Page 1

Kaspersky Internet Security 2012
User Guide
APPLICATION VERSION: 12.0
Page 2
2
Dear User!
Thank you for choosing our product. We hope that you will find this documentation useful and that it will provide answers
to most of your questions that may arise.
Warning! This document is the property of Kaspersky Lab ZAO (herein also referred to as Kaspersky Lab): all rights to
this document are reserved by the copyright laws of the Russian Federation and by international treaties. Illegal
reproduction and distribution of this document or parts hereof will result in civil, administrative or criminal liability in
accordance with applicable law.
Any type of reproduction or distribution of any materials, including translations, is allowed only with the written permission
of Kaspersky Lab.
This document and related graphic images can be used exclusively for informational, non-commercial or personal use.
This document may be amended without prior notification. The latest version of this document can be found on the
Kaspersky Lab website at http://www.kaspersky.com/docs.
Kaspersky Lab assumes no liability for the content, quality, relevance, or accuracy of any materials used in this
document the rights to which are held by third parties, or for any potential damages associated with the use of such
documents.
This document uses registered trademarks and service marks which are the property of their respective owners.
Document revision date: 4/19/2011
© 1997-2011 Kaspersky Lab ZAO. All Rights Reserved.
http://www.kaspersky.com
http://support.kaspersky.com
Page 3

3
CONTENT
ABOUT THIS GUIDE ..................................................................................................................................................... 9
In this guide .............................................................................................................................................................. 9
Document conventions ........................................................................................................................................... 11
SOURCES OF INFORMATION ABOUT THE APPLICATION ..................................................................................... 12
Sources of information for independent research ................................................................................................... 12
Discussing Kaspersky Lab applications on the Forum ........................................................................................... 13
Contacting the Sales Department ........................................................................................................................... 13
Contacting the Documentation Development Team by email ................................................................................. 13
KASPERSKY INTERNET SECURITY.......................................................................................................................... 14
What's new ................................................................................................ ................................ ............................. 14
Distribution kit ......................................................................................................................................................... 14
Service for registered users .................................................................................................................................... 15
Hardware and software requirements ..................................................................................................................... 15
INSTALLING AND REMOVING THE APPLICATION .................................................................................................. 17
Standard installation procedure .............................................................................................................................. 17
Step 1. Searching for a newer version of the application .................................................................................. 18
Step 2. Making sure the system meets the installation requirements ............................................................... 18
Step 3. Selecting installation type ..................................................................................................................... 19
Step 4. Reviewing the license agreement ......................................................................................................... 19
Step 5. Kaspersky Security Network Data Collection Statement ...................................................................... 19
Step 6. Searching for incompatible applications ............................................................................................... 19
Step 7. Selecting the destination folder ............................................................................................................. 20
Step 8. Preparing for installation ....................................................................................................................... 20
Step 9. Installing ............................................................................................................................................... 21
Step 10. Finishing the installation ..................................................................................................................... 21
Step 11. Activating the application .................................................................................................................... 21
Step 12. Registering a user............................................................................................................................... 21
Step 13. Completing the activation ................................................................................................................... 22
Updating the previous version of Kaspersky Internet Security................................................................................ 22
Step 1. Searching for a newer version of the application .................................................................................. 23
Step 2. Making sure the system meets the installation requirements ............................................................... 23
Step 3. Selecting installation type ..................................................................................................................... 24
Step 4. Reviewing the license agreement ......................................................................................................... 24
Step 5. Kaspersky Security Network Data Collection Statement ...................................................................... 24
Step 6. Searching for incompatible applications ............................................................................................... 24
Step 7. Selecting the destination folder ............................................................................................................. 25
Step 8. Preparing for installation ....................................................................................................................... 25
Step 9. Installing ............................................................................................................................................... 26
Step 10. Wizard completion .............................................................................................................................. 26
Non-standard installation scenarios ........................................................................................................................ 26
Getting started ........................................................................................................................................................ 27
Removing the application ....................................................................................................................................... 27
Step 1. Saving data for reuse............................................................................................................................ 27
Step 2. Confirmation of application removal...................................................................................................... 28
Page 4

U S E R G U I DE
4
Step 3. Removing the application. Completing removal .................................................................................... 28
LICENSING THE APPLICATION ................................................................................................................................. 29
About the End User License Agreement ................................................................................................................ 29
About data provision ............................................................................................................................................... 29
About the license .................................................................................................................................................... 29
About the activation code ....................................................................................................................................... 30
APPLICATION INTERFACE ........................................................................................................................................ 31
The notification area icon........................................................................................................................................ 31
The context menu ................................................................................................................................................... 32
The Kaspersky Internet Security main window ....................................................................................................... 33
Notification windows and pop-up messages ........................................................................................................... 34
The application settings window ............................................................................................................................. 36
The Kaspersky Gadget ........................................................................................................................................... 37
News Agent ............................................................................................................................................................ 37
STARTING AND STOPPING THE APPLICATION ...................................................................................................... 38
Enabling and disabling automatic launch ............................................................................................................... 38
Launching and closing the application manually ..................................................................................................... 38
MANAGING THE COMPUTER PROTECTION ............................................................................................................ 39
Diagnostics and elimination of problems in your computer protection .................................................................... 39
Enabling and disabling the protection ..................................................................................................................... 40
Pausing and resuming protection ........................................................................................................................... 41
SOLVING TYPICAL TASKS ......................................................................................................................................... 43
How to activate the application ............................................................................................................................... 43
How to purchase or renew a license ....................................................................................................................... 44
What to do when application notifications appear ................................................................................................... 45
How to update application databases and modules .............................................................................................. 45
How to scan critical areas of your computer for viruses ........................................................................................ 46
How to scan a file, folder, disk, or another object for viruses .................................................................................. 46
How to perform a full scan of your computer for viruses ........................................................................................ 48
How to scan your computer for vulnerabilities ........................................................................................................ 48
How to protect your personal data against theft ..................................................................................................... 48
Protection against phishing ............................................................................................................................... 49
Protection against data interception at the keyboard ........................................................................................ 50
Protection of confidential data entered on websites .......................................................................................... 51
What to do if you suspect an object is infected with a virus .................................................................................... 51
How to run an unknown application without doing any harm to the system ........................................................... 52
What to do with a large number of spam messages ............................................................................................... 52
What to do if you suspect your computer is infected .............................................................................................. 53
How to restore a file that has been deleted or disinfected by the application ........................................................ 54
How to create and use a Rescue Disk .................................................................................................................... 54
Creating a Rescue Disk .................................................................................................................................... 55
Starting the computer from the Rescue Disk..................................................................................................... 57
How to view the report on the application's operation ............................................................................................. 57
How to restore default application settings ............................................................................................................. 58
How to transfer settings to Kaspersky Internet Security installed on another computer ......................................... 59
How to use the Kaspersky Gadget ......................................................................................................................... 59
How to know the reputation of an application ......................................................................................................... 61
Page 5

C O N T E N T
5
ADVANCED APPLICATION SETTINGS ...................................................................................................................... 62
General protection settings ..................................................................................................................................... 63
Restricting access to Kaspersky Internet Security ............................................................................................ 63
Selecting a protection mode.............................................................................................................................. 64
Scan ....................................................................................................................................................................... 64
Virus scan ......................................................................................................................................................... 64
Vulnerability Scan ............................................................................................................................................. 72
Managing scan tasks. Task Manager ............................................................................................................... 72
Update .................................................................................................................................................................... 72
Selecting an update source............................................................................................................................... 73
Creating the update startup schedule ............................................................................................................... 75
Rolling back the last update .............................................................................................................................. 76
Running updates under a different user account .............................................................................................. 76
Using a proxy server ......................................................................................................................................... 77
File Anti-Virus ......................................................................................................................................................... 77
Enabling and disabling File Anti-Virus ............................................................................................................... 78
Automatically pausing File Anti-Virus ................................................................................................................ 78
Creating the protection scope of File Anti-Virus ................................................................................................ 79
Changing and restoring the file security level.................................................................................................... 80
Selecting file scan mode ................................................................................................................................... 80
Using heuristic analysis when working with File Anti-Virus ............................................................................... 81
Selecting file scan technology ........................................................................................................................... 81
Changing the action to take on infected files..................................................................................................... 81
Scan of compound files by File Anti-Virus ................................ ......................................................................... 82
Optimizing file scan ........................................................................................................................................... 83
Mail Anti-Virus ........................................................................................................................................................ 83
Enabling and disabling Mail Anti-Virus .............................................................................................................. 84
Creating the protection scope of Mail Anti-Virus ............................................................................................... 84
Changing and restoring the email security level ................................................................................................ 85
Using heuristic analysis when working with Mail Anti-Virus ............................................................................. 86
Changing the action to take on infected email messages ................................................................ ................. 86
Filtering attachments in email messages .......................................................................................................... 86
Scan of compound files by Mail Anti-Virus ........................................................................................................ 87
Email scanning in Microsoft Office Outlook ....................................................................................................... 87
Email scanning in The Bat! ............................................................................................................................... 87
Web Anti-Virus ........................................................................................................................................................ 88
Enabling and disabling Web Anti-Virus ................................................................................................ ............. 89
Changing and restoring the web traffic security level ........................................................................................ 90
Changing the action to take on dangerous objects from web traffic ................................................................. 90
Checking URLs on web pages .......................................................................................................................... 90
Using heuristic analysis when working with Web Anti-Virus ............................................................................. 93
Blocking dangerous scripts ............................................................................................................................... 93
Scan optimization .............................................................................................................................................. 94
Controlling access to regional domains ............................................................................................................ 94
Controlling access to online banking services................................................................................................... 95
Creating a list of trusted addresses ................................................................................................................... 95
IM Anti-Virus ........................................................................................................................................................... 96
Enabling and disabling IM Anti-Virus ................................................................................................................ 96
Page 6

U S E R G U I DE
6
Creating the protection scope of IM Anti-Virus .................................................................................................. 96
Checking URLs in messages from IM clients .................................................................................................... 97
Using heuristic analysis when working with IM Anti-Virus ................................................................................. 97
Proactive Defense .................................................................................................................................................. 97
Enabling and disabling Proactive Defense ................................ ........................................................................ 98
Creating a group of trusted applications ........................................................................................................... 98
Using the dangerous activity list ........................................................................................................................ 99
Changing the action to be taken on applications' dangerous activity ................................................................ 99
System Watcher ..................................................................................................................................................... 99
Enabling and disabling System Watcher ......................................................................................................... 100
Using patterns of dangerous activity (BSS)..................................................................................................... 100
Rolling back a malicious program's actions .................................................................................................... 101
Application Control ............................................................................................................................................... 101
Enabling and disabling Application Control ..................................................................................................... 102
Placing applications into groups ...................................................................................................................... 102
Viewing application activity ............................................................................................................................. 103
Modifying a group and restoring the default group .......................................................................................... 103
Working with Application Control rules ............................................................................................................ 104
Interpreting data on application usage by the participants of the Kaspersky Security Network ...................... 108
Network protection ................................................................................................................................................ 109
Firewall............................................................................................................................................................ 109
Network Attack Blocker ................................................................................................................................... 113
Encrypted connections scan ........................................................................................................................... 116
Network Monitor .............................................................................................................................................. 118
Configuring the proxy server ........................................................................................................................... 118
Creating a list of monitored ports .................................................................................................................... 119
Anti-Spam ............................................................................................................................................................. 120
Enabling and disabling Anti-Spam .................................................................................................................. 121
Changing and restoring the spam protection level .......................................................................................... 122
Training Anti-Spam ......................................................................................................................................... 122
Checking URLs in email messages ................................................................................................................ 125
Detecting spam by phrases and addresses. Creating lists ............................................................................. 125
Regulating threshold values of the spam rate ................................................................................................. 130
Using additional features affecting the spam rate ........................................................................................... 131
Selecting a spam recognition algorithm .......................................................................................................... 131
Adding a label to the message subject ........................................................................................................... 132
Scanning messages from Microsoft Exchange Server .................................................................................... 132
Configuring spam processing by mail clients .................................................................................................. 132
Anti-Banner ........................................................................................................................................................... 135
Enabling and disabling Anti-Banner ................................................................................................................ 135
Selecting a scan method ................................................................ ................................ ................................. 135
Creating lists of blocked and allowed banner addresses ................................................................................ 136
Exporting and importing lists of addresses ..................................................................................................... 136
Safe Run for Applications and Safe Run for Websites ......................................................................................... 137
About Safe Run ............................................................................................................................................... 138
About Safe Run for Websites .......................................................................................................................... 141
Using a shared folder ...................................................................................................................................... 143
Parental Control .................................................................................................................................................... 143
Configuring a user's Parental Control ............................................................................................................. 144
Page 7
C O N T E N T
7
Viewing reports of a user's activity .................................................................................................................. 153
Trusted zone ......................................................................................................................................................... 154
Creating a list of trusted applications .............................................................................................................. 154
Creating exclusion rules ................................................................ ................................ .................................. 155
Performance and compatibility with other applications ................................................................ ......................... 155
Selecting detectable threat categories ............................................................................................................ 156
Battery saving ................................................................................................................................................. 156
Advanced Disinfection .................................................................................................................................... 156
Distributing computer resources when scanning for viruses ........................................................................... 157
Running tasks in background mode ................................................................................................................ 157
Full-screen mode. Gaming Profile ................................................................................................................... 158
Kaspersky Internet Security self-defense ............................................................................................................. 159
Enabling and disabling self-defense ............................................................................................................... 159
Protection against external control .................................................................................................................. 159
Quarantine and Backup ........................................................................................................................................ 160
Storing files in Quarantine and Backup ........................................................................................................... 160
Working with quarantined files ........................................................................................................................ 161
Working with objects in Backup ...................................................................................................................... 162
Scanning files in Quarantine after an update .................................................................................................. 163
Additional tools for better protection of your computer ......................................................................................... 163
Privacy Cleaner ............................................................................................................................................... 164
Configuring a browser for safe work ............................................................................................................... 165
Rolling back changes made by Wizards ......................................................................................................... 167
Reports ................................................................................................................................................................. 167
Creating a report for the selected protection component ................................................................................ 168
Data filtering .................................................................................................................................................... 168
Events search ................................................................................................................................................. 169
Saving a report to file ...................................................................................................................................... 170
Storing reports ................................................................................................................................................ 170
Clearing application reports ............................................................................................................................ 170
Recording non-critical events into the report ................................................................................................... 171
Configuring the notification of report availability .............................................................................................. 171
Application appearance. Managing active interface elements .............................................................................. 171
Translucence of notification windows .............................................................................................................. 171
Animation of the application icon in the notification area ................................................................................ 172
Text on Microsoft Windows logon screen........................................................................................................ 172
Notifications .......................................................................................................................................................... 172
Enabling and disabling notifications ................................................................................................................ 172
Configuring the notification method ................................................................................................................. 173
Disabling news delivery .................................................................................................................................. 174
Kaspersky Security Network ................................................................................................................................. 174
Enabling and disabling participation in Kaspersky Security Network .............................................................. 175
Verifying connection to Kaspersky Security Network ...................................................................................... 175
TESTING THE APPLICATION'S OPERATION .......................................................................................................... 176
About the test file EICAR ...................................................................................................................................... 176
Testing the application's functioning using the test file EICAR ............................................................................. 176
About the types of the test file EICAR .................................................................................................................. 177
Page 8

U S E R G U I DE
8
CONTACTING THE TECHNICAL SUPPORT SERVICE ........................................................................................... 179
How to get technical support ................................................................................................................................ 179
Using the trace file and the AVZ script ................................................................................................................. 179
Creating a system state report ........................................................................................................................ 180
Creating a trace file ......................................................................................................................................... 180
Sending data files ........................................................................................................................................... 180
AVZ script execution ....................................................................................................................................... 181
Technical support by phone .................................................................................................................................. 182
Obtaining technical support via My Kaspersky Account ....................................................................................... 182
APPENDIX ................................................................................................................................................................. 184
Working with the application from the command line ............................................................................................ 184
Activating the application ................................................................................................................................ 185
Starting the application ................................................................................................................................... 186
Stopping the application ................................................................................................ .................................. 186
Managing application components and tasks ................................................................................................. 186
Virus scan ....................................................................................................................................................... 188
Updating the application ................................................................................................................................. 190
Rolling back the last update ............................................................................................................................ 191
Exporting protection settings ........................................................................................................................... 191
Importing protection settings ........................................................................................................................... 191
Creating a trace file ......................................................................................................................................... 192
Viewing Help ................................................................................................................................................... 192
Return codes of the command line ................................................................................................................. 193
Kaspersky Internet Security notifications list ......................................................................................................... 194
Notifications in any protection mode ............................................................................................................... 194
Notifications in interactive protection mode ..................................................................................................... 201
GLOSSARY ............................................................................................................................................................... 212
KASPERSKY LAB ZAO ............................................................................................................................................. 221
INFORMATION ABOUT THIRD-PARTY CODE ........................................................................................................ 222
INDEX ........................................................................................................................................................................ 223
Page 9
9
ABOUT THIS GUIDE
IN THIS SECTION:
In this guide ....................................................................................................................................................................... 9
Document conventions .................................................................................................................................................... 11
Greetings from Kaspersky Lab specialists!
This guide contains information about how to install, configure, and use Kaspersky Internet Security. We hope that
information provided by this guide, will help you work with the application with the maximum of ease.
This guide is intended to:
help you install, activate, and use Kaspersky Internet Security;
ensure a quick search of information on application-related issues;
describe additional sources of information about the application and ways of cooperating with the Technical
Support Service.
For proper use of the application, you should have basic computer skills: be acquainted with the interface of the
operating system that you use, handle the main techniques specific for that system, know how to work with email and the
Internet.
IN THIS GUIDE
This guide comprises the following sections.
Sources of information about the application
This section describes sources of information about the application and lists websites that you can use to discuss the
application's operation.
Kaspersky Internet Security
This section describes the application's features and provides brief information about the application's functions and
components. You will learn what items are included in the distribution kit, and what services are available for registered
users of the application. This section provides information about software and hardware requirements that a computer
should meet to allow a user to install the application on it.
Installing and removing the application
This section provides information about how to install the application on a computer and how to uninstall it.
Licensing the application
This section provides information about general terms related to the application activation. Read this section to learn
more about the purpose of the license agreement, license types, ways of activating the application, and the license
renewal.
Page 10

