Page 1
Wireless-G Notebook Adapter
Chapter 6:Driver Installation and
Configuration for Windows XP
After inserting the Adapter into your notebook, you will install the driver and
configure the Adapter.
1. Windows XP will automatically detect the Adapter. Insert the Setup CD-
ROM into the CD-ROM drive. Click the radio button next to Install the
software automatically (Recommended). Then click the Next button.
11
Figure 6-1
Overview
Driver Installation for Windows XP
Instant Wireless®Series
10
Chapter 5:Hardware Installation
1. Turn off your notebook PC.
2. Locate an available CardBus slot on your notebook PC.
3. With the Adapter’s
label facing up, as
shown in Figure 5-1,
slide the Adapter
completely into the
CardBus slot.
4. Restart your notebook PC.
5. Windows will begin copying the driver files to your computer. If Windows
asks you for the original Windows CD-ROM, insert the CD-ROM, and
direct Windows to its proper location (e.g., D:\).
If your PC is using Windows 98SE, Me, or 2000,proceed to the next section, “Chapter 7: Using the WLAN Monitor for Windows 98SE, Me , and
2000.”
If your PC is using Windows XP, proceed to “Chapter 6: Driver
Installation and Configuration for Windows XP.”
Figure 5-1
Important for Windows 98SE, Me, and 2000 users: You must run
the Setup W izard to install the software before installing the hardware.
Important for Windows XP users: You must install the Adapter’s
hardware before installing the software.
Page 2
Wireless-G Notebook Adapter
13
Instant Wireless®Series
2. When Windows has finished installing the driver, click the Finish button.
You have now completed the driver installation for
the Adapter.To configure the Adapter, proceed to the next section,
“Windows XP Wireless Zero Configuration.”
12
Figure 6-2
1. After installing the Adapter, the
Windows XP Wireless Zero
Configuration icon will appear in
your computer’s system tray (see
Figure 6-3). Double-click the icon.
2. The screen that appears will
show any available wireless
network. Select the network
you want.
If this network has WEP
encryption enabled, go to
step 3. If this network does
not have WEP encryption
enabled, then the screen in
Figure 6-4 will appear.
Check the box next to Allow
me to connect to the selected
wireless network, even
though it is not secure. Then
click the Connect button and
go to step 4.
For W indo ws XP users:W indo ws XP has a built-in configuration tool.
Use Windows XP Wireless Zero Configuration (in the system tray at
the bottom of your screen) to configure the Adapter.
Figure 6-3
Figure 6-4
Note: In Steps 2 and 3, these are the instr uctions and screenshots for
Windows XP with Service Pack 1 installed. If you have not installed
Service Pack 1, select the network you want, and click the Connect
button. If the network has WEP encryption enabled, enter the WEP
key in the Network key field, and then click the Connect button.
Windows XP Wireless Zero Configuration
Page 3
Wireless-G Notebook Adapter
15
Instant Wireless®Series
14
Chapter 7:Using the WLAN
Monitor for Windows 98SE, Me,
and 2000
Use the WLAN Monitor to check the link information, search for available
wireless networks, or create profiles that hold different configuration settings.
After installing the Adapter, the Wireless-G Notebook Adapter
WLAN Monitor icon will appear in your system tray. Doubleclick the icon (see Figure 7-1).
The Link Information screen will appear. From this screen, you can find out
how strong the current wireless signal is and how good the connection’s quality is. You can also click the More Information button to view additional status
information about the current wireless connection. T o search for a v ailable wireless networks, click the Site Survey tab. To perform configuration changes,
click the Profiles tab.
Figure 7-1
Figure 7-2
Accessing the WLAN Monitor
Overview
3. The screen in Figure 6-5 will appear. Enter the WEP key of your wireless
network in the Network key field, and re-enter it in the Confirm network ke y
field. Click the Connect button.
4. The screen in Figure 6-6 will
appear if your connection is
active.
For more information about WEP, refer to your access point’s documentation,
or visit www.linksys.com.
For more information about wireless networking on a Windows XP computer,
enter the keyword wireless in the Windows XP search engine.
Congratulations!
Your notebook is now connected to your wireless network.
Figure 6-5
Note: Wireless Zero Configuration does not support the use of a
passphrase. Enter the exact WEP key used by your access point.
Figure 6-6
Page 4

Wireless-G Notebook Adapter
17
Instant Wireless®Series
The Link Information screen displays signal strength and link quality informa-
tion about the current connection and provides a button to click for additional
status information.
Ad-Hoc Mode or Infrastructure Mode - The screen indicates whether the
Adapter is currently working in ad-hoc or infrastructure mode.
