Juniper NETWORK AND SECURITY MANAGER 2010.3 - M-SERIES AND MX-SERIES DEVICES GUIDE REV1, NETWORK AND SECURITY MANAGER 2010.3 User Manual
Page 1
Network and Security
Manager
M-series and MX-series Devices Guide
Release
2010.3
Published: 2010-08-18
Revision 1
Copyright © 2010, Juniper Networks, Inc.
Page 2

Juniper Networks, Inc.
1194 North Mathilda Avenue
Sunnyvale, California 94089
USA
408-745-2000
www.juniper.net
This productincludes the Envoy SNMP Engine, developed by Epilogue Technology,an Integrated Systems Company.Copyright ©1986-1997,
Epilogue Technology Corporation. All rights reserved. This program and its documentation were developed at private expense, and no part
of them is in the public domain.
This product includes memory allocation software developed by Mark Moraes, copyright © 1988, 1989, 1993, University of Toronto.
This product includes FreeBSD software developed by the University of California, Berkeley, and its contributors. All of the documentation
and software included in the 4.4BSD and 4.4BSD-Lite Releases is copyrighted by the Regents of the University of California. Copyright ©
1979, 1980, 1983, 1986, 1988, 1989, 1991, 1992, 1993, 1994. The Regents of the University of California. All rights reserved.
GateD software copyright © 1995, the Regents of the University. All rights reserved. Gate Daemon was originated and developed through
release 3.0 by Cornell University and its collaborators. Gated is based on Kirton’s EGP, UC Berkeley’s routing daemon (routed), and DCN’s
HELLO routing protocol. Development of Gated has been supported in part by the National Science Foundation. Portions of the GateD
software copyright © 1988, Regents of the University of California. All rights reserved. Portions of the GateD software copyright © 1991, D.
L. S. Associates.
This product includes software developed by Maker Communications, Inc., copyright © 1996, 1997, Maker Communications, Inc.
Juniper Networks, Junos, Steel-Belted Radius, NetScreen, and ScreenOS are registered trademarks of Juniper Networks, Inc. in the United
States and other countries. The Juniper Networks Logo, the Junos logo, and JunosE are trademarks of Juniper Networks, Inc. All other
trademarks, service marks, registered trademarks, or registered service marks are the property of their respective owners.
Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper Networks reserves the right to change, modify,
transfer, or otherwise revise this publication without notice.
Products made or sold by Juniper Networks or components thereof might be covered by one or more of the following patents that are
owned by or licensed to Juniper Networks: U.S. Patent Nos. 5,473,599, 5,905,725, 5,909,440, 6,192,051, 6,333,650, 6,359,479, 6,406,312,
6,429,706, 6,459,579, 6,493,347, 6,538,518, 6,538,899, 6,552,918, 6,567,902, 6,578,186, and 6,590,785.
Network and Security Manager M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.
All rights reserved. Printed in USA.
Writing: Merisha Wazna and Remya Naroth
Editing: Joanne McClintock
Cover Design: Edmonds Design
Revision History
August 2010—Revision 1
The information in this document is current as of the date listed in the revision history.
Copyright © 2010, Juniper Networks, Inc.ii
Page 3

END USER LICENSE AGREEMENT
READ THIS END USER LICENSE AGREEMENT (“AGREEMENT”) BEFORE DOWNLOADING, INSTALLING, OR USING THE SOFTWARE.
BY DOWNLOADING, INSTALLING, OR USING THE SOFTWARE OR OTHERWISE EXPRESSING YOUR AGREEMENT TO THE TERMS
CONTAINED HEREIN, YOU (AS CUSTOMER OR IF YOU ARE NOT THE CUSTOMER, AS A REPRESENTATIVE/AGENT AUTHORIZED TO
BIND THE CUSTOMER)CONSENT TO BE BOUNDBY THIS AGREEMENT.IF YOUDO NOTOR CANNOT AGREE TO THE TERMS CONTAINED
HEREIN, THEN (A) DO NOT DOWNLOAD, INSTALL, OR USE THE SOFTWARE, AND (B) YOU MAY CONTACT JUNIPER NETWORKS
REGARDING LICENSE TERMS.
1. The Parties. The parties to this Agreement are (i) Juniper Networks, Inc. (if the Customer’s principal office is located in the Americas) or
Juniper Networks (Cayman) Limited (ifthe Customer’sprincipal officeis located outsidethe Americas) (such applicable entitybeing referred
to herein as“Juniper”),and (ii) the person or organization thatoriginally purchased from Juniperor an authorized Juniperreseller the applicable
license(s) for use of the Software (“Customer”) (collectively, the “Parties”).
2. The Software. In this Agreement, “Software” means the program modules and features of the Juniper or Juniper-supplied software, for
which Customer has paid the applicable license or support fees to Juniper or an authorized Juniper reseller, or which was embedded by
Juniper in equipment which Customer purchased from Juniper or an authorized Juniper reseller. “Software” also includes updates, upgrades
and new releases of such software. “Embedded Software” means Software which Juniper has embedded in or loaded onto the Juniper
equipment and any updates, upgrades, additions or replacements which are subsequently embedded in or loaded onto the equipment.
3. License Grant. Subject topayment of the applicablefees and the limitations and restrictions set forth herein, Juniper grants toCustomer
a non-exclusive and non-transferable license, without right to sublicense, to use the Software, in executable form only, subject to the
following use restrictions:
a. Customer shall use Embedded Software solely as embedded in, and for execution on, Juniper equipment originally purchased by
Customer from Juniper or an authorized Juniper reseller.
b. Customer shall use the Software on a single hardware chassis having a single processing unit, or as many chassis or processing units
for which Customer has paid the applicable license fees; provided, however, with respect to the Steel-Belted Radius or Odyssey Access
Client software only, Customer shall use such Software on a single computer containing a single physical random access memory space
and containing any number of processors. Use of the Steel-Belted Radius or IMS AAA software on multiple computers or virtual machines
(e.g., Solaris zones) requires multiple licenses, regardless of whether such computers or virtualizations are physically contained on a single
chassis.
c. Product purchase documents, paper or electronic user documentation, and/or the particular licenses purchased by Customer may
specify limitsto Customer’s useof the Software. Suchlimits may restrictuse to amaximum numberof seats, registered endpoints, concurrent
users, sessions, calls, connections, subscribers, clusters, nodes, realms, devices, links, ports or transactions, or require the purchase of
separate licenses to use particular features, functionalities, services, applications, operations, or capabilities, or provide throughput,
performance, configuration, bandwidth, interface, processing, temporal, or geographical limits. In addition, such limits may restrict the use
of the Software to managing certain kinds of networks or require the Software to be used only in conjunction with other specific Software.
Customer’s use of the Software shall be subject to all such limitations and purchase of all applicable licenses.
d. For any trial copy of the Software, Customer’s right to use the Software expires 30 days after download, installation or use of the
Software. Customer may operate the Software after the 30-day trial period only if Customer pays for a license to do so. Customer may not
extend or create an additional trial period by re-installing the Software after the 30-day trial period.
e. The Global Enterprise Edition of the Steel-Belted Radius software may be used by Customer only to manage access to Customer’s
enterprise network. Specifically, service provider customers are expressly prohibited from using the Global Enterprise Edition of the
Steel-Belted Radius software to support any commercial network access services.
The foregoing license is not transferable or assignable by Customer. No license is granted herein to any user who did not originally purchase
the applicable license(s) for the Software from Juniper or an authorized Juniper reseller.
4. Use Prohibitions. Notwithstanding the foregoing, the license provided herein does not permit the Customer to, and Customer agrees
not to and shall not: (a) modify, unbundle, reverse engineer, or create derivative works based on the Software; (b) make unauthorized
copies of the Software (except as necessary for backup purposes); (c) rent, sell, transfer, or grant any rights in and to any copy of the
Software,in any form, toany thirdparty; (d)remove any proprietarynotices, labels,or marks on orin any copy of the Softwareor any product
in which the Software is embedded; (e) distribute any copy of the Software to any third party, including as may be embedded in Juniper
equipment sold inthe secondhand market; (f)use any ‘locked’ orkey-restricted feature,function, service, application, operation, orcapability
without first purchasing the applicable license(s) and obtaining a valid key from Juniper, even if such feature, function, service, application,
operation, or capability is enabled without a key; (g) distribute any key for the Software provided by Juniper to any third party; (h) use the
iiiCopyright © 2010, Juniper Networks, Inc.
Page 4

Software in any manner that extends or is broader than the uses purchased by Customer from Juniper or an authorized Juniper reseller; (i)
use Embedded Software on non-Juniper equipment; (j) use Embedded Software (or make it available for use) on Juniper equipment that
the Customer did not originally purchase from Juniper or an authorized Juniper reseller; (k) disclose the results of testing or benchmarking
of the Software to any third party without the prior written consent of Juniper; or (l) use the Software in any manner other than as expressly
provided herein.
5. Audit. Customer shall maintain accurate records as necessary to verify compliance with this Agreement. Upon request by Juniper,
Customer shall furnish such records to Juniper and certify its compliance with this Agreement.
6. Confidentiality. The Parties agree that aspects of the Software and associated documentation are the confidential property of Juniper.
As such, Customer shall exercise all reasonable commercial efforts to maintain the Software and associated documentation in confidence,
which at a minimum includes restricting access to the Software to Customer employees and contractors having a need to use the Software
for Customer’s internal business purposes.
7. Ownership. Juniper and Juniper’s licensors, respectively, retain ownership of all right, title, and interest (including copyright) in and to
the Software, associated documentation, and all copies of the Software. Nothing in this Agreement constitutes a transfer or conveyance
of any right, title, or interest in the Software or associated documentation, or a sale of the Software, associated documentation, or copies
of the Software.
8. Warranty, Limitation of Liability, Disclaimer of Warranty. The warranty applicable to the Software shall be as set forth in the warranty
statementthat accompaniesthe Software (the“Warranty Statement”).Nothing inthis Agreement shallgive riseto any obligation to support
the Software. Support services may be purchased separately. Any such support shall be governed by a separate, written support services
agreement. TO THE MAXIMUM EXTENT PERMITTED BY LAW, JUNIPER SHALL NOT BE LIABLE FOR ANY LOST PROFITS, LOSS OF DATA,
OR COSTSOR PROCUREMENTOF SUBSTITUTEGOODS ORSERVICES,OR FOR ANY SPECIAL,INDIRECT,OR CONSEQUENTIALDAMAGES
ARISING OUTOF THIS AGREEMENT,THE SOFTWARE,OR ANY JUNIPEROR JUNIPER-SUPPLIEDSOFTWARE. INNO EVENT SHALLJUNIPER
BE LIABLE FOR DAMAGES ARISING FROM UNAUTHORIZED OR IMPROPER USE OF ANY JUNIPER OR JUNIPER-SUPPLIED SOFTWARE.
EXCEPT AS EXPRESSLY PROVIDED IN THE WARRANTY STATEMENT TO THE EXTENT PERMITTED BY LAW, JUNIPER DISCLAIMS ANY
AND ALL WARRANTIES IN AND TO THE SOFTWARE (WHETHER EXPRESS, IMPLIED, STATUTORY, OR OTHERWISE), INCLUDING ANY
IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE, OR NONINFRINGEMENT. IN NO EVENT DOES
JUNIPER WARRANT THAT THE SOFTWARE, OR ANY EQUIPMENT OR NETWORK RUNNING THE SOFTWARE, WILL OPERATE WITHOUT
ERROR OR INTERRUPTION, OR WILL BE FREE OF VULNERABILITY TO INTRUSION OR ATTACK. In no event shall Juniper’s or its suppliers’
or licensors’ liability to Customer, whether in contract, tort (including negligence), breach of warranty, or otherwise, exceed the price paid
by Customer for the Software that gave rise to the claim, or if the Software is embedded in another Juniper product, the price paid by
Customer for such other product. Customer acknowledges and agrees that Juniper has set its prices and entered into this Agreement in
reliance upon the disclaimers of warranty and the limitations of liability set forth herein, that the same reflect an allocation of risk between
the Parties (including the risk that a contract remedy may fail of its essential purpose and cause consequential loss), and that the same
form an essential basis of the bargain between the Parties.
9. Termination. Any breach of this Agreement or failure by Customer to pay any applicable fees due shall result in automatic termination
of the license granted herein. Upon such termination, Customer shall destroy or return to Juniper all copies of the Software and related
documentation in Customer’s possession or control.
10. Taxes. All license fees payable under this agreement are exclusive of tax. Customer shall be responsible for paying Taxes arising from
the purchase of the license, or importation or use of the Software. If applicable, valid exemption documentation for each taxing jurisdiction
shall be provided to Juniper prior to invoicing, and Customer shall promptly notify Juniper if their exemption is revoked or modified. All
payments made by Customer shall be net of any applicable withholding tax. Customer will provide reasonable assistance to Juniper in
connection with such withholding taxes by promptly: providing Juniper with valid tax receipts and other required documentation showing
Customer’s payment of any withholding taxes; completing appropriate applications that would reduce the amount of withholding tax to
be paid; and notifying and assisting Juniper in any audit or tax proceeding related to transactions hereunder. Customer shall comply with
all applicable tax laws and regulations, and Customer will promptly pay or reimburse Juniper for all costs and damages related to any
liability incurred by Juniper as a result of Customer’s non-compliance or delay with its responsibilities herein. Customer’s obligations under
this Section shall survive termination or expiration of this Agreement.
11. Export. Customer agrees to comply with all applicable export laws and restrictions and regulations of any United States and any
applicable foreign agency or authority, and not to export or re-export the Software or any direct product thereof in violation of any such
restrictions, laws or regulations, or without all necessary approvals. Customer shall be liable for any such violations. The version of the
Software supplied to Customer may contain encryption or other capabilities restricting Customer’s ability to export the Software without
an export license.
Copyright © 2010, Juniper Networks, Inc.iv
Page 5

12. Commercial Computer Software. The Software is “commercial computer software” and is provided with restricted rights. Use,
duplication, or disclosure by the United States government is subject to restrictions set forth in this Agreement and as provided in DFARS
227.7201 through 227.7202-4, FAR 12.212, FAR 27.405(b)(2), FAR 52.227-19, or FAR 52.227-14(ALT III) as applicable.
13. Interface Information. To the extent required by applicable law, and at Customer's written request, Juniper shall provide Customer
with the interface information needed to achieve interoperability between the Software and another independently created program, on
payment of applicable fee, if any. Customer shall observe strict obligations of confidentiality with respect to such information and shall use
such information in compliance with any applicable terms and conditions upon which Juniper makes such information available.
14. Third Party Software. Any licensor of Juniper whose software is embedded in the Softwareand any supplier of Juniper whose products
or technology are embedded in (or services are accessed by) the Software shall be a third party beneficiary with respect to this Agreement,
and such licensor or vendor shall have the right to enforce this Agreement in itsown name asif it were Juniper. In addition, certain third party
software may be provided with the Software and is subject to the accompanying license(s), if any, of its respective owner(s). To the extent
portions of the Software are distributed under and subject to open source licenses obligating Juniper to make the source code for such
portions publicly available (such as the GNU General Public License (“GPL”) or the GNU Library General Public License (“LGPL”)), Juniper
will make such source code portions (including Juniper modifications, as appropriate) available upon request for a period of up to three
years from the date of distribution. Such request can be made in writing to Juniper Networks, Inc., 1194 N. Mathilda Ave., Sunnyvale, CA
94089, ATTN: General Counsel. You may obtain a copy of the GPL at http://www.gnu.org/licenses/gpl.html, and a copy of the LGPL
at http://www.gnu.org/licenses/lgpl.html .
15. Miscellaneous. This Agreement shall be governed by the laws of the State of California without reference to its conflicts of laws
principles. The provisions of the U.N. Convention for the International Sale of Goods shall not apply to this Agreement. For any disputes
arising under this Agreement, the Parties hereby consent to the personal and exclusive jurisdiction of, and venue in, the state and federal
courts within Santa Clara County, California. This Agreement constitutes the entire and sole agreement between Juniper and the Customer
with respect to the Software, and supersedes all prior and contemporaneous agreements relating to the Software, whether oral or written
(including any inconsistent terms contained in a purchase order), except that the terms of a separate written agreement executed by an
authorized Juniper representative and Customer shall govern to the extent such terms are inconsistent or conflict with terms contained
herein. No modification to this Agreement nor any waiver of any rights hereunder shall be effective unless expressly assented to in writing
by the party to be charged. If any portion of this Agreement is held invalid, the Parties agree that such invalidity shall not affect the validity
of the remainder of this Agreement. This Agreement and associated documentation has been written in the English language, and the
Parties agree that the English version will govern. (For Canada: Les parties aux présentés confirment leur volonté que cette convention de
même que tous les documents y compris tout avis qui s'y rattaché, soient redigés en langue anglaise. (Translation: The parties confirm that
this Agreement and all related documentation is and will be in the English language)).
vCopyright © 2010, Juniper Networks, Inc.
Page 6

Copyright © 2010, Juniper Networks, Inc.vi
Page 7

Table of Contents
About This Guide . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxvii
Objectives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxvii
Audience . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxvii
Documentation Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxvii
Documentation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxix
Requesting Technical Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxx
Self-Help Online Tools and Resources . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxxi
Opening a Case with JTAC . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxxi
Part 1 Getting Started
Chapter 1 Getting Started with NSM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
Introduction to Network and Security Manager . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
Installing NSM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
Role-Based Administration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4
Chapter 2 Understanding the JUNOS CLI and NSM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
NSM and Device Management Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
Understanding the CLI and NSM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
Comparing the CLI To the NSM UI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7
NSM Services Supported for M-series and MX-series Devices . . . . . . . . . . . . . . . . 10
How NSM Works with the CLI and Distributed Data Collection . . . . . . . . . . . . . . . . 11
Device Schemas . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12
Communication Between a Device and NSM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
Chapter 3 Before You Begin Adding M-series and MX-series Devices . . . . . . . . . . . . . . 15
M-series and MX-series Devices Supported by NSM . . . . . . . . . . . . . . . . . . . . . . . 15
Considering the Device Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
Configuring a Deployed M-series or MX-series Device for Importing to NSM . . . . 16
Configure an IP Address and a User with Full Administrative Privileges for
the Device . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
Check Network Connectivity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
Check Connectivity to the NSM Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
Configure a Static Route to the NSM Server . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
Establish a Telnet or an SSHv2, and a NETCONF protocol over SSH
Connection to the NSM Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
Part 2 Integrating M-series and MX-series Devices
Chapter 4 Adding M-series and MX-series Devices Overview . . . . . . . . . . . . . . . . . . . . . 23
About Device Creation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
Supported Add Device Workflows for M-series and MX-series Devices . . . . . . . . 24
viiCopyright © 2010, Juniper Networks, Inc.
Page 8

M-series and MX-series Devices
Chapter 5 Updating M-series and MX-series Devices Overview . . . . . . . . . . . . . . . . . . . 29
Part 3 Configuring M-series and MX-series Devices
Chapter 6 Configuring M-series and MX-series Devices Overview . . . . . . . . . . . . . . . . . 41
Chapter 7 Configuring Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 47
Importing Devices Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
Modeling Devices Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
Adding Multiple Devices Using Automatic Discovery (JUNOS Software Devices
Only) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27
Adding Device Groups Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27
About Updating M-series and MX-series Devices . . . . . . . . . . . . . . . . . . . . . . . . . 29
How the Update Process Works . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
Job Manager . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
Tracking Updated Devices Using Job Manager . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
Reviewing Job Information Displayed in Job Manager . . . . . . . . . . . . . . . . . . . . . . 33
Device States Displayed in Job Manager During Update . . . . . . . . . . . . . . . . . . . . 34
Understanding Updating Errors Displayed in the Job Manager . . . . . . . . . . . . . . . 35
About Device Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41
M-series and MX-series Device Configuration Settings Supported in NSM . . . . . . 42
Configuring Device Features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44
Example: Configuration of Interfaces for MPLS in the CLI and NSM . . . . . . . . . . . 45
Configuring Address-Assignment Pools (NSM Procedure) . . . . . . . . . . . . . . . . . . 47
Configuring Access Address Pools (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 50
Configuring Access Group Profile (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 51
Configuring the LDAP Options (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . 52
Configuring the LDAP Server (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
Configuring Access Profiles for L2TP or PPP Parameters (NSM Procedure) . . . . 54
Configuring Access Profile (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 55
Configuring Accounting Parameters for Access Profiles (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 55
Configuring the Accounting Order (NSM Procedure) . . . . . . . . . . . . . . . . . . . 56
Configuring the Authentication Order (NSM Procedure) . . . . . . . . . . . . . . . . 57
Configuring the Authorization Order (NSM Procedure) . . . . . . . . . . . . . . . . . . 57
Configuring the L2TP Client (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 58
Configuring the Client Filter Name (NSM Procedure) . . . . . . . . . . . . . . . . . . . 59
Configuring the LDAP Options (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 60
Configuring the LDAP Server (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 61
Configuring the Provisioning Order (NSM Procedure) . . . . . . . . . . . . . . . . . . . 62
Configuring RADIUS Parameters for AAA Subscriber Management (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63
Configuring the RADIUS Parameters (NSM Procedure) . . . . . . . . . . . . . . . . . 66
Configuring the RADIUS for Subscriber Access Management, L2TP, or PPP
(NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67
Configuring Session Limit (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . 67
Configuring the RADIUSfor SubscriberAccessManagement, L2TP,or PPP(NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 68
Configuring the SecurID Server (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 69
Copyright © 2010, Juniper Networks, Inc.viii
Page 9