U S E R G U I DE
10
Application interface
This section provides information about basic elements of the graphic interface of the application: application icon and
application icon context menu, main window, settings window, and notification windows.
Starting and stopping the application
This section contains information on starting and shutting down the application.
Managing the computer protection
This section provides information about how to detect threats to the computer's security and how to configure the security
level. Read this section to learn more about how to enable, disable, and pause the protection when using the application.
Solving typical tasks
This section provides information about how to resolve the most common issues related to protection of the computer
using the application.
Advanced application settings
This section provides detailed information about how to configure each of the application components.
Testing the application's operation
This section provides information about how to ensure that the application detects viruses and their modifications and
performs the correct actions on them.
Contacting the Technical Support Service
This section provides information about how to contact the Technical Support Service at Kaspersky Lab.
Appendix
This section provides information that complements the document text.
Glossary
This section contains a list of terms mentioned in the document and their respective definitions.
Kaspersky Lab ZAO
This section provides information about Kaspersky Lab.
Information about third-party code
This section provides information about the third-party code used in the application.
Index
This section allows you to quickly find required information within the document.
Page 11
A B O U T T H I S G U I D E
11
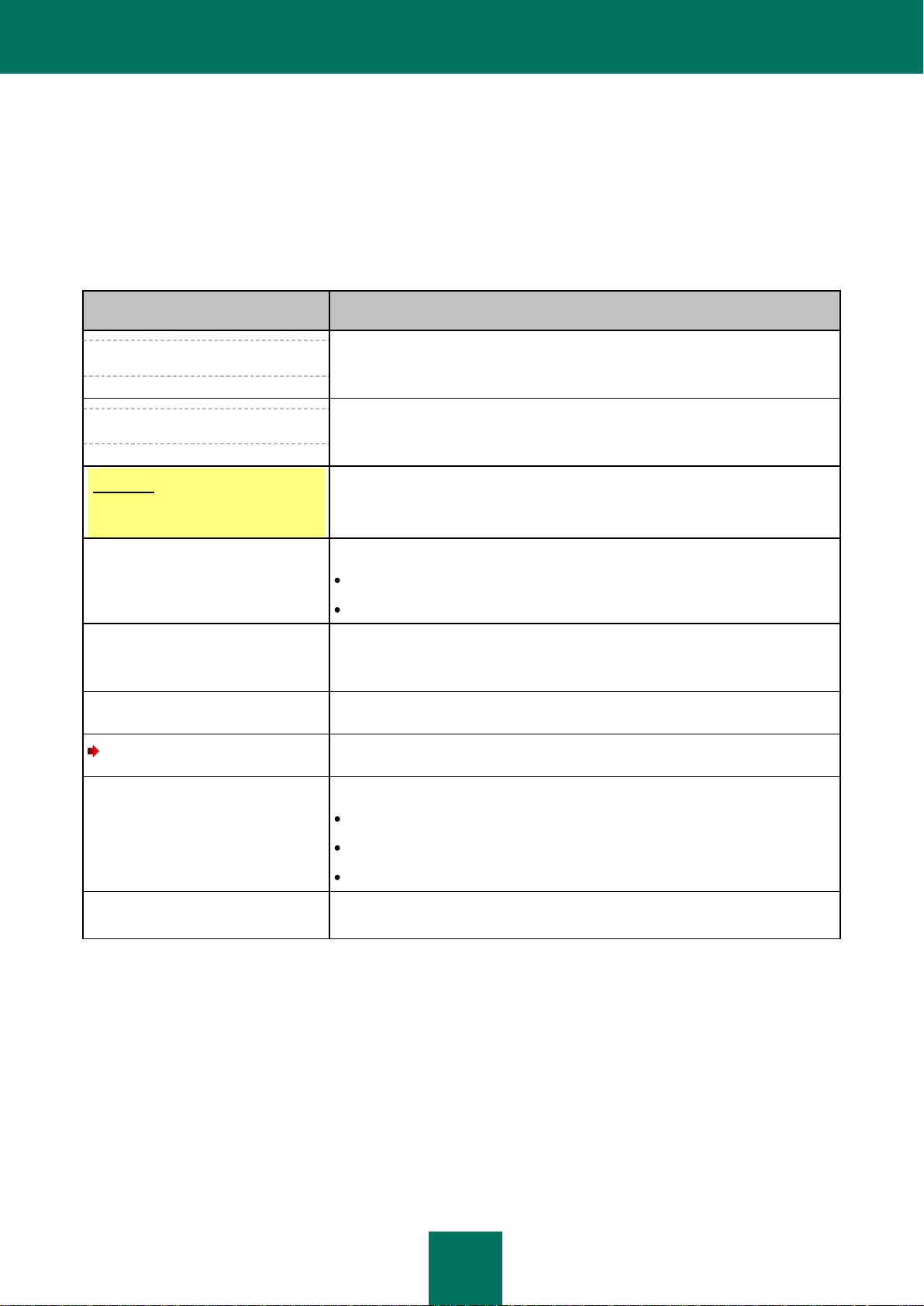
SAMPLE TEXT
DOCUMENT CONVENTIONS DESCRIPTION
Note that...
Warnings are highlighted with red color and boxed.
Warnings provide information about probable unwanted actions that may lead to
data losses or failures in the computer's operation.
It is recommended to use...
Notes are boxed.
Notes may contain useful hints, recommendations, specific values, or important
particular cases in the application's operation.
Example:
...
Examples are set out on a yellow background under the heading "Example".
Update means...
The Databases are out of date event
occurs.
The following semantic elements are italicized in the text:
new terms;
names of application statuses and events.
Press ENTER.
Press ALT+F4.
Names of keyboard keys appear in a bold typeface and are capitalized.
Names of keys connected by a + (plus) sign indicate the use of a key
combination. Those keys should be pressed simultaneously.
Click the Enable button.
Names of application interface elements, such as entry fields, menu items, and
buttons, are set off in bold.
To configure a task schedule:
Introductory phrases of instructions are italicized and accompanied by the arrow
sign.
Enter help in the command line.
The following message then appears:
Specify the date in dd:mm:yy
format.
The following types of text content are set off with a special font:
text in the command line;
text of messages displayed on the screen by the application;
data that the user should enter.
<IP address of your
computer>
Variables are enclosed in angle brackets. Instead of a variable, the
corresponding value should be inserted, with angle brackets omitted.
DOCUMENT CONVENTIONS
The text herein is accompanied by semantic elements that should be given particular attention – warnings, hints,
examples.
Document conventions are used to highlight semantic elements. Document conventions and examples of their use are
shown in the table below.
Table 1. Document conventions
Page 12
12
SOURCES OF INFORMATION ABOUT THE
IN THIS SECTION:
Sources of information for independent research ............................................................................................................ 12
Discussing Kaspersky Lab applications on the Forum .................................................................................................... 13
Contacting the Sales Department ................................................................................................................................... 13
Contacting the Documentation Development Team by email .......................................................................................... 13
APPLICATION
This section describes sources of information about the application and lists websites that you can use to discuss the
application's operation.
You can select the most suitable information source, depending on the issue's level of importance and urgency.
SOURCES OF INFORMATION FOR INDEPENDENT RESEARCH
You can use the following sources to find information about the application:
the application page on the Kaspersky Lab website;
the application page on the Technical Support Service website (Knowledge Base);
online help;
documentation.
If you cannot solve an issue on your own, we recommend that you contact the Technical Support Service at Kaspersky
Lab (see section "Technical support by phone" on page 182).
To use information sources on the Kaspersky Lab website, an Internet connection should be established.
The application page on the Kaspersky Lab website
The Kaspersky Lab website features an individual page for each application.
On such a page (http://www.kaspersky.com/kaspersky_internet_security), you can view general information about an
application, its functions and features.
The page http://www.kaspersky.com features a URL to the eStore. There you can purchase or renew the application.
The application page on the Technical Support Service website (Knowledge Base)
Knowledge Base is a section of the Technical Support Service website that provides recommendations on how to work
with Kaspersky Lab applications. Knowledge Base comprises reference articles grouped by topics.
Page 13
S O U R C E S O F I NF O R M A T I O N A B O U T T H E AP P L I C A T I O N
13
On the page of the application in the Knowledge Base (http://support.kaspersky.com/kis2012), you can read articles that
provide useful information, recommendations, and answers to frequently asked questions on how to purchase, install,
and use the application.
Articles may provide answers to questions that are out of scope of Kaspersky Internet Security, being related to other
Kaspersky Lab applications. They also may contain news from the Technical Support Service.
Online help
The online help of the application comprises help files.
The context help provides information about each window of the application, listing and describing the corresponding
settings and a list of tasks.
The full help provides detailed information about how to manage the computer's protection using the application.
Documentation
The application user guide provides information about how to install, activate, and configure the application, as well as
application operation data. The document also describes the application interface and provides ways of solving typical
user tasks while working with the application.
DISCUSSING KASPERSKY LAB APPLICATIONS ON THE FORUM
If your question does not require an urgent answer, you can discuss it with Kaspersky Lab specialists and other users on
our Forum (http://forum.kaspersky.com).
In this forum you can view existing topics, leave your comments, create new topics.
CONTACTING THE SALES DEPARTMENT
If you have any questions on how to select, purchase, or renew the application, you can contact our Sales Department
specialists in one of the following ways:
By calling our HQ office in Moscow by phone (http://www.kaspersky.com/contacts).
By sending a message with your question to sales@kaspersky.com.
The service is provided in Russian and English.
CONTACTING THE DOCUMENTATION DEVELOPMENT TEAM BY EMAIL
To contact the Documentation Development Team, send an email to docfeedback@kaspersky.com. Please use
"Kaspersky Help Feedback: Kaspersky Internet Security" as the subject line in your message.
Page 14
14
KASPERSKY INTERNET SECURITY
IN THIS SECTION:
What's new ................................ ................................................................ ...................................................................... 14
Distribution kit .................................................................................................................................................................. 14
Service for registered users ............................................................................................................................................ 15
Hardware and software requirements ............................................................................................................................. 15
This section describes the application's features and provides brief information about the application's functions and
components. You will learn what items are included in the distribution kit, and what services are available for registered
users of the application. This section provides information about software and hardware requirements that a computer
should meet to allow a user to install the application on it.
WHAT'S NEW
Kaspersky Internet Security provides the following new features:
The improved interface of the main window of Kaspersky Internet Security ensures quick access to the
application's functions.
The logic of operations with Quarantine and Backup (see page 160) has been improved: now they are
represented on two separate tabs, each of them with its respective unique scope.
The Task Manager has been added for an easy task management in Kaspersky Internet Security (see section
"Managing scan tasks. Task Manager" on page 72).
Participation in the Kaspersky Security Network (see page 174) allows us to identify the reputation of
applications and websites based on data received from users from all over the world.
When Web Anti-Virus is enabled, you can separately enable the heuristic analysis to check web pages for
phishing (see section "Using heuristic analysis when working with Web Anti-Virus" on page 93). When checking
pages for phishing, the heuristic analysis will be applied regardless of whether it has been enabled for Web AntiVirus.
The appearance of Kaspersky Gadget has been redesigned (see page 37).
DISTRIBUTION KIT
You can purchase the application in one of the following ways:
Boxed. Distributed via stores of our partners.
At the online store. Distributed at online stores of Kaspersky Lab (for example, http://www.kaspersky.com,
section eStore) or via partner companies.
Page 15
K A S P E RS K Y I N T E R N E T S E C U R I T Y
15
If you purchase the boxed version of the application, the distribution kit contains the following items:
sealed envelope with the setup CD that contains application files and documentation files;
brief User Guide with an activation code;
license agreement that stipulates the terms, on which you can use the application.
The content of the distribution kit may differ depending on the region, in which the application is distributed.
If you purchase Kaspersky Internet Security at an online store, you copy the application from the website of the store.
Information required for the application activation, will be sent to you by email on payment.
For more details on ways of purchasing and the distribution kit, contact the Sales Department.
SERVICE FOR REGISTERED USERS
On purchasing a user license for the application, you become a registered user of Kaspersky Lab applications and can
benefit from the following services during the entire validity term of the license:
updating databases and providing new versions of the application;
consulting by phone and by email on issues related to installation, configuration, and use of the application;
notifying you of releases of new applications by Kaspersky Lab and new viruses. To use this service, you should
be subscribed to the news delivery from Kaspersky Lab on the Technical Support Service website.
No consulting services are provided on issues related to the functioning of operating systems, third-party
software and technologies.
HARDWARE AND SOFTWARE REQUIREMENTS
To ensure the proper functioning of Kaspersky Internet Security, your computer should meet the following requirements:
General requirements:
480 MB free disk space on the hard drive (including 380 MB on the system drive).
CD / DVD-ROM (for installing Kaspersky Internet Security from a distribution CD).
Internet access (for the application activation and for updating databases and software modules).
Microsoft Internet Explorer 6.0 or higher.
Microsoft Windows Installer 2.0.
Requirements for Microsoft Windows XP Home Edition (Service Pack 2 or higher), Microsoft Windows XP Professional
(Service Pack 2 or higher), and Microsoft Windows XP Professional x64 Edition (Service Pack 2 or higher):
Intel Pentium 800 MHz 32-bit (x86) / 64-bit (x64) processor or higher (or a compatible equivalent);
512 MB free RAM.
Page 16
U S E R G U I DE
16
Requirements for Microsoft Windows Vista Home Basic, Microsoft Windows Vista Home Premium, Microsoft Windows
Vista Business, Microsoft Windows Vista Enterprise, Microsoft Windows Vista Ultimate, Microsoft Windows 7 Starter,
Microsoft Windows 7 Home Basic, Microsoft Windows 7 Home Premium, Microsoft Windows 7 Professional, and
Microsoft Windows 7 Ultimate:
Intel Pentium 1 GHz 32-bit (x86) / 64-bit (x64) processor or higher (or a compatible equivalent).
1 GB free RAM (for 32-bit operating systems); 2 GB free RAM (for 64-bit operating systems).
You cannot enable Safe Run when working under a Microsoft Windows XP (64-bit) operating system. Use of Safe Run is
restricted when working in Microsoft Windows Vista (64-bit) and Microsoft Windows 7 (64-bit) operating systems.
Requirements for netbooks:
Intel Atom 1.6 GHz processor or a compatible equivalent.
Intel GMA950 video card with at least 64 MB of video RAM (or a compatible equivalent).
Screen size no less than 10.1".
Page 17
17
INSTALLING AND REMOVING THE
IN THIS SECTION:
Standard installation procedure ....................................................................................................................................... 17
Updating the previous version of Kaspersky Internet Security ........................................................................................ 22
Non-standard installation scenarios ................................................................................................................................ 26
Getting started ................................................................................................................................................................. 27
Removing the application ................................................................................................................................................ 27
APPLICATION
This section provides information about how to install the application on a computer and how to uninstall it.
STANDARD INSTALLATION PROCEDURE
Kaspersky Internet Security will be installed on your computer in an interactive mode using the Setup Wizard.
The Wizard consists of a series of screens (steps) that you can navigate through using the Back and Next buttons. To
close the Wizard once it has completed its task, click the Finish button. To stop the Wizard at any stage, click the
Cancel button.
If the application protects more than one computer (the maximum number of computers depends on your license), it will
be installed in the same manner on all computers. Note that in this case, according to the license agreement, the license
term begins from the date of the first activation. When you activate the application on the second computers and so on,
the license validity term decreases for the amount of time that has elapsed since the first activation. So, the license
validity term will expire simultaneously for all installed copies of the application.
To install Kaspersky Internet Security on your computer,
run the setup file (the file with an EXE extension) from the CD with the product.
Installation of Kaspersky Internet Security from a setup file downloaded online is identical to installation from the
installation CD.
Page 18
U S E R G U I DE
18
IN THIS SECTION:
Step 1. Searching for a newer version of the application ................................................................................................ 18
Step 2. Making sure the system meets the installation requirements .............................................................................. 18
Step 3. Selecting installation type ................................................................................................................................... 19
Step 4. Reviewing the license agreement ....................................................................................................................... 19
Step 5. Kaspersky Security Network Data Collection Statement ..................................................................................... 19
Step 6. Searching for incompatible applications .............................................................................................................. 19
Step 7. Selecting the destination folder ........................................................................................................................... 20
Step 8. Preparing for installation ..................................................................................................................................... 20
Step 9. Installing .............................................................................................................................................................. 21
Step 10. Finishing the installation .................................................................................................................................... 21
Step 11. Activating the application .................................................................................................................................. 21
Step 12. Registering a user ............................................................................................................................................. 21
Step 13. Completing the activation .................................................................................................................................. 22
STEP 1. SEARCHING FOR A NEWER VERSION OF THE APPLICATION
Before setup, the Setup Wizard checks the Kaspersky Lab update servers for a newer version of Kaspersky Internet
Security.
If it does not find a newer product version on the Kaspersky Lab update servers, the Setup Wizard for the current version
will be started.
If the update servers offer a newer version of Kaspersky Internet Security, you will see a prompt to download and install it
on the computer. It is recommended that you install the new version of the application, because newer versions include
further enhancements that ensure you have the most reliable protection for your computer. If you cancel the new version
download, the Setup Wizard for the current version will be started. If you decide to install the newer version, product
distribution files will be downloaded to your computer and the Setup Wizard for that new version will be started
automatically. For a further description of the installation procedure for the newer version, please refer to the
corresponding documentation.
STEP 2. MAKING SURE THE SYSTEM MEETS THE INSTALLATION
REQUIREMENTS
Before installation of Kaspersky Internet Security on your computer, the installer checks the operating system and
service packs to make sure they meet the software requirements for product installation (see section "Hardware and
software requirements" on page 15). In addition, the installer checks for the presence of required software and the
credentials necessary to install applications. If any of the above-listed requirements is not met, a notification to that effect
will be displayed on the screen.
If the computer meets all the requirements, the Wizard searches for Kaspersky Lab applications which, when run
together with Kaspersky Internet Security, may result in conflicts. If such applications are found, you will be asked to
remove them manually.
Page 19
I N S T A L L I N G A N D R E M O V I N G T H E A P P L I C A T I O N
19
If an earlier version of Kaspersky Anti-Virus or Kaspersky Internet Security is found, all data that can be used by
Kaspersky Internet Security 2012 (for example, activation information or application settings) will be saved and used
when installing the new application, while the one installed earlier will be automatically removed.
STEP 3. SELECTING INSTALLATION TYPE
At this step, you can choose the most suitable type of Kaspersky Internet Security installation:
Standard installation. If you choose this option (the Change installation settings box is unchecked), the
application will be fully installed on your computer with the protection settings recommended by Kaspersky Lab
experts.
Custom installation. In this case (the Change installation settings box is checked), you will be asked to specify
the destination folder into which the application should be installed (see section "Step 7. Selecting the
destination folder" on page 20) and disable the installation process protection, if necessary (see section "Step 8.
Preparing for installation" on page 20).
To proceed with the installation, click the Next button.
STEP 4. REVIEWING THE LICENSE AGREEMENT
At this step, you should review the license agreement between you and Kaspersky Lab.
Read the agreement carefully and, if you accept all its terms, click the I agree button. The installation will continue.
If you cannot accept the license agreement, cancel the application installation by clicking the Cancel button.
STEP 5. KASPERSKY SECURITY NETWORK DATA COLLECTION STATEMENT
At this stage, you will be invited to participate in the Kaspersky Security Network. Participation in the program involves
sending information about new threats detected on your computer, running applications, and downloaded signed
applications, as well as your system information, to Kaspersky Lab. We guarantee that none of your personal data will be
sent.
Review the Kaspersky Security Network Data Collection Statement. To read the complete version of the Statement, click
the Full KSN Agreement button. If you agree with all terms of the Statement, check the I accept the terms of
participation in Kaspersky Security Network box in the Wizard window.
Click the Next button if you have selected the custom installation (see section "Step 3. Selecting installation type" on
page 19). If performing the standard installation, click the Install button. The installation will continue.
STEP 6. SEARCHING FOR INCOMPATIBLE APPLICATIONS
At this step, the application checks whether any applications incompatible with Kaspersky Internet Security are installed
on your computer.
If no such applications are found, the Wizard automatically proceeds to the next step.
If any incompatible applications are detected, they are displayed in a list on the screen, and you will be prompted to
remove them. Applications that Kaspersky Internet Security cannot remove automatically should be removed manually.
When removing incompatible applications, you will need to reboot your operating system, after which installation of
Kaspersky Internet Security will continue automatically.
To proceed with the installation, click the Next button.
Page 20
U S E R G U I DE
20
STEP 7. SELECTING THE DESTINATION FOLDER
This step of the Setup Wizard is only available if the custom installation is selected (see section "Step 3. Selecting
installation type" on page 19). When performing a standard installation, this step is skipped and the application is
installed to the default folder.
At this stage you are asked to choose the folder to which Kaspersky Internet Security will be installed. The following path
is set by default:
<disk>\Program Files\Kaspersky Lab\Kaspersky Internet Security 2012 – for 32-bit systems;
<disk>\Program Files (х86)\Kaspersky Lab\Kaspersky Internet Security 2012 – for 64-bit systems.
To install Kaspersky Internet Security to a different folder, specify the path to the desired folder in the input field or click
the Browse button and choose a folder in the window that opens.
Keep in mind the following restrictions:
The application cannot be installed on network or removable drives, or on virtual drives (those created using the
SUBST command).
We recommend that you avoid installing the application in a folder that already contains files or other folders,
because that folder will then become inaccessible for editing.
The path to the installation folder cannot be longer than 160 characters or contain the special characters
/, ?, :, *, ", >, < or |.
To find out if there is enough disk space on your computer to install the application, click the Disk Usage button. In the
window that opens you can view the disk space information. To close the window, click OK.
To proceed with the installation, click the Next button in the Wizard window.
STEP 8. PREPARING FOR INSTALLATION
This step of the Setup Wizard is only available if the custom installation is selected (see section "Step 3. Selecting
installation type" on page 19). For the standard installation, this step is skipped.
Since your computer may be infected with malicious programs that may impact the installation of Kaspersky Internet
Security, the installation process should be protected.
By default, installation process protection is enabled – the Protect the installation process box is checked in the
Wizard window.
You are advised to uncheck this box if the application cannot be installed (for example, when performing remote
installation using Windows Remote Desktop). Enabled protection may be the reason.
In this case, you should interrupt installation, restart it, check the Change installation settings box at the Select
installation type step (see section "Step 3. Selecting installation type" on page 19), and when you reach the Preparing for
installation step, uncheck the Protect the installation process box.
To proceed with the installation, click the Install button.
When installing the application on a computer running under Microsoft Windows XP, active network connections are
terminated. The majority of terminated connections are restored after a pause.
Page 21
I N S T A L L I NG A N D R E M O V I N G T H E A P P L I C A T I O N
21
STEP 9. INSTALLING
Installation of the application can take some time. Wait for it to finish.
Once the installation is complete, the Wizard will automatically proceed to the next step.
If an installation error occurs, which may be due to malicious programs that prevent anti-virus applications from being
installed on your computer, the Setup Wizard will prompt you to download Kaspersky Virus Removal Tool, a special
utility for neutralizing infections.
If you agree to install the utility, the Setup Wizard downloads it from the Kaspersky Lab servers, after which installation of
the utility starts automatically. If the Wizard cannot download the utility, you will be asked to download it on your own by
clicking the link provided.
After you finish working with the utility, you should delete it and restart the installation of Kaspersky Internet Security.
STEP 10. FINISHING THE INSTALLATION
This window of the Wizard informs you of the successful completion of the application installation. To run Kaspersky
Internet Security, make sure that the Run Kaspersky Internet Security 2012 box is checked and click the Finish
button.
In some cases, you may need to reboot your operating system. If the Run Kaspersky Internet Security 2012 box is
checked, the application will be run automatically after you reboot your operating system.
If you unchecked the box before closing the Wizard, you should run the application manually (see section "Launching
and closing the application manually" on page 38).
STEP 11. ACTIVATING THE APPLICATION
Activation is the procedure of activating a license that allows you to use a fully functional version of the application until
the license expires.
You will need an Internet connection to activate the application.
You will be offered the following options for Kaspersky Internet Security activation:
Activate commercial version. Select this option and enter the activation code if you have purchased a
commercial version of the application.
If you specify an activation code for Kaspersky Anti-Virus in the entry field, the procedure of switching to
Kaspersky Anti-Virus starts after the completion of activation.
Activate trial version. Use this activation option if you want to install the trial version of the application before
making the decision to purchase a commercial version. You will be able to use the fully-functional version of the
application for the duration of a term limited by the license for the trial version of the application. When the
license expires, it cannot be activated for a second time.
STEP 12. REGISTERING A USER
This step is only available when activating the commercial version of the application. When activating the trial version,
this step is skipped.
Page 22
U S E R G U I DE
22
You need to register in order to be able to contact Kaspersky Lab Technical Support Service in the future.
If you agree to register, specify your registration data in the corresponding fields and click the Next button.
STEP 13. COMPLETING THE ACTIVATION
The Wizard informs you that Kaspersky Internet Security has been successfully activated. In addition, information about
the license is provided: license type (commercial or trial), date of expiry, and number of hosts for the license.
If you have activated a subscription, information about the subscription status is displayed instead of the license expiry
date.
Click the Finish button to close the Wizard.
UPDATING THE PREVIOUS VERSION OF KASPERSKY INTERNET SECURITY
If Kaspersky Internet Security 2010 or 2011 is already installed on your computer, you should update the application to
Kaspersky Internet Security 2012. If you have an active license for Kaspersky Internet Security 2010 or 2011, you will not
have to activate the application: the Setup Wizard will automatically retrieve the information about your license for
Kaspersky Internet Security 2010 or 2011 and use it during the installation process.
Kaspersky Internet Security will be installed on your computer in an interactive mode using the Setup Wizard.
The Wizard consists of a series of screens (steps) that you can navigate through using the Back and Next buttons. To
close the Wizard once it has completed its task, click the Finish button. To stop the Wizard at any stage, click the
Cancel button.
If the application protects more than one computer (the maximum number of computers depends on your license), it will
be installed in the same manner on all computers. Note that in this case, according to the license agreement, the license
term begins from the date of the first activation. When you activate the application on the second computers and so on,
the license validity term decreases for the amount of time that has elapsed since the first activation. So, the license
validity term will expire simultaneously for all installed copies of the application.
To install Kaspersky Internet Security on your computer,
run the setup file (the file with an EXE extension) from the CD with the product.
Installation of Kaspersky Internet Security from a setup file downloaded online is identical to installation from the
installation CD.
Page 23
I N S T A L L I N G A N D R E M O V I N G T H E A P P L I C A T I O N
23
IN THIS SECTION:
Step 1. Searching for a newer version of the application ................................................................................................ 23
Step 2. Making sure the system meets the installation requirements .............................................................................. 23
Step 3. Selecting installation type ................................................................................................................................... 24
Step 4. Reviewing the license agreement ....................................................................................................................... 24
Step 5. Kaspersky Security Network Data Collection Statement ..................................................................................... 24
Step 6. Searching for incompatible applications .............................................................................................................. 24
Step 7. Selecting the destination folder ........................................................................................................................... 25
Step 8. Preparing for installation ..................................................................................................................................... 25
Step 9. Installing .............................................................................................................................................................. 26
Step 10. Wizard completion ............................................................................................................................................ 26
STEP 1. SEARCHING FOR A NEWER VERSION OF THE APPLICATION
Before setup, the Setup Wizard checks the Kaspersky Lab update servers for a newer version of Kaspersky Internet
Security.
If it does not find a newer product version on the Kaspersky Lab update servers, the Setup Wizard for the current version
will be started.
If the update servers offer a newer version of Kaspersky Internet Security, you will see a prompt to download and install it
on the computer. It is recommended that you install the new version of the application, because newer versions include
further enhancements that ensure you have the most reliable protection for your computer. If you cancel the new version
download, the Setup Wizard for the current version will be started. If you decide to install the newer version, product
distribution files will be downloaded to your computer and the Setup Wizard for that new version will be started
automatically. For a further description of the installation procedure for the newer version, please refer to the
corresponding documentation.
STEP 2. MAKING SURE THE SYSTEM MEETS THE INSTALLATION
REQUIREMENTS
Before installation of Kaspersky Internet Security on your computer, the installer checks the operating system and
service packs to make sure they meet the software requirements for product installation (see section "Hardware and
software requirements" on page 15). In addition, the installer checks for the presence of required software and the
credentials necessary to install applications. If any of the above-listed requirements is not met, a notification to that effect
will be displayed on the screen.
If the computer meets all the requirements, the Wizard searches for Kaspersky Lab applications which, when run
together with Kaspersky Internet Security, may result in conflicts. If such applications are found, you will be asked to
remove them manually.
If an earlier version of Kaspersky Anti-Virus or Kaspersky Internet Security is found, all data that can be used by
Kaspersky Internet Security 2012 (for example, activation information or application settings) will be saved and used
when installing the new application, while the one installed earlier will be automatically removed.
Page 24
U S E R G U I DE
24
STEP 3. SELECTING INSTALLATION TYPE
At this step, you can choose the most suitable type of Kaspersky Internet Security installation:
Standard installation. If you choose this option (the Change installation settings box is unchecked), the
application will be fully installed on your computer with the protection settings recommended by Kaspersky Lab
experts.
Custom installation. In this case (the Change installation settings box is checked), you will be asked to specify
the destination folder into which the application should be installed (see section "Step 7. Selecting the
destination folder" on page 20) and disable the installation process protection, if necessary (see section "Step 8.
Preparing for installation" on page 20).
To proceed with the installation, click the Next button.
STEP 4. REVIEWING THE LICENSE AGREEMENT
At this step, you should review the license agreement between you and Kaspersky Lab.
Read the agreement carefully and, if you accept all its terms, click the I agree button. The installation will continue.
If you cannot accept the license agreement, cancel the application installation by clicking the Cancel button.
STEP 5. KASPERSKY SECURITY NETWORK DATA COLLECTION STATEMENT
At this stage, you will be invited to participate in the Kaspersky Security Network. Participation in the program involves
sending information about new threats detected on your computer, running applications, and downloaded signed
applications, as well as your system information, to Kaspersky Lab. We guarantee that none of your personal data will be
sent.
Review the Kaspersky Security Network Data Collection Statement. To read the complete version of the Statement, click
the Full KSN agreement button. If you agree with all terms of the Statement, check the I accept the terms of
participation in Kaspersky Security Network box in the Wizard window.
Click the Next button if you have selected the custom installation (see section "Step 3. Selecting installation type" on
page 19). If performing the standard installation, click the Install button. The installation will continue.
STEP 6. SEARCHING FOR INCOMPATIBLE APPLICATIONS
At this step, the application checks whether any applications incompatible with Kaspersky Internet Security are installed
on your computer.
If no such applications are found, the Wizard automatically proceeds to the next step.
If any incompatible applications are detected, they are displayed in a list on the screen, and you will be prompted to
remove them. Applications that Kaspersky Internet Security cannot remove automatically should be removed manually.
When removing incompatible applications, you will need to reboot your operating system, after which installation of
Kaspersky Internet Security will continue automatically.
To proceed with the installation, click the Next button.
Page 25
I N S T A L L I N G A N D R E M O V I N G T H E A P P L I C A T I O N
25
STEP 7. SELECTING THE DESTINATION FOLDER
This step of the Setup Wizard is only available if the custom installation is selected (see section "Step 3. Selecting
installation type" on page 19). When performing a standard installation, this step is skipped and the application is
installed to the default folder.
At this stage you are asked to choose the folder to which Kaspersky Internet Security will be installed. The following path
is set by default:
<disk>\Program Files\Kaspersky Lab\Kaspersky Internet Security 2012 – for 32-bit systems;
<disk>\Program Files (х86)\Kaspersky Lab\Kaspersky Internet Security 2012 – for 64-bit systems.
To install Kaspersky Internet Security to a different folder, specify the path to the desired folder in the input field or click
the Browse button and choose a folder in the window that opens.
Keep in mind the following restrictions:
The application cannot be installed on network or removable drives, or on virtual drives (those created using the
SUBST command).
We recommend that you avoid installing the application in a folder that already contains files or other folders,
because that folder will then become inaccessible for editing.
The path to the installation folder cannot be longer than 160 characters or contain the special characters
/, ?, :, *, ", >, < or |.
To find out if there is enough disk space on your computer to install the application, click the Disk Usage button. In the
window that opens you can view the disk space information. To close the window, click OK.
To proceed with the installation, click the Next button in the Wizard window.
STEP 8. PREPARING FOR INSTALLATION
This step of the Setup Wizard is only available if the custom installation is selected (see section "Step 3. Selecting
installation type" on page 19). For the standard installation, this step is skipped.
Since your computer may be infected with malicious programs that may impact the installation of Kaspersky Internet
Security, the installation process should be protected.
By default, installation process protection is enabled – the Protect the installation process box is checked in the
Wizard window.
You are advised to uncheck this box if the application cannot be installed (for example, when performing remote
installation using Windows Remote Desktop). Enabled protection may be the reason.
In this case, you should interrupt installation, restart it, check the Change installation settings box at the Select
installation type step (see section "Step 3. Selecting installation type" on page 19), and when you reach the Preparing for
installation step, uncheck the Protect the installation process box.
To proceed with the installation, click the Install button.
When installing the application on a computer running under Microsoft Windows XP, active network connections are
terminated. The majority of terminated connections are restored after a pause.
Page 26
U S E R G U I DE
26
STEP 9. INSTALLING
Installation of the application can take some time. Wait for it to finish.
Once the installation is complete, the Wizard will automatically proceed to the next step.
If an installation error occurs, which may be due to malicious programs that prevent anti-virus applications from being
installed on your computer, the Setup Wizard will prompt you to download Kaspersky Virus Removal Tool, a special
utility for neutralizing infections.
If you agree to install the utility, the Setup Wizard downloads it from the Kaspersky Lab servers, after which installation of
the utility starts automatically. If the Wizard cannot download the utility, you will be asked to download it on your own by
clicking the link provided.
After you finish working with the utility, you should delete it and restart the installation of Kaspersky Internet Security.
STEP 10. WIZARD COMPLETION
This window of the Wizard informs you of the successful completion of the application installation. To run Kaspersky
Internet Security, make sure that the Run Kaspersky Internet Security 2012 box is checked and click the Finish
button.
In some cases, you may need to reboot your operating system. If the Run Kaspersky Internet Security 2012 box is
checked, the application will be run automatically after you reboot your operating system.
If you unchecked the box before closing the Wizard, you should run the application manually (see section "Launching
and closing the application manually" on page 38).
NON-STANDARD INSTALLATION SCENARIOS
This section describes application installation scenarios which differ from those of standard installation or update from
the previous version.
Installing Kaspersky Internet Security and activating later using a Kaspersky Anti-Virus activation
code
If, when installing Kaspersky Internet Security, at the Activating the application step, you enter a Kaspersky Anti-Virus
activation code, a switching procedure starts which results in Kaspersky Anti-Virus being installed on your computer.
If, when installing Kaspersky Internet Security, at the Activating the application step, you select Activate later and then
activate the installed application with a Kaspersky Anti-Virus activation code, the switching procedure also starts, which
results in Kaspersky Anti-Virus being installed on your computer.
Installing Kaspersky Internet Security 2012 over Kaspersky Anti-Virus 2010 or 2011
If you run the installation of Kaspersky Internet Security 2012 on a computer, on which Kaspersky Anti-Virus 2010 or
2011 with an active license is already installed, the Setup Wizard detects the information about the license and prompts
you to select one of the following further actions:
Use the current license of Kaspersky Anti-Virus 2010 or 2011. In this case, the switching procedure starts,
which results in Kaspersky Anti-Virus 2012 being installed on your computer. You will be able to use Kaspersky
Anti-Virus 2012 as long as the license for Kaspersky Anti-Virus 2010 or 2011 remains valid.
Proceed with installation of Kaspersky Internet Security 2012. In this case, the installation procedure will
continue according to the standard scenario, starting from the Activating the application step.
Page 27
I N S T A L L I N G A N D R E M O V I N G T H E A P P L I C A T I O N
27
IN THIS SECTION:
Step 1. Saving data for reuse .......................................................................................................................................... 27
Step 2. Confirmation of application removal .................................................................................................................... 28
Step 3. Removing the application. Completing removal .................................................................................................. 28
GETTING STARTED
The application is ready to be used after installation. To ensure proper protection of your computer, we recommend
performing the following immediately after installation and configuration:
Update application databases (see section "How to update application databases and modules" on page 45).
Scan your computer for viruses (see section "How to perform a full scan of your computer for viruses" on
page 48) and vulnerabilities (see section "How to scan your computer for vulnerabilities" on page 48).
Check the protection status of your computer and eliminate problems in protection, if necessary.
REMOVING THE APPLICATION
After uninstalling Kaspersky Internet Security, your computer and personal data will be unprotected!
Kaspersky Internet Security is uninstalled with the help of the Setup Wizard.
To start the Wizard,
in the Start menu, select Programs Kaspersky Internet Security 2012 Remove Kaspersky Internet
Security 2012.
STEP 1. SAVING DATA FOR REUSE
At this point you can specify which of the data used by the application you want to retain for reuse during the next
installation of the application (e.g., a newer version of the application).
By default, the application is completely removed from the computer.
To save data for reuse:
1. Choose the option Save application objects.
2. Check the boxes for the data types you want to save:
Activation data – data that eliminates the need to activate the application in the future by automatically
using the current license as long as it has not expired by the time of the next installation.
Backup and Quarantine files – files checked by the application and placed into backup storage or
quarantine.
Operational settings of the application – values of the application settings selected during configuration.
iChecker data – files which contain information about the objects that have already been scanned for
viruses.
Page 28

