Page 1

McAfee VirusScan
User’s Guide
Version 5.1
Page 2

COPYRIGHT
Copyright © 2000 Network Associates, Inc. and its Affiliated Companies. All Rights Reserved. No part
of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated
into any language in any form or by any means without the written permissio n of Network A ssociates,
Inc.
TRADEMARK ATTRIBUTI ONS
* ActiveHelp, Bomb Shelter, Building a World of Trust, CipherLink, Clean-Up, Cloaking, CNX,
Compass 7, CyberCop, CyberMedia, Data Security Letter, Discover, Distributed Sniffer System, Dr
Solomon’s, Enterprise Secure Cast, First Aid, ForceField, Gauntlet, GMT, GroupShield, HelpDesk,
Hunter, ISDN Tel/Scope, LM 1, LA NGuru, Leadin g Help Desk Technolo gy, Magic Solu tions, Magi cSpy,
MagicTree, Magic University, MagicWin, MagicWord, McAfee, McAfee Associates, MoneyMagic, More
Power To You, Multimedia Cloaking, NetCrypto, NetOctopus, NetRoom, NetSca n, Net Shield, NetShiel d,
NetStalker, Net Tools, Network Associates, Network General, Network Uptime!, NetXRay, Nuts & Bolts,
PC Medic, PCNotary, PGP, PGP (Pretty Good Privacy), PocketScope, Pop-Up, PowerTelnet, Pretty
Good Privacy, PrimeSupport, RecoverKey, RecoverKey-International, ReportMagic, RingFence, Router
PM, Safe & Sound, SalesMagic, SecureCast, Service Level Manager, ServiceMagic, Site Meter, Sniffer,
SniffMaster, SniffNet, Stalker, Statistical Information Retrieval (SIR), SupportMagic, Switch PM,
TeleSniffer, TIS, TMach, TMeg, Tota l Network Security, Total Network Vis ibility, Total Service Desk,
Total Virus Defense, T-POD, Trusted Ma ch, Trusted Ma il, Uninstall er, Virex, Vi rex-PC, Virus Fo rum,
ViruScan, VirusScan, VShi eld, WebScan , Web Shield, W ebS niffer , WebSt alker W ebW all , and ZAC 2000
are registered trademarks of Network Associates and/or its affiliates in the US and/or other countries. All
other registered and unregistered trademarks in this document are the sole property of their respective
owners.
LICENSE AGREEMENT
NOTICE TO ALL USERS: CAREFULLY READ THE FOLLOWING LEGAL AGREEMENT
("AGREEMENT"), FOR THE LICENSE OF SPECIFIED SOFTWARE ("SOFTWARE") BY
NETWORK ASSOCIATES, INC. ("McAfee"). BY CLICKING THE ACCEPT BUTTON OR
INSTALLING THE SOFTWARE, YOU (EITHER AN INDIVIDUAL OR A SINGLE ENTITY)
CONSENT TO BE BOUND BY AND BECOME A PARTY TO THIS AGREEMENT. IF YOU DO
NOT AGREE TO ALL OF THE TERMS OF THIS AGREEMENT, CLICK THE BUTTON THAT
INDICATES THAT YOU DO NOT ACCEPT THE TERMS OF THIS AGREEMENT AND DO NOT
INSTALL THE SOFTWARE. (IF APPLICABLE, YOU MAY RETURN THE PRODUCT TO THE
PLACE OF PURCHASE FOR A FULL REFUND.)
1. License Grant. Subject to the payment of the applicable license fees, and subject to the terms and
conditions of this Agreement, McAfee hereby grants to you a non-exclusive, non-transferable right
to use one copy of the specified version of the Software and the accompanying documentation (the
"Documentation"). You may install one copy of the Software on one computer, workstation,
personal digital assistant, pager, "smart phone" or other electronic device for which the Software
was designed (each, a "Client Device"). If the Software is licensed as a suite or bundle with more
than one specified Software product, this license applies to all such specified Software products,
subject to any restrictions or usage terms specified on the applicable price list or product packaging
that apply to any of such Software products individually.
Issued July 2000/McAfee VirusScan v5.1
Page 3
Table of Contents
Preface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .vii
What happened? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .vii
Why worry? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .vii
Where do viruses come from? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . viii
Virus prehistory . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . viii
Viruses and the PC revolution . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
On the frontier . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .xii
Where next? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xiv
How to protect yourself . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .xv
Chapter 1. About VirusScan Software . . . . . . . . . . . . . . . . . . . . . . . . . . .17
Introducing VirusScan anti-virus software . . . . . . . . . . . . . . . . . . . . . . . . . . . .17
How does VirusScan software work? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .19
What comes with VirusScan software? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .22
What’s new in this release? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .27
Chapter 2. Installing VirusScan Software . . . . . . . . . . . . . . . . . . . . . . . .31
Before you begin . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .31
System requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .31
Other recommendations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .31
Preparing to install VirusScan software . . . . . . . . . . . . . . . . . . . . . . . . .32
Installation options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .32
Installation steps . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .32
Using the Emergency Disk Creation utility . . . . . . . . . . . . . . . . . . . . . . .43
Determining when you must restart your computer . . . . . . . . . . . . . . . .48
Testing your installation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .49
Modifying or removing your VirusScan installation . . . . . . . . . . . . . . . .50
Chapter 3. Removing Infections
From Your System . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .53
If you suspect you have a virus... . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .53
Deciding when to scan for viruses . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .56
User’s Guide iii
Page 4

Table of Contents
Recognizing when you don’t have a virus . . . . . . . . . . . . . . . . . . . . . . . . . . . .57
Understanding false detections . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .58
Responding to viruses or malicious software . . . . . . . . . . . . . . . . . . . . . . . . .59
Submitting a virus sample . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .70
Using the SendVirus utility to submit a file sample . . . . . . . . . . . . . . . .71
Capturing boot sector, file-infecting, and macro viruses . . . . . . . . . . . .75
Chapter 4. Using the VShield Scanner . . . . . . . . . . . . . . . . . . . . . . . . . . .81
What does the VShield scanner do? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .81
Why use the VShield scanner? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .82
Browser and e-mail client support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .83
Enabling or starting the VShield scanner . . . . . . . . . . . . . . . . . . . . . . . . . . . . .84
Using the VShield configuration wizard . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .89
Setting VShield scanner properties . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .93
Using the VShield shortcut menu . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .149
Disabling or stopping the VShield scanner . . . . . . . . . . . . . . . . . . . . . . . . . .149
Tracking VShield software status information . . . . . . . . . . . . . . . . . . . . . . . .155
Chapter 5. Using the
VirusScan application . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .157
What is the VirusScan application? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .157
Why use the VirusScan application? . . . . . . . . . . . . . . . . . . . . . . . . . . .158
Starting the VirusScan application . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .159
Configuring the VirusScan Classic interface . . . . . . . . . . . . . . . . . . . . . . . . .164
Configuring the VirusScan Advanced interface . . . . . . . . . . . . . . . . . . . . . .169
Chapter 6. Creating and Configuring Scheduled Tasks . . . . . . . . . . . .187
What does VirusScan Console do? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .187
Why schedule scan operations? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .187
Starting the VirusScan Console . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .188
Using the Console window . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .190
Working with default tasks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .192
Working with the VShield task . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .194
Working with the AutoUpgrade and AutoUpdate tasks . . . . . . . . . . . .195
Creating new tasks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .196
Enabling tasks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .200
iv McAfee VirusScan
Page 5

Table of Contents
Checking task status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .202
Configuring VirusScan application options . . . . . . . . . . . . . . . . . . . . . . . . . .204
Chapter 7. Using Specialized
Scanning Tools . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 223
Scanning Microsoft Exchange and Outlook mail . . . . . . . . . . . . . . . . . . . . .223
When and why you should use the E-Mail Scan extension . . . . . . . . .223
Using the E-Mail Scan extension . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .224
Configuring the E-Mail Scan extension . . . . . . . . . . . . . . . . . . . . . . . . .225
Scanning cc:Mail . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .239
Using the ScreenScan utility . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .239
Chapter 8. Using VirusScan Utilities . . . . . . . . . . . . . . . . . . . . . . . . . . .247
Understanding the VirusScan control panel . . . . . . . . . . . . . . . . . . . . . . . . .247
Opening the VirusScan control panel . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .247
Choosing VirusScan control panel options . . . . . . . . . . . . . . . . . . . . . . . . . .248
Using the Alert Manager Client Configuration utility . . . . . . . . . . . . . . . . . .251
VirusScan software as an Alert Manager client . . . . . . . . . . . . . . . . . . . . . . .252
Configuring the Alert Manager client utility . . . . . . . . . . . . . . . . . . . . . . . . . .252
Chapter 9. About Safe & Sound . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .257
Using Safe & Sound . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .258
Protected Volume Files (The Ultimate Backup Protection) . . . . . . . . .258
Why You Should Make Regular Backups With Safe & Sound . . . . . . .258
How Safe & Sound Creates Automatic Backups . . . . . . . . . . . . . . . . . .259
Defining Your Backup Strategy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .259
Where Will You Store the Backup Set? . . . . . . . . . . . . . . . . . . . . . . . . .260
What Files are Important to You? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .260
How Often Should You or Safe & Sound Make Backups? . . . . . . . . . .261
Chapter 10. About Quarantine . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .263
Using Quarantine . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .263
Reporting New Viruses or Objects . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .264
Submitting Virus Information to Anti-Virus Emergency Response Team . .264
Appendix A. Default Vulnerable and Compressed File Extensions . . 267
User’s Guide v
Page 6

Table of Contents
Adding file name extensions for scanning . . . . . . . . . . . . . . . . . . . . . . . . . . .267
Current list of vulnerable file name extensions . . . . . . . . . . . . . . . . . . . . . . .268
Current list of compressed files scanned . . . . . . . . . . . . . . . . . . . . . . . . . . .272
Appendix B. Product Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .275
Updates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .275
How to Contact McAfee . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .275
Customer service . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .276
Technical support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .276
Appendix C. Download Information (License ID #: VSF500R) . . . . . . .279
SecureCast™ (For Windows 95/98 Retail Version): . . . . . . . . . . . . . . . . . . .279
Internet Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .279
Appendix D. Using the SecureCast Service to Get New Data Files . . 281
Introducing the SecureCast service . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .281
Why should I update my data files? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .282
Which data files does the SecureCast service deliver? . . . . . . . . . . . .282
Installing the BackWeb client and SecureCast service . . . . . . . . . . . . . . . . .283
System requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .283
Troubleshooting the Enterprise SecureCast service . . . . . . . . . . . . . .293
Unsubscribing from the SecureCast service . . . . . . . . . . . . . . . . . . . . .293
Support resources . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .293
SecureCast service . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .293
BackWeb client . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .294
Appendix E. Understanding iDAT Technology . . . . . . . . . . . . . . . . . . .295
Understanding incremental .DAT files . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .295
How does iDAT updating work? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .296
What does McAfee VirusScan Software post each week? . . . . . . . . . .297
Best practices . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .298
Frequently asked questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .299
Index . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .301
vi McAfee VirusScan
Page 7

Preface
What happened?
If you’ve ever lost important files stored on your hard disk, watched in dismay
as your computer ground to a halt only to display a prankster’s juvenile
greeting on your monitor, or found yourself having to apologize for abusive
e-mail messages you never sent, you know first-hand how computer viruses
and other harmful programs can disrupt your productivity. If you haven’t yet
suffered from a virus “infection,” count yourself lucky. But with more than
50,000 known viruses in circulation capable of attacking Windows- and
DOS-based computer systems, it really is only a matter of time before you do.
The good news is that of those thousands of circulating viruses, only a small
proportion have the means to do real damage to your data. In fact, the term
“computer virus” identifies a broad array of programs that have only one
feature in common: they “reproduce” themselves automatically by attaching
themselves to host software or disk sectors on your computer, usually without
your knowledge. Most viruses cause relatively trivial problems, ranging from
the merely annoying to the downright insignificant. Often, the primary
consequence of a virus infection is the cost you incur in time and effort to track
down the source of the infection and eradicate all of its traces.
Why worry?
So why worry about virus infections, if most attacks do little harm? The
problem is twofold. First, although relatively few viruses have destructive
effects, that fact says nothing about how widespread the malicious viruses are.
In many cases, viruses with the most debilitating effects are th e hardest to
detect—the virus writer bent on causing harm will take extra steps to avoid
discovery. Second, even “benign” viruses can interfere with the normal
operation of your computer and can cause unpredictable behavior in other
software. Some viruses contain bugs, poorly written code, or other problems
severe enough to cause crashes when they run. Other times, legitimate
software has problems running when a virus has, inten tionally or otherwise,
altered system parameters or other aspects of the computing environment.
Tracking down the source of resulting system freezes or crashes can drain time
and money from more productive activities.
Beyond these problems lies a problem of perception: once infected, your
computer can serve as a source of infection for other computers. If you
regularly exchange data with colleagues or customers, you could unwittingly
pass on a virus that could do more damage to your reputation or your dealings
with others than it does to your computer.
User’s Guide vii
Page 8

Preface
The threat from viruses and other malicious software is real, and it is growing
worse. Some estimates have placed the total worldwide cost in time and lost
productivity for merely detecting and cleaning virus infections at more than
$10 billion per year, a figure that doesn’t include the costs of data loss and
recovery in the wake of attacks that destroyed data.
Where do viruses come from?
As you or one of your colleagues recovers from a virus attack or hears about
new forms of malicious softw are appearing in commonly used programs,
you’ve probably asked yourself a number of questions about how we as
computer users got to this point. Where do viruses and other malicious
programs come from? Who writes them? Why do those who write them seek
to interrupt workflows, destroy data, or cost people the time and money
necessary to eradicate them? What can stop them?
Why did this happen to me?
It probably does n’t consol e you much to hear that t he programmer w ho wrote
the virus that erased your hard disk’s file allocation table didn’t target you or
your computer specifically. Nor will it cheer you up to learn that the virus
problem will probably always be with us. But knowing a bit about the history
of computer viruses and how they work can help you better protect yourself
against them.
Virus prehistory
Historians have identified a number of programs that incorporated features
now associated with virus software. Canadian researcher and educator Robert
M. Slade traces virus lineage back to special-purpose utilities used to reclaim
unused file space and perform other useful tasks in the earliest networked
computers. Slade reports that computer scientists at a Xerox Corporation
research facility called programs like these “worms,” a term coined after the
scientists noticed “holes” in printouts from computer memory maps that
looked as though worms had eaten them. The term survives to this day to
describe programs that make copies of themselves, but without necessarily
using host software in the process.
A strong academic tradition of computer prank pl aying most likely
contributed to the shift away from utility programs and toward more
malicious uses of the programming techniques found in worm software.
Computer science students, often to test their program ming abilities, would
construct rogue worm programs and unleash them to “fight” against each
other, competing to see whose program could “survive” while shutting down
rivals. Those same students also found uses for worm programs in practical
jokes they played on unsuspecting colleagues.
viii McAfee VirusScan
Page 9

Some of these students soon discovered that they could use certain features of
the host computer’s operating system to give them unauthorized access to
computer resources. Others took advantage of users who had relatively little
computer knowledge to substitute their own programs—written for their own
purposes—in place of common or innocuous ut ilities. These unsophisticated
users would run what they thought was their usual software only to find their
files erased, to have their account passwords stolen, or to suffer other
unpleasant consequences. Such “Trojan horse” programs or “Trojans,” so
dubbed for their metaphorical resemblance to the ancient Greek gift to the city
of Troy, remain a significant, and growing, threat to computer users today.
Viruses and the PC revolution
What we now think of as true computer viruses first appeared, according to
Robert Slade, soon after the first personal computers reached the mass market
in the early 1980s. Other researchers date the advent of virus programs to 19 86,
with the appearance of the “Brain” virus. Whichever date has the better claim,
the link between the virus threat and the personal computer is not
coincidental.
The new mass distribution of computers meant that viruses could spread to
many more hosts than before, when a comparatively few, closely guarded
mainframe systems dominated the computing world from their bastions in
large corporations and universities. Nor did the individual users who bought
PCs have much use for the sophisticated security measures needed to protect
sensitive data in those environments. As further catalyst, virus writers found
it relatively easy to exploit some PC technologies to serve their own ends.
Preface
Boot-sector viruses
Early PCs, for example, “booted” or loaded their operating systems from
floppy disks. The authors of the Brain virus discovered that they could
substitute their own program for the executable code present on the boot
sector of every floppy disk formatted with Microsoft’s MS-DOS, whether or
not it included system files. Users thereby loaded the virus into memory every
time they started their computers with any formatted disk in their floppy
drives. Once in memory, a virus can copy itself to boot sectors on other floppy
or hard disks. Those who unintentionally loaded Brain from an infected
floppy found themselves reading an ersatz “advertisement” for a computer
consulting company in Pakistan.
With that advertisement, Brain pioneered another characteristic feature of
modern viruses: the payload. The payload is the prank or malicious behavior
that, if triggered, causes effects that range from annoying messages to data
destruction. It’s the virus characteristic that draws the most attention—many
virus authors now write their viruses specifically to deliver their payloads to
as many computers as possible.
User’s Guide ix
Page 10

Preface
For a time, sophisticated descendants of this first boot-sector virus represe nted
the most serious virus threat to computer users. Variants of boot sector viruses
also infect the Master Boot Record (MBR), which stores the partition
information your computer needs to figure out where to find each of your
hard disk partitions and the boot sector itself.
Realistically, nearly every step in the boot process, from reading the MBR to
loading the operating system, is vulnerable to virus sabotage. Some of the
most tenacious and destructive viruses still include the ability to infect your
computer’s boot sector or MBR among their repertoire of tricks. Among other
advantages, loading at boot time can give a virus a chance to do its work before
your anti-virus software has a chance to run. Many McAfee VirusScan’s
anti-virus products anticipate th is possibility by allowing you to create an
emergency disk you can use to boot your computer and remove infections.
But most boot sector and MBR viruses had a particular weakness: they spread
by means of floppy disks or other removable media, riding concealed in that
first track of disk space. As fewer users exchanged floppy disks and as
software distribution came to rely on other media, such as CD-ROMs and
direct downloading from the Internet, other virus types eclipsed the boot
sector threat. But it’s far from gone—many later-generation viruses routinely
incorporate functions that infect your hard disk boot sector or MBR, even if
they use other methods as their primary means of transmission.
Those same viruses have also be nefitted from sever al generation s of evolution ,
and therefore incorporate much more sophisticat ed infection and concealment
techniques that make it far from simple to detect them, even when they hide
in relatively predictable places.
File infector viruses
At about the same time as the authors of th e B rain virus found vulnerabilities
in the DOS boot sector, other virus writers found out how to use other
software to help replicate their creations. An early example of this type of virus
showed up in computers at Lehigh University in Pennsylvania. The virus
infected part of the DOS command interpreter COMMAND.COM, which it
used to load itself into memory. Once there, it spread to other uninfected
COMMAND.COM files each time a user entered any standard DOS command
that involved disk access. This limited its spread to floppy disks that
contained, usually, a full operating system.
Later viruses quickly overcame this limitati on, sometimes with fairly clever
programming. Virus writers might, for instance, have their virus add its co de
to the beginning of an executable file, so that when users start a program, the
virus code executes immediately, then transfers control back to the legitimate
software, which runs as though nothing unusual has happened. Once it
activates, the virus “hooks” or “traps” requests that legitimate software makes
to the operating system and substitutes its own responses.
x McAfee VirusScan
Page 11

