Page 1

Model No.
HP200
User Guide
WIRELESS
GHz
802.11g
2,4
PC Card
Home Wireless-G
Page 2
Home Wireless-G PC Card
Copyright and Trademarks
Specifications are subject to change without notice. Linksys is a registered trademark or trademark of Cisco
Systems, Inc. and/or its affiliates in the U.S. and certain other countries. Copyright © 2005 Cisco Systems, Inc . All
rights reserved. Other brands and product names are trademarks or registered trademarks of their respective
holders.
How to Use this User Guide
This user guide has been designed to make understanding networking with the Home Wireless-G PC Card easier
than ever. Look for the following items when reading this User Guide:
In addition to these symbols, there are definitions for technical terms that are presented like this:
Also, each figure (diagram, screenshot, or other image) is provided with a figure number and description, like
this:
Figure numbers and descriptions can also be found in the “List of Figures” section.
This exclamation point means there is a caution or warning and is
something that could damage your property or the PC Card.
word: definition.
This checkmark means there is a note of interest and is something you
should pay special attention to while using the PC Card.
This question mark provides you with a reminder about something
you might need to do while using the PC Card.
Figure 0-1: Sample Figure Description
HP200-UG-50322A JL
Page 3

Home Wireless-G PC Card
Table of Contents
Chapter 1: Introduction 1
Welcome 1
What’s in this User Guide? 1
Chapter 2: Planning your Wireless Network 3
Network Topology 3
Roaming 3
Network Layout 4
Chapter 3: Getting to Know the Home Wireless-G PC Card 5
The LED Indicators 5
Chapter 4: Setting up the Home Wireless-G PC Card 6
Using the Setup Wizard 6
Chapter 5: Inserting the Home Wireless-G PC Card 11
Connecting the PC Card 11
Chapter 6: Using the Wireless Network Monitor 12
Using the Wireless Network Monitor Icon 12
Link Information 12
Site Survey 15
Profiles 16
Creating a New Profile 17
Appendix A: Troubleshooting 28
Common Problems and Solutions 28
Frequently Asked Questions 29
Appendix B: Wireless Security 32
Security Precautions 32
Security Threats Facing Wireless Networks 32
Appendix C: Windows Help 35
Appendix D: Glossary 36
Appendix E: Specifications 40
Appendix F: Warranty Information 41
Appendix G: Regulatory Information 42
Appendix H: Contact Information 48
Page 4

Home Wireless-G PC Card
List of Figures
Figure 3-1: Front Panel 5
Figure 4-1: Setup Wizard’s Welcome Screen 6
Figure 4-2: Setup Wizard’s License Agreement 6
Figure 4-3: Setup Wizard’s Wireless Mode Screen 7
Figure 4-4: Setup Wizard’s Ad-Hoc Mode Settings Screen 7
Figure 4-5: Setup Wizard’s Wireless Security Screen 8
Figure 4-6: Setup Wizard’s Wireless Security - WEP Screen 8
Figure 4-7: Setup Wizard’s Wireless Security - WPA Personal Using TKIP Screen 9
Figure 4-8: Setup Wizard’s Check Settings Screen 9
Figure 4-9: Setup Wizard’s Congratulations Screen 10
Figure 5-1: Inserting the PC Card 11
Figure 6-1: Wireless Network Monitor Icon 12
Figure 6-2: Link Information 12
Figure 6-3: More Information - Wireless Network Status 13
Figure 6-4: More Information-Network Statistics 14
Figure 6-5: Site Survey 15
Figure 6-6: WEP Key Needed for Connection 15
Figure 6-7: PSK (Pre-Shared Key) Needed for Connection 15
Figure 6-8: Profiles 16
Figure 6-9: Import a Profile 16
Figure 6-10: Export a Profile 16
Figure 6-11: Create a New Profile 17
Figure 6-12: Enter Profile Name 17
Figure 6-13: Wireless Mode for New Profile 17
Figure 6-14: Ad-Hoc Mode Settings for New Profile 18
Figure 6-15: Network Settings for New Profile 18
Figure 6-16: Wireless Security for New Profile 19
Figure 6-17: Wireless Security - WEP for New Profile 19
Figure 6-18: Wireless Security - WPA Personal for New Profile 20
Figure 6-19: Wireless Security - WPA Personal Settings 20
Page 5
Home Wireless-G PC Card
Figure 6-20: Wireless Security - WPA Enterprise for New Profile 21
Figure 6-21: Wireless Security - WPA Enterprise (Encryption) 21
Figure 6-22: Wireless Security - WPA Enterprise Using EAP-TLS Settings 22
Figure 6-23: Wireless Security - WPA Enterprise Using EAP-TTLS Settings 22
Figure 6-24: Wireless Security - WPA Enterprise Using EAP-PEAP Settings 23
Figure 6-25: Wireless Security - WPA Enterprise Using LEAP Settings 23
Figure 6-26: Wireless Security - RADIUS for New Profile 24
Figure 6-27: Wireless Security - RADIUS Using EAP-TLS Settings 24
Figure 6-28: Wireless Security - RADIUS Using EAP-TTLS Settings 25
Figure 6-29: Wireless Security - RADIUS Using EAP-PEAP Settings 25
Figure 6-30: Wireless Security - RADIUS Using LEAP Settings 26
Figure 6-31: Confirm New Settings for New Profile 26
Figure 6-32: Congratulations for New Profile 27
Page 6

1
Chapter 1: Introduction
Welcome
Home Wireless-G PC Card
Chapter 1: Introduction
Welcome
Thank you for choosing the Home Wireless-G PC Card. With this PC Card, your wireless networking experience
will be faster and easier than ever.
How does the PC Card do this? Like all wireless products, the PC Card allows for greater range and mobility
within your wireless network, whether it’s using the Wireless-G (802.11g) or Wireless-B (802.11b) standard.
But what does all of this mean?
Networks are useful tools for sharing computer resources. You can access one printer from different computers
and access data located on another computer's hard drive. Networks are even used for playing multiplayer video
games. So, networks are not only useful in homes and offices, they can also be fun.
PCs equipped with wireless cards and adapters can communicate without cumbersome cables. By sharing the
same wireless settings, within their transmission radius, they form a wireless network.
The included Setup Wizard walks you through configuring the PC Card to your wireless network settings, step by
step. Use the instructions in this Guide to help you set up and connect the PC Card using the Setup Wizard. These
instructions should be all you need to get the most out of the PC Card.
What’s in this User Guide?
This user guide covers the steps for setting up and using the Home Wireless-G PC Card.
• Chapter 1: Introduction
This chapter describes the PC Card’s applications and this User Guide.
• Chapter 2: Planning Your Wireless Network
This chapter discusses a few of the basics about wireless networking.
• Chapter 3: Getting to Know the Home Wireless-G PC Card
This chapter describes the physical features of the PC Card.
• Chapter 4: Setting up the Home Wireless-G PC Card
This chapter instructs you on how to install the PC Card’s Setup Wizard and configure the PC Card.
802.11b: a wireless networking standard that
specifies a maximum data transfer rate of 11Mbps
and an operating frequency of 2.4GHz.
adapter: a device that adds network functionality
to your PC.
network: a series of computers or devices
connected for the purpose of data sharing,
storage, and/or transmission between users.
802.11g: a wireless networking standard that
specifies a maximum data transfer rate of 54Mbps
and an operating frequency of 2.4GHz.
Page 7

2
Chapter 1: Introduction
What’s in this User Guide?
Home Wireless-G PC Card
• Chapter 5: Inserting the Home Wireless-G PC Card
This chapter shows you how to insert the PC Card into your PC.
• Chapter 6: Using the Wireless Network Monitor
This chapter show you how to use the PC Card’s Wireless Network Monitor.
• Appendix A: Troubleshooting
This appendix describes some potential problems and solutions, as well as frequently asked questions,
regarding installation and use of the PC Card.
• Appendix B: Wireless Security
This appendix discusses security issues regarding wireless networking and measures you can take to help
protect your wireless network.
• Appendix C: Windows Help
This appendix describes how you can use Windows Help for instructions about networking, such as installing
the TCP/IP protocol.
• Appendix D: Glossary
This appendix gives a brief glossary of terms frequently used in networking.
• Appendix E: Specifications
This appendix provides the PC Card’s technical specifications.
• Appendix F: Warranty Information
This appendix supplies the PC Card’s warranty information.
• Appendix G: Regulatory Information
This appendix supplies the PC Card’s regulatory information.
• Appendix H: Contact Information
This appendix provides contact information for a variety of Linksys resources, including Technical Support.
Page 8

