Page 1
Kaspersky Mobile Security 9
USER GUIDE
P R O GR A M V ER S IO N : 9 . 0
for BlackBerry OS
Page 2
2
Dear User!
Thank you for choosing our product. We hope that this documentation will help you in your work and will provide answers
regarding this software product.
Note! This document is the property of Kaspersky Lab ZAO (herein also referred to as Kaspersky Lab): all rights to this
document are reserved by the copyright laws of the Russian Federation, and by international treaties. Illegal reproduction
and distribution of this document or parts hereof will result in civil, administrative or criminal liability by the applicable law.
Reproduction or distribution of any materials in any format, including translations, is only allowed with the written
permission of Kaspersky Lab.
This document, and graphic images related to it, may be used exclusively for informational, non-commercial, and
personal purposes.
Kaspersky Lab reserves the right to amend this document without additional notification. You can find the latest version
of this document at the Kaspersky Lab website, at http://www.kaspersky.com/docs.
Kaspersky Lab shall not be liable for the content, quality, relevance, or accuracy of any materials used in this document
for which the rights are held by third parties, or for any potential or actual losses associated with the use of these
materials.
In this document, registered trademarks and service trademarks are used which are the property of the corresponding
rights holders.
Revision date: 20.01.2011
© 1997-2011 Kaspersky Lab ZAO. All Rights Reserved.
http://www.kaspersky.com
http://support.kaspersky.com
Page 3
3
KASPERSKY LAB END USER LICENSE AGREEMENT
IMPORTANT LEGAL NOTICE TO ALL USERS: CAREFULLY READ THE FOLLOWING LEGAL AGREEMENT BEFORE
YOU START USING THE SOFTWARE.
BY CLICKING THE ACCEPT BUTTON IN THE LICENSE AGREEMENT WINDOW OR BY ENTERING
CORRESPONDING SYMBOL(-S) YOU CONSENT TO BE BOUND BY THE TERMS AND CONDITIONS OF THIS
AGREEMENT. SUCH ACTION IS A SYMBOL OF YOUR SIGNATURE AND YOU ARE CONSENTING TO BE BOUND
BY AND ARE BECOMING A PARTY TO THIS AGREEMENT AND AGREE THAT THIS AGREEMENT IS
ENFORCEABLE LIKE ANY WRITTEN NEGOTIATED AGREEMENT SIGNED BY YOU. IF YOU DO NOT AGREE TO
ALL OF THE TERMS AND CONDITIONS OF THIS AGREEMENT, CANCEL THE INSTALLATION OF THE SOFTWARE
AND DO NOT INSTALL THE SOFTWARE.
AFTER CLICKING THE ACCEPT BUTTON IN THE LICENSE AGREEMENT WINDOW OR AFTER ENTERING
CORRESPONDING SYMBOL(-S) YOU HAVE THE RIGHT TO USE THE SOFTWARE IN ACCORDANCE WITH THE
TERMS AND CONDITIONS OF THIS AGREEMENT.
1. Definitions
1.1. Software means software including any Updates and related materials.
1.2. Rightholder (owner of all rights, whether exclusive or otherwise to the Software) means Kaspersky Lab ZAO, a
company incorporated according to the laws of the Russian Federation.
1.3. Computer(s) means hardware(s), including personal computers, laptops, workstations, personal digital
assistants, ‘smart phones’, hand-held devices, or other electronic devices for which the Software was designed
where the Software will be installed and/or used.
1.4. End User (You/Your) means individual(s) installing or using the Software on his or her own behalf or who is
legally using a copy of the Software; or, if the Software is being downloaded or installed on behalf of an
organization, such as an employer, "You" further means the organization for which the Software is downloaded
or installed and it is represented hereby that such organization has authorized the person accepting this
agreement to do so on its behalf. For purposes hereof the term "organization," without limitation, includes any
partnership, limited liability company, corporation, association, joint stock company, trust, joint venture, labor
organization, unincorporated organization, or governmental authority.
1.5. Partner(s) means organizations or individual(s), who distributes the Software based on an agreement and
license with the Rightholder.
1.6. Update(s) means all upgrades, revisions, patches, enhancements, fixes, modifications, copies, additions or
maintenance packs etc.
1.7. User Manual means user manual, administrator guide, reference book and related explanatory or other
materials.
2. Grant of License
2.1. The Rightholder hereby grants You a non-exclusive license to store, load, install, execute, and display (to "use")
the Software on a specified number of Computers in order to assist in protecting Your Computer on which the
Software is installed, from threats described in the User Manual, according to the all technical requirements
described in the User Manual and according to the terms and conditions of this Agreement (the "License") and
you accept this License:
Trial Version. If you have received, downloaded and/or installed a trial version of the Software and are hereby
granted an evaluation license for the Software, you may use the Software only for evaluation purposes and only
during the single applicable evaluation period, unless otherwise indicated, from the date of the initial installation.
Any use of the Software for other purposes or beyond the applicable evaluation period is strictly prohibited.
Multiple Environment Software; Multiple Language Software; Dual Media Software; Multiple Copies; Bundles. If
you use different versions of the Software or different language editions of the Software, if you receive the
Software on multiple media, if you otherwise receive multiple copies of the Software, or if you received the
Software bundled with other software, the total permitted number of your Computers on which all versions of the
Software are installed shall correspond to the number of computers specified in licenses you have obtained
from the Rightholder provided that unless the licensing terms provide otherwise, each acquired license entitles
you to install and use the Software on such a number of Computer(s) as is specified in Clauses 2.2 and 2.3.
2.2. If the Software was acquired on a physical medium You have the right to use the Software for protection of such
a number of Computer(s) as is specified on the Software package or as specified in additional agreement.
2.3. If the Software was acquired via the Internet You have the right to use the Software for protection of such a
number of Computers that was specified when You acquired the License to the Software or as specified in
additional agreement.
2.4. You have the right to make a copy of the Software solely for back-up purposes and only to replace the legally
owned copy if such copy is lost, destroyed or becomes unusable. This back-up copy cannot be used for other
purposes and must be destroyed when you lose the right to use the Software or when Your license expires or is
Page 4
U S E R G U I D E
4
terminated for any other reason according to the legislation in force in the country of your principal residence or
in the country where You are using the Software.
2.5. From the time of the Software activation or after license key file installation (with the exception of a trial version
of the Software) You have the right to receive the following services for the defined period specified on the
Software package (if the Software was acquired on a physical medium) or specified during acquisition (if the
Software was acquired via the Internet):
- Updates of the Software via the Internet when and as the Rightholder publishes them on its website or
through other online services. Аny Updates that you may receive become part of the Software and the
terms and conditions of this Agreement apply to them;
- Technical Support via the Internet and Technical Support telephone hotline.
3. Activation and Term
3.1. If You modify Your Computer or make changes to other vendors’ software installed on it, You may be required
by the Rightholder to repeat activation of the Software or license key file installation. The Rightholder reserves
the right to use any means and verification procedures to verify the validity of the License and/or legality of a
copy of the Software installed and/or used on Your Computer.
3.2. If the Software was acquired on a physical medium, the Software can be used, upon your acceptance of this
Agreement, for the period that is specified on the package commencing upon acceptance of this Agreement or
as specified in additional agreement.
3.3. If the Software was acquired via the Internet, the Software can be used, upon your acceptance of this
Agreement, for the period that was specified during acquisition or as specified in additional agreement.
3.4. You have the right to use a trial version of the Software as provided in Clause 2.1 without any charge for the
single applicable evaluation period (7 days) from the time of the Software activation according to this Agreement
provided that the trial version does not entitle You Updates and Technical support via the Internet and Technical
support telephone hotline. If Rightholder sets another duration for the single applicable evaluation period You
will be informed via notification.
3.5. Your License to Use the Software is limited to the period of time as specified in Clauses 3.2 or 3.3 (as
applicable) and the remaining period can be viewed via means described in User Manual.
3.6. If You have acquired the Software that is intended to be used on more than one Computer then Your License to
Use the Software is limited to the period of time starting from the date of activation of the Software or license
key file installation on the first Computer.
3.7. Without prejudice to any other remedy in law or in equity that the Rightholder may have, in the event of any
breach by You of any of the terms and conditions of this Agreement, the Rightholder shall at any time without
notice to You be entitled to terminate this License to use the Software without refunding the purchase price or
any part thereof.
3.8. You agree that in using the Software and in using any report or information derived as a result of using this
Software, you will comply with all applicable international, national, state, regional and local laws and
regulations, including, without limitation, privacy, copyright, export control and obscenity law.
3.9. Except as otherwise specifically provided herein, you may not transfer or assign any of the rights granted to you
under this Agreement or any of your obligations pursuant hereto.
3.10. If You have acquired the Software with activation code valid for language localization of the Software of that
region in which it was acquired from the Rightholder or its Partners, You cannot activate the Software with
applying the activation code intended for other language localization.
3.11. If You have acquired the Software intended for operation with particular telecoms operator such the Software
may be used only for operation with operator specified during acquisition.
3.12. In case of limitations specified in Clauses 3.10 and 3.11 information about these limitations is stated on package
and/or website of the Rightholder and/or its Partners.
4. Technical Support
The Technical Support described in Clause 2.5 of this Agreement is provided to You when the latest Update of the
Software is installed (except for a trial version of the Software).
Technical support service: http://support.kaspersky.com
5. Limitations
5.1. You shall not emulate, clone, rent, lend, lease, sell, modify, decompile, or reverse engineer the Software or
disassemble or create derivative works based on the Software or any portion thereof with the sole exception of
a non-waivable right granted to You by applicable legislation, and you shall not otherwise reduce any part of the
Software to human readable form or transfer the licensed Software, or any subset of the licensed Software, nor
permit any third party to do so, except to the extent the foregoing restriction is expressly prohibited by applicable
law. Neither Software’s binary code nor source may be used or reverse engineered to re-create the program
algorithm, which is proprietary. All rights not expressly granted herein are reserved by Rightholder and/or its
suppliers, as applicable. Any such unauthorized use of the Software shall result in immediate and automatic
termination of this Agreement and the License granted hereunder and may result in criminal and/or civil
prosecution against You.
Page 5
A B O U T T H I S G U I D E
5
5.2. You shall not transfer the rights to use the Software to any third party except as set forth in additional
agreement.
5.3. You shall not provide the activation code and/or license key file to third parties or allow third parties access to
the activation code and/or license key which are deemed confidential data of Rightholder and you shall exercise
reasonable care in protecting the activation code and/or license key in confidence provided that you can transfer
the activation code and/or license key to third parties as set forth in additional agreement.
5.4. You shall not rent, lease or lend the Software to any third party.
5.5. You shall not use the Software in the creation of data or software used for detection, blocking or treating threats
described in the User Manual.
5.6. The Rightholder has the right to block the key file or to terminate Your License to use the Software in the event
You breach any of the terms and conditions of this Agreement and without any refund to You.
5.7. If You are using the trial version of the Software You do not have the right to receive the Technical Support
specified in Clause 4 of this Agreement and You don’t have the right to transfer the license or the rights to use
the Software to any third party.
6. Limited Warranty and Disclaimer
6.1. The Rightholder guarantees that the Software will substantially perform according to the specifications and
descriptions set forth in the User Manual provided however that such limited warranty shall not apply to the
following: (w) Your Computer’s deficiencies and related infringement for which Rightholder’s expressly disclaims
any warranty responsibility; (x) malfunctions, defects, or failures resulting from misuse; abuse; accident; neglect;
improper installation, operation or maintenance; theft; vandalism; acts of God; acts of terrorism; power failures
or surges; casualty; alteration, non-permitted modification, or repairs by any party other than Rightholder; or any
other third parties’ or Your actions or causes beyond Rightholder’s reasonable control; (y) any defect not made
known by You to Rightholder as soon as practical after the defect first appears; and (z) incompatibility caused
by hardware and/or software components installed on Your Computer.
6.2. You acknowledge, accept and agree that no software is error free and You are advised to back-up the
Computer, with frequency and reliability suitable for You.
6.3. You acknowledge, accept and agree that Rightholder is not responsible or liable for data deletion authorized by
You. The mentioned data may include any personal or confidential information.
6.4. The Rightholder does not provide any guarantee that the Software will work correctly in case of violations of the
terms described in the User Manual or in this Agreement.
6.5. The Rightholder does not guarantee that the Software will work correctly if You do not regularly download
Updates specified in Clause 2.5 of this Agreement.
6.6. The Rightholder does not guarantee protection from the threats described in the User Manual after the
expiration of the period specified in Clauses 3.2 or 3.3 of this Agreement or after the License to use the
Software is terminated for any reason.
6.7. THE SOFTWARE IS PROVIDED "AS IS" AND THE RIGHTHOLDER MAKES NO REPRESENTATION AND
GIVES NO WARRANTY AS TO ITS USE OR PERFORMANCE. EXCEPT FOR ANY WARRANTY,
CONDITION, REPRESENTATION OR TERM THE EXTENT TO WHICH CANNOT BE EXCLUDED OR
LIMITED BY APPLICABLE LAW THE RIGHTHOLDER AND ITS PARTNERS MAKE NO WARRANTY,
CONDITION, REPRESENTATION, OR TERM (EXPRESSED OR IMPLIED, WHETHER BY STATUTE,
COMMON LAW, CUSTOM, USAGE OR OTHERWISE) AS TO ANY MATTER INCLUDING, WITHOUT
LIMITATION, NONINFRINGEMENT OF THIRD PARTY RIGHTS, MERCHANTABILITY, SATISFACTORY
QUALITY, INTEGRATION, OR APPLICABILITY FOR A PARTICULAR PURPOSE. YOU ASSUME ALL
FAULTS, AND THE ENTIRE RISK AS TO PERFORMANCE AND RESPONSIBILITY FOR SELECTING THE
SOFTWARE TO ACHIEVE YOUR INTENDED RESULTS, AND FOR THE INSTALLATION OF, USE OF, AND
RESULTS OBTAINED FROM THE SOFTWARE. WITHOUT LIMITING THE FOREGOING PROVISIONS, THE
RIGHTHOLDER MAKES NO REPRESENTATION AND GIVES NO WARRANTY THAT THE SOFTWARE WILL
BE ERROR-FREE OR FREE FROM INTERRUPTIONS OR OTHER FAILURES OR THAT THE SOFTWARE
WILL MEET ANY OR ALL YOUR REQUIREMENTS WHETHER OR NOT DISCLOSED TO THE
RIGHTHOLDER .
7. Exclusion and Limitation of Liability
TO THE MAXIMUM EXTENT PERMITTED BY APPLICABLE LAW, IN NO EVENT SHALL THE RIGHTHOLDER OR ITS
PARTNERS BE LIABLE FOR ANY SPECIAL, INCIDENTAL, PUNITIVE, INDIRECT, OR CONSEQUENTIAL DAMAGES
WHATSOEVER (INCLUDING, BUT NOT LIMITED TO, DAMAGES FOR LOSS OF PROFITS OR CONFIDENTIAL OR
OTHER INFORMATION, FOR BUSINESS INTERRUPTION, FOR LOSS OF PRIVACY, FOR CORRUPTION, DAMAGE
AND LOSS OF DATA OR PROGRAMS, FOR FAILURE TO MEET ANY DUTY INCLUDING ANY STATUTORY DUTY,
DUTY OF GOOD FAITH OR DUTY OF REASONABLE CARE, FOR NEGLIGENCE, FOR ECONOMIC LOSS, AND FOR
ANY OTHER PECUNIARY OR OTHER LOSS WHATSOEVER) ARISING OUT OF OR IN ANY WAY RELATED TO THE
USE OF OR INABILITY TO USE THE SOFTWARE, THE PROVISION OF OR FAILURE TO PROVIDE SUPPORT OR
OTHER SERVICES, INFORMATON, SOFTWARE, AND RELATED CONTENT THROUGH THE SOFTWARE OR
OTHERWISE ARISING OUT OF THE USE OF THE SOFTWARE, OR OTHERWISE UNDER OR IN CONNECTION
WITH ANY PROVISION OF THIS AGREEMENT, OR ARISING OUT OF ANY BREACH OF CONTRACT OR ANY TORT
(INCLUDING NEGLIGENCE, MISREPRESENTATION, ANY STRICT LIABILITY OBLIGATION OR DUTY), OR ANY
Page 6
U S E R G U I D E
6
BREACH OF STATUTORY DUTY, OR ANY BREACH OF WARRANTY OF THE RIGHTHOLDER OR ANY OF ITS
PARTNERS, EVEN IF THE RIGHTHOLDER OR ANY PARTNER HAS BEEN ADVISED OF THE POSSIBILITY OF
SUCH DAMAGES.
YOU AGREE THAT IN THE EVENT THE RIGHTHOLDER AND/OR ITS PARTNERS ARE FOUND LIABILE, THE
LIABILITY OF THE RIGHTHOLDER AND/OR ITS PARTNERS SHALL BE LIMITED BY THE COSTS OF THE
SOFTWARE. IN NO CASE SHALL THE LIABILITY OF THE RIGHTHOLDER AND/OR ITS PARTNERS EXCEED THE
FEES PAID FOR THE SOFTWARE TO THE RIGHTHOLDER OR THE PARTNER (AS MAY BE APPLICABLE).
NOTHING IN THIS AGREEMENT EXCLUDES OR LIMITS ANY CLAIM FOR DEATH AND PERSONAL INJURY.
FURTHER IN THE EVENT ANY DISCLAIMER, EXCLUSION OR LIMITATION IN THIS AGREEMENT CANNOT BE
EXLUDED OR LIMITED ACCORDING TO APPLICABLE LAW THEN ONLY SUCH DISCLAIMER, EXCLUSION OR
LIMITATION SHALL NOT APPLY TO YOU AND YOU CONTINUE TO BE BOUND BY ALL THE REMAINING
DISCLAIMERS, EXCLUSIONS AND LIMITATIONS.
8. GNU and Other Third Party Licenses
The Software may include some software programs that are licensed (or sublicensed) to the user under the GNU
General Public License (GPL) or other similar free software licenses which, among other rights, permit the user to copy,
modify and redistribute certain programs, or portions thereof, and have access to the source code ("Open Source
Software"). If such licenses require that for any software, which is distributed to someone in an executable binary format,
that the source code also be made available to those users, then the source code should be made available by sending
the request to source@kaspersky.com or the source code is supplied with the Software. If any Open Source Software
licenses require that the Rightholder provide rights to use, copy or modify an Open Source Software program that are
broader than the rights granted in this Agreement, then such rights shall take precedence over the rights and restrictions
herein.
9. Intellectual Property Ownership
9.1 You agree that the Software and the authorship, systems, ideas, methods of operation, documentation and
other information contained in the Software, are proprietary intellectual property and/or the valuable trade
secrets of the Rightholder or its partners and that the Rightholder and its partners, as applicable, are protected
by civil and criminal law, and by the law of copyright, trade secret, trademark and patent of the Russian
Federation, European Union and the United States, as well as other countries and international treaties. This
Agreement does not grant to You any rights to the intellectual property including any the Trademarks or Service
Marks of the Rightholder and/or its partners ("Trademarks"). You may use the Trademarks only insofar as to
identify printed output produced by the Software in accordance with accepted trademark practice, including
identification of the Trademark owner’s name. Such use of any Trademark does not give you any rights of
ownership in that Trademark. The Rightholder and/or its partners own and retain all right, title, and interest in
and to the Software, including without limitation any error corrections, enhancements, Updates or other
modifications to the Software, whether made by the Rightholder or any third party, and all copyrights, patents,
trade secret rights, trademarks, and other intellectual property rights therein. Your possession, installation or
use of the Software does not transfer to you any title to the intellectual property in the Software, and you will not
acquire any rights to the Software except as expressly set forth in this Agreement. All copies of the Software
made hereunder must contain the same proprietary notices that appear on and in the Software. Except as
stated herein, this Agreement does not grant you any intellectual property rights in the Software and you
acknowledge that the License, as further defined herein, granted under this Agreement only provides you with a
right of limited use under the terms and conditions of this Agreement. Rightholder reserves all rights not
expressly granted to you in this Agreement.
9.2 You acknowledge that the source code, activation code and/or license key file for the Software are proprietary
to the Rightholder and constitutes trade secrets of the Rightholder. You agree not to modify, adapt, translate,
reverse engineer, decompile, disassemble or otherwise attempt to discover the source code of the Software in
any way.
9.3 You agree not to modify or alter the Software in any way. You may not remove or alter any copyright notices or
other proprietary notices on any copies of the Software.
10. Governing Law; Arbitration
This Agreement will be governed by and construed in accordance with the laws of the Russian Federation without
reference to conflicts of law rules and principles. This Agreement shall not be governed by the United Nations
Convention on Contracts for the International Sale of Goods, the application of which is expressly excluded. Any dispute
arising out of the interpretation or application of the terms of this Agreement or any breach thereof shall, unless it is
settled by direct negotiation, be settled by in the International Commercial Arbitration Court at the Russian Federation
Chamber of Commerce and Industry in Moscow, the Russian Federation. Any award rendered by the arbitrator shall be
final and binding on the parties and any judgment on such arbitration award may be enforced in any court of competent
jurisdiction. Nothing in this Section 10 shall prevent a Party from seeking or obtaining equitable relief from a court of
competent jurisdiction, whether before, during or after arbitration proceedings.
Page 7
A B O U T T H I S G U I D E
7
11. Period for Bringing Actions
No action, regardless of form, arising out of the transactions under this Agreement, may be brought by either party hereto
more than one (1) year after the cause of action has occurred, or was discovered to have occurred, except that an action
for infringement of intellectual property rights may be brought within the maximum applicable statutory period.
12. Entire Agreement; Severability; No Waiver
This Agreement is the entire agreement between you and Rightholder and supersedes any other prior agreements,
proposals, communications or advertising, oral or written, with respect to the Software or to subject matter of this
Agreement. You acknowledge that you have read this Agreement, understand it and agree to be bound by its terms. If
any provision of this Agreement is found by a court of competent jurisdiction to be invalid, void, or unenforceable for any
reason, in whole or in part, such provision will be more narrowly construed so that it becomes legal and enforceable, and
the entire Agreement will not fail on account thereof and the balance of the Agreement will continue in full force and
effect to the maximum extent permitted by law or equity while preserving, to the fullest extent possible, its original intent.
No waiver of any provision or condition herein shall be valid unless in writing and signed by you and an authorized
representative of Rightholder provided that no waiver of any breach of any provisions of this Agreement will constitute a
waiver of any prior, concurrent or subsequent breach. Rightholder’s failure to insist upon or enforce strict performance of
any provision of this Agreement or any right shall not be construed as a waiver of any such provision or right.
13. Rightholder Contact Information
Should you have any questions concerning this Agreement, or if you desire to contact the Rightholder for any reason,
please contact our Customer Service Department at:
Kaspersky Lab ZAO, 10 build. 1, 1st Volokolamsky Proezd
Moscow, 123060
Russian Federation
Tel: +7-495-797-8700
Fax: +7-495-645-7939
E-mail: info@kaspersky.com
Web site: www.kaspersky.com
© 1997-2011 Kaspersky Lab ZAO. All Rights Reserved. The Software and any accompanying documentation are
copyrighted and protected by copyright laws and international copyright treaties, as well as other intellectual property
laws and treaties.
Page 8