U S E R G U I DE
28
Anti-Spam databases – databases containing signatures of spam messages downloaded and saved by
the application.
Safe Run shared folder data – files saved by the application when working in a safe environment in a
special folder that is also accessible in the normal environment.
STEP 2. CONFIRMATION OF APPLICATION REMOVAL
Since removing the application threatens the security of the computer and your personal data, you will be asked to
confirm your intention to remove the application. To do this, click the Remove button.
To stop removal of the application at any time, you can cancel this operation by clicking the Cancel button.
STEP 3. REMOVING THE APPLICATION. COMPLETING REMOVAL
At this step, the Wizard removes the application from your computer. Wait until removal is complete.
When removing the application, you may need to reboot your operating system. If you cancel the immediate reboot,
completion of the removal procedure will be postponed until the operating system is rebooted or the computer is turned
off and then restarted.
Page 29
29
LICENSING THE APPLICATION
IN THIS SECTION:
About the End User License Agreement ......................................................................................................................... 29
About data provision ....................................................................................................................................................... 29
About the license ............................................................................................................................................................. 29
About the activation code ................................................................................................................................................ 30
This section provides information about general terms related to the application activation. Read this section to learn
more about the purpose of the license agreement, license types, ways of activating the application, and the license
renewal.
ABOUT THE END USER LICENSE AGREEMENT
License Agreement is a legal agreement concluded between you and Kaspersky Lab ZAO that stipulates the terms of
use for the application.
Read through the terms of the License Agreement carefully before you start using the application.
You can read through the terms of the License Agreement when installing the Kaspersky Lab application.
The terms of the License Agreement are regarded as accepted in the following cases:
Upon unsealing the box with the setup CD (only if you have purchased the application in the boxed version or at
a store of any of our partners).
Upon confirming your acceptance of the text of the License Agreement when installing the application.
If you do not accept the terms of the License Agreement, you have to interrupt the application installation.
ABOUT DATA PROVISION
In order to increase the level of real-time protection, accepting the terms of the License Agreement means that you agree
to send information about checksums of processed objects (MD5), information required to determine the reputation of
URLs, and statistical data for anti-spam protection, in automatic mode. Information retrieved does not contain any private
data and other types of confidential information. Information retrieved is protected by Kaspersky Lab pursuant to the
requirements stipulated by the existing legislation. You can obtain more details on the website:
http://support.kaspersky.com.
ABOUT THE LICENSE
License is a time-limited right to use the application provided to you in accordance with the License Agreement. The
license contains a unique code for the activation of your copy of Kaspersky Internet Security.
Page 30
U S E R G U I DE
30
The license grants you the right to benefit the following services:
Using the application on one or several devices.
Number of devices, on which you can use the application, is specified in the License Agreement.
Contacting the Technical Support Service of Kaspersky Lab.
Enjoying the complete set of services provided to you by Kaspersky Lab or its partners during the validity term
of the license (see section "Service for registered users" on page 15).
The scope of services provided and the validity term of the application depend on the type of license used to activate the
application.
The following license types are provided:
Trial – a free license with a limited validity period, offered to allow you to become familiar with the application.
If you copy the application from the website http://www.kaspersky.com, you automatically become the owner of
the trial license. As soon as the license expires, all Kaspersky Internet Security features are disabled. To
continue using the application, you should purchase the commercial license.
Commercial – a paid license with a limited validity period, offered upon purchase of the application.
After the expiration of the commercial license, the application keeps on running in limited functionality mode.
You will still be able to scan your computer for viruses and use other application components but only with
databases installed before the license has expired. To continue using Kaspersky Internet Security, you should
renew the commercial license.
We recommend that you renew the license on the day the current license expires at the latest in order to ensure
the most comprehensible anti-virus protection of your computer.
ABOUT THE ACTIVATION CODE
Activation code is a code that you receive on purchasing the commercial license for Kaspersky Internet Security. This
code is required for activation of the application.
The activation code is an alphanumeric string of Latin characters in xxxxx-xxxxx-xxxxx-xxxxx format.
The activation code is provided in one of the following forms, depending on the way you purchase the application:
If you have purchased the boxed version of Kaspersky Internet Security, the activation code is specified in the
documentation or on the box containing the setup CD.
If you have purchased Kaspersky Internet Security at an online store, the activation code is sent to the email
address that you have specified when ordering the product.
The validity term of the license starts from the moment you have activated the application. If you have purchased a
license intended for the use of Kaspersky Internet Security on several devices, the validity term of the license starts
counting down from the moment you have entered the code on the first of those devices.
If you have lost or accidentally deleted your activation code after the activation, you should send a request to the
Technical Support Service at Kaspersky Lab from My Kaspersky Account (see section "Obtaining technical support via
My Kaspersky Account" on page 182).
On completion of the application activation with a code, you are assigned a client ID. Client ID is the personal ID for a
user, that is needed for receiving technical support by phone or via My Kaspersky Account (see section "Obtaining
technical support via My Kaspersky Account" on page 182).
Page 31
31
APPLICATION INTERFACE
IN THIS SECTION:
The notification area icon ................................................................................................................................................ 31
The context menu ........................................................................................................................................................... 32
The Kaspersky Internet Security main window ................................................................................................................ 33
Notification windows and pop-up messages ................................................................................................................... 34
The application settings window ...................................................................................................................................... 36
The Kaspersky Gadget.................................................................................................................................................... 37
News Agent ..................................................................................................................................................................... 37
This section provides information about basic elements of the graphic interface of the application: application icon and
application icon context menu, main window, settings window, and notification windows.
THE NOTIFICATION AREA ICON
Immediately after installation of the application, the application icon appears in the Microsoft Windows taskbar notification
area.
In the Microsoft Windows 7 operating system the application icon is hidden by default, but you can display it to access
the application more easily (see the operating system documentation).
The icon has the following purposes:
It is an indicator of the application's operation.
It provides access to the context menu, the main application window and the news window.
Indication of application operation
This icon serves as an indicator of the application's operation. It also indicates the protection status and displays the
basic functions currently being performed by the application:
– scanning an email message;
– scanning web traffic;
– updating databases and application modules;
– computer needs to be restarted to apply updates;
– a failure occurred in the operation of an application component.
Page 32

U S E R G U I DE
32
The icon is animated by default: for example, during the email message scan, a tiny letter symbol blinks in front of the
application icon; when the update is in progress, you see a revolving globe. Animation can be deactivated (see section
"Translucence of notification windows" on page 171).
When the animation is disabled, the icon may take the following forms:
(colored symbol) – all or some protection components are activated;
(black-and-white symbol) – all protection components are disabled.
Access to the context menu and application windows
Using the icon, you can open the context menu (on page 32) (by right-clicking) and the main application window (see
section "The Kaspersky Internet Security main window" on page 33) (by left-clicking).
If news from Kaspersky Lab is available, the icon appears in the Microsoft Windows taskbar notification area. Doubleclick this icon to open the News Agent (see section "News Agent" on page 37).
THE CONTEXT MENU
Using the context menu, you can quickly take various actions on the application.
The Kaspersky Internet Security menu contains the following items:
Task Manager – opens the Task Manager window.
Update – runs the update of application databases and modules.
Tools – opens a submenu containing the following items:
Applications Activity – opens the Applications Activity window;
Network Monitor – opens the Network Monitor window;
Virtual Keyboard – displays the Virtual Keyboard.
Safe Run for Applications – runs a safe desktop designed for handling applications that you suppose to be
unsafe. If Safe Run for Applications is already active, the application switches to it.
When working with Safe Run for Applications, this menu item is named Return to the main desktop, serving
for switching to the main desktop.
Kaspersky Internet Security – opens the main application window.
Pause protection / Resume protection – temporarily disables / enables real-time protection components. This
menu item does not affect the application's updates or the execution of virus scans.
Enable Parental Control / Disable Parental Control – enables / disables Parental Control for the current
account.
Settings – opens the application settings window.
About – opens a window containing information about the application.
Page 33

A P P L I C A T I O N I N T E R F AC E
33
News – opens the News Agent window (see section "News Agent" on page 37). This menu item is displayed if
there is unread news.
Exit – closes Kaspersky Internet Security (when this item is selected, the application is unloaded from the
computer’s RAM).
Figure 1. The context menu
If a virus scan or update task is running at the moment that you open the context menu, its name as well as its progress
status (percentage complete) is displayed in the context menu. If you select a menu item with the name of a task, you
can switch to the main window with a report of current task run results.
To open the context menu,
position the cursor over the application icon in the taskbar notification area and right-click it.
In the Microsoft Windows 7 operating system the application icon is hidden by default, but you can display it to access
the application more easily (see the operating system documentation).
THE KASPERSKY INTERNET SECURITY MAIN WINDOW
The main application window contains interface elements that provide access to all the main features of the application.
The main window can be divided into two parts:
The top part of the window provides information about the protection status of your computer.
Figure 2. Top part of the main window
Page 34

U S E R G U I DE
34
In the bottom part of the window, you can quickly switch to using the main features of the application (for
example, running virus scan tasks, updating databases and software modules).
Figure 3. Bottom part of the main window
If you select any of the sections in the bottom part of the window, the window of the corresponding function opens. You
can return to selecting functions by clicking the Back button in the top left corner of the window.
You can also use the following buttons and links:
Cloud protection – to switch to information about Kaspersky Security Network (on page 174).
Settings – to open the application settings window (see section "The application settings window" on page 36).
Reports – to switch to the application operation reports.
News – to switch to viewing news in the News Agent window (see section "News Agent" on page 37). This link
is displayed after the application receives a piece of news.
Help – to view the Kaspersky Internet Security help system.
My Kaspersky Account – to enter the user's personal account on the Technical Support Service website.
Support – to open the window containing information about the system and links to Kaspersky Lab information
resources (Technical Support Service website, forum).
Manage License – to go to Kaspersky Internet Security activation and license renewal.
You can open the main application window using one of the following methods:
By left-clicking the application icon in the taskbar notification area.
In the Microsoft Windows 7 operating system the application icon is hidden by default, but you can display it to
access the application more easily (see the operating system documentation).
By selecting Kaspersky Internet Security from the context menu (see section "Context menu" on page 32).
By clicking the Kaspersky Internet Security icon located in the center of the Kaspersky Gadget (only for
Microsoft Windows Vista and Microsoft Windows 7).
NOTIFICATION WINDOWS AND POP-UP MESSAGES
Kaspersky Internet Security notifies you of important events occurring during its operation using notification windows and
pop-up messages that appear over the application icon in the taskbar notification area.
Page 35

A P P L I C A T I O N I N T E R F AC E
35
Notification windows are displayed by Kaspersky Internet Security when various actions can be taken in connection with
an event: for example, if a malicious object is detected, you can block access to it, delete it, or try to disinfect it. The
application prompts you to select one of the available actions. A notification window only disappears from the screen if
you select one of the actions.
Figure 4. Notification window
Pop-up messages are displayed by Kaspersky Internet Security in order to inform you of events that do not require you
to select an action. Some pop-up messages contain links that you can use to take an action offered by the application:
for example, run a database update or initiate activation of the application). Pop-up messages automatically disappear
from the screen soon after they appear.
Figure 5. Pop-up message
Depending on the importance of an event for the viewpoint of the computer's security, notifications and pop-up
messages are divided into three types:
Critical notifications – inform you of events that have a critical importance for the computer's security, such as
detection of a malicious object or a dangerous activity in the system. Windows of critical notifications and popup messages are red-colored.
Important notifications – inform you of events that are potentially important for the computer's security, such as
detection of a potentially infected object or a suspicious activity in the system. Windows of important
notifications and pop-up messages are yellow-colored.
Information notifications – inform you of events that do not have critical importance for the computer's security.
Windows of information notifications and pop-up messages are green-colored.
Page 36