3
Chapter 2: Planning your Wireless Network
Network Topology
Home Wireless-G PC Card
Chapter 2: Planning your Wireless Network
Network Topology
A wireless network is a group of computers, each equipped with one wireless adapter. Computers in a wireless
network must be configured to share the same radio channel. Several PCs equipped with wireless cards or
adapters can communicate with one another to form an ad-hoc network.
Linksys wireless adapters also provide users access to a wired network when using an access point or wireless
router. An integrated wireless and wired network is called an infrastructure network. Each wireless PC in an
infrastructure network can talk to any computer in a wired network infrastructure via the access point or wireless
router.
An infrastructure configuration extends the accessibility of a wireless PC to a wired network, and can double the
effective wireless transmission range for two wireless adapter PCs. Since an access point is able to forward data
within a network, the effective transmission range in an infrastructure network can be doubled.
Roaming
Infrastructure mode also supports roaming capabilities for mobile users. Roaming means that you can move your
wireless PC within your network and the access points will pick up the wireless PC's signal, provided that they
both share the same channel and SSID.
Choose a feasible radio channel and optimum access point position. Proper access point positioning combined
with a clear radio signal will greatly enhance performance.
infrastructure: a wireless network that is
bridged to a wired network via an access point.
ad-hoc: a group of wireless devices
communicating directly with each other (peerto-peer) without the use of an access point.
roaming: the ability to take a wireless device
from one access point's range to another without
losing the connection.
ssid: your wireless network's name.
topology: the physical layout of a network.
Page 9

4
Chapter 2: Planning your Wireless Network
Network Layout
Home Wireless-G PC Card
Network Layout
Linksys wireless access points and wireless routers have been designed for use with 802.11b and 802.11g
products. Products using the 802.11g and 802.11b standards can communicate with each other.
Access points and wireless routers are compatible with 802.11b and 802.11g adapters, such as the notebook
adapters for your laptop computers, PCI adapters for your desktop PCs, and USB adapters for when you want to
enjoy USB connectivity. Wireless products will also communicate with a wireless print server.
When you wish to connect your wireless network to your wired network, network ports on access points and
wireless routers can be connected to any of Linksys's switches or routers.
With these, and many other, Linksys products, your networking options are limitless. Go to the Linksys website at
www.linksys.com/international for more information about wireless products.
Page 10

5
Chapter 3: Getting to Know the Home Wireless-G PC Card
The LED Indicators
Home Wireless-G PC Card
Chapter 3: Getting to Know the Home Wireless-G PC Card
The LED Indicators
The PC Card's LEDs display information about network activity.
Power Green. The Power LED lights up when the PC Card is powered on.
Link Green. The Link LED lights up when the PC Card has an active connection.
Figure 3-1: Front Panel
Page 11
6
Chapter 4: Setting up the Home Wireless-G PC Card
Using the Setup Wizard
Home Wireless-G PC Card
Chapter 4: Setting up the Home Wireless-G PC Card
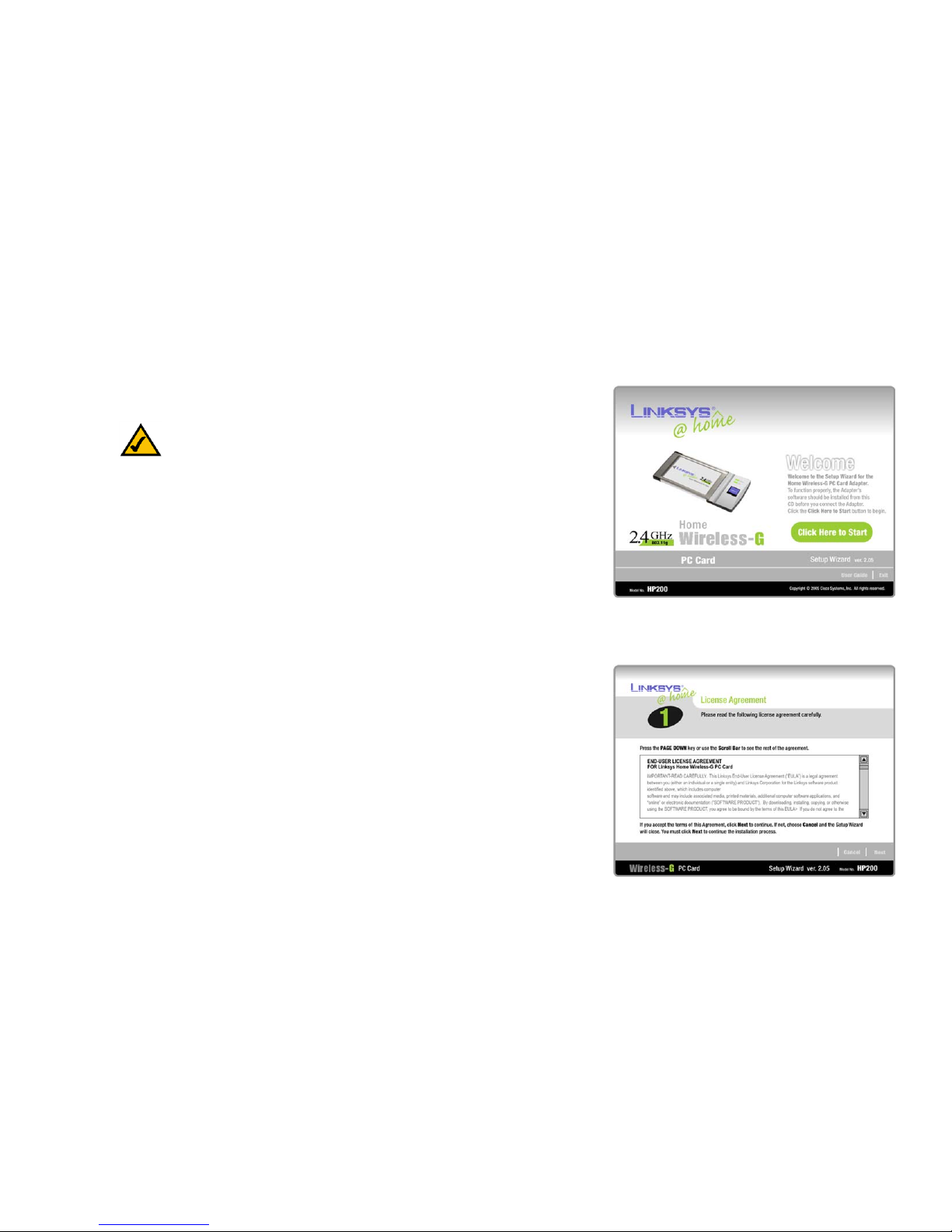
The Home Wireless-G PC Card Setup Wizard will guide you through the installation procedure. The Setup Wizard
will install the driver and Wireless Network Monitor, as well as configure the PC Card.
Using the Setup Wizard
Insert the Setup Wizard CD-ROM into your CD-ROM drive. The Setup Wizard should run automatically, and the
Welcome screen should appear. If it does not, click the Start button and choose Run. In the field that appears,
enter D:\setup.exe (if “D” is the letter of your CD-ROM drive).
On the Welcome screen, you have the following choices:
Click Here to Start - Click the Click Here to Start button to begin the software installation process.
User Guide - Click the User Guide button to open the PDF file of this User Guide.
Exit - Click the Exit button to exit the Setup Wizard.
1. To install the PC Card, click the Click Here to Start button on the Welcome screen.
2. After reading the License Agreement, click the Next button if you agree, or click the Cancel button to end the
installation.
Figure 4-1: Setup Wizard’s Welcome Screen
Figure 4-2: Setup Wizard’s License Agreement
NOTE: You must run the Setup Wizard before inserting the PC Card
into your computer.
Page 12
7
Chapter 4: Setting up the Home Wireless-G PC Card
Using the Setup Wizard
Home Wireless-G PC Card
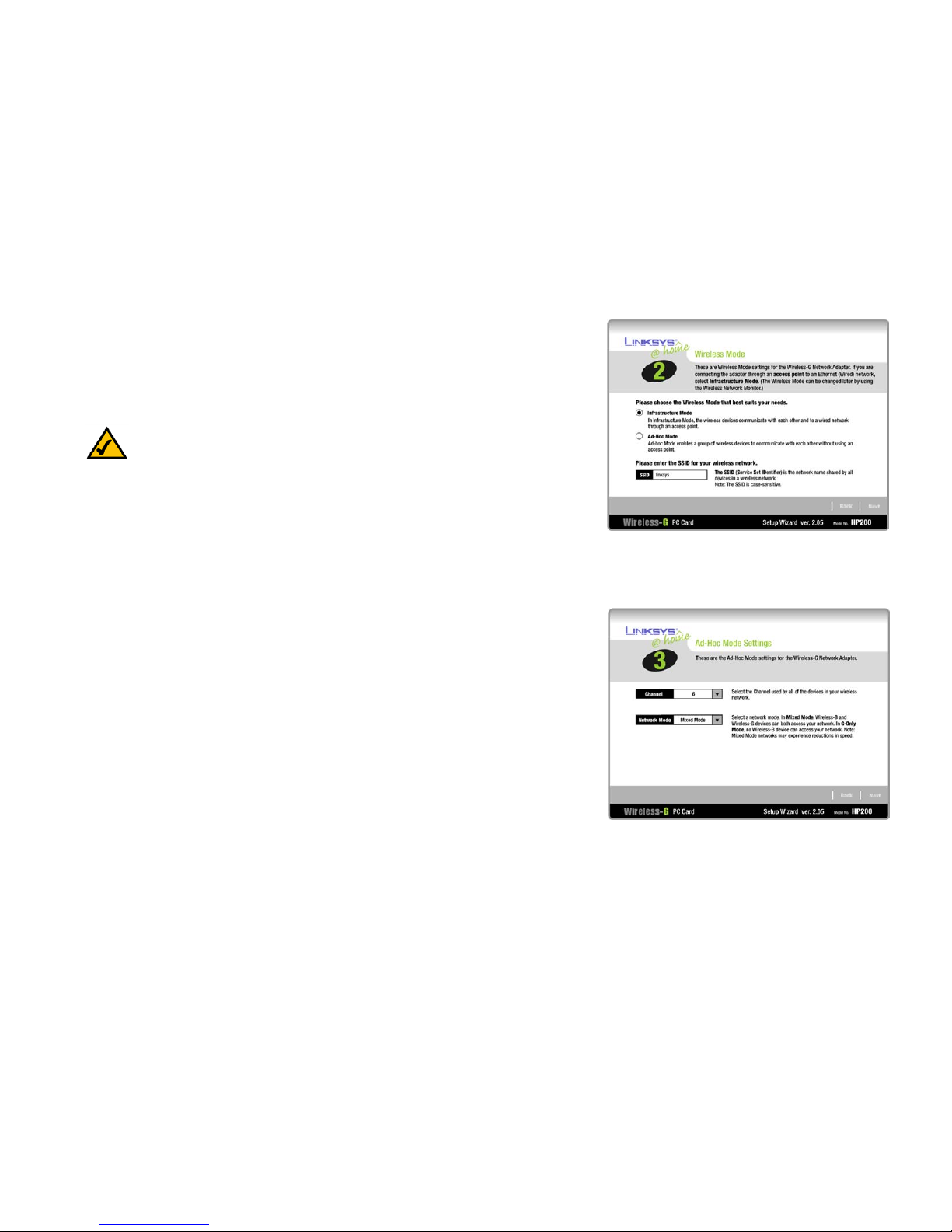
3. The Setup Wizard will ask you to choose a network mode. Click the Infrastructure Mode radio button if you
want to connect to a wireless router or access point. Click the Ad-Hoc Mode radio button if you want to
connect directly to another wireless device without using a wireless router or access point.
In the SSID field, enter the SSID or name of your wireless network. The SSID must be identical for all devices
in the network. The default setting is linksys (all lowercase). Click the Next button.
4. If you chose Infrastructure Mode, go to Step 5 now. If you chose Ad-Hoc Mode , select the correct operating
channel for your network. Then, select the Network Mode from the drop-down menu. Click the Next button,
and go to Step 5. Click the Back button to change any settings.
Channel - The channel you choose should match the channel set on the other devices in your wireless
network. If you are unsure about which channel to use, keep the default channel.
Network Mode - Select Mixed Mode if you want to allow Wireless-G and Wireless-B computers on the
network, even though network speeds will be reduced. For maximum speed, select G-Only Mode; however,
no Wireless-B users will be allowed on the network.
Figure 4-3: Setup Wizard’s Wireless Mode Screen
NOTE: Network SSIDs should be unique to your network and identical for all
devices within the network.
Figure 4-4: Setup Wizard’s Ad-Hoc Mode Settings Screen
Page 13