8
TABLE OF CONTENTS
ABOUT THIS GUIDE ................................................................................................................................................... 10
In this document ..................................................................................................................................................... 10
Document conventions ........................................................................................................................................... 12
ADDITIONAL DATA SOURCES .................................................................................................................................. 14
Information sources for further research ................................................................................................................. 14
Contacting the Sales Department ........................................................................................................................... 15
Discussion of Kaspersky Lab applications on the Web forum ................................................................................ 15
Contacting the Documentation Development Group .............................................................................................. 15
KASPERSKY MOBILE SECURITY 9 ........................................................................................................................... 16
Distribution kit ......................................................................................................................................................... 16
Hardware and software requirements ..................................................................................................................... 17
INSTALLING KASPERSKY MOBILE SECURITY 9 ..................................................................................................... 18
UNINSTALLING THE APPLICATION .......................................................................................................................... 19
GETTING STARTED.................................................................................................................................................... 20
Activating the application ........................................................................................................................................ 20
Activating the commercial version ..................................................................................................................... 21
Activating the subscription for Kaspersky Mobile Security 9 ............................................................................. 22
Purchasing an activation code online ................................................................................................................ 22
Activating the trial version ................................................................................................................................. 23
Setting the secret code ........................................................................................................................................... 23
Enabling the option to recover the secret code ....................................................................................................... 24
Recovering the secret code .................................................................................................................................... 24
Starting the application ........................................................................................................................................... 25
Viewing information about the application .............................................................................................................. 26
MANAGING THE LICENSE ......................................................................................................................................... 27
About the License Agreement ................................................................................................................................ 27
About Kaspersky Mobile Security 9 licenses .......................................................................................................... 27
View License Information........................................................................................................................................ 28
Renewing the license ............................................................................................................................................. 29
Renewing the license with the activation code ................................ .................................................................. 29
Renewing the license online ............................................................................................................................. 30
Renewing the license by activating the subscription ......................................................................................... 30
Unsubscribing ................................................................................................................................................... 31
Renewing the subscription ................................................................................................................................ 31
APPLICATION INTERFACE ........................................................................................................................................ 31
Application menu .................................................................................................................................................... 32
Protection status window ........................................................................................................................................ 32
FILTERING OF INCOMING CALLS AND SMS ............................................................................................................ 34
About Call&SMS Filter ............................................................................................................................................ 34
About Call&SMS Filter modes ................................................................................................................................ 34
Changing the Call&SMS Filter mode ...................................................................................................................... 35
Creating the Black List ............................................................................................................................................ 35
Page 9

