Page 1
McAfee Email and Web Security
Appliance 5.1
Installation Guide
Page 2

COPYRIGHT
Copyright © 2009 McAfee, Inc. All Rights Reserved.
No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language in any form
or by any means without the written permission of McAfee, Inc., or its suppliers or affiliate companies.
TRADEMARK ATTRIBUTIONS
AVERT, EPO, EPOLICY ORCHESTRATOR, FLASHBOX, FOUNDSTONE, GROUPSHIELD, HERCULES, INTRUSHIELD, INTRUSION INTELLIGENCE,
LINUXSHIELD, MANAGED MAIL PROTECTION, MAX (MCAFEE SECURITYALLIANCE EXCHANGE), MCAFEE, MCAFEE.COM, NETSHIELD,
PORTALSHIELD, PREVENTSYS, PROTECTION-IN-DEPTH STRATEGY, PROTECTIONPILOT, SECURE MESSAGING SERVICE, SECURITYALLIANCE,
SITEADVISOR, THREATSCAN, TOTAL PROTECTION, VIREX, VIRUSSCAN, WEBSHIELD are registered trademarks or trademarks of McAfee, Inc.
and/or its affiliates in the US and/or other countries. McAfee Red in connection with security is distinctive of McAfee brand products. All other
registered and unregistered trademarks herein are the sole property of their respective owners.
LICENSE INFORMATION
License Agreement
NOTICE TO ALL USERS: CAREFULLY READ THE APPROPRIATE LEGAL AGREEMENT CORRESPONDING TO THE LICENSE YOU PURCHASED,
WHICH SETS FORTH THE GENERAL TERMS AND CONDITIONS FOR THE USE OF THE LICENSED SOFTWARE. IF YOU DO NOT KNOW WHICH
TYPE OF LICENSE YOU HAVE ACQUIRED, PLEASE CONSULT THE SALES AND OTHER RELATED LICENSE GRANT OR PURCHASE ORDER DOCUMENTS
THAT ACCOMPANIES YOUR SOFTWARE PACKAGING OR THAT YOU HAVE RECEIVED SEPARATELY AS PART OF THE PURCHASE (AS A BOOKLET,
A FILE ON THE PRODUCT CD, OR A FILE AVAILABLE ON THE WEB SITE FROM WHICH YOU DOWNLOADED THE SOFTWARE PACKAGE). IF YOU
DO NOT AGREE TO ALL OF THE TERMS SET FORTH IN THE AGREEMENT, DO NOT INSTALL THE SOFTWARE. IF APPLICABLE, YOU MAY RETURN
THE PRODUCT TO MCAFEE OR THE PLACE OF PURCHASE FOR A FULL REFUND.
License Attributions
Refer to the product Release Notes.
McAfee Email and Web Security Appliance 5.1 Installation Guide2
Page 3

Contents
Preface. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
Pre-installation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8
Using this guide. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
Audience. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
Graphical conventions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7
Documentation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7
What’s in the box. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8
Plan the installation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Inappropriate use. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Operating conditions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Positioning the appliance. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Considerations about Network Modes. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10
Transparent bridge mode. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11
Transparent router mode. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12
Explicit proxy mode. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
Deployment Strategies for Using the Appliance in a DMZ. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
SMTP configuration in a DMZ. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Connecting and Configuring the Appliance. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
Installation quick reference table. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
Ports and Connections. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
3000, 3100 panel layout. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
3200 panel layout. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
3300 and 3400 panel layout. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20
Panel components: 3000, 3100, 3200, 3300, 3400. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20
Physically installing the appliance. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
Connect to the network. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
Port numbers. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
Using Copper LAN connections. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
Using Fiber LAN connections. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
Monitor and keyboard. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
Supplying power to the appliance. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
3McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 4

Contents
Installing the software. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
Using the Configuration Console. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
Configurable settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
Configuring the appliance using the Setup Wizard. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
Logging on to the Setup Wizard. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
Welcome page. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
Performing a standard installation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
Performing a custom setup. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
Using the Appliance. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
Updates and HotFixes. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
After installation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Testing the Configuration. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Introducing the user interface. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Testing the appliance. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
Exploring the Appliance. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Generating reports. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Further report information. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Using policies to manage message scanning. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
Creating an anti-virus scanning policy. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
Creating an anti-spam scanning policy. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
Creating an email compliance policy. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
Creating a content filtering policy. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
Troubleshooting. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
General problems. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
The appliance is not receiving power. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
The appliance is not receiving traffic from the network. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
FAQ. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
General issues. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Interface problems. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Mail issues. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Delivery. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Email attachments. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
POP3. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
Physical configuration. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 47
System configuration. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 47
System maintenance. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 47
Anti-virus automatic updating. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 48
McAfee Email and Web Security Appliance 5.1 Installation Guide4
Page 5

Contents
Anti-spam. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 48
Getting more help — the links bar. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 50
5McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 6

Preface
This guide provides the necessary information for installing the McAfee®Email and Web Security
Appliance 5.1. It provides steps and verification of the installation process.
This guide demonstrates how to configure Email and Web Security software and when completed
the user will have a fully functional appliance.
Contents
Using this guide
Audience
Graphical conventions
Documentation
Using this guide
This guide helps you to:
• Understand the appliance features and functions.
• Plan and perform the appliance installation and deployment.
• Begin to use the appliance.
• Test the appliance in a laboratory environment (optional).
You can find additional information about McAfee Email and Web Security Appliance scanning
features in the online help. This includes information about:
• Basic concepts
• Policies
• Protocols (SMTP, POP3, FTP, HTTP and ICAP)
• Maintenance
• Monitoring
Audience
The information in this guide is intended primarily for network administrators who are responsible
for their company’s anti-virus and security program.
McAfee Email and Web Security Appliance 5.1 Installation Guide6
Page 7

Preface
Graphical conventions
Graphical conventions
Figures in this guide use the following symbols.
InternetAppliance
Documentation
This Installation Guide is included with your appliance. Additional information is available in the
online help, and other documentation available from the documentation CD.
Mail server
VLAN)
Other server (such as DNS
server)
RouterUser or client computer
FirewallSwitch
NetworkNetwork zone (DMZ or
Perceived data pathActual data path
7McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 8
Pre-installation
To ensure the safe operation of the Email and Web Security Appliance, consider the following
before you begin the installation.
• Familiarize yourself with its operational modes and capabilities. It is important that you
choose a valid configuration.
• Decide how to integrate the appliance into your network and determine what information
you need before you start. For example, the name and IP address for the appliance.
• Unpack the appliance as close to its intended location as possible.
• Remove the appliance from any protective packaging and place it on a flat surface.
• Observe all provided safety warnings.
CAUTION: Review and be familiar with all safety information provided.
Contents
What’s in the box
Plan the installation
Inappropriate use
Operating conditions
Positioning the appliance
What’s in the box
To check that all appliance components were delivered, refer to the packing list supplied with
your appliance.
Generally, you should have:
• An appliance
• Power cords
• Network cables
• Secure Messaging Gateway v5.0 installation and recovery CD
• Linux source code CD
• Quarantine Manager v5.0 CD
• Documentation CD
If an item is missing or damaged, contact your supplier.
McAfee Email and Web Security Appliance 5.1 Installation Guide8
Page 9
Pre-installation
Plan the installation
Plan the installation
Before unpacking your appliance, it is important to plan the installation and deployment.
Consider the following:
• How you need to prepare your site.
• Environmental requirements.
• Power requirements and considerations.
• Hardware specifications and requirements.
• Configuration scenarios.
• Preparing for installation.
Inappropriate use
The appliance is:
• Not a firewall.
You must use it within your organization behind a correctly configured firewall.
• Not a server for storing extra software and files.
Do not install any software on the appliance or add any extra files to it unless instructed by
the product documentation or your support representative. The appliance cannot handle all
types of traffic. If you use explicit proxy mode, only protocols that are to be scanned should
be sent to the appliance.
Operating conditions
Relative humidity
Maximum shock
Positioning the appliance
10 to 35°C (50 to 95°F).Temperature
20% to 80% (non-condensing) with a maximum humidity
gradient of 10% per hour.
0.25 G at 3–200 Hz for 15 minutes.Maximum vibration
One shock pulse in the positive z axis (one pulse on each
side of the unit) of 31 G for up to 2.6 ms.
-16 to 3,048 m (-50 to 10,000 ft.).Altitude
Install the appliance so that you can control physical access to the unit and access the ports
and connections.
A rack-mounting kit is supplied with the appliance, allowing you to install the appliance in a
19-inch rack — see Mounting the appliance in a rack.
9McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 10

