Juniper SECURITY THREAT RESPONSE MANAGER 2008.2 R2 - REV1, Security Threat Response Manager 2008.2 R2 User Manual
Security Threat Response Manager
STRM Users Guide
Release 2008.2 R2
Juniper Networks, Inc.
1194 North Mathilda Avenue
Sunnyvale, CA 94089
USA
408-745-2000
www.juniper.net
Part Number: 530-027294-01, Revision 1
Copyright Notice
Copyright © 2008 Juniper Networks, Inc. All rights reserved. Juniper Networks and the Juniper Networks logo are registered trademarks of Juniper
Networks Inc. in the United States and other countries. All other trademarks, service marks, registered trademarks, or registered service marks in this
document are the property of Juniper Networks or their respective owners. All specifications are subject to change without notice. Juniper Networks
assumes no responsibility for any inaccuracies in this document or for any obligation to update information in this document. Juniper Networks reserves
the right to change, modify, transfer, or otherwise revise this publication without notice.
FCC Statement
The following information is for FCC compliance of Class A devices: This equipment has been tested and found to comply with the limits for a Class A
digital device, pursuant to part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference when the
equipment is operated in a commercial environment. The equipment generates, uses, and can radiate radio-frequency energy and, if not installed and
used in accordance with the instruction manual, may cause harmful interference to radio communications. Operation of this equipment in a residential
area is likely to cause harmful interference, in which case users will be required to correct the interference at their own expense. The following
information is for FCC compliance of Class B devices: The equipment described in this manual generates and may radiate radio-frequency energy. If it
is not installed in accordance with NetScreen’s installation instructions, it may cause interference with radio and television reception. This equipment has
been tested and found to comply with the limits for a Class B digital device in accordance with the specifications in part 15 of the FCC rules. These
specifications are designed to provide reasonable protection against such interference in a residential installation. However, there is no guarantee that
interference will not occur in a particular installation. If this equipment does cause harmful interference to radio or television reception, which can be
determined by turning the equipment off and on, the user is encouraged to try to correct the interference by one or more of the following measures:
Reorient or relocate the receiving antenna. Increase the separation between the equipment and receiver. Consult the dealer or an experienced radio/TV
technician for help. Connect the equipment to an outlet on a circuit different from that to which the receiver is connected.
Caution: Changes or modifications to this product could void the user's warranty and authority to operate this device.
Disclaimer
THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET
THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE
SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR JUNIPER NETWORKS REPRESENTATIVE FOR A COPY.
STRM Users Guide
Release 2008.2 R2
Copyright © 2008, Juniper Networks, Inc.
All rights reserved. Printed in USA.
Revision History
September 2008—Revision 1
The information in this document is current as of the date listed in the revision history.
2
CONTENTS
ABOUT THIS GUIDE
Conventions 1
Technical Documentation 1
Contacting Customer Support 2
1 ABOUT STRM
Logging In to STRM 3
Dashboard 4
Offense Manager 5
Event Viewer 5
Flow Viewer 6
Assets 6
Network Surveillance 8
Reports 9
Using STRM 9
Sorting Results 9
Refreshing the Interface 10
Pausing the Interface 10
Investigating IP Addresses 10
Viewing STRM Time 11
Accessing On-line Help 11
STRM Administration Console 11
2 USING THE DASHBOARD
About the Dashboard 13
Using the Dashboard 15
Network Surveillance 16
Traffic 16
TopN 17
Offense Manager 18
Offenses 18
Attackers and Targets 19
Categories 19
Event Viewer 20
Events Over Time 20
Events By Severity 20
Top Devices 21
Reports 22
Enterprise Security State 22
Enterprise Vulnerability State 23
System Summary 24
Adding Items 24
3 MANAGING YOUR NETWORK ACTIVITY
Using the Network Surveillance Menu 25
Global Views 25
Asset Map 26
Bookmarks 27
QRL Options 27
Viewing Network Activity 28
Interpreting the Graphs 28
Changing the View 30
Changing Flow Attributes 32
Changing Traffic Location 33
Investigating Traffic Using TopN 34
Viewing the TopN Information 34
Investigating Traffic 35
Investigating Flows 36
4 MANAGING SENTRIES
About Sentries 40
Types of Sentries 40
Viewing Sentries 42
Creating a Sentry 43
Creating a Security/Policy Sentry 44
Creating a Behavior Sentry 49
Creating an Anomaly Sentry 56
Creating a Threshold Sentry 61
Creating a Custom Sentry 66
Editing a Sentry 72
5 INVESTIGATING OFFENSES
Using the Offense Manager 78
Managing My Offenses 78
Managing Offenses 79
Viewing Offenses 79
Searching Offenses 88
Removing Offenses 90
Assigning Offenses to Users 92
Viewing Offense By Category 93
Managing Offenses By Attacker 97
Viewing Offenses by Attacker 97
Searching Attackers 104
Managing Offenses By Targets 106
Viewing Offenses By Targets 106
Searching Targets 112
Managing Offenses By Networks 114