T A B L E O F C O N T E N T S
9
Adding entries to the Black List ......................................................................................................................... 36
Editing entries in the Black List ......................................................................................................................... 37
Deleting entries from the Black List ................................................................................................................... 38
Creating a White List .............................................................................................................................................. 38
Adding entries to the White List ........................................................................................................................ 39
Editing entries in the White List ......................................................................................................................... 40
Deleting entries from the White List .................................................................................................................. 40
Responding to SMS messages and calls from contacts not in the phone book...................................................... 41
Responding to SMS messages from non-numeric numbers................................................................................... 42
Selecting a response to incoming SMS .................................................................................................................. 42
Selecting response to incoming calls ...................................................................................................................... 43
DATA PROTECTION IN THE EVENT OF LOSS OR THEFT OF THE DEVICE .......................................................... 44
About Anti-Theft ...................................................................................................................................................... 44
Blocking the device ................................................................................................................................................. 45
Deleting personal data ............................................................................................................................................ 46
Creating a list of folders to delete ........................................................................................................................... 48
Monitoring the replacement of a SIM card on the device ........................................................................................ 49
Determining the device's geographical coordinates................................................................................................ 50
Starting Anti-Theft functions remotely ..................................................................................................................... 51
APPLICATION LOGS................................................................................................................................................... 53
About logs ............................................................................................................................................................... 53
Viewing Log records ............................................................................................................................................... 53
Deleting Log records .............................................................................................................................................. 53
CONFIGURING ADDITIONAL SETTINGS .................................................................................................................. 54
Changing the secret code ....................................................................................................................................... 54
Displaying prompts ................................................................................................................................................. 54
CONTACTING THE TECHNICAL SUPPORT SERVICE ................................ ................................ ............................. 55
GLOSSARY ................................................................................................................................................................. 56
KASPERSKY LAB ........................................................................................................................................................ 58
INFORMATION ABOUT THIRD PARTY CODE ........................................................................................................... 59
Distributed program code ....................................................................................................................................... 59
ADB .................................................................................................................................................................. 59
ADBWINAPI.DLL .............................................................................................................................................. 59
ADBWINUSBAPI.DLL ....................................................................................................................................... 59
Other information .................................................................................................................................................... 61
INDEX ................................................................................................................................................................ .......... 62
Page 10
10
ABOUT THIS GUIDE
IN THIS SECTION
In this document .............................................................................................................................................................. 10
Document conventions .................................................................................................................................................... 12
This document is the Guide for the installation, configuration and use of Kaspersky Mobile Security 9. The document is
designed for a wide audience.
Objectives of the document:
help the user independently set up the application on a mobile device, activate it and optimize the application for
their needs;
provide a rapid information search on issues connected with the application;
give information on alternative sources of information about the application and possibilities of receiving
technical support.
IN THIS DOCUMENT
The following sections are included in the document:
Additional data sources
This section describes additional sources of information about the application and Internet resources, on which users can
discuss the application, ask questions, and get answers.
Kaspersky Mobile Security 9
This section describes the application's features and provides a brief overview of its components and main functions.
This section provides information about the purpose of the distribution kit. This section lists hardware and software
requirements that a mobile device should meet to allow installation of Kaspersky Mobile Security 9.
Installing Kaspersky Mobile Security 9
This section contains instructions that can help you install the application on a mobile device.
Uninstalling the application
This section contains instructions that can help you uninstall the application from a mobile device.
Updating the application
This section contains instructions that can help you update the previous version of the application.
Page 11
A B O U T T H I S G U I D E
11
Getting started
This section provides information about how to start working with Kaspersky Mobile Security 9: activate it, set a secret
code for the application, enable the option of secret code recovery, recover the secret code, start the application, update
anti-virus databases, and scan a device for viruses.
Managing the license
This section contains information about common terms used in the framework of the application licensing. Furthermore,
the section presents information about how to find information on the Kaspersky Mobile Security 9 license and extend the
term of its validity.
Application interface
This section includes information on the main elements of the Kaspersky Mobile Security 9 interface.
File system protection
This section provides information on the Protection component which enables avoidance of infections of your device's file
system. The section also describes how to activate/stop the Protection and adjust its operation settings.
Scanning the device
This section gives information about scanning the device on demand, which can detect and remove threats on your
device. The section also describes how to launch a scan of the device, set up an automatic scheduled file system scan,
select files for scanning, and set the action that the application will take when a malicious object is detected.
Quarantining malware objects
This section provides information on the quarantine, a special folder where potential malicious objects are placed. This
section also describes how to view, restore or delete malicious objects found in the folder.
Filtering of incoming calls and SMS
This section gives information about Call&SMS Filter which prevents unwanted calls and SMS according to the Black
and White Lists you create. The section also describes how to select the mode in which Call&SMS Filter scans incoming
calls and SMS, how to configure additional filtering settings for incoming SMS and calls and also how to create Black and
White Lists.
Restricting outgoing calls and SMS messages. Parental Control
The section presents information on the Parental Control component, which allows limiting outgoing calls and SMS
messages to defined numbers. Furthermore, the section describes how to create a list of allowed and banned numbers
and set the Parental Control settings.
Data protection in the event of loss or theft of the device
This section gives information about Anti-Theft which, in the case of theft or loss, blocks unauthorized access to data
saved on your mobile device and makes it easy to find the device.
This section also specifies how to enable/disable the Anti-Theft function, set the parameters of its operation and start
Anti-Theft from another mobile device remotely.
Privacy Protection
The section presents information about Privacy Protection, which can hide the user's confidential information.
Page 12
U S E R G U I D E
12
Filtering network activity. Firewall
This section gives information about the Firewall which controls network connections on your device. This section
describes how to enable/disable the Firewall and select the required mode for it.
Encrypting personal data
This section gives information about Encryption, which can encrypt folders on the device. It also describes how to
encrypt and decrypt selected folders.
Updating the application's databases
This section provides information on updating the application databases, which ensures up-to-date protection of your
device. Furthermore, this section describes how to view information on the installed anti-virus databases, run the update
manually, and configure automatic update of anti-virus databases.
Application logs
This section presents information on logs which register the operation of every component and the execution of every
task (e.g. application database updates, virus scans).
Configuring additional settings
This section provides information on additional options of Kaspersky Mobile Security 9: how to manage the application's
sound notification and screen backlight and how to enable/disable the display of the hints, protection icon and protection
status window.
Contacting the Technical Support Service
This section contains recommendations for contacting Kaspersky Lab for help from your Personal Cabinet on the
Technical Support Service website or by phone.
Glossary
This section contains a list of terms used within the document and their respective definitions.
Kaspersky Lab
The section provides information on Kaspersky Lab ZAO.
Information about third party code
This section gives you information on third-party code used in the application.
Index
This section enables you to quickly find the required information in the document.
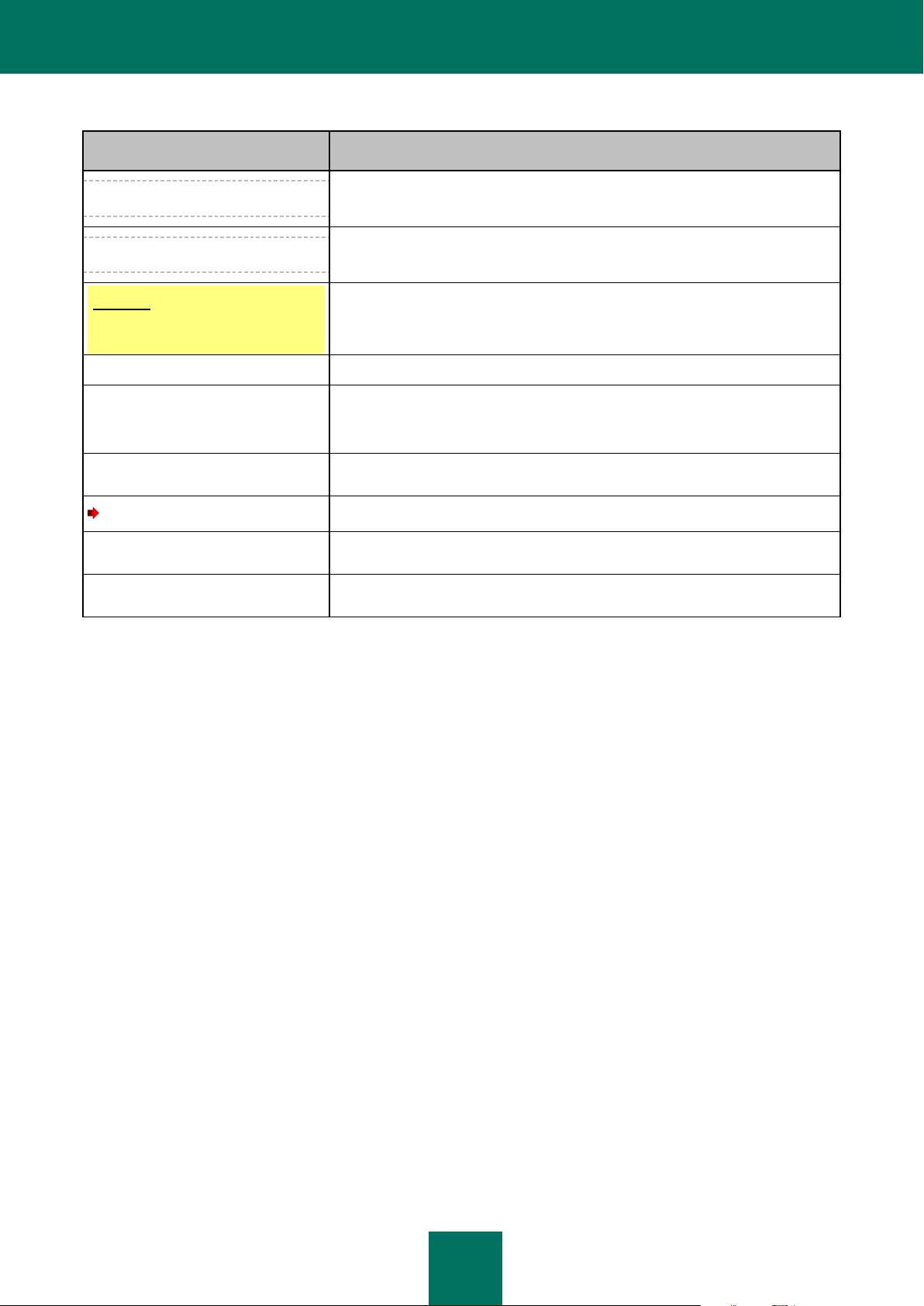
DOCUMENT CONVENTIONS
Conventions described in the table below, are used in this document.
Page 13
A B O U T T H I S G U I D E
13
SAMPLE TEXT
DOCUMENT CONVENTIONS DESCRIPTION
Note that...
Warnings are highlighted in red and enclosed in frames. Warnings contain
important information, for example, on safety-critical computer operations.
It is recommended to use...
Notes are enclosed in frames. Notes contain additional and reference
information.
Example:
...
Examples are given by section, on a yellow background, and under the heading
"Example".
Update means...
New terms are marked by italics.
ALT+F4
Names of keyboard keys appear in a bold typeface and are capitalized.
Names of the keys followed by a "plus" sign indicate the use of a key
combination.
Enable
Names of interface elements, for example, input fields, menu commands,
buttons, etc., are marked in a bold typeface.
To configure a task schedule:
Instruction introductory phrases are marked in italics.
help
Texts in the command line or texts of messages displayed on the screen have a
special font.
<IP address of your computer>
Variables are enclosed in angle brackets. Instead of variables, the corresponding
values are placed in each case (angle brackets are omitted).
Table 1. Document conventions
Page 14
14
ADDITIONAL DATA SOURCES
IN THIS SECTION
Information sources for further research ......................................................................................................................... 14
Contacting the Sales Department ................................................................................................................................... 15
Discussion of Kaspersky Lab applications on the Web forum ......................................................................................... 15
Contacting the Documentation Development Group ....................................................................................................... 15
If you have questions about setting up or using Kaspersky Mobile Security 9, you can find answers from them, using
various sources of information. You can choose the most suitable source according to how important or urgent your
request is.
INFORMATION SOURCES FOR FURTHER RESEARCH
You can view the following sources of information about the application:
the Kaspersky Lab application website;
the application's Knowledge Base page at the Technical Support Service website;
the installed Help system and hints;
the installed application documentation.
Page on Kaspersky Lab website
http://www.kaspersky.com/kaspersky_mobile_security
This page will provide you with general information about Kaspersky Mobile Security 9 and its features and options.
You can also purchase Kaspersky Mobile Security 9 at our E-Store.
The application's page at the Technical Support Service website (Knowledge Base).
http://support.kaspersky.com
This page contains articles written by experts from the Technical Support Service.
These articles contain useful information, recommendations and Frequently Asked Questions (FAQs) relating to the
purchase, installation and use of Kaspersky Mobile Security 9. They are arranged in topics, such as "Database
updates" and "Troubleshooting". The articles may answer questions about not only Kaspersky Mobile Security 9, but
other Kaspersky Lab products too. They may also contain news from the Technical Support Service.
The installed Help system
If you have any questions about specific windows or tabs in Kaspersky Mobile Security 9, you can view the context
help.
To open the context help, open the required screen and select Help.
Page 15

A D D I T I O N A L D A T A S O U R C E S
15
The installed Documentation
The User Guide contains detailed information about the application's functions and how to use Kaspersky Mobile
Security 9, together with advice and recommendations about configuring the application.
The documents are included in PDF format in the Kaspersky Mobile Security 9 distribution package.
You can also download these documents in electronic format from Kaspersky Lab's website.
CONTACTING THE SALES DEPARTMENT
If you have questions about selecting or purchasing Kaspersky Mobile Security, or extending your license, please phone
the Sales Department specialists in our Central Office in Moscow, at:
+7 (495) 797-87-00, +7 (495) 645-79-39, +7 (495) 956-70-00
The service is provided in Russian or English.
You can also send your questions to the Sales Department by email, at sales@kaspersky.com.
DISCUSSION OF KASPERSKY LAB APPLICATIONS ON THE WEB FORUM
If your question does not require an urgent answer, you can discuss it with Kaspersky Lab's specialists and other users
of Kaspersky Lab's anti-virus applications in our forum at http://forum.kaspersky.com.
In the forum you can view existing discussions, leave your comments, and create new topics, or use the search engine
for specific enquiries.
CONTACTING THE DOCUMENTATION DEVELOPMENT GROUP
If you have any questions about the documentation, or you have found an error in it, or would like to leave a comment,
please contact our User documentation development group. To contact the Documentation Development Group send an
email to docfeedback@kaspersky.com. Use the subject line: "Kaspersky Help Feedback: Kaspersky Mobile Security 9".
Page 16
16
KASPERSKY MOBILE SECURITY 9
IN THIS SECTION
Distribution kit .................................................................................................................................................................. 16
Hardware and software requirements ............................................................................................................................. 17
Kaspersky Mobile Security 9 protects mobile devices running BlackBerry OS operating system. The application controls
incoming SMS and calls and protects information on the device in case of theft or loss. Every type of threat is processed
in separate components of the program. This allows to fine-tune the application settings depending on user needs.
Kaspersky Mobile Security 9 includes the following protection components:
Call&SMS Filter. Scans all incoming SMS messages and calls for spam. The component allows the flexible
blocking of text messages and calls considered undesirable.
Anti-Theft folder. This protects information on the device from unauthorized access when it is lost or stolen and
also makes it easier to find. Anti-Theft enables you to lock your device remotely, delete any information stored
there, and pinpoint its geographic location (if your mobile device has a GPS receiver) using SMS commands
from another device. Furthermore, Anti-Theft allows you to lock your device if the SIM card is replaced or if the
device is activated without a SIM card.
Besides, the application contains a set of service features. These increase the application's possible uses, as well as
helping the user in their work:
Protection status. The status of the program's components is displayed on screen. Based on the information
presented, you can evaluate the current information protection status on your device.
Events log. Each of the program's components has its own events log, which contains information about the
component's operations (e.g. remote launch of the Anti-Theft function, status of the program's license validity
period).
Uninstalling the application. To prevent access to protected information, Kaspersky Mobile Security 9 can only
be uninstalled from the application's interface.
Kaspersky Mobile Security 9 is not intended for backup and restore.
DISTRIBUTION KIT
You can purchase Kaspersky Mobile Security 9 online, in which case the application's distribution kit and documentation
are provided in electronic form. Kaspersky Mobile Security 9 can be also purchased from all good phone and technology
retail stores. For detailed information about purchasing the application and receiving the distribution kit, please contact
our sales department at sales@kaspersky.com.
Page 17