8
Chapter 4: Setting up the Home Wireless-G PC Card
Using the Setup Wizard
Home Wireless-G PC Card
5. If you don’t want to use encryption, select Disabled and then click the Next button to continue. Proceed to
Step 7.
Select the method of security you want to use: WEP or WPA Personal. WEP stands for Wired Equivalent
Privacy, and WPA stands for Wi-Fi Protected Access.
Click the Next button to continue or the Back button to return to the previous screen.
6. Proceed to the appropriate section for your security method: WEP or WPA Personal.
WEP
WEP - Select 64-bit or 128-bit encryption from the drop-down menu, and enter a passphrase or WEP key.
Passphrase - Enter a passphrase in the Passphrase field, so a WEP key is automatically generated. It is case-
sensitive and should not be longer than 16 alphanumeric characters. This passphrase must match the
passphrase of your other wireless network devices and is compatible with Linksys wireless products only. (If
you have any non-Linksys wireless products, enter the WEP key manually on those products.)
WEP Key - The WEP key you enter must match the WEP key of your wireless network. For 64-bit encryption,
enter exactly 10 hexadecimal characters. For 128-bit encryption, enter exactly 26 hexadecimal characters.
Valid hexadecimal characters are “0” to “9” and “A” to “F”.
Advanced Users
TX Key - The default transmit key number is 1. If your network’s access point or wireless router uses transmit
key number 2, 3, or 4, select the appropriate number from the TX Key drop-down box.
Authentication -The default is set to Auto, so it will auto-detect for Shared Key or Open System
authentication. For Shared Key authentication, both the sender and the recipient share a WEP key for
authentication. For Open System authentication, the sender and the recipient do not share a WEP key for
authentication. If you are not sure which authentication method to select, keep the default, Auto.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 4-5: Setup Wizard’s Wireless Security Screen
Figure 4-6: Setup Wizard’s Wireless Security -
WEP Screen
encryption: encoding data transmitted in a network.
wep (wired equivalent privacy): a method of encrypting
network data transmitted on a wireless network for greater
security.
wpa (wi-fi protected access: a wireless security protocol
using TKIP (Temporal Key Integrity Protocol) encryption,
which can be used in conjunction with a RADIUS server.
Page 14

9
Chapter 4: Setting up the Home Wireless-G PC Card
Using the Setup Wizard
Home Wireless-G PC Card
WPA Personal
WPA Personal offers two encryption methods, TKIP and AES, with dynamic encryption keys. Select the type of
algorithm, TKIP or AES, used for encryption. Then enter a Passphrase that is 8-63 characters in length.
Encryption - Select the type of algorithm you want to use, TKIP or AES, for the Encryption setting.
Passphrase - Enter a Passphrase, also called a Pre-Shared Key, of 8-63 characters in the Passphrase field.
The longer and more complex your Passphrase is, the more secure your network will be.
Click the Next button to continue. Click the Back button to return to the previous screen.
7. The Setup Wizard will ask you to review your settings before it starts to install files. Click the Next button if
you are satisfied with your settings, or click the Back button to change any settings.
Figure 4-7: Setup Wizard’s Wireless Security -
WPA Personal Using TKIP Screen
Figure 4-8: Setup Wizard’s Check Settings Screen
Page 15

10
Chapter 4: Setting up the Home Wireless-G PC Card
Using the Setup Wizard
Home Wireless-G PC Card
8. After the software has been successfully installed, the Congratulations screen will appear. Click the Exit
button to exit the Setup Wizard, or click the Online Registration button to register the PC Card.
Proceed to “Chapter 5: Inserting the Home Wireless-G PC Card.”
Figure 4-9: Setup Wizard’s Congratulations Screen
Page 16

11
Chapter 5: Inserting the Home Wireless-G PC Card
Connecting the PC Card
Home Wireless-G PC Card
Chapter 5: Inserting the Home Wireless-G PC Card
Connecting the PC Card
1. Power down your notebook PC.
2. Locate an available CardBus slot on your notebook PC.
3. With the connector pin end facing the CardBus slot and the label facing up, slide the PC Card into the CardBus
slot until it locks in place.
4. Restart your notebook PC. The Power LED should light up when the PC Card is installed correctly.
5. Windows will begin copying the driver files to your computer. If Windows asks you for the original Windows
CD-ROM, insert the CD-ROM, and direct Windows to its correct location (e.g., D:\).
The installation of the Home Wireless-G PC Card is complete.
If you want to check the link information, search for available wireless networks, or make additional
configuration changes, go to “Chapter 6: Using the Wireless Network Monitor.”
Figure 5-1: Inserting the PC Card
NOTE: You must run the Setup Wizard to install the software before installing the hardware.
Page 17

12
Chapter 6: Using the Wireless Network Monitor
Using the Wireless Network Monitor Icon
Home Wireless-G PC Card
Chapter 6: Using the Wireless Network Monitor
Use the Wireless Network Monitor to check the link information, search for available wireless networks, or create
profiles that hold different configuration settings.
Using the Wireless Network Monitor Icon
After installing the PC Card, the Home Wireless-G PC Card Wireless Monitor icon will appear in your system tray. If
the Wireless Network Monitor is enabled, then the icon will be green. If the Wireless Network Monitor is disabled
or the PC Card is not connected, then the icon will be gray.
Double-click the Wireless Network Monitor icon to activate the Wireless Network Monitor. Then the Link
Information screen will appear. From this screen, you can find out how strong the current wireless signal is and
how good the connection’s quality is. You can also click the Mo re Information button to view additional status
information about the current wireless connection. To search for available wireless networks, click the Site
Survey tab. To perform configuration changes, click the Profiles tab.
Link Information
The Link Information screen displays network mode, signal strength, and link quality information about the
current connection. It also provides a button to click for additional status information.
Ad-Hoc Mode or Infrastructure Mode - The screen indicates whether the PC Card is currently working in adhoc or infrastructure mode.
Signal Strength - The Signal Strength bar indicates signal strength.
Link Quality - The Link Quality bar indicates the quality of the wireless network connection.
Click the More Information button to view additional information about the wireless network connection.
Clicking the More Information button displays the Wireless Network Status screen, which displays more
information about the PC Card’s connection.
Figure 6-1: Wireless Network Monitor Icon
Figure 6-2: Link Information
Page 18