Signal Strength - The Signal Strength bar indicates signal strength, from 0 to
100%.
Link Quality - The Link Quality bar indicates the quality of the wireless network connection, from 0 to 100%.
Click the More Information button to view more information about the wireless network connection.
Click the X (Close) button in the upper right corner to exit the WLAN Monitor.
16
TCP/IP Setting
IP Address - The IP Address of the Adapter.
Subnet Mask - The Subnet Mask of the Adapter.
Default Gateway - The Default Gateway address of the Adapter.
DHCP - The status of the DHCP client.
DNS - The DNS address of the Adapter.
Wireless Network Status
State - The status of the wireless network connection.
SSID - The unique name of the wireless network.
Wireless Mode - The mode of the wireless network currently in use.
Transfer Rate - The data transfer rate of the current connection.
Channel - The channel to which the wireless network devices are set.
WEP - The status of the WEP encryption security feature.
MAC - The MAC address of the wireless network’s access point.
Signal Strength - The Signal Strength bar indicates signal strength, from 0 to
100%.
Link Quality - The Link Quality bar indicates the quality of the wireless network connection, from 0 to 100%.
Click the Back button to return to the initial Link Information screen. Click the
X (Close) button in the upper right corner to exit the WLAN Monitor.
Figure 7-4
Link Information
Figure 7-3
Page 5
Wireless-G Notebook Adapter
In the WEP drop-down box, select the type of WEP encryption used by the
wireless network: 64-bit, or 128-bit WEP.
If the wireless network uses a passphrase, enter the passphrase in the
Passphrase field. If the wireless network uses a WEP key, enter the WEP key
in the Key 1 field.
Click the OK button to complete the network connection and return to the Site
Survey screen, or click the Cancel button to cancel the network connection and
return to the Site Survey screen.
On the Site Survey screen, click the X (Close) button in the upper right corner
to exit the WLAN Monitor.
19
Instant Wireless®Series
18
Figure 7-6
The Site Survey screen displays a list of infrastructure and ad-hoc networks
available for connection.
SSID - The SSID or unique name of the wireless network.
Signal - The percentage of signal strength, from 0 to 100%.
Site Information
Wireless Mode - The mode of the wireless network currently in use.
Channel - The channel to which the wireless network devices are set.
WEP - The status of the WEP encryption security feature.
MAC - The MAC address of the wireless network’s access point.
Surveyed at - The time at which the wireless network was scanned.
Refresh - Click the Refresh button to perform a new search for wireless
devices.
Connect - T o connect to one of the networks on the list, select the wireless network, and click the Connect button. If the wireless network has WEP encryption enabled, you will see the screen shown in Figure 7-6.
Figure 7-5
Site Survey
Page 6
Wireless-G Notebook Adapter
21
Instant Wireless®Series
20
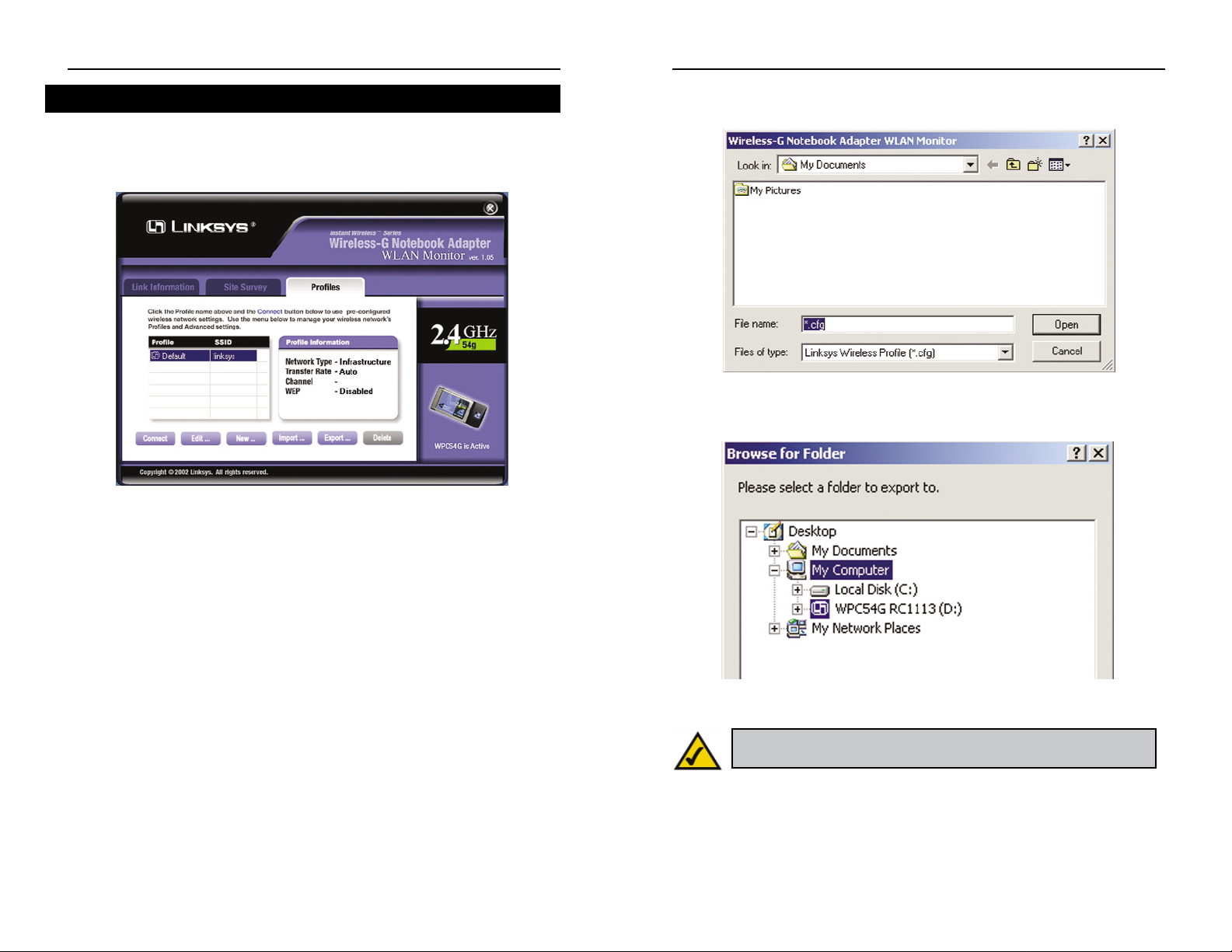