Preface
Particularly clever viruses can even subvert attempts to clear them from
memory by trapping the CTRL+ALT+DEL keyboard sequence for a warm
reboot, then faking a restart. Sometimes the only outward indication that
anything on your system is amiss—before an y payload detonates, that
is—might be a small change in the file size of infected legitimate software.
Stealth, mutation, encryption, and polymorphic techniques
Unobtrusive as they might be, changes in file size and other scant evidence of
a virus infection usually gives mos t anti-virus software enough of a scent to
locate and remove the offending code. One of the virus writer’s principal
challenges, therefore, is to find ways to hide his or her handiwork. The earliest
disguises were a mixture of innovative programming and obvious giveaways.
The Brain virus, for instance, redirected requests to see a disk’s boot sector
away from the actual location of the infected sector to the new location of the
boot files, which the virus had moved. This “stealth” capability enabled this
and other viruses to hide from conventional search techniques.
Because viruses needed to avoid continuously reinfecting host systems—
doing so would quickly balloon an infected file’s size to easily detectable
proportions or would consume enough system resources to point to an
obvious culprit—their authors also needed to tell them to leave certain files
alone. They addressed this problem by having the virus write a characteristic
byte sequence or, in 32-bit Windows operating systems, create a particular
registry key that would flag infected files with the software equivalent of a “do
not disturb” sign. Although that kept the virus from giving itself away
immediately, it opened the way for anti-virus software to use the “do not
disturb” sequence itself, along with other characteristic patterns that the virus
wrote into files it infected, to spot its “code signature.” Most anti-virus
vendors now compile and regularly update a database of virus “definitions”
that their products use to recognize those code signatures in the files they scan.
In response, virus writers found ways to conceal the code signatures. Some
viruses would “mutate” or transform their code sign atures with each new
infection. Others encrypted themselves and, as a result, their code signatures,
leaving only a couple of bytes to use as a key for decryption. The most
sophisticated new viruses employed stealth, mutation and encryption to
appear in an almost undetectable variety of new forms. Finding these
“polymorphic” viruses required software engineers to develop very elaborate
programming techniques for anti-virus software.
User’s Guide xi
Page 12

Preface
Macro viruses
By 1995 or so, the virus war had come to something of a standstill. New viruses
appeared continuously, prompted in part by the availability of ready-made
virus “kits” that enabled even some non-programmers to whip up a new virus
in no time. But most existing anti-virus software easily kept pace with updates
that detected and disposed of the new virus variants, which consisted
primarily of minor tweaks to well-known templates.
But 1995 marked the emergence of th e Concept virus, which added a new and
surprising twist to virus history. Before Concept, most virus researchers
thought of data files—the text, spreadsheet, or drawing documents created by
the software you use—as immune to infection. Viruses, after all, are programs
and, as such, needed to run in the same w ay executable software did in o rder
to do their damage. Data files, on the other hand, simply stored information
that you entered when you worked with your software.
That distinction melted away when Microsoft began adding macro
capabilities to Word and Excel, the flagship applications in its Office suite.
Using the stripped-down version of its Visual Basic language included with
the suite, users could create document templates that would automatically
format and add other features to documents created with Word and Excel.
Other vendors quickly followed suit with their products, either using a
variation of the same Microsoft macro language or incorporating one of their
own. Virus writers, in turn, seized the opportunity that this presented to
conceal and spread viruses in documents that you, the user, created yourself.
The exploding popularity of the Internet and of e-mail software that allowed
users to attach files to messages ensured that macro viruses would spread very
quickly and very widely. Within a year, macro viruses became the most potent
virus threat ever.
On the frontier
Even as viruses grew more sophisticated and continued to threaten the
integrity of computer systems we all ha d come to depend upon, still other
dangers began to emerge from an unexpected source: the World Wide Web.
Once a repository of research papers and academic treatises, the web has
transformed itself into perhaps the most versatile and adaptable medium ever
invented for communication and commerce.
Because its potential seems so vast, the web has attracted the attention and the
developmental energies of nearly every computer-related company in the
industry.
xii McAfee VirusScan
Page 13

Convergences in the technologies that have resulted from this feverish pace of
invention have given website designers tools they can use to collect and
display information in ways never previously available. Websites soon sprang
up that could send and receive e-mail, formulate and execute queries to
databases using advanced search engines, send and receive live audio and
video, and distribute data and multimedia resources to a worldwide audience.
Much of the technology that made these features possible consisted of small,
easily downloaded programs that interact with your browser software and,
sometimes, with other software on your hard disk. This same avenue served
as an entry point into your computer system for other—less benign—
programs to use for their own purposes.
Java, ActiveX, and scripted objects
These programs, whether beneficial or harmful, come in a variety of forms.
Some are special-purpose miniature applications, or “applets,” written in Java,
a programming language first developed by Sun M icrosystems. Others are
developed using ActiveX, a Microsoft technology that programmers can use
for similar purposes.
Both Java and ActiveX make extensive use of prewritten software modules, or
“objects,” that programmers can write themselves or take from existing
sources and fashion into the plug-ins, applets, device drivers and other
software needed to power the web. Java objects are called “classes,” while
ActiveX objects are called “controls.” The principle difference between them
lies in how they run on the host system. Java applets run in a Java “virtual
machine” designed to interpret Java programming and translate it into action
on the host ma chi ne, while ActiveX cont ro ls run as native Window s software
that links and passes data among other Windows programs.
Preface
The overwhelming majority of these objects are useful, even necessary, parts
of any interactive website. But despite the best efforts of Sun and Microsoft
engineers to design security measures into them, determined programmers
can use Java and ActiveX tools to plant harmful objects on websites, where
they can lurk until visitors unwittingly allow them access to vulnerable
computer systems.
Unlike viruses, harmful Java and ActiveX objects usually don’t seek to
replicate themselves. The web provides them with plenty of opportunities to
spread to target computer systems, while their small size and innocuous
nature makes it easy for them to evade detection. In fact, unless you tell your
web browser specifically to block them, Java and ActiveX obj ects download to
your system automatically whenever you visit a website that hosts them.
User’s Guide xiii
Page 14

Preface
Instead, harmful objects exist to deliver their equivalent of a virus payload.
Programmers have written objects, for example, that can read data from your
hard disk and send it back to the website you visited, that can “hijack” your
e-mail account and send out offensive messages in your name, or that can
watch data that passes between your computer and other computers.
Even more powerful agents have begun to appear in applications that run
directly from websites you visit. JavaScript, a scripting language with a name
similar to the unrelated Java language, first appeared in Netscape Navigator,
with its implementation of version 3.2 of the Hyper Text Markup Language
(HTML) standard. Since its introduction, JavaScript has grown tremendously
in capability and power, as have the host of other scripting technologies that
have followed it—including Microsoft VBScript and Active Server Pages,
Allaire Cold Fusion, and others. These technologies now allow software
designers to create fully realized applications that run o n web servers, interact
with databases and other data sources, and directly manipulate features in the
web browser and e-mail client software running on your computer.
As with Java and ActiveX objects, significant security measures exist to
prevent malicious actions, but virus writers and security hackers have found
ways around these. Because the benefits these innovations bring to the web
generally outweigh the risks, however, most users find themselves calculating
the tradeoffs rather than shunning the technologies.
Where next?
Malicious software has even intruded into areas once thought completely out
of bounds. Users of the mIRC Internet Relay Chat client, for example, have
reported encountering viruses constructed from the mIRC scripting language.
The chat client sends script viruses as plain text, which would ordinarily
preclude them from infecting systems, but older versions of the mIRC client
software would interpret the instructions coded into the script and perform
unwanted actions on the recipient’s computer.
The vendors moved quickly to disable this capability in updated versions of
the software, but the mIRC incident illustrates the general rule that where a
way exists to exploit a software security hole, someone will find it and use it.
Late in 1999, another virus writer demonstrated this rule yet again with a
proof-of-concept virus called VBS/Bubbleboy that ran directly within the
Microsoft Outlook e-mail client by hijacking its built-in VBScript support. This
virus crossed the once-sharp line that divided plain-text e-mail messages from
the infectable attachments they carried. VBS/Bubbleboy didn’t even require
you to open the e-mail message—simply viewing it from the Outlook preview
window could infect your system.
xiv McAfee VirusScan
Page 15

How to protect yourself
McAfee VirusScan’s anti-virus software already gives you an important
bulwark against infection and damage to your data, but anti-virus software is
only one part of the security measures you should take to protect yourself.
Anti-virus software, moreover, is only as good as its latest update. Because as
many as 200 to 300 viruses and variants appear each month, the virus
definition (.DAT) files that enable McAfee VirusScan’s software to detect and
remove viruses can get quickly outdated. If you have not updated the files that
originally came with your so ftware, you could risk infection from newly
emerging viruses. McAfee VirusScan’s Software has, however, assembled the
world’s largest and most experienced anti-virus research staff in its Anti-Virus
Emergency Response Team (AVERT)*. This means that the files you need to
combat new viruses appear as soon as—and often before—you need them.
Most other security measures are common sense—checking disks you receive
from unknown or questionable sources, either with anti-virus software or
some kind of verification utility, is always a good idea. Malicious
programmers have gone so far as to mimic the programs you trust to guard
your computer, pasting a familiar face on software with a less-than-friendly
purpose. Neither McAfee VirusScan’s nor any other anti-virus software,
however, can detect when someone substitutes an as-yet unidentified Trojan
horse or other malicious program for one of your favorite shareware or
commercial utilities—that is, until aft er the fact.
Preface
Web and Internet access poses its own risks. VirusScan* anti-virus software
gives you the ability to block dangerous web sites so that users can’t
inadvertently download malicious software from known hazards; it also
catches hostile objects that get downloaded anyway. But having a top-notch
firewall in place to protect your network and implementing other network
security measures is a necessity when unscrupulous attackers can penetrate
your network from nearly any point on the globe, whether to steal sensitive
data or implant malicious code. You should also make sure that your network
is not accessible to unauthorized users, and that you have an adequate training
program in place to teach and enforce security standards. To learn about the
origin, behavior and other characteristics of particul ar viruses, consult the
Virus Information Library maintained on the AVERT website.
McAfee VirusScan Software can provide you with other powerful software in
the Active Virus Defense* (AVD) and Total Virus Defense (TVD) suites, the
most comprehensive anti-virus solutions available. Related companies within
the Network Associates family provide other technologies that also help to
protect your network, including the PGP Security CyberCop product line, and
the Sniffer Technologies network monitoring product suite. Contact your
Network Associates representative, or visit the Network Associates website,
to find out how to enlist the power of these security sol utions on your side.
User’s Guide xv
Page 16

Preface
xvi McAfee VirusScan
Page 17
1About VirusScan Software
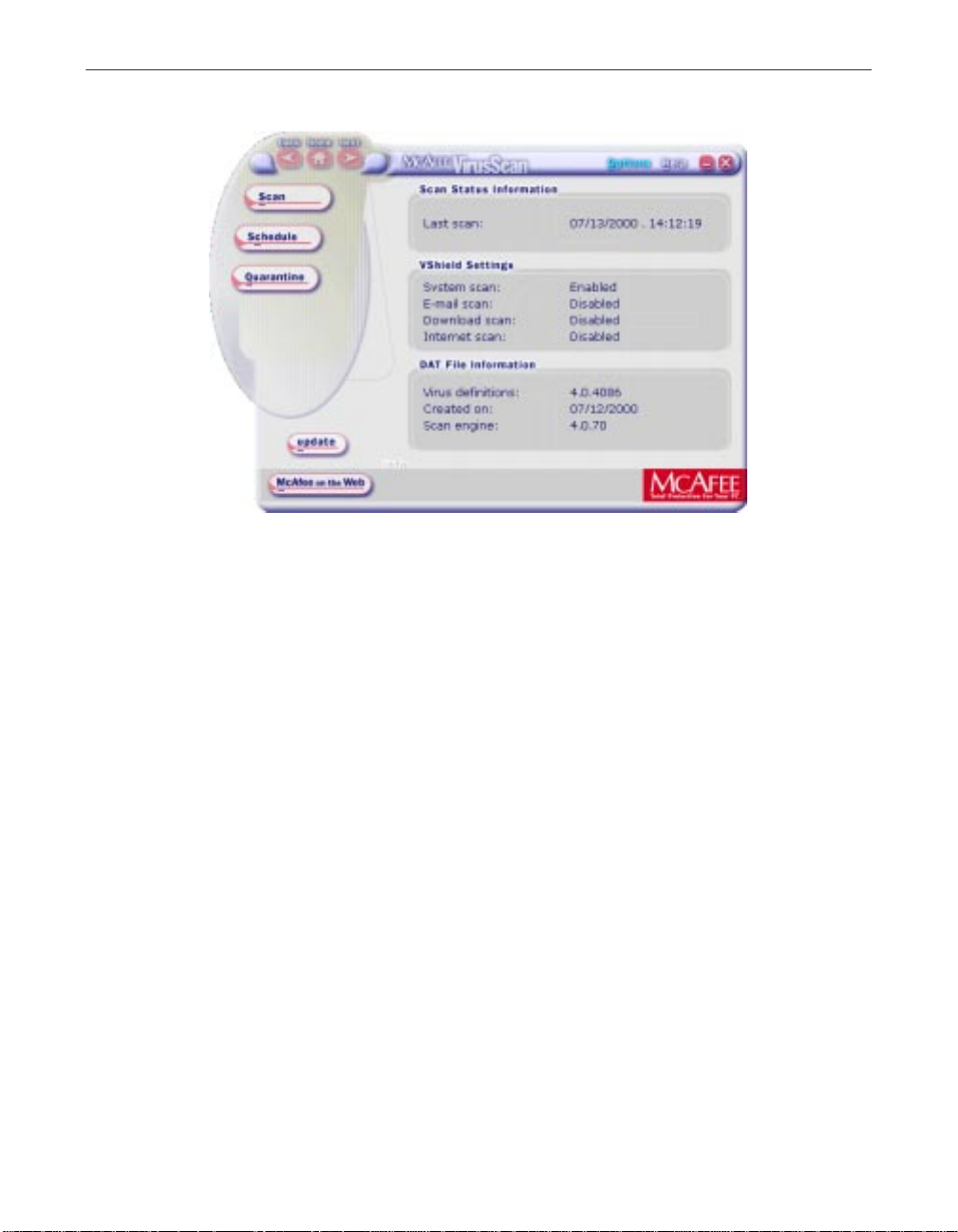
The VirusScan Central is your main entry poin t in using all of the available
components of McAfee VirusScan. This home screen provides relevant
information such as the last time a virus scan was performed on your
computer; what VShield settings are enabled or disabled (for more
information see Using VShield Scanner; and available DAT information and
when it was created.
Through this user-friendly interface, you can access the main functions of
McAfee VirusScan. Click the appropriate buttons as displayed to start
performing a particular task within McAfee VirusScan (e.g., Scan, Schedule,
Quarantine, etc).
You can also click the Update button to start searching and downloading any
available updates to McAfee VirusScan installed on your computer. Make sure
that you are connected to the Internet prior to using this feature. For more
information and step-by-step instructions, click the Help icon on the upper
right-hand corner of the window. To view available options in customizing
how you want McAfee VirusScan components to work on your PC, click the
Options button.
1
Introducing VirusScan anti-virus softw are
Eighty percent of the Fortune 100—and more than 50 million users
worldwide—choose VirusScan anti-virus software to protect their computers
from the staggering range of viruses and other malicious agents that has
emerged in the last decade to invade co rpora te n etworks a nd cause havo c for
business users. They do so because VirusScan software offers the most
comprehensive desktop anti-virus security solution available, with features
that spot viruses, block hostile ActiveX and Java objects, identify dangerous
websites, stop infectious e-mail messages—and even root out “zombie” agents
that assist in large-scale denial-of-service attacks from across the Internet.
They do so also because they recognize how much value McAfee VirusScan
anti-virus research and development brings to their fight to maintain network
integrity and service levels, ensure data security, and reduce ownership costs.
With more than 50,000 viruses and malicious agents now in circulation, the
stakes in this battle have risen considerably. Viruses and worms now have
capabilities that can cost an enterprise real money, not just in terms of lost
productivity and cleanup costs, but in direct bottom-line reductions in
revenue, as more businesses move into e-commerce and online sales, and as
virus attacks proliferate.
User’s Guide 17
Page 18

About VirusScan Software
VirusScan software first honed its technological edge as one of a handful of
pioneering utilities developed to combat the earliest virus epidemics of the
personal computer age. It has developed considerably in the intervening years
to keep pace with each new subterfuge that virus writers have unleashed. As
one of the first Internet-aware anti-virus applications, it maintains its value
today as an indispensable business utility for the new electronic economy.
Now, with this release, VirusScan software adds a whole new level of
manageability and integration with other McAfee VirusScan’s anti-virus tools.
Architectural improvements mean that each VirusScan component meshes
closely with the others, sharing data and resources for better application
response and fewer demands on your system. Full support for Network
Associates ePolicy Orchestrator management software means that network
administrators can handle the details of component and task configuration,
leaving you free to concentrate on your own work. A new incremental
updating technology, meanwhile, means speedier and less
bandwidth-intensive virus definition and scan engine downloads—now the
protection you need to deal with the blindingly quick distribution rates of
new-generation viruses can arrive faster than ever before.
The new release also adds multiplatform support for Windows 95, Windows
98, Windows ME, Windows NT Workstation v4.0, and Windows 2000
Professional, all in a single package with a sing le installer, but optimized to
take advantage of the benefits each platform offers. Windows NT Workstation
v4.0 and Windows 2000 Professional users, for example, can run VirusScan
software with differing security levels that provide a range of enforcement
options for system administrators. That way, corporate anti-virus policy
implementation can vary from the relatively casual—where an administrator
might lock down a few critical settings, for example—to the very strict, with
predefined settings that users cannot change or disable at all.
At the same time, as the cornerstone product in the McAfee VirusScan’s Active
Virus Defense and Total Virus Defense security suites, VirusScan software
retains the same core features that have made it the utility of choice for the
corporate desktop. These include a virus detection rate second to none,
powerful heuristic capabilities, Trojan horse program detection and removal,
rapid- response updating with weekly virus definition (.DAT) file releases,
daily beta .DAT releases, and EXTRA.DAT file support in crisis or outbreak
situations. Because more than 300 new viruses or malicious software agents
appear each month McAfee VirusScan Software backs its software with a
worldwide reach and 24-hour “follow the sun” coverage from its Anti-Virus
Emergency Response Team (AVERT).
18 McAfee VirusScan
Page 19

