Juniper JUNOSE 11.1.X - SYSTEM EVENT LOGGING REFERENCE GUIDE 3-24-2010, JUNOSe 11.1.X Reference Manual
Page 1
JUNOSe™ Software
for E Series™ Broadband Services Routers
System Event Logging Reference Guide
Release 11.1.x
Juniper Networks, Inc.
1194 North Mathilda Avenue
Sunnyvale, California 94089
USA
408-745-2000
www.juniper.net
Published: 2010-03-24
Page 2

Juniper Networks, the Juniper Networks logo, JUNOS, NetScreen, ScreenOS, and Steel-Belted Radius are registered trademarks of Juniper Networks, Inc. in
the United States and other countries. JUNOSe is a trademark of Juniper Networks, Inc. All other trademarks, service marks, registered trademarks, or
registered service marks are the property of their respective owners.
Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper Networks reserves the right to change, modify, transfer, or
otherwise revise this publication without notice.
Products made or sold by Juniper Networks or components thereof might be covered by one or more of the following patents that are owned by or licensed
to Juniper Networks: U.S. Patent Nos. 5,473,599, 5,905,725, 5,909,440, 6,192,051, 6,333,650, 6,359,479, 6,406,312, 6,429,706, 6,459,579, 6,493,347,
6,538,518, 6,538,899, 6,552,918, 6,567,902, 6,578,186, and 6,590,785.
JUNOSe™ Software for E Series™ Broadband Services Routers System Event Logging Reference Guide
Release 11.1.x
Copyright © 2010, Juniper Networks, Inc.
All rights reserved. Printed in USA.
Writing: Krupa Chandrashekar, Subash Babu Asokan, Mark Barnard, Diane Florio, Bruce Gillham, Sarah Lesway-Ball, Brian Wesley Simmons, Fran Singer
Editing: Benjamin Mann
Illustration: Nathaniel Woodward
Cover Design: Edmonds Design
Revision History
April 2010—FRS JUNOSe 11.1.x
The information in this document is current as of the date listed in the revision history.
YEAR 2000 NOTICE
Juniper Networks hardware and software products are Year 2000 compliant. The JUNOS Software has no known time-related limitations through the year
2038. However, the NTP application is known to have some difficulty in the year 2036.
ii ■
Page 3

END USER LICENSE AGREEMENT
READ THIS END USER LICENSE AGREEMENT (“AGREEMENT”) BEFORE DOWNLOADING, INSTALLING, OR USING THE SOFTWARE. BY DOWNLOADING,
INSTALLING, OR USING THE SOFTWARE OR OTHERWISE EXPRESSING YOUR AGREEMENT TO THE TERMS CONTAINED HEREIN, YOU (AS CUSTOMER
OR IF YOU ARE NOT THE CUSTOMER, AS A REPRESENTATIVE/AGENT AUTHORIZED TO BIND THE CUSTOMER) CONSENT TO BE BOUND BY THIS
AGREEMENT. IF YOU DO NOT OR CANNOT AGREE TO THE TERMS CONTAINED HEREIN, THEN (A) DO NOT DOWNLOAD, INSTALL, OR USE THE SOFTWARE,
AND (B) YOU MAY CONTACT JUNIPER NETWORKS REGARDING LICENSE TERMS.
1. The Parties. The parties to this Agreement are (i) Juniper Networks, Inc. (if the Customer’s principal office is located in the Americas) or Juniper Networks
(Cayman) Limited (if the Customer’s principal office is located outside the Americas) (such applicable entity being referred to herein as “Juniper”), and (ii)
the person or organization that originally purchased from Juniper or an authorized Juniper reseller the applicable license(s) for use of the Software (“Customer”)
(collectively, the “Parties”).
2. The Software. In this Agreement, “Software” means the program modules and features of the Juniper or Juniper-supplied software, for which Customer
has paid the applicable license or support fees to Juniper or an authorized Juniper reseller, or which was embedded by Juniper in equipment which Customer
purchased from Juniper or an authorized Juniper reseller. “Software” also includes updates, upgrades and new releases of such software. “Embedded
Software” means Software which Juniper has embedded in or loaded onto the Juniper equipment and any updates, upgrades, additions or replacements
which are subsequently embedded in or loaded onto the equipment.
3. License Grant. Subject to payment of the applicable fees and the limitations and restrictions set forth herein, Juniper grants to Customer a non-exclusive
and non-transferable license, without right to sublicense, to use the Software, in executable form only, subject to the following use restrictions:
a. Customer shall use Embedded Software solely as embedded in, and for execution on, Juniper equipment originally purchased by Customer from Juniper
or an authorized Juniper reseller.
b. Customer shall use the Software on a single hardware chassis having a single processing unit, or as many chassis or processing units for which Customer
has paid the applicable license fees; provided, however, with respect to the Steel-Belted Radius or Odyssey Access Client software only, Customer shall use
such Software on a single computer containing a single physical random access memory space and containing any number of processors. Use of the
Steel-Belted Radius or IMS AAA software on multiple computers or virtual machines (e.g., Solaris zones) requires multiple licenses, regardless of whether
such computers or virtualizations are physically contained on a single chassis.
c. Product purchase documents, paper or electronic user documentation, and/or the particular licenses purchased by Customer may specify limits to
Customer’s use of the Software. Such limits may restrict use to a maximum number of seats, registered endpoints, concurrent users, sessions, calls,
connections, subscribers, clusters, nodes, realms, devices, links, ports or transactions, or require the purchase of separate licenses to use particular features,
functionalities, services, applications, operations, or capabilities, or provide throughput, performance, configuration, bandwidth, interface, processing,
temporal, or geographical limits. In addition, such limits may restrict the use of the Software to managing certain kinds of networks or require the Software
to be used only in conjunction with other specific Software. Customer’s use of the Software shall be subject to all such limitations and purchase of all applicable
licenses.
d. For any trial copy of the Software, Customer’s right to use the Software expires 30 days after download, installation or use of the Software. Customer
may operate the Software after the 30-day trial period only if Customer pays for a license to do so. Customer may not extend or create an additional trial
period by re-installing the Software after the 30-day trial period.
e. The Global Enterprise Edition of the Steel-Belted Radius software may be used by Customer only to manage access to Customer’s enterprise network.
Specifically, service provider customers are expressly prohibited from using the Global Enterprise Edition of the Steel-Belted Radius software to support any
commercial network access services.
The foregoing license is not transferable or assignable by Customer. No license is granted herein to any user who did not originally purchase the applicable
license(s) for the Software from Juniper or an authorized Juniper reseller.
4. Use Prohibitions. Notwithstanding the foregoing, the license provided herein does not permit the Customer to, and Customer agrees not to and shall
not: (a) modify, unbundle, reverse engineer, or create derivative works based on the Software; (b) make unauthorized copies of the Software (except as
necessary for backup purposes); (c) rent, sell, transfer, or grant any rights in and to any copy of the Software, in any form, to any third party; (d) remove
any proprietary notices, labels, or marks on or in any copy of the Software or any product in which the Software is embedded; (e) distribute any copy of
the Software to any third party, including as may be embedded in Juniper equipment sold in the secondhand market; (f) use any ‘locked’ or key-restricted
feature, function, service, application, operation, or capability without first purchasing the applicable license(s) and obtaining a valid key from Juniper, even
if such feature, function, service, application, operation, or capability is enabled without a key; (g) distribute any key for the Software provided by Juniper
to any third party; (h) use the Software in any manner that extends or is broader than the uses purchased by Customer from Juniper or an authorized Juniper
reseller; (i) use Embedded Software on non-Juniper equipment; (j) use Embedded Software (or make it available for use) on Juniper equipment that the
Customer did not originally purchase from Juniper or an authorized Juniper reseller; (k) disclose the results of testing or benchmarking of the Software to
any third party without the prior written consent of Juniper; or (l) use the Software in any manner other than as expressly provided herein.
5. Audit. Customer shall maintain accurate records as necessary to verify compliance with this Agreement. Upon request by Juniper, Customer shall furnish
such records to Juniper and certify its compliance with this Agreement.
■ iii
Page 4

6. Confidentiality. The Parties agree that aspects of the Software and associated documentation are the confidential property of Juniper. As such, Customer
shall exercise all reasonable commercial efforts to maintain the Software and associated documentation in confidence, which at a minimum includes
restricting access to the Software to Customer employees and contractors having a need to use the Software for Customer’s internal business purposes.
7. Ownership. Juniper and Juniper’s licensors, respectively, retain ownership of all right, title, and interest (including copyright) in and to the Software,
associated documentation, and all copies of the Software. Nothing in this Agreement constitutes a transfer or conveyance of any right, title, or interest in
the Software or associated documentation, or a sale of the Software, associated documentation, or copies of the Software.
8. Warranty, Limitation of Liability, Disclaimer of Warranty. The warranty applicable to the Software shall be as set forth in the warranty statement that
accompanies the Software (the “Warranty Statement”). Nothing in this Agreement shall give rise to any obligation to support the Software. Support services
may be purchased separately. Any such support shall be governed by a separate, written support services agreement. TO THE MAXIMUM EXTENT PERMITTED
BY LAW, JUNIPER SHALL NOT BE LIABLE FOR ANY LOST PROFITS, LOSS OF DATA, OR COSTS OR PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES,
OR FOR ANY SPECIAL, INDIRECT, OR CONSEQUENTIAL DAMAGES ARISING OUT OF THIS AGREEMENT, THE SOFTWARE, OR ANY JUNIPER OR
JUNIPER-SUPPLIED SOFTWARE. IN NO EVENT SHALL JUNIPER BE LIABLE FOR DAMAGES ARISING FROM UNAUTHORIZED OR IMPROPER USE OF ANY
JUNIPER OR JUNIPER-SUPPLIED SOFTWARE. EXCEPT AS EXPRESSLY PROVIDED IN THE WARRANTY STATEMENT TO THE EXTENT PERMITTED BY LAW,
JUNIPER DISCLAIMS ANY AND ALL WARRANTIES IN AND TO THE SOFTWARE (WHETHER EXPRESS, IMPLIED, STATUTORY, OR OTHERWISE), INCLUDING
ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE, OR NONINFRINGEMENT. IN NO EVENT DOES JUNIPER
WARRANT THAT THE SOFTWARE, OR ANY EQUIPMENT OR NETWORK RUNNING THE SOFTWARE, WILL OPERATE WITHOUT ERROR OR INTERRUPTION,
OR WILL BE FREE OF VULNERABILITY TO INTRUSION OR ATTACK. In no event shall Juniper’s or its suppliers’ or licensors’ liability to Customer, whether
in contract, tort (including negligence), breach of warranty, or otherwise, exceed the price paid by Customer for the Software that gave rise to the claim, or
if the Software is embedded in another Juniper product, the price paid by Customer for such other product. Customer acknowledges and agrees that Juniper
has set its prices and entered into this Agreement in reliance upon the disclaimers of warranty and the limitations of liability set forth herein, that the same
reflect an allocation of risk between the Parties (including the risk that a contract remedy may fail of its essential purpose and cause consequential loss),
and that the same form an essential basis of the bargain between the Parties.
9. Termination. Any breach of this Agreement or failure by Customer to pay any applicable fees due shall result in automatic termination of the license
granted herein. Upon such termination, Customer shall destroy or return to Juniper all copies of the Software and related documentation in Customer’s
possession or control.
10. Taxes. All license fees payable under this agreement are exclusive of tax. Customer shall be responsible for paying Taxes arising from the purchase of
the license, or importation or use of the Software. If applicable, valid exemption documentation for each taxing jurisdiction shall be provided to Juniper prior
to invoicing, and Customer shall promptly notify Juniper if their exemption is revoked or modified. All payments made by Customer shall be net of any
applicable withholding tax. Customer will provide reasonable assistance to Juniper in connection with such withholding taxes by promptly: providing Juniper
with valid tax receipts and other required documentation showing Customer’s payment of any withholding taxes; completing appropriate applications that
would reduce the amount of withholding tax to be paid; and notifying and assisting Juniper in any audit or tax proceeding related to transactions hereunder.
Customer shall comply with all applicable tax laws and regulations, and Customer will promptly pay or reimburse Juniper for all costs and damages related
to any liability incurred by Juniper as a result of Customer’s non-compliance or delay with its responsibilities herein. Customer’s obligations under this
Section shall survive termination or expiration of this Agreement.
11. Export. Customer agrees to comply with all applicable export laws and restrictions and regulations of any United States and any applicable foreign
agency or authority, and not to export or re-export the Software or any direct product thereof in violation of any such restrictions, laws or regulations, or
without all necessary approvals. Customer shall be liable for any such violations. The version of the Software supplied to Customer may contain encryption
or other capabilities restricting Customer’s ability to export the Software without an export license.
12. Commercial Computer Software. The Software is “commercial computer software” and is provided with restricted rights. Use, duplication, or disclosure
by the United States government is subject to restrictions set forth in this Agreement and as provided in DFARS 227.7201 through 227.7202-4, FAR 12.212,
FAR 27.405(b)(2), FAR 52.227-19, or FAR 52.227-14(ALT III) as applicable.
13. Interface Information. To the extent required by applicable law, and at Customer's written request, Juniper shall provide Customer with the interface
information needed to achieve interoperability between the Software and another independently created program, on payment of applicable fee, if any.
Customer shall observe strict obligations of confidentiality with respect to such information and shall use such information in compliance with any applicable
terms and conditions upon which Juniper makes such information available.
14. Third Party Software. Any licensor of Juniper whose software is embedded in the Software and any supplier of Juniper whose products or technology
are embedded in (or services are accessed by) the Software shall be a third party beneficiary with respect to this Agreement, and such licensor or vendor
shall have the right to enforce this Agreement in its own name as if it were Juniper. In addition, certain third party software may be provided with the
Software and is subject to the accompanying license(s), if any, of its respective owner(s). To the extent portions of the Software are distributed under and
subject to open source licenses obligating Juniper to make the source code for such portions publicly available (such as the GNU General Public License
(“GPL”) or the GNU Library General Public License (“LGPL”)), Juniper will make such source code portions (including Juniper modifications, as appropriate)
available upon request for a period of up to three years from the date of distribution. Such request can be made in writing to Juniper Networks, Inc., 1194
N. Mathilda Ave., Sunnyvale, CA 94089, ATTN: General Counsel. You may obtain a copy of the GPL at http://www.gnu.org/licenses/gpl.html, and
a copy of the LGPL at http://www.gnu.org/licenses/lgpl.html.
15. Miscellaneous. This Agreement shall be governed by the laws of the State of California without reference to its conflicts of laws principles. The provisions
of the U.N. Convention for the International Sale of Goods shall not apply to this Agreement. For any disputes arising under this Agreement, the Parties
hereby consent to the personal and exclusive jurisdiction of, and venue in, the state and federal courts within Santa Clara County, California. This Agreement
constitutes the entire and sole agreement between Juniper and the Customer with respect to the Software, and supersedes all prior and contemporaneous
iv ■
Page 5

