, as shown in the following configuration example.
Configuring the external management interface
Complete the following steps to configure port EXT7 for external management:
1. Use Telnet to access the switch CLI, and configure the external management interface:
>> # /cfg/l3/if 249 (Select IP interface 249)
>> IP Interface 249# addr 100.20.10.3 (Assign IP address for the interface)
>> IP Interface 249# ena (Enable the interface)
>> IP Interface 249# ..
>> Layer 3# gw 253 (Select gateway 253)
>> Default gateway 253# addr 100.20.10.5 (Assign IP address for the gateway)
>> Default gateway 253# ena (Enable the gateway)
>> Default gateway 253# apply (Make the configuration active)
>> Default gateway 253# save (Save your changes)
Interface 249 and gateway 253 are used for switch management through port EXT7.
2. Enable port EXT7.
>> # /cfg/port ext7/ena (Enable port EXT7)
>> Port EXT7# apply (Make the configuration active)
>> Port EXT7# save (Save your changes)
By default, port EXT7 is a member of management VLAN 4094.
Once the external management network is configured, you can start a Telnet session,
Browser-Based Interface (Web) session, a Secure Shell session, or a secure HTTPS session to
the GbESM. To access the GbESM through the external management port, use the IP address
for IP interface 249.
Chapter 1: Accessing the Switch 42C4911, January 2007
28
Page 29
Alteon OS Application Guide
Using Telnet
Use the management module to access the GbE Switch Module through Telnet. Choose
I/O Module T asks > Configuration from the navigation pane on the left. Select a bay number
and click Advanced Configuration > Start Telnet/Web Session > Star t Telnet Session. A
Telnet window opens a connection to the Switch Module (requires Java 1.4 Plug-in).
Once you have configured the GbE Switch Module with an IP address and gateway, you can
access the switch from any workstation connected to the management network. Telnet access
provides the same options for user and administrator access as those available through the
management module, minus certain telnet and management commands.
To establish a Telnet connection with the switch, you can run the Telnet program on your
workstation and issue the Telnet command, followed by the switch IP address:
telnet <switch IP address> [-m|-mgt|-e|-ext7|-d|-data]
By default, the -m or -mgt option for management ports is used. To use the internal
management port, specify the -m or -mgt option. To use the external management port,
specify the -e or -ext7 option.
Connect to the Switch via SSH
The SSH (Secure Shell) protocol enables you to securely log into another computer over a network to execute commands remotely . As a secure alternative to using Telnet to manage switch
configuration, SSH ensures that all data sent over the network is encrypted and secure. For
more information, see “Secure Shell and Secure Copy” on page 55. For more information on
the CLI, see the Alteon OS Command Reference.
BOOTP Relay Agent
The GbE Switch Module can function as a Bootstrap Protocol relay agent, enabling the switch
to forward a client request for an IP address up to two BOOTP servers with IP addresses that
have been configured on the switch.
When a switch receives a BOOTP request from a BOOTP client requesting an IP address, the
switch acts as a proxy for the client. The request is then forwarded as a UDP Unicast MAC
layer message to two BOOTP servers whose IP addresses are configured on the switch. The
servers respond to the switch with a Unicast reply that contains the default gateway and IP
address for the client. The switch then forwards this reply back to the client.
Chapter 1: Accessing the Switch
2942C4911, January 2007
Page 30
Alteon OS Application Guide
Figure 1-2 shows a basic BOOTP network example.
Boston Raleigh
20.1.1.1
BladeCenter
BladeCenter
BladeCenter
10.1.1.2
BOOT Client
asks for IP from
BOOTP server
BladeCenter acts as
BOOTP Relay Agent
BOOTP Server
Figure 1-2 BOOTP Relay Agent Configuration
The use of two servers provide failover redundancy. The client request is forwarded to both
BOOTP servers configured on the switch. However, no health checking is supported.
Configuring the BOOTP Relay Agent
To enable the GbE Switch Module to be the BOOTP forwarder, you need to configure the
BOOTP server IP addresses on the switch, and enable BOOTP relay on the interface(s) on
which the BOOTP requests are received.
Generally, you should configure the command on the switch IP interface that is closest to the
client, so that the BOOTP server knows from which IP subnet the newly allocated IP address
should come.
Use the following commands to configure the switch as a BOOTP relay agent:
>> # /cfg/l3/bootp
>> Bootstrap Protocol Relay# addr <IP address>(IP address of BOOTP server)
>> Bootstrap Protocol Relay# addr2 <IP address>(IP address of 2nd BOOTP server)
>> Bootstrap Protocol Relay# on (Globally turn BOOTP relay on)
>> Bootstrap Protocol Relay# off (Globally turn BOOTP relay off)
>> Bootstrap Protocol Relay# cur (Display current configuration)
Use the following command to enable the Relay functionality on an IP interface:
>> # /cfg/l3/if <interface number>/relay ena
Chapter 1: Accessing the Switch 42C4911, January 2007
30
Page 31

Alteon OS Application Guide
P
er
DHCP Relay Agent
DHCP is described in RFC 2131, and the DHCP relay agent supported on the GbESM is
described in RFC 1542. DHCP uses UDP as its transport protocol. The client sends messages
to the server on port 67 and the server sends messages to the client on port 68.
DHCP defines the methods through which clients can be assigned an IP address for a finite
lease period and allowing reassignment of the IP address to another client later. Additionally,
DHCP provides the mechanism for a client to gather other IP configuration parameters it needs
to operate in the TCP/IP network.
In the DHCP environment, the switch acts as a relay agent. The DHCP relay feature
(/cfg/l3/bootp) enables the switch to forward a client request for an IP address to two
BOOTP servers with IP addresses that have been configured on the switch.
When a switch receives a UDP broadcast on port 67 from a DHCP client requesting an IP
address, the switch acts as a proxy for the client, replacing the client source IP (SIP) and destination IP (DIP) addresses. The request is then forwarded as a UDP Unicast MAC layer message to two BOOTP servers whose IP addresses are configured on the switch. The servers
respond as a a UDP Unicast message back to the switch, with the default gateway and IP
address for the client. The destination IP address in the server response represents the interface
address on the switch that received the client request. This interface address tells the switch on
which VLAN to send the server response to the client.
DHCP Relay Agent Configuration
T o enable the GbESM to be the BOOTP forwarder, you need to configure the DHCP/BOOTP
server IP addresses on the switch. Generally, you should configure the command on the switch
IP interface closest to the client so that the DHCP server knows from which IP subnet the
newly allocated IP address should come.
The following figure shows a basic DHCP network example:
GbESM
DHC
Serv
BladeCenter
BladeCenter
Figure 1-3 DHCP Relay Agent Configuration
Chapter 1: Accessing the Switch
3142C4911, January 2007
Page 32

Alteon OS Application Guide
In GbESM implementation, there is no need for primary or secondary servers. The client
request is forwarded to the BOOTP servers configured on the switch. The use of two servers
provide failover redundancy. However, no health checking is supported.
Use the following commands to configure the switch as a DHCP relay agent:
>> # /cfg/l3/bootp
>> Bootstrap Protocol Relay# addr (Set IP address of BOOTP server)
>> Bootstrap Protocol Relay# addr2 (Set IP address of 2nd BOOTP server)
>> Bootstrap Protocol Relay# on (Globally turn BOOTP relay on)
>> Bootstrap Protocol Relay# off (Globally turn BOOTP relay off)
>> Bootstrap Protocol Relay# cur (Display current configuration)
Additionally, DHCP Relay functionality can be assigned on a per interface basis. Use the following command to enable the Relay functionality:
>> # /cfg/l3/if <interface number>/relay ena
Chapter 1: Accessing the Switch 42C4911, January 2007
32
Page 33

Alteon OS Application Guide
Using the Browser-Based Interface
Use the management module to access the GbE Switch Module through a W eb session. Choose
I/O Module T asks > Configuration from the navigation pane on the left. Select a bay number
and click Advanced Configuration > Start Telnet/Web Session > Start Web Session. A
browser window opens a connection to the Switch Module.
The Browser-based Interface (BBI) provides access to the common configuration, management and operation features of the GbE Switch Module through your Web browser. For more
information, refer to the BBI Quick Guide.
By default, BBI access is enabled on the switch (/cfg/sys/access/http ena).
Configuring BBI Access via HTTP
To enable BBI access on the switch via HTTP, use the following command:
/cfg/sys/access/http ena
The management module requires the default HTTP web server port (port 80) to access the
BBI. However, you can change the default Web server port with the following comm a nd:
/cfg/sys/access/wport <x>
For workstation access to your switch via the Browser-Based Interface, open a Web browser
window and type in the URL using the IP interface address of the switch, such as http://
10.10.10.1.
Configuring BBI Access via HTTPS
The BBI can also be accessed via a secure HTTPS connection over management and data
ports.
To enable BBI Access on the switch via HTTPS, use the following command:
/cfg/sys/access/https/access ena
To change the HTTPS Web server port number from the default port 443, use the following
command:
/cfg/sys/access/https/port <x>
Chapter 1: Accessing the Switch
3342C4911, January 2007
Page 34

Alteon OS Application Guide
Accessing the BBI via HTTPS requires that you generate a certificate to be used during the key
exchange. A default certificate is created the first time HTTPS is enabled, but you can create a
new certificate defining the information you want to be used in the various fields.
>> /cfg/sys/access/https/generate
Country Name (2 letter code) [ ]: <country code>
State or Province Name (full name) []: <state>
Locality Name (eg, city) []: <city>
Organization Name (eg, company) []: <company>
Organizational Unit Name (eg, section) []: <org. unit>
Common Name (eg, YOUR name) []: <name>
Email (eg, email address) []: <email address>
Confirm generating certificate? [y/n]: y
Generating certificate. Please wait (approx 30 seconds)
restarting SSL agent
The certificate can be saved to flash for use if the switch is rebooted by using the apply and
save commands.
When a client (e.g. web browser) connects to the switch, they will be asked if they accept the
certificate and can verify that the fields are what expected. Once BBI access is granted to the
client, the BBI can be used as described in the BBI Quick Guide.
The BBI is organized at a high level as follows:
Context buttons – allow you to select the type of action you wish to perform. The Configura-
tion button provides access to the configuration elements for the entire switch. The Statistics
button provides access to the switch statistics and state information. The Dashboard button
allows you to display settings and operating status of a variety of switch features.
Navigation Window – provides a menu list of switch features and functions, as follows:
System – this folder provides access to the configuration elements for the entire switch.
General
User Table
Radius
TACACS+
LDAP
NTP
Boot
Syslog/Trap Features
Config/Image Control
Mgmt
Chapter 1: Accessing the Switch 42C4911, January 2007
34
Page 35

Alteon OS Application Guide
Sw itch Ports – configure each of the physical ports on the switch.
Port-Based Port Mirroring – configure port mirroring and mirror port.
Layer 2 – Configure Qu alit y of Servi c e (QoS) features for the switch.
802.1x
FDB
Virtual LANs
Spanning Tree Groups
MSTP/RSTP
Failover
Trunk Groups
Trunk Hash
LACP
Uplink Fast
Layer 3 – Configure Layer 3 features for the switch.
IP Interfaces
Network Routes
Static IPMC Routes
ARP
Network Filters
Route Maps
Border Gateway Protocol
Default Gateways
IGMP
OSPF Routing Protocol
Routing Information Protocol
Virtual Router Redundancy Protocol
Domain Name System
Bootstrap Protocol Relay
General
QoS – Configure Quality of Service (QoS) features for the switch.
802.1p
DSCP
Access Control – Configure Access Control Lists to filter IP packets.
Access Control Lists
Access Control List Groups
Chapter 1: Accessing the Switch
3542C4911, January 2007
Page 36