13
Chapter 6: Using the Wireless Network Monitor
Link Information
Home Wireless-G PC Card
Wireless Network Status
The Wireless Network Status screen provides information on your current network settings.
Status - The status of the wireless network connection.
SSID - This is the unique name of the wireless network.
Wireless Mode - The mode of the wireless network currently in use is displayed here.
Transfer Rate - The data transfer rate of the current connection is shown here.
Channel - This is the channel to which the wireless network devices are set.
Security - The status of the wireless security feature is displayed here.
Authentication - This is your wireless network’s authentication method.
IP Address - The IP Address of the PC Card is displayed here.
Subnet Mask - The Subnet Mask of the PC Card is shown here.
Default Gateway - The Default Gateway address of the PC Card is displayed here.
DNS - This is the DNS address of the PC Card.
DHCP Client - This displays the PC Card’s status as a DHCP client.
MAC - The MAC address of the wireless network’s access point is shown here.
Signal Strength - The Signal Strength bar indicates the signal strength.
Link Quality - The Link Quality bar indicates the quality of the wireless network connection.
Click the Back button to return to the initial Link Information screen. Click the Statistics button to go to the
Wireless Network Statistics screen. Click the Save to Profile button to save the currently active connection
settings to a profile.
Figure 6-3: More Information - Wireless Network Status
Page 19

14
Chapter 6: Using the Wireless Network Monitor
Link Information
Home Wireless-G PC Card
Wireless Network Statistics
The Wireless Networks Statistics screen provides statistics on your current network settings.
Tran smit Rate - This is the data transfer rate of the current connection. (In Auto mode, the PC Card dynamically
shifts to the fastest data transfer rate possible at any given time.)
Receive Rate - This is the rate at which data is received.
Packets Received - This shows the packets received by the PC Card, in real time, since connecting to the
Wireless Network or since the Refresh Statistics button was last pressed.
Packets Transmitted - This shows the packets transmitted from the PC Card, in real time, since connecting to
the Wireless Network or since the Refresh Statistics button was last pressed.
Bytes Received - This shows the bytes received by the PC Card, in real time, since connecting to the Wireless
Network or since the Refresh Statistics button was last pressed.
Bytes Transmitted - This shows the bytes transmitted from the PC Card, in real time, since connecting to the
Wireless Network or since the Refresh Statistics button was last pressed.
Noise Level - This shows the level of background noise affecting the wireless signal. A lower reading translates
into a higher quality signal.
Signal Strength - This is the intensity of the wireless signal received by the PC Card.
Up Time - This indicates the length of the most recent connection to a wireless network.
Total Up Time - This indicates the cumulative total of the PC Card’s connection time.
Driver Version - This shows the version of the PC Card’s driver.
Signal Strength - The Signal Strength bar indicates the signal strength.
Link Quality - The Link Quality bar indicates the quality of the wireless network connection.
Click the Back button to return to the initial Link Information screen. Click the Status button to go to the Wireless
Network Status screen. Click the Save to Profile button to save the currently active connection settings to a
profile. Click the Refresh Statistics button to update or reset the statistics.
Figure 6-4: More Information-Network Statistics
Page 20

15
Chapter 6: Using the Wireless Network Monitor
Site Survey
Home Wireless-G PC Card
Site Survey
The Site Survey screen displays a list of infrastructure and ad-hoc networks available for connection in the table
on the left. This table shows the network’s SSID, Channel, and the quality of the wireless signal the PC Card is
receiving. You may click SSID, CH (Channel), or Signal, to sort by that field.
Site Information
For each network selected, the following settings are listed:
SSID - This the SSID or unique name of the wireless network.
Wireless Mode - This is the mode of the wireless network currently in use.
Channel - This is the channel to which the wireless network devices are set.
Security - The status of the wireless security feature is displayed here.
MAC - The MAC address of the wireless network’s access point is displayed here.
Refresh - Click the Refresh button to perform a new search for wireless devices.
Connect - To connect to one of the networks on the list, select the wireless network, and click the Connect
button. If the network has encryption enabled, then you will see a new screen appear.
From the Security drop-down menu, select the network’s encryption method, WEP or WPA Personal (PSK).
If you selected WEP, then you will see the WEP Key Needed for Connection screen. Select the appropriate level of
WEP encryption, 64-bit or 128-bit. Then enter the network’s Passphrase or WEP Key. Click the Connect button.
To cancel the connection, click the Cancel button.
If you selected WPA Personal (PSK), then you will see the WPA Personal or PSK (Pre-Shared Key) Needed for
Connection screen. Select the appropriate encryption type, TKIP or AES. Then enter the network’s Passphrase or
Pre-Shared Key in the Passphrase field. Then click the Connect button. To cancel the connection, click the
Cancel button.
Figure 6-5: Site Survey
Figure 6-6: WEP Key Needed for Connection
Figure 6-7: PSK (Pre-Shared Key) Needed
for Connection
Page 21

16
Chapter 6: Using the Wireless Network Monitor
Profiles
Home Wireless-G PC Card
Profiles
The Profiles screen lets you save different configuration profiles for different network setups. The table on the left
displays a list of infrastructure and ad-hoc networks available for connection. This table shows the network’s
profile name and the wireless network’s SSID, as set in the connection profile.
Profile Information
For each profile selected, the following are listed:
Wireless Mode - This is the mode of the wireless network currently in use.
Transfer Rate - The PC Card is set to Auto mode, so it will dynamically shift to the fastest data transfer rate
possible at any given time.
Channel - This is the channel to which the wireless network devices are set.
Security - The status of the wireless security feature is displayed here.
Authentication - The authentication setting for the network is shown here.
Connect - To connect to a wireless network using a specific profile, select the profile, and click the Connect
button.
New - Click the New button to create a new profile. See the next section, “Creating a New Profile,” for detailed
instructions.
Edit - Select a profile, and click the Edit button to change an existing profile.
Import - Click the Import button to import a profile that has been saved in another location. Select the
appropriate file, and click the Open button.
Export - Select the profile you want to save in a different location, and click the Export button. Direct Windows to
the appropriate folder, and click the OK button.
Delete - Click the Delete button to delete a profile.
Figure 6-9: Import a Profile
Figure 6-10: Export a Profile
Figure 6-8: Profiles
NOTE: If you want to export more than one profile, you have to export them one at a time.
Page 22

17
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
Creating a New Profile
1. On the Profiles screen, click the New button to create a new profile.
2. Enter a name for the new profile, and click the OK button. Click the Cancel button to return to the Profiles
screen without entering a name.
3. The Wireless Mode screen shows a choice of two wireless modes. Click the Infrastructure Mode radio
button if you want to connect to a wireless router or access point. Click the Ad-Hoc Mode radio button if you
want to connect directly to another wireless device without using a wireless router or access point. Then
enter the SSID or name of your network.
Click the Next button to continue or the Back button to return to the previous screen.
Infrastructure Mode - This mode allows wireless and wired networks to communicate through an access
point.
Ad-Hoc Mode - This mode allows wireless-equipped computers to communicate directly with each other. No
access point is used.
SSID - This is the network name. It must be used for all the devices in your wireless network. It is case-
sensitive and should be a unique name to help prevent others from entering your network.
Figure 6-11: Create a New Profile
Figure 6-12: Enter Profile Name
Figure 6-13: Wireless Mode for New Profile
Page 23

18
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
4. The Ad-Hoc Mode Settings screen will appear. If you chose Infrastructure Mode, go to Step 5 now. If you
chose Ad-Hoc Mode, select the correct operating channel for your network from the Channel drop-down
menu. Then, select the Network Mode from the drop-down menu. Click the Next button, and go to Step 5.
Click the Back button to change any settings.
Channel - The channel you choose should match the channel set on the other devices in your wireless
network. If you are unsure about which channel to use, keep the default channel.
Network Mode - Select Mixed Mode, and both Wireless-G and Wireless-B computers will be allowed on the
network, but the speed may be reduced. Select G-Only Mode for maximum speed, but no Wireless-B users
will be allowed on the network.
5. The Network Settings screen will appear. If your network has a router or other DHCP server, click the radio
button next to Obtain network settings automatically (DHCP). Click the Next button to continue, or click
the Cancel button to return to the Profiles screen.
If your network does not have a DHCP server, click the radio button next to Specify network settings. Enter
an IP Address, Subnet Mask, Default Gateway, and DNS address appropriate for your network. You must
specify the IP Address and Subnet Mask on this screen. If you are unsure about the Default Gateway and DNS
address, leave these fields empty. Click the Next button to continue, or click the Cancel button to return to
the Profiles screen.
IP Address - This IP Address must be unique to your network.
Subnet Mask - The PC Card’s Subnet Mask must be the same as your wired network’s Subnet Mask.
Default Gateway - Enter the IP address of your network’s Gateway here.
DNS 1 and DNS 2 - Enter the DNS address of your wired Ethernet network here.
Figure 6-14: Ad-Hoc Mode Settings for New Profile
Figure 6-15: Network Settings for New Profile
Page 24