agreements relating to the Software, whether oral or written (including any inconsistent terms contained in a purchase order), except that the terms of a
separate written agreement executed by an authorized Juniper representative and Customer shall govern to the extent such terms are inconsistent or conflict
with terms contained herein. No modification to this Agreement nor any waiver of any rights hereunder shall be effective unless expressly assented to in
writing by the party to be charged. If any portion of this Agreement is held invalid, the Parties agree that such invalidity shall not affect the validity of the
remainder of this Agreement. This Agreement and associated documentation has been written in the English language, and the Parties agree that the English
version will govern. (For Canada: Les parties aux présentés confirment leur volonté que cette convention de même que tous les documents y compris tout
avis qui s'y rattaché, soient redigés en langue anglaise. (Translation: The parties confirm that this Agreement and all related documentation is and will be
in the English language)).
■ v
Page 6

vi ■
Page 7

Abbreviated Table of Contents
About the Documentation xxi
Part 1 Chapters
Chapter 1 System Logging Overview 3
Chapter 2 Event Categories 23
Part 2 Event Categories
Chapter 3 A Commands 27
Chapter 4 B Commands 35
Chapter 5 C Commands 51
Chapter 6 D Commands 57
Chapter 7 E Commands 79
Chapter 8 F Commands 81
Chapter 9 G and H Commands 87
Chapter 10 I Commands 91
Chapter 11 L Commands 129
Chapter 12 M Commands 145
Chapter 13 N Commands 165
Chapter 14 O Commands 169
Chapter 15 P Commands 195
Chapter 16 Q Commands 217
Chapter 17 R Commands 219
Chapter 18 S Commands 233
Chapter 19 T Commands 251
Chapter 20 U Commands 259
Chapter 21 V Commands 261
Part 3 Index
Index 267
Abbreviated Table of Contents ■ vii
Page 8
JUNOSe 11.1.x System Event Logging Reference Guide
viii ■
Page 9
Table of Contents
About the Documentation xxi
E Series and JUNOSe Documentation and Release Notes ..............................xxi
Audience ......................................................................................................xxi
E Series and JUNOSe Text and Syntax Conventions .....................................xxi
Obtaining Documentation ..........................................................................xxiii
Documentation Feedback ...........................................................................xxiii
Requesting Technical Support .....................................................................xxiii
Self-Help Online Tools and Resources ..................................................xxiv
Opening a Case with JTAC ....................................................................xxiv
Part 1 Chapters
Chapter 1 System Logging Overview 3
Overview of System Logging ...........................................................................3
Log Severity ..............................................................................................3
Log Verbosity ............................................................................................4
Persistent Logs ..........................................................................................4
Logging Platform Considerations .....................................................................5
Configuring Event Logging ..............................................................................5
Configuring Log Severity for Individual and Systemwide Logs .......................10
Configuring Log Verbosity for Individual Logs or All Logs ..............................14
Setting the Timestamp for Log Messages .......................................................14
Configuring Log Filters ..................................................................................16
Turning Off Log Filters ..................................................................................17
Monitoring Logging System Events ................................................................17
Chapter 2 Event Categories 23
Part 2 Event Categories
Chapter 3 A Commands 27
aaaAtm1483Cfg ............................................................................................27
aaaEngineGeneral .........................................................................................28
Table of Contents ■ ix
Page 10
JUNOSe 11.1.x System Event Logging Reference Guide
aaaQosCfg .....................................................................................................28
aaaServerGeneral ..........................................................................................29
aaaUserAccess ...............................................................................................29
addressServerGeneral ....................................................................................30
ar1AaaServerGeneral .....................................................................................30
atm ...............................................................................................................31
atm1483 .......................................................................................................32
atm1483VcClass ............................................................................................32
atmAal5 ........................................................................................................33
atmVcClass ....................................................................................................33
auditIpsec ......................................................................................................34
Chapter 4 B Commands 35
bfdAdaptivity .................................................................................................35
bfdEvents ......................................................................................................36
bfdGeneral ....................................................................................................36
bfdSession .....................................................................................................37
bgpConnections ............................................................................................37
bgpDampening ..............................................................................................38
bgpEvents .....................................................................................................39
bgpGeneral ....................................................................................................40
bgpGracefulRestart ........................................................................................41
bgpIpv6NextHops ..........................................................................................42
bgpKeepAlives ...............................................................................................42
bgpMessages .................................................................................................43
bgpNeighborChanges ....................................................................................44
bgpNextHops ................................................................................................45
bgpRoutes .....................................................................................................45
bridge ............................................................................................................48
bridgeEngine .................................................................................................49
bridgingMgr ...................................................................................................49
bulkStats .......................................................................................................50
Chapter 5 C Commands 51
cacGeneral ....................................................................................................51
cacIntf ...........................................................................................................52
cliCommand ..................................................................................................52
cliGeneral ......................................................................................................53
connectionManager .......................................................................................53
cops ..............................................................................................................54
copsPr ...........................................................................................................54
coreDump .....................................................................................................55
ctreeLog ........................................................................................................56
x ■ Table of Contents
Page 11
Table of Contents
Chapter 6 D Commands 57
dcm ...............................................................................................................58
dcmEngineGeneral ........................................................................................58
debounceEvents ............................................................................................59
debounceGeneral ..........................................................................................59
dhcpCapture ..................................................................................................60
dhcpExternal .................................................................................................60
dhcpExternalEngine ......................................................................................61
dhcpGeneral ..................................................................................................61
dhcpIssuLog ..................................................................................................62
dhcpLocalClients ...........................................................................................63
dhcpLocalGeneral ..........................................................................................63
dhcpLocalHighAvailability .............................................................................64
dhcpLocalPool ...............................................................................................64
dhcpLocalProtocol .........................................................................................65
dhcpOfferLog ................................................................................................66
dhcpPbeGeneral ............................................................................................66
dhcpProxyGeneral .........................................................................................67
dhcpRelayGeneral .........................................................................................67
dhcpRelayNvWriterGeneral ...........................................................................68
dhcpv6Client .................................................................................................68
dhcpv6DemuxGeneral ...................................................................................69
dhcpv6LsGeneral ...........................................................................................69
dismanEventMgr ...........................................................................................70
dnsGeneralLog ..............................................................................................71
dosProtection ................................................................................................71
ds1 ................................................................................................................72
ds3 ................................................................................................................72
dvmrpGeneral ...............................................................................................73
dvmrpGracefulRestart ...................................................................................74
dvmrpMcastTable ..........................................................................................75
dvmrpProbeRcv ............................................................................................75
dvmrpProbeSent ...........................................................................................76
dvmrpRtTable ...............................................................................................76
Chapter 7 E Commands 79
ethernet ........................................................................................................79
ethernetStateSession .....................................................................................79
Chapter 8 F Commands 81
fileSystem .....................................................................................................81
flowInspection ...............................................................................................82
flowInspectionEngine ....................................................................................82
flowServicesFirewallAlert ..............................................................................83
flowServicesFirewallAudit ..............................................................................83
Table of Contents ■ xi
Page 12
JUNOSe 11.1.x System Event Logging Reference Guide
frameRelay ....................................................................................................84
fsAgent ..........................................................................................................84
ft1 .................................................................................................................85
ftpClient ........................................................................................................85
ftpServer .......................................................................................................86
Chapter 9 G and H Commands 87
gplaan ...........................................................................................................87
ha ..................................................................................................................87
hdlc ...............................................................................................................88
hotfixGeneral .................................................................................................89
httpServer .....................................................................................................89
Chapter 10 I Commands 91
icImageFixServer ...........................................................................................92
icmpTraffic ....................................................................................................93
icmpv6Traffic ................................................................................................94
icrPartitionManager .......................................................................................95
igmpGeneral ..................................................................................................95
igmpGracefulRestart ......................................................................................96
igmpGroupState ............................................................................................97
ikeCertificateMgr ...........................................................................................98
ikeEnrollment ................................................................................................98
ikepki ............................................................................................................99
interModuleCommunication ..........................................................................99
ipAccessList .................................................................................................100
ipEngine ......................................................................................................101
ipflowstats ...................................................................................................101
ipflowstatsEngine ........................................................................................102
ipGeneral .....................................................................................................102
ipIfCreator ...................................................................................................104
ipInterface ...................................................................................................104
ipNhopTrackerGeneral ................................................................................105
ipProfileMgr ................................................................................................105
ipRoutePolicy ..............................................................................................106
ipRouteTable ...............................................................................................107
ipsecIdDb ....................................................................................................107
ipsecP1Throttler ..........................................................................................108
ipsecXcfgSM ................................................................................................108
ipSubscriberMgr ..........................................................................................109
ipTraffic .......................................................................................................109
ipTunnel ......................................................................................................110
ipv6AccessList .............................................................................................110
ipv6General .................................................................................................111
ipv6Interface ...............................................................................................112
ipv6ProfileMgr .............................................................................................113
ipv6RouteTable ...........................................................................................113
ipv6Traffic ...................................................................................................114
xii ■ Table of Contents
Page 13