Alteon OS Application Guide
Using SNMP
Alteon OS provides SNMP v1.0 and SNMP v3.0 support for access through any network management software, such as IBM Director or HP-OpenView.
SNMP v1.0
T o access the SNMP agent on the GbESM, the read and write community strings on the SNMP
manager should be configured to match those on the switch. The default read community
string on the switch is public and the default write community string is private.
The read and write community strings on the switch can be changed using the following commands on the CLI:
>> /cfg/sys/ssnmp/rcomm
and
>> /cfg/sys/ssnmp/wcomm
The SNMP manager should be able to reach the management interface or any one of the IP
interfaces on the switch.
For the SNMP manager to receive the traps sent out by the SNMP agent on the switch
(SNMPv1 only), configure the trap host on the switch with the following command:
/cfg/sys/ssnmp/trsrc <1-250>
SNMP v3.0
SNMPv3 is an enhanced version of the Simple Network Management Protocol, approved by
the Internet Engineering Steering Group in March, 2002. SNMP v3.0 contains additional security and authentication features that provide data origin authentication, data integrity checks,
timeliness indicators and encryption to protect against threats such as masquerade, modification of information, message stream modification and disclosure.
SNMPv3 ensures that the client can use SNMPv3 to query the MIBs, mainly for security.
To access the SNMP v3.0 menu, enter the following command in the CLI:
>> # /cfg/sys/ssnmp/snmpv3
Chapter 1: Accessing the Switch 42C4911, January 2007
36
Page 37

Alteon OS Application Guide
For more information on SNMP MIBs and the commands used to configure SNMP on the
switch, see the Alteon OS Command Reference.
Default configuration
Alteon OS has two SNMP v3 users by default. Both of the following users have access to all
the MIBs supported by the switch:
1) username 1: adminmd5/password adminmd5. Authentication used is MD5.
2) username 2: adminsha/password adminsha. Authentication used is SHA.
To configure an SNMP user name, enter the following command from the CLI:
>> # /cfg/sys/ssnmp/snmpv3/usm 1
User Configuration:
Users can be configured to use the authentication/privacy options. The GbESM support two
authentication algorithms: MD5 and SHA, as specified in the following command:
/c/sys/ssnmp/snmpv3/usm <x>/auth md5|sha
1. To configure a user with name 'admin,' authentication type MD5, and authentication
password of 'admin,' privacy option DES with privacy password of 'admin,' use the following CLI commands.
>> # /cfg/sys/ssnmp/snmpv3/usm 5
>> SNMPv3 usmUser 5# name "admin" (Configure ‘admin’ user type)
>> SNMPv3 usmUser 5# auth md5
>> SNMPv3 usmUser 5# authpw admin
>> SNMPv3 usmUser 5# priv des
>> SNMPv3 usmUser 5# privpw admin
2. Configure a user access group, along with the views the group may access. Use the access
table to configure the group’s access level.
>> # /cfg/sys/ssnmp/snmpv3/access 5
>> SNMPv3 vacmAccess 5# name "admingrp" (Configure an access group)
>> SNMPv3 vacmAccess 5# level authPriv
>> SNMPv3 vacmAccess 5# rview "iso"
>> SNMPv3 vacmAccess 5# wview "iso"
>> SNMPv3 vacmAccess 5# nview "iso"
Because the read view (rview), write view (wview), and notify view (nview) are all set to
“iso,” the user type has access to all private and public MIBs.
Chapter 1: Accessing the Switch
3742C4911, January 2007
Page 38

Alteon OS Application Guide
3. Assign the user to the user group. Use the group table to link the user to a particular
access group.
>> # /cfg/sys/ssnmp/snmpv3/group 5
>> SNMPv3 vacmSecurityToGroup 5# uname admin
>> SNMPv3 vacmSecurityToGroup 5# gname admingrp
If you want to allow user access only to certain MIBs, see the 'View based Configuration' section.
View based Configurations
CLI User equivalent
To configure an SNMP user equivalent to the CLI 'user,' use the following configuration:
/c/sys/ssnmp/snmpv3/usm 4 (Configure the user)
name "usr"
/c/sys/ssnmp/snmpv3/access 3 (Configure access group 3)
name "usrgrp"
rview "usr"
wview "usr"
nview "usr"
/c/sys/ssnmp/snmpv3/group 4 (Assign user to access group 3)
uname usr
gname usrgrp
/c/sys/ssnmp/snmpv3/view 6 (Cre ate views for user)
name "usr"
tree "1.3.6.1.4.1.1872.2.5.1.2" (Agent statistics)
/c/sys/ssnmp/snmpv3/view 7
name "usr"
tree "1.3.6.1.4.1.1872.2.5.1.3" (Agent information)
/c/sys/ssnmp/snmpv3/view 8
name "usr"
tree "1.3.6.1.4.1.1872.2.5.2.2" (L2 statistics)
/c/sys/ssnmp/snmpv3/view 9
name "usr"
tree "1.3.6.1.4.1.1872.2.5.2.3" (L2 information)
/c/sys/ssnmp/snmpv3/view 10
name "usr"
tree "1.3.6.1.4.1.1872.2.5.3.2" (L3 statistics)
/c/sys/ssnmp/snmpv3/view 11
name "usr"
tree "1.3.6.1.4.1.1872.2.5.3.3" (L3 information)
Chapter 1: Accessing the Switch 42C4911, January 2007
38
Page 39

Alteon OS Application Guide
CLI oper equivalent
/c/sys/ssnmp/snmpv3/usm 5 (Configure the oper)
name "oper"
/c/sys/ssnmp/snmpv3/access 4 (Configure access group 4)
name "opergrp"
rview "oper"
wview "oper"
nview "oper"
/c/sys/ssnmp/snmpv3/group 4 (Assign oper to access group 4)
uname oper
gname opergrp
/c/sys/ssnmp/snmpv3/view 20 (Create views for oper)
name "usr"
tree "1.3.6.1.4.1.1872.2.5.1.2" (Agent statistics)
/c/sys/ssnmp/snmpv3/view 21
name "usr"
tree "1.3.6.1.4.1.1872.2.5.1.3" (Agent information)
/c/sys/ssnmp/snmpv3/view 22
name "usr"
tree "1.3.6.1.4.1.1872.2.5.2.2" (L2 statistics)
/c/sys/ssnmp/snmpv3/view 23
name "usr"
tree "1.3.6.1.4.1.1872.2.5.2.3" (L2 information)
/c/sys/ssnmp/snmpv3/view 24
name "usr"
tree "1.3.6.1.4.1.1872.2.5.3.2" (L3 statistics)
/c/sys/ssnmp/snmpv3/view 25
name "usr"
tree "1.3.6.1.4.1.1872.2.5.3.3" (L3 information)
Configuring SNMP Trap Hosts
SNMPv1 trap host
1. Configure a user with no authentication and password.
/c/sys/ssnmp/snmpv3/usm 10 (Configure user named “v1trap”)
name "v1trap"
2. Configure an access group and group table entries for the user. Use the following com-
mand to specify which traps can be received by the user
/c/sys/ssnmp/snmpv3/access <x>/nview
Chapter 1: Accessing the Switch
3942C4911, January 2007
Page 40

Alteon OS Application Guide
In the example below the user will receive the traps sent by the switch.
/c/sys/ssnmp/snmpv3/access 10 (Define access group to view SNMPv1 traps)
name "v1trap"
model snmpv1
nview "iso"
/c/sys/ssnmp/snmpv3/group 10 (Assign user to the access group)
model snmpv1
uname v1trap
gname v1trap
3. Configure an entry in the notify table.
/c/sys/ssnmp/snmpv3/notify 10 (Assign user to the notify table)
name v1trap
tag v1trap
4. Specify the IP address and other trap parameters in the targetAddr and targetParam
tables. Use the following command to specify the user name used with this targetParam
table:
c/sys/ssnmp/snmpv3/tparam <x>/uname
/c/sys/ssnmp/snmpv3/taddr 10 (Define an IP address to send traps)
name v1trap
addr 47.80.23.245
taglist v1trap
pname v1param
/c/sys/ssnmp/snmpv3/tparam 10 (Specify SNMPv1 traps to send)
name v1param
mpmodel snmpv1
uname v1trap
model snmpv1
5. Use the community table to specify which community string is used in the trap.
/c/sys/ssnmp/snmpv3/comm 10 (Define the community string)
index v1trap
name public
uname v1trap
Chapter 1: Accessing the Switch 42C4911, January 2007
40
Page 41

Alteon OS Application Guide
SNMPv2 trap host configuration
The SNMPv2 trap host configuration is similar to the SNMPv1 trap host configuration.
Wherever you specify the model, use snmpv2 instead of snmpv1.
c/sys/ssnmp/snmpv3/usm 10 (Configure user named “v2trap”)
name "v2trap"
/c/sys/ssnmp/snmpv3/access 10 (Define access group to view SNMPv2 traps)
name "v2trap"
model snmpv2
nview "iso"
/c/sys/ssnmp/snmpv3/group 10 (Assign user to the access group)
model snmpv2
uname v2trap
gname v2trap
/c/sys/ssnmp/snmpv3/notify 10 (Assign user to the notify table)
name v2trap
tag v2trap
/c/sys/ssnmp/snmpv3/taddr 10 (Define an IP address to send traps)
name v2trap
addr 47.81.25.66
taglist v2trap
pname v2param
/c/sys/ssnmp/snmpv3/tparam 10 (Specify SNMPv2 traps to send)
name v2param
mpmodel snmpv2c
uname v2trap
model snmpv2
/c/sys/ssnmp/snmpv3/comm 10 (Define the community string)
index v2trap
name public
uname v2trap
SNMPv3 trap host configuration
T o configure a user for SNMPv3 traps, you can choose to send the traps with both privacy and
authentication, with authentication only, or without privacy or authentication.
This is configured in the access table using the following commands:
/c/sys/ssnmp/snmpv3/access <x>/level
/c/sys/ssnmp/snmpv3/tparam <x>
Configure the user in the user table accordingly.
It is not necessary to configure the community table for SNMPv3 traps because the community
string is not used by SNMPv3.
Chapter 1: Accessing the Switch
4142C4911, January 2007
Page 42

Alteon OS Application Guide
The following example shows how to configure a SNMPv3 user v3trap with authentication
only:
/c/sys/ssnmp/snmpv3/usm 11 (Configure user named “v3trap”)
name "v3trap"
auth md5
authpw v3trap
/c/sys/ssnmp/snmpv3/access 11 (Define access group to view SNMPv3 traps)
name "v3trap"
level authNoPriv
nview "iso"
/c/sys/ssnmp/snmpv3/group 11 (Assign user to the access group)
uname v3trap
gname v3trap
/c/sys/ssnmp/snmpv3/notify 11 (Assign user to the notify table)
name v3trap
tag v3trap
/c/sys/ssnmp/snmpv3/taddr 11 (Define an IP address to send traps)
name v3trap
addr 47.81.25.66
taglist v3trap
pname v3param
/c/sys/ssnmp/snmpv3/tparam 11 (Specify SNMPv3 traps to send)
name v3param
uname v3trap
level authNoPriv (Set the authentication level)
Chapter 1: Accessing the Switch 42C4911, January 2007
42
Page 43

Alteon OS Application Guide
Securing Access to the Switch
Secure switch management is needed for environments that perform significant management
functions across the Internet. The following are some of the functions for secured management:
Authentication and authorization of remote administrators: see “RADIUS Authentication
and Authorization” on page 44
Encryption of management information exchanged between the remote administrator and
the switch: see “Secure Shell and Secure Copy” on page 55
The following sections are addressed in this section:
“RADIUS Authentication and Authorization” on page 44
“TACACS+ Authentication” on page 48
“LDAP Authentication and Authorization” on page 53
“Secure Shell and Secure Copy” on page 55
“End User Access Control” on page 61
Chapter 1: Accessing the Switch
4342C4911, January 2007
Page 44