Pre-installation
Considerations about Network Modes
Considerations about Network Modes
Before you install and configure your appliance, you must decide which network mode to use.
The mode you choose determines how you physically connect your appliance to your network.
You can choose from the following network modes.
• Transparent bridge mode
the appliance acts as an Ethernet bridge.
• Transparent router mode
the appliance acts as a router.
• Explicit proxy mode
the appliance acts as a proxy server and a mail relay.
If you are still unsure about the mode to use after reading this and the following sections,
consult your network expert.
Architectural considerations about network modes
The main considerations regarding the network modes are:
• Whether communicating devices are aware of the existence of the appliance. That is, if the
appliance is operating in one of the transparent modes.
• How the appliance physically connects to your network.
• The configuration needed to incorporate the appliance into your network.
• Where the configuration takes place in the network.
Considerations before changing network modes
In explicit proxy and transparent router modes, you can set up the appliance to sit on more
than one network by setting up multiple IP addresses for the LAN1 and LAN2 ports.
If you change to transparent bridge mode from explicit proxy or transparent router mode, only
the enabled IP addresses for each port are carried over.
TIP: After you select an operational mode, McAfee recommends not changing it unless you
move the appliance or restructure your network.
Contents
Transparent bridge mode
Transparent router mode
Explicit proxy mode
McAfee Email and Web Security Appliance 5.1 Installation Guide10
Page 11
Pre-installation
Considerations about Network Modes
Transparent bridge mode
In transparent bridge mode, the communicating devices are unaware of the appliance — the
appliance’s operation is transparent to the devices.
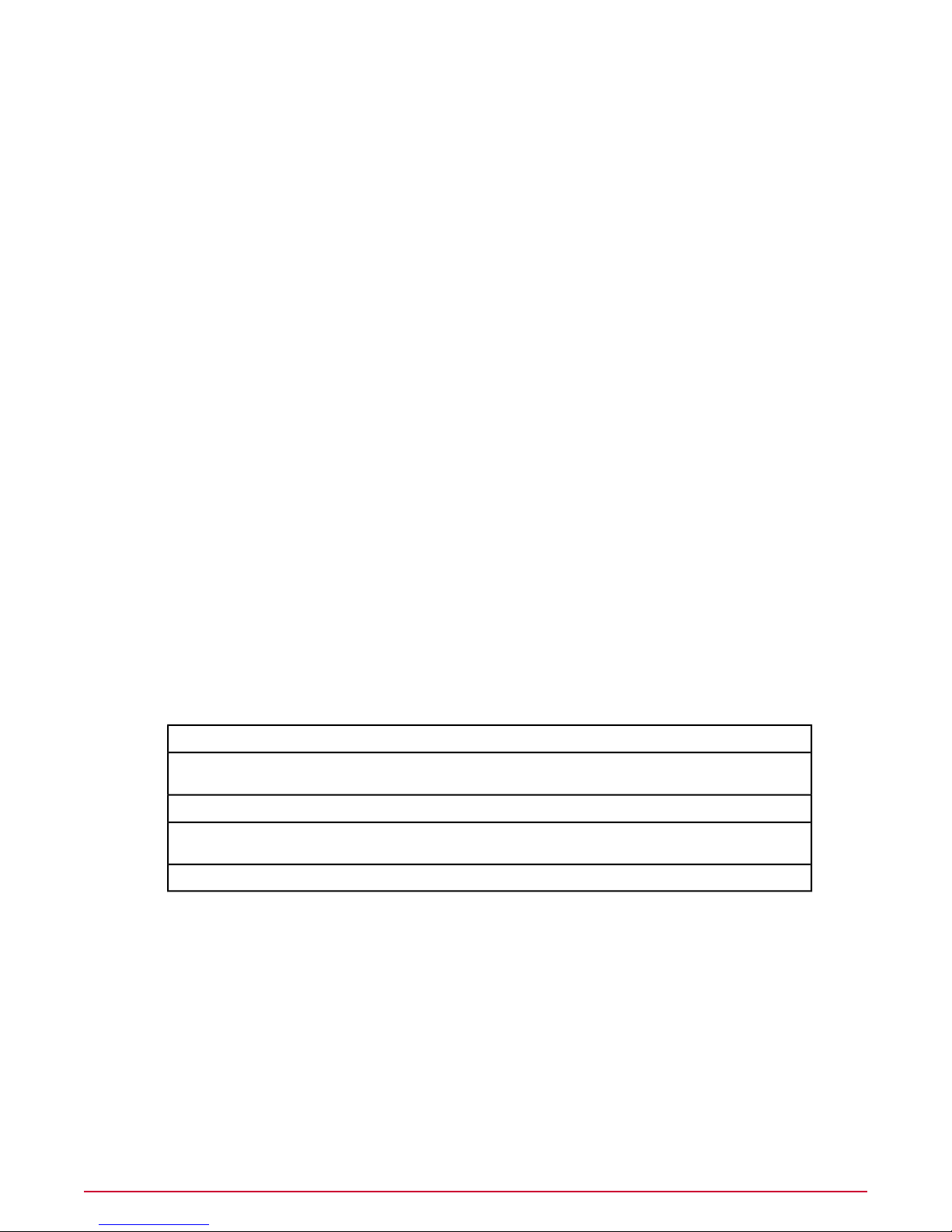
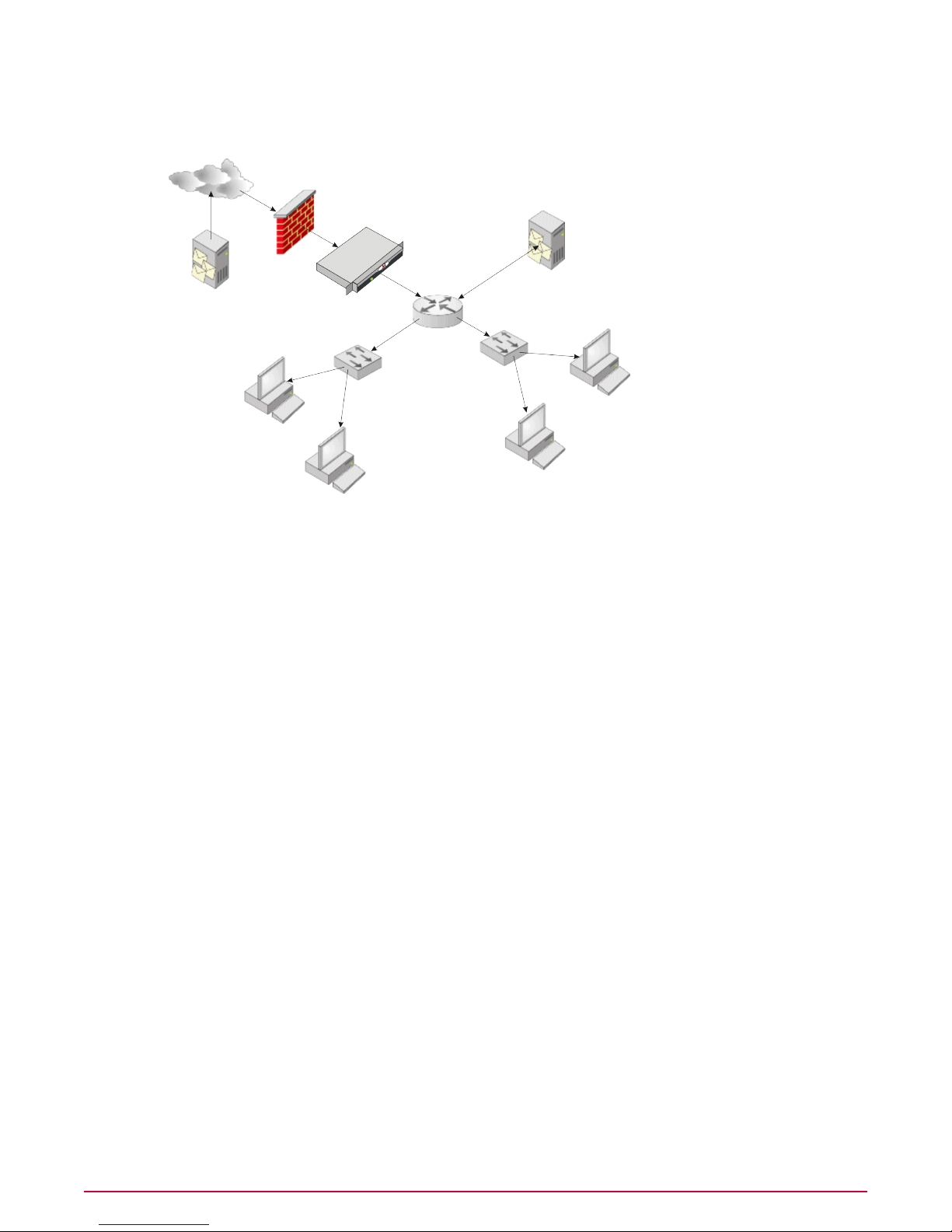
Figure 1: Transparent communication
In Figure 1: Transparent communication, the external mail server (A) sends email messages
to the internal mail server (C). The external mail server is unaware that the email message is
intercepted and scanned by the appliance (B).
The external mail server seems to communicate directly with the internal mail server — the
path is shown as a dotted line. In reality, traffic might pass through several network devices
and be intercepted and scanned by the appliance before reaching the internal mail server.
What the appliance does
In transparent bridge mode, the appliance connects to your network using the LAN1 and LAN2
ports. The appliance scans the traffic it receives, and acts as a bridge connecting two separate
physical networks, but treats them as a single logical network.
Configuration
Transparent bridge mode requires less configuration than transparent router and explicit proxy
modes. You do not need to reconfigure all your clients, default gateway, MX records, Firewall
NAT or mail servers to send traffic to the appliance. Because the appliance is not a router in
this mode, you do not need to update a routing table.
Where to place the appliance
For security reasons, you must use the appliance inside your organization, behind a firewall.
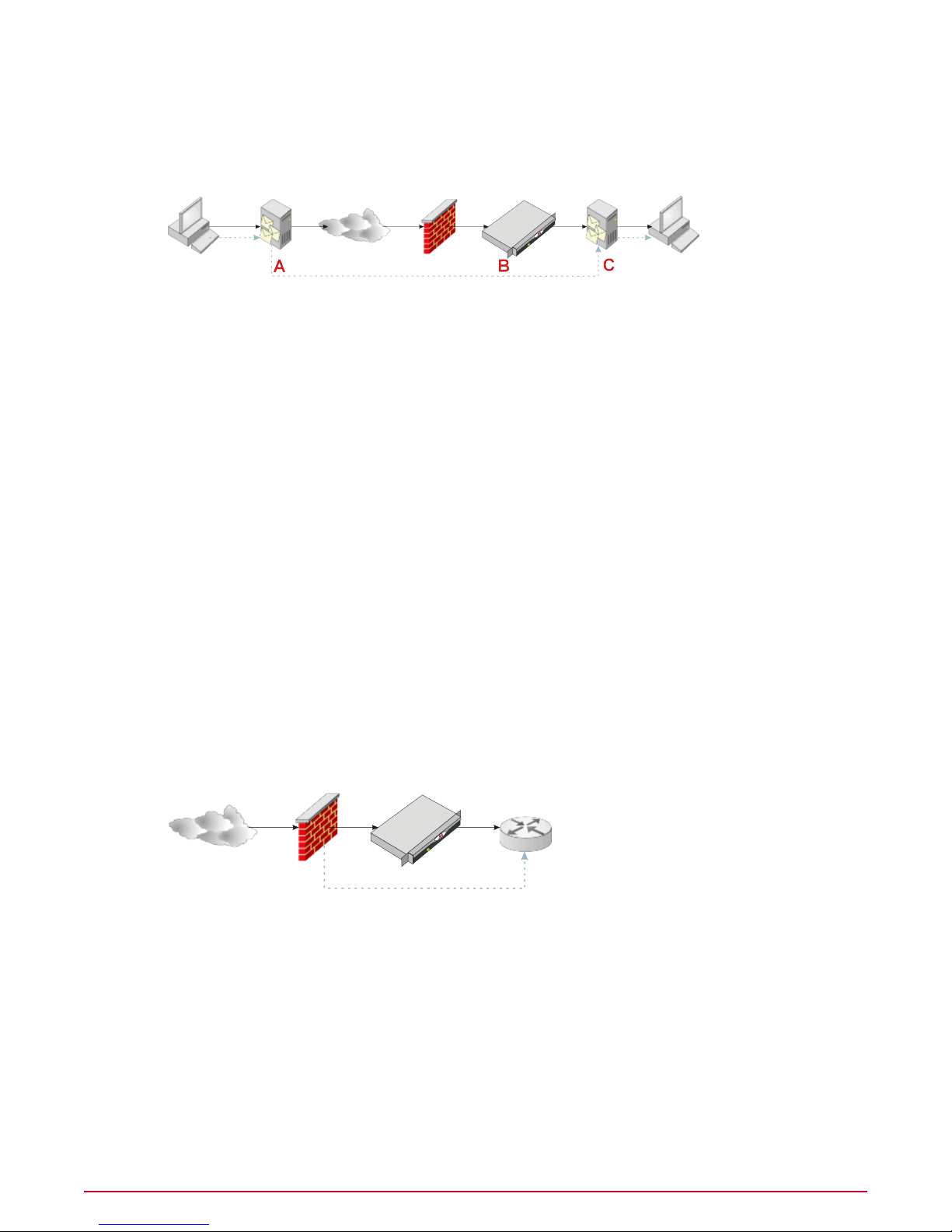
Figure 2: Single logical network
TIP: In transparent bridge mode, position the appliance between the firewall and your router,
as shown in Figure 2: Single logical network.
In this mode, you physically connect two network segments to the appliance, and the appliance
treats them as one logical network. Because the devices — firewall, appliance, and router —
are on the same logical network, they must all have compatible IP addresses on the same
subnet.
Devices on one side of the bridge (such as a router) that communicate with devices on the
other side of the bridge (such as a firewall) are unaware of the bridge. They are unaware that
11McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 12
Pre-installation
Considerations about Network Modes
traffic is intercepted and scanned, therefore the appliance is said to operate as a transparent
bridge.
Figure 3: Transparent bridge mode
Transparent router mode
In transparent router mode, the appliance scans email traffic between two networks. The
appliance has one IP address for outgoing scanned traffic, and must have one IP address for
incoming traffic.
The communicating network devices are unaware of the intervention of the appliance — the
appliance’s operation is
What the appliance does
In transparent router mode, the appliance connects to your networks using the LAN1 and LAN2
ports. The appliance scans the traffic it receives on one network, and forwards it to the next
network device on a different network. The appliance acts as a router, routing the traffic between
networks, based on the information held in its routing tables.
Configuration
Using transparent router mode, you do not need to explicitly reconfigure your network devices
to send traffic to the appliance. You need only configure the routing table for the appliance,
and modify some routing information for the network devices on either side of it (the devices
connected to its LAN1 and LAN2 ports). For example, you might need to make the appliance
your default gateway.
In transparent router mode, the appliance must join two networks. The appliance must be
positioned inside your organization, behind a firewall.
transparent
to the devices.
NOTE: Transparent router mode does not support Multicast IP traffic or non-IP protocols, such
as NETBEUI and IPX.
McAfee Email and Web Security Appliance 5.1 Installation Guide12
Page 13
Pre-installation
Considerations about Network Modes
Where to place the appliance
Use the appliance in transparent router mode to replace an existing router on your network.
TIP: If you use transparent router mode and you do not replace an existing router, you must
reconfigure part of your network to route traffic correctly through the appliance.
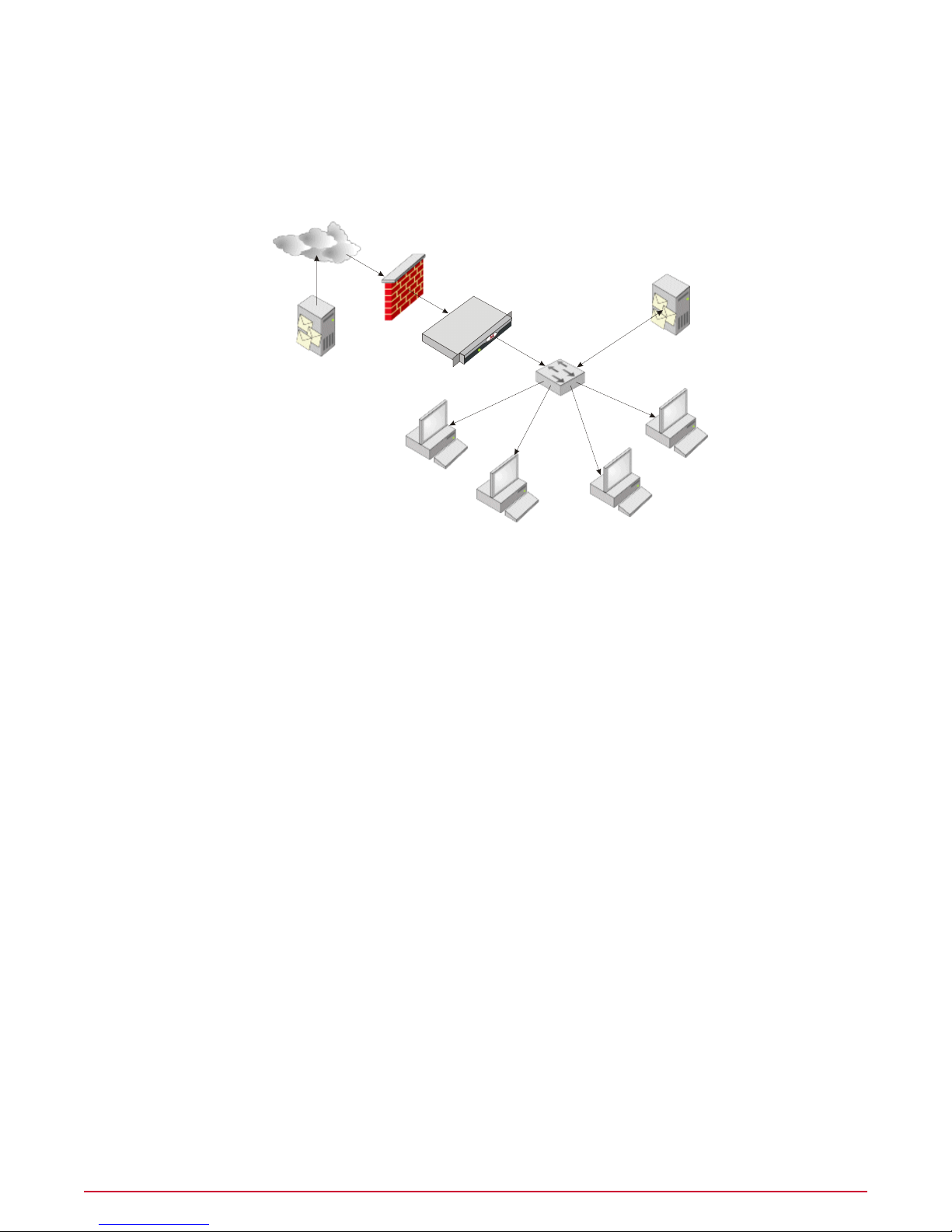
Figure 4: Transparent router mode configuration
You need to:
• Configure your client devices to point to the default gateway.
• Configure the appliance to use the Internet gateway as its default gateway.
• Ensure your client devices can deliver email messages to the mail servers within your
organization.
Explicit proxy mode
In explicit proxy mode, some network devices must be set up explicitly to send traffic to the
appliance. The appliance then works as a proxy or relay, processing traffic on behalf of the
devices.
Explicit proxy mode is best suited to networks where client devices connect to the appliance
through a single upstream and downstream device.
TIP: This might not be the best option if several network devices must be reconfigured to send
traffic to the appliance.
Network and device configuration
If the appliance is set to explicit proxy mode, you must explicitly configure your internal mail
server to relay email traffic to the appliance. The appliance scans the email traffic before
forwarding it, on behalf of the sender, to the external mail server. The external mail server then
forwards the email message to the recipient.
13McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 14