Viewing Offenses By Networks 114
Searching Networks 124
Marking an Item For Follow-Up 125
Adding Notes 125
Configuring Notification 126
Managing Network Anomalies 127
Viewing Network Anomaly Offenses 127
Closing Offenses 129
Forwarding Network Anomaly Offenses 130
Exporting Offenses 131
6 USING THE EVENT VIEWER
Using the Event Viewer Interface 134
Using the Toolbar 134
Using the Right-Click Menu Options 134
Viewing Events 135
Viewing Normalized Events 135
Viewing Raw Events 139
Viewing Aggregate Normalized Events 140
Searching Events 145
Searching Events 145
Deleting Saved Searches 148
Viewing the Associated Offense 148
Modifying Event Mapping 149
Tuning False Positives 151
Exporting Events 152
7 USING THE FLOW VIEWER
Using the Flow Viewer Interface 154
Using the Toolbar 154
Using the Right-Click Menu Options 154
Viewing Flows 155
Viewing Flows 155
Viewing Aggregated Flows 158
Using the Search 164
Searching Flows 164
Deleting Saved Searches 167
Exporting Flows 167
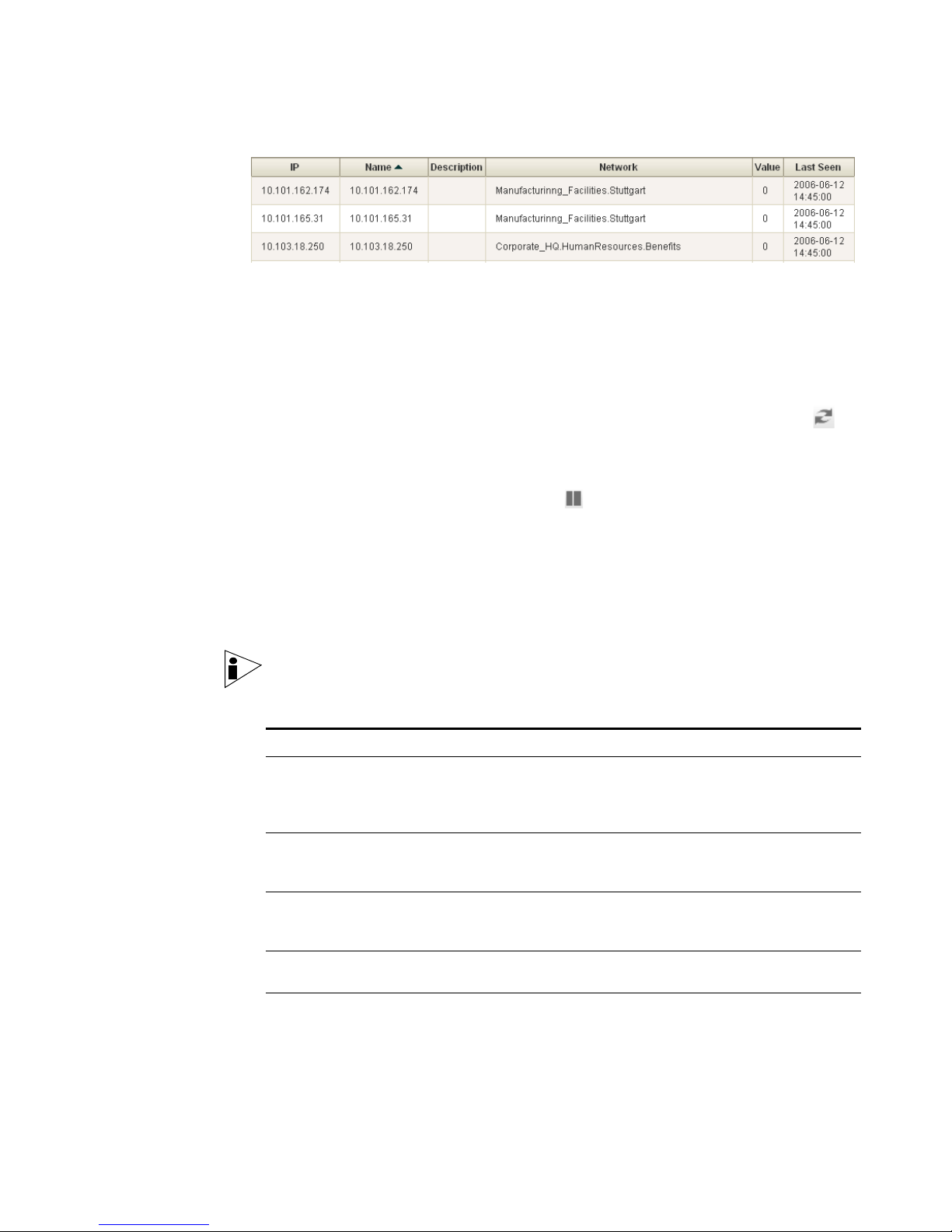
8 MANAGING ASSETS
Searching Asset Profiles 169
Adding an Asset Profile 175
Editing an Asset 176
Deleting Assets 178
Deleting an Asset 178
Deleting All Assets 178
Importing Asset Profiles 179
Exporting Assets 180
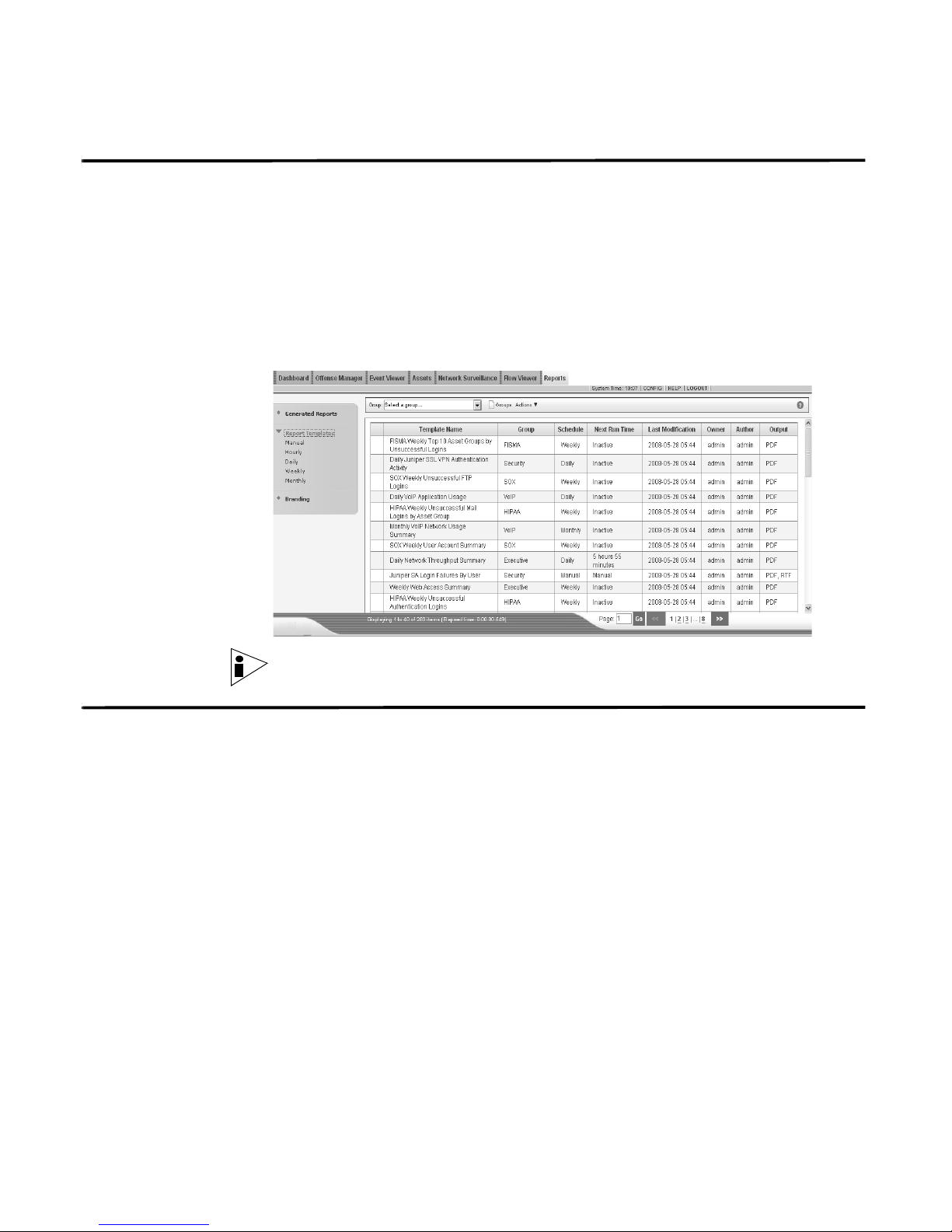
9 MANAGING REPORTS
Using the Reports Interface 182
Using the Navigation Menu 182
Using the Toolbar 183
Viewing Reports 183
Grouping Reports 184
Creating a Group 185
Editing a Group 186
Copying a Template to Another Group 186
Deleting a Template From a Group 187
Assigning a Report to a Group 188
Creating a Report 188
Creating a Template 189
Configuring Charts 196
Selecting a Graph Type 214
Using Default Report Templates 216
Generating a Report 217
Duplicating a Report 217
Sharing a Report 218
Branding Your Report 218
10 USING TNC RECOMMENDATIONS
Configuring TNC Recommendations 221
Removing TNC Recommendations 223
A GLOSSARY
INDEX
ABOUT THIS GUIDE
The STRM Users Guide provides information on managing STRM including the
Dashboard, Offense Manager, Reports, Event Viewer, and Network Surveillance
interfaces.
Conventions Table 1 lists conventions that are used throughout this guide.
Table 1 Icons
Icon Type Description
Information note Information that describes important features or
instructions.
Caution Information that alerts you to potential loss of
data or potential damage to an application,
system, device, or network.
Warning Information that alerts you to potential personal
injury.
Technical
Documentation
You can access technical documentation, technical notes, and release notes
directly from the Juniper Networks support web site at https://juniper.net/support.
Once you access the Juniper Networks support web site, locate the product and
software release for which you require documentation.
Your comments are important to us. Please send your e-mail comments about this
guide or any of the Juniper Networks documentation to:
documentation@juniper.net.
Include the following information with your comments:
• Document title
• Page number
STRM Users Guide
2 ABOUT THIS GUIDE
Contacting
Customer Support
To help you resolve any issues that you may encounter when installing or
maintaining STRM, you can contact Customer Support as follows:
• Log a support request 24/7: https://juniper.net/support/
For access to the Juniper Networks support web site, please contact Customer
Support.
• Access Juniper Networks support and Self-Service support using e-mail:
support@juniper.net
• Telephone assistance: 1-800-638-8296.
STRM Users Guide
1
ABOUT STRM
STRM is a network security management platform that provides situational
awareness and compliance support through the combination of flow-based
network knowledge, security event correlation, and asset-based vulnerability
assessment. This chapter provides an overview of the STRM interface including:
• Logging In to STRM
• Dashboard
• Offense Manager
• Event Viewer
• Flow Viewer
• Assets
• Network Surveillance
• Network Surveillance
• Reports
• Using STRM
• STRM Administration Console
Note: When navigating STRM, do not use the browser Back button. Use the
navigation options available with STRM to navigate the interface.
Logging In to STRM To login to STRM:
Step 1 Open your web browser.
Step 2 Log in to STRM:
https://<
Where <
are:
Username: admin
Password: <root password>
Where
installation process. For more information, see the STRM Installation Guide.
IP Address>
IP Address> is the IP address of the STRM system. The default values
<root password> is the password assigned to STRM during the
STRM Users Guide

4 ABOUT STRM
Step 3 Click Login To STRM.
For your STRM Console, a default license key provides you access to the interface
for 5 weeks. A window appears providing the date that the temporary license key
will expire. For information on installing a permanent license key, see the STRM
Administration Guide.
Dashboard The Dashboard tab is the default interface that appears when you log in to STRM.
The Dashboard tab provides summary and detailed information on offenses
occurring on your network, your network overall security and vulnerability state, as
well as in depth views into your network traffic behavior. The Dashboard is
customizable on a per user basis to focus on individual user’s security or network
operations responsibilities.
Note: For more information on using the Dashboard, see Chapter 2 Using the
Dashboard.