Table of Contents
Configuring the Access Profile (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . 70
Chapter 8 Configuring Accounting Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 71
Configuring Accounting Options (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 71
Configuring Class Usage Profiles (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 71
Configuring a Log File (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
Configuring the Filter Profile (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 73
Configuring the Interface Profile (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 74
Configuring the Policy Decision Statistics Profile (NSM Procedure) . . . . . . . . 75
Configuring the MIB Profile (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 76
Configuring the Routing Engine Profile (NSM Procedure) . . . . . . . . . . . . . . . . 77
Chapter 9 Configuring Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 79
Configuring the Application and Application Set (NSM Procedure) . . . . . . . . . . . 79
Chapter 10 Configuring Bridge Domains . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 81
Configuring Bridge Domains Properties (NSM Procedure) . . . . . . . . . . . . . . . . . . . 81
Configuring a Bridge Domain (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 81
Configuring Layer 2Learning and ForwardingProperties for aBridge Domain
(NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 82
Configuring Forwarding Options (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 84
Configuring Logical Interfaces (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 85
Configuring Multicast Snooping Options (NSM Procedure) . . . . . . . . . . . . . . 86
Configuring IGMP Snooping (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 89
Configuring VLAN ID (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 94
Chapter 11 Configuring Chassis . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 97
Configuring Aggregated Devices (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 97
Configuring Chassis Alarms (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 98
Configuring Container Interfaces (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 99
Configuring Chassis FPC (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 100
Configuring a T640 Router on a Routing Matrix (NSM Procedure) . . . . . . . . . . . 105
Configuring Routing Engine Redundancy (NSM Procedure) . . . . . . . . . . . . . . . . . 110
Configuring a Routing Engine to Reboot or Halt on Hard Disk Errors (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 111
Chapter 12 Configuring Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 113
Configuring RADIUS Authentication (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 113
Configuring TACACS+ Authentication (NSM Procedure) . . . . . . . . . . . . . . . . . . . 114
Configuring Authentication Order (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . 115
Configuring User Access (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 116
Configuring Login Classes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 116
Configuring User Accounts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 117
Configuring Template Accounts (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 117
Creating a Remote Template Account . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 118
Creating a Local Template Account . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 119
Chapter 13 Configuring Class of Service Features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 121
Configuring CoS Classifiers (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 122
Configuring CoS Code Point Aliases (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 124
Configuring CoS Drop Profile (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . 125
ixCopyright © 2010, Juniper Networks, Inc.
Page 10

M-series and MX-series Devices
Chapter 14 Configuring Event Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 151
Chapter 15 Configuring Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 159
Chapter 16 Configuring Forwarding Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 183
Configuring CoS Forwarding Classes (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 127
Configuring CoS Forwarding Policy (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 129
Configuring CoS Fragmentation Maps (NSM Procedure) . . . . . . . . . . . . . . . . . . . 130
Configuring CoS Host Outbound Traffic (NSM Procedure) . . . . . . . . . . . . . . . . . . 131
Configuring CoS Interfaces (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 132
Configuring CoS Routing Instances (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 138
Configuring CoS Schedulers (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . 139
Configuring CoS and Applying Scheduler Maps (NSM Procedure) . . . . . . . . . . . . 141
Configuring CoS Restricted Queues (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 142
Configuring Tracing Operations (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 143
Configuring CoS Traffic Control Profiles (NSM Procedure) . . . . . . . . . . . . . . . . . 144
Configuring CoS Translation Table (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 145
Configuring Destinations for File Archiving (NSM Procedure) . . . . . . . . . . . . . . . . 151
Configuring Event Script (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 152
Generating Internal Events (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 154
Configuring Event Policy (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 154
Configuring Event Policy Tracing Operations (NSM Procedure) . . . . . . . . . . . . . . 157
Configuring the Firewall Filter for Any Family Type (NSM Procedure) . . . . . . . . . 159
Configuring the Firewall Filter for Bridge Family Type (NSM Procedure) . . . . . . . 161
Configuring the Firewall Filter for Ccc Family Type (NSM Procedure) . . . . . . . . . 163
Configuring Filters for inet Family Type (NSM Procedure) . . . . . . . . . . . . . . . . . . 165
Configuring Firewall Filter for inet Family Type (NSM Procedure) . . . . . . . . . 165
Configuring Prefix-specific Actions (NSM Procedure) . . . . . . . . . . . . . . . . . . 167
Configuring Service Filters (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 168
Configuring Simple Filters (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 169
Configuring Filters for inet6 Family Type (NSM Procedure) . . . . . . . . . . . . . . . . . 170
Configuring Firewall Filter for inet6 Family Type (NSM Procedure) . . . . . . . . 171
Configuring Service Filters for inet6 (NSM Procedure) . . . . . . . . . . . . . . . . . . 173
Configuring the Firewall Filter for MPLS Family Type (NSM Procedure) . . . . . . . 174
Configuring the Firewall Filter for VPLS Family Type (NSM Procedure) . . . . . . . . 177
Configuring a Policer for a Firewall Filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 180
Configuring Accounting Options (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . 183
Configuring the Extended DHCP Agent (NSM Procedure) . . . . . . . . . . . . . . . . . . 185
Configuring Authentication Support for the DHCP Relay Agent (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 185
Configuring Group (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 186
Overriding the Default Configuration Settings for the Extended DHCP Relay
Agent (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 187
Configuring Relay Option 60 Information for Forwarding Client Traffic to
Specific DHCP Servers (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 189
Configuring Relay Option 82 for a DHCP Server (NSM Procedure) . . . . . . . 190
Specifying the Name of a Group of DHCP Server Addresses for Use by the
Extended DHCP Relay Agent (NSM Procedure) . . . . . . . . . . . . . . . . . . . 191
Copyright © 2010, Juniper Networks, Inc.x
Page 11

Table of Contents
Configuring Operations for Extended DHCP Relay Agent Processes (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 192
Specifying Address Family for Filters (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 193
Configuring Load Balancing Using Hash Key (NSM Procedure) . . . . . . . . . . . . . . 194
Configuring Helpers (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 195
Configuring a Router or Interface to Act as a Bootstrap Protocol Relay
Agent . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 196
Enabling DNS Request Packet Forwarding . . . . . . . . . . . . . . . . . . . . . . . . . . 199
Configuring a Port for a DHCP or BOOTP Relay Agent . . . . . . . . . . . . . . . . . 201
Configuring Tracing Operations for BOOTP, DNS, and TFTP Packet
Forwarding . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 202
Configuring Per-Flow and Per-Prefix Load Balancing (NSM Procedure) . . . . . . 203
Configuring Port Mirroring (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 204
Chapter 17 Configuring Interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 207
Configuring Interfaces on the Routing Platform (NSM Procedure) . . . . . . . . . . . 207
Configuring Interface Properties (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 207
Damping Interface Transitions (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 208
Configuring Receive Bucket Properties on Interfaces (NSM Procedure) . . . 209
Configuring Tracing Operations of an Individual Router Interface (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 210
Configuring Transmit Leaky Bucket Properties (NSM Procedure) . . . . . . . . . 211
Configuring Logical Interface Properties (NSM Procedure) . . . . . . . . . . . . . . 212
Configuring Logical Unit Properties (NSM Procedure) . . . . . . . . . . . . . . 212
Configuring an IP Demux Underlying Interface (NSM Procedure) . . . . . 213
Configuring the Logical Demux Source Family Type on the IP Demux
Underlying Interface (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 214
Configuring Epd Threshold for the Logical Interface (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 214
Configuring Protocol Family Information for the Logical Interface (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 215
Configuring Protocol Family (Ccc) Information for the Logical Interface
(NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 215
Configuring Protocol Family (Inet) Information for the Logical Interface
(NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 217
Configuring Protocol Family (Inet6)Information for the Logical Interface
(NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 223
Configuring Protocol Family (ISO) Information for the Logical Interface
(NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 229
Configuring Protocol Family (MPLS) Information for the Logical Interface
(NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 230
Configuring Protocol Family (TCC) Information for the Logical Interface
(NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 232
Configuring the Traffic Shaping Profile (NSM Procedure) . . . . . . . . . . . . . . . 232
Configuring Interface set on the Routing Platform (NSM Procedure) . . . . . . . . . 234
Configuring Trace Options on the Routing Platform (NSM Procedure) . . . . . . . . 235
Chapter 18 Configuring Multicast Snooping Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . 237
Configuring Multicast Snooping Options (NSM Procedure) . . . . . . . . . . . . . . . . . 237
xiCopyright © 2010, Juniper Networks, Inc.
Page 12

M-series and MX-series Devices
Chapter 19 Configuring Policy Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 241
Chapter 20 Configuring Protocols . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 251
Configuring an AS Path in a BGP Routing Policy (NSM Procedure) . . . . . . . . . . . 241
Configuring an AS Path Group in a BGP Routing Policy (NSM Procedure) . . . . . 242
Configuring a Community for use in BGP Routing Policy Conditions(NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 243
Configuring a BGP Export Policy Condition (NSM Procedure) . . . . . . . . . . . . . . . 244
Configuring Flap Dampingto Reduce the Number of BGP UpdateMessages(NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 245
Configuring a Routing Policy Statement (NSM Procedure) . . . . . . . . . . . . . . . . . 247
Configuring Prefix List (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 248
Configuring the BFD Protocol (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . 251
Configuring BGP (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 252
Configuring the ILMI Protocol (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 255
Configuring Layer 2 Address Learning and Forwarding Properties (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 256
Configuring Layer 2 Circuit (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 257
Configuring Local Interface Switching (NSM Procedure) . . . . . . . . . . . . . . . 257
Configuring the Neighbor Interface for the Layer 2 Circuit (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 258
Tracing Layer 2 Circuit Creation and Changes (NSM Procedure) . . . . . . . . . 261
Configuring Layer 2 Protocol Tunneling and BPDU Protection (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 262
Configuring Label Distribution Protocol (NSM Procedure) . . . . . . . . . . . . . . . . . 264
Configuring Link Management Protocol (NSM Procedure) . . . . . . . . . . . . . . . . . 275
Configuring MPLS Protocol (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . 279
Enabling MPLS on the Router (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 279
Configuring Administrative Group (NSM Procedure) . . . . . . . . . . . . . . . . . . 282
Configuring Administrative Groups (NSM Procedure) . . . . . . . . . . . . . . . . . 282
Configuring Bandwidth for the Reroute Path (NSM Procedure) . . . . . . . . . . 283
Configuring DiffServ-Aware Traffic Engineering (NSM Procedure) . . . . . . . 284
Configuring MPLS on Interfaces (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 285
Configure a Label Switched Path (LSP) to Use in Dynamic MPLS . . . . . . . . 287
Configuring Label Switched Path (NSM Procedure) . . . . . . . . . . . . . . . 287
Configuring Administrative Group (NSM Procedure) . . . . . . . . . . . . . . . 290
Configuring Automatic Bandwidth Allocation for LSPs (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 291
Configuring Bandwidth for the Reroute Path (NSM Procedure) . . . . . . 292
Configuring Fast Reroute (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 293
Adding LSP-Related Routes to the inet.3 Routing Table (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 294
Configuring MPLS LSPs for GMPLS (NSM Procedure) . . . . . . . . . . . . . 295
Configuring BFD for MPLS IPv4 LSPs (NSM Procedure) . . . . . . . . . . . . 296
Configuring the Primary Point-to-Multipoint LSP (NSM Procedure) . . 298
Configuring Policers for LSPs (NSM Procedure) . . . . . . . . . . . . . . . . . . 299
Configuring Primary Paths for an LSP (NSM Procedure) . . . . . . . . . . . 300
Configuring Secondary Paths for an LSP (NSM Procedure) . . . . . . . . . 305
Copyright © 2010, Juniper Networks, Inc.xii
Page 13

Table of Contents
Configuring System Log Messages and SNMP Traps for LSPs (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 313
Configuring BFD for MPLS IPv4 LSPs (NSM Procedure) . . . . . . . . . . . . . . . . 314
Configuring Named Paths (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 316
Configuring MTU Signaling in RSVPs (NSM Procedure) . . . . . . . . . . . . . . . . 317
Configuring static LSPs on the Ingress Router (NSM Procedure) . . . . . . . . . 318
Configuring MPLS Statistics (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . 319
Tracing MPLS Packets and Operations (NSM Procedure) . . . . . . . . . . . . . . 320
Configuring MSDP Protocol (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . 321
Configuring MSDP on the Router (NSM Procedure) . . . . . . . . . . . . . . . . . . . 321
Configuring the MSDP Active Source Limit (NSM Procedure) . . . . . . . . . . . 322
Configuring Export Policy (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 323
Configuring MSDP Peer Group . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 324
Configuring MSDP Peer Group (NSM Procedure) . . . . . . . . . . . . . . . . . 324
Configuring MSDP Peers (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 325
Configuring a Routing Table Group with MSDP (NSM Procedure) . . . . 327
Configuring Per-Source Active Source Limit (NSM Procedure) . . . . . . . 328
Configuring MSDP Traceoptions (NSM Procedure) . . . . . . . . . . . . . . . . 328
Configuring MSTP (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 329
Configuring OSPF (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 331
Configuring RIP (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 335
Configuring RIPng Protocol (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . 337
Configuring RIPng on the Router (NSM Procedure) . . . . . . . . . . . . . . . . . . . 337
Configuring Graceful Restart for RIPng (NSM Procedure) . . . . . . . . . . . . . . 338
Configuring Group . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 339
Configuring Group-Specific RIPng Properties (NSM Procedure) . . . . . 339
Applying Policies to Routes Exported by RIPng (NSM Procedure) . . . . . 341
Applying Policies to Routes Imported by RIPng (NSM Procedure) . . . . 341
Configuring RIPng Neighbor Properties . . . . . . . . . . . . . . . . . . . . . . . . . 342
Enable or Disable Receiving of Update Messages (NSM Procedure) . . . . . . 345
Configuring RIPng Send Update Messages (NSM Procedure) . . . . . . . . . . . 345
Configuring RIPng Traceoptions (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 346
Configuring Router Advertisement (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 347
Configuring ICMP Router Discovery (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 350
Configuring RSVP (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 351
Configuring VRRP (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 358
Configuring VSTP (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 359
Chapter 21 Configuring Routing Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 361
Configuring Confederation (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 362
Configuring Dynamic Tunnels (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 363
Configuring Fate Sharing (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 364
Configuring Flow Route (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 366
Configuring Forwarding Table (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 368
Configuring Generated Routes (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 369
Configuring Instance Export (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . 370
Configuring Instance Import (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . 371
Configuring Interface Routes (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . 372
Configuring Martian Addresses (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 373
xiiiCopyright © 2010, Juniper Networks, Inc.
Page 14

M-series and MX-series Devices
Chapter 22 Configuring Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 389
Chapter 23 Configuring Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 391
Configuring Maximum Paths (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . 374
Configuring Maximum Prefixes (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 375
Configuring Multicast (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 377
Configuring Options (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 380
Configuring Routing Tables (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . 381
Configuring Routing Table Groups (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 383
Configuring Source Routing (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . 384
Configuring Static Routes (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 385
Configuring Topologies (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 386
Configuring Traceoptions (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 387
Configuring Authentication Key Updates (NSM Procedure) . . . . . . . . . . . . . . . . 389
Configuring Adaptive Services PICs (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 391
Configuring Border Signaling Gateways (NSM Procedure) . . . . . . . . . . . . . . . . . 392
Configuring Gateway Properties (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 392
Configuring Gateway (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 393
Configuring an Admission Controller (NSM Procedure) . . . . . . . . . . . . 393
Configuring Session Policy Decision Function (NSM Procedure) . . . . . 394
Configuring Service Point (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 396
Configuring SIP Policies and Timers (NSM Procedure) . . . . . . . . . . . . . 397
Configuring Traceoptions (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 407
Configuring Class of Service (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . 412
Configuring Intrusion Detection Service (NSM Procedure) . . . . . . . . . . . . . . . . . . 415
Tracing Services PIC Operations (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . 419
Configuring Network Address Translation (NSM Procedure) . . . . . . . . . . . . . . . 420
Configuring PGCP (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 425
Configuring Gateway (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 426
Configuring a Virtual Border Gateway Function on the Router (NSM
Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 426
Configuring Data Inactivity Detection (NSM Procedure) . . . . . . . . . . . . 427
Configuring Gateway Controller (NSM Procedure) . . . . . . . . . . . . . . . . 428
Configuring Graceful Restart (NSM Procedure) . . . . . . . . . . . . . . . . . . . 429
Configuring H248 Options Properties (NSM Procedure) . . . . . . . . . . . . . . . 430
Configuring H248 Options (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 430
Changing Encoding Defaults (NSM Procedure) . . . . . . . . . . . . . . . . . . . 431
Configuring Service Change (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 431
Configuring H248 Properties (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 436
Configuring Application Data Inactivity Detection (NSM Procedure) . . 437
Configuring Base Root (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 437
Configuring Differentiated Services (NSM Procedure) . . . . . . . . . . . . . 440
Configuring Event Timestamp Notification (NSM Procedure) . . . . . . . . 441
Hanging Termination Detection (NSM Procedure) . . . . . . . . . . . . . . . . . 441
Configuring Inactivity Timer (NSM Procedure) . . . . . . . . . . . . . . . . . . . 442
Configuring Notification Behavior (NSM Procedure) . . . . . . . . . . . . . . . 443
Configuring Segmentation (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 444
Copyright © 2010, Juniper Networks, Inc.xiv
Page 15

Table of Contents
Configuring Traffic Management (NSM Procedure) . . . . . . . . . . . . . . . 445
Configuring H248 Timers (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 447
Configuring the Monitor (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . 448
Configuring Overload Control (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 449
Configuring Session Mirroring (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . 450
Configuring Media Service (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . 450
Configuring a Rule (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 451
Configuring Rule Set (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 452
Configuring Session Mirroring (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 452
Configuring Traceoptions (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 453
Configuring Virtual Interface (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 454
Configuring Service Interface Pools (NSM Procedure) . . . . . . . . . . . . . . . . . . . . 455
Configuring a Service Set (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 456
Configuring Stateful Firewall (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . 460
Chapter 24 Configuring SNMP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 463
Configuring Basic System Identification for SNMP (NSM Procedure) . . . . . . . . 463
Configuring SNMP Communities (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . 464
Configuring SNMP Trap Groups (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . 466
Configuring SNMP Views (NSM Procedure) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 467
Part 4 Managing M-series and MX-series Devices
Chapter 25 Managing M-series and MX-series Devices Overview . . . . . . . . . . . . . . . . . . 471
Managing M-series and MX-series Device Software Versions . . . . . . . . . . . . . . . 471
Chapter 26 Viewing the M-series and MX-series Device Inventory in NSM and the
CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 473
Viewing and Reconciling Device Inventory . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 473
Comparing Device Inventory in NSM and the CLI . . . . . . . . . . . . . . . . . . . . . . . . . 474
Viewing Device Inventory in NSM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 474
Viewing Device Inventory from the CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 476
Chapter 27 Topology Manager . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 479
Overview of the NSM Topology Manager . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 479
Requisites for a Topology Discovery . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 479
About the NSM Topology Manager Toolbar . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 480
Part 5 Monitoring M-series and MX-series Devices
Chapter 28 Real Time Monitoring of M-series and MX-series . . . . . . . . . . . . . . . . . . . . . 485
About the Realtime Monitor . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 485
Viewing Device Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 486
Viewing Device Monitor Alarm Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 488
Setting the Polling Interval For Device Alarm Status . . . . . . . . . . . . . . . . . . . . . . 489
Part 6 Index
Index . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 493
xvCopyright © 2010, Juniper Networks, Inc.
Page 16

M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.xvi
Page 17

List of Figures
Part 1 Getting Started
Chapter 2 Understanding the JUNOS CLI and NSM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
Figure 1: Overview of the User Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8
Figure 2: NSM Network Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12
Part 2 Integrating M-series and MX-series Devices
Chapter 5 Updating M-series and MX-series Devices Overview . . . . . . . . . . . . . . . . . . . 29
Figure 3: Job Information Dialog Box . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Figure 4: Failed Update Job Information Dialog Box . . . . . . . . . . . . . . . . . . . . . . . . 36
Part 3 Configuring M-series and MX-series Devices
Chapter 6 Configuring M-series and MX-series Devices Overview . . . . . . . . . . . . . . . . . 41
Figure 5: MPLS Configuration in the CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Figure 6: MPLS Configuration in NSM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
Part 4 Managing M-series and MX-series Devices
Chapter 26 Viewing the M-series and MX-series Device Inventory in NSM and the
CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 473
Figure 7: The Device Inventory Window . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 474
Figure 8: Viewing the Hardware Inventory . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 475
Figure 9: Viewing the Software Inventory . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 475
xviiCopyright © 2010, Juniper Networks, Inc.
Page 18