Table of Contents
ipv6Types ....................................................................................................115
isisAdjChange ..............................................................................................115
isisAdjPackets ..............................................................................................116
isisBfdEvents ...............................................................................................117
isisChecksumErr ..........................................................................................117
isisGeneral ...................................................................................................118
isisHelloGeneral ...........................................................................................119
isisHelloPackets ...........................................................................................119
isisIpv6Log ..................................................................................................120
isisLdpEvents ..............................................................................................120
isisLocalUpdate ...........................................................................................121
isisMplsTeAdvertisements ...........................................................................122
isisMplsTeEvents .........................................................................................122
isisNsfEvents ...............................................................................................123
isisProtocolErr .............................................................................................123
isisSnpPackets .............................................................................................124
isisSpfEvents ...............................................................................................124
isisSpfStatistics ............................................................................................125
isisSpfTriggers .............................................................................................126
isisUpdatePackets ........................................................................................126
isVoice .........................................................................................................127
itm ..............................................................................................................127
Chapter 11 L Commands 129
l2cGeneral ...................................................................................................130
l2cKeepAlive ...............................................................................................130
l2cPacket .....................................................................................................131
l2tp ..............................................................................................................131
l2tpDialoutGenerator ...................................................................................132
l2tpDisconnectCause ...................................................................................132
l2tpIpLowerBinding .....................................................................................133
l2tpStateMachine .........................................................................................133
lasv6General ................................................................................................134
ldpConnect ..................................................................................................134
ldpGeneral ...................................................................................................135
ldpGracefulRestart .......................................................................................135
ldpHelloMessages ........................................................................................136
ldpHelloMgr .................................................................................................137
ldpInterface .................................................................................................137
ldpMessages ................................................................................................138
ldpPeer ........................................................................................................139
ldpShimInterface .........................................................................................139
ldpSocket ....................................................................................................140
ldpTimer .....................................................................................................141
ldpVpls ........................................................................................................141
ldpWorker ...................................................................................................142
localAddressServerGeneral ..........................................................................142
localAuthServer ...........................................................................................143
localEnableAuthServer .................................................................................143
Table of Contents ■ xiii
Page 14
JUNOSe 11.1.x System Event Logging Reference Guide
localLinePassword .......................................................................................144
Chapter 12 M Commands 145
macroData ..................................................................................................146
macroSchedular ..........................................................................................146
mgtmGeneral ..............................................................................................147
mgtmGracefulRestart ..................................................................................148
mgtmv6General ..........................................................................................148
mgtmv6GracefulRestart ...............................................................................149
mldGeneral ..................................................................................................150
mldGracefulRestart ......................................................................................151
mldGroupState ............................................................................................151
mmcd .........................................................................................................152
mobileIpv4HaBinding ..................................................................................153
mobileIpv4HaEng ........................................................................................153
mobileIpv4HaEvent .....................................................................................154
mobileIpv4HaLog ........................................................................................154
mplsFwdTable .............................................................................................155
mplsGeneral ................................................................................................155
mplsHighAvailability ...................................................................................156
mplsMajorInterface .....................................................................................156
mplsMinorInterface .....................................................................................157
mplsRouter ..................................................................................................158
mplsShimInterface ......................................................................................159
mplsTraffic ..................................................................................................160
mrInfoLog ...................................................................................................160
mrInfoRcvdLog ............................................................................................161
mrInfoSentLog ............................................................................................161
mtraceLog ...................................................................................................162
mtraceRcvdLog ...........................................................................................162
mtraceSentLog ............................................................................................163
multicastTraffic ...........................................................................................163
Chapter 13 N Commands 165
nameResolverLog ........................................................................................165
nfsClient ......................................................................................................165
noneAaaAddrServer ....................................................................................166
noneAaaServer ............................................................................................167
ntpGeneral ..................................................................................................167
Chapter 14 O Commands 169
oam3ahAssociations ....................................................................................170
oam3ahEvents ............................................................................................170
oam3ahPdus ...............................................................................................171
os ................................................................................................................171
ospfElectDr ..................................................................................................172
xiv ■ Table of Contents
Page 15
Table of Contents
ospfGeneral .................................................................................................173
ospfHelloPktsRcvd .......................................................................................174
ospfHelloPktsSent .......................................................................................175
ospfInterface ...............................................................................................176
ospfLdpEvents .............................................................................................176
ospfLsa ........................................................................................................177
ospfNeighbor ...............................................................................................178
ospfPktsRcvd ...............................................................................................178
ospfPktsSent ...............................................................................................179
ospfRestart ..................................................................................................179
ospfRoute ....................................................................................................180
ospfSpfExt ...................................................................................................181
ospfSpfInter .................................................................................................181
ospfSpfIntra .................................................................................................182
ospfTeDatabase ...........................................................................................183
ospfTeSpf ....................................................................................................183
ospfv3ElectDr ..............................................................................................184
ospfv3General .............................................................................................185
ospfv3HelloPktsRcvd ...................................................................................186
ospfv3HelloPktsSent ....................................................................................186
ospfv3Interface ...........................................................................................187
ospfV3Lsa ....................................................................................................188
ospfv3Neighbor ...........................................................................................188
ospfv3PktsRcvd ...........................................................................................189
ospfv3PktsSent ............................................................................................190
ospfv3Route ................................................................................................190
ospfV3SpfExt ...............................................................................................191
ospfV3SpfInter ............................................................................................192
ospfV3SpfIntra ............................................................................................192
Chapter 15 P Commands 195
pimAutoRPRcvdLog .....................................................................................196
pimAutoRPSentLog .....................................................................................197
pimBsrRcvdLog ...........................................................................................197
pimBsrSentLog ............................................................................................198
pimGracefulRestartLog ................................................................................199
pimHelloRcvdLog ........................................................................................199
pimHelloSentLog .........................................................................................200
pimIpv6AutoRPRcvdLog ..............................................................................200
pimIpv6AutoRPSentLog ...............................................................................202
pimIpv6BsrRcvdLog ....................................................................................202
pimIpv6BsrSentLog .....................................................................................203
pimIpv6GracefulRestartLog .........................................................................203
pimIpv6HelloRcvdLog .................................................................................204
pimIpv6HelloSentLog ..................................................................................205
pimIpv6PktsRcvdLog ...................................................................................206
pimIpv6PktsSentLog ....................................................................................206
pimPktsRcvdLog ..........................................................................................207
pimPktsSentLog ..........................................................................................208
Table of Contents ■ xv
Page 16
JUNOSe 11.1.x System Event Logging Reference Guide
pimsmGeneral .............................................................................................208
pimsmMvpn ................................................................................................209
policyMgrAttachment ..................................................................................209
policyMgrGeneral ........................................................................................210
policyMgrPacketLog ....................................................................................210
ppp ..............................................................................................................211
pppoe ..........................................................................................................212
pppoeControlPacket ....................................................................................212
pppPacket ...................................................................................................213
pppStateMachine .........................................................................................214
profileMgr ...................................................................................................214
Chapter 16 Q Commands 217
qm ..............................................................................................................217
qos ..............................................................................................................217
qosAttachment ............................................................................................218
Chapter 17 R Commands 219
radiusAttributes ...........................................................................................219
radiusClient .................................................................................................220
radiusCoAAttributes ....................................................................................220
radiusDisconnectGeneral .............................................................................221
radiusRelayGeneral .....................................................................................222
radiusSendAttributes ...................................................................................222
remOps .......................................................................................................223
resourceThresholdTrap ................................................................................223
ripBfd ..........................................................................................................224
ripGeneral ...................................................................................................225
ripRoute ......................................................................................................225
ripRtTable ...................................................................................................226
routeDownloader ........................................................................................227
routerLog .....................................................................................................227
rsvpAsyncMgr .............................................................................................228
rsvpBfd ........................................................................................................228
rsvpGeneral .................................................................................................229
rsvpGracefulRestart .....................................................................................230
rsvpInterface ...............................................................................................230
rsvpTunnel ..................................................................................................231
Chapter 18 S Commands 233
security .......................................................................................................234
serviceability ...............................................................................................234
serviceMgr ...................................................................................................235
serviceMgrClientSession ..............................................................................235
serviceMgrDcm ...........................................................................................236
serviceMgrMacroManager ...........................................................................236
xvi ■ Table of Contents
Page 17
Table of Contents
serviceMgrPerformance ..............................................................................237
serviceMgrServiceDef ..................................................................................237
serviceMgrServiceInstance ..........................................................................238
serviceMgrServiceSession ............................................................................238
serviceMgrSubscriberSession .......................................................................239
slep .............................................................................................................239
snmp ...........................................................................................................240
snmpIfMib ...................................................................................................241
snmpPduAudit ............................................................................................241
snmpSetPduAudit ........................................................................................242
snmpTrap ....................................................................................................242
sonet ...........................................................................................................243
sonetPath ....................................................................................................243
sonetVT .......................................................................................................244
ssccDetailPm ...............................................................................................244
ssccDetailSsc ...............................................................................................245
ssccGeneral .................................................................................................245
ssccLacGeneral ............................................................................................246
ssh ..............................................................................................................247
stTunnel ......................................................................................................247
stTunnelEngine ...........................................................................................248
system ........................................................................................................248
Chapter 19 T Commands 251
tacacsPlusServer ..........................................................................................251
tcpGeneral ...................................................................................................252
tcpTraffic .....................................................................................................252
tcpv6Traffic .................................................................................................253
telnet ...........................................................................................................254
telnetClient ..................................................................................................254
tftpClient .....................................................................................................255
trackerEvents ..............................................................................................255
trackerGeneral .............................................................................................256
tsm ..............................................................................................................257
Chapter 20 U Commands 259
udpTraffic ....................................................................................................259
udpv6Traffic ................................................................................................260
Chapter 21 V Commands 261
vrrp .............................................................................................................261
vrrpTracking ................................................................................................262
vsm .............................................................................................................262
vsmEngine ..................................................................................................263
Table of Contents ■ xvii
Page 18
JUNOSe 11.1.x System Event Logging Reference Guide
Part 3 Index
Index ...........................................................................................................267
xviii ■ Table of Contents
Page 19
List of Tables
About the Documentation xxi
Table 1: Notice Icons ...................................................................................xxii
Table 2: Text and Syntax Conventions ........................................................xxii
Part 1 Chapters
Chapter 1 System Logging Overview 3
Table 3: Log Severity Descriptions ...................................................................4
List of Tables ■ xix
Page 20