U S E R G U I DE
36
THE APPLICATION SETTINGS WINDOW
The Kaspersky Internet Security settings window (also referred to as "settings window") is designed for configuring the
entire application and separate protection components, scanning and update tasks, and for running other advanced
configuration tasks (see section "Advanced application settings" on page 62).
Figure 6. The application settings window
The application settings window consists of two parts:
in the left part of the window you can choose the application component, task or another item that should be
configured;
the right part of the window contains the controls that you can use to configure the item selected in the left part
of the window.
The components, tasks and other items in the left part of the window are grouped in the following sections:
– Protection Center;
– Scan;
– Update;
– Advanced Settings.
Page 37

A P P L I C A T I O N I N T E R F AC E
37
You can open the settings window using one of the following methods:
by clicking the Settings link in the top part of the main application window (see section "The Kaspersky Internet
Security main window" on page 33);
by selecting Kaspersky Internet Security from the context menu (see section "Context menu" on page 32);
by clicking the button with the Settings icon in the Kaspersky Gadget interface (only for Microsoft Windows
Vista and Microsoft Windows 7 operating systems). The function of opening the settings window should be
assigned to the button (see section "How to use the Kaspersky Gadget" on page 59).
THE KASPERSKY GADGET
When using Kaspersky Internet Security on a computer running under Microsoft Windows Vista or Microsoft Windows 7,
you can also use the Kaspersky Gadget (hereinafter the gadget). The Kaspersky Gadget is designed for quick access to
the main features of the application (for example, protection status indication, virus scanning of objects, application
operation reports).
After you install Kaspersky Internet Security on a computer running under Microsoft Windows 7, the gadget appears on
your desktop automatically. After you install the application on a computer running under Microsoft Windows Vista, you
should add the gadget to the Microsoft Windows Sidebar manually (see the operating system documentation).
Figure 7. The Kaspersky Gadget
NEWS AGENT
Using News Agent, Kaspersky Lab informs you of all important events related to Kaspersky Internet Security and protection against computer threats.
The application will notify you of news by displaying a special icon in the taskbar notification area (see below) and a popup message. Information about the number of unread news items is also displayed in the main application window. A
news icon appears in the Kaspersky Internet Security gadget interface.
You can read the news in one of the following ways:
by clicking the icon in the taskbar notification area;
by clicking the Read news link in the pop-up news message;
by clicking the News link in the main application window;
by clicking the icon which is displayed in the center of the Gadget when a piece of news appears (only for
Microsoft Windows Vista and Microsoft Windows 7).
The above-listed methods of opening the News Agent window are only operable if any unread news is available.
If you do not want to receive any news, you can disable the news delivery.
Page 38

38
STARTING AND STOPPING THE
IN THIS SECTION:
Enabling and disabling automatic launch ........................................................................................................................ 38
Launching and closing the application manually ............................................................................................................. 38
APPLICATION
This section contains information on starting and shutting down the application.
ENABLING AND DISABLING AUTOMATIC LAUNCH
Automatic launch of the application means that Kaspersky Internet Security launches after the operating system startup.
This is the default start mode.
To disable or enable automatic launch of the application:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the General Settings subsection.
3. To disable automatic launch of the application, uncheck the Launch Kaspersky Internet Security at computer
startup box in the Autorun section in the right part of the window. Check this box to enable automatic launch of
the application.
LAUNCHING AND CLOSING THE APPLICATION MANUALLY
Kaspersky Lab specialists do not recommend that you stop Kaspersky Internet Security, because the protection of your
computer and personal data will then be at risk. It is recommended that you temporarily pause the computer's protection,
without closing the application.
Kaspersky Internet Security should be started manually if you have disabled automatic launch of the application (see
section "Enabling and disabling automatic launch" on page 38).
To launch the application manually,
in the Start menu, select Programs Kaspersky Internet Security 2012 Kaspersky Internet Security 2012.
To exit the application,
right-click to open the context menu of the application icon in the taskbar notification area and select Exit.
In the Microsoft Windows 7 operating system the application icon is hidden by default, but you can display it to
access the application more easily (see the operating system documentation).
Page 39

39
MANAGING THE COMPUTER PROTECTION
IN THIS SECTION:
Diagnostics and elimination of problems in your computer protection ............................................................................. 39
Enabling and disabling the protection ............................................................................................................................. 40
Pausing and resuming protection .................................................................................................................................... 41
This section provides information about how to detect threats to the computer's security and how to configure the security
level. Read this section to learn more about how to enable, disable, and pause the protection when using the application.
DIAGNOSTICS AND ELIMINATION OF PROBLEMS IN YOUR
COMPUTER PROTECTION
Problems with computer protection are indicated by the computer indicator located in the left part of the main application
window (see section "The Kaspersky Internet Security main window" on page 33). The indicator is shaped as a monitor
icon that changes color depending on the protection status of the computer: green means that the computer is protected,
yellow indicates protection-related problems, red alerts of serious threats to the computer's security.
Figure 8. Protection status indicator
You are advised to fix the problems and security threats immediately.
Page 40

U S E R G U I DE
40
Clicking the indicator in the main application window opens the Security Problems window (see the figure below)
containing detailed information about the status of computer protection and troubleshooting suggestions for the detected
problems and threats.
Figure 9. The Security Problems window
Problems with the protection are grouped by categories. For each problem, actions are listed that you can use to solve
the problem.
ENABLING AND DISABLING THE PROTECTION
By default, Kaspersky Internet Security is launched when the operating system loads and protects your computer until it
is switched off. All protection components are running.
You can fully or partially disable the protection provided by Kaspersky Internet Security.
Kaspersky Lab specialists strongly recommend that you do not disable protection, since this may lead to an infection of
your computer and data loss. It is recommended that you pause the protection for the required time interval (see section
"Pausing and resuming protection" on page 41).
The following signs indicate that the protection is paused or disabled:
inactive (gray) application icon in the taskbar notification area (see section "The notification area icon" on
page 31);
a red security indicator in the upper part of the main application window.
Page 41

M A N A G I N G T H E C O M P U T E R P R O T E C T I O N
41
In this case, the protection is regarded as the set of protection components. Disabling or pausing protection components
does not affect the performance of virus scan tasks and Kaspersky Internet Security updates.
You can enable or disable the protection or individual application components from the application settings window (see
section "The application settings window" on page 36).
To completely enable or disable protection:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the General Settings subsection.
3. Uncheck the Enable protection box if you need to disable protection. Check this box if you need to enable
protection.
To disable or enable a protection component:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the component that should be enabled or
disabled.
3. In the right part of the window, uncheck the Enable <component name> box if you need to disable this
component. Check this box if you need to enable the component.
PAUSING AND RESUMING PROTECTION
Pausing protection means temporarily disabling all protection components for a period of time.
The following signs indicate that the protection is paused or disabled:
inactive (gray) application icon in the taskbar notification area (see section "The notification area icon" on
page 31);
a red security indicator in the upper part of the main application window.
In this case, the protection is regarded as the set of protection components. Disabling or pausing protection components
does not affect the performance of virus scan tasks and Kaspersky Internet Security updates.
If network connections were established at the moment protection was paused, a notification about the termination of
such connections is displayed.
When working on a computer running under Microsoft Windows Vista or Microsoft Windows 7, you can pause protection
using the Kaspersky Gadget. To do this, you should assign the protection pausing function to a button of the gadget (see
section "How to use the Kaspersky Gadget" on page 59).
To pause the protection of your computer:
1. Open the Pause protection window using one of the following methods:
select Pause protection from the context menu of the application icon (see section "The context menu" on
page 32);
click the button with the Pause protection icon in the Kaspersky Gadget interface (only for Microsoft
Windows Vista and Microsoft Windows 7 operating systems).
Page 42

U S E R G U I DE
42
2. In the Pause protection window, select the time interval after which protection should be resumed:
Pause for the specified time – protection will be enabled on expiration of the time interval selected from
the dropdown list below.
Pause until reboot – protection will be enabled after the application is restarted or the operating system is
rebooted (provided that automatic application launch is enabled (see section "Enabling and disabling
automatic launch" on page 38)).
Pause – protection will be enabled when you decide to resume it (please see below).
To resume computer protection,
select Resume protection from the context menu of the application icon (see section "The context menu" on
page 32).
You can use this method to resume computer protection when the Pause option has been selected, or when you have
selected Pause for the specified time or Pause until reboot.
Page 43

43
SOLVING TYPICAL TASKS
IN THIS SECTION:
How to activate the application ........................................................................................................................................ 43
How to purchase or renew a license ............................................................................................................................... 44
What to do when application notifications appear ........................................................................................................... 45
How to update application databases and modules ........................................................................................................ 45
How to scan critical areas of your computer for viruses .................................................................................................. 46
How to scan a file, folder, disk, or another object for viruses .......................................................................................... 46
How to perform a full scan of your computer for viruses ................................................................................................. 48
How to scan your computer for vulnerabilities ................................................................................................................. 48
How to protect your personal data against theft .............................................................................................................. 48
What to do if you suspect an object is infected with a virus............................................................................................. 51
How to run an unknown application without doing any harm to the system .................................................................... 52
What to do with a large number of spam messages ....................................................................................................... 52
What to do if you suspect your computer is infected ....................................................................................................... 53
How to restore a file that has been deleted or disinfected by the application .................................................................. 54
How to create and use a Rescue Disk ............................................................................................................................ 54
How to view the report on the application's operation ..................................................................................................... 57
How to restore default application settings ...................................................................................................................... 58
How to transfer settings to Kaspersky Internet Security installed on another computer .................................................. 59
How to use the Kaspersky Gadget .................................................................................................................................. 59
How to know the reputation of an application .................................................................................................................. 61
This section provides information about how to resolve the most common issues related to protection of the computer
using the application.
HOW TO ACTIVATE THE APPLICATION
Activation is the procedure of activating a license that allows you to use a fully functional version of the application until
the license expires.
If you did not activate the application during installation, you can do so later. You will be reminded about the need to
activate the application by Kaspersky Internet Security messages appearing in the taskbar notification area.
Page 44

U S E R G U I DE
44
To run the Kaspersky Internet Security activation wizard, perform one of the following:
Click the Activate link in the Kaspersky Internet Security notice window that appears in the taskbar notification
area.
Click the Insert your activation code here link in the bottom part of the main application window. In the
Manage License window that opens, click the Activate the application button.
When working with the application activation wizard, you should specify values for a collection of settings.
Step 1. Enter activation code
Enter the activation code in the corresponding field and click the Next button.
Step 2. Requesting activation
If the activation request is sent successfully, the Wizard automatically proceeds to the next step.
Step 3. Entry of registration data
User registration is necessary for the user to be able to contact the Technical Support Service. Unregistered
users receive only minimal support.
Specify your registration data and click the Next button.
Step 4. Activation
If the application activation has been successful, the Wizard automatically proceeds to the next window.
Step 5. Wizard completion
This window displays information on the activation results: the type of license used and the license expiry date.
Click the Finish button to close the Wizard.
HOW TO PURCHASE OR RENEW A LICENSE
If you have installed Kaspersky Internet Security without a license, you can purchase one after installation. When
purchasing a license, you receive an activation code that you should use to activate the application (see section "How to
activate the application" on page 43).
When your license expires, you can renew it. You can purchase a new license before the validity period of your current
activation code expires. To do this, you should add the new code as a reserve activation code. When the validity term of
the current license expires, Kaspersky Internet Security will be automatically activated using the reserve activation code.
To purchase a license:
1. Open the main application window.
2. Click the Manage License link in the bottom part of the main window to open the Manage License window.
3. In the window that opens, click the Buy activation code button.
The eStore web page opens, where you can purchase a license.
Page 45

S O L V I N G T Y P I C A L T A S K S
45
To add a reserve activation code:
1. Open the main application window.
2. Click the Manage License link in the bottom part of the main window to open the Manage License window.
The Manage License window opens.
3. In the window that opens, in the New activation code section, click the Enter activation code button.
The Application Activation Wizard opens.
4. Enter the activation code in the corresponding fields and click the Next button.
Kaspersky Internet Security then sends the data to the activation server for verification. If the verification is
successful, the Wizard automatically proceeds to the next step.
5. Select New code and click the Next button.
6. When you have finished with the Wizard, click the Finish button.
WHAT TO DO WHEN APPLICATION NOTIFICATIONS APPEAR
Notifications that appear in the taskbar notification area inform you of events occurring in the application's operation
which require your attention. Depending on how critical the event is, you may receive the following types of notification:
Critical notifications – inform you of events that have a critical importance for the computer's security, such as
detection of a malicious object or a dangerous activity in the system. Windows of critical notifications and popup messages are red-colored.
Important notifications – inform you of events that are potentially important for the computer's security, such as
detection of a potentially infected object or a suspicious activity in the system. Windows of important
notifications and pop-up messages are yellow-colored.
Information notifications – inform you of events that do not have critical importance for the computer's security.
Windows of information notifications and pop-up messages are green-colored.
If such a notification is displayed on the screen, you should select one of the options suggested in it. The optimal option
is the one recommended as the default by Kaspersky Lab experts.
HOW TO UPDATE APPLICATION DATABASES
AND MODULES
By default, Kaspersky Internet Security automatically checks for updates on the Kaspersky Lab update servers. If the
server stores a set of recent updates, Kaspersky Internet Security downloads and installs them in background mode. You
can start updating Kaspersky Internet Security manually at any moment.
To download updates from Kaspersky Lab servers, you should be connected to Internet.
To start an update from the context menu,
select Update from the context menu of the application icon.
To start an update from the main application window:
1. Open the main application window and select the Update section in the lower part of the window.
2. In the Update window that opens, click the Run update button.
Page 46

U S E R G U I DE
46
HOW TO SCAN CRITICAL AREAS OF YOUR COMPUTER
FOR VIRUSES
Critical areas scan means scanning the following objects:
objects loaded at the startup of the operating system;
system memory;
boot sectors of the disk;
objects added by the user (see section "Creating a list of objects to scan" on page 67).
You can start the scan of critical areas using one of the following methods:
using a shortcut created earlier (see page 71).
from the main application window (see section "The Kaspersky Internet Security main window" on page 33).
To start the scan using a shortcut:
1. Open the Microsoft Windows Explorer window and go to the folder where you created the shortcut.
2. Double-click the shortcut to start the scan.
To start a scan from the main application window:
1. Open the main application window and select the Scan section in the lower part of the window.
2. In the Scan window that opens, in the Critical Areas Scan section, click the button.
HOW TO SCAN A FILE, FOLDER, DISK, OR ANOTHER
OBJECT FOR VIRUSES
You can use the following methods to scan an object for viruses:
using the context menu for the object;
from the main application window (see section "The Kaspersky Internet Security main window" on page 33);
using the Kaspersky Internet Security Gadget (only for Microsoft Windows Vista and Microsoft Windows 7
operating systems).
To start a virus scan task from the object context menu:
1. Open Microsoft Windows Explorer and go to the folder which contains the object to be scanned.
2. Right-click to open the context menu of the object (see the figure below) and select Scan for Viruses.
Page 47

S O L V I N G T Y P I C A L T A S K S
47
The process and the outcome of the task will be displayed in the Task Manager window.
Figure 10. The context menu of an object in Microsoft Windows
To start scanning an object from the main application window:
1. Open the main application window and select the Scan section in the lower part of the window.
2. Specify the object to scan using one of the following methods:
Click the specify link in the bottom right part of the window to open the Custom Scan window, and check
the boxes next to folders and drives that you need to scan.
If the window displays no object to be scanned:
a. Click the Add button.
b. In the Select object to scan window that opens, select an object to be scanned.
Drag an object to scan into the dedicated area of the main window (see figure below).
The progress of the task will be displayed in the Task Manager window.
Figure 11. An area of the Scan window, into which you should drag an object to scan
To scan an object for viruses using the gadget,
drag the object to scan onto the gadget.
The progress of the task will be displayed in the Task Manager window.
Page 48

U S E R G U I DE
48
HOW TO PERFORM A FULL SCAN OF YOUR COMPUTER
FOR VIRUSES
You can start a full scan for viruses using one of the following methods:
using a shortcut created earlier (see page 71);
from the main application window (see section "The Kaspersky Internet Security main window" on page 33).
To start a full scan using a shortcut:
1. Open the Microsoft Windows Explorer window and go to the folder where you created the shortcut.
2. Double-click the shortcut to start the scan.
To start a full scan from the main application window:
1. Open the main application window and select the Scan section in the lower part of the window.
2. In the Scan window that opens, in the Full Scan section, click the button.
HOW TO SCAN YOUR COMPUTER FOR VULNERABILITIES
Vulnerabilities are unprotected portions of software code which intruders may deliberately use for their purposes, for
example, to copy data used in unprotected applications. Scanning your computer for vulnerabilities helps you to reveal
any such weak points in your computer. You are advised to remove the detected vulnerabilities.
You can use the following methods to scan the system for vulnerabilities:
from the main application window (see section "The Kaspersky Internet Security main window" on page 33);
using a shortcut created earlier (see page 71).
To start the task using a shortcut:
1. Open the Microsoft Windows Explorer window and go to the folder where you created the shortcut.
2. Double-click the shortcut to start scanning the system for vulnerabilities.
To start the task from the main application window:
1. Open the main application window and select the Scan section in the lower part of the window.
2. In the Scan window that opens, in the Vulnerability Scan section, click the button.
HOW TO PROTECT YOUR PERSONAL DATA AGAINST THEFT
With Kaspersky Internet Security, you can protect your personal data against theft; this includes data such as:
passwords, usernames, and other registration data;
account numbers and bank card numbers.
Page 49

S O L V I N G T Y P I C A L T A S K S
49
IN THIS SECTION:
Protection against phishing ............................................................................................................................................. 49
Protection against data interception at the keyboard ...................................................................................................... 50
Protection of confidential data entered on websites ........................................................................................................ 51
Kaspersky Internet Security comprises the following components and tools that help you protect your private data:
Anti-Phishing. Protects against data thefts involving the phishing.
Virtual Keyboard. Prevents interception of data entered at the keyboard.
Parental Control (see page 143). Restricts sending of private data over the Internet.
PROTECTION AGAINST PHISHING
Protection against phishing is ensured by Anti-Phishing, implemented in the Web Anti-Virus, Anti-Spam, and IM AntiVirus components. Kaspersky Lab recommends that you enable the checking for phishing for all protection components.
To enable protection against phishing when Web Anti-Virus is running:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. The Web Anti-Virus window opens.
5. In the window that opens, on the General tab, in the Kaspersky URL Advisor section, check the Check web
pages for phishing box.
To enable protection against phishing when IM Anti-Virus is running:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the IM Anti-Virus component.
3. In the right part of the window, in the Scan methods section, check the Check if URLs are listed in the
database of phishing URLs box.
To enable protection against phishing when Anti-Spam is running:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Anti-Spam component.
3. Click the Settings button in the right part of the window.
The Anti-Spam window will be displayed.
4. In the window that opens, on the Exact methods tab, in the Consider message as spam section, check the If
it contains phishing elements box.
Page 50

U S E R G U I DE
50
PROTECTION AGAINST DATA INTERCEPTION AT THE KEYBOARD
When working on the Internet, you frequently need to enter your personal data or your username and password. This
happens, for example, during account registration on web sites, web shopping or Internet banking.
There is a risk that this personal information can be intercepted using hardware keyboard interceptors or keyloggers,
which are programs that register keystrokes.
The Virtual Keyboard tool prevents the interception of data entered via the keyboard.
The Virtual Keyboard cannot protect your personal data if the website requiring the entry of such data has been hacked,
because in this case the information is obtained directly by the intruders.
Many of the applications classified as spyware have the function of making screenshots which are then transmitted to an
intruder for further analysis and extraction of the user's personal data. The Virtual Keyboard prevents the personal data
being entered, from being intercepted through the use of screenshots.
The Virtual Keyboard only prevents the interception of personal data when working with Microsoft Internet Explorer,
Mozilla Firefox and Google Chrome browsers.
The Virtual Keyboard has the following features:
You can click the Virtual Keyboard buttons using the mouse.
Unlike with real keyboards, there is no way to click several keys simultaneously on a Virtual Keyboard.
Therefore, to use combinations of keys (e.g., ALT+F4), you have to click the first key (e.g., ALT), then the next
key (e.g., F4), and then click the first key again. The second click of the key acts in the same way as the key
release on a real keyboard.
Input language for the Virtual Keyboard is toggled using the key combination CTRL+SHIFT (the SHIFT key
should be clicked using the right mouse button) or CTRL+LEFT ALT (the LEFT ALT key should be clicked
using the right mouse button), depending upon the specified settings.
You can open the Virtual Keyboard in the following ways:
from the context menu of the application icon;
from the main application window;
from the Microsoft Internet Explorer, Mozilla Firefox or Google Chrome browser windows;
using keyboard shortcuts.
To open the Virtual Keyboard from the context menu of the application icon,
select Tools Virtual Keyboard from the context menu of the application icon.
To open the Virtual Keyboard from the main application window,
in the lower part of the main application window select Virtual Keyboard.
To open the Virtual Keyboard from the browser window,
click the Virtual Keyboard button in the toolbar of Microsoft Internet Explorer, Mozilla Firefox, or Google
Chrome.
To open the Virtual Keyboard using the computer keyboard,
press the CTRL+ALT+SHIFT+P shortcut.
Page 51

S O L V I N G T Y P I C A L T A S K S
51
PROTECTION OF CONFIDENTIAL DATA ENTERED ON WEBSITES
To protect confidential data entered on websites (for example, bank card numbers, passwords to access online banking
services), Kaspersky Internet Security prompts you to open such websites in Safe Run for Websites.
You can enable access control for online banking services (see section "Controlling access to online banking services"
on page 94) to determine banking websites automatically and also start Safe Run for Websites manually.
Safe Run for Websites can be started in the following ways:
from the Kaspersky Internet Security main window (see section "The Kaspersky Internet Security main window"
on page 33);
using a shortcut on the desktop (see section "Creating a shortcut for Safe Run on the desktop" on page 141).
To start Safe Run for Websites from the main Kaspersky Internet Security window:
1. Open the main application window.
2. In the bottom part of the window, select the Safe Run for Websites section.
3. In the window that opens, click the Start Safe Run for Websites button.
WHAT TO DO IF YOU SUSPECT AN OBJECT IS INFECTED
WITH A VIRUS
If you suspect an object is infected, scan it using Kaspersky Internet Security (see section "How to scan a file, folder,
disk, or another object for viruses" on page 46).
If the application scans an object and then considers it as not infected although you suspect the contrary, you can
perform any of the following actions:
Move the object to Quarantine. Objects moved to Quarantine do not pose any threat to your computer. After the
databases are updated, Kaspersky Internet Security may be able to clearly identify and remove the threat.
Send the object to the Virus Lab. Virus Lab specialists scan the object. If it turns out to be infected with a virus,
they add the description of the new virus into the databases that will be downloaded by the application with an
update (see section "How to update application databases and modules" on page 45).
You can move a file to Quarantine using one of two methods:
by clicking the Move to Quarantine button in the Quarantine window;
using the context menu for the file.
To move a file to Quarantine from the Quarantine window:
1. Open the main application window.
2. In the lower part of the window, select the Quarantine section.
3. On the Quarantine tab click the Move to Quarantine button.
4. In the window that opens, select the file that you want to move to Quarantine.
Page 52