M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.xviii
Page 19

List of Tables
About This Guide . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxvii
Table 1: Notice Icons . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxviii
Table 2: Text Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxviii
Table 3: Syntax Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xxix
Table 4: Network and Security Manager Publications . . . . . . . . . . . . . . . . . . . . . xxix
Part 1 Getting Started
Chapter 3 Before You Begin Adding M-series and MX-series Devices . . . . . . . . . . . . . . 15
Table 5: M-series Internet Routers and MX-series Internet Service Routers . . . . . . 15
Part 2 Integrating M-series and MX-series Devices
Chapter 5 Updating M-series and MX-series Devices Overview . . . . . . . . . . . . . . . . . . . 29
Table 6: Device States During Update . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 35
Part 3 Configuring M-series and MX-series Devices
Chapter 6 Configuring M-series and MX-series Devices Overview . . . . . . . . . . . . . . . . . 41
Table 7: The JUNOS Configuration Hierarchy and the NSM Configuration
Chapter 7 Configuring Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 47
Table 8: Address Assignment Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 48
Table 9: Access Address Pool Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 51
Table 10: Access Group Profile Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 51
Table 11: LDAP Options Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
Table 12: LDAP Server Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54
Table 13: Access Profile Properties Configuration Details . . . . . . . . . . . . . . . . . . . . 55
Table 14: Accounting Parameter Configuration Details . . . . . . . . . . . . . . . . . . . . . 56
Table 15: Accounting Order Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 57
Table 16: Authentication Order Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 57
Table 17: Authorization Order Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 58
Table 18: Client Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 58
Table 19: Client Filter Name Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 60
Table 20: Ldap Options Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 60
Table 21: Ldap Server Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 62
Table 22: Provisioning Order Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 62
Table 23: RADIUS Parameter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 63
Table 24: RADIUS Parameters Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 66
Table 25: RADIUS Server Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 67
Table 26: Session Limit Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 68
Tree . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
xixCopyright © 2010, Juniper Networks, Inc.
Page 20
M-series and MX-series Devices
Chapter 8 Configuring Accounting Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 71
Chapter 9 Configuring Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 79
Chapter 10 Configuring Bridge Domains . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 81
Chapter 11 Configuring Chassis . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 97
Chapter 12 Configuring Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 113
Chapter 13 Configuring Class of Service Features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 121
Table 27: RADIUS Server Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 69
Table 28: SecurID Server Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 70
Table 29: Access Profile Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70
Table 30: Class Usage Profile Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 72
Table 31: Log File Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 73
Table 32: Filter Profile Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 74
Table 33: Interface Profile Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 75
Table 34: Policy Decision Statistics Profile Configuration Details . . . . . . . . . . . . . 76
Table 35: MIB Profile Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 77
Table 36: Routing Engine Profile Configuration Details . . . . . . . . . . . . . . . . . . . . . 78
Table 37: Applications Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 80
Table 38: Bridge Domain Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 82
Table 39: Bridge Options Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 83
Table 40: Forwarding Options Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 84
Table 41: Logical Interface Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 86
Table 42: Multicast Snooping Options Configuration Details . . . . . . . . . . . . . . . . . 87
Table 43: Igmp Snooping Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 90
Table 44: VLAN ID Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 95
Table 45: Aggregated Devices Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 98
Table 46: Chassis Alarms Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 99
Table 47: Container Interfaces Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 99
Table 48: FPC Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 100
Table 49: Lcc Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 105
Table 50: Chassis Redundancy Configuration Details . . . . . . . . . . . . . . . . . . . . . . 110
Table 51: Chassis Routing Engine Configuration Details . . . . . . . . . . . . . . . . . . . . . 112
Table 52: RADIUS Authentication Configuration Details . . . . . . . . . . . . . . . . . . . . 113
Table 53: TACACS+ Authentication Configuration Details . . . . . . . . . . . . . . . . . . . 114
Table 54: Login Class Authentication Configuration Details . . . . . . . . . . . . . . . . . 116
Table 55: User Authentication Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 117
Table 56: Remote Template Account Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 118
Table 57: Local Template Account Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 119
Table 58: Configuring and Applying Behavior Aggregate Classifiers . . . . . . . . . . . 122
Table 59: Configuring Code Point Aliases . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 125
Table 60: Drop Profile Configuration Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 126
Table 61: Assigning Forwarding Classes to Output Queues . . . . . . . . . . . . . . . . . 128
Table 62: Forwarding Policy Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 129
Table 63: Fragmentation Maps Configuration Details . . . . . . . . . . . . . . . . . . . . . . 131
Table 64: Host Outbound Traffic Configuration Details . . . . . . . . . . . . . . . . . . . . 132
Table 65: Interfaces Configuration Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 133
Copyright © 2010, Juniper Networks, Inc.xx
Page 21

List of Tables
Table 66: Routing Instances Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 138
Table 67: Configuring Schedulers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 140
Table 68: Assigning Forwarding Classes to Output Queues . . . . . . . . . . . . . . . . . 141
Table 69: Restricted Queue Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 143
Table 70: Traceoptions Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 143
Table 71: Traffic Control profile Configuration Details . . . . . . . . . . . . . . . . . . . . . . 145
Table 72: Translation Table Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 146
Chapter 14 Configuring Event Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 151
Table 73: Destination Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 151
Table 74: Event Script Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 153
Table 75: Generate Event Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 154
Table 76: Configure Event Policy Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 155
Table 77: Event Options Traceoptions Configuration Details . . . . . . . . . . . . . . . . 158
Chapter 15 Configuring Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 159
Table 78: Firewall Filter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 160
Table 79: Bridge Filter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 161
Table 80: Ccc Filter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 163
Table 81: Firewall Filter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 165
Table 82: Prefix Actions Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 168
Table 83: Service Filter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 168
Table 84: Simple Filter Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 170
Table 85: Inet6 Firewall Filter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 171
Table 86: inet6 Service Filter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 173
Table 87: MPLS Firewall Filter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 175
Table 88: VPLS Firewall Filter Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 178
Table 89: Configuring a Policer for a Firewall Filter . . . . . . . . . . . . . . . . . . . . . . . . 180
Chapter 16 Configuring Forwarding Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 183
Table 90: Accounting Options Configuration Details . . . . . . . . . . . . . . . . . . . . . . 183
Table 91: Authentication Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 186
Table 92: Group Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 187
Table 93: Overrides Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 188
Table 94: Relay Option 60 Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 189
Table 95: Relay option 82 Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 191
Table 96: Sever Group Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 192
Table 97: DHCP Relay Traceoptions Configuration Details . . . . . . . . . . . . . . . . . . 192
Table 98: Address Family Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 193
Table 99: Load Balance Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 195
Table 100: BOOTP Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 196
Table 101: DNS and TFTP Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 200
Table 102: Port Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 202
Table 103: Traceoptions Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 203
Table 104: Load Balancing Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 204
Table 105: Port Mirroring Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 205
Chapter 17 Configuring Interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 207
Table 106: Interface Properties Configuration Details . . . . . . . . . . . . . . . . . . . . . 208
Table 107: Hold Time Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 209
xxiCopyright © 2010, Juniper Networks, Inc.
Page 22

M-series and MX-series Devices
Chapter 18 Configuring Multicast Snooping Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . 237
Chapter 19 Configuring Policy Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 241
Chapter 20 Configuring Protocols . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 251
Table 108: Receive Bucket Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 210
Table 109: Trace Options Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 211
Table 110: Transmit Bucket Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 212
Table 111: Logical Unit Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 213
Table 112: IP Demux Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 214
Table 113: IP Demux Source Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 214
Table 114: Epd Threshold Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 215
Table 115: Ccc Family Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 216
Table 116: Inet Family Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 218
Table 117: Inet6 Family Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 224
Table 118: Iso Family Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 230
Table 119: MPLS Family Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 231
Table 120: TCC Family Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 232
Table 121: Traffic Shaping Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 233
Table 122: Interface Set Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 234
Table 123: Traceoption Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 235
Table 124: Multicast Snooping Options Configuration Details . . . . . . . . . . . . . . . 238
Table 125: AS Path Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 242
Table 126: AS Path Group Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 243
Table 127: Community Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 244
Table 128: Condition Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 245
Table 129: Damping Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 246
Table 130: Configuring Policy Statement Fields . . . . . . . . . . . . . . . . . . . . . . . . . . 247
Table 131: Configuring Prefix List Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 249
Table 132: Configuring Bfd Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 252
Table 133: BGP Configuration Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 253
Table 134: Trace Options Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 255
Table 135: L2 Learning Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 257
Table 136: Local Switching Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 258
Table 137: Neighbor Interface Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 259
Table 138: Layer2 Circuit Traceoption Configuration Details . . . . . . . . . . . . . . . . . 261
Table 139: Layer2 Circuit Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 262
Table 140: LDP Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 265
Table 141: Link Management Protocol Configuration Details . . . . . . . . . . . . . . . . 276
Table 142: MPLS Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 280
Table 143: Administrative Group Configuration Details . . . . . . . . . . . . . . . . . . . . 282
Table 144: Administrative Groups Configuration Details . . . . . . . . . . . . . . . . . . . 283
Table 145: Automatic Policers Configuration Details . . . . . . . . . . . . . . . . . . . . . . 284
Table 146: Diffserv-Aware Traffic Engineering Configuration Details . . . . . . . . . 285
Table 147: Interface Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 286
Table 148: LSP Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 288
Table 149: Administrative Group Configuration Details . . . . . . . . . . . . . . . . . . . . . 291
Table 150: Automatic Bandwidth Configuration Details . . . . . . . . . . . . . . . . . . . 292
Table 151: Bandwidth Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 293
Copyright © 2010, Juniper Networks, Inc.xxii
Page 23

List of Tables
Table 152: Fast Reroute Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 293
Table 153: Install Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 295
Table 154: Lsp Attributes Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 296
Table 155: Oam Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 297
Table 156: P2mp Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 299
Table 157: Policer Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 299
Table 158: Primary Paths Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 300
Table 159: Administrative Group Configuration Details . . . . . . . . . . . . . . . . . . . . 302
Table 160: Bandwidth Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 303
Table 161: Oam Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 303
Table 162: Secondary Paths Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 306
Table 163: Administrative Group Configuration Details . . . . . . . . . . . . . . . . . . . . 308
Table 164: Bandwidth Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 309
Table 165: Oam Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 309
Table 166: Egress Router Address Configuration Details . . . . . . . . . . . . . . . . . . . . 312
Table 167: LSP Traceoptions Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 312
Table 168: Log Updown Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 313
Table 169: Oam Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 314
Table 170: Named Path Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 317
Table 171: Path MTU Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 317
Table 172: Static Path Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 318
Table 173: MPLS Statistics Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 320
Table 174: Traceoptions Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 321
Table 175: MSDP Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 322
Table 176: Active Source Limit Configuration Details . . . . . . . . . . . . . . . . . . . . . . 323
Table 177: Export Policy Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 323
Table 178: Peer Group Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 324
Table 179: MSDP Peer Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 326
Table 180: Rib Group Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327
Table 181: Active Source Limit Configuration Details . . . . . . . . . . . . . . . . . . . . . . 328
Table 182: MSDP Traceoption Configuration Details . . . . . . . . . . . . . . . . . . . . . . 329
Table 183: MSTP Configuration Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 330
Table 184: OSPF Configuration Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 332
Table 185: RIP Configuration Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 336
Table 186: RIPng Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 338
Table 187: Graceful Restart Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 339
Table 188: Group Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 340
Table 189: RIPng Export Policy Configuration Details . . . . . . . . . . . . . . . . . . . . . . 341
Table 190: Import Policy Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 342
Table 191: Neighbor Properties Configuration Details . . . . . . . . . . . . . . . . . . . . . . 343
Table 192: Import Policy Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 343
Table 193: Receive Message Update Configuration Details . . . . . . . . . . . . . . . . . 344
Table 194: Send Update Message Configuration Details . . . . . . . . . . . . . . . . . . . 345
Table 195: Receive Message Update Configuration Details . . . . . . . . . . . . . . . . . 345
Table 196: RIPng Send Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 346
Table 197: RIPng Traceoption Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 347
Table 198: Router Advertisement Configuration Details . . . . . . . . . . . . . . . . . . . 348
Table 199: Router Discovery Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 350
Table 200: RSVP Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 352
xxiiiCopyright © 2010, Juniper Networks, Inc.
Page 24

M-series and MX-series Devices
Chapter 21 Configuring Routing Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 361
Chapter 22 Configuring Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 389
Chapter 23 Configuring Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 391
Table 201: VRRP Configuration Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 358
Table 202: VSTP Configuration Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 360
Table 203: Confederation Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 362
Table 204: Dynamic Tunnels Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 363
Table 205: Fate Sharing Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 365
Table 206: Flow Route Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 367
Table 207: Forwarding Table Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 368
Table 208: Generated Routes Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 370
Table 209: Interface Routes Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 372
Table 210: Configuring Martian Address Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . 373
Table 211: Configuring Maximum Paths Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . 375
Table 212: Configuring Maximum Prefixes Fields . . . . . . . . . . . . . . . . . . . . . . . . . 376
Table 213: Configuring Multicast Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 377
Table 214: Configuring Options Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 381
Table 215: Rib Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 382
Table 216: Rib Group Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 384
Table 217: Source Routing Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 385
Table 218: Static Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 386
Table 219: Topology Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 387
Table 220: Traceoption Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 388
Table 221: Security Authentication Key Configuration Details . . . . . . . . . . . . . . . 390
Table 222: Adaptive Services Pics Configuration Details . . . . . . . . . . . . . . . . . . . 392
Table 223: Gateway Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 393
Table 224: Admission Controller Configuration Details . . . . . . . . . . . . . . . . . . . . 394
Table 225: Session Policy Decision Configuration Details . . . . . . . . . . . . . . . . . . 395
Table 226: Service Point Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . 397
Table 227: Message Manipulate Rules Configuration Details . . . . . . . . . . . . . . . . 398
Table 228: New Call Usage Policy Configuration Details . . . . . . . . . . . . . . . . . . . 400
Table 229: New Call Usage Policy Set Configuration Details . . . . . . . . . . . . . . . . 403
Table 230: Transaction Policy Configuration Details . . . . . . . . . . . . . . . . . . . . . . 404
Table 231: Transaction Policy Set Configuration Details . . . . . . . . . . . . . . . . . . . 406
Table 232: Timers Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 407
Table 233: Traceoption BSG Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 408
Table 234: CoS Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 413
Table 235: IDS Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 416
Table 236: Traceoptions Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 420
Table 237: NAT Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 422
Table 238: Virtual BGF Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 426
Table 239: Data Inactivity Detection Configuration Details . . . . . . . . . . . . . . . . . 428
Table 240: Gateway Controller Configuration Details . . . . . . . . . . . . . . . . . . . . . 429
Table 241: Graceful Restart Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 430
Table 242: H248 Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 431
Table 243: Encoding Defaults Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 431
Table 244: Context indication Configuration Details . . . . . . . . . . . . . . . . . . . . . . 432
Copyright © 2010, Juniper Networks, Inc.xxiv
Page 25

List of Tables
Table 245: Control Association Configuration Details . . . . . . . . . . . . . . . . . . . . . 434
Table 246: Virtual Interface Indications Configuration Details . . . . . . . . . . . . . . . 436
Table 247: Data Inactivity Detection Configuration Details . . . . . . . . . . . . . . . . . 437
Table 248: Base Root Package Configuration Details . . . . . . . . . . . . . . . . . . . . . 439
Table 249: Diffserv Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 440
Table 250: Event Timestamp Notification Configuration Details . . . . . . . . . . . . . 441
Table 251: Hanging Termination Detection Configuration Details . . . . . . . . . . . . 442
Table 252: Inactivity Timer Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . 443
Table 253: Notification Behavior Configuration Details . . . . . . . . . . . . . . . . . . . . 444
Table 254: Segmentation Package Configuration Details . . . . . . . . . . . . . . . . . . 445
Table 255: Traffic Management Configuration Details . . . . . . . . . . . . . . . . . . . . . 446
Table 256: H248 Timers Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 448
Table 257: Monitor Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 449
Table 258: Overload Control Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 449
Table 259: Session Mirroring Configuring Details . . . . . . . . . . . . . . . . . . . . . . . . . 450
Table 260: Media Service Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 451
Table 261: Configuring Rule . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 451
Table 262: Configuring Rule Set . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 452
Table 263: Session Mirroring Configuration Details . . . . . . . . . . . . . . . . . . . . . . . 453
Table 264: Traceoptions Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . 454
Table 265: Virtual Interface Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 455
Table 266: Service Interface Pools Configuration Details . . . . . . . . . . . . . . . . . . 456
Table 267: Service Set Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . 457
Table 268: Stateful Firewall Configuration Details . . . . . . . . . . . . . . . . . . . . . . . . 461
Chapter 24 Configuring SNMP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 463
Table 269: Basic System Identification Details . . . . . . . . . . . . . . . . . . . . . . . . . . 463
Table 270: Configuring Community Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 465
Table 271: Configuring SNMP Trap Group Fields . . . . . . . . . . . . . . . . . . . . . . . . . . 466
Table 272: Configuring SNMP View Fields . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 468
Part 5 Monitoring M-series and MX-series Devices
Chapter 28 Real Time Monitoring of M-series and MX-series . . . . . . . . . . . . . . . . . . . . . 485
Table 273: Device Status Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 486
xxvCopyright © 2010, Juniper Networks, Inc.
Page 26