Alteon OS Application Guide
RADIUS Authentication and Authorization
Alteon OS supports the RADIUS (Remote Authentication Dial-in User Service) method to
authenticate and authorize remote administrators for managing the switch. This method is
based on a client/server model. The Remote Access Server (RAS)—the switch—is a client to
the back-end database server. A remote user (the remote administrator) interacts only with the
RAS, not the back-end server and database.
RADIUS authentication consists of the following components:
A protocol with a frame format that utilizes UDP over IP (based on RFC 2138 and 2866)
A centralized server that stores all the user authorization information
A client, in this case, the switch
The GbE Switch Module—acting as the RADIUS client—communicates to the RADIUS
server to authenticate and authorize a remote administrator using the protocol definitions specified in RFC 2138 and 2866. Transactions between the client and the RADIUS server are
authenticated using a shared key that is not sent over the network. In addition, the remote
administrator passwords are sent encrypted between the RADIUS client (the switch) and the
back-end RADIUS server.
How RADIUS Authentication Works
1. Remote administrator connects to the switch and provides user name and password.
2. Using Authentication/Authorization protocol, the switch sends request to authentication
server.
3. Authentication server checks the request against the user ID database.
4. Using RADIUS protocol, the authentication server instructs the switch to grant or deny
administrative access.
Configuring RADIUS on the Switch
Use the following procedure to configure Radius authentication on your GbE Switch Module.
For more information, see Appendix B, “RADIUS Server Configuration Notes.”
Chapter 1: Accessing the Switch 42C4911, January 2007
44
Page 45

Alteon OS Application Guide
1. Turn RADIUS authentication on, then configure the Primary and Secondary RADIUS
servers.
>> Main# /cfg/sys/radius (Select the RADIUS Server menu)
>> RADIUS Server# on (Turn RADIUS on)
Current status: OFF
New status: ON
>> RADIUS Server# prisrv 10.10.1.1 (Enter primary server IP)
Current primary RADIUS server: 0.0.0.0
New pending primary RADIUS server: 10.10.1.1
>> RADIUS Server# secsrv 10.10.1.2 (Enter secondary server IP)
Current secondary RADIUS server: 0.0.0.0
New pending secondary RADIUS server: 10.10.1.2
2. Configure the RADIUS secret.
>> RADIUS Server# secret
Enter new RADIUS secret: <1-32 character secret>
CAUTION—If you configure the RADIUS secret using any method other than through the con-
!
sole port or management module, the secret may be transmitted over the network as clear text.
3. If desired, you may change the default UDP port number used to listen to RADIUS.
The well-known port for RADIUS is 1645.
>> RADIUS Server# port
Current RADIUS port: 1645
Enter new RADIUS port [1500-3000]: <UDP port number>
4. Configure the number r etry attempts for contacting the RADIUS server, and the timeout
period.
>> RADIUS Server# retries
Current RADIUS server retries: 3
Enter new RADIUS server retries [1-3]: < server retries>
>> RADIUS Server# time
Current RADIUS server timeout: 3
Enter new RADIUS server timeout [1-10]: 10(Enter the timeout period in minutes)
Chapter 1: Accessing the Switch
4542C4911, January 2007
Page 46

Alteon OS Application Guide
RADIUS Authentication Features in Alteon OS
Alteon OS supports the following RADIUS authentication features:
Supports RADIUS client on the switch, based on the protocol definitions in RFC 2138 and
RFC 2866.
Allows RADIUS secret password up to 32 by tes and less than 16 octets.
Supports secondary authentication server so that when the primary authentication server
is unreachable, the switch can send client authentication requests to the secondary authentication server. Use the /cfg/sys/radius/cur command to show the currently
active RADIUS authentication server.
Supports user-configurable RADIUS server retry and time-out values:
Time-out value = 1-10 seconds
Retries = 1-3
The switch will time out if it does not receive a response from the RADIUS server in 1-3
retries. The switch will also automatically retry connecting to the RADIUS server before it
declares the server down.
Supports user-configurable RADIUS application port.
The default is 1645/UDP-based on RFC 2138. Port 1812 is also supported.
Allows network administrator to define privileges for one or more specific users to access
the switch at the RADIUS user database.
SecurID is supported if the R ADIUS server can do an ACE/Server client proxy. The pass-
word is the PIN number, plus the token code of the SecurID card.
Chapter 1: Accessing the Switch 42C4911, January 2007
46
Page 47

Alteon OS Application Guide
Switch User Accounts
The user accounts listed in Table 1-2 can be defined in the RADIUS server dictionary file.
Table 1-2 User Access Levels
User Account Description and Tasks Performed Password
User The User has no direct responsibility for switch management.
He/she can view all switch status information and statistics but
cannot make any configuration changes to the switch.
Operator The Operator manages all functions of the switch. The Operator
can reset ports or the entire switch.
Administrator The super-user Administrator has complete access to al l menus,
information, and configuration commands on the switch, including the ability to change both the user and administrator passwords.
user
oper
admin
RADIUS Attributes for Alteon OS User Privileges
When the user logs in, the switch authenticates his/her level of access by sending the RADIUS
access request, that is, the client authentication request, to the RADIUS authentication server.
If the remote user is successfully authenticated by the authentication server, the switch will
verify the privileges of the remote user and authorize the appropriate access. The administrator
has an option to allow backdoor access via Telnet. The default is disable for Telnet access.
Backdoor access is always enabled on the console port.
NOTE – To obtain the RADIUS backdoor password for your GbESM, contact your IBM
Service and Support line.
All user privileges, other than those assigned to the Administrator, have to be defined in the
RADIUS dictionary. RADIUS attribute 6 which is built into all RADIUS servers defines the
administrator. The file name of the dictionary is RADIUS vendor-dependent. The following
RADIUS attributes are defined for Alteon OS user privileges levels:
Table 1-3 Alteon OS-proprietary Attributes for RADIUS
User Name/Access User-Service-Type Value
User Vendor-supplied 255
Operator Vendor-supplied 252
Admin Vendor-supplied 250
Chapter 1: Accessing the Switch
4742C4911, January 2007
Page 48

Alteon OS Application Guide
TACACS+ Authentication
Alteon OS supports authentication and authorization with networks using the Cisco Systems
TACACS+ protocol. The GbE Switch Module functions as the Network Access Server (NAS)
by interacting with the remote client and initiating authentication and authorization sessions
with the TACACS+ access server. The remote user is defined as someone requiring management access to the GbE Switch Module either through a data or management port.
TACACS+ offers the following advantages over RADIUS:
TACACS+ uses TCP-based connection-oriented transport; whereas RADIUS is UDP-
based. TCP offers a connection-oriented transport, while UDP offers best-effort delivery.
RADIUS requires additional programmable variables such as re-transmit attempts and
time-outs to compensate for best-effort transport, but it lacks the level of built-in support
that a TCP transport offers.
TACACS+ offers full packet encryption whereas RADIUS offers password-only encryp-
tion in authentication requests.
TACACS+ separates authentication, authorization and accounting.
How TACACS+ Authentication Works
TACACS+ works much in the same way as RADIUS authentication as described on page 44.
1. Remote administrator connects to the switch and provides user name and password.
2. Using Authentication/Authorization protocol, the switch sends request to authentication
server.
3. Authentication server checks the request against the user ID database.
4. Using TACACS+ protocol, the authentication server instructs the switch to grant or deny
administrative access.
During a session, if additional authorization checking is needed, the switch checks with a
TACACS+ server to determine if the user is granted permission to use a particular command.
TACACS+ Authentication Features in Alteon OS
Authentication is the action of determining the identity of a user, and is generally done when
the user first attempts to log in to a device or gain access to its services. Alteon OS supports
ASCII inbound login to the device. PAP, CHAP and ARAP login methods, TACACS+ change
password requests, and one-time password authentication are not supported.
Chapter 1: Accessing the Switch 42C4911, January 2007
48
Page 49

Alteon OS Application Guide
Authorization
Authorization is the action of determining a user’s privileges on the device, and usually takes
place after authentication.
The default mapping between TACACS+ authorization levels and Alteon OS management
access levels is shown in Table 1-4. The authorization levels must be defined on the TACACS+
server.
Table 1-4 Default TACA CS+ Authorization Levels
Alteon OS User Access Level TACACS+ level
user 0
oper 3
admin 6
Alternate mapping between TACACS+ authorization levels and Alteon OS management
access levels is shown in Table 1-5. Use the command /cfg/sys/tacacs/cmap ena
to use the alternate TACACS+ authorization levels.
Table 1-5 Alternate TACACS+ Authorization Levels
Alteon OS User Access Level TACACS+ level
user 0 - 1
oper 6 - 8
admin 14 - 15
If the remote user is successfully authenticated by the authentication server, the switch verifies
the privileges of the remote user and authorizes the appropriate access. The administrator has
an option to allow backdoor access via Telnet (/cfg/sys/tacacs/telnet). The default
value for Telnet access is disabled. The administrator also can enable secure backdoor
(/cfg/sys/tacacs/secbd), to allow access if both the primary and the secondary
TACACS+ servers fail to respond.
NOTE – To obtain the TACACS+ backdoor password for your GbESM, contact your IBM
Service and Support line.
Chapter 1: Accessing the Switch
4942C4911, January 2007
Page 50

Alteon OS Application Guide
Accounting
Accounting is the action of recording a user's activities on the device for the purposes of billing
and/or security. It follows the authentication and authorization actions. If the authentication
and authorization is not performed via TAC ACS+, there are no TACACS+ accounting messages sent out.
You can use TACACS+ to record and track software logins, configuration changes, and interactive commands.
The GbE Switch Module supports the following TACACS+ accounting attributes:
protoco l (con sole/telnet/ssh/http)
start_time
stop_time
elapsed_time
disc-cause
NOTE – When using the Browser-Based Interface, the TACACS+ Accounting Stop records are
sent only if the Quit button on the browser is clicked.
Command Authorization and Logging
When T ACACS+ Command Authorization is enabled (/cfg/sys/tacacs/cauth ena),
Alteon OS configuration commands are sent to the TACACS+ server for authorization. When
TACACS+ Command Logging is enabled (/cfg/sys/tacacs/clog ena), Alteon OS
configuration commands are logged on the TACACS+ server.
The following examples illustrate the format of Alteon OS commands sent to the TACACS+
server:
authorization request, cmd=cfgtree, cmd-arg=/cfg/l3/if
accounting request, cmd=/cfg/l3/if, cmd-arg=1
authorization request, cmd=cfgtree, cmd-arg=/cfg/l3/if/ena
accounting request, cmd=/cfg/l3/if/ena
authorization request, cmd=cfgtree, cmd-arg=/cfg/l3/if/addr
accounting request, cmd=/cfg/l3/if/addr, cmd-arg=10.90.90.91
authorization request, cmd=apply
accounting request, cmd=apply
Chapter 1: Accessing the Switch 42C4911, January 2007
50
Page 51

Alteon OS Application Guide
The following rules apply to TACACS+ command authorization and logging:
Only commands from a Console, Telnet, or SSH connection are sent for authorization and
logging. SNMP, BBI, or file-copy commands (for example, TFTP or sync) are not sent.
Only leaf-level commands are sent for authorization and logging. For example, /cfg is
not sent, but /cfg/l3/tacacs/cauth is sent.
The full path of each command is sent for authorization and logging. For example,
/cfg/sys/tacacs/cauth
Command arguments are not sent for authorization. For /cauth ena, only /cauth is
authorized. The command and its first argument are logged, if issued on the same line.
Only executed commands are logged.
Invalid commands are checked by Alteon OS, and are not sent for authorization or log-
ging.
Authorization is performed on each leaf-level command separately. If the user issues mul-
tiple commands at once, each command is sent separately as a full path.
Only the following global commands are sent for authorization and logging:
apply
diff
ping
revert
save
telnet
traceroute
TACACS+ Password Change
Alteon OS supports TACACS+ password change. When enabled, users can change
their passwords after successful TACACS+ authorization. Use the command
/cfg/sys/tacacs/passch to enable or disable this feature.
Use the following commands to change the password for the primary and secondary
TACACS+ servers:
>> # /cfg/sys/tacacs/chpass_p (Change primary TACACS+ password)
>> # /cfg/sys/tacacs/chpass_s (Change secondary TACACS+ password)
Chapter 1: Accessing the Switch
5142C4911, January 2007
Page 52