STRM Users Guide
Offense Manager 5
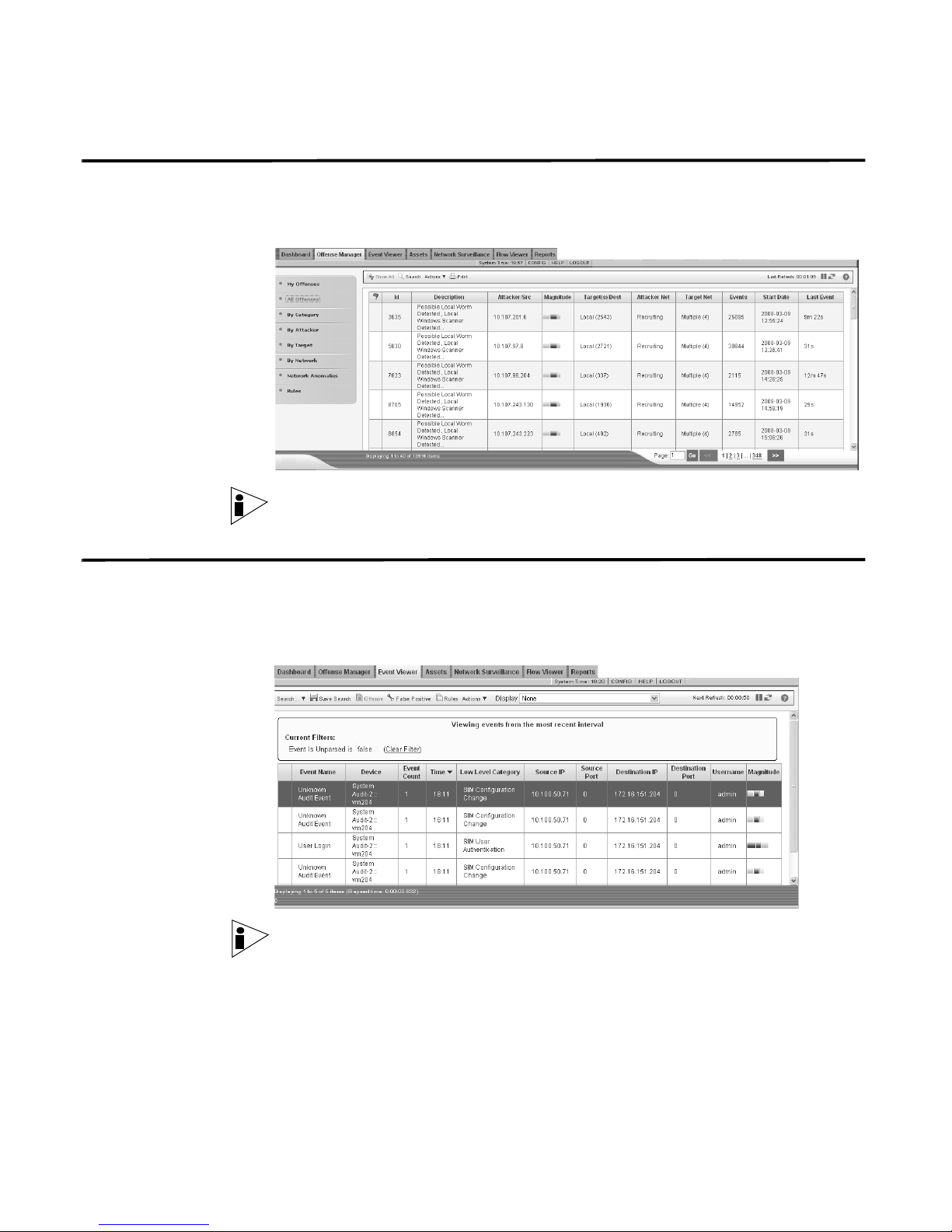
Offense Manager The Offense Manager tab provides a view into all offenses occurring on your
network. From the Offense Manager, you can investigate an offense to determine
the root cause of an issue. You can also resolve the issue.
Note: For more information on Offense Manager, see Chapter 5 Investigating
Offenses.
Event Viewer The Event Viewer allows you to view event logs being sent to STRM in real-time,
or through powerful searches. The Event Viewer is a powerful tool for performing
in-depth investigations on event data. It is also useful for quickly identifying false
positives and tuning STRM.
Note: For more information, see Chapter 6 Using the Event Viewer.
STRM Users Guide
6 ABOUT STRM
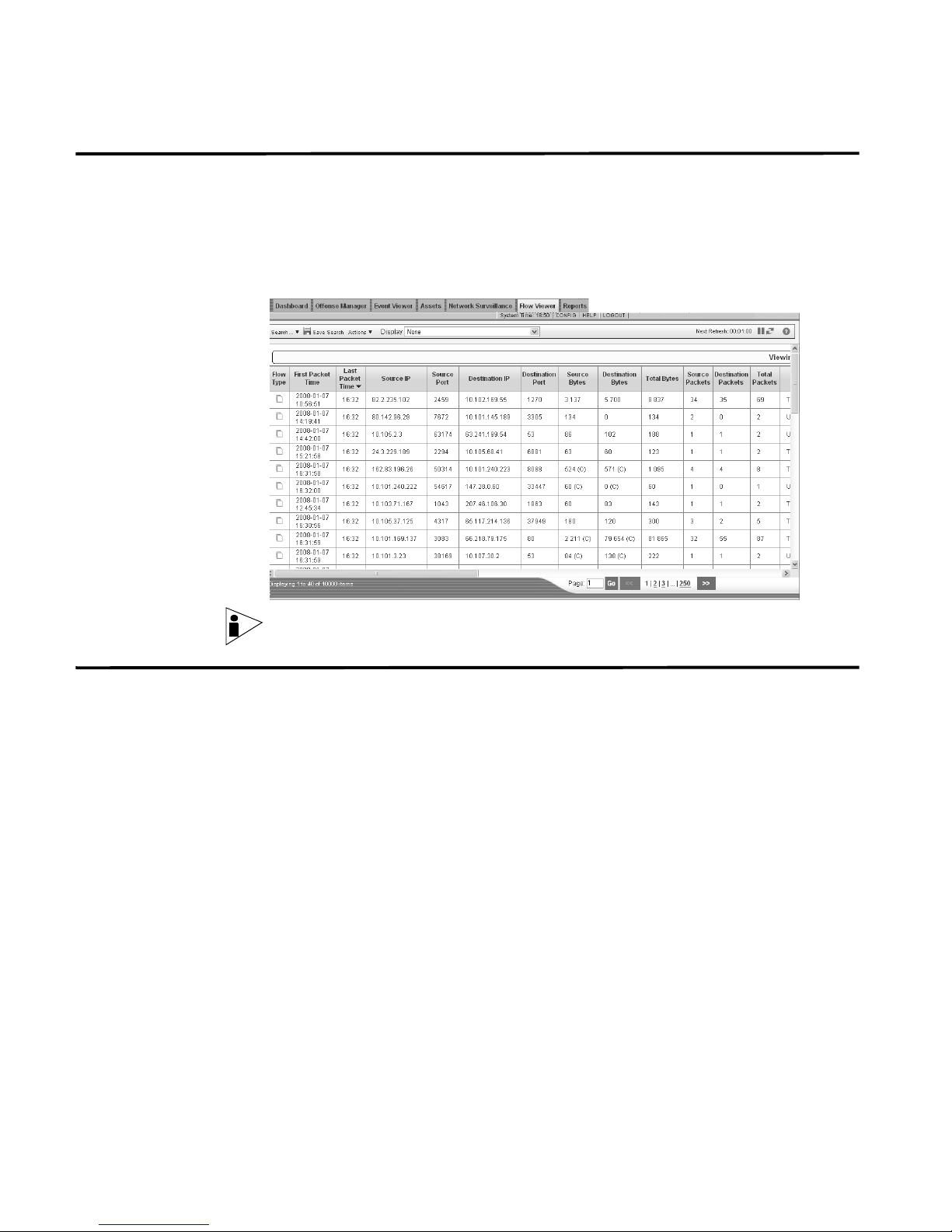
Flow Viewer The Flow Viewer tab allows you to monitor and investigate flow data in real-time or
perform advanced searches. A flow is a communication session between two
hosts. Viewing flow information allows you to determine how the traffic is
communicated, what was communicated (if the content capture option is enabled),
and includes such details as when, who, how much, protocols, ASN values, IfIndex
values, or priorities.
Note: For more information, see Chapter 7 Using the Flow Viewer.
Assets STRM automatically discovers assets (servers and hosts) operating on your
network, based on passive QFlow data as well as vulnerability data allowing STRM
to build an asset profile. Asset profiles display what services are running on each
asset. This profile data is used for correlation purposes to help reduce false
positives, for example, if an attack occurs trying to exploit a specific service
running on a specific asset, STRM can determine if the asset is vulnerable to this
attack by correlating the attack to the asset profile. Using the Assets tab, you can
view all the learned assets or search for specific assets to view there profiles.