M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.xxvi
Page 27
About This Guide
•
Objectives on page xxvii
•
Audience on page xxvii
•
Documentation Conventions on page xxvii
•
Documentation on page xxix
•
Requesting Technical Support on page xxx
Objectives
Juniper Networks Network and Security Manager (NSM) is a software application that
centralizescontrol and management of your Juniper Networksdevices. With NSM, Juniper
Networks delivers integrated, policy-based security and network management for all
devices.
M-series and MX-series devices are routers that run JUNOS software using the
command-line interface (CLI) for installation and configuration.
This guide provides the information you need to understand, configure, and maintain an
M-series or MX-series device using NSM. This guide explains how to use basic NSM
functionality, includingadding newdevices, deploying newdevice configurations, updating
device firmware, and monitoringthe status of your M-series or MX-series device. Use this
guide in conjunction with the NSM Online Help,which provides step-by-step instructions
that complement the information in this guide.
NOTE: If the information in the latest NSM Release Notes differs from the information
in this guide, follow the NSM Release Notes.
Audience
This guide is for the system administrator responsible for configuring the M-series and
MX-series devices.
Documentation Conventions
The sample screens used throughout this guide are representations of the screens that
appear when you install and configure the NSM software. The actual screens may differ.
xxviiCopyright © 2010, Juniper Networks, Inc.
Page 28
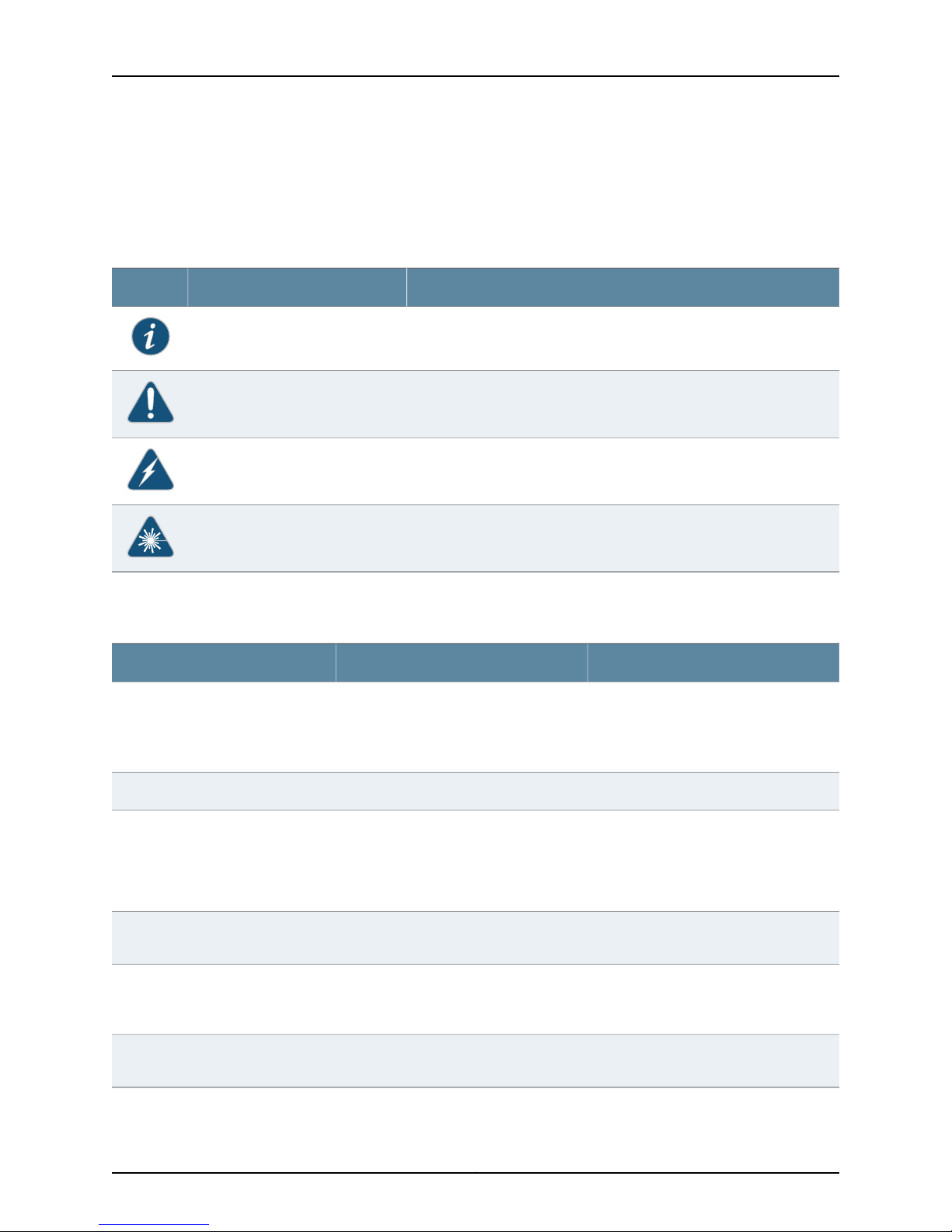
M-series and MX-series Devices
Table 1: Notice Icons
All examples show default file paths. If you do not accept the installation defaults, your
paths will vary from the examples.
Table 1 on page xxviii defines notice icons used in this guide.
DescriptionMeaningIcon
Indicates important features or instructions.Informational note
Indicates a situation that might result in loss of data or hardware damage.Caution
Alerts you to the risk of personal injury or death.Warning
Table 2 on page xxviii defines text conventions used in this guide.
Table 2: Text Conventions
Bold typeface like this
fixed-width font
Keynames linkedwith a plus (+) sign
Alerts you to the risk of personal injury from a laser.Laser warning
•
Represents commands and keywords
in text.
•
Represents keywords
•
Represents UI elements
Represents information as displayed on
the terminal screen.
keys simultaneously.
ExamplesDescriptionConvention
•
Issue the clock source command.
•
Specify the keyword exp-msg.
•
Click User Objects
user inputRepresents text that the user must type.Bold typeface like this
host1#
show ip ospf
Routing Process OSPF 2 with Router
ID 5.5.0.250
Router is an area Border Router
(ABR)
Ctrl + dIndicates that you must press two or more
Italics
The angle bracket (>)
•
Emphasizes words
•
Identifies variables
Indicates navigation paths through the UI
by clicking menu options and links.
•
The product supports two levels of
access, user and privileged.
•
clusterID, ipAddress.
Object Manager > User Objects > Local
Objects
Copyright © 2010, Juniper Networks, Inc.xxviii
Page 29
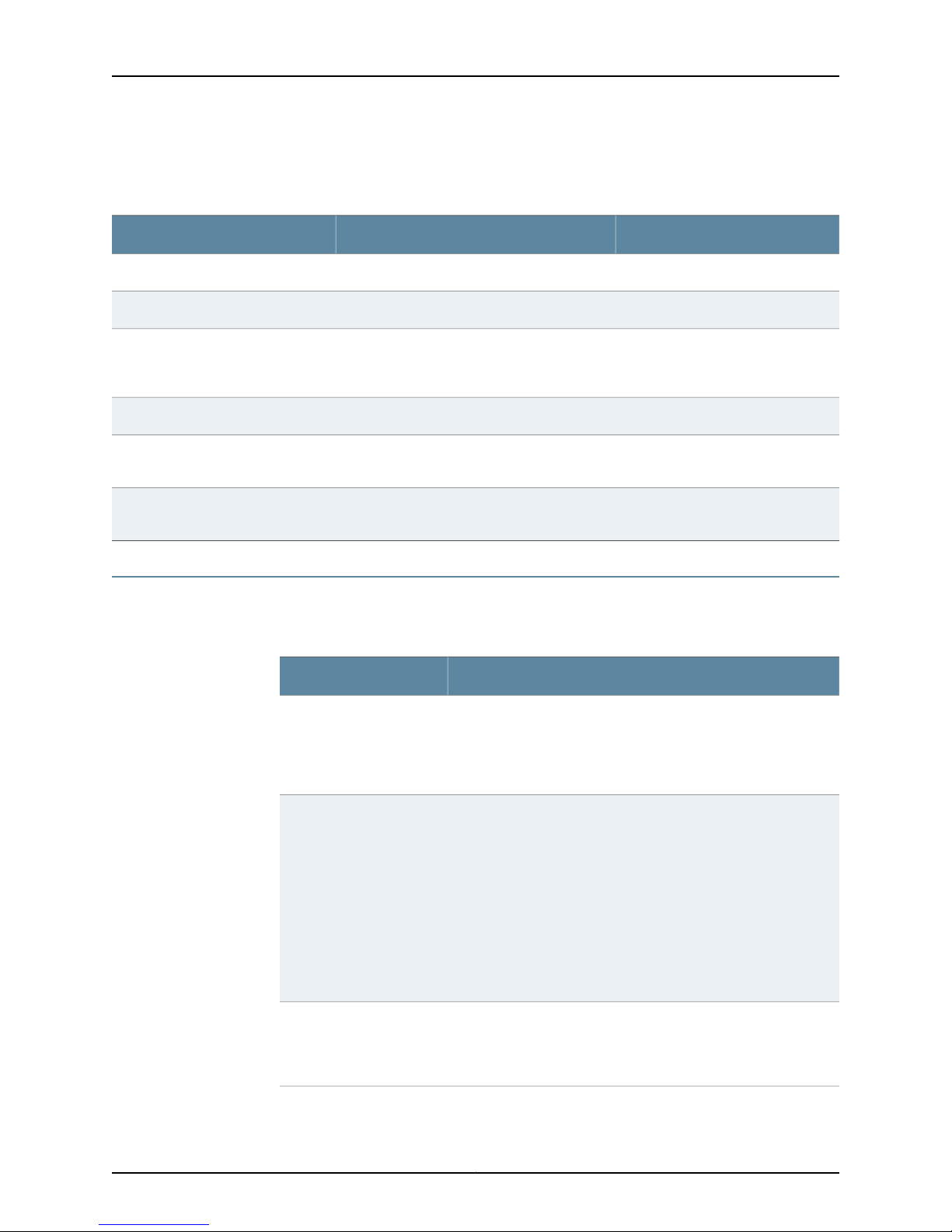
Table 3 on page xxix defines syntax conventions used in this guide.
Table 3: Syntax Conventions
About This Guide
ExamplesDescriptionConvention
terminal lengthRepresent keywordsWords in plain text
mask, accessListNameRepresent variablesWords in italics
Words separated by the pipe ( | )
symbol
Words enclosed in brackets followed
by and asterisk ( [ ]*)
Documentation
Table 4 on page xxix describes documentation for the NSM.
Table 4: Network and Security Manager Publications
Network and Security
Manager Installation Guide
variable to the left or right of this symbol. The
keywordor variable canbe optional or required.
can be entered more than once.
Represent required keywords or variables.Words enclosed in braces ( { } )
DescriptionBook
Describes the steps to install the NSM management system on a
single server or on separate servers. It also includes information on
how to install and run the NSMuser interface.This guideis intended
for IT administrators responsible for the installation or upgrade of
NSM.
diagnostic | lineRepresent a choice to select one keyword or
[ internal | external ]Represent optional keywords or variables.Words enclosed in brackets ( [ ] )
[ level1 | level2 | 11 ]*Represent optional keywords or variables that
{ permit | deny } { in |out } { clusterId
| ipAddress }
Network and Security
Manager Administration
Guide
Network and Security
Manager Configuring
ScreenOS and IDP Devices
Guide
Describes how to use and configure key management features in
the NSM. Itprovides conceptual information, suggested workflows,
and examples. This guide is best used in conjunction with the NSM
Online Help,which provides step-by-step instructions for performing
management tasks in the NSM UI.
This guide is intended for application administrators or those
individuals responsible for owning the server and security
infrastructure and configuring the product for multi-user systems.
It is also intended for device configuration administrators, firewall
and VPN administrators, and network security operation center
administrators.
Provides details about configuring the device features for all
supported ScreenOS and IDP platforms.
xxixCopyright © 2010, Juniper Networks, Inc.
Page 30
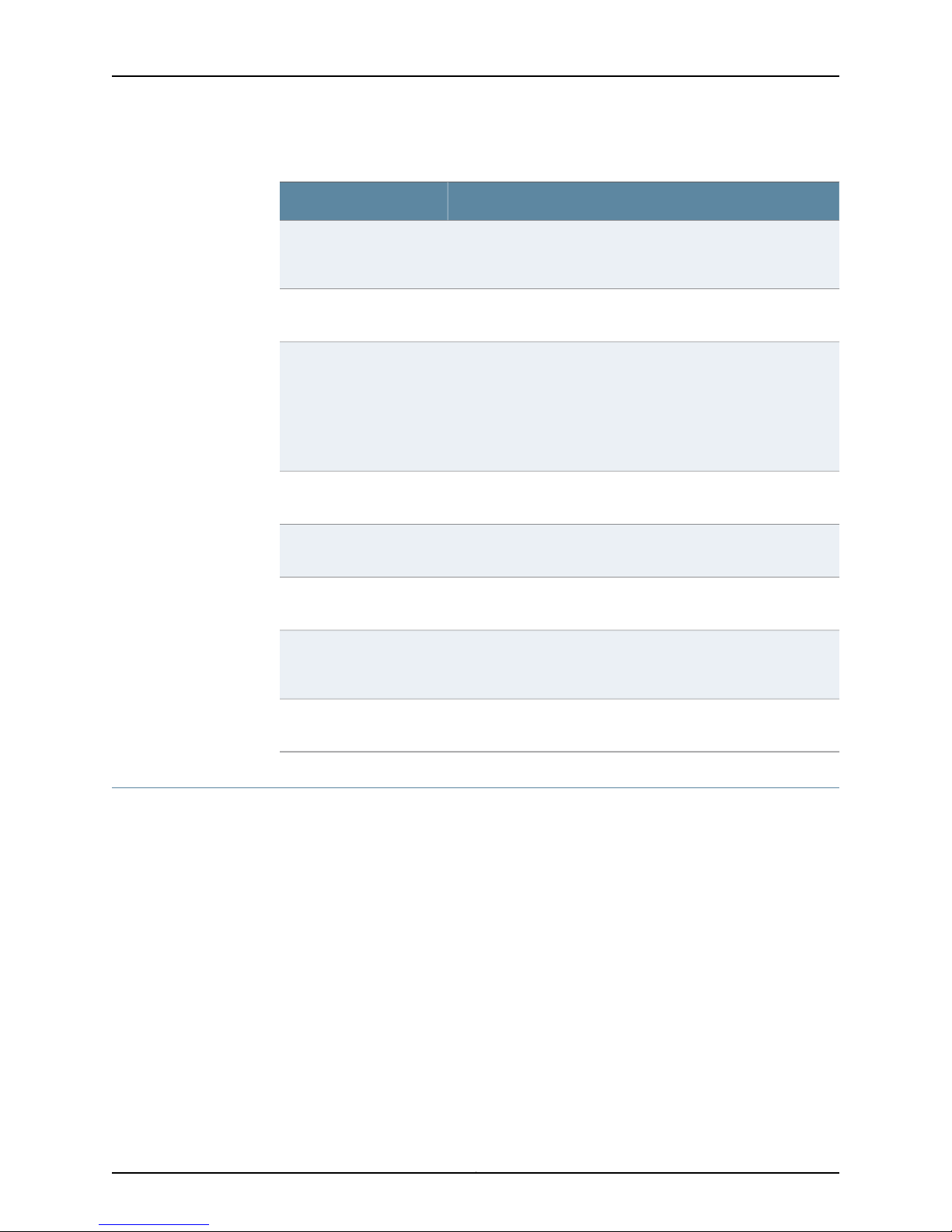
M-series and MX-series Devices
Table 4: Network and Security Manager Publications (continued)
DescriptionBook
Network and Security
Manager Online Help
Network and Security
Manager API Guide
Network and Security
Manager Release Notes
Configuring Infranet
Controllers Guide
Configuring Secure Access
Devices Guide
Configuring EX-series
Switches Guide
Configuring J-series Services
Routers and SRX-series
Services Gateways Guide
Provides procedures for basic tasks in the NSM user interface. It
also includes a brief overview of the NSM system and a description
of the GUI elements.
Provides complete syntax and description of the SOAP messaging
interface to NSM.
Provides the latest information about features, changes, known
problems, resolved problems, and system maximum values. If the
information in the Release Notesdiffers from the information found
in the documentation set, follow the Release Notes.
Release notes are included on the corresponding software CD and
are available on the Juniper Networks Website.
Provides details about configuring the device features for all
supported Infranet Controllers.
Provides details about configuring the device features for all
supported Secure Access Devices.
Provides details about configuring the device features for all
supported EX-series platforms .
Provides details about configuring the device features for all
supported J-series Services Routers and SRX-series Services
Gateways.
M-series and MX-series
Devices Guide
Requesting Technical Support
Technical productsupport is availablethrough theJuniper Networks Technical Assistance
Center (JTAC). If you are a customer with an active J-Care or JNASC support contract,
or are covered under warranty, and need post-sales technical support, you can access
our tools and resources online or open a case with JTAC.
•
JTAC policies—For a complete understanding of our JTAC procedures and policies,
review the JTAC User Guide located at
http://www.juniper.net/us/en/local/pdf/resource-guides/7100059-en.pdf .
•
Product warranties—For product warranty information, visit
http://www.juniper.net/support/warranty/ .
•
JTAC hours of operation—The JTAC centers have resources available 24 hours a day,
7 days a week, 365 days a year.
Provides details about configuring the device features for M-series
and MX-series platforms.
Copyright © 2010, Juniper Networks, Inc.xxx
Page 31

Self-Help Online Tools and Resources
For quick and easy problem resolution, Juniper Networks has designed an online
self-service portal called the Customer Support Center (CSC) that provides you with the
following features:
•
Find CSC offerings: http://www.juniper.net/customers/support/
•
Search for known bugs: http://www2.juniper.net/kb/
•
Find product documentation: http://www.juniper.net/techpubs/
•
Find solutions and answer questions using our Knowledge Base: http://kb.juniper.net/
•
Download the latest versions of software and review release notes:
http://www.juniper.net/customers/csc/software/
•
Search technical bulletins for relevant hardware and software notifications:
https://www.juniper.net/alerts/
•
Join and participate in the Juniper Networks Community Forum:
http://www.juniper.net/company/communities/
About This Guide
•
Open a case online in the CSC Case Management tool: http://www.juniper.net/cm/
To verifyservice entitlement byproduct serial number,use our Serial Number Entitlement
(SNE) Tool: https://tools.juniper.net/SerialNumberEntitlementSearch/
Opening a Case with JTAC
You can open a case with JTAC on the Web or by telephone.
•
Use the Case Management tool in the CSC at http://www.juniper.net/cm/ .
•
Call 1-888-314-JTAC (1-888-314-5822 toll-free in the USA, Canada, and Mexico).
For international or direct-dial options in countries without toll-free numbers, see
http://www.juniper.net/support/requesting-support.html .
xxxiCopyright © 2010, Juniper Networks, Inc.
Page 32

M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.xxxii
Page 33

PART 1
Getting Started
•
Getting Started with NSM on page 3
•
Understanding the JUNOS CLI and NSM on page 5
•
Before You Begin Adding M-series and MX-series Devices on page 15
1Copyright © 2010, Juniper Networks, Inc.
Page 34

M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.2
Page 35

CHAPTER 1
Getting Started with NSM
•
Introduction to Network and Security Manager on page 3
•
Installing NSM on page 3
•
Role-Based Administration on page 4
Introduction to Network and Security Manager
Juniper Networks Network and Security Manager (NSM)gives you complete control over
your network. Using NSM, you can configure all your Juniper Networks devices from one
location, at one time.
NSM works with networks of all sizes and complexity. You can add a single device, or
create device templates tohelp you deploy multiple devices. You can create new policies,
or edit existing policies for security devices. The management system tracks and logs
each administrative change in real time, providing you with a complete administrative
record and helping you perform fault management.
Related Topics Installing NSM on page 3•
Installing NSM
NSM also simplifies control of your network with a straightforward user interface. Making
all changes to your devices from a single, easy-to-use interface can reduce deployment
costs, simplify network complexity, speed configuration, and minimize troubleshooting
time.
For more detailed information about NSM, including a technical overview, working in the
NSM user interface (UI), and new features in NSM 2010.3, see the section on getting
started with NSM in the Network and Security Manager Administration Guide.
• Role-Based Administration on page 4
• NSM and Device Management Overview on page 5
NSM is a software application that enables you to integrate and centralize management
of your JuniperNetworks environment. You needto install two main software components
to run NSM: the NSM management system and the NSM user interface (UI).
3Copyright © 2010, Juniper Networks, Inc.
Page 36

M-series and MX-series Devices
The overall process for installing NSM is as follows:
•
Management System Installation Process
•
User Interface Installation Process
Refer to the Network Security Manager Installation Guide for details on the steps to install
the NSM management system on a single server or on separate servers. It also includes
information on how to install and run the NSM user interface. The Network Security
Manager Installation Guide is intendedfor ITadministrators responsible for the installation
of or upgrade to NSM.
Related Topics Introduction to Network and Security Manager on page 3•
• Role-Based Administration on page 4
• NSM and Device Management Overview on page 5
Role-Based Administration
The NSM role-based administration (RBA) feature enables you to define strategic roles
for your administrators, delegate management tasks, and enhance existing permission
structures using task-based functions.
Use NSM to create a secure environment that reflects your current administrator roles
and responsibilities. By specifying the exact tasks your NSM administrators can perform
within a domain, you minimize the probability oferrors and security violations and enable
a clear audit trail for every management event.
For moredetailedinformation about role-based administration, including using role-based
administration more effectively and configuring role-based administration, see
“Configuring Role-Based Administration” in the Network and Security Manager
Administration Guide.
Related Topics • Introduction to Network and Security Manager on page 3
• Installing NSM on page 3
• NSM and Device Management Overview on page 5
Copyright © 2010, Juniper Networks, Inc.4
Page 37

CHAPTER 2
Understanding the JUNOS CLI and NSM
•
NSM and Device Management Overview on page 5
•
Understanding the CLI and NSM on page 6
•
Comparing the CLI To the NSM UI on page 7
•
NSM Services Supported for M-series and MX-series Devices on page 10
•
How NSM Works with the CLI and Distributed Data Collection on page 11
•
Device Schemas on page 12
•
Communication Between a Device and NSM on page 13
NSM and Device Management Overview
NSM is the Juniper Networks network management tool that allows distributed
administration of network appliances like the M-series and MX-series routers. You can
use the NSM application to centralize status monitoring, logging, and reporting, and to
administer device configurations. The term device is used in NSM to describe a router or
platform.
Related Topics Understanding the CLI and NSM on page 6•
With NSM you can manage andadminister a device from a single management interface.
In addition,NSM letsyou manage most of the parameters thatyou canconfigure through
the command-line interface (CLI). Although the configuration screens rendered in NSM
look different, the top-level configuration elements essentiallycorrespond to commands
in the CLI.
NSM incorporates a broad configuration management framework that allows
comanagement using other methods. To manage the device configuration, you can also
use the XML files import and export feature, or you can manage from the device’s admin
console.
• Comparing the CLI To the NSM UI on page 7
• NSM Services Supported for M-series and MX-series Devices on page 10
• How NSM Works with the CLI and Distributed Data Collection on page 11
• Device Schemas on page 12
5Copyright © 2010, Juniper Networks, Inc.
Page 38

M-series and MX-series Devices
• Communication Between a Device and NSM on page 13
Understanding the CLI and NSM
M-series and MX-series devices are routers that have the JUNOS software installed as
the operating system. With the JUNOS software you use the command-line interface
(CLI) to access an individual router (which is called a device in NSM)—whether from the
consoleor througha network connection. The CLI isa JUNOSsoftware-specific command
shell that runs on top of a UNIX-based operating system kernel. The CLI is a
straightforward command interface you can use to monitor and configure a router. You
type commands on a single line, and the commands are executed when you press the
Enter key. For more information on the CLI, see the JUNOS CLI User Guide.
Network and Security Manager (NSM) is a software application that centralizes control
and management of your Juniper Networks devices. NSM is a three-tier management
system made up of the following:
•
A user interface (UI)
Related Topics NSM and Device Management Overview on page 5•
•
Management system
•
Managed devices
The devices process your network traffic and arethe enforcement points that implement
your policies. The UI and management system tiers are software-based so you can deploy
them quickly and easily. Because the management system uses internal databases for
storage and authentication, you do not need LDAP or an external database. For more
information about NSM architecture, see the technical overview in the Network Security
Manager Administration Guide.
With NSM you can manage most of the parameters that you can configure through the
CLI. Although the configuration screens rendered in NSM look different, the top-level
configuration elements essentially correspond to commands in the CLI.
Typically, M-series and MX-series devices are managed individually using the CLI. The
advantage of using NSM is that you can centralize status monitoring and administration
of the configurations of a network of M-series and MX-series devices.
• Comparing the CLI To the NSM UI on page 7
• NSM Services Supported for M-series and MX-series Devices on page 10
• How NSM Works with the CLI and Distributed Data Collection on page 11
• Device Schemas on page 12
• Communication Between a Device and NSM on page 13
Copyright © 2010, Juniper Networks, Inc.6
Page 39