Alteon OS Application Guide
Configuring TACACS+ Authentication on the Switch
1. Turn TACACS+ authentication on, then configure the Primary and Secondary
TACACS+ servers.
>> Main# /cfg/sys/tacacs+ (Select the TACACS+ Server menu)
>> TACACS+ Server# on (Turn TACACS+ on)
Current status: OFF
New status: ON
>> TACACS+ Server# prisrv 10.10.1.1 (Enter primary server IP)
Current primary TACACS+ server: 0.0.0.0
New pending primary TACACS+ server: 10.10.1.1
>> TACACS+ Server# secsrv 10.10.1.2 (Enter secondary server IP)
Current secondary TACACS+ server: 0.0.0.0
New pending secondary TACACS+ server: 10.10.1.2
2. Configure the TACACS+ secret and second secret.
>> TACACS+ Server# secret
Enter new TACACS+ secret: <1-32 character secret>
>> TACACS+ Server# secret2
Enter new TACACS+ second secret: <1-32 character secret>
CAUTION—If you configure the TACACS+ secret using any method other than a direct console
!
connection or through a secure management module connection, the secret may be transmitted
over the network as clear text.
3. If desired, you may change the default TCP port number used to listen to TACACS+.
The well-known port for TACACS+ is 49.
>> TACACS+ Server# port
Current TACACS+ port: 49
Enter new TACACS+ port [1-65000]: <port number>
4. Configure the number of retry attempts, and the timeout period.
>> TACACS+ Server# retries
Current TACACS+ server retries: 3
Enter new TACACS+ server retries [1-3]: < server retries>
>> TACACS+ Server# time
Current TACACS+ server timeout: 5
Enter new TACACS+ server timeout [4-15]: 10(Enter the timeout period in minutes)
5. Apply and save the configuration.
Chapter 1: Accessing the Switch 42C4911, January 2007
52
Page 53

Alteon OS Application Guide
LDAP Authentication and Authorization
Alteon OS supports the LDAP (Lightweight Directory Access Protocol) method to authenti-
cate and authorize remote administrators to manage the switch. LDAP is based on a client/
server model. The switch acts as a client to the LDAP server. A remote user (the remote administrator) interacts only with the switch, not the back-end server and database.
LDAP authentication consists of the following components:
A protocol with a frame format that utilizes TCP over IP
A centralized server that stores all the user authorization information
A client, in this case, the switch
Each entry in the LDAP server is referenced by its Distinguished Name (DN). The DN consists
of the user-account name concatenated with the LDAP domain name. If the user-account name
is John, the following is an example DN:
uid=John,ou=people,dc=domain,dc=com
Configuring the LDAP Server
GbESM user groups and user accounts must reside within the same domain. On the LDAP
server, configure the domain to include GbESM user groups and user accounts, as follows:
User Accounts:
Use the uid attribute to define each individual user account.
User Groups:
Use the members attribute in the groupOfNames object class to create the user groups. The
first word of the common name for each user group must be equal to the user group names
defined in the GbESM, as follows:
admin
oper
user
Chapter 1: Accessing the Switch
5342C4911, January 2007
Page 54

Alteon OS Application Guide
Configuring LDAP Authentication on the Switch
1. T urn LDAP authentication on, then configure the Primary and Secondary LDAP servers.
>> Main# /cfg/sys/ldap (Select the LDAP Server menu)
>> LDAP Server# on (Turn LDAP on)
Current status: OFF
New status: ON
>> LDAP Server# prisrv 10.10.1.1 (Enter primary server IP)
Current primary LDAP server: 0.0.0.0
New pending primary LDAP server: 10.10.1.1
>> LDAP Server# secsrv 10.10.1.2 (Enter secondary server IP)
Current secondary LDAP server: 0.0.0.0
New pending secondary LDAP server: 10.10.1.2
2. Configure the domain name.
>> LDAP Server# domain
Current LDAP domain name: ou-people,dc=domain,dc=com
Enter new LDAP domain name: ou=people,dc=mydomain,dc=com
3. If desired, you may change the default TCP port number used to listen to LDAP.
The well-known port for LDAP is 389.
>> LDAP Server# port
Current LDAP port: 389
Enter new LDAP port [1-65000]: <port number>
4. Configure the number of retry attempts for contacting the LDAP server, and the timeout
period.
>> LDAP Server# retries
Current LDAP server retries: 3
Enter new LDAP server retries [1-3]: < server retries>
>> LDAP Server# timeout
Current LDAP server timeout: 5
Enter new LDAP server timeout [4-15]: 10 (Enter the timeout period in minutes)
5. Apply and save the configuration.
Chapter 1: Accessing the Switch 42C4911, January 2007
54
Page 55

Alteon OS Application Guide
Secure Shell and Secure Copy
Secure Shell (SSH) and Secure Copy (SCP) use secure tunnels to encrypt and secure messages
between a remote administrator and the switch. Telnet does not provide this level of security.
The Telnet method of managing a GbE Switch Module does not provide a secure connection.
SSH is a protocol that enables remote administrators to log securely into the GbE Switch Module over a network to execute management commands.
SCP is typically used to copy files securely from one machine to another. SCP uses SSH for
encryption of data on the network. On a GbE Switch Module, SCP is used to download and
upload the switch configuration via secure channels.
The benefits of using SSH and SCP are listed below:
Authentication of remote administrators
Identifying the administrator using Name/Password
Authorization of remote administrators
Determining the permitted actions and customizing service for individual administrators
Encryption of management messages
Encrypting messages between the remote administrator and switch
Secure copy support
The Alteon OS implementation of SSH supports both versions 1.5 and 2.0. and supports SSH
clients version 1.5 - 2.x. The followi ng SSH clients have been tested
SSH 1.2.23 and SSH 1.2.27 for Linux (freeware)
SecureCRT 3.0.2 and SecureCRT 3.0.3 for Windows NT (Van Dyke Technologies, Inc.)
F-Secu re SSH 1.1 fo r Windows (Data Fellows)
Putty SSH
Cygwin OpenSSH
Mac X OpenSSH
Solaris 8 OpenSSH
AxeSSH SSHPro
SSH Communications Vandyke SSH A
F-Secure
Chapter 1: Accessing the Switch
5542C4911, January 2007
Page 56

Alteon OS Application Guide
Configuring SSH/SCP features on the switch
Before you can use SSH commands, use the following commands to turn on SSH/SCP. SSH
and SCP are disabled by default.
To enable or disable the SSH feature:
Begin a Telnet session from the console port and enter the following commands:
>> # /cfg/sys/sshd/on (Turn SSH on)
Current status: OFF
New status: ON
>> # /cfg/sys/sshd/off (Turn SSH off)
Current status: ON
New status: OFF
To enable or disable SCP apply and save:
Enter the following commands from the switch CLI to enable the SCP putcfg_apply and
putcfg_apply_save commands:
>> # /cfg/sys/sshd/ena (Enable SCP apply and save)
SSHD# apply (Apply the changes to start generating RSA
host and server keys)
RSA host key generation starts
.............................................................
......................................................
RSA host key generation completes (lasts 212549 ms)
RSA host key is being saved to Flash ROM, please don't reboot
the box immediately.
RSA server key generation starts
............................................................
RSA server key generation completes (lasts 75503 ms)
RSA server key is being saved to Flash ROM, please don't reboot
the box immediately.
-----------------------------------------------------------------Apply complete; don't forget to "save" updated configuration.
>> # /cfg/sys/sshd/dis
(Disable SSH/SCP apply and save)
Chapter 1: Accessing the Switch 42C4911, January 2007
56
Page 57

Alteon OS Application Guide
Configuring the SCP Administrator Password
To configure the scpadm (SCP Administrator) password, first connect to the switch via the
serial console port. For security reasons, the scpadm password may only be configured when
connected through the console port.
To configure the password, enter the following command via the CLI. At factory default settings, the current SCP administrator password is admin.
>> /cfg/sys/sshd/scpadm
Changing SCP-only Administrator password; validation required...
Enter current administrator password: <password>
Enter new SCP-only administrator password: <new password>
Re-enter new SCP-only administrator password: <new password>
New SCP-only administrator password accepted.
Using SSH and SCP Client Commands
This section shows the format for using some client commands. The examples below use
205.178.15.157 as the IP address of a sample switch.
To log in to the switch:
Syntax:
ssh <switch IP address> or ssh -l <login-name> <switch IP address>
Example:
>> # ssh 205.178.15.157
>> # ssh -l <login-name> 205.178.15.157 (Login to the switch)
To download the switch configuration using SCP:
Syntax:
scp <username>@<switch IP address>:getcfg <local filename>
Example:
>> # scp scpadmin@205.178.15.157:getcfg ad4.cfg
Chapter 1: Accessing the Switch
5742C4911, January 2007
Page 58

Alteon OS Application Guide
To upload the configuration to the switch:
Syntax:
scp <local filename> <username>@<switch IP address>:putcfg
Example:
>> # scp ad4.cfg scpadmin@205.178.15.157:putcfg
To apply and save the configuration
The apply and save commands are still needed after the last command, or use the following
commands:
>> # scp ad4.cfg scpadmin@205.178.15.157:putcfg_apply
>> # scp ad4.cfg scpadmin@205.178.15.157:putcfg_apply_save
The diff command is automatically executed at the end of putcfg to notify the remote
client of the difference between the new and the current configurations.
putcfg_apply runs the apply command after the putcfg is done.
putcfg_apply_save saves the new configuration to the flash after putcfg_apply
is done.
The putcfg_apply and putcfg_apply_save commands are provided because
extra apply and save commands are usually required after a putcfg; however, an
SCP session is not in an interactive mode at all.
SSH and SCP Encryption of Management Messages
The following encryption and authentication methods are supported for SSH and SCP:
Server Host Authentication: Client RSA authenticates the switch at the beginning of
every connection
Key Exchange: RSA
Encryption: 3DES-CBC, DES
User Authentication: Local password authentication, RADIUS, SecurID
(via RADIUS, TACACS+, for SSH only—does not apply
to SCP)
Chapter 1: Accessing the Switch 42C4911, January 2007
58
Page 59

Alteon OS Application Guide
Generating RSA Host and Server Keys for SSH Access
T o support the SSH server feature, two sets of RSA keys (host and server keys) are required.
The host key is 1024 bits and is used to identify the GbE Switch Module. The server key is 768
bits and is used to make it impossible to decipher a captured session by breaking into the GbE
Switch Module at a later time.
When the SSH server is first enabled and applied, the switch automatically generates the RSA
host and server keys and is stored in the FLASH memory.
NOTE – To configure RSA host and server keys, first connect to the GbE Switch Module
through the console port (commands are not available via external Telnet connection), and
enter the following commands to generate them manually.
>> # /cfg/sys/sshd/hkeygen (Generates the host key)
>> # /cfg/sys/sshd/skeygen (Generates the server key)
These two commands take effect immediately without the need of an apply command.
When the switch reboots, it will retrieve the host and server keys from the FLASH memory. If
these two keys are not available in the flash and if the SSH server feature is enabled, the switch
automatically generates them during the system reboot. This process may take several minutes
to complete.
The switch can also automatically regenerate the RSA server key. To set the interval of RSA
server key autogeneration, use this command:
>> # /cfg/sys/sshd/intrval <number of hours (0-24)>
A value of 0 (zero) denotes that RSA server key autogeneration is disabled. When greater than
0, the switch will autogenerate the RSA server key every specified interval; however, RSA
server key generation is skipped if the switch is busy doing other key or cipher generation
when the timer expires.
NOTE – The switch will perform only one session of key/cipher generation at a time. Thus, an
SSH/SCP client will not be able to log in if the switch is performing key generation at that
time, or if another client has logged in immediately prior. Also, key generation will fail if an
SSH/SCP client is logging in at that time.
Chapter 1: Accessing the Switch
5942C4911, January 2007
Page 60