About VirusScan Software
Even with the rise of viruses and worms that use e-mail to spread, that flood
e-mail servers, or that infect groupware products and file servers directly, the
individual desktop remains the single largest source of infections, and is often
the most vulnerable point of entry. VirusScan software acts as a tireless
desktop sentry, guarding your system against more venerable virus threats
and against the latest threats that lurk on websites, often without the site
owner’s knowledge, or spread via e-mail, whether solicited or not.
In this environment, taking precautions to protect yourself from malicious
software is no longer a luxury, but a necessity. Consider the extent to which
you rely on the data on your computer and the time, trouble and money it
would take to replace that data if it became corrupted or unusable because of
a virus infection. Corporate anti-virus cleanup co sts, by some estimates,
topped $16 billion in 1999 alon e. Bala nce the probability of infection—and
your company’s share of the resulting costs—against the time and effort it
takes to put a few common sense security measures in place, and you can
quickly see the utility in protecting yourself.
Even if your own data is relatively unimportant to you, neglecting to guard
against viruses might mean tha t your computer could play unwitting host to
a virus that could spread to computers that your co-workers and colleagues
use. Checking your hard disk periodically with VirusScan software
significantly reduces your system’s vulnerability to infection and keeps you
from losing time, money an d data unnecessarily.
How does VirusScan software work?
VirusScan software combines the anti-virus industry’s most capable scan
engine with top-notch interface enhancements that give you complete access
to that engine’s power. The VirusScan graphical user interface unifies its
specialized program components, but without sacrificing the flexibility you
need to fit the software into your computing environment. The scan engine,
meanwhile, combines the best features of technologies that McAfee and
McAfee VirusScan researchers developed independently for more than a
decade.
Fast, accurate virus de tection
The foundation for that combination is the unique development environmen t
that McAfee VirusScan researchers constructed for the engine. That
environment includes Virtran, a specialized programming language with a
structure and “vocabulary” optimized for the particular requirements that
virus detection and removal impose. Using specific library functions from this
language, for instance, virus researchers can pinpoint those sections within a
User’s Guide 19
Page 20

About VirusScan Software
file, a boot sector, or a master boot record that viruses tend to infect, either
because they can hide within them, or because they can hijack their execution
routines. This way, the scanner avoids having to examine the entire file for
virus code; it can instead sample the file at well defined poin ts to look for virus
code signatures that indicate an infection.
The development environment brings as much speed to .DAT file construction
as it does to scan engine routines. The environment provides tools researchers
can use to write “generic” definitions that identify entire virus families, and
that can easily detect the tens or hundreds of variants that make up the bulk of
new virus sightings. Continual refinements to this technique have moved
most of the hand-tooled virus definitions that used to reside in .DAT file
updates directly into the scan engine as bundles of generic routines.
Researchers can even employ a Virtran architectural feature to plug in new
engine “verbs” that, when combined with existing engine functions, can add
functionality needed to deal with new infection techniques, new variants, or
other problems that emerging viruses now pose.
This results in blazingly quick enhancements the engine’s detection
capabilities and removes the need for continuous updates tha t target virus
variants.
Encrypted polymorphic virus detection
Along with generic virus variant detection, the scan engine now inco rpora tes
a generic decryption engine, a set of ro utines that en ables VirusScan so ftware
to track viruses that try to conceal themselves by encrypting and mutating
their code signatures. These “polymorphic” viruses are notoriously difficult to
detect, since they change their code signature each time they replicate.
This meant that the simple pattern-matching method that earlier scan engine
incarnations used to find many viruses simply no longer worked, since no
constant sequence of bytes existed to detect. To respond to this threat, McAfee
VirusScan researchers developed the PolyScan Decryption Engine, which
locates and analyzes the algorithm that these types of viruses use to encrypt
and decrypt themselves. It then runs this code through its paces in an
emulated virtual machine in order to understand how the viruses mutate
themselves. Once it does so, the engine can spot the “undisguised” nature of
these viruses, and thereby detect them reliably no matter how they try to hide
themselve s.
20 McAfee VirusScan
Page 21

About VirusScan Software
“Double heuristics” analysis
As a further engine enhancement, McAfee VirusScan researchers have honed
early heuristic scanning technologies—originally developed to detect the
astonishing flood of macro virus variants that erupted after 1995 —into a set of
precision instruments. Heuristic scanning techniques rely on the engine’s
experience with previous viruses to predict the likelihood that a suspicious file
is an as-yet unidentified or unclassified new virus.
The scan engine now incorporates ViruLogic, a heuristic technique that can
observe a program’s behavior and evaluate how closely it resembles either a
macro virus or a file-infecting virus. ViruLogic looks for virus-like behaviors
in program functions, such as covert file modifications, background calls or
invocations of e-mail clients, and other methods that viruses can use to
replicate themselves. When the number of these types of behaviors—or their
inherent quality—reaches a predetermined threshold of tolerance, th e engine
fingers the program as a likely virus.
The engine also “triangulates” its evaluation by looking for program behavior
that no virus would display—prompting for some types of user input, for
example—in order to eliminate false positive detections. This double-heuristic
combination of “positive” and “negative” techniques results in an
unsurpassed detection rate with few, if any, costly misidentifications.
Wide-spectrum coverage
As malicious agents have evolved to take advantage of the instant
communication and pervasive reach of the Internet, so VirusScan software has
evolved to counter the threats they present. A computer “virus” once meant a
specific type of agent—one designed to replicate on its own and cause a
limited type of havoc on the unlucky recipient’s computer. In recent years,
however, an astounding range of malicious agents has emerged to assault
personal computer users from nearly every conceivable angle. Many of these
agents—some of the fastest-spreading worms, for instance—use updated
versions of vintage techniques to infect systems, but many others make full
use of the new opportunities that web-based scripting and application hosting
present.
Still others open “back doors” into desktop systems or create security holes in
a way that closely resembles a deliberate attempt at network penetration,
rather than the more random mayhem that most viruses tend to leave in their
wakes.
The latest VirusScan software releases, as a consequence, do not simply wait
for viruses to appear on your system, they scan proactively at the source or
work to deflect hostile agents away from your system. The VShield scanner
that comes with VirusScan software has three modules that concentrate on
agents that arrive from the Internet, that spread via e-mail, or that lurk on
User’s Guide 21
Page 22

About VirusScan Software
Internet sites. It can look for particular Java and ActiveX objects that pose a
threat, or block access to dangerous Internet sites. Meanwhile, an E-Mail Scan
extension to Microsoft Exchange e-mail clients, such as Microsoft Outlook, can
“x-ray” your mailbox on the server, looking for malicious agents before they
arrive on your desktop.
VirusScan software even protects itself against attempts to use its own
functionality against your computer. Some virus writers embed their viruses
inside documents that, in turn, they embed in other files in an attempt to evade
detection. Still others take this technique to an absurd extreme, constructing
highly recursive—and very large—compressed archive files in an attempt to
tie up the scanner as it digs through the file looking for infections. VirusScan
software accurately scans the majority of popular compressed file and archive
file formats, but it also includes logic tha t keeps it from getting trapped in an
endless hunt for a virus chimera.
What comes with VirusSca n softwa re?
VirusScan software consists of several components that combine one or more
related programs, each of which play a part in defending your computer
against viruses and other malicious software. The components are:
• The VirusScan Central. This is your main entry point in using all of the
available components of McAfee VirusScan. This home screen (see Figure
1-2) provides relevant information such as the last time a virus scan was
performed on your computer; what VShield settings are enabled or
disabled and available DAT information and when it was created.
22 McAfee VirusScan
Page 23
About VirusScan Software
Figure 1-1. McAfee VirusScan Central screen
Through this user-friendly interface, you can access the mai n functions of
McAfee VirusScan. Click the appropriate buttons as displayed to start
performing a particular task within McAfee VirusScan (e.g., Scan, Schedule,
Quarantine, etc).
You can also click the Update button to start searching and downloading any
available updates to McAfee VirusScan installed on your computer. Make sure
that you are connected to the Internet prior to using this feature. For more
information and step-by-step instructions, click the Help icon on the upper
right-hand corner of the window. To view available options in customizing
how you want McAfee VirusScan components to work on your PC, click the
Options button.
• The VirusScan Console. This component allows you to create, configure
and run VirusScan tasks at times you specify. A “task” can include
anything from running a scan operat ion on a set of disks at a specific time
or interval, to running an update o r upgrade operation. You can also en able
or disable the VShield scanner from the Console window.
The Console comes with a preset list of tasks tha t ensures a minimal level
of protection for your system—you can, for example, immediately scan and
clean your C: drive or all disks on your computer.
User’s Guide 23
Page 24
About VirusScan Software
• The VShield scanner. This component gives you continuous anti-virus
protection from viruses that arrive on floppy disks, from your network, or
from various sources on the Internet. The VShield scanner starts when you
start your computer, and stays in memory until you shut down. A flexible
set of property pages lets you tell the scanner which parts of yo ur system
to examine, what to look for, which parts to leave alone, and how to
respond to any infected files it finds. In addition, the scanner can alert you
when it finds a virus, and can summarize each of its actions.
The VShield scanner comes with three other specialized modules that
guard against hostile Java applets and ActiveX controls, that scan e-mail
messages and attachments that you receive from the Internet via Lotus
cc:Mail, Microsoft Mail or other mail clients that comply with Microsoft’s
Messaging Application Programming Interface (MAPI) standard, and that
block access to dangerous Internet sites. Secure password protection for
your configuration options prevents others from making unauthorized
changes. The same convenient dialog box controls co nf iguration options
for all VShield modules. See “Using the VShield Scanner” on page 85 of the
VirusScan Us er’s Guide for details.
• Safe & Sound. This component allows you to create backup sets in
protected volume files, which is the safest and preferred type of backup. A
protected volume file is a sectioned-off area of the drive, sometimes called a
logical drive.
• Quarantine. This component allows you to move infected files to a
• The E-Mail Scan extension. This component allows you to scan your
24 McAfee VirusScan
NOTE: Sa fe & Sound is only avai labl e for Wi ndow s 95, 98 and
Windows ME. For more information, read Chapter 10 “About
Safe & Sound”.
quarantine folder. This moves infected files from areas where they can be
accessed and enables you to clean or delete them at your convenience.
NOTE: For more information, read Chapter 11 “About
Quarantine”.
Microsoft Exchange or Outlook mailbox, or public folders to which you
have access, directly on the server. This invaluable “x-ray” peek into your
mailbox means that VirusScan software can find potential infections before
they make their way to your desktop, which can stop a Melissa-like virus
in its tracks.
Page 25

About VirusScan Software
• A cc:Mail scanner. This component includes technology optimized for
scanning Lotus cc:Mail mailboxes that do not use the MAPI standard.
Install and use this component if your workgroup or network uses cc:Mail
v8.x or earlier.
• The Alert Manager Client configuration uti lity. This component lets you
choose a destination for Alert Manager “events” that VirusScan software
generates when it detects a virus or takes other noteworthy actions. You
can also specify a destination directory for older-style Centralized Alerting
messages, or supplement either method with Desktop Management
Interface (DMI) alerts sent via your DMI client software.
• The ScreenScan utility. This optional component scans your computer as
your screen saver runs during idle periods.
• The SendVirus utility. This component gives you an easy and painless
way to submit files that you believe are infected directly to McAfee
VirusScan’s anti-virus researchers. A simple wizard guides you as you
choose files to submit, include contact details and, if you prefer, strip out
any personal or confidential data from document files.
• The Emergency Disk creation utility. This essential utility helps you to
create a floppy disk that you can use to boot your computer into a
virus-free environment, then scan essential system areas to remove any
viruses that could load at startup.
• Command-line scanners. This component consists of a set of full-featured
scanners you can use to run targeted scan operations from the MS-DOS
Prompt or Command Pro mpt windows, or from pr otected MS-DO S mode.
The set includes:
– FINDVIRU.EXE, a scanner for 32-bit environments only. This is the
primary command-line interface. When you run this file, it first
checks its environment to see whether it can run by itself. If your
computer is running in 16-bit or protected mode, it will transfer
control to one of the other scanners.
– SCANPM.EXE, a scanner for 16- and 32-bit environments. This
scanner provides you with a full set of scanning options for 16- and
32-bit protected-mode DOS environments. It also includes support
for extended memory and flexible memory allocations.
FINDVIRU.EXE will transfer control to this scanner when its
capabilities can enable your scan opera tion to run more efficiently.
– SCAN86.EXE, a scanner for 16-bit environments only. This scanner
includes a limited set of capabilities geared to 16-bit environments.
FINDVIRU.EXE will transfer control to this scanner if your system
runs in 16-bit mode, but without special memory configurations.
User’s Guide 25
Page 26

About VirusScan Software
All of the command-line scanners allow you to initia te targ et ed scan
operations from an MS-DOS Prompt or Command Prompt window, or
from protected MS-DOS mode. Ordinarily, you'll use the VirusScan
application's graphical user interface (GUI) to perform most scanning
operations, but if you have trouble starting Windows or if the VirusScan
GUI components will not run in your environment, yo u can use the
command-line scanners as a backup.
• Documentation. VirusScan software documentation includes:
– BOOTSCAN.EXE, a smaller, specialized scanner for use primarily
with the Emergency Disk utility. This scanner ordinarily runs from
a floppy disk you create to provide you with a virus-free boot
environment.
When you run the Emergency Disk creation wizard, VirusScan
software copies BOOTSCAN.EXE, and a specialized set of .DAT
files to a single floppy disk. BOOTSCAN.EXE will not detect or
clean macro viruses, but it will detect or clean other viruses that can
jeopardize your VirusScan software installation or infect files at
system startup. Once you identify and respond to those viruses, you
can safely run VirusScan software to clean the rest of your system.
–A printed Getting Started Guide, which introduces the product,
provides installation instructions, outlines how to respond if you
suspect your computer has a virus, and provides a brief product
overview. The printed Getting Started Guide comes with the
VirusScan software copies distributed on CD-ROM discs—you can
also download it as vs51_getstart.PDF from Network Associates
website or from other electronic services.
26 McAfee VirusScan
– This user’s guide saved on the VirusScan software CD-ROM or
installed on your hard disk in Adobe Acrobat .PDF format. You ca n
also download it as vscan51_userguide.PDF from Network
Associates website or from other electronic services. The VirusScan
User’s Guide describes in detail how to use VirusScan and includes
other information useful as background or as advanced
configuration options. Acrobat .PDF files are flexible online
documents that contain hyperlinks, outlines and other aids for easy
navigation and information retrieval.
– An administrator’s guide saved on the VirusScan software
CD-ROM or installed on your hard disk in Adobe Acrobat .PDF
format. The VirusScan Administrator’s Guide describes in detail how
to manage and configure VirusScan software from a local or remote
desktop.
Page 27
About VirusScan Software
– An online help file. This file gives you quick access to a full range of
topics that describe VirusScan software. You can open this file either
by choosing Help Topics from the Help menu in the VirusScan
main window, or by c licking any of the Help buttons dis p layed in
VirusScan dialog boxes.
The help file also includes extensive context-sensitive—or “What's
This”—help. To see these help topics, right-click buttons, lists, icons,
some text boxes, and other elements that you see within dialog
boxes. You can also click the ? symbol at the top-right corner in most
dialog boxes, then click the element you want to see described to
display the relevant topic. The dialog boxes with Help buttons open
the help file to the specific topic that describes the entire dialog box.
– A LICENSE.TXT file. This file outlines the terms of your license to
use VirusScan software. Read it carefully—by in stalling VirusScan
software you agree to its terms.
– A README.TXT file. This file contains last-minute additions or
changes to the documentation, lists any known behavior or other
issues with the product release, and often describes new product
features incorporated into incremental product updates. You’ll find
the README.TXT file at the root level of your VirusScan software
CD-ROM or in the VirusScan software program folder—you can
open and print it from Windows Notepad, or from nearly any
word-processing software.
What’s new in this release?
This VirusScan release introduces a number of innovative new features to the
product’s core functionality, to its range of coverage, and to the details of its
application architecture. The single most significant change between previous
VirusScan versions and this release, however, is the integration of two
separate VirusScan versions optimized to run on separate Windows platforms
into a single product that runs on both. This single product also takes full
advantage of each platform’s strengths.
The next sections discuss other changes that this VirusScan release introduces.
Installation and distribution features
McAfee VirusScan’s anti-virus products, including VirusScan software, now
use the Microsoft Windows Installer (MSI), which comes with all Windows
2000 Professional systems. This Setup utility offers a wealth of custom
installation and configuration features that make VirusScan software rollout
much easier and more intuitive.
User’s Guide 27
Page 28
About VirusScan Software
Interface enhancements
This release moves the VirusScan interface for all supported platforms solidly
into the territory VirusScan anti-virus software for Windows 95, Windows 98
and Window ME pioneered with its v4.0.1 release. This adds extensive
VShield scanner configuration options for the Windows NT Workstation v4.0
and Windows 2000 Professional platforms, while reducing the complexity of
some previous configuration options. Alert Manager ser ver configuration, for
example, moves entirely over to the NetShield product line—VirusScan
software now acts strictly as a configurable client application.
This release also adds a new VirusScan control panel, which functions as a
central point from which you can enable and disable all VirusScan
components. This control panel also lets you set a ceiling for the number of
items you can scan in or exclude from a single operation, and can set the
VShield scanner and VirusScan control panel to run at startup. Other changes
include:
• New VShield system tray icon states tell you more about which VShield
modules are active. These states are:
– All VShield modules are active
– The System Scan module is active, but one or more of the other
VShield modules is inactive
• New interface settings for task configuration allow you to tell the
• An updated randomization feature for sch eduled ta sks allows you to set a
• System Scan module action options now include a new Prompt Type
28 McAfee VirusScan
– The System Scan module is inactive, but one or more of the other
VShield modules is active
– All VShield modules are inactive
VirusScan application how you want it to appear as your scheduled task
runs and what you want it to do when it finishes. You can also set a
password to protect individual task settings from changes, or to protect an
entire task configuration at once.
time for the task to run, then set a randomization “window.” The
VirusScan Console then picks a random time within the window to
actually start the task.
configuration option for Windows 95 and Windows 98 systems. This
option lets you determine how the Prompt for user action alert appears.
Page 29
About VirusScan Software
Changes in product functionality
• A new Alert Manager Client configuration utility allows you to choose an
Alert Manager server installed on your network as an alert message
destination, or to select a network share as a destination for Centralized
Alerting messages. You can also supplement either of these alert methods
with Desktop Management Interface alert messages.
• The Alert Manager server supports Intel Pentium III processor serial
numbers to identify individual machines for virus notification. For more
information about Intel processor serial numbers, consult the Intel FAQ at
http://support.intel.com/support/processors/pentiumiii/psqa.htm.
New update options for your VirusScan software
Even with the majority of the virus definitions it requires now incorporated
directly into its engine in generic routines, VirusScan software still requires
regular .DAT file updates to keep pace with the 200 to 300 new viruses that
appear each month. To meet this need, McAfee VirusScan Software has
incorporated updating technology in VirusScan software from its earliest
incarnations. With this release, that technology takes a quantum leap forward
with incremental .DAT file updating.
The Network Associates SecureCast service provides a convenient method
you can use to receive the latest virus definition (.DAT) file updates
automatically, as they become available, wit hout your having to download
them.
NOTE: To update the McAfee VirusScan software installed on your
computer, click the update button in the McAfee VirusScan main
window. Make sure that your PC is connected to the Internet prior to
performing this task.
User’s Guide 29
Page 30