U S E R G U I DE
52
To move a file to Quarantine using the context menu:
1. Open Microsoft Windows Explorer and go to the folder that contains the file that you want to move to
Quarantine.
2. Right-click to open the context menu of the file and select Move to Quarantine.
To send a file to the Virus Lab:
1. Go to the Virus Lab request page (http://support.kaspersky.com/virlab/helpdesk.html).
2. Follow the instructions on this page to send your request.
HOW TO RUN AN UNKNOWN APPLICATION
WITHOUT DOING ANY HARM TO THE SYSTEM
When the safety of any application raises doubts, it can be executed in Safe Run.
Safe Run is isolated from the main operating system of the computer. In Safe Run, real operating system files do not
undergo changes. Thus, if you launch an infected application in Safe Run, its actions will not affect the operating system
of the computer.
You can start Safe Run as a separate desktop (see page 138) or run an application in Safe Run on the main desktop.
Applications started in Safe Run are marked with a green frame around the application window and have a safe run
indicator in the list of applications monitored by Application Control (see section "Application Control" on page 101).
After the application is closed, all changes made by this application will be discarded automatically.
To run an application in the safe environment from the Microsoft Windows context menu,
right-click to open the context menu for the selected object (application shortcut or executable file) and select Safe
Run.
WHAT TO DO WITH A LARGE NUMBER OF SPAM MESSAGES
If you receive large amounts of unwanted messages (spam), enable the Anti-Spam component and set the
recommended security level for it.
To enable Anti-Spam and set the recommended security level:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Anti-Spam component.
3. In the right part of the window, check the Enable Anti-Spam box.
4. Make sure that the Recommended security level is set in the Security level section.
If the security level is set to Low or Custom, click the Default level button. The security level will automatically
be set to Recommended.
Page 53

S O L V I N G T Y P I C A L T A S K S
53
WHAT TO DO IF YOU SUSPECT YOUR COMPUTER IS
INFECTED
If you suspect your operating system of being corrupted due to malware activity or system failures, use Microsoft
Windows Troubleshooting, which removes any traces of malicious objects from the system. Kaspersky Lab recommends
that you run the Wizard after the computer has been disinfected to make sure that all threats and damage caused by
infections have been fixed.
Microsoft Windows Troubleshooting checks the system for modifications and faults (such as modifications of file
extensions, blockage of the network environment and control panel). Modifications and faults may be caused by malware
activity, an improper system configuration, system failures, or incorrect operation of system optimization applications.
After the review is complete, the Wizard analyzes the information to evaluate whether there is system damage which
requires immediate attention. Based on the review, a list of actions necessary to eliminate the problems is generated.
The Wizard groups these actions by category based on the severity of the problems detected.
To start the System Restore Wizard:
1. Open the main application window (see page 33).
2. In the lower part of the window, select the Tools section.
3. In the window that opens, in the Microsoft Windows Troubleshooting section, click the Start button.
The Microsoft Windows Troubleshooting window opens.
The Wizard consists of a series of screens (steps) that you can navigate through using the Back and Next buttons. To
close the Wizard once it has completed its task, click the Finish button. To stop the Wizard at any stage, click the
Cancel button.
Step 1. Starting system restoration
Make sure that the Wizard option to Search for problems caused by malware activity is selected and click
the Next button.
Step 2. Problems search
The Wizard will search for problems and damage which should be fixed. Once the search is complete, the
Wizard will proceed automatically to the next step.
Step 3. Selecting troubleshooting actions
All damage found during the previous step is grouped on the basis of the type of danger it poses. For each
damage group, Kaspersky Lab recommends a sequence of actions to repair the damage. There are three
groups of actions:
Strongly recommended actions eliminate problems posing a serious security threat. You are advised to
perform all actions in this group.
Recommended actions eliminate problems presenting a potential threat. You are also advised to perform all
actions in this group.
Additional actions repair system damage which does not pose a current threat, but may pose a danger to
the computer's security in the future.
To view the actions within a group, click the + icon to the left of the group name.
Page 54

U S E R G U I DE
54
To make the Wizard perform a certain action, check the box to the left of the corresponding action description.
IN THIS SECTION:
Creating a Rescue Disk................................................................................................................................................... 55
Starting the computer from the Rescue Disk ................................................................................................................... 57
By default, the Wizard performs all recommended and strongly recommended actions. If you do not wish to
perform a certain action, uncheck the box next to it.
It is strongly recommended that you not uncheck the boxes selected by default, as doing so will leave your
computer vulnerable to threats.
Having defined the set of actions which the Wizard will perform, click the Next button.
Step 4. Eliminating problems
The Wizard will perform the actions selected during the previous step. The elimination of problems may take
some time. Once the troubleshooting is complete, the Wizard will automatically proceed to the next step.
Step 5. Wizard completion
Click the Finish button to close the Wizard.
HOW TO RESTORE A FILE THAT HAS BEEN DELETED
OR DISINFECTED BY THE APPLICATION
Kaspersky Lab recommends that you avoid restoring deleted and disinfected files, as they may pose a threat to your
computer.
If you want to restore a deleted or disinfected file, you can use a backup copy of it which was created by the application
during the scan.
To restore a file that has been deleted or disinfected by the application:
1. Open the main application window.
2. In the lower part of the window, select the Quarantine section.
3. On the Storage tab, select the required file from the list and click the Restore button.
HOW TO CREATE AND USE A RESCUE DISK
After you install Kaspersky Internet Security and perform the first scan of your computer, it is recommended that you
create the Rescue Disk.
The Rescue Disk is an application named Kaspersky Rescue Disk and recorded on a removable medium (CD or USB
flash drive).
You will then be able to use Kaspersky Rescue Disk for scanning and disinfecting infected computers that cannot be
disinfected using other methods (e.g., with anti-virus applications).
Page 55

S O L V I N G T Y P I C A L T A S K S
55
CREATING A RESCUE DISK
Creating a Rescue Disk consists in creating a disk image (ISO file) with the up-to-date version of Kaspersky Rescue
Disk, and writing it on a removable medium.
You can download the original disk image from the Kaspersky Lab server or copy it from a local source.
The Rescue Disk is created using the Kaspersky Rescue Disk Creation Wizard. The rescuecd.iso file created by the
Wizard is saved on your computer's hard drive:
in Microsoft Windows XP – in the following folder: Documents and Settings\All Users\Application
Data\Kaspersky Lab\AVP12\Data\Rdisk\;
in Microsoft Windows Vista and Microsoft Windows 7 operating systems – in the following folder:
ProgramData\Kaspersky Lab\AVP12\Data\Rdisk\.
To create a Rescue Disk:
1. Open the main application window.
2. In the lower part of the window, select the Tools section.
3. In the window that opens, in the Kaspersky Rescue Disk section, click the Create button.
The Kaspersky Rescue Disk Creation Wizard window opens.
The Wizard consists of a series of screens (steps) that you can navigate through using the Back and Next buttons. To
close the Wizard once it has completed its task, click the Finish button. To stop the Wizard at any stage, click the
Cancel button.
Let us review the steps of the Wizard in more detail.
Step 1. Starting the Wizard. Searching for an existing disk image
The first window of the Wizard contains information about Kaspersky Rescue Disk.
If the Wizard detects an existing Rescue Disk ISO file in the dedicated folder (see above), the Use existing ISO
image box will be displayed in the first window of the Wizard. Check the box to use the detected file as the
original ISO image and go directly to the Updating disk image step (see below). Uncheck this box if you do not
want to use the disk image that was detected. The Wizard will proceed to the Select disk image source
window.
Step 2. Selecting a disk image source
If you have checked the Use existing ISO image box in the first Wizard window, then this step will be skipped.
At this step, you should select a disk image source from the options suggested:
If you already have a recorded copy of the Rescue Disk or an ISO image saved on your computer or on a
local network resource, select Copy ISO image from local or network drive.
If you have no ISO image file created for the Rescue Disk, and you want to download one from the
Kaspersky Lab server (file size is about 175 MB), select Download ISO image from Kaspersky Lab
server.
Page 56

U S E R G U I DE
56
Step 3. Copying (downloading) the disk image
If you have checked the Use existing ISO image box in the first Wizard window, then this step will be skipped.
If you have selected Copy ISO image from local or network drive at the previous step, click the Browse
button. After you have specified the path to the file, click the Next button. The progress of copying the disk
image is displayed in the Wizard window.
If you have selected Download ISO image from Kaspersky Lab server at the previous step, the progress of
downloading the disk image is displayed immediately.
When copying or downloading of the ISO image is complete, the Wizard automatically proceeds to the next
step.
Step 4. Updating the ISO image file
The updating procedure for the ISO image file comprises the following operations:
updating anti-virus databases;
updating configuration files.
Configuration files determine whether the computer can be booted from a removable medium (such as a
CD / DVD or a USB flash drive with Kaspersky Rescue Disk) created by the Wizard.
When updating anti-virus databases, those distributed at the last update of Kaspersky Internet Security are
used. If databases are out of date, it is recommended that you run the update task and launch the Kaspersky
Rescue Disk Creation Wizard again.
To begin updating the ISO file, click the Next button. The update's progress will be displayed in the Wizard
window.
Step 5. Recording the disk image on a medium
At this step, the Wizard informs you of a successful creation of a disk image and offers you to record it on a
medium.
Specify a data medium for recording Kaspersky Rescue Disk:
To record the disk image on a CD / DVD, select Record to CD / DVD and specify a medium, on which you
want to record the disk image.
To record the disk image on a USB flash drive, select Record to USB flash drive and specify a device, on
which you want to record the disk image.
Kaspersky Lab recommends that you do not record the ISO image on devices which are not designed
specifically for data storage, such as smartphones, cellphones, PDAs, and MP3 players. Recording ISO
images on these devices may lead to their functioning incorrectly in the future.
To record the disk image on the hard drive of your computer or on the hard drive of another one that you
can access via a network, select Save the disk image to file on local or network drive and specify a
folder, in which you want to record the disk image, and the name of the ISO file.
Page 57

S O L V I N G T Y P I C A L T A S K S
57
Step 6. Wizard completion
To close the Wizard once it has completed its task, click the Finish button. You can use the newly created
Rescue Disk to boot the computer (see page 57) if you cannot boot it and run Kaspersky Internet Security in
normal mode due to an impact caused by viruses or malware.
STARTING THE COMPUTER FROM THE RESCUE DISK
If the operating system cannot be booted as a result of a virus attack, use the Rescue Disk.
To boot the operating system, you should use a CD / DVD or a USB flash drive with Kaspersky Rescue Disk copied on it
(see section "Creating a Rescue Disk" on page 55).
Booting a computer from a removable media is not always possible. In particular, this mode is not supported by some
obsolete computer models. Before shutting down your computer for subsequent booting from a removable media, make
sure that this operation can be performed.
To boot your computer from the Rescue Disk:
1. In the BIOS settings, enable booting from a CD / DVD or a USB device (for detailed information, please refer to
the documentation for your computer's motherboard).
2. Insert a CD / DVD into the CD / DVD drive of an infected computer or connect a USB flash device with
Kaspersky Rescue Disk copied on it.
3. Restart your computer.
For detailed information about the use of the Rescue Disk, please refer to the Kaspersky Rescue Disk User Guide.
HOW TO VIEW THE REPORT ON THE APPLICATION'S
OPERATION
Kaspersky Internet Security creates operation reports for each component. Using a report, you can obtain statistical
information about the application's operation (for example, learn how many malicious objects have been detected and
neutralized for a specified time period, how many times the application has been updated for the same period, how many
spam messages have been detected and much more).
When working on a computer running under Microsoft Windows Vista or Microsoft Windows 7, you can open reports
using the Kaspersky Gadget. To do this, the Kaspersky Gadget should be configured so that the option of opening the
reports window is assigned to one of its buttons (see section "How to use the Kaspersky Gadget" on page 59).
To view the application operation report:
1. Open the Reports window using any of the following methods:
click the Reports link in the top part of the main application window;
click the button with the Reports icon in the Kaspersky Gadget interface (only for Microsoft Windows
Vista and Microsoft Windows 7 operating systems).
The Reports window displays reports on the application's operation represented as diagrams.
2. If you want to view a detailed application operation report (for example, a report on the operation of each
component), click the Detailed report button in the bottom part of the Report window.
The Detailed report window will open, where data are represented in a table. For convenient viewing of reports,
you can select various entry sorting options.
Page 58

U S E R G U I DE
58
HOW TO RESTORE DEFAULT APPLICATION SETTINGS
You can restore the default application settings recommended by Kaspersky Lab for Kaspersky Internet Security, at any
time. The settings can be restored using the Application Configuration Wizard.
When the Wizard completes its operation, the Recommended security level is set for all protection components. When
restoring the recommended security level, you can save the previously specified values for some of the settings of
application components.
To restore the default settings of the application:
1. Open the application settings window.
2. Run the Application Configuration Wizard using one of the following methods:
click the Restore link in the bottom part of the window;
in the left part of the window, select the Manage Settings subsection in the Advanced Settings section
and click the Restore button in the Restore default settings section.
Let us review the steps of the Wizard in more detail.
Step 1. Starting the Wizard
Click the Next button to proceed with the Wizard.
Step 2. Restore settings
This Wizard window shows which Kaspersky Internet Security protection components have settings that differ
from the default value because they were either changed by the user or accumulated by Kaspersky Internet
Security through training (Firewall or Anti-Spam). If special settings have been created for any of the
components, they will also be shown in this window.
Special settings include lists of allowed and blocked phrases and addresses used by Anti-Spam, lists of trusted
web addresses and ISP phone numbers, protection exclusion rules created for application components, and
filtering rules applied by Firewall to packets and applications.
The special settings are created when working with Kaspersky Internet Security with regard for individual tasks
and security requirements. Kaspersky Lab recommends that you save your special settings when restoring the
default application settings.
Check the boxes for the settings that you want to save and click the Next button.
Step 3. System analysis
At this stage, information about Microsoft Windows applications is collected. These applications are added to
the list of trusted applications which have no restrictions imposed on the actions they perform in the system.
Step 4. Finishing restoration
Once the analysis is complete, the Wizard will automatically proceed to the next step.
To close the Wizard once it has completed its task, click the Finish button.
Page 59

S O L V I N G T Y P I C A L T A S K S
59
HOW TO TRANSFER SETTINGS TO KASPERSKY INTERNET SECURITY INSTALLED ON ANOTHER COMPUTER
Once you have configured the product, you can apply its settings to Kaspersky Internet Security installed on another
computer. Consequently, the application will be configured identically on both computers. This is a helpful feature when,
for example, Kaspersky Internet Security is installed on your home computer and in your office.
The application settings are stored in a special configuration file that you can transfer to another computer.
The settings of Kaspersky Internet Security can be transferred to another computer in three steps:
1. Saving the application settings in a configuration file.
2. Transferring a configuration file to another computer (for example, by email or on a removable medium).
3. Applying settings from a configuration file to the application installed on another computer.
To export the current settings of Kaspersky Internet Security:
1. Open the application settings window.
2. In the left part of the window, in the Advanced Settings section, select the Manage Settings subsection.
3. Click the Save button in the right part of the window.
4. In the window that opens, enter the name of the configuration file and the path where it should be saved.
5. Click the OK button.
To import the application's settings from a saved configuration file:
1. Open the application settings window.
2. In the left part of the window, in the Advanced Settings section, select the Manage Settings subsection.
3. Click the Load button in the right part of the window.
4. In the window that opens, select the file from which you wish to import the Kaspersky Internet Security settings.
5. Click the OK button.
HOW TO USE THE KASPERSKY GADGET
When using Kaspersky Internet Security on a computer running under Microsoft Windows Vista or Microsoft Windows 7,
you can also use the Kaspersky Gadget (hereinafter the gadget). After you install Kaspersky Internet Security on a
computer running under Microsoft Windows 7, the gadget appears on your desktop automatically. After you install the
application on a computer running under Microsoft Windows Vista, you should add the gadget to the Microsoft Windows
Sidebar manually (see the operating system documentation).
The Gadget color indicator displays your computer's protection status in the same manner as the indicator in the main
application window (see section "Diagnostics and elimination of problems in your computer protection" on page 39).
Green indicates that your computer is duly protected, while yellow indicates that there are protection problems, and red
indicates that your computer's security is at serious risk. Gray indicates that the application is stopped.
While updating the application databases and software modules, a revolving globe-shaped icon is displayed in the center
part of the gadget.
Page 60

U S E R G U I DE
60
You can use the gadget to perform the following actions:
resume the application if it has been paused earlier;
open the main application window;
scan specified objects for viruses;
open the news window.
Also, you can configure the buttons of the gadget so that they could initiate additional actions:
run an update;
edit the application settings;
view application reports;
switch to Safe Run (for 32-bit operating systems only);
view Parental Control reports;
view information about network activity (Network Monitor) and applications' activity;
pause the protection;
open the Virtual Keyboard;
open the Task Manager window.
To start the application using the gadget,
click the Enable icon located in the center of the gadget.
To open the main application window using the gadget,
click the monitor icon in the center area of the gadget.
To scan an object for viruses using the gadget,
drag the object to scan onto the gadget.
The progress of the task will be displayed in the Task Manager window.
To open the news window using the gadget,
click the icon , which is displayed in the center of the gadget when news is released.
To configure the gadget:
1. Open the gadget settings window by clicking the icon that appears in the upper right corner of the gadget
block if you position the cursor over it.
2. In the dropdown lists corresponding to gadget buttons, select actions that should be performed when you click
those buttons.
3. Click the OK button.
Page 61

S O L V I N G T Y P I C A L T A S K S
61
SEE ALSO:
Kaspersky Security Network ......................................................................................................................................... 174
HOW TO KNOW THE REPUTATION OF AN APPLICATION
Kaspersky Internet Security allows you to learn the reputation of applications from users all over the world. Reputation of
an application comprises the following criteria:
name of the vendor;
information about the digital signature (available if a digital signature exists);
information about the group, in which the application has been included by Application Control or a majority of
users of Kaspersky Security Network;
number of users of Kaspersky Security Network that use the application (available if the application has been
included in the Trusted group in Kaspersky Security Network database);
time, at which the application has become known in Kaspersky Security Network;
countries, in which the application is the most widespread.
To verify the reputation of an application, you should agree to participate in Kaspersky Security Network (see page 175)
when installing Kaspersky Internet Security.
To know the reputation of an application,
open the context menu of the executable file of the application and select Check reputation in KSN.
Page 62
62
ADVANCED APPLICATION SETTINGS
IN THIS SECTION:
General protection settings ............................................................................................................................................. 63
Scan ................................................................................................................................................................................ 64
Update............................................................................................................................................................................. 72
File Anti-Virus .................................................................................................................................................................. 77
Mail Anti-Virus ................................................................................................................................................................. 83
Web Anti-Virus ................................................................................................................................................................ 88
IM Anti-Virus .................................................................................................................................................................... 95
Proactive Defense ........................................................................................................................................................... 97
System Watcher .............................................................................................................................................................. 99
Application Control ................................................................................................ ........................................................ 101
Network protection ........................................................................................................................................................ 109
Anti-Spam ..................................................................................................................................................................... 120
Anti-Banner ................................................................................................................................................................... 135
Safe Run for Applications and Safe Run for Websites .................................................................................................. 137
Parental Control ............................................................................................................................................................ 143
Trusted zone ................................................................................................................................................................. 154
Performance and compatibility with other applications .................................................................................................. 155
Kaspersky Internet Security self-defense ...................................................................................................................... 159
Quarantine and Backup................................................................................................................................................. 160
Additional tools for better protection of your computer .................................................................................................. 163
Reports.......................................................................................................................................................................... 167
Application appearance. Managing active interface elements ....................................................................................... 171
Notifications ................................................................................................................................................................... 172
Kaspersky Security Network ......................................................................................................................................... 174
This section provides detailed information about how to configure each of the application components.
Page 63

A D V A N C E D A P P L I C A T I O N S E T T I N G S
63
IN THIS SECTION:
Restricting access to Kaspersky Internet Security .......................................................................................................... 63
Selecting a protection mode ............................................................................................................................................ 64
GENERAL PROTECTION SETTINGS
In the application settings window, in the General Settings subsection of the Protection Center section, you can:
disable all protection components (see section "Enabling and disabling protection" on page 40);
select the interactive or automatic protection mode (see section "Selecting a protection mode" on page 64);
restrict users' access to the application by setting a password (see section "Restricting access to Kaspersky
Internet Security" on page 63);
disable or enable automatic launching of the application at operating system startup (see section "Enabling and
disabling automatic launch" on page 38);
enable a custom key combination for displaying the virtual keyboard on the screen (see section "Protection
against data interception at the keyboard" on page 50).
RESTRICTING ACCESS TO KASPERSKY INTERNET SECURITY
A computer may be used by several users with various levels of computer literacy. Unrestricted user access to
Kaspersky Internet Security and its settings may lead to a reduced level of computer protection.
To restrict access to the application, you can set a password and specify which actions should require the password to
be entered:
changing application settings;
enabling and configuring Parental Control;
closing the application;
removing the application.
Be careful when using a password to restrict access to application removal. If you forget the password, the application
will be difficult to remove from your computer.
To restrict access to Kaspersky Internet Security with a password:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the General Settings subsection.
3. In the right part of the window, in the Password protection section, check the Enable password protection
box and click the Settings button.
4. In the Password protection window that opens, enter the password and specify the area to be covered by the
access restriction.
Page 64