Alteon OS Application Guide
SSH/SCP Integration with Radius Authentication
SSH/SCP is integrated with RADIUS authentication. After the RADIUS server is enabled on
the switch, all subsequent SSH authentication requests will be redirected to the specified
RADIUS servers for authentication. The redirection is transparent to the SSH clients.
SSH/SCP Integration with TACACS+ Authentication
SSH/SCP is integrated with TACACS+ authentication. After the TACACS+ server is enabled
on the switch, all subsequent SSH authentication requests will be redirected to the specified
TACACS+ servers for authentication. The redirection is transparent to the SSH clients.
SecurID Support
SSH/SCP can also work with SecurID, a token card-based authentication method. The use of
SecurID requires the interactive mode during login, which is not provided by the SSH connection.
NOTE – There is no SNMP or Browser-Based Interface (BBI) support for SecurID because the
SecurID server, ACE, is a one-time password authentication and requires an interactive session.
Using SecurID with SSH
Using SecurID with SSH involves the following tasks.
To log in using SSH, use a special username, “ace,” to bypass the SSH authentication.
After an SSH connection is established, you are prompted to enter the username and pass-
word (the SecurID authentication is being performed now).
Provide your username and the token in your SecurID card as a regular Telnet user.
Using SecurID with SCP
Using SecurID with SCP can be accomplished in two ways:
Using a RADIUS server to store an administrator password.
You can configure a regular administrator with a fixed password in the RADIUS server if
it can be supported. A regular administrator with a fixed password in the RADIUS server
can perform both SSH and SCP with no additional authentication required.
Using an SCP-only administrator password.
Use the command, /cfg/sys/sshd/scpadm to bypass the checking of SecurID.
Chapter 1: Accessing the Switch 42C4911, January 2007
60
Page 61

Alteon OS Application Guide
An SCP-only administrator’s password is typically used when SecurID is used. For example, it can be used in an automation program (in which the tokens of SecurID are not available) to back up (download) the switch configurations each day.
NOTE – The SCP-only administrator’s password must be different from the regular administrator’s password. If the two passwords are the same, the administrator using that password will
not be allowed to log in as an SSH user because the switch will recognize him as the SCP-only
administrator. The switch will only allow the administrator access to SCP commands.
End User Access Control
Alteon OS allows an administrator to define end user accounts that permit end users to perform
operation tasks via the switch CLI commands. Once end user accounts are configured and
enabled, the switch requires username/password authentication.
For example, an administrator can assign a user, who can then log into the switch and perform
operational commands (effective only until the next switch reboot).
Considerations for Configuring End User Accounts
A maximum of 10 user IDs are supported on the switch.
Alteon OS supports end user support for Console, Telnet, BBI, and SSHv1/v2 access to
the switch. As a result, only very limited access will be granted to the Primary Administrator under the BBI/SSH1 mode of access.
If RADIUS authentication is used, the user password on the Radius server will override
the user password on the GbE Switch Module. Also note that the password change command on the switch only modifies the use switch password and has no effect on the user
password on the Radius server. Radius authentication and user password cannot be used
concurrently to access the switch.
Passwords can be up to 15 characters in length for TACACS, RADIUS, T elnet, SSH, Con-
sole, and Web access.
Chapter 1: Accessing the Switch
6142C4911, January 2007
Page 62

Alteon OS Application Guide
Strong Passwords
The administrator can require use of Strong Passwords for users to access the GbESM. Strong
Passwords enhance security because they make password guessing more difficult.
The following rules apply when Strong Passwords are enabled:
Each passwords must be 8 to 14 characters
Within the first 8 characters, the password:
must have at least one number or one symbol
must have both upper and lower case letters
cannot be the same as any four previously used passwords
The following are examples of strong passwords:
123 4AbcXyz
Super+User
Exo1 cet2
The administrator can choose the number of days allowed before each password expires. When
a strong password expires, the user is allowed to log in one last time (last time) to change the
password. A warning provides advance notice for users to change the password.
Use the Strong Password menu to configure Strong Passwords.
>> # /cfg/sys/access/user/strongpw
User Access Control Menu
The end user access control menu is located in the System access menu.
>> # /cfg/sys/access/user
Setting up User IDs
Up to 10 user IDs can be configured in the User ID menu.
>> # /cfg/sys/access/user/uid 1
Chapter 1: Accessing the Switch 42C4911, January 2007
62
Page 63

Alteon OS Application Guide
Defining User Names and Passwords
Use the User ID menu to define user names and passwords.
>> User ID 1 # name user1 (Assign name to user ID 1)
Current user name:
New user name: user1
>> User ID 1 # passwd (Assign password to user ID 1)
Changing user password; validation required:
Enter current admin password: <current administrator password>
Enter new user1 password: <new user password>
Re-enter new user1 password: <new user password>
New user1 password accepted.
Defining a User’s Access Level
The end user is by default assigned to the user access level (also known as class of service, or
CoS). CoS for all user accounts have global access to all resources except for User CoS, which
has access to view only resources that the user owns. For more information, see Table 1-2
“User Access Levels” on page 47.
To change the user’s level, enter the class of service
cos command, and select one of the fol-
lowing options:
>> User ID 1 # cos <user|oper|admin>
Validating a User’s Configuration
User ID 2 # cur
name jane , dis, cos user , password valid, offline
Enabling or Disabling a User
An end user account must be enabled before the switch recognizes and permits login under the
account. Once enabled, the switch requires any user to enter both username and password.
>> # /cfg/sys/access/user/uid <#>/ena
>> # /cfg/sys/access/user/uid <#>/dis
Chapter 1: Accessing the Switch
6342C4911, January 2007
Page 64

Alteon OS Application Guide
Listing Current Users
The cur command displays defined user accounts and whether or not each user is currently
logged into the switch.
# /cfg/sys/access/user/cur
Usernames:
user - Enabled - offline
oper - Disabled - offline
admin - Always Enabled - online 1 session
Current User ID table:
1: name jane , ena, cos user , password valid, online
2: name john , ena, cos user , password valid, online
Logging into an End User Account
Once an end user account is configured and enabled, the user can login to the switch username/
password combination. The level of switch access is determined by the CoS established for the
end user account.
Chapter 1: Accessing the Switch 42C4911, January 2007
64
Page 65

Alteon OS Application Guide
Chapter 1: Accessing the Switch
6542C4911, January 2007
Page 66

Alteon OS Application Guide
Chapter 1: Accessing the Switch 42C4911, January 2007
66
Page 67

CHAPTER 2
Port-based Network Access Control
Port-Based Network Access control provides a means of authenticating and authorizing
devices attached to a LAN port that has point-to-point connection characteristics. It prevents
access to ports that fail authentication and authorization. This feature provides security to ports
of the GbESM that connect to blade servers.
The following topics are discussed in this section:
“Extensible Authentication Protocol over LAN” on page 68
“802 .1 x Authentication Process” on page 69
“802.1x Port States” on page 71
“Supported RADIUS Attributes” on page 72
“Configuration Guidelines” on page 73
42C4911, January 2007 67
Page 68

Alteon OS Application Guide
Extensible Authentication Protocol over LAN
Alteon OS can provide user-level security for its ports using the IEEE 802.1x protocol, which
is a more secure alternative to other methods of port-based network access control. Any device
attached to an 802.1x-enabled port that fails authentication is prevented access to the network
and denied services offered through that port.
The 802.1x standard describes port-based network access control using Extensible Authentication Protocol over LAN (EAPoL). EAPoL provides a means of authenticating and authorizing
devices attached to a LAN port that has point-to-point connection characteristics and of preventing access to that port in cases of authentication and authorization failures.
EAPoL is a client-server protocol that has the following components:
Supplicant or Client
The Supplicant is a device that requests network access and provides the required credentials (user name and password) to the Authenticator and the Authenticator Server.
Authenticator
The Authenticator enforces authentication and controls access to the network. The
Authenticator grants network access based on the information provided by the Supplicant
and the response from the Authentication Server. The Authenticator acts as an intermediary between the Supplicant and the Authentication Server: requesting identity information
from the client, forwarding that information to the Au thent icati on Server for validat ion,
relaying the server’s responses to the client, and authorizing network access based on the
results of the authentication exchange. The GbESM acts as an Authenticator.
Authentication Server,
The Authentication Server validates the credentials provided by the Supplicant to determine if the Authenticator should grant access to the network. The Authentication Server
may be co-located with the Authenticator. The GbESM re lies on external RADIUS servers
for authentication.
Upon a successful authentication of the client by the server, the 802.1x-controlled port transitions from unauthorized to authorized state, and the client is allowed full access to services
through the port. When the client sends an EAP-Logoff message to the authenticator, the port
will transition from authorized to unauthorized state.
Chapter 2: Port-based Network Access Control 42C4911, January 2007
68
Page 69

Alteon OS Application Guide
8
RADIUS
r
802.1x Authentication Process
The clients and authenticators communicate using Extensible Authentication Protocol (EAP),
which was originally designed to run over PPP, and for which the IEEE 802.1x Standard has
defined an encapsulation method over Ethernet frames, called EAP over LAN (EAPOL).
Figure 2-1 shows a typical message exchange initiated by the client.
02.1x Client
EAPOL
Ethernet
GbESM
(Authenticator)
(RADIUS Client)
RADIUS-EAP
UDP/IP
Serve
Port Unauthorized
EAPOL-Start
EAP-Request (Credentials)
EAP-Response (Credentials)
Radius-Access-Request
EAP-Request (Credentials)
EAP-Response (Credentials)
EAP-Success
Radius-Access-Challenge
Radius-Access-Request
Radius-Access-Accept
Port Authorized
Figure 2-1 Authenticating a Port Using EAPoL
Chapter 2: Port-based Network Access Control
6942C4911, January 2007
Page 70

Alteon OS Application Guide
EAPoL Message Exchange
During authentication, EAPOL messages are exchanged between the client and the GbESM
authenticator, while RADIUS-EAP messages are exchanged between the GbESM authenticator and the RADIUS server.
Authentication is initiated by one of the following methods:
GbESM authenticator sends an EAP-Request/ Id entity packet to the client
Client sends an EAPOL-Start frame to the GbESM authenticator, which responds with an
EAP-Request/Identity frame.
The client confirms its identity by sending an EAP-Response/Identity frame to the GbESM
authenticator, which forwards the frame encapsulated in a RADIUS packet to the server.
The RADIUS authentication server chooses an EAP-supported authentication algorithm to
verify the client’s identity, and sends an EAP-Request packet to the client via the GbESM
authenticator. The client then replies to the RADIUS server with an EAP-Response containing
its credentials.
Upon a successful authentication of the client by the server, the 802.1x-controlled port transitions from unauthorized to authorized state, and the client is allowed full access to services
through the controlled port. When the client later sends an EAPOL-Logoff message to the
GbESM authenticator, the port transitions from authorized to unauthorized state.
If a client that does not support 802.1x connects to an 802.1x-controlled port, the GbESM
authenticator requests the client's identity when it detects a change in the operational state of
the port. The client does not respond to the request, and the port remains in the unauthorized
state.
NOTE – When an 802.1x-enabled client connects to a port that is not 802.1x-controlled, the client initiates the authentication process by sending an EAPOL-Start frame. When no response is
received, the client retransmits the request for a fixed number of times. If no response is
received, the client assumes the port is in authorized state, and begins sending frames, even if
the port is unauthorized.
Chapter 2: Port-based Network Access Control 42C4911, January 2007
70
Page 71