Import - Click the Import button to import a prof ile that has been saved in
another location. Select the appropriate file, and click the Open button.
Export - To save the profile(s) in a different location, click the Export button.
Direct Windows to the appropriate folder, and click the OK button.
Delete - Click the Delete button to delete a profile.
Click the X (Close) button in the upper right corner to exit the WLAN Monitor.
Figure 7-8
Figure 7-9
Note: If you have more than one profile, all prof iles will be automatically selected and exported to the same folder.
The Profiles screen lets you save different configuration prof iles for different
network setups. You can also import or export profiles. The default profile
holds the initial configuration saved when you ran the Setup Wizard.
Profile - Name of the connection prof ile.
SSID - The wireless network’s unique name, as set in the connection profile.
Profile Information
Network Type - The mode of the wireless network currently in use.
Transfer Rate - The data transfer rate of the current connection. (In Auto
mode, the Adapter dynamically shifts to the fastest data transfer rate possible
at any given time.)
Channel - The channel to which the wireless network devices are set.
WEP - The status of the WEP encryption security feature.
Connect - To connect to a wireless network using a specif ic profile, select the
profile, and click the Connect button.
Edit - Select a profile, and click the Edit button to change an existing profile.
New - Click the New button to create a new profile. See the next section,
“Creating a New Profile,” for detailed instructions.
Figure 7-7
Profiles
Page 7

Wireless-G Notebook Adapter
2. The Choose a network type screen shows a choice of two wireless modes.
Click the Infrastructure Mode radio button if you want your wireless
computers to communicate with computers on your wired network via a
wireless access point. Click the Ad-Hoc Mode radio button if you want
multiple wireless computers to communicate directly with each other . Click
the Next button to continue or the Back button to return to the previous
screen.
Infrastructure Mode - This mode allows wireless and wired networks to
communicate through an access point.
Ad-Hoc Mode - This mode allows wireless-equipped computers to communicate directly with each other. No access point is used.
23
Instant Wireless®Series
1. On the Profiles screen, click the New button to create a new prof ile.
2. When the Create connection profile screen appears, enter a name for the
new profile. Click OK to save the profile name or click Cancel to return to
the previous screen.
22
Figure 7-11
Creating a New Profile
Figure 7-10
Figure 7-12
Page 8

Wireless-G Notebook Adapter
25
Instant Wireless®Series
3. The W ireless Settings screen will appear. If you chose Infrastructure Mode,
go to Step 4 now. If you chose Ad-Hoc Mode, select the correct operating
channel for your network from the Channel drop-down menu. Then, select
the Network Mode from the drop-down menu. Click the Next button, and
go to Step 4. Click the Back button to change any settings.
