Page 1
Moxa EtherDevice™ Switch
EDS-510A Series User’s Manual
www.moxa.com/product
Third Edition, February 2008
Moxa Inc.
Tel: +886-2-8919-1230
Fax: +886-2-8919-1231
Web:
www.moxa.com
Moxa Technical Support
Worldwide:
support@moxa.com
The Americas:
support@usa.moxa.com
Page 2

Moxa EtherDevice™ Switch
EDS-510A Series User’s Manual
The software described in this manual is furnished under a license agreement and may be used only in
accordance with the terms of that agreement.
Copyright Notice
Copyright © 2008 Moxa Inc.
All rights reserved.
Reproduction without permi ssion is pr ohibited.
Trademarks
Moxa is a registered trademark of the Moxa Inc.
All other trademarks or registered marks in this manual belong to their respective manufacturers.
Disclaimer
Information in this document is subject to change without notice and does not represent a commitment on the
part of Moxa.
Moxa provides this document “as is,” without warranty of any kind, either expressed or implied, including, but
not limited to, its particular purpose. Moxa reserves the right to make improvements and/or changes to this
manual, or to the products and/or the programs described in this manual, at any time.
Information provided in this manual is intended to be accurate and reliable. However, Moxa assumes no
responsibility for its use, or for any infringements on the rights of third parties that may result from its use.
This product might include unintentional technical or typographical errors. Changes are periodically made to the
information herein to correct such errors, and these changes are incorporated into new editions of the
publication.
Page 3

Table of Contents
Chapter 1 Introduction ...............................................................................................1-1
Overview.............................................................................................................................. 1-2
Package Checklist................................................................................................................. 1-2
Features ................................................................................................................................ 1-2
Industrial Networking Capability.............................................................................. 1-2
Designed for Industrial Applications.........................................................................1-2
Useful Utility and Remote Configuration ................................................................. 1-3
Recommended Software and Accessories................................................................. 1-3
Chapter 2 Getting Started ..........................................................................................2-1
RS-232 Console Configuration (115200, None, 8, 1, VT100) ............................................. 2-2
Configuration using a T elnet Console.................................................................................. 2-5
Configuration using a Web Browser..................................................................................... 2-6
Disabling T elnet and Browser Access .................................................................................. 2-8
Chapter 3 Featured Functions...................................................................................3-1
Configuring Basic Settings................................................................................................... 3-2
System Identification................................................................................................. 3-2
Password ................................................................................................................... 3-3
Accessible IP............................................................................................................. 3-4
Port............................................................................................................................ 3-5
Network..................................................................................................................... 3-6
Time.......................................................................................................................... 3-8
Turbo Ring DIP Switch............................................................................................. 3-9
System File Update—By Remote TFTP................................................................. 3-12
System File Update—By Local Import/Export....................................................... 3-13
System File Update—By Backup Media ................................................................ 3-14
Restart ..................................................................................................................... 3-14
Factory Default........................................................................................................ 3-15
Using Port Trunking........................................................................................................... 3-15
The Port Trunking Concept..................................................................................... 3-16
Configuring Port Trunking...................................................................................... 3-16
Configuring SNMP............................................................................................................. 3-18
SNMP Read/Write Settings..................................................................................... 3-19
Trap Settings ........................................................................................................... 3-20
Private MIB information......................................................................................... 3-21
Using Communication Redundancy................................................................................... 3-21
Gigabit Ethernet Redundant Ring Capability (< 50 ms) ......................................... 3-22
The Turbo Ring Concept......................................................................................... 3-22
Configuring “Turbo Ring” and “Turbo Ring V2”................................................... 3-27
The STP/RSTP Concept.......................................................................................... 3-32
Configuring STP/RSTP........................................................................................... 3-37
Using Traffic Prioritization................................................................................................. 3-39
The Traffic Prioritization Concept.......................................................................... 3-39
Configuring Traffic Prioritization........................................................................... 3-41
Using Virtual LAN............................................................................................................. 3-44
The Virtual LAN (VLAN) Concept........................................................................ 3-44
Sample Applications of VLANs using Moxa EDS-510A....................................... 3-47
Configuring Virtual LAN........................................................................................ 3-48
Page 4

Using Multicast Filtering.................................................................................................... 3-51
The Concept of Multicast Filtering......................................................................... 3-51
Configuring IGMP Snooping.................................................................................. 3-54
Add Static Multicast MAC...................................................................................... 3-55
Configuring GMRP................................................................................................. 3-56
GMRP Table ........................................................................................................... 3-56
Using Bandwidth Management.......................................................................................... 3-56
Traffic Rate Limiting Settings................................................................................. 3-57
Using Port Access Control.................................................................................................. 3-57
Configuring Static Port Lock .................................................................................. 3-59
Configuring IEEE 802.1X....................................................................................... 3-59
Using Auto Warning........................................................................................................... 3-62
Configuring Email Warning.................................................................................... 3-63
Event Type.............................................................................................................. 3-63
Email Setup............................................................................................................. 3-65
Configuring Relay Warning.................................................................................... 3-66
Event Setup ............................................................................................................. 3-66
Warning List............................................................................................................ 3-67
Using Line-Swap-Fast-Recovery........................................................................................ 3-68
Configuring Line-Swap Fast Recovery................................................................... 3-68
Using Set Device IP............................................................................................................ 3-68
Configuring Set Device IP ...................................................................................... 3-69
Using Diagnosis.................................................................................................................. 3-70
Mirror Port .............................................................................................................. 3-70
Ping ......................................................................................................................... 3-71
Using Monitor .................................................................................................................... 3-71
Monitor by Switch................................................................................................... 3-71
Monitor by Port....................................................................................................... 3-72
Using the MAC Address Tabl e........................................................................................... 3-72
Using Event Log................................................................................................................. 3-73
Using Syslog....................................................................................................................... 3-74
Using HTTPS/SSL ............................................................................................................. 3-75
Chapter 4 EDS Configurator GUI...............................................................................4-1
Starting EDS Configurator ................................................................................................... 4-2
Broadcast Search.................................................................................................................. 4-2
Search by IP address............................................................................................................. 4-3
Upgrade Firmware................................................................................................................ 4-4
Modify IP Address................................................................................................................ 4-4
Export Configuration............................................................................................................ 4-5
Import Configuration............................................................................................................ 4-6
Unlock Server....................................................................................................................... 4-7
Appendix A MIB Groups...............................................................................................A-1
Appendix B Specifications...........................................................................................B-1
Page 5

1
1
Chapter 1 Introduction
Welcome to the MOXA EDS-510A Series of EtherDevice Switches, the Gigabit Managed
Redundant Ethernet Switches designed specially for connecting Ethernet-enabled devices in
industrial field applications.
The following topics are covered in this chapter:
Overview
Package Checklist
Features
Page 6

EDS-510A Series User’s Manual Introduction
1-2
Overview
As the world’s network and information technology becomes more mature, the trend is to use
Ethernet as the major communications interface in many industrial communications and
automation applications. In fact, a whole new industry has sprung up to provide Ethernet products
that comply with the requirements of demanding industrial applications.
The EDS-510A comes equipped with 3 gigabit Ethernet ports. Two of the ports can be used for
building a redundant Gigabit ring called Gigabit Turbo Ring, which gives system maintainers a
convenient means of setting up a versatile yet stable Gigabit Ethernet network. With Gigabit
Turbo Ring, if any segment of the network gets disconnected, your automation system will be
back to normal in under 300 ms. The third Gigabit Ethernet port can be a uplink port, which can
give 1000 Mbps link capability for transmitting all of the data to the control center. By providing
this third Gigabit Ethernet port, the EDS-510A can help the user build a complete Gigabit Ethernet
backbone network.
Package Checklist
The EDS-510A is shipped with the following items. If any of these items are missing or damaged,
please contact your customer service representative for assistance.
y 1 Moxa EtherDevice Switch EDS-510A
y Hardware Installation Guide
y CD-ROM with User’s Manual and Windows Utility
y Moxa Product Warranty statement
y RJ45 to DB9 console port cable
y Protective caps for unused ports
y DIN-Rail mounting kit (attached to the EDS-510A’s rear panel by default)
Features
Industrial Networking Capability
y 2 gigabit Ethernet ports for Redundant Gigabit Ethernet Ring (recovery time < 20 ms at full
load) and RSTP/STP (IEEE802.1W/D), plus 1 gigabit Ethernet port for uplinking
y IGMP Snooping and GMRP for filtering multicast traffic from industrial Ethernet protocols
y Supports IEEE 802.1Q, tag-based VLAN, GVRP, and port-based VLAN to make network
planning easier
y Supports QoS—IEEE 802.1p/1Q and TOS/DiffServ to increase determinism
y Supports 802.3ad, LACP for optimum bandwidth utilization
y Supports IEEE 802.1X and SSL to enhance network security
y SNMP V1/V2c/V3 for different levels of network management security
y RMON for efficient network monitoring and proactive capability
Designed for Industrial Applications
y Bandwidth management prevents unpredictable network status
y Support ABC-01 (Automatic Backup Configurator) for system configuration backup
y Long-haul transmission distance of 40 km or 80 km (with optional mini-GBIC)
y Redundant, dual 12 to 45 VDC power inputs
y IP30, rugged high-strength metal case
Page 7

EDS-510A Series User’s Manual Introduction
1-3
y DIN-Rail or panel mounting ability
y Bandwidth management to prevent unpredictable network status
y Lock port for allowing access to authorized MAC addresses only
y Port mirroring for online debugging
y Automatic warning by exception through email, relay output
y Digital inputs to integrate a sensor and alarm with an IP network
y Automatic recovery of connected device IP addresses
y Line-swap fast recovery
Useful Utility and Remote Configuration
y Configurable using a Web browser, Telnet/Serial console, or Windows utility
y Send ping commands to identify network segment integrity
Recommended Software and Accessories
y SFP-1GSXLC:
Small form factor pluggable transceiver with 1000BaseSX, LC, 0.5 km, 0 to 60°C
y SFP-1GSXLC-T:
Small form factor pluggable transceiver with 1000BaseSX, LC, 0.5 km, -20 to 75°C
y SFP-1GLXLC:
Small form factor pluggable transceiver with 1000BaseLX, LC, 10 km, 0 to 60°C
y SFP-1GLXLC-T:
Small form factor pluggable transceiver with 1000BaseLX, LC, 10 km, -40 to 75°C
y SFP-1GLHXLC:
Small form factor pluggable transceiver with 1000BaseLHX, LC, 40 km, 0 to 60°C
y SFP-1GLHXLC-T:
Small form factor pluggable transceiver with 1000BaseLHX, LC, 40 km, -40 to 75°C
y SFP-1GZXLC:
Small form factor pluggable transceiver with 1000BaseZX, 80 km, LC, 0 to 60°C
y ABC-01: Automatic Backup Configurator via RS-232 console port, 0 to 60°C
y DR-4524: 45W/2A DIN-Rail 24 VDC power supply with 85 to 264 VAC input
y DR-75-24: 75W/3.2A DIN-Rail 24 VDC power supply with 85 to 264 VAC input
y DR-120-24: 120W/5A DIN-Rail 24 VDC power supply with 88 to 132 VAC/176 to 264 VAC
input by switch
y EDS-SNMP OPC Server Pro: CD with EDS-SNMP OPC Server software and manual
y WK-46: Wall Mounting Kit
Page 8
2
2
Chapter 2 Getting Started
This chapter explains how to access the EDS-510A for the first time. There are three ways to
access the switch: serial console, Telnet console, and web browser. The serial console connection
method, which requires using a short serial cable to connect the EDS-510A to a PC’s COM port,
can be used if you do not know the EDS-510A’s IP address. The Telnet consol e an d web browser
connection methods can be used to access the EDS-510A over an Ethernet LAN, or over the
Internet.
The following topics are covered in this chapter:
RS-232 Console Configuration (115200, None, 8, 1, VT100)
Configuration using a Telnet Console
Configuration using a Web Browser
Disabling Telnet and Browser Access
Page 9

EDS-510A Series User’s Manual Getting Started
2-2
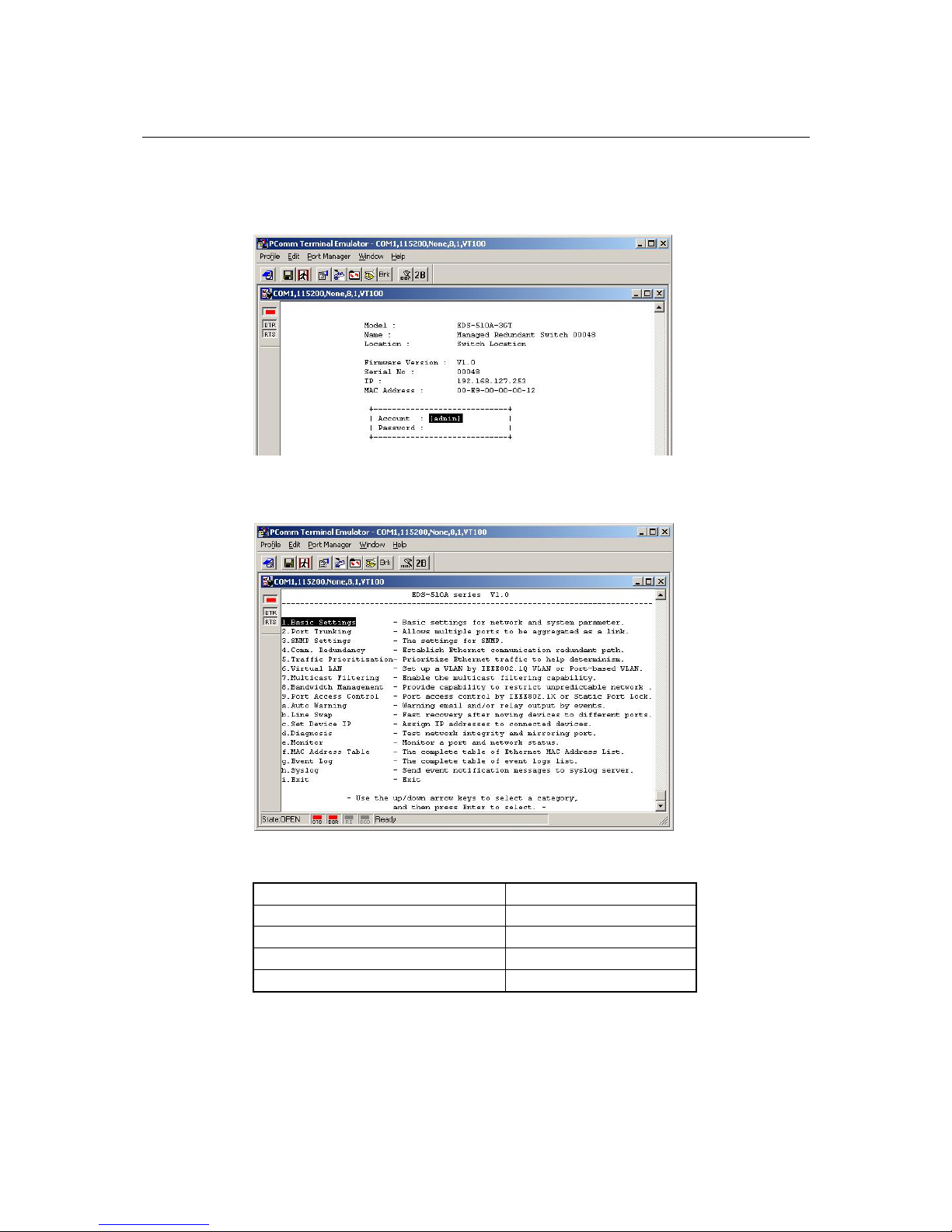
RS-232 Console Configuration (115200, None, 8, 1, VT100)
NOTE
Connection Caution!
1. You cannot connect to the EDS-510A simultaneously by serial console and Telnet.
2. You can connect to the EDS-510A simultaneously by web browser and serial console, or by
web browser and Telnet.
However, we strongly suggest that you do NOT use more than one connection method at the
same time. Following this advice will allow you to maintain better control over the
configuration of your EDS-510A.
NOTE
We recommend using Moxa PComm Terminal Emulator, which can be downloaded free of
charge from Moxa’s website.
Before running PComm Terminal Emulator, use an RJ45 to DB9-F (or RJ45 to DB25-F) cable to
connect the EDS-510A’s RS-232 console port to your PC’s COM port (gen erally CO M1 or COM2,
depending on how your system is set up).
After installing PComm Terminal Emulator, perform the following steps to access the RS-232
console utility.
1. From the Windows desktop, click Start Æ Programs Æ PCommLite2.5 Æ Terminal
Emulator.
2. Select Open under Port Manager to open a new connection.
Page 10

EDS-510A Series User’s Manual Getting Started
2-3
3. The Communication Parameter page of the Property window opens. Select the appropriate
COM port for Console Connection, 115200 for Baud Rate, 8 for Data Bits, None for Parity,
and 1 for Stop Bits.
4. Click the Terminal tab, and select VT100 for Terminal Type. Click OK to continue.
5. Type 1 to select ansi/VT100 terminal type, and then press Enter.
Page 11
EDS-510A Series User’s Manual Getting Started
2-4
6. The Console login screen will appear. Press Enter to open the Account pop-up selector and
then select either admin or user. Use the keyboard’s down arrow to move the cursor to the
Password field, enter the Console Password (this is the same as the Web Browser password;
leave the Password field blank if a console password has not been set), and then press Enter.
7. The EDS-510A’s Main Menu will be displayed. (NOTE: To modify the appearance of the
PComm Terminal Emulator window, select Font… under the Edit menu, and then choose the
desired formatting options.)
8. After entering the Main Menu, use the following keys to move the cursor, and to select
options.
Key Function
Up/Down/Left/Right arrows, or Tab Move the onscreen cursor
Enter Display & select options
Space Toggle options
Esc Previous Menu
Page 12
EDS-510A Series User’s Manual Getting Started
2-5
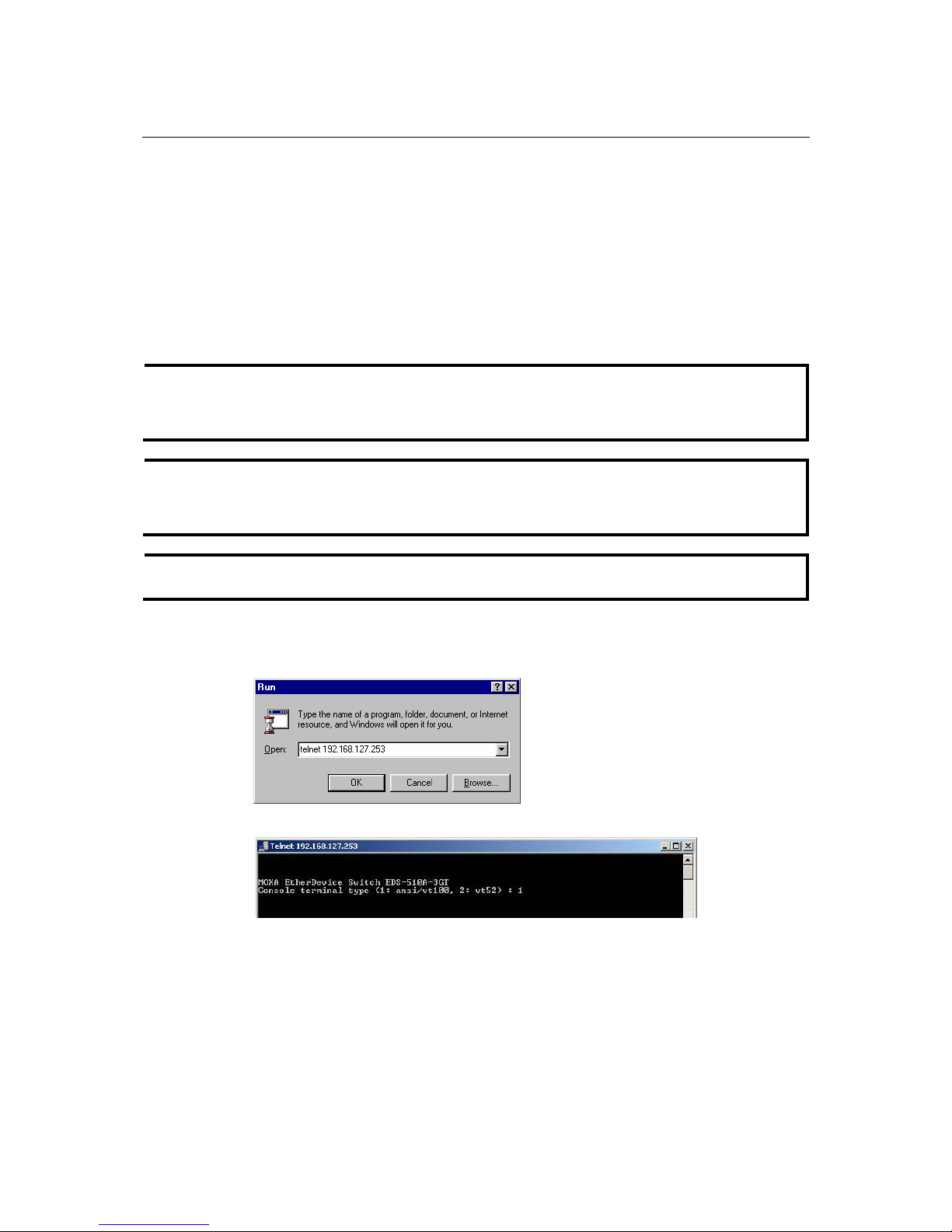
Configuration using a Telnet Console
You may use Telnet to access the EDS-510A’s console utility over a network. To be able to access
the EDS’s functions over the network (by Telnet or web browser) from a PC host that is connected
to the same LAN as the EDS-510A, you need to make sure that the PC host and the EDS-510A are
on the same logical subnet. To do this, check your PC host’s IP address and subnet mask. By
default, the EDS-510A’s IP address is 192.168.127.2 53 and the EDS-510A’s subnet mask is
255.255.255.0 (for a Class C network). If you do not change these values, and your PC host’s
subnet mask is 255.255.0.0, then its IP address must have the form 192.168.xxx.xxx. On the other
hand, if your PC host’s subnet mask is 255.255.255.0, then its IP address must have the form
192.168.127.xxx.
NOTE
To use the EDS-510A’s management and monitoring functions from a PC host connected to the
same LAN as the EDS-510A, you must make sure that the PC host and the EDS-510A are
connected to the same logical subnet.
NOTE
Before accessing the console utility via Telnet, first connect one of the EDS-510A’s RJ45
Ethernet ports to your Ethernet LAN, or directly to your PC’s Ethernet card (NIC). You can use
either a straight-through or cross-over Ethernet cable.
NOTE
The EDS-510A’s default IP address is 192.168.127.253.
Perform the following steps to access the console utility via Telnet.
1. Click Start Æ Run, and then telnet to the EDS-510A’s IP address from the Windows Run
window. (You may also issue the telnet command from the MS-DOS prompt.)
2. Type 1 to choose ansi/vt100, and then press Enter.
Page 13
EDS-510A Series User’s Manual Getting Started
2-6
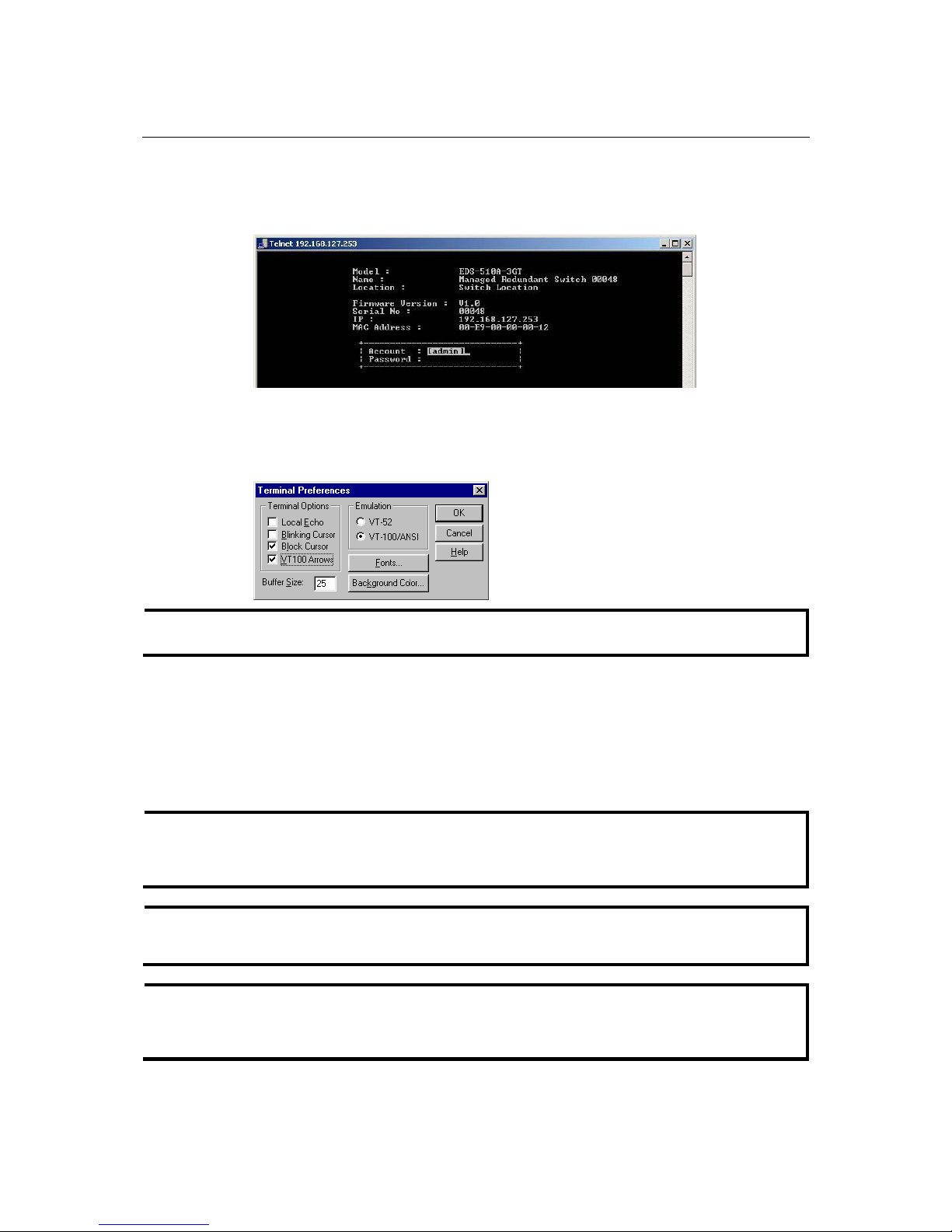
3. The Console login screen will appear. Press Enter to open the Account pop-up selector and
then select either admin or user. Use the keyboard’s down arrow to move the cursor to the
Password field, enter the Console Password (this is the same as the Web Browser password;
leave the Password field blank if a console password has not been set), and then press Enter.
4. When the Main Menu of the EDS-510A’s console utility opens, click Terminal Æ
preferences… from the menu at the top of the window.
5. When the Terminal Preferences window opens, make sure that the VT100 Arrows option is
selected.
NOTE
The Telnet Console looks and operates in precisely the same manner as the RS-232 Console.
Configuration using a Web Browser
The EDS-510A’s web browser interface provides a convenient way to modify the switch’s
configuration and access the built-in monitoring and network administration functions. The
recommended web browser is Microsoft Internet Explorer 5.5 or 6.0 with JVM (Java Virtual
Machine) installed.
NOTE
To use the EDS-510A’s management and monitoring functions from a PC host connected to the
same LAN as the EDS-510A, you must make sure that the PC host and the EDS-510A are on the
same logical subnet.
NOTE
If the EDS-510A is configured for other VLAN settings, you must make sure your PC host is on
the management VLAN.
NOTE
Before accessing the EDS-510A’s web browser interface, first connect one of the switch’s RJ45
Ethernet ports to your Ethernet LAN, or connect directly to your PC’s Ethernet card (NIC). You
can establish a connection using either a straight-through or cross-over Ethernet cable.
Page 14
EDS-510A Series User’s Manual Getting Started
2-7
NOTE
The EDS-510A’s default IP is 192.168.127.253.
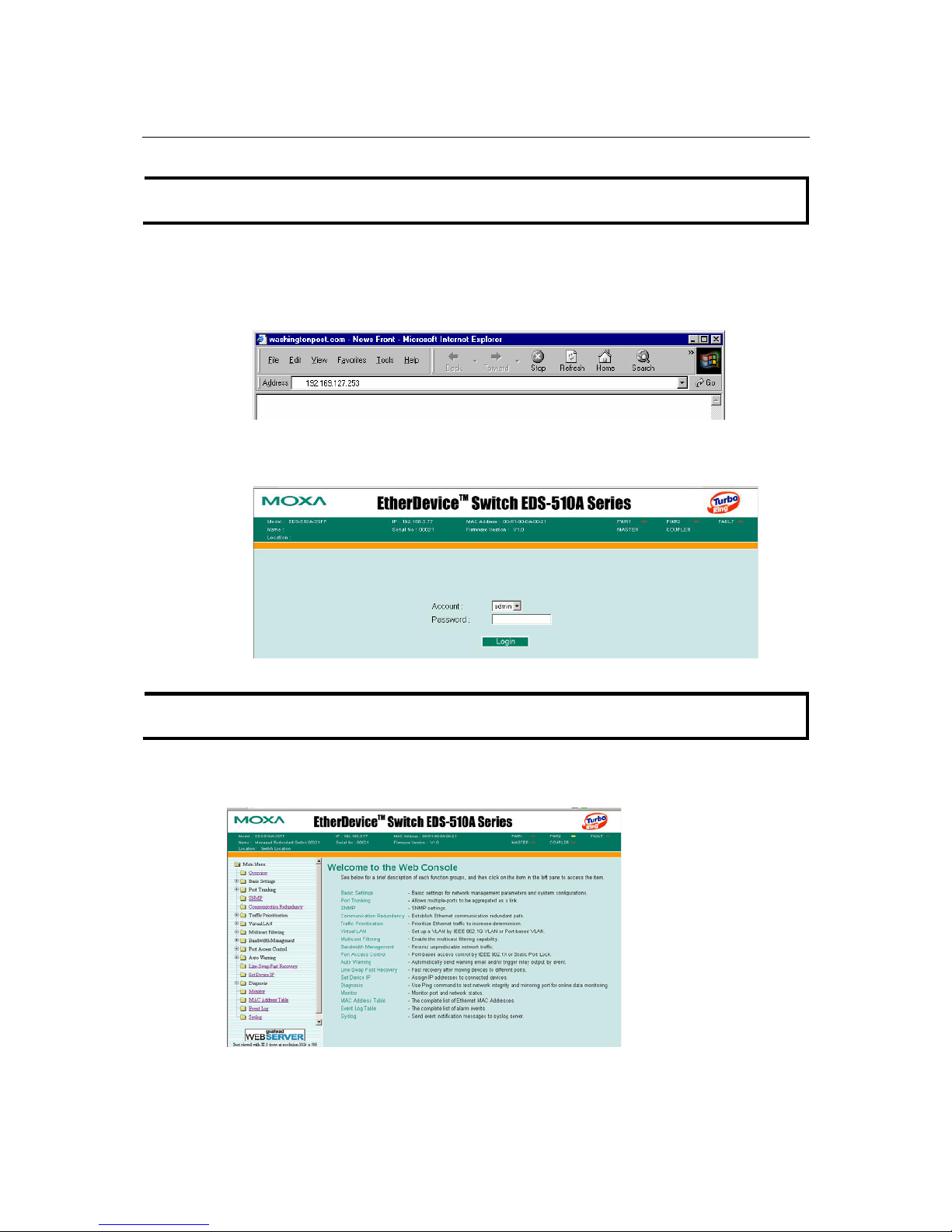
Perform the following steps to access the EDS-510A’s web browser interface.
1. Open Internet Explorer and type EDS-510A’s IP address in the Address field. Press Enter to
establish the connection.
2. The web login page will open. Select the login account (Admin or User) and enter the
Password (this is the same as the Console password), and then click Login to continue. Leave
the Password field blank if a password has not been set.
NOTE
By default, the EDS-510A’s password is not set (i.e., is blank).
You may need to wait a few moments for the web page to be downloaded to your computer. Use
the menu tree on the left side of the window to open the function pages to access each of the
switch’s functions.
Page 15
EDS-510A Series User’s Manual Getting Started
2-8
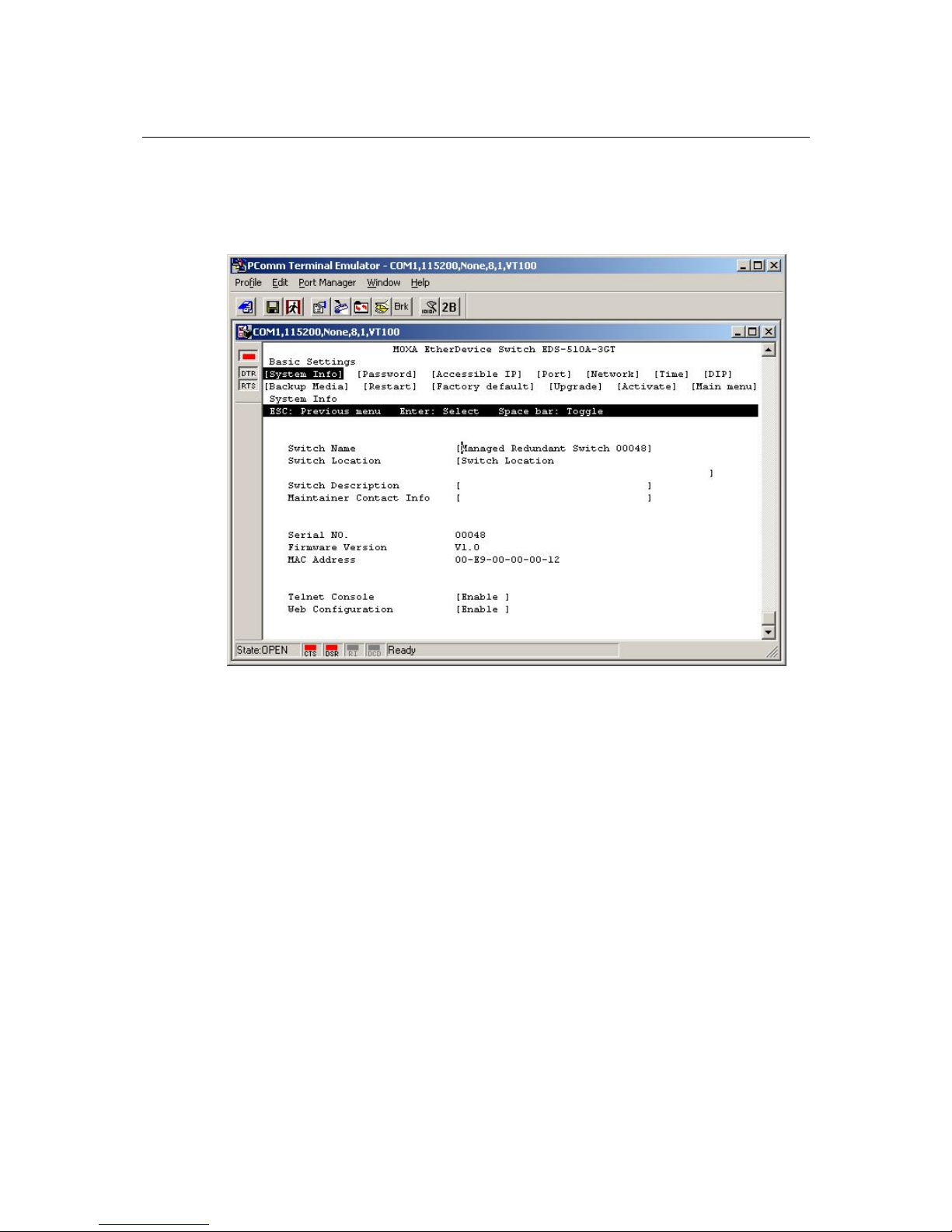
Disabling Telnet and Browser Access
If you are connecting the EDS-510A to a public networ k, but do not intend to use its management
functions over the network, we suggest using the RS-232 console’s Basic Settings Æ System Info
page to disable both Telnet Console and Web Configuration, as shown in the following figure.
Page 16