Pre-installation
Considerations about Network Modes
In a similar way, the network must be configured so that incoming email messages from the
Internet are delivered to the appliance, not the internal mail server.
Figure 5: Relaying email traffic
The appliance scans the traffic before forwarding it, on behalf of the sender, to the internal
mail server for delivery, as shown in Figure 5: Relaying email traffic.
For example, an external mail server can communicate directly with the appliance, although
traffic might pass through several network devices before reaching the appliance. The perceived
path is from the external mail server to the appliance.
Protocols
To scan a supported protocol, you must configure your other network devices or client computers
to route that protocol through the appliance, so that no traffic bypasses the appliance.
Firewall rules
Explicit proxy mode invalidates any firewall rules set up for client access to the Internet. The
firewall sees only the IP address information for the appliance, not the IP addresses of the
clients, so the firewall cannot apply its Internet access rules to the clients.
Where to place the appliance
Configure the network devices so that traffic needing to be scanned is sent to the appliance.
This is more important than the location of the appliance.
The router must allow all users to connect to the appliance.
Figure 6: Explicit proxy configuration
The appliance must be positioned inside your organization, behind a firewall, as shown in Figure
6: Explicit proxy configuration.
Typically, the firewall is configured to block traffic that does not come directly from the appliance.
If you are unsure about your network’s topology and how to integrate the appliance, consult
your network expert.
McAfee Email and Web Security Appliance 5.1 Installation Guide14
Page 15

Pre-installation
Deployment Strategies for Using the Appliance in a DMZ
Use this configuration if:
• The appliance is operating in explicit proxy mode.
• You are using email (SMTP).
For this configuration, you must:
• Configure the external Domain Name System (DNS) servers or Network Address Translation
(NAT) on the firewall so that the external mail server delivers mail to the appliance, not to
the internal mail server.
• Configure the internal mail servers to send email messages to the appliance. That is, the
internal mail servers must use the appliance as a smart host. Ensure that your client devices
can deliver email messages to the mail servers within your organization.
• Ensure that your firewall rules are updated. The firewall must accept traffic from the
appliance, but must not accept traffic that comes directly from the client devices. Set up
rules to prevent unwanted traffic entering your organization.
Deployment Strategies for Using the Appliance in
a DMZ
A demilitarized zone (DMZ) is a network separated by a firewall from all other networks, including
the Internet and other internal networks. The typical goal behind the implementation of a DMZ
is to lock down access to servers that provide services to the Internet, such as email.
Hackers often gain access to networks by identifying the TCP/UDP ports on which applications
are listening for requests, then exploiting known vulnerabilities in applications. Firewalls
dramatically reduce the risk of such exploits by controlling access to specific ports on specific
servers.
The appliance can be added easily to a DMZ configuration. The way you use the appliance in
a DMZ depends on the protocols you intend to scan.
Contents
SMTP configuration in a DMZ
SMTP configuration in a DMZ
The DMZ is a good location for encrypting mail. By the time the mail traffic reaches the firewall
for the second time (on its way from the DMZ to the internal network), it has been encrypted.
Appliances which scan SMTP traffic in a DMZ are usually configured in explicit proxy mode.
Configuration changes need only be made to the MX records for the mail servers.
NOTE: You can use transparent bridge mode when scanning SMTP within a DMZ. However, if
you do not control the flow of traffic correctly, the appliance scans every message twice, once
in each direction. For this reason, explicit proxy mode is usually used for SMTP scanning.
15McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 16

Pre-installation
Deployment Strategies for Using the Appliance in a DMZ
Mail relay
Figure 7: Appliance in explicit proxy configuration in a DMZ
If you have a mail relay already set up in your DMZ, you can replace the relay with the appliance.
To use your existing firewall policies, give the appliance the same IP address as the mail relay.
Mail gateway
SMTP does not provide methods to encrypt mail messages — you can use Transport Layer
Security (TLS) to encrypt the link, but not the mail messages. As a result, some companies do
not allow such traffic on their internal network. To overcome this, they often use a proprietary
mail gateway, such as Lotus Notes®or Microsoft®Exchange, to encrypt the mail traffic before
it reaches the internal network.
To implement a DMZ configuration using a proprietary mail gateway, add the appliance to the
DMZ on the SMTP side of the gateway.
Figure 8: Protecting a mail gateway in DMZ
In this situation, configure:
McAfee Email and Web Security Appliance 5.1 Installation Guide16
Page 17