19
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
6. If you don’t want to use encryption, select Disabled and then click the Next button to continue. Proceed to
Step 8.
Select the method of security you want to use: WEP, WPA Personal , WPA Enterprise, or RADIUS. WEP
stands for Wired Equivalent Privacy, and WPA stands for Wi-Fi Protected Access. RADIUS stands for Remote
Authentication Dial-In User Service.
Click the Next button to continue or the Back button to return to the previous screen.
7. Proceed to the appropriate section for your security method: WEP, WPA Personal, WPA Enterprise, or RADIUS.
WEP
WEP - Select 64-bit or 128-bit encryption from the drop-down menu, and enter a passphrase or WEP key.
Passphrase - Enter a passphrase in the Passphrase field, so a WEP key is automatically generated. It is case-
sensitive and should not be longer than 16 alphanumeric characters. This passphrase must match the
passphrase of your other wireless network devices and is compatible with Linksys wireless products only. (If
you have any non-Linksys wireless products, enter the WEP key manually on those products.)
WEP Key - The WEP key you enter must match the WEP key of your wireless network. For 64-bit encryption,
enter exactly 10 hexadecimal characters. For 128-bit encryption, enter exactly 26 hexadecimal characters.
Valid hexadecimal characters are “0” to “9” and “A” to “F”.
Advanced Users
TX Key - The default transmit key number is 1. If your network’s access point or wireless router uses transmit
key number 2, 3, or 4, select the appropriate number from the TX Key drop-down box.
Authentication -The default is set to Auto, so it will auto-detect for Shared Key or Open System
authentication. For Shared Key authentication, both the sender and the recipient share a WEP key for
authentication. For Open System authentication, the sender and the recipient do not share a WEP key for
authentication. If you are not sure which authentication method to select, keep the default, Auto.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-16: Wireless Security for New Profile
Figure 6-17: Wireless Security - WEP for New Profile
radius (remote authentication dial-in user service): a
protocol that uses an authentication server to control
network access.
Page 25

20
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
WPA Personal
WPA Personal offers two encryption methods, TKIP and AES, with dynamic encryption keys. Select the type of
algorithm, TKIP or AES, for encryption. Then enter a Passphrase that is 8-63 characters in length.
Encryption - Select the type of algorithm you want to use, TKIP or AES, for encryption.
Passphrase - Enter a Passphrase, also called a Pre-Shared Key, of 8-63 characters in the Passphrase field.
The longer and more complex your Passphrase is, the more secure your network will be.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-18: Wireless Security - WPA Personal for
New Profile
Figure 6-19: Wireless Security - WPA Personal Settings
Page 26

21
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
WPA Enterprise
WPA Enterprise features a Pre-Shared Key used in coordination with a RADIUS server. (This should only be
used when a RADIUS server is connected to the Router.) WPA Enterprise offers two encryption methods, TKIP
and AES, with dynamic encryption keys, as well as four authentication methods, EAP-TLS, EAP-TTLS, EAPPEAP, and LEAP.
Encryption - Select the type of encryption, TKIP or AES, from the Encryption drop-down menu.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-20: Wireless Security - WPA Enterprise for
New Profile
Figure 6-21: Wireless Security - WPA Enterprise
(Encryption)
Page 27

22
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
Authentication - Select the authentication method your network is using, EAP-TLS, EAP-TTLS, EAP-PEAP,
or LEAP. Then proceed to the appropriate instructions.
EAP-TLS
If you selected EAP-TLS, enter the login name of your wireless network in the Login Name field. From the
Certificate drop-down menu, select the certificate you have installed to authenticate you on your wireless
network.
Click the Next button to continue. Click the Back button to return to the previous screen.
EAP-TTLS
If you selected EAP-TTLS, enter the login name of your wireless network in the Login Name field. Enter the
password of your wireless network in the Password field. From the TTLS Protocol drop-down menu, select
the protocol you are using, PAP, CHAP, MS CHAP V2, or EAP.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-22: Wireless Security - WPA Enterprise Using
EAP-TLS Settings
Figure 6-23: Wireless Security - WPA Enterprise Using
EAP-TTLS Settings
Page 28

23
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
EAP-PEAP
If you selected EAP-PEAP, enter the login name of your wireless network in the Login Name field. Enter the
password of your wireless network in the Password field. From the Peap Inner Eap drop-down menu, select
the appropriate method, TOKEN CARD or MS Chap V2.
Click the Next button to continue. Click the Back button to return to the previous screen.
LEAP
If you selected LEAP, enter the login name of your wireless network in the Login Name field. Enter the
password of your wireless network in the Password field.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-24: Wireless Security - WPA Enterprise Using
EAP-PEAP Settings
Figure 6-25: Wireless Security - WPA Enterprise Using
LEAP Settings
Page 29

24
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
RADIUS
RADIUS features use of a RADIUS server . (This should only be used when a RADIUS s erver is connected to the
Router.) RADIUS offers four authentication methods: EAP-TLS, EAP-TTLS, PEAP, and LEAP.
Authentication - Select the authentication method your network is using, EAP-TLS, EAP-TTLS, EAP-PEAP,
or LEAP. Then proceed to the appropriate instructions.
EAP-TLS
If you selected EAP-TLS, enter the login name of your wireless network in the Login Name field. From the
Certificate drop-down menu, select the certificate you have installed to authenticate you on your wireless
network.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-26: Wireless Security - RADIUS for New Profile
Figure 6-27: Wireless Security - RADIUS Using
EAP-TLS Settings
Page 30

25
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
EAP-TTLS
If you selected EAP-TTLS, enter the login name of your wireless network in the Login Name field. Enter the
password of your wireless network in the Password field. From the TTLS Protocol drop-down menu, select
the protocol you are using, PAP, CHAP,
MS CHAP V2, or EAP.
Click the Next button to continue. Click the Back button to return to the previous screen.
EAP-PEAP
If you selected EAP-PEAP, enter the login name of your wireless network in the Login Name field. Enter the
password of your wireless network in the Password field. From the Certificate drop-down menu, select the
certificate you have installed to authenticate you on your wireless network. From the Peap Inner Eap dropdown menu, select the appropriate method, TOKEN CARD or MS Chap V2.
Click the Next button to continue. Click the Back button to return to the previous screen.
Figure 6-28: Wireless Security - RADIUS Using
EAP-TTLS Settings
Figure 6-29: Wireless Security - RADIUS Using
EAP-PEAP Settings
Page 31

26
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
LEAP
If you selected LEAP, enter the login name of your wireless network in the Login Name field. Enter the
password of your wireless network in the Password field.
Click the Next button to continue. Click the Back button to return to the previous screen.
8. The Confirm New Settings screen will appear next and show the new settings. To save the new settings, click
the Save button. To edit the new settings, click the Back button. To exit the Wireless Network Monitor, click
the Exit button.
Figure 6-30: Wireless Security - RADIUS Using
LEAP Settings
Figure 6-31: Confirm New Settings for New Profile
Page 32

27
Chapter 6: Using the Wireless Network Monitor
Creating a New Profile
Home Wireless-G PC Card
9. The Congratulations screen will appear next. Click Return to Profiles Screen to keep the current settings
active and return to the Profiles screen. Click Connect to Network to implement the new settings
immediately and return to the Link Information screen.
You have successfully created a connection profile.
Figure 6-32: Congratulations for New Profile
Page 33

28
Appendix A: Troubleshooting
Common Problems and Solutions
Home Wireless-G PC Card
Appendix A: Troubleshooting
This appendix consists of two parts: “Common Problems and Solutions” and “Frequently Asked Questions.” This
appendix provides solutions to problems that may occur during the installation and operation of the Home
Wireless-G PC Card. Read the description below to solve your problems. If you can't find an answer here, check
the Linksys website at www.linksys.com/international.
Common Problems and Solutions
1. My computer does not recognize the Home Wireless-G PC Card.
Make sure that the Home Wireless-G PC Card is properly inserted into the CardBus slot.
2. The Home Wireless-G PC Card does not work properly.
Reinsert the Home Wireless-G PC Card into the notebook or desktop’s USB port.
For Windows 98SE or Me, right-click on My Computer, and select Properties. Select the Device Manager
tab, and click on the Network Adapter. You will find the Home Wireless-G PC Card if it is installed
successfully. If you see a yello w exclamation mark, the resources may be conflicting and you must follow the
steps below:
• Uninstall the driver software from your PC.
• Restart your PC and repeat the software and hardware installation as specified in this User Guide.
3. I cannot communicate with the other computers linked via Ethernet in the Infrastructure
configuration.
Make sure that the notebook or desktop is powered on.
Make sure that the Home Wireless-G PC Card is configured with the same SSID and security settings as the
other computers in the Infrastructure configuration.
Page 34

29
Appendix A: Troubleshooting
Frequently Asked Questions
Home Wireless-G PC Card
Frequently Asked Questions
Can I run an application from a remote computer over the wireless network?
This will depend on whether or not the application is designed to be used over a network. Consult the
application’s user guide to determine if it supports operation over a network.
Can I play computer games with other members of the wireless network?
Yes, as long as the game supports multiple players over a LAN (local area network). Refer to the game’s user
guide for more information.
What is the IEEE 802.11b standard?
It is one of the IEEE standards for wireless networks. The 802.11b standard allows wireless networking hardware
from different manufacturers to communicate, provided that the hardware complies with the 802.11b standard.
The 802.11b standard states a maximum data transfer rate of 11Mbps and an operating frequency of 2.4GHz.
What is the IEEE 802.11g standard?
It is one of the IEEE standards for wireless networks. The 802.11g standard allows wireless networking hardware
from different manufacturers to communicate, provided that the hardware complies with the 802.11g standard.
The 802.11g standard states a maximum data transfer rate of 54Mbps and an operating frequency of 2.4GHz.
What IEEE 802.11b features are supported?
The product supports the following IEEE 802.11b functions:
• CSMA/CA plus Acknowledge protocol
• Multi-Channel Roaming
• Automatic Rate Selection
• RTS/CTS feature
• Fragmentation
• Power Management
What IEEE 802.11g features are supported?
The product supports the following IEEE 802.11g functions:
• CSMA/CA plus Acknowledge protocol
• OFDM protocol
• Multi-Channel Roaming
• Automatic Rate Selection
• RTS/CTS feature
• Fragmentation
• Power Management
Page 35