3
3
Chapter 3 Featured Functions
In this chapter, we explain how to access the EDS-510A’s configuration options, perform
monitoring, and use administration functions. There are three ways to access these functions:
RS-232 console, Telnet console, and web browser. The serial console connection method, which
requires using a short serial cable to connect the EDS-510A to a PC’s COM port, can be used if
you do not know the EDS-510A’s IP address. The Telnet console and web browser connection
methods can be used to access the EDS-510A over an Ethernet LAN, or over the Internet.
The web console is the most user-friendly way to configure the EDS-510A. In this chapter, we use
the web console interface to introduce the functions. There are only a few differences between the
web console, serial console, and Telnet console.
The following topics are covered in this chapter:
Configuring Basic Settings
Using Port Trunking
Configuring SNMP
Using Communication Redundancy
Using Traffic Prioritization
Using Virtual LAN
Using Multicast Filtering
Using Bandwidth Management
Using Port Access Control
Using Auto Warning
Using Line-Swap-Fast-Recovery
Using Set Device IP
Using Diagnosis
Using Monitor
Using the MAC Address Table
Using Event Log
Using Syslog
Using HTTPS/SSL
Page 17
EDS-510A Series User’s Manual Featured Functions
3-2
Configuring Basic Settings
The Basic Settings group includes the most commonly used settings required by administrators to
maintain and control EDS-510A.
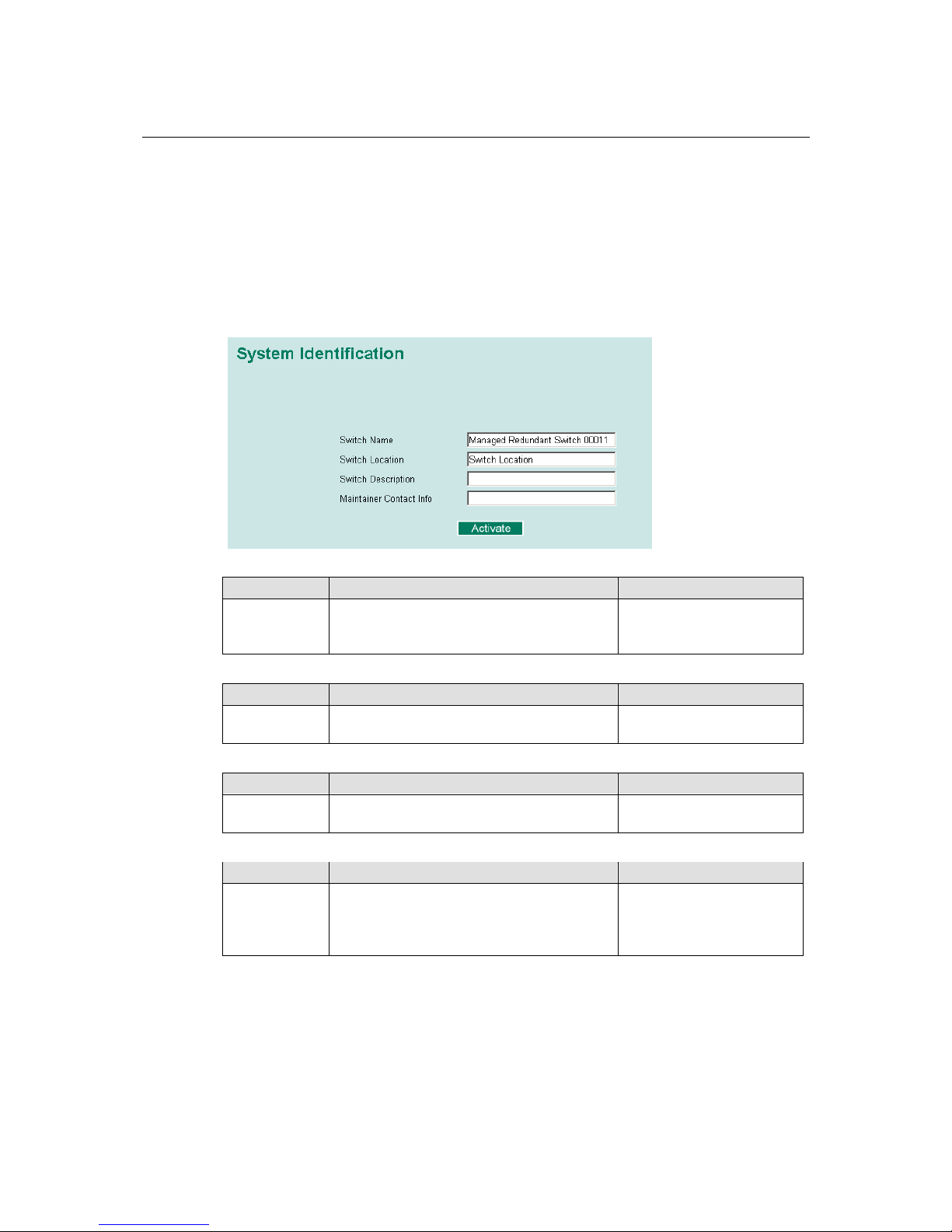
System Identification
The system identification items are displayed at the top of the web page, and will be included in
alarm emails. Entering the system identification information makes it easier to identify the
different switches connected to your network.
Switch Name
Setting Description Factory Default
Max. 30
Characters
This option is useful for specifying the role or
application of different EDS-510A units.
E.g., Factory Switch 1.
Managed Redundant Switch
[Serial No. of this switch]
Switch Location
Setting Description Factory Default
Max. 80
Characters
To specify the location of different EDS-510A
units. E.g., production line 1.
Switch Location
Switch Description
Setting Description Factory Default
Max. 30
Characters
Use this to enter a more detailed description of
the EDS-510A unit.
None
Maintainer Contact Info
Setting Description Factory Default
Max. 30
Characters
To provide information about whom to contact
in order to resolve problems. Use this to enter
contact information of the person responsible
for maintaining this EDS-510A.
None
Page 18
EDS-510A Series User’s Manual Featured Functions
3-3
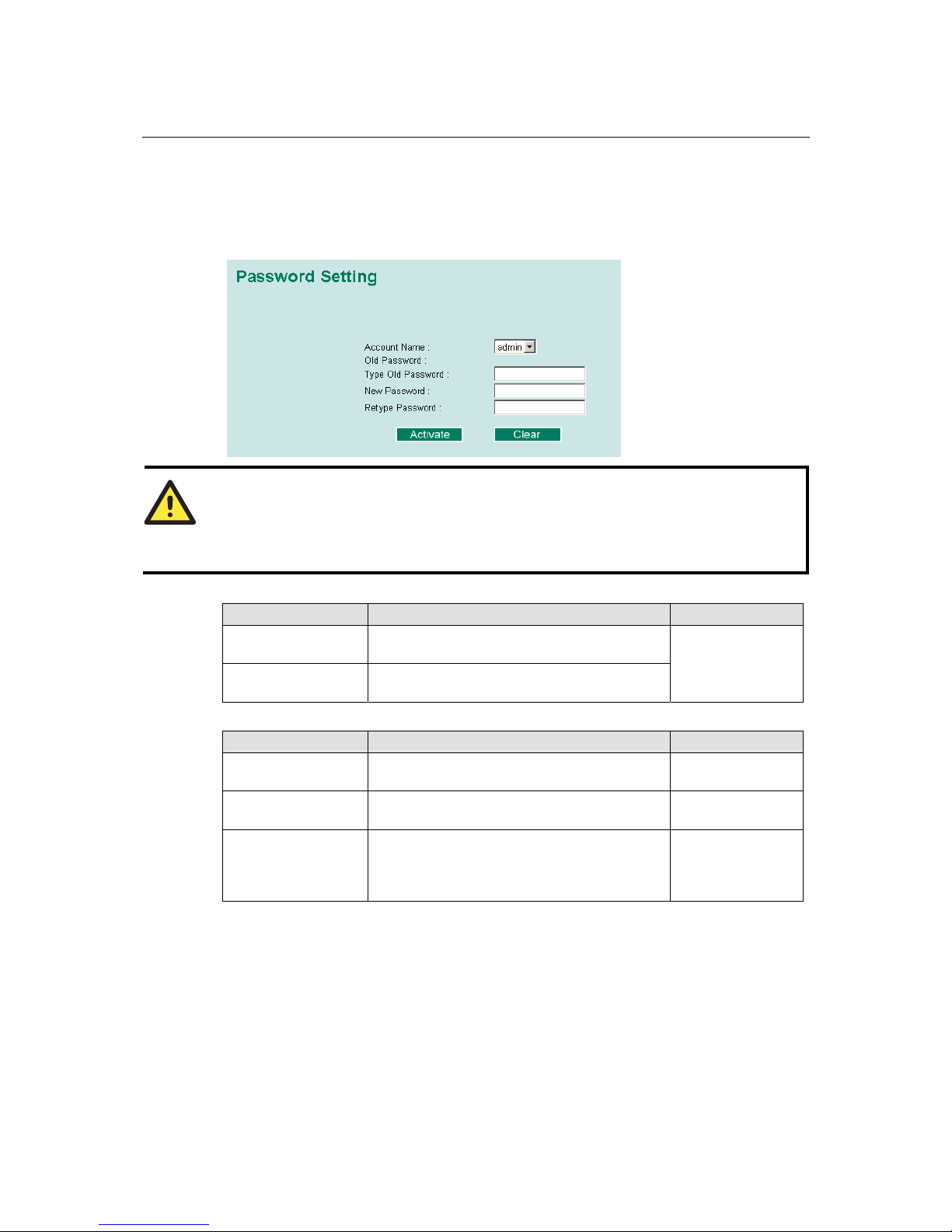
Password
The EDS-510A provides two levels of access privilege: admin privilege gives read/write access to
all EDS-510A configuration parameters, and user privilege provides read access only. You will be
able to view the configuration, but will not be able to make modifications.
ATTENTION
The EDS-510A’s default Password is not set (i.e., is blank). If a Password is already set, then
you will be required to type the Password when logging into the RS-232 console, Telnet console,
or web browser interface.
Account
Setting Description Factory Default
admin “admin” privilege allows the user to modify all
EDS-510A configurations.
user “user” privilege only allows viewing EDS-510A
configurations.
admin
Password
Setting Description Factory Default
Old Password
(Max. 16 Characters)
Type current password when changing the
password
None
New Password
(Max. 16 Characters)
Type new password when changing the password None
Retype Password
(Max. 16 Characters)
If you type a new password in the Password field,
you will be required to retype the password in the
Retype new password field before updat ing the
new password.
None
Page 19

EDS-510A Series User’s Manual Featured Functions
3-4
Accessible IP
The EDS-510A uses an IP address-based filtering method to control access to the EDS-510A
units.
Accessible IP Settings allows you to add or remove “Legal” remote host IP addresses to prevent
unauthorized access. Access to the EDS-510A is controlled by IP address. If a host’s IP address is
in the accessible IP table, then the host will be allowed access to the EDS-510A. You can allow
one of the following cases by setting this parameter:
y Only one host with the specified IP address can access the EDS-510A
E.g., enter “192.168.1.1/255.255.255.255” to allow access to just the IP address 192.168.1.1.
y Any host on a specific subnetwork can access the EDS-510A
E.g., enter “192.168.1.0/255.255.255.0” to allow access to all IPs on the subnet defined by
this IP address/subnet mask combination.
y Any host can access the EDS-510A
Disable this function by deselecting the Enable the accessible IP list option.
The following table shows additional configuration examples:
Allowable Hosts Input format
Any host Disable
192.168.1.120 192.168.1.120 / 255.255.255.255
192.168.1.1 to 192.168.1.254 192.168.1.0 / 255.255.255.0
192.168.0.1 to 192.168.255.254 192.168.0.0 / 255.255.0.0
192.168.1.1 to 192.168.1.126 192.168.1.0 / 255.255.255.128
192.168.1.129 to 192.168.1.254 192.168.1.128 / 255.255.255.128
Page 20
EDS-510A Series User’s Manual Featured Functions
3-5
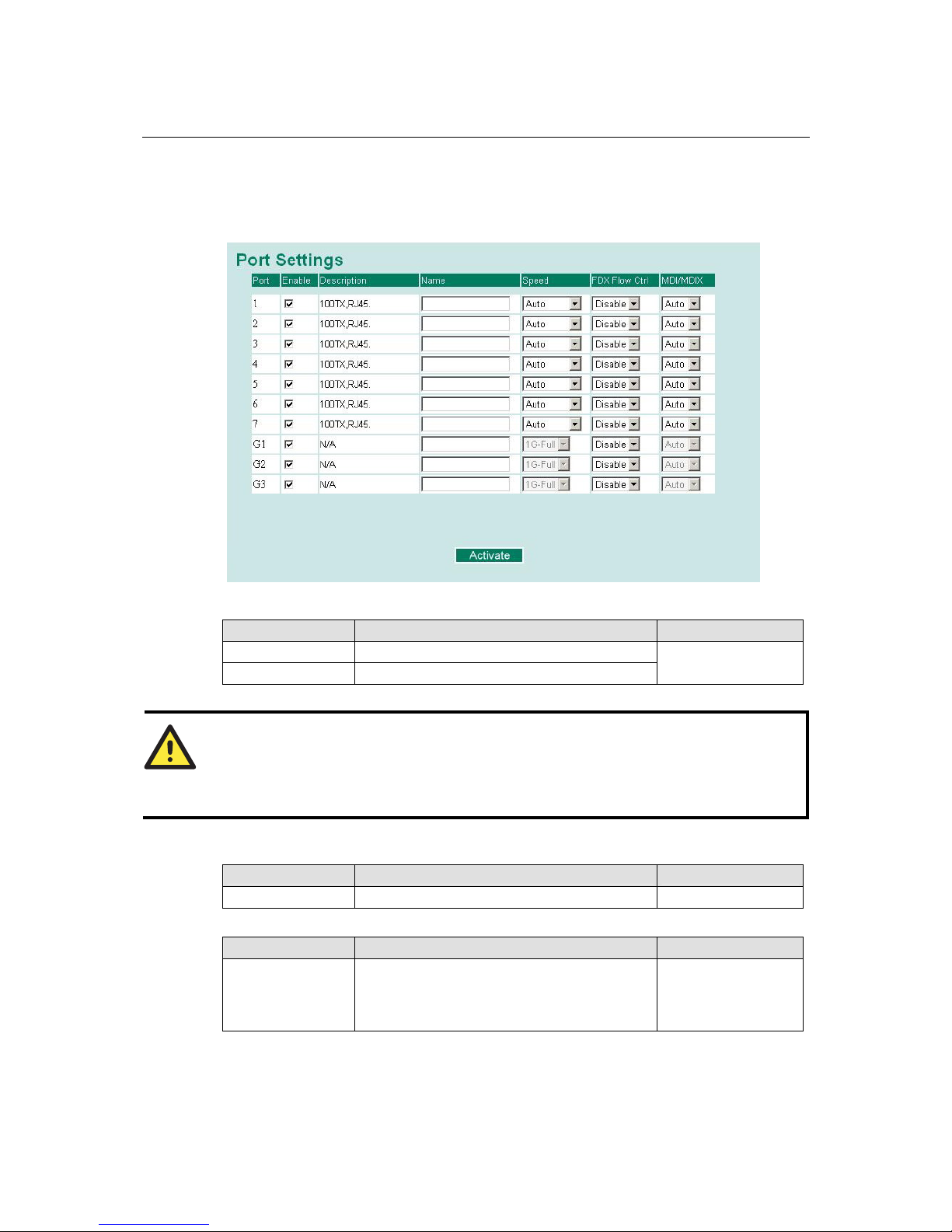
Port
Port settings are included to give the user control over Port Access, Port Transmission Speed,
Flow Control, and Port Type (MDI or MDIX). An explanation of each configuration item follows:
Enable
Setting Description Factory Defaul t
checked Allows data transmission through the port.
unchecked Immediately shuts off port access.
enabled
ATTENTION
If a connected device or sub-network is wreaking havoc on the rest of the network, the Disable
option under Advanced Settings/Port gives the administrator a quick way to shut off access
through this port immediately.
Description
Setting Description Factory Defaul t
Media type Displays the media type for each module’s port N/A
Name
Setting Description Factory Defaul t
Max. 63 Characters Specify an alias for each port, and assist the
administrator in remembering important
information about the port.
E.g., PLC 1
None
Page 21
EDS-510A Series User’s Manual Featured Functions
3-6
Speed
Setting Description Factory Defaul t
Auto Allows the port to use the IEEE 802.3u protocol
to negotiate with connected devices. The port and
connected devices will determine the best speed
for that connection.
100M-Full
100M-Half
10M-Full
10M-Half
Choose one of these fixed speed options if the
opposing Ethernet device has trouble
auto-negotiating line speed.
Auto
FDX Flow Ctrl
This setting enables or disables the flow control capability of this port when the “port
transmission speed” setting is in “auto” mode. The final result will be determined by the “auto”
process between the EDS-510A and connected devices.
Setting Description Factory Defaul t
Enable Enables flow control for this port when in
auto-negotiate mode.
Disable Disables flow control for this port when in
auto-negotiate mode.
Disable
MDI/MDIX
Setting Description Factory Defaul t
Auto Allows the port to auto detect the port type of the
opposing Ethernet device and change the port
type accordingly.
MDI
MDIX
Choose the MDI or MDIX option if the opposing
Ethernet device has trouble auto-negotiating port
type.
Auto
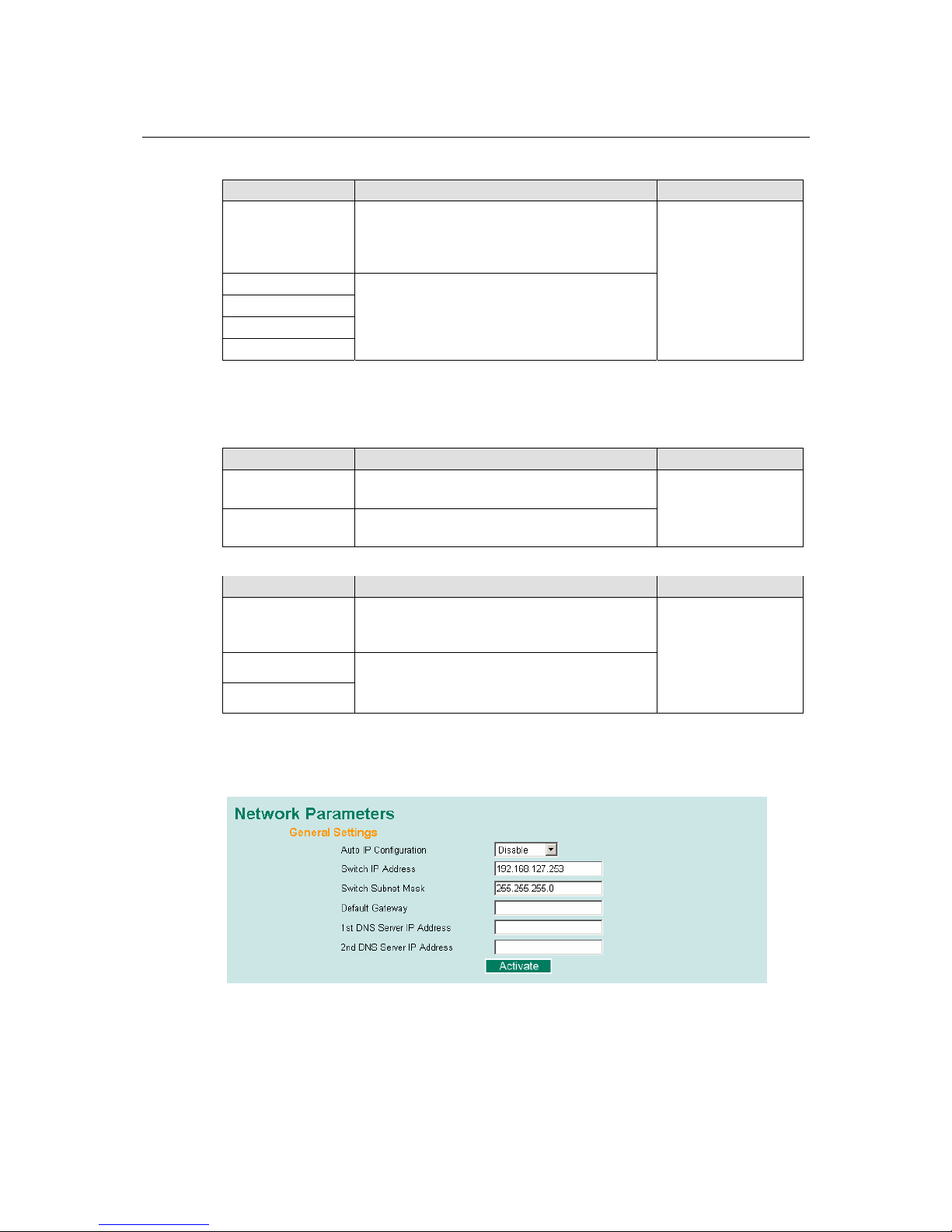
Network
The Network configuration allows users to m odi fy the usu al TCP/ IP network parameters. An
explanation of each configuration item follows.
Page 22
EDS-510A Series User’s Manual Featured Functions
3-7
Auto IP Configuration
Setting Description Factory Default
Disable Set up the EDS-510A’s IP address manually.
By DHCP The EDS-510A’s IP address will be assigned
automatically by the network’s DHCP server.
By BOOTP The EDS-510A’s IP address will be assigned
automatically by the network’s BOOTP server.
Disable
Switch IP Address
Setting Description Factory Default
IP Address of the
EDS-510A
Identifies the EDS-510A on a TCP/IP network. 192.168.127.253
Switch Subnet Mask
Setting Description Factory Default
Subnet mask of the
EDS-510A
Identifies the type of network to which the
EDS-510A is connected (e.g., 255.255.0.0 for a
Class B network, or 255.255.255.0 for a Class
C network).
255.255.255.0
Default Gateway
Setting Description Factory Default
Default Gateway of the
EDS-510A
The IP address of the router that connects the
LAN to an outside network.
None
DNS IP Address
Setting Description Factory Default
1st DNS Server’s
IP Address
The IP address of the DNS Server used by your
network. After entering the DNS Server’s IP
address, you can input the EDS-510A’s URL
(e.g.,
www.eds.company.com) in your
browser’s address field, instead of entering the
IP address.
None
2nd DNS Server’s
IP Address
The IP address of the DNS Server used by your
network. The EDS-510A will try to locate the
2nd DNS Server if the 1st DNS Server fails to
connect.
None
Page 23
EDS-510A Series User’s Manual Featured Functions
3-8
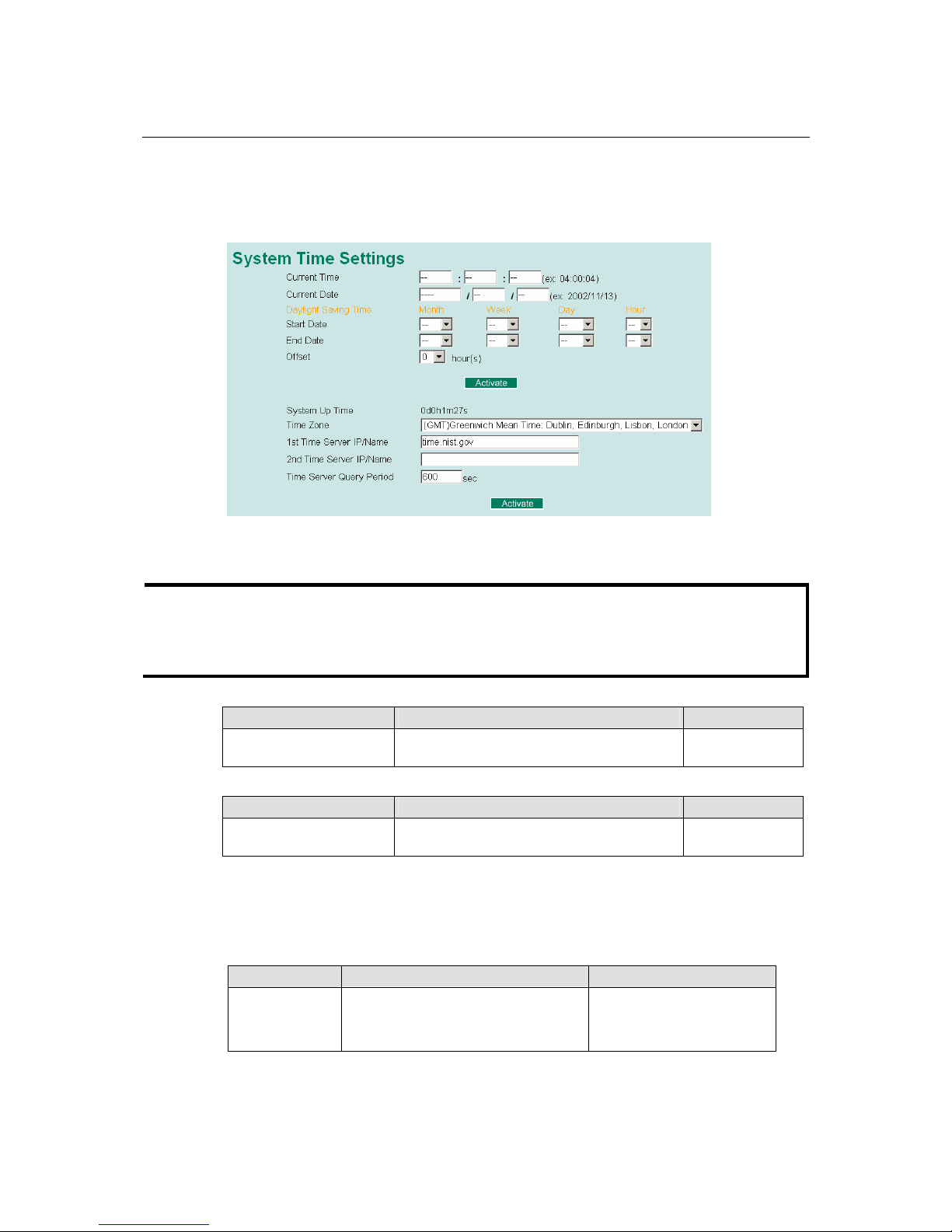
Time
The Time configuration page lets users set the time, date, and other settings. An explanation of
each setting is given below the figure.
The EDS-510A has a time calibration function based on information from an NTP server or user
specified Time and Date information. Functions such as Auto warning “Email” can add real-time
information to the message.
NOTE
The EDS-510A does not have a real time clock. The user must update the Current Time and
Current Date to set the initial time for the EDS-510A after each reboot, especially when the
network does not have an Internet connection for an NTP server or there is no NTP server on the
LAN.
Current Time
Setting Description Factory Default
User adjustable time. The time parameter allows configuration of the
local time in local 24-hour format.
None (hh:mm:ss)
Current Date
Setting Description Factory Default
User adjustable date. The date parameter allows configuration of the
local date in yyyy/mm/dd format.
None
(yyyy/mm/dd)
Daylight Saving Time
Daylight saving time (also know as DST or summer time) involves advancing clocks (usually 1
hour) during the summer time to provide an extra hour of daylight in the afternoon.
Start Date
Setting Description Factory Def au l t
User adjustable
date.
The Start Date parameter allows users
to enter the date that daylight saving
time begins.
None
Page 24