STRM Users Guide
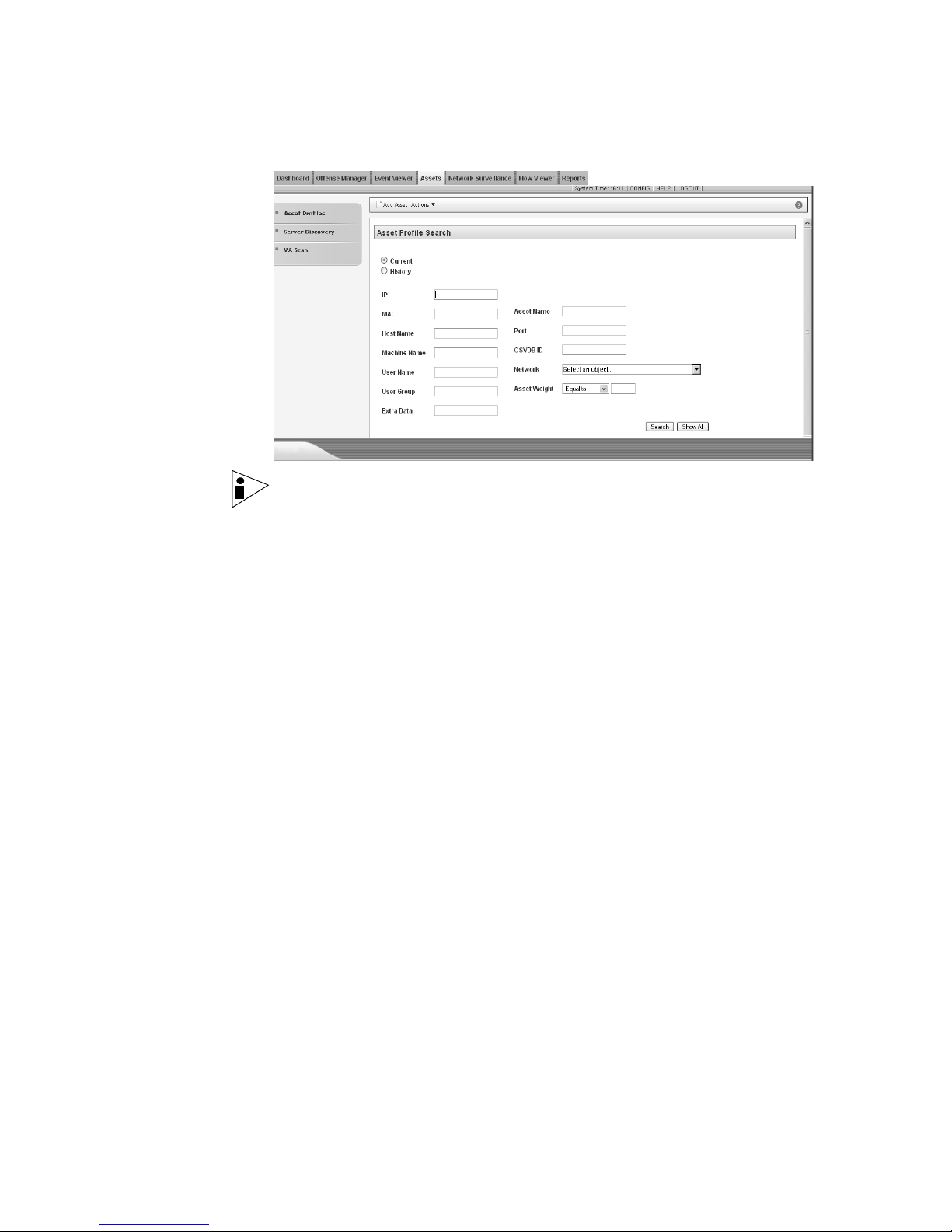
Note: For more information, see Chapter 8 Managing Assets.
Assets 7
STRM Users Guide
8 ABOUT STRM
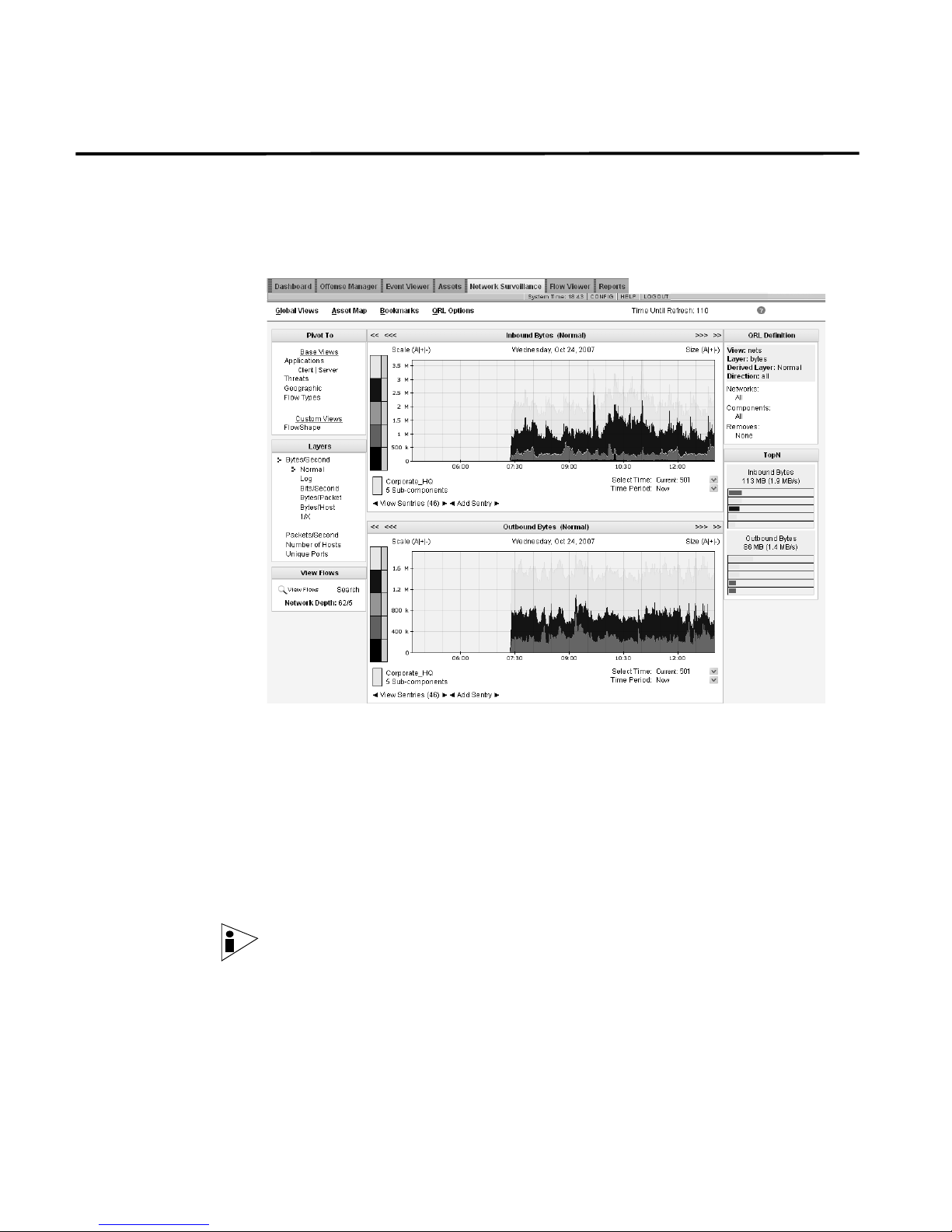
Network
Surveillance
The Network Surveillance tab is a real-time network behavioral and anomaly
monitoring interface that allows you to monitor the traffic on your network and how
your network is behaving. The Network Surveillance tab displays what areas of
your network are producing the most traffic, what applications are running, and
what types of threatening or out of policy traffic are present on your network.
Using the Network Surveillance interface, you can:
• Sentries are a technology that monitors traffic seen in any Network Surveillance
view, such as apps, network , asset groups and geographies, and alert on
normal behavior. Using the Network Surveillance interface, you can add
sentries to any view you are monitoring. The alerts that sentries create can be
correlated with events sent from other security and infrastructure devices to
create offenses, viewed within the Offense Manager.
• View and investigate your network activity. For more information, see Chapter 3
Managing Your Network Activity.
Note: For more information on using the Network Surveillance interface, see
Chapter 3 Managing Your Network Activity.
STRM Users Guide
Reports 9
Reports Reports is a flexible and robust reporting package that allows you to create,
distribute, and manage reports for any data within STRM. Reports allows you to
create customized reports for operational and executive use by combining any
combination of information (such as, security or network) into a single report. You
can also use the many pre-installed report templates included with STRM.
The Reports tab also allows you to brand your reports with your customized logos
enabling you to support various unique logos for each report. This is beneficial for
distributing reporting to different audiences.
Note: For more information on Reports, see Chapter 9 Managing Reports.
Using STRM Using STRM, you can:
• Sort the results. See Sorting Results.
• Refresh the interface. See Refreshing the Interface.
• Pause the current display. See Pausing the Interface.
• Further investigate an IP address. See Investigating IP Addresses.
• View the time of the STRM Console. See Viewing STRM Time.
• Access the on-line Help. See Accessing On-line Help.
Sorting Results In the Event Viewer, Offense Manager, Flow Viewer, and Reports interfaces, you
can sort the resulting tables by clicking on a column heading. A single click of the
desired column sorts the results in descending order and a second click on the
heading sorts the results in ascending order. An arrow at the top of the column
indicates the direction of the sort.
For example, if you wish to sort the events by Name, click the Name heading. An
arrow appears in the column heading to indicate the results are sorted in
descending order.
STRM Users Guide
10 ABOUT STRM
Click the Name column heading again if you wish to sort the information in
ascending order.
Refreshing the
Interface
Several STRM interfaces, including the Event Viewer, Offense Manager, Flow
Viewer, and the Dashboard allow you to refresh the interface. This refresh option is
located in the right corner of the interface. The timer indicates the amount of time
since the interface was refreshed. To refresh the interface, click the refresh
icon.
Pausing the Interface You can use the refresh timer, located on the right, to pause the current display. To
pause the interface, click the pause icon . The timer flashes red to indicate the
current display is paused. Click the icon again to restart the timer.
Investigating IP
Addresses
You can use the right-mouse button (right-click) on any IP address or asset name
to access additional menus, which allow you to further investigate that IP address
or asset. For more information on assets, see the STRM Administration Guide.
The menu options include:
Note: For information on customizing the right-click menu, see the Customizing
the Right-Click Menu Technical Note.