About VirusScan Software
30 McAfee VirusScan
Page 31

2Installing VirusScan
Software
Before you begin
McAfee VirusScan Software distributes VirusScan software in two ways: 1) as
an archived file that you can download from the McAfee Web site; and 2) on
CD-ROM. Although the method you use to transfer VirusScan files from an
archive you download differs from the method you use to transfer files from
a CD-ROM you place in your CD-ROM drive, the installation steps you follow
after that are the same for both distribution types. Review the system
requirements to verify that VirusScan software will run on your system.
System requirements
VirusScan software will install and run on any IBM PC or PC-compatible
computer equipped with:
• A processor equivalent to at least an Intel Pentium- class or compatible
processor. McAfee VirusScan Software recommends an Intel Pentium
processor or Celeron processor running at a minimum of 166 MHz.
• A CD-ROM drive. If you downloaded your copy of VirusScan software,
this is an optional item.
2
• At least 16MB of free hard disk space.
• At least 16MB of free random-access memory (RAM). McAfee VirusScan
Software recommends at least 20MB.
• Microsoft Windows 95, Windows 98, Window s ME, Windows NT
Workstation v4.0 with Service Pack 4 or later, or Windows 2000
Professional. McAfee VirusScan Software recommends that you also have
Microsoft Internet Explorer v4.0.1 or later installed, particularly if your
system runs any Windows 95 version.
Other recommendations
To take full advantage of VirusScan software’s automatic update features, you
should have an Internet connection via a high-speed modem and an Internet
service provider.
User’s Guide 31
Page 32

Installing VirusScan Software
Preparing to install VirusScan software
After inserting the McAfee VirusScan on your CD-ROM drive , you should see
a VirusScan welcome image appear automatically. To install VirusScan
software immediately, click Install VirusScan, then skip to Step 4 to continue
with Setup. If the welcome image does not appear, or if you are installing
VirusScan software from files you downloaded, start with Step 2.
Ë IMPORTANT: Because Setup installs some VirusScan files as services on
Windows NT Workstation v4.0 and Windows 2000 Professional systems,
you must log in to your system with Administrator rights to install this
product. To run Setup on Windows 95 or Windows 98, you do not need
to log in with any particular profile or rights.
Installation options
The Installation steps section describes how to install VirusScan software with
its most common options on a single compu ter or workstati on. You can choo se
to do a Typical setup—which installs commonly used VirusScan components
but leaves out some VShield modules and the ScreenScan utility—or you can
choose to do a Custom setup, which gi ves you the option to install all
VirusScan components.
Installation steps
McAfee VirusScan Software recommends that you first quit all other
applications you have running on your system before you start Setup. Doing
so reduces the possibility that software conflicts will interfere with your
installation.
To install VirusScan sof tware, follo w these step s:
1. If your computer runs Windows NT Workstation v4.0 or Windows 2000
Professional, log on to your sys tem as Administrator. You must have
administrative rights to install VirusScan software on your system.
32 McAfee VirusScan
Page 33

Installing VirusScan Software
2. Choose Run from the Start menu in the Windows taskbar.
The Run dialog box will appear (Figure 2-1).
Figure 2-1. Run dialog box
3. Type <X>:\SETUP.EXE in the text box provided, then click OK.
Here, <X> represents the drive letter for your CD-ROM drive or the path
to the folder that contains your extracted VirusScan files. To search for
the correct files on your hard disk or CD-ROM, click Browse.
NOTE: If your VirusScan software copy came on an Active Virus
Defense or a Total Virus Defense CD-ROM, you must also specify
which folder contains the VirusScan software.
Before it continues with the installation, Setup first checks to see whether
your computer already has version 1.1 of the Microsoft Windows
Installer (MSI) utility running as part of your system software.
If your computer runs Windows 2000 Professional, this MSI version
already exists on your system. If your computer runs an earlier Windows
release, you might still have this MSI version on your system if you
previously installed other software that uses MSI. In e ither of these cases,
Setup will display its first wizard panel immedia tely. Skip to Step 4 to
continue.
If Setup does not find MSI v1.1 on your computer, it installs files it needs
to continue the installation, then prompts you to restart your computer.
Click Restart System.
When your computer restarts, Setup will continue from where it left off.
The Setup welcome panel will appear (Figure 2-2).
User’s Guide 33
Page 34

Installing VirusScan Software
4. This first panel tells you where to locate the README.TXT file, which
describes product features, lists any known issues, and includes the latest
available product information for this VirusScan version. When you
have read the text, click Next> to continue.
Figure 2-2. Setup welcome panel
5. The next wizard panel displays the VirusScan software end-user license
34 McAfee VirusScan
agreement. Read this agreement carefully—if you install VirusScan
software, you agree to abide by the terms of the license.
If you do not agree to the license terms, select I do not agree to the
terms of the License Agreement, then click Cancel. Setup will quit
immediately. Otherwise, click I agree to the terms of the License
Agreement, then click Next> to continue.
Setup next checks to see whether previous VirusScan versions or
incompatible software exists on your computer. If you have no other
anti-virus software or any previous VirusScan versions on your system,
it will display the Security Type or the Setup Type panel. Skip to Step 8
to continue.
If Setup discovers an earlier VirusScan version on your system, it will tell
you that it must remove that earlier version. If your computer runs
Windows 95 or Windows 98, Setup also gives you the option to preserve
the VShield configuration settings you chose for the earlier version.
If your computer runs Windows NT Workstation v4.0 or Windows 2000
Professional, Setup will remove the previous VirusScan version, but will
not preserve any previous VShield scanner settings.
Page 35
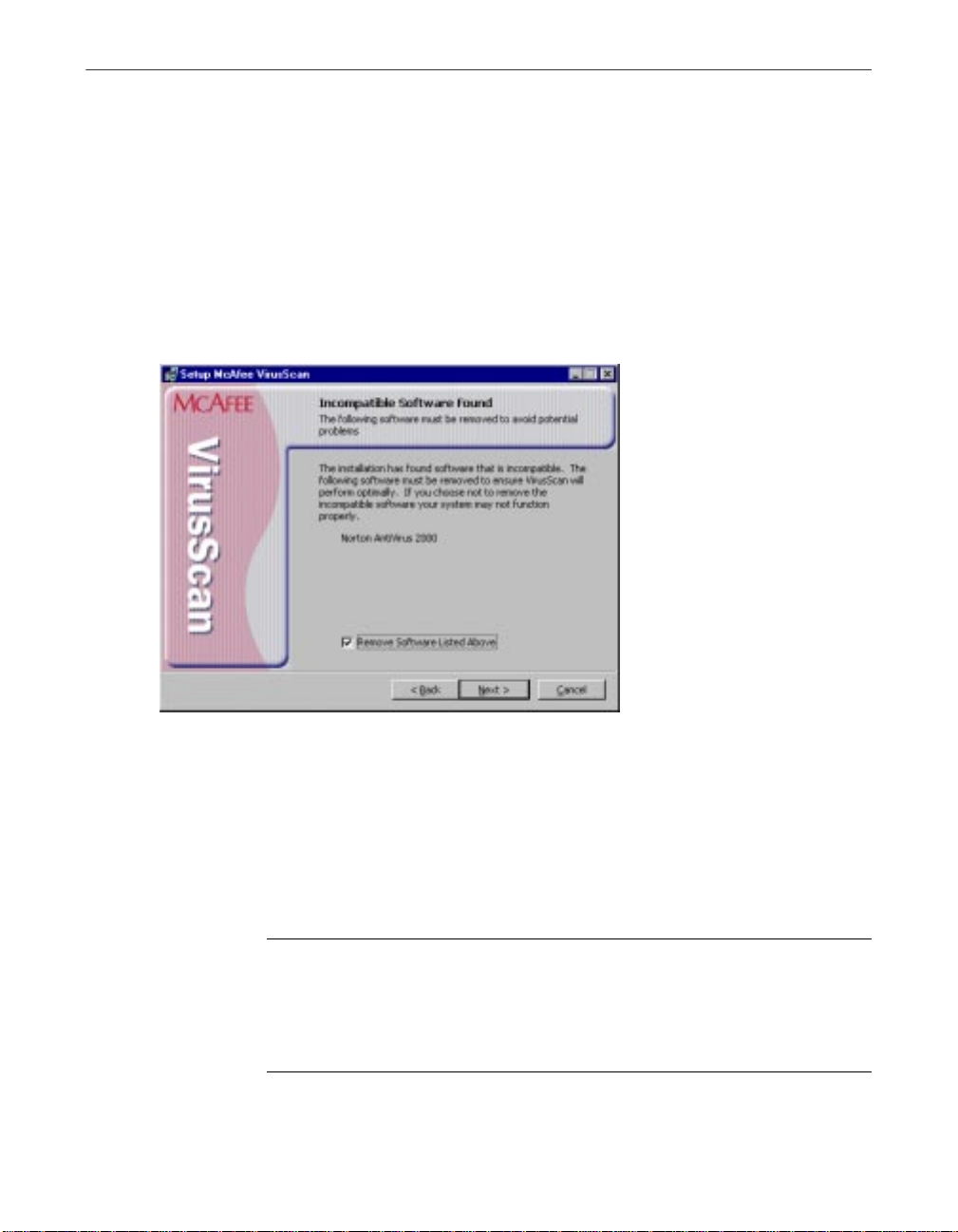
Installing VirusScan Software
6. Select Preserve On Access Settings, if the option is available, th en click
Next> to continue.
If Setup finds incompatible software, it will display a wizard panel that
gives you the option to remove the conflicting software (see Figure 2-3).
If you have no incompatible software on your system and your computer
runs Windows 95 or Windows 98, skip to Step 9 to continue with the
installation. If you have no incompatible software and your system runs
Windows NT Workstation v4.0 or Windows 2000 Professional, skip to
Step 8 to continue. Otherwise, continue with Step 7.
Figure 2-3. Incompatible software panel
7. Select the checkbox shown, then click Next>. Setup will start the
uninstallation utility that the conflicting software normally uses, and
allow it to remove the software. The uninstallation utility might tell you
that you need to restart your computer to completely remove the other
software. You do not need to do so to continue with your VirusScan
installation—so long as the other software is not active, Setup can
continue without conflicts.
NOTE: M cAfee VirusScan Software strongly recommends that you
remove incompatible software. Because most anti-virus software
operates at a very low level within your system, two anti-virus
programs that compete for access to the same files or that perform
critical operations can make yo ur system very unstable.
User’s Guide 35
Page 36

Installing VirusScan Software
If your computer runs Windows NT Workstation v4.0 or Windows 2000
Professional, Setup next asks you which security mode you want to use
to run VirusScan software on your system.
The options in this panel govern whether others who use your computer
can make changes to the configuration options you choose, can schedule
and run tasks, or can enable and disable VirusScan components.
VirusScan software includes extensive security measures to ensure that
unauthorized users cannot make any changes to software configurations
in Maximum Security mode. The Standard Security mode allows all
users to have access to all configuration options .
Either option you choose here will install the same VirusScan version,
with the same configuration options, and with the same scheduled tasks
for all system users.
8. Select the security mode you prefer. Your choices are:
• Use Maximum Security. Select this option to require users to have
Administrator rights to your computer in order to change any
configuration options, to enable or disable any VirusScan
component, or to configure and run scheduled tasks.
Users who do not have administrative rights may still configure and
run their own scan operations with the VirusScan application and
save settings for those operations in a .VSC file, but they cannot
change default VirusScan applicatio n settings.
36 McAfee VirusScan
• Use Standard Security. Select this option to give any user who logs
into your computer the ability to cha nge any configuration option,
enable or disable and VirusScan component, or schedule and run
any task.
Setup next asks you to choose a Typical or a Custom setup for this
computer.
Page 37

Installing VirusScan Software
Figure 2-4. Setup Type panel
9. Choose the Setup Type you prefer. Your choices are:
• Typical Installation. This option installs all available features
contained in the McAfee VirusScan product.
• Custom In stallation. This option allows you to customized
McAfee VirusScan by only selecting specific features of the product
to be installed on your computer.
10. Choose the option you prefer, then click Next> to continue.
If you chose Custom Setup, you’ll see the panel shown in Figure 2-5.
Otherwise, skip to Step 13 to continue with your installation.
User’s Guide 37
Page 38

Installing VirusScan Software
11. Choose the VirusScan components you want to install. You can:
• Add a component to the installation. Click beside a
Figure 2-5. Custom Setup panel
component name, then choose This feature will be installed on
local hard drive from the menu that appears. To add a component
and any related modules within the component, choose
This feature, and all subfeatures, will be installed on local
hard drive instead. You can choose this option only if a component
has related modules.
12. When you have chosen the components you want to install, click Next>
38 McAfee VirusScan
• Remove a component from the installation. Click beside a
component name, then choose This feature will not be
available from the menu that appears.
NOTE: Th e VirusScan Setup utility does not support the other
options shown in this menu. You may not install VirusScan
components to run from a network, and VirusScan software
has no components that you can install on an as-needed basis.
You can also specify a different disk and destination directory for the
installation. Click Change, then locate the drive or directory you want to
use in the dialog box that appears. To see a summary of VirusScan disk
usage requirements relative to your available hard disk space, click Disk
Usage. The wizard will highlight disks that have insufficient space.
to continue.
Page 39

Installing VirusScan Software
Setup will show you a wizard panel that confirms its readiness to begin
installing files (Figure 2-6).
Figure 2-6. Ready to Install panel
13. Click Install to begin copying files to your hard drive. Otherwise, click
<Back to change any of the Setup options you chose.
Setup first removes any previous VirusScan versions or incompatible
software from your system, then copies VirusScan program files to your
hard disk. When it has finished, it displays a panel that asks if you want
to configure the product you installed (Figure 2-7).
Figure 2-7. VirusScan Configuration panel
User’s Guide 39
Page 40

Installing VirusScan Software
14. From the VirusScan Configuration panel (Figure 2-7), you can skip
configuration to finish your installation, or you can select to configure the
available options displayed.
• Scan boot record at startup. Select this checkbox to have Setup
write these lines to your Windows AUTOEXE C.BAT f ile:
C:\PROGRA~1\COMMON~1\NETWOR~1\VIRUSS~1\40~1.XX\SCAN
.EXE C:\
@IF ERRORLEVEL 1 PAUSE
This tells your system to start the VirusScan Command Line scanner
when your system starts. The scanner, in turn, will pause if it detects
a virus on your system so that you can shut down and use the
VirusScan Emergency Disk to restart.
If your computer runs Windows NT Workstation v4.0, Windows
ME, or Windows 2000 Professional, you may not choose Scan boot
record at startup, but you may choose either of the other o ptions.
Neither Windows NT Workstation, Windows ME, nor
Windows 2000 permit software to scan or make changes to hard
disk boot sectors or master boot records. Also, these operating
systems do not use an AUTOEXEC.BAT file for system startup.
15. The next set of screens will display options that will allow you to run
40 McAfee VirusScan
other components of McAfee VirusScan such as running the Safe &
Sound utility, the VirusScan update, and the Rescue Disk (Figure 2-8).
NOTE: Safe & Sound utility will not be available when installing in
Windows NT or Windows 2000.
Page 41

Installing VirusScan Software
Figure 2-8. Configuration panel
Choose configuration options for your installation. You can choose to
scan your system, create an emergency disk, or update your virus
definition files before you start the VShield scanner and the VirusScan
Console.
NOTE: For more information on any of these options, you can refer to the
online Help of McAfee VirusScan.
16. In the next screen (Figure 2-9), select the Enable McAfee VirusScan
Protection checkbox, then click Finish. The VirusScan software “splash
screens” will appear, and the VShield scanner and VirusScan Console
icons will appear in the Windows system tray. Your software is ready for
use.
User’s Guide 41
Page 42

Installing VirusScan Software
17. After you click Finish, the McAfee VirusScan Installer Information dialog
box is displayed where you will be prompted to restart your computer
(Figure 2-10).
Figure 2-9. Successful Installation panel
42 McAfee VirusScan
Figure 2-10. McAfee VirusScan Installer Information dialog box
NOTE: If you had a previous VirusScan version installed on your
computer, you must restart your system in order to start the VShield
scanner. Click Yes to restart your computer.
Page 43