EDS-510A Series User’s Manual Featured Functions
3-9
End Date
Setting Description Factory Def au l t
User adjustable
date.
TheEnd Date parameter allows users to
enter the date that daylight saving time
ends.
None
Offset
Setting Description Factory Def au l t
User adjustable
hour.
The offset parameter indicates how
many hours forward the clock should
be advanced.
None
System Up Time
Indicates the EDS-510A’s up time from the last cold start. The unit is seconds.
Time Zone
Setting Description Factory Default
User selectable time zone The time zone setting allows conversion from
GMT (Greenwich Mean Time) to local time.
GMT (Greenwich
Mean Time)
NOTE
Changing the time zone will automatically correct the current time. You should configure the
time zone before setting the time.
Time Server IP/Name
Setting Description Factory Default
1st Time Server IP/Name IP or Domain address (e.g., 192.168.1.1 or
time.stdtime.gov.tw or time.nist.gov).
2nd Time Server IP/Name
The EDS-510A will try to locate the 2nd NTP
Server if the 1st NTP Server fails to connect.
None
Time Server Query Period
Setting Description Factory Default
Query Period This parameter determines how frequently the
time is updated from the NTP server.
600 seconds
Turbo Ring DIP Switch
The Turbo Ring DIP Switch page allows users to disable the four DIP switches located on the
EDS’s outer casing. When enabled, the DIP switches can be used to configure basic settings for
either the “Turbo Ring” protocol or “Turbo Ring V2” protocol. A complete description of the
settings is given below.
Page 25
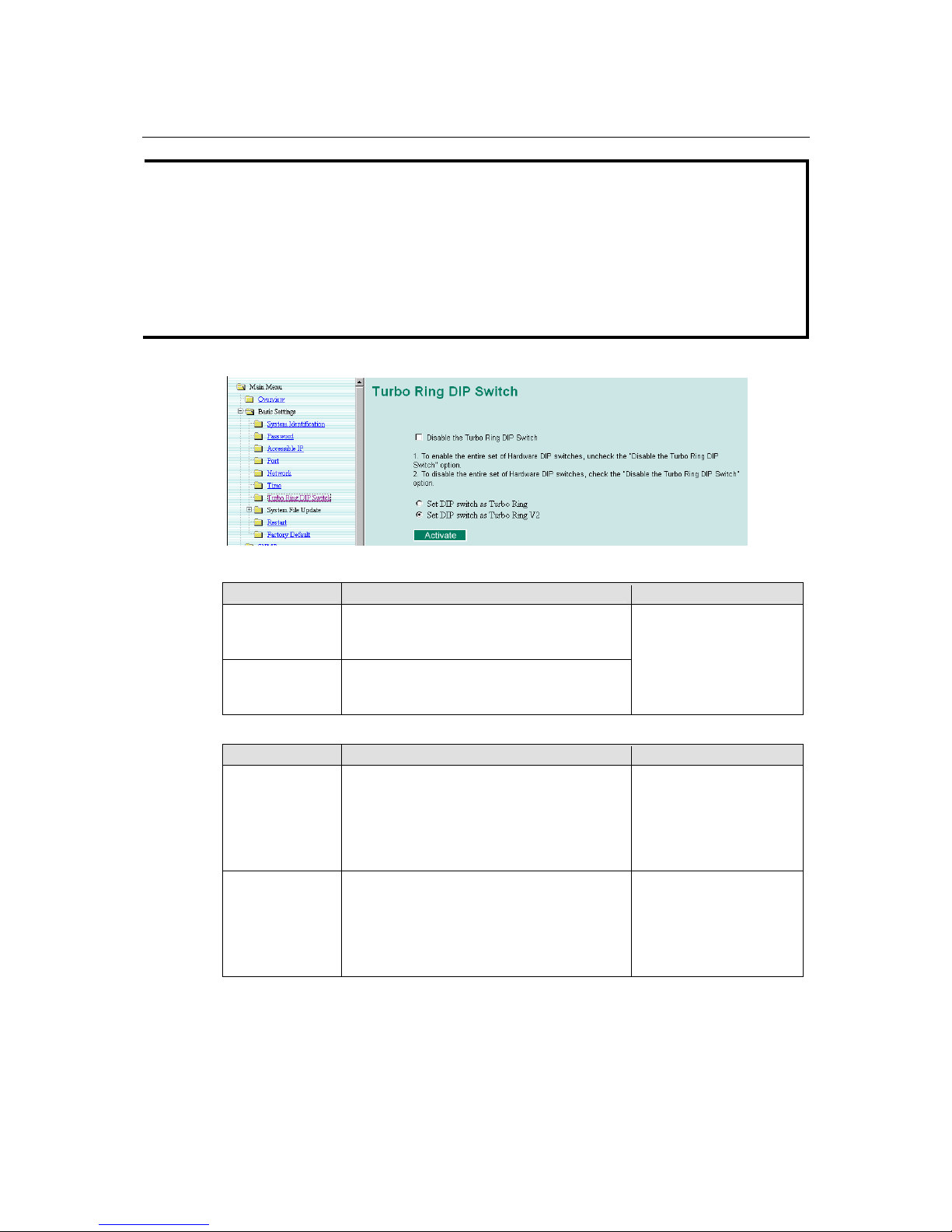
EDS-510A Series User’s Manual Featured Functions
3-10
NOTE
The proprietary “Turbo Ring” protocol (recovery time < 300 ms) was developed by MOXA in
2003 to provide better network reliability and faster recovery time for redundant ring topologies.
The “Turbo Ring V2” protocol (recovery time < 20 ms), which was released in 2007, supports
additional redundant ring architectures.
In this manual, we use the terminology “Turbo Ring” ring and “Turbo Ring V2” ring to
differentiate between rings configured for one or the other of these protocols.
For a detailed description of “Turbo Ring” and “Turbo Ring V2” please refer to the Using
Communication Redundancy section later in this chapter.
How to Enable or Disable the Turbo Ring DIP Switches
Disable the Turbo Ring DIP Switch
Setting Description Factory Default
Enable the Turbo
Ring DIP
Switches
The four DIP switches are enabled when the
“Disable the Turbo Ring DIP Switch” box is
not checked.
Disable the Turbo
Ring DIP
Switches
The four DIP switches are disabled when the
“Disable the Turbo Ring DIP Switch” box is
checked.
Not checked (i.e., the
Turbo Ring DIP Switches
are enabled by default)
Set DIP switch as Turbo Ring / Set DIP switch as Turbo Ring V2
Setting Description Factory Default
Set DIP switch as
Turbo Ring
Select this option to enable the Turbo Ring DIP
switches to configure the EDS for a “Turbo
Ring” ring.
This is the default if you do
NOT reset the switch to
factory default settings
(provided you upgraded the
firmware for Turbo Ring
V2).
Set DIP switch as
Turbo Ring V2
Select this option to enable the Turbo Ring DIP
switches to configure the EDS for a “Turbo
Ring V2” ring.
This is the default if you
DO reset the switch to
factory default settings
(provided you upgraded the
firmware for Turbo Ring
V2).
Page 26
EDS-510A Series User’s Manual Featured Functions
3-11
NOTE
If you upgrade the firmware of your EDS from Turbo Ring to Turbo Ring V2, but do no t re set the
switch to factory defaults, the DIP switches will be set to configure the EDS for a “Turbo Ring”
ring. If you reset the switch to factory defaults, the DIP switches will be set to configure the EDS
for a “Turbo Ring V2” ring.
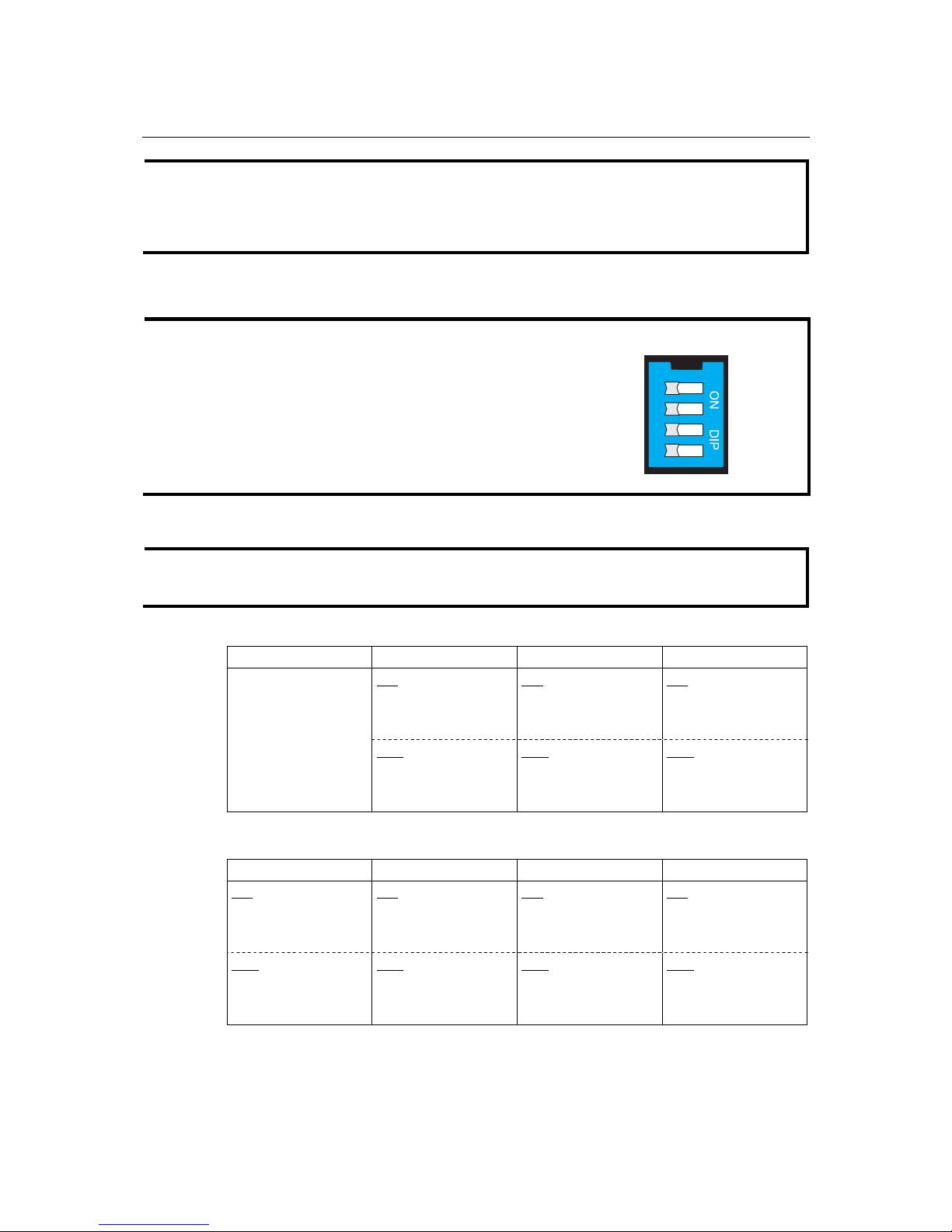
How to Configure the Turbo Ring DIP Switches
The Turbo Ring DIP Switches are set to the OFF position at the factory.
NOTE
The four DIP Switches are used to configure both the “Turbo Ring”
and “Turbo Ring V2” protocols, depending on whi c h protocol is
active. To select which protocol the EDS will use, start the user
interface software, and then use the left menu to navigate to the
Communication Redundancy page. To use one of the Turbo Ring
protocols for the EDS, select either “Turbo Ring” or “Turbo Ring
V2” in the Redundancy Protocol drop-down box.See the
Configuring “Turbo Ring” and “Turbo Ring V2” section in this
chapter for details.
12
------
MASTER
COUPLER
TURBO
RING
34
The following tables show how to use the DIP switches to configure the EDS for “Turbo Ring”
or “Turbo Ring V2”.
NOTE
DIP switch 4 must be set to the ON position to enable DIP switches 1, 2, and 3. If DIP switch 4 is
set to the “OFF” position, then DIP switches 1, 2, and 3 will all be disabled.
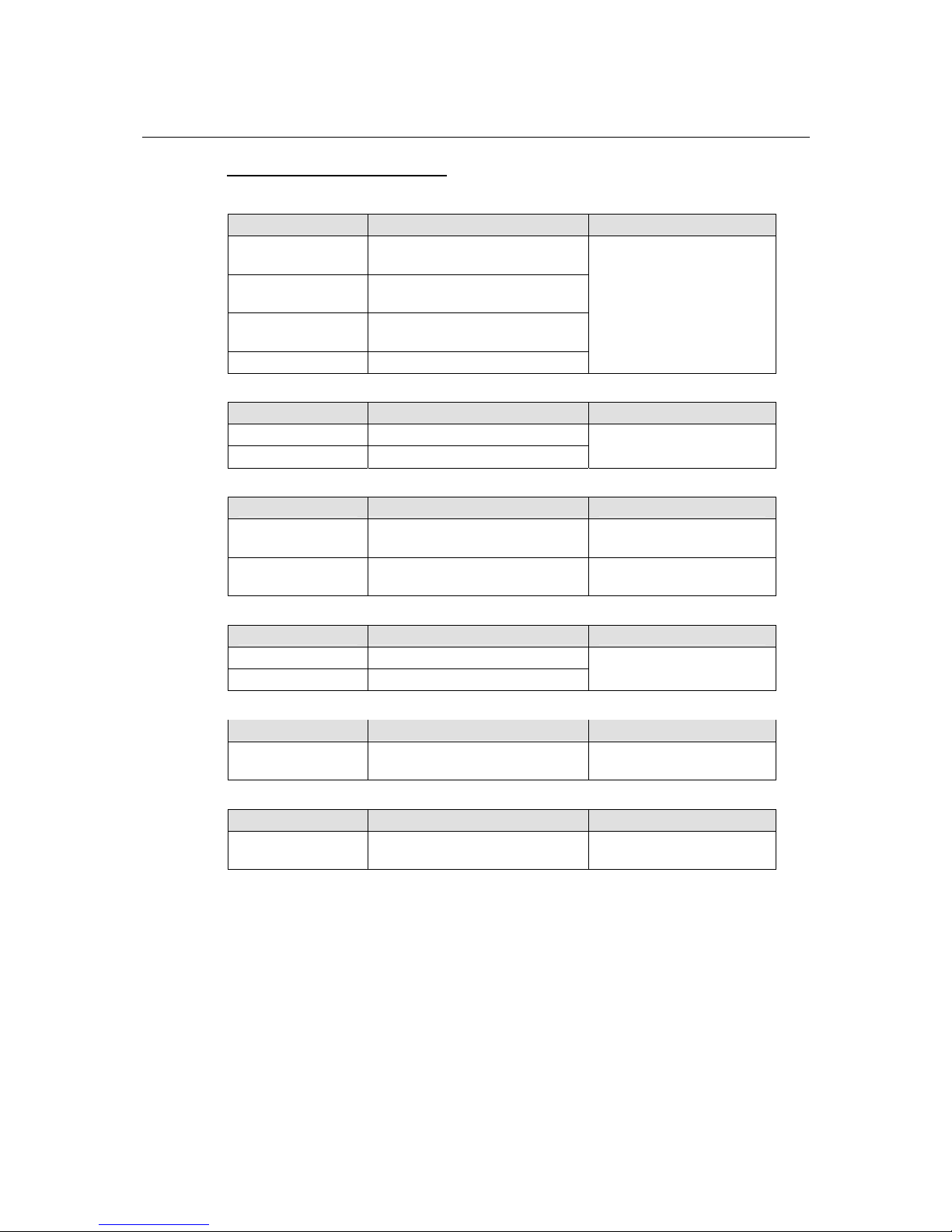
“T urbo Ring” DIP Switch Settings
DIP 1 DIP 2 DIP 3 DIP 4
ON: Enables this EDS
as the Ring Master.
ON: Enables the
default “Ring
Coupling” ports.
ON
: Activates DIP
switches 1, 2, 3 to
configure “Turbo
Ring” settings.
Reserved for future
use.
OFF
: This EDS will
not be the Ring
Master.
OFF
: Do not use this
EDS as the ring
coupler.
OFF
: DIP switches 1,
2, 3 will be disabled.
“T urbo Ring V2” DIP Switch Settings
DIP 1 DIP 2 DIP 3 DIP 4
ON: Enables the
default “Ring
Coupling (backup)”
port.
ON
: Enables this EDS
as the Ring Master.
ON: Enables the
default “Ring
Coupling” port.
ON
: Activates DIP
switches 1, 2, 3 to
configure “Turbo Ring
V2” settings.
OFF: Enables the
default “Ring
Coupling (primary)”
port.
OFF
: This EDS will
not be the Ring
Master.
OFF
: Do not use this
EDS as a ring coupler.
OFF: DIP switches 1,
2, 3 will be disabled.
Page 27
EDS-510A Series User’s Manual Featured Functions
3-12
NOTE
The DIP 1 setting will only be active if DIP 3 is in the ON position. If you set DIP 3 to OFF, then
the default Ring Coupling port will NOT be enabled, even if DIP 1 is ON.
Protocol Default Turbo Ring Ports Default Ring Coupling Port(s)
Tur bo Ring
ports G2 and G3 port 7
Tur bo Ring V2
ports G2 and G3 port G1
NOTE
The Turbo Ring Ports and Coupling Ports will be added automatically to all VLANs if you set
DIP Switch 4 to the “ON” position.
NOTE
If you do not enable any of the EDS-510A switches to be the Ring Master, the Turbo Ring
protocol will automatically choose the EDS-510A with the smallest MAC address range to be the
Ring Master. If you accidentally enable more than one EDS-510A to be the Ring Master, these
EDS-510A switches will auto-negotiate to determine which one will be the Ring Master.
NOTE
If you use the browser interface to enable the DIP switches (by un-checking the “Disable the
Turbo Ring DIP switch” checkbox), and then flip DIP switch 4 from ON to OFF, the Ring Ports
and Coupling Ports that were added to all VLANs will be restored to their previous software
settings. (For details, please refer to the “Using Virtual LANs” section of this manual).
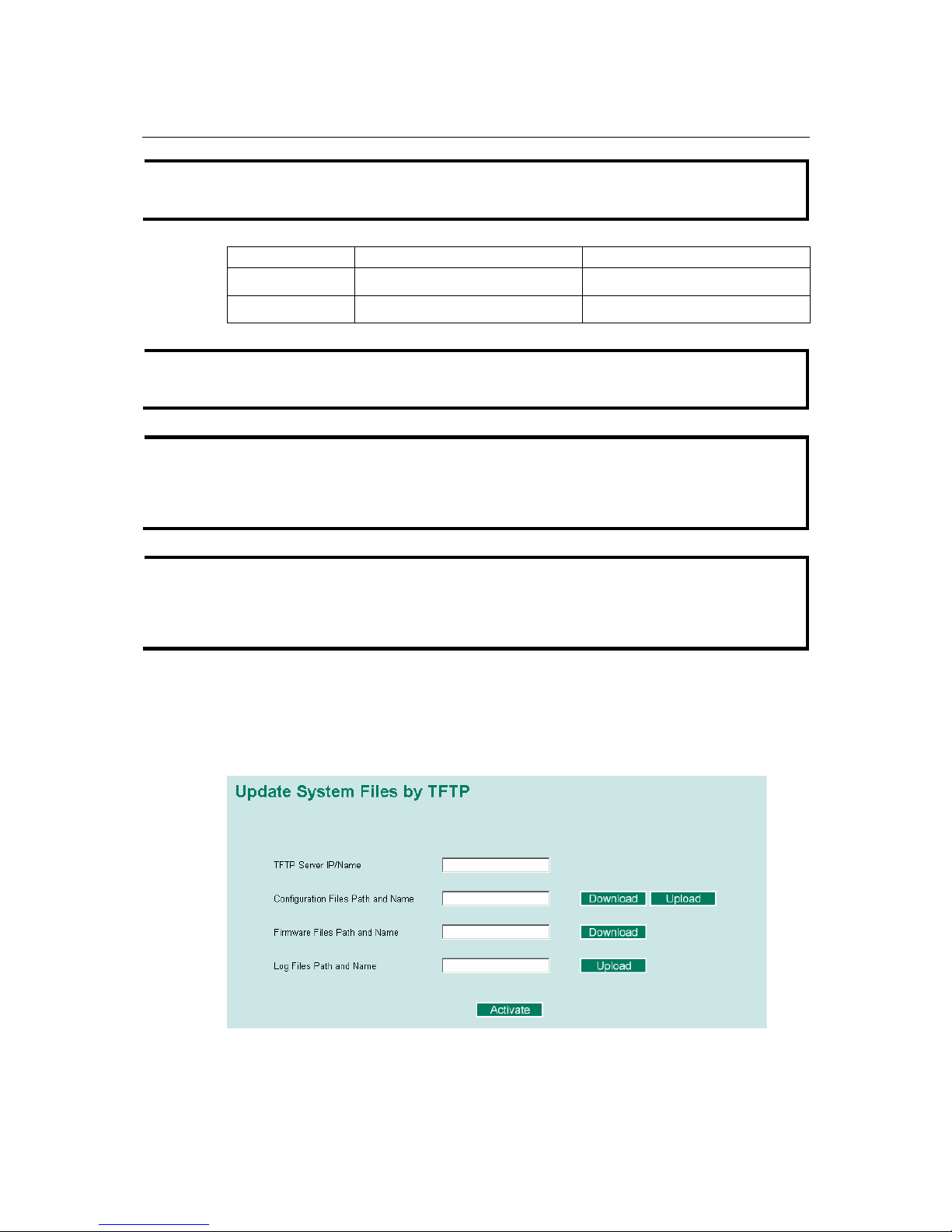
System File Update—By Remote TFTP
The EDS-510A supports saving your configuration file to a remote TFTP server or local host to
allow other EDS-510A switches to use the same configuration at a later time, or saving the Log
file for future reference. Loading pre-saved firmware or a configuration file from the TFTP server
or local host is also supported for easy upgrading or config urati o n of the EDS -5 1 0A.
Page 28
EDS-510A Series User’s Manual Featured Functions
3-13
TFTP Server IP/Name
Setting Description Factory Default
IP Address of TFTP
Server
The IP or name of the remote TFTP server. Must be
set up before downloading or uploading fil es.
None
Configuration Files Path and Name
Setting Description Factory Default
Max. 40 Characters The path and file name of the EDS-510A’s
configuration file in the TFTP server.
None
Firmware Files Path and Name
Setting Description Factory Default
Max. 40 Characters The path and file name of the EDS-510A’s
firmware file.
None
Log Files Path and Name
Setting Description Factory Default
Max. 40 Characters The path and file name of the EDS-510A’s log file None
After setting up the desired path and file name, click Activate to save the setting, and then click
Download to download the prepared file from the remote TFTP server, or click Upload to upload
the desired file to the remote TFTP server.
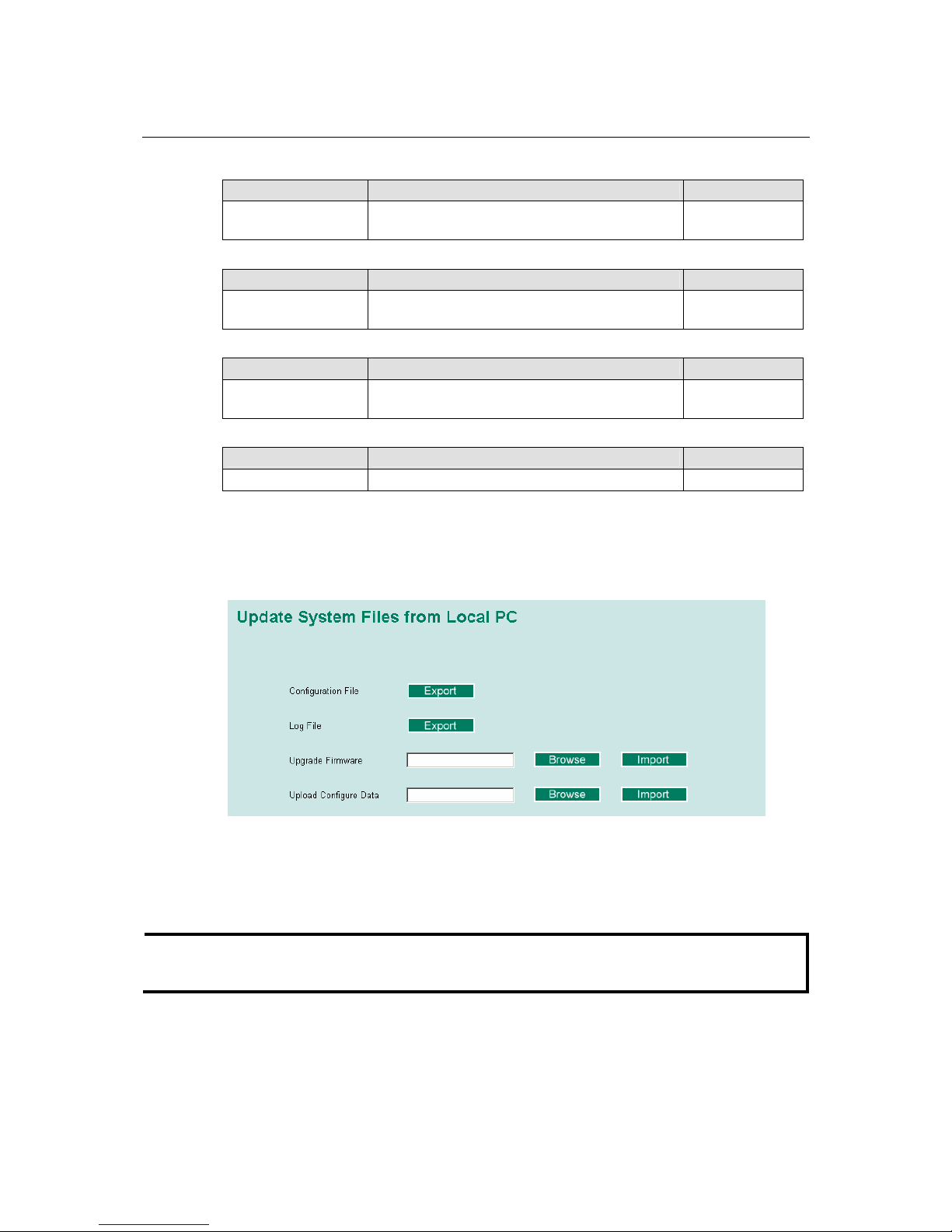
System File Update—By Local Import/Export
Configuration File
To export the configuration file of this EDS-510A, click Export to save it to the local host.
Log File
To export the Log file of this EDS-510A, click Export and save it to the local host.
NOTE
Some operating systems will open the configuration file and log file directly in the web page. In
such cases, right click Export to save as a file.
Page 29
EDS-510A Series User’s Manual Featured Functions
3-14
Upgrade Firmware
To import the firmware file of this EDS-510A, click Browse to select the firmware file already
saved on your computer. The upgrade procedure will proceed automatically after clicking Import.
Upload Configuration Data
To import the configuration file of this EDS-510A, click Browse to select the configuration file
already saved on your computer. The upgrade procedure will proceed automatically after clicking
Import.
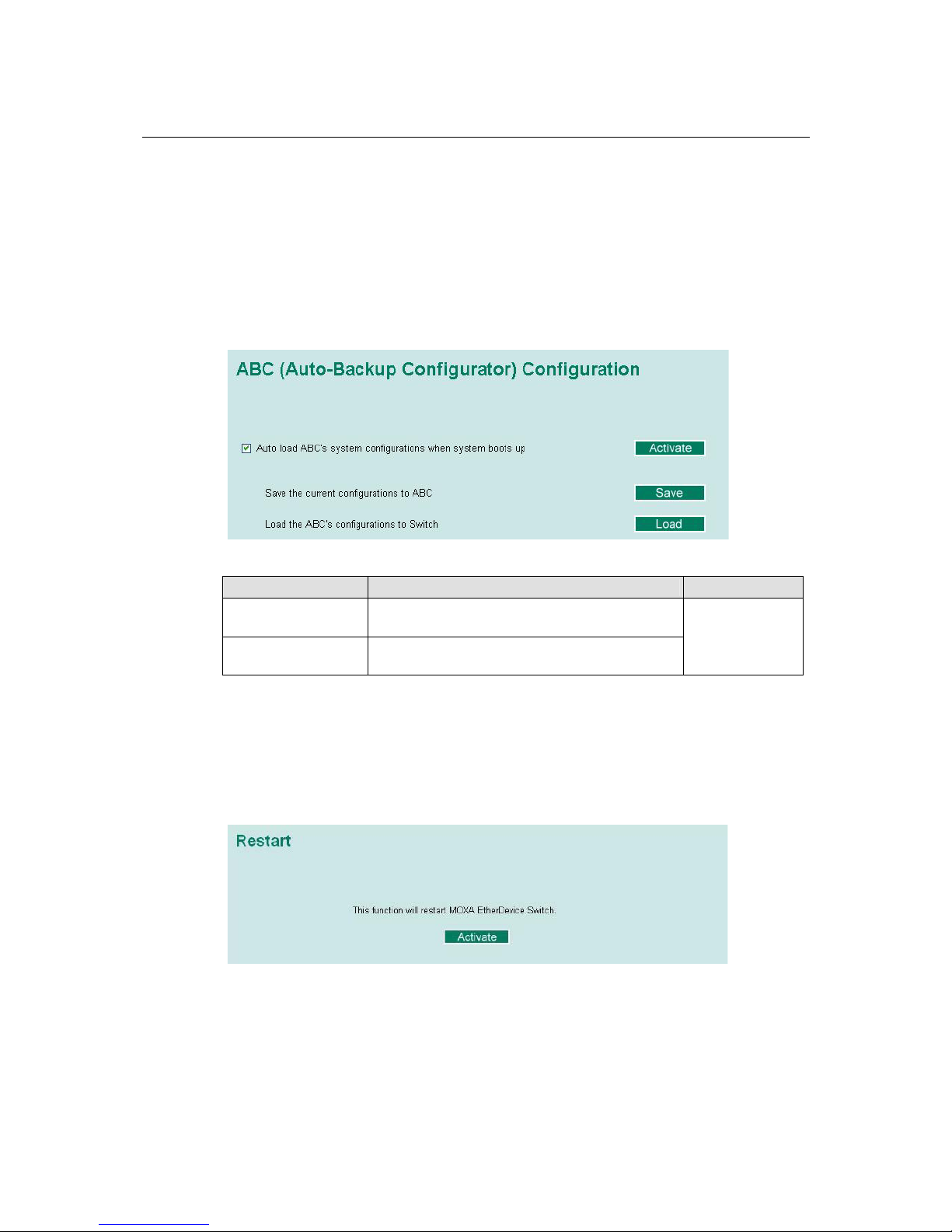
System File Update—By Backup Media
Auto load system configurations when system boots up
Setting Description Factory Default
Enable
Enables Auto load system configurations when
system boots up
Disable
Disables Auto load system configurations when
system boots up
Enable
Save the current configurations to ABC
To export the current configuration file of the EDS-510A, click on Save to save it to the ABC.
Load the ABC’s configurations to the Switch
To import the configuration file of the EDS-510A, click on Load to load it to the Switch.
Restart
This function is used to restart the MOXA EtherDevice Switch.
Page 30
EDS-510A Series User’s Manual Featured Functions
3-15
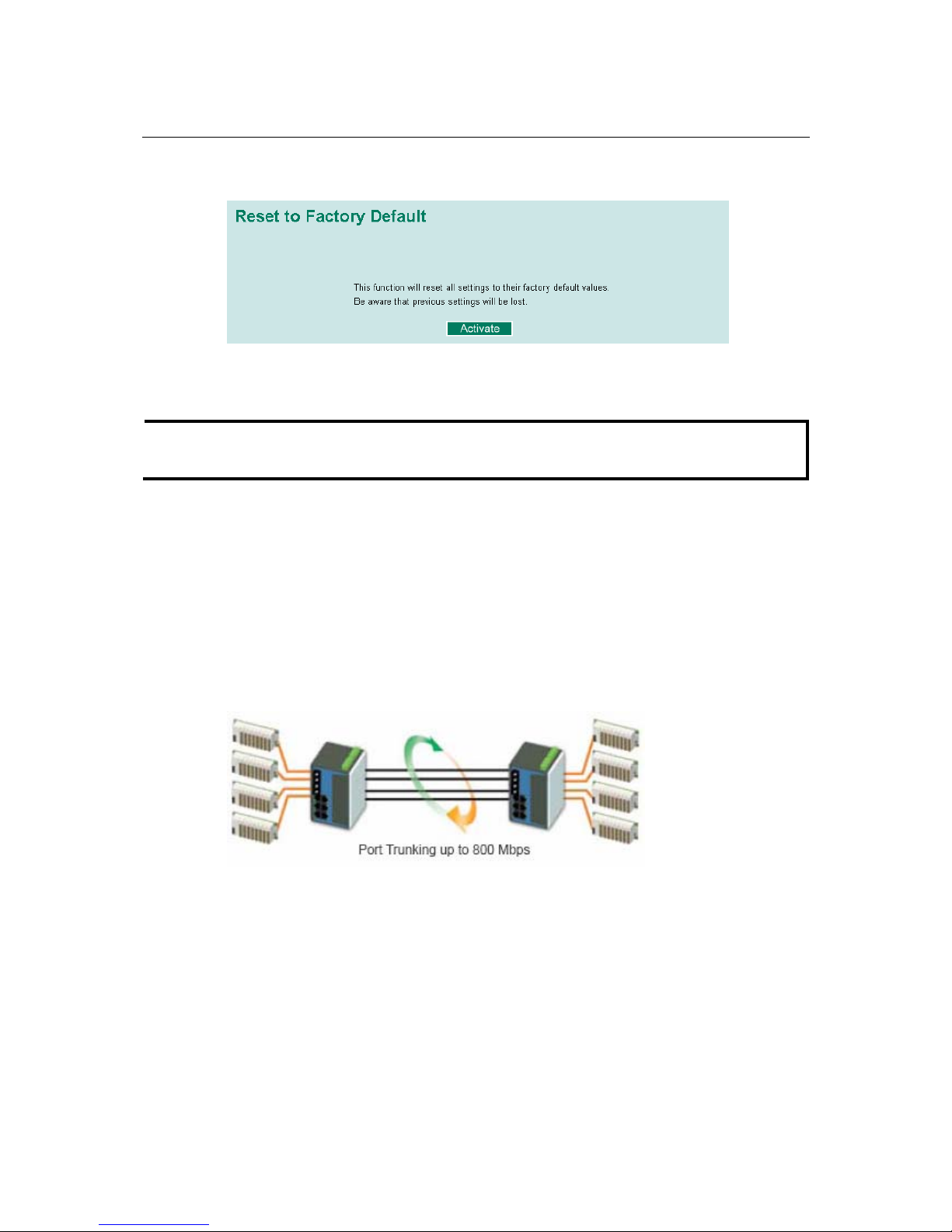
Factory Default
The Factory Default function is included to give users a quick way of restoring EDS-510A’s
configuration settings to their factory default values. This function is available in the Console
utility (serial or Telnet), and Web Browser interface.
NOTE
After activating the Factory Default function, you will need to use the default network settin gs to
re-establish a web-browser or Telnet connection with your EDS-510A.
Using Port Trunking
Link Aggregation allows one or more links to be aggregated together to form a Link Aggregation
Group. A MAC client can treat Link Aggregation Groups as if they were a single link.
The EDS-510A’s Port Trunking feature allows devices to communicate by aggregating up to 4
trunk groups, with a maximum of 8 ports for each group (due to the interface limitation, there is a
limit of 3 gigabit ports or 7 10/100 Mbps ports for each Trk trunk group). If one of the 8 ports fails,
the other seven ports will provide back up and share the traffic automatically.
Port trunking can be used to combine up to 8 ports between two EDS-510A switches. If all ports
on both switch units are configured as 100BaseTX and they are operating in full duplex, the
potential bandwidth of the connection will be 800 Mbps.
Page 31