Comparing the CLI To the NSM UI
Because NSM is a UI and the CLI is a command-line interface, the way you access
configuration, monitoring, and management information is different in each interface.
The CLI has two modes: operational mode and configuration mode.
•
Operational mode—This mode displays the current router status. In operational mode,
you enter commands to monitor and troubleshoot the software, network connectivity,
and router.
•
Configuration mode—A router configuration is stored as a hierarchy of statements. In
configuration mode, you enter these statements to define all properties of the JUNOS
software, including interfaces, general routing information, routing protocols, user
access, and several system hardware properties.
The following sample output shows the operational mode commands available at the
top level of the CLI operational mode:
user@host> ?
Possible completions:
clear Clear information in the system
configure Manipulate software configuration information
file Perform file operations
help Provide help information
monitor Show real-time debugging information
mtrace Trace multicast path from source to receiver
op Invoke an operation script
ping Ping remote target
quit Exit the management session
request Make system-level requests
restart Restart software process
set Set CLI properties, date/time, craft interface message
show Show system information
ssh Start secure shell on another host
start Start shell
telnet Telnet to another host
test Perform diagnostic debugging
traceroute Trace route to remote host
Chapter 2: Understanding the JUNOS CLI and NSM
The following sample output shows the protocols configuration of an M-series device:
[edit]
user@host# show protocols
mpls {
interface ge-1/3/3.0;
interface fe-0/1/2.0;
interface fe-0/1/1.0;
}
ospf {
traffic-engineering;
area 0.0.0.1 {
interface lo0.0 {
passive;
}
interface ge-1/3/3.0;
interface fe-0/1/2.0;
interface fe-0/1/1.0;
7Copyright © 2010, Juniper Networks, Inc.
Page 40

M-series and MX-series Devices
}
}
For moreinformation about operational and configurationmode, see the JUNOS CLI User
Guide.
In contrast, the NSM UI displaysa set of menus, toolbaricons atthe top of the UI window,
and a navigation tree that includes an Investigate panel, a Configure panel, and an
Administer panel. For some components, right-click menus are available to perform
tasks.
Figure 1 on page 8 shows the NSM UI with the Configure navigation tree expanded and
the maindisplay area containing the services available from the Configure panel. Different
services display when you select the Investigate or Administer panels.
Figure 1: Overview of the User Interface
Copyright © 2010, Juniper Networks, Inc.8
Page 41

Chapter 2: Understanding the JUNOS CLI and NSM
•
Menu bar—Contains clickable commands. You can access many menu bar commands
using keyboard shortcuts. For a complete list of keyboards shortcuts, see the Network
and Security Manager Online Help.
•
Toolbar—Contains buttons for common tasks. The buttons displayed in the toolbar
are determined by the selected module.
•
Domain menu—Contains a pull-down menu above the navigation tree where domains
and subdomains are selected. The domains and subdomains displayed are those to
which the current user has access.
•
Navigation Tree—The navigation tree displays the 11 NSM modules in the left pane of
the NSM window.
•
Investigate panel—Provides NSM modules with tree structures for monitoring your
network.
•
Configure panel—Provides NSM modules with tree structures for configuring devices,
policies, virtual private networks (VPNs), and other objects.
•
Administer panel—Provides NSM modules with tree structures for managing the NSM
servers, ongoing jobs, and other actions.
Related Topics NSM and Device Management Overview on page 5•
•
Main display area—Displays the content for the currently selected module or module
contents.
•
Common tasks pane—Provides links to commonly accessed tasks throughout the UI.
These common tasks change depending on what tasks are often selected in the UI.
•
Status bar—Displays additional information for a selected module.
For details about the Investigate, Configure, and Administer panels, see “NSM Modules"
in the Network Security Manager Administration Guide.
• Understanding the CLI and NSM on page 6
• NSM Services Supported for M-series and MX-series Devices on page 10
• How NSM Works with the CLI and Distributed Data Collection on page 11
• Device Schemas on page 12
• Communication Between a Device and NSM on page 13
9Copyright © 2010, Juniper Networks, Inc.
Page 42

M-series and MX-series Devices
NSM Services Supported for M-series and MX-series Devices
NSM supports the following services for the M-series and MX-series devices:
•
Device management—Enables addition of new devices, editingand deletion of existing
devices, software version update, reconfiguration of existing devices, activation of
modeled devices, and master Routing Engine switchover with synchronized commits.
In addition, Return Merchandise Authorization (RMA) updates enable failed device
replacement without a serial number or connection statistics.
•
Device discovery—Uses sets of rules tofind, add, and import multipledevices into NSM.
In addition, configure and run rules to search a network and find devices in a specified
subnet, or within a specified range of IP addresses. M-series and MX-series devices
must be configured with static IP addresses to be found by device discovery rules.
•
Topology management—Provides discoveryand management ofthe physical topology
of a network of devices connected to a Juniper Networks EX-series switch. These
include networking devices such as the J-series, M-series, MX-series and EX-series as
well as ScreenOS and Intrusion Detection and Prevention (IDP) devices, IP phones,
desktops, printers, and servers. The Topology Manager also provides details about
connections between a device and the EX-series switch.
Related Topics NSM and Device Management Overview on page 5•
•
Inventory and license management—Displays device inventory and licensing details.
In adual RoutingEngine system, the inventory data is collected from the master Routing
Engine.
•
Upgrading software for single and dual Routing Engines.
•
Configurationmanagement—Enables in-device configurationand editing,configuration
groups, and template configuration.
•
Status monitoring—Displays a list of all managed devices, including status, name,
domain, OS version, synchronization status, connection details, and current alarms.
•
Job management—Displays details of the update process in a dedicated information
window and includes the update’s success or failure and the errors involved in a failed
update.
Below is a summary of theservices that are not supportedfor theM-series and MX-series
devices:
•
Adding, deleting, or editing licensing information, (though licenses can be viewed).
•
Downgrading software.
•
Configuration of cluster objects, policy manager, VPN manager, and shared objects.
•
JUNOS Redundancy Protocol (JSRP), VPN, and IDP cluster monitor.
• Understanding the CLI and NSM on page 6
• Comparing the CLI To the NSM UI on page 7
Copyright © 2010, Juniper Networks, Inc.10
Page 43

Chapter 2: Understanding the JUNOS CLI and NSM
• How NSM Works with the CLI and Distributed Data Collection on page 11
• Device Schemas on page 12
• Communication Between a Device and NSM on page 13
How NSM Works with the CLI and Distributed Data Collection
Before we can discuss how NSM works with the CLI, the following terms need to be
defined:
•
ADM (Abstract Data Model)—The Abstract Data Model is an XML file that contains all
the configuration information for a domain.
•
configlet—A configlet is a small, static configuration file that contains information on
how a device can connect to NSM.
•
Device Server—The Device Server is the component of the NSM management system
that handles communication between the GUI Server and the device, collects data
from the managed devices on your network, formats configuration information sent
to your managed device, and consolidates log and event data.
•
DM (Data Model)—A Data Model is an XML file that contains configuration data for
an individual device. The DM is stored in the Device Server; when you create, update,
or import a device, the GUI Server edits the Abstract Data Model (ADM) to reflect the
changes, then translates that information to the DM
•
GUI Server—The GUI Server manages the system resources and data that drives NSM
functionality. The GUI Server contains the NSM databases and centralizes information
for devices and their configurations, attack and server objects, and policies.
NSM andthe CLIcommunicatethrough theGUI andDevice Servers that translate objects
and object attributes in both directions. Device configuration information is translated
into Data Model (DM) objects or Abstract Data Model (ADM) object attributes, and
conversely DM objects and ADM object attributes are translated into XML configlets and
documents.
NSM uses a distributed data collection system. Each device is described by a unique DM.
The DM is stored in the Device Server which communicates with the GUI Server and the
device.
When you create, update, or import a device into NSM, the GUI Server edits the ADM to
reflect the changes, then translates that information to the DM. The ADM contains
configuration data for all objects in a specific domain. When you use the UI to interface
with your managed devices, the ADM and DMs work together.
11Copyright © 2010, Juniper Networks, Inc.
Page 44

M-series and MX-series Devices
Figure 2: NSM Network Architecture
•
When you update a device configuration, the GUI Server translates the objects and
object attributes in the ADM domain into device configuration information in a DM. For
DMI based devices which include the M-series and MX-series, the Device Server converts
the DM into an XML configlet and sends the configlet through NetConf protocol to the
device.
Related Topics NSM and Device Management Overview on page 5•
Device Schemas
•
When you import a device configuration, the device sends the configuration through
the NetConf protocol as an XML document to the Device Server, which translates the
XML document into a DM with device configuration information. The GUI Server then
translates the device configuration in the DM into objects and object attributes in the
ADM, and uses the ADM to display current information in the UI.
For more details on the ADM and DMs, see “Managing Devices” in the Network Security
Manager Administration Guide.
The management system also provides an application programming interface (API) for
integrating NSM into larger enterprise business systems. This NSM API provides an
alternative interface to that provided by the UI. For details, see the Network and Security
Manager API Guide.
• Understanding the CLI and NSM on page 6
• Comparing the CLI To the NSM UI on page 7
• NSM Services Supported for M-series and MX-series Devices on page 10
• Device Schemas on page 12
• Communication Between a Device and NSM on page 13
The structure of the ADM and the DMs is defined by a DM schema, which lists all the
possible fields and attributes for a type of object or device. The DM schema reads from
a capability file, which lists the fields and attributes that a specific operating system
version supports, to determine the supported features for the operating system version
Copyright © 2010, Juniper Networks, Inc.12
Page 45

that is running on the managed devices. NSM uses capability files to enable JUNOS
software upgrades without changing the device configuration in NSM.
The M-series and MX-series device families are described by schemasthat are maintained
on a schema repository owned by Juniper Networks. These schemas can be added
dynamically to NSM.
Related Topics NSM and Device Management Overview on page 5•
• Understanding the CLI and NSM on page 6
• Comparing the CLI To the NSM UI on page 7
• NSM Services Supported for M-series and MX-series Devices on page 10
• How NSM Works with the CLI and Distributed Data Collection on page 11
• Communication Between a Device and NSM on page 13
Communication Between a Device and NSM
Chapter 2: Understanding the JUNOS CLI and NSM
The M-series and MX-series devices and the NSM application communicate through the
Device Management Interface (DMI). DMI is a collection of schema-driven protocols that
run on a common transport (TCP). DMI is designed to work with routers running the
JUNOS software to makedevice management consistent across alladministrativerealms.
The DMI protocols that are supported include NetConf (for inventory management,
XML-based configuration, text-basedconfiguration,alarm monitoring,and device-specific
commands), structured syslog, and threat flow for network profiling. DMI supports
third-party network management systems that incorporate the DMI standard; however,
only one DMI-based agent per device is supported.
The configuration of the M-series and MX-series device is represented as a hierarchical
tree of configuration items. This structure is expressed in XML that can be manipulated
with NetConf. NetConf is a network management protocol that uses XML. DMI uses
NetConf’s generic configuration management capability and applies it to allow remote
configuration of the device.
The schema repository enables access to XSD and XML files defined for each device,
model, and software version.
Related Topics • NSM and Device Management Overview on page 5
• Understanding the CLI and NSM on page 6
• Comparing the CLI To the NSM UI on page 7
• NSM Services Supported for M-series and MX-series Devices on page 10
• How NSM Works with the CLI and Distributed Data Collection on page 11
• Device Schemas on page 12
13Copyright © 2010, Juniper Networks, Inc.
Page 46

M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.14
Page 47

CHAPTER 3
Before You Begin Adding M-series and
MX-series Devices
•
M-series and MX-series Devices Supported by NSM on page 15
•
Considering the Device Status on page 16
•
Configuring a Deployed M-series or MX-series Device for Importing to NSM on page 16
M-series and MX-series Devices Supported by NSM
Table 5 on page 15 lists the M-series Internet routers, MX-series Internet Services routers,
and the operating system versions supported by NSM.
Table 5: M-series Internet Routersand MX-series Internet Service Routers
Operating System VersionDevice
JUNOS Release 9.3Juniper Networks M7i Internet router
Related Topics Considering the Device Status on page 16•
JUNOS Release 9.3Juniper Networks M10i Internet router
JUNOS Release 9.3Juniper Networks M40e Internet router
JUNOS Release 9.3Juniper Networks M120 Internet router
JUNOS Release 9.3Juniper Networks M320 Internet router
JUNOS Release 9.3Juniper Networks MX240 Internet Services router
JUNOS Release 9.3Juniper Networks MX480 Internet Services router
JUNOS Release 9.3Juniper Networks MX960 Internet Services router
• Configuring a Deployed M-series or MX-series Device for Importing to NSM on page 16
15Copyright © 2010, Juniper Networks, Inc.
Page 48

M-series and MX-series Devices
Considering the Device Status
The network statusof yourdevice influences the preliminary configurationrequired before
you can addthe device to NSMand themethod you useto add the device to NSM. Devices
can be deployed in your network or undeployed. Deployed devices can be configured
with a static or dynamic IP address, which influences the method you use to add them
to NSM. Also, undeployed devices are treated differently from deployed devices.
•
Deployed devices—Deployed devices are the devices you are currently using in your
existing network. These devices have already been configured with a static or dynamic
IP address andother basicinformation. Youcan import a devicewith a static or dynamic
IP address to NSM, so long as it has the following enabled:
•
The management interface (fxp0) with the IP address of the device and a user with
full administrative privileges for the NSM administrator.
•
A physical connection to your network with access to network resources.
•
Connectivity to the NSM device server, which can be with a static IP address.
•
Telnet or SSHv2, and NETCONF protocol over SSH.
The NSM process of importing a deployed device differs depending on whether your
device is configuredwith a static ordynamic IP address. For information aboutimporting
a device with astatic IPaddress or about importinga devicewith adynamic IP address,
see the Network Security Manager Administration Guide.
NOTE: Toimport device configurations, the connection between NSM and the managed
device must be at least 28.8 Kbps. For details on installing NSM on your network, refer
to the Network and Security Manager Installation Guide.
•
Undeployed devices—Undeployed devices are devices that you are not currently using
in your network and, typically, for which you do not have IP addresses, zones, or other
basic network information. For undeployed devices, you can model a new device
configuration and later install that configuration on the device. For more information
on addingundeployeddevices, see “Modelinga Device”in theNetwork Security Manager
Administration Guide.
Related Topics M-series and MX-series Devices Supported by NSM on page 15•
• Configuring a Deployed M-series or MX-series Device for Importing to NSM on page 16
Configuring a Deployed M-series or MX-series Device for Importing to NSM
A deployed device is a device you are currently using in your network. Before you can add
a deployed device to NSM, you must configure the following parameters on the device,
regardless of the static or dynamic nature of the IP address:
Copyright © 2010, Juniper Networks, Inc.16
Page 49

Chapter 3: Before You Begin Adding M-series and MX-series Devices
•
The management interface (fxp0) with the IP address of the device
•
A user with full administrative privileges for the NSM administrator
•
A physical connection to your network with access to network resources
•
Connectivity to the NSM device server, which can be with a static IP address
•
Telnet or SSHv2, and NETCONF protocol over SSH
To configure these parameters, perform the following tasks:
•
Configure an IP Address and a User with Full Administrative Privileges for the
Device on page 17
•
Check Network Connectivity on page 17
•
Check Connectivity to the NSM Server on page 17
•
Configure a Static Route to the NSM Server on page 18
•
Establish a Telnet or an SSHv2, and a NETCONF protocol over SSH Connection to the
NSM Server on page 19
Configure an IP Address and a User with Full Administrative Privileges for the Device
Purpose Before you canadd an M-series or MX-seriesdevice to NSM, you must have an IP address
configured on the management interface (fxp0) and a user with full administrative
privileges for the NSM administrator.
Action Generally when you install the JUNOS software, you configure the router from scratch
and at that point you configure the management interface (fxp0) with the IP address
and a user with full administrative privileges.
For information on configuring the router from scratch, see the JUNOS System Basics
Configuration Guide.
For step-by-step instructions on reconfiguring names, addresses, and the root password
after reinstalling the JUNOS software, see “Configure Names and Addresses” and “Set
the Root Password.”
Check Network Connectivity
Purpose Establish that the M-series or MX-series device has a connection to your network.
Action To check that the device has a connection to your network, log on to the M-series or
MX-series device and issue a ping command to a system on your network:
root@> ping address
If there is no response, verify that there is a route to the address using the show route
command. If the address is outside your fxp0 subnet, add a static route.
Check Connectivity to the NSM Server
Purpose Establish that the M-series or MX-series device has a connection to the NSM server.
17Copyright © 2010, Juniper Networks, Inc.
Page 50

M-series and MX-series Devices
Action To check that the device has a connection to the NSM server, log on to the M-series or
MX-series device and issue a ping command to the IP address of the NSM server:
root@> ping address
If there is no response, verify that there is a route to the address using the show route
command.If the address isoutside your fxp0 subnet, add a staticroute to theNSM server.
Configure a Static Route to the NSM Server
Purpose When your M-series or MX-series device and the NSM server are in different subnets, you
can install a static route on the device to connect to the NSM server. The static route is
installed in the routing table only when the route is active; that is, the list of next-hop
routersconfigured for that route contains at least one next hop on an operational interface.
Action To configure a static route, follow these steps:
1. Log on to the M-series or MX-series device and, in configuration mode, go to the
following hierarchy level:
[edit]
user@host# edit routing-options
2. Configure a static route to the NSM server with the retain option so that the static
route remains in the forwarding table when the routing protocol process shuts down
normally:
[edit routing-options]
user@host# set static route destination-prefix next-hop address retain
3. Configure the no-readvertiseoption so that the route is not eligiblefor readvertisement
by dynamic routing protocols:
[edit routing-options]
user@host# set static route destination-prefix next-hop address no-readvertise
4. Verify the configuration:
user@host# show
5. Commit the configuration:
user@host# commit
6. Verify the connection to the NSM server:
user@host# run ping destination
Sample Output user@host> edit
Entering configuration mode
[edit]
user@host# edit routing-options
[edit routing-options]
user@host# set static route 192.193.60.181/32 next-hop 192.193.76.254
[edit routing-options]
user@host# set static route 192.193.60.181/32 retain
Copyright © 2010, Juniper Networks, Inc.18
Page 51

Chapter 3: Before You Begin Adding M-series and MX-series Devices
[edit routing-options]
user@host# set static route 192.193.60.181/32 no-readvertise
[edit routing-options]
user@host# show
static {
}
route 192.193.60.181/32 {
next-hop 192.193.76.254;
retain;
no-readvertise;
}
}
[edit routing-options]
user@host# commit
commit complete
[edit routing-options]
user@host# run ping 192.193.60.181
PING 192.193.60.181 (192.193.60.181): 56 data bytes
64 bytes from 192.193.60.181: icmp_seq=0 ttl=64 time=23.050 ms
64 bytes from 192.193.60.181: icmp_seq=1 ttl=64 time=18.129 ms
64 bytes from 192.193.60.181: icmp_seq=2 ttl=64 time=0.304 ms
^C
--- 192.193.60.181 ping statistics --3 packets transmitted, 3 packets received, 0% packet loss
round-trip min/avg/max/stddev = 0.304/13.828/23.050/9.771 ms
Meaning The sample output shows that a static route (192.193.60.181/32) to the NSM server is
configured and committed, and that there is a connection between the router and the
server because the ping command shows that three packets were transmitted and
received.
Establish a Telnet or an SSHv2, and a NETCONF protocol over SSH Connection to the NSM
Server
To configure an M-series or MX-series device before adding it to NSM, take the following
steps:
1. Log on to the M-series or MX-series device.
2. In configuration mode, go to the following hierarchy level:
[edit system services]
3. At the [edit system services] hierarchy level, enter the following commands:
user@host# set ftp
user@host# set ssh protocol-version v2
user@host# set telnet
user@host# set netconf ssh
4. Verify the configuration:
user@host# show
19Copyright © 2010, Juniper Networks, Inc.
Page 52

M-series and MX-series Devices
Sample Output [edit]
5. Commit the configuration:
user@host# commit
user@host# edit system services
[edit system services]
user@host# set ftp
[edit system services]
user@host# set ssh protocol-version v2
[edit system services]
user@host# set telnet
[edit system services]
user@host# set netconf ssh
[edit system services]
user@host# show
ftp;
ssh {
protocol-version v2;
}
telnet;
netconf {
ssh;
}
[edit system services]
user@host# commit
commit complete
Copyright © 2010, Juniper Networks, Inc.20
Page 53

PART 2
Integrating M-series and MX-series
Devices
•
Adding M-series and MX-series Devices Overview on page 23
•
Updating M-series and MX-series Devices Overview on page 29
21Copyright © 2010, Juniper Networks, Inc.
Page 54