Using the Emergency Disk Creation utility
If you choose to create an Emergency Disk during installation, Setup will start
the Emergency Disk wizard in the middle of the VirusScan software
installation, then will return to the Setup sequence when it finishes. To learn
how to create an Emergency Disk, begin with Step 1. Y ou can also start the
Emergency Disk wizard at any point after you install VirusScan software.
NOTE: McAfee VirusScan strongly recommends that you create an
Emergency Disk during installation, but that you do so after VirusScan
software has scanned your system memory for viruses. If VirusScan
software detects a virus on your system, do not create an Emergency Disk
on the infected computer.
The Emergency Disk you create includes BOOTSCAN.EXE, a specialized,
small-footprint command-line scanner that can scan your hard disk boot
sectors and Master Boot Record (MBR). BOOTSCAN.EXE works with a
specialized set of .DAT files that focus on ferreting out boot-sector viruses. If
you have already installed VirusScan software with default Setup options, you
can find these .DAT files in this location on your hard disk:
C:\Program Files\Common Files\McAfee VirusScan\VirusScan Engine\4.0.xx
Installing VirusScan Software
The special .DAT files have these names:
• EMCLEAN.DAT
• EMNAMES.DAT
•EMSCAN.DAT
McAfee VirusScan Software periodically updates these .DAT files to detect
new boot-sector viruses. You can download updated Emergency .DAT files
from this location:
http://www.nai.com/asp_set/anti_virus/avert/tools.asp
NOTE: McAfee VirusScan Software recommends that you download
new Emergency .DAT files directly to a newly formatted floppy disk in
order to reduce the risk of infection.
Because the wizard renames the files and prepares them for use when it
creates your floppy disk, you may not simply copy th em directly to an
Emergency Disk that you create yourself. Use the creation wizard to prepare
your Emergency Disk.
User’s Guide 43
Page 44

Installing VirusScan Software
To start the wizard after installation, click Start in the Windows taskbar, point
to Programs, then to McAfee VirusScan. Next, choose Create Emergency
Disk.
The Emergency Disk wizard welcome panel will appear (Figure 2-11).
Figure 2-11. Emergency Disk welcome panel
1. Click Next> to continue.
The next wizard panel appears (Figure 2-12).
Figure 2-12. Second Emergency Disk panel
44 McAfee VirusScan
Page 45

Installing VirusScan Software
If your computer runs Windows NT Workstation or Windows 2000
Professional, the wizard tells you that it will format your Emergency
Disk with the NAI-OS.
You must use these proprietary operating system files to create your
Emergency Disk, because Windows NT Workstation v4.0 and
Windows 2000 Professional system files do not fit on a single floppy disk.
If your computer runs Windows 95 or Windows 98, the wizard will offer
to format your Emergency Disk either with the NAI-OS or with
Windows startup files.
2. If the wizard offers you a choice, choose which operating system files you
want to use, then click Next> to continue. Depending on which operating
system you choose, the wizard displays a different panel next:
• If you chose to format your disk with the NAI-OS, the wizard
displays an informational panel.
Follow these substeps to continue:
a. Insert an unlocked and unformatted 1.44MB floppy disk into
your floppy drive, then click Next>.
The Emergency Disk wizard will copy its files from a disk
image stored in the VirusScan program directory. As it does so,
it will display its progress in a wizard panel.
b. Click Finish to quit the wizard when it has created your disk.
Next, remove the disk from your floppy drive, lock it, label it
VirusScan Emergency Boot Disk and store it in a safe place.
• If you chose to format your disk with Windows system files, the
wizard displays a panel that lets you choose whether to format your
floppy disk.
Your choices are:
•If you have a virus-free, formatted floppy disk that contains only
DOS or Windows system files, insert it into your floppy drive. Next,
select the Don’t Format checkbox, then click Next> to cont inue.
This tells the Emergency Disk wizard to copy only the VirusScan
software Command Line component the emergency .DAT files, and
support files to the floppy disk. Skip to Step 3 to continue.
•If you do not have a virus-free floppy disk formatted with DOS or
Windows system files, you must create one in order to use the
Emergency Disk to start your computer. Follow these substeps:
User’s Guide 45
Page 46

Installing VirusScan Software
a. Insert an unlocked and unformatted floppy disk into your
floppy drive. McAfee VirusScan Software recommends that
you use a completely new disk that you have never previously
formatted to prevent the possibility of virus infections on your
Emergency Disk.
b. Verify that the Don’t format checkbox is clear.
c. Click Next>.
The Windows disk format dialog box appears (see Figure 2-11).
3. Click Next> to continue. Setup will scan your newly formatted disk for
46 McAfee VirusScan
Figure 2-13. Windows Format dialog box
d. Verify that the Full checkbox in the Format Type area and the
Copy system files checkbox in the Other Options area are
both selected. Next, click Start.
Windows will format your floppy disk and copy th e system
files necessary to start your computer.
e. Click Close when Windows has finished formatting your disk,
then click Close again to return to the Emergency Disk panel.
viruses (Figure 2-14).
Page 47

Installing VirusScan Software
Figure 2-14. Scanning Emergency Disk for viruses
If VirusScan software does not detect any viruses during its scan
operation, Setup will immediately copy BOOTSCAN.EXE and its
support files to the floppy disk you created. If VirusScan software does
detect a virus, quit Setup immediately.
4. When the wizard finishes copying the Emergency Disk files, it displays
the final wizard panel (Figure 2-15).
Figure 2-15. Final Emergency Disk panel
5. Click Finish to quit the wizard. Next, remove the new Emergency Disk
from your floppy drive, label it, write-protect it, and store it in a safe
place.
User’s Guide 47
Page 48

Installing VirusScan Software
NOTE: A locked or write-protected floppy disk shows two holes
near the edge of the disk opposite the metal shutter. If you don’t see
two holes, look for a plastic sliding tab at one of the disk corners,
then slide the tab until it locks in an open position.
Determining when you must restart your computer
In many circumstances, you can install and use this VirusScan release
immediately, without needing to restart your computer. In some cases,
however, the Microsoft Installer (MSI) will need to replace or initialize certain
files, or previous McAfee VirusScan Software product installa tions might
require you to remove files in order for VirusScan software to run correctly.
These requirements can also vary for each supported Windows platform.
In these cases, you will need to restart your system during the
installation—usually to install MSI files—or after the installation i tself.
48 McAfee VirusScan
Page 49

Installing VirusScan Software
Table 2-1. Circumstances that require you to restart your system
Windows 95 and
Circumstance
Installation on com puter with no
previous VirusSca n version and
no incompatible software
Installation on computer with
previous V irusScan vers ion
Installation on computer with
incompatible software
Windows 98
No restart required,
unless you have
Novell Client32 for
NetWare installed,
then restart required
Restart required Restart required
No restart required,
but Setup will ask if
you wish to restart.
You can safely click
No.
Installation on a computer with
Microsoft Installer (MSI) v1.0
NOTE: Microsoft Office 2000
installs this MSI version
Installation on a computer with
Microsoft Installer v1.1
.DAT file update No restart required No restart required
Restart required
after MSI files
installed and before
Setup can continue
No restart required,
except on Windows
98 Second Edition
systems, or if some
drivers or .DLL files
used
Windows NT and
Windows 2000
Restart required
No restart required,
but Setup will ask if
you wish to restart.
You can safely click
No.
Restart required
after MSI files
installed and before
Setup can continue
No restart required
Scan engine update via McAfee
VirusScan SuperDAT utility
Testing your installation
Once you install it, VirusScan software is ready to scan your system for
infected files. You can verify that it has installed correctly and that it can
properly scan for viruses with a test developed by the European Institute of
Computer Anti-virus Research (EICAR), a coalition of anti-virus vendors, as a
method for their customers to test any anti-virus software installation.
No restart required No restart required
User’s Guide 49
Page 50

Installing VirusScan Software
To test your ins tallati on, fo llow th ese steps:
1. Open a standard Windows text editor, such as Notepad, then type this
character string as one line, with no spaces or carriage returns:
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUSTEST-FILE!$H+H*
2. Save the file with the name EICAR.COM. The file size will be 69 or 70
bytes.
NOTE: The line shown above should appear as one line in your text
editor window, so be sure to maximize your text editor window and
delete any carriage returns. Also, be sure to type the letter O, not the
number 0, in the “X5O...” that begins the test message.
If you are reading this manual on your computer, you can copy the
line directly from the Acrobat .PDF file and paste it into Notepad.
You can also copy this text string direct ly from the “Testing your
installation” section of the README.TXT file, which you can find in
your VirusScan program directory. If you copy the line from either
of these sources, be sure to delete any carriage returns or spaces.
3. Start your VirusScan software and allow it to scan the directory that
contains EICAR.COM. When VirusScan software examines this file, it
will report finding the EICAR-STANDARD-A V- TEST-FILE virus.
IMPORTANT:
Ë
other files, or otherwise harm your system. Delete the file when you
have finished testing your installation to avoid alarming other users.
This file is
not a virus—
it cannot s pread or infect
Modifying or removing your VirusScan installation
The Microsoft Windows Installer version that VirusScan software uses also
includes a standard method to modify or remove your VirusScan installation.
To modify, or remove VirusScan softw are, follow these steps:
1. Click Start in the Windows taskbar, point to Settings, then choose
Control Panel.
2. Locate and double-click the Add/Remove Programs control panel.
3. In the Add/Remove Programs Properties dialog box, choose McAfee
VirusScan v5.1 in the list, then click Add/Remove.
50 McAfee VirusScan
Page 51

Installing VirusScan Software
Setup will start and display the first Maintenance wizard panel.
4. Click Next> to continue.
Setup displays the Program Maintenance wizard panel. Choose whether
to modify VirusScan components or to remove VirusScan software from
your system completely. Your choices are:
• Modify. Select this option to add or remove individual VirusScan
components. Setup will display the Custom wizard panel (see
Figure 2-5). Start with Step 11 to choose the components you want
to add or remove.
• Remove. Select this option to remove VirusScan software from
your computer completely. Setup will ask you to confi rm that you
want to remove the software from your system.
Click Remove. Setup will display progress information as it deletes
VirusScan software from your system. When it has finished, click
Finish to close the wizard panel.
User’s Guide 51
Page 52

Installing VirusScan Software
52 McAfee VirusScan
Page 53

3Removing Infections
From Your System
If you suspect you have a virus...
First of all, don’t panic! Although far from harmless, most viruses that infect
your machine will not destroy data, play pranks, or render your computer
unusable. Even the comparatively rare viruses that do carry a destructive
payload usually produce their nasty effects in respon se to a trigger event. In
most cases, unless you actually see evidence of a payl oad that has activated,
you will have time to deal with the infection properly. The very presence of
these small snippets of unwanted computer code can, however, interfere w ith
your computer’s normal operation, consume system resources and have other
undesirable effects, so you should take them seriously and be sure to remove
them when you encounter them.
A second idea to keep in mind is that odd computer behavior, unexplained
system crashes, or other unpredictable events might have causes other than
virus infections. If you believe you have a virus on your computer because of
occurrences such as these, scanning for viruses might not produce the results
you expect, but it will help eliminate one potential cause of your computer
problems.
The safest course of action you can take is to install VirusScan software, then scan
your system immediately and thoroughly.
3
When you install VirusScan software, Setup starts the VirusScan application
to examine your computer’s memory and your hard disk boot sectors in order
to verify that it can safely copy its files to your hard disk without risking their
infection. If the application does not detect any infections, continue with the
installation, then scan your sy stem thoroughly as soon as you restart your
computer. File-infector viruses that don’t load into your computer’s memory
or hide in your hard disk boot blocks might still be lurking somewhere on your
system.
If the VirusScan application detects a virus during Setup, you’ll need to
remove it from your system before you install the program.
Ë IMPORTANT: To ensure maximum security, you should also follow
these same steps if a VirusScan component detects a virus in your
computer’s memory at some point after installation.
User’s Guide 53
Page 54

Removing Infections From Your System
If VirusScan software fou nd an infect ion duri ng instal lation , follow t hese
steps carefully:
1. Quit Setup immediately, then shut down your computer.
Be sure to turn the power to your system off completely. Do not press
CTRL+ALT+DEL
viruses can remain intact during this type of “warm” reboot.
2. If you created a VirusScan Emergency Disk during installation, or if your
VirusScan copy came with one, lock the disk, then insert it into your
floppy drive.
NOTE: If your VirusScan software copy did not come with an
Emergency Disk, or if you could not create an Emergency Disk
during Setup, you must create a disk on an uninfected computer.
3. Wait at least 15 seconds, then start your computer again.
NOTE: If you have your computer's BIOS configured to look for its
boot code first on your C: drive, you should change your BIOS
settings so that your computer looks first on your A: or B: drive.
Consult your hardware documentation to learn how to configure
your BIOS settings.
or reset your computer to restart your system—some
4. Type y to continue, then skip to Step7. If you did not, type n, then turn
5. Read the notice shown on your screen, then press any key on your
54 McAfee VirusScan
After it starts your computer, the Emergency Disk runs a batch file that
leads you through an emergency scan operation. The batch file first asks
you whether you cycled the power on your computer.
your computer completely off and begin again.
The batch file next tells you that it will star t a scan operation.
keyboard to continue.
The Emergency Disk will load the files it needs to conduct the scan
operation into memory. If you have extended memory on your
computer, it will load its database files into that memory for faster
execution.
BOOTSCAN.EXE, the command-line scanner that comes with the
Emergency Disk, will make four scanning passes to examine your hard
disk boot sectors, your Master Boot Record (MBR), your system
directories, program files, and other likely points of infection on all of
your local computer's hard disks.
Page 55

Removing Infections From Your System
NOTE: McAfee VirusScan Software strongly recommends that you
do not interrupt the BOOTSCAN.EXE scanner as it runs its scan
operation. The Emergency Disk will not detect macro viruses, script
viruses, or Trojan horse programs, but it will detect common
file-infecting and boot-sector viruses.
If BOOTSCAN.EXE finds a virus, it will try to clean the infected file. If it
fails, it will deny access to the file and continue the scan operation. After
it finishes all of its scanni ng passes, it shows a summary report the
actions it took for each hard disk on the screen. The report tells you:
• How many files the scanner examined
• How many files of that number are clean, or uninfected
• How many files contain potential infections
• How many files of that number the scanner cleaned
• How many boot sector and MBR files the scanner examined
• How many boot sector and MBR files contain potential infections
If the scanner detects a virus, it beeps and reports the name and location
of the virus on the screen.
6. When the scanner finishes examining your hard disk, remove the
Emergency Disk from your floppy drive, then shut your computer off
again.
7. When BOOTSCAN.EXE finishes examining your system, you can either:
• Return to working with your computer. If BOOTSCAN.EXE did
not find a virus, or if it cleaned any infected files it did find, remove
the Emergency Disk from your floppy drive, then restart your
computer normally. If you had planned to install VirusScan
software on your computer but stopped when Setup found an
infection, you can now continue with your installation.
• Try to clean or delete infected files yourself. If BOOTSCAN.EXE
found a virus that it could not remove, it will identify the infected
files and tell you that it could not clean them, or that it does not have
a current remover for the infecting virus.
As your next step, locate and delete the infected file or files. You will
need to restore any files that you delete from backup files. Be sure to
check your backup files for infections also. Be sure also to use the
VirusScan application at your earliest o pportunity to scan your system
completely in order to ensure that your system is virus-free.
User’s Guide 55
Page 56

Removing Infections From Your System
Deciding when to scan for viruses
Maintaining a secure computing environment means scanning for viruses
regularly. Depending on the degree to which you swap floppy disks with
other users, share files over your local area network, or interact with other
computers via the Internet, scanning “regularly” could mean scanning as little
as once a month, or as often as several times a day. Other good habits to
cultivate include scanning right before you back up your data, scanning before
you install new or upgraded software—particularly software you download
from other computers—and scanning when you start or shut down your
computer each day. Use the VShield scanner to examine your computer’s
memory and maintain a constant level of vigilance between scan operations.
Under most circumstances this should protect your system’s integrity.
If you connect to the Internet frequently or download files often, you might
want to supplement regular scan operations with tasks based on certain
events. Use the VirusScan Console to schedule a set of scan tasks to monitor
your system at likely points of virus entry, such as
• whenever you insert a floppy disk into your computer’s floppy drive
• whenever you start an application or open a file
• whenever you connect to or map a network drive to your sys tem
Even the most diligent scan operation can miss new viruses, however, if your
virus definition (.DAT) files are not up to date. Your VirusScan software
purchase entitles you to free virus updates for the life of your product, so you
can update frequently to keep current. The VirusScan Console includes
AutoUpdate and AutoUpgrade tasks you can us e to update your .DAT files
and the VirusScan engine.
56 McAfee VirusScan
Page 57

Removing Infections From Your System
Recognizing when you don’t have a virus
Personal computers have evolved, in their short life span, into highly complex
machines that run ever-more-complicated software. Even the most farsighted
of the early PC advocates could never have imagined the tasks for which
workers, scientists and others have harnessed the modern PC’s speed,
flexibility and power. But that power comes with a price: hardware and
software conflicts abound, applications and operating systems crash, and
hundreds of other problems can crop up in unlikely places. In some cases,
these failures can resemble the sorts of effects that you see when you have a
virus infection with a destructive payload. Other computer failures seem to
defy explanation or diagnosis, so frustrated users blame virus infections,
perhaps as a last resort.
Because viruses do leave traces, however, you can usually eliminate a virus
infection as a possible cause for computer failure relatively quickly and easily.
Running a full VirusScan scan operation will uncover all of the known virus
variants that can infect your computer, and quite a few of those that have no
known name or defined behavior. Although th at do esn’t give you much he lp
when your problem really results from an interrupt conflict, it does allow you
to eliminate one possible cause. With that knowledge, you can then go on to
troubleshoot your system with a full-featured system diagnosis utility.
More serious is the confusion that results from virus-like programs, virus
hoaxes, and real security breaches. Anti-virus software simply cannot detect
or respond to such destructive agents as Trojan horse programs that have
never appeared previously, or the perception that a virus exists where none in
fact does.
The best way to determine whether your computer failure resulted from a
virus attack is to run a complete scan operation, then pay attention to the
results. If the VirusScan application does not report a virus infection, the
chances that your problem results from one are slight—look to other causes for
the symptoms you see. Furthermore, in the very rare even t that the VirusScan
application does miss a macro virus or another virus type that has in fact
infected your system, the chances are relatively small that serious failures will
follow in its wake. You can, however, rely on McAfee VirusScan researchers
to identify and isolate the virus, then to update VirusScan software
immediately so that you can detect and, if possible, remove the virus when
you next encounter it.
User’s Guide 57
Page 58