17
HARDWARE AND SOFTWARE REQUIREMENTS
Kaspersky Mobile Security 9 can be installed on mobile devices using the BlackBerry OS 4.5, 4.6, 4.7, 5.0 and 6.0
operating systems.
Page 18
18
INSTALLING KASPERSKY MOBILE SECURITY 9
The application is installed on a mobile device in several steps.
To install Kaspersky Mobile Security 9:
1. Perform one of the following actions:
If you have purchased the program on a CD, connect the mobile device to the computer using the
BlackBerry Desktop Manager and run the automatic Kaspersky Mobile Security 9 installation on the CD
purchased.
Installation is only possible if Blackberry Desktop Manager is installed on the computer.
If you have purchased the distribution package on the Internet, perform one of the following actions on the
mobile device:
Open the message with the link to the distribution package, follow the link and download the
application distribution package to the mobile device;
Download the application distribution package at Kaspersky Lab eStore.
Installation starts automatically and the application will be installed on the device.
If you have purchased the distribution package on the Internet, you can only install the application through
the mobile device itself. In this case, installation of Kaspersky Mobile Security 9 through a computer is not
supported.
2. Run the application. To do this, select Menu Download KMS 9 and launch the application by using the
scroll bar or selecting Menu Open.
3. Set the application secret code. To this end, fill in the Enter new code and Confirm code fields and press
ENTER.
Page 19
19
UNINSTALLING THE APPLICATION
The application can only be uninstalled from the device if hiding of confidential information is disabled. Before uninstalling
the application, you should ensure that this condition is fulfilled.
To uninstall Kaspersky Mobile Security 9:
1. Disable hiding of confidential information.
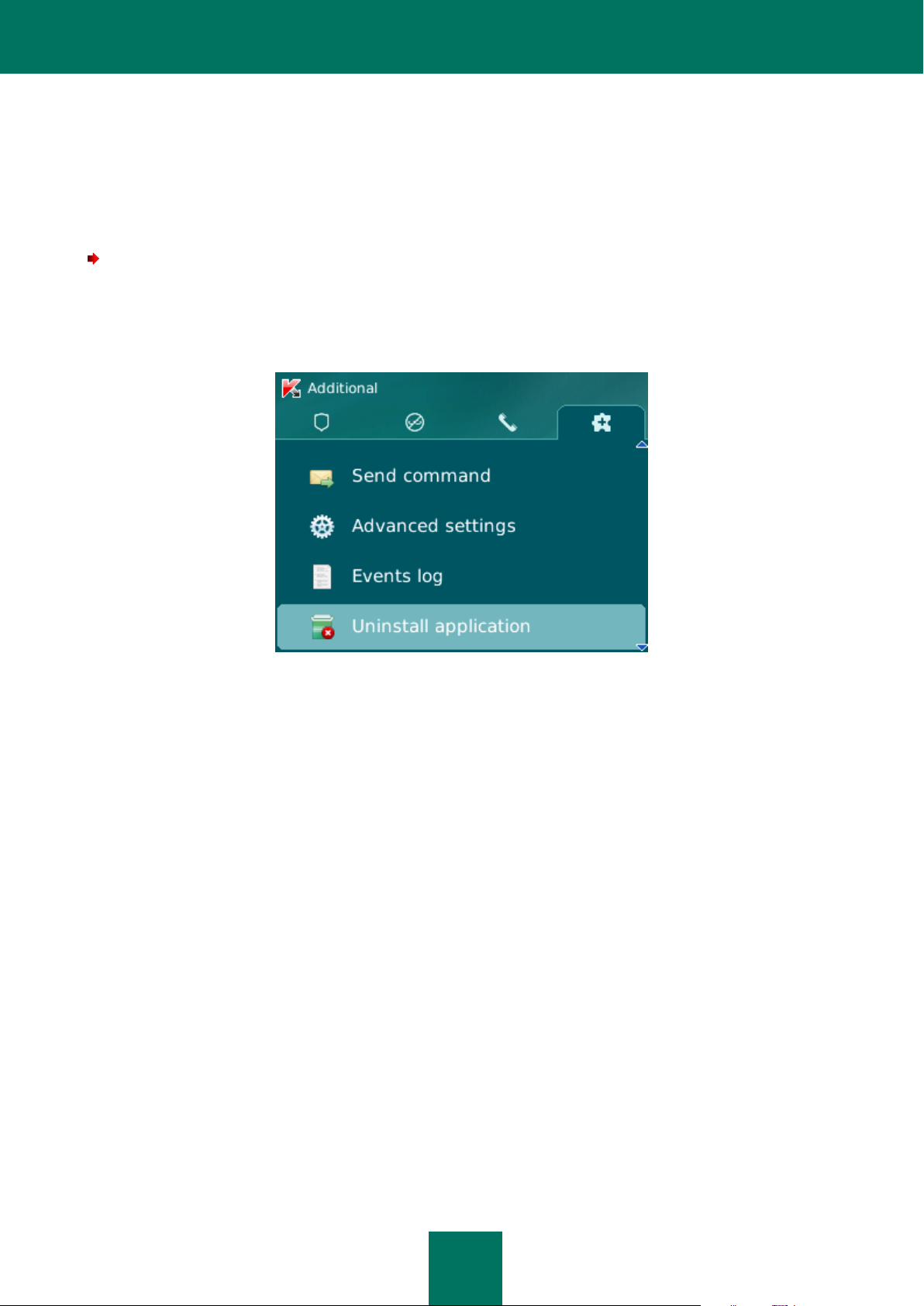
2. Uninstall Kaspersky Mobile Security 9. To do this, select Delete application on the Additional tab (see Figure
below).
Figure 1: Uninstalling the application
A confirm deletion window opens.
3. Confirm the deletion of Kaspersky Mobile Security 9 by pressing the Yes button.
The deletion of the application begins.
4. Restart the device in order to complete the uninstalling of the application.
Page 20

20
GETTING STARTED
IN THIS SECTION
Activating the application................................................................................................................................................. 20
Setting the secret code.................................................................................................................................................... 23
Enabling the option to recover the secret code ............................................................................................................... 24
Recovering the secret code ............................................................................................................................................. 24
Starting the application .................................................................................................................................................... 25
Viewing information about the application ....................................................................................................................... 26
This section provides information about how to start working with Kaspersky Mobile Security 9: activate it, set a secret
code for the application, enable the option of secret code recovery, recover the secret code and start the application.
ACTIVATING THE APPLICATION
Before starting to use Kaspersky Mobile Security 9, it needs to be activated.
To activate Kaspersky Mobile Security 9 on your device, you must have an Internet connection configured.
Before activating the application, make sure that the device's system date and time settings are correct.
You can activate the application as follows:
Activate trial license. When you activate the trial version, the application receives a free trial license. The
Activate commercial license. To activate the commercial version, you should use the activation code that you
validity period of the trial license is displayed on the screen after the activation is complete. Once the validity
period of the trial license expires, the application's functions will be limited. The following features will only be
available:
Activating the application;
managing the application license;
Kaspersky Mobile Security 9 Help system;
It is impossible to reactivate a trial version.
have received when purchasing the application. When activating the commercial version, the application
receives a commercial license, which grants you access to all the application's functions. The license validity
period is displayed on the screen of the device. Once the validity period of the trial license expires, the
application's functions will be limited.
You can obtain an activation code as follows:
online, by going from the Kaspersky Mobile Security 9 application to the special Kaspersky Lab website for
mobile devices;
Page 21

G E T T I N G S T A R T E D
21
IN THIS SECTION
Activating the commercial version ................................................................................................................................... 21
Activating the subscription for Kaspersky Mobile Security 9 ........................................................................................... 22
Purchasing an activation code online .............................................................................................................................. 22
Activating the trial version ............................................................................................................................................... 23
at Kaspersky Lab eStore (http://www.kaspersky.com/globalstore);
from Kaspersky Lab distributors.
Activate subscription. When activating the subscription, the application receives a commercial license with
subscription. The validity period of the commercial license with subscription is limited to 30 days. When the
subscription is activated, the application renews the license each 30 days. When the license is renewed, a fixed
payment for application use specified at the subscription activation, is written off from your personal account.
The funds are debited by sending a payable SMS message. Once the funds are debited, the application
receives a new license from the activation server, with a subscription which grants access to all functions of the
application. You can cancel the subscription for Kaspersky Mobile Security 9. In this case, when the current
license expires, the application's functionality becomes limited.
ACTIVATING THE COMMERCIAL VERSION
To activate the commercial version of the application with the activation code:
1. Open the device’s main menu.
2. Select the folder Download KMS 9.
The application installation folder may vary depending on the mobile device model.
3. Start the application. To do this, use the scroll bar or select Menu Open.
4. Select Enter activation code.
The Kaspersky Mobile Security 9 activation window opens.
5. Enter the activation code that you have received when purchasing the application and press Activate.
6. Confirm the connection to the Internet by pressing Yes.
The application will send a request to the Kaspersky Lab activation server and receive a license. When the
license is successfully received, information about it will be displayed on the screen.
If the activation code you entered is invalid for any reason, an information message is displayed on the screen.
In such a case, we recommend checking that the entered activation code is correct and contact the software
vendor you have purchased Kaspersky Mobile Security 9 from.
If any errors have occurred when connecting to the server and no license has been received, the activation is
canceled. In this event, it is recommended verifying the parameters of connecting to the Internet. If it was not
possible to rectify the errors, contact Technical Support.
7. Go to setting the application secret code.
Page 22

U S E R G U I D E
22
ACTIVATING THE SUBSCRIPTION FOR KASPERSKY MOBILE SECURITY 9
To activate the subscription, an Internet connection should be established on the device.
To activate the subscription for Kaspersky Mobile Security 9:
1. Open the device’s main menu.
2. Select the folder Download KMS 9.
The application installation folder may vary depending on the mobile device model.
Start the application. To do this, use the scroll bar or select Menu Open.
3. Select One-Click Buy.
4. Confirm the connection to the Internet by pressing Yes.
The application will check if the subscription service is accessible to the mobile service provider that you use. If
the subscription service is available, the Activation screen opens, displaying information about the terms of
subscription.
If the subscription service cannot be provided, the application will notify you of this and switch back to the
screen on which you can select another way of activating the application.
5. Read through the terms of subscription and then confirm the activation of subscription for Kaspersky Mobile
Security 9 by pressing Activate.
The application will send a payable SMS and then receive a license from the activation server of Kaspersky
Lab. When the subscription becomes activated, Kaspersky Mobile Security 9 will notify you of this.
If your balance has not enough funds to send a payable SMS message, the subscription activation will be
canceled.
If any errors have occurred when connecting to the server and no license has been received, the activation is
canceled. In this event, it is recommended verifying the parameters of connecting to the Internet. If it was not
possible to rectify the errors, contact Technical Support.
If you do not agree the terms of subscription, press Cancel. In this case, the application cancels the
subscription activation and goes back to the screen in which you can reselect the way of activating the
application.
6. On completing the activation go to setting the secret code.
PURCHASING AN ACTIVATION CODE ONLINE
In order to purchase an activation code for the application online, perform the following steps:
1. Open the device’s main menu.
2. Select the folder Download KMS 9.
The application installation folder may vary depending on the mobile device model.
Start the application. To do this, use the scroll bar or select Menu Open.
Page 23

G E T T I N G S T A R T E D
23
3. Select Buy online.
This will open the Buy online window.
4. Press Open.
A special Kaspersky Lab website for mobile devices opens, on which you will be offered to order the license
renewal.
5. Follow the step-by-step instructions.
6. After you are done with purchasing an activation code, proceed with (see section "Activating the commercial
version" on page 21).
ACTIVATING THE TRIAL VERSION
To activate the trial version of Kaspersky Mobile Security 9:
1. Open the device’s main menu.
2. Select the folder Download KMS 9.
The application installation folder may vary depending on the mobile device model.
Start the application. To do this, use the scroll bar or select Menu Open.
3. Select Trial version.
4. Confirm the connection to the Internet by pressing Yes.
The application will send a request to the Kaspersky Lab activation server and receive a license.
If any errors have occurred when connecting to the server and no license has been received, the activation is
canceled. In this event, it is recommended verifying the parameters of connecting to the Internet. If it was not
possible to rectify the errors, contact Technical Support.
5. Go to setting the application secret code.
SETTING THE SECRET CODE
After starting the application you will be asked to enter the application secret code. Application secret code prevents any
unauthorized access to the application settings.
You can later change the secret code installed.
Kaspersky Mobile Security 9 requests the secret code in the following circumstances:
for access to the application;
when sending an SMS command from another mobile device to start the following functions remotely: Block,
Data Wipe, SIM Watch, GPS Find.
The secret code is comprised of numerals. The minimum number of characters is four.
If you forget the application secret code, you can restore it (see the "Recovering the secret code" section on page 24).
For this purpose, the recovery of secret code option must be enabled in advance (see the "Enabling the option to recover
the secret code" section on page 24).
Page 24

U S E R G U I D E
24
To enter the secret code:
1. Confirm that you wish to create an application secret code. To do this, after the application first launches, press
OK.
The screen for entering the application secret code opens.
2. Enter the figures that will form your code in the Enter new code field.
3. Re-enter the same code in the Confirm code field.
4. Press ENTER on the keyboard.
The code entered is automatically verified.
If the secret code entered is valid, the protection status window opens.
If the code is deemed invalid according to the results of the verification, a warning message is displayed and the
application requests confirmation. To use the code, press Yes.
In order to create a new code, press No. The Enter new code and Confirm code fields will empty. Enter a new
application secret code.
ENABLING THE OPTION TO RECOVER THE SECRET CODE
After the initial activation of the application, you can enable the option of secret code recovery. Then, in the future, you
will be able to recover the secret code if it is forgotten.
If you have canceled the option enabling during the initial activation of the application, you can enable it after
reinstallation of Kaspersky Mobile Security 9 on the device.
You can only recover the application secret code (see the "Recovering the secret code" section on page 24) if the
recovery of secret code option is enabled. If you forget the password, and the recovery of secret code option is disabled,
it will not be possible to manage the functions of Kaspersky Mobile Security 9.
To enable the recovery of secret code option:
1. After you have installed the secret code for the application (see the "Setting the secret code" section on
page 23) enter your email address on the Enabling the option to recover the secret code screen.
2. Confirm the enabling of the option of secret code recovery, by clicking Enable.
The email address that you give will be used during recovery of the secret code.
The application will establish an Internet connection with the secret code recovery server, send the information
entered and enable the recovery of secret code option.
RECOVERING THE SECRET CODE
You can only recover the secret code enabling the recovery of secret code option in advance (see "Enabling the option to
recover the secret code" on page 24).
To recover the application secret code:
1. Open the device’s main menu.
Page 25

G E T T I N G S T A R T E D
25
2. Select the folder Download KMS 9.
The application installation folder may vary depending on the mobile device model.
Start the application. To do this, use the scroll bar or select Menu Open.
3. Press Menu Secret code recovery.
The following information will then be displayed on the screen:
Kaspersky Lab website for recovery of secret code;
device identification code.
4. Press Go.
The website http://mobile.kaspersky.com/recover-code opens to recover the secret code.
5. Enter the following information in the appropriate fields:
the email address that you previously designated for recovery of the secret code;
device identification code.
As a result, the recovery code will be sent to the email address that you indicated.
6. Go to Kaspersky Mobile Security 9 screen.
7. Press Menu Enter recovery code and enter the recovery code that you have received.
8. Enter the new application secret code. To do this, enter a new application secret code in the field Enter new
code and Confirm code.
9. Press ENTER on the keyboard.
The code entered is automatically verified.
If the secret code entered is valid, the protection status window opens.
If the code is deemed invalid according to the results of the verification, a warning message is displayed and the
application requests confirmation. To use the code, press Yes.
In order to create a new code, press No. The Enter new code and Confirm code fields will empty. Enter a new
application secret code.
STARTING THE APPLICATION
To start Kaspersky Mobile Security 9:
1. Open the device’s main menu.
2. Select the folder Download KMS 9.
The application installation folder may vary depending on the mobile device model.
3. Start the application. To do this, use the scroll bar or select Menu Open.
4. Enter the secret code of the application and press OK.
Page 26

U S E R G U I D E
26
The application displays a window showing the current status of Kaspersky Mobile Security 9.
VIEWING INFORMATION ABOUT THE APPLICATION
You can view general information about Kaspersky Mobile Security 9 and its version.
To view information on the application,
on the Additional tab, select About.
Page 27