30
Appendix A: Troubleshooting
Frequently Asked Questions
Home Wireless-G PC Card
What is ad-hoc mode?
When a wireless network is set to ad-hoc mode, the wireless-equipped computers are configured to
communicate directly with each other. This type of network will not communicate with any wired network.
What is infrastructure mode?
When a wireless network is set to infrastructure mode, the wireless network is configured to communicate with a
wired network through a wireless access point.
What is roaming?
Roaming is the ability of a portable computer user to communicate continuously while moving freely throughout
an area greater than that covered by a single access point. Before using the roaming function, the workstation
must make sure that it is the same channel number with the access point of dedicated coverage area.
To achieve true seamless connectivity, the wireless LAN must incorporate a number of different functions. Each
node and access point, for example, must always acknowledge receipt of each message. Each node must
maintain contact with the wireless network even when not actually transmitting data. Achieving these functions
simultaneously requires a dynamic RF networking technology that links access points and nodes. In such a
system, the user’s end node undertakes a search for the best possible access to the system. First, it evaluates
such factors as signal strength and quality, as well as the message load currently being carried by each access
point and the distance of each access point to the wired backbone. Based on that information, the node next
selects the right access point and registers its address. Communications between end node and host computer
can then be transmitted up and down the backbone.
As the user moves on, the end node’s RF transmitter regularly checks the system to determine whether it is in
touch with the original access point or whether it should seek a new one. When a node no longer receives
acknowledgment from its original access point, it undertakes a new search. Upon finding a new access point, it
then re-registers, and the communication process continues.
What is ISM band?
The FCC and their counterparts outside of the U.S. have set aside bandwidth for unlicensed use in the ISM
(Industrial, Scientific and Medical) band. Spectrum in the vicinity of 2.4 GHz, in particular, is being made available
worldwide. This presents a truly revolutionary opportunity to place convenient high-speed wireless capabilities in
the hands of users around the globe.
What is Spread Spectrum?
Spread Spectrum technology is a wideband radio frequency technique developed by the military for use in
reliable, secure, mission-critical communications systems. It is designed to trade off bandwidth efficiency for
reliability, integrity, and security. In other words, more bandwidth is consumed than in the case of narrowband
transmission, but the trade-off produces a signal that is, in effect, louder and thus easier to detect, provided that
the receiver knows the parameters of the spread-spectrum signal being broadcast. If a receiver is not tuned to
Page 36

31
Appendix A: Troubleshooting
Frequently Asked Questions
Home Wireless-G PC Card
the right frequency, a spread-spectrum signal looks like background noise. There are two main alternatives,
Direct Sequence Spread Spectrum (DSSS) and Frequency Hopping Spread Spectrum (FHSS).
What is DSSS? What is FHSS? And what are their differences?
Frequency-Hopping Spread-Spectrum (FHSS) uses a narrowband carrier that changes frequency in a pattern that
is known to both transmitter and receiver. Properly synchronized, the net effect is to maintain a single logical
channel. To an unintended receiver, FHSS appears to be short-duration impulse noise. Direct-Sequence SpreadSpectrum (DSSS) generates a redundant bit pattern for each bit to be transmitted. This bit pattern is called a chip
(or chipping code). The longer the chip, the greater the probability that the original data can be recovered. Even if
one or more bits in the chip are damaged during transmission, statistical techniques embedded in the radio can
recover the original data without the need for retransmission. To an unintended receiver, DSSS appears as low
power wideband noise and is rejected (ignored) by most narrowband receivers.
What is WEP?
WEP is Wired Equivalent Privacy, a data privacy mechanism based on a shared key algorithm, as described in the
802.11 standard.
Page 37

32
Appendix B: Wireless Security
Security Precautions
Home Wireless-G PC Card
Appendix B: Wireless Security
Linksys wants to make wireless networking as safe and easy for you as possible. The current generation of
Linksys products provide several network security features, but they require specific action on your part for
implementation. So, keep the following in mind whenever you are setting up or using your wireless network.
Security Precautions
The following is a complete list of security precautions to take (at least steps 1 through 5 should be followed):
1. Change the default SSID.
2. Disable SSID Broadcast.
3. Change the default password for the Administrator account.
4. Enable MAC Address Filtering.
5. Change the SSID periodically.
6. Use the highest encryption algorithm possible. Use WPA if it is available. Please note that this may reduce
your network performance.
7. Change the WEP encryption keys periodically.
Security Threats Facing Wireless Networks
Wireless networks are easy to find. Hackers know that in order to join a wireless network, wireless networking
products first listen for “beacon messages”. These messages can be easily decrypted and contain much of the
network’s information, such as the network’s SSID (Service Set Identifier). Here are the steps you can take:
Change the administrator’s password regularly. With every wireless networking device you use, keep in mind
that network settings (SSID, WEP keys, etc.) are stored in its firmware. Your network administrator is the only
person who can change network settings. If a hacker gets a hold of the administrator’s password, he, too, can
change those settings. So, make it harder for a hacker to get that information. Change the administrator’s
password regularly.
SSID. There are several things to keep in mind about the SSID:
NOTE: Some of these security features are
available only through the network router or
access point. Refer to the router or access
point’s documentation for more information.
Page 38

33
Appendix B: Wireless Security
Security Threats Facing Wireless Networks
Home Wireless-G PC Card
1. Disable Broadcast
2. Make it unique
3. Change it often
Most wireless networking devices will give you the option of broadcasting the SSID. While this option may be
more convenient, it allows anyone to log into your wireless network. This includes hackers. So, don’t broadcast
the SSID.
Wireless networking products come with a default SSID set by the factory. (The Linksys default SSID is “linksys”.)
Hackers know these defaults and can check these against your network. Change your SSID to something unique
and not something related to your company or the networking products you use.
Change your SSID regularly so that any hackers who have gained access to your wireless network will have to
start from the beginning in trying to break in.
MAC Addresses. Enable MAC Address filtering. MAC Address filtering will allow you to provide access to only
those wireless nodes with certain MAC Addresses. This makes it harder for a hacker to access your network with
a random MAC Address.
WEP Encryption. Wired Equivalent Privacy (WEP) is often looked upon as a cure-all for wireless security
concerns. This is overstating WEP’s ability. Again, this can only provide enough security to make a hacker’s job
more difficult.
There are several ways that WEP can be maximized:
1. Use the highest level of encryption possible
2. Use “Shared Key” authentication
3. Change your WEP key regularly
WPA. Wi-Fi Protected Access (WPA) is the newest and best av ailable standard in Wi-Fi security. Three modes are
available: WPA-PSK (WPA Personal), WPA RADIUS (WPA Enterprise), and RADIUS. WPA-PSK (WPA Personal) gives
you a choice of two encryption methods: TKIP (Temporal Key Integrity Protocol), which utilizes a stronger
encryption method and incorporates Message Integrity Code (MIC) to provide protection against hackers, and AES
(Advanced Encryption System), which utilizes a symmetric 128-Bit block data encryption. WPA RADIUS (WPA
Enterprise) offers two encryption methods, TKIP and AES, with dynamic encryption keys. RADIUS (Remote
Authentication Dial-In User Service) utilizes a RADIUS server for authentication.
IMPORTANT: Always remember that each
device in your wireless network MUST use
the same encryption method and encryption
key or your wireless network will not function
properly.
Page 39

34
Appendix B: Wireless Security
Security Threats Facing Wireless Networks
Home Wireless-G PC Card
WPA-PSK (WPA Personal). If you do not have a RADIUS server, Select the type of algorithm, TKIP or AES , and
enter a password in the Passphrase field of 8-63 characters.
WPA RADIUS (WPA Enterprise). WPA used in coordination with a RADIUS server. (This should only be used
when a RADIUS server is connected to the Router or other device.) WPA RADIUS offers two encryption
methods, TKIP and AES, with dynamic encryption keys.
RADIUS. WEP used in coordination with a RADIUS server. (This should only be used when a RADIUS server is
connected to the Router or other device.)
Implementing encryption may have a negative impact on your network’s performance, but if you are transmitting
sensitive data over your network, encryption should be used.
These security recommendations should help keep your mind at ease while you are enjoying the most flexible
and convenient technology Linksys has to offer.
Page 40