EDS-510A Series User’s Manual Featured Functions
3-16
The Port Trunking Concept
Moxa has developed a proprietary Port Trunking protocol that provides the following benefits:
y Gives you more flexibility in setting up your network connections, since the bandwidth of a
link can be doubled, tripled, or quadr u pl e d.
y Provides redundancy—if one link is broken, the remaining trunked ports share the traffic
within this trunk group.
y Load sharing—MAC Client traffic may be distributed across multiple links.
y To avoid broadcast storms or loops in your network while configuring a trunk, first disable or
disconnect all ports that you want to add to the trunk or remove from the trunk. After you
finish configuring the trunk, enable or re-connect the ports.
If all ports on both switch units are configured as 100BaseTX and they are operating in full duplex,
the potential bandwidth of the connection will be up to 800 Mbps on the EDS-510A. This means
that users can connect one EDS to another EDS by Port Trunking to double, triple, or quadruple
the bandwidth of the connection.
When configuring Port Trunking, note that Each EDS-510A can set a maximum of 4 Port
Trunking groups (designated Trk1, Trk2, Trk3, Trk4).
When you activate Port Trunking settings, some advanced functions that you set up with the
original ports will either be set to factory default values, or disabled:
y Communication Redundancy will be set to the factory default
y Traffic Prioritization will be set to the factory default
y Port-based VLAN or 802.1Q VLAN will be set to the factory default
y Multicast Filtering will be set to the factory default
y Rate Limiting will be set to the factory default
y Port Access Control will be set to the factory default
y Email and Relay Warning will be set to the factory default
y Set Device IP will be set to the factory default
y Mirror Port will be set to the factory default
You can setup these features again on your Trunking Port.
Configuring Port Trunking
The Port Trunking Settings page is used to assign ports to a Trunk Group.
Page 32

EDS-510A Series User’s Manual Featured Functions
3-17
Step 1: Select Trk1, Trk2, Trk3, or Trk4 from the Trunk Group drop-down box.
Step 2: Select Static, or LACP from the Trunk Type drop-down box.
Step 3: Under Member Ports and Available Ports, select the specific ports.
Step 4: Use the Up / Down buttons to add/remove designated ports to/from a trunk group.
Trunk Group (Maximum of 3 trunk groups)
Setting Description Factory Default
Trk1, Trk2, Trk3, Trk4 Display or designate the Trunk Type and Member
Ports for Trunk Group 1, 2, 3, 4.
Trk1
Trunk Type
Setting Description Factory Default
Static Designated Moxa proprietary trunking protocol Static
LACP
Designated LACP (IEEE 802.3ad, Link
Aggregation Control Protocol)
Static
Available Ports/Member Port
Setting Description Factory Default
Member/Available
Ports
Use Up/Down buttons to add/remove specific ports
from available ports to/from trunk group.
N/A
Check box Check to designate which ports to add or remove. Unchecked
Port Port number N/A
Port description Displays the media type for each module’s port N/A
Name Max. 63 Characters N/A
Speed
Indicates the transmission speed (100M-Full,
100M-Half, 10M-Full, or 10M-Half )
N/A
FDX Flow Control
Indicates if the FDX flow control of this port is
“Enabled” or “Disabled.”
N/A
Up
Add designated ports into trunk group from
available ports.
N/A
Down
Remove designated ports from trunk group t o
available port.
N/A
Page 33

EDS-510A Series User’s Manual Featured Functions
3-18
Trunk Table
Setting Description
Trunk Group Displays the Trunk Type and Trunk Group.
Member Port Display which member ports belong to the trunk group.
Status Success means por t trunking is working properly.
Fail means port trunking is not working properly.
Standby means port trunking is working as a standby port. When there
are more than eight ports trunked as a trunking group, the 9
th
port will
be the standby port.
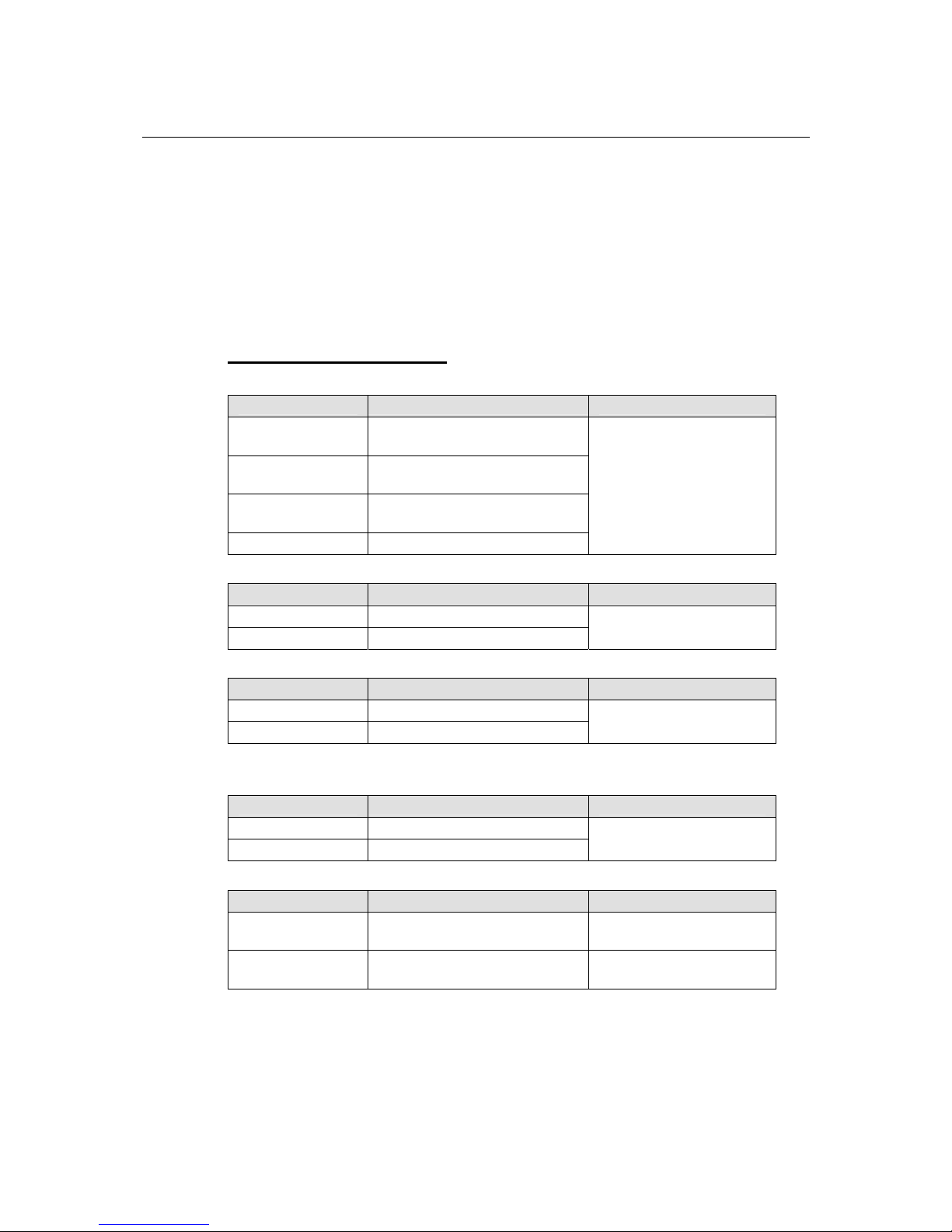
Configuring SNMP
The EDS-510A supports SNMP V1/V2c/V3. SNMP V1, and SNMP V2c use a community string
match for authentication, which means that SNMP servers access all objects with read-only or
read/write permissions using the community string public/private (default value). SNMP V3,
which requires you to select an authentication level of MD5 or SHA, is the most secure protocol.
You can also enable data encryption to enhance data security.
SNMP security modes and security levels supported by the EDS-510A are shown in the following
table. Select the security mode and level that will be used to communicate between the SNMP
agent and manager.
Protocol
Version
UI Setting
Authentication
Type
Data
Encryption
Method
V1, V2c
Read
Community
Community
string
No
Use a community string match
for authentication
SNMP V1,
V2c
V1, V2c
Write/Read
Community
Community
string
No
Use a community string match
for authentication
No-Auth No No
Use account with admin or user
to access objects
MD5 or SHA
Authentication
based on MD5
or SHA
No
Provides authentication based on
HMAC-MD5, or HMAC-SHA
algorithms. 8-character
passwords are the minimum
requirement for authentication.
SNMP V3
MD5 or SHA
Authentication
based on MD5
or SHA
Data encryption
key
Provides authentication based on
HMAC-MD5 or HMAC-SHA
algorithms, and data encryption
key. 8-character passwords and a
data encryption key are the
minimum requirements for
authentication and encryption.
These parameters are configured on the SNMP page. A more detailed explanation of each
parameter follows.
Page 34

EDS-510A Series User’s Manual Featured Functions
3-19
SNMP Read/Write Settings
SNMP Versions
Setting Description Factory Default
V1, V2c, V3, or
V1, V2c, or
V3 only
Select the SNMP protocol version used to
manage the switch.
V1, V2c
V1, V2c Read Community
Setting Description Factory Default
V1, V2c Read
Community
Use a community string match with a
maximum of 30 characters for
authentication. The SNMP agent accesses
all objects with read-only permissions
using the community string public.
public
V1, V2c Write/Read Community
Setting Description Factory Default
V1, V2c
Read/Write
Community
Uses a community string match with a
maximum of 30 characters for
authentication. The SNMP servers access
all objects with read/write permissions
using the community string private.
private
For SNMP V3, there are two levels of privileges for different accounts to access the EDS-510A.
Admin privilege allows access, and authorization to read and write the MIB file. User privilege
only allows reading the MIB file, but does not have authorization to write.
Admin Auth. Type (for SNMP V1, V2c, V3, and V3 only)
Setting Description Factory Default
No-Auth
Use admin. account to access objects.
No authentication
No
MD5-Auth
Provide authentication based on the
HMAC-MD5 algorithms. 8-character
passwords are the minimum requirement
for authentication.
No
SHA-Auth
Provide authentication based on the
HMAC-SHA algorithms. 8-character
passwords are the minimum requirement
for authentication.
No
Admin Data Encryption Key (for SNMP V1, V2c, V3, and V3 only)
Setting Description Factory Default
Enable
8-character data encryption key is the
minimum requirement for data encryption
(maximum of 30 characters)
No
Disable No data encryption No
Page 35

EDS-510A Series User’s Manual Featured Functions
3-20
User Auth. Type (for SNMP V1, V2c, V3 and V3 only)
Setting Description Factory Default
No-Auth
Use admin account or user account to
access objects. No authentication.
No
MD5-Auth
Provides authentication based on the
HMAC-MD5 algorithms. 8-character
passwords are the minimum requirement
for authentication.
No
SHA-Auth
Provides authentication based on the
HMAC-SHA algorithms. 8-character
passwords are the minimum requirement
for authentication.
No
User Data Encryption Key (for SNMP V1, V2c, V3 and V3 only)
Setting Description Factory Default
Enable
8-character data encryption key is the
minimum requirement for data encryption
(maximum of 30 characters)
No
Disable No data encryption No
Trap Settings
1st Trap Server IP/Name
Setting Description Factory Default
IP or Name
Enter the IP address or name of the 1
st
Trap Server used by your network.
None
1st Trap Community
Setting Description Factory Default
character string
Use a community string match for
authentication (maximum of 30
characters).
public
2nd Trap Server IP/Name
Setting Description Factory Default
IP or Name
Enter the IP address or name of the 2
nd
Trap Server used by your network.
None
2nd Trap Community
Setting Description Factory Default
character string
Use a community string match for
authentication (maximum of 30
characters).
public
Page 36

EDS-510A Series User’s Manual Featured Functions
3-21
Private MIB information
Switch Object ID
Setting Description Factory Default
8691.7.10 EDS-510A’s enterprise value Fixed
NOTE: The Switch Object ID cannot be changed.
Using Communication Redundancy
Setting up Communication Redundancy on your network helps protect critical links against failure,
protects against network loops, and keeps network downtime at a minimum.
The Communication Redundancy function allows the user to set up redundant loops in the
network to provide a backup data transmission route in the event that a cable is inadvertently
disconnected or damaged. This is a particularly important feature for industrial applications, since
it could take several minutes to locate the disconnected or severed cable. For example, if the
EDS-510A is used as a key communications component of a production line, several minutes of
downtime could cause a big loss in production and revenue. The EDS supports three different
protocols to support this communication redundancy function— Rapid Spanning Tree/
Spanning Tree Protocol (IEEE 802.1W/1D), Turbo Ring, and Turbo Ring V2.
When configuring a redundant ring, all switches on th e same ring must be configured to use the
same redundancy protocol. You cannot mix the “Turbo Ring,” “Turbo Ring V2,” and STP/RSTP
protocols on the same ring. The following table lists the key differences between each feature. Use
this information to evaluate the benefits of each, and then determine which features are most
suitable for your network.
Turbo Ring V2 Turbo Ring STP RSTP
Topology Ring Ring Ring, Mesh Ring, Mesh
Recovery Time < 20 ms < 300 ms Up to 30 sec. Up to 5 sec
NOTE
Most of MOXA’s managed switches now support two proprietary Turbo Ring protocols:
(1) “Turbo Ring” refers to the original version of MOXA’s proprietary redundant ring
protocol, which has a recovery time of under 300 ms.
(2) “Turbo Ring V2” refers to the new generation Turbo Ring, which has a recovery time
of under 20 ms.
In this manual, we use the terminology “Turbo Ring” ring and “Turbo Ring V2” ring to
differentiate between rings configured for one or the other of these protocols.
Page 37

EDS-510A Series User’s Manual Featured Functions
3-22
Gigabit Ethernet Redundant Ring Capability (< 50 ms)
Ethernet has become the default data
communications medium for industrial automation
applications. In fact, Ethernet is often used to
integrate video, voice, and high-rate industrial
application data transfers into one network. The
EDS-510A, which comes equipped with a
redundant gigabit Ethernet protocol call ed Gigabit
Turbo Ring, gives system maintainers a convenient
means of setting up a versatile yet stable gigabit
Ethernet network. With Gigabit Turbo Ring, if any
segment of the network gets disconnected, your
automation system will be back to normal in less
than 300 ms (Turbo Ring) or 50 ms (Turbo Ring
V2).
Gigabit Turbo Ring
Recovery Time < 50 ms
NOTE
Port trunking and Turbo Ring can be enabled simultaneously to form a backbone. Doing so will
increase the bandwidth of the backbone, and also provide redundancy. For example, suppose that
two physical ports, 1 and 2, are trunked to form trunk group Trk1, and then Trk1 is set as one
Turbo Ring path, if port 1 gets disconnected, the remaining trunked port, port 2, will share the
traffic. If port 1 and port 2 are both disconnected, Turbo Ring will create the back up path within
300 ms.
The Turbo Ring Concept
MOXA developed the proprietary Turbo Ring protocol to optimize communication redundancy
and achieve a faster recovery time on the network.
The Turbo Ring and Turbo Ring V2 protocols iden tify one switch as the master of the network,
and then automatically block packets from traveling through any of the network’s redundant loops.
In the event that one branch of the ring gets disconnected from the rest of the network, the protocol
automatically readjusts the ring so that the part of the network that was disconnected can
reestablish contact with the rest of the network.
Initial setup of a “Turbo Ring” or “Turbo Ring V2” ring
1. Select any two ports as redundant ports.
2. Connect the redundant ports to form the
Tur bo Ring
Page 38

EDS-510A Series User’s Manual Featured Functions
3-23
The user does not need to configure any of the switches as the master to use Turbo Ring or Turbo
Ring V2. If none of the switches in the ring is configured as the master, then the protocol will
automatically assign master status to one of the switches. In fact, the master is only used to
identify which segment in the redundant ring acts as the backup path. In the following subsections,
we explain how the redundant path is selected for rings configured for Turbo Ring, and Turbo
Ring V2.
Determining the Redundant Path of a “Turbo Ring” Ring
In this case, the redundant segment (i.e., the segment that will be blocked during normal operation)
is determined by the number of EDS units that make up the ring, and where the ring master is
located.
When the number of EDS-510A units in the Turbo Ring is even.
Master
If there are 2N EDS units (an even number) in
the “Turbo Ring” ring, then the backup segment
is one of the two segments connected to the
(N+1)st EDS (i.e., the EDS unit directly opposite
the master).
When the number of EDS-510A units in the Turbo Ring is odd.
Master
Segment N+1
If there are 2N+1 EDS units (an odd number) in
the “Turbo Ring” ring, with EDS units and
segments labeled counterclockwise, then
segment N+1 will serve as the backup path.
For the example shown here, N=1, so that
N+1=2.
Page 39

EDS-510A Series User’s Manual Featured Functions
3-24
Determining the Redundant Path of a “Turbo Ring V2” Ring
Master
For a “Turbo Ring V2” ring, the backup
segment is the segment connected to the 2nd
redundant port on the master.
See Configuring “Turbo Ring V2” in the
Configuring “Turbo Ring” and “Turbo Ring
V2” section below.
Ring Coupling Configuration
For some systems, it may not be convenient to connect all devices in the system to create one BIG
redundant ring, since some devices could be located in a remote area. For these systems, “Ring
Coupling” can be used to separate the devices into different smaller redundant rings, but in such a
way that they can still communicate with each other.
ATTENTION
In a VLAN environment, the user must set “Redundant Port” “Coupling Port” and “Coupling
Control Port” to join all VLANs, since these ports act as the “backbone” to transmit all packets
of different VLANs to different EDS units.
Ring Coupling for a “Turbo Ring” Ring
Switch A: "Coupler"
Switch B
Switch C
Switch D
Main Path
Coupling Port
Backup Path
Coupling
Control Port
Page 40

EDS-510A Series User’s Manual Featured Functions
3-25
To configure the Ring Coupling function for a “Turbo Ring” ring, select two EDS units (e.g.,
Switch A and B in the above figure) in the ring, and another two EDS units in the adjacent ring
(e.g., Switch C and D). Decide which two ports in each switch are appropriate to be used as
coupling ports, and then link them together. Next, assign one switch (e.g., Switch A) to be the
“coupler” and connect the coupler’s coupling control port with Switch B (for this example).
The coupler switch (i.e., Switch A) will monitor switch B through the coupling control port to
determine whether or not the coupling port’s backup path should be recovered.
Ring Coupling for a “Turbo Ring V2” Ring
Switch A
Switch B
Switch D
Coupling Port (Primary)
Switch C
Main Path
Coupling Port (Backup)
Backup Path
Note that the ring coupling settings for a “Turbo Ring V2” ring are different from a “Turbo
Ring” ring. For Turbo Ring V2, Ring Coupling is enabled by configuring the “Coupling Port
(Primary)” on Switch B, and the “Coupling Port (Backup)” on Switch A only. You do not need
to set up a coupling control port, so that a “Turbo Ring V2” ring does not use a coupling control
line.
The “Coupling Port (Backup)” on Switch A is used for the backup path, and co nnect s di rect l y to
an extra network port on Switch C. The “Coupling Port (Primary)” on Switch B monitors the
status of the main path, and connects directly to an extra network port on Switch D. With ring
coupling established, Switch A can activate the backup path as soon as it detects a problem with
the main path.
ATTENTION
Ring Coupling only needs to be enabled on one of the switches serving as the Ring Coupler. The
Coupler must designate different ports as the two Turbo Ring ports and the coupling port.
NOTE
You do not need to use the same EDS unit for both Ring Coupling and Ring Master.
Page 41

EDS-510A Series User’s Manual Featured Functions
3-26
Dual-Ring Configuration (applies only to “Turbo Ring V2”)
The “dual-ring” option provides another ring coupling configuration, in which two adjacent rings
share one switch. This type of configuration is ideal for applications that have inherent cabling
difficulties.
Dual-Ring for a “Turbo Ring V2” Ring
Ring A
Master
Master
Ring B
Dual-Homing Configuration (applies only to “Turbo Ring V2”)
The “dual-homing” option uses a single Ethernet switch to connect two networks. The primary
path is the operating connection, and the backup p a th is a back-up connection that is activated in
the event that the primary path connection fails.
Dual-Homing for a “Turbo Ring V2” Ring
Primary
Path
Ring A
Master
Master
Ring B
Backup
Path
Page 42
EDS-510A Series User’s Manual Featured Functions
3-27
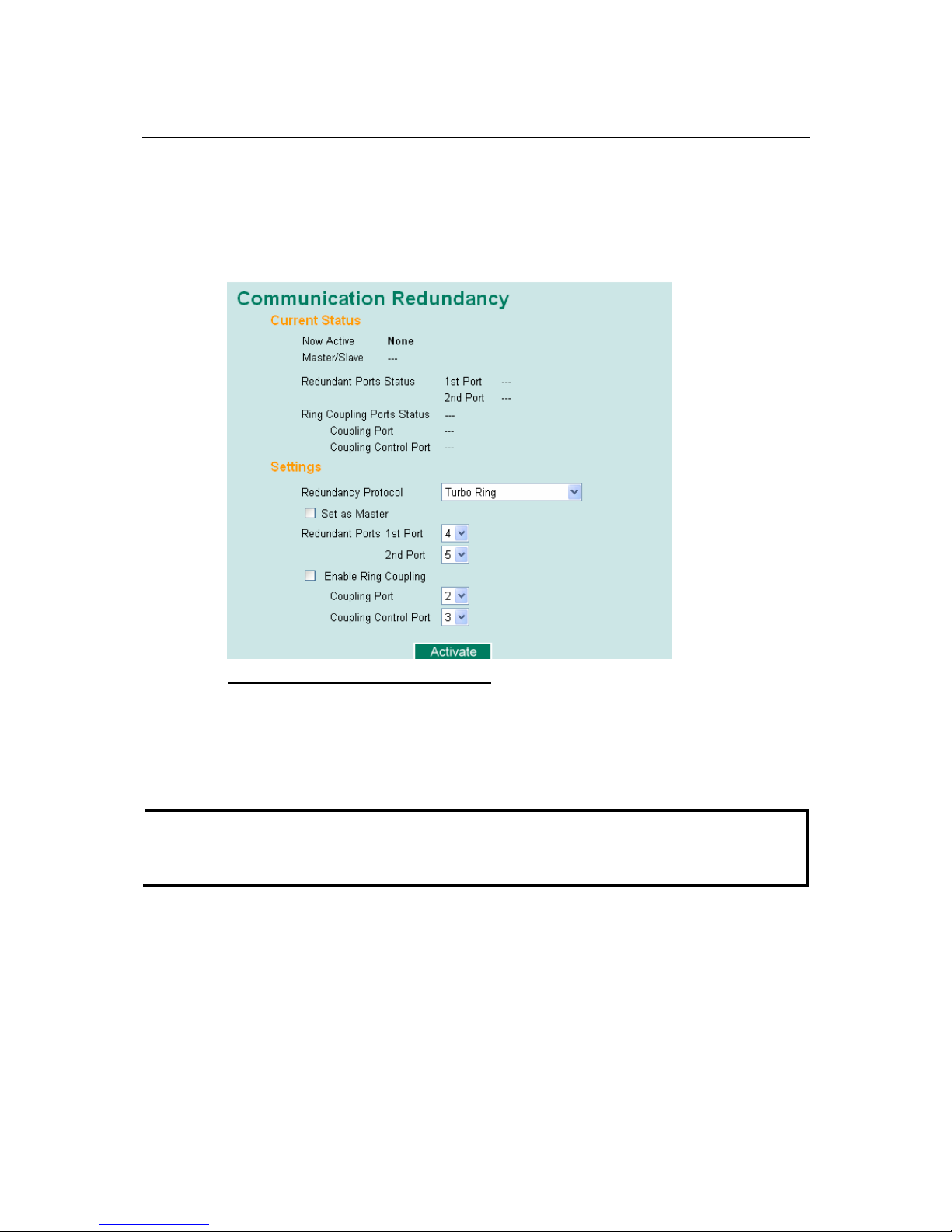
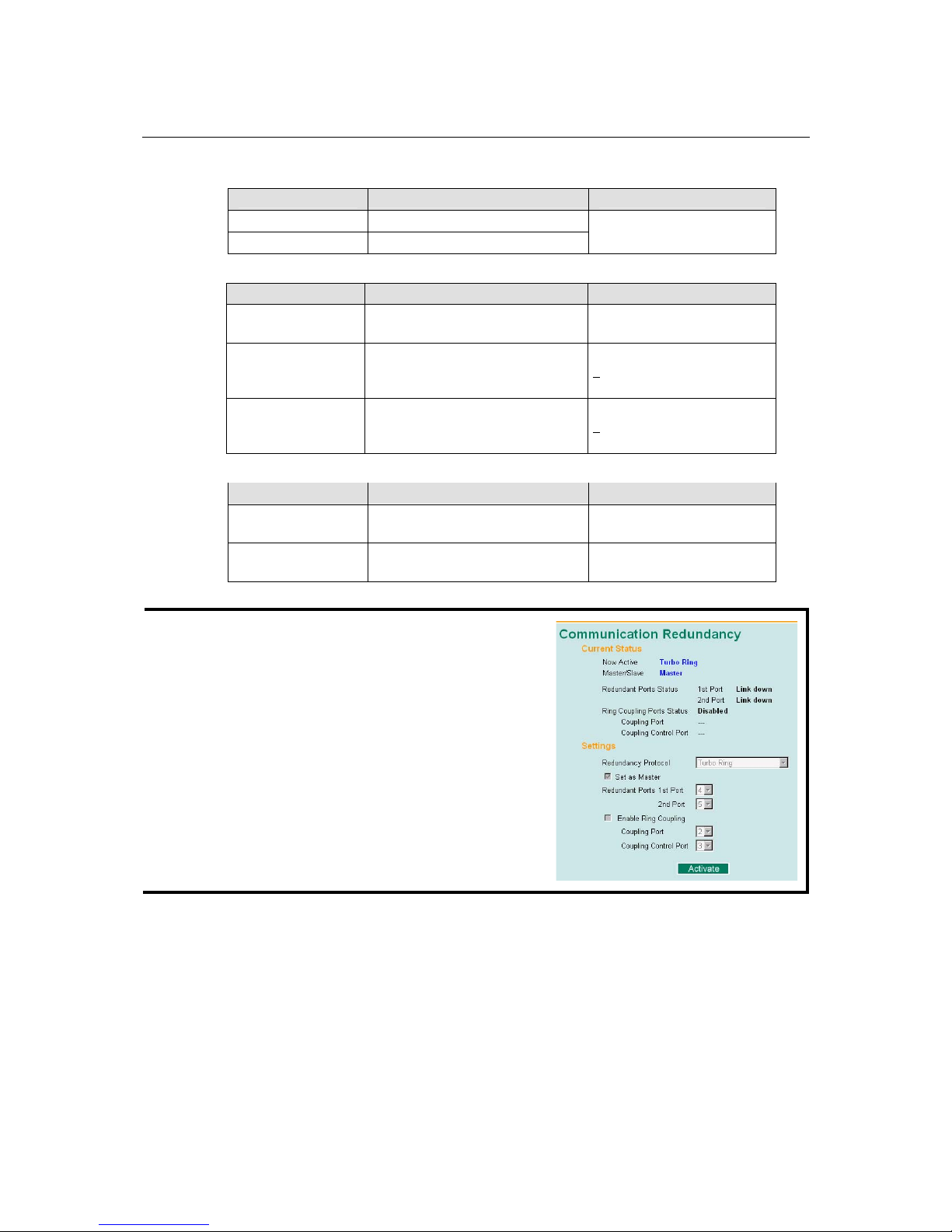
Configuring “Turbo Ring” and “Turbo Ring V2”
Use the Communication Redundancy page to configure select “Turbo Ring” or “Turbo Ring
V2” Note that configuration pages for these two protocols are different.
Configuring “Turbo Ring”
Explanation of “Current Status” Items
Now Active
Shows which communication protocol is in use: Turbo Ring, Turbo Ring V2, RSTP, or none.
Master/Slave
Indicates whether or not this EDS is the Master of the Turbo Ring. (This field appears only when
selected to operate in Turbo Ring or Turbo Ring V2 mode.)
NOTE
The user does not need to set the master to use Turbo Ring. If no master is set, the Turbo Ring
protocol will assign master status to one of the EDS units in the ring. The master is only used to
determine which segment serves as the backup path.
Redundant Ports Status (1st Port, 2nd Port)
Ring Coupling Ports Status (Coupling Port, Coupling Control Port)
The “Ports Status” indicators show Forwarding for normal transmission, Blocking if this port is
connected to a backup path and the path is blocked, and Link down if there is no connection.
Page 43
EDS-510A Series User’s Manual Featured Functions
3-28
Explanation of “Settings” Items
Redundancy Protocol
Setting Description Factory Def au l t
Turbo Ring
Select this item to change to the
Turbo Ring configuration page.
Turbo Ring V2
Select this item to change to the
Turbo Ring V2 configuration page.
RSTP (IEEE
802.1W/1D)
Select this item to change to the
RSTP configuration page.
None Ring redundancy is not active
None
Set as Master
Setting Description Factory Def au l t
Enabled Select this EDS as Master
Disabled Do not select this EDS as Master
Not checked
Redundant Ports
Setting Description Factory Def au l t
1st Port
Select any port of the EDS to be
one of the redundant ports.
port G2
2nd Port
Select any port of the EDS to be
one of the redundant ports.
port G3
Enable Ring Coupling
Setting Description Factory Def au l t
Enable Select this EDS as Coupler
Disable Do not select this EDS as Coupler
Not checked
Coupling Port
Setting Description Factory Def au l t
Coupling Port
Select any port of the EDS to be the
coupling port
port 7
Coupling Control Port
Setting Description Factory Def au l t
Coupling Control Port
Select any port of the EDS to be the
coupling control port
port G1
Page 44