Channel - The channel you choose should match the channel set on the
other devices in your wireless netw ork. If y ou are unsure about which channel to use, select the default channel (Channel 6).
Network Mode - Select Mixed Mode, and both Wireless-G and WirelessB computers will be allow ed on the network, but the speed will be reduced.
Select G-Only Mode for maximum speed, but no Wireless-B users will be
allowed on the network.
24
4. The Network Setting screen will appear.
If your network has a DHCP server, click the radio button next to Obtain
an IP address automatically (DHCP). Click the Next button to continue,
or click the Back button to return to the previous screen. Then go to Step 5.
If your network does not have a DHCP server , click the radio button ne xt to
Specify the IP address. Enter an IP Address, Subnet Mask, Default
Gateway, and DNS appropriate for your network. Enter each address in this
format: xxx.xxx.xxx.xxx (the x’s represent the numbers that make up each
address). You must specify the IP Address and Subnet Mask on this screen.
If you are unsure about the Default Gateway and DNS addresses, then leav e
these fields alone.
Click the Next button to continue or the Back button to return to the previous screen. Then go to Step 5.
IP Address - This IP Address must be unique to your network.
Subnet Mask - The Adapter’s Subnet Mask must be the same as your wired
network’s Subnet Mask.
Default Gateway - Enter the IP address of your network’s Gateway here.
DNS - Enter the DNS addresses of your Ethernet (wired) network here.
Figure 7-13
Figure 7-14
Page 9

Wireless-G Notebook Adapter
27
Instant Wireless®Series
5. The Security Settings screen will appear. Enable or disable Wired
Equivalent Privacy (WEP) encryption for your wireless network. If you
enable WEP, enter a Passphrase or WEP key. Click the Next button to continue or the Back button to return to the previous screen.
WEP (Disabled/64-bit WEP/128-bit WEP) - If you do not want to use
WEP encryption, choose Disabled. To use WEP encryption (recommended
to increase network security), select 64-bit or 128-bit WEP from the dropdown menu, and enter either a Passphrase or WEP key.
Passphrase - Instead of manually entering WEP keys, you can enter a
Passphrase, so that a WEP key is automatically generated. It is case-sensitive and should not be longer than 16 alphanumeric characters. This
passphrase must match the passphrase of your wireless network and is compatible with other Linksys wireless products only. (If you have any nonLinksys wireless products, enter the WEP key(s) manually on those products.)
Key 1 - This WEP key must match the WEP key of your wireless network.
If you are using 64-bit WEP encryption, then the key must consist of e xactly 10 hexadecimal characters. If you are using 128-bit WEP encryption,
then the key must consist of exactly 26 hexadecimal characters. Valid hexadecimal characters are “0” to “9” and “A” to “F”.
26
6. The Conf irm New Settings screen will appear. To save the new settings,
click the Yes button. T o cancel the settings and return to the Profiles screen,
click the No button. To edit the new settings, click the Back button.
7. The Congratulations screen will appear next. Click Activate new settings
now to implement the new settings immediately and return to the Link
Information screen. Click Activate new settings later to keep the current
settings active, and return to the Profiles screen so that you can edit your
profile or create another profile.
You have successfully cr eated a connection pr ofile. Click the X (Close) but-
ton in the upper right corner to exit the WLAN Monitor.
Figure 7-16
Figure 7-17
Figure 7-15
Page 10

Wireless-G Notebook Adapter
3.I cannot communicate with a wired computer linked via an access point in the
infrastructure configuration.
• Make sure that the notebook PC is powered on.
• Make sure that the Adapter is configured with the same SSID and security
options as the other computers in the infrastructure conf iguration.
Can I run an application from a remote computer over the wireless network?
This will depend on whether or not the application is designed to be used over
a network. Consult the application’s user guide to determine if it supports operation over a network.
Can I play computer games with other members of the wireless network?
Yes, as long as the game supports multiple players over a LAN (local area network). Refer to the game’s user guide for more information.
What is the IEEE 802.11b standard?
It is one of the IEEE standards for wireless networks. The 802.11b standard
allows wireless networking hardware from different manufacturers to communicate, provided that the hardware complies with the 802.11b standard. The
802.11b standard states a maximum data transfer rate of 11Mbps and an oper-
ating frequency of 2.4GHz.
29
Instant Wireless®Series
Appendix A:Troubleshooting
This chapter provides solutions to problems that may occur during the installation and operation of the Wireless-G Notebook Adapter. Read the descriptions
below to solve your problems. If you can’t find an answer here, check the
Linksys website at www.linksys.com.
1.My computer does not recognize the Adapter.