Pre-installation
Deployment Strategies for Using the Appliance in a DMZ
• The public MX records to instruct external mail servers to send all inbound mail to the
appliance (instead of the gateway).
• The appliance to forward all inbound mail to the mail gateway, and deliver all outbound mail
using DNS or an external relay.
• The mail gateway to forward all inbound mail to the internal mail servers and all other
(outbound) mail to the appliance.
• The firewall to allow inbound mail that is destined for the appliance only.
NOTE: Firewalls configured to use Network Address Translation (NAT), and that redirect inbound
mail to internal mail servers, do not need their public MX records reconfigured. This is because
they are directing traffic to the firewall rather than the mail gateway itself. In this case, the
firewall must instead be reconfigured to direct inbound mail requests to the appliance.
Firewall rules specific to Lotus Notes
By default, Lotus Notes servers communicate over TCP port 1352. The firewall rules typically
used to secure Notes servers in a DMZ allow the following through the firewall:
• Inbound SMTP requests (TCP port 25) originating from the Internet and destined for the
appliance.
• TCP port 1352 requests originating from the Notes gateway and destined for an internal
Notes server.
• TCP port 1352 requests originating from an internal Notes server and destined for the Notes
gateway.
• SMTP requests originating from the appliance and destined for the Internet.
All other SMTP and TCP port 1352 requests are denied.
Firewall rules specific to Microsoft Exchange
A Microsoft Exchange-based mail system requires a significant workaround.
When Exchange servers communicate with each other, they send their initial packets using the
RPC protocol (TCP port 135). However, once the initial communication is established, two ports
are chosen dynamically and used to send all subsequent packets for the remainder of the
communication. You cannot configure a firewall to recognize these dynamically-chosen ports.
Therefore, the firewall does not pass the packets.
The workaround is to modify the registry on each of the Exchange servers communicating
across the firewall to always use the same two “dynamic” ports, then open TCP 135 and these
two ports on the firewall.
We mention this workaround to provide a comprehensive explanation, but we do not recommend
it. The RPC protocol is widespread on Microsoft networks — opening TCP 135 inbound is a red
flag to most security professionals.
If you intend to use this workaround, details can be found in the following Knowledge Base
articles on the Microsoft website:
• Q155831
• Q176466
17McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 18

Connecting and Configuring the Appliance
We recommend that you consider installing the appliance in the following order:
1 Unpack the appliance and confirm no parts are missing (check against parts lists in the
box)
2 Rack-mount the appliance.
3 Connect the peripherals and power (monitor, keyboard).
4 Connect the appliance to the network, noting deployment scenarios and intended network
mode.
5 Install the software onto the appliance.
6 Use the Configuration Console to carry out the basic configuration (server name, IP
addresses, gateway, and so on).
7 Connect to the administration interface.
8 Run the Setup Wizard.
9 Route test network traffic through the appliance.
10 Test that the network traffic is being scanned.
11 Configure policies and reporting.
12 Route production traffic through the appliance.
CAUTION: Connecting the appliance to your network can disrupt Internet access or other
network services. Ensure that you have arranged network down-time for this, and that you
schedule this during periods of low network usage.
Contents
Installation quick reference table
Physically installing the appliance
Connect to the network
Supplying power to the appliance
Installation quick reference table
To install the appliance, go through the steps in this table:
1.
parts lists in the box.
McAfee Email and Web Security Appliance 5.1 Installation Guide18
is described here ...This step ...
What’s in the boxUnpack the pallet and check the contents against the
Mounting the appliance in a rackRack-mount the appliance.2.
Monitor and keyboardConnect the peripherals and power.3.
Page 19

Connecting and Configuring the Appliance
Ports and Connections
Ports and Connections
is described here ...This step ...
Connect to the networkConnect the appliance to the network.4.
Installing the softwareInstall the software.5.
Using the Configuration ConsolePerform basic configuration.6.
Configuring the appliance using the Setup WizardConnect to the administration interface.7.
Configuring the appliance using the Setup WizardRun the Setup Wizard.8.
Testing the applianceRoute the test network traffic through the appliance.12.
Testing the applianceTest that the network traffic is being scanned.13.
Using policies to manage message scanningConfigure policies and reporting.14.
Configuring the appliance using the Setup WizardConfigure production traffic through the system.15.
This chapter shows the panel layouts for each model of appliance.
3000, 3100 panel layout
3200 panel layout
3300 and 3400 panel layout
Panel components: 3000, 3100, 3200, 3300, 3400
3000, 3100 panel layout
3200 panel layout
19McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 20

Connecting and Configuring the Appliance
Ports and Connections
3300 and 3400 panel layout
Panel components: 3000, 3100, 3200, 3300, 3400
CD-ROM drive
Use the CD-ROM drive only when restoring, upgrading, or diagnosing system faults on the
appliance.
System status and hard disk drive (HDD) LEDs
System status LED
• Lights blue — during normal use.
• Flashes blue — when the System
Identification ( ) button is pressed.
• Flashes amber when there is a system
fault.
HDD LED
• Flashes green when the hard disk drive is
in use.
Power and LED
Turns the appliance on and off.
• Lights green — when the appliance is operational.
• Flashes green — whenthe appliance is in standby mode. It is receiving power through the
power socket, but the power button is off. The network ports remain active but no protocols
or data intended for the appliance can pass through the appliance.
Power socket
Use the correct power cord for your location.
NOTE: 3300 and 3400 appliances only — We recommend you connect both power supplies.
McAfee Email and Web Security Appliance 5.1 Installation Guide20
Page 21
Connecting and Configuring the Appliance
Ports and Connections
System identification button
The system identification buttons on the front and back panels help you locate the appliance
within a rack. Push the button to flash the System Status LEDs () on the front panel and System
indication button LED on the back panel. Push the button again to stop the LEDs flashing.
Monitor port
Connect a monitor to this port when you are:
• Initially configuring the appliance.
• Restoring and upgrading the appliance’s software.
• Diagnosing system faults.
Keyboard port
For connecting a keyboard.
3200, 3300 and 3400 appliances only — these appliances now use USB Keyboards.
Mouse port
Not used by the appliance.
Copper LAN1 port (NIC 1) and LAN2 port (NIC 2)
See the labeling on the back of the unit to identify the LAN ports.
Both ports are RJ-45 10/100/1000 Mbps auto-negotiating (auto-sensing) Ethernet network
ports. They must only be used with equipment designed for 10 Mbps, 100 Mbps or 1000 Mbps
(1Gb) Ethernet network use.
NOTE: 3100 only — the 3100 appliances can only be used with equipment designed or 10 Mbps
or 100 Mbps Ethernet.
Each LAN port has built-in LEDs:
• Lights green — when the port has a good link to the attached Ethernet.
• Flashes amber — when the port detects activity on the attached Ethernet.
3300 and 3400 appliances only
These appliances are now supplied with 4 NIC connectors. Currently, only the LAN1 and LAN2
ports are used.
Fiber LAN1 port and LAN2 port (3300 and 3400 appliances only)
The 3300 and 3400 appliances also have two fiber LC connectors for 1000 BASE-SX Ethernet
network connections. You can use copper or the fiber LAN ports.
The fiber ports are disabled by default.
To enable the fiber ports, use one of the copper LAN ports to make a management connection;
a local management connection using copper LAN2, or a remote Management Connection using
copper LAN1. Use a web browser to access the interface and enable the fiber ports using the
Setup Wizard. See the Product Guide for more information.
NOTE: The fiber ports have covers to protect the optics when not in use. Remove covers before
use and replace covers if disconnecting the fiber connections.
21McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 22

Connecting and Configuring the Appliance
Ports and Connections
The following information applies to the copper and fiber ports.
LAN1 port
The LAN1 port is used to connect the appliance to your network. It receives and transmits the
following traffic:
• Inbound and outbound protocol traffic.
• Management and log data, including the communication from the remote web browser that
you use to access the appliance’s user interface. If you use ePolicy Orchestrator software
with the appliance, its communication is also transmitted through this port.
The LAN1 port has a default IP address of 10.1.1.108 (subnet mask 255.255.255.0) to allow
you to access the appliance initially across the network.
LAN2 port
The LAN2 port has a default IP address of 10.1.2.108 (subnet mask 255.255.255.0).
The operation of the LAN2 port depends on how you are using the appliance:
• Explicit Proxy mode — The LAN2 port is only used for direct local management connections.
It cannot receive and transmit inbound and outbound protocol traffic. Use this port if you
cannot achieve a remote management connection through the LAN1 port, because:
• The LAN1 port IP address is in a different subnet to your remote computer.
• You have forgotten the LAN1 port IP address that you set, and have disabled the default
IP address of 10.1.1.108 for that port.
• You connected fiber cables to the fiber LAN1 and LAN2 ports, and now want to enable
these ports.
• Transparent Router and Transparent Bridge modes — The LAN2 port is used (with
LAN1) to connect the appliance to your network. It receives and transmits the same type
of traffic as the LAN1 port.
Remote Access Card — 3300 and 3400 appliances only
Provides remote access and limited management of the 3300 and 3400 appliances. It allows
you to reboot the appliance using a CD in a remote administration computer. You can connect
an Ethernet Cat 5e cable to the RJ-45 port.
Hard disk drives
3000, 3100 appliances only — The 3000 and 3100 appliances have a single hard disk drive.
3200, 3300 and 3400 appliances only — There are two “hot-pluggable” SCSI hard disk
drives, managed in a RAID 1 (mirror) configuration.
The drives mirror the appliance’s operating system and data, ensuring seamless operation in
the event of a problem with one of the drives. You can then remove the failed drive and insert
a new drive without needing to turn off the appliance, see Troubleshooting.
The LEDs show the following status information:
• Operational — the top LED lights green when the drive is in use.
CAUTION: Do not remove a drive when it is operational because this can cause data loss or
hardware damage.
McAfee Email and Web Security Appliance 5.1 Installation Guide22
Page 23

Connecting and Configuring the Appliance
Physically installing the appliance
• Predicted failure — The bottom LED flashes green, amber, and off if the drive is about to
fail.
• Failure — The bottom LED flashes amber when the drive has failed.
• No power — Both LEDs are off when the drive is not receiving power from the appliance.
HTTP and ICAP Accelerator Card — 3400 appliances only
The accelerator card enhances the anti-virus scanning of HTTP and ICAP traffic. The LEDs on
the card show that the card is active.
USB Connectors
Connect Keyboard (not 3000 or 3100) and Out of Band Management adapter (if required).
Physically installing the appliance
Use this task to physically install the appliance.
Task
1 Remove the appliance from the protective packaging and place it on a flat surface.
2 If you are going to install the appliance in a 19-inch rack, perform the steps in Mounting
the appliance in a rack.
3 Connect a monitor and keyboard to the appliance.
4 Connect power leads to the monitor and the appliance, but do not connect to the power
supplies yet.
5 Connect the appliance to the network, taking into consideratation your chosen operating
mode.
Connect to the network
This section describes how to connect the appliance to your network.
The ports and cables that you use to connect the appliance to your network depend on how
you are going to use the appliance. For information about network modes, see Considerations
about Network Modes.
Port numbers
When you connect the Appliance to your network, use the following port numbers:
• For HTTPS, use Port 443.
• For HTTP, use Port 80.
• For SMTP, use Port 25.
• For POP3, use port 110.
• For FTP, use Port 21.
23McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 24