EDS-510A Series User’s Manual Featured Functions
3-29
Configuring “Turbo Ring V2”
NOTE
When using the Dual-Ring architecture, users must configure settings for both Ring 1 and Ring 2.
In this case, the status of both rings will appear under “Current Status.”
Explanation of “Current Status” Items
Now Active
Shows which communication protocol is in use: Turbo Ring, Turbo Ring V2, RSTP, or none.
Ring 1/2—Status
Shows Healthy if the ring is operating normally, and shows Break if the ring’s backup link is
active.
Ring 1/2—Master/Slave
Indicates whether or not this EDS is the Master of the Turbo Ring. (This field appears only when
selected to operate in Turbo Ring or Turbo Ring V2 mode.)
NOTE
The user does not need to set the master to use Turbo Ring. If no master is set, the Turbo Ring
protocol will assign master status to one of the EDS units in the ring. The master is only used to
determine which segment serves as the backup path.
Page 45
EDS-510A Series User’s Manual Featured Functions
3-30
Ring 1/2—1st Ring Port Status
Ring 1/2—2nd Ring Port Statu
The “Ports Status” indicators show Forwarding for normal transmission, Blocking if this port is
connected to a backup path and the path is blocked, and Link down if there is no connection.
Coupling—Mode
Indicates either None, Dual Homing, or Ring Coupling.
Coupling—Coupling Port status
Indicates either Primary, or Backup.
Explanation of “Settings” Items
Redundancy Protocol
Setting Description Factory Def au l t
Turbo Ring
Select this item to change to the
Turbo Ring configuration page.
Turbo Ring V2
Select this item to change to the
Turbo Ring V2 configuration page.
RSTP (IEEE
802.1W/1D)
Select this item to change to the
RSTP configuration page.
None Ring redundancy is not active
None
Enable Ring 1
Setting Description Factory Def au l t
Enabled Enable the Ring 1 settings
Disabled Disable the Ring 1 settings
Not checked
Enable Ring 2*
Setting Description Factory Def au l t
Enabled Enable the Ring 2 settings
Disabled Disable the Ring 2 settings
Not checked
*You should enable both Ring 1 and Ring 2 when using the Dual-Ring architecture.
Set as Master
Setting Description Factory Def au l t
Enabled Select this EDS as Master
Disabled Do not select this EDS as Master
Not checked
Redundant Ports
Setting Description Factory Def au l t
1st Port
Select any port of the EDS to be
one of the redundant ports.
port G2
2nd Port
Select any port of the EDS to be
one of the redundant ports.
port G3
Page 46
EDS-510A Series User’s Manual Featured Functions
3-31
Enable Ring Coupling
Setting Description Factory Def au l t
Enable Select this EDS as Coupler
Disable Do not select this EDS as Coupler
Not checked
Coupling Mode
Setting Description Factory Default
Dual Homing
Select this item to change to the
Dual Homing configuration page
Primary Port: port G1
Backup Port: port G2
Ring Coupling
(backup)
Select this item to change to the
Ring Coupling (backup)
configuration page
p
ort G1
Ring Coupling
(primary)
Select this item to change to the
Ring Coupling (primary)
configuration page
p
ort G1
Primary/Backup Port
Setting Description Factory Def au l t
Primary Port
Select any port of the EDS to be the
primary port.
port G1
Backup Port
Select any port of the EDS to be the
backup port.
port G2
NOTE
The Turbo Ring DIP Switches located on the
EDS-510A’s outer casing can be used to configure the
EDS’s Turbo Ring protocols. (Fo r det ai ls on how to do
this, refer to “Configuring Basic Settings—Turbo Ring
DIP Switch” section in this manual.)
If you use the web interface, console interface, or
Telnet interface to enable the Turbo Ring DIP
Switches, and then set DIP Switch 4 on the switch’s
outer casing to the “ON” position, you will not be able
to use the web interface, console interface, or Telnet
interface to change the status of the DIP Switch. In
this case, the Communication Redundancy settings
will be “grayed out” in the web browser as shown in
the following figure:
Page 47
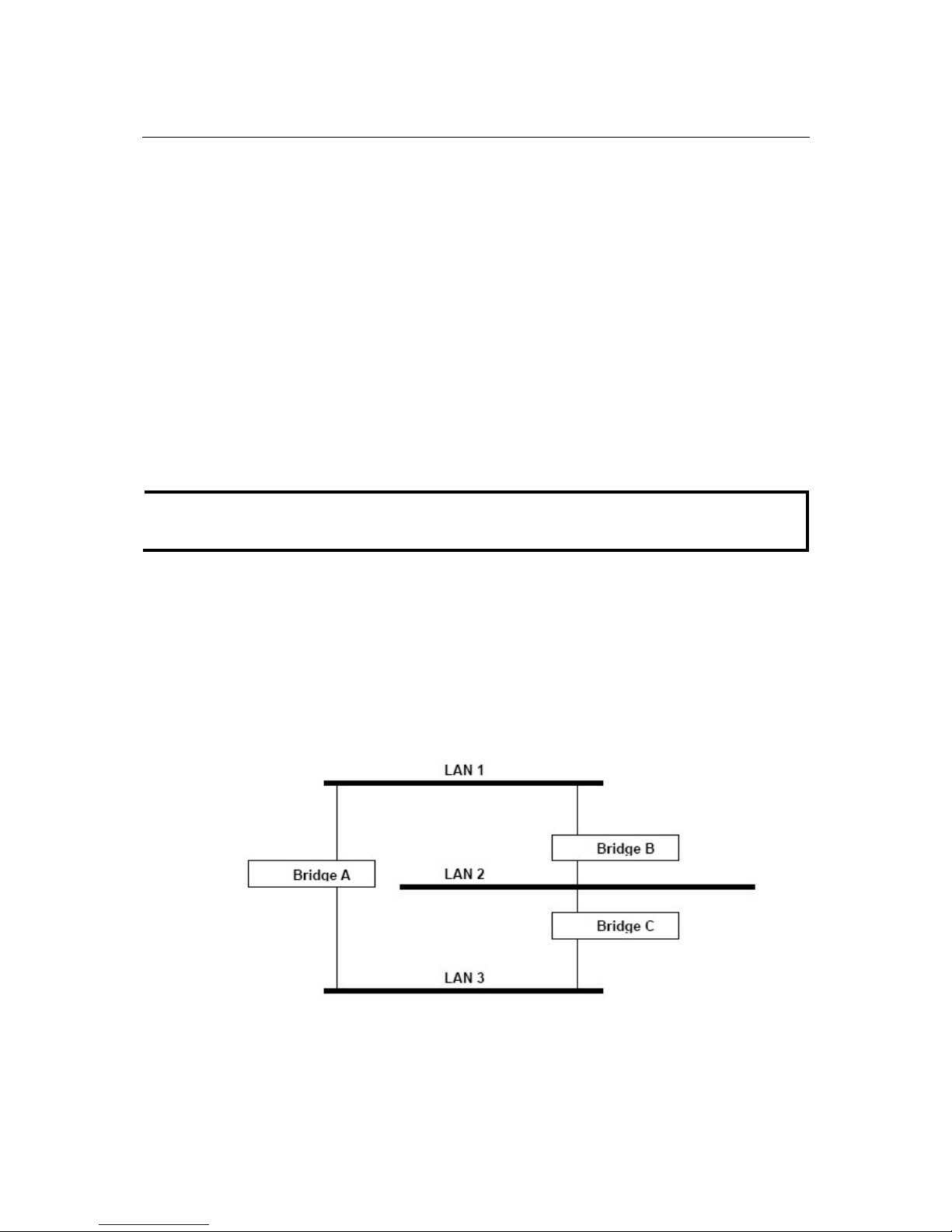
EDS-510A Series User’s Manual Featured Functions
3-32
The STP/RSTP Concept
Spanning Tree Protocol (STP) was designed to help reduce link failures in a network, and provide
protection from loops. Networks that have a complicated architecture are prone to broadcast
storms caused by unintended loops in the network. Moxa EDS-510A’s STP feature is disabled by
default. To be completely effective, you must enable RSTP/STP on every EDS-510A connected to
your network.
Rapid Spanning Tree Protocol (RSTP) implements the Spanning Tree Algorithm and Protocol
defined by IEEE Std 802.1w-2001. RSTP provides the following benefits:
y The topology of a bridged network will be determined much more quickly compared to STP.
y RSTP is backward compatible with STP, making it relatively easy to deploy. For example:
¾ Defaults to sending 802.1D style BPDUs if packets with this format are received.
¾ STP (802.1D) and RSTP (802.1w) can operate on different ports of the same EDS-510A.
This feature is particularly helpful when EDS-510A ports connect to older equipment,
such as legacy switches.
You get essentially the same functionality with RSTP and STP. To see how the two systems differ,
see the Differences between RSTP and STP section in this chapter.
NOTE
The STP protocol is part of the IEEE Std 802.1D, 1998 Edition bridge specification. The
following explanation uses bridge instead of switch.
What is STP?
STP (802.1D) is a bridge-based system that is used to implement parallel paths for network traffic.
STP uses a loop-detection process to:
y Locate and then disable less efficient paths (i.e., paths that have a lower bandwidth).
y Enable one of the less efficient paths if the most efficient path fails.
The figure below shows a network made up of three LANs separated by three bridges. Each
segment uses at most two paths to communicate with the other segments. Since this configuration
can give rise to loops, the network will overload if STP is NOT enabled.
Page 48

EDS-510A Series User’s Manual Featured Functions
3-33
If STP is enabled, it will detect duplicate paths and prevent, or block, one of them from forwarding
traffic. In the following example, STP determined that traffic from LAN segment 2 to LAN
segment 1 should flow through Bridges C and A because this path has a greater bandwidth and is
therefore more efficient.
What happens if a link failure is detected? As shown in next figure, the STP process reconfigures
the network so that traffic from LAN segment 2 flows through Bridge B.
STP will determine which path between each bridged segment is most efficient, and then assigns a
specific reference point on the network. When the most efficient path has been identified, the other
paths are blocked. In the previous 3 figures, STP first determined that the path through Bridge C
was the most efficient, and as a result, blocked the path through Bridge B. After the failure of
Bridge C, STP re-evaluated the situation and opened the path through Bridge B.
Page 49

EDS-510A Series User’s Manual Featured Functions
3-34
How STP Works
When enabled, STP determines the most appropriate path for traffic through a network. The way it
does this is outlined in the sections below.
STP Requirements
Before STP can configure the network, the system must satisfy the following requirements:
y Communication between all the bridges. This communication is carried out using Bridge
Protocol Data Units (BPDUs), which are transmitted in packets with a known multicast
address.
y Each bridge must have a Bridge Identifier that specifies which bridge acts as the central
reference point, or Root Bridge, for the STP system—bridges with a lower Bridge Identifier
are more likely to be designated as the Root Bridge. The Bridge Identifier is calculated using
the MAC address of the bridge and a priority defined for the bridge. The default priority of
EDS-510A is 32768.
y Each port has a cost that specifies the efficiency of each link. The efficiency cost is usually
determined by the bandwidth of the link, with less efficient links assigned a higher cost. The
following table shows the default port costs for a switch:
Port Speed Path Cost 802.1D,
1998 Edition
Path Cost
802.1w-2001
10 Mbps 100 2,000,000
100 Mbps 19 200,000
1000 Mbps 4 20,000
STP Calculation
The first step of the STP process is to perform calculations. During this stage, each bridge on the
network transmits BPDUs. The following items will be calculated:
y Which bridge should be the Root Bridge. The Root Bridge is the central reference point from
which the network is configured.
y The Root Path Costs for each bridge. This is the cost of the paths from each bridge to the Root
Bridge.
y The identity of each bridge’s Root Port. The Root Port is the port on the bridge that connects
to the Root Bridge via the most efficient path. In other words, the port connected to the Root
Bridge via the path with the lowest Root Path Cost. The Root Bridge, however, does not have
a Root Port.
y The identity of the Designated Bridge for each LAN segment. The Designated Bridge is the
bridge with the lowest Root Path Cost from that segment. If several bridges have the same
Root Path Cost, the one with the lowest Bridge Identifier becomes the Designated Bridge.
Traffic transmitted in the direction of the Root Bridge will flow through the Designated
Bridge. The port on this bridge that connects to the segment is called the Designated Bridge
Port.
STP Configuration
After all the bridges on the network agree on the identity of the Root Bridge, and all other relevant
parameters have been established, each bridge is configured to forward traffic only between its
Root Port and the Designated Bridge Ports for the respective network segments. All other ports are
blocked, which means that they will not be allowed to receive or forward traffic.
Page 50

EDS-510A Series User’s Manual Featured Functions
3-35
STP Reconfiguration
Once the network topology has stabilized, each bridge listens for Hello BPDUs transmitted from
the Root Bridge at regular intervals. If a bridge does not receive a Hello BPDU after a certain
interval (the Max Age time), the bridge assumes that the Root Bridge, or a link between itself and
the Root Bridge, has gone down. This will trigger the bridge to reconfigure the network to account
for the change. If you have configured an SNMP trap destination, when the topology of your
network changes, the first bridge to detect the change sends out an SNMP trap.
Differences between RSTP and STP
RSTP is similar to STP, but includes additional information in the BPDUs that allow each bridge
to confirm that it has taken action to prevent loops from forming when it decides to enab le a link
to a neighboring bridge. Adjacent bridges connected via point-to-point links will be able to enable
a link without waiting to ensure that all other bridges in the network have had time to react to the
change. The main benefit of RSTP is that the configuration decision is made locally rather than
network-wide, allowing RSTP to carry out automatic configuration and restore a link faster than
STP.
STP Example
The LAN shown in the following figure has three segments, with adjacent segments connected
using two possible links. The various STP factors, such as Cost, Root Port, Designated Bridge Port,
and Blocked Port are shown in the figure.
Bridge A
LAN Segment 3
LAN Segment 2
LAN Segment 1
Port 2
(Root Bridge)
Port 1
(Designated
Bridge Port)
Bridge B
Port 2
(Designated
Bridge Port)
Port 1
(Root Port)
Cost =100
Bridge X
Port 2
(Blocked Port)
Port 1
(Root Port)
Cost =100
Bridge C
Port 2
(Designated
Bridge Port)
Port 1
(Root Port)
Cost =100
Bridge Y
Port 2
(Blocked Port)
Port 1
(Root Port)
Cost =200
y Bridge A has been selected as the Root Bridge, since it was determined to have the lowest
Bridge Identifier on the network.
y Since Bridge A is the Root Bridge, it is also the Designated Bridge for LAN segment 1. Port 1
on Bridge A is selected as the Designated Bridge Port for LAN Segment 1.
y Ports 1 of Bridges B, C, X, and Y are all Root Ports sine they are nearest to the Root Bridge,
and therefore have the most efficient path.
Page 51

EDS-510A Series User’s Manual Featured Functions
3-36
y Bridges B and X offer the same Root Path Cost for LAN segment 2. However, Bridge B was
selected as the Designated Bridge for that segment since it has a lower Bridge Identifier. Port
2 on Bridge B is selected as the Designated Bridge P ort fo r LAN Segment 2.
y Bridge C is the Designated Bridge for LAN segment 3, because it has the lowest Root Path
Cost for LAN Segment 3:
¾ The route through Bridges C and B costs 200 (C to B=100, B to A=100)
¾ The route through Bridges Y and B costs 300 (Y to B=200, B to A=100)
y The Designated Bridge Port for LAN Segment 3 is Port 2 on Bridge C.
Using STP on a Network with Multiple VLANs
IEEE Std 802.1D, 1998 Edition, does not take into account VLANs when calculating STP
information—the calculations only depend on the physical connections. Consequently, some
network configurations will result in VLANs being subdivided into a number of isolated sectio ns
by the STP system. You must ensure that every VLAN configuration on your network takes into
account the expected STP topology and alternative topologies that may result from link failures.
The following figure shows an example of a network that con tains VL ANs 1 and 2. The VLANs
are connected using the 802.1Q-tagged link between Switch B and Switch C. By default, this link
has a port cost of 100 and is automatically blocked because the other Switch-to-Switch
connections have a port cost of 36 (18+18). This m eans tha t both VLANs are now
subdivided—VLAN 1 on Switch units A and B cannot communicate with VLAN 1 on Switch C,
and VLAN 2 on Switch units A and C cannot communicate with VLAN 2 on Switch B.
Block
Switch A
Switch B Switch C
VLAN1
VLAN2
802.1Q tagged,
10BaseTx
half-duplex Link
carries VLAN1, 2
(path cost = 100)
100BaseTX
full-duplex Link;
only carries VLAN2
(path cost = 18)
100BaseTX
full-duplex Link;
only carries VLAN1
(path cost = 18)
VLAN1
VLAN2
VLAN1
VLAN2
To avoid subdividing VLANs, all inter-switch connections should be made members of all
available 802.1Q VLANs. This will ensure connectivity at all times. For example, the connections
between Switches A and B, and between Switches A and C should be 802.1Q tagged and carrying
VLANs 1 and 2 to ensure connectivity.
See the “Configuring Virtual LANs” section for more information about VLAN Tagging.
Page 52

EDS-510A Series User’s Manual Featured Functions
3-37
Configuring STP/RSTP
The following figures indicate which Spanning Tree Prot o col pa rameters can be configured. A
more detailed explanation of each parameter follows.
At the top of this page, the user can check the “Current Status ” of this function. For RSTP, you
will see:
Now Active:
This will show which communication protocol is being used—Turbo Ring, RSTP, or neither.
Root/Not Root
This field will appear only when selected to operate in RSTP mode. It indicates whether or not this
EDS-510A is the Root of the Spanning Tree (the root is determined automatically).
At the bottom of this page, the user can configure the “Settings” of this function. For RSTP, you
can configure:
Protocol of Redundancy
Setting Description Factory Default
Turbo Ring Select th is item to change to the Turbo Ring
configuration page.
None
RSTP (IEEE 802.1W/1D) Select this item to change to the RSTP
configuration page.
None
Bridge priority
Setting Description Factory Default
Numerical value selected
by user
Increase this device’s bridge priority by
selecting a lower number. A device with a
higher bridge priority has a greater chance of
being established as the root of the Spanning
Tree topology.
32768
Page 53
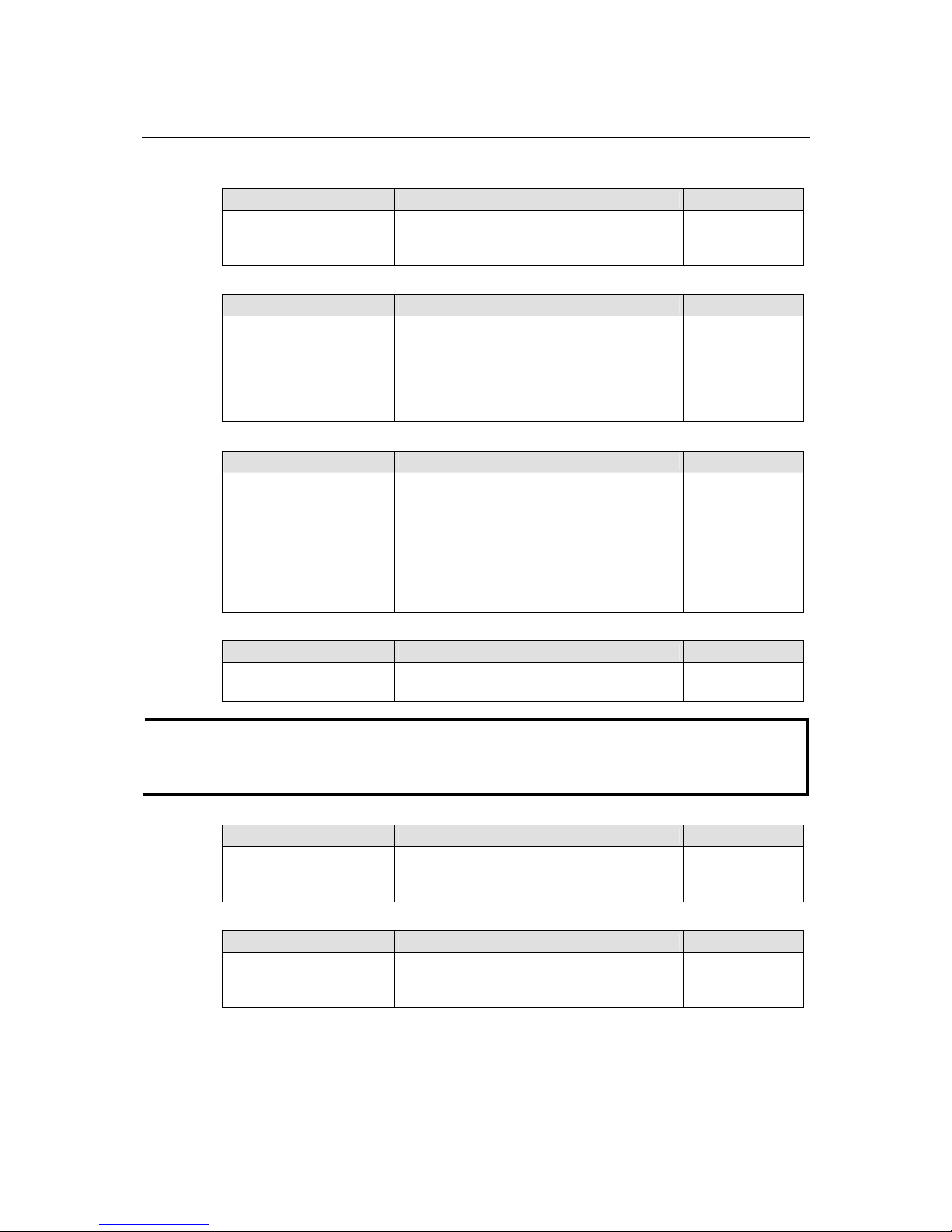
EDS-510A Series User’s Manual Featured Functions
3-38
Forwarding Delay
Setting Description Factory Default
Numerical value input by
user
The amount of time this device waits before
checking to see if it should change to a
different state.
15 (sec.)
Hello time (sec.)
Setting Description Factory Default
Numerical value input by
user
The root of the Spanning Tree topology
periodically sends out a “hello” message to
other devices on the network to check if the
topology is healthy. The “hello time” is the
amount of time the root waits between sending
hello messages.
2
Max. Age (sec.)
Setting Description Factory Default
Numerical value input by
user
If this device is not the root, and it has not
received a hello message from the root in an
amount of time equal to “Max. Age,” then this
device will reconfigure itself as a root. Once
two or more devices on the network are
recognized as a root, the devices will
renegotiate to set up a new Spanning Tree
topology.
20
Enable STP per Port
Setting Description Factory Default
Enable/Disable Select to enable the port as a node on the
Spanning Tree topology.
Disabled
NOTE
We suggest not enabling the Spanning Tree Protocol once the port is connected to a device (PLC,
RTU, etc.) as opposed to network equipment. The reason is that it will cause unnecessary
negotiation.
Port Priority
Setting Description Factory Default
Numerical value selected
by user
Increase this port’s priority as a node on the
Spanning Tree topology by entering a lower
number.
128
Port Cost
Setting Description Factory Default
Numerical value input by
user
Input a higher cost to indicate that this port is
less suitable as a node for the Spanning Tree
topology.
200000
Port Status
Indicates the current Spanning Tree status of this port. “Forwarding” for normal transmission, or
“Blocking” to block transmission.
Page 54

EDS-510A Series User’s Manual Featured Functions
3-39
Configuration Limits of RSTP/STP
The Spanning Tree Algorithm places limits on three of the configuration items described
previously:
[Eq. 1]: 1 sec ≦ Hello Time ≦ 10 sec
[Eq. 2]: 6 sec ≦ Max. Age ≦ 40 sec
[Eq. 3]: 4 sec ≦ Forwarding Delay ≦ 30 sec
These three variables are further restricted by the following two inequalities:
[Eq. 4]: 2 * (Hello Time + 1 sec) ≦ Max. Age ≦ 2 * (Forwarding Delay – 1 se c)
Moxa EDS-510A’s firmware will alert you immediately if any of these restrictions are violated.
For example, setting
Hello Time = 5 sec, Max. Age = 20 sec, and Forwarding Delay = 4 sec does not violate Eqs. 1
through 3, but does violate Eq. 4, since in this case,
2 * (Hello Time + 1 sec) = 12 sec, and 2 * (Forwarding Delay – 1 sec) = 6 sec.
You can remedy the situation in many ways. One solution is simply to increase the Forwarding
Delay value to at least 11 sec.
HINT: Perform the following steps to avoid guessing:
Step 1: Assign a value to “Hello Time” and then calculate the left most part of Eq. 4 to get the
lower limit of “Max. Age.”
Step 2: Assign a value to “Forwarding Delay” and then calculate the right most part of Eq. 4 to
get the upper limit for “Max. Age.”
Step 3: Assign a value to “Forwarding Delay” that satisfies the conditions in Eq. 3 and Eq. 4.
Using Traffic Prioritization
EDS-510A’s traffic prioritization capability provides Quality of Service (QoS) to your network by
making data delivery more reliable. You can prioritize traffic on your network to ensure that high
priority data is transmitted with minimum delay. Traffic can be controlled by a set of rules to
obtain the required Quality of Service for your network. The rules define different types of traffic
and specify how each type should be treated as it passes through the switch. Moxa EDS-510A can
inspect both IEEE 802.1p/1Q layer 2 CoS tags, and even layer 3 TOS information to provide
consistent classification of the entire network. EDS-510A’s QoS capability improves the
performance and determinism of industrial networks for mission critical applications.
The Traffic Prioritization Concept
What is Traffic Prioritization?
Traffic prioritization allows you to prioritize data so that time-sensitive and system-critical data
can be transferred smoothly and with minimal delay over a network. The benefits of using traffic
prioritization are:
y Improve network performance by controlling a wide variety of traffic and managing
congestion.
y Assign priorities to different categories of traffic. For example, set higher priorities for
time-critical or business-critical applications.
y Provide predictable throughput for multimedia applications, such as video conferencing or
voice over IP, and minimize traffic delay and jitter.
y Improve network performance as the amount of traffic grows. This will save cost by reducing
the need to keep adding bandwidth to the network.
Page 55

EDS-510A Series User’s Manual Featured Functions
3-40
How Traffic Prioritization Works
Traffic prioritization uses the four traffic queues that are present in your EDS-510A to ensure that
high priority traffic is forwarded on a different queue from lower priority traffic. This is what
provides Quality of Service (QoS) to your network.
EDS-510A traffic prioritization depends on two industry-standard methods:
y IEEE 802.1D—a layer 2 marking scheme.
y Differentiated Services (DiffServ)—a layer 3 marking scheme.
IEEE 802.1D Traffic Marking
The IEEE Std 802.1D, 1998 Edition marking scheme, which is an enhancement to IEEE Std
802.1D, enables Quality of Service on the LAN. Traffic service levels are defined in the IEEE
802.1Q 4-byte tag, which is used to carry VLAN identification as well as IEEE 802.1p priority
information. The 4-byte tag immediately follows the destination MAC address and So urce MAC
address.
The IEEE Std 802.1D, 1998 Edition priority marking scheme assigns an IEEE 802.1p priority
level between 0 and 7 to each frame. This determines the level of service that that type of traffic
should receive. Refer to the table below for an example of how different traffic types can be
mapped to the eight IEEE 802.1p priority levels.
IEEE 802.1p Priority Level IEEE 802.1D Traffic Type
0 Best Effort (default)
1 Background
2 Standard (spare)
3 Excellent Effort (business critical)
4 Controlled Load (streaming multimedia)
5 Video (interactive media); less than 100 milliseconds
of latency and jitter
6 Voice (interactive voice); less than 10 milliseconds of
latency and jitter
7 Network Control Reserved traffic
Even though the IEEE 802.1D standard is the most widely used prioritization scheme in the LAN
environment, it still has some restrictions:
y It requires an additional 4-byte tag in the frame, which is normally optional in Ethernet
networks. Without this tag, the scheme cannot work.
y The tag is part of the IEEE 802.1Q header, so to implement QoS at layer 2, the entire network
must implement IEEE 802.1Q VLAN tagging.
It is only supported on a LAN and not routed across WAN links, since the IEEE 802.1Q tags are
removed when the packets pass through a router.
Differentiated Services (DiffServ) Traffic Marking
DiffServ is a Layer 3 marking scheme that uses the DiffServ Code Point (DSCP) field in the IP
header to store the packet priority information. DSCP is an advanced intelligent method of traffic
marking as you can choose how your network prioritizes different types of traffic. DSCP uses 64
values that map to user-defined service levels, allowing you to establish more control over
network traffic.
Page 56

EDS-510A Series User’s Manual Featured Functions
3-41
Advantages of DiffServ over IEEE 802.1D are:
y Configure how you want your switch to treat selected applications and types of traffic by
assigning various grades of network service to them.
y No extra tags are required in the packet.
y DSCP uses the IP header of a packe t and therefore priority is preserved across the Internet.
y DSCP is backward compatible with IPV4 TOS, which allows operation with existing devices
that use a layer 3 TOS enabled prioritization scheme.
Traffic Prioritization
EDS-510A classifies traffic based on layer 2 of the OSI 7 layer model, and the switch prioritizes
received traffic according to the priority information define d in the received packet. Incoming
traffic is classified based upon the IEEE 802.1D frame and is assigned to the appropriate priority
queue based on the IEEE 802.1p service level value defined in that packet. Service level markings
(values) are defined in the IEEE 802.1Q 4-byte tag, and consequently traffic will only contain
802.1p priority markings if the network is configured with VLANs and VLAN tagging. The traffic
flow through the switch is as follows:
1. A packet received by the EDS-510A may or may not have an 802.1p tag associated with it. If
it does not, then it is given a default 802.1p tag (which is usually 0). Alternatively, the packet
may be marked with a new 802.1p value, which will result in all kno wledge of the old 802.1p
tag being lost.
2. As the 802.1p priority levels are fixed to the traffic queues, the packet will be placed in the
appropriate priority queue, ready for transmission through the appropriate egress port. When
the packet reaches the head of its queue and is about to be transmitted, the device determines
whether or not the egress port is tagged for that VLAN. If it is, then the new 802.1p tag is
used in the extended 802.1D header.
The EDS-510A will check a packet received at the ingress port for IEEE 802.1D traffic
classification, and then prioritize it based upon the IEEE 802.1p value (service levels) in that tag.
It is this 802.1p value that determines to which traffic queue the packet is mapped.
Traffic Queues
The EDS-510A hardware has multiple traffic queues that allow packet prioritization to occur.
Higher priority traffic can pass through the EDS-510A without being delayed by lower priority
traffic. As each packet arrives in the EDS-510A, it passes through any ingress processing (which
includes classification, marking/re-marking), and is then sorted into the appropriate queue. The
switch then forwards packets from each queue.
EDS-510A supports two different queuing mechanisms:
y Weight Fair: This method services all the traffic queues, giving priority to the higher priority
queues. Under most circumstances, this method gives high priority precedence over
low-priority, but in the event that high-priority traffic exceeds the link capacity, lower priority
traffic is not blocked.
y Strict: This method services high traffic queues first; low priority queues are delayed until no
more high priority data needs to be sent. This method always gives precedence to high priority
over low-priority.
Configuring Traffic Prioritization
Quality of Service (QoS) provides a traffic prioritization capability to ensure that important data is
delivered consistently and predictably. EDS-510A Series can inspect IEEE 802.1p /1Q layer 2 CoS
tags, and even layer 3 TOS information, to provide a consistent classification of the entire network.
EDS-510A Series’ QoS capability improves your industrial network’s performance and
determinism for mission critical applications.
Page 57