M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.22
Page 55

CHAPTER 4
Adding M-series and MX-series Devices
Overview
•
About Device Creation on page 23
•
Supported Add Device Workflows for M-series and MX-series Devices on page 24
•
Importing Devices Overview on page 25
•
Modeling Devices Overview on page 26
•
Adding Multiple Devices Using Automatic Discovery (JUNOS Software Devices
Only) on page 27
•
Adding Device Groups Overview on page 27
About Device Creation
Before Network and Security Manager (NSM) can manage devices, you must first add
those devices to the management system using the NSM user interface (UI). To add a
device, you create an object in the UI that represents the physical device, and then create
a connection between the UI object and the physical device so that their information is
linked. When you make a change to the UI device object, you can push that information
to the real device so the two remain synchronized. You can add a single device at a time
or add multiple devices all at once.
NOTE: The connection between a managed device and the NSM Device Server must
be at least 28.8 Kbps.
How you add your devices to the management system depends on the network status
of the device. You can import deployed devices, or you can model devices that have not
yet been deployed:
•
Import deployed devices—Deployed devices are the devices you are currently using in
your existing network. These devices have already been configured with a static or
dynamic IP address and other basic information. For deployed devices, you can import
the existing device configuration information into NSM.
23Copyright © 2010, Juniper Networks, Inc.
Page 56

M-series and MX-series Devices
NOTE: Toimport device configurations, the connection between NSM and the managed
device must be at least 28.8 Kbps. For details on installing NSM on your network, refer
to the Network and Security Manager Installation Guide.
•
Model undeployed devices—Undeployed devices are devices thatyou are not currently
using in your network and, typically for which, you do not have IP addresses, zones, or
other basic network information. For undeployed devices, you can model a new device
configuration and later install that configuration on the device.
To help you add a device, the UI contains an Add Device wizard that walks you through
each step of the device creation process. The Add Device wizard prompts you to first
choose a workflow from the given options. Device is reachable is the default option. The
wizard then prompts you for specific device information, such as the device platform
name, OS name and version, IP address, and device administrator name, and then uses
that information todetect thedevice. You can then choose to modify the displayedname
of the device and assign a color to the device. If the host name is not unique within NSM
or is undetected, the Add Device wizard generates a validation error, forcing you to add
a valid device name in order to proceed with adding the physical device to the Device
Server.
After the physical device connects, it is considered to be a managed device, meaning it
is now under the control of NSM.
For more detailed information about verifying and managing a device, see “About Device
Creation” in the Network and Security Manager Administration Guide.
Related Topics Supported Add Device Workflows for M-series and MX-series Devices on page 24•
• Importing Devices Overview on page 25
• Modeling Devices Overview on page 26
• Adding Multiple Devices Using Automatic Discovery (JUNOS Software Devices Only)
on page 27
• Adding Device Groups Overview on page 27
Supported Add Device Workflows for M-series and MX-series Devices
An M-seriesor MX-seriesdevice canbe addedusing the following methods or workflows:
•
Import device with static IP address
•
Import device with dynamic IP address
•
Model and activate device
•
Rapid deployment (configlets)
•
Device discovery
Copyright © 2010, Juniper Networks, Inc.24
Page 57

•
Import many devices (CSV file) with static IP addresses
•
Import many devices (CSV file) with dynamic IP addresses
The model many devices (CSV file) workflow is not supported.
Related Topics About Device Creation on page 23•
• Importing Devices Overview on page 25
• Modeling Devices Overview on page 26
• Adding Multiple Devices Using Automatic Discovery (JUNOS Software Devices Only)
on page 27
• Adding Device Groups Overview on page 27
Importing Devices Overview
NSM can import device configurations from M-series and MX-series devices running
JUNOS 9.3 or later.
Chapter 4: Adding M-series and MX-series Devices Overview
When importing from a device, the management system connects to the device and
imports Data Model (DM) information that contains details of the device configuration.
The connection is secured using Secure Server Protocol (SSP), a proprietary encryption
method; an always-on connection exists between the management system and the
device.
For details about adding multiple devices at one time, see the Network and Security
Manager Administration Guide.
Requirements To import a single device, you must have available the following requirements:
• A management interface (fxp0) with the IP address of the device
• A user with full administrative privileges for the NSM administrator
• Device connection information (IP address, connection method) and the device
administrator's name and password
NOTE: All passwords handled by NSM are case-sensitive.
• A physical connection to your network with access to network resources
• Connectivity to the NSM Device Server, which can be with a static IP address
• A Telnet or an SSHv2, and a NETCONF protocol over SSH connection
25Copyright © 2010, Juniper Networks, Inc.
Page 58

M-series and MX-series Devices
NOTE: After importing a device configuration, log entries from that device begin to
appear in the Log Viewer. However,until you update the device from NSM, the following
log fields display 0 (or unknown):
• domain
• rulebase
• policy
• rule number
• source zone
• destination zone
After you update the imported device configuration using NSM, the appropriate values
are displayed for log entries from the device.
When you import a device configuration,the Log Viewer displaysthe appropriate values
for the device's log entries. This feature eliminates the need to update the device after
importing it.
For moredetailedinformation about adding and importing devices with staticand dynamic
IP addresses and verifying imported device configurations, see “Adding Devices” in the
Network and Security Manager Administration Guide.
Related Topics About Device Creation on page 23•
• Supported Add Device Workflows for M-series and MX-series Devices on page 24
• Modeling Devices Overview on page 26
• Adding Multiple Devices Using Automatic Discovery (JUNOS Software Devices Only)
on page 27
• Adding Device Groups Overview on page 27
Modeling Devices Overview
For an undeployed M-series or MX-series device, you can create a device configuration
in NSM, and then install that device configuration on the physical device.
Adding a single undeployed device to NSM is a four-stage process:
1. Model the device in the UI.
2. Create the device object configuration.
3. Activate the device.
4. Update the device configuration.
Copyright © 2010, Juniper Networks, Inc.26
Page 59

Chapter 4: Adding M-series and MX-series Devices Overview
For moredetailedinformation and steps about modeling adevice, see “Modeling Devices”
in the Network and Security Manager Administration Guide.
Related Topics About Device Creation on page 23•
• Supported Add Device Workflows for M-series and MX-series Devices on page 24
• Importing Devices Overview on page 25
• Adding Multiple Devices Using Automatic Discovery (JUNOS Software Devices Only)
on page 27
• Adding Device Groups Overview on page 27
Adding Multiple Devices Using Automatic Discovery (JUNOS Software Devices Only)
You can use automatic discovery to add and import multiple JUNOS software devices
into NSM. You do so by configuring and running discovery rules. For a JUNOS software
device to be discovered by this mechanism, it mustbe configured with astatic IPaddress.
By configuring and running a discovery rule, you can search a network to discover devices
in a specified subnet or within a range of IP addresses. Authentication of the devices is
through administrator login SSHv2 credentials and SNMP community settings, which
you also configure as part of the rule. Devices that match the rules for discovery also
present an SSH key for your verification before the device is added to NSM.
For more detailed information and steps about adding multiple M-series and MX-series
devices using automatic discovery, see “Adding a Device Discovery Rule” and “Running
a Device Discovery Rule” in the Network and Security Manager Administration Guide.
Related Topics About Device Creation on page 23•
• Supported Add Device Workflows for M-series and MX-series Devices on page 24
• Importing Devices Overview on page 25
• Modeling Devices Overview on page 26
• Adding Device Groups Overview on page 27
Adding Device Groups Overview
You can create groups of devices to manage multiple devices at one time. Use device
groups to organize your managed devices, making it easier for you to configure and
manage devices within a domain. You can group devicesby type (such as all the M-series
in a domain), by physical location (such as all the devices in the San Jose office), or
logically (such as all the devices in sales offices throughout western Europe).
Use the groups to:
•
Deploy new or updated device configurations to the entire device group.
•
Deploy new or updated policies to the entire device group.
27Copyright © 2010, Juniper Networks, Inc.
Page 60

M-series and MX-series Devices
Related Topics • About Device Creation on page 23
The devices that you add to a device group must exist; that is, you must have previously
added or modeled the devices in the domain. You can group devices before configuring
them. You can add a device to more than one device group. You can also add a device
group to another device group.
NOTE: You cannot apply a template to a device group. You must apply templates to
individual devices in a device group. If you need to apply the same set of templates to
multiple devices, you can create a single template that includes all the templates that
are to be applied to a device, and then apply the combined template to each device.
For an example of creating a device group, see “Adding Device Groups” in the Network
and Security Manager Administration Guide.
• Supported Add Device Workflows for M-series and MX-series Devices on page 24
• Importing Devices Overview on page 25
• Modeling Devices Overview on page 26
• Adding Multiple Devices Using Automatic Discovery (JUNOS Software Devices Only)
on page 27
Copyright © 2010, Juniper Networks, Inc.28
Page 61

CHAPTER 5
Updating M-series and MX-series Devices
Overview
•
About Updating M-series and MX-series Devices on page 29
•
How the Update Process Works on page 30
•
Job Manager on page 31
•
Tracking Updated Devices Using Job Manager on page 32
•
Reviewing Job Information Displayed in Job Manager on page 33
•
Device States Displayed in Job Manager During Update on page 34
•
Understanding Updating Errors Displayed in the Job Manager on page 35
About Updating M-series and MX-series Devices
When you update a managed device, you modify the running device configuration (the
configuration currently installed on the physical device) with the modeled device
configuration (the configuration currently modeled in Network and Security Manager
(NSM).
You can update a single device, multiple devices, or device groups simultaneously. For
example, if you have created a device group that includes only M-series devices, you can
update the entire device group in a single update procedure. During the update, NSM
displaysthe progressof the update on each individual device so you can see exactly what
is happening. Simultaneous updating also reduces downtime to unaffected devices and
areas of your network.
Updating a device is a three-step process.
1. Ensure that you have configured the device correctly, created and assigned a policy
to the device,and establisheda connection between the device and the management
server.
2. From the Device Managerlaunchpad, select Update Device. The launchpad displays
the Update Device(s) dialog box.
All connected and managed devices appear in the device list. Modeled devices and
devices awaiting import for the first time do not appear.
29Copyright © 2010, Juniper Networks, Inc.
Page 62

M-series and MX-series Devices
3. Select the devices or device groups you want to update and click Apply Changes.
NSM updates the selected devices or device groups with the modeled configuration.
NSM uses centralized control and tracking to indicate when you need to update a device,
and to follow the progress of the device configuration you are updating. Before updating
your managed devices, you can use other NSM modules and tools to identify devices
that need to be updated, validate their modeled configurations, and preview how those
devices accept the new configuration. After updating, you can use the same tools to
verify a successful update. These tools include:
•
Audit Log Viewer—This NSM module records changes made to a device configuration.
The audit log entry also identifies the administrator who performed the change, shows
when the change was updated on the device, and provides a history of change details.
•
ConfigurationSummaries—These tools provide apreview of the modeled configuration,
enabling you to compare it with the configuration that is running on the device. Use
configuration summaries to ensure the modeled configuration is consistent with what
you want to update on the device.
•
Job Manager—This NSM module tracks the status of running and completed update
processes. The Job Manager displays details of the update process in a dedicated
information window and includes the update’s success or failure and errors involved
in a failed update.
For more information about updating devices, including knowing when to update, using
preview tools, performingupdates,tracking updates and rebooting devices, see“Updating
Devices” in the Network and Security Manager Administration Guide.
Related Topics How the Update Process Works on page 30•
• Job Manager on page 31
• Tracking Updated Devices Using Job Manager on page 32
• Reviewing Job Information Displayed in Job Manager on page 33
• Device States Displayed in Job Manager During Update on page 34
• Understanding Updating Errors Displayed in the Job Manager on page 35
How the Update Process Works
After you have successfully added the device to NSM, reviewed the device configuration,
updated the device, and have the managed device functioning normally, an event might
occur on the managed device that requires a change to the device configuration. For
example, malicious traffic might have entered your network, requiring you to update the
device to detect and prevent that attack.
Copyright © 2010, Juniper Networks, Inc.30
Page 63

Chapter 5: Updating M-series and MX-series Devices Overview
1. Using the NSM monitoring tools, you learn of the attack and locate the cause of the
event. Using NSM modules such as the Realtime Monitor and Log Viewer, you
determine the exact attack that penetrated the device. From the Report Manager,
you also determine what rule in the security policy was ineffective in blocking the
attack.
2. You update the modeled device configuration, editing the configuration to detect
and prevent the attack from entering your network again.
3. Before updating the running configuration, you review the modeled device
configuration. Using a delta configuration summary, compare the modeled
configurationwith therunning configuration on the device toconfirm thedifferences.
Fine-tune the modeled configuration, if needed.
4. When you are confident that the modeled configuration is valid, update the device.
NSM updates the running configuration with only the new changes (delta). During
the update, you track the update progressusing JobManager in realtime andobserve
the transfer of the configuration from NSM to the device.
If the update is unsuccessful, use the information in the Job information dialog box
to correct the problems in the modeled configuration.
Related Topics About Updating M-series and MX-series Devices on page 29•
Job Manager
5. After updating, run a second delta configuration summary to identify any remaining
differences between the modeled configuration and the running configuration on
the device. When the delta configuration summary reveals no differences between
the new configuration and the old configuration on the device, you have successfully
updated the running configuration.
• Job Manager on page 31
• Tracking Updated Devices Using Job Manager on page 32
• Reviewing Job Information Displayed in Job Manager on page 33
• Device States Displayed in Job Manager During Update on page 34
• Understanding Updating Errors Displayed in the Job Manager on page 35
You canview theprogress of communication to and fromyour devices inthe JobManager,
that is located in the Administer panel. NSM sends commands to managed devices at
your request, typically to import, update or reboot devices, and view configuration and
delta configuration summaries. When you send a command to a device or group of
devices, NSM creates a job for that command and displays information about that job
in the Job Manager module.
Job Manager tracks the progress of the command as it travels to the device and back to
the management system. Each job contains:
31Copyright © 2010, Juniper Networks, Inc.
Page 64

M-series and MX-series Devices
Related Topics About Updating M-series and MX-series Devices on page 29•
•
Name of the command
•
Date and time the command was sent
•
Completion status for each device that received the command
•
Detailed description of command progress
•
Command output, such as a configuration list or command-line interface (CLI) changes
on the device
NOTE: Job Manager configurationsummaries and job information details do not display
passwordsin the list of CLI commands for administratorsthat do not have the assigned
activity “View Device Passwords.” By default, only the super administrator has this
assigned activity.
• How the Update Process Works on page 30
• Tracking Updated Devices Using Job Manager on page 32
• Reviewing Job Information Displayed in Job Manager on page 33
• Device States Displayed in Job Manager During Update on page 34
• Understanding Updating Errors Displayed in the Job Manager on page 35
Tracking Updated Devices Using Job Manager
Use JobManager to track device updates in real time. You canview the status ofa running
update and the status of completed updates in the Job Manager module.
When you send a command to a device or group ofdevices using NSM, the management
system creates a job for that command and displays information about that job in the
Job Information dialog box. The command you send is called a directive.
Job Manager includes the following utilities and information:
•
View Controls—Use View controls to set the information level you want displayed in
Job Manager:
•
Expand All displays all devices associated with a directive type.
•
Collapse All displays the directive type.
•
Job Type (Directive) List—Displays the job type (directives) and associated timestamp
completionstatus information. All currentand completed jobsappear,including device
updates. However, if you have not yet performed an update using NSM, the Job List
does not display an Update Configuration directive.
Copyright © 2010, Juniper Networks, Inc.32
Page 65

Chapter 5: Updating M-series and MX-series Devices Overview
•
Notification Controls—Enables you to manually view job completion status.
•
Job Information—Enables you to view job information, including errors, job completion
status, job state, automatic job completion notification setting, and start time of job.
Related Topics About Updating M-series and MX-series Devices on page 29•
• How the Update Process Works on page 30
• Job Manager on page 31
• Reviewing Job Information Displayed in Job Manager on page 33
• Device States Displayed in Job Manager During Update on page 34
• Understanding Updating Errors Displayed in the Job Manager on page 35
Reviewing Job Information Displayed in Job Manager
The Job Information dialog box displays the changing device states as the directive is
executed. Device state changes, error messages, and warning messages are displayed
in real time. A sample Job Information dialog box is shown in Figure 3 on page 33.
Figure 3: Job Information Dialog Box
Job Manager tracks the overall progress of one or more jobs executed on a single device.
For multiple device updates, Job Manager tracks the progress of each job on each device
in addition to the overall progress for all devices. To view the job status for an individual
device (including error messages and percent complete), select the device in the Percent
Complete pane; the status appears in the Output pane.
The job information includes:
33Copyright © 2010, Juniper Networks, Inc.
Page 66

M-series and MX-series Devices
•
Job Type—The type of task being tracked. Job types include Update Device, Reboot
Device, and Config Summary. Job type is also known as a directive.
•
Timestamp—The time at which NSM began executing the directive.
•
Admin Name—The name of the administrator logged into NSM.
•
Status—The current state of the job.
•
Completion—The number of jobs completed out of the total number of jobs.
•
Percent—The percentage oftotal jobssuccessfullyexecuted. When performing multiple
jobs on multiple devices, this field displays the percentage complete for each device.
When the job has completed, successfully or unsuccessfully, this field displays 100%.
•
Name—The name of the device on which the job is executed.
•
Description—The current state of the job.
•
Completion—The percentage of a job that has executed successfully.
•
Output—Displays the content of the update, including commands that have been
interpretedfrom the NSM data model into device-specific commands, errormessages,
and existing commands deleted from the device. The Output Display Region displays
all errors, warnings,device verification output, and devicestate information associated
with the job.
NOTE: If the Job Information dialog box might contain Chinese, Japanese, or Korean
characters, you must uncheck the Fixed Font box to display them.
NOTE: Job Manager configurationsummaries and job information details do not display
passwordsin the list of CLI commands for administratorsthat do not have the assigned
activity “View Device Passwords.” By default, only the super administrator has this
assigned activity.
Related Topics About Updating M-series and MX-series Devices on page 29•
• How the Update Process Works on page 30
• Job Manager on page 31
• Tracking Updated Devices Using Job Manager on page 32
• Device States Displayed in Job Manager During Update on page 34
• Understanding Updating Errors Displayed in the Job Manager on page 35
Device States Displayed in Job Manager During Update
During an update, the managed device changes device state. You can view the current
device state in real time in the State Description field of the Job Information dialog box.
Table 6 on page 35 lists the states that a device can have.
Copyright © 2010, Juniper Networks, Inc.34
Page 67

Chapter 5: Updating M-series and MX-series Devices Overview
Table 6: Device States During Update
DescriptionDevice State
No update activity has occurred on the device.None
Related Topics About Updating M-series and MX-series Devices on page 29•
Loading in Progress
Pending
Converting Data Model to
Device Data Model
Successful Completion
Failed
• How the Update Process Works on page 30
• Job Manager on page 31
• Tracking Updated Devices Using Job Manager on page 32
• Reviewing Job Information Displayed in Job Manager on page 33
• Understanding Updating Errors Displayed in the Job Manager on page 35
NSM is sending the update image to the flash memory of the
device.
Device is accepting the parameters from the update
configuration that has been sent to the device flash memory.
The parameters that have been set in the NSM configuration
are being changed to corresponding device-specific CLI
commands that execute on the device.
Device has successfully been updated with the modeled
configuration.
Device has not been successfully updated with the modeled
configuration. The Job Information dialog box displays error
messages and error codes.
Understanding Updating Errors Displayed in the Job Manager
When anupdate fails forany reason, Job Managerdisplays error codesand errormessages
that can help you identify and locate the problem. Typical errors include:
•
The modeled configuration contained invalid values that the device could not process.
•
During theupdate process, theconnection between the managed device andthe Device
Server was lost.
•
The modeled configuration caused the managed device to lose its connection to NSM.
•
An exclusive lock on the configuration prevented NSM from completing an update.
This error is specific to devices running the Device Management Interface (DMI), such
as the M-series and MX-series devices.
For these update errors, the Job Information dialog box displays the job status as “Failed.”
Figure 4 on page 36 shows that on December 4 a configuration update to an MX960
failed. The super user was locked out by the root user as indicated in the text of the error
35Copyright © 2010, Juniper Networks, Inc.
Page 68

M-series and MX-series Devices
that shows lock Failed and configuration database locked by: root. For an M-series or
MX-series device, NSM attempts to acquire an exclusive lock on the candidate
configurationso thatthe updatecan proceed. In this instance, the root user was updating
the configuration, probably from the CLI, preventing NSM from locking and successfully
updating the configuration.
Figure 4: Failed Update Job Information Dialog Box
In the Job Information dialog box, the update:
•
Successfully checked sanity
•
Unsuccessfully attempted to lock the configuration that was already locked by the
root user
At the end of the error message, there are some suggestions as to how to proceed. In
this particular case, the second solution, > request system logout pid xxxx, is the
appropriate action. From the CLI, the request system logout pid pid command can be
used to forcibly log out the root user. The root user is represented by pid pid, which
indicatesthe user session using thespecified managementprocess identifier (PID). After
the root user is locked out, you can try to update the configuration again. NSM should
lock the configuration and continue successfully.
Copyright © 2010, Juniper Networks, Inc.36
Page 69