35
Appendix C: Windows Help
Home Wireless-G PC Card
Appendix C: Windows Help
Almost all wireless products require Microsoft Windows. Windows is the most used operating system in the world
and comes with many features that help make networking easier. These features can be accessed through
Windows Help and are described in this appendix.
TCP/IP
Before a computer can communicate with an access point or wireless router, TCP/IP must be enabled. TCP/IP is a
set of instructions, or protocol, all PCs follow to communicate over a network. This is true for wireless networks
as well. Your PCs will not be able to utilize wireless networking without having TCP/IP enabled. Windows Help
provides complete instructions on enabling TCP/IP.
Shared Resources
If you wish to share printers, folder, or files over your network, Windows Help provides complete instructions on
utilizing shared resources.
Network Neighborhood/My Network Places
Other PCs on your network will appear under Network Neighborhood or My Network Places (depending upon the
version of Windows you're running). Windows Help provides complete instructions on adding PCs to your
network.
Page 41

36
Appendix D: Glossary
Home Wireless-G PC Card
Appendix D: Glossary
802.11b - A wireless networking standard that specifies a maximum data transfer rate of 11Mbps and an
operating frequency of 2.4GHz.
802.11g - A wireless networking standard that specifies a maximum data transfer rate of 54Mbps, an operating
frequency of 2.4GHz, and backward compatibility with 802.11b devices.
Access Point - A device that allows wireless-equipped computers and other devices to communicate with a
wired network. Also used to expand the range of a wireless network.
Adapter - A device that adds network functionality to your PC.
Ad-hoc - A group of wireless devices communicating directly with each other (peer-to-peer) without the use of
an access point.
AES (Advanced Encryption Standard) - A method that uses up to 256-bit key encryption to secure data.
Backbone - The part of a network that connects most of the systems and networks together, and handles the
most data.
Bandwidth - The transmission capacity of a given device or network.
Bit - A binary digit.
CSMA/CA (Carrier Sense Multiple Access/Collision Avoidance) - A method of data transfer that is used to prevent
data collisions.
CTS (Clear To Send) - A signal sent by a wireless device, signifying that it is ready to receive data.
Default Gateway - A device that forwards Internet traffic from your local area network.
DHCP (Dynamic Host Configuration Protocol) - A networking protocol that allows administrators to assign
temporary IP addresses to network computers by "leasing" an IP address to a user for a limited amount of time,
instead of assigning permanent IP addresses.
DNS (Domain Name Server) - The IP address of your ISP's server, which translates the names of websites into IP
addresses.
Page 42

37
Appendix D: Glossary
Home Wireless-G PC Card
DSSS (Direct-Sequence Spread-Spectrum) - Frequency transmission with a redundant bit pattern resulting in a
lower probability of information being lost in transit.
EAP (Extensible Authentication Protocol) - A general authentication protocol used to control network access.
Many specific authentication methods work within this framework.
EAP-PEAP (Extensible Authentication Protocol-Protected Extensible Authentication Protocol) - A mutual
authentication method that uses a combination of digital certificates and another system, such as passwords.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security) - A mutual authentication method that
uses digital certificates.
Encryption - Encoding data transmitted in a network.
Ethernet - a standard network protocol that specifies how data is placed on and retrieved from a common
transmission medium.
Firmware - The programming code that runs a networking device.
Fragmentation -Breaking a packet into smaller units when transmitting over a network medium that cannot
support the original size of the packet.
Gateway - A device that interconnects networks with different, incompatible communications protocols.
Hardware - The physical aspect of computers, telecommunications, and other information technology devices.
Infrastructure - A wireless network that is bridged to a wired network via an access point.
IP (Internet Protocol) - A protocol used to send data over a network.
IP Address - The address used to identify a computer or device on a network.
ISM band - Radio bandwidth utilized in wireless transmissions.
ISP (Internet Service Provider) - A company that provides access to the Internet.
LAN - The computers and networking products that make up your local network.
LEAP (Lightweight Extensible Authentication Protocol) - A mutual authentication method that uses a username
and password system.
MAC (Media Access Control) Address - The unique address that a manufacturer assigns to each networking
device.
Page 43

38
Appendix D: Glossary
Home Wireless-G PC Card
Network - A series of computers or devices connected for the purpose of data sharing, storage, and/or
transmission between users.
Node - A network junction or connection point, typically a computer or work station.
Packet - A unit of data sent over a network.
Passphrase - Used much like a password, a passphrase simplifies the WEP encryption process by automatically
generating the WEP encryption keys for Linksys products.
Roaming - The ability to take a wireless device from one access point's range to another without losing the
connection.
Router - A networking device that connects multiple networks together.
RTS (Request To Send) - A networking method of coordinating large packets through the RTS Threshold setting.
Server - Any computer whose function in a network is to provide user access to files, printing, communications,
and other services.
SMTP (Simple Mail Transfer Protocol) - The standard e-mail protocol on the Internet.
SNMP (Simple Network Management Protocol) - A widely used network monitoring and control protocol.
Software - Instructions for the computer. A series of instructions that performs a particular task is called a
"program".
SPI (Stateful Packet Inspection) Firewall - A technology that inspects every incoming packet of information
before allowing it to enter the network.
Spread Spectrum - Wideband radio frequency technique used for more reliable and secure data transmission.
SSID (Service Set IDentifier) - Your wireless network's name.
Static IP Address - A fixed address assigned to a computer or device that is connected to a network.
Static Routing - Forwarding data in a network via a fixed path.
Subnet Mask - An address code that determines the size of the network.
Switch - 1. A data switch that connects computing devices to host computers, allowing a large number of
devices to share a limited number of ports. 2. A device for making, breaking, or changing the connections in an
electrical circuit.
Page 44

39
Appendix D: Glossary
Home Wireless-G PC Card
TCP (Transmission Control Protocol) - A network protocol for transmitting data that requires acknowledgement
from the recipient of data sent.
TCP/IP (Transmission Control Protocol/Internet Protocol) - A set of instructions PCs use to communicate over a
network.
Telnet - A user command and TCP/IP protocol used for accessing remote PCs.
TFTP (Trivial File Transfer Protocol) - A version of the TCP/IP FTP protocol that has no directory or password
capability.
Throughput - The amount of data moved successfully from one node to another in a given time period.
TKIP (Temporal Key Integrity Protocol) - a wireless encryption protocol that provides dynamic encryption keys for
each packet transmitted.
Topology - The physical layout of a network.
TX Rate - Transmission Rate.
UDP (User Datagram Protocol) - A network protocol for transmitting data that does not require acknowledgement
from the recipient of the data that is sent.
Upgrade - To replace existing software or firmware with a newer version.
Upload - To transmit a file over a network.
URL (Uniform Resource Locator) - The address of a file located on the Internet.
WAN (Wide Area Network)- The Internet.
WEP (Wired Equivalent Privacy) - A method of encrypting network data transmitted on a wireless network for
greater security.
WINIPCFG - A Windows 98 and Me utility that displays the IP address for a particular networking device.
WLAN (Wireless Local Area Network) - A group of computers and associated devices that communicate with
each other wirelessly.
WPA (Wi-Fi Protected Access) - a wireless security protocol using TKIP (Temporal Key Integrity Protocol)
encryption, which can be used in conjunction with a RADIUS server.
Page 45

40
Appendix E: Specifications
Home Wireless-G PC Card
Appendix E: Specifications
Standards IEEE 802.11g, IEEE 802.11b
Channels 13 Channels (Europe, Japan)
LEDs Power, Link
Transmit Power 18 dBm
Protocols 802.11b: CCK (11 Mbps), DQPSK (2 Mbps), DBPSK (1 Mbps); 802.11g: OFDM
Network Protocols TCP/IP
Security Features WEP, WPA (AES, TKIP), 802.1x
WEP Key Bits 64, 128 Bit
Dimensions 115 mm x 54 mm x 7.5 mm (4,53" x 2,13" x 0,30")
Unit Weight 0,047 kg (1,66 oz.)
Certifications CE, Wi-Fi, WHQL
Operating Temp. 0ºC to 55ºC (32ºF to 131ºF)
Storage Temp. -25ºC to 70ºC (-13ºF to 158ºF)
Operating Humidity 5% to 95%, Non-Condensing
Storage Humidity 5% to 95%, Non-Condensing
Page 46