Connecting and Configuring the Appliance
Connect to the network
Using Copper LAN connections
Using the LAN1 and LAN2 switch connections and the supplied network cables (or equivalent
Cat 5e or Cat 6 Ethernet cables), connect the appliance to your network according to the network
mode you have chosen.
Transparent bridge mode
Use the copper LAN cables (supplied) to connect the appliance’s LAN1 and LAN2 switches to
your network so that the appliance is inserted into the data stream.
Transparent router mode
The appliance functions as a router. The LAN segments connected to its two network interfaces
must therefore be on different IP subnets. It must replace an existing router, or a new subnet
must be created on one side of the appliance. Do this by changing the IP address or the netmask
used by the computers on that side.
Explicit proxy mode
Use a copper LAN cable (supplied) to connect the LAN1 or LAN2 switch to your network. The
cable is a straight-through (uncrossed) cable, and connects the appliance to a normal uncrossed
RJ-45 network switch.
In explicit proxy mode, the unused switch connection can be used as a dedicated management
port. To manage the appliance locally, use a crossover Cat 5e Ethernet cable to connect the
appliance to your local computer’s network card.
Using Fiber LAN connections
Use the fiber cables to connect the LAN1 and LAN2 connectors to your network. The connectors
use depend on how you are going to use the appliance.
Transparent bridge mode
Use the fiber cables to connect the LAN1 and LAN2 switches to your network.
Transparent router mode
Use the fiber cables to connect the LAN1 and LAN2 switches to different IP subnets.
Explicit proxy mode
Use a fiber cable to connect the appliance’s LAN1 switches to your network.
In explicit proxy mode, the unused connector can be used as a dedicated management port.
If your management computer has a compatible Network Interface Card (NIC), connect it to
the remaining connector for local management.
Monitor and keyboard
Connect a monitor and keyboard to the appliance.
McAfee Email and Web Security Appliance 5.1 Installation Guide24
Page 25

Connecting and Configuring the Appliance
Supplying power to the appliance
Supplying power to the appliance
Use this task to supply power to the appliance and switch it on.
Task
1 Connect the monitor and appliance power cables to power outlets.
NOTE: If the power cord is not suitable for the country of use, contact your supplier.
2 Turn on the appliance by pushing the power button. After booting up, the Configuration
Console appears on the monitor. See Using the Configuration Console.
Installing the software
Use this task to install the Email and Web Security software on the appliance.
Tasks
1 From a computer with internet access, download the latest version of the Email and Web
Security software from the McAfee download site. (You will need your Grant Number to do
this.)
2 Create a CD from this image.
3 Attach a monitor and keyboard to the appliance.
4 With the appliance switched on, insert the CD into the CD-ROM drive.
5 Re-boot the appliance. The software is installed on the appliance.
Using the Configuration Console
The Configuration Console enables you to configure the basic network settings for the appliance,
without having to configure an additional computer to match the settings of your appliance.
The console launches automatically at the end of the startup sequence after either:
• an unconfigured appliance starts,
• or after an applianceis reset to its factory defaults.
When launched, the console prompts you to enter information for each configurable setting.
Configurable settings
Configurable settings
You can use the console to configure:
• Host name and domain that the appliance is to use
• Operational mode for the appliance
• LAN1 settings
• LAN2 Settings
• NIC settings
• Gateway information
25McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 26

Connecting and Configuring the Appliance
Configuring the appliance using the Setup Wizard
• DNS server settings
When you have entered all the information, you must apply the configuration to the appliance.
Depending on the settings entered, the appliance might reboot. After the configuration
information is applied, the console will not appear on reboots, unless you restore the factory
defaults or install new versions of the software.
Configuring the appliance using the Setup Wizard
The Setup Wizard appears automatically when you first connect to the appliance IP address,
and provides a quick way to configure the system.
You can choose to configure the appliance using:
• the Standard Setup option
• the Custom Setup option
In the standard pages, McAfee configure some of the most-commonly used settings for you.
The custom pages enable you to sellect these settings yourself.
Some of the settings in the Setup Wizard reflect choices you made when you used the
Configuration Console.
Logging on to the Setup Wizard
Welcome page
Performing a standard installation
Performing a custom setup
Logging on to the Setup Wizard
Use this task to log on to the Setup Wizard.
Task
1 From a browser on the same network as the appliance, type: https://<IP address>
2 At the logon window, type the user name scmadmin and password scmchangeme. The
Setup Wizard appears.
The number of the current Setup Wizard page is highlighted. The Setup Wizard incudes a help
panel to the left of each page.
Welcome page
Use this page to select the type of installation you want to perform.
• Select Standard Setup to configure the appliance for transparent bridge mode only.
• Select Custom Setup (default) to select the network mode you want to use.
Performing a standard installation
For the Standard Setup, the wizard includes these pages:
• Traffic
• Basic Settings
McAfee Email and Web Security Appliance 5.1 Installation Guide26
Page 27

Traffic
Connecting and Configuring the Appliance
Configuring the appliance using the Setup Wizard
• Summary
CAUTION: Choosing Standard Setup forces the appliance to run in Transparent bridge mode.
Use this page to specify the type of traffic that the appliance scans.
Web traffic includes HTTP traffic only. After installation:
• The appliance protects your network against viruses, and uses McAfee SiteAdvisor when
visiting web sites.
• If you want to scan more types of traffic, you can enable each protocol from its page. From
the menu, select Web | Web Configuration | HTTP, Web | Web Configuration |
ICAP or Web | Web Configuration | FTP.
Email traffic includes SMTP traffic only. After installation:
• Theappliance protects your network against viruses, spam and phish, and uses McAfee
Reputation Service to protect your network from unwanted email.
• If you want to scan more types of traffic, you can enable each protocol from its page. From
the menu, select Email | Email Configuration | Protocol Configuration | Connection
Settings (POP3) or Email | Email Configuration | Protocol Configuration |
Connection Settings (SMTP).
McAfee Anti-Spyware protects your network from many types of potentially unwanted software
such as spyware, adware, remote administration tools, dialers and password crackers. This
feature is not enabled by default.
NOTE: McAfee Anti-Spyware is designed to detect and, with your permission, remove potentially
unwanted programs (PUPs). Some purchased or intentionally downloaded programs act as
hosts for PUPs. Removing these PUPs may prevent their hosts from working. Be sure to review
the license agreements for these host programs for further details. McAfee, Inc. neither
encourages nor condones breaking any license agreements that you may have entered into.
Please read the details of all license agreements and privacy policies carefully before downloading
or installing any software.
Basic Settings
Use this page to specify basic settings for the appliance, in transparent bridge mode.
Firewall or Gateway server
McAfee®Email and Web Security Appliance 5.1
27McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 28

Connecting and Configuring the Appliance
Configuring the appliance using the Setup Wizard
Active Directory or Domain Name System server
Option definitions
DefinitionOption
Specifies a name, such as appliance1.Device name
Specifies a name, such as domain1.com.Domain name
IP address
Gateway IP
DNS Server IP
Specifies an address, such as 198.168.200.10.
The fully qualified domain name (Device name. Domain name) must resolve to this IP
address when the DNS server (specified here) is called. We recommend that this IP address
resolves to the FQDN in a reverse lookup.
Specifies a subnet address, such as 255.255.255.0.Subnet
Specifies an address, such as 198.168.10.1. This is likely to be a router or a firewall. You can
test later that the appliance can communicate with this device.
Specifies the address of a Domain Name Server that the appliance will use to convert website
addresses to IP addresses. This can be an Active Directory or a Domain Name Service server.
You can test later that the appliance can communicate with this server.
Specifies the mode - Transparent bridge, transparent router or explicit proxy.Mode
User ID
Password
Time zone
Set time now
Summary
Use this page to review a summary of the settings that you have made through the Setup
Wizard. To change any value, click its blue link to display the page where you originally typed
the value.
After you click Finish, the setup wizard has completed.
Use the IP address shown here to access the interface. For example https://192.168.200.10.
Note that the address begins with https, not http.
When you first log onto the interface, type the user name, scmadmin and the password that
you gave to this setup wizard.
The scmadmin user is the super administrator. You cannot change or disable this account
and the account cannot be deleted. However, you can add more login accounts after
installation.
Specifies the new password. Change the password as soon as possible to keep yourappliance
secure.
You must type the new password twice to confirm it. The original default password is
scmchangeme.
Offers a choice of time zones. The zones are organized from West to East to cover mid-Pacific,
America, Europe, Asia, Africa, India, Japan, and Australia.
Specifies the date and the local time. To set the date, click the calendar icon.System Time
When clicked, sets the time on the appliance. You need to click this button before you click
Next.
If it is needed, you can configure Network Time Protocol (NTP) after installation.
Option definitions
DefinitionOption
The value is set according to best practice.
McAfee Email and Web Security Appliance 5.1 Installation Guide28
Page 29
Connecting and Configuring the Appliance
Configuring the appliance using the Setup Wizard
DefinitionOption
The value is probably not correct.
Although the value is valid, it is not set according to best practice. Check the value before continuing.
No value has been set. The value has not been changed from the default. Check the value before
continuing.
Performing a custom setup
For the Custom setup, the wizard includes these these pages:
• Basis Settings
• Network Settings
• DNS and Routing
• Traffic
• Time Settings
• Password
• Summary
Basic Settings
Use this page to specify basic settings for the appliance.
Option definitions
Gateway IP
Network Settings
Use this page to configure the IP address and network speeds for the appliance.
To prevent duplication of IP addresses on your network and to deter hackers, give the appliance
new IP addresses, and disable the default IP addresses. The IP addresses must be unique and
suitable for your network. Specify only as many IP addresses as you need.
DefinitionOption
Specifies a name, such as appliance1.Device name
Specifies a name, such as domain.example.com.Domain name
Specifies an address, such as 198.168.10.1. You can test later that the appliance can
communicate with this server.
Offers a choice of mode.Operating mode
In Transparent Route or Transparent Bridge mode, other network devices, such
as mail servers, are unaware that the appliance has intercepted and scanned the
email before forwarding it. The appliance’s operation is
In Explicit Proxy mode, some network devices send traffic to the appliance. The
appliance then works as a
proxy
, processing traffic on behalf of the devices.
transparent
to the devices.
29McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 30

Connecting and Configuring the Appliance
Configuring the appliance using the Setup Wizard
Option definitions
DefinitionOption
IP Address
DNS and Routing
Use this page to configure the appliance’s use of DNS and routes.
Domain Name System (DNS) servers translate or "map" the names of network devices into IP
addresses (and the reverse operation). The appliance sends requests to DNS servers in the
order that they are listed here.
Option definitions
Server Address
Specifies network addresses to enable the appliance to communicate with your
network.
You can specify multiple IP addresses for the appliance's ports. If the appliance is in
Transparent Bridge mode, the IP addresses are combined into one list for both ports.
In the other modes, click Network Interface 1 or Network Interface 2 to work
on each of the two lists.
The IP address at the top of a list is the primary address. Any IP addresses below it
are “aliases.”
Specifies network mask, for example: 255.255.255.0.Network Mask
DefinitionOption
Specifies the DNS servers. The first server in the list must be your fastest or most
reliable server. If the first server cannot resolve the request, the appliance contacts
the second server. If no servers in the list can resolve the request, the appliance
forwards the request to the DNS root name servers on the Internet.
If your firewall prevents DNS lookup (typically on port 53), specify the IP address of
a local device that provides name resolution.
Traffic
Displays the network address of a routing device.Network Address
Displays the network subnet mask such as 255.255.255.0.Mask
Gateway
Enable dynamic routing
Specifies the IP addresses of other gateways (typically firewall or routers) through
which the appliance will communicate with the network.
The Basic Settings page specified the default gateway.
Displays a number used by routing software. Default value is 0.0.Metric
Dynamic routing allows your network devices, including the appliance, to listen for the
routing information that routers broadcast on your network. The devices can use that
information to configure their own routing information.
NOTE: The appliance supports only the Routing Information Protocol (RIP) and Open
Shortest Path First (OSPF) routing protocols.
Use this page to specify the type of traffic that the appliance scans.
• Web traffic includes HTTP (for web browsing), ICAP (for use with ICAP clients), and FTP for
file transfer.
• Email traffic includes SMTP and POP3.
McAfee Email and Web Security Appliance 5.1 Installation Guide30
Page 31