Removing Infections From Your System
Understanding false detections
A false detection occurs when VirusScan software sends a virus alert message
or makes a log file entry that identifies a virus where none actually exists. You
are more likely to see false detections if you have anti-virus software from
more than one vendor installed on your computer, because some anti-virus
software stores the code signatures it uses for detection unprotected in
memory.
The safest course to take when you see an alert message or log entry is to treat
it as a genuine virus threat, and to take the appropriate steps to remove the
virus from your system. If, however, you believe that a VirusScan component
has generated a false detection—it has, for example, flagged as infected a file
that you have used safely for years—verify that you are not seeing one of these
situations before you call McAfee VirusScan technical support:
• You have more than one anti-virus program running. If so, VirusScan
components might detect unprotected code signatures that another
program uses and report them as viruses. To avoid this problem, configure
your computer to run only one anti-virus program, then shut the computer
down and turn off the power. Wait a few seconds before you start the
computer again so that the system can clear the other program’s code
signature strings from memory.
• You have a BIOS chip with anti-virus features. Som e B IOS ch i ps pr ov ide
anti-virus features that can trigger false detections when VirusScan
software runs. Consult the user’s guide for your computer to learn about
how its anti-virus features work and how to disable them if necessary.
• You have an older Hewlett-Packard or Zenith PC. Some older models
from these manufacturers modify the boot sectors on their hard disks each
time they start up. VirusScan components might detect these modifications
as viruses, when they are not. Consult the user’s guide for your computer
to learn whether it uses self-modifying boot code. To solve the problem,
use the VirusScan Command Line scanner to add validation information to
the startup files themselves. This method does not save information about
the boot sector or the master boot record.
• You have copy-protected software. Depending on the type of copy
protection used, VirusScan components might detect a virus in the boot
sector or the master boot record on some floppy disks or other media.
If none of these situations apply, contact McAfee VirusScan technical support
or send e-mail to virus_research@nai.com with a detailed explanation of the
problem you encountered.
58 McAfee VirusScan
Page 59

Removing Infections From Your System
Responding to viruses or malicio us software
Because VirusScan software consists of several component programs, any one
of which could be active at one time, your possible responses to a virus
infection or to other malicious softwa re w ill depend upon which program
detected the harmful object, how you have that program configured to
respond, and other circumstances. The following sections give an overview of
the default responses available with each program component. To learn abou t
other possible responses, see the chapter that discusses each component in
detail.
Responding when the VShield scanner detects malicious software
The VShield scanner consists of four related modules that provide you with
continuous background protection against viruses, harmful Java and ActiveX
objects, and dangerous websites. A fifth module controls security settings for
the other four. You can configure and activate each module separately, or use
them together to provide maximum protection. Because each module detects
different objects or scans different virus entry points, each has a different set
of default responses.
Responding when the System Scan module detects a virus
How this module reacts when it finds a virus depends on which operating
system your computer runs and, on Windows 95 and Windows 98 systems, on
which prompt option you chose in the module’s Action page.
By default on Windows 95 and Windows 98 systems, this module looks for
viruses each time you run, copy, create, or rename any file on your system, or
whenever you read from a floppy disk. On Win dows NT Workstation v4.0
and Windows 2000 Professional systems, the System Scan module looks for
viruses whenever your system or another computer reads files from or writes
files to your hard disk or a floppy disk.
Because it scan s fi les t his wa y, the Syst em Sca n mo dule can se rv e as a bac ku p
in case any of the other VShield modules does not detect a virus when it first
enters your system. In its initial configuration, the module will deny access to
any infected file it finds, whichever Windows version your computer runs. It
will also display an alert message that asks you what you want to do about the
virus. The response options you see in this dialog box come from default
choices or choices you make in the System Scan module’s Action page.
As this dialog box awaits your response, your computer will continue to
process any other tasks it is running in the backgro und.
User’s Guide 59
Page 60

Removing Infections From Your System
Figure 3-1. Initial System Scan response options
If your computer runs Windows 95 or Windows 98, you can choose to display
a different virus alert message. If you select BIOS in the Prompt Type area in
the System Scan module Action page, you’ll see instead a full-screen warning
that offers you response options.
This alert message brings your system to a complete halt as it awaits your
response. No other programs or system operations run on your system until
you choose one of the response options shown.
The BIOS prompt type also allows you to substitute a Continue option for the
Move File option. To do so, select the Continue access checkbox in the
module’s Action page.
60 McAfee VirusScan
Figure 3-2. Full-screen Warning - System Scan response options
NOTE: The Continue access checkbox is unavailable if your computer
runs Windows NT Workstation v4.0 or Windows 2000, or if you choose
the GUI prompt type on Windows 95 and Windows 98 systems.
Page 61

Removing Infections From Your System
To take one of the actions shown in an alert message, click a button in the
Access to File Was Denied dialog box, or type the letter highlighted in yellow
when you see the full-screen warning. If you want the same response to apply
to all infected files that the System Scan module finds during this scan
operation, select the Apply to all items checkbox in the dialog box. This option
is not available in the full-screen alert message.
Your response options are:
• Clean the file. Click Clean in the dialog box, or type C when you see the
full-screen warning, to tell the System Scan module to try to remove the
virus code from the infected file. If th e mod ule succeed s, it w ill restore th e
file to its original state and record its success in its log file.
If the module cannot clean the file—either because it has no remover or
because the virus has damaged the file beyond repair—it will note th is
result in its log file, but will take no other action. In most cases, you should
delete such files and restore them from backups.
• Delete the file. Click Delete in the dialog box, or type D when you see the
full-screen warning, to tell the System Scan module to delete the infected
file immediately. By default, the module notes the name of th e infected file
in its log file so that you have a record of which files it flagged as infected.
You can then restore deleted files from backup copies.
• Move the file to a different locat ion. Click Move File to in the dialog box.
This opens a browse window you can use to locate your quarantine folder
or another folder you want to use to isolate infected files. Once you select a
folder, the System Scan module moves the infected file to it immediately.
This option does not appear in the full-screen warning.
• Continue working. Type O when you see the full-screen warning to tell the
System Scan module to let you continue working with the file and not take
any other action. Normally, you would use this option to bypass files that
you know do not have viruses. If you have its reporting option enabled, the
module will note each incident in its log file. This option is not available in
the Access to File Was Denied dialog box.
• Stop the scan operation. Click Stop in the dialog box, or type S when yo u
see the full-screen warning, to tell the System Scan module to deny any
access to the file but not to take any other action. Denying access to the file
prevents anyone from opening, saving, copying or renaming it. To
continue, you must click OK. If you have its reporting option enabled, the
module will note each incident in its log file.
• Exclude the file from scan operations. Click Exclude in the dialog box, or
type E when you see the full-screen warning, to tell the System Scan
module to exclude this file from future scan operations. Normally, you
would use this option to bypass files that you know do not have viruses.
User’s Guide 61
Page 62

Removing Infections From Your System
Responding when the E-mail Scan module detects a virus
NOTE: This feature only applies to exchange server e-mails.
This module looks for viruses in e-mail messages you receive via corporate
e-mail systems such as cc:Mail a nd Microsoft Exchange. In its initial
configuration, the module will prompt you to choose a response from among
five options whenever it detects a virus.
Figure 3-3. E-mail Scan module response options
Click the button that corresponds to the response you want. Your choices are:
• Stop. Click this button to stop the scan operation immediately. The E-Mail
• Clean. Click this button to have the E-Mail Scan module software try to
• Delete. Click this button to delete the file from your system immediately.
• Move file to. Click this button to open a dialog box that you can use to
62 McAfee VirusScan
Scan module will record each detection in its log file , bu t it will take no
other action to respond to the virus.
remove the virus code from the infected file. If it cannot clean the
file—either because it has no remover or because the virus has damaged
the file beyond repair—it will record the incident in its log file and suggest
alternative responses. In the example shown in Figure 3-3, the module
failed to clean the EICAR test file—a mock “virus” written specifically to
test whether your anti-virus software installed correctly. Here, Clean is no t
an available response option. In most cases, you should delete such files
and restore them from backups.
By default, the E-Mail Scan module will record the name of the infected file
in its log so that you can restore the file from a backup copy.
locate your quarantine folder, or another suitable folder. Once you have
located the correct folder, click OK to transfer the file to that location.
Page 63

Removing Infections From Your System
• Exclude. Click this button to prevent th e E-Mail Scan module from
flagging this file as a virus in future scan operations. If you copy this file to
your hard disk, this also prevents the System Scan module from detecting
the file as a virus.
When you choose your action, the E-Mail Scan module will implement it
immediately and add a notice to the top of the e-mail message that contained
the infected attachment. The notice gives the file name of the infected
attachment, identifies the name of the infecting virus, and describes the action
that the module took in response.
To apply the response you chose to all infected files that the E-Mail Scan
module finds during this scan operation, select the Apply to all items
checkbox in the dialog box.
Responding when the Download Scan module detects a virus
This module looks for viruses in e-mail messa ges and other files you receive
over the Internet via a web browser or such e-mail client programs as Eudora
Light, Netscape Mail, Outlook Express, and others. It will not detect files you
download with FTP client applications, terminal applications, or through
similar channels. In its initial configuration, the module will prompt you to
choose a response from among three options whenever it detects a virus
(Figure 3-4). A fourth option provides you with additional information.
Figure 3-4. Download Scan response options
Click the button that corresponds to the response you want. Your choices are:
• Continue. Click this to tell the Download S c an module to take no action
and to resume scanning. The module will continue until it finds another
virus on your system or until it finishes the scan operation. Normally, you
would use this option to bypass files that you know do not have viruses, or
if you plan to leave your computer unattended as you download e-mail or
other files. The module will note each incident in its log file.
• Delete. Click this to tell the Download Scan module to delete the infected
file or e-mail attachment you received. By default, the module notes the
name of the infected file in its log file.
User’s Guide 63
Page 64

Removing Infections From Your System
• Move. Click this to tell the Download Scan module to move the infected file
to the quarantine directory you chose in the module’s Action property
page.
When you choose your action, the Download Scan module will implement it
immediately and add a notice to the top of the e-mail message that contained
the infected attachment. The notice gives the file name of the infected
attachment, identifies the name of the infecting virus, and describes the action
that the module took in response.
Responding when Internet Filter detects a virus
This module looks for hostile Java classes or ActiveX controls whenever you
visit a website or download files from the Internet. You can also use the
module to block your browser from connecting to dangerous Internet sites. In
its initial configuration, the module will a sk you whenever it encounters a
potentially harmful object whether you want to Deny the object access to your
system or you want to Continue and allow th e object a ccess. It will offer you
the same choice when you try to connect to a potentially dangerous website
(Figure 3-5).
Figure 3-5. Internet Filter response options
Responding when the VirusScan application detects a virus
When you first run a scan operation with the VirusScan application, it will
look at all files on your C: drive that are susceptible to virus infection. This
provides you with a basic level of protection that you can extend by
configuring VirusScan software to suit your own needs.
With this initial configuration, the program will prompt you for a response
when it finds a virus (Figure 3-6).
64 McAfee VirusScan
Page 65

Removing Infections From Your System
Figure 3-6. VirusScan response options
To respond to the infection, click one of the buttons shown. You can tell the
VirusScan application to:
• Continue. Click this button to proceed with the scan operation and have
the application list each infected file in the lo wer portion of its main
window (Figure 3-7), record each detection in its log file, but take no other
action to respond to the virus. Once the application finishes examining
your system, you can right-click each file listed in the main window, then
choose an individual response from the shortcut menu that appears.
Figure 3-7. VirusScan main window
• Stop. Click this button to stop the scan operation imm edi ately. The
VirusScan application will list the infected files it has already found in the
lower portion of its main window (Figure 3-7) and record each detection in
its log file, but it will take no other action to respond to the virus.
Right-click each infected file listed in the main window, then choose an
individual response from the shortcut menu that appears.
User’s Guide 65
Page 66

Removing Infections From Your System
• Clean. Click this button to have the VirusScan application try to remove
the virus code from the infected file. If it cannot clean the file—either
because it has no remover or because the virus has damaged the file
beyond repair—it will record the incident in its log file and suggest
alternative responses.
In the example shown in Figure 3-6, the appli cation failed to clean the
EICAR Test Virus—a mock “virus” written specifically to test whether
your anti-virus software installed correctly. Here, Clean is not an available
response option. In most cases, you should delete such files and restore
them from backups.
• Delete. Click this button to delete the file from your sy stem immediately.
By default, the VirusScan application will record the name of the infected
file in its log so that you can restore the file from a backup copy.
• Move file to . Click this to open a dialog box that you can use to locate your
quarantine folder, or another suitable folder. Once you have located the
correct folder, click OK to transfer the file to that location.
• Info. Click this to connect to the McAfee VirusScan Virus Information
Library. This choice does not take any action against the virus that the
application detected.
Responding when the E-Mail Scan extension detects a virus
NOTE: This feature only applies to exchange server e-mails.
The E-Mail Scan extension included with VirusScan software lets you scan
incoming Microsoft Exchange or Microsoft Outlook e-mail messages for
viruses at your initiative. You can start it from within either e-mail client and
use it to supplement the continuous e-mail background scanning you get with
the VShield E-Mail Scan module. The E-Mail Scan module also offers the
ability to clean infected file attachments or stop the scan operation, a capability
that complements the continuous monitoring that the E-Mail Scan module
provides. In its initial configuration , E-Mail Scan extension will prompt you
for a response when it finds a virus (Figure 3-8).
66 McAfee VirusScan
Page 67

Removing Infections From Your System
Figure 3-8. E-Mail Scan response options
To respond to the infection, click one of the buttons shown. You can tell the
E-Mail Scan extension to:
• Continue. Click this button to have the E-Mail Scan extension proceed with
its scan operation, list each infected file it finds in the lo wer portion of its
main window (Figure 3-9), and record each detection in its log file, but it
will take no other action to respond to th e virus. The extension will
continue until it finds another virus on your system or until it finishes the
scan operation. Once it has finished examining your system, you can
right-click each file listed in the main window, then choose an individual
response from the shortcut menu that appears.
• Stop. Click this button to stop the scan operation immediately. The E-Mail
Scan extension will list the infected files it has already f oun d in th e low er
portion of its main window (Figure 3-9) and record each detection in its log
file, but it will take no other action to respond to the virus. Right-click each
infected file listed in the main window, then choose an individual response
from the shortcu t menu that appears.
User’s Guide 67
Page 68

Removing Infections From Your System
Figure 3-9. E-Mail Scan extension window
• Clean. Click this button to remove the virus code from the infected file. If
the E-Mail Scan extension cannot clean the file—either because it has no
remover or because the virus has damaged the file beyond repair—it will
record the incident in its log file and suggest alternative responses. In the
example shown in Figure 3-8, Clean is not an available response option. In
most cases, you should delete such files and restore them from backups.
• Delete. Click this button to delete the file from your system. By default, the
E-Mail Scan extension will record the name of the infected file in its log so
that you can restore the file from a backup copy.
• Move. Click this button to open a dialog box that you can use to locate your
quarantine folder, or another suitable folder. Once you have located the
correct folder, click OK to transfer the file to that location.
• Info. Click this to connect to the McAfee VirusScan Virus Information
Library. This choice does not cause the E-Mail Scan extension to take any
action against the virus it detected.
Viewing virus information
Clicking Info in any of the virus response dialog boxes will connect you to the
McAfee VirusScan online Virus Information Library, provided you have an
Internet connection and web browsing software available on your computer
(Figure 3-10).
68 McAfee VirusScan
Page 69

Removing Infections From Your System
Figure 3-10. McAfee VirusScan Virus Information Library page
The Virus Information Library has a collection of documents that give you a
detailed overview of each virus that VirusScan software can detect or clean,
along with information about how the virus infects and alters files, and the
sorts of payloads it deploys. The site lists the most prevalent or riskiest viruses,
provides a search engine you can use to search for particular virus
descriptions alphabetically or by virus name, displays prevalence tables,
technical documents, and white papers, and gives you access to technical data
you can use to remove viruses from your system.
To connect directly to the library, visit the site at:
http://vil.nai.com/villib/alpha.asp
You can also connect directly to the Library from the VirusScan Console
—choose Virus List from the View menu in the Console window.
You’ll find the Library at McAfee VirusScan AVERT website:
http://www.nai.com/asp_set/anti_virus/avert/intro.asp
The AVERT website has a wealth of virus-related data and software.
Examples include:
• Current information and risk assessments on emerg ing and active virus
threats
• Software tools you can use to extend or supplement your McAfee
VirusScan anti-virus software
User’s Guide 69
Page 70

Removing Infections From Your System
• Contact addresses and other information for submitting questions, virus
samples, and other data
• Virus definition updates-this includes daily beta .DAT file updates,
EXTRA.DAT files, updated Emergency .DAT files, current scan engine
versions, regular weekly .DAT and SuperDAT updates, and new
incremental virus definition files (.UPD)
• Beta and “first look” software
Viewing file information
If you right-click a file listed either in the VirusScan main win d ow or the
E-Mail Scan window (see Figure 3-9), then choose File Info from the shortcut
menu that appears, VirusScan software will open an Infected Item Information
dialog box that names the file, lists its type and size in bytes, gives its creation
and modification dates, and describes its attributes (Figure 3-11).
Figure 3-11. Infected File Information property page
Submitting a virus sample
If you have a suspicious file that you believe contains a virus, or experience a
system condition that might result from an infection—but VirusScan software
has not detected a virus—McAfee VirusScan Software recommends that you
send a sample to its anti-virus research team for analysis. When you do so, be
sure to start your system in the apparently infected st ate—don’t start your
system from a clean floppy disk.
70 McAfee VirusScan
Page 71

Removing Infections From Your System
Several methods exist for capturing virus samples and submitting them. The
next sections discuss methods suited to particular conditions.
Using the SendVirus utility to submit a file sample
Because the majority of later-generation viruses tend to infect document and
executable files, VirusScan software comes with SENDVIR.EXE, a utility that
makes it easy to submit an infected file sample to McAfee VirusScan
researchers for analysis.
To submit a sample file, follow these step s:
1. If you must connect to your network or Internet Service Provider (ISP) to
send e-mail, do so first. If you are continuously connected to your
network or ISP, skip this step and go to Step 2.
2. Locate the file SENDVIR.EXE in your VirusScan program directory. If
you installed your VirusScan software with default Setup options, you’ll
find the file here:
C:\Program Files\McAfee VirusScan\VirusScan
3. Double-click the file to display the first AVERT Labs Response Center
wizard panel (Figure 3-12).
Figure 3-12. First SENDVIR.EXE panel
4. Read the welcome message, then click Next> to continue.
The Contact Information wizard panel appears.
User’s Guide 71
Page 72