Chapter 5: Updating M-series and MX-series Devices Overview
After a device is updated, you can run a delta configuration summary to determine any
remaining differences between the modeled configurationand the running configuration;
the output of this summary appears in the Job Information dialog box. For successful
updates, no discrepancies arefound or displayed. For failed updates, the Job Information
dialog box lists the remaining discrepancies.
You can also check the Connection Status and Configuration Status columns for the
device in the Realtime Monitor to determine whether the device is running. For more
information, see “About the Realtime Monitor.”
Related Topics • About Updating M-series and MX-series Devices on page 29
• How the Update Process Works on page 30
• Job Manager on page 31
• Tracking Updated Devices Using Job Manager on page 32
• Reviewing Job Information Displayed in Job Manager on page 33
• Device States Displayed in Job Manager During Update on page 34
37Copyright © 2010, Juniper Networks, Inc.
Page 70

M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.38
Page 71

PART 3
Configuring M-series and MX-series
Devices
•
Configuring M-series and MX-series Devices Overview on page 41
•
Configuring Access on page 47
•
Configuring Accounting Options on page 71
•
Configuring Applications on page 79
•
Configuring Bridge Domains on page 81
•
Configuring Chassis on page 97
•
Configuring Authentication on page 113
•
Configuring Class of Service Features on page 121
•
Configuring Event Options on page 151
•
Configuring Firewall on page 159
•
Configuring Forwarding Options on page 183
•
Configuring Interfaces on page 207
•
Configuring Multicast Snooping Options on page 237
•
Configuring Policy Options on page 241
•
Configuring Protocols on page 251
•
Configuring Routing Options on page 361
•
Configuring Security on page 389
•
Configuring Services on page 391
•
Configuring SNMP on page 463
39Copyright © 2010, Juniper Networks, Inc.
Page 72

M-series and MX-series Devices
Copyright © 2010, Juniper Networks, Inc.40
Page 73

CHAPTER 6
Configuring M-series and MX-series
Devices Overview
•
About Device Configuration on page 41
•
M-series and MX-series Device Configuration Settings Supported in NSM on page 42
•
Configuring Device Features on page 44
•
Example: Configuration of Interfaces for MPLS in the CLI and NSM on page 45
About Device Configuration
This topic does not provide extensive details for configuring features on M-series and
MX-series devices in Network and Security Manager (NSM). For detailed information
about configuring specific features for M-series and MX-series devices, see the following
JUNOS software configuration guide:
•
JUNOS System Basics Configuration Guide for system, chassis, security, and access
parameters.
•
JUNOS Network Interfaces Configuration Guide for interface parameters.
•
JUNOS Policy Framework Configuration Guide for forwarding options and firewall
parameters.
•
JUNOS Configuration and Diagnostic Automation Guide for event options parameters.
•
JUNOS Network Management Configuration Guide for SNMP and accounting options
parameters.
•
JUNOS Routing Protocols Configuration Guide for routing options and protocols
parameters.
•
JUNOS VPNs Configuration Guide for policy options parameters.
•
JUNOS Class of Service Configuration Guide for class of service parameters.
•
JUNOS Software with Enhanced Services Security Configuration Guide for security
parameters.
•
JUNOS Services Interface Configuration Guide for service parameters.
41Copyright © 2010, Juniper Networks, Inc.
Page 74

M-series and MX-series Devices
For more information about editing device configurations in NSM, including using device
templates, using configuration groups, and using configuration groups with templates,
see “Configuring Devices” in the Network and Security Manager Administration Guide.
Related Topics M-series and MX-series Device Configuration Settings Supported in NSM on page 42•
• Configuring Device Features on page 44
• Example: Configuration of Interfaces for MPLS in the CLI and NSM on page 45
M-series and MX-series Device Configuration Settings Supported in NSM
You can configure JUNOS software features in NSM. Although the configuration screens
rendered in NSM look different than the JUNOS command-line interface (CLI), the
top-level configuration elements mostly correspond to commands in the CLI.
NOTE: For detailed information about configuring specific features for M-series and
MX-series devices, see the appropriate JUNOS software configuration guide.
NOTE: Because the NSM device-side configurationguides are not updated on the same
release schedule as the JUNOS releases, consult the JUNOS Software Documentation
for information about configuration settings that might occur in NSM and not in the
device-side configuration guides or vice versa.
Table 7 on page 42 provides a general guideline of the CLI hierarchy levels that are
supported in the NSMconfigurationtree. Forthe exact parameters available,double-click
the device in the Device Manager and select the Configuration tab. The configuration
tree appears in the main display area with all parameters viewable or configurable from
NSM.
Table 7: The JUNOS Configuration Hierarchy and the NSM Configuration
Tree
Available in the NSM
Configuration TreeHierarchy Level
Yesedit access
Yesedit accounting-options
Yesedit applications
Yesedit bridge domains
Yesedit chassis
Yesedit class-of-service
Copyright © 2010, Juniper Networks, Inc.42
Page 75

Chapter 6: Configuring M-series and MX-series Devices Overview
Table 7: The JUNOS Configuration Hierarchy and the NSM Configuration
Tree (continued)
Available in the NSM
Configuration TreeHierarchy Level
Yesedit dynamic profiles
Noedit ethernet-switching-options
Yesedit event-options
Yesedit firewall
Yesedit forwarding-options
Yesedit groups
Yesedit interfaces
Yesedit logical-systems
Yesedit multicast-snooping-options
Noedit poe
Yesedit policy-options
Yes.edit protocols
Yesedit routing-instances]
Yesedit routing-options
Noedit schedulers
Yesedit security
Yesedit services
Yesedit snmp
Yesedit switch-options
Yesedit system
Noedit virtual-chassis
Noedit vlans
43Copyright © 2010, Juniper Networks, Inc.
Page 76

M-series and MX-series Devices
Related Topics About Device Configuration on page 41•
When you use NSM to edit the software configuration on the device, you initially make
the changes to a device object that models the device in NSM. When you are satisfied
with your configuration changes, you use the Update Device directive to push the
configuration from the device object in NSM to the device itself. At that point, the edited
configuration becomes active.
NOTE: If you import an existing device configuration, NSM automatically imports all
objects defined in that configuration.
For more information about editing device configurations, using device templates, using
configuration groups, and using configuration groups with templates, see “Configuring
Devices” in the Network and Security Manager Administration Guide.
• Configuring Device Features on page 44
• Example: Configuration of Interfaces for MPLS in the CLI and NSM on page 45
Configuring Device Features
You can configure JUNOS software features in NSM. Although the configuration screens
rendered in NSM look different than the JUNOS command-line interface (CLI), the
top-level configuration elements mostly correspond to commands in the CLI.
NOTE: For detailed information about configuring specific features for M-series and
MX-series devices, see the appropriate JUNOS software configuration guide.
To configure a device that has been added, imported, or modeled in NSM:
1. In the navigation tree, select Device Manager > Devices.
2. Open the device configuration using one of the following methods:
•
Double-click the device object in the security device tree or the device list.
•
Select the device object and then click the Edit icon.
•
Right-click the device object and select Edit.
3. Select the Configuration tab.
The device configuration tree appears in the left pane.
4. In the device navigation tree, select a function heading to see device parameters,
and then select the configuration parameter you want to configure.
5. Make your changes to the device configuration, then choose one of the following:
•
•
Click OK to save your changes and close the device configuration.
Click Apply to save your changes and continue making changes.
Copyright © 2010, Juniper Networks, Inc.44
Page 77

Chapter 6: Configuring M-series and MX-series Devices Overview
•
Click Cancel to discard all changes and close the device configuration.
To reset a device feature to its default value, right-click on the feature name in the device
editor and select Revert to template/default value.
Related Topics About Device Configuration on page 41•
• M-series and MX-series Device Configuration Settings Supported in NSM on page 42
• Example: Configuration of Interfaces for MPLS in the CLI and NSM on page 45
Example: Configuration of Interfaces for MPLS in the CLI and NSM
With NSM you can manage most of the parameters that you can configure through the
CLI. Although the configuration screens rendered in NSM look different, the top-level
configurationelements essentially correspond to commands inthe CLI. Youcan configure
an M-series or MX-series device using the CLI, then import the configuration into NSM to
create a template and apply it to multiple devices.
The following figures show the same configuration displayed in the CLI and the NSM UI.
Figure 5 on page 45 shows the CLI configuration of MPLS at the [edit protocols mpls]
hierarchy level, and Figure 6 on page 46 shows the same configuration in the NSM UI.
Figure 5 on page 45 shows output for the show command in configuration mode. At this
level, the show command typically displays the entire configuration for the device. For
the purpose of this illustration, all parts of the configuration not relevant to our example
were removed [...Output Truncated...]. The remaining output shows the protocols and
MPLS hierarchy levels. Included at the hierarchy level are three interfaces, two Fast
Ethernet interfaces (fe) and one Gigabit Ethernet interface (ge).
Figure 5: MPLS Configuration in the CLI
Figure 6 on page 46 shows the NSM UI with the same information as in the CLI example.
On the left, the Navigation tree is expanded at Protocols, and then further expanded at
MPLS, similar to the CLI hierarchy levels. Within MPLS, Interface is highlighted, indicating
that the information on the right relates to interfaces within MPLS. The information in
the NSM UI example is similar to the information in the CLI example though the
presentation is somewhat different.
45Copyright © 2010, Juniper Networks, Inc.
Page 78

M-series and MX-series Devices
Figure 6: MPLS Configuration in NSM
In addition, Figure 6 on page 46 shows parts of the configuration tree that are grayed out,
indicating that those particular parameters are not supported for the M-series and
MX-series devices.
Related Topics • About Device Configuration on page 41
• M-series and MX-series Device Configuration Settings Supported in NSM on page 42
• Configuring Device Features on page 44
Copyright © 2010, Juniper Networks, Inc.46
Page 79

CHAPTER 7
Configuring Access
•
Configuring Address-Assignment Pools (NSM Procedure) on page 47
•
Configuring Access Address Pools (NSM Procedure) on page 50
•
Configuring Access Group Profile (NSM Procedure) on page 51
•
Configuring the LDAP Options (NSM Procedure) on page 52
•
Configuring the LDAP Server (NSM Procedure) on page 53
•
Configuring Access Profiles for L2TP or PPP Parameters (NSM Procedure) on page 54
•
Configuring the RADIUS for Subscriber Access Management, L2TP, or PPP (NSM
Procedure) on page 68
•
Configuring the SecurID Server (NSM Procedure) on page 69
•
Configuring the Access Profile (NSM Procedure) on page 70
Configuring Address-Assignment Pools (NSM Procedure)
The address-assignment pool feature supports subscriber management functionality
by enablingyou to createaddress pools that canbe sharedby different clientapplications.
An address-assignment pool can support either IPv4 address or IPv6 addresses. You
cannot use the same pool for both types of address.
To configure address assignment pools in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Address Assignment.
5. Add or modify settings as specified in Table 8 on page 48.
6. Click one:
•
•
OK—Saves the changes.
Cancel—Cancels the modifications.
47Copyright © 2010, Juniper Networks, Inc.
Page 80

M-series and MX-series Devices
Table 8: Address Assignment Configuration Details
Your ActionTask
Configure the name of an
address-assignment pool.
1. Click Pool next to Address Assignment.
2. Click Add new entry next to Pool.
3. In the Name box, enter the name to be assigned to the
address-assignment pool.
4. In the Comment box, enter the comment.
Configuresubnet information
for an IPv4
address-assignment pool.
Configure address pools that
can be used by different
client applications.
1. Click Family next to Pool.
2. Click Enable Feature check box to enable the option.
3. Click Inet next to Family.
4. In the Comment box, enter the comment.
5. In the Network box, enter thesubnet informationfor an IPv4
address-assignment pool.
1. Click Dhcp Attributes next to Inet.
2. In the Comment box, enter the comment.
3. From the Maximum Lease Time list, select the maximum
length of time, in seconds, that the lease is held for a client
if the client does not renew the lease. This is equivalent to
DHCP option 51.
4. From the Grace Period list, select the amount of time that
the client retains the address lease after the lease expires.
Range: 0 through 4,294,967,295 seconds
Default: 0 (no grace period)
5. In the Domain Name box, enter the name of the domain in
which clients search for a DHCP server host.
6. In the Boot File box, enter the location of the boot file on the
boot server. The filename can include a pathname.
7. In the Boot Server box, enter the name of the boot server
advertised to DHCP clients.
8. In the Tftp Server box, enter the IP address of the TFTP
server.
9. Fromthe Netbios Node Type list, select oneof the following
node types.
b-node—Broadcast node
h-node—Hybrid node
m-node—Mixed node
p-node—Peer-to-peer node
10. In theSip Server Domain Name box, enter thedomain name
of the SIP outbound proxy server.
Configure one or more
Domain NameSystem (DNS)
name servers availableto the
client to resolve
hostname-to-client
mappings.
1. Click Name Sever next to Dhcp Attributes.
2. Click Add new entry next to Name Server.
3. In the Name box, enter the IP addressesof thedomain name
servers, listed in order of preference.
4. In the Comment box, enter the comment.
Copyright © 2010, Juniper Networks, Inc.48
Page 81

Chapter 7: Configuring Access
Table 8: Address Assignment Configuration Details (continued)
Your ActionTask
Specify user-defined options
that are added to client
packets.
1. Click Option next to Dhcp Attributes.
2. Click Add new entry next to Option.
3. From the Name list, selectthe ID number to beused toindex
the option.
4. In the Comment box, enter the comment.
5. Click Flag next to option.
6. From the Flag list, select the flag type.
Specify alist ofmatch criteria
used to determine which
named address range in the
address-assignment pool to
use.
Specify one or more routers
located on the client’s
subnet.
Specify SIP Servers list of
IPv6 addresses available to
the client.
1. Click Option Match next to Dhcp Attributes.
2. In the Comment box, enter the comment.
3. Click Option 82 next to Option Match.
4. In the Comment box, enter the comment.
5. Click Circuit Id next to Option 82.
6. Click Add new entry next to Circuit Id.
7. In theName box, enter the name of the address-assignment
pool range to be used.
8. In the Comment box, enter the comment.
9. In the Range box, enter the range.
10. Click Remote Id next to Option 82.
11. Click Add new entry next to Remote Id.
12. In the Namebox, enter the name of the address-assignment
pool range to be used.
13. In the Comment box, enter the comment.
14. In the Range box, enter the range.
1. Click Router next to Dhcp Attributes.
2. Click Add new entry next to Router.
3. In the Name box, enter the name of the router.
4. In the Comment box, enter the comment.
1. Click Sip Server Address next to Dhcp Attributes.
2. Click Add new entry next to Sip Server Address.
3. In the Namebox, enterthe SIP Servers list of IPv6 addresses
available to the client.
4. In the Comment box, enter the comment.
Specify one ormore NetBIOS
name servers (NBNS) that
the client uses to resolve
NetBIOS names.
1. Click Wins Server next to Dhcp Attributes.
2. Click Add new entry next to Wins Server.
3. In theName box, enterthe IP address of eachNetBIOS name
server.
4. In the Comment box, enter the comment.
49Copyright © 2010, Juniper Networks, Inc.
Page 82

M-series and MX-series Devices
Table 8: Address Assignment Configuration Details (continued)
Your ActionTask
Configure a static binding for
the specified client.
1. Click Host next to Inet.
2. Click Add new entry next to Host.
3. In the Name box, enter the name of the client.
4. In the Comment box, enter the comment.
5. In the Hardware Address box, enter the MAC address of the
client
6. In the IP Address box, enter the IP version 4 (IPv4) address.
Configure a named range of
IPv4 addresses or IPv6
prefixes, used within an
address-assignment pool.
1. Click Range next to Inet.
2. Click Add new entry next to Range.
3. In the Name box, enter the name assigned to the range of
IPv4 addresses or IPv6 prefixes.
4. In the Comment box, enter the comment.
5. In the Low box, enter the lower limit of an address range or
IPv6 prefix range.
6. In the High box, enter the upper limit of an address range or
IPv6 prefix range.
Related Topics Configuring Access Address Pools (NSM Procedure) on page 50•
• Configuring Access Group Profile (NSM Procedure) on page 51
Configuring Access Address Pools (NSM Procedure)
With an address pool, you configure an address or address range. When you define an
address pool for a client, the layer2 tunneling protocol network server (LNS) allocates
IP addresses for clients from an address pool.
To configure access address pools in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Address Pool.
5. Add or modify settings as specified in Table 9 on page 51.
6. Click one:
•
•
OK—Saves the changes.
Cancel—Cancels the modifications.
Copyright © 2010, Juniper Networks, Inc.50
Page 83

Related Topics Configuring Address-Assignment Pools (NSM Procedure) on page 47•
Table 9: Access Address Pool Configuration Details
Your ActionTask
Allocate IP addresses for
clients.
1. Click Address Pool next to Access.
2. Click Add new entry next to Address Pool.
3. In theName box, enter the nameto beassigned to anaddress
pool.
4. In the Comment box, enter the comment.
5. Click Address next to address-pool.
Select one of the following:
•
Select address to enter the address.
•
Select address-range to configure the address range.
a. In the Low box, enter the lower limit of an address
range.
b. In the High box, enter the upper limit of an address
range.
Chapter 7: Configuring Access
• Configuring Access Group Profile (NSM Procedure) on page 51
Configuring Access Group Profile (NSM Procedure)
You can configure the group profile to define the Point-to-Point Protocol (PPP) using
the Group Profile option.
To configure access group profile in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Group Profile.
5. Add or modify settings as specified in Table 10 on page 51.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 10: Access Group Profile Configuration Details
Configure the group profile.
Your ActionTask
1. Click Add new entry next to Group Profile.
2. In the Name box, enter the name to be assigned to the group
profile.
3. In the Comment box, enter the comment.
51Copyright © 2010, Juniper Networks, Inc.
Page 84

M-series and MX-series Devices
Table 10: Access Group Profile Configuration Details (continued)
Your ActionTask
Configure the PPP
attributes for a group
profile.
1. Click Ppp next to group-profile.
2. Select the Enable Feature check box to enable the option.
3. In the Comment box, enter the comment.
4. From the FramedPool list, selectthe configured address pool.
5. From the Idle Timeout list, select the number of seconds a
user can remain idle before the session is terminated.
Range: 0 through 4,294,967,295 seconds
Default: 0
6. From the Keep Alive list, select the time period that must
elapse before the JUNOS Software checks the status of the
Point-to-Point Protocol (PPP) session by sending an echo
request to the peer.
Range: 0 through 32,767 seconds
Default: 10
7. In the Primary Dns box, enter the primary Domain Name
System (DNS) server.
8. In the Secondary Dns box, enterthe secondary Domain Name
System (DNS) server.
9. In the Primary Wins box, enter the primary Windows Internet
name server.
10. In the Secondary Wins box, enter the secondary Windows
Internet name server.
11. From the Encapsulation Overhead list, select the number of
bytes used as encapsulation overhead for the session.
12. Select the Cell Overhead check box to configure the session
to use Asynchronous Transfer Mode (ATM)-aware egress
shaping on the IQ2 PIC.
13. In the Interface Id box, enter the interface identifier.
Related Topics Configuring Access Profiles for L2TP or PPP Parameters (NSM Procedure) on page 54•
Configuring the LDAP Options (NSM Procedure)
You can configure Lightweight Directory Access Protocols (LDAP) options using the
LDAP Options option.
To configure LDAP options in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Ldap Options.
5. Add or modify settings as specified in Table 11 on page 53.
6. Click one:
Copyright © 2010, Juniper Networks, Inc.52
Page 85

•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 11: LDAP Options Configuration Details
Your ActionTask
Configure lightweight
directory access protocol
options.
1. In the Comment box, enter the comment.
2. From the Revert Interval list, select the amount of time the
router waits after a server has become unreachable.
Range: 60 through 4,294,967,295
Default: 600
3. In the Base Distinguished Name box, enter the suffix when
assembling user distinguished name (DN) or base DN under
which to search for user DN.
Chapter 7: Configuring Access
Derive user distinguished
name from common-name
and
base-distinguished-name.
1. Click Assemble next to Ldap Options.
2. Select one of the following:
•
•
Related Topics Configuring the LDAP Server (NSM Procedure) on page 53•
Configuring the LDAP Server (NSM Procedure)
You can configure the Lightweight Directory Access Protocol (LDAP) server using the
LDAP Server option.
assemble—To derive user distinguished name from
common-name and base-distinguished-name.
a. In the Comment box, enter the comment.
b. In the Common Name box, enter the common name.
search—To search for user's distinguished name.
a. In the Comment box, enter the comment.
b. In the Search Filter box, enter the filter to use in
search.
c. Click Admin Search next to Search.
d. In the Comment box, enter the comment.
e. In the Distinguished Name box, enter the user
distinguished name.
f. In the Password box, enter the password.
To configure LDAP server in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Ldap Server.
5. Add or modify settings as specified in Table 12 on page 54.
6. Click one:
53Copyright © 2010, Juniper Networks, Inc.
Page 86