27
MANAGING THE LICENSE
IN THIS SECTION
About the License Agreement ......................................................................................................................................... 27
About Kaspersky Mobile Security 9 licenses ................................................................................................................... 27
View License Information ................................ ................................ ................................................................................ 28
Renewing the license ...................................................................................................................................................... 29
In the context of licensing Kaspersky Lab applications, it is important to know these terms below:
License Agreement;
license.
These terms are inseparably interlinked and constitute a single licensing pattern. Let us have a closer look at every term.
Furthermore, the section presents information about how to find information on the Kaspersky Mobile Security 9 license
and extend the term of its validity.
ABOUT THE LICENSE AGREEMENT
The License Agreement is an agreement between a private individual or a legal entity which legally owns a copy of
Kaspersky Mobile Security 9 and Kaspersky Lab. The agreement is included in every Kaspersky Lab application. It
stated detailed information on the rights and limitations on using Kaspersky Mobile Security.
In accordance with the License Agreement, when purchasing and installing a Kaspersky Lab application, you obtain the
unlimited right to owning its copy.
Kaspersky Lab also provides you with additional services:
technical support;
updating of Kaspersky Mobile Security 9 anti-virus databases;
updating of Kaspersky Mobile Security 9 program modules.
In order to benefit, you must purchase and activate a license.
ABOUT KASPERSKY MOBILE SECURITY 9 LICENSES
A license is the right to use Kaspersky Mobile Security 9 and the additional services associated with it as provided by
Kaspersky Lab or its partners.
Every license has a validity period and type.
License term – a period during which the additional services are offered:
technical support;
Page 28

U S E R G U I D E
28
updating of Kaspersky Mobile Security 9 anti-virus databases;
updating of Kaspersky Mobile Security 9 program modules.
The scope of services provided depends on the license type.
The following license types are available:
Trial—free license with a limited validity period, for example, 30 days, offered to get acquainted with Kaspersky
Mobile Security 9.
The trial license can only be used once.
If you have a trial license, you can only contact Technical Support Service if your question is about activating
the product or purchasing a commercial license. As soon as the Kaspersky Mobile Security 9 trial license
expires, all features become disabled. To proceed with the application, you should activate it.
Commercial—paid license with a limited validity period (for example, one year), provided upon purchase of
Kaspersky Mobile Security 9.
If a commercial license is activated, all application features and additional services are available.
On termination of the validity period of the commercial license, some functions of Kaspersky Mobile Security 9
become inaccessible, and the application databases will not be updated. One week before the license expiration
date, the application will notify you of this event so you could renew the license in advance.
Commercial with subscription – paid license with an option to renew it in automatic or manual mode. A license
with subscription is distributed by service providers.
The subscription is valid for a limited period (30 days). After the subscription expires, it can be renewed
manually or automatically. Method of renewing the subscription depends on the legislation and mobile service
provider. The subscription is renewed automatically subject to timely prepayment to the provider.
In this case, the fixed amount specified in the terms of subscription is debited from your personal account.
Funds are debited from your personal account after you send a payable SMS message to the number of the
service provider.
If the subscription is not renewed, Kaspersky Mobile Security 9 stops updating the application databases, and
the application's functionality becomes limited.
When using the subscription, you can activate the commercial license with an activation code. In this case, the
subscription will be canceled automatically.
When using the commercial license, you can activate the subscription. If already have an activated license with
a limited term at the time of subscription activation, it is substituted with the subscription license.
VIEW LICENSE INFORMATION
You can view the following license information: license number, type, activation date, expiration date, number of days to
expiration and device serial number.
To view the license information:
1. Select the Additional tab.
2. Select the item License About license.
This will open the About license window.
Page 29

M A N A G I N G T H E L I C E N S E
29
IN THIS SECTION
Renewing the license with the activation code ................................................................................................................ 29
Renewing the license online ............................................................................................................................................ 30
Renewing the license by activating the subscription ....................................................................................................... 30
Unsubscribing ................................................................................................................................................................. 31
Renewing the subscription .............................................................................................................................................. 31
RENEWING THE LICENSE
Kaspersky Mobile Security 9 allows you to renew the application license.
The license can be extended in one of the following ways:
Enter activation code - activate the application with the activation code. You can purchase the activation code at
http://www.kaspersky.com/globalstore, or from your local Kaspersky Lab distributor.
Buy activation code online – go to the website visited from your mobile device, and purchase an activation code
online.
Subscribe for Kaspersky Mobile Security 9 – activate the subscription in order to renew the license each 30
days.
To activate the application on your mobile device, you must have an Internet connection configured.
RENEWING THE LICENSE WITH THE ACTIVATION CODE
To renew the license with the activation code:
1. Open the Additional tab.
2. Select the item License Enter activation code.
3. Enter the activation code obtained in four fields and then select Next.
4. Confirm establishing Internet connection by pressing Yes.
This will open the Activation window.
The application will send a request to the Kaspersky Lab activation server and receive a license. When the
license is successfully received, information about it will be displayed on the screen.
If the activation code you entered is invalid for any reason, an information message is displayed on the screen.
In such a case, we recommend checking that the entered activation code is correct and contact the software
vendor you have purchased Kaspersky Mobile Security 9 from.
If any errors have occurred when connecting to the server and no license has been received, the activation is
canceled. In this event, it is recommended verifying the parameters of connecting to the Internet. If it was not
possible to rectify the errors, contact Technical Support.
5. On completion, press OK.
Page 30

U S E R G U I D E
30
RENEWING THE LICENSE ONLINE
To renew your license online:
1. Select the Additional tab.
2. Select the item License Buy online.
This will open the Buy online window.
3. Press Open.
A website opens, which offers you to order the license renewal.
If the license has expired, a special Kaspersky Lab website for mobile devices opens on which you can buy an
activation code online.
4. Follow the step-by-step instructions.
5. When the order to renew the license is processed, enter the activation code obtained (see the "License renewal
with activation code" section on page 29).
RENEWING THE LICENSE BY ACTIVATING THE SUBSCRIPTION
In the Additional menu, you can extend the license validity term by activating the subscription (see the "About Kaspersky
Mobile Security 9 licenses" section on page 27) for Kaspersky Mobile Security 9. When the subscription is activated,
Kaspersky Mobile Security 9 renews the license each 30 days. Every time the license is renewed, the fixed amount
specified in the terms of subscription is debited from your personal account.
To activate the subscription for Kaspersky Mobile Security 9 on your device, you should have an Internet connection
established.
To activate the subscription for Kaspersky Mobile Security 9:
1. Open the Additional tab.
Select the item License One-Click Buy.
2. Confirm the connection to the Internet by pressing Yes.
The application will check if the subscription service is accessible to the mobile service provider that you use.
If the subscription service is available, the Activation screen opens, displaying information about the terms of
subscription.
If the subscription service cannot be provided, the application will inform you of this event and switch back to the
screen on which you can select another method of renewing the license. The subscription activation will be
canceled.
3. Read through the terms of subscription and then confirm the activation of subscription for Kaspersky Mobile
Security 9 by pressing Next.
The application will send a payable SMS and then receive a license from the activation server of Kaspersky
Lab. When the subscription becomes activated, Kaspersky Mobile Security 9 will notify you of this.
If your balance has not enough funds to send a payable SMS message, the subscription activation will be
canceled.
Page 31

A P P L I C A T I O N I N T E R F A C E
31
If any errors have occurred when connecting to the server and no license has been received, the activation is
canceled. In this event, it is recommended verifying the parameters of connecting to the Internet. If it was not
possible to rectify the errors, contact Technical Support.
If you do not agree the terms of subscription, press Cancel. In this case, the application will cancel the
subscription activation and switch back to the screen on which you can select another method of renewing the
license.
4. On completion, press OK.
UNSUBSCRIBING
You can cancel the subscription for Kaspersky Mobile Security 9. In this case, Kaspersky Mobile Security 9 will not
renew the license each 30 days. When the current license expires, the application's functionality becomes limited, and
the application databases are no longer updated.
If you have canceled your subscription, you can resume it (see section "Renewing the subscription" on page 31).
To unsubscribe for Kaspersky Mobile Security 9:
1. Select the Additional tab.
2. Select the item License Unsubscribe.
3. Confirm the subscription cancellation by pressing Yes.
Kaspersky Mobile Security 9 will notify you of cancellation of the subscription.
RENEWING THE SUBSCRIPTION
If you have canceled the subscription, you can resume it. In this case, Kaspersky Mobile Security 9 will renew the license
every 30 days.
When resuming the subscription, funds are only debited from your personal account if the current license expires sooner
than in three days.
To resume the subscription:
1. Open the Additional tab.
2. Select the item License One-Click Buy.
If your current license has expired, Kaspersky Mobile Security 9 will offer you to activate the subscription again (see
section "Renewing the license by activating the subscription" on page 30).
If the current license has not expired yet, Kaspersky Mobile Security 9 resumes the subscription and renews it each 30
days after the current license expires.
APPLICATION INTERFACE
This section includes information on the main elements of the Kaspersky Mobile Security 9 interface.
Page 32

U S E R G U I D E
32
IN THIS SECTION
Application menu ............................................................................................................................................................. 32
Protection status window................................................................................................................................................. 32
APPLICATION MENU
The application components are arranged logically and are accessible on the application tabs. Every tab ensures access
to the settings of the component selected and its tasks.
The Kaspersky Mobile Security 9 menu contains the following tabs:
Protection status – shows the status of all application components.
Anti-Theft – protection of information on the device in the event of theft or loss.
Call&SMS Filter – filtering of unwanted incoming calls and SMS.
Additional – general application settings, start of synchronization of the device with the remote administration
system, uninstalling the application, information about application and license.
You can switch between tabs by using the scroll bar.
PROTECTION STATUS WINDOW
The status of the main application components is displayed in the protection status window (see Figure below).
Figure 2: Current status window
The status window is immediately accessible after starting the application and contains the following information:
Call&SMS Filter – mode for checking calls and SMS (see the "Filtering of incoming calls and SMS" section on
page 34).
Block, Data Wipe, SIM Watch, GPS Find represent the Anti-Theft status (see Section "Data protection in the
event of loss or theft of the device" on page 44).
Page 33

A P P L I C A T I O N I N T E R F A C E
33
The On status means that the Anti-Theft function is enabled. The Off status means that the Anti-Theft function
is disabled.
The protection status window is displayed when the application launches. You can also go to the protection status
window by selecting the Protection status tab.
Page 34

34
FILTERING OF INCOMING CALLS AND SMS
IN THIS SECTION
About Call&SMS Filter..................................................................................................................................................... 34
About Call&SMS Filter modes ......................................................................................................................................... 34
Changing the Call&SMS Filter mode ............................................................................................................................... 35
Creating the Black List .................................................................................................................................................... 35
Creating a White List ....................................................................................................................................................... 38
Responding to SMS messages and calls from contacts not in the phone book .............................................................. 41
Responding to SMS messages from non-numeric numbers ........................................................................................... 42
Selecting a response to incoming SMS ........................................................................................................................... 42
Selecting response to incoming calls .............................................................................................................................. 43
This section gives information about Call&SMS Filter which prevents unwanted calls and SMS according to the Black
and White Lists you create. The section also describes how to select the mode in which Call&SMS Filter scans incoming
calls and SMS, how to configure additional filtering settings for incoming SMS and calls and also how to create Black and
White Lists.
ABOUT CALL&SMS FILTER
Call&SMS Filter prevents unwanted calls and SMS to be delivered based on the Black List and White List that you have
compiled.
The lists consist of entries. An entry in either list contains the following information:
The telephone number, from which Call&SMS Filter blocks any information if the number is on the Black List
and delivers any information if the number is on the White List.
The type of event that Call&SMS Filter blocks if it is on the Black List and delivers if it is on the White List. The
following types of communications are available: calls and SMS, calls only, and SMS only.
The key phrase used by Call&SMS Filter to identify wanted and unwanted SMS. For the Black List, Call&SMS
Filter blocks SMS, which contain this phrase, while delivering the ones, which do not contain it. For the White
Anti-Spam filters calls and messages as prescribed by the selected mode (see the "About Call&SMS Filter modes"
section on page 34). According to the mode, Call&SMS Filter scans every incoming SMS or call and then determines
whether this SMS or call is wanted or unwanted (spam). As soon as Call&SMS Filter assigns the wanted or unwanted
status to an SMS or call, the scan is finished.
Information about blocked SMS and calls is registered in the application's log (see section "Application logs" on page 53).
List, Call&SMS Filter delivers SMS, which contain this phrase, while blocking the ones, which do not contain it.
ABOUT CALL&SMS FILTER MODES
The mode defines the rules according to which Call&SMS Filter filters incoming calls and SMS.
Page 35

F I L T E R I N G O F I N C O M I N G C A L L S A N D S M S
35
The following Call&SMS Filter modes are available:
Off – all incoming calls and SMS are allowed.
Black List – all calls and SMS are allowed except those originating from numbers on the Black List.
White List – only calls and SMS originating from numbers on the White List are allowed.
Both lists – incoming calls and SMS from White List numbers are allowed while those from Black List numbers
are blocked. Following a conversation with or the reading of an SMS from a number on neither list, Call&SMS
Filter will prompt you to enter the number in either one of the lists.
You can change the Call&SMS Filter mode (see the "Changing the Call&SMS Filter mode" section on page 35). The
current Call&SMS Filter mode is displayed on the Call&SMS Filter tab next to the item Mode.
CHANGING THE CALL&SMS FILTER MODE
To change the mode of Call&SMS Filter:
1. On the Call&SMS Filter tab, select the menu item Mode.
The Call&SMS Filter opens.
2. Select the value for the setting Call&SMS Filter mode (see figure above).
Figure 3: Changing the Call&SMS Filter mode
3. Select Menu Save to save the changes.
CREATING THE BLACK LIST
The Black List contains entries of banned numbers, i.e., the numbers from which Call&SMS Filter blocks calls and SMS.
Each entry contains the following information:
Telephone number from which Call&SMS Filter blocks calls and / or SMS.
Types of events that Call&SMS Filter blocks from this number. The following types of events are available: calls
and SMS, calls only, and SMS only.
Key phrase that Call&SMS Filter uses to classify an SMS as unsolicited (spam). Call&SMS Filter only blocks
SMS containing the key phrase, while delivering all other SMS.
Page 36

U S E R G U I D E
36
Call&SMS Filter blocks calls and SMS that comply with all the criteria of an entry on the Black List. Calls and SMS that
IN THIS SECTION
Adding entries to the Black List ....................................................................................................................................... 36
Editing entries in the Black List ....................................................................................................................................... 37
Deleting entries from the Black List ................................................................................................................................. 38
fail to comply with even one of the criteria of an entry on the Black List will be allowed by Call&SMS Filter.
You cannot add a phone number with identical filtering criteria to both the Black List and the White List.
Information about blocked SMS and calls is registered in the log (see the "Application logs" section on page 53).
ADDING ENTRIES TO THE BLACK LIST
Bear in mind that the same number with identical filtering criteria cannot be included in the Black and White Lists of
Call&SMS Filter numbers at the same time. If a number with such filtering criteria is already saved on either of the lists,
Kaspersky Mobile Security 9 will notify you of this event, and a relevant message will appear on the screen.
To add an entry to the Call&SMS Filter Black List:
1. Select Black List in the Call&SMS Filter tab.
This will open the Black List window.
2. Select Menu Add.
This will open the New entry window.
3. Set values for the following settings (see Figure below):
Block incoming – type of event from a telephone number which Call&SMS Filter blocks for Black List
numbers:
Calls and SMS: block incoming calls and SMS messages.
Calls only: block incoming calls only.
SMS only: block incoming SMS messages only.
Phone number – telephone number for which Call&SMS Filter blocks incoming information. The phone
number should comprise only alphanumeric characters; it may begin with a digit, a letter, or be preceded by
the "+" symbol. As a number, it is also possible to use the masks "*" or "?" (where "*" is any amount of
symbols, and "?" any one symbol). For example, *1234? on the Black List. Call&SMS Filter blocks calls or
SMS from a number in which any symbol follows the figure 1234.
Containing text – key phrase indicating that the received SMS message is unwanted (spam). Call&SMS
Filter only blocks SMS containing the key phrase, while delivering all other SMS.
If you want all incoming SMS from a specific number on the Black List to be blocked, leave this entry’s
Containing text field blank.
Page 37