Alteon OS Application Guide
802.1x Port States
The state of the port determines whether the client is granted access to the network, as follows:
Unauthorized
While in this state the port discards all ingress and egress traffic except EAP packets.
Authorized
When the client is successfully authenticated, the port transitions to the authorized state
allowing all traffic to and from the client to flow normally.
Force Unauthorized
You can configure this state that denies all access to the port.
Force Authorized
You can configure this state that allows full access to the port.
Use the 802.1x Global Configuration Menu (/cfg/l2/8021x/global) to
configure 802.1x authentication for all ports in the switch. Use the 802.1x Port Menu
(/cfg/l2/8021x/port x) to configure a single port.
Chapter 2: Port-based Network Access Control
7142C4911, January 2007
Page 72

Alteon OS Application Guide
Supported RADIUS Attributes
The Alteon 802.1x Authenticator relies on external RADIUS servers for authentication
with EAP. Table 2 lists the RADIUS attributes that are supported as part of
RADIUS-EAP authentication based on the guidelines specified in Annex D of the 802.1x
standard and RFC 3580.
Table 2 Support for RADIUS Attributes
# Attribute Attribute Value A-R A-A A-C A-R
1 User-Name The value of the Type-Data field from the supplicant’s
EAP-Response/Identity message. If the Identity is
unknown (i.e. Type-Data field is zero bytes in length), this
attribute will have the same value as the Calling-StationId.
4 NAS-IP-Address IP address of the authenticator used for Radius commu-
nication.
5 NAS-Port Port number of the authenticator port to which the suppli-
cant is attached.
24 S tate Server-specific value. This is sent unmodified back to the
server in an Access-Request that is in response to an
Access-Challenge.
30 Called-Station-ID The MAC address of the authenticator encoded as an
ASCII string in canonical format, e.g. 000D5622E3 9F.
31 Calling-St ation-ID The MAC address of the supplicant encoded as an ASCII
string in canonical format, e.g. 00034B436206.
79 EAP-Message Encapsulated EAP packets from the supplicant to the
authentication server (Radius) and vice-versa. The
authenticator relays the decoded packet to both devices.
80 Message-Authentica-
tor
Always present whenever an EAP-Message attribute is
also included. Used to integrity-protect a packet.
10-10 0
1000
1000
0-1 0-1 0-1 0
1000
1000
1+ 1+ 1+ 1+
1111
87 NAS-Port-ID Name assigned to the authenticator port, e.g.
Server1_Port3
Legend:
RADIUS Packet Types: A-R (Access-Request), A-A (Access-Accept), A-C (Access-Challenge), A-R (Access-Reject)
RADIUS Attribute Support:
0 This attribute MUST NOT be present in a packet.
0+ Zero or more instances of this attribute MAY be present in a packet.
0-1 Zero or one instance of this attribute MAY be present in a packet.
1 Exactly one instance of this attribute MUST be present in a packet.
1+ One or more of these attributes MUST be present.
Chapter 2: Port-based Network Access Control 42C4911, January 2007
72
1000
Page 73

Alteon OS Application Guide
Configuration Guidelines
When configuring EAPoL, consider the following guidelines:
The 802.1x port -based authentication is currently supported only in point-to-point config-
urations, that is, with a single supplicant connected to an 802.1x-enabled switch port.
When 802.1x is enabl e d, a port has to be in the authorized state before any other Layer 2
feature can be operationally enabled. For example, the STG state of a port is operationally
disabled while the port is in the unauthorized state.
The 802.1x supplicant capability is not supported. Therefore, none of its ports can suc-
cessfully connect to an 802.1x-enabled port of another device, such as another switch, that
acts as an authenticator, unless access control on the remote port is disabled or is configured in forced-authorized mode. For example, if a GbESM is connected to another
GbESM, and if 802.1x is enabled on both switches, the two connected ports must be configured in force-authorized mode.
The 802.1x standard has optional provisions for supporting dynamic virtual LAN
assignment via RADIUS tunnelling attributes, for example, Tunnel-Type (=VLAN),
Tunnel-Medium-Type (=802), and Tunnel-Private-Group-ID (=VLAN id).
These attributes are not supported and might affect 802.1x operations. Other unsupported
attributes include Service-Type, Session-Timeout, and Termination-Action.
RADIUS accounting service for 802.1x-authenticated devices or users is not supported.
Configuration changes performed using SNMP and the standard 802.1x MIB will take
effect immediately.
Chapter 2: Port-based Network Access Control
7342C4911, January 2007
Page 74

Alteon OS Application Guide
Chapter 2: Port-based Network Access Control 42C4911, January 2007
74
Page 75

CHAPTER 3
VLANs
This chapter describes network design and topology considerations for using V irtual Local Area
Networks (VLANs). VLANs are commonly used to split up groups of network users into manageable broadcast domains, to create logical segmentation of workgroups, and to enforce security
policies among logical segments. The following topics are discussed in this chapter:
“VLANs and Port VLA N ID Nu mbers” on page 77
“VLAN Tagging” on page 80
“VLAN Topologies and Design Considerations” on page 84
This section discusses how you can logically connect users and segments to a host that
supports many logical segments or subnets by using the flexibility of the multiple VLAN
system.
“Protocol-based VLANs” on page 87
NOTE – Basic VLANs can be configured during initial switch configuration (see “Using the
Setup Utility” in the Alteon OS Command Reference). More comprehensive VLAN configuration can be done from the Command Line Interface (see “VLAN Configuration” as well as
“Port Configuration” in the Alteon OS Command Reference).
42C4911, January 2007 75
Page 76

Alteon OS Application Guide
Overview
Setting up virtual LANs (VLANs) is a way to segment networks to increase network flexibility
without changing the physical network topology. W ith network segmentation, each switch port
connects to a segment that is a single broadcast domain. When a switch port is configured to be
a member of a VLAN, it is added to a group of ports (workgroup) that belong to one broadcast
domain.
Ports are grouped into broadcast domains by assigning them to the same VLAN. Frames
received in one VLAN can only be forwarded within that VLAN, and multicast, broadcast,
and unknown unicast frames are flooded only to ports in the same VLAN. The GbE Switch
Module supports jumbo frames, up to 12288 bytes.
Chapter 3: VLANs 42C4911, January 2007
76
Page 77

Alteon OS Application Guide
VLANs and Port VLAN ID Numbers
VLAN Numbers
Alteon OS supports up to 1024 VLANs per switch. Even though the maximum number
of VLANs supported at any given time is 1024, each can be identified with any number
between 1 and 4095. VLAN 1 is the default VLAN for the external ports and the internal blade
ports. VLAN 4095 is reserved for use by the internal management ports (MGT1 and MGT2).
VLAN 4094 is reserved for use by the external management port (EXT7).
Viewing VLANs
VLAN information menu:
VLAN Name Status Ports
---- ------------------------ ------ ------------------------1 Default VLAN ena INT1-INT14 EXT1-EXT6
2 VLAN 2 dis empty
4094 EXT-Mgmt VLAN ena EXT7
4095 Mgmt VLAN ena MGT1-MGT2
PVLAN Protocol FrameType EtherType Priority Status Ports
----- -------- -------------------- -------- ------ ----------1 2 empty 0000 0 dis empty
PVLAN PVLAN-Tagged Ports
----- --------------------------none none
NOTE – The sample screens that appear in this document might differ slightly from the screens
displayed by your system. Screen content varies based on the type of BladeCenter unit that you
are using and the firmware versions and options that are installed.
PVID Numbers
Each port in the switch has a configurable default VLAN number, known as its PVID. By
default, the PVID for all non-management ports is set to 1, which correlates to the default
VLAN ID. The PVID for each port can be configured to any VLAN number between 1 and
4094.
Chapter 3: VLANs
7742C4911, January 2007
Page 78

Alteon OS Application Guide
Viewing and Configuring PVIDs
Use the following CLI commands to view PVIDs:
Port information:
Alias Port Tag Fast PVID NAME VLAN(s)
----- ---- --- ---- ---- -------------- ----------------------------
--INT1 1 n n 1 INT1 1
INT2 2 n n 1 INT2 1
INT3 3 n n 1 INT3 1
INT4 4 n n 1 INT4 1
INT5 5 n n 1 INT5 1
INT6 6 n n 1 INT6 1
INT7 7 n n 1 INT7 1
INT8 8 n n 1 INT8 1
INT9 9 n n 1 INT9 1
INT10 10 n n 1 INT10 1
INT11 11 n n 1 INT11 1
INT12 12 n n 1 INT12 1
INT13 13 n n 1 INT13 1
INT14 14 n n 1 INT14 1
MGT1 15 n n 4095 MGT1 4095
MGT2 16 n n 4095 MGT2 4095
EXT1 17 n n 1 EXT1 1
EXT2 18 n n 1 EXT2 1
EXT3 19 n n 1 EXT3 1
EXT4 20 n n 1 EXT4 1
EXT5 21 n n 1 EXT5 1
EXT6 22 n n 1 EXT6 1
EXT7 23 n n 4094 EXT7 4094
* = PVID is tagged.
NOTE – The sample screens that appear in this document might differ slightly from the screens
displayed by your system. Screen content varies based on the type of BladeCenter unit that you
are using and the firmware versions and options that are installed.
Port Configuration:
>> /cfg/port INT7/pvid 7
Current port VLAN ID: 1
New pending port VLAN ID: 7
>> Port INT7#
Chapter 3: VLANs 42C4911, January 2007
78
Page 79

Alteon OS Application Guide
Each port on the switch can belong to one or more VLANs, and each VLAN can have any
number of switch ports in its membership. Any port that belongs to multiple VLANs, however,
must have VLAN tagging enabled (see “VLAN Tagging” on page 80).
Chapter 3: VLANs
7942C4911, January 2007
Page 80

Alteon OS Application Guide
VLAN Tagging
Alteon OS software supports 802.1Q VLAN tagging, providing standards-based VLAN support for Ethernet systems.
Tagging places the VLAN identifier in the frame header of a packet, allowing each port to
belong to multiple VLANs. When you add a port to multiple VLANs, you also must enable
tagging on that port.
Since tagging fundamentally changes the format of frames transmitted on a tagged port, you
must carefully plan network designs to prevent tagged frames from being transmitted to
devices that do not support 802.1Q VLAN tags, or devices where tagging is not enabled.
Important terms used with the 802.1Q tagging feature are:
VLAN identifier (VID)—the 12-bit portion of the VLAN tag in the frame header that
identifies an explicit VLAN.
Port VLAN identifier (PVID)—a classification mechanism that associates a port with a
specific VLAN. For example, a port with a PVID of 3 (PVID =3) assigns all untagged
frames received on this port to VLAN 3. Any untagged frames received by the switch are
classified with the PVID of the receiving port.
Tagged frame—a frame that carries VLAN tagging information in the header. This VLAN
tagging information is a 32-bit field (VLAN tag) in the frame header that identifies the
frame as belonging to a specific VLAN. Untagged frames are marked (tagged) with this
classification as they leave the switch through a port that is configured as a tagged port.
Untagged frame— a frame that does not carry any VLAN tagging information in the
frame header.
Untagged member—a port that has been configured as an untagged member of a specific
VLAN. When an untagged frame exits the switch through an untagged member port, the
frame header remains unchanged. When a tagged frame exits the switch through an
untagged member port, the tag is stripped and the tagged frame is changed to an untagged
frame.
Tagged member—a port that has been configured as a tagged member of a specific
VLAN. When an untagged frame exits the switch through a tagged member port, the
frame header is modified to include the 32-bit tag associated with the PVID. When a
tagged frame exits the switch through a tagged member port, the frame header remains
unchanged (original VID remains).
NOTE – If a 802.1Q tagged frame is received by a port that has VLAN-tagging disabled, then
the frame is dropped at the ingress port.
Chapter 3: VLANs 42C4911, January 2007
80
Page 81