JUNOSe 11.1.x System Event Logging Reference Guide
xx ■ List of Tables
Page 21
About the Documentation
■ E Series and JUNOSe Documentation and Release Notes on page xxi
■ Audience on page xxi
■ E Series and JUNOSe Text and Syntax Conventions on page xxi
■ Obtaining Documentation on page xxiii
■ Documentation Feedback on page xxiii
■ Requesting Technical Support on page xxiii
E Series and JUNOSe Documentation and Release Notes
For a list of related JUNOSe documentation, see
http://www.juniper.net/techpubs/software/index.html .
If the information in the latest release notes differs from the information in the
documentation, follow the JUNOSe Release Notes.
To obtain the most current version of all Juniper Networks® technical documentation,
see the product documentation page on the Juniper Networks website at
http://www.juniper.net/techpubs/.
Audience
This guide is intended for experienced system and network specialists working with
Juniper Networks E Series Broadband Services Routers in an Internet access
environment.
E Series and JUNOSe Text and Syntax Conventions
Table 1 on page xxii defines notice icons used in this documentation.
E Series and JUNOSe Documentation and Release Notes ■ xxi
Page 22
JUNOSe 11.1.x System Event Logging Reference Guide
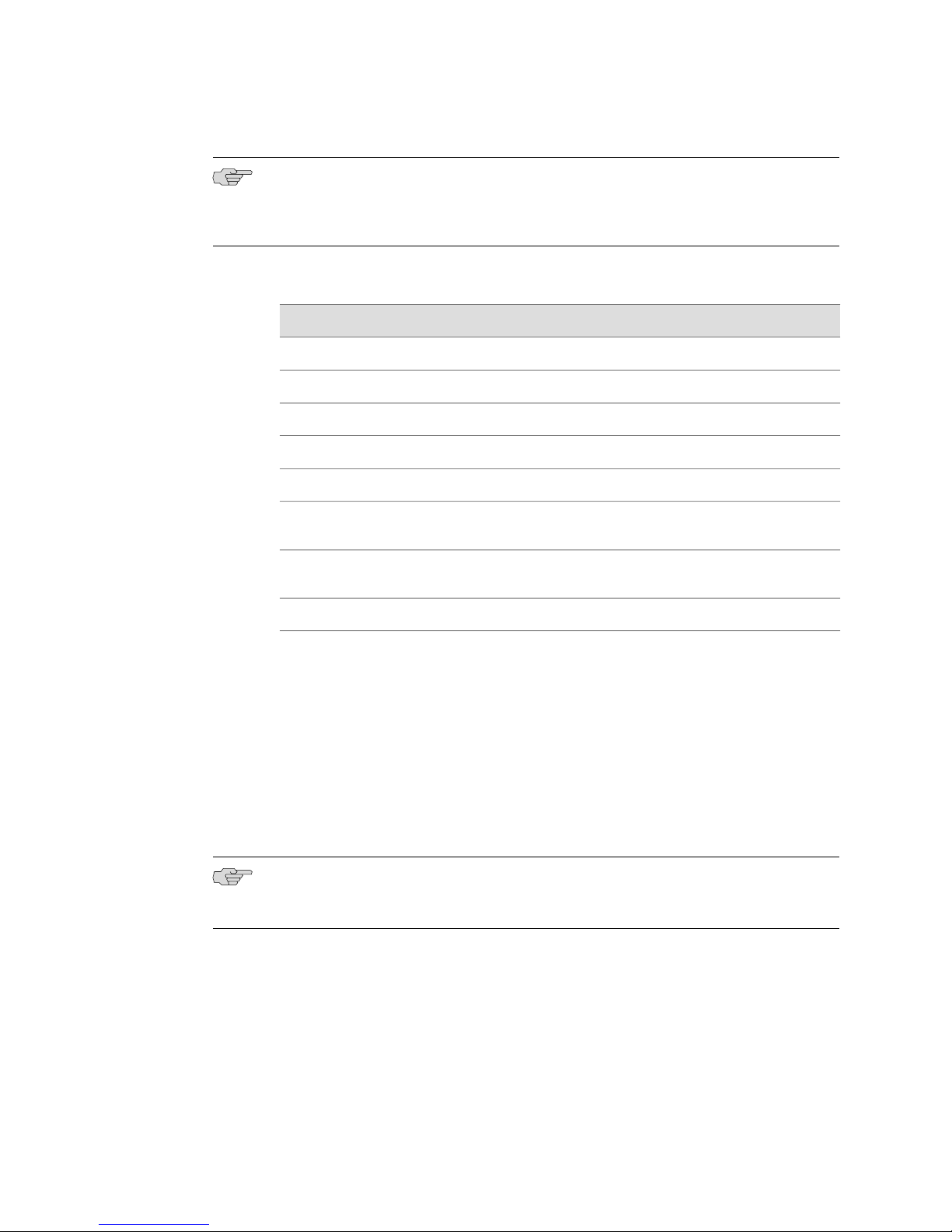
Table 1: Notice Icons
Table 2 on page xxii defines text and syntax conventions that we use throughout the
E Series and JUNOSe documentation.
DescriptionMeaningIcon
Indicates important features or instructions.Informational note
Indicates a situation that might result in loss of data or hardware damage.Caution
Alerts you to the risk of personal injury or death.Warning
Alerts you to the risk of personal injury from a laser.Laser warning
Table 2: Text and Syntax Conventions
Represents commands and keywords in text.Bold text like this
Bold text like this
Fixed-width text like this
Represents text that the user must type.
Represents information as displayed on your
terminal’s screen.
Italic text like this
Emphasizes words.
■
Identifies variables.
■
Identifies chapter, appendix, and book
■
names.
Plus sign (+) linking key names
keys simultaneously.
Syntax Conventions in the Command Reference Guide
ExamplesDescriptionConvention
Issue the clock source command.
■
Specify the keyword exp-msg.
■
host1(config)#traffic class low-loss1
host1#show ip ospf 2
Routing Process OSPF 2 with Router
ID 5.5.0.250
Router is an Area Border Router
(ABR)
There are two levels of access: user and
■
privileged.
clusterId, ipAddress.
■
Appendix A, System Specifications
■
Press Ctrl + b.Indicates that you must press two or more
terminal lengthRepresents keywords.Plain text like this
| (pipe symbol)
xxii ■ E Series and JUNOSe Text and Syntax Conventions
mask, accessListNameRepresents variables.Italic text like this
diagnostic | lineRepresents a choice to select one keyword
or variable to the left or to the right of this
symbol. (The keyword or variable can be
either optional or required.)
Page 23
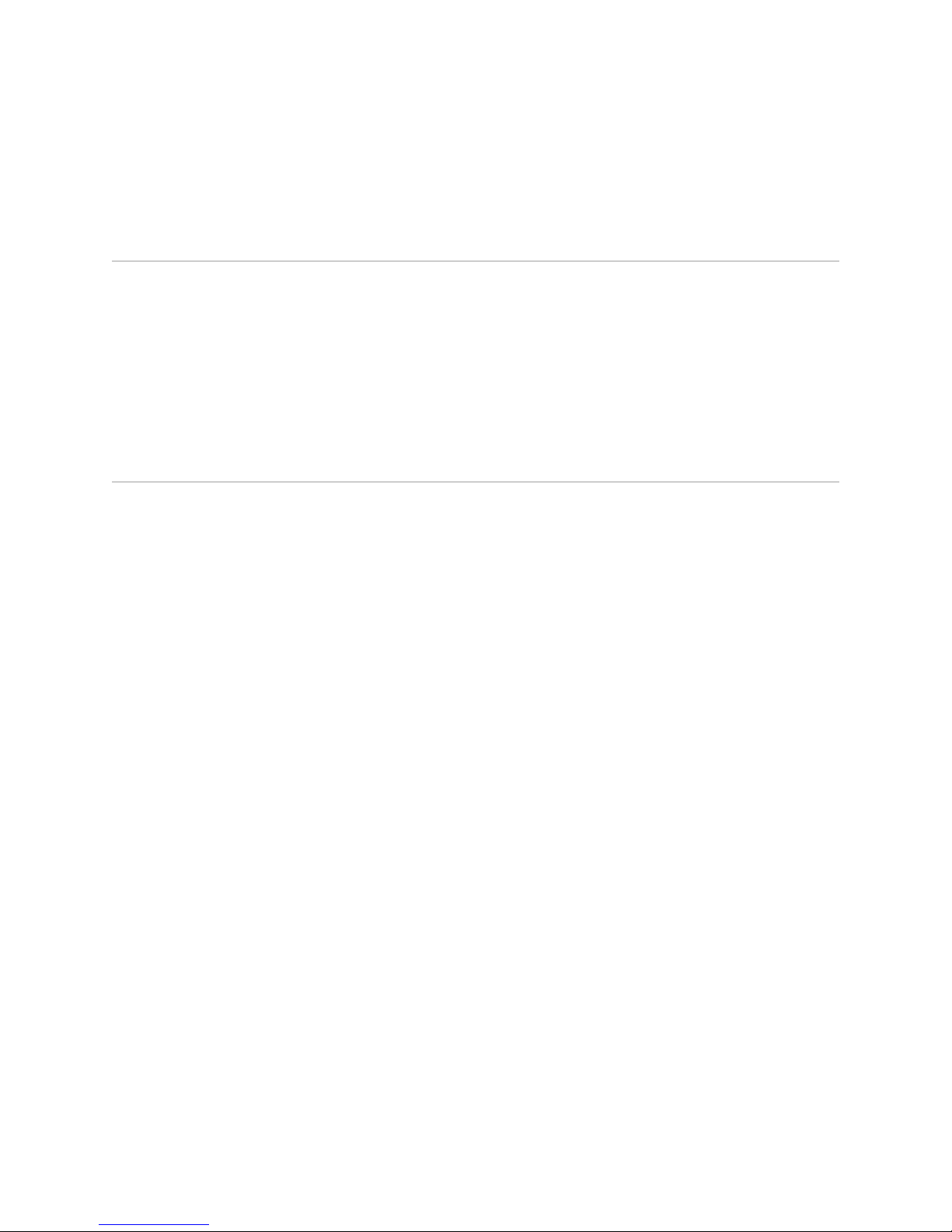
Table 2: Text and Syntax Conventions (continued)
About the Documentation
ExamplesDescriptionConvention
[ internal | external ]Represent optional keywords or variables.[ ] (brackets)
[ ]* (brackets and asterisk)
that can be entered more than once.
Represent required keywords or variables.{ } (braces)
Obtaining Documentation
To obtain the most current version of all Juniper Networks technical documentation,
see the Technical Documentation page on the Juniper Networks Web site at
http://www.juniper.net/.
To download complete sets of technical documentation to create your own
documentation CD-ROMs or DVD-ROMs, see the Offline Documentation page at
http://www.juniper.net/techpubs/resources/cdrom.html
Copies of the Management Information Bases (MIBs) for a particular software release
are available for download in the software image bundle from the Juniper Networks
Web site athttp://www.juniper.net/.
Documentation Feedback
[ level1 | level2 | l1 ]*Represent optional keywords or variables
{ permit | deny } { in | out }
{ clusterId | ipAddress }
We encourage you to provide feedback, comments, and suggestions so that we can
improve the documentation to better meet your needs. Send your comments to
techpubs-comments@juniper.net, or fill out the documentation feedback form at
https://www.juniper.net/cgi-bin/docbugreport/. If you are using e-mail, be sure to include
the following information with your comments:
■ Document or topic name
■ URL or page number
■ Software release version
Requesting Technical Support
Technical product support is available through the Juniper Networks Technical
Assistance Center (JTAC). If you are a customer with an active J-Care or JNASC support
contract, or are covered under warranty, and need post-sales technical support, you
can access our tools and resources online or open a case with JTAC.
■ JTAC policies—For a complete understanding of our JTAC procedures and policies,
review the JTAC User Guide located at
http://www.juniper.net/customers/support/downloads/7100059-EN.pdf .
Obtaining Documentation ■ xxiii
Page 24

JUNOSe 11.1.x System Event Logging Reference Guide
■ Product warranties—For product warranty information, visit
http://www.juniper.net/support/warranty/ .
■ JTAC hours of operation—The JTAC centers have resources available 24 hours a
day, 7 days a week, 365 days a year.
Self-Help Online Tools and Resources
For quick and easy problem resolution, Juniper Networks has designed an online
self-service portal called the Customer Support Center (CSC) that provides you with
the following features:
■
Find CSC offerings: http://www.juniper.net/customers/support/
■
Search for known bugs: http://www2.juniper.net/kb/
■
Find product documentation: http://www.juniper.net/techpubs/
■ Find solutions and answer questions using our Knowledge Base:
http://kb.juniper.net/
■ Download the latest versions of software and review release notes:
http://www.juniper.net/customers/csc/software/
■ Search technical bulletins for relevant hardware and software notifications:
https://www.juniper.net/alerts/
■ Join and participate in the Juniper Networks Community Forum:
http://www.juniper.net/company/communities/
■
Open a case online in the CSC Case Management tool: http://www.juniper.net/cm/
To verify service entitlement by product serial number, use our Serial Number
Entitlement (SNE) Tool: https://tools.juniper.net/SerialNumberEntitlementSearch/
Opening a Case with JTAC
You can open a case with JTAC on the Web or by telephone.
■
Use the Case Management tool in the CSC at http://www.juniper.net/cm/ .
■ Call 1-888-314-JTAC (1-888-314-5822 toll-free in the USA, Canada, and Mexico).
For international or direct-dial options in countries without toll-free numbers, see
http://www.juniper.net/support/requesting support.html .
xxiv ■ Requesting Technical Support
Page 25

Part 1
Chapters
■ System Logging Overview on page 3
■ Event Categories on page 23
Chapters ■ 1
Page 26

JUNOSe 11.1.x System Event Logging Reference Guide
2 ■ Chapters
Page 27
Chapter 1
System Logging Overview
E Series Broadband Services Routers enable you to log system events to discover
and isolate problems with your system. This chapter explains how to use the
command-line interface (CLI) to monitor your system’s log configuration and stay
informed about all system events that you want to track.
This chapter contains the following sections:
■ Overview of System Logging on page 3
■ Logging Platform Considerations on page 5
■ Configuring Event Logging on page 5
■ Configuring Log Severity for Individual and Systemwide Logs on page 10
■ Configuring Log Verbosity for Individual Logs or All Logs on page 14
■ Setting the Timestamp for Log Messages on page 14
■ Configuring Log Filters on page 16
■ Turning Off Log Filters on page 17
■ Monitoring Logging System Events on page 17
Overview of System Logging
System events are classified into event categories. Using the CLI, you can determine
which event categories to log. To fully utilize the logging facility, you need to
understand log severity and log verbosity.
Log Severity
Log severity is a level that is assigned to an event or log message. Log severity levels
apply to event categories, such as bulkStats, bgpRoutes, or atm1483.
The minimum severity of a log message for an individual category is described either
by a severity number in the range 0–7 or a descriptive priority term, such as
emergency or debug. The lower the severity number is, the higher the priority. See
Table 3 on page 4.
Overview of System Logging ■ 3
Page 28
JUNOSe 11.1.x System Event Logging Reference Guide
NOTE: Not every event category supports every severity level. For a list of event
categories and the severity levels that each category supports, see “Event Categories”
on page 23.
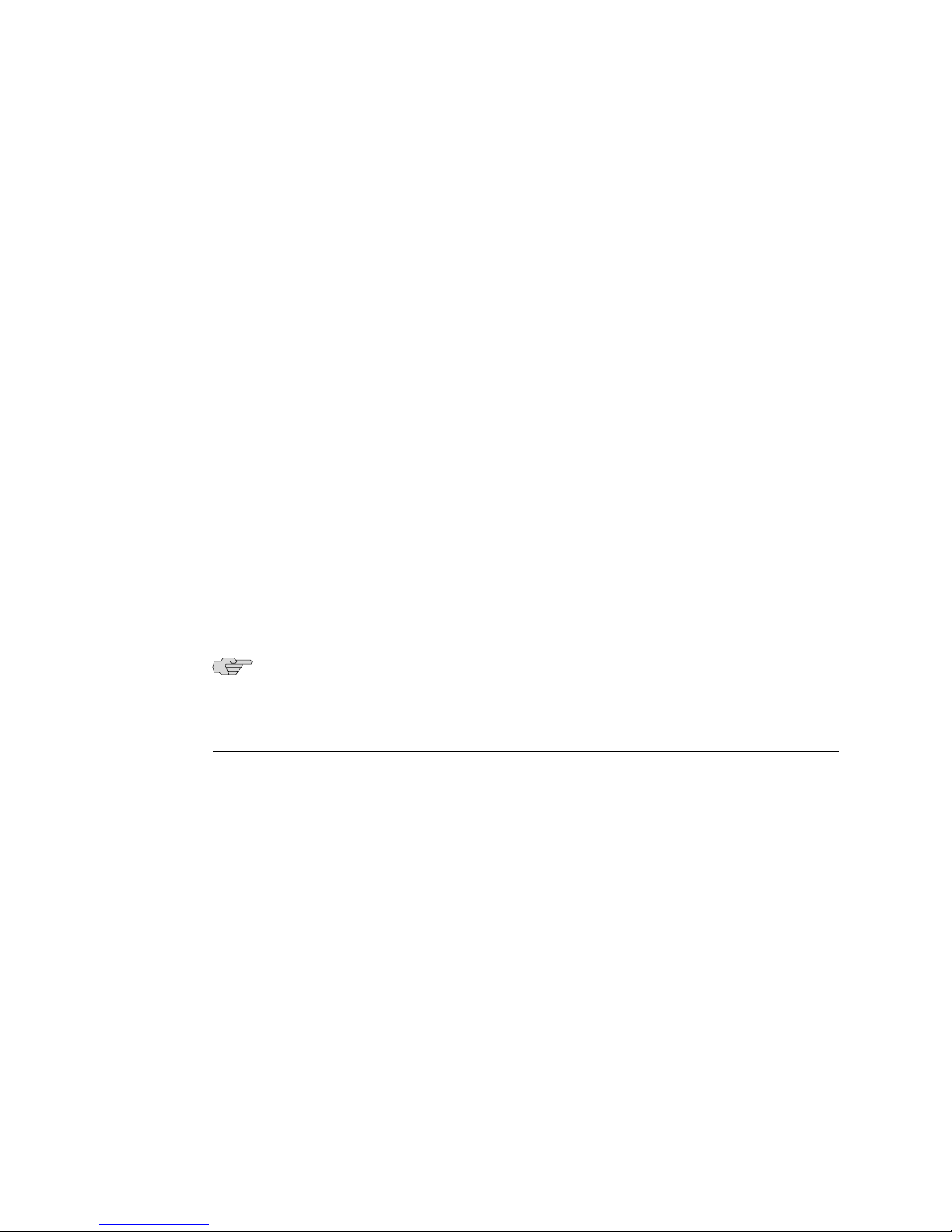
Table 3: Log Severity Descriptions
System ResponseSeverity NameSeverity Number
System unusable; shelf resetEmergency0
Immediate action needed; card resetAlert1
Critical conditions exist; interface is downCritical2
Error conditions; nonrecoverable software errorError3
Warning conditions; recoverable software errorWarning4
Log Verbosity
Notice5
Info6
Normal but significant conditions; nonerror,
low-verbosity information
Informational messages; nonerror, medium-verbosity
information
Debug messages; nonerror, high-verbosity informationDebug7
The verbosity level determines the amount of information that appears in each
message. You can assign the verbosity level for the log category. Verbosity levels can
be any of the following:
■ Low—Terse
■ Medium—Moderate
■ High—Verbose
NOTE: Many event categories provide only low-verbosity detail regardless of the
verbosity setting.
Persistent Logs
Log messages can survive a system reboot. After a reboot, the system rebuilds the
list of log messages. However, if the system detects any problems or has gone through
a power cycle, the buffer is reset, and the log messages from the previous session
are lost.
4 ■ Overview of System Logging
Page 29
Log messages are not synchronized between primary and redundant SRP modules.
During a switchover from a primary to a redundant SRP module, existing log messages
are not transferred to the redundant SRP module.
Logging Platform Considerations
System logs are supported on all E Series routers.
For information about the modules supported on E Series routers:
■ See the ERX Module Guide for modules supported on ERX7xx models, ERX14xx
models, and the Juniper Networks ERX310 Broadband Services Router.
■ See the E120 and E320 Module Guide for modules supported on the Juniper
Networks E120 and E320 Broadband Services Routers.
Configuring Event Logging
Chapter 1: System Logging Overview
By default, event logging is enabled and has default settings. This section explains
how to change settings to customize event logging to fit your needs.
■ Set a baseline for when the system begins logging messages.
host1#baseline log 11:12:55 April 30 2002
■ Set the log severity.
host1(config)#log severity warning
■ Remove the limit on the number of buffers available for an event category.
host1(config)#log unlimit qos
■ Set the log verbosity.
host1(config)#log verbosity low
■ Log messages to a specified destination.
host1(config)#log destination syslog 10.10.9.5 include ospfGeneral
mplsGeneral os
■ Select fields to be added to logs.
host1(config)#log fields timestamp instance no-calling-task
■ Enable logs destined for a console to be displayed at the current console device.
The next sections explain how to configure individual and systemwide logs, how to
format timestamps for log messages, and how to configure log filters.
host1#log here
Logging Platform Considerations ■ 5
Page 30
JUNOSe 11.1.x System Event Logging Reference Guide
baseline log ■ Use to set a baseline for logging events. Only log messages timestamped after
the baseline appear when you enter the show log data delta command.
■ To use the current system time, do not enter any options.
■ To set a specific time, use the following syntax:
Hour:Minute[:Second]—Current time in 24-hour format. Seconds are optional.
■ utc—Enter this keyword to indicate that the time entered is in universal
coordinated time (UTC), rather than local time.
■ To set a specific date, use the following syntax:
Month Day Year—You must spell out the name of the month.
■ last-reset—Causes the system to display log messages generated since the last
time the system was reset
■ Examples
host1#baseline log 11:12:55 April 30 2002
host1#baseline log last-reset
■ There is no no version.
■ See baseline log.
log destination ■ Use to log messages to the specified destination, including system log, console,
and nv-file (nonvolatile storage).
NOTE: You can display traffic logs—such as ipTraffic, icmpTraffic, tcpTraffic, and
udpTraffic—only through the show log data command or from the SRP module
console. You cannot redirect traffic logs elsewhere, such as to a system log or
nonvolatile storage file, or to a Telnet session.
■ Use the severity keyword to limit the messages logged based on priority level.
■ The following information applies to logging messages to system log servers.
■ You can have multiple system log servers, but must configure logging to
each one separately.
■ A particular message within a specified event category is logged to a particular
system log server only if the priority of the message is greater than or equal
to both the priority of the event category and the priority of that system log
server.
■ If you log messages to a system log server, you can also specify:
6 ■ Configuring Event Logging
■ facility—Specifies a facility ID on the system log destination host. The
range is 0–7, representing the logging facilities local0–local7.
■ include—Logs only the listed categories to system log; no other
categories are logged unless specifically included by issuing this
command again.
Page 31

Chapter 1: System Logging Overview
■ exclude—Logs all categories to system log except the listed categories;
all other categories are logged unless specifically excluded by issuing
this command again.
■ Issuing an include command after an exclude command (or vice versa)
overrides the earlier command. Therefore, you cannot enter a command
including certain categories and then follow it with a command excluding
others. Similarly, you cannot enter a command excluding certain categories
and then follow it with a command including others.
■ You can issue successive include commands or successive exclude
commands; in this case, the successive commands expand the list of included
or excluded categories.
■ Example 1—The first command causes only the osfpGeneral, mplsGeneral, and
os event categories to be logged to system log at 10.10.9.5. The second command
reverses this inclusion and restores the logging of all event categories.
host1(config)#log destination syslog 10.10.9.5 include ospfGeneral
mplsGeneral os
host1(config)#no log destination syslog 10.10.9.5
■ Example 2—The first command again causes only the osfpGeneral, mplsGeneral,
and os event categories to be logged to system log at 10.10.9.5. The second
command reverses the inclusion of ospfGeneral and os. The mplsGeneral category
is still included and is thus the only category logged.
host1(config)#log destination syslog 10.10.9.5 include ospfGeneral mplsGeneral
os
host1(config)#no log destination syslog 10.10.9.5 include ospfGeneral os
■ Example 3—The first command causes the isisGeneral, ipRoutePolicy, and
ipTraffic event categories to be excluded from logging to system log at 10.1.2.3.
The second command reverses this exclusion and restores the logging of all
event categories.
host1(config)#log destination syslog 10.1.2.3 exclude isisGeneral ipRoutePolicy
ipTraffic
host1(config)#no log destination syslog 10.1.2.3 exclude
■ Example 4—The first command again causes the isisGeneral, ipRoutePolicy, and
ipTraffic event categories to be excluded from logging to system log at 10.1.2.3.
The second command reverses the exclusion of ipRoutePolicy and ipTraffic. The
isisGeneral category is still excluded; all other events are logged.
host1(config)#log destination syslog 10.1.2.3 exclude isisGeneral
ipRoutePolicy ipTraffic
host1(config)#no log destination syslog 10.1.2.3 exclude isisGeneral
■ Example 5—The first command causes the isisGeneral event category to be
excluded from logging to system log at 10.1.2.3. The second command causes
ospfGeneral to also be excluded from logging.
host1(config)#log destination syslog 10.1.2.3 exclude isisGeneral
host1(config)#log destination syslog 10.1.2.3 exclude ospfGeneral
Configuring Event Logging ■ 7
Page 32

JUNOSe 11.1.x System Event Logging Reference Guide
■ Example 6—The first command causes the isisGeneral event category to be
excluded from logging to system log at 10.1.2.3; all other events are logged. The
second command overrides the first and causes the exclusion of all events except
ospfGeneral.
host1(config)#log destination syslog 10.1.2.3 exclude isisGeneral
host1(config)#log destination syslog 10.1.2.3 include ospfGeneral
■ Use the no version to reverse the effects of previous commands or restore the
default, which is to log all event categories.
■ See log destination.
log destination syslog
source
■ Use to specify a source interface type and location for events logged to system
log at the specified IP address.
■ Overrides the actual source interface type and location. The IP address associated
with the specified source interface is used as the source address for subsequent
system log messages.
■ Example
host1(config)#log destination syslog 10.1.2.3 source atm 0/1
■ Use the no version to restore the actual source interface type and location.
■ See log destination syslog source.
log engineering ■ Use to enable engineering logs.
■ Provides troubleshooting information to assist you when contacting Juniper
Networks Technical Assistance Center (JTAC).
■ Example
host1(config)#log engineering
■ Use the no form of this command to disable engineering logs.
■ See log engineering.
log fields ■ Use to select fields to be added to all logs. These fields include a timestamp for
the message, an instance identifier, and the name of the internal software
application that created the message.
■ Example
■ Use the no version to restore the default log field settings.
■ See log fields.
8 ■ Configuring Event Logging
host1(config)#log fields timestamp instance no-calling-task
Page 33

Chapter 1: System Logging Overview
log here ■ Use to enable logs destined for a console to be displayed at the current console.
■ By default, the local console automatically receives all log messages if console
is a destination. The exception is the cliCommand log, whose log events do not
appear on the console.
■ By default, Telnet consoles do not receive log messages.
■ Example
host1#log here
■ Use the no version to disable logs destined for a console from being displayed
on this console.
■ See log here.
log severity ■ Use to set the severity level for systemwide logs (that is, when you do not specify
an individual event category) or for a specific event category. For a list of severity
values, see Table 3 on page 4.
NOTE: Assigning a log severity to an individual event category changes its state to
Assigned. You cannot change the severity of that event category using systemwide
level commands until you return the event category to its default, unassigned state
with the no log severity command.
■ If you do not specify a category, the severity value changes for all categories
except individual categories for which you previously set a specific severity level.
See “Configuring Log Severity for Individual and Systemwide Logs” on page 10
for details.
■ Each event category has its own default severity value. For most categories, the
default is Error.
■ To disable all default level log messages, use the off keyword without specifying
an event category.
■ To disable individual level log messages, use the off keyword and specify the
event category that you want to disable.
■ Example
host1(config)#log severity warning
■ Use the no version to return the systemwide (when assigned) or default severity
values to event categories.
■ Use the no version with an* (asterisk) to return all event categories (modified
either systemwide or individually) to their default severity setting. For example:
■ See log severity.
host1(config)#no log severity *
Configuring Event Logging ■ 9
Page 34

JUNOSe 11.1.x System Event Logging Reference Guide
log unlimit ■ Use to remove the limit on the number of outstanding buffers for an event
category, such as when the system is dropping logs of a particular category.
■ Example
host1(config)#log unlimit qos
■ Use the no version to return to the default value.
■ See log unlimit.
log verbosity ■ Use to set the verbosity level for a selected category or for all categories.
■ If you do not specify a category, then the verbosity level is set for all categories.
■ The default verbosity setting for all logs is low.
■ Example
host1(config)#log verbosity low
■ Use the no version to return to the default verbosity (low) for the selected
category.
■ See log verbosity.
Configuring Log Severity for Individual and Systemwide Logs
You can change the severity setting for individual logs and the systemwide value.
When working with log severities, keep the following in mind:
■ All log event categories have a default. However, the default values can vary for
each category. For example, most event categories have a default severity of
Error. However, some event categories may have a default severity of Notice,
Warning, Info, and so on.
■ Log event categories have two states—unassigned (default) and assigned. How
a log event category reacts to the log severity command depends on its current
state.
■ You can change log severities for event categories at a systemwide level or an
individual level. Systemwide changes are those that modify a large number of
unassigned event categories at one time; for example, the command log severity
debug off. Individual changes are those that indicate an explicit event category
that you want to change; for example, the command log severity notice
clicommand.
■ Changes to log event categories at an individual level take precedence over those
made at the systemwide level.
■ Changes to log event categories at the systemwide level take precedence over
the default.
■ Assigning a log severity to an individual event category changes its state to
Assigned. This means that you cannot change the severity of that event category
10 ■ Configuring Log Severity for Individual and Systemwide Logs
Page 35

Chapter 1: System Logging Overview
using systemwide level commands until you return the event category to its
default, unassigned state by using the no log severity eventCategory command.
■ To return all logs, systemwide and individual, to their default, unassigned severity
level, use the no log severity * command.
■ To see whether individual or systemwide severity and verbosity settings are in
effect, use the show log configuration command.
Example The following example demonstrates the effects of event category state in regard to
using systemwide commands:
1. In Configuration mode and having made no changes to the severity settings of
any event categories, view the log configuration:
host1(config)#run show log config
log destination console severity WARNING
log destination nv-file severity CRITICAL
log destination syslog 10.10.4.240 facility 7 severity DEBUG
no log engineering
log fields timestamp instance no-calling-task
no log here
Warning: Logging to this terminal is disabled
no log severity
category severity verbosity filters notes
-------------------- -------- --------- ------- ----aaaAtm1483Cfg ERROR low
aaaEngineGeneral ERROR low
aaaServerGeneral ERROR low
aaaUserAccess ERROR low
addressServerGeneral ERROR low
ar1AaaServerGeneral ERROR low
atm ERROR low
atm1483 ERROR low
atmAal5 ERROR low
Notice that the atm event category has a default severity of Error.
2. Change all event categories to Warning, systemwide, and view the log
configuration:
host1(config)#log severity warning
host1(config)#run show log config
log destination console severity WARNING
log destination nv-file severity CRITICAL
log destination syslog 10.10.4.240 facility 7 severity DEBUG
no log engineering
log fields timestamp instance no-calling-task
no log here
Warning: Logging to this terminal is disabled
log severity WARNING
category severity verbosity filters notes
-------------------- -------- --------- ------- ----aaaAtm1483Cfg WARNING low 1
aaaEngineGeneral WARNING low 1
Configuring Log Severity for Individual and Systemwide Logs ■ 11
Page 36

JUNOSe 11.1.x System Event Logging Reference Guide
aaaServerGeneral WARNING low 1
aaaUserAccess WARNING low 1
addressServerGeneral WARNING low 1
ar1AaaServerGeneral WARNING low 1
atm WARNING low 1
atm1483 WARNING low 1
atmAal5 WARNING low 1
3. Change the atm category to have a log severity of Emergency and view the log
configuration:
host1(config)#log severity emergency atm
host1(config)#run show log config
log destination console severity WARNING
log destination nv-file severity CRITICAL
log destination syslog 10.10.4.240 facility 7 severity DEBUG
no log engineering
log fields timestamp instance no-calling-task
no log here
Warning: Logging to this terminal is disabled
log severity WARNING
category severity verbosity filters notes
-------------------- -------- --------- ------- ----aaaAtm1483Cfg WARNING low 1
aaaEngineGeneral WARNING low 1
aaaServerGeneral WARNING low 1
aaaUserAccess WARNING low 1
addressServerGeneral WARNING low 1
ar1AaaServerGeneral WARNING low 1
atm EMERGENCY low 2
atm1483 WARNING low 1
atmAal5 WARNING low 1
4. Change all event categories to Alert, systemwide, and view the log configuration:
host1(config)#log severity alert
host1(config)#run show log config
log destination console severity WARNING
log destination nv-file severity CRITICAL
log destination syslog 10.10.4.240 facility 7 severity DEBUG
no log engineering
log fields timestamp instance no-calling-task
no log here
Warning: Logging to this terminal is disabled
log severity ALERT
12 ■ Configuring Log Severity for Individual and Systemwide Logs
category severity verbosity filters notes
-------------------- -------- --------- ------- ----aaaAtm1483Cfg ALERT low 1
aaaEngineGeneral ALERT low 1
aaaServerGeneral ALERT low 1
aaaUserAccess ALERT low 1
addressServerGeneral ALERT low 1
ar1AaaServerGeneral ALERT low 1
atm EMERGENCY low 2
atm1483 ALERT low 1
atmAal5 ALERT low 1
Page 37

Chapter 1: System Logging Overview
Notice that the atm event category that you individually assigned in Step 3 does
not change.
5. Turn off log notification, systemwide, and view the log configuration:
host1(config)#log severity off
host1(config)#run show log config
log destination console severity WARNING
log destination nv-file severity CRITICAL
log destination syslog 10.10.4.240 facility 7 severity DEBUG
no log engineering
log fields timestamp instance no-calling-task
no log here
Warning: Logging to this terminal is disabled
log severity OFF
category severity verbosity filters notes
-------------------- --------- --------- ------- ----aaaAtm1483Cfg OFF low 1
aaaEngineGeneral OFF low 1
aaaServerGeneral OFF low 1
aaaUserAccess OFF low 1
addressServerGeneral OFF low 1
ar1AaaServerGeneral OFF low 1
atm EMERGENCY low 2
atm1483 OFF low 1
atmAal5 OFF low 1
Notice that the atm event category does not change.
6. Remove the assigned status of the atm event category and view the log
configuration:
host1(config)#no log severity atm
host1(config)#run show log config
log destination console severity WARNING
log destination nv-file severity CRITICAL
log destination syslog 10.10.4.240 facility 7 severity DEBUG
no log engineering
log fields timestamp instance no-calling-task
no log here
Warning: Logging to this terminal is disabled
log severity OFF
category severity verbosity filters notes
-------------------- -------- --------- ------- ----aaaAtm1483Cfg OFF low 1
aaaEngineGeneral OFF low 1
aaaServerGeneral OFF low 1
aaaUserAccess OFF low 1
addressServerGeneral OFF low 1
ar1AaaServerGeneral OFF low 1
atm OFF low 1
atm1483 OFF low 1
atmAal5 OFF low 1
Configuring Log Severity for Individual and Systemwide Logs ■ 13
Page 38

JUNOSe 11.1.x System Event Logging Reference Guide
Notice that the atm event category follows the systemwide severity level of OFF.
The systemwide setting takes precedence over the atm event category default
of Error.
7. Change all event categories, systemwide, to their default/unassigned levels, and
view the log configuration:
host1(config)#no log severity *
Please wait....
host1(config)#run show log config
log destination console severity WARNING
log destination nv-file severity CRITICAL
log destination syslog 10.10.4.240 facility 7 severity DEBUG
no log engineering
log fields timestamp instance no-calling-task
no log here
Warning: Logging to this terminal is disabled
no log severity
category severity verbosity filters notes
-------------------- -------- --------- ------- ----aaaAtm1483Cfg ERROR low
aaaEngineGeneral ERROR low
aaaServerGeneral ERROR low
aaaUserAccess ERROR low
addressServerGeneral ERROR low
ar1AaaServerGeneral ERROR low
atm ERROR low
atm1483 ERROR low
atmAal5 ERROR low
Configuring Log Verbosity for Individual Logs or All Logs
The default verbosity setting for all logs is low. To change the logging verbosity of
an individual log, specify a category when you enter the log verbosity command.
To change the log verbosity of every log, do not specify an event category when you
enter the log verbosity command. However, after you enter the log verbosity
command without specifying a particular event category, all logs are set to the new
verbosity. No log verbosity overrides are saved.
Example The following example sets all log categories to verbosity medium, and then it sets
the verbosity level for ds3 events to high.
host1(config)#log verbosity medium
host1(config)#log verbosity high ds3
Setting the Timestamp for Log Messages
You can use the service timestamps command to format timestamps for log
messages. By default, log messages display universal coordinated time (UTC) without
the time zone.
14 ■ Configuring Log Verbosity for Individual Logs or All Logs
Page 39

Chapter 1: System Logging Overview
The following examples illustrate how you can change the timestamp on log messages.
■ Set the time zone to eastern daylight time (EDT), 5 hours behind UTC, and display
the local time on the log messages.
host1(config)#clock timezone EDT -5
■ Display UTC, but no time zone, on the log messages.
host1(config)#service timestamps log datetime
host1#exit
host1#show log data category cliCommand severity info
***********************************************************
NOTICE 05/14/2001 18:24:49 cliCommand: "configure terminal", console
NOTICE 05/14/2001 18:24:45 cliCommand: "service timestamps log datetime",
console
***********************************************************
■ Display UTC and the time zone on the log messages.
host1#configure terminal
host1(config)#service timestamps log datetime show-timezone
host1(config)#exit
host1#show log data category cliCommand severity info
***********************************************************
NOTICE 05/14/2001 18:28:45 UTC EDT cliCommand: "configure terminal",
console
NOTICE 05/14/2001 18:28:42 UTC EDT cliCommand: "service timestamps log
datetime show-timezone", console
***********************************************************
■ Display no timestamp on the log messages.
host1#configure terminal
host1(config)#no service timestamps
host1#exit
host1#show log data category cliCommand severity info
***********************************************************
NOTICE 134 cliCommand: "configure terminal", console
NOTICE 133 cliCommand: "no service timestamps", console
***********************************************************
service timestamps ■ Use to format timestamps for log messages.
■ For information about setting local times and time zones, see JUNOSe System
Basics Configuration Guide.
■ The show log data command displays the log data with the current timestamp
format.
■ The show log data nv-file command displays the log data with the timestamp
format in effect at the time the log record was written.
■ Use the no version to remove timestamps from log messages.
■ See service timestamps.
Setting the Timestamp for Log Messages ■ 15
Page 40

JUNOSe 11.1.x System Event Logging Reference Guide
Configuring Log Filters
Many event categories contain filters so you can further refine the type of information
that the system logs. For example, when logging BGP connections, you can limit the
information logged to a specific access class, peer, route map, or virtual router.
You define filters when you set the log severity for an event category. The online
Help shows the options you can set for each filter.
NOTE: You can use the packet flow monitoring feature to create user-defined
classification parameters that specify the packet data that is logged. See Packet
Tagging Overview.
The following example creates a filter that logs BGP connection information at the
debug severity level on traffic that matches access list ListOne, and is incoming traffic
to virtual router default.
host1(config)# log severity debug bgpevents ?
access-class Select an access list for the filter
in Select import/in direction for the filter
out Select export/out direction for the filter
peer Select a peer IP address for the filter
route-map Select a route map for the filter
router Identify an instance of a virtual router
<cr>
host1(config)# log severity debug bgpevents access-class ?
WORD The access list
host1(config)# log severity debug bgpevents access-class ListOne ?
filtering-router Identify virtual router where access-class/route-map are defined
in Select import/in direction for the filter
out Select export/out direction for the filter
route-map Select a route map for the filter
<cr>
host1(config)# log severity debug bgpevents access-class ListOne route-map ?
WORD The route map
host1(config)# log severity debug bgpevents access-class ListOne route-map default ?
filtering-router Identify virtual router where access-class/route-map are defined
in Select import/in direction for the filter
out Select export/out direction for the filter
<cr>
host1(config)# log severity debug bgpevents access-class ListOne route-map default in
The next example limits the logging of PPP debug events to traffic to or from the
POS interface in slot 2/0.
host1(config)#log severity debug ppp ?
atm Specify an ATM PPP interface
fastEthernet Specify a fastEthernet interface
gigabitEthernet Specify a gigabitEthernet interface
mlppp Specify an MLPPP network interface
pos Specify a POS PPP interface
serial Specify a serial PPP interface
16 ■ Configuring Log Filters
Page 41

<cr>
host1(config)#log severity debug ppp pos 2/0
To obtain a list of the filters available in each event category, see “Event Categories”
on page 23 .
Turning Off Log Filters
You can turn off filters in three ways:
■ Turn off all filters
■ Turn off all filters for an event category
■ Turn off a specific filter
To turn off all filters:
Chapter 1: System Logging Overview
host1(config)#no log filters
To turn off all filters for an event category, use the no version of the log severity
command along with the category name. For example:
host1(config)#no log severity bgpEvents filters
To turn off a specific filter, use the no version of the log severity command that you
used to add the filter. For example:
host1(config)#no log severity bgpEvents peer 10.0.0.2 10.0.0.1
no log filters ■ Use to turn off log filters.
■ To turn off all filters for an event category, specify the category name.
■ Example
host1(config)#no log filters
■ To turn off a specific filter, use the no version of the log severity command that
you used to add the filter.
■ See no log filters.
Monitoring Logging System Events
Use the show log configuration command to display your log configuration. Use the
show log data command to display system events on your screen.
You can use the output filtering feature of the show command to include or exclude
lines of output based on a text string you specify. See show Commands in JUNOSe
System Basics Configuration Guide for details.
Turning Off Log Filters ■ 17
Page 42

JUNOSe 11.1.x System Event Logging Reference Guide
show log configuration ■ Use to show the logging configuration on your system.
■ Example 1—Factory defaults are set
host1#show log configuration
log destination console severity WARNING
log destination nv-file severity CRITICAL
no log engineering
log fields timestamp instance no-calling-task
no log severity
category severity verbosity filters
------------------------- -------- --------- ------NameResolverLog ERROR low
aaaAtm1483Cfg ERROR low
aaaEngineGeneral ERROR low
aaaServerGeneral ERROR low
addressServerGeneral ERROR low
atm ERROR low
atm1483 ERROR low
atmAal5 ERROR low
bgpConnections ERROR low
...
cliCommand NOTICE low
controlNetworkSlave ERROR low
cops ERROR low
...
udpTraffic ERROR low
■ Example 2—Individual log udpTraffic is set to warning
host1#(config)#log severity warning udpTraffic
host1##show log configuration
log destination console severity WARNING
log destination nv-file severity CRITICAL
no log engineering
log fields timestamp instance no-calling-task
no log severity
category severity verbosity filters
------------------------- -------- --------- ------NameResolverLog ERROR low
aaaAtm1483Cfg ERROR low
aaaEngineGeneral ERROR low
aaaServerGeneral ERROR low
addressServerGeneral ERROR low
atm ERROR low
atm1483 ERROR low
atmAal5 ERROR low
bgpConnections ERROR low
...
cliCommand NOTICE low
controlNetworkSlave ERROR low
cops ERROR low
...
udpTraffic WARNING* low
* Default severity setting is overridden by the individual log severity
setting.
18 ■ Monitoring Logging System Events
Page 43

■ Example 3—Log severity is set to alert
host1#(config)#log severity alert
host1#show log configuration
log destination console severity WARNING
log destination nv-file severity CRITICAL
no log engineering
log fields timestamp instance no-calling-task
log severity ALERT
category severity verbosity filters
------------------------- -------- --------- ------NameResolverLog ALERT# low
aaaAtm1483Cfg ALERT# low
aaaEngineGeneral ALERT# low
aaaServerGeneral ALERT# low
addressServerGeneral ALERT# low
atm ALERT# low
atm1483 ALERT# low
atmAal5 ALERT# low
bgpConnections ALERT# low
...
cliCommand ALERT# low
controlNetworkSlave ALERT# low
cops ALERT# low
...
udpTraffic ALERT# low
Chapter 1: System Logging Overview
* Default severity setting is overridden by the system-wide severity
setting.
■ Example 4—Individual log atm is set to severity warning
host1#(config)#log severity warning atm
host1#show log configuration
log destination console severity WARNING
log destination nv-file severity CRITICAL
no log engineering
log fields timestamp instance no-calling-task
log severity ALERT
category severity verbosity filters
------------------------- -------- --------- ------NameResolverLog ALERT# low
aaaAtm1483Cfg ALERT# low
aaaEngineGeneral ALERT# low
aaaServerGeneral ALERT# low
addressServerGeneral ALERT# low
atm WARNING* low
atm1483 ALERT# low
atmAal5 ALERT# low
bgpConnections ALERT# low
...
cliCommand ALERT# low
controlNetworkSlave ALERT# low
cops ALERT# low
...
udpTraffic ALERT# low
Monitoring Logging System Events ■ 19
Page 44

JUNOSe 11.1.x System Event Logging Reference Guide
* Default severity setting is overridden by the system-wide severity
setting.
* Default severity setting is overridden by the individual log severity
setting.
■ See show log configuration.
show log data ■ Use to display system events.
■ Use keywords to select which events are displayed:
■ category—Limits the display to a single log event category. See the CLI online
Help for available categories.
■ Example
host1#show log data category os
■ delta—Limits the display to events that occurred after the time set with the
log baseline command.
■ nv-file—Displays the information that is currently logged to nonvolatile
storage.
■ Example
host1# show log data nv-file
logFile.temp: The system cannot find the file specified.
ALERT 09/12/2000 21:29:17 os: ASSERTION FAILED: file mplsNvs2.cc, line
789
ALERT 09/20/2000 02:18:06 os: ASSERTION FAILED: file osPool.cc, line 819
ALERT 09/20/2000 02:26:35 os: ASSERTION FAILED: file osPool.cc, line 819
ALERT 09/20/2000 02:44:33 os: ASSERTION FAILED: file osPool.cc, line 819
ALERT 09/20/2000 04:56:35 os: ASSERTION FAILED: file osPool.cc, line 819
ALERT 09/27/2000 03:10:25 os: ASSERTION FAILED: file
/sw0/sc/nvs/include/../nvMapBackend.h, line 235
ALERT 10/02/2000 04:05:42 os: ASSERTION FAILED: file osHeap.cc, line 439
ALERT 10/02/2000 04:08:04 os: ASSERTION FAILED: file osMessageQueue.cc,
line
42, rip1
ALERT 10/12/2000 03:43:38 os: PANIC: file osSemaphore.cc, line 54
ALERT 11/01/2000 02:03:49 os: ASSERTION FAILED: file cliCommand.cc, line
195
■ severity—Displays events that have a specific severity level.
20 ■ Monitoring Logging System Events
Page 45

Chapter 1: System Logging Overview
■ Example
host1# show log data severity notice
NOTICE 01/10/2001 00:59:50 os: config -- using running
NOTICE 01/10/2001 00:59:52 os: srp application, build date: 0x3a437424 (FRI DEC 22 2000 15:32:52 UTC)
NOTICE 01/10/2001 00:59:52 os: last reset: user reboot, reason: not specified
NOTICE 01/10/2001 00:59:52 os: OsIsrRegistrar: 0xb
NOTICE 01/10/2001 00:59:52 os: OsIsrRegistrar: 0xa
NOTICE 01/10/2001 00:59:52 os: OsIsrRegistrar: 0x2
■ By combining keywords, you can further limit the information displayed. See
the CLI online Help for information about the keywords available at each level.
host1#show log data nv-file severity alert
■ See show log data.
Monitoring Logging System Events ■ 21
Page 46

JUNOSe 11.1.x System Event Logging Reference Guide
22 ■ Monitoring Logging System Events
Page 47

Chapter 2
Event Categories
This chapter lists each event category in the system software. To help you determine
the severity level to set when troubleshooting, the log strategy for each event category
is included. The log strategy shows the type of information logged for each severity
level. In addition, this chapter includes the filters available in each event category.
■ 23
Page 48

JUNOSe 11.1.x System Event Logging Reference Guide
24 ■
Page 49

Part 2
Event Categories
■ A Commands on page 27
■ B Commands on page 35
■ C Commands on page 51
■ D Commands on page 57
■ E Commands on page 79
■ F Commands on page 81
■ G and H Commands on page 87
■ I Commands on page 91
■ L Commands on page 129
■ M Commands on page 145
■ N Commands on page 165
■ O Commands on page 169
■ P Commands on page 195
■ Q Commands on page 217
■ R Commands on page 219
■ S Commands on page 233
■ T Commands on page 251
■ U Commands on page 259
■ V Commands on page 261
Event Categories ■ 25
Page 50

JUNOSe 11.1.x System Event Logging Reference Guide
26 ■ Event Categories
Page 51

Chapter 3
A Commands
■ aaaAtm1483Cfg on page 27
■ aaaEngineGeneral on page 28
■ aaaQosCfg on page 28
■ aaaServerGeneral on page 29
■ aaaUserAccess on page 29
■ addressServerGeneral on page 30
■ ar1AaaServerGeneral on page 30
■ atm on page 31
■ atm1483 on page 32
■ atm1483VcClass on page 32
■ atmAal5 on page 33
■ atmVcClass on page 33
■ auditIpsec on page 34
aaaAtm1483Cfg
Description AAA ATM 1483 subinterface configuration
Emergency None
Alert None
Critical None
Error None
Warning Log Illegal service category traffic parameter received from AAA; unable to modify circuit
Notice Log None
Info None
traffic parameters using those received from AAA
aaaAtm1483Cfg ■ 27
Page 52

JUNOSe 11.1.x System Event Logging Reference Guide
Debug Notification from AAA indicating that an ATM 1483 subinterface configuration is
available; ATM 1483 processing configuration received from AAA; unable to get ATM
1483 subinterface information; number of ATM 1483 configuration entries is out of
range
Filter None
aaaEngineGeneral
Description AAA engine general
Emergency None
Alert None
Warning Log None
Notice Log Control flow and key events, less verbose than debug
aaaQosCfg
Description AAA QoS configuration logs
Emergency None
Critical None
Error None
Info None
Debug Control flow and key events
Filter None
Alert None
Critical None
Error None
Warning Log None
28 ■ aaaEngineGeneral
Page 53

Notice Log None
Info None
Debug AAA QoS configuration tracking
Filter None
aaaServerGeneral
Description AAA server general
Emergency None
Alert None
Chapter 3: A Commands
Critical None
Error Subscriber count exceeds license plus grace; internal attachment errors
Warning Log Subscriber count exceeds license; cannot grow internal memory pools; accounting
message failures; the Framed-IPv6-Prefix RADIUS attribute is used for both IPv6
Neighbor Discovery router advertisements and DHCPv6 Prefix Delegation.
Notice Log Authentication failures resulting from memory allocation failures
Info None
Debug Authentication failures resulting from reasons other than memory allocation failures;
status of authentication; accounting and address assignment requests sent to local
(internal) servers; duplicate accounting message failures; EAP challenge received;
memory allocation failure for tunnel definition table and profile; failed to insert tunnel
attribute and tunnel tag table; container size exceeded: creating new; found
unexpected tunnel table; dsl-forum atrribute type parse error: limited data or overflow
Filter None
aaaUserAccess
Description AAA user access
Emergency None
Alert None
aaaServerGeneral ■ 29
Page 54

JUNOSe 11.1.x System Event Logging Reference Guide
Critical None
Error None
Warning Log None
Notice Log None
Info User is granted or denied access
Debug None
Filter None
addressServerGeneral
Description Address server general
Emergency None
Alert None
Critical None
Error None
Warning Log Address server request failure (for example, configured address server is not available)
Notice Log None
Info None
Debug None
Filter None
ar1AaaServerGeneral
Description Platform-dependent AAA server
Emergency None
30 ■ addressServerGeneral
Page 55

Alert None
Critical None
Error Internal (NVS) errors for limit configuration per interface
Warning Log None
Notice Log None
Info None
Debug Interface information insufficient to identify the user’s interface location
Filter None
Chapter 3: A Commands
atm
Description ATM interface
Emergency None
Alert None
Critical None
Error Unable to reenable ILMI administrative state after UNI version change
Warning Log Error getting location of underlying physical interface; error binding or unbinding to
physical interface; error allocating memory for new interface; error setting system
identifier; error adding or configuring an interface; error getting capabilities of
interface; error getting maximum VPI/VCI for interface; error getting maximum
virtual circuit descriptor for interface; unable to store or allocate memory for F4 OAM
circuit data; unable to configure F4 OAM circuit for interface
Notice Log Interface pool expanded by an incremental number of entries; report retry delay in
seconds when waiting for the underlying physical interface to be created; unable to
allocate a message to send an interface up or down notification; unable to add or
configure interface
Info Dropping interface up, down, or not present notification due to removal of interface;
discarding F4 OAM circuits when interface does not support F4 OAM
Debug None
atm ■ 31
Page 56

JUNOSe 11.1.x System Event Logging Reference Guide
Filter None
atm1483
Description ATM 1483 data service
Emergency None
Alert None
Critical None
Error Error applying static map entry for a newly created circuit of an NBMA interface;
unable to configure interfaces on ATM interface; unable to determine interface
location for ATM AAL5 interface; unable to determine maximum interface
configuration count for interface; unable to configure interface on ATM interface
Warning Log Error getting location of underlying AAL5 or ATM interface; error binding to AAL5
Notice Log Interface pool, interface binding pool, or subscriber pool expanded by an incremental
Info Dropping subinterface up or down notification due to removal of subinterface;
Debug None
Filter None
atm1483VcClass
Description Application of attributes configured in a virtual circuit (VC) class to PVCs
interface; error opening a circuit for an NBMA interface; attempting to associate a
static map to an underlying ATM interface that does not exist; error restoring circuits
from NVS; error removing static map entry; NVS entry not found for static map entry;
error storing static map entry in NVS; error expanding interface pool, interface binding
pool, or subscriber pool
number of entries; unable to allocate a message to send a subinterface up or down
notification
configure interfaces on ATM interface; elapsed time for downloading interfaces;
elapsed time for ATM AAL5 present notification; maximum interface count per call
Emergency None
Alert None
Critical None
32 ■ atm1483
Page 57

Chapter 3: A Commands
Error In routers with high availability enabled, failure to mirror the VC modification or
failure to associate the VC modification with the standby SRP module
Warning Log Failure to find the PVCs associated with this VC class; failure to apply the VC class
attributes to the appropriate PVCs; the log message displays a brief description of
the failure
Notice Log None
Info None
Debug None
Filter None
atmAal5
Description ATM Adaptation Layer 5
Emergency None
Alert None
Critical None
Error None
Warning Log Error getting location of underlying ATM interface; error binding to ATM interface;
unable to expand interface pool; error creating interface; unable to set administrative
status of interface
Notice Log Interface pool expanded by an incremental number of entries; report retry delay in
seconds when waiting for the underlying ATM interface to be created; unable to
allocate a message to send an interface up or down notification
Info Dropping interface up or down notification due to removal of interface
Debug None
Filter None
atmVcClass
Description Information on VC class operational errors
atmAal5 ■ 33
Page 58

JUNOSe 11.1.x System Event Logging Reference Guide
Emergency None
Alert None
Critical None
Error Resource failure errors, such as error allocating memory for adding a VC class; internal
software errors; error processing a VC class association; when using SNMP, unable
to set a VC class state from not in service to in service, or vice-versa; unable to find
an existing VC class in the internal data structure; unable to complete processing
after a high availability switchover
Warning Log None
Notice Log None
auditIpsec
Description IKE SA negotiations
Emergency None
Warning Log None
Info None
Debug Unable to update mirrored storage for a high availability switchover
Filter None
Alert None
Critical None
Error None
Notice Log Information about IKE SA negotiation payloads
Info None
Debug None
Filter None
34 ■ auditIpsec
Page 59

Chapter 4
B Commands
■ bfdAdaptivity on page 35
■ bfdEvents on page 36
■ bfdGeneral on page 36
■ bfdSession on page 37
■ bgpConnections on page 37
■ bgpDampening on page 38
■ bgpEvents on page 39
■ bgpGeneral on page 40
■ bgpGracefulRestart on page 41
■ bgpIpv6NextHops on page 42
■ bgpKeepAlives on page 42
■ bgpMessages on page 43
■ bgpNeighborChanges on page 44
■ bgpNextHops on page 45
■ bgpRoutes on page 45
■ bridge on page 48
■ bridgeEngine on page 49
■ bridgingMgr on page 49
■ bulkStats on page 50
bfdAdaptivity
Description BFD adaptivity events
Emergency None
Alert None
Critical None
bfdAdaptivity ■ 35
Page 60

JUNOSe 11.1.x System Event Logging Reference Guide
Error None
Warning Log None
Notice Log None
Info BFD session adaptivity events
Debug BFD session adaptivity events
Filter None
bfdEvents
Description BFD Events
Emergency None
Warning Log None
Notice Log None
bfdGeneral
Alert None
Critical None
Error None
Info BFD session state changes
Debug None
Filter None
Description BFD general events
Emergency None
Alert None
36 ■ bfdEvents
Page 61

Critical None
Error None
Warning Log None
Notice Log BFD enabled/disabled on an interface from a client
Info None
Debug None
Filter None
Chapter 4: B Commands
bfdSession
Description BFD session events
Emergency None
Warning Log Unknown BFD session
Notice Log Session state changes
Alert None
Critical None
Error None
Info Session parameter changes
Debug None
Filter None
bgpConnections
Description BGP TCP/IP connection activity
Emergency None
bfdSession ■ 37
Page 62

JUNOSe 11.1.x System Event Logging Reference Guide
Alert None
Critical None
Error Error setting password for specified peer; error binding to update-source address for
specified peer
Warning Log TCP error occurred while receiving data
Notice Log Outbound TCP connection initiated, completed, or failed; inbound TCP connection
accepted, refused, or failed; TCP connection closed by peer
Info None
Debug TCP connection is ready to send; data received on TCP connection; notification
message sent; could not send notification message due to flow control—will retry
later; error while sending notification message; keepalive message sent; could not
send keepalive message due to flow control—will retry later; error while sending
keepalive message; message other than notification or keepalive sent; could not send
other message than notification or keepalive due to flow control—will retry later;
error while sending other message than notification or keepalive
Filter 1 access-class—This filter is not currently supported
Filter 2 peer—See description of the bgpRoutes peer filter for information about this filter
Filter 3 route-map—This filter is not currently supported
Filter 4 router—See description of the bgpRoutes router filter for information about this filter
Filter 5 in—This filter is not currently supported
Filter 6 out—This filter is not currently supported
bgpDampening
Description BGP dampening
Emergency None
Alert None
Critical None
38 ■ bgpDampening
Page 63

Chapter 4: B Commands
Error None
Warning Log None
Notice Log Route is suppressed by route-flap dampening; route is no longer suppressed by
route-flap dampening
Info None
Debug None
Filter 1 access-class—This filter is not currently supported
Filter 2 peer—See description of the bgpRoutes peer filter for information about this filter
bgpEvents
Description BGP finite state machine (FSM) events and transitions
Emergency None
Filter 3 route-map—This filter is not currently supported
Filter 4 router—See description of the bgpRoutes router filter for information about this filter
Filter 5 in—This filter is not currently supported
Filter 6 out—This filter is not currently supported
Alert None
Critical None
Error Event occurred that was not expected for current state
Warning Log None
Notice Log One of the following events occurred: start, stop, inbound-connection-arrived,
outbound-connection-complete, connection-error, connection-closed,
start-timer-expired, connect-timer-expired, hold-timer-expired,
keep-alive-timer-expired, open-received, update-received, keep-alive-received,
notification-received, route-refresh, route-refresh-cisco
Info None
bgpEvents ■ 39
Page 64

JUNOSe 11.1.x System Event Logging Reference Guide
Debug None
Filter 1 access-class—This filter is not currently supported
Filter 2 peer—See description of the bgpRoutes peer filter for information about this filter
Filter 3 route-map—This filter is not currently supported
Filter 4 router—See description of the bgpRoutes router filter for information about this filter
Filter 5 in—This filter is not currently supported
Filter 6 out—This filter is not currently supported
bgpGeneral
Description BGP general information
Emergency None
Warning Log None
Notice Log BGP IPv4 route-target-signaling address family enabled or disabled; making local
Alert None
Critical None
Error None
route to multihomed site less preferred (local-preference <> ) because down bit is
set
Info None
Debug Setting local preference to <> for redistributed route of layer2 site
Filter 1 access-class—This filter is not currently supported
Filter 2 peer—See description of the bgpRoutes peer filter for information about this filter
Filter 3 route-map—This filter is not currently supported
Filter 4 router—See description of the bgpRoutes router filter for information about this filter
40 ■ bgpGeneral
Page 65

Filter 5 in—This filter is not currently supported
Filter 6 out—This filter is not currently supported
bgpGracefulRestart
Description BGP Graceful Restart Feature log
Emergency None
Alert None
Critical None
Error None
Chapter 4: B Commands
Warning Log None
Notice Log Log BGP performed or did not perform a graceful restart; router supports or does
not support non-stop forwarding; router is capable of switching gracefully, deferring,
or resuming best path selection decision process; BGP routes allowed or prevented
from being downloaded to line cards; graceful-restart timer expiration; marking or
removing stale routes; waiting to receive end-of-rib marker from peer; received
end-of-rib marker from all peers
Info None
Debug Standby SRP will wait for BGP convergence on next restart
Filter 1 access-class—This filter is not currently supported
Filter 2 peer—This filter is not currently supported
Filter 3 route-map—This filter is not currently supported
Filter 4 router—See description of the bgpRoutes router filter for information about this filter
Filter 5 in—This filter is not currently supported
Filter 6 out—This filter is not currently supported
bgpGracefulRestart ■ 41
Page 66

JUNOSe 11.1.x System Event Logging Reference Guide
bgpIpv6NextHops
Description BGP indirect next-hops for IPv6 NLRI
Emergency None
Alert None
Critical None
Error Errors in BGP IPv6 next hop events and state transitions
Warning Log None
Notice Log State transitions of BGP IPv6 next hops
Debug BGP IPv6 indirect next-hop events
Filter 1 router—See description of the bgpRoutes router filter for information about this filter
Filter 2 remote-ipv6-address—Matches on the IPv6 address of the BGP indirect next-hop
bgpKeepAlives
Description BGP keepalive messages
Emergency None
Alert None
Critical None
Info None
Error None
Warning Log Keepalive message received with unexpected additional data after header
Notice Log Keepalive message received; keepalive message sent
Info None
42 ■ bgpIpv6NextHops
Page 67

Chapter 4: B Commands
Debug None
Filter 1 access-class—This filter is not currently supported
Filter 2 peer—See description of the bgpRoutes peer filter for information about this filter
Filter 3 route-map—This filter is not currently supported
Filter 4 router—See description of the bgpRoutes router filter for information about