Removing Infections From Your System
5. If you want AV ERT researchers to contact you about your submission,
enter your name, e-mail address, and any message you would like to
send along with your submission in th e text boxes provided, then click
Next> to continue.
NOTE: You may submit samples anonymously, if you prefer—
simply leave the text boxes in this panel blank. You are under no
obligation to supply any information at all here.
Figure 3-13. Your Contact Information panel
72 McAfee VirusScan
The Choose Files to Submit panel appears (Figure 3-14).
Figure 3-14. Choose Files to Submit panel
Page 73

Removing Infections From Your System
6. Click Add to open a dialog box you can use to locate the files you believe
are infected.
Choose as many files as you want to submit for analysis. To remove any
of the files shown in the submission lis t, select it, then click Remove.
When you have chosen all of the files you want to submit, click Next> to
continue.
The Choose Upload Options panel appears (Figure 3- 15).
Figure 3-15. Choose Upload options panel
If the file you want to submit is a Microsoft Office document or another
file that contains information you want to keep confidential, select the
Remove my personal data from file checkbox, then click Next> to
continue. This tells the SENDVIR.EXE utility to strip everything out of
the file except macros or executable code.
The Choose E-Mail Service panel appears (Figure 3-16).
User’s Guide 73
Page 74

Removing Infections From Your System
7. Select the type of e-mail client application you have installed on your
computer. Your choices are:
• Use outgoing Internet mail. Click this button to send your sample
via a Simple Mail Transfer Protocol e-mail client, such as Eudora,
NetScape Mail, or Microsoft Outlook Express. Next, enter the name
of your outgoing mail server in the text box
provided-mail.domain.com, for example.
Figure 3-16. Choose E-mail Service panel
8. Click Finish to send yo ur sample.
74 McAfee VirusScan
• Use Microsoft Exchange. Click this button to send your sample via
your corporate e-mail system. To use this option, your e-mail
system must support the Messagin g Application Programming
Interface (MAPI) standard. Examples of such systems include
Microsoft Exchange, Microsoft Outlook, and Lotus cc:Mail v8.0 and
later.
NOTE: Although McAfee VirusScan researchers appreciate your
submission, their receipt of your message does not obligate them to
take any action, provide any remedy, or respond in any way to you.
SENDVIR.EXE will use the e-mail client you specif ied to send your
sample. You must have connected to your network or ISP in order for this
process to succeed.
Page 75

Removing Infections From Your System
Capturing boot sector, file-infecting, and macro viruses
If you suspect you have a virus infection, you can collect a sample of the virus,
then either create a floppy disk image to send via e-mail, or mail the floppy
disk itself to McAfee VirusScan anti-virus researchers. The researchers would
also benefit from having samples of your current system files on a separate
floppy disk.
Capturing boot-sector infections
Boot-sector viruses frequently hide in areas of your hard disk or floppy disks
that you ordinarily cannot see or read. You can, however, capture a sample of
a boot-sector virus by deliberately infecting a floppy disk with it.
To do so, follow th ese ste ps:
1. Insert a new, unformatted floppy disk into your floppy drive.
2. Click Start in the Windows task bar, point to Programs, then choose
MS-DOS Prompt if your computer runs Windows 95 or Windows 98, or
Command Prompt if your computer runs Windows NT Workstation
v4.0 or Windows 2000 Professional.
3. Type this line at the command prompt:
format a: /s
If your system hangs as it tries to format the disk, remove the disk from
your floppy drive. Next, label the disk “Damaged during infected format
as boot disk,” then set it aside.
4. Insert a new, formatted floppy disk into your floppy drive.
5. Copy your current system files to that disk. For most DOS versions, those
files will include:
•IO.SYS
•MSDOS.SYS
•COMMAND.COM
For Windows systems, copy these files to the sam e prefo r matted disk:
• GDI.EXE
• KRNL286.EXE or KRNL386.EXE
• PROGMAN.EXE
6. Label the diskette “Contain s infected files,” then set it aside.
User’s Guide 75
Page 76

Removing Infections From Your System
Capturing file-infecting or macro viruses
If you suspect you have a file-infecting virus or a macro virus that has infected
any of your Microsoft Word, Excel, or PowerPoint files, send these files to
McAfee VirusScan’s anti-virus researchers, either with the SENDVIR.EXE
utility, via e-mail as floppy disk ima ges, or through the mail on floppy disk:
• If you suspect that a virus has infected executable files on yo ur system,
copy COMMAND.COM to a formatted floppy disk, then change its file
extension to a non-executable extension.
• If you suspected that a macro virus has infected your Microsoft Word files,
copy NORMAL.DOT and all files from the Microsoft Office Startup folder
to the floppy disk. You’ll find the Microsoft Office startup files h ere, if you
installed Office to its default location:
C:\Program Files\Microsoft Office\Office\Startup
• If you suspect that a macro virus has infected your Microsoft Excel files,
copy all files from C:\Program Files\Microsoft Office\Office\XLSTART
to the disk. Include all files you have installed in alternative startup file
locations.
• If you suspect that a macro virus has infected your PowerPoint files, copy
the file BLANKPRESENTATION.POT from C:\Program Files\Microsoft
Office\Templates to the disk.
Making disk images
To send the files now stored on any floppy disks you created, you can use a
McAfee VirusScan AVERT Labs tool called RWFLOPPY.EXE to ma ke a floppy
disk image that encapsulates the infection. The RWFLOPPY.EXE tool does not
come with your VirusScan software, but you can download it from this
location:
The AVERT site stores the tool as a compressed .ZIP file. Download the file to
your computer, then extract it to a temporary folder on your hard disk. The
.ZIP package contains a brief text file that explains the syntax for using the
RWFLOPPY.EXE utility.
76 McAfee VirusScan
http://www.nai.com/asp_set/anti_virus/avert/tools.asp
NOTE: If you suspect you have a boot virus, you must use RWFLOPPY
to send your samples electronically; otherwise, you must send your
samples physically on a diskette. If you send them electronically without
using RWFLOPPY, the samples w ill be incomplete or unusable, as boot
viruses often hide beyond the last sectors of a diskette, and other diskette
image creation programs cannot obtain this data.
Page 77

Removing Infections From Your System
Once you create images of the disks you want to send, you can send them as
file attachments in an e-mail message to McAfee VirusScan’s anti-virus
researchers.
Preparing file archives to send
Try to fit as many of file samples as you can on a single floppy disk. To do so,
compress the samples that you captured on disk to a single .ZIP file with
password protection. Here’s a suggested procedure that uses the WinZip
utility:
1. Start WinZip.
2. Press CTRL+N to create a new archive.
The New Archive dialog box appears.
3. Enter a name for the new archive, then click OK.
4. Press CTRL+A to add files to the new archive.
The Add dialog box appears.
5. Click Password to display the Password dialog box.
6. Type INFECTED in the Password text box, then click OK.
7. When prompted, retype your password to verify its accuracy, then click
OK.
The Add With Password dialog box appears.
8. Select your sample files, then click OK.
WinZip applies the password you entered to all files that you add to or
extract from your archive. Password-protected files appear in the archive
list with a plus sign (+) after their names.
NOTE: If you do not protect your samples with the password
INFECTED, McAfee VirusScan’s anti-virus scanners may detect and
clean samples before they reach our researchers.
9. Attach the .ZIP file that you created to an e-mail message.
Sending samples via e-m ail
Once you’ve made disk images or created a file archive for your samples, send
them to McAfee VirusScan’s researchers at one of these e-mail addresses:
User’s Guide 77
Page 78

Removing Infections From Your System
In the United States virus_research@nai.com
In the United Kingdom vsample@nai.com
In Germany virus_research_de @nai .c om
In Japan virus_research_ja pan @nai .c om
In Australia virus_research_ap ac @nai .co m
In the Netherlands virus_research_eu rope @ na i.c om
In your message, include this info rm ation:
• Which symptoms cause you to suspect that y our ma chine is infected
• Which product and version number detected the virus, if any did, and
what the results were
• Your VirusScan and .DAT file version numbers
• Details about your system that might help to reproduce the environment in
which you detected the virus
• Your name, company name, phone number, and e-mail addre ss, if possible
• A list of all items contai ned in the package you are sending
Mailing infected floppy disks
You can also mail the actual disks you created directly to McAfee VirusScan
anti-virus researchers. McAfee VirusScan Software recommends that you
create a text file or write a message to accompany the disks that includes the
same information you would submit with an electronic disk image. Send your
sample to only one research lab address so that you can receive the fastest
possible response to your issue. Use these mailing addresses:
In the United States:
Network Associates, Inc.
Virus Research
20460 NW Von Neumann Drive
Beaverton, OR 97006
In the United Kingdom:
Network Associates, Inc.
Virus Research
Gatehouse Way
Aylesbury, Bucks HP19 3XU
UK
78 McAfee VirusScan
Page 79

Removing Infections From Your System
In Germany:
Network Associates, Inc.
Virus Research
Luisenweg 40
20537 Hamburg
Germany
In Australia:
Network Associates, Inc.
Virus Research
500 Pacific Highway, Level 1
St. Leonards, NSW
Sydney
Australia 2065
In Japan:
Network Associa tes, Inc.
Virus Research
9F Toranomon Mori-bldg. 33
3-8-21 Toranomon, Minato-Ku
Tokyo
Japan 105-0001
In Europe:
Network Associa tes, Inc.
Virus Research
Gatwickstraat 25
1043 GL Amsterdam
Netherlands
NOTE: Network Associates AVERT Labs does keep all submitted
samples, but once you submit a sample, AVERT cannot return it to you.
AVERT does not accept or process Iomega Ditto or Jazz cartridges,
Iomega Zip disks, or other types of removable media .
User’s Guide 79
Page 80

Removing Infections From Your System
80 McAfee VirusScan
Page 81
4Using the VShield Scanner
What does the VShield scann er do?
McAfee VirusScan desktop anti-virus products use two g e neral methods to
protect your system. The first method, background scanning, operates
continuously, watching for viruses as you use your computer for everyday
tasks. In the VirusScan product, the VShield scanner performs this function. A
second method allows you to initiate your own scan operations. The
VirusScan application generally handles these tasks.
Depending on how you configure it, the VShield scanner can monitor any file
that arrives on or leaves your system, whether on floppy disk, over your
network, in file attachments that accompany e-mail messages, or from the
Internet. The scanner looks for viruses as you open, save, copy, rename or
otherwise modify your files, and it probes your computer’s memory during
any file activity. The scanner starts when you start your computer, and stays
in memory until you shut it or your system down. The scanner also includes
optional features that guard against hostile Java applets and ActiveX controls,
and that keep your computer from connecting to dangerous Internet sites.
The VShield scanner consists of five related modules, each of which has a
specialized function. You can configure settings for all of these modules in the
VShield Properties dialog box. The VShield modules are:
4
• System Scan. This module looks for viruses on your hard disk as you work
with your computer. It tracks files as your system or other computers read
files from your hard disk or write files to it. It can also scan floppy disks and
network drives mapped to your system.
• E-Mail Scan. This module scans e-mail messages and message attachments
that you receive via intraoffice e-mail systems, and via the Internet. It scans
your Microsoft Exchange or Outlook mailbox on your Microsoft Exchange
server, and older cc:Mail e-mail systems.
It works in conjunction with the Download Scan module to scan Internet
mail that arrives via Simple Mail Transfer Protocol (SMTP) or Post Office
Protocol (POP-3) sources.
• Download Scan. This module scans files that you download to your
system from the Internet. If you have enabled the Internet mail option in
the E-Mail Scan module, this will include e-mail and file attachments that
arrive via SMTP or POP-3 e-mail systems, which include such e-mail client
programs as Eudora Pro, Microsoft Outlook Express, NetScape mail, and
America Online mail.
User’s Guide 81
Page 82

Using the VShield Scanner
• Internet Filter. This module looks for and blocks hostile Java classes and
ActiveX controls from downloading to and executing from your system as
you visit Internet sites. It can also block your browser from connecting to
potentially dangerous Internet sites that harbor malicious software.
IMPORTANT: To use the E-Mail Scan, Download Scan or Internet
Ë
Filter modules, you must install them from the Custom option in
Setup.
• Security. This module provides password protection for the remaining
VShield modules. You can protect any or all individual module property
pages and set a password to prevent unauthorized changes.
NOTE: Because the VShield scanner runs continuously, you should
not install or run more than one VShield scanner on the same
workstation. Doing so can cause the scanners to interfere with each
others' operations.
Why use the VShield scanner?
The VShield scanner has unique capabilities that make it an integral part of the
VirusScan comprehensive anti-virus software security package. These
capabilities include:
• On-access scanning. This means that the scanner looks for viruses i n f iles
that you open, copy, save, or otherwise modify, and files that you read
from or write to floppy disks and network drives. It therefore can detect
and stop viruses as soon as they appear on your system, including those
that arrive via e-mail or as downloads from the Internet. This means you
can make the VShield scanner both your first line of anti-virus defense, and
your backstop protection in between each scan operation that you perform .
The VShield scanner detects viruses in memory and as they attempt to
execute from within infected files.
• Malicious object detection and blocking. The VShield scanner can block
harmful ActiveX and Java objects from gaining access to your system,
before they pose a threat. The scanner does this by scanning the hundreds
of objects you download as you connect to the web o r to other Internet sites,
and the file attachments you receive with your e-mail. It compares these
items against a current list of harmful objects that it maintains, and blocks
those that could cause problems.
82 McAfee VirusScan
Page 83

• Internet site filtering. The VSh ield scanner comes with a list of dangerous
web- or Internet sites that pose a hazard to your system, usually in the form
of downloadable malicious software. You can add any other site that you
want to keep your browser software from connecting to, either by listing its
Internet Protocol (IP) address or its domain name.
• Automatic operation. The VShield scanner integrates with a range of
browser software and e-mail client applications. This allows the scanner to
log on to and scan your e-mail attachments for viruses before they ever
reach your computer.
If you connect to the Internet or work on a network in any capacity, leaving
this component running at all tim es can significantly improve your ability to
detect and dispose of harmful software before it has a chance to damage your
system.
Browser and e-mail client support
The VShield scanner works seamlessly with many of the mo st popular web
browsers and e-mail client software available for the Windows platform. To
work with your browser, the scanner requires no setup beyond what you have
already done to connect your computer to the Internet. You must configure the
scanner, however, to work correctly with your e-mail client software.
Using the VShield Scanner
McAfee VirusScan Software has tested these web browsers and verified that
they work correctly with the VShield scanner:
• Netscape Navigator v3.x
• Netscape Navigator v4.0.x (not including v4.0.6)
• Microsoft Internet Explorer v3.x, v4.x and v5.x
User’s Guide 83
Page 84

Using the VShield Scanner
McAfee VirusScan Software has also tested these e-mail clients and verified
that they work with the VShield Download Scan module:
• Microsoft Outlook Express
• Qualcomm Eudora v3.x and v4.x
• Netscape Mail (included with most versions of Netscape Navigator and
Netscape Communicator)
• America Online mail v3.0, v4.0 and v5.0
In order to work with the VShield E-mail Scan module, your corporate e-mail
system must use Lotus cc:Mail, Microsoft Exchange, or Microsoft Outlook
client. McAfee VirusScan Software has tested these clients and has verified
that they work correctly with the E-mail Scan module:
• Microsoft Exchange v4.0, v5.0 and v5.5
• Microsoft Outlook 97 and Outlook 98
• Lotus cc:Mail v6.x, v7.x, and v8.x (not MAPI-compliant)
McAfee VirusScan Software does not certify VShield s oftware compatibility
with client software not listed above.
Enabling or starting the VShield scanner
At the end of the VirusScan installation, Setup asks if you want to enable the
VShield scanner at that time. If you agree, the VShield scanner should load
into memory immediately and begin working with a default set of options that
give you basic anti-virus protection. If you do not agree, the VShield scanner
will load automatically the next time yo u restart your computer.
When the VShield scanner first starts, it displays an icon in the Windows
system tray that indicates which of its modul e s are active.
At first, the scanner enables only its System Scan module, which scan s viruses
that arrive on your system from floppy disks and other removable media,
from local-area network connections, and similar areas. The System Scan
module also scans files that arrive via your e-mail system and from the
Internet, but to do so, it requires the aid of the other VShield modules: E-Mail
Scan, Download Scan, and Internet Filter.
Ë IMPORTANT: To use the E-Mail Scan, Download Scan or Internet Filter
If your computer runs Windows NT Workstation v4.0 or Windows 2000
Professional, the VShield scanner loads as a Windows NT service called
McShield, which you can see in the Windows Services control panel.
84 McAfee VirusScan
modules, you must install them from the Custom option in Setup.
Page 85

Using the VShield Scanner
NOTE: McAfee VirusScan Software recommends that you do not start or
stop the VShield service from the Windows control panel. Instead, you
can stop and restart the scanner from the provided VirusScan control
panel.
If your computer runs Windows 95 or Windows 98, the scanner loads in a way
that mimics a Windows service on that platform. This service is not visible in
the Windows user interface.
Starting the scanner automatically
If the VShield scanner does not start automatically, you can set it to do so in
the VirusScan control panel.
Follow these steps :
1. Click Start in the Windows taskbar, point to Settings, then choose
Control Panel.
2. Locate and double-click the VirusScan control panel to open it.
3. Click the Componen ts tab (Figure 4-1).
Figure 4-1. VirusScan control panel - Components page
4. Select the Load VShield on startup checkbox at the top of the
Components property page.
5. Click OK to close the control panel.
Enabling the VShield scanner and its modules
Once you have all VShield components installed, you can use any of four
methods to enable them, in various combinations.
User’s Guide 85
Page 86

Using the VShield Scanner
NOTE: Enabling a module means activating it and loading it into your
Method 1: Use the VShield shortcut menu
Follow these steps :
1. Right-click the VShield icon in the Windows system tray to display its
2. Point to Quick Enable.
3. Choose one of the module names shown without a check mark. Module
Depending on which combination of modules you enable, the VShield icon
will display a different state.
computer’s memory for use. The VShield scanner can start and remain
active in memory even with none of its modules enabled.
shortcut menu.
names that have a check mark beside them are active. Those without a
check mark are inactive. If you use this method to enable a module, it
remains enabled until you restart your VirusScan software or your
computer. At that point, its state will depend on whether you have
enabled or disabled the module in the VirusScan Properties dialog box.
Method 2: Use the System Scan Status dialog box
Follow these steps :
1. Double-click the VShield icon in the Windows system tray to open the
System Scan Status dialog box (Figure 4-1).
Figure 4-1. System Scan Status dialog box
2. For each module that you want to enable, click the corresponding tab,
then click Enable. The same button in the property page for active
modules will read Disable.
3. Click Close to close the dialog box.
86 McAfee VirusScan
Page 87