Table 1-1 Additional Options
Menu Sub-Menu Description
Navigate View Network
Location
View Attacker
Summary
View Target
Summary
Information DNS Lookup Searches for DNS entries based on the IP
WHOIS Lookup Searches for the registered owner of a
Opens the Network Surveillance interface
displaying the network activity for the
network that the selected IP address is
associated with.
Displays the attacker summary window that
displays all offenses associated with the
selected attacker.
Displays the target summary window that
displays all offenses associated to the
selected target.
address.
remote IP address (Default system server:
whois.crsnic.net.)
STRM Users Guide
Table 1-1 Additional Options (continued)
Menu Sub-Menu Description
Port Scan Performs a NMAP scan of the selected IP
address. This option is only available if
NMAP is installed on your system. For more
information on installing NMAP, see your
vendor documentation.
Asset Profile Displays asset profile information. This menu
option is only available when profile data has
been acquired either actively (through a
scan) or passively (through flow sources).
For information, see the STRM
Administration Guide.
Search Flows Allows you search for flows. For information,
see
Chapter 7 Using the Flow Viewer.
Resolver Actions View Resolver
Actions
Add Resolver
Action
TNC
Recommendations
Displays the Resolver Actions applied to this
IP address.
Executes the Add Resolver process. This
option is available when a Resolver is online
and able to resolve any protocol. However,
since a TCP Reset Resolver is effective for
TCP-based communications only, you
cannot execute a TCP Reset Resolver from
Allows you to restrict or deny network access
to users based on user name or other
credentials.
For more information, see
TNC Recommendations
STRM Administration Console 11
Chapter 10 Using
.
Viewing STRM Time The right corner of the STRM interface displays STRM time, which is the time of
the STRM Console. The STRM Console time synchronizes all STRM appliances
within the STRM deployment, and is used to determine the time events were
received from other devices for proper time sync correlation.
Accessing On-line
Help
STRM
Administration
Console
You can access the STRM on-line Help through the main STRM interface. To
access the on-line Help, click Help > Help Contents. The Help interface appears.
The STRM Administration Console is a client-based application that provides
administrative users access to administrative functionality including:
• System Configuration - Allows you configure system wide STRM settings
including, users, thresholds, system settings, network hierarchy, authentication,
sentries, or automatic updates.
• Access the deployment editor - Allows you to manage the individual
components of your STRM and SIM deployment.
• Configure views - Allows you to manage your views.
STRM Users Guide

12 ABOUT STRM
• Managing vulnerability assessment and scanners - Allows you to schedule
scans to keep your vulnerability assessment data up-to-date.
• Configure sensor devices - Allows you to configure sensor devices, which
provide events to your deployment through DSMs.
• Configure flow sources - Allows you to configure flow sources, such as,
NetFlow or Packeteer.
All configuration updates using the Administration Console are saved to a staging
area. Once all changes are complete, you can deploy the configuration changes or
all configuration settings to the remainder of your deployment.
For more information regarding the STRM Administration Console, see the STRM
Administration Guide.
STRM Users Guide
2
USING THE DASHBOARD
The Dashboard allows you to create a customized portal to monitor any data
STRM collects, to which you have access. The Dashboard is the default view
when you log in to STRM and allows you to monitor several areas of your network
at the same time. Normal activity, vulnerabilities, and suspicious behaviors can be
investigated directly from the Dashboard. All information displayed on the
Dashboard is current and provides you with a real-time portal into the status of
your network traffic and assets. You can detach an item and monitor the item
directly from your desktop.
This chapter includes:
• About the Dashboard
• Network Surveillance
• Offense Manager
• Event Viewer
About the
Dashboard
• Reports
• Enterprise Security State
• Enterprise Security State
• Enterprise Vulnerability State
• System Summary
• Adding Items
The Dashboard allows you to monitor your overall network behavior, security and
vulnerability posture, top targeted assets, top attackers, and worst and most recent
security offenses - all from one window.
By default, for non-administrative users, the Dashboard is empty. For
administrative users, the Dashboard displays the following:
• System Summary
• Events - Average Events Per Second
• Offenses - New Offense Count
• Most Severe Offenses
STRM Users Guide

14 USING THE DASHBOARD
• Most Recent Offenses
• Local Networks - Inbound Bytes
• Local Networks - Outbound Bytes
• Top Category Types
• Top Attackers
Note: The items that appear on your Dashboard depends on the access you have
been granted. For more information on user roles, see the STRM Administration
Guide.
The content that appears on the Dashboard is user-specific. You can design the
Dashboard as you wish, as the changes made within a STRM session affect only
your system. The next time you log in, STRM reflects your last Dashboard
configuration.
You can move and position items to meet your requirements. You can stack items
in one panel or distribute them evenly within the three panels. When positioning
items, each item automatically resizes in proportion to the panel. The Dashboard
interface refreshes regularly to display the most recent information.
STRM Users Guide
About the Dashboard 15
Using the Dashboard You can add, remove, or detach items on the Dashboard. Once added, each item
appears with a titlebar. Using the Dashboard, you can:
• Adding Items - Provides the list of items that you can add to your Dashboard.
You can monitor the following items:
- Network Surveillance
- Offense Manager
- Event Viewer
- Enterprise Security State
- Reports
- Enterprise Security State
- Enterprise Vulnerability State
- System Summary
• Removing an Item - To remove an item from the Dashboard, click the red icon
located in the upper right corner of the item.
A confirmation window appears before an item is removed. Removing an item
does not remove the item from STRM. Removing an item clears the item from
the Dashboard. You can add the item again at any time.
• Detaching an Item - To detach an item from the Dashboard, click the green
icon located in the upper right of the item. Detaching an item does not
remove the item from STRM; detaching an item duplicates the data in a new
window.
Detaching an item allows you to temporarily monitor one or more particular
items on your desktop. You can detach the item then remove the item from the
Dashboard - the detached window remains open and refreshes during
scheduled intervals. If you close the STRM application, the detached window
remains open for monitoring and continues to refresh until you manually close
the window or shut down your computer system.
Note: STRM does not save the status of a detached Dashboard item when you
end your STRM session.
STRM Users Guide
16 USING THE DASHBOARD
Network
Surveillance
You can add several Network Surveillance items to your Dashboard to display your
current network traffic activity. You can choose to display traffic data and TopN
data. Traffic data is displayed by graphs, complete with legends; TopN data is
displayed in bar charts, and allows you to investigate your traffic from the
Dashboard.
Network Surveillance options include:
• Traffic
• TopN
Within the TopN and Traffic options, you can add the following items to your
Dashboard.
• Threats
• Local Networks
• Client Applications
• Server Applications
• Geographic
• Flow Types
• Custom Views
• Bookmarks - This menu option only appears if you have configured bookmarks
using the Network Surveillance interface. For more information on bookmarks,
see Chapter 3 Managing Your Network Activity.
Note: The available views are dependent on the Global or Custom Views your
Network Administrator has enabled/disabled. If enabled, you can add any custom
view to your Dashboard.
Traffic Traffic is a graphical representation of bytes, packets, or hosts from a selected
view. Traffic data appears with a legend and identifies the traffic you are viewing.
STRM Users Guide

Network Surveillance 17
Note: You can click any area of the graph, or click the dynamic legend to
immediately access the Network Surveillance interface.
To customize your Threats display:
• Period of Time - Using the drop-down list box, select the period of time you
wish the Dashboard graph to display.
• Chart Type - You can display the data using a Time Series (default), Line
Chart, or Pie Chart. To change the chart type, click Time Series, Line Chart or
Pie Chart at the top of the graph.
TopN TopN data displays the most active objects from the top of your network providing
you with information from the most active network objects. Active objects can
include threats, applications, protocols, etc. The active object appears as a bar
chart and displays the highest level of activity by the number of assets, bytes,
packets, active ports, and number of flows. This is determined by the current view
displayed on the STRM graphs.
Note: You can double-click the bars to immediately navigate to the Network
Surveillance interface and display the traffic on the STRM graphs.
STRM Users Guide
18 USING THE DASHBOARD
Offense Manager You can add several Offense Manager items to your Dashboard. The Offense
Manager displays data for offenses, attackers, and local targets detected on your
network. Offense Manager options include:
• Offenses
• Attackers and Targets
• Categories
Note: Hidden or closed offenses are not included in the values that appear in the
Dashboard.