U S E R G U I DE
64
SELECTING A PROTECTION MODE
IN THIS SECTION:
Virus scan ....................................................................................................................................................................... 64
Vulnerability Scan ........................................................................................................................................................... 72
Managing scan tasks. Task Manager .............................................................................................................................. 72
By default, Kaspersky Internet Security runs in automatic protection mode. In this mode the application automatically
applies actions recommended by Kaspersky Lab in response to dangerous events. If you wish Kaspersky Internet
Security to notify you of all hazardous and suspicious events in the system and to allow you to decide which of the
actions offered by the application should be applied, you can enable the interactive protection mode.
To select a protection mode:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the General Settings subsection.
3. In the Interactive protection section, check or uncheck the boxes depending on your choice of protection
mode:
to enable the interactive protection mode, uncheck the Select action automatically box;
to enable automatic protection mode, check the Select action automatically box.
If you do not want Kaspersky Internet Security to delete suspicious objects when running in automatic
mode, check the Do not delete suspicious objects box.
SCAN
Scanning the computer for vulnerabilities, viruses and other riskware is one of the most important tasks when ensuring
the computer's security.
It is necessary to regularly scan your computer for viruses and other riskware in order to rule out the possibility of
spreading malicious programs that have not been detected by protection components, for example, due to a low security
level set, or for other reasons.
The vulnerability scan performs diagnostics of operating system safety and detects software features that could be used
by intruders to spread malicious objects and obtain access to personal information.
This section contains information about scan task features and configuration, security levels, scan methods, and scan
technologies.
VIRUS SCAN
To detect viruses and other riskware, Kaspersky Internet Security comprises the following tasks:
Full Scan. Scan of the entire system. By default, Kaspersky Internet Security scans the following objects:
system memory;
objects loaded on operating system startup;
Page 65

A D V A N C E D A P P L I C A T I O N S E T T I N G S
65
system backup;
email databases;
removable storage media, hard and network drives.
Critical Areas Scan. By default, Kaspersky Internet Security scans objects loaded at the startup of the
operating system.
Custom Scan. Kaspersky Internet Security scans objects selected by the user. You can scan any object from
the list below:
system memory;
objects loaded on operating system startup;
system backup;
email databases;
removable storage media, hard and network drives;
any file or folder that you have selected.
The Full Scan and the Critical Areas Scan tasks have their peculiarities. For these tasks, it is not recommended that you
edit the lists of objects to scan.
Each scan task is performed in a specified area and can be started according to a previously created schedule. Each
scan task is also characterized by a security level (a combination of settings that impact the depth of the scan). By
default, the signature mode (the one using records from application databases to search for threats) is always enabled.
You can also apply various scan methods and technologies.
After the full scan task or the critical areas scan task is started, the scan run progress is displayed in the Scan window, in
the section with the name of the task running, and in the Task Manager (see section "Managing scan tasks. Task
Manager" on page 72).
If a threat is detected, Kaspersky Internet Security assigns one of the following statuses to the found object:
Malicious program (such as a virus or Trojan).
Potentially infected (suspicious) status if the scan cannot determine whether the object is infected or not. The
file may contain a sequence of code characteristic of viruses, or modified code from a known virus.
The application displays a notification (see page 172) about the detected threat and performs the prescribed action. You
can change the actions to be taken when a threat is detected.
If you are working in automatic mode (see section "Selecting a protection mode" on page 64), when dangerous objects
are detected, Kaspersky Internet Security automatically applies the actions recommended by Kaspersky Lab specialists.
For malicious objects, this action is Disinfect. Delete if disinfection fails, for suspicious objects – Move to Quarantine.
If dangerous objects are detected when working in interactive mode (see section "Selecting a protection mode" on
page 64), the application displays a notification on the screen that you can use to select the required action the list of
available ones.
Before attempting to disinfect or delete an infected object, Kaspersky Internet Security creates a backup copy for
subsequent restoration or disinfection. Suspicious (potentially infected) objects are quarantined. You can enable
automatic scanning of quarantined objects after each update.
Information on the scan results and events which have occurred during the execution of the task is logged in a
Kaspersky Internet Security report (see page 167).
Page 66

U S E R G U I DE
66
IN THIS SECTION:
Changing and restoring the security level ....................................................................................................................... 66
Creating the scan startup schedule ................................................................................................................................. 67
Creating a list of objects to scan ..................................................................................................................................... 67
Selecting a scan method ................................................................................................................................................. 68
Selecting scan technology ............................................................................................................................................... 68
Changing the actions to be performed when a threat is detected ................................................................................... 69
Running a scan under a different user account ............................................................................................................... 69
Changing the type of objects to scan .............................................................................................................................. 69
Scanning of compound files ............................................................................................................................................ 70
Scan optimization ............................................................................................................................................................ 70
Scanning removable drives on connection ...................................................................................................................... 71
Creating a task shortcut .................................................................................................................................................. 71
CHANGING AND RESTORING THE SECURITY LEVEL
Depending on your current needs, you can select one of the preset security levels or modify the scan settings manually.
When configuring scan task settings, you can always restore the recommended ones. These settings are considered
optimal, recommended by Kaspersky Lab, and grouped in the Recommended security level.
To change the established security level:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the Security level section, set the desired security level for the task selected, or click the Settings button to
modify scan settings manually.
If you modify the settings manually, the name of the security level will change to Custom.
To restore the default scan settings:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the Security level section, click the Default level button for the task selected.
Page 67

A D V A N C E D A P P L I C A T I O N S E T T I NGS
67
CREATING THE SCAN STARTUP SCHEDULE
You can create a schedule to automatically start virus scan tasks: specify task run frequency, start time (if necessary),
and advanced settings.
If it is not possible to start the task for any reason (for example, the computer was not on at that time), you can configure
the skipped task to start automatically as soon as it becomes possible. You can automatically pause the scan when a
screensaver is inactive or the computer is unlocked. This functionality postpones launching the task until the user has
finished working on the computer. The scan will then not take up system resources during work.
The special Idle Scan mode (see section "Running tasks in background mode" on page 157) allows you to start
automatic updates when your computer is idle.
To modify the schedule for scan tasks:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Vulnerability Scan).
3. Click the Run mode button in the right part of the window.
4. In the window that opens, on the Run mode tab, in the Schedule section, select By schedule and configure
the scan run mode by specifying required values for the Frequency setting.
To enable automatic launching of a skipped task:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan or
Vulnerability Scan).
3. Click the Run mode button in the right part of the window.
4. In the window that opens, on the Run mode tab in the Schedule section, select By schedule and check the
Run skipped tasks box.
To launch scans only when the computer is not being used:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Vulnerability Scan).
3. Click the Run mode button in the right part of the window.
4. In the window that opens, on the Run mode tab, in the Schedule section, select By schedule and check the
Run scheduled scan when screensaver is active or computer is locked box.
CREATING A LIST OF OBJECTS TO SCAN
Each virus scan task has its own default list of objects. These objects may include items in the computer's file system,
such as logical drives and email databases, or other types of objects, such as network drives. You can edit this list.
If the scan scope is empty, or it contains no selected objects, a scan task cannot be started.
Page 68

U S E R G U I DE
68
To create a list of objects for a custom scan task:
1. Open the main application window.
2. In the bottom part of the window, select the Scan section.
3. In the bottom part of the window that opens, click the specify link to open a list of objects to be scanned.
4. In the Custom Scan window that opens, click the Add button.
5. In the Select object to scan window that opens, select the desired object and click the Add button. Click the
OK button after you have added all the objects you need. To exclude any objects from the list of objects to be
scanned, uncheck the boxes next to them.
You can also drag files to be scanned directly into a marked area located in the Scan section.
To create a list of objects for Full Scan, Critical Areas Scan or Vulnerability Scan tasks:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired scan task (Full Scan, Critical Areas Scan,
or Vulnerability Scan).
3. In the right part of the window, click the Scan scope button.
4. In the Scan scope window that opens, use the Add, Edit, and Delete buttons to create a list. To exclude any
objects from the list of objects to be scanned, uncheck the boxes next to them.
Objects which appear in the list by default cannot be edited or deleted.
SELECTING A SCAN METHOD
During a virus scan, signature analysis is always used: Kaspersky Internet Security compares the object found with the
database records.
You can use additional scan methods to increase scan efficiency: heuristic analysis (analysis of the actions an object
performs within the system) and rootkit scan (a scan for tools that can hide malicious programs in your operating
system).
To select which scan method to use:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the Security level section, click the Settings button for the task selected.
4. In the window that opens, on the Additional tab in the Scan methods section, select the desired scan
methods.
SELECTING SCAN TECHNOLOGY
In addition to the scan methods you can use special object scan technologies which allow you to increase virus scan
speed by excluding the files that have not been modified since they were last scanned.
Page 69

A D V A N C E D A P P L I C A T I O N S E T T I N G S
69
To specify the object scan technologies:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the Security level section, click the Settings button for the task selected.
4. In the window that opens, on the Additional tab in the Scan technologies section, select the desired values.
CHANGING THE ACTIONS TO BE PERFORMED WHEN A THREAT IS DETECTED
If infected objects are detected, the application performs the selected action.
To change the action that should be performed when a threat is detected:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the right part of the window, select the desired option in the Action on threat detection section.
RUNNING A SCAN UNDER A DIFFERENT USER ACCOUNT
By default, the scan tasks are run under your system account. However, you may need to run a task under a different
user account. You can specify an account to be used by the application when performing a scan task.
To start a scan under a different user's account:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Vulnerability Scan).
3. Click the Run mode button in the right part of the window.
4. In the window that opens, on the Run mode tab in the User account section, check the Run task as box.
Specify the user name and password.
CHANGING THE TYPE OF OBJECTS TO SCAN
When specifying the type of objects to scan, you establish which file formats will be scanned for viruses when the
selected scan task runs.
When selecting file types, please remember the following:
The probability of malicious code penetrating some file formats (such as TXT) and its subsequent activation is
quite low. However, there are formats that contain or may contain an executable code (such as EXE, DLL,
DOC). The risk of penetration and activation of malicious code in such files is quite high.
An intruder can send a virus to your computer in an executable file renamed as a TXT file. If you have selected
scanning of files by extension, such a file is skipped by the scan. If scanning of files by format is selected, then,
regardless of the extension, File Anti-Virus will analyze the file header and reveal that the file is an EXE file.
Such a file would be thoroughly scanned for viruses.
Page 70

U S E R G U I DE
70
To change the type of objects to be scanned:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the Security level section, click the Settings button for the task selected.
4. In the window that opens, on the Scope tab in the File types section, select the desired option.
SCANNING OF COMPOUND FILES
A common method of concealing viruses is to embed them into compound files: archives, installation packages,
embedded OLE objects, and mail file formats. To detect viruses that are hidden in this way, a compound file should be
unpacked, which can significantly decrease scanning speed.
For each type of compound file, you can choose to scan either all files or only new ones. To make your selection, click
the link next to the name of the object. It changes its value when you left-click it. If you select the scan new and changed
files only mode (see page 70), the links for choosing whether to scan all or only new files will not be available.
You can restrict the maximum size of a compound file to be scanned. Compound files larger than the specified value will
not be scanned.
When large files are extracted from archives, they will be scanned even if the Do not unpack large compound files box
is checked.
To modify the list of compound files to be scanned:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the Security level section, click the Settings button for the task selected.
4. In the window that opens, on the Scope tab in the Scan of compound files section, select the desired types of
compound files to be scanned.
To set the maximum size of compound files to be scanned:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the Security level section, click the Settings button for the task selected.
4. In the window that opens, on the Scope tab in the Scan of compound files section, click the Additional
button.
5. In the Compound files window that opens, check the Do not unpack large compound files box and specify
the maximum file size.
SCAN OPTIMIZATION
You can shorten the scan time and speed up Kaspersky Internet Security. This can be achieved by scanning only new
files and those files that have altered since the last time they were scanned. This mode applies both to simple and
compound files.
Page 71

A D V A N C E D A P P L I C A T I O N S E T T I N G S
71
You can also set a restriction on scan duration for any one object. When the specified time interval expires, the object will
be excluded from the current scan (except for archives and files comprised of several objects).
To scan only new and changed files:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the Security level section, click the Settings button for the task selected.
4. In the window that opens, on the Scope tab in the Scan optimization section, check the Scan only new and
changed files box.
To set a restriction on scan duration:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select the desired task (Full Scan, Critical Areas Scan, or
Custom Scan).
3. In the Security level section, click the Settings button for the task selected.
4. In the window that opens, on the Scope tab in the Scan optimization section, check the Skip objects
scanned longer than box and specify the scan duration for a single file.
SCANNING REMOVABLE DRIVES ON CONNECTION
Nowadays, malicious objects which use operating systems' vulnerabilities to replicate via networks and removable media
have become increasingly widespread. Kaspersky Internet Security allows you to scan removable drives when
connecting them to the computer.
To configure scanning of removable media on connection:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select General Settings.
3. In the Scan removable drives on connection section, select the action and define the maximum size of a
drive to be scanned in the field below, if necessary.
CREATING A TASK SHORTCUT
The application provides the option of creating shortcuts for the full, quick, and vulnerability scan tasks. This allows you
to start the required scan without opening the main application window or a context menu.
To create a shortcut to start a scan:
1. Open the application settings window.
2. In the left part of the window, in the Scan section, select General Settings.
3. In the right part of the window, in the Scan tasks quick run section, click the Create shortcut button next to
the name of the desired task (Critical Areas Scan, Full Scan, or Vulnerability Scan).
4. Specify the path for saving the shortcut and its name in the window that opens. By default, the shortcut is
created with the name of the task in the My Computer folder of the current computer user.
Page 72

U S E R G U I DE
72
VULNERABILITY SCAN
Vulnerabilities may appear in the operating system, for example, due to programming errors, insecure passwords, or
actions of malicious programs. When performing the vulnerability scan, the application refers to various security
procedures, for example, examining the system, analyzing the settings of the operating system and the browser, and
searching for vulnerable services.
The diagnostics may take some time. When it is complete, detected problems are analyzed from the standpoint of the
danger they pose to the system.
After the vulnerability scan task is started (see page 48), its run progress is displayed in the Scan window (in the
Vulnerability Scan section) and in the Task Manager (see section "Managing scan tasks. Task Manager" on page 72).
Information about results of the vulnerability scan task run is recorded in a report of Kaspersky Internet Security (see
page 167).
As with virus scan tasks, you can set a startup schedule for a vulnerability scan task, create a list of objects to scan (see
page 67), specify an account (see section "Running a scan under a different user account" on page 69) and create a
shortcut for quick start of the task. By default, the applications already installed on the computer are selected as scan
objects.
MANAGING SCAN TASKS. TASK MANAGER
Task Manager displays information about last scan tasks that have been run or that are currently running (for example,
virus scan, vulnerability scan, rootkit scan, or advanced disinfection).
You can use Task Manager to view the progress and the result of a task run, or stop a task. For some tasks, additional
actions are also available (for example, on completion of vulnerability scan, you can open the list of detected
vulnerabilities and fix them).
To open Task Manager:
1. Open the main application window.
2. In the bottom part of the window, select the Scan section.
3. In the Scan window that opens, click the Manage Tasks button in the top right corner of the window.
UPDATE
Updating the databases and program modules of Kaspersky Internet Security ensures up-to-date protection for your
computer. New viruses, Trojans, and other types of malware appear worldwide on a daily basis. Information about
threats and ways of neutralizing them is provided by Kaspersky Internet Security databases. For timely detection of new
threats, you should update databases and application modules on a regular basis.
Regular updates require an active license for application usage. If no license is installed, you can perform an update only
once.
When performing an update, the application downloads and installs the following objects on your computer:
Kaspersky Internet Security databases.
Protection of information is ensured by databases containing threat signatures, descriptions of network attacks,
and information about how to resist them. Protection components use this information to search for and disinfect
dangerous objects on your computer. The databases are supplemented every hour with records of new threats
and ways to fight them. Therefore, you are strongly advised to update databases on a regular basis.
Page 73

A D V A N C E D A P P L I C A T I O N S E T T I N G S
73
IN THIS SECTION:
Selecting an update source ............................................................................................................................................. 73
Creating the update startup schedule ............................................................................................................................. 75
Rolling back the last update ............................................................................................................................................ 76
Running updates under a different user account ............................................................................................................. 76
Using a proxy server ....................................................................................................................................................... 76
In addition to the Kaspersky Internet Security databases, the network drivers that enable the application's
components to intercept network traffic are updated.
Application modules.
In addition to the Kaspersky Internet Security databases, you can also update the program modules. The
updates for the application modules fix Kaspersky Internet Security's vulnerabilities and supplement or improve
the existing functionality.
During an update, the application modules and databases on your computer are compared with the up-to-date version at
the update source. If your current databases and application modules differ from those in the current version of the
application, the missing portion of the updates will be installed on your computer.
If the databases are outdated, the update package may be large, which may cause additional Internet traffic (up to
several dozen MB).
Prior to updating the databases, Kaspersky Internet Security creates backup copies of them in case you want to return to
the previous version of the databases (see section "Rolling back the last update" on page 76).
Information about the current condition of Kaspersky Internet Security databases is displayed in the Update section of
the main application window.
Information on the update results and events which occurred during the execution of the update task is logged in a
Kaspersky Internet Security report (see page 167).
You can select an update source (see section "Selecting an update source" on page 73) and configure the automatic
update startup.
SELECTING AN UPDATE SOURCE
An update source is a resource containing updates for databases and application modules of Kaspersky Internet
Security.
The main update sources are the Kaspersky Lab update servers, where database updates and application module
updates for all Kaspersky Lab products are stored.
Your computer should be connected to the Internet for successful downloading of updates from our servers. By default,
the Internet connection settings are determined automatically. If you use a proxy server, you may need to adjust the
connection settings (see section "Configuring the proxy server" on page 118).
When updating Kaspersky Internet Security, you can copy database and program module updates received from
Kaspersky Lab servers into a local folder (see section "Updating the application from a shared folder" on page 74) and
then provide access to other networked computers. This saves Internet traffic.
Page 74

U S E R G U I DE
74
If you do not have access to Kaspersky Lab's update servers (for example, Internet access is restricted), you can call the
Kaspersky Lab headquarters (http://www.kaspersky.com/contacts) to request the contact information of Kaspersky Lab
partners who can provide you with updates on removable media.
When ordering updates on removable media, please specify whether you also require updates for the application
modules.
ADDING AN UPDATE SOURCE
By default, the list of update sources contains only Kaspersky Lab's update servers. You can add a local folder or a
different server as update source. If several resources are selected as update sources, Kaspersky Internet Security tries
to connect to them one after another, starting from the top of the list, and retrieves updates from the first available
source.
To add an update source:
1. Open the application settings window.
2. In the left part of the window, in the Update section, select the Update Settings component.
3. Click the Update source button in the right part of the window.
4. In the window that opens, on the Source tab, open the selection window by clicking the Add button.
5. In the Select update source window that opens, select the folder that contains the updates, or enter an
address in the Source field to specify the server from which the updates should be downloaded.
SELECTING THE UPDATE SERVER REGION
If you use Kaspersky Lab servers as the update source, you can select the optimal server location when downloading
updates. Kaspersky Lab servers are located in several countries.
Using the closest Kaspersky Lab update server allows you to reduce the time required for receiving updates and
increase operation performance speed. By default, the application uses information about the current region from the
operating system's registry. You can select the region manually.
To select the server region:
1. Open the application settings window.
2. In the left part of the window, in the Update section, select the Update Settings component.
3. Click the Update source button in the right part of the window.
4. In the window that opens, on the Source tab in the Regional settings section, select the Select from the list
option, and then select the country nearest to your current location from the dropdown list.
UPDATING THE APPLICATION FROM A SHARED FOLDER
To save Internet traffic, you can configure updates of Kaspersky Internet Security from a shared folder when updating the
application on networked computers. If you do this, one of the networked computers receives an update package from
Kaspersky Lab servers or from another web resource that contains the required set of updates. The updates received
are copied into a shared folder. Other networked computers access this folder to receive updates for Kaspersky Internet
Security.
When logged on under a guest account in Microsoft Windows 7, updates are not copied into the shared folder. It is
recommended that you log on under a different account in order to allow copying updates.
Page 75

A D V A N C E D A P P L I C A T I O N S E T T I N G S
75
To enable update distribution mode:
1. Open the application settings window.
2. In the left part of the window, in the Update section, select the Update Settings component.
3. Check the Copy updates to folder box in the Additional section and specify the path to a public folder where
all downloaded updates will be copied in the field below. You can also select a folder by clicking the Browse
button.
To download updates for your computer from a specified shared folder:
1. Open the application settings window.
2. In the left part of the window, in the Update section, select the Update Settings component.
3. Click the Update source button in the right part of the window.
4. In the window that opens, on the Source tab, open the selection window by clicking the Add button.
5. In the Select update source window that opens, select a folder or enter the full path to it in the Source field.
6. On the Source tab uncheck the Kaspersky Lab update servers box.
CREATING THE UPDATE STARTUP SCHEDULE
You can create a schedule to automatically start an update task: specify the frequency, start time (if necessary), and
advanced settings.
If it is not possible to start the task for any reason (for example, the computer was not on at that time), you can configure
the skipped task to start automatically as soon as it becomes possible.
You can also postpone automatic startup of the task after the application is started. Note that all scheduled tasks will be
run only after a specified time interval elapses from the startup of Kaspersky Internet Security.
The special Idle Scan mode (see section "Running tasks in background mode" on page 157) allows you to start
automatic updates when your computer is idle.
To configure the update task startup schedule:
1. Open the application settings window.
2. In the left part of the window, in the Update section, select the Update Settings component.
3. Click the Run mode button in the right part of the window.
4. In the window that opens, on the Run mode tab in the Schedule section, select the By schedule option and
configure the update run mode.
To enable automatic launching of a skipped task:
1. Open the application settings window.
2. In the left part of the window, in the Update section, select the Update Settings component.
3. Click the Run mode button in the right part of the window.
4. In the window that opens, on the Run mode tab in the Schedule section, select By schedule and check the
Run skipped tasks box.
Page 76

U S E R G U I DE
76
To postpone running a task after application startup:
1. Open the application settings window.
2. In the left part of the window, in the Update section, select the Update Settings component.
3. Click the Run mode button in the right part of the window.
4. In the window that opens, on the Run mode tab in the Schedule section, select the By schedule option and fill
in the Postpone running after application startup for field to specify how long the task run should be
postponed.
ROLLING BACK THE LAST UPDATE
After the first update of Kaspersky Internet Security, the option of rolling back to the previous databases becomes
available.
The update rollback feature is useful in case a new database version contains an invalid signature that makes Kaspersky
Internet Security block a safe application.
In the event of damage done to Kaspersky Internet Security databases, it is recommended that you run the update task
to download the up-to-date set of databases.
To roll back to the previous database version:
1. Open the main application window.
2. Select the Update section in the lower part of the window.
3. In the Update window that opens, click the button and select Roll back to the previous databases from
the menu that opens.
RUNNING UPDATES UNDER A DIFFERENT USER ACCOUNT
By default, the update procedure is run under your system account. However, Kaspersky Internet Security can update
from a source for which you have no access rights (for example, from a network folder containing updates) or authorized
proxy user credentials. You can run Kaspersky Internet Security updates on behalf of a user account that has such
rights.
To start the update under a different user's account:
1. Open the application settings window.
2. In the left part of the window, in the Update section, select the Update Settings component.
3. Click the Run mode button in the right part of the window.
4. In the window that opens, on the Run mode tab in the User account section, check the Run task as box.
Specify the user name and password.
Page 77