M-series and MX-series Devices
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 12: LDAP Server Configuration Details
Your ActionTask
Configure LDAP server.
1. Click Add new entry next to Ldap Server.
2. In the Name box, enter the name of the server.
3. In the Comment box, enter the comment.
4. From the Portlist, select theport number on which to contact
the Radius server (LDAP server)
5. In the Source Address box, enter a valid IPv4 address
configured on one of the router interfaces. On M Series
routers only, the source address can be an IPv6 address and
the UDP source port is 514.
6. From the Routing Instances list, select the routing instance
name.
7. From theRetry list, selectthe numberof timesthat therouter
is allowed to attempt to contact a Radius server.
Range: 1 through 10
Default: 3
8. From the Timeout list, select the amount of time that the
local router waits toreceive aresponse froma Radius server.
Range: 3 through 90
Default: 5
Related Topics Configuring the LDAP Options (NSM Procedure) on page 52•
Configuring Access Profiles for L2TP or PPP Parameters (NSM Procedure)
You can set up access profiles tovalidate Layer 2 Tunneling Protocol (L2TP) connections
and sessionrequests. You can configure multiple profiles.You canalso configure multiple
clients for each profile. See the following topics:
1. Configuring Access Profile (NSM Procedure) on page 55
2. Configuring Accounting Parameters for Access Profiles (NSM Procedure) on page 55
3. Configuring the Accounting Order (NSM Procedure) on page 56
4. Configuring the Authentication Order (NSM Procedure) on page 57
5. Configuring the Authorization Order (NSM Procedure) on page 57
6. Configuring the L2TP Client (NSM Procedure) on page 58
7. Configuring the Client Filter Name (NSM Procedure) on page 59
8. Configuring the LDAP Options (NSM Procedure) on page 60
9. Configuring the LDAP Server (NSM Procedure) on page 61
10. Configuring the Provisioning Order (NSM Procedure) on page 62
Copyright © 2010, Juniper Networks, Inc.54
Page 87

11. Configuring RADIUS Parameters for AAA Subscriber Management (NSM
Procedure) on page 63
12. Configuring the RADIUS Parameters (NSM Procedure) on page 66
13. Configuring the RADIUS for Subscriber Access Management, L2TP, or PPP (NSM
Procedure) on page 67
14. Configuring Session Limit (NSM Procedure) on page 67
Configuring Access Profile (NSM Procedure)
To configure an access profile in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 13 on page 55.
Chapter 7: Configuring Access
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 13: Access Profile Properties Configuration Details
Your ActionTask
Configure access profile
properties.
1. Click Add new entry next to Profile.
2. In the Name box, enter the name of the profile.
3. In the Comment box, enter the comment.
Configuring Accounting Parameters for Access Profiles (NSM Procedure)
To configure RADIUS accounting parameters for an access profile in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 14 on page 56.
6. Click one:
•
•
OK—Saves the changes.
Cancel—Cancels the modifications.
55Copyright © 2010, Juniper Networks, Inc.
Page 88

M-series and MX-series Devices
Table 14: Accounting Parameter Configuration Details
Your ActionTask
Configure RADIUS
accounting parameters and
enable RADIUS accounting
for an access profile.
1. Click Add new entry next to Profile.
2. Click Accounting next to profile.
3. In the Comment box, enter the comment.
4. Select theAccountingStop On Failurecheck box toconfigure
RADIUS accounting to send an Acct-Stop message when
client access fails AAA but the AAA server grants access.
5. Select the Accounting Stop On Access Deny check box to
configureRADIUS accounting to send anAcct-Stop message
when the AAA server denies a client access.
6. Select the Immediate Update check box to configure the
router to send an Acct-Update message to the RADIUS
accounting server on receipt of a response (for example, an
ACK or timeout) to the Acct-Start message.
7. From the Update Interval list, select the amount of time
between updates, in minutes.
Range: 10 through 1440 minutes
Default: no updates
8. From the Statistics list, select the time statistics for the
sessions being managed by AAA.
Configuring the Accounting Order (NSM Procedure)
Beginning with JUNOS Release 8.0, you can configure RADIUS accounting for an Layer
2 Tunneling Protocol (L2TP) profile. With RADIUS accounting enabled, Juniper Networks
routers, acting as RADIUS clients, can notify the RADIUS server about user activities such
as software logins, configuration changes, and interactive commands. When you enable
RADIUS accounting for an L2TP profile, it applies to all the clients within that profile. You
must enable RADIUS accounting on at least one LT2P profile for the RADIUS
authentication server to send accounting stop and start messages.
To configure accounting order in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 15 on page 57.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Copyright © 2010, Juniper Networks, Inc.56
Page 89

Table 15: Accounting Order Configuration Details
Your ActionTask
Configure the accounting
order.
1. Click Add new entry next to Profile.
2. Click Accounting Order next to Profile.
3. Click Add new entry next to Accounting Order.
4. In the New accounting-order window, select radius to use
RADIUS accounting method.
Configuring the Authentication Order (NSM Procedure)
You can configure the order in which the JUNOS Software tries different authentication
methods when authenticating peers. For each access attempt, the software tries the
authentication methods in order, from first to last.
To configure authentication order in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
Chapter 7: Configuring Access
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 16 on page 57.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 16: Authentication Order Configuration Details
Your ActionTask
Configurethe authentication
order.
1. Click Add new entry next to Profile.
2. Click Authentication Order next to Profile.
3. Click Add new entry next to Accounting Order.
4. In the New authentication-order window, select the order in
which the JUNOS Software tries different authentication
methods when verifying that a client can access the router.
Configuring the Authorization Order (NSM Procedure)
To configure authorization order in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
57Copyright © 2010, Juniper Networks, Inc.
Page 90

M-series and MX-series Devices
5. Add or modify settings as specified in Table 17 on page 58.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 17: Authorization Order Configuration Details
Configure the authorization
order.
Configuring the L2TP Client (NSM Procedure)
To configure the Layer 2 Tunneling Protocol (L2TP) Client in NSM:
Your ActionTask
1. Click Add new entry next to Profile.
2. Click Authorization Order next to Profile.
3. Click Add new entry next to Authorization Order.
4. In the New authorization-order window, select the
authorization order.
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 18 on page 58.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 18: Client Configuration Details
Your ActionTask
Configure the client.
1. Click Add new entry next to Profile.
2. Click Client next to Profile.
3. Click Add new entry next to Client.
4. In the Name box, enter the client name.
5. In the Comment box, enter the comment.
6. In the Chap Secret box, enter the secret key associated with
a peer.
7. In the pap password box, enter the Password Authentication
Protocol (PAP) password.
Configure a client group.
1. Click Client Group next to client.
2. Click Add new entry next to Client Group.
3. In the New client-group window, enter the client group.
Copyright © 2010, Juniper Networks, Inc.58
Page 91

Table 18: Client Configuration Details (continued)
Your ActionTask
Configure a firewall user.
1. Click Firewall User next to client.
2. In the Comment box, enter the comment.
3. In the Password box, enter the password.
Chapter 7: Configuring Access
ConfigurePPP propertiesfor
a client profile.
1. Click Ppp next to client.
2. Select ike to configure an IKE access profile.
a. In the Comment box, enter the comment.
b. Select Initiate Dead Peer Detection to detect inactive
c. In the Interface Id box, enter the interface identifier.
d. Click Allowed Proxy Pair next to Ike.
e. Click Add new entry next to Allowed Proxy Pair.
f. In the Local box, enter the network address of the local
g. In the Remote box, enter the network address of the
h. In the Comment box, enter the comment.
i. Click Pre Shared Key next to Ike.
Configuring the Client Filter Name (NSM Procedure)
peers on dynamic IPSec tunnels.
peer.
remote peer.
a. Select pre-shared-key to configure the key used to
authenticate a dynamic peer during IKE phase 1
negotiation and select the key.
b. In the Comment box, enter the comment.
c. Click Ascii Text next to Pre Shared key.
d. In the ascii-text box, enter the string.
e. Select Ike-policy to authenticate dynamic peers
during IKE negotiation and select the policy name.
To configure restrictions on client names in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 22 on page 62.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
59Copyright © 2010, Juniper Networks, Inc.
Page 92

M-series and MX-series Devices
Table 19: Client Filter Name Configuration Details
Your ActionTask
Configure the restrictions on
client names.
1. Click Add new entry next to Profile.
2. Click Client Name Filter next to profile.
3. In the Comment box, enter the comment.
4. In the Domain Name box, enter the domain name.
5. In theSeparatorbox, enter the separator character in domain
6. From the Count list, select the number of separator
Configuring the LDAP Options (NSM Procedure)
To configure Lightweight Directory Access Protocol (LDAP) options in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
name.
instances.
Range: 0 through 255
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 20 on page 60.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 20: Ldap Options Configuration Details
Your ActionTask
Configure lightweight
directory access protocol
options.
1. Click Add new entry next to Profile.
2. Click Ldap Options next to profile.
3. In the Comment box, enter the comment.
4. From the Revert Interval list, select the amount of time the
router waits after a server has become unreachable.
Range: 60 through 4294967295
Default: 600
5. In the Base Distinguished Name box, enter the suffix when
assembling user distinguished name (DN) or base DN under
which to search for user DN.
Copyright © 2010, Juniper Networks, Inc.60
Page 93

Chapter 7: Configuring Access
Table 20: Ldap Options Configuration Details (continued)
Your ActionTask
Derive user distinguished
name from common-name
and
base-distinguished-name.
1. Click Assemble next to Ldap Options.
2. Select one of the following:
•
assemble—To derive user distinguished name from
common-name and base-distinguished-name.
a. In the Comment box, enter the comment.
b. In the Common Name box, enter the common name.
•
search—To search for user's distinguished name.
a. In the Comment box, enter the comment.
b. In the Search Filter box, enter the filter to use in
search.
c. Click Admin Search next to Search.
d. In the Comment box, enter the comment.
e. In the Distinguished Name box, enter the user
distinguished name.
f. In the Password box, enter the password.
Configuring the LDAP Server (NSM Procedure)
To configure Lightweight Directory Access Protocol (LDAP) server in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 21 on page 62.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
61Copyright © 2010, Juniper Networks, Inc.
Page 94

M-series and MX-series Devices
Table 21: Ldap Server Configuration Details
Your ActionTask
Configure LDAP server.
1. Click Add new entry next to Profile.
2. Click Ldap Server next to profile.
3. Click Add new entry next to Ldap Server.
4. In the Name box, enter the name of the server.
5. In the Comment box, enter the comment.
6. From the Port list, selectthe port number on whichto contact
the RADIUS server (LDAP server)
7. In the Source Address box, enter a valid IPv4 address
configuredon one of the router interfaces.On MSeries routers
only, the source address canbe an IPv6 addressand the UDP
source port is 514.
8. From the Routing Instances list, select the routing instance
name.
9. From the Retry list, selectthe number oftimes that the router
is allowed to attempt to contact a RADIUS server.
Range: 1 through 10
Default: 3
10. From the Timeout list, select the amount of time that the
localrouter waits toreceive aresponse from aRADIUS server.
Range: 3 through 90
Default: 5
Configuring the Provisioning Order (NSM Procedure)
To configure the provisioning order in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 22 on page 62.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 22: Provisioning Order Configuration Details
Your ActionTask
Configure the provisioning
order.
1. Click Add new entry next to Profile.
2. Click Provisioning Order next to profile.
3. Click Add new entry next to Provisioning Order.
4. In the New provisioning-order window, select the order in
which provisioning mechanisms are used.
Copyright © 2010, Juniper Networks, Inc.62
Page 95

Chapter 7: Configuring Access
Configuring RADIUS Parameters for AAA Subscriber Management (NSM Procedure)
You can specify the RADIUS parameters for the subscriber access manager feature. You
can specify the IP addresses of the RADIUS servers used for authentication and
accounting, options that provide configuration information for the RADIUS servers, and
how RADIUS attributes are used.
To configure RADIUS parameters for AAA subscriber management in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 23 on page 63.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 23: RADIUS Parameter Configuration Details
Your ActionTask
Configure the RADIUS
parameters.
Specify a list of the RADIUS
accounting servers used for
accountingfor DynamicHost
Configuration Protocol
(DHCP), Layer 2 Tunneling
Protocol (L2TP), and
Point-to-Point Protocol
(PPP) clients.
1. Click Add new entry next to Profile.
2. Click Radius next to Profile.
3. In the Comment box, enter the comment.
1. Click Attributes next to Radius.
2. In the Comment box, enter the comment.
63Copyright © 2010, Juniper Networks, Inc.
Page 96

M-series and MX-series Devices
Table 23: RADIUS Parameter Configuration Details (continued)
Your ActionTask
Configure the router to
exclude the specified
attributes from the specified
type of RADIUS message.
1. Click Exclude next to Radius.
2. In the Comment box, enter the comment.
3. From the listed RADIUS attribute type, select the attributes
to be excluded.
RADIUS attribute types are:
•
accounting-authentic—RADIUS attribute 45,
Acct-Authentic
•
accounting-delay-time—RADIUS attribute 41,
Acct-Delay-Time
•
accounting-session-id—RADIUS attribute 44,
Acct-Session-Id
•
accounting-terminate-cause—RADIUS attribute 49,
Acct-Terminate-Cause
•
called-station-id—RADIUS attribute 30, Called-Station-Id
•
calling-station-id—RADIUSattribute 31, Calling-Station-Id
•
class—RADIUS attribute 25, Class
•
dhcp-gi-address—Juniper VSA 26-57, DHCP-GI-Address
•
dhcp-mac-address—Juniper VSA 26-56,
DHCP-MAC-Address
•
Dhcp Options— Excludes RADIUS attribute 26-55
•
event-timestamp—RADIUS attribute 55,
Event-Timestamp
•
framed-ip-address—RADIUS attribute 8,
Framed-IP-Address
•
framed-ip-netmask—RADIUS attribute 9,
Framed-IP-Netmask
•
input-filter—Juniper VSA 26-10, Ingress-Policy-Name
•
input-gigapackets—Juniper VSA 26-42,
Acct-Input-Gigapackets
•
input-gigawords—RADIUS attribute 52,
Acct-Input-Gigawords
•
interface-description—Juniper VSA26-53, Interface-Desc
•
nas-identifier—RADIUS attribute 32, NAS-Identifier
•
nas-port—RADIUS attribute 5, NAS-Port
•
nas-port-id—RADIUS attribute 87, NAS-Port-Id.
•
nas-port-type—RADIUS attribute 61, NAS-Port-Type
•
output-filter—Juniper VSA 26-11, Egress-Policy-Name
•
output-gigapackets—Juniper VSA 25-43,
Acct-Output-Gigapackets
•
output-gigawords—RADIUS attribute 53,
Acct-Output-Gigawords
Copyright © 2010, Juniper Networks, Inc.64
Page 97

Chapter 7: Configuring Access
Table 23: RADIUS Parameter Configuration Details (continued)
Your ActionTask
Configure the routerto ignore
the specified attributes in
RADIUS Access-Accept
messages.
1. Click Ignore next to client.
2. In the Comment box, enter the comment.
3. Select the following check boxes to ignore the specified
attributes:
•
output-filter—Egress-Policy-Name (VSA 26-11)
•
input-filter—Ingress-Policy-Name (VSA 26-10)
•
framed-ip-netmask—Framed-IP-Netmask (RADIUS
attribute 9
•
logical-system-routing-instance—Virtual-Router (VSA
26-1)
Specify a list of the RADIUS
authentication servers used
to authenticate DHCP, L2TP,
and PPP clients.
Configure the options used
by RADIUS authentication
and accounting servers.
1. Click Authentication Server next to Radius.
2. Click Add new entry next to Authentication Server.
3. In the New authentication-server window, enter the IPv4
address.
1. Click Options next to Radius.
2. In the Comment box, enter the comment.
3. Select the Ethernet Port Type Virtual check box to specify
a port type of virtual.
4. From the Interface Description Format list, select the
information that is included in or omitted from the interface
description that the router passes to RADIUS for inclusion in
the RADIUS attribute 87 (NAS-Port-Id).
Select one of the following:
•
sub-interface—To specify the subinterface.
•
adapter—To specify the adapter.
5. In the Nas Identifier box, enter a string in the range from 1 to
64 characters.
6. From the Accounting Session Id Format list, select the
format the router uses to identify the accounting session.
Select one of the following:
•
decimal—To use the decimal format.
•
description—To use the generic format, in the form jnpr
interface-specifier:subscriber-session-id.
Default: decimal
7. From the Revert Interval list, select the amount of time the
router waits after a server has become unreachable.
Range: 60 through 4294967295 seconds
Default: 600 seconds
8. Select the vlan-nas-port-stacked-format check box to
configure RADIUS attribute 5 (NAS-Port) to include the
S-VLAN ID, in addition to the VLAN ID, for subscribers on
Ethernet interfaces.
65Copyright © 2010, Juniper Networks, Inc.
Page 98

M-series and MX-series Devices
Table 23: RADIUS Parameter Configuration Details (continued)
Your ActionTask
Configure the RADIUS client
to use the extended format
for RADIUS attribute 5
(NAS-Port) and specify the
width of the fields in the
NAS-Port attribute.
1. Click Nas Port Extended Format next to Options.
2. In the Comment box, enter the comment.
3. From the Slot Width list, select the number of bits in theslot
field.
4. From the AdapterWidth list, select the number of bits in the
adapter field.
5. From the PortWidth list, selectthe numberof bitsin the port
field.
6. From the Stacked Vlan Width list, select the number of bits
in the SVLAN ID field.
7. From the Vlan Width list, select the number of bits in the
VLAN ID field.
Configuring the RADIUS Parameters (NSM Procedure)
You can specify the options used by the RADIUS authentication and accounting servers.
To configure the RADIUS parameters in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 24 on page 66.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
NOTE: To create a profile, the device should be in the in-device policy mode.
Table 24: RADIUS Parameters Configuration Details
Your ActionTask
Configure the RADIUS
parameters.
1. Click Add new entry next to Profile.
2. Click Radius Options next to Profile.
3. In the Comment box, enter the comment.
4. From the Revert Interval list, select the amount of time the
router waits after a server has become unreachable.
Default: 600 seconds
Copyright © 2010, Juniper Networks, Inc.66
Page 99

Chapter 7: Configuring Access
Configuring the RADIUS for Subscriber Access Management, L2TP, or PPP (NSM Procedure)
You can configure RADIUS for subscriber access management, L2TP, or PPP. The servers
are tried in order and in a round-robin fashion until a valid response is received from one
of the servers or until all the configured retry limits are reached.
To configure the RADIUS server in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 25 on page 67.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 25: RADIUS Server Configuration Details
Your ActionTask
Configure the RADIUS
servers.
1. Click Add new entry next to Profile
2. Click Radius Server next to Profile.
3. In the Name box, enter the profile name.
4. In the Comment box, enter the comment.
5. From thePort list, selectthe portnumber onwhich tocontact
the RADIUS server.
Default: 1812 (as specified in RFC 2865)
6. In the Secret box, enterthe password to usewith theRADIUS
server. The secret password used by the local router must
match that used by the server.
7. From the Timeout list, select the amount of time that the
local router waits toreceivea responsefrom a RADIUSserver.
Range: 3 through 90 seconds
Default: 3 seconds
8. From the Retry list, selectthe numberof times that therouter
is allowed to attempt to contact a RADIUS server.
Range: 1 through 10
Default: 3
9. In the Source Address box, enter a valid IPv4 address
configured on one of the router interfaces.
10. From the Routing Instance list, select the routing instance
name.
Configuring Session Limit (NSM Procedure)
To configure the timeout limit in NSM:
67Copyright © 2010, Juniper Networks, Inc.
Page 100

M-series and MX-series Devices
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Profile.
5. Add or modify settings as specified in Table 26 on page 68.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Table 26: Session Limit Configuration Details
Your ActionTask
Configure the timeout
interval.
1. Click Add new entry next to Profile.
2. Click Session Options next to Profile.
3. In the Comment box, enter the comment.
4. From the Client Idle Timeout list, select the time in minutes
of idleness after which access is denied.
Range: 1 through 255 minutes
5. From the Client Session Timeout list, select the time in
minutes since initial access after which access is denied.
Configure a client group.
1. Click Client Group next to Session Option.
2. Click Add new entry next to Client Group.
3. In the New client-group window, enter the client group.
Configuring the RADIUS for Subscriber Access Management, L2TP, or PPP (NSM
Procedure)
You can configure RADIUS for subscriber access management, layer 2 tunneling protocol
(L2TP), orpoint-to-point protocol (PPP). The servers are tried inorder andin a round-robin
fashion until a validresponse is received from one of the servers or until all the configured
retry limits are reached.
To configure the RADIUS server in NSM:
1. In the NSM navigation tree, select Device Manager > Devices.
2. Click the Device Tree tab, and then double-click the device to select it.
3. Click the Configuration tab. In the configuration tree, expand Access.
4. Select Radius Server.
5. Add or modify settings as specified in Table 27 on page 69.
6. Click one:
•
OK—Saves the changes.
•
Cancel—Cancels the modifications.
Copyright © 2010, Juniper Networks, Inc.68
 Loading...
Loading...