• Make sure the Adapter is properly inserted into the CardBus slot. Note that
the Adapter can be inserted either way, but is correctly only w hen it is inserted so that the “Instant Wireless” logo on the front of the Adapter cannot be
seen. If in doubt, try inserting the Adapter both ways. The Adapter will slide
in further when it is correct.
2.The Adapter does not work properly.
• Reinsert the Adapter into your notebook’s CardBus slot. A beep should be
heard if the Adapter is properly inserted.
• For non-Windows environments, make sure that a PCMCIA card service
driver is installed on your PC.
• Open the Control Panel and click the PC Card. Check whether it has a
PCMCIA card in one of the sockets or not. If you find the Adapter in one of
the sockets, it means that the Adapter has been detected properly. If you see
a yellow question mark, the resources are in conflict.
• Right-click My Computer and select Properties. Select Device Manager
and click the Network Adapter. You will find the Wireless-G Notebook
Adapter if it is installed successfully. If you see the y ello w e xclamation mark,
the resources are in conflict. Click PCMCIA card and then click PCMCIA
card service. You will see the status of the Adapter. If there is a yellow question mark please check the following:
• Make sure that your notebook has a free IRQ.
• Make sure that you have inserted the right Adapter and installed the prop-
er driver.
If the Adapter does not function after attempting the above steps, remove the
Adapter and do the following:
• Uninstall the driver software from your PC.
• Restart your PC and repeat the hardware and software installation as specified in this User Guide.
28
Frequently Asked Questions
Common Problems and Solutions
Page 11

As the user moves on, the end node’s RF transmitter regularly checks the system to determine whether it is in touch with the original access point or whether
it should seek a new one. When a node no longer receives acknowledgment
from its original access point, it undertakes a new search. Upon finding a new
access point, it then re-registers, and the communication process continues.
What is ISM band?
The FCC and their counterparts outside of the U.S. have set aside bandwidth
for unlicensed use in the ISM (Industrial, Scientific and Medical) band.
Spectrum in the vicinity of 2.4 GHz, in particular, is being made available
worldwide. This presents a truly revolutionary opportunity to place convenient
high-speed wireless capabilities in the hands of users around the globe.
What is Spread Spectrum?
Spread Spectrum technology is a wideband radio frequency technique developed by the military for use in reliable, secure, mission-critical communications systems. It is designed to trade off bandwidth efficiency for reliability,
integrity, and security. In other words, more bandwidth is consumed than in the
case of narrowband transmission, but the trade-off produces a signal that is, in
effect, louder and thus easier to detect, provided that the receiver knows the
parameters of the spread-spectrum signal being broadcast. If a receiver is not
tuned to the right frequency, a spread-spectrum signal looks like background
noise. There are two main alternatives, Direct Sequence Spread Spectrum
(DSSS) and Frequency Hopping Spread Spectrum (FHSS).
What is DSSS? What is FHSS? And what are their differences?
Frequency-Hopping Spread-Spectrum (FHSS) uses a narrowband carrier that
changes frequency in a pattern that is known to both transmitter and receiver.
Properly synchronized, the net effect is to maintain a single logical channel. To
an unintended receiver, FHSS appears to be short-duration impulse noise.
Direct-Sequence Spread-Spectrum (DSSS) generates a redundant bit pattern
for each bit to be transmitted. This bit pattern is called a chip (or chipping
code). The longer the chip, the greater the probability that the original data can
be recovered. Even if one or more bits in the chip are damaged during transmission, statistical techniques embedded in the radio can recover the original
data without the need for retransmission. To an unintended receiver, DSSS
appears as low power wideband noise and is rejected (ignored) by most narrowband receivers.
What IEEE 802.11b features are supported?
The product supports the following IEEE 802.11b functions:
• CSMA/CA plus Acknowledge protocol
• Multi-Channel Roaming
• Automatic Rate Selection
• RTS/CTS feature
• Fragmentation
• Power Management
What is ad-hoc mode?
When a wireless network is set to ad-hoc mode, the wireless-equipped computers are configured to communicate directly with each other. The ad-hoc
wireless network will not communicate with any wired network.
What is infrastructure mode?
When a wireless network is set to infrastructure mode, the wireless network is
configured to communicate with a wired network through a wireless access
point.
What is roaming?
Roaming is the ability of a portable computer user to communicate continuously while mo ving freel y throughout an area greater than that co vered b y a single access point. Before using the roaming function, the workstation must make
sure that it is the same channel number with the access point of dedicated coverage area.