A D V A N C E D A P P L I C A T I O N S E T T I N G S
77
USING A PROXY SERVER
If you use a proxy server for Internet connection, you should reconfigure it to allow proper updating of Kaspersky Internet
Security.
To configure the proxy server:
1. Open the application settings window.
2. In the left part of the window, in the Update section, select the Update Settings component.
3. Click the Update source button in the right part of the window.
4. In the window that opens, on the Source tab, click the Proxy server button.
5. Configure the proxy server settings in the Proxy server settings window that opens.
FILE ANTI-VIRUS
File Anti-Virus prevents infection of the computer's file system. The component launches at the startup of the operating
system, remains in the RAM of the computer, and scans all files opened, saved, or run on your computer and on all
connected drives for viruses and other riskware.
You can create a protection scope and set a security level (a collection of settings that determine the scan's
thoroughness).
When the user or a program attempts to access a protected file, File Anti-Virus checks whether iChecker and iSwift
databases contain information about this file, and makes a decision on whether the file should be scanned.
By default, the signature analysis – a mode that uses records from application databases to search for threats – is
always enabled. You can also enable heuristic analysis and various scan technologies.
If a threat is detected in a file, Kaspersky Internet Security assigns one of the following statuses to the file:
Status designating the type of the malicious program detected (for example, virus, Trojan).
Potentially infected (suspicious) status if the scan cannot determine whether the file is infected or not. The file
may contain a code sequence typical of viruses and other malware, or the modified code of a known virus.
After that, the application displays a notification (see page 172) of the detected threat on the screen and performs the
action specified in the File Anti-Virus settings. You can change the action (see page 81) that the application should
perform if a threat is detected.
If you are working in automatic mode (see section "Selecting a protection mode" on page 64), when dangerous objects
are detected, Kaspersky Internet Security automatically applies the actions recommended by Kaspersky Lab specialists.
For malicious objects, this action is Disinfect. Delete if disinfection fails, for suspicious objects – Move to Quarantine.
If dangerous objects are detected when working in interactive mode (see section "Selecting a protection mode" on
page 64), the application displays a notification on the screen that you can use to select the required action the list of
available ones.
Before attempting to disinfect or delete an infected object, Kaspersky Internet Security creates a backup copy for
subsequent restoration or disinfection. Suspicious (potentially infected) objects are quarantined. You can enable
automatic scanning of quarantined objects after each update.
Page 78

U S E R G U I DE
78
IN THIS SECTION:
Enabling and disabling File Anti-Virus ............................................................................................................................. 78
Automatically pausing File Anti-Virus .............................................................................................................................. 78
Creating the protection scope of File Anti-Virus .............................................................................................................. 79
Changing and restoring the file security level .................................................................................................................. 80
Selecting file scan mode ................................................................................................................................................. 80
Using heuristic analysis when working with File Anti-Virus ............................................................................................. 81
Selecting file scan technology ......................................................................................................................................... 81
Changing the action to take on infected files ................................................................................................................... 81
Scan of compound files by File Anti-Virus ....................................................................................................................... 82
Optimizing file scan ................................ ......................................................................................................................... 83
ENABLING AND DISABLING FILE ANTI-VIRUS
By default, File Anti-Virus is enabled, running in a mode recommended by Kaspersky Lab specialists. You can disable
File Anti-Virus if necessary.
To disable File Anti-Virus:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the right part of the window, uncheck the Enable File Anti-Virus box.
AUTOMATICALLY PAUSING FILE ANTI-VIRUS
When doing resource-intensive work, you can pause File Anti-Virus. To reduce workload and ensure quick access to
objects, you can configure automatic pausing of the component at a specified time or when handling specified programs.
Pausing File Anti-Virus in case of a conflict with some applications is an emergency measure. If any conflicts arise when
working with the component, please contact Kaspersky Lab Technical Support Service (http://support.kaspersky.com).
The support specialists will help you resolve the simultaneous operation of Kaspersky Internet Security with other
applications on your computer.
To pause the component at a specified time:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the Security level section in the right part of the window click the Settings button.
Page 79

A D V A N C E D A P P L I C A T I O N S E T T I N G S
79
4. In the window that opens, on the Additional tab in the Pause task section, check the By schedule box and
click the Schedule button.
5. In the Pause task window, specify the time (in 24-hour hh:mm format) for which protection will be paused (the
Pause task at and Resume task at fields).
To pause the component when running specified applications:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the Security level section in the right part of the window click the Settings button.
4. In the window that opens, on the Additional tab in the Pause task section, check the At application startup
box and click the Select button.
5. In the Applications window, create a list of applications which pause the component when running.
CREATING THE PROTECTION SCOPE OF FILE ANTI-VIRUS
The protection scope implies the location and type of files being scanned. By default, Kaspersky Internet Security scans
only potentially infectable files stored on any hard drive, network drive or removable media.
To create the protection scope:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. In the window that opens, on the General tab, in the File types section, specify the type of files that you want to
be scanned by File Anti-Virus:
If you want to scan all files, select All files.
If you want to scan files of formats that are the most vulnerable to infection, select Files scanned by
format.
If you want to scan files with extensions that are the most vulnerable to infection, select Files scanned by
extension.
When selecting type of files to be scanned, you should note that:
The probability of malicious code penetrating some file formats (such as TXT) and its subsequent activation
is quite low. However, there are formats that contain or may contain an executable code (such as EXE,
DLL, DOC). The risk of penetration and activation of malicious code in such files is quite high.
A hacker may send a virus or other riskware to your computer within an executable file renamed as one
with the TXT extension. If you have selected scanning files by extension, such a file is skipped by the scan.
If scanning of files by format is selected, then, regardless of the extension, File Anti-Virus will analyze the
file header and reveal that the file is an EXE file. Such file is thoroughly scanned for viruses and other
riskware.
5. In the Protection scope list, perform one of the following actions:
If you want to add a new object to the list of objects to be scanned, click the Add link.
If you want to change an object's location, select one from the list and click the Edit link.
Page 80

U S E R G U I DE
80
The Select object to scan window opens.
If you want to delete an object from the list of objects to be scanned, select one from the list and click the
Delete link.
The deletion confirmation window opens.
6. Perform one of the following actions:
If you want to add a new object to the list of objects to be scanned, select one in the Select object to scan
window and click the OK button.
If you want to change an object's location, edit the path to one in the Object field in the Select object to
scan window and click the OK button.
If you want to delete an object from the list of objects to be scanned, click the Yes button in the deletion
confirmation window.
7. If necessary, repeat steps 6 – 7 to add, relocate, or delete objects from the list of objects to be scanned.
8. To exclude an object from the list of objects to be scanned, uncheck the box next to one in the Protection
scope list. However, the object remains on the list of objects to be scanned, though it is excluded from the scan
by File Anti-Virus.
CHANGING AND RESTORING THE FILE SECURITY LEVEL
Depending on your current needs, you can select one of the preset file/memory security levels or configure File AntiVirus on your own.
When configuring File Anti-Virus, you can always restore the recommended values. These settings are considered
optimal, recommended by Kaspersky Lab, and grouped in the Recommended security level.
To change the file security level:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the right part of the window, in the Security level section, set the desired security level, or click the Settings
button to modify the settings manually.
If you modify the settings manually, the name of the security level will change to Custom.
To restore the default file security level:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. Click the Default level button in the Security level section in the right part of the window.
SELECTING FILE SCAN MODE
A scan mode means a condition, under which File Anti-Virus starts scanning files. By default, Kaspersky Internet Security
runs in smart mode. When running in this file scan mode, File Anti-Virus makes decisions on file scan based on the
analysis of actions that the user takes on files, and on the type of those files. For example, when working with a Microsoft
Office document, Kaspersky Internet Security scans the file when it is first opened and last closed. Intermediate
operations that overwrite the file do not cause it to be scanned.
Page 81

A D V A N C E D A P P L I C A T I O N S E T T I N G S
81
To change the files scan mode:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the Security level section in the right part of the window click the Settings button.
4. In the window that opens, on the Additional tab in the Scan mode section, select the desired mode.
When selecting scan mode, you should take account of the types of files, with which you have to work with the
majority of time.
USING HEURISTIC ANALYSIS WHEN WORKING WITH FILE ANTI-VIRUS
During File Anti-Virus operation, signature analysis is always used: Kaspersky Internet Security compares the object
found with the database records.
To improve protection efficiency, you can use heuristic analysis (i.e., analysis of activity that an object performs in the
system). This analysis makes it possible to detect new malicious objects which are not yet described in the databases.
To enable heuristic analysis:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the Security level section in the right part of the window click the Settings button.
4. In the window that opens, on the Performance tab in the Scan methods section, check the Heuristic Analysis
box and specify the detail level for the scan.
SELECTING FILE SCAN TECHNOLOGY
In addition to the heuristic analysis, you can involve specific technologies that allow optimizing the file scan performance
due to excluding files from scan if they have not been modified since the last scan.
To specify the object scan technologies:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the Security level section in the right part of the window click the Settings button.
4. In the window that opens, on the Additional tab in the Scan technologies section, select the desired values.
CHANGING THE ACTION TO TAKE ON INFECTED FILES
If infected objects are detected, the application performs the selected action.
To change the action that should be taken on infected objects:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the right part of the window, select the desired option in the Action on threat detection section.
Page 82

U S E R G U I DE
82
SCAN OF COMPOUND FILES BY FILE ANTI-VIRUS
A common method of concealing viruses is to embed them into compound files: archives, installation packages,
embedded OLE objects, and mail file formats. To detect viruses that are hidden in this way, a compound file should be
unpacked, which can significantly decrease scanning speed.
For each type of compound file, you can choose to scan either all files or only new ones. To make your selection, click
the link next to the name of the object. It changes its value when you left-click it. If you select the scan new and changed
files only mode, the links for choosing whether to scan all or only new files will not be available.
By default, Kaspersky Internet Security scans only embedded OLE objects.
When large compound files are scanned, their preliminary unpacking may take a long time. This period can be reduced
by enabling unpacking of compound files in background mode if they exceed the specified file size. If a malicious object
is detected while working with such a file, the application will notify you about it.
You can restrict the maximum size of a compound file to be scanned. Compound files larger than the specified value will
not be scanned.
When large files are extracted from archives, they will be scanned even if the Do not unpack large compound files box
is checked.
To modify the list of compound files to be scanned:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the Security level section in the right part of the window click the Settings button.
4. In the window that opens, on the Performance tab in the Scan of compound files section, select the desired
type of compound files to be scanned.
To set the maximum size of compound files to be scanned:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the Security level section in the right part of the window click the Settings button.
4. In the window that opens, on the Performance tab in the Scan of compound files section, click the Additional
button.
5. In the Compound files window, check the Do not unpack large compound files box and specify the
maximum file size.
To unpack large compound files in background mode:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. In the Security level section in the right part of the window click the Settings button.
4. In the window that opens, on the Performance tab in the Scan of compound files section, click the Additional
button.
5. In the Compound files window, check the Extract compound files in the background box and specify the
minimum file size.
Page 83

A D V A N C E D A P P L I C A T I O N S E T T I N G S
83
OPTIMIZING FILE SCAN
You can shorten the scan time and speed up Kaspersky Internet Security. This can be achieved by scanning only new
files and those files that have altered since the last time they were scanned. This mode applies both to simple and
compound files.
To scan only new and changed files:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the File Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. In the window that opens, on the Performance tab in the Scan optimization section, check the Scan only new
and changed files box.
MAIL ANTI-VIRUS
Mail Anti-Virus scans incoming and outgoing messages for malicious objects. It starts when the operating system
launches and runs continually, scanning all email messages sent or received via the POP3, SMTP, IMAP, MAPI and
NNTP protocols, as well as over secure connections (SSL) via POP3 and IMAP (see section "Encrypted connections
scan" on page 116).
The indicator of the component's operation is the application icon in the taskbar notification area, which looks like
whenever an email message is being scanned.
Mail Anti-Virus intercepts and scans each email message received or sent by the user. If no threats are detected in an
email message, it becomes available for the user.
You can specify the types of messages which should be scanned and select the security level (see page 85)
(configuration settings affecting the scan intensity).
By default, the signature analysis – a mode that uses records from application databases to search for threats – is
always enabled. In addition, you can enable heuristic analysis. Furthermore, you can enable filtering of attachments (see
page 86), which allows automatic renaming or deletion of specified file types.
If a threat is detected in a file, Kaspersky Internet Security assigns one of the following statuses to the file:
Status designating the type of the malicious program detected (for example, virus, Trojan).
Potentially infected (suspicious) status if the scan cannot determine whether the file is infected or not. The file
may contain a code sequence typical of viruses and other malware, or the modified code of a known virus.
After that, the application blocks the email message, displays a notification (see page 172) of the detected threat on the
screen, and performs the action specified in the settings of Mail Anti-Virus. You can change the actions to be taken when
a threat is detected (see section "Changing the action to take on infected email messages" on page 86).
If you are working in automatic mode (see section "Selecting a protection mode" on page 64), when dangerous objects
are detected, Kaspersky Internet Security automatically applies the actions recommended by Kaspersky Lab specialists.
For malicious objects, this action is Disinfect. Delete if disinfection fails, for suspicious objects – Move to Quarantine.
If dangerous objects are detected when working in interactive mode (see section "Selecting a protection mode" on
page 64), the application displays a notification on the screen that you can use to select the required action the list of
available ones.
Before attempting to disinfect or delete an infected object, Kaspersky Internet Security creates a backup copy for
subsequent restoration or disinfection. Suspicious (potentially infected) objects are quarantined. You can enable
automatic scanning of quarantined objects after each update.
Page 84

U S E R G U I DE
84
If disinfection is successful, the email message becomes available. If the disinfection fails, the infected object is deleted
IN THIS SECTION:
Enabling and disabling Mail Anti-Virus ............................................................................................................................ 84
Creating the protection scope of Mail Anti-Virus ............................................................................................................. 84
Changing and restoring the email security level .............................................................................................................. 85
Using heuristic analysis when working with Mail Anti-Virus............................................................................................. 86
Changing the action to take on infected email messages ............................................................................................... 86
Filtering attachments in email messages ........................................................................................................................ 86
Scan of compound files by Mail Anti-Virus ...................................................................................................................... 87
Email scanning in Microsoft Office Outlook ..................................................................................................................... 87
Email scanning in The Bat! .............................................................................................................................................. 87
from the email message. Mail Anti-Virus expands the subject of the email message by adding text that notifies the user
that this email message has been processed by Kaspersky Internet Security.
An integrated plug-in is provided for Microsoft Office Outlook that allows you to fine-tune the email client.
If you use The Bat!, Kaspersky Internet Security can be used in conjunction with other anti-virus applications. At that, the
email traffic processing rules are configured directly in The Bat! and have a higher priority than the mail protection
settings of Kaspersky Internet Security.
When working with other widespread mail clients, including Microsoft Outlook Express/Windows Mail, Mozilla
Thunderbird, Eudora, and Incredimail, Mail Anti-Virus scans email on the SMTP, POP3, IMAP, and NNTP protocols.
Note that when working with the Thunderbird mail client, email messages transferred via IMAP will not be scanned for
viruses if any filters moving messages from the Inbox folder are used.
ENABLING AND DISABLING MAIL ANTI-VIRUS
By default, Mail Anti-Virus is enabled, running in a mode recommended by Kaspersky Lab specialists. You can disable
Mail Anti-Virus if necessary.
To disable Mail Anti-Virus:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Mail Anti-Virus component.
3. In the right part of the window, uncheck the Enable Mail Anti-Virus box.
CREATING THE PROTECTION SCOPE OF MAIL ANTI-VIRUS
Protection scope comprises a type of email messages to be scanned, protocols with traffic scanned by Kaspersky
Internet Security, and settings for integration of Mail Anti-Virus into the system.
By default, Kaspersky Internet Security is integrated into Microsoft Office Outlook and The Bat!, scans both incoming and
outgoing email messages, and scans traffic of POP3, SMTP, NNTP and IMAP email protocols.
Page 85

A D V A N C E D A P P L I C A T I O N S E T T I N G S
85
To disable scanning of outgoing emails:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Mail Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. Use the General tab in the Protection scope section of the displayed window to select the Incoming
messages only option.
If you have selected scanning incoming messages only, it is recommended that you scan outgoing mail when
first running Kaspersky Internet Security, since your computer may be infected with email worms that use your
email to breed and spread. Scanning outgoing mail allows you to avoid problems occurring due to uncontrolled
sending of email messages from your computer.
To select the protocols to scan and the settings for integrating Mail Anti-Virus into the system:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Mail Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. In the window that opens, on the Additional tab in the Connectivity section, select the desired settings.
CHANGING AND RESTORING THE EMAIL SECURITY LEVEL
Depending on your current needs, you can select one of the preset email security levels or configure Mail Anti-Virus on
your own.
Kaspersky Lab advises you not to configure Mail Anti-Virus settings on your own. In most cases, it is sufficient to select a
different security level.
When configuring Mail Anti-Virus, you can always restore the recommended values. These settings are considered
optimal, recommended by Kaspersky Lab, and grouped in the Recommended security level.
To change the current email security level:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Mail Anti-Virus component.
3. In the right part of the window, in the Security level section, set the desired security level, or click the Settings
button to modify the settings manually.
If you modify the settings manually, the name of the security level will change to Custom.
To restore the default mail protection settings:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Mail Anti-Virus component.
3. Click the Default level button in the Security level section in the right part of the window.
Page 86

U S E R G U I DE
86
USING HEURISTIC ANALYSIS WHEN WORKING WITH MAIL ANTI-VIRUS
During Mail Anti-Virus operation, signature analysis is always used: Kaspersky Internet Security compares the object
found with the database records.
To improve protection efficiency, you can use heuristic analysis (i.e., analysis of activity that an object performs in the
system). This analysis makes it possible to detect new malicious objects which are not yet described in the databases.
To enable heuristic analysis:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Mail Anti-Virus component.
3. In the Security level section in the right part of the window click the Settings button.
4. In the window that opens, on the General tab in the Scan methods section, check the Heuristic Analysis box
and specify the detail level for the scan.
CHANGING THE ACTION TO TAKE ON INFECTED EMAIL MESSAGES
If infected objects are detected, the application performs the selected action.
To change the action that should be taken on infected email messages:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Mail Anti-Virus component.
3. In the right part of the window, select the desired option in the Action on threat detection section.
FILTERING ATTACHMENTS IN EMAIL MESSAGES
Malicious programs may spread via email as attachments in email messages. You can configure filtering by type of
attachments in email messages, which allows the renaming or deleting files of specified types automatically.
To configure filtering of attachments:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Mail Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. Use the Attachment filter tab of the displayed window to select the filtering mode for attachments. When you
select either of the last two modes, the list of file types (extensions) will be enabled; there you can select the
desired types or add a new type mask.
To add a mask of a new type to the list, click the Add link to open the Input file name mask window and enter
the required information.
Page 87

A D V A N C E D A P P L I C A T I O N S E T T I N G S
87
SCAN OF COMPOUND FILES BY MAIL ANTI-VIRUS
A common method of concealing viruses is to embed them into compound files: archives, installation packages,
embedded OLE objects, and mail file formats. To detect viruses that are hidden in this way, a compound file should be
unpacked, which can significantly decrease scanning speed.
You can enable or disable scanning of compound files, and limit the maximum size of compound files to be scanned.
If your computer is not protected by any local network software (you access the Internet directly without a proxy server or
a firewall), it is not recommended that you disable the scanning of compound files.
To configure the scanning of compound files:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Mail Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. Use the General tab in the window that opens to define the necessary settings.
EMAIL SCANNING IN MICROSOFT OFFICE OUTLOOK
While installing Kaspersky Internet Security, a special plug-in is integrated into Microsoft Office Outlook. It allows you to
quickly switch to configuration of Mail Anti-Virus from Microsoft Office Outlook, and determine when email messages
should be scanned for viruses and other riskware, whether this should be done when receiving, opening, or sending a
message.
Configuration of Mail Anti-Virus from Microsoft Office Outlook is available if this option is selected in the protection scope
settings of Mail Anti-Virus.
To switch to the email scan settings in Microsoft Office Outlook:
1. Open the main Microsoft Office Outlook window.
2. Select Tools Options from the application menu.
3. In the Settings window that opens, select the Email protection tab.
EMAIL SCANNING IN THE BAT!
Actions with regard to infected email objects in The Bat! are defined using the application's own tools.
Mail Anti-Virus settings which determine whether incoming and outgoing messages should be scanned, which actions
should be performed in regard to dangerous objects in email, and which exclusions should apply are ignored. The only
thing that The Bat! takes into account is the scanning of attached archives.
The email protection settings extend to all the anti-virus components installed on the computer that support working with
the Bat!.
Note that incoming email messages are first scanned by Mail Anti-Virus and only then by the plug-in for The Bat!. If a
malicious object is detected, Kaspersky Internet Security immediately notifies you of this. If you select the Disinfect
(Delete) action in the Mail Anti-Virus notification window, actions aimed at eliminating the threat are performed by Mail
Anti-Virus. If you select the Ignore option in the notification window, the object will be disinfected by the plug-in for The
Bat!. When sending email messages, they are first scanned by the plug-in and then by Mail Anti-Virus.
Page 88

U S E R G U I DE
88
The settings of Mail Anti-Virus are available from The Bat! if this option is selected in the protection scope settings of Mail
Anti-Virus.
To configure email scanning in The Bat! you must define the following criteria:
which mail stream (incoming, outgoing) should be scanned;
when mail objects should be scanned (when opening a message, before saving to disk);
what actions are to be performed by the mail client if dangerous objects are detected in email messages. For
example, you can select:
Attempt to disinfect infected parts – if this option is selected, the attempt is made to disinfect the infected
object; if it cannot be disinfected, the object remains in the message.
Delete infected parts – if this option is selected, the dangerous object in the message is deleted
regardless of whether it is infected or suspected to be infected.
By default, The Bat! places all infected email objects in Quarantine without attempting to disinfect them.
Email messages that contain dangerous objects are not marked with the special subject add-on when scanned by the
plug-in for The Bat!.
To switch to the email scan settings in The Bat!:
1. Open the main window of the The Bat!.
2. In the Properties menu, select Settings.
3. Select the Virus protection object from the settings tree.
WEB ANTI-VIRUS
Each time you work on the Internet, you endanger information stored on your computer, by exposing it to a risk of being
infected with viruses and other malware. They may penetrate your computer when you download free applications or
view information on websites that had been attacked by hackers before you have visited them. Moreover, network worms
may penetrate into your computer even before you open a web page or download a file, just at the moment your
computer establishes an Internet connection.
Web Anti-Virus protects information received by your computer and sent from it over HTTP, HTTPS and FTP protocols,
and prevents hazardous scripts from being run on your computer.
Web Anti-Virus only monitors web traffic transferred via ports specified on the list of monitored ports. A list of monitored
ports that are most commonly used for data transfer, is included in the Kaspersky Internet Security distribution kit. If you
use ports that are not included in the list of monitored ports, you should add them to the list of monitored ports (see
section "Creating a list of monitored ports" on page 119) to ensure protection of web traffic transferred via them.
Web Anti-Virus scans web traffic with regard for a specific collection of settings named security level. If Web Anti-Virus
detects a threat, it will perform the prescribed action. Malicious objects are detected using both Kaspersky Internet
Security databases and a heuristic algorithm.
Kaspersky Lab advises you not to configure Web Anti-Virus settings on your own. In most cases, it is sufficient to select
an appropriate security level.
Page 89