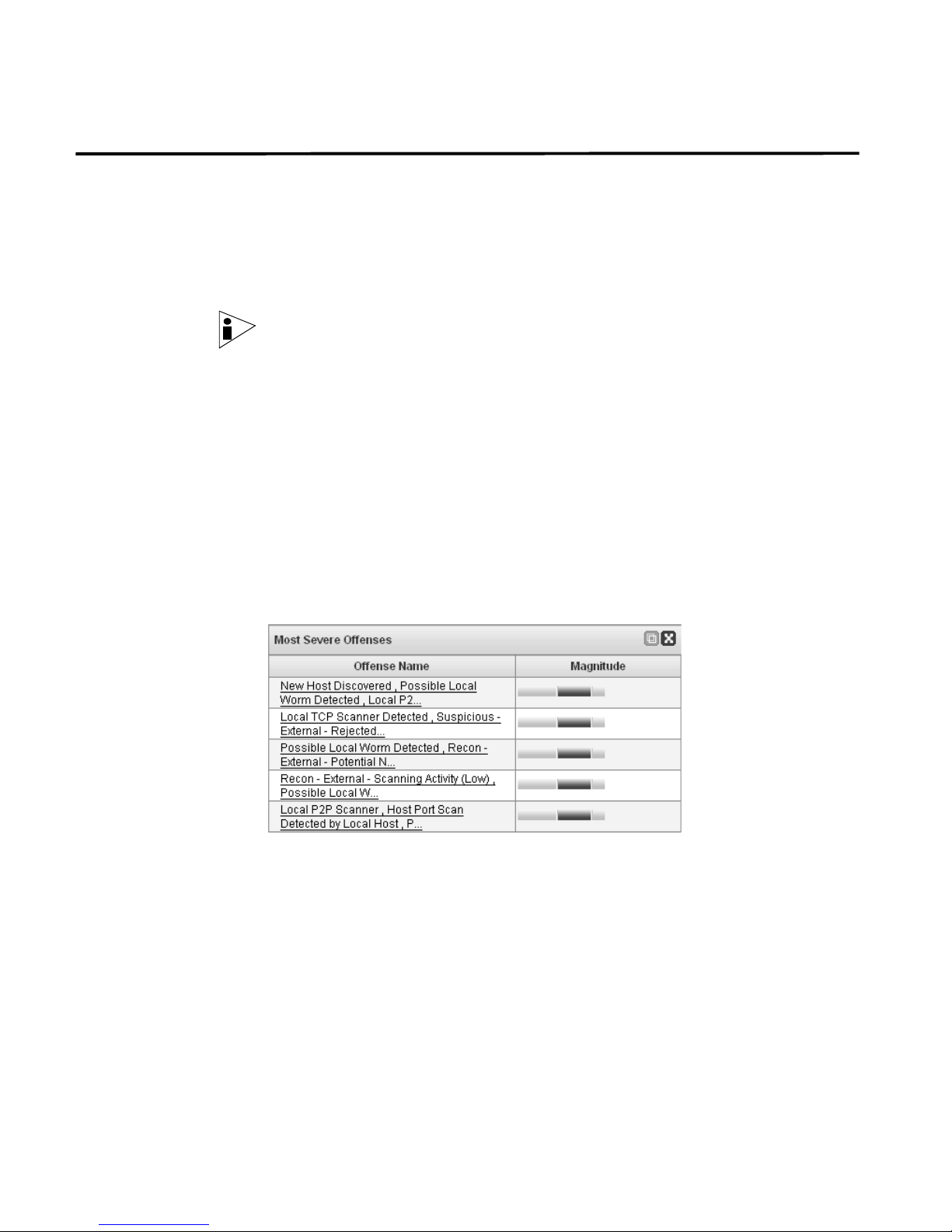
Offenses The Offenses option displays the five most recent offenses, severe offenses, or
the new offenses over time including:
• Most Severe and Most Recent Offenses
• My Offenses
• New Offense Over Time
Most Severe and Most Recent Offenses
The most recent and severe offenses are identified and classed with a magnitude
bar to inform you of the importance of the offense. Point your mouse to the IP
address to view detailed information for the IP address.
My Offenses
The My Offenses item displays all offenses assigned to you. The offenses are
identified and classed with a magnitude bar to inform you of the importance of the
offense. Point your mouse to the IP address to view detailed information for the IP
address.
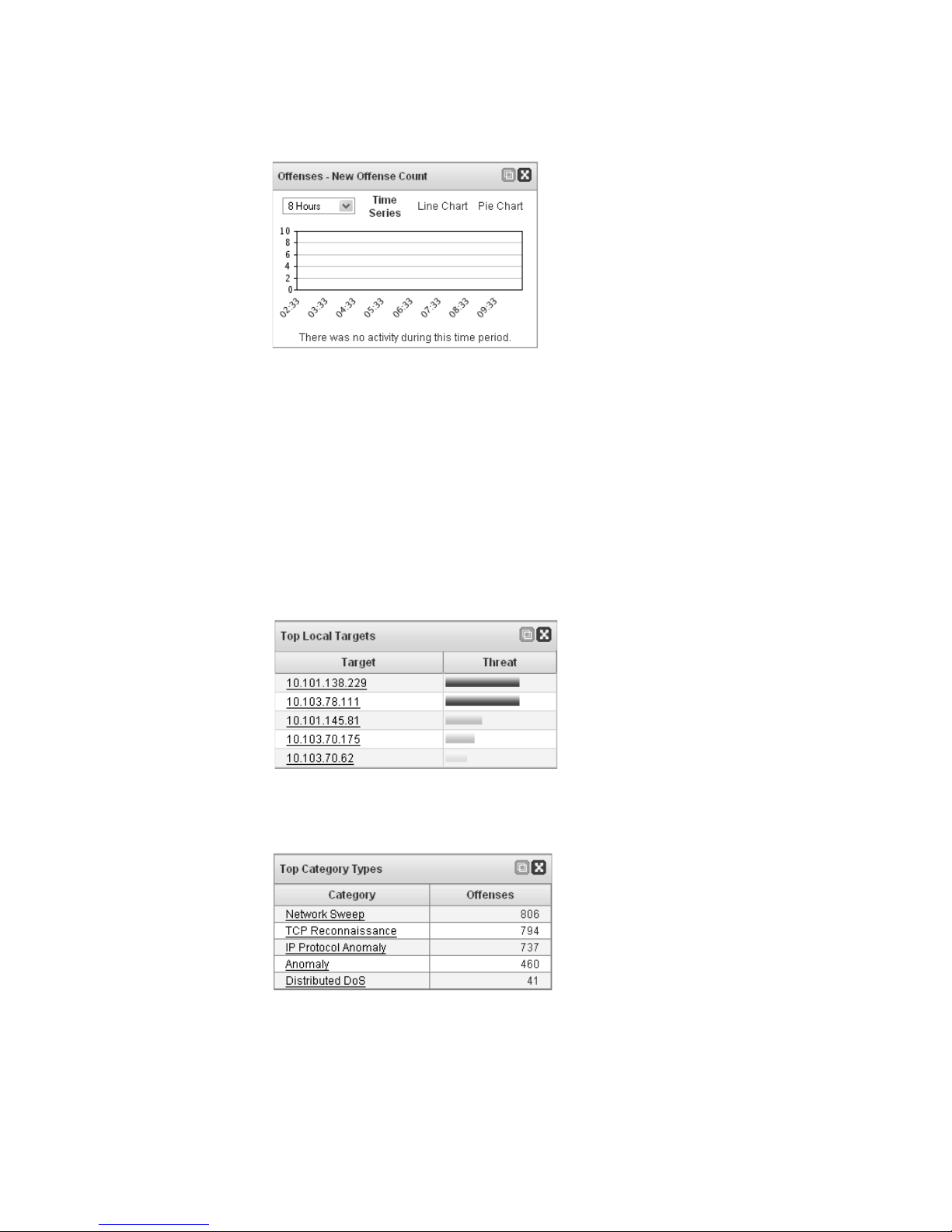
New Offense Over Time
The new offenses over time appears as a graph displaying the total number of new
offenses over the past 8 hours in 15 minute intervals. The chart differentiates
between policy and security events similar to the Offense Manager.
STRM Users Guide
Offense Manager 19
To customize your display:
• Period of Time - Using the drop-down list box, select the period of time you
wish the Dashboard graph to display.
• Chart Type - You can display the data using a Time Series (default), Line
Chart, or Pie Chart. To change the chart type, click Time Series, Line Chart or
Pie Chart at the top of the graph.
Attackers and
Targets
The Attackers and Targets option displays the top five attackers or top five local
targets. Each target is identified with a magnitude bar to inform you of the
importance of the target. Point your mouse to the IP address to view detailed
information for the IP address.
Categories The Categories option displays the top five categories associated with the highest
number of offenses.
STRM Users Guide
20 USING THE DASHBOARD
Event Viewer The Event Viewer items allow you to monitor and investigate events in real-time.
Event Viewer options include:
• Events Over Time
• Events By Severity
• Top Devices
Note: Hidden or closed events are not included in the values that appear in the
Dashboard.