To achieve true seamless connectivity, the wireless LAN must incor porate a
number of different functions. Each node and access point, for example, must
always acknowledge receipt of each message. Each node must maintain contact
with the wireless network even when not actually transmitting data. Achieving
these functions simultaneously requires a dynamic RF networking technology
that links access points and nodes. In such a system, the user’s end node undertakes a search for the best possible access to the system. First, it evaluates such
factors as signal strength and quality, as well as the message load currently
being carried by each access point and the distance of each access point to the
wired backbone. Based on that information, the node next selects the right
access point and registers its address. Communications between end node and
host computer can then be transmitted up and down the backbone.
Wireless-G Notebook Adapter
31
Instant Wireless®Series
30
Page 12

Appendix B:Glossary
802.11b - One of the IEEE standards for wireless networking hardware.
Products that adhere to a specific IEEE standard will work with each other,
even if they are manufactured by different companies. The 802.11b standard
specifies a maximum data transfer rate of 11Mbps, an operating frequency of
2.4GHz, and WEP encryption for security. 802.11b networks are also referred
to as Wi-Fi networks.
802.11g - Refers to the proposed extension of the IEEE 802.11 standard for
wireless networking, which has not been ratified by IEEE. The draft 802.11g
specifications used by Linksys specifies a maximum data transfer rate of
54Mbps using OFDM modulation, an operating frequency of 2.4GHz, backward compatibility with IEEE 802.11b devices and WEP encryption for security.
Ad-hoc Network - An ad-hoc network is a group of computers, each with a
wireless adapter, connected as an independent 802.11 wireless LAN. Ad-hoc
wireless computers operate on a peer-to-peer basis, communicating directly
with each other without the use of an access point. Ad-hoc mode is also
referred to as an Independent Basic Service Set (IBSS) or as peer-to-peer
mode, and is useful at a departmental scale or SOHO operation.
CTS (Clear To Send) - An RS-232 signal sent from the receiving station to the
transmitting station that indicates it is ready to accept data.
Default Gateway - The router used to forward all traffic that is not addressed
to a station within the local subnet.
DHCP (Dynamic Host Configuration Protocol) - A protocol that lets network
administrators manage centrally and automate the assignment of Internet
Protocol (IP) addresses in an organization’s network. Using the Internet’s set of
protocol (TCP/IP), each machine that can connect to the Internet needs a
unique IP address. When an organization sets up its computer users with a connection to the Internet, an IP address must be assigned to each machine.
Without DHCP, the IP address must be entered manually at each computer and,
if computers move to another location in another part of the network, a new IP
address must be entered. DHCP lets a network administrator supervise and distribute IP addresses from a central point and automatically sends a new IP
address when a computer is plugged into a different place in the network.
Would the information be intercepted while transmitting on air?
WLAN features two-fold protection in security. On the hardware side, as with
Direct Sequence Spread Spectrum technology, it has the inherent security feature of scrambling. On the software side, WLAN offers the encryption function
(WEP) to enhance security and access control.
What is WEP?
WEP is Wired Equivalent Privacy, a data privacy mechanism based on a 64-bit
or 128-bit shared key algorithm, as described in the IEEE 802.11 standard.
Wireless-G Notebook Adapter
33
Instant Wireless®Series
32
Page 13

international standards. The organization publishes a number of journals, has
many local chapters, and several large societies in special areas, such as the
IEEE Computer Society.
Infrastructure Network - An infrastructure network is a group of computers
or other devices, each with a wireless adapter, connected as an 802.11 wireless
LAN. In infrastructure mode, the wireless devices communicate with each
other and to a wired network by first going through an access point. An infrastructure wireless network connected to a wired network is referred to as a
Basic Service Set (BSS). A set of two or more BSS in a single network is
referred to as an Extended Service Set (ESS). Infrastr ucture mode is useful at
a corporation scale, or when it is necessary to connect the wired and wireless
networks.
IP Address - In the most widely installed level of the Internet Protocol (IP)
today, an IP address is a 32-binary digit number that identifies each sender or
receiver of information that is sent in packet across the Internet. When you
request an HTML page or send e-mail, the Internet Protocol part of TCP/IP
includes your IP address in the message (actually, in each of the packets if more
than one is required) and sends it to the IP address that is obtained by looking
up the domain name in the Uniform Resource Locator you requested or in the
e-mail address you're sending a note to. At the other end, the recipient can see
the IP address of the Web page requester or the e-mail sender and can respond
by sending another message using the IP address it received.
IPCONFIG - A utility that provides for querying, defining and managing IP
addresses within a network. A commonly used utility, under Windows NT and
2000, for configuring networks with static IP addresses.
ISP - An ISP (Internet service provider) is a company that pro vides individuals
and companies access to the Internet and other related services such as W eb site
building and virtual hosting.