F I L T E R I N G O F I N C O M I N G C A L L S A N D SM S
37
Figure 4: Settings for entries in the Black List
4. Select Menu Save to save the changes.
EDITING ENTRIES IN THE BLACK LIST
You can change the values of all settings for entries from the Black List.
To edit an entry in the Call&SMS Filter Black List:
1. Select Black List in the Call&SMS Filter tab.
This will open the Black List window.
2. Select the element from the list which you wish to edit and then select Menu Edit.
The Changing an entry screen opens.
3. Change the necessary settings:
Block incoming – type of event from a telephone number which Call&SMS Filter blocks for Black List
numbers:
Calls and SMS: block incoming calls and SMS messages.
Calls only: block incoming calls only.
SMS only: block incoming SMS messages only.
Phone number – telephone number for which Call&SMS Filter blocks incoming information. The phone
number should comprise only alphanumeric characters; it may begin with a digit, a letter, or be preceded by
the "+" symbol. As a number, it is also possible to use the masks "*" or "?" (where "*" is any amount of
symbols, and "?" any one symbol). For example, *1234? on the Black List. Call&SMS Filter blocks calls or
SMS from a number in which any symbol follows the figure 1234.
Containing text – key phrase indicating that the received SMS message is unwanted (spam). Call&SMS
Filter only blocks SMS containing the key phrase, while delivering all other SMS.
If you want all incoming SMS from a specific number on the Black List to be blocked, leave this entry’s
Containing text field blank.
4. Select Menu Save to save the changes.
Page 38

U S E R G U I D E
38
IN THIS SECTION
Adding entries to the White List ....................................................................................................................................... 39
Editing entries in the White List ....................................................................................................................................... 40
Deleting entries from the White List ................................................................................................................................ 40
DELETING ENTRIES FROM THE BLACK LIST
You can delete a number from the Black list. Furthermore, you can clear the Call&SMS Filter Black List by removing all
the entries from it.
To delete an entry from the Call&SMS Filter Black List:
1. Select Black List in the Call&SMS Filter tab.
This will open the Black List window.
2. Select the entry to be deleted on the list and then select Menu Delete.
The confirmation window opens.
3. Confirm the uninstalling by pressing the Yes button.
To clear the Call&SMS Filter Black List:
1. Select Black List in the Call&SMS Filter tab.
This will open the Black List window.
2. Select Menu Delete all.
The confirmation window opens.
3. Confirm the uninstalling by pressing the Yes button.
The list is emptied.
CREATING A WHITE LIST
The White List contains entries of allowed numbers, i.e., numbers from which Call&SMS Filter delivers calls and SMS to
the user. Each entry contains the following information:
Telephone number from which Call&SMS Filter delivers calls and / or SMS.
Types of events that Call&SMS Filter delivers from this number. The following types of events are available:
calls and SMS, calls only, and SMS only.
Key phrase used by Call&SMS Filter to classify an SMS as solicited (not spam). Call&SMS Filter only delivers
SMS containing the key phrase, while blocking all other SMS.
Call&SMS Filter allows only calls and SMS that comply with all the criteria of an entry on the White List. Calls and SMS
that fail to comply with even one of the criteria of an entry on the White List will be blocked by Call&SMS Filter.
Page 39

F I L T E R I N G O F I N C O M I N G C A L L S A N D SM S
39
ADDING ENTRIES TO THE WHITE LIST
Bear in mind that the same number with identical filtering criteria cannot be included in the Black and White Lists of
Call&SMS Filter numbers at the same time. If a number with such filtering criteria is already saved on either of the lists,
Kaspersky Mobile Security 9 will notify you of this event, and a relevant message will appear on the screen.
To add an entry to the Call&SMS Filter White List:
1. On the Call&SMS Filter tab, select the White List.
This will open the White List window.
2. Select the Menu Add.
3. Make the following settings for the new entry (see Figure below):
Allow incoming – type of event from a telephone number which Call&SMS Filter allows for Black List
numbers:
Calls and SMS: allow incoming calls and SMS messages.
Calls only: allow incoming calls only.
SMS only: allow incoming SMS messages only.
Phone number – telephone number for which Call&SMS Filter blocks incoming information.. The phone
number should comprise only alphanumeric characters; it may begin with a digit, a letter, or be preceded by
the "+" symbol. As a number, it is also possible to use the masks "*" or "?" (where "*" is any amount of
symbols, and "?" any one symbol). For example, *1234? in the White List. Call&SMS Filter delivers calls or
SMS from a number in which any symbol follows the figure 1234.
Containing text – key phrase indicating that the received SMS message is wanted. For numbers on the
White List, Call&SMS Filter only delivers SMS messages containing the key phrase and blocks all others.
If you want all incoming SMS from a specific number on the White List to be delivered, leave this entry’s
Containing text field blank.
Figure 5: Settings for entries in the White List
4. Select Menu Save to save the changes.
Page 40

U S E R G U I D E
40
EDITING ENTRIES IN THE WHITE LIST
For an entry from the White list of allowed numbers, you can change the values of all settings.
To edit an entry in the Call&SMS Filter White List:
1. On the Call&SMS Filter tab, select the White List.
This will open the White List window.
2. Select the element from the list which you wish to edit and then select Menu Edit.
The Changing an entry screen opens.
3. Change the necessary settings:
Allow incoming – type of event from a telephone number which Call&SMS Filter allows for Black List
numbers:
Calls and SMS: allow incoming calls and SMS messages.
Calls only: allow incoming calls only.
SMS only: allow incoming SMS messages only.
Phone number – telephone number for which Call&SMS Filter blocks incoming information.. The phone
number should comprise only alphanumeric characters; it may begin with a digit, a letter, or be preceded by
the "+" symbol. As a number, it is also possible to use the masks "*" or "?" (where "*" is any amount of
symbols, and "?" any one symbol). For example, *1234? in the White List. Call&SMS Filter delivers calls or
SMS from a number in which any symbol follows the figure 1234.
Containing text – key phrase indicating that the received SMS message is wanted. For numbers on the
White List, Call&SMS Filter only delivers SMS messages containing the key phrase and blocks all others.
If you want all incoming SMS from a specific number on the White List to be delivered, leave this entry’s
Containing text field blank.
4. Select Menu Save to save the changes.
DELETING ENTRIES FROM THE WHITE LIST
You can delete one entry from the White List as well as completely clear it.
To delete an entry from the Call&SMS Filter White List:
1. On the Call&SMS Filter tab, select the White List.
This will open the White List window.
2. Select the entry to be deleted on the list and then select Menu Delete.
The confirmation window opens.
3. Confirm the uninstalling by pressing the Yes button.
To clear the Call&SMS Filter White List:
1. On the Call&SMS Filter tab, select the White List.
Page 41

F I L T E R I N G O F I N C O M I N G C A L L S A N D SM S
41
This will open the White List window.
2. Press Menu Delete all.
The confirmation window opens.
3. Confirm the uninstalling by pressing the Yes button.
The White List is emptied.
RESPONDING TO SMS MESSAGES AND CALLS FROM
CONTACTS NOT IN THE PHONE BOOK
If the Both lists or White List modes (see the "About Call&SMS Filter modes" section on page 34) are selected for
Call&SMS Filter, you can additionally set a response from Call&SMS Filter to SMS and calls from subscribers, whose
numbers are not saved in Contacts. In addition, Call&SMS Filter allows expansion of the White List by adding numbers
from the list of contacts to it.
To select Call&SMS Filter's response to a number not included in the phonebook:
1. Select the Mode menu item on the Call&SMS Filter tab.
The Call&SMS Filter opens.
2. Select the required value for setting Allow Contacts (see Figure below):
for Call&SMS Filter to count numbers from Contacts as additional White List and block SMS messages and
calls from subscribers not in Contacts, check the Allow Contacts box;
in order for Call&SMS Filter to filter SMS messages and calls based on the Call&SMS Filter mode set,
uncheck the Allow contacts box.
Figure 6: Call&SMS Filter response to numbers not included in the device's phone book
3. Select Menu Save to save the changes.
Page 42

U S E R G U I D E
42
RESPONDING TO SMS MESSAGES FROM NON-NUMERIC
NUMBERS
If the Call&SMS Filter mode Both lists or Black List is selected (see the "About Call&SMS Filter modes" section on
page 34), you can also expand the Black List by including all non-numeric numbers (including letters). In this case,
Call&SMS Filter processes calls and SMS messages from non-numeric numbers the same way as from numbers on the
Black List.
To set Call&SMS Filter's response when receiving messages from non-numeric numbers:
1. On the Call&SMS Filter tab, select the menu item Mode.
2. The Call&SMS Filter opens.
3. Select a value for the Block non-numeric numbers setting (see Figure below):
in order for Call&SMS Filter to block SMS from non-numeric numbers, check the Block non-numeric
numbers box;
In order for Call&SMS Filter to filter SMS from non-numeric numbers on the basis of the Anti-Spam mode
set, uncheck the Block non-numeric numbers box.
SELECTING A RESPONSE TO INCOMING SMS
In Both lists mode (see the "About Call&SMS Filter modes" section on page 34), Call&SMS Filter checks incoming
SMS against the Black and White lists.
After receiving an SMS message from a number that is not included on either list, Call&SMS Filter will prompt you to
enter the number in one of the lists (see Figure below).
You can select one of the following actions to be performed in respect of the SMS:
Figure 7: Configuring Call&SMS Filter action when receiving SMS messages from non-numeric numbers
4. Select Menu Save to save the changes.
To block the SMS message and add the sender's telephone number to the Black List, select Add to Black List.
To deliver the SMS message and add the sender's telephone number to the White List, select Add to White
List.
Page 43

F I L T E R I N G O F I N C O M I N G C A L L S A N D SM S
43
To deliver the SMS message without adding the sender's telephone number to either list, press Skip.
Figure 8: Call&SMS Filter notification about the receipt of an SMS
Information about blocked SMS is registered in the application's log (see the "Application logs" section on page 53).
SELECTING RESPONSE TO INCOMING CALLS
In Both lists mode (see the "About Call&SMS Filter modes" section on page 34), Call&SMS Filter checks incoming
calls according to the Black and White lists. Following a call received from a number on neither list, Call&SMS Filter will
prompt you to enter the number in one of the lists (see Figure below).
You can select one of the following actions for the number from which the call was made:
To add the caller's telephone number to the Black List, select Add to Black List.
To add the caller's telephone number to the White List, select Add to White List.
If you don't want to add the caller's number to either list, press Skip.
Figure 9: Call&SMS Filter notification about the receipt of an SMS
Information about blocked calls is registered in the application's log (see the "Application logs" section on page 53).
Page 44

44
DATA PROTECTION IN THE EVENT OF
IN THIS SECTION
About Anti-Theft .............................................................................................................................................................. 44
Blocking the device ......................................................................................................................................................... 45
Deleting personal data .................................................................................................................................................... 46
Creating a list of folders to delete .................................................................................................................................... 48
Monitoring the replacement of a SIM card on the device ................................................................................................ 49
Determining the device's geographical coordinates ........................................................................................................ 50
Starting Anti-Theft functions remotely ............................................................................................................................. 51
LOSS OR THEFT OF THE DEVICE
This section gives information about Anti-Theft which, in the case of theft or loss, blocks unauthorized access to data
saved on your mobile device and makes it easy to find the device.
This section also specifies how to enable/disable the Anti-Theft function, set the parameters of its operation and start
Anti-Theft from another mobile device remotely.
ABOUT ANTI-THEFT
Anti-Theft protects information stored on your mobile device from unauthorized access.
Anti-Theft includes the following functions:
Block – allows blocking the device remotely and gives the text to be displayed on the screen of the blocked
device.
Data Wipe – can remotely delete the user's personal data from the device (entries in Contacts, SMS, picture
gallery, calendar, logs, Internet connection settings) and information from the storage cards, folders from list for
deletion.
SIM Watch allows obtaining the current phone number in the event that the SIM card is replaced, as well as
locking the device in the event the SIM card is replaced or the device is activated without a SIM card.
Information about a new telephone number is sent as a message to a phone number and / or email that you
specified.
The GPS Find functionality enables you to locate a device. The geographical coordinates of the device are sent
After installing Kaspersky Mobile Security 9, all Anti-Theft functions are disabled.
Kaspersky Mobile Security 9 can remotely start Anti-Theft with sending SMS commands from another mobile device.
To start Anti-Theft remotely, you have to know the secret code set when Kaspersky Mobile Security 9 was first started.
as a message to the phone number from which a special SMS command was sent, and to an email address.
The current status of every function is displayed in the Anti-Theft screen next to the name of the function.
Page 45

D A T A P R O T E C T I O N I N T H E E V E N T O F L O S S O R T H E F T O F T H E D E V I C E
45
Information about the component's operation is entered in the application's log (see "Application Logs" on page 53).
BLOCKING THE DEVICE
After a special SMS command is received, the Block function allows you to remotely block access to the device and data
stored on it. The device can only be unblocked by entering the secret code.
This function does not block the device but simply enables the remote blocking option.
To enable the Block function:
1. Select the Block item on the Anti-Theft tab.
This will open the Block window.
2. Check the Enable Block box.
3. Enter the message which is displayed on the device's screen in blocked mode in the Text when blocked field
(see Figure below). By default, the standard text in which you can add the owner's telephone is used for the
message.
Figure 10: Block function settings
4. Select Menu Save to save the changes.
If the Block function is enabled on another device, you can block it using any of the following methods:
Use a Kaspersky Lab mobile application, such as Kaspersky Mobile Security 9, on another mobile device to
create and send an SMS command to your device. To create a special SMS command, use the Send
command function. As a result, your device will receive a covert SMS, and the device will be blocked.
On another mobile device, create and send an SMS with the special text and the secret code previously set for
the receiving device. As a result, your device will receive a covert SMS, and the device will be blocked.
Outgoing SMS messages will be billed at the rates set by the other mobile device’s mobile service provider.
To block the device remotely, it is advised that you use the secure method with the Sending a command function. The
application secret code is then sent in encrypted form.
Page 46