Figure 3-1 Default VLAN settings
802.1Q Switch
Alteon OS Application Guide
VLAN 1
Port 1
PVID = 1
DA
SA
Incoming
untagged
packet
Key
By default:
Data
CRC
All ports are assigned PVID = 1
All external ports are untagged members of VLAN 1
All internal server ports are untagged members of VLAN 1
Port 2 Port 3 Port 4 Port 5
CRC
Outgoing
untagged packet
(unchanged)
Data
SA
DA
Port 6 ...
Port 7
BS45010A
NOTE – The port numbers specified in these illustrations may not directly correspond to the
physical port configuration of your switch model.
When a VLAN is configured, ports are added as members of the VLAN, and the ports are
defined as either tagged or untagged (see Figure 3-2 through Figure 3-5).
In Figure 3-1, untagged incoming packets are assigned directly to VLAN 2 (PVID = 2). Port 5
is configured as a tagged member of VLAN 2, and port 7 is configured as an untagged member
of VLAN 2.
The default configuration settings for GbE Switch Modules have all ports set as untagged
members of VLAN 1 with all ports configured as PVID = 1. In the default configuration example shown in Figure 3-1 on page 81, all incoming packets are assigned to VLAN 1 by the
default port VLAN identifier (PVID =1).
Figure 3-2 through Figure 3-5 illustrate generic examples of VLAN tagging.
Chapter 3: VLANs
8142C4911, January 2007
Page 82

Alteon OS Application Guide
A
P
Tagged member
NOTE – The port assignments in the following figures are not meant to match the
GbE Switch Module.
Figure 3-2 Port-based VLAN assignment
PVID = 2
Untagged packet
B
efore
Port 1
DASADataCRC
Port 4
Port 6
Port 2 Port 3
802.1Q Switch
Port 7 Port 8
Tagged member
of VLAN 2
Port 5
Untagged member
of VLAN 2
BS45011A
As shown in Figure 3-3, the untagged packet is marked (tagged) as it leaves the switch through
port 5, which is configured as a tagged member of VLAN 2. The untagged packet remains
unchanged as it leaves the switch through port 7, which is configured as an untagged member
of VLAN 2.
Figure 3-3 802.1Q tagging (after port-based VLAN assignment)
VID = 2
Untagged memeber
untagged packet
Port 1
Port 4
Port 6 Port 7 Port 8
of VLAN 2
Outgoing
(unchanged)
Port 2 Port 3
802.1Q Switch
CRC
Data
SA
DA
of VLAN 2
Port 5
(*Recalculated)
Key
Priority
CFI
VID
DASADataCRC* Tag
8100 CFI
16 bits 3 bits 1 bits 12 bits
After
- User_priority
- Canonical format indicator
- VLAN identifier
VID = 2Priority
BS45012
Chapter 3: VLANs 42C4911, January 2007
82
Page 83

Alteon OS Application Guide
A
PVID = 2
In Figure 3-4, tagged incoming packets are assigned directly to VLAN 2 because of the tag
assignment in the packet. Port 5 is configured as a tagged member of VLAN 2, and port 7 is
configured as an untagged member of VLAN 2.
Figure 3-4 802.1Q tag assignment
Tagged packet
B
efore
PVID = 2
DASATagDataCRC
Port 1
Port 4
Port 6
Port 2 Port 3
802.1Q Switch
Port 7 Port 8
Tagged member
of VLAN 2
Port 5
Untagged member
of VLAN 2
As shown in Figure 3-5, the tagged packet remains unchanged as it leaves the switch through
port 5, which is configured as a tagged member of VLAN 2. Howe ver, the tagged packet is
stripped (untagged) as it leaves the switch through port 7, which is configured as an untagged
member of VLAN 2.
Figure 3-5 802.1Q tagging (after 802.1Q tag assignment)
Port 5
Key
Tagged member
of VLAN 2
8100 CFI
16 bits 3 bits 1 bit 12 bits
After
Priority
CFI
VID
- User_priority
- Canonical format indicator
- VLAN identifier
DASADataCRC Tag
Port 1
Port 4
Port 6 Port 7 Port 8
Untagged member
of VLAN 2
Port 2 Port 3
802.1Q Switch
(*Recalculated)
CRC*
Data
Outgoing
SA
untagged packet
changed
DA
(tag removed)
BS45013A
VID = 2Priority
BS45014
NOTE – Set the configuration to factory default (/boot/conf factory) to reset all non-
management ports to VLAN 1.
Chapter 3: VLANs
8342C4911, January 2007
Page 84

Alteon OS Application Guide
VLAN Topologies and Design Considerations
By default, the Alteon OS software is configured so that tagging is disabled on all external
ports and all internal ports.
By default, the Alteon OS software is configured so that all internal ports are members of
VLAN 1.
By default, the Alteon OS software is configured so that the management ports (MGT1
and MGT2) are members of th e managem ent VLAN 4095.
By default, the Alteon OS software is configured so that the external management port
(EXT7) is a member of VLAN 4094.
If configuring Spanning Tree Groups (STG), note that Spanning Tree Groups 2-128 may
contain only one VLAN.
VLAN configuration rules
VLANs operate according to specific configuration rules. When creating VLANs, consider the
following rules that determine how the configured VLAN reacts in any network topology:
All ports involved in trunking and port mirroring must have the same VLAN configura-
tion. If a port is on a trunk with a mirroring port, the VLAN configuration cannot be
changed. For more information trunk groups, see “Po rt Trunking Example” on page 97.
All ports that are involved in port mirroring must have memberships in the same VLANs.
If a port is configured for port mirroring, the port’s VLAN membership cannot be
changed. For more information on configuring port mirroring, see “Monitoring Ports” on
page 246.
Chapter 3: VLANs 42C4911, January 2007
84
Page 85

Alteon OS Application Guide
Example 1: Multiple VLANs with Tagging Adapters
BladeCenter
VLAN #3
VLAN #1, 2, 3
GbE
GbE
Switch Module
Switch Module
Figure 3-6 Example 1: Multiple VLANs with VLAN-Tagged Gigabit Adapters
The features of this VLAN are described below:
Component Description
GbE Switch
Module
This switch is configured for three VLANs that represent three different IP subnets. Two servers and five clients are attached to the switch.
Server #1 This server is a member of VLAN 3 and has presence in only one IP
subnet. The associated internal switch port is only a member of VLAN
3, so tagging is disabled.
Server #2 This high-use server needs to be accessed from all VLANs and IP sub-
nets. The server has a VLAN-tagging adapter installed with VLAN tagging turned on. The adapter is attached to one of the internal switch
ports, that is a member of VLANs 1, 2, and 3, and has tagging enabled.
Because of the VLAN tagging capabilities of both the adapter and the
switch, the server is able to communicate on all three IP subnets in this
network. Broadcast separation between all three VLANs and subnets,
however, is maintained.
Chapter 3: VLANs
8542C4911, January 2007
Page 86

Alteon OS Application Guide
Component Description
PCs #1 and #2 These PCs are attached to a shared media hub that is then connected to
PC #3 A member of VLAN 1, this PC can only communicate with Server 2
PC #4 A member of VLAN 3, this PC can only communicate with Server 1
PC #5 A member of both VLAN 1 and VLAN 2, this PC has a VLAN-tagging
NOTE – VLAN tagging is required only on ports that are connected to other GbE Switch
Modules or on ports that connect to tag-capable end-stations, such as servers with VLANtagging adapters.
the switch. They belong to VLAN 2 and are logically in the same IP
subnet as Server 2 and PC 5. The associated external switch port has
tagging disabled.
and PC 5. The associated external switch port has tagging disabled.
and Server 2. The associated external switch port has tagging disabled.
Gigabit Ethernet adapter installed. It can communicate with Server 2
and PC 3 via VLAN 1, and to Server 2, PC 1 and PC 2 via VLAN 2.
The associated external switch port is a member of VLAN 1 and
VLAN 2, and has tagging enabled.
Chapter 3: VLANs 42C4911, January 2007
86
Page 87

Alteon OS Application Guide
Protocol-based VLANs
Protocol-based VLANs (PVLANs) allow you to segment network traffic according to the network protocols in use. Traffic generated by supported network protocols can be confined to a
particular port-based VLAN. You can give different priority levels to traffic generated by different network protocols.
With PVLAN, the switch classifies incoming packets by Ethernet protocol of the packets, not
by the configuration of the ingress port. When an untagged or priority-tagged frame arrives at
an ingress port, the protocol information carried in the frame is used to determine a VLAN to
which the frame belongs. If a frame’s protocol is not recognized as a pre-defined PVLAN type,
the ingress port’s PVID is assigned to the frame. When a tagged frame arrives, the VLAN ID in
the frame’s tag is used.
Each VLAN can contain up to eight different PVLANs. You can configure separate PVLANs
on different VLANs, with each PVLAN segmenting traffic for the same protocol type. For
example, you can configure PVLAN 1 on VLAN 2 to segment IPv4 traffic, and PVLAN 8 on
VLAN 100 to segment IPv4 traffic.
T o define a PVLAN on a VLAN, configure a PVLAN number (1-8) and specify the frame type
and the Ethernet type of the PVLAN protocol. You must assign at least one port to the PVLAN
before it can function. Define the PVLAN frame type and Ethernet type as follows:
Frame type—consists of one of the following values:
Ether2 (Ethernet II)
SNAP (Simple Network Access Protocol)
LLC (Logical Link Control)
Ethernet type —consists of a 4-digit (16 bit) hex value that defines the Ethernet type. You
can use common Ethernet protocol values, or define your own values. Following are
examples of common Ethernet protocol values:
IPv4 = 0080
IPv6 = 86dd
ARP = 0806
Chapter 3: VLANs
8742C4911, January 2007
Page 88

Alteon OS Application Guide
Port-based vs. Protocol-based VLANs
Each VLAN supports both port-based and protocol-based association, as follows:
The default VLAN configuration is port-based. All data ports are members of VLAN 1,
with no PVLAN association.
When you add ports to a PVLAN, the ports become members of both the port-based
VLAN and the PVLAN. For example, if you add port EXT1 to PVLAN 1 on VLAN 2, the
port also becomes a member of VLAN 2.
When you delete a PVLAN, it’s member ports remain members of the port-based VLAN.
For example, if you delete PVLAN 1 from VLAN 2, port EXT1 remains a member of
VLAN 2.
When you delete a port from a VLAN, the port is deleted from all corresponding
PVLANs.
PVLAN Priority Levels
You can assign each PVLAN a priority value of 0-7, used for Quality of Service (QoS).
PVLAN priority takes precedence over a port’s configured priority level. If no priority level is
configured for the PVLAN (priority = 0), each port’s priority is used (if configured).
All member ports of a PVLAN have the same PVLAN priority level.
PVLAN Tagging
When PVLAN tagging is enabled, the switch tags frames that match the PVLAN protocol. For
more information about tagging, see “VLAN Tagging” on page 80.
Untagged ports must have PVLAN tagging disabled. Tagged ports can have PVLAN tagging
either enabled or disabled.
PVLAN tagging has higher precedence than port-based tagging. If a port is tag enabled
(/cfg/port x/tag), and the port is a member of a PVLAN, the PVLAN tags egress
frames that match the PVLAN protocol.
Use the tag list command (/cfg/l2/vlan x/pvlan x/taglist) to define the complete list of tag-enabled ports in the PVLAN. Note that all ports not included in the PVLAN tag
list will have PVLAN tagging disabled.
Chapter 3: VLANs 42C4911, January 2007
88
Page 89