LAN - A local area network (LAN) is a group of computers and associated
devices that share a common communications line and typically share the
resources of a single processor or server within a small geographic area (for
example, within an office building).
MAC Address - The MAC (Media Access Control) address is your computer’s
unique hardware number.
DHCP uses the concept of a “lease” or amount of time that a given IP address
will be valid for a computer. The lease time can vary depending on how long a
user is likely to require the Internet connection at a particular location. It’s especially useful in education and other environments where users change frequently. Using very short leases, DHCP can dynamically reconfigure networks
in which there are more computers than there are available IP addresses.
DHCP supports static addresses for computers containing Web servers that
need a permanent IP address.
DNS - The domain name system (DNS) is the way that Internet domain name
are located and translated into Internet Protocol (IP) addresses. A domain name
is a meaningful and easy-to-remember “handle” for an Internet address.
DSSS (Direct-Sequence Spread Spectr um) - DSSS generates a redundant bit
pattern for all transmitted data. This bit pattern is called a chip (or chipping
code). Even if one or more bits in the chip are damaged during transmission,
statistical techniques embedded in the receiver can recover the original data
without the need for retransmission. To an unintended receiver, DSSS appears
as low power wideband noise and is rejected (ignored) by most narrowband
receivers. However, to an intended receiver (i.e. another wireless LAN endpoint), the DSSS signal is recognized as the only valid signal, and interference
is inherently rejected (ignored).
Dynamic IP Address - An IP address that is automatically assigned to a client
station in a TCP/IP network, typically by a DHCP server. Network devices that
serve multiple users, such as servers and printers, are usually assigned static IP
addresses.
ESS (Extended Service Set) - A set of more than two or more BSSs (multiple
access points) forming a single network.
Firmware - Code that is written onto read-only memory (ROM) or programmable read-only memory (PROM). Once firmware has been written onto the
ROM or PROM, it is retained even when the device is turned off.
IEEE - The Institute of Electrical and Electronics Engineers. The IEEE
describes itself as “the world’s largest technical professional society—promoting the development and application of electrotechnology and allied sciences
for the benefit of humanity, the advancement of the profession, and the wellbeing of our members.”
The IEEE fosters the development of standards that often become national and
Wireless-G Notebook Adapter
35
Instant Wireless®Series
34
Page 14

Subnet Mask - The method used for splitting IP networks into a series of subgroups, or subnets. The mask is a binary pattern that is matched up with the IP
address to turn part of the host ID address field into a f ield for subnets.
TCP (Transmission Control Protocol) - A method (protocol) used along with
the IP (Internet Protocol) to send data in the form of message units (datagram)
between netw ork devices ov er a LAN or WAN. While IP takes care of handling
the actual delivery of the data (routing), TCP takes care of keeping track of the
individual units of data (called packets) that a message is divided into for efficient delivery over the network. TCP is known as a "connection oriented" protocol due to requiring the receiver of a packet to return an acknowledgment of
receipt to the sender of the packet resulting in transmission control.
TCP/IP (Transmission Control Protocol/Internet Protocol) - The basic com-
munication language or set of protocols for communications over a network
(developed specifically for the Internet). TCP/IP defines a suite or group of
protocols and not only TCP and IP.
UDP (User Datagram Protocol) - A method (protocol) used along with the IP
(Internet Protocol) to send data in the form of message units (datagram)
between netw ork devices ov er a LAN or WAN. While IP takes care of handling
the actual delivery of the data (routing), UDP takes care of keeping track of the
individual units of data (called packets) that a message is divided into for efficient delivery over the network. UDP is known as a “connection-less” protocol
due to NOT requiring the receiver of a packet to return an acknowledgment of
receipt to the sender of the packet (as opposed to TCP).
WEP (Wired Equivalent Privacy) - A data privacy mechanism based on a 64-
bit shared key algorithm, as described in the IEEE 802.11b standard.
WINIPCFG - Conf iguration utility based on the Win32 API for querying,
defining and managing IP addresses within a network. A commonly used utility under Windows 95, 98SE, and Me.
WLAN (Wireless Local Area Network) - A group of computers and associated devices that communicate with each other wirelessly.
mIRC - mIRC runs under Windows and provides a graphical interface for logging onto IRC servers and listing, joining and leaving channels.
Network Mask - also known as the “Subnet Mask.”
OFDM - Developed for wireless applications, Orthogonal Frequency Division
Multiplexing (OFDM) technology offers superior performance-increased data
rates and more reliable transmissions-than previous technologies, such as
DSSS. OFDM is a scheme in which numerous signals of different frequencies
are combined to form a single signal for transmission on the medium.