U S E R G U I D E
46
To send an SMS command to another device using the Send command function:
1. Select the Send command menu item on the Additional tab.
This will open the Send command window.
2. For the Select SMS command setting, select Block.
3. In the Phone number field, enter the phone number of the device that receives the SMS command.
4. In the Remote device code field, enter the application secret code set on the device that receives the SMS
command.
5. Select Menu Send.
To create an SMS with the phone's standard SMS creation functions,
send a standard SMS to another device; it should contain the text block:<code>, where <code> is the secret
code of the application set on another device. The message is not case sensitive, and spaces before or after the
colon are ignored.
DELETING PERSONAL DATA
After a special SMS command is received, the Data Wipe function allows deleting the following information stored in the
device:
the user's personal data (entries in Contacts, calendar, email messages, call log);
information on storage card;
files from the list of objects for deletion (see the "Creating a list of folders to delete" section on page 48).
This function does not delete the data saved on the device, but includes the option to delete them.
To enable the Data Wipe function:
1. Select the Data Wipe item on the Anti-Theft tab.
This will open the Data Wipe screen.
2. Select the Mode item.
This will open the Data Wipe screen.
3. Check the Enable Data Wipe box.
4. Select information that you want to delete. To do this, check the boxes next to the required settings in the
Delete section (see Figure below).
to delete personal data, check the Personal data box;
to delete files from folders on the memory card and from the list of objects for deletion, check the
box Selected folders.
Page 47

D A T A P R O T E C T I O N I N T H E E V E N T O F L O S S O R T H E F T O F T H E D E V I C E
47
Figure 11: Data Wipe function settings
5. Go to creation of a list of objects for deletion (see the "Creating a list of folders to delete" section on page 48).
6. Select Menu Save to save the changes.
You can delete personal data from the device with the function enabled by using the following methods:
Use a Kaspersky Lab mobile application, such as Kaspersky Mobile Security 9, on another mobile device to
create and send an SMS command to your device. As a result, your device receives a covert SMS message
after which the information is deleted. To create a special SMS command, use the Sending a command
function.
On another mobile device, create and send an SMS with the special text and the secret code previously set for
the receiving device. As a result, your device receives a covert SMS message after which the information is
deleted.
Outgoing SMS messages will be billed at the rates set by the other mobile device’s mobile service provider.
To delete information from the device remotely, you are advised to use the secure method with the Sending a command
function. The application secret code is then sent in encrypted form.
To send an SMS command to another device using the Send command function:
1. Select the Send command menu item on the Additional tab.
This will open the Send command window.
2. For the Select SMS command setting, select Data Wipe.
3. In the Phone number field, enter the phone number of the device that receives the SMS command.
4. In the Remote device code field, enter the application secret code set on the device that receives the SMS
command.
5. Select Menu Send.
To create an SMS with the phone's standard SMS creation functions:
send a standard SMS to another device; it should contain the text wipe:<code> where <code> is the secret code
of the application set on another device. The message is not case sensitive, and spaces before or after the colon are
ignored.
Page 48

U S E R G U I D E
48
CREATING A LIST OF FOLDERS TO DELETE
The Data Wipe function allows creating a list of folders to be deleted after a special SMS command is received.
For Anti-Theft to delete the objects from the list after receiving a special SMS command, ensure that Selected folders is
checked on the Anti-Theft Data Wipe tab.
The administrator may add to the list of folders to be deleted. These folders cannot be deleted from the list.
To add a folder to the list of folders to be deleted:
1. Select the Data Wipe item on the Anti-Theft tab.
This will open the Data Wipe screen.
2. Go to the list of objects for deletion.
3. Select Menu Add folder (see Figure below).
Figure 12: Adding folders
4. Select the necessary folder from the folder tree and press Menu Select.
The folder is added to the Selected folders list.
5. Select Menu Save.
To remove a folder from the list:
1. Select the Data Wipe item on the Anti-Theft tab.
This will open the Data Wipe screen.
2. Go to the list of objects for deletion.
3. Select the folder from the list and then select Menu Delete folder.
The confirmation window opens.
4. Confirm the deleting of the folder by pressing Yes.
The folder will be deleted from the Selected folders list.
Page 49

D A T A P R O T E C T I O N I N T H E E V E N T O F L O S S O R T H E F T O F T H E D E V I C E
49
5. Select Menu Save.
MONITORING THE REPLACEMENT OF A SIM CARD ON THE
DEVICE
If the SIM card is replaced, SIM Watch allows you to send a message with the new number to your phone number
and / or email, or lock the device.
To enable the SIM Watch function and monitor the replacement of the SIM card:
1. On the Anti-Theft tab, select the SIM Watch item.
This will open the SIM Watch window.
2. Check the Enable SIM Watch box.
3. To check the replacement of the SIM card on the device, make the following settings (see Figure below):
To automatically receive an SMS message with the new number being used in your telephone, enter the
telephone number to which the SMS message should be sent in the SMS to phone number field within the
When the SIM card is replaced, send the new number box.
The phone number may begin with a digit or with a "+", and must contain digits only.
To receive an email with the new telephone number, in the When the SIM card is replaced, send the new
number block in the Message to email field, enter the email address.
To block the device if the SIM card is replaced, or if the device is turned on with the SIM card removed,
check the Block device box in the Additional block. You can unblock the device only by entering the
application secret code.
To display a message on the screen in blocked mode, enter it in the Text when blocked field. By default,
the standard text in which you can add the owner's number is used for the message.
Figure 13: SIM Watch function settings
4. Select Menu Save to save the changes.
Page 50

U S E R G U I D E
50
DETERMINING THE DEVICE'S GEOGRAPHICAL
COORDINATES
After a special SMS command is received, GPS Find allows detecting the device's geographical coordinates and sending
them by SMS and email to the requesting device and an email address.
Outgoing SMS messages are billed at your mobile service provider’s current rate.
This function only works with devices with in-built GPS receiver. The GPS receiver is enabled automatically after the
device receives a special SMS command. If the device is within the area reached by satellites, the GPS Find function
receives and sends the geographical coordinates of the device. If the satellites are unavailable at the time of the query,
GPS Find will periodically re-attempt to find them and send device location results.
To enable the GPS Find function:
1. Select the GPS Find item on the Anti-Theft tab.
This will open the GPS Find window.
2. Check the Enable GPS Find box.
After receiving a special SMS command, Kaspersky Mobile Security 9 sends the device's coordinates by return
SMS.
3. To receive the coordinates of the device by email, in the Send device coordinates block for the setting
You can request the coordinates of a device on which GPS Find is enabled, using the following methods:
Message to email enter email address (see Figure below).
Figure 14: GPS Find function settings
4. Select Menu Save to save the changes.
Use a Kaspersky Lab mobile application, such as Kaspersky Mobile Security 9, on another mobile device to
create and send an SMS command to your device. As a result, your device will receive a covert SMS, and the
application will send the device's coordinates. To create a special SMS command, use the Sending a command
function.
On another mobile device, create and send an SMS with the special text and the secret code previously set for
the receiving device. As a result, your device will receive a covert SMS, and the application will send the
device's coordinates.
Page 51

D A T A P R O T E C T I O N I N T H E E V E N T O F L O S S O R T H E F T O F T H E D E V I C E
51
Outgoing SMS messages will be billed at the rates set by the other mobile device’s mobile service provider.
To receive the device's location, you are advised to use the secure method with the Send command function. The
application secret code is then sent in encrypted mode.
To send a command to another device using the Send command function:
1. Select the Send command menu item on the Additional tab.
This will open the Send command window.
2. Select the GPS Find value for the Select SMS command setting.
3. In the Phone number field, enter the phone number of the device that receives the SMS command.
4. In the Remote device code field, enter the application secret code set on the device that receives the SMS
command.
5. Select Menu Send.
To create an SMS with the phone's standard SMS creation functions:
send a standard SMS to another device; it should contain the text find:<code>, where <code> is the application
secret code set on another device. The message is not case sensitive, and spaces before or after the colon are
ignored.
An SMS message with the device's coordinates will be sent to the phone number from which the SMS command was
sent and to an email address if you have specified one in the GPS Find options.
STARTING ANTI-THEFT FUNCTIONS REMOTELY
The application allows sending a special SMS command to run Anti-Theft functions remotely on another device with
Kaspersky Mobile Security installed on it. An SMS command is sent as an encrypted SMS and contains the application
secret code set on the other device. Reception of the SMS command will not be noticed.
SMS is billed at your mobile service provider’s current rate.
To send an SMS command to another device:
1. Select the Send command item on the Additional tab.
This will open the Send command window.
2. Select the function for remote launch on another mobile device. Select one of the proposed values for the
Select SMS command setting (see Figure below):
Block device (on page 45).
Data Wipe (see "Deleting personal data" section on page 46).
GPS Find (see the "Determining the device's geographical coordinates" section on page 50).
Page 52

U S E R G U I D E
52
Figure 15: Remote startup of Anti-Theft and Privacy Protection functions
3. In the Phone number field, enter the phone number of the device that receives the SMS command.
4. In the Remote device code field, enter the application secret code set on the device that receives the SMS
command.
5. Select Menu Send.
Page 53

53
APPLICATION LOGS
IN THIS SECTION
About logs ....................................................................................................................................................................... 53
Viewing Log records ........................................................................................................................................................ 53
Deleting log records ........................................................................................................................................................ 53
This section gives information about logs, in which each component's operations are recorded, as well as each task that
is completed (e.g. receipt of an SMS command from another device).
ABOUT LOGS
The application's logs store records about events that occur during Kaspersky Mobile Security 9 operation. Entries are
sorted by time of the event and starting with the most recent events.
For every component, a separate events log is used.
VIEWING LOG RECORDS
To view the entries in a component's log,
on the tab of the necessary component, select the item Events log.
The selected component's log opens.
Use the scroll bar to scroll through the log.
To view detailed log record information,
select the necessary entry and press ENTER on the keyboard.
DELETING LOG RECORDS
You can clear all logs. Information on the operation of all components of Kaspersky Mobile Security 9 will be deleted.
To clear all logs:
1. On the tab of any component, select the Events log.
The Events log window opens.
2. Select Menu Clear Log.
3. Confirm the uninstalling by pressing the Yes button.
All entries from all components' logs will be deleted.
Page 54

54
CONFIGURING ADDITIONAL SETTINGS
IN THIS SECTION
Changing the secret code ............................................................................................................................................... 54
Displaying prompts .......................................................................................................................................................... 54
This section provides information on additional options of Kaspersky Mobile Security 9: how to change the secret code
and how to enable/disable the display of the hints.
CHANGING THE SECRET CODE
You can change the secret code set after the first start up of the application.
To change the secret code:
1. Select the Additional settings menu item on the Additional tab.
The Additional settings screen opens.
2. Select Change code.
3. Enter the current secret code of the application in the Enter code entry field.
4. Enter the new secret code in the Enter new code and Confirm code fields.
The code entered is automatically verified.
If the secret code entered is valid, it will be saved.
If the code is deemed invalid according to the results of the verification, a warning message is displayed and the
application requests confirmation. To use the code, press Yes.
In order to create a new code, press No. The Enter new code and Confirm code fields will empty. Enter a new
application secret code.
DISPLAYING PROMPTS
When you configure the settings of components, Kaspersky Mobile Security 9 displays by default a prompt with a short
description of the function selected. You can configure the display of Kaspersky Mobile Security 9 hints.
To configure the display of hints, perform the following steps:
1. Select the Additional settings menu item on the Additional tab.
The Additional settings screen opens.
2. Enable / disable the display of prompts. To do this, select Hints.
The status of the display of prompts will be shown next to the Hints menu item. The radio button icon to the
right changes according to the status of the display of prompts.
Page 55

55
CONTACTING THE TECHNICAL SUPPORT SERVICE
If you have already purchased Kaspersky Internet Security, you can obtain information about it from the Technical
Support Service, either over the phone or via the Internet.
Technical Support Service specialists will answer any of your questions about installing and using the application. They
will also help you to eliminate the consequences of malware activities if your device has been infected.
Before contacting the Technical support service, please read the Support rules for Kaspersky Lab’s products
(http://support.kaspersky.com/support/rules).
E-mailing your question to the Technical Support Service
You can forward your question to the Technical Support Service specialists by filling out a Helpdesk web form at
(http://support.kaspersky.com/helpdesk.html).
You can write your inquiry in Russian, English, German, French or Spanish.
To send an e-mail message with your question, you must include the Customer ID and password you received
when you registered at the Technical Support Service's website.
If you are not a registered user of Kaspersky Lab's applications, you can fill out a registration form
(https://support.kaspersky.com/personalcabinet/registration/form/). During registration enter the activation code for your
application, or the key filename.
The Technical Support Service will respond to your request in your Personal Cabinet
(https://support.kaspersky.com/PersonalCabinet) and to the e-mail address you specified in your inquiry.
In your inquiry, please describe the problem you have encountered. Specify the following in the mandatory fields:
Request type. Select a topic which corresponds to the arising problem most closely, for instance "Product
Installation/Removal Problem" or "Anti-Virus scan/virus removal problem". If you do not find an appropriate
topic, select "General question".
Application name and version number.
Request text. Describe the problem you encountered, providing as much relevant detail as possible.
Customer ID and password. Enter the customer ID and password you received when you registered at the
Technical Support Service's website.
E-mail address. The Technical Support Service will reply to your question at this email address.
Technical support by phone
If you have an urgent problem, you can call your local Technical Support Service. Before contacting your local
(http://support.kaspersky.com/support/support_local) or international
(http://support.kaspersky.com/support/international) Technical Support Service, please collect the necessary
information (http://support.kaspersky.com/support/details) about your device and the installed anti-virus application.
This will enable our specialists to help you more quickly.
Page 56

56
GLOSSARY
A
A C T I V A T I N G T H E A P P L I C A T I O N
Switching the application into full-function mode. The user needs a license to activate the application.
A P P L I C A T I O N S E CR E T C O DE
The secret code prevents unauthorized access to the application settings and to blocked information on the device. The
user sets it on first starting the application and it consists of at least four characters. The secret code is requested in the
following instances:
for access to application settings;
when sending an SMS command from another mobile device to start the following functions remotely: Block,
Data Wipe, SIM Watch, GPS Find.
B
B L A C K L I S T
The entries in this list contain the following information:
Telephone number from which Call&SMS Filter blocks calls and / or SMS.
Types of events that Call&SMS Filter blocks from this number. The following types of events are available: calls
and SMS, calls only, and SMS only.
Key phrase that Call&SMS Filter uses to classify an SMS as unsolicited (spam). Call&SMS Filter only blocks
SMS containing the key phrase, while delivering all other SMS.
D
D E L E T I N G S M S M E S S A G E S
Method of processing an SMS message containing SPAM features, by deleting it. You are advised to use this method
with SMS messages which definitely contain spam.
N
N ON- N U M E R I C N U M B E R
A phone number that includes letters or consists only of letters.
T
T E L E P H O N E N U M B E R M A S K
Putting a telephone number in the Black or White List using wildcards. The two basic wildcards used in telephone
number masks are "*" and "?", (where "*" represents any number of characters and "?" stands for any single character).
For example, *1234? on the Black List. Call&SMS Filter blocks calls or SMS from a number in which any symbol follows
the figure 1234.
Page 57