EDS-510A Series User’s Manual Featured Functions
3-42
QoS Classification
Moxa EDS-510A supports inspection of layer 3 TOS and/or layer 2 CoS tag information to
determine how to classify traffic packets.
Queuing Mechanism
Setting Description Factory Default
Weighted Fair EDS-510A has 4 priority queues. In the weighted fair
scheme, an 8, 4, 2, 1 weighting is applied to the four
priorities. This approach prevents the lower priority
frames from being starved of opportunit y for
transmission with only a slight delay to the higher
priority frames.
Strict In the Strict-priority scheme, all top-priority frames
egress a port until that priority’s queue is empty, and
then the next lower priority queue’s frames egress. This
approach can cause the lower priorities to be starved of
opportunity for transmitting any frames but ensures all
high priority frames to egress the switch as soon as
possible.
Weight Fair
Port Highest Priority
Setting Description Factory Default
Enable/Disable Set the Port Priority of the ingress frames to “High”
queues.
Disable
Inspect TOS
Setting Description Factory Default
Enable/Disable Select the option to enable EDS-510A to inspect the
Type of Service (TOS) bits in IPV4 frame to determine
the priority of each frame.
Enable
Page 58
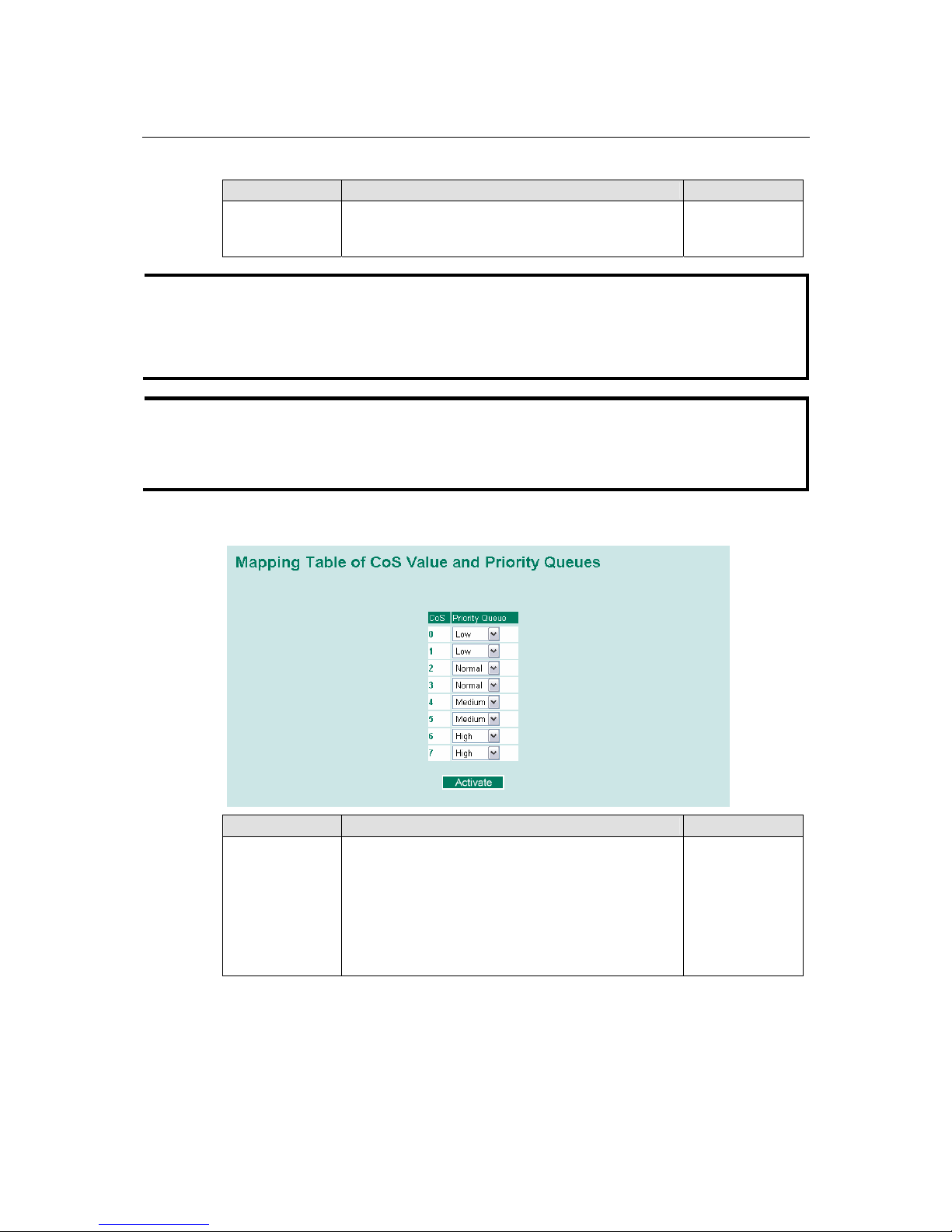
EDS-510A Series User’s Manual Featured Functions
3-43
Inspect COS
Setting Description Factory Defau l t
Enable/Disable Select the option to enable EDS-510A to inspect the
802.1p COS tag in the MAC frame to determine the
priority of each frame.
Enable
NOTE
The priority of an ingress frame is determined in order by:
1. Port Highest Priority
2. Inspect TOS
3. Inspect CoS
NOTE
The designer can enable these classifications individually or in combination. For instance, if a
‘hot,’ higher priority port is required for a network design, “Inspect TOS” and “Inspect CoS”
can be disabled. This setting leaves only port default priority active, which results in all ingress
frames being assigned the same priority on that port.
CoS Mapping
Setting Description Factory
Low/Normal/
Medium/High
Set the mapping table of different CoS values to 4
different egress queues.
0: Low
1: Low
2: Normal
3: Normal
4: Medium
5: Medium
6: High
7: High
Page 59

EDS-510A Series User’s Manual Featured Functions
3-44
TOS/DiffServ Mapping
Setting Description Factory Default
Low/Normal/
Medium/High
Set the mapping table of different TOS values to 4
different egress queues.
1 to 16: Low
17 to 32: Normal
33 to 48: Medium
49 to 64: High
Using Virtual LAN
Setting up Virtual LANs (VLANs) on your EDS-510A increases the efficien cy of your network by
dividing the LAN into logical segments, as opposed to physical segments. In general, VLANs are
easier to manage.
The Virtual LAN (VLAN) Concept
What is a VLAN?
A VLAN is a group of devices that can be located anywhere on a network, but which
communicate as if they are on the same physical segment. With VLANs, you can segment your
network without being restricted by physical connections—a limitation of traditional network
design. As an example, with VLANs you can segment your network according to:
y Departmental groups—You could have one VLAN for the Marketing department, another
for the Finance department, and another for the Development department.
y Hierarchical groups—You could have one VLAN for directors, another for managers, and
another for general staff.
y Usage groups—You could have one VLAN for e-mail users, and another for multimedia
users.
Page 60
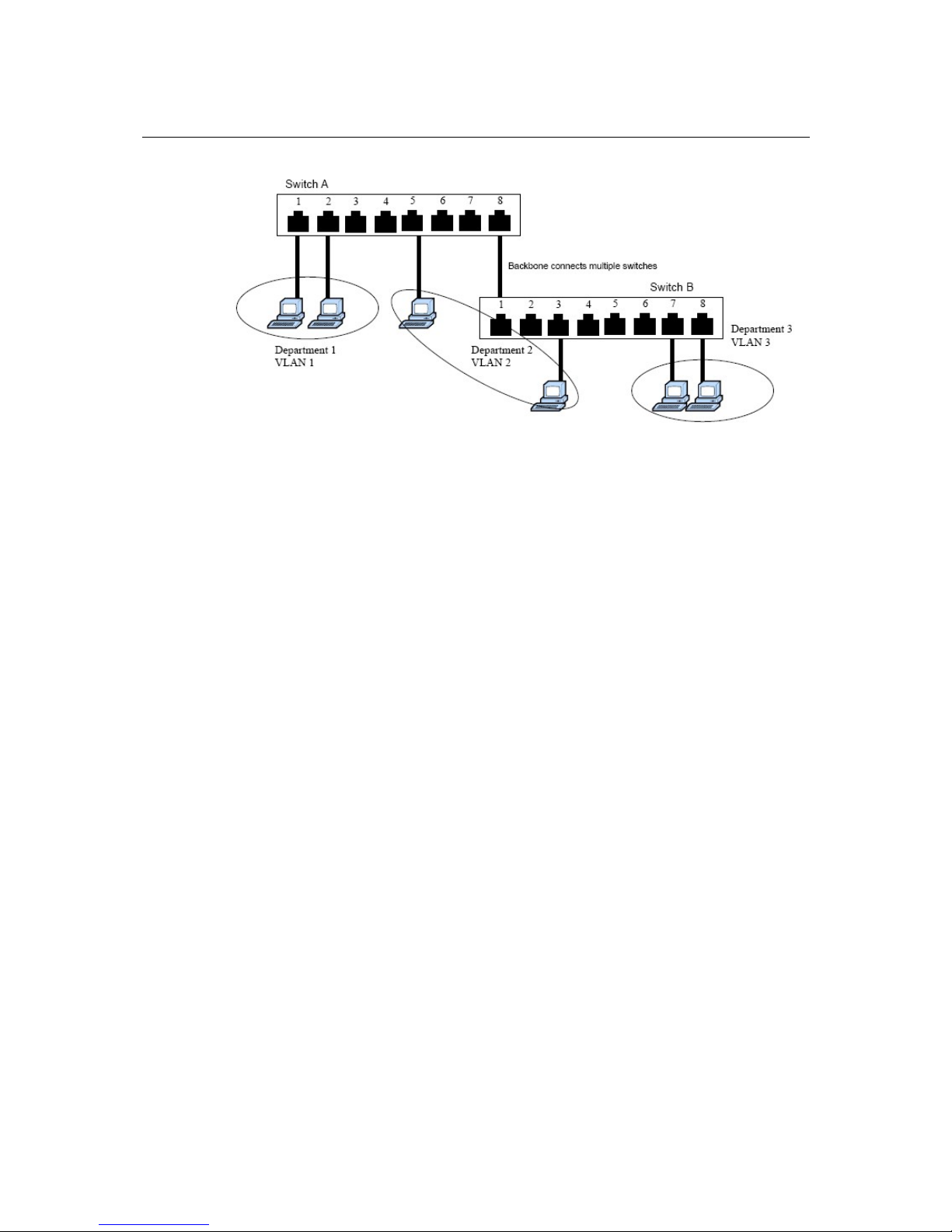
EDS-510A Series User’s Manual Featured Functions
3-45
Benefits of VLANs
The main benefit of VLANs is that they provide a network segmentation system that is far more
flexible than traditional networks. Using VLANs also provides you with three other benefits:
y VLANs ease the relocation of devices on networks: With tra di t i onal networks, network
administrators spend most of their time dealing with moves and changes. If users move to a
different subnetwork, the addresses of each host must be updated manually. With a VLAN
setup, if a host on VLAN Marketing, for example, is moved to a port in another part of the
network, and retains its original subnet membership, you only need to specify that the new
port is on VLAN Marketing. You do not need to carry out any re-cabling.
y VLANs provide extra security: Devices within each VLAN can only communicate with
other devices on the same VLAN. If a device on VLAN Marketing needs to communicate
with devices on VLAN Finance, the traffic must pass through a routing device or Layer 3
switch.
y VLANs help control traffic: With traditional networks, congestion can be caused by
broadcast traffic that is directed to all network devices, regardless of whether or not they need
it. VLANs increase the efficiency of your network because each VLAN can be set up to
contain only those devices that need to communicate with each other.
VLANs and Moxa EtherDevice Switch
Your EDS-510A provides support for VLANs using IEEE Std 802.1Q-1998. This standard allows
traffic from multiple VLANs to be carried across one physical link. The IEEE Std 802.1Q-1998
standard allows each port on your EDS-510A to be placed in:
y Any one VLAN defined on the EDS-510A.
y Several VLANs at the same time using 802.1Q tagging.
The standard requires that you define the 802.1Q VLAN ID for each VLAN on your EDS-510A
before the switch can use it to forward traffic:
Managing a VLAN
A new or initialized EDS-510A contains a single VLAN—the Default VLAN. This VLAN has the
following definition:
y VLAN Name—Management VLAN
y 802.1Q VLAN ID—1 (if tagging is required)
All the ports are initially placed on this VLAN, and it is the only VLAN that allows you to access
the management software of the EDS-510A over the network.
Page 61

EDS-510A Series User’s Manual Featured Functions
3-46
Communication Between VLANs
If devices connected to a VLAN need to communicate to devices on a different VLAN, a router or
Layer 3 switching device with connections to both VLANs needs to be installed. Communication
between VLANs can only take place if they are all connected to a routing or Layer 3 switching
device.
VLANs: Tagged and Untagged Membership
The EDS-510A supports 802.1Q VLAN tagging, a system that allows traffic for multiple VLANs
to be carried on a single physical (backbone, trunk) link. When setting up VLANs you need to
understand when to use untagged and tagged membership of VLANs. Simply put, if a port is on a
single VLAN it can be an untagged member, but if the port needs to be a member of multiple
VLANs, tagged membership must be defined.
A typical host (e.g., clients) will be untagged members of one VLAN, defined as “Access Port” in
the EDS-510A, while inter-switch connections will be tagged members of all VLANs, defined as
“Trunk Port” in the EDS-510A.
The IEEE Std 802.1Q-1998 defines how VLANs ope rate wi thi n an open packet -switched network.
An 802.1Q compliant packet carries additional information that allows a switch to determine
which VLAN the port belongs. If a frame is carrying the additional information, it is known as a
tagged frame.
To carry multiple VLANs across a single physical (backbone, trunk) link, each packet must be
tagged with a VLAN identifier so that the switches can identify which packets belong to which
VLAN. To communicate between VLANs, a router must be used.
The EDS-510A supports two types of VLAN port settings:
y Access Port: The port connects to a single device that is not tagged. The user must define the
default port PVID that determines to which VLAN the device belongs. Once the ingress
packet of this Access Port egresses to another Trunk Port (the port needs all packets to carry
tag information), the EDS-510A will insert this PVID into this packet to help the next 802.1Q
VLAN switch recognize it.
y Trunk Port: The port connects to a LAN that consists of untagged devices/tagged devices
and/or switches and hubs. In general, the traffic of the Trunk Port must have a Tag. Users can
also assign PVID to a Trunk Port. The untagged packet on the Trunk Port will be assigned the
port default PVID as its VID.
The following section illustrates how to use these ports to set up different applications.
Page 62

EDS-510A Series User’s Manual Featured Functions
3-47
Sample Applications of VLANs using Moxa EDS-510A
Port 3 (Trunk Port, PVID 1)
VLAN 5 Untagged Device
VLAN 3 Untagged
Device
VLAN 4 Untagged
Device
VLAN 5 Untagged Device
VLAN 2 Untagged
Device
VLAN 4 Tagged Device, VID 4
VLAN 3 Tagged Device, VID 3
VLAN 2 Untagged
Device
VLAN 2 Untagged
Device
Device A Switch A Switch B
Device C
Device B
Device D
Device E
Device F
Device G
Device H
Device I
Port 1 (Access Port
PVID 5)
Port 7 (Access Port
PVID 4)
Port 5 (Access Port
PVID 3)
Port 4 (Access
Port PVID 2)
Port 2 (Trunk Port PVID 2,
Fixed VLAN (Tagged)=3,4)
Port 6 (Access Port PVID 5)
HUB
In this application,
y Port 1 connects a single untagged device and assigns it to VLAN 5; it should be configured as
“Access Port” with PVID 5.
y Port 2 connects a LAN with two untagged devices belonging to VLAN 2. One tagged device
with VID 3 and one tagged device with VID 4. It should be configured as “Trunk Port” with
PVID 2 for untagged device and Fixed VLAN (Tagged) with 3 and 4 for tagged device. Since
each port can only have one unique PVID, all untagged devices on the same port can only
belong to the same VLAN.
y Port 3 connects with another switch. It should be configured as “Trunk Port.” GVRP protocol
will be used through the Trunk Port.
y Port 4 connects a single untagged device and assigns it to VLAN 2; it should be configured as
“Access Port” with PVID 2.
y Port 5 connects a single untagged device and assigns it to VLAN 3; it should be configured as
“Access Port” with PVID 3.
y Port 6 connect a single untagged device and assigns it to VLAN 5; it should be configured as
“Access Port” with PVID 5.
y Port 7 connects a single untagged device and assigns it to VLAN 4; it should be configured as
“Access Port” with PVID 4.
After proper configuration:
y Packets from device A will travel through “Trunk Port 3” with tagged VID 5. Switch B will
recognize its VLAN, pass it to port 6, and then remove tags received successfully by device G,
and vice versa.
y Packets from device B and C will travel through “Trunk Port 3” with tagged VID 2. Switch B
recognizes its VLAN, passes it to port 4, and then removes tags received successfully by
device F, and vice versa.
Page 63
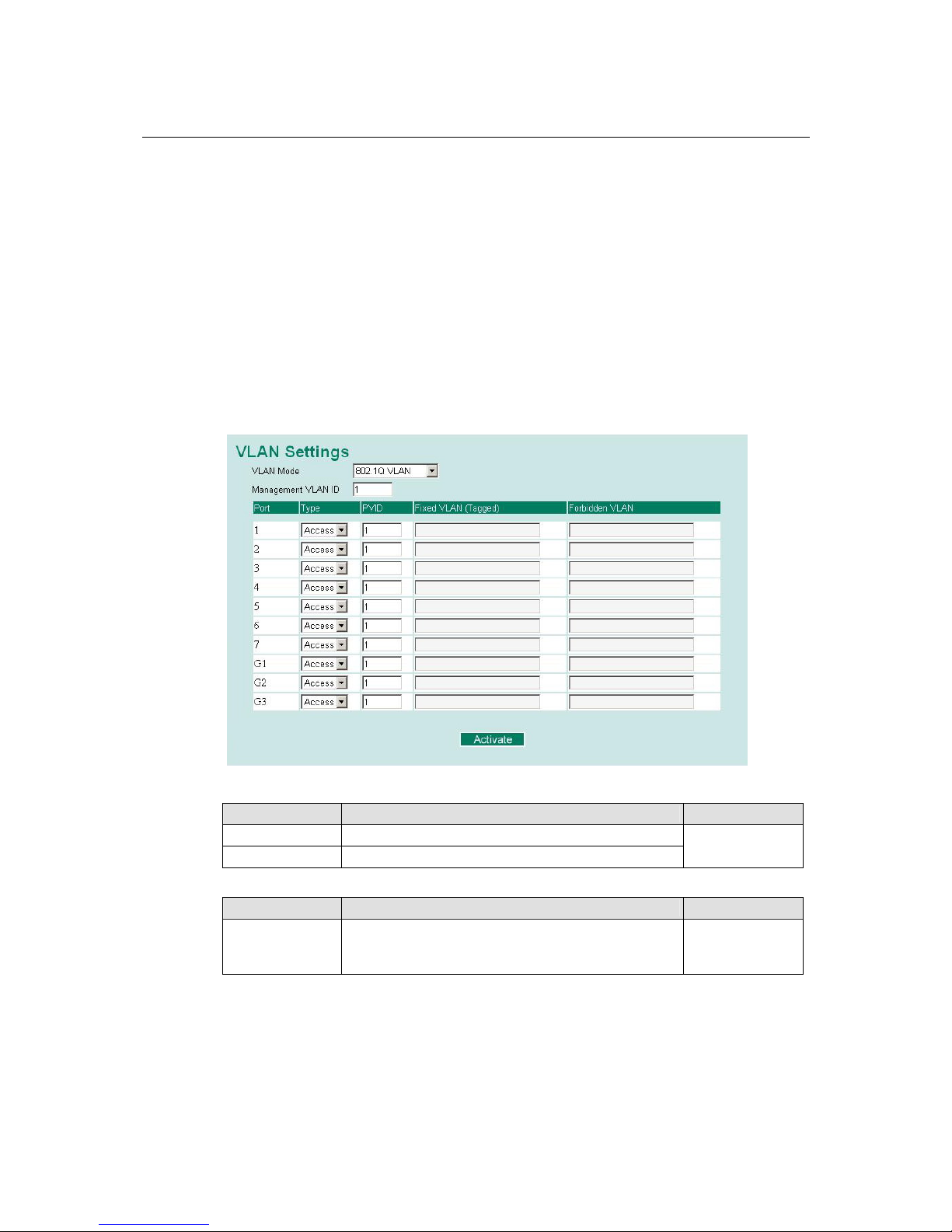
EDS-510A Series User’s Manual Featured Functions
3-48
y Packets from device D will travel through “Trunk Port 3” with tagged VID 3. Switch B will
recognize its VLAN, pass to port 5, and then remove tags received successfully by device H.
Packets from device H will travel through “Trunk Port 3” with PVID 3. Switch A will
recognize its VLAN and pass it to port 2, but will not remove tags received successfully by
device D.
y Packets from device E will travel through “Trunk Port 3” with tagged VID 4. Switch B will
recognize its VLAN, pass it to port 7, and then remove tags received successfully by device I.
Packets from device I will travel through “Trunk Port 3” with tagged VID 4. Switch A will
recognize its VLAN and pass it to port 2, but will not remove tags received successfully by
device E.
Configuring Virtual LAN
VLAN Settings
To configure the EDS-510A’s 802.1Q VLAN, use the VLAN Settings page to configure th e ports.
VLAN Mode
Setting Description Factory Default
802.1Q VLAN Set VLAN mode to 802.1Q VLAN
Port-based VLAN Set VLAN mode to Port-based VLAN
802.1Q VLAN
Management VLAN ID
Setting Description Factory Default
VLAN ID
ranges from
1 to 4094
Set the management VLAN of this EDS-510A. 1
Page 64

EDS-510A Series User’s Manual Featured Functions
3-49
Port Type
Setting Description Factory Default
Access This port type is used to connect single devices without
tags.
Trunk Select “Trunk” port type to connect another 802.1Q
VLAN aware switch or another LAN that combines
tagged and/or untagged devi ces and/ o r ot her
switches/hubs.
Access
ATTENTION
For communication redundancy in the VLAN environment, set “Redundant Port,” “Coupling
Port,” and “Coupling Control Port” as “Trunk Port,” since these ports act as the “backbone” to
transmit all packets of different VLANs to different EDS-510A units.
Port PVID
Setting Description Factory Default
VID range from 1
to 4094
Set the port default VLAN ID for untagged devices that
connect to the port.
1
Fixed VLAN List (Tagged)
Setting Description Factory Default
VID range from 1
to 4094
This field will be active only when selecting the “Trunk”
port type. Set the other VLAN ID for tagged devices that
connect to the “Trunk” port. Use commas to separate
different VIDs.
None
Forbidden VLAN List
Setting Description Factory Default
VID range from 1
to 4094
This field will be active only when selecting the “Trunk”
port type. Set the VLAN IDs that will not be supported
by this trunk port. Use commas to separate different
VIDs.
None
Page 65

EDS-510A Series User’s Manual Featured Functions
3-50
To configure the EDS-510A’s Port-based VLAN, use the VLAN Setting page to configure the
ports.
VLAN Mode
Setting Description Factory Default
802.1Q VLAN Set VLAN mode to 802.1Q VLAN
Port-based VLAN Set VLAN mode to Port-based VLAN
802.1Q VLAN
Port
Setting Description Factory Default
Enable/Disable Set port to specific VLAN Group. Enable
(all ports belong to
VLAN1)
VLAN Table
In 802.1Q VLAN table, you can review the VLAN groups that were created, Joined Access Ports,
and Trunk Ports, and in Port-based VLAN table, you can review the VLAN group and Joined port.
Page 66

EDS-510A Series User’s Manual Featured Functions
3-51
NOTE
The physical network can have a maximum of 64 VLAN settings.
Using Multicast Filtering
Multicast filtering improves the performance of networks that carry multicast traffic. This section
explains multicasts, multicast filtering, and how multicast filtering can be implemented on your
EDS-510A.
The Concept of Multicast Filtering
What is an IP Multicast?
A multicast is a packet sent by one host to multiple hosts. Only those hosts that belong to a
specific multicast group will receive the multicast. If the network is set up correctly, a multicast
can only be sent to an end-station or a subset of end-stations on a LAN or VLAN that belong to
the multicast group. Multicast group members can be distributed across multiple subnets, so that
multicast transmissions can occur within a campus LAN or over a WAN. In addition, networks
that support IP multicast send only one copy of the desired information across the network until
the delivery path that reaches group members diverges. To make more efficient use of network
bandwidth, it is only at these points that multicast packets are duplicated and forwarded. A
multicast packet has a multicast group address in the destination address field of the packet’s IP
header.
Benefits of Multicast
The benefits of using IP multicast are that it:
y Uses the most efficient, sensible method to deliver the same information to many receivers
with only one transmission.
y Reduces the load on the source (for example, a server) since it will not need to produce
several copies of the same data.
y Makes efficient use of network bandwidth and scales well as the number of multicast group
members increases.
y Works with other IP protocols and services, such as Quality of Service (QoS).
Multicast transmission makes more sense and is more efficient than unicast transmission for some
applications. For example, multicasts are often used for video-conferenci n g, since hi g h vol umes of
traffic must be sent to several end-stations at the same time, but where broadcasting the traffic to
all end-stations would cause a substantial reduction in network performance. Furthermore, several
industrial automation protocols, such as Allen-Bradley, EtherNet/IP, Siemens Profibus, and
Foundation Fieldbus HSE (High Speed Ethernet), use multicast. These industrial Ethernet
protocols use publisher/subscri ber com munications models by multicasting packets that could
flood a network with heavy traffic. IGMP Snooping is used to prune multicast traffic so that it
travels only to those end destinations that require the traffic, reducing the amount of traffic on the
Ethernet LAN.
Multicast Filtering
Multicast filtering ensures that only end-stations that have joined certain groups receive multicast
traffic. With multicast filtering, network devices only forward multicast traffic to the ports that are
connected to registered end-stations. The following two figures illustrate how a network behaves
without multicast filtering, and with multicast filtering.
Page 67

EDS-510A Series User’s Manual Featured Functions
3-52
Network without multicast filtering
12345678
Serial ports
Console LAN
910111213141516
IGMP Group2
Group 1 Multicast Stream Group 2 Multicast Stream
IGMP Group1 IGMP Group2 IGMP Group1
All hosts receive the multicast traffic, even if they don’t need it.
Network with multicast filtering
IGMP Group2
Group 1 Multicast Stream Group 2 Multicast Stream
IGMP Group1 IGMP Group2 IGMP Group1
Hosts only receive dedicated traffic from other hosts belonging to the same group.
Multicast Filtering and Moxa EtherDevice Switch
The EDS-510A has three ways to achieve multicast filtering: IGMP (Internet Group Management
Protocol) Snooping, GMRP (GARP Multicast Registration Protocol), and adding a static multicast
MAC manually to filter multicast traffic automatically.
IGMP (Internet Group Management Protocol)
Snooping Mode
Snooping Mode allows your switch to forward multicast packets only to the appropriate ports. The
switch “snoops” on exchanges between hosts and an IGMP device, such as a router, to find those
ports that want to join a multicast group, and then configures its filters accordingly.
Page 68

EDS-510A Series User’s Manual Featured Functions
3-53
Query Mode
Query mode allows the EDS-510A to work as the Querier if it has the lowest IP address on the
subnetwork to which it belongs. IGMP querying is en abled by default on the EDS-510A to help
prevent interoperability issues with some multicast routers that may not follow the lowest IP
address election method. Enable query mode to run multicast sessions on a network that does not
contain IGMP routers (or queriers).
NOTE
The EDS-510A is compatible with any device that conforms to the IGMP v2 and IGMP v3
device protocol.
IGMP Multicast Filtering
IGMP is used by IP-supporting network devices to register hosts with multicast groups. It can be
used on all LANs and VLANs that contain a multicast capable IP router, and on other network
devices that support multicast filtering. IGMP works as follows:
1. The IP router (or querier) periodically sends query packets to all end-stations on the LANs or
VLANs that are connected to it. For networks with more than one IP router, the router with
the lowest IP address is the querier. A switch with IP address lower than the IP address of any
other IGMP queriers connected to the LAN or VLAN can become the IGMP querier.
2. When an IP host receives a query packet, it sends a report packet back that identifies the
multicast group that the end-station would like to join.
3. When the report packet arrives at a port on a switch with IGMP Snooping enabled, the switch
knows that the port should forward traffic for the multicast group, and then proceeds to
forward the packet to the router.
4. When the router receives the report packet, it registers that the LAN or VLAN requires traffic
for the multicast groups.
5. When the router forwards traffic for the multicast group to the LAN or VLAN, the switches
only forward the traffic to ports that received a report packet.
GMRP (GARP Multicast Registration Protocol)
The EDS-510A supports IEEE 802.1D-1998 GMRP (GARP Multicast Registration Protocol),
which differs from IGMP (Internet Group Management Protocol). GMRP is a MAC-based
multicast management protocol, whereas IGMP is IP-based. GMRP provides a mechanism that
allows bridges and end stations to register or de-register Group membership information
dynamically. GMRP functions similarly to GVRP, except that GMRP registers multicast addresses
on ports. When a port receives a GMRP-join message, it will register the multicast address to its
database if the multicast address is not registered, and all the multicast packets with that multicast
address are able to be forwarded from this port. When a port receives a GMRP-leave message, it
will de-register the multicast address from its database, and all the multicast packets with this
multicast address are not able to be forwarded from this port.
Static Multicast MAC
Some devices may only support multicast packets, but not support either IGMP Snooping or
GMRP. The EDS-510A supports adding multicast groups manually to enable multicast filtering.
Enabling Multicast Filtering
Use the serial console or Web interface to enable or disable IGMP Snooping and IGMP querying.
If IGMP Snooping is not enabled, then IP multicast traffic is always forwarded, flooding the
network.
Page 69
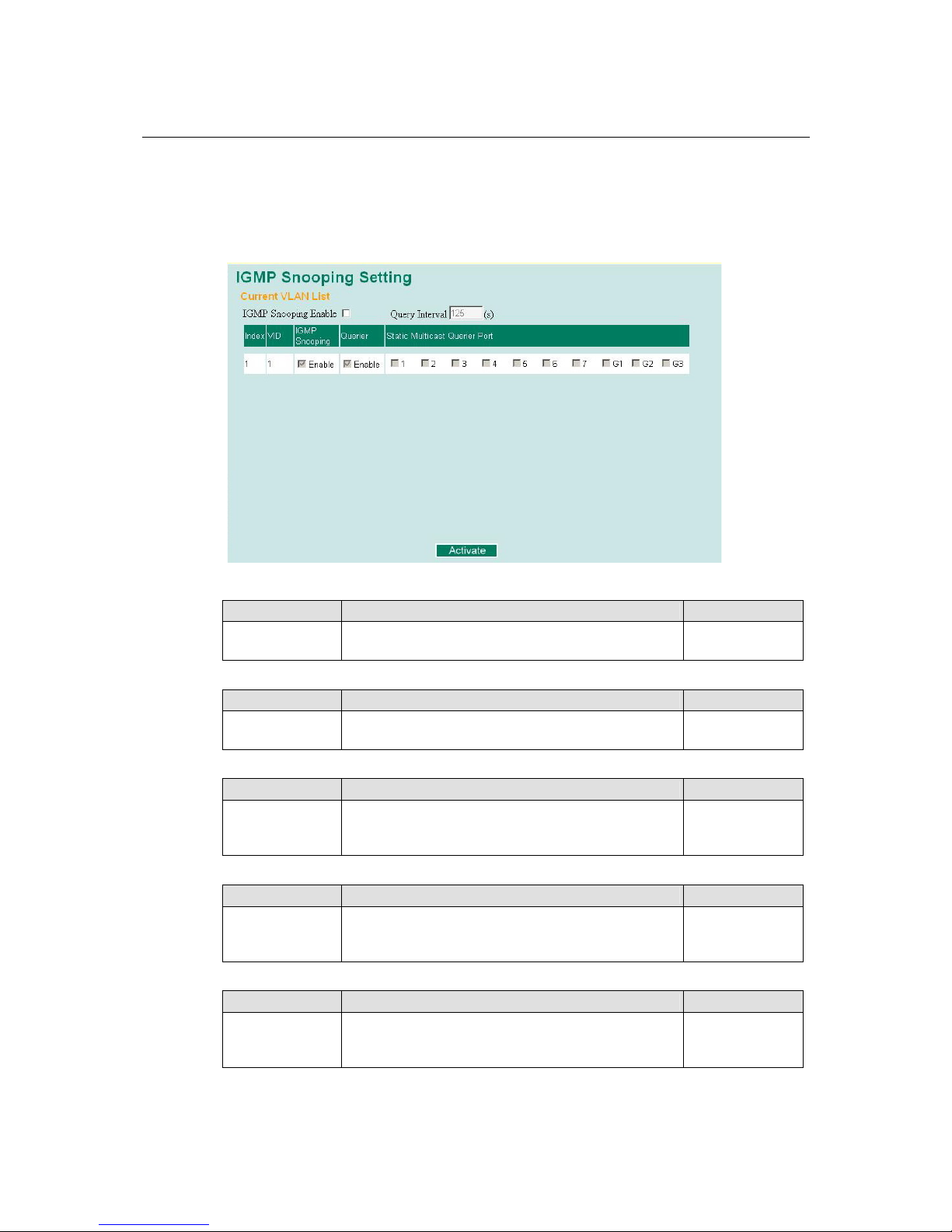
EDS-510A Series User’s Manual Featured Functions
3-54
Configuring IGMP Snooping
IGMP Snooping provides the ability to prune multicast traffic so that it travels only to those end
destinations that require that traffic, thereby reducing the amount of traffic on the Ethernet LAN.
IGMP Snooping Settings
IGMP Snooping Enable
Setting Description Factory Default
Enable/Disable Select the option to enable the IGMP Snooping function
globally.
Disabled
Query Interval
Setting Description Factory Default
Numerical value
input by user
Set the query interval of the Querier function globally.
Valid settings are from 20 to 600 seconds.
125 seconds
IGMP Snooping
Setting Description Factory Default
Enable/Disable Select the option to enable the IGMP Snooping function
per VLAN.
Enabled if IGMP
Snooping Enabled
Globally
Querier
Setting Description Factory Default
Enable/Disable Select the option to enable the EDS-510A’s querier
function.
Enabled if IGMP
Snooping is
Enabled Globally
Static Multicast Router Port
Setting Description Factory Default
Select/Deselect Select the option to select which ports will connect to
the multicast routers. It’s active only when IGMP
Snooping is enabled.
Disabled
Page 70