Connecting and Configuring the Appliance
Configuring the appliance using the Setup Wizard
You can enable or disable each protocol (SMTP, POP3, HTTP, ICAP and FTP). If the appliance
is in Transparent Router or Transparent Bridge mode, and the protocol is disabled, traffic for
the protocol passes through the appliance, but is not scanned.
If the appliance is in Explicit Proxy mode, and a protocol is disabled, traffic directed to the
appliance for that protocol is refused. The protocol is blocked at the appliance. In Explicit Proxy
mode, only SMTP, POP3, HTTP, ICAP and FTP traffic is handled by the appliance. All other traffic
is refused.
If, after installation, you do not want to scan any of the types of traffic, you can disable each
protocol from its page. From the menu, select Email | Email Configuration | Protocol
Configuration or Web | Web Configuration
Time Settings
Use this page to set the time and date, and any details for the use of the Network Time Protocol
(NTP). NTP synchronizes timekeeping among devices in a network. Some Internet Service
Providers (ISPs) provide a timekeeping service. For more information about NTP, see RFC 1305
at www.apps.ietf.org/rfc/rfc1305.html, www.ntp.org or www.ntp.isc.org
The appliance can synchronize its time settings to other devices, keeping its own logs, reports
and schedules accurate. Because NTP messages are not sent often, they do not noticeably
affect the appliances performance.
Option definitions
Time zone
Set time now
Enable NTP client
broadcasts
NTP Server
Password Settings
DefinitionOption
Specifies your local time zone. You might need to set this twice each year if your region
observes daylight saving time.
Specifies the date and the local time. To set the date, click the calendar icon.System time (local)
When clicked, sets the time on the appliance. You need to click this button before
you click Next.
If it is needed, you can configure Network Time Protocol (NTP) after installation.
When selected, accepts NTP messages from a specified server or a network broadcast.Enable NTP
When selected, accepts NTP messages from network broadcasts only. This method
is useful on a busy network but must trust other devices in the network.
When deselected, accepts NTP messages only from servers specified in the list.
Displays the network address or a domain name of one or more NTP servers that
the appliance uses.
If you specify several servers, the appliance examines each NTP message in turn to
determine the correct time.
Use this page to specify a password for the appliance. For a strong password, include letters
and numbers. You can type up to 15 characters.
Option definitions
DefinitionOption
This is scmadmin. You can add more users later.User ID
31McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 32
Connecting and Configuring the Appliance
Using the Appliance
DefinitionOption
Password
Summary
Use this page to review a summary of the settings that you have made through the Setup
Wizard. To change any value, click its blue link to display the page where you originally typed
the value.
After you click Finish, the setup wizard has completed.
Use the IP address shown here to access the interface. For example https://192.168.200.10.
Note that the address begins with https, not http.
When you first log onto the interface, type the user name, scmadmin and the password that
you gave to this setup wizard.
Option definitions
Specifies the new password. Change the password as soon as possible to keep your
appliance secure.
You must enter the new password twice to confirm it. The original default password
is scmchangeme.
DefinitionOption
The value is set according to best practice.
The value is probably not correct.
Although the value is valid, it is not set according to best practice. Check the value before continuing.
No value has been set. The value has not been changed from the default. Check the value before
continuing.
Using the Appliance
Read this information before you use the appliance.
Contents
Updates and HotFixes
After installation
Updates and HotFixes
Before deploying the appliance, download and apply the latest applicable updates and HotFixes
from the download site:
http://www.mcafee.com/us/downloads/
NOTE: You will need a valid grant number.
McAfee Email and Web Security Appliance 5.1 Installation Guide32
Page 33

Connecting and Configuring the Appliance
Testing the Configuration
After installation
After you have installed the appliance, make sure that your configuration is working correctly.
See Testing the appliance.
Testing the Configuration
You are now ready to test the configuration on the appliance. This section includes some
information to help you get started:
• How to start the user interface again.
• Tasks to complete to make sure that the appliance is working correctly.
Contents
Introducing the user interface
Testing the appliance
Introducing the user interface
To start the user interface on the appliance, you must log on using the username and password.
The user interface opens on the Dashboard page.
NOTE: The interface you see might look slightly different from that shown here, because it can
vary depending on the appliance’s hardware platform, software version and language.
Figure 9: Interface components - System Status page
Tab barD
Navigation bar
Support control buttonsENavigation barA
View controlFUser information barB
Content areaGSection iconsC
33McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 34

Connecting and Configuring the Appliance
Testing the Configuration
The navigation bar contains four areas: user information, section icons, tab bar, and support
controls.
User information bar
The left-hand side of the user information bar displays a list of currently logged on users (and
the server they’re logged on to), a Change Password button, and a Log Off button. On the
right-hand side of the bar, About the Appliance gives you appliance and package version
information. Resources provides instructions on how to submit a virus sample to McAfee correctly
and links to additional McAfee resources such as our Service Portal and the Virus Information
Library.
These links can be accessed from the user information bar.
Frequently asked questions on the McAfee website.Technical Support
Instructions for submitting a virus sample to McAfee.Submit a Sample
Virus Information Library
Help Topics
Links to the Virus information Library, which describes every virus and other
potentially unwanted programs that McAfee detects and cleans.
Product and licensing information.About
Contact information and other information.Resources
Help information. Similar to clicking Show Quick Help in the navigation
pane.
Section icons
There are five or six section icons depending on the software that you are using. Click an icon
to change the information in the content area and the tab bar.
Tab bar
The contents of the tab bar are controlled by the selected section icon. The selected tab dictates
what is displayed in the content area.
Support control buttons
The support control buttons are actions that apply to the content area. They are (from left to
right) Back and Help. Two additional buttons appear when you configure something that allows
you to apply or cancel your changes.
View control
The view control button turns an optional Status window on and off.
Content area
The content area contains the currently active content and is where most of your interaction
will be.
NOTE: The changes that you make take effect after you click the green tick.
Testing the appliance
Use these tasks to test:
• The appliance configuration
• Mail traffic
• Virus detection
• Spam detection
NOTE: Before using the appliance, update its DAT files.
McAfee Email and Web Security Appliance 5.1 Installation Guide34
Page 35

Connecting and Configuring the Appliance
Testing the Configuration
Testing connectivity
Use this task to confirm basic connectivity.
Task
1 On the appliance, select Troubleshoot | Tests | System Tests.
2 Click Start in the upper-right corner. Each test should succeed.
3 Look in the System Tests area and check that all the tests are successful.
Testing mail traffic
Use this task to ensure that mail traffic is passing through the appliance.
Task
1 Send an email message from an external email account (such as Hotmail) to an internal
mailbox and confirm that it arrived.
2 Select Dashboard.
The SMTP protocol section shows that a message was received.
Testing virus detection
Use this task to test the software by running the EICAR Standard AntiVirus Test File. This file
is a combined effort by anti-virus vendors throughout the world to implement one standard by
which customers can verify their anti-virus installations.
Task
1 Copy the following line into a file, making sure you do not include any spaces or line breaks:
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
2 Save the file with the name EICAR.COM.
3 From an external email account, create a message that contains the EICAR.COM file as an
attachment and send the message to an internal mailbox.
4 Return to the Dashboard.
The SMTP protocol section shows that a virus was detected.
Delete the message when you finish testing your installation, to avoid alarming unsuspecting
users.
NOTE: This file is not a virus. For more information about the EICAR test file, visit:
http://www.eicar.org//.
Testing spam detection
Use this task to run a
Anti-Spam Module is detecting incoming spam.
Task
1 From an external email account (SMTP client), create a new email message.
General Test mail for Unsolicited Bulk Email
(GTUBE) to verify that the
35McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 36

Connecting and Configuring the Appliance
Testing the Configuration
2 In the body of the message, copy the following text:
XJS*C4JDBQADN1.NSBN3*2IDNEN*GTUBE-STANDARD-ANTI-UBE-TEST-EMAIL*C.34X
Make sure that you type this line with no line breaks.
3 Send the new email message to an internal mailbox address.
The Anti-Spam Module scans the message, recognizes it as a junk email message, and deals
with it accordingly. The GTUBE overrides blacklists and whitelists.
For more information about the GTUBE, visit http://spamassassin.apache.org//.
McAfee Email and Web Security Appliance 5.1 Installation Guide36
Page 37
Exploring the Appliance
This section contains tasks and scenarios that show some key benefits of using a appliance to
protect your gateway.
To complete the tasks and scenarios, you will need some of the information that you entered
in the configuration console and Setup Wizard.
Tasks
Generating reports
Using policies to manage message scanning
Generating reports
The appliance log displays event information according to the report type and period you select.
The appliance’s own reporting features can generate reports, or show logs, statistics, performance
counters and graphs for a wide range of data about the appliance and its activities, such as
memory and processor usage.
For example, after you performed the steps in Testing virus detection, look at the Detections
pane, select Anti-Virus Engine detections, then click Next. The log shows the EICAR test
file that you detected.
Task
Use this task to update the appliance’s DAT files and to then view the the update report.
NOTE: The System Status page is displayed by default each time you log on to the appliance.
1 In the navigation pane, select System | Component Management | Update Status.
2 From the Version information and updates, click Update now for any anti-virus or
anti-spam DAT file updates that you want to update.
3 Return to the navigation pane and select Reports | System reports.
4 Select Filter | Updates.
5 Click Apply. Information about the updates applied to your appliance is displayed.
Further report information
You can:
• Double-click an event to see more information about it.
• Save or print the report.
• Select Options to search for a specific event.
• Use the Show Chart feature to see a graphical representation of the information.
37McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 38

Exploring the Appliance
Using policies to manage message scanning
Using policies to manage message scanning
Use these tasks to demonstrate the appliance scanning features in action. It provides step-by-step
instructions to create and test some sample policies and tells you how to generate applicable
reports.
A policy is a collection of settings and rules that tells the appliance how to combat specific
threats to your network. When you create real scanning policies for your organization, it is
important that you spend time researching and planning your requirements. You can find
guidelines to help you in your policy planning in the
Before you create policies
All quarantine actions are disabled by default. Before you enable them, configure the appliance
to use the McAfee Quarantine Manager to manage the quarantine location. To do this:
1 From the user interface, select Email | Quarantine Configuration.
2 Enter details of your McAfee Quarantine Manager.
Online help
.
Creating an anti-virus scanning policy
Create an anti-virus scanning policy to:
• Detect viruses in incoming messages.
• Quarantine the original email.
• Notify the recipient.
• Alert the sender.
Task
Use this task to demonstrate what happens when a mass mailer virus rule is triggered by the
EICAR test file, and actions that can be taken.
1 On the appliance, ensure that you are using McAfee Quarantine Manager (Email |
Quarantine Configuration).
2 Select Email | Email Configuration | Sending Email.
3 Enter an email address for the Postmaster address.
Without this configuration, the appliance does not include a From: address on the email
notification. Most email servers do not deliver email without a From: address.
4 Click Apply All Changes.
5 Select Email | Email Policies | Scanning Policies | Anti-Virus | Viruses: .
6 Select Attempt to clean as the primary action if cleaning succeeds.
7 Select Deliver a notification email to the sender and Quarantine the original email
as the secondary actions.
8 Select Replace detected item with an alert (Modify) if cleaning fails.
9 Click OK.
10 Select Email | Email Policies | Scanning Policies | Anti-Virus | McAfee
Anti-Spyware:.
11 Select Custom Malware Options; select Mass mailers.
12 In Custom actions, set If detected to Deny connection (Block).
McAfee Email and Web Security Appliance 5.1 Installation Guide38
Page 39