OFDM works by breaking one high-speed data stream into a number of lowerspeed data streams, which are then transmitted in parallel. Each lower speed
stream is used to modulate a subcarrier. Essentially, this creates a multi-carrier
transmission by dividing a wide frequency band or channel into a number of
narrower frequency bands or sub-channels. OFDM is also used for other applications, including powerline networking.
Plug-and-Play - The ability of a computer system to configure expansion
boards and other devices automatically without requiring the user to turn off
the system during installation.
Roaming - In an infrastructure mode wireless network, this refers to the ability to move out of one access point's range and into another and transparently
reassociate and reauthenticate to the new access point. This reassociation and
reauthentication should occur without user intervention and ideally without
interruption to network connectivity. A typical scenario would be a location
with multiple access points, where users can physically relocate from one area
to another and easily maintain connectivity.
SSID (Service Set Identifier) - An identification name that wireless devices
use to make connections. In order for wireless devices to communicate, they
must all be set to the same channel and they all must use the same SSID. For
instance, if you are using an access point to connect two computers using wireless devices, the access point and each of the wireless devices must use the
same SSID. Even if they are set to the same channel, they cannot communicate
unless the SSID is the same.
Static IP Address - A permanent IP address that is assigned to a node in a
TCP/IP network.
Wireless-G Notebook Adapter
37
Instant Wireless®Series
36
Page 15

Appendix C:Specifications
Standards: IEEE 802.11b,IEEE draft 802.11g
Modulations: 802.11b: CCK (11 Mbps), DQPSK (2 Mbps),
DBPSK (1 Mbps); 802.11g: OFDM
Channels:
802.11b, 11 Channels (USA)
draft 802.11g 13 Channels (Europe)
14 Channels (Japan)
PCMCIA: CardBus
RF Outpur power 20dBm
LEDs: Power,Link
WEP Key Bits: 64-Bit and 128-Bit
Wireless-G Notebook Adapter
Dimensions: 4.53" x 2.13" x 0.30"
(115 mm x 54 mm x 7.5 mm)
Unit Weight: 1.66 oz. (0.047 kg)
Power: 3.3V Bus powered
Certifications: FCC,CE
Operating Temp.: 32ºF to 185ºF (0ºC to 85ºC)
Storage Temp.: 40ºF to 194ºF (-40ºC to 90ºC)
Operating Humidity: 5% to 95%, Non-Condensing
Storage Humidity: 5% to 95%, Non-Condensing
39
Instant Wireless®Series
38
Environmental
Page 16

Appendix E:Contact Information
For help with the installation or operation of the Wireless-G Notebook Adapter,
contact Linksys Technical Support at one of the phone numbers or Internet
addresses below.
Sales Information 800-546-5797 (LINKSYS)
Technical Support 800-326-7114
RMA (Return Merchandise
Authorization) Issues www.linksys.com (or call 949-271-5461)
Fax 949-265-6655
E-mail support@linksys.com
Web http://www.linksys.com
FTP Site ftp.linksys.com
Appendix D:Warranty Information
BE SURE TO HAVE YOUR PROOF OF PURCHASE AND A BARCODE
FROM THE PRODUCT’S PACKAGING ON HAND WHEN CALLING.
RETURN REQUESTS CANNOT BE PROCESSED WITHOUT PROOF OF
PURCHASE.
IN NO EVENT SHALL LINKSYS’LIABILITY EXCEED THE PRICE PAID
FOR THE PRODUCT FROM DIRECT, INDIRECT, SPECIAL, INCIDENTAL, OR CONSEQUENTIAL DAMAGES RESULTING FROM THE USE
OF THE PRODUCT, ITS ACCOMPANYING SOFTWARE, OR ITS DOCUMENTATION. LINKSYS DOES NOT OFFER REFUNDS FOR ANY PRODUCT.
LINKSYS OFFERS CROSS SHIPMENTS, A FASTER PROCESS FOR PROCESSING AND RECEIVING YOUR REPLACEMENT. LINKSYS PAYS
FOR UPS GROUND ONLY. ALL CUSTOMERS LOCATED OUTSIDE OF
THE UNITED STATES OF AMERICA AND CANADA SHALL BE HELD
RESPONSIBLE FOR SHIPPING AND HANDLING CHARGES. PLEASE
CALL LINKSYS FOR MORE DETAILS.
Wireless-G Notebook Adapter
41
Instant Wireless®Series
40
Page 17

© Copyright 2003 Linksys,All Rights Reserved.
http://www.linksys.com
 Loading...
Loading...