G L O S S A R Y
57
W
W H I T E L I S T
The entries in this list contain the following information:
Telephone number from which Call&SMS Filter delivers calls and / or SMS.
Types of events that Call&SMS Filter delivers from this number. The following types of events are available:
calls and SMS, calls only, and SMS only.
Key phrase used by Call&SMS Filter to classify an SMS as solicited (not spam). Call&SMS Filter only delivers
SMS containing the key phrase, while blocking all other SMS.
Page 58

58
KASPERSKY LAB
Kaspersky Lab website
http://www.kaspersky.com
Virus Encyclopedia:
http://www.securelist.com/
Anti-virus laboratory:
newvirus@kaspersky.com
(only for sending suspicious objects in archives)
http://support.kaspersky.com/virlab/helpdesk.html
(for sending requests to virus analysts)
Kaspersky Lab web forum:
http://forum.kaspersky.com
Kaspersky Lab was founded in 1997. Today it is the leading developer of a wide range of high-performance information
security software products, including anti-virus, anti-spam and anti-hacking systems.
Kaspersky Lab is an international company. Headquartered in the Russian Federation, the company has offices in the
United Kingdom, France, Germany, Japan, the Benelux countries, China, Poland, Romania and the USA (California). A
new company department, the European Anti-Virus Research Centre, has recently been established in France.
Kaspersky Lab's partner network includes over 500 companies worldwide.
Today, Kaspersky Lab employs over a thousand highly qualified specialists, including 10 MBA degree holders and 16
PhD degree holders. All the Kaspersky Lab's senior anti-virus experts are members of the Computer Anti-Virus
Researchers Organization (CARO).
Kaspersky Lab offers best-of-breed security solutions, based on its unique experience and knowledge, and gained in
over 14 years of fighting computer viruses. A thorough analysis of computer virus activities enables the company's
specialists to foresee trends in the development of malware and to provide our users with timely protection against new
types of attacks. This advantage is the basis of Kaspersky Lab's products and services. At all times, the company’s
products remain at least one step ahead of many other vendors in delivering extensive anti-virus coverage for home
users and corporate customers alike.
Years of hard work have made the company one of the top anti-virus software developers. Kaspersky Lab was the first to
develop many of the modern standards for anti-virus software. The company's flagship product, Kaspersky Anti-Virus,
reliably protects all types of computer systems against virus attacks, including workstations, file servers, mail systems,
firewalls, Internet gateways and hand-held computers. Kaspersky Lab's customers benefit from a wide range of
additional services that ensure both stable operation of the company's products, and compliance with specific business
requirements. Many well-known manufacturers use the Kaspersky Anti-Virus ®kernel in their products, including: Nokia
ICG (USA), Aladdin (Israel), Sybari (USA), G Data (Germany), Deerfield (USA), Alt-N (USA), Microworld (India), and
BorderWare (Canada).
Kaspersky Lab's customers enjoy a wide range of additional services that ensure both stable operation of the company's
products, and full compliance with the customer’s specific business requirements. We plan, install, and support corporate
anti-virus suites. Kaspersky Lab's anti-virus database is updated hourly. The company provides its customers with 24hour technical support service in several languages.
If you have any questions, comments, or suggestions, you can contact us through our dealers, or at Kaspersky Lab
directly. Detailed consultations are provided by phone or email. You will receive full answers to all of your questions.
Page 59

59
INFORMATION ABOUT THIRD PARTY CODE
IN THIS SECTION
Distributed program code ................................................................................................................................................ 59
Other information ............................................................................................................................................................ 61
IN THIS SECTION
ADB ................................................................................................................................................................................. 59
ADBWINAPI.DLL ............................................................................................................................................................ 59
ADBWINUSBAPI.DLL ..................................................................................................................................................... 59
Third party code is used to create the application.
DISTRIBUTED PROGRAM CODE
Within the application, an independent third-party program code is distributed in source or binary form, without any
changes made.
ADB
ADB
Copyright (C) 2005-2008, The Android Open Source Project
-----------------------------------------------------------------------------
Distributed under the terms of the Apache License, version 2.0 of the License
ADBWINAPI.DLL
ADBWINAPI.DLL
Copyright (C) 2005-2008, The Android Open Source Project
-----------------------------------------------------------------------------
Distributed under the terms of the Apache License, version 2.0 of the License
ADBWINUSBAPI.DLL
ADBWINUSBAPI.DLL
Copyright (C) 2005-2008, The Android Open Source Project
Page 60

U S E R G U I D E
60
-----------------------------------------------------------------------------
Apache License
Version 2.0, January 2004
http://www.apache.org/licenses/
TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION
1. Definitions.
"License" shall mean the terms and conditions for use, reproduction, and distribution as defined by Sections 1 through 9
of this document.
"Licensor" shall mean the copyright owner or entity authorized by the copyright owner that is granting the License.
"Legal Entity" shall mean the union of the acting entity and all other entities that control, are controlled by, or are under
common control with that entity. For the purposes of this definition, "control" means (i) the power, direct or indirect, to
cause the direction or management of such entity, whether by contract or otherwise, or (ii) ownership of fifty percent
(50%) or more of the outstanding shares, or (iii) beneficial ownership of such entity.
"You" (or "Your") shall mean an individual or Legal Entity exercising permissions granted by this License.
"Source" form shall mean the preferred form for making modifications, including but not limited to software source code,
documentation source, and configuration files.
"Object" form shall mean any form resulting from mechanical transformation or translation of a Source form, including but
not limited to compiled object code, generated documentation, and conversions to other media types.
"Work" shall mean the work of authorship, whether in Source or Object form, made available under the License, as
indicated by a copyright notice that is included in or attached to the work (an example is provided in the Appendix below).
"Derivative Works" shall mean any work, whether in Source or Object form, that is based on (or derived from) the Work
and for which the editorial revisions, annotations, elaborations, or other modifications represent, as a whole, an original
work of authorship. For the purposes of this License, Derivative Works shall not include works that remain separable
from, or merely link (or bind by name) to the interfaces of, the Work and Derivative Works thereof.
"Contribution" shall mean any work of authorship, including the original version of the Work and any modifications or
additions to that Work or Derivative Works thereof, that is intentionally submitted to Licensor for inclusion in the Work by
the copyright owner or by an individual or Legal Entity authorized to submit on behalf of the copyright owner. For the
purposes of this definition, "submitted" means any form of electronic, verbal, or written communication sent to the
Licensor or its representatives, including but not limited to communication on electronic mailing lists, source code control
systems, and issue tracking systems that are managed by, or on behalf of, the Licensor for the purpose of discussing
and improving the Work, but excluding communication that is conspicuously marked or otherwise designated in writing
by the copyright owner as "Not a Contribution."
"Contributor" shall mean Licensor and any individual or Legal Entity on behalf of whom a Contribution has been received
by Licensor and subsequently incorporated within the Work.
2. Grant of Copyright License. Subject to the terms and conditions of this License, each Contributor hereby grants to You
a perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable copyright license to reproduce, prepare
Derivative Works of, publicly display, publicly perform, sublicense, and distribute the Work and such Derivative Works in
Source or Object form.
3. Grant of Patent License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a
perpetual, worldwide, non-exclusive, no-charge, royalty-free, irrevocable (except as stated in this section) patent license
to make, have made, use, offer to sell, sell, import, and otherwise transfer the Work, where such license applies only to
those patent claims licensable by such Contributor that are necessarily infringed by their Contribution(s) alone or by
combination of their Contribution(s) with the Work to which such Contribution(s) was submitted. If You institute patent
litigation against any entity (including a cross-claim or counterclaim in a lawsuit) alleging that the Work or a Contribution
incorporated within the Work constitutes direct or contributory patent infringement, then any patent licenses granted to
You under this License for that Work shall terminate as of the date such litigation is filed.
Page 61

I N F O R M A T I O N A B O U T T H I R D P A R T Y C O DE
61
4. Redistribution. You may reproduce and distribute copies of the Work or Derivative Works thereof in any medium, with
or without modifications, and in Source or Object form, provided that You meet the following conditions:
(a) You must give any other recipients of the Work or Derivative Works a copy of this License; and
(b) You must cause any modified files to carry prominent notices stating that You changed the files; and
(c) You must retain, in the Source form of any Derivative Works that You distribute, all copyright, patent, trademark, and
attribution notices from the Source form of the Work, excluding those notices that do not pertain to any part of the
Derivative Works; and
(d) If the Work includes a "NOTICE" text file as part of its distribution, then any Derivative Works that You distribute must
include a readable copy of the attribution notices contained within such NOTICE file, excluding those notices that do not
pertain to any part of the Derivative Works, in at least one of the following places: within a NOTICE text file distributed as
part of the Derivative Works; within the Source form or documentation, if provided along with the Derivative Works; or,
within a display generated by the Derivative Works, if and wherever such third-party notices normally appear. The
contents of the NOTICE file are for informational purposes only and do not modify the License. You may add Your own
attribution notices within Derivative Works that You distribute, alongside or as an addendum to the NOTICE text from the
Work, provided that such additional attribution notices cannot be construed as modifying the License. You may add Your
own copyright statement to Your modifications and may provide additional or different license terms and conditions for
use, reproduction, or distribution of Your modifications, or for any such Derivative Works as a whole, provided Your use,
reproduction, and distribution of the Work otherwise complies with the conditions stated in this License.
5. Submission of Contributions. Unless You explicitly state otherwise, any Contribution intentionally submitted for
inclusion in the Work by You to the Licensor shall be under the terms and conditions of this License, without any
additional terms or conditions. Notwithstanding the above, nothing herein shall supersede or modify the terms of any
separate license agreement you may have executed with Licensor regarding such Contributions.
6. Trademarks. This License does not grant permission to use the trade names, trademarks, service marks, or product
names of the Licensor, except as required for reasonable and customary use in describing the origin of the Work and
reproducing the content of the NOTICE file.
7. Disclaimer of Warranty. Unless required by applicable law or agreed to in writing, Licensor provides the Work (and
each Contributor provides its Contributions) on an "AS IS" BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY
KIND, either express or implied, including, without limitation, any warranties or conditions of TITLE, NONINFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A PARTICULAR PURPOSE. You are solely responsible for
determining the appropriateness of using or redistributing the Work and assume any risks associated with Your exercise
of permissions under this License.
8. Limitation of Liability. In no event and under no legal theory, whether in tort (including negligence), contract, or
otherwise, unless required by applicable law (such as deliberate and grossly negligent acts) or agreed to in writing, shall
any Contributor be liable to You for damages, including any direct, indirect, special, incidental, or consequential damages
of any character arising as a result of this License or out of the use or inability to use the Work (including but not limited
to damages for loss of goodwill, work stoppage, computer failure or malfunction, or any and all other commercial
damages or losses), even if such Contributor has been advised of the possibility of such damages.
9. Accepting Warranty or Additional Liability. While redistributing the Work or Derivative Works thereof, You may choose
to offer, and charge a fee for, acceptance of support, warranty, indemnity, or other liability obligations and/or rights
consistent with this License. However, in accepting such obligations, You may act only on Your own behalf and on Your
sole responsibility, not on behalf of any other Contributor, and only if You agree to indemnify, defend, and hold each
Contributor harmless for any liability incurred by, or claims asserted against, such Contributor by reason of your
accepting any such warranty or additional liability.
END OF TERMS AND CONDITIONS
OTHER INFORMATION
Additional information about third-party code.
To create and verify digital signatures, Kaspersky Internet Security uses Crypto C data security software library by
CryptoEx LLC.
CryptoEx LLC corporate website: http://www.cryptoex.ru
Page 62

62
INDEX
A
Activating the application.............................................................................................................................................. 20
license .................................................................................................................................................................... 27
Adding
Call&SMS Filter Black List ...................................................................................................................................... 36
Call&SMS Filter White List ...................................................................................................................................... 39
Allowing
incoming calls ......................................................................................................................................................... 39
incoming SMS ........................................................................................................................................................ 39
Anti-Theft ...................................................................................................................................................................... 44
Block ....................................................................................................................................................................... 45
Data Wipe ................................ ................................................................ ................................ ......................... 46, 48
GPS Find ................................................................................................................................................................ 50
SIM Watch .............................................................................................................................................................. 49
Application secret code .................................................................................................................................... 23, 24, 54
B
Black List
Call&SMS Filter ...................................................................................................................................................... 35
Blocking
device ..................................................................................................................................................................... 45
incoming calls ................................................................................................................................................... 35, 38
incoming SMS ........................................................................................................................................................ 35
C
Call&SMS Filter ............................................................................................................................................................ 34
action on call ........................................................................................................................................................... 43
action on SMS ........................................................................................................................................................ 42
Black List ................................................................................................................................................................ 35
modes ..................................................................................................................................................................... 34
non-numeric numbers ............................................................................................................................................. 42
numbers out of Contacts......................................................................................................................................... 41
White list ................................................................................................................................................................. 38
Code
activation code .................................................................................................................................................. 21, 22
application secret code ........................................................................................................................................... 23
D
Data
remote delete .......................................................................................................................................................... 46
Delete
Call&SMS Filter Black List ...................................................................................................................................... 38
Call&SMS Filter White List ...................................................................................................................................... 40
Deleting
Log records ............................................................................................................................................................. 53
Determining the device's location ................................................................................................................................. 50
Disabling
Call&SMS Filter ................................................................................................................................................ 34, 35
E
Edit
Call&SMS Filter Black List ...................................................................................................................................... 37
Call&SMS Filter White List ...................................................................................................................................... 40
Enabling
Page 63

I N D E X
63
Call&SMS Filter ...................................................................................................................................................... 35
Entry
Call&SMS Filter Black List ...................................................................................................................................... 36
Call&SMS Filter White List ...................................................................................................................................... 39
Events log
deleting entries ....................................................................................................................................................... 53
viewing entries ........................................................................................................................................................ 53
F
FILTERING
INCOMING CALLS ................................................................................................................................................. 34
INCOMING SMS .................................................................................................................................................... 34
H
Hardware requirements ................................................................................................................................................ 17
I
INSTALLING THE APPLICATION ............................................................................................................................... 18
L
License
activating the application ........................................................................................................................................ 20
information .............................................................................................................................................................. 28
License Agreement ................................................................................................................................................. 27
renewal ................................................................................................................................................................... 29
M
Modes
Call&SMS Filter ................................................................................................................................................ 34, 35
R
Renewing the license ................................................................................................................................................... 29
S
Send SMS command ................................................................................................................................................... 51
Starting
application .............................................................................................................................................................. 25
U
UNINSTALLING
APPLICATION ........................................................................................................................................................ 19
W
White list
Call&SMS Filter ...................................................................................................................................................... 38
Wipe
information saved on the device ............................................................................................................................. 46
 Loading...
Loading...