Exploring the Appliance
Using policies to manage message scanning
The sending mail server receives a Code 550: denied by policy error message. The
appliance keeps a list of connections that are not allowed to send email under any
circumstances.
13 Test the configuration:
a Send an email from <client email address> to <server email address>.
b Create a text file that includes the following string:
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
c Save the file as eicar.txt.
d Attach the file to the email.
The gateway security device replaces the file with an alert and the sender receives a
notification alert.
14 Return to Custom Malware Actions and select Specific detection name:
15 Type EICAR.
16 Set the custom action to Refuse the data and return an error code (Block), then click
OK.
17 From an external email account, create a message and attach the EICAR test file.
The email client returns with an error 550: denied by policy error message.
18 In Custom Actions, change the custom action to Deny connection (Block), then click
OK.
19 Send the same email and check the denied connection. It has the IP address of your client
machine (example IP address).
20 Try to send a benign email. This is also denied because of the denied connections list. To
the sending server, it appears that the server is not online.
The appliance checks the message as it enters your mail gateway and identifies that it contains
a virus. It quarantines the message and notifies the intended recipient and the sender that the
message was infected.
Creating an anti-spam scanning policy
Use this task to set up a policy to protect your organization from receiving unsolicited messages.
A policy like this protects users from receiving unsolicited email messages that reduce productivity
and increase the message traffic through your servers.
Task
1 On the appliance, ensure that you are using McAfee Quarantine Manager (Email |
Quarantine Configuration).
2 Select Email | Email Policies | Scanning Policies.
You must set up a separate anti-spam policy for the SMTP and POP3 protocols.
3 Set the primary action to Accept and drop the data.
4 Set the secondary action to Quarantine the original E-mail. Change the spam score to
5.
If you enable anti-spam detection, we recommend that you also enable anti-phishing
detection. Scanning performance is not impacted by performing both anti-spam and
anti-phish checks.
5 From an external email account, create a message to a mailbox protected by the appliance.
39McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 40

Exploring the Appliance
Using policies to manage message scanning
6 In the message body, use the text:
XJS*C4JDBQADN1.NSBN3*2IDNEN*GTUBE-STANDARD-ANTI-UBE-TEST-EMAIL*C.34X
7 Send the message.
8 Open McAfee Quarantine Manager and look at the spam queue.
9 Release the spam message.
10 Check the recipient email account to see the message.
Detected messages are sent to McAfee Quarantine Manager and can be managed by an
administrator.
Creating an email compliance policy
Use this task to set up a policy to ensure that messages your users send to external mail accounts
comply with official content libraries.
This policy maintains regulatory compliance to standards such as the HIPAA personal medical
information privacy standard and privacy standards on messages that contain sensitive
information. It notifies senders that their messages failed the compliance requirements.
Task
1 On the appliance, select Email | Email configuration | Sending email.
2 Select the email compliance options.
3 Set two secondary actions to Deliver an email notification to the sender, and Forward
the original email to GUI defined recipient(s).
4 Click OK.
5 Create an email on the server from <example server email address> to <example client
email address>. Include the line: Hi: You are scheduled for an X-Ray later this week which may
give more indication as to the eventual diagnosis. Please call 123-4567.
6 Check the email client; it should not have received the email. The server account should
receive two email messages: an email notification, and a copy of the original email.
7 Use Monitor | Logs | Content to see the results.
The client email agent does not receive the email. The server email account should receive two
email messages: an email notification that the message failed the compliancy test and a copy
of the original email.
Creating a content filtering policy
Use this task to set up a policy to quarantine incoming messages that contain unwanted content.
Task
1 On the appliance, ensure that you are using McAfee Quarantine Manager (Email |
Quarantine Configuration)
2 On the appliance, select Email | Email Policies| Content | Content scanning.
3 Select Yes to enable Content Scanning.
4 Select Create a new content scanning rule.
5 Select the Gambling (English) dictionary.
McAfee Email and Web Security Appliance 5.1 Installation Guide40
Page 41

Exploring the Appliance
Using policies to manage message scanning
6 Select the action listed under If Triggered.
7 In If the content scanning rule is triggered, select Replace the content with an
alert.
8 In And also, select Quarantine the original email.
9 Click OK.
10 Click OK.
11 Apply the configuration (click the green check icon on the top right of the screen).
12 From an external email account, create a message to a test mailbox that the appliance
protects.
13 In the message body, type the words: See you at the blackjack table tonight!
14 Send the message.
15 Open the mailbox to which you addressed the message and view the alert message.
16 Click Dashboard to view Email Detections and Email Queues. The Content filtered
and the Quarantined messages counts have increased.
17 Click the Quarantined messages link to display information on these messages.
18 Using the recipient’s email account, open McAfee Quarantine Manager User interface and
select Unwanted Content.
19 Select the message and click Submit for Release.
20 Open the McAfee Quarantine Manager Administrator interface and select User
Submissions.
21 Select Submitted for Release.
22 Select the message and click Release.
23 Open the mailbox to which you sent the message to view the received message.
The appliance checks the message as it enters your mail gateway and identifies that it contains
content that needs to be filtered.a virus. The appliance quarantines the message and notifies
the intended recipient that the message included filtered content.
41McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 42
Troubleshooting
This section includes solutions to problems that you might encounter when installing and running
the appliance, as well as an FAQ.
General problems
FAQ
Getting more help — the links bar
General problems
This section lists some general problems.
The appliance is not receiving power
Check that the appliance is using the correct power cord(s) and is connected properly to a
working power outlet. If the power outlet has a switch, make sure it is on.
If the appliance is still not receiving power, check the power outlet by connecting other equipment
to it. If the power outlet is working, there is a problem with the appliance or its power cord.
Contact your supplier.
The appliance is not receiving traffic from the network
Check the following:
• The appliance is switched on and its software is running.
If the power button LED is orange, the appliance is connected but is not turned on. If the
power LED is green, the appliance is connected and turned on.
• The network cables are undamaged and connected properly to the appliance’s ports and
your network equipment. If you have not used the cables supplied with the appliance, ensure
that your cables meet the correct specification.
• Your network equipment is connected to the correct LAN ports on the appliance.
• The NIC speeds and full or half duplex settings at both ends of the connections are compatible
and have auto-negotiated their settings correctly.
• The LAN LEDs are on.
If the appliance is still not receiving network traffic, check the network cables and the network
ports on your network equipment. If the cables and ports are working, there is a problem with
the appliance. Contact your supplier.
McAfee Email and Web Security Appliance 5.1 Installation Guide42
Page 43

Troubleshooting
FAQ
FAQ
This section describes some of the problems you might encounter when integrating your
appliance into the existing network.
General issues
This section describes general issues.
I increased the number of listeners, but the performance is worse.
Increasing the number of listeners increases the number of transfers that the appliance can
handle in parallel. However, running more listeners means using more memory, and possibly
more swapping to disk. Eventually, the advantage of more parallel connections is offset by the
increased disk swapping, leading to slower overall performance. The defaults provide guidance
about the correct value to use.
I increased the memory for anti-virus scanning per listener, but performance is
worse.
The appliance allocates an area of memory for anti-virus scanning. When this size is exceeded,
a message is written to disk before being scanned, which is slower. Usually, a larger area of
memory means better performance. However, if you set the memory area too high, the appliance
cannot allocate the memory and starts swapping to disk. This leads to an overall slowing of
performance. The defaults provide guidance about the correct value to use.
Interface problems
This section contains solutions to problems you might encounter when trying to configure the
appliance through its interface.
Why does using the Back button on my browser take me to the Logon screen?
This is a known issue with the web browser version of the appliance software. Use the appliance
application instead.
I cannot access the Logon screen.
Check the following:
• The appliance is turned on and its software is running — the power LED is lit and the hard
disk drive LEDs are off.
• You used https (not http) in the address field of your web browser. Ensure that your
browser supports Secure Sockets Layer (SSL) encryption and that it is enabled.
• The computer you are using to manage the appliance does not have the appliance configured
as its proxy. If you have a proxy between the management computer and the appliance,
the proxy must be configured with the appliance as its handoff host.
• If you are remotely connected to the appliance (across the network) through the LAN1 port,
ensure that:
• The computer you are using has a working connection to your network, and that it can
reach the same subnet to which the appliance is connected.
43McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 44

Troubleshooting
FAQ
• You have used the new IP address that you configured for the LAN1 port, in the URL
field of your web browser. If you have not disabled or deleted the default IP address
10.1.1.108, try using that IP address (https://10.1.1.108).
The appliance’s IP address must be suitable for the subnet to which the appliance is
connected. If it is not, use the default IP address and, if that fails, try a direct management
connection.
NOTE: You can obtain a direct management connection through the LAN2 port only if
you are using the appliance in explicit proxy mode and you have not disabled the LAN2
port
• The appliance has a working connection to your existing network, indicated by the NIC
1 network activity LED flashing on the control panel.
If the LEDs are not flashing, ensure that the cable you are using is undamaged and
connected properly to the appliance’s LAN1 port and your existing network equipment.
If you have not used the blue cable supplied with the appliance, ensure that the cable
is a UTP straight-through (uncrossed) network cable.
• If the appliance is operating in explicit proxy mode and you have a direct local management
connection through its LAN2 port, ensure that:
• You have not disabled the LAN2 port. Connect remotely to check this.
• You used the new IP address that you configured for the LAN2 port (the default is
10.1.2.108), in the URL field of your web browser.
• The appliance has a working connection to your computer, indicated by the NIC 2 network
activity LED flashing on the control panel.
If the LED is not flashing, ensure that the cable you are using is undamaged and connected
properly to the appliance’s LAN2 port and your computer’s network port. If you have not
used the orange cable supplied with the appliance, ensure that the cable is a UTP crossed
network cable.
My password does not work.
If you recently restored the appliance’s software without maintaining the previous settings, the
management password reverts to the default password, scmchangeme.
I forgot my password.
Using the appliance’s recovery CD, return the appliance’s password to the default passwords,
which are scmchangeme and dlpchangeme.
Some of the interface does not display properly.
The appliance’s interface is intended for Internet Explorer 6.0 or later on Windows, and Mozilla
Firefox 2.0 on Linux. Check the accompanying release notes for known issues when using some
web browsers on particular operating systems.
Client (software) cannot communicate through theappliance.
Check the following:
• The correct protocols are enabled for the appliance (all protocols are enabled by default).
• The clients and other devices are configured to route traffic to and from the appliance.
• The network has no problems, and your device is connected correctly.
McAfee Email and Web Security Appliance 5.1 Installation Guide44
Page 45