A D V A N C E D A P P L I C A T I O N S E T T I N G S
89
IN THIS SECTION:
Enabling and disabling Web Anti-Virus ........................................................................................................................... 89
Changing and restoring the web traffic security level ...................................................................................................... 90
Changing the action to take on dangerous objects from web traffic ................................................................................ 90
Checking URLs on web pages ........................................................................................................................................ 90
Using heuristic analysis when working with Web Anti-Virus ............................................................................................ 93
Blocking dangerous scripts ............................................................................................................................................. 93
Scan optimization ............................................................................................................................................................ 94
Controlling access to regional domains ........................................................................................................................... 94
Controlling access to online banking services ................................................................................................................. 94
Creating a list of trusted addresses ................................................................................................................................. 95
Web traffic scan algorithm
Each web page or file that is accessed by the user or an application via the HTTP, HTTPS, or FTP protocols is
intercepted and scanned for malicious code by Web Anti-Virus:
If a web page or a file accessed by the user contains malicious code, access to it is blocked. A notification is
displayed that the requested file or web page is infected.
If the file or web page does not contain malicious code, the program immediately grants the user access to it.
Script scan algorithm
Each script run is intercepted by Web Anti-Virus and is analyzed for malicious code:
If a script contains malicious code, Web Anti-Virus blocks it and displays a notification on the screen.
If no malicious code is discovered in the script, it is run.
Web Anti-Virus intercepts only scripts based on the Microsoft Windows Script Host functionality.
ENABLING AND DISABLING WEB ANTI-VIRUS
By default, Web Anti-Virus is enabled, running in a mode recommended by Kaspersky Lab specialists. You can disable
Web Anti-Virus, if necessary.
To disable Web Anti-Virus:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. In the right part of the window, uncheck the Enable Web Anti-Virus box.
Page 90

U S E R G U I DE
90
CHANGING AND RESTORING THE WEB TRAFFIC SECURITY LEVEL
Depending on your current needs, you can select one of the preset web traffic security levels or configure Web Anti-Virus
on your own.
When configuring Web Anti-Virus, you can always restore the recommended values. These settings are considered
optimal, recommended by Kaspersky Lab, and grouped in the Recommended security level.
To change the web traffic security level:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. In the right part of the window, in the Security level section, set the desired security level, or click the Settings
button to modify the settings manually.
If you modify the settings manually, the name of the security level will change to Custom.
To restore the default web traffic security level:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Default level button in the Security level section in the right part of the window.
CHANGING THE ACTION TO TAKE ON DANGEROUS OBJECTS
FROM WEB TRAFFIC
If infected objects are detected, the application performs the selected action.
Web Anti-Virus always blocks actions by dangerous scripts and displays messages that inform the user of the action
taken. You cannot change the action to be taken on a dangerous script; all you can do is disable script scan (see section
"Blocking dangerous scripts" on page 93).
To change the action to be performed with regard to detected objects:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. In the right part of the window, select the desired option in the Action on threat detection section.
CHECKING URLS ON WEB PAGES
Scanning web pages for phishing allows you to prevent phishing attacks. Phishing attacks are, as a rule, email
messages from alleged financial organizations that contain URLs to websites of such organizations. The email message
convinces the reader to click the URL and enter private information in the window that opens, for example, the number of
a banking card or the login and the password of an online banking account. A phishing attack can be disguised, for
example, as a letter from your bank with a link to its official website. By clicking the link, you go to an exact copy of the
bank's website and can even see the bank site's address in the browser, even though you are on a counterfeit site. From
this point forward, all your actions on the site are tracked and can be used to steal your money.
Since links to phishing web sites may be received not only in email, but also from other sources, such as ICQ messages,
Web Anti-Virus monitors attempts to access a phishing web site on the level of web traffic and blocks access to such
locations.
Page 91

A D V A N C E D A P P L I C A T I O N S E T T I N G S
91
IN THIS SECTION:
Enabling and disabling the checking of URLs ................................................................................................................. 91
Using Kaspersky URL Advisor ........................................................................................................................................ 91
Blocking access to dangerous websites .......................................................................................................................... 92
In addition to Kaspersky Internet Security databases, heuristic analysis (see page 93) can also be used for scanning web
pages for phishing.
ENABLING AND DISABLING THE CHECKING OF URLS
To enable URL checks using the databases of suspicious web addresses and phishing addresses:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
The Web Anti-Virus window opens.
4. On the General tab, in the Kaspersky URL Advisor section, check the Check if URLs are listed in the
database of suspicious URLs and Check web pages for phishing boxes.
USING KASPERSKY URL ADVISOR
Kaspersky URL Advisor is integrated into Microsoft Internet Explorer, Mozilla Firefox, and Google Chrome as a plug-in.
Kaspersky URL Advisor checks all URLs on a web page to find out if they are included in the list of suspicious URLs. It
also checks them for phishing, highlighting each one in the browser window.
You can create a list of websites, on which all URLs should be checked, check URLs on all websites except those
included in the list of exclusions, check URLs in search results only, or specify categories of websites with URLs that
should be checked.
Not only can you configure Kaspersky URL Advisor in the application settings window, but also in the Kaspersky URL
Advisor settings window, which is available from your web browser.
To specify websites, on which all URLs should be checked:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. The Web Anti-Virus window opens.
5. On the Safe Surf tab, in the Kaspersky URL Advisor section, check the Check URLs box.
6. Select the websites on which the links need to be scanned:
a. If you want to create a list of websites, on which all URLs should be checked, select Only websites from
the list and click the Specify button. In the Checked URLs window that opens, create a list of websites to
be checked.
b. If you want to check URLs on all websites except those specified, select All but the exclusions and click
the Exclusions button. In the Exclusions window that opens, create a list of websites that do not need any
check of URLs on them.
Page 92

U S E R G U I DE
92
To check URLs in search results only:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. The Web Anti-Virus window opens.
5. On the Safe Surf tab, in the Kaspersky URL Advisor section, check the Check URLs box and click the
Settings button.
6. In the Kaspersky URL Advisor settings window that opens, in the Check mode section, select Only URLs in
search results.
To select categories of websites with URLs that should be checked:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
4. The Web Anti-Virus window opens.
5. On the Safe Surf tab, in the Kaspersky URL Advisor section, check the Check URLs box and click the
Settings button.
6. In the Kaspersky URL Advisor settings window that opens, in the Websites categories section, check the
Show information on the categories of websites content box.
7. In the list of categories, check the boxes next to categories of websites with URLs that should be checked.
To open the Kaspersky URL Advisor settings window from your web browser,
click the button with the Kaspersky Internet Security icon in the browser toolbar.
BLOCKING ACCESS TO DANGEROUS WEBSITES
You can block access to websites which have been deemed suspicious or phishing sites by Kaspersky URL Advisor (see
section "Using Kaspersky URL Advisor" on page 91).
To block access to dangerous websites:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
The Web Anti-Virus window opens.
4. On the Safe Surf tab, in the Blocking Dangerous Websites section, check the Block dangerous websites
box.
Page 93

A D V A N C E D A P P L I C A T I O N S E T T I N G S
93
USING HEURISTIC ANALYSIS WHEN WORKING WITH WEB ANTI-VIRUS
To improve protection efficiency, you can use heuristic analysis (i.e., analysis of activity that an object performs in the
system). This analysis makes it possible to detect new malicious objects which are not yet described in the databases.
When Web Anti-Virus is running, you can separately enable the heuristic analysis for scanning web traffic and for
checking web pages for phishing.
To enable the heuristic analysis for scanning web traffic:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
The Web Anti-Virus window opens.
4. On the General tab in the Heuristic Analysis section, check the Use Heuristic Analysis box and set a scan
detail level.
To enable the heuristic analysis for checking web pages for phishing:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
The Web Anti-Virus window opens.
4. On the General tab, in the Kaspersky URL Advisor section, click the Additional button.
5. In the Anti-Phishing settings window that opens, check the Use Heuristic Analysis to check web pages for
phishing box and set a scan detail level.
BLOCKING DANGEROUS SCRIPTS
Web Anti-Virus scans all scripts processed in Microsoft Internet Explorer, as well as any other WSH scripts (for example,
JavaScript, Visual Basic Script, etc.) launched when you are working on the computer. If a script presents a threat to
your computer, it will be blocked.
To disable blocking of dangerous scripts:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
The Web Anti-Virus window opens.
4. On the General tab in the Additional section uncheck the Block dangerous scripts in Microsoft Internet
Explorer box.
Page 94

U S E R G U I DE
94
SCAN OPTIMIZATION
To improve efficiency of detection of malicious code, Web Anti-Virus uses the caching of fragments of objects coming
from the Internet. Using the caching, Web Anti-Virus scans objects only after they are received on the computer in their
entirety.
The caching increases the amount of time required to process objects and pass it to the user for further operations.
Caching can cause problems when downloading or processing large objects, as the connection with the HTTP client may
time out.
You can solve this problem using the option of limiting the caching of fragments of objects coming from the Internet.
Upon expiration of a certain time interval, each fragment of an object is passed to the user unscanned. When copying is
complete, the object will be scanned entirely. This allows us to reduce the amount of time required to pass objects to the
user and solving the problem with connection losses. The Internet security level is not reduced.
Lifting restrictions on the duration of web traffic caching leads to improved efficiency of virus scans, though it may slow
down access to objects.
To set or remove a time limit for fragment buffering:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
The Web Anti-Virus window opens.
4. On the General tab, in the Additional section, check the Limit traffic caching time to 1 sec to optimize scan
box.
CONTROLLING ACCESS TO REGIONAL DOMAINS
Depending on your choice, Web Anti-Virus in Geo Filter mode can block or allow access to websites on the grounds of
their belonging to regional web domains. This allows you, for example, to block access to websites which belong to
regional domains with a high risk of infection.
To allow or block access to websites which belong to specified domains:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
The Web Anti-Virus window opens.
4. On the Geo Filter tab, check the Enable filtering by regional domains box and specify in the list of controlled
domains below which domains should be allowed or blocked, and for which ones the application should request
permission for access using a notification (see section "Request for permission to access a website from a
regional domain" on page 197).
By default, access is allowed for regional domains that match your location. Requesting permission for access is
set for other domains by default.
Page 95
A D V A N C E D A P P L I C A T I O N S E T T I N G S
95
CONTROLLING ACCESS TO ONLINE BANKING SERVICES
When working with online banking, your computer needs an especially reliable protection, since leakages of confidential
information may lead to financial losses. Web Anti-Virus can control access to online banking services, thus ensuring
safe interaction with them (see section "About Safe Run for Websites" on page 141). Web Anti-Virus automatically
determines which web resources are online banking services. For guaranteed identification of a web resource as online
banking service, you can specify its URL in the list of banking websites.
To configure control of access to online banking services:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
The Web Anti-Virus window opens.
4. On the Online Banking tab, check the Enable control box. You will be prompted to start the Certificate
Installation Wizard that you can use to install a Kaspersky Lab certificate for scanning encrypted connections.
5. If necessary, create a list of resources that Kaspersky Internet Security should identify as online banking
services.
CREATING A LIST OF TRUSTED ADDRESSES
Web Anti-Virus does not scan web traffic for dangerous objects if it comes from trusted URLs.
To create a list of trusted web addresses:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Web Anti-Virus component.
3. Click the Settings button in the right part of the window.
The Web Anti-Virus window opens.
4. On the Trusted URLs tab, check the Do not scan web traffic from trusted URLs box.
5. Create a list of websites / web pages with content that you trust. To do this:
a. Click the Add button.
The Address mask (URL) window will open.
b. Enter the address of a website / web page or the address mask of a website / web page.
c. Click the OK button.
A new record appears on the list of trusted URLs.
6. If necessary, repeat steps from a to c.
Page 96

U S E R G U I DE
96
IM ANTI-VIRUS
IN THIS SECTION:
Enabling and disabling IM Anti-Virus ................................................................................................ ............................... 96
Creating the protection scope of IM Anti-Virus ................................................................................................................ 96
Checking URLs in messages from IM clients .................................................................................................................. 97
Using heuristic analysis when working with IM Anti-Virus ............................................................................................... 97
IM Anti-Virus scans the traffic of instant messaging clients (so-called Internet pagers).
IM messages may contain links to suspicious websites and to websites used by hackers to organize phishing attacks.
Malicious programs use IM clients to send spam messages and links to programs (or the programs themselves) which
steal users' ID numbers and passwords.
Kaspersky Internet Security ensures safe operation of various instant messaging applications, including ICQ, MSN, AIM,
Yahoo! Messenger, Jabber, Google Talk, Mail.Ru Agent and IRC.
Some IM clients, such as Yahoo! Messenger and Google Talk, use encrypted connections. To scan the traffic generated
by those programs, you have to enable encrypted connections scanning (see page 116).
IM Anti-Virus intercepts messages and scans them for dangerous objects or URLs. You can select the types of
messages to scan and various scanning methods.
If threats are detected in a message, IM Anti-Virus replaces this message with a warning message for the user.
Files transferred via IM clients are scanned by the File Anti-Virus component (on page 77) when attempts are made to
save them.
ENABLING AND DISABLING IM ANTI-VIRUS
By default, IM Anti-Virus is enabled and functions in normal mode. You can disable IM Anti-Virus if necessary.
To disable IM Anti-Virus:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the IM Anti-Virus component.
3. In the right part of the window, uncheck the Enable IM Anti-Virus box.
CREATING THE PROTECTION SCOPE OF IM ANTI-VIRUS
The protection scope is the type of messages to be scanned. By default, Kaspersky Internet Security scans both
incoming and outgoing messages. If you are sure that messages you send cannot contain any dangerous objects, you
may disable scanning of outgoing traffic.
Page 97

A D V A N C E D A P P L I C A T I O N S E T T I N G S
97
To disable scanning of outgoing messages:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the IM Anti-Virus component.
3. In the right part of the window, in the Protection scope section, select the Incoming messages only option.
CHECKING URLS IN MESSAGES FROM IM CLIENTS
To scan messages for suspicious and phishing URLs:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the IM Anti-Virus component.
3. In the right part of the window, in the Scan methods section, check the Check if URLs are listed in the
database of suspicious URLs and Check if URLs are listed in the database of phishing URLs boxes.
USING HEURISTIC ANALYSIS WHEN WORKING WITH IM ANTI-VIRUS
To improve protection efficiency, you can use heuristic analysis (i.e., analysis of activity that an object performs in the
system). This analysis makes it possible to detect new malicious objects which are not yet described in the databases.
When using heuristic analysis, any script included in an IM client's message is executed in a protected environment. If
the script's activity is typical of malicious objects, the object is likely to be classed as malicious or suspicious. By default,
heuristic analysis is enabled.
To enable heuristic analysis:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the IM Anti-Virus component.
3. In the right part of the window, in the Scan methods section, check the Heuristic Analysis box and set the
necessary scanning intensity level.
PROACTIVE DEFENSE
Proactive Defense protects your computer against new threats which are not yet included in Kaspersky Internet Security
databases.
The functioning of Proactive Defense is based on proactive technologies. Proactive technologies allow you to neutralize
a new threat before it does any harm to your computer. Unlike responsive technologies, which analyze code based on
records in Kaspersky Internet Security databases, preventative technologies recognize a new threat on your computer by
the sequence of actions executed by a program. If, as a result of activity analysis, the sequence of an application's
actions arouses suspicion, Kaspersky Internet Security blocks the activity of this application.
For example, when actions such as a program copying itself to network resources, the startup folder and the system
registry are detected, it is highly likely that this program is a worm.
Hazardous sequences of actions also include attempts to modify the HOSTS file, hidden installation of drivers, etc. You
can turn off monitoring (see page 99) for any hazardous activity or edit its monitoring rules (see page 99).
As opposed to the Application Control protection component (on page 101), Proactive Defense responds immediately to
a defined sequence of an application's actions. Activity analysis is applied to all applications running on your computer,
including those allocated in the Trusted group by the Application Control protection component.
Page 98

U S E R G U I DE
98
You can create a group of trusted applications (see page 98) for Proactive Defense. You will not be notified of the
IN THIS SECTION:
Enabling and disabling Proactive Defense ...................................................................................................................... 98
Creating a group of trusted applications .......................................................................................................................... 98
Using the dangerous activity list ...................................................................................................................................... 99
Changing the action to be taken on applications' dangerous activity .............................................................................. 99
activities of these applications.
If your computer runs under Microsoft Windows XP Professional x64 Edition, Microsoft Windows Vista, Microsoft
Windows Vista x64, Microsoft Windows 7, or Microsoft Windows 7 x64, control will not apply to all events. This is due to
specific features of these operating systems. For example, control will not apply fully to the sending of data through
trusted applications and suspicious system activities.
ENABLING AND DISABLING PROACTIVE DEFENSE
By default, Proactive Defense is enabled, running in a mode recommended by Kaspersky Lab specialists. You can
disable Proactive Defense if necessary.
To disable Proactive Defense:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Proactive Defense component.
3. In the right part of the window, uncheck the Enable Proactive Defense box.
CREATING A GROUP OF TRUSTED APPLICATIONS
Programs recognized by the Application Control protection component as Trusted pose no threat for the system.
However, their activities will also be monitored by Proactive Defense.
You can create a group of trusted applications exerting activity that should not be controlled by Proactive Defense. By
default, the list of trusted applications includes applications with verified digital signatures and applications that are
trusted in the Kaspersky Security Network database.
To change the settings of the trusted applications group:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Proactive Defense component.
3. In the right part of the window, in the Trusted applications section, perform the following actions:
If you want applications with verified digital signatures to be included in the group of trusted applications,
check the Applications with digital signature box.
If you want applications trusted by the Kaspersky Security Network database to be included in the group of
trusted applications, check the Trusted in Kaspersky Security Network database box.
Page 99

A D V A N C E D A P P L I C A T I O N S E T T I N G S
99
USING THE DANGEROUS ACTIVITY LIST
The list of actions typical of dangerous activity cannot be edited. However, you can refuse to control a selected case of
dangerous activity.
To turn off monitoring for one dangerous activity or another:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Proactive Defense component.
3. Click the Settings button in the right part of the window.
4. In the Proactive Defense window that opens, uncheck the box next to the type of activity which you do not want
to be monitored.
CHANGING THE ACTION TO BE TAKEN ON APPLICATIONS'
DANGEROUS ACTIVITY
The list of actions typical of dangerous activity cannot be edited. However, you can change the action that Kaspersky
Internet Security takes when applications' dangerous activity is detected.
To change the action that Kaspersky Lab application takes on dangerous activity of another application:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the Proactive Defense component.
3. Click the Settings button in the right part of the window.
4. In the Proactive Defense window that opens, in the Event column, select the desired event for which you want
to edit the rule.
5. Configure the settings for the selected event using the links in the Rule description section. For example:
a. Click the link with the preset action and select the desired action in the Select action window that opens.
b. Click the On / Off link to indicate that a report on operation execution should be created.
SYSTEM WATCHER
System Watcher collects data about application actions on your computer and provides information to other components
for improved protection.
Based on information collected by System Watcher, Kaspersky Internet Security can roll back actions performed by
malicious programs.
Rolling back actions performed by malicious programs can be initiated by one of the following protection components:
System Watcher - based on patterns of dangerous activity;
Proactive Defense;
File Anti-Virus;
when performing a virus scan.
Page 100

U S E R G U I DE
100
If suspicious events are detected in the system, Kaspersky Internet Security protection components can request
IN THIS SECTION:
Enabling and disabling System Watcher ....................................................................................................................... 100
Using patterns of dangerous activity (BSS) ................................................................................................................... 100
Rolling back a malicious program's actions ................................................................................................ ................... 101
additional information from System Watcher. In interactive protection mode of Kaspersky Internet Security (see section
"Selecting a protection mode" on page 64), you can view data collected by the System Watcher component and
presented as a report on dangerous activity history. This data can help you make a decision when selecting an action in
the notification window. When the component detects a malicious program, the link to the System Watcher's report is
displayed in the top part of the notification window (see page 197), along with a prompt for action.
ENABLING AND DISABLING SYSTEM WATCHER
By default, System Watcher is enabled, running in a mode recommended by Kaspersky Lab specialists. You can disable
System Watcher if necessary.
You are advised not to disable the component unless it is absolutely necessary, since this inevitably decreases the
efficiency of Proactive Defense and other protection components that may request data collected by System Watcher in
order to identify the potential threat detected.
To disable System Watcher:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the System Watcher component.
3. In the right part of the window, uncheck the Enable System Watcher box.
USING PATTERNS OF DANGEROUS ACTIVITY (BSS)
Patterns of dangerous activity (BSS – Behavior Stream Signatures) contain sequences of actions typical of applications
classified as dangerous. If an application's activity matches a pattern of dangerous activity, Kaspersky Internet Security
performs the prescribed action.
To provide real-time effective protection, Kaspersky Internet Security adds patterns of dangerous activity, which are used
by System Watcher, during the database updates.
By default, when Kaspersky Internet Security is running in automatic mode, if an application's activity matches a pattern
of dangerous activity, System Watcher moves this application to Quarantine. When running in interactive mode, System
Watcher prompts for action. You can specify the action that the component should perform when an application's activity
matches a pattern of dangerous activity.
In addition to exact matches between applications' activities and patterns of dangerous activity, System Watcher also
detects actions that partly match patterns of dangerous activity and are considered suspicious based on the heuristic
analysis. If suspicious activity is detected, System Watcher prompts for action regardless of the operation mode.
To select the action that the component should perform if an application's activity matches a pattern of dangerous
activity:
1. Open the application settings window.
2. In the left part of the window, in the Protection Center section, select the System Watcher component.
 Loading...
Loading...