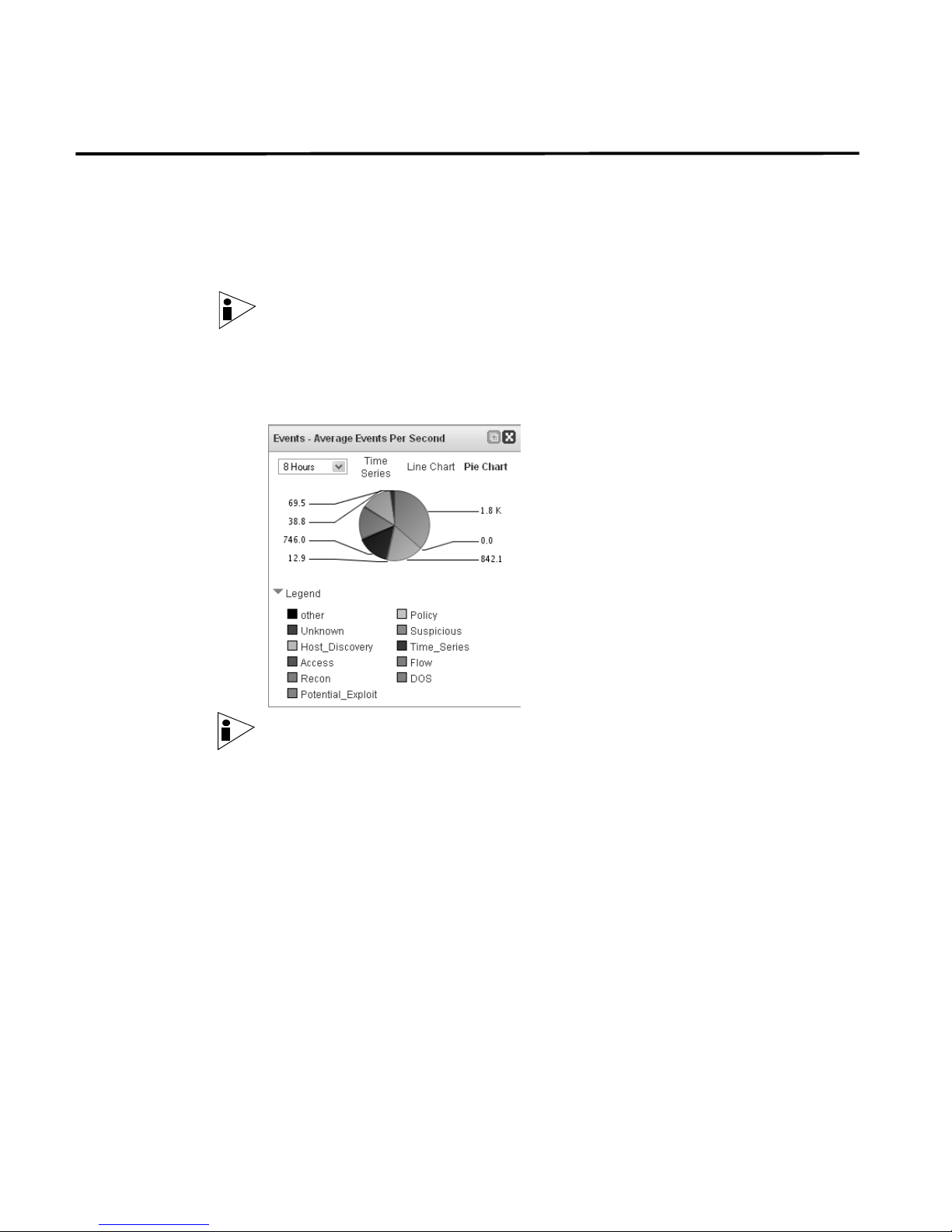
Events Over Time The Events Over Time option displays events received over the last 8 hours in 15
minute intervals, categorized by the event category.
Note: You must have the required permissions to access Event Viewer items.
To customize your display:
• Period of Time - Using the drop-down list box, select the period of time you
wish the Dashboard graph to display.
• Chart Type - You can display the data using a Time Series (default), Line
Chart, or Pie Chart. To change the chart type, click Time Series, Line Chart, or
Pie Chart at the top of the graph.
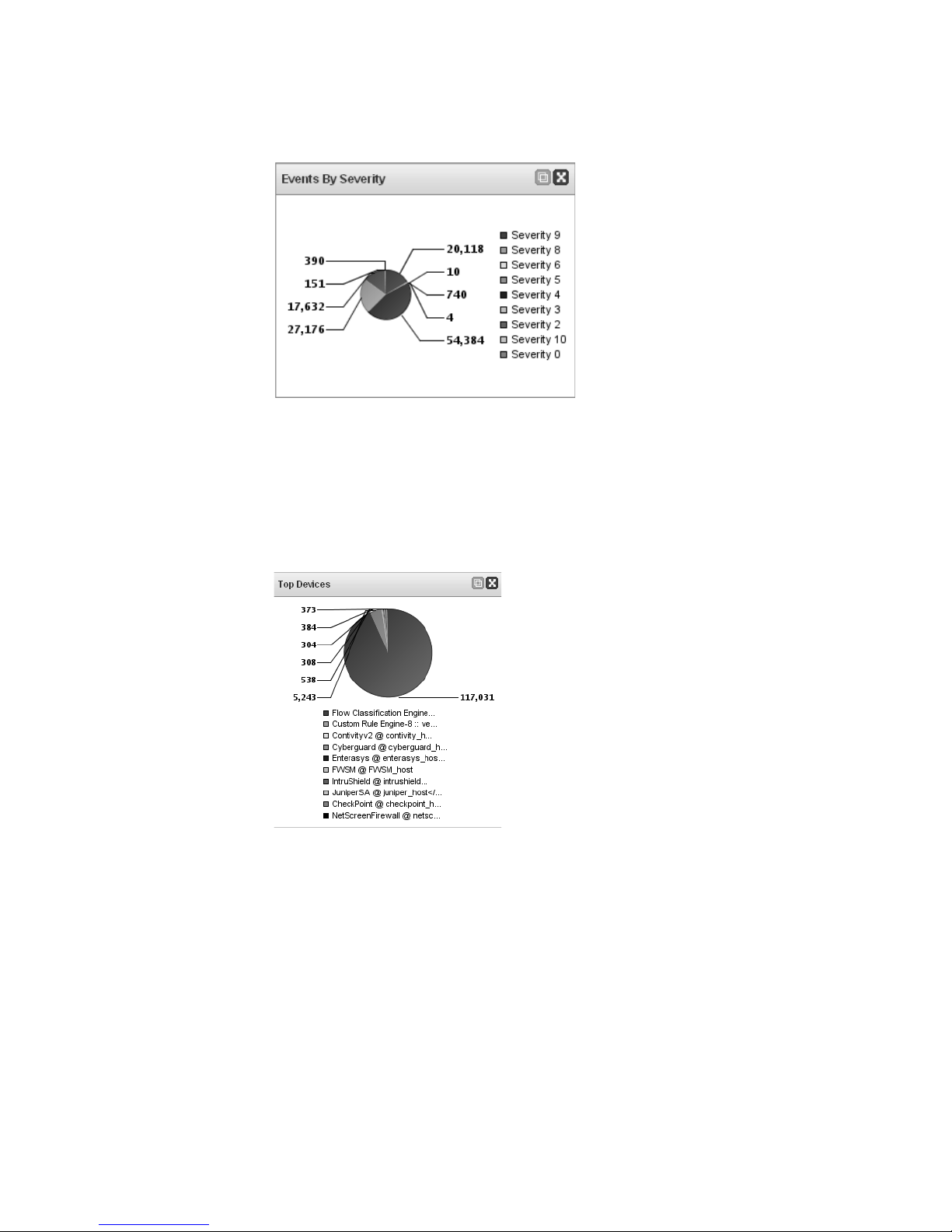
Events By Severity The Events By Severity item displays a pie chart that specifies the number of
active events grouped by severity. This item allows you to see the number of
events that are being received by the level of severity that has been assigned.
Severity indicates the amount of threat an attacker poses in relation to how
prepared the target is for the attack. The range of severity is 0 (low) to 10 (high).
STRM Users Guide
Event Viewer 21
Top Devices The Top Devices item displays a pie chart that specifies the top 10 devices that
sent events to STRM within the last 15 minutes. The number of events sent from
the specified device is indicated in the pie chart. This item allows you to view
potential changes in behavior, for example, if a firewall device that is typically not in
the top 10 list is now contributing to a large percentage of the overall message
count, you should investigate this occurrence.