Troubleshooting
FAQ
Web browsing does not work or URL blocking is not enforced.
The appliance must have access to a DNS server to verify web browsing (HTTP) requests and
determine which URLs to block, if URL blocking is configured.
Mail issues
This section discusses mail issues.
Anti-relay is not working.
To enable the anti-relay feature:
1 In the navigation pane, select Configure | SMTP.
2 Select Protocol Settings | Anti-Relay Settings.
3 Specify at least one local domain in Local Domains. Otherwise, the appliance is open to
relaying and abuse by spammers from outside your network.
Why can’t I just give the name of the sender that I want to block from relaying?
Think of anti-relay as system-to-system blocking, while anti-spam is sender-based blocking.
Anti-relay is configured using the domains and networks that the appliance delivers mail for,
while the anti-spam configuration blocks a message based on who sent it.
Directory Harvest Prevention does not work.
For Directory Harvest Prevention to work correctly, your email server must check for valid
recipients during the SMTP conversation, and then send a non-delivery report.
Several email servers do not send User unknown errors as part of the SMTP configuration.
These include (but might not be limited to):
• Microsoft Exchange 2000 and 2003 (when using their default configuration).
• qmail.
• Lotus Domino.
Check the user documentation for your email server to see if your email server can be configured
to send 550 Recipient address rejected: User unknown reports as part of the SMTP conversation
when a message to an unknown recipient is encountered.
LDAP integration can provide a workaround for this. See the
Appliances 4.5 Product Guide
Delivery
Messaging and Web Security
.
This section describes delivery issues.
When I select Retry All in the Deferred Mail folder, why are the messages not sent?
After selecting Retry All, select Refresh to see the progress that the appliance has made
through the list of messages.
The appliance works through the messages until each one is sent. If there is still a delivery
problem caused by the network or an appliance configuration problem, the message is returned
to the Deferred Mail folder.
45McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 46

Troubleshooting
FAQ
The appliance automatically retries all the deferred messages after 30 minutes, and periodically
after that.
What can I check if I have problems with mail delivery?
To deliver mail via DNS, ensure that the DNS option is selected in the interface.
If your internal mail server is not receiving inbound mail, check that this mail server is configured
to accept email from the appliance.
In the list of local domains for email delivery, do not specify a wildcard catch-all rule. Instead,
enable the fallback relay, and specify it there.
Email attachments
This section discusses email attachment issues.
The appliance blocks all email when I reduce the number of attachments to block.
This setting is intended to block email messages with huge numbers of attachments, which
waste bandwidth.
Some mail clients (like Outlook Express) store extra information in extra attachments, and even
embed the main body of the message in an attachment.
If this number is set too low, even normal email might be rejected.
EICAR (the test virus) or content that must be blocked is still getting through.
Make sure the appliance is in the mail path. Look at the headers of an email message (in Outlook,
select View | Options | Internet Headers).
If the appliance is in the mail path, you see a header of the form Received: from sender by
server_name via ws_smtp with sender and server_name replaced with the actual sender’s
name and the name of the appliance.
When the appliance detects a virus, I get notification of a content violation.
This problem might be due to a conflict between the HTML template warning page, and a
content-scanning rule.
For example, if you are content-filtering on the word Virus but you have also set up the HTML
template for virus detection to warn you that a virus has been detected, an incoming message
containing a virus triggers the message to be replaced with the message, A virus has been
detected. This replacement message then passes through the content filter which triggers on
the word Virus, and the message is replaced with a content violation instead of a virus
notification.
Mail from some senders is getting through, while others are being blocked.
Check the configuration of your inside and outside networks. Make sure that the list of outside
networks has an asterisk (*) as the last entry. Also, make sure that the list of inside networks
does not have an asterisk.
POP3
This section discusses POP3 issues.
McAfee Email and Web Security Appliance 5.1 Installation Guide46
Page 47

Troubleshooting
FAQ
I set up a dedicated POP3 connection, and POP3 no longer works.
Check that the generic and dedicated servers do not share the same port. The default port
number for POP3 is 110. The dedicated server will override the generic server.
When fetching mail with Outlook Express over POP3, I sometimes get a time-out
message, giving me the option to Cancel or Wait.
The appliance needs to download and scan the entire mail message before it can start passing
it to Outlook Express. For a large message or a slow mail server, this can take some time. Click
Wait to force Outlook Express to wait for the appliance to finish processing the message.
I sometimes get two copies of POP3 mail messages.
Some mail clients do not handle timeouts correctly. If the appliance is downloading and scanning
a very large message, the client might time out while waiting for a response.
A popup window prompts you to wait for or cancel the download. If you select Cancel and try
to download again, two copies of the message might appear in your mailbox.
Physical configuration
This section discusses physical configuration issues.
I connected the appliance to the network but I cannot connect to it with my browser.
In explicit proxy mode, make sure you have connected the LAN1 adapter to your network. LAN2
is for administration only, and needs to connect directly to a laptop or computer.
My network has two appliances but I can log on to only one
If you have installed a appliance, or recently used the Restore Configuration option, two or
more appliances on your network might have the same default IP addresses.
To make sure all appliances have unique IP addresses, you can use:
• The Setup Wizard.
• The network settings.
• The Configuration Console.
System configuration
This section discusses system configuration issues.
I set up different rules for inbound and outbound traffic. When I receive email
messages or browse outside websites, the Outbound rule is triggered instead of the
Inbound rule.
Make sure that the IP address of the firewall is included in the list of outside networks.
Connections from the outside may appear to the appliance as though they were coming from
the firewall.
System maintenance
This section discusses system maintenance issues.
47McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 48

Troubleshooting
FAQ
The appliance does not accept the HotFix file.
Do not unzip the HotFix file before uploading it to the appliance. The appliance accepts the
original file as you received it — with a .TGZ extension.
How can I control the size of the appliance’s log files?
The appliance stores its log files in a text-like (XML) format in a partition (/log) on its internal
disk. By default, the logs are purged every few days. The appliance issues warnings when its
areas are nearing full, typically at 75% and 90%.
• To find the percentage usage of the logging partition, select Monitor | Status in the
navigation pane. Click Settings to adjust the indicator colors.
• To purge the log, select Configure | Logging, Alerting and SNMP in the navigation
pane, then under Channel settings, select the XML tab.
• To adjust the warning levels, select Monitor | Resources in the navigation pane, then
select Disk usage.
Anti-virus automatic updating
This section discusses issues with anti-virus automatic updating.
When I request an immediate update, nothing happens. How do I know when the
DAT is updated?
To see the installed DAT version number:
• In the navigation pane, select Monitor | System Status, then General Status.
• Alternatively, select Monitor | Updates.
The DAT files are downloaded, checked and applied.
The appliance does not wait for the update to complete (which can take a few minutes even
with a fast Internet connection) but starts it in the background.
Select Monitor | System Status to show the new DAT version number when you next view
the page after the new DAT files have been successfully installed.
Anti-spam
This section discusses anti-spam issues.
I cannot find the anti-spam features described in this guide.
Some anti-spam features need the Anti-Spam Module to be enabled.
I have configured the appliance to reject spam with an RBL Servers check but some
spam mail is still getting through.
No anti-spam software is fully effective, and cannot guarantee to block all spam email messages.
The appliance uses a list of the names of known email abusers and the networks they use.
These lists are effective in reducing unwanted email messages but are not complete.
To block a specific sender of spam:
1 In the navigation pane, select Configure | SMTP.
2 Select Protocol Settings | Permit and Deny Settings.
McAfee Email and Web Security Appliance 5.1 Installation Guide48
Page 49

Troubleshooting
FAQ
3 At Deny Sender, type the sender’s email address.
Users are not getting normal email messages.
Users might not receive normal email messages for several reasons:
• The email messages might be coming from someone listed in the Deny Sender list. You
might need to:
• Refine the Deny Sender list to ensure that wanted email messages are not blocked. For
example, you might need to type specific email addresses rather than ban a whole domain
or network.
• Add the sender, domain, or network to the Permit Sender list. The appliance does scan
email from senders, domains and networks in this list for spam. The Permit Senders
list overrides entries in the Deny Sender lists.
• The email message might have been blocked because it comes from a sender or organization
that has been recognized by one of your real time anti-spam lists as a potential source of
spam.
• The balance between blocking spam and normal email messages might need changing. For
example, if the appliance is blocking email messages when there is only a small chance that
they contain spam, you risk unintentionally blocking normal email messages. It is better to
risk letting some spam through.
• The email message might contain a virus or potentially unwanted program, and has been
blocked by anti-virus scanning.
Users are still receiving spam.
Users might still receive spam for several reasons:
• No anti-spam software can block all email messages that might contain spam. For the best
chance of detecting and preventing spam, ensure that the appliance is using the latest
versions of the anti-spam engine, anti-spam rules, and extra rules files, as well as using all
the features that can block unwanted email.
• The appliance is allowing streaming media to pass through.
NOTE: Allowing streaming media to pass through the appliance is a security risk, because
streaming media is not scanned by the appliance. We recommend that you do not allow
streaming media of type
application/octet-stream or application/*
to pass through the
appliance because these MIME types are executable and are a security risk
• Scanning for spam is not enabled on the appliance. Scanning must be enabled in the right
direction for spam detection. To detect spam from an external source, enable inbound
scanning. To detect spam from an internal source, enable outbound scanning.
• You might need a more stringent anti-spam policy. For example, you might want to ensure
that more email messages are marked as spam before they are received by users, or to
simply block the spam at the appliance.
• The email messages might be coming from senders, domains, or networks that are in the
Permit Sender list. Review the list to make sure that you really want email messages from
these senders to bypass anti-spam scanning. You might need to refine the entry in the list.
For example, rather than permitting whole domains or networks, specify individual email
addresses instead.
• The mail client software does not automatically move unwanted messages into a spam
folder, so users still see spam in their inboxes.
49McAfee Email and Web Security Appliance 5.1 Installation Guide
Page 50
Troubleshooting
Getting more help — the links bar
• The email message might be larger than is permitted, so it is not scanned for spam. See
your advanced settings for spam to change the size.
• Email messages are not being routed through an appliance with the Anti-Spam Module
enabled.
How can I stop a particular type of spam?
To ensure that you have the best chance of detecting and preventing spam, check that:
• The appliance is using the latest versions of the anti-spam engine and anti-spam rules.
• The appliance has not been configured to allow streaming media to pass through.
Why has the performance changed?
Scanning email messages for spam requires appliance resources and affects SMTP performance.
Users are complaining that their mailboxes are full.
If users automatically divert spam to a spam folder in the mailbox, their mailboxes can quickly
exceed their size limit. Remind users to regularly check their spam folder and delete spam.
Getting more help — the links bar
The links bar in the appliance interface window provides links to more sources of information.
You can:
• Access the McAfee online virus information library to find out more about a specific virus.
• Submit a virus sample to McAfee for analysis.
• Contact McAfee Technical Support.
See the
Online help
for more information.
McAfee Email and Web Security Appliance 5.1 Installation Guide50
 Loading...
Loading...