EDS-510A Series User’s Manual Featured Functions
3-55
NOTE
At least one switch must be designated the Querier or enable IGMP snooping and GMRP when
enabling Turbo Ring and IGMP snooping simultaneously.
IGMP Table
The EDS-510A displays the current active IGMP groups that were detected.
The information includes VID, Auto-learned Multicast Router Port, Static Multicast Router
Port, Querier Connected Port, and the IP and MAC addresses of active IGMP groups.
Add Static Multicast MAC
If required, the EDS-510A also supports adding multicast groups manually.
Add New Static Multicast Address to the List
Setting Description Factory Default
MAC Address Inpu t the multicast MAC address of this host. None
MAC Address
Setting Description Factory Default
integer Input the number of the VLAN to which the host with
this MAC Address belongs.
None
Join Port
Setting Description Factory Default
Select/Deselect Select the appropriate options to select the join ports for
this multicast group.
None
Page 71

EDS-510A Series User’s Manual Featured Functions
3-56
Configuring GMRP
GMRP is a MAC-based multicast management protocol, whereas IGMP is IP-based. GMRP
provides a mechanism that allows bridges and end stations to register or un-register Group
membership information dynamically.
GMRP enable
Setting Description Factory Default
Enable/Disable Select the option to enable the GMRP function for the
port listed in the Port column
Disable
GMRP Table
The EDS-510A displays the current active GMRP groups that were detected.
Setting Description
Fixed Ports This multicast address is defined by static multicast.
Learned Ports This multicast address is learned by GMRP.
Using Bandwidth Management
In general, one host should not be allowed to occupy unlimited bandwidth, particularly when the
device malfunctions. For example, so-called “broadcast storms” could be caused by an
incorrectly configured topology, or a malfunctioning device. The EDS-510A series not only
prevents broadcast storms, but can also be configured to a different ingress rate for all packets,
giving administrators full control of their limited bandwidth to prevent undesirable effects caused
by unpredictable faults.
Page 72

EDS-510A Series User’s Manual Featured Functions
3-57
Traffic Rate Limiting Settings
Ingress
Setting Description Factory Default
Ingress rate Select the ingress rate for all packets from the following
options: Not Limited, 128K, 256K, 512K, 1M, 2M, 4M,
8M
N/A
Using Port Access Control
The EDS-510A provides two kinds of Port-Based Access Controls. One is Static Port Lock and the
other is IEEE 802.1X.
Static Port Lock
The EDS-510A can also be configured to protect static MAC addresses for a specific port. With
the Port Lock function, these locked ports will not learn any additional addresses, but only allow
traffic from preset static MAC addresses, helping to block crackers and careless usage.
IEEE 802.1X
The IEEE 802.1X standard defines a protocol for client/server-based access control and
authentication. The protocol restricts unauthorized clients from connecting to a LAN through ports
that are open to the Internet, and which otherwise would be readily accessible. The purpose of the
authentication server is to check each client that requests access to the port. The client is only
allowed access to the port if the client’s permission is authenticated.
The IEEE 802.1X Concept
Three components are used to create an authentication mechanism based on 802.1X standards:
Client/Supplicant, Authentication Server, and Authenticator.
Supplicant: The end station that requests access to the LAN and switch services and responds to
the requests from the switch.
Authentication server: The server that performs the actual authentication of the supplicant.
Authenticator: Edge switch or wireless access point that acts as a proxy between the supplicant
and the authentication server, requesting identity information from the supplicant, verifying the
information with the authentication server, and relaying a response to the supplicant.
Page 73

EDS-510A Series User’s Manual Featured Functions
3-58
The EDS-510A acts as an authenticator in the 802.1X environment. A supplicant and an
authenticator exchange EAPOL (Extensible Authentication Protocol over LAN) frames with each
other. We can either use an external RADIUS server as the authentication server, or implement the
authentication server in the EDS-510A by using a Local User Database as the authentication
look-up table. When we use an external RADIUS server as the authentication server, the
authenticator and the authentication server exchange EAP frames between each other.
Authentication can be initiated either by the supplicant or the authenticator . When the supplicant
initiates the authentication process, it sends an “EAPOL-Start” frame to the authenticator. When
the authenticator initiates the authentication process or when it receives an “EAPOL Start” frame,
it sends an “EAP Request/Identity” frame to ask for the username of the supplicant. The following
actions are described below:
Message Exchange
Authentication
server
(RADIUS)
Client
EAPOL-Start
EAP-Request/Identity
EAP-Response/Identity
EAP-Request/OTP
EAP-Response/OTP
EAP-Success
EAPOL-Logoff
Port Authorized
Port Unauthorized
RADIUS Access-Request
RADIUS Access-Challenge
RADIUS Access-Request
RADIUS Access-Accept
1. When the supplicant receives an “EAP Request/Identity” frame, it sends an “EAP
Response/Identity” frame with its username back to the authenticator.
2. If the RADIUS server is used as the authentication server, the authenticator relays the “EAP
Response/Identity” frame from the supplicant by encapsulating it into a “RADIUS
Access-Request” frame and sends to the RADIUS server. When the authentication server
receives the frame, it looks up its database to check if the username exists. If the username is
not present, the authentication server replies with a “RADIUS Access-Reject” frame to the
authenticator if the server is a RADIUS server or just indicates failure to the authenticator if
the Local User Database is used. The authenticator sends an “EAP-Failure” frame to the
supplicant.
3. The RADIUS server sends a “RADIUS Access-Challenge,” which contains an “EAP Request”
with an authentication type to the authenticator to ask for the passwo rd from the client. RFC
2284 defines several EAP authentication types, such as “MD5-Challenge,” “One-Time
Password,” and “Generic Token Card.” Currently, only “MD5-Challenge” is supp orted. If the
Local User Database is used, this step is skipped.
4. The authenticator sends an “EAP Request/MD5-Challenge” frame to the supplicant. If the
RADIUS server is used, th e “EAP Request/MD5-Challenge” frame is retrieved directly from
the “RADIUS Access-Challenge” frame.
Page 74
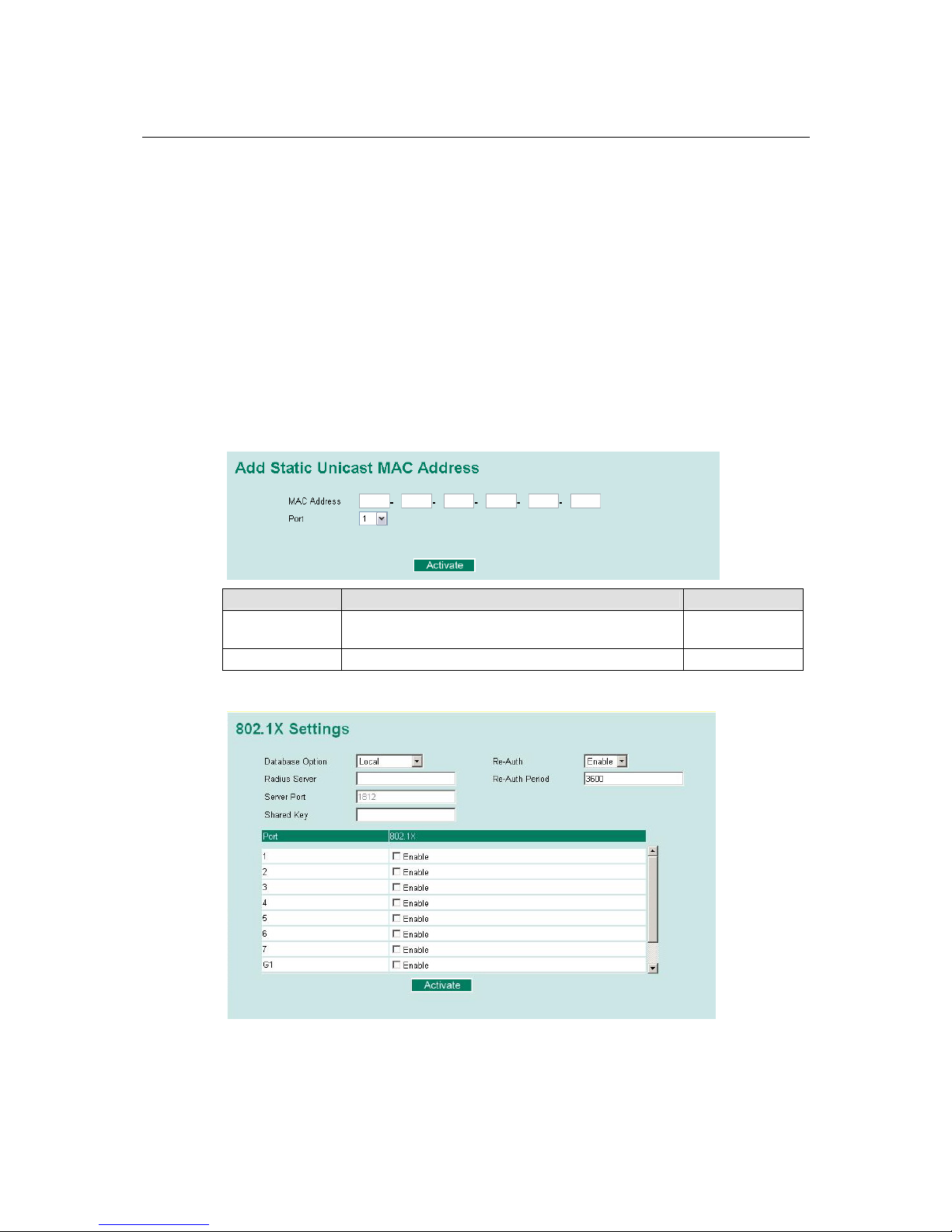
EDS-510A Series User’s Manual Featured Functions
3-59
5. The supplicant responds to the “EAP Request/MD5-Challenge” by sending an “EAP
Response/MD5-Challenge” frame that encapsulates the user’s password using the MD5 hash
algorithm.
6. If the RADIUS server is used as the authentication server, the authenticator relays the “EAP
Response/MD5-Challenge” frame from the supplicant by encapsulating it into a “RADIUS
Access-Request” frame along with a “Shared Secret,” which must be the same within the
authenticator and the RADIUS server, and sends the frame to the RADIUS server. The
RADIUS server checks against the password with its database, and replies with “RADIUS
Access-Accept” or “RADIUS Access-Reject” to the authenticator. If the Local User Database
is used, the password is checked against its database and indicates success or failure to the
authenticator.
7. The authenticator sends “EAP Success” or “EAP Failure” based on the reply from the
authentication server.
Configuring Static Port Lock
The EDS-510A supports adding unicast groups manually if required .
Setting Description Factory Default
MAC Address Add the static unicast MAC address into the address
table.
None
Port Fix the static address with a dedicated port. 1
Configuring IEEE 802.1X
Page 75

EDS-510A Series User’s Manual Featured Functions
3-60
Database Option
Setting Description Factory Default
Local
(Max. 32 users)
Select this option when setting the Local User Database
as the authentication database.
Local
Radius Select this option to set an external RADIUS server as
the authentication database. The authentication
mechanism is “EAP-MD5.”
Local
Radius, Local Select this option to make an external RADIUS server as
the authentication database with first priority. The
authentication mechanism is “EAP-MD5.” The first
priority is to set the Local User Database as the
authentication database.
Local
Radius Server
Setting Description Factory Default
IP address or
domain name
The IP address or domain name of the RADIUS server localhost
Server Port
Setting Description Factory Default
Numerical The UDP port of the RADIUS Server 1812
Shared Key
Setting Description Factory Default
alphanumeric
(Max. 40
characters)
A key to be shared between the external RADIUS server
and the EDS-510A. Both ends must be configured to use
the same key.
None
Re-Auth
Setting Description Factory Default
Enable/Disable Select to require re-authentication of the client after a
preset time period of no activity has elapsed.
Disable
Re-Auth Period
Setting Description Factory Default
Numerical
(60-65535 sec.)
Specify how frequently the end stations need to reenter
usernames and passwords in order to stay connected.
3600
802.1X
Setting Description Factory Default
Enable/Disable Select the option under the 802.1X column to enable
IEEE 802.1X for one or more ports. All end stations
must enter usernames and passwords before access to
these ports is allowed.
Disable
Page 76
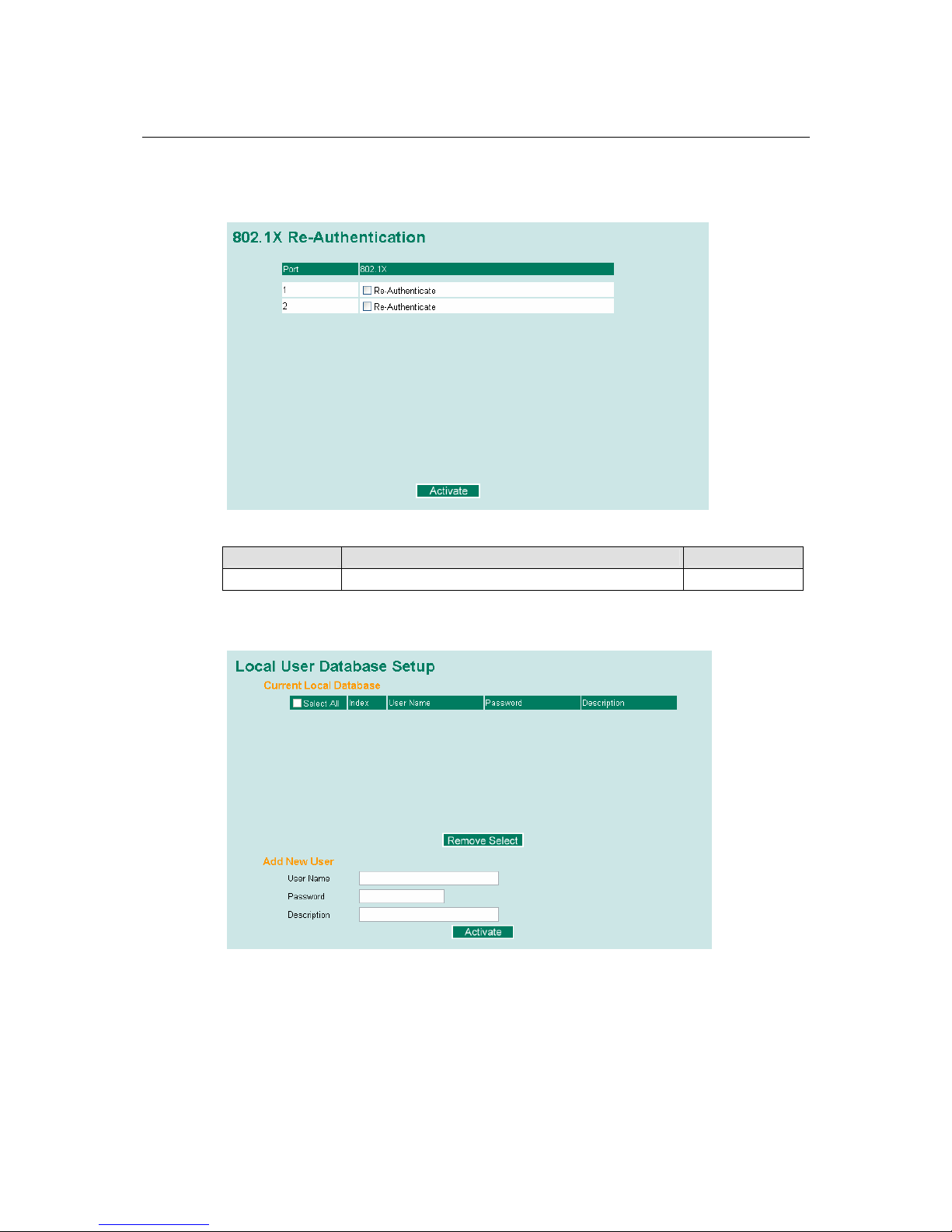
EDS-510A Series User’s Manual Featured Functions
3-61
802.1X Re-Authentication
The EDS-510A can force connected devices to be re-authorized manually.
802.1X Re-Authentication
Setting Description Factory Default
Enable/Disable Select the option to enable 802.1X Re-Authentication Disable
Local User Database Setup
When setting the Local User Database as the authentication database, set the database first.
Page 77
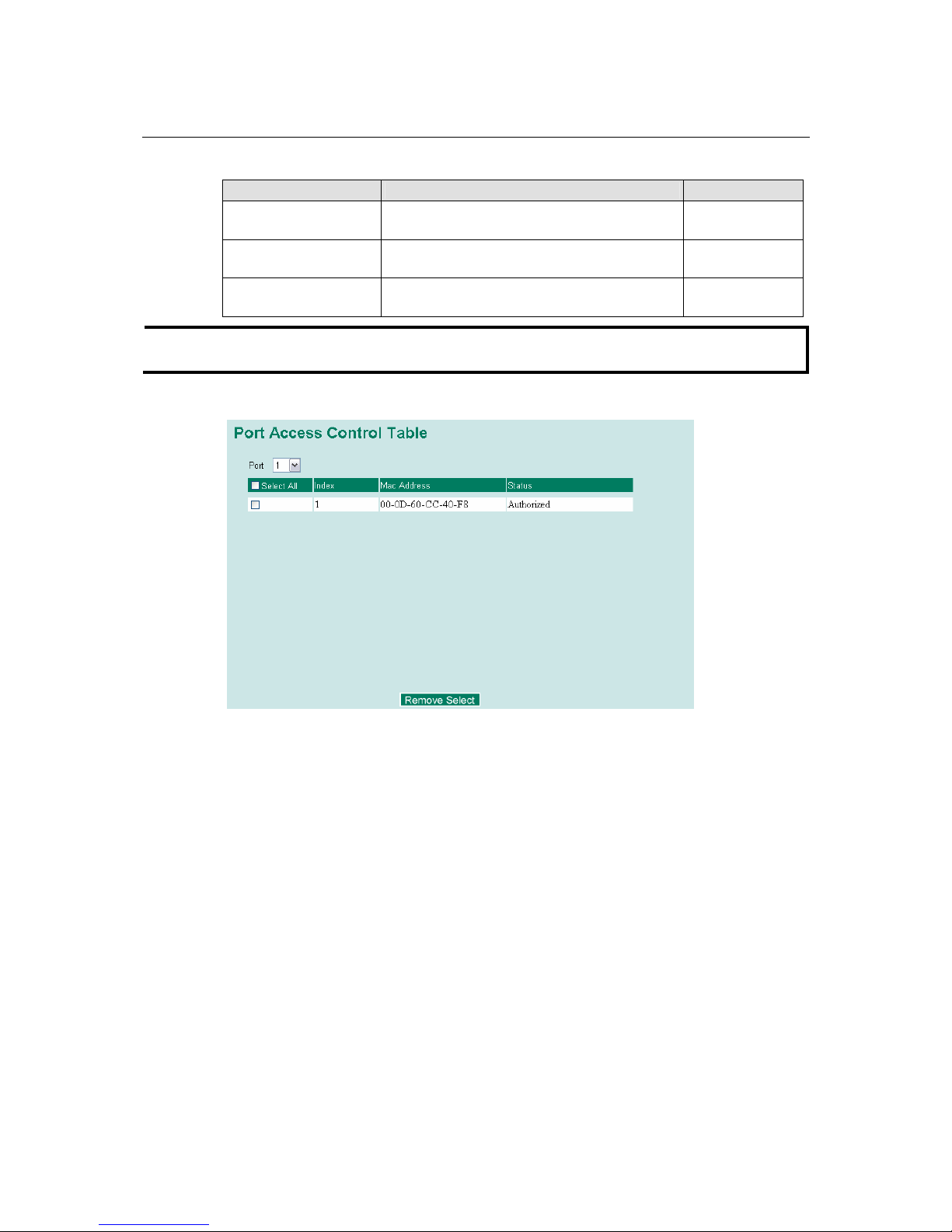
EDS-510A Series User’s Manual Featured Functions
3-62
Local User Database Setup
Setting Description Factory Default
User Name
(Max. 30 characters)
User Name for Local User Database None
Password
(Max. 16 characters)
Password for Local User Database None
Description
(Max. 30 characters)
Description for Local User Database None
NOTE
The user name for the Local User Database is case-insensitive.
Port Access Control Table
The port status will indicate whether the access is authorized or unauthorized.
Using Auto Warning
Since industrial Ethernet devices are often located at the endpoints of a system, these devices will
not always know what is happening elsewhere on the network. This means that an industrial
Ethernet switch that connects to these devices must provide system maintainers with real-time
alarm messages. Even when control engineers are out of the control room for an extended period
of time, they can still be informed of the status of devices almost instantaneously when exceptions
occur. The EDS-510A supports different appro a ches to warn engineers automatically, such as by
using email and relay output. It also supports two digital inputs to integrate sensors into your
system to automate alarms using email and relay output.
Page 78

EDS-510A Series User’s Manual Featured Functions
3-63
Configuring Email Warning
The Auto Email Warning function uses e-mail to alert the user when certain user-configured
events take place.
Three basic steps are required to set up the Auto Warning function:
1. Configuring Email Event Types
Select the desired Event types from the Console or Web Browser Event type page (a
description of each event type is given later in the Email Alarm Events setting subsection).
2. Configuring Email Settings
To configure the EDS-510A’s email setup from the Console interface or browser interface,
enter your Mail Server IP/Name (IP address or name), Account Name, Account Password,
Retype New Password, and the email address to which warning messages will be sent.
3. Activate your settings and if necessary, test the email
After configuring and activating your EDS-510A’s Event Types an d Email Setup, you can use
the Test Email function to see if your e-mail addresses and mail server address have been
properly configured.
Event Type
Event Types can be divided into two basic groups: System Events and Port Events. System
Events are related to the overall function of the switch, whereas Port Events are related to the
activity of a specific port.
Page 79
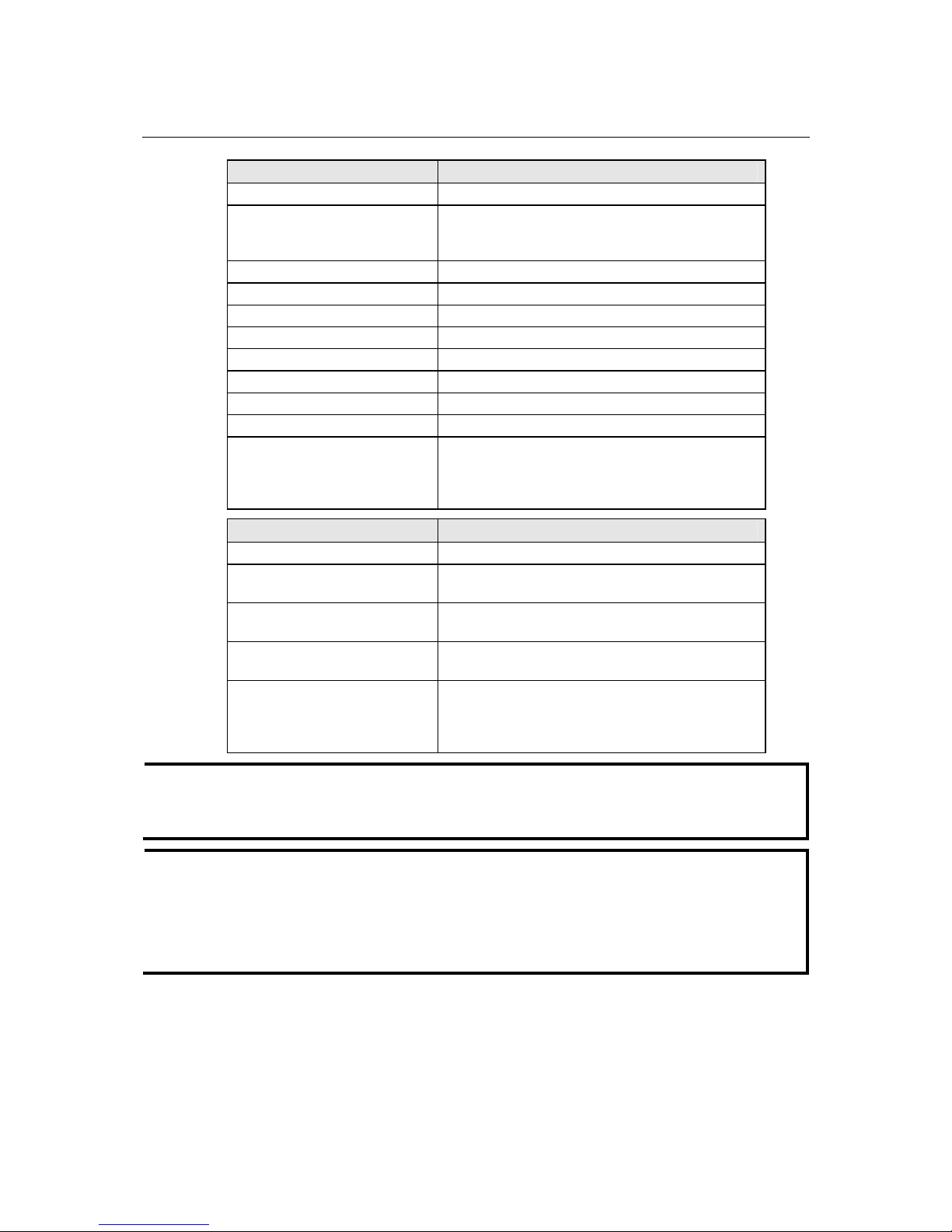
EDS-510A Series User’s Manual Featured Functions
3-64
System Events Warning e-mail is sent when…
Switch Cold Start Power is cut off and then reconnected.
Switch Warm Start The EDS-510A is rebooted, such as when network
parameters are changed (IP address, subnet mask,
etc.).
Power Transition (OnÆOff) The EDS-510A is powered down.
Power Transition (OffÆOn) The EDS-510A is powered up.
DI1 (OnÆOff) Digital Input 1 is triggered by on to off transition
DI1 (OffÆOn) Digital Input 1 is triggered by off to on transition
DI2 (OnÆOff) Digital Input 2 is triggered by on to off transition
DI2 (OffÆOn) Digital Input 2 is triggered by off to on transition
Configuration Change Activated A configuration item has been changed.
Authentication Failure An incorrect password is entered.
Comm. Redundancy Topology
Changed
Spanning Tree Protocol switches have changed their
position (applies only to the root of the tree).
The Master of the Turbo Ring has changed or the
backup path is activated.
Port Events Warning e-mail is sent when…
Link-ON The port is connected to another device.
Link-OFF
The port is disconnected (e.g., the cable is pulled out,
or the opposing device shuts down).
Traffic-Overload
The port’s traffic surpasses the Traffic-Threshold for
that port (provided this item is Enabled).
Traffic-Threshold (%)
Enter a non-zero number if the port’s
Traffic-Overload item is Enabled.
Traffic-Duration (sec.)
A Traffic-Overload warning is sent every
Traffic-Duration seconds if th e average
Traffic-Threshold is surpassed during that time
period.
NOTE
The Traffic-Overload, Traffic-Threshold (%), and Traffic-Duration (sec.) Port Event items
are related. If you Enable the Traffic-Overload event, then be sure to enter a non-zero
Traffic-Threshold percentage, as well as a Traffic-Durati on bet ween 1 and 300 seconds.
NOTE
Warning e-mail messages will have the sender field formatted in the form:
Moxa_EtherDevice_Switch_0001@Switch_Location
where Moxa_EtherDevice_Switch is the default Switch Name, 0001 is the EDS-510A’s serial
number, and Switch_Location is the default Server Location.
Refer to the Basic Settings section to see how to modify Switch Name and Switch Location.
Page 80
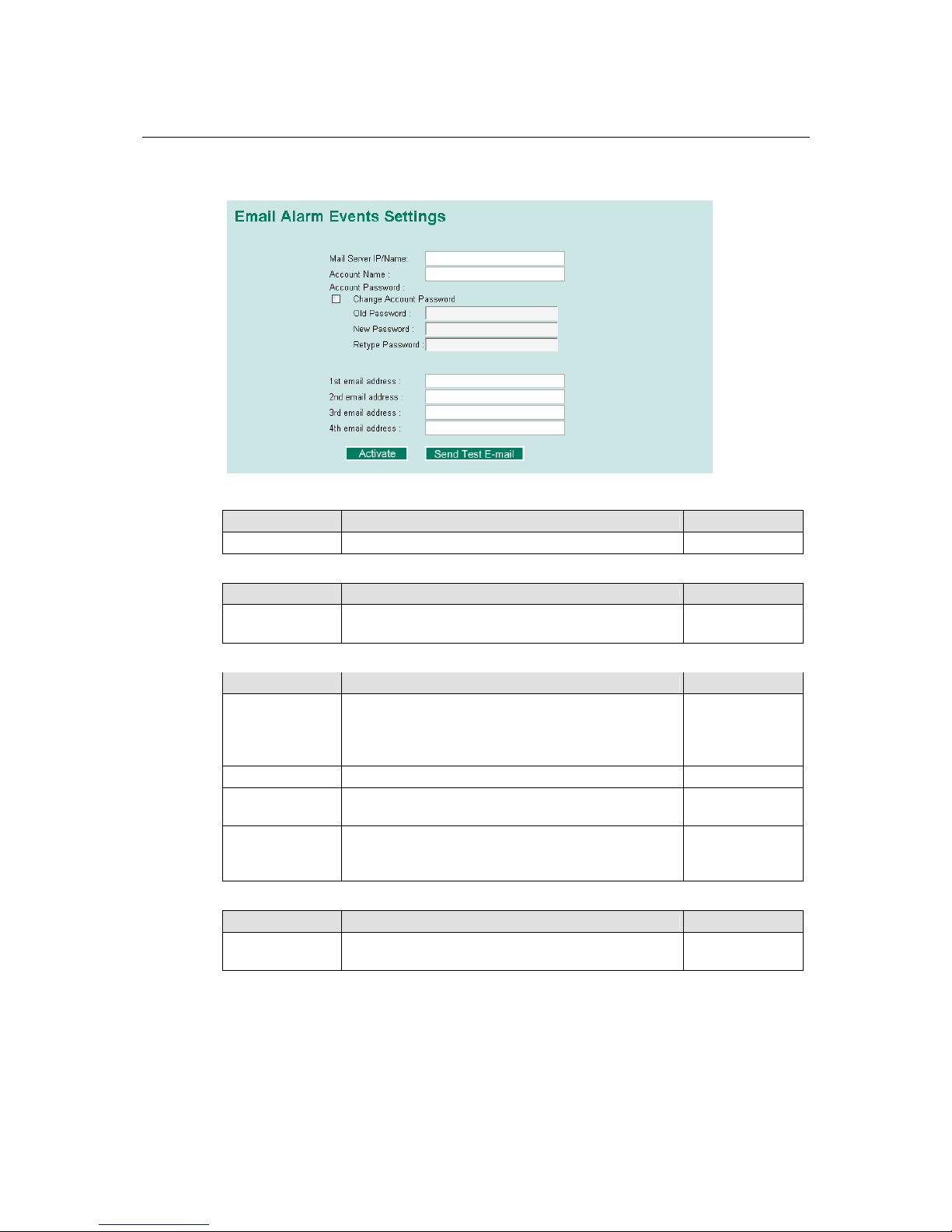
EDS-510A Series User’s Manual Featured Functions
3-65
Email Setup
Mail Server IP/Name
Setting Description Factory Default
IP address The IP Address of your email server. None
Account Name
Setting Description Factory Default
Max. 45
Characters
Your email account name (typically your user name) None
Password Setting
Setting Description Factory Default
Disable/Enable to
change Password
To reset the Password from the Web Browser interface,
click the Change password check-box, type the Old
Password, type the New Password, retype the New
password, and then click Activate; Max. 45 Characters.
Disable
Old Password Type the current password when changing the password None
New Password Type new password when enabled to change password;
Max. 45 Characters.
None
Retype Password If you type a new password in the Password field, you
will be required to retype the password in the Retype
new password field before updating the new password.
None
Email Address
Setting Description Factory Default
Max. 30
characters
You can set up to 4 email addresses to receive alarm
emails from the EDS-510A.
None
Send Test Email
After configuring the email settings, you should first click Activate to activate those settings, and
then click Send Test Email to verify that the settings are correct.
Page 81