Alteon OS Application Guide
PVLAN Configuration Guidelines
Consider the following guidelines when you configure protocol-based VLANs:
Each port can support up to 16 VLAN protocols.
The GbESM can support up to 16 protocols simultaneously.
Each PVLAN must have at least one port assigned before it can be activated.
The same port within a port-based VLAN can belong to multiple PVLANs.
An untagged port can be a member of multiple PVLANs.
A port cannot be a member of different VLANs with the same protocol association.
Configuring PVLAN
Follow this procedure to configure a Protocol-based VLAN (PVLAN).
1. Create a VLAN and define the protocol type(s) supported by the VLAN.
>> /cfg/l2/vlan 2 (Select VLAN 2)
>> VLAN 2# ena
Current status: disabled
New status: enabled
>> VLAN 2# pvlan
Enter protocol number [1-8]:1 (Select a protocol number)
>> VLAN 2 Protocol 1# pty
Current FrameType: empty; EtherType: empty
Enter new frame type(Ether2/SNAP/LLC): ether2 (Define the frame type)
Enter new Ether type: 0800 (Define the Ethernet type)
New pending FrameType: Ether2; EtherType: 0800
2. Configure the priority value for the protocol.
>> VLAN 2 Protocol 1# prio (Configure the priority value)
Current protocol priority: 0
Enter new protocol priority [0-7]: 1
Chapter 3: VLANs
8942C4911, January 2007
Page 90

Alteon OS Application Guide
3. Add member ports for this PVLAN.
>> VLAN 2 Protocol 1# add int1
Port INT1 is an UNTAGGED port and its current PVID is 1.
Confirm changing PVID from 1 to 2 [y/n]: y
Current ports for VLAN 2: empty
Current ports for VLAN 1, Protocol 3: empty
Pending new ports for VLAN 2: INT1
Pending new ports for VLAN 2, Protocol 1: INT1
>> VLAN 2 Protocol 1# add ext1
Port EXT1 is an UNTAGGED port and its current PVID is 1.
Confirm changing PVID from 1 to 2 [y/n]: y
Current ports for VLAN 2: empty
Current ports for VLAN 1, Protocol 2: empty
Pending new ports for VLAN 2: INT1 EXT1
Pending new ports for VLAN 2, Protocol 1: INT1 EXT1
4. Configure VLAN tagging for ports.
>> VLAN 2 Protocol 1# /cfg/port int1/tag ena (Enable tagging on port)
Current VLAN tag support: disabled
New VLAN tag support: enabled
Port INT1 changed to tagged.
>> Port INT1# /cfg/l2/vlan 2/pvlan 1/tagpvl (Enable PVLAN tagging)
Enter port to be tagged: int1
Ena/Dis pvlan tag: ena
Current status: disabled
New status: enabled
WARN: Tagging status of Port 1 in VLAN 2 will be changed for
all protocols.
Confirm changing port's pvlan tagging status [y/n]: y
5. Enable the PVLAN.
>> VLAN 2 Protocol 1# ena (Enable the protocol-based VLAN)
Current status: disabled
New status: enabled
>> VLAN 2 Protocol 1# apply (Apply the configuration)
>> VLAN 2 Protocol 1# save (Save your changes)
Chapter 3: VLANs 42C4911, January 2007
90
Page 91

Alteon OS Application Guide
6. Verify PVLAN operation.
>> /info/l2/vlan (View VLAN information)
VLAN Name Status Ports
---- ------------------------ ------ ------------------------1 Default VLAN ena INT1-INT14 EXT2-EXT6
2 VLAN 2 ena INT1 EXT1
4094 EXT-Mgmt VLAN ena EXT7
4095 Mgmt VLAN ena MGT1 MGT2
PVLAN Protocol FrameType EtherType Priority Status Ports
----- -------- -------------------- -------- ------ ----------2 1 Ether2 0800 0 ena INT1
PVLAN PVLAN-Tagged Ports
----- --------------------------2 INT1 INT2
Chapter 3: VLANs
9142C4911, January 2007
Page 92

Alteon OS Application Guide
Chapter 3: VLANs 42C4911, January 2007
92
Page 93

CHAPTER 4
Ports and Trunking
Trunk groups can provide super-bandwidth, multi-link connections between GbE Switch Modules or other trunk-capable devices. A trunk group is a group of ports that act together, combining their bandwidth to create a single, larger virtual link. This chapter provides configuration
background and examples for trunking multiple ports together:
“ Overview” on this page
“Port Trunking Example” on page 97
“Configurable Trunk Hash Algorithm” on page 100
“Link Aggregation Control Protocol” on page 101
42C4911, January 2007 93
Page 94

Alteon OS Application Guide
Overview
When using port trunk groups between two switches, as shown in Figure 4-1, you can create a
virtual link between the switches, operating up to 60Gb per second, depending on how many
physical ports are combined. Each GbESM supports up to 13 trunk groups, and each trunk
group can contain up to six member ports.
BladeCenter
!
1
2
3456
RS 232
7
Aggregate
port trunk
Alteon Application Switch
Figure 4-1 Port Trunk Group
Trunk groups are also useful for connecting a GbE Switch Module to third-party devices that
support link aggregation, such as Cisco routers and switches with EtherChannel technology
(not ISL trunking technology) and Sun's Quad Fast Ethernet Adapter. T runk Group technology
is compatible with these devices when they are configured manually.
Chapter 4: Ports and Trunking 42C4911, January 2007
94
Page 95

Alteon OS Application Guide
Statistical Load Distribution
Network traffic is statistically distributed between the ports in a trunk group. The Alteon OSpowered switch uses the Layer 2 MAC address information present in each transmitted frame
for determining load distribution.
Each packet’s particular combination of source and destination MAC addresses results in
selecting one line in the trunk group for data transmission. If there are enough Layer 2 devices
feeding the trunk lines, then traffic distribution becomes relatively even.
Built-In Fault Tolerance
Since each trunk group is comprised of multiple physical links, the trunk group is inherently
fault tolerant. As long as one connection between the switches is available, the trunk remains
active.
Statistical load balancing is maintained whenever a port in a trunk group is lost or returned to
service.
Before you configure static trunks
When you create and enable a static trunk, the trunk members (switch ports) take on certain
settings necessary for correct operation of the trunking feature.
Before you configure your trunk, you must consider these settings, along with specific configuration rules, as follows:
1. Read the configuration rules provided in the section, “Trunk group configuration rules”
on page 96.”
2. Determine which switch ports (up to six) ar e to become tr unk m embers (the specific ports
making up the trunk).
Ensure that the chosen switch ports are set to enabled, using the /cfg/port command.
Trunk member ports must have the same VLAN configuration.
3. Consider how the existing Spanning Tree will react to the new trunk configuration. See
Chapter 5, “Spanning Tree Group” for Spanning Tree Group configuration guidelines.
4. Consider how existing VLANs will be affected by the addition of a trunk.
Chapter 4: Ports and Trunking
9542C4911, January 2007
Page 96

Alteon OS Application Guide
Trunk group configuration rules
The trunking feature operates according to specific configuration rules. When creating trunks,
consider the following rules that determine how a trunk group reacts in any network topology:
All trun ks must originate from one device, and lead to one destination device. For exam-
ple, you cannot combine a link from Server 1 and a link from Server 2, into one trunk
group.
Any physical switch port can belong to only one trunk group.
Trunking from third-party devices must comply with Cisco
All trun k mem ber ports must be assigned to the same VLAN configuration before the
trunk can be enabled.
If you change the VLAN settings of any trunk member, you cannot apply the change until
you change the VLAN settings of all trunk members.
When an active port is configured in a trunk, the port becomes a trunk member when you
enable the trunk using the /cfg/l2/trunk/ena command. The Spanning T ree
parameters for the port then change to reflect the new trunk settings.
All trunk members must be in the same Spanning Tree Group (STG) and can belong to
only one Spanning Tree Group (STG). However if all ports are tagged, then all trunk ports
can belong to multiple STGs.
®
EtherChannel® technology.
If you change the Spanning Tree participation of any trunk member to enabled or dis-
abled, the Spanning Tree participation of all members of that trunk changes similarly.
When a trunk is enabled, the trunk Spanning Tree participation setting takes precedence
over that of any trunk member.
You cannot configure a trunk member as a monitor port in a port-mirroring configuration.
Trunks cannot be monitored by a monitor port; however, trunk members can be moni-
tored.
To guarantee proper trunking behavior, all ports in static trunks must be configured for
full-duplex mode (cfg/port x/gig/mode full).
Chapter 4: Ports and Trunking 42C4911, January 2007
96
Page 97

Alteon OS Application Guide
Alteon Application Switch
Port Trunking Example
In the example below, three ports are trunked between two switches.
Trunk 3: Ports 2, 12, and 22
Trunk 1: Ports EXT1, EXT2, and EXT3
GbE Switch
Module
Prior to configuring each switch in the above example, you must connect to the appropriate
switch’s Command Line Interface (CLI) as the administrator.
NOTE – For details about accessing and using any of the menu commands described in this
example, see the Alteon OS Command Reference.
BladeCenter
Figure 4-2 Port Trunk Group Configuration Example
Chapter 4: Ports and Trunking
9742C4911, January 2007
Page 98

Alteon OS Application Guide
1. Connect the switch ports that will be members in the trunk group.
2. Follow these steps on the GbESM:
(a) Define a trunk group.
>> # /cfg/l2/trunk 1 (Select trunk group 1)
>> Trunk group 1# add EXT1 (Add port EXT1 to trunk group 1)
>> Trunk group 1# add EXT2 (Add port EXT2 to trunk group 1)
>> Trunk group 1# add EXT3 (Add port EXT3 to trunk group 1)
>> Trunk group 1# ena (Enable trunk group 1)
(b)Apply and verify the configuratio n.
>> Trunk group 1# apply (Make your changes active)
>> Trunk group 1# cur (View current trunking configuration)
Examine the resulting information. If any settings are incorrect, make appropriate changes.
(c) Save your new configuration changes.
>> Trunk group 1# save (Save for restore after reboot)
3. Repeat the process on the other switch.
>> # /cfg/l2/trunk 3 (Select trunk group 3)
>> Trunk group 3# add 2 (Add port 2 to trunk group 3)
>> Trunk group 3# add 12 (Add port 12 to trunk group 3)
>> Trunk group 3# add 22 (Add port 22 to trunk group 3)
>> Trunk group 3# ena (Enable trunk group 3)
>> Trunk group 3# apply (Make your changes active)
>> Trunk group 3# cur (View current trunking configuration)
>> Trunk group 3# save (Save for restore after reboot)
Trunk group 1 (on the GbESM) is now connected to trunk group 3 (on Alteon Application
Switch).
NOTE – In this example, a GbE Switch Module and an application switch are used. If a thirdparty device supporting link aggregation is used (such as Cisco routers and switches with
EtherChannel technology or Sun's Quad Fast Ethernet Adapter), trunk groups on the thirdparty device should be configured manually. Connection problems could arise when using
automatic trunk group negotiation on the third-party device.
Chapter 4: Ports and Trunking 42C4911, January 2007
98
Page 99

Alteon OS Application Guide
4. Examine the trunking information on each switch.
>> /info/l2/trunk (View trunking information)
Information about each port in each configured trunk group is displayed. Make sure that trunk
groups consist of the expected ports and that each port is in the expected state.
The following restrictions apply:
Any physical switch port can belong to only one trunk group.
Up to six ports can belong to the same trunk group.
Best performance is achieved when all ports in any given trunk group are configured for
the same speed.
Trunking from third-party devices must comply with Cisco
®
EtherChannel® technology.
Chapter 4: Ports and Trunking
9942C4911, January 2007
Page 100

Alteon OS Application Guide
Configurable Trunk Hash Algorithm
This feature allows you to configure the particular parameters for the GbESM Trunk Hash
algorithm instead of having to utilize the defaults. You can configure new default behavior for
Layer 2 traffic and Layer 3 traffic using the CLI menu cfg/l2/thash. You can select a
minimum of one or a maximum of two parameters to create one of the following configurations:
So ur ce IP (SIP)
Destination IP (DIP)
Source MAC (SMAC)
Destination MAC (DM AC)
So ur ce IP (SIP) + Destination IP (DIP)
Source MAC (SMAC) + Destination MAC (DMAC)
Chapter 4: Ports and Trunking 42C4911, January 2007
100
 Loading...
Loading...