STRM Users Guide
22 USING THE DASHBOARD
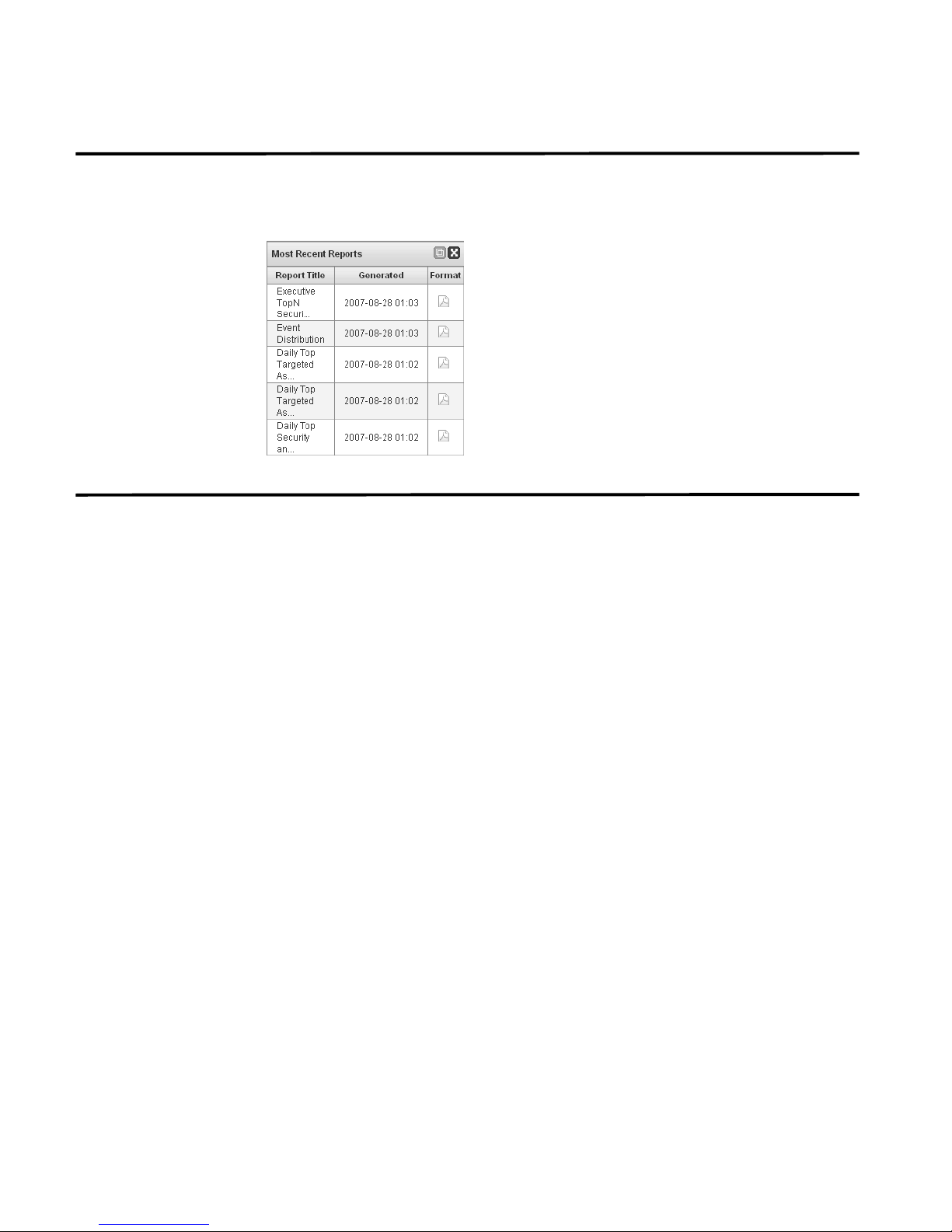
Reports The Reports option allows you to display the top recently generated reports. The
display provides the report title, the time and date the report was generated, and
the format of the report.
Enterprise Security
State
The Enterprise Security State represents your network’s current security posture.
The security state is formulated from monitoring the security data from flows,
external events, and security data to create a single metric that reveals the security
health of your network. The Enterprise Security State is a graphical representation
of the following calculated weighted averages:
• Attacker Threat Posing - The value applied to the threat that an attacker
poses over time.
The magnitudes of all offenses that involved the attacker
during the interval are added together. This value is then added to the value of
the previous interval and stored as the new threat posed by the attacker. STRM
then scales this value based on the maximum threat posing in the database to a
weight value (0 to 10). This value is reported by the Magistrate component and
is calculated each interval.
• Target Threat Under - The value applied to the threat a target is under over
time. For each offense in which the target is involved during the interval, an
average of the offense category is accumulated and added together to obtain a
value. This value is then added to the previous interval value and stored as the
new threat under for the target. STRM then scales this value based on the
maximum threat under in the database to a weight value (0 to 10). This value is
reported by the Magistrate component and is calculated each interval.
• Network Threat Posing - The value applied to the threat a network poses
during a 15 minute interval. This is calculated by summing the threat posing for
all attackers seen on that network during an interval and then calculating an
averaged weighted value (0 to 10). This value is calculated each interval.
• Network Threat Under - The value applied to the threat a network is under
during a 15 minute interval. This is calculated by summing the threat under for
all attackers seen on that network during an interval and then calculating an
averaged weighted value (0 to 10). This value is calculated each interval.
STRM Users Guide

Enterprise Vulnerability State 23
• Vulnerability Risk - The vulnerability risk level (0 to 10) applied to an asset.
This is a weighted value applied by calculating the average of the risks of each
asset in your network.
• Network Weight - The numerical value applied to the importance of each
network. The network weight is user defined.
Enterprise
Vulnerability State
The Enterprise Vulnerability State represents the network’s current vulnerability
posture. The vulnerability state is formulated from monitoring all vulnerability data
across the entire network to create a single metric that reveals the vulnerability
state of your network. For each leaf in your asset map, the vulnerability value is
calculated by averaging the risk level of all hosts in that leaf. Once that value is
obtained, a scaled average (0 to 10) is calculated for that leaf node. This value is
averaged with all other leaf node values in your asset map and one vulnerability
state average is displayed in the Dashboard.
STRM Users Guide
24 USING THE DASHBOARD
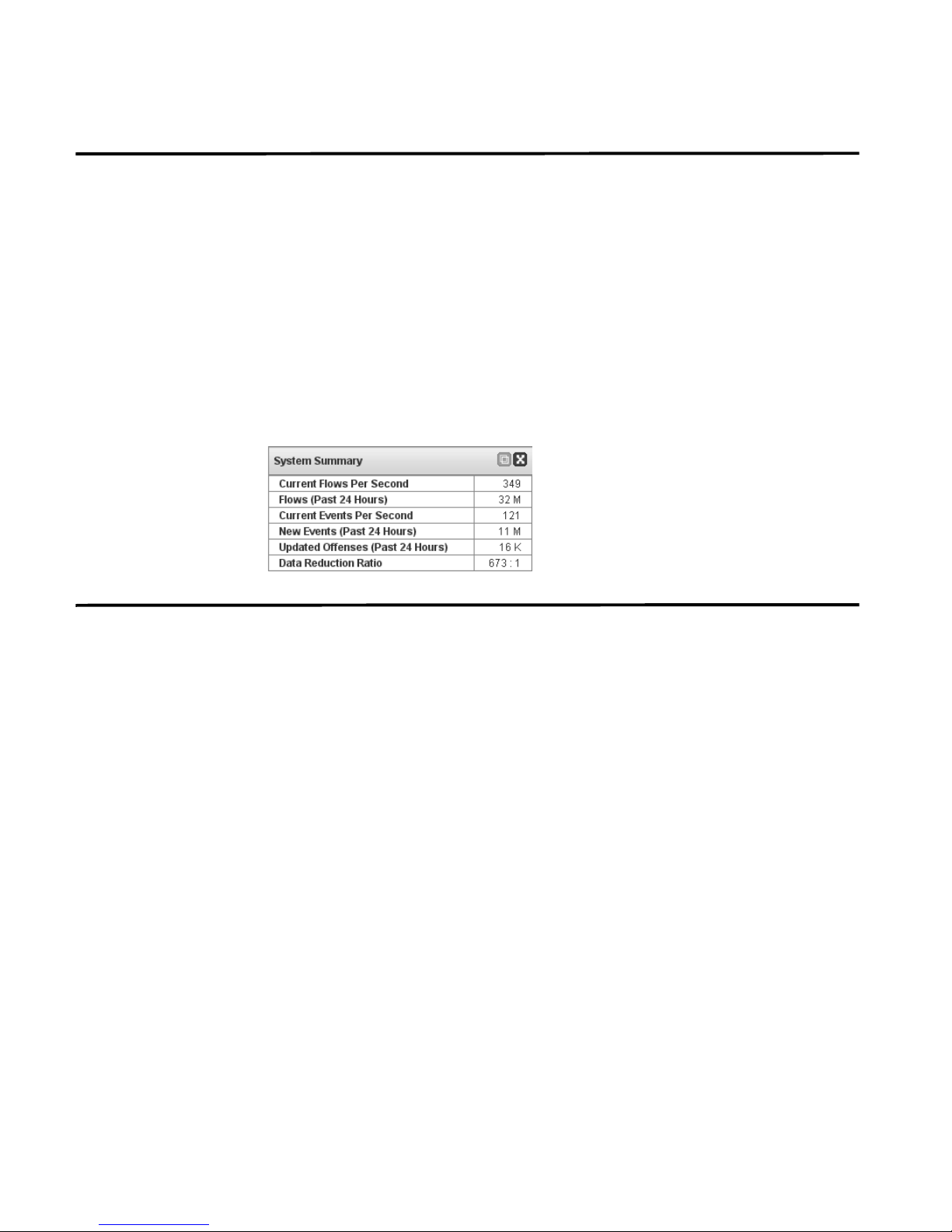
System Summary The Summary item provides a high-level summary of activity within the past 24
hours. Within the summary item, you can view the following information:
• Flows (Past 24 Hours) - Specifies the total number of active flows seen within
the last 24 hours.
• Events (Past 24 Hours) - Specifies the total number of new events received
within the last 24 hours.
• Modified Offenses (Past 24 Hours) - Specifies the total number of offenses
that have been either created or modified with new evidence within the last 24
hours.
• Data Reduction Ratio - Specifies the ratio of data reduced based on the total
events detected within the last 24 hours and the number of modified offenses
within the last 24 hours.
Adding Items You can add multiple displays to the Dashboard interface. To add an item to the
Dashboard:
Step 1 Click the Dashboard tab.
The Dashboard interface appears.
Step 2 From the toolbar, click Add Item.
A list of menu items appears.
Step 3 Navigate through the categories, options include:
• Network Surveillance
• Offense Manager
• Event Viewer
• Reports
• Enterprise Security State
• Enterprise Security State
• Enterprise Vulnerability State
• System Summary
STRM Users Guide
 Loading...
Loading...