41
Appendix F: Warranty Information
Home Wireless-G PC Card
Appendix F: Warranty Information
Linksys warrants to You that, for a period of two years (the “Warranty Period”), your Linksys Product will be substantially free
of defects in materials and workmanship under normal use. Your exclusive remedy and Linksys' entire liability under this
warranty will be for Linksys at its option to repair or replace the Product or refund Your purchase price less any rebates. This
limited warranty extends only to the original purchaser.
If the Product proves defective during the Warranty Period call Linksys Technical Support in order to obtain a Return
Authorization Number, if applicable. BE SURE TO HAVE YOUR PROOF OF PURCHASE ON HAND WHEN CALLING. If You are
requested to return the Product, mark the Retu rn Authorization Number clearly on the outside of the package and include a
copy of your original proof of purchase. RETURN REQUESTS CANNOT BE PROCESSED WITHOUT PROOF OF PURCHASE. You
are responsible for shipping defective Products to Linksys. Linksys pays for UPS Ground shipping from Linksys back to You
only. Customers located outside of the United States of America and Canada are responsible for all shipping and handling
charges.
ALL IMPLIED WARRANTIES AND CONDITIONS OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE ARE LIMITED
TO THE DURATION OF THE WARRANTY PERIOD. ALL OTHER EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND
WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF NON-INFRINGEMENT, ARE DISCLAIMED. Some jurisdictions do not
allow limitations on how long an implied warranty lasts, so the above limitation may not apply to You. This warranty gives
You specific legal rights, and You may also have other rights which vary by jurisdiction.
This warranty does not apply if the Product (a) has been altered, except by Linksys, (b) has not been installed, operated,
repaired, or maintained in accordance with instructions supplied by Linksys, or (c) has been subjected to abnormal physical
or electrical stress, misuse, negligence, or accident. In addition, due to the continual development of new techniques for
intruding upon and attacking networks, Linksys does not warrant that the Product will be free of vulnerability to intrusion or
attack.
TO THE EXTENT NOT PROHIBITED BY LAW, IN NO EVENT WILL LINKSYS BE LIABLE FOR ANY LOST DATA, REVENUE OR PROFIT,
OR FOR SPECIAL, INDIRECT, CONSEQUENTIAL, INCIDENTAL OR PUNITIVE DAMAGES, REGARDLESS OF THE THEORY OF
LIABILITY (INCLUDING NEGLIGENCE), ARISING OUT OF OR RELATED TO THE USE OF OR INABILITY TO USE THE PRODUCT
(INCLUDING ANY SOFTWARE), EVEN IF LINKSYS HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. IN NO EVENT
WILL LINKSYS’ LIABILITY EXCEED THE AMOUNT PAID BY YOU FOR THE PRODUCT. The foregoing limitations will apply even if
any warranty or remedy provided under this Agreement fails of its essential purpose. Some jurisdictions do not allow the
exclusion or limitation of incidental or consequential damages, so the above limitation or exclusion may not apply to You.
This Warranty is valid and may be processed only in the country of purchase.
Please direct all inquiries to: Linksys, P.O. Box 18558, Irvine, CA 92623.
Page 47

42
Appendix G: Regulatory Information
Home Wireless-G PC Card
Appendix G: Regulatory Information
Compliance Information for 2.4-GHz Wireless Products Relevant to the EU and Other Countries Following
the EU Directive 1999/5/EC (R&TTE Directive)
Declaration of Conformity with Regard to the EU Directive 1995/5/EC (R&TTE Directive)
Page 48

43
Appendix G: Regulatory Information
Home Wireless-G PC Card
The following standards were applied during the assessment of the product against the requirements of the
Directive 1999/5/EC:
• Radio: EN 300 328
• EMC: EN 301 489-1, EN 301 489-17
• Safety: EN 60950
NOTE: If you need any technical documentation, see the “How to Access T echnical
Documents on www.linksys.com/international” section for more information.
Page 49

44
Appendix G: Regulatory Information
Home Wireless-G PC Card
CE Marking
For the Linksys Wireless-B and Wireless-G products, the following CE mark, notified body number (where applicable), and
class 2 identifier are added to the equipment.
Check the CE label on the product to find out which notified body was involved during the assessment.
National Restrictions
This product may be used in all EU countries (and other countries following the EU directive 1999/5/EC) without any
limitation except for the countries mentioned below:
Ce produit peut être utilisé dans tous les pays de l’UE (et dans tous les pays ayant transposés la directive 1999/5/CE) sans
aucune limitation, excepté pour les pays mentionnés ci-dessous:
Questo prodotto è utilizzabile in tutte i paesi EU (ed in tutti gli altri paesi che seguono le direttive EU 1999/5/EC) senza
nessuna limitazione, eccetto per i paesii menzionati di seguito:
Das Produkt kann in allen EU Staaten ohne Einschränkungen eingesetzt werden (sowie in anderen Staaten die der EU
Direktive 1995/5/CE folgen) mit Außnahme der folgenden aufgeführten Staaten:
Belgium
The Belgian Institute for Postal Services and Telecommunications (BIPT) must be notified of any outdoor wireless link
having a range exceeding 300 meters. Please check http://www.bipt.be for more details.
Draadloze verbindingen voor buitengebruik en met een reikwijdte van meer dan 300 meter dienen aangemeld te worden
bij het Belgisch Instituut voor postdiensten en telecommunicatie (BIPT). Zie http://www.bipt.be voor meer gegevens.
Les liaisons sans fil pour une utilisation en extérieur d’une distance supérieure à 300 mètres doivent être notifiées à
l’Institut Belge des services Postaux et des Télécommunications (IBPT). Visitez
http://www.ibpt.be pour de plus amples détails.
France
In case the product is used outdoors, the output power is restricted in some parts of the band. See Table 1 or check
http://www.art-telecom.fr/ for more details.
or
or
Page 50

45
Appendix G: Regulatory Information
Home Wireless-G PC Card
Dans la cas d’une utilisation en extérieur, la puissance de sortie est limitée pour certaines parties de la bande. Reportezvous à la table 1 ou visitez http://www.art-telecom.fr/ pour de plus amples détails.
Italy
This product meets the National Radio Interface and the requirements specified in the National Frequency Allocation T able
for Italy. Unless operating within the boundaries of the owner’s property, the use of this 2.4 GHz Wireless LAN product
requires a ‘general authorization’. Please check with http://www.comunicazioni.it/it/ for more details.
Questo prodotto è conforme alla specifiche di Interfaccia Radio Nazionali e rispetta il Piano Nazionale di ripartizione delle
frequenze in Italia. Se non viene installato all’interno del proprio fondo, l’utilizzo di prodotti Wireless LAN a 2.4 GHz richiede
una “Autorizzazione Generale”. Consultare http://www.comunicazioni.it/it/ per maggiori dettagli.
Product Usage Restrictions
This product is designed for indoor usage only. Outdoor usage is not recommended.
This product is designed for use with the included integral or external (dedicated) antenna(s). Use of non-dedicated or
third-party antenna(s) is not recommended and is not supported by Linksys.
Power Output of Your Device
To comply with your country’s regulations, you may have to change the power output of your wireless device. Proceed to
the appropriate section for your device.
Table 1: Applicable Power Levels in France
Location Frequency Range (MHz) Power (EIRP)
Indoor (No restrictions) 2400-2483.5 100 mW (20 dBm)
Outdoor 2400-2454
2454-2483.5
100 mW (20 dBm)
10 mW (10 dBm)
Note: The power output setting may not be available on all wireless products.
For more information, refer to the documentation on your product’s CD or at
http://www.linksys.com/international.
Page 51

46
Appendix G: Regulatory Information
Home Wireless-G PC Card
Wireless Adapters
Wireless adapters have the power output set to 100% by default. Maximum power output on each adapter does not exceed
20 dBm (100 mW); it is generally 18 dBm (64 mW) or below. If you need to alter your wireless adapter’s power output,
follow the appropriate instructions for your computer’s Windows operating system:
Windows XP
1. Double-click the Wireless icon in your desktop’s system tray.
2. Open the Wireless Network Connection window.
3. Click the Properties button.
4. Select the General tab, and click the Configure button.
5. In the Properties window, click the Advanced tab.
6. Select Power Output.
7. From the pull-down menu on the right, select the wireless adapter’s power output percentage.
Windows 2000
1. Open the Control Panel.
2. Double-click Network and Dial-Up Connections.
3. Select your current wireless connection, and select Properties.
4. From the Properties screen, click the Configure button.
5. Click the Advanced tab, and select Power Output.
6. From the pull-down menu on the right, select the wireless adapter’s power setting.
If your computer is running Windows Millennium or 98, then refer to Windows Help for instructions on how to access the
advanced settings of a network adapter.
Wireless Access Points, Routers, or Other Wireless Products
If you have a wireless access point, router or other wireless product, use its Web-based Utility to configure its power
output setting (refer to the product’s documentation for more information).
Page 52

47
Appendix G: Regulatory Information
Home Wireless-G PC Card
Technical Documents on www.linksys.com/international
Follow these steps to access technical documents:
1. Browse to http://www.linksys.com/international.
2. Click the region in which you reside.
3. Click the name of the country in which you reside.
4. Click Products.
5. Click the appropriate product category.
6. Select a product.
7. Click the type of documentation you want. The document will automatically open in PDF format.
Note: If you have questions regarding the compliance of these products or you
cannot find the information you are looking for, please contact your local sales
office. Visit http://www.linksys.com/international for more details.
Page 53

48
Appendix H: Contact Information
Home Wireless-G PC Card
Appendix H: Contact Information
Need to contact Linksys?
Visit us online for information on the latest products and updates to your existing products at:
http://www.linksys.com/international
If you experience problems with any Linksys product, you can e-mail us at:
In Europe E-mail Address
Austria support.at@linksys.com
Belgium support.be@linksys.com
Denmark support.dk@linksys.com
France support.fr@linksys.com
Germany support.de@linksys.com
Italy support.it@linksys.com
Netherlands support.nl@linksys.com
Norway support.no@linksys.com
Portugal support.pt@linksys.com
Spain support.es@linksys.com
Sweden support.se@linksys.com
Switzerland support.ch@linksys.com
United Kingdom & Ireland support.uk@linksys.com
Outside of Europe E-mail Address
Latin America support.la@linksys.com
U.S. and Canada support@linksys.com
 Loading...
Loading...