Using the VShield Scanner
Depending on which combin ation of modules you enable, the VShield icon
will display a different state.
Method 3: Use the VShield Properties dialog bo x
Follow these steps :
1. Right-click the VShield icon in the Windows system tray to display the
VShield shortcut menu, point to Properties, then choose System Sca n
to open the VShield Properties dialog box.
Figure 4-2. VShield Properties dialog box
2. For each module that you want to enable, click the corresponding icon
along the left side of the dialog box, then click the Detection tab.
3. Select the Enable checkbox at the top of each page.
As you do so, the scanner enables that module. Depending on which
combination of modules you enable, the VShield icon displays a different
state.
If you enable all of its modules, the sca nner will display in the Windows
system tray, unless you clear the Show icon in the taskbar checkbox in the
System Scan Detection property page.
User’s Guide 87
Page 88

Using the VShield Scanner
Method 4: Use the VirusScan Console
Follow these steps :
1. Double-click the VirusScan Console icon in the Windows system tray
2. Select VShield in the task list, then choose Enable from the Task menu.
3. Click the minimize or the close button in the upper-right corner of the
Understanding the VShield system tray icon states
to bring the Console window to the foreground.
the Console will enable the System Scan module a nd a ny o ther module
you had enabled previously. You cannot use this method to enable
individual modules other than the System Scan module.
Console window to shrink the Console window back to a system tray
icon.
NOTE: Do not choose Exit from the Task menu. This will shut the
Console down and unload it from memory. To run any tasks you
have scheduled, the Console must be active.
The VShield scanner displays four different icon states in the Windows system
tray to indicate which, if any, of its modules are active. An active module is one
that the VShield scanner has enabled, or loaded in to memory, and that is ready
to scan inbound and outbound files. An inactive module is one that the
VShield scanner has disabled. Such modules do not scan files.
The following table shows and describes each icon state:
This icon means that the VShield scanner has started and all VShield
modules are active
This icon means that the System Scan mo dule is activ e, but one or more
of the other VShield modules is inactive
This icon means that the System Scan module is inactive, but one or
more of the other VShield modules is active
This icon means that all VShield modules are inactive
88 McAfee VirusScan
Page 89

Using the VShield Scanner
Using the VShield configuration wizard
After you install VirusScan software and restart your computer, the VShield
scanner loads into memory immediately and begins working with a default set
of options that give you basic anti-virus protectio n. Unless you disable it or
one of its modules—or stop it entirely—you never have to worry about
starting the scanner or scheduli ng scan tasks for it.
To ensure more than a minimal level of security, however, you should
configure the scanner to work with your e-mail client software and have it
examine your Internet traffic closely for viruses and malicious software. The
VShield configu ratio n wizard can help you se t up ma ny of t hese opt ions r ight
away—you can then tailor the program to wor k better in your environment a s
you become more familiar with the scanner and your system’s susceptibility
to harmful software.
To start the VShie ld co nfi guratio n wizard:
1. Right-click the VShield icon in the Windows system tray to display the
VShield shortcut menu, point to Properties, then choose System Sca n
to open the VShield Properties dialog box.
2. Click Wizard in the lower-left corner of the dialog box to display the
configuration wizard welcome panel (Figure 4-3).
Figure 4-3. VShield configuration wizard - Welcome panel
3. Click Next> to display the System S c an configuration panel.
User’s Guide 89
Page 90

Using the VShield Scanner
Figure 4-4. VShield configuration wizard - System Scan panel
Here you can tell the VShield scanner to look for viruses in files
susceptible to infection whenever you open, run, copy, save or otherwise
modify them. Susceptible files include various types of executable files
and document files with embedded macros, such as Microsoft Office
files. The System Scan module will also scan files stored on floppy disks
whenever you read from or write to them, or when you shut down your
computer.
4. To enable these functions, click Yes, then click Next>. Otherwise, click
90 McAfee VirusScan
If it finds a virus, the module will sound an alert and prompt you for a
response. The module will also record its actions and summarize its
current settings in a log file that you can review later.
No, then click Next> to continue.
The E-mail Scan wizard panel will appear (Figure 4-5).
Figure 4-5. VShield configuration wizard - E-mail Scan panel
Page 91

Using the VShield Scanner
5. Select the Enable e-mail scanning checkbox, then select the checkbox
that corresponds to the type of e-mail client you use. Your choices are:
• Internet e-mail clients. Select this checkbox if you use a Post Office
Protocol (POP-3) or Simple Mail Transfer Protocol (SMTP) e-mail
client that sends and receives standard Internet mail directly or
through a dial-up connection. If you send and receive e-mail from
home and use Netscape Mail, America Online, or such popular
clients as Qualcomm’s Eudora or Microsoft’s Outlook Express, be
sure to select this option.
• Enable Corporate Mail. Select this checkbox if you use a
proprietary e-mail system at work or in a networked environment.
Most such systems use a central network server to receive and
distribute mail that individual users send to each other from client
applications. Such systems might send and receive mail f r om
outside the network or from the Internet, but they usually do so
through a “gateway” application run from the server.
The E-Mail Scan module supports corporate e-mail systems that fall
into two general categories:
– Lotus cc:Mail. Select this button if you use cc:Mail versions 6.x
and later, which use a proprietary Lotus protocol for sending
and receiving mail.
– MAPI-compliant e-mail client. Select this button if you use
Microsoft Exchange or Microsoft Outlook, as your corporate
e-mail system.
Specify which e-mail system you use, then click Next> to continue.
NOTE: If you use both types of mail systems, select both
checkboxes. Note that the E-Mail Scan module supports only
one type of corporate e-mail system at a time, however. If you
need to verify which e-mail system your office uses, check with
your network administrator.
Be sure to distinguish between Microsoft Outlook and
Microsoft Outlook Express. Although the two programs share
similar names, Outlook 97 and Outlook 98 are MAPIcompliant corporate e-mail systems, while Outlook Express
sends and receives e-mail through the POP-3 and SMTP
protocols. To learn more about these programs, consult your
Microsoft documentation.
User’s Guide 91
Page 92

Using the VShield Scanner
6. To have the Download Scan module look for viruses in each file that you
The next wizard panel sets options for the VShield Download Scan
module (Figure 4-6).
Figure 4-6. VShield Configuration Wizard - Download Scan panel
download from the Internet, select the Yes, do scan my downloaded
files for viruses checkbox, then click Next> to co ntinue.
The module will look for viruses in those files most susceptible to
infection and will scan compressed files a s you receive them.
Otherwise, select the No, do not enable download scanning checkbox,
then click Next> to continue.
The next wizard panel sets options for the VShield Internet Filter module
(Figure 4-7).
Figure 4-7. VShield configuration wizard - Internet Filter panel
92 McAfee VirusScan
Page 93

Using the VShield Scanner
7. To have the Internet Filter module block hostile Java and ActiveX objects
or dangerous Internet sites that can cause your system harm, select Yes,
enable hostile applet protection and access prevention to unsafe
websites, then click Next>.
The Internet Filter module maintains a list of harmful objects and sites
that it uses to check the sites you visit and the objects you encounter. If it
finds a match, it can either block it automatically, or offer you the chance
to allow or deny access.
To disable this function, select No, do not enable hostile applet
protection and access prevention to unsafe websites, then click
Next> to continue.
The final wizard panel summarizes the options you chose (Figure 4-8).
Figure 4-8. VShield configuration wizard - summary panel
8. If the summary list accurately reflects your choices, click Finish to save
your changes and return to the VShield Properties dialog box. Otherwise,
click <Back to change any options you chose, or Cancel to return to the
VShield Properties dialog box without saving any of your changes.
Setting VShield scanner properties
To ensure its optimal performance on your computer or in your network
environment, the VShield scanner needs to know what you want it to scan,
what you want it to ignore, what you want it to do if it finds a virus or other
malicious software, and how it should let you know when it has. You can use
the configuration wizard to enable most of the scanner’s protective options,
but if you want complete control over the program and the ability to adapt it
to your needs—including the ability to protect your settings with a
password—choose your options in the VShield Properties dialog box.
User’s Guide 93
Page 94

Using the VShield Scanner
The VShield Properties dialog box consists of a series of property pages that
control the settings for each program module. To choose your options, click
the icon for the appropriate program module, then click each tab in the
VShield Properties dialog box in turn.
To open the VShield Properties dialog box, right-click the VShield icon in
the Windows system tray to display the VShi el d shor tcut menu, point to
Properties, then choose System Scan.
The dialog box appears with the System Scan icon selected (Figure 4-9).
Figure 4-9. System Scan Properties dialog box - Detection page
Configuring the System Scan module
The VShield System Scan module is at the heart of the VShield
scanner. It scans files that come from any source, including those
that the other VShield modules direct to it from Internet
downloads and e-mail messages. The module can check your
system for viruses each time you open, run, copy, save, rename or otherwise
modify files on your hard disk, on any removable media attached to your
computer, or on network drives mapped to your system. It can also detect
viruses each time you read from or write to a floppy disk. As an advanced
option, you can activate heuristic scanning, which gives the scanner the
capability to detect unidentified or unclassified viruses.
94 McAfee VirusScan
Page 95

Using the VShield Scanner
The module can take a variety of automatic actions to respond to any viruses
it finds, and can report what it has done either with an alert message when it
takes the action or in a log file you can examine at your leisure. You can also
set it to ask you what to do when it finds a virus.
Elsewhere in this module, you can choose options that tell the VShield scanner
to display a state icon in the Windows taskbar that tells you at a glance
which, if any, VShield modules are active. Another option lets you disable the
System Scan module. This option might not be available if you run the
VirusScan software in secure mode.
To choose your options, click the System Scan icon at the left side of the System
Scan Properties dialog box to display the property pages for this module. The
next sections describe each of the configuration options for this module.
Choosing Detection options
When you first activate it, the System Scan module initially assumes that you
want it to scan for viruses each time you work with any file susceptible to virus
infection, whether on your hard disk or on floppy disks, and whether you read
the file from or write the file to your hard disk. The module will also examine
compressed files by default, but will not use heuristic scanning unless you
activate it.
NOTE: This property page will vary its appearance and have a different
option set, depending on which operating system your computer runs.
To modify these settings , follow t hese step s:
1. Verify that the Enable System Scan checkbox is selected.
Selecting this checkbox activates the rem aining options in this property
page. Clear the checkbox to disable all configuration options in this page
and to prevent the System Scan module from scannin g your system.
2. Tell the module when and where you want it to look for viruses. You can
have it
• Scan files as you work with them. Each time you open, run, copy,
save, rename, or otherwise use files on your hard disk, virus code
can execute and spread infections to other files.
To prevent this on computers that run Windows NT Workstation
v4.0 or Windows 2000 Professional, select both the Inbound files
and the Outbound files checkboxes. On computers that run
Windows 95 or Windows 98, select each of the Run, Copy, Create,
and Rename checkboxes for full coverage.
User’s Guide 95
Page 96

Using the VShield Scanner
“Inbound” files are files that your computer or another system on
the network saves or writes to local hard disks attached to your
computer or to any network hard disks you have mapped to your
system. To include network drives mapped to your system for a
scan session, you must also select the Network drives checkbox.
Your system can receive data from your computer's memory, from
a floppy disk in your computer's floppy drive, from other systems,
from e-mail, or from other sources, then write that data to a file on
your hard disk. The VShield scanner treats all such data as
“inbound.”
“Outbound” files, meanwhile, are files that your computer or ot her
systems on the network read from local hard disks attached to your
system or from network disks mapped to your system. To include
network drives mapped to your system for a scan session, here too
you must select the Network drives checkbox.
Whenever your computer or another system reads data from a file
stored on a local hard disk attached to your system or a network
disk mapped to your system, the System Scan module treats that
data as “outbound.”
NOTE: If you have network drives mapped to your computer
from which yo u co py fi les, or i f othe r net wor k use rs c opy fil es
from your computer, McAfee VirusScan strongly recommends
that you have the VShield scanner installed both on your
computer and on the computer that “owns” the network drive.
Also, select all checkboxes in the Scan area in the Detection
page, plus the Network drives checkbox in the What to Scan
area.
96 McAfee VirusScan
Your copy of the System Scan module will then examine files
as your computer reads them from your hard disk, then again
as it writes them to the destination computer’s hard disk. If th e
destination computer has its own copy of the System Scan
module active, it too will scan the file as you write it to the
network drive if that System Scan module has the Inbound
files checkbox selected.
Page 97

Using the VShield Scanner
If you tend to copy files from one server that does n ot copy files
from your computer, and if other network users do the same,
you might want to configure your computers to scan only files
that they write to their hard disks—or only files that they read
from their hard disks—in order to prevent two computers from
scanning the same file. If you do so, however, you should
configure each computer identically. Otherwise, one computer
that scans only outbound files could copy an infected file from
a server that scans only inbound files.
• Scan files on floppy disks. Boot-sector viruses can hide in the boot
blocks of any formatted floppy disk, then load into memory as soon
as your computer reads your floppy drive. Select the Access
checkbox to have the System Scan module examine floppy disks
each time your computer reads from them or writes to them. Select
the Shutdown checkbox to have the module scan any floppy disks
that you leave in your drive as you shut down your computer. This
ensures that no viruses can load when your computer reads your
floppy drive at startup.
3. Specify the types of files you want the System Scan module to examine.
You can
• Scan compressed files. Select the Compressed files checkbox to
have the module look for viruses in compressed files or in file
archives. This option ensures that viruses do not spread from
compressed files, but because the module uncompresses these files
before it scans them, choosing this option can lengthen the time it
takes to scan a given set of files as you work with your computer.
NOTE: When the System Scan module examines a file archive,
it will scan only the file archive itself, not the compressed files
within the archive.
• Choose file types for scanning. Viruses cannot infect files that
contain no executable code, whether script, macro, or binary code.
You can, therefore, safely narrow the scope of your scan sessions so
that the module examines only those files most susceptible to virus
infection.To do so, select the Program files only button.
To see or designate the file name extensions that the System Scan
module will examine, click Extensions to open the Program File
Extensions dialog box (Figure 4-10).
User’s Guide 97
Page 98

Using the VShield Scanner
Figure 4-10. Program File Extensions dialog box
• Scan all files. Select the All files button to have the System Scan
module examine any file, whatever its extension, whenever you or
a system process modifies it in any wa y.
• Scan networked drives. To have the System Scan module look for
viruses on any drives mapped to your system that yo u use in any
way, select the Network drives checkbox.
NOTE: If you have network disks mounted on your system,
the System Scan module treats any files your system writes to
such drives as “inbound” files and any files your system reads
from such drives as “outbound” files. To ensure complete
coverage, select both of these checkboxes in the Scan area when
you select the Network drives checkbox.
4. Choose VShield software management options. These options let you
98 McAfee VirusScan
control your interaction with the VShield scanner. You can
• Disable the System Scan module at will. Select the System Scan
can be disabled checkbox in order to have the option to disable this
module. Note that McAfee VirusScan Software recommends that
you leave the System Scan module enabled for maximum
protection. Clearing this checkbox removes the Exit and System
Scan items from the VShield shortcut menu and the Disable button
from the VShield Status dialog box.
TIP: To ensure that nobody else who uses your computer will
Ð
disable the VShield scanner, or to enforce an anti-virus security
policy among VirusScan users on your network, clear this
checkbox, then protect the settings with a password. This will
keep other users from disabling the scanner from within the
VirusScan Cons ole, or fr om the VShi eld Prope rties dial og box.
Page 99

Using the VShield Scanner
You can also run the entire VirusScan product in secure mode,
which disables access to all configurable options .
• Display the VShield icon in the Windows system tray. Select the
Show icon in the Taskbar checkbox to have the VShield scanner
display this icon in the system tray. The particular state in which
the icon appears depends on which VShield modules you have
enabled.
Double-clicking the icon opens the VShield Status dialog box.
Right-clicking the icon displays a shortcut menu.
5. Turn on heuristic scan ning. Click Advanced to open the Advanced Scan
Settings dialog box (Figure 4-11).
Figure 4-11. Advanced Scan Settings dialog box
Heuristic scanning technology enables the System Scan module to
recognize new viruses based on their resemblance to similar viruses that
the module already knows. To do this, the module looks for certain
“virus-like” characteristics in the files you’ve asked it to scan. The
presence of a sufficient number of these characteristics in a file leads the
module to identify the file as potentially infected with a new or
previously unidentified virus.
Because the System Scan module looks simultaneously for file
characteristics that rule out the possibility of virus infection, it will rarely
give you a false indication of a virus infection. Therefore, unless you
know that the file does not contain a virus, you should treat “potential”
infections with the same caution you would confirmed infections.
The System Scan module starts out without any heuristic scan options
active. To activate heuristics scanning, foll ow these substeps:
a. Select the Enable heuristics scanning checkbox. The remaining
options in the dialog box activate.
User’s Guide 99
Page 100

Using the VShield Scanner
b. Select the types of heuristics scanning you want the System Scan
module to use. Your choices are:
– Enable macro heuristics scanning. Choose this option to
have the System Scan module identify all Microsoft Word,
Microsoft Excel, and other Microsoft Offic e files that contain
embedded macros, then compare the macro code to its virus
definitions database. The module will identify exact matches
with the virus name; code signatures that resemble existing
viruses cause the module to tell you it has found a potential
macro virus.
– Enable program file heuristics scanning. Choose this option
to have the System Scan module locate new viruses in program
files by examining file characteristics and comparing them
against a list of known virus characteristics. The module will
identify files with a sufficient number of these characteristics as
potentia l v ir u s e s .
– Enable macro and program file heuristics scanning.
Choose this option to have the module use both types of
heuristics scanning. McAfee VirusScan Software recommends
that you use this option for complete anti-virus protection.
6. Click the Action tab to choose additional System Scan module options.
100 McAfee VirusScan
NOTE: The System Scan module will use heuristic
scanning techniques only on the file types you design ate
in the Program File Extensions dialog box. If you choose
to scan All files, the module will use heuristic scanning for
all file types.
c. Click OK to save your settings and return to the VShield Properties
dialog box.
To save your changes without closing the System Scan Properties dialog
box, click Apply. To save your changes and close the dialog box, click
OK. To close the dialog box without saving your changes, click Cancel.
NOTE: Clicking Cancel will not undo any changes you already
saved by clicking Apply.
 Loading...
Loading...