EDS-510A Series User’s Manual Featured Functions
3-66
NOTE
Auto warning e-mail messages will be sent through an authentication protected SMTP server that
supports the CRAM-MD5, LOGIN, and PLAIN methods of SASL (Simple Authentication and
Security Layer) authentication mechanism.
We strongly recommend not entering your Account Name and Account Password if auto warning
e-mail messages can be delivered without using an authentication mechanism.
Configuring Relay Warning
The Auto Relay Warning function uses relay output to alert the user when certain user-configured
events take place. There are two basic steps required to set up the Relay Warning function:
1. Configuring Relay Event Types
Select the desired Event types from the Console or Web Browser Event type page (a
description of each event type is given later in the Relay Alarm Events setting subsection).
2. Activate your settings
After completing the configuration procedure, you will need to activate your EDS-510A’s
Relay Event Types.
Event Setup
Event Types can be divided into two basic groups: System Events and Port Events. System
Events are related to the overall function of the switch, whereas Port Events are related to the
activity of a specific port. The EDS-510A supports two relay outputs. You can configure which
relay output is related to which events. This helps administrators identify the importance of the
different events.
Page 82

EDS-510A Series User’s Manual Featured Functions
3-67
System Events Warning Rel a y output is triggered when…
Power Transition (OnÆOff) The EDS-510A is powered on.
Power Transition (OffÆOn) The EDS-510A is powered down.
DI1 (OnÆOff) Digital Input 1 is triggered by on to off transition
DI1 (OffÆOn) Digital Input 1 is triggered by off to on transition
DI2 (OnÆOff) Digital Input 2 is triggered by on to off transition
DI2 (OffÆOn) Digital Input 2 is triggered by off to on transition
Turbo Ring Break (Ring Master
Only)
When the EDS-510A is the Master of this Turbo
Ring, and the Turbo Ring is disconnected.
Port Events Warning e-mail is sent when…
Link-ON The port is connected to another device.
Link-OFF
The port is disconnected (e.g., the cable is pulled out,
or the opposing device shuts down).
Traffic-Overload
The port’s traffic surpasses the Traffic-Threshold for
that port (provided this item is Enabled).
Traffic-Threshold (%)
Enter a non-zero number if the port’s
Traffic-Overload item is Enabled.
Traffic-Duration (sec.)
A Traffic-Overload warning is sent every
Traffic-Duration seconds if th e average
Traffic-Threshold is surpassed during that time
period.
NOTE
The Traffic-Overload, Traffic-Threshold (%), and Traffic-Duration (sec) Port Event items
are related. If you Enable the Traffic-Overload event, then be sure to enter a non-zero
Traffic-Threshold percentage, as well as a Traffic-Durati on bet ween 1 and 300 seconds.
Override relay alarm settings
Select this option to override the relay warning setting temporarily. Releasing the relay output will
allow administrators to fix any problems with the warning condition.
Warning List
Use this table to see if any relay alarms have been issued.
Page 83

EDS-510A Series User’s Manual Featured Functions
3-68
Using Line-Swap-Fast-Recovery
The Line-Swap Fast Recovery function, which is enabled by default, allows the EDS-510A to
return to normal operation extremely quickly after devices are unplugged and then re-plugged into
different ports. The recovery time is on the order of a few milliseconds (compare this with
standard commercial switches for which the recovery time could be on the order of several
minutes). To disable the Line-Swap Fast Recovery function, or to re-enable the function after it
has already been disabled, access either the Console utility’s Line-Swap recovery page, or the
Web Browser interface’s Line-Swap fast recovery page, as the following figure shows:
Configuring Line-Swap Fast Recovery
Enable Line-Swap-Fast-Recovery
Setting Description Factory Default
Enable/Disable Select this option to enable the
Line-Swap-Fast-Recovery function
Enable
Using Set Device IP
To reduce the effort required to set up IP addresses, the EDS-510A series comes equipped with
DHCP/BOOTP server and RARP protocol to set up IP addresses of Ethernet-enabled devices
automatically.
When enabled, the Set device IP function allows the EDS-510A to assign specific IP addresses
automatically to connected devices that are equIPped with DHCP Client or RARP protocol. In
effect, the EDS-510A acts as a DHCP server by assigning a connected device with a specific IP
address stored in its internal memory. Each time the connected device is switched on or rebooted,
the EDS-510A sends the device the desired IP address.
Perform the following steps to use the Set device IP function:
Page 84

EDS-510A Series User’s Manual Featured Functions
3-69
STEP 1—set up the connected devices
Set up those Ethernet-enabled devices connected to
the EDS-510A for which you would like IP addresses
to be assigned automatically. The devices must be
configured to obtain their IP address automatically.
The devices’ configuration utility should include a
setup page that allows you to choose an option
similar to Obtain an IP address automatically.
For example, Windows’ TCP/IP Properties window
is shown at the right. Although your device’s
configuration utility may look quite a bit different,
this figure should give you some idea of what to look
for.
You also need to decide to which of the EDS-510A’s
ports your Ethernet-enabled devices will be
connected. You will need to set up each of these ports
separately, as described in the following step.
STEP 2
Configure the EDS-510A’s Set device IP function, either from the Console utility or from the
Web Browser interface. In either case, you simply need to enter the Desired IP for each port that
needs to be configured.
STEP 3
Be sure to activate your settings before exiting.
• When using the Web Browser interface, activate by clicking Activate.
• When using the Console utility, activate by first highlighting the Activate menu option, and
then press Enter. You should receive the Set device IP settings are now active! (Press any
key to continue) message.
Configuring Set Device IP
Desired IP Address
Setting Description Factory Default
IP Address Set the desired IP of connected devices. None
Page 85

EDS-510A Series User’s Manual Featured Functions
3-70
Using Diagnosis
The EDS-510A provides two important tools for administrators to diagnose network systems.
Mirror Port
The Mirror port function can be used to monitor data being transmitted through a specific port.
This is done by setting up another port (the mirror port) to receive the same data being transmitted
from, or both to and from, the port under observation. This allows the network administrator to
“sniff” the observed port and thus keep tabs on network activity.
Perform the following steps to set up the Mirror Port function:
STEP 1
Configure the EDS-510A’s Mirror Port function from either the Console utility or Web Browser
interface. You will need to configure three settings:
Monitored Port
Select the port number of the port whose network activity will be
monitored.
Mirror Port
Select the port number of the port that will be used to monitor the
activity of the monitored port.
Watch Direction
Select one of the following three watch direction options:
y Input data stream
Select this option to monitor only those data packets coming in
through the EDS-510A’s port.
y Output data stream
Select this option to monitor only those data packets being sent out
through the EDS-510A’s port.
y Bi-directional
Select this option to monitor data packets both coming into, and
being sent out through, the EDS-510A’s port.
STEP 2
Be sure to activate your settings before exiting.
• When using the Web Browser interface, activate by clicking Activate.
• When using the Console utility, activate by first highlighting the Activate menu option, and
then press Enter. You should receive the Mirror port settings are now active! (Press any
key to continue) message.
Page 86

EDS-510A Series User’s Manual Featured Functions
3-71
Ping
The Ping function uses the ping command to give users a simple but powerful tool for
troubleshooting network problems. The function’s most unique feature is that even though the
ping command is entered from the user’s PC keyboard, the actual ping command originates from
the EDS-510A itself. In this way, the user can essentially control the EDS-510A and send ping
commands out through its ports.
To use the Ping function, type in the desired IP address, and then press Enter from the Console
utility, or click Ping when using the Web Browser interface.
Using Monitor
You can monitor statistics in real time from the EDS-510A’s web console and serial console.
Monitor by Switch
Access the Monitor by selecting “System” from the left selection bar. Monitor by System allows
the user to view a graph that shows the combined data transmission activity of all the EDS-510A’s
18 ports. Click one of the four options—Total Packets, TX Packets, RX Packets, or Error
Packets—to view transmission activity of specific types of packets. Recall that TX Packets are
packets sent out from the EDS-510A, RX Packets are packets received from connected devices,
and Error Packets are packets that did not pass TCP/IP’s error checking algorithm. The Total
Packets option displays a graph that combines TX, RX, and TX Error, RX Error Packets activity.
The graph displays data transmission activity by showing Packets/s (i.e., packets per second, or
pps) versus sec. (seconds). In fact, three curves are displayed on the same graph: Unicast packets
(in red color), Multicast packets (in green color), and Broadcast packets (in blue color). The
graph is updated every few seconds, allowing the user to analyze data transmission activity in
real-time.
Page 87

EDS-510A Series User’s Manual Featured Functions
3-72
Monitor by Port
Access the Monitor by Port function by selecting ALL 10/100M or 1G Ports or Port i, in which
i= 1, 2, …, G2, from the left pull-down list. The Port i options are identical to the Monitor by
System function discussed above, in that users can view graphs that show All Packets, TX Packets,
RX Packets, or Error Packets activity, but in this case, only for an individual port.
The All Ports
option is essentially a graphical display of the individual port activity that can be viewed with th e
Console Monitor function discussed above. The All Ports option shows three vertical bars for each
port. The height of the bar represents Packets/s for the type of packet, at the instant the bar is
being viewed. That is, as time progresses, the height of the bar moves up or down so that the user
can view the change in the rate of packet transmission. The blue colored bar shows Unicast
packets, the red colored bar shows Multicast packets, and the orange colored bar shows
Broadcast packets. The graph is updated every few seconds, allowing the user to analyze data
transmission activity in real-time.
Using the MAC Address Table
This section explains the information provided by the EDS-510A’s MAC address table.
The MAC Address table can be configured to display the following EDS-510A MAC address
groups.
ALL Select this item to show all EDS-510A MAC addresses
ALL Learned Select this item to show all EDS-510A Learned MAC addresses
ALL Static Lock Select this item to show all EDS-510A Static Lock MAC addresses
ALL Static Select this item to show all EDS-510A Static/Static Lock /Static
Multicast MAC addresses
ALL Static
Multicast
Select this item to show all EDS-510A Static Multicast MAC
addresses
Port x Select this item to show all MAC addresses of dedicated ports
Page 88

EDS-510A Series User’s Manual Featured Functions
3-73
The table will display the following information:
MAC This field shows the MAC address
Type This field shows the type of this MAC address
Port This field shows the port that this MAC address belongs to
Using Event Log
Bootup This field shows how many times the EDS-510A has been rebooted or cold started.
Date The date is updated based on how the current date is set in the “Basic Setting” page.
Time The time is updated based on how the current time is set in the “Basic Setting” page.
System
Startup
Time
The system startup time related to this event.
Events Events that have occurre d.
NOTE
The following events will be recorded into the EDS-510A’s Event Log table:
1. Cold start
2. Warm start
3. Configuration change activated
4. Power 1/2 transition (Off Æ On), Power 1/2 transition (On Æ Off)
5. Authentication fail
6. Topology changed
7. Master setting is mismatched
8. DI 1/2 transition (Off Æ On), DI 1/2 transition (On Æ Off)
9. Port traffic overload
10. dot1x Auth Fail
11. Port link off / on
Page 89

EDS-510A Series User’s Manual Featured Functions
3-74
Using Syslog
This function provides the event logs for the syslog server. The function supports 3 configurable
syslog servers and syslog server UDP port numbers. When an event occurs, the event will be sent
as a syslog UDP packet to the specified syslog servers.
Syslog Server 1
Setting Description Factory Default
IP Address Enter the IP address of 1st Syslog Server used by your
network.
None
Port Destination
(1 to 65535)
Enter the UDP port of 1st Syslog Server. 514
Syslog Server 2
Setting Description Factory Default
IP Address Enter the IP address of 2nd Syslog Server used by your
network.
None
Port Destination
(1 to 65535)
Enter the UDP port of 2nd Syslog Server. 514
Syslog Server 3
Setting Description Factory Default
IP Address Enter the IP address of 3rd Syslog Server used by your
network.
None
Port Destination
(1 to 65535)
Enter the UDP port of 3rd Syslog Server. 514
Page 90

EDS-510A Series User’s Manual Featured Functions
3-75
NOTE
The following events will be recorded into the EDS-510A’s Event Log table, and will then be
sent to the specified Syslog Server:
1. Cold start
2. Warm start
3. Configuration change activated
4. Power 1/2 transition (Off Æ On), Power 1/2 transition (On Æ Off)
5. Authentication fail
6. Topology changed
7. Master setting is mismatched
8. DI 1/2 transition (Off Æ On), DI 1/2 transition (On Æ Off)
9. Port traffic overload
10. dot1x Auth Fail
11. Port link off / on
Using HTTPS/SSL
To secure your HTTP access, the EDS-510A supports HTTPS/SSL to encrypt all HTTP traffic.
Perform the following steps to access the EDS-510A’s web browser interface via HTTPS/SSL.
1. Open Internet Explorer and type https://EDS-510A’s IP address in the address field. Press
Enter to establish the connection.
2. Warning messages will pop out to warn the user that the security certificate was issued by a
company they have not chosen to trust.
3. Select Yes to enter the EDS-510A’s web browser interface and access the web browser
interface secured via HTTPS/SSL.
Page 91

EDS-510A Series User’s Manual Featured Functions
3-76
NOTE
Moxa provides a Root CA certificate .After installing this certificate into your PC or notebook,
you can access the web browser interface directly and will not see any warning messages again.
You may download the certificate from the EDS-510A’s CD-ROM.
Page 92

4
4
Chapter 4 EDS Configurator GUI
EDS Configurator is a comprehensive Windows-based GUI that is used to configure and maintain
multiple EDS-510A switches. A suite of useful utilities is available to help you locate the
EDS-510A switches attached to the same LAN as the PC host (regardless of whether or not you
know the IP addresses of the switches), connect to an EDS-510A whose IP address is known,
modify the network configurations of one or multiple EDS-510A switches, and update the
firmware of one or more EDS-510A switches. EDS Configurator is designed to provide you with
instantaneous control of all of your EDS-510A switches, regardless of location. You may
download the EDS Configurator software from Moxa’s website free of charge.
This chapter includes the following sections:
Starting EDS Configurator
Broadcast Search
Search by IP address
Upgrade Firmware
Modify IP Address
Export Configuration
Import Configuration
Unlock Server
Page 93
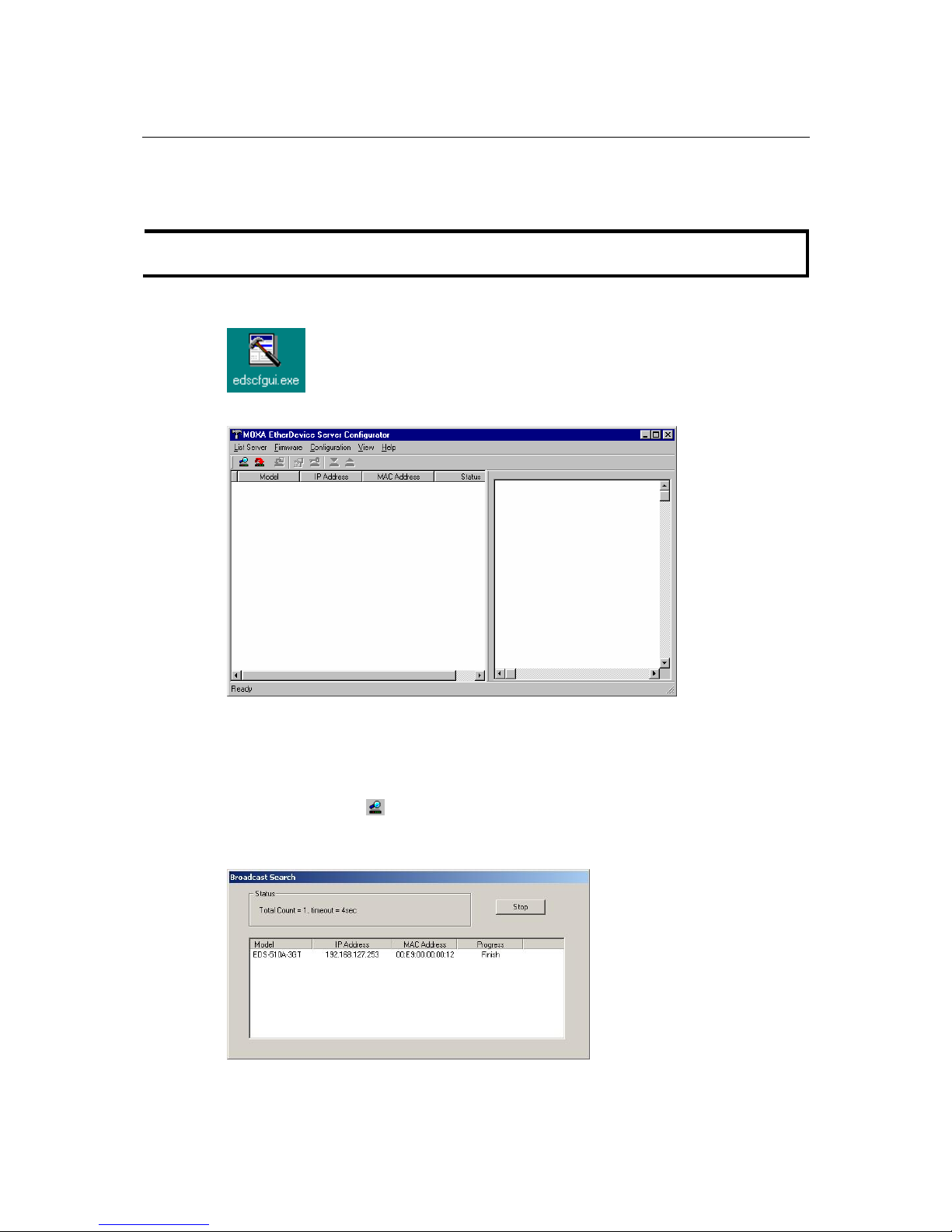
EDS-510A Series User’s Manual EDS Configurator GUI
4-2
Starting EDS Configurator
To start EDS Configurator, locate and then run the executable file edscfgui.exe.
NOTE
You may download the EDS Configurator software from Moxa’s website at www.moxa.com.
For example, if the file was placed on the Windows desktop, it should appear as follows. Simply
double click on the icon to run the program.
The Moxa EtherDevice Server Configurator window will open, as shown below.
Broadcast Search
Use the Broadcast Search utility to search the LAN for all EDS-510A switches that are connected
to the LAN. Note that since the search is done by MAC address, Broadcast Search will not be able
to locate Moxa EtherDevice Servers connected outside the PC host’s LAN. Start by clicking the
Broadcast Search icon
, or by selecting Broadcast Search under the List Server menu.
The Broadcast Search window will open, displaying a list of all switches located on the network ,
as well as the progress of the search.
Page 94
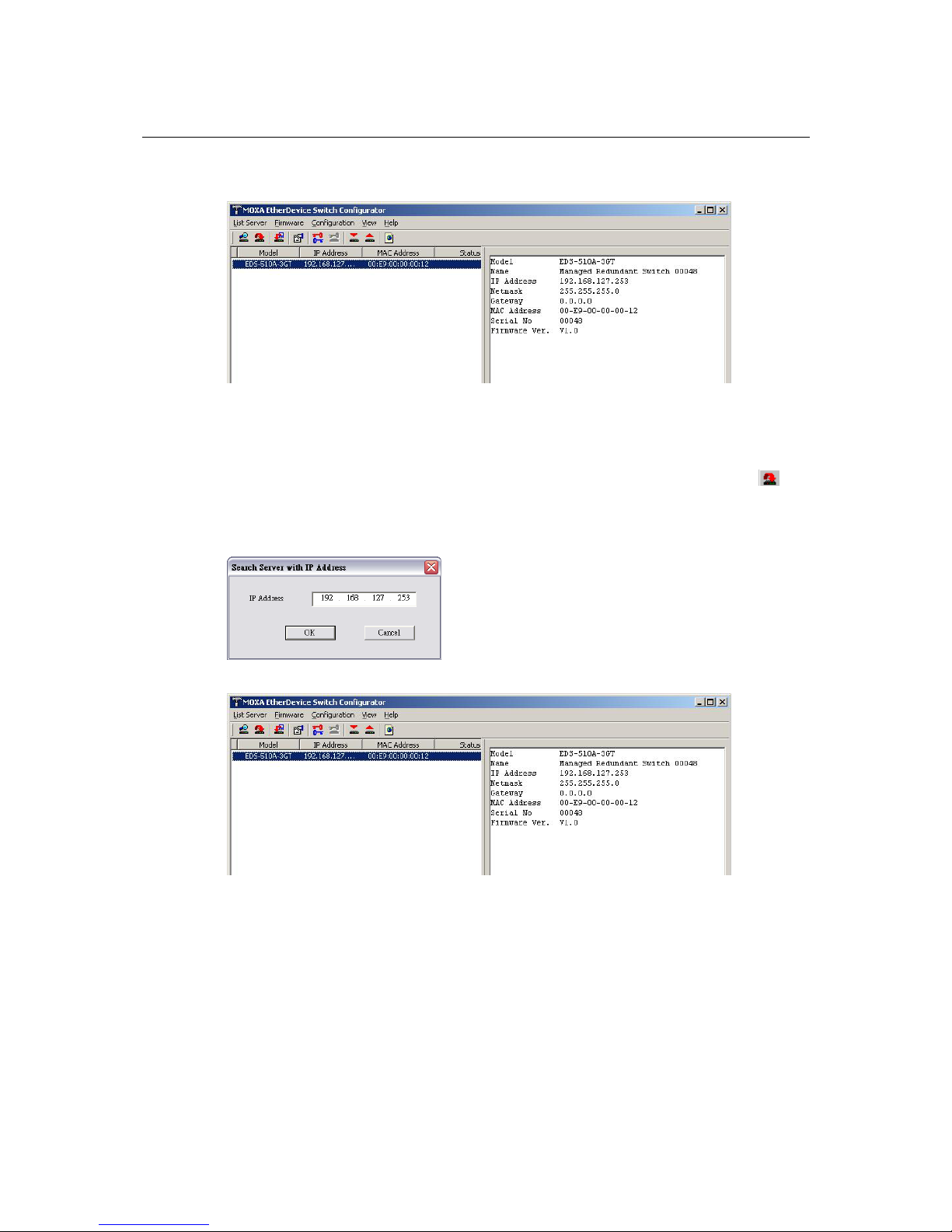
EDS-510A Series User’s Manual EDS Configurator GUI
4-3
Once the search is complete, the Configurator window will display a list of all switches that were
located.
Search by IP address
This utility is used to search for EDS-510A switches one at a time. Note that the search is
conducted by IP address, so you should be able to locate any EDS-510A that is properly connected
to your LAN, WAN, or even the Internet. Start by clicking the Specify by IP address icon
, or
by selecting Specify IP address under the List Server menu.
The Search Server with IP Address window will open. Enter the IP address of the switch you
wish to search for, and then click OK.
Once the search is complete, the Configurator window will add the switch to the list of switches.
Page 95
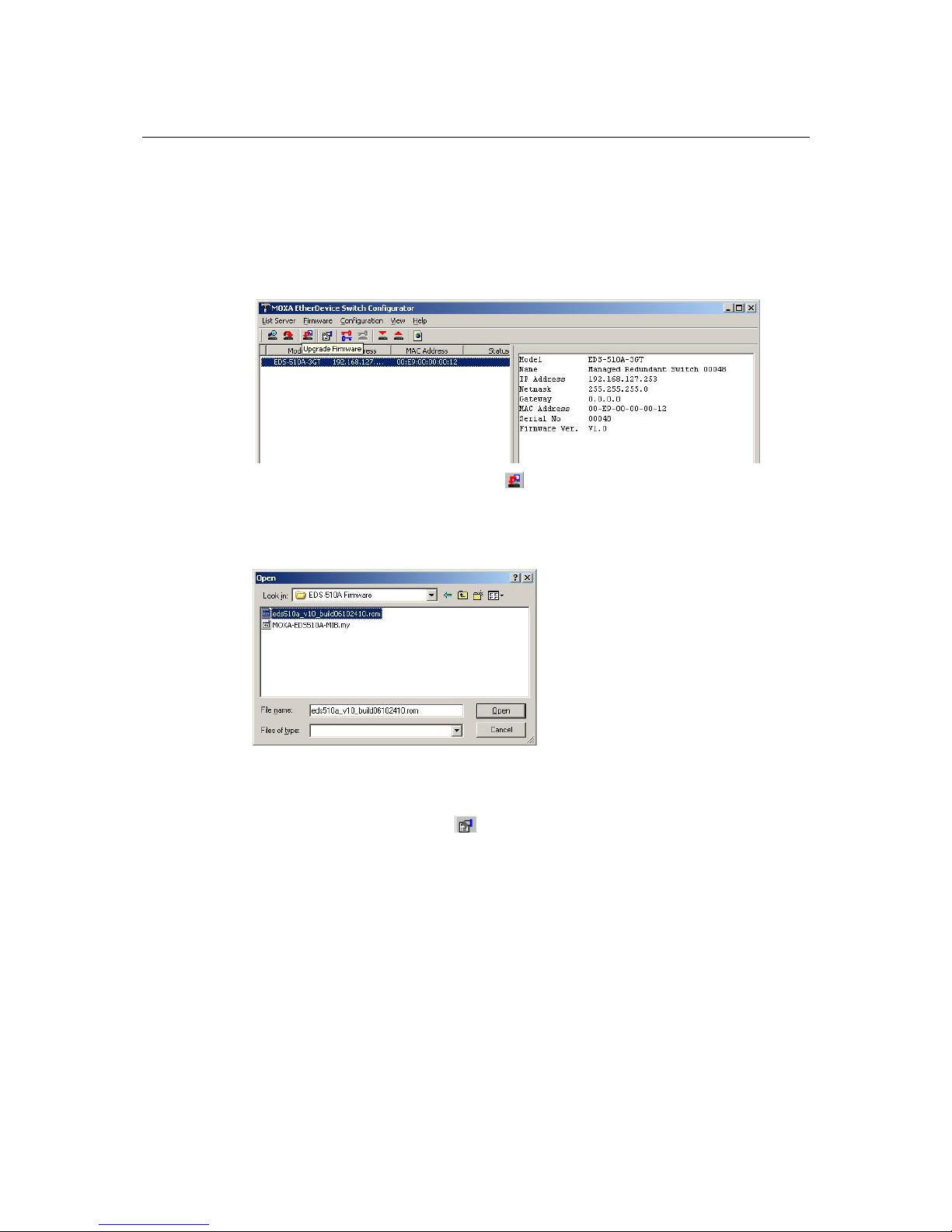
EDS-510A Series User’s Manual EDS Configurator GUI
4-4
Upgrade Firmware
Keep your EDS-510A up to date with the latest firmware from Moxa. Perform the following steps
to upgrade the firmware:
1. Download the updated firmware (*.rom) file from the Moxa website (www.moxa.com).
2. Click the switch (from the Moxa EtherDevice Server Configurator window) whose
firmware you wish to upgrade to highlight it.
3. Click the Upgrade Firmware toolbar icon
, or select Upgrade under the Firmware menu.
If the switch is Locked, you will be prompted to input the switch’s User Name and Password.
4. Use the Open window to navigate to the folder that contains the firmware upgrade file, and
then click the correct “*.rom” file (eds.rom in the example shown below) to select the file.
Click Open to activate the upgrade process.
Modify IP Address
You may use the Modify IP Address function to reconfigure EDS-510A’s network settings. Start
by clicking the Modify IP address icon
, or by selecting Modify IP address under the
Configuration menu.
The Setup Configuration window will open. Checkmark the box to the left of those items that
you wish to modify, and then Disable or Enable DHCP, and enter IP Address, Subnet mask,
Gateway, and DNS IP. Click OK to accept the changes to the configuration.
Page 96

EDS-510A Series User’s Manual EDS Configurator GUI
4-5
Export Configuration
The Export Configuration utility is used to save the entire configuration of a particular
EDS-510A to a text file. Take the following steps to export a configuration:
1. Highlight the switch (from the Server list in the Configurator window’s left pane), and then
click the Export toolbar icon
or select Export Configuration from the Configuration
menu. Use the Open window to navigate to the folder in which you want to store the
configuration, and then type the name of the file in the File name input box. Click Open.
2. Click OK when the Export configuration to file OK message appears.
Page 97

EDS-510A Series User’s Manual EDS Configurator GUI
4-6
3. You may use a standard text editor, such as Notepad under Windows, to view and modify the
newly created configuration file.
Import Configuration
The Import Configuration function is used to import an entire configuration from a text file to
the EDS-510A. This utility can be used to transfer the configuration from one EDS-510A to
another, by first using the Export Configuration function (described in the previous section) to
save a switch configuration to a file, and then using the Import Configuration function. Perform
the following steps to import a configuration:
1. Highlight the server (from the Moxa EtherDevice Switch list in the Configurator window’s
left pane), and then click the Import toolbar icon
, or select Import Configuration from
the Configuration menu.
2. Use the Open window to navigate to the text file that contains the desired configuration. Once
the file is selected, click Open to initiate the import procedure.
Page 98

EDS-510A Series User’s Manual EDS Configurator GUI
4-7
3. The Setup Configuration window will be displayed, with a special note attached at the
bottom. Parameters that have been changed will be activated with a checkmark. You may
make more changes if necessary, and then click OK to accept the changes.
4. Click Yes in response to the following warning message to accept the new settings.
Unlock Server
The Unlock Server function is used to open a password protected switch so that the user can
modify its configuration, import/export a configuration, etc. There are six possible responses under
the Status column. The Status of an EDS-510A indicates how the switch was located (by Moxa
EtherDevice Switch Configurator), and what type of password protection it has.
The six options are as follows (note that the term Fixed is borrowed from the standard fixed IP
address networking terminolo gy ):
y Locked
The switch is password protected, “Broadcast Search” was used to locate it, and the password
has not yet been entered from within the current Configurator session.
y Unlocked
The switch is password protected, “Broadcast Search” was used to locate it, and the password
has been entered from within the current Configurator session. Henceforth during this
Configurator session, activating various utilities for this switch will not require re-entering the
server password.
y Blank
The EDS-510A is not password protected, and “Broadcast Search” was used to locate it.
y Fixed
The EDS-510A is not password protected, and “Search by IP address” was used to locate it manually.
Page 99

EDS-510A Series User’s Manual EDS Configurator GUI
4-8
y Locked Fixed
The EDS-510A is password protected, “Search by IP address” was used to locate it manually, and
the password has not yet been entered from within the current Configurator session.
y Unlocked Fixed
The EDS-510A is password protected, “Search by IP address” was used to locate it manually,
and the password has been entered from within the current Configurator session. Henceforth
during this Configurator session, activating various utilities for this EDS-510A will not
require re-entering the server password.
Follow the steps given below to unlock a locked EDS-510A (i.e., an EDS-510A with Status
“Locked” or “Locked Fixed”). Highlight the server (from the Moxa EtherDevice Switch list in the
Configurator window’s left pane), and then click the Unlock toolbar icon
, or select Unlock
from the Configuration menu.
1. Enter the switch’s User Name and Password when prompted, and then click OK.
2. When the Unlock status window reports Progress as OK, click the Close button in the upper
right corner of the window.
3. The status of the switch will now read either Unlocked or Unlocked Fixed.
Page 100

A
A
Appendix A MIB Groups
The EDS-510A comes with built-in SNMP (Simple Network Management Protocol) agent
software that supports cold/warm start trap, line up/down trap, and RFC 1213 MIB-II.
The standard MIB groups that the EDS-510A series support are:
MIB II.1 – System Group
sysORTable
MIB II.2 – Interfaces Group
ifTable
MIB II.4 – IP Group
ipAddrTable
ipNetToMediaTable
IpGroup
IpBasicStatsGroup
IpStatsGroup
MIB II.5 – ICMP Group
IcmpGroup
IcmpInputStatus
IcmpOutputStats
MIB II.6 – TCP Group
tcpConnTable
TcpGroup
TcpStats
MIB II.7 – UDP Group
udpTable
UdpStats
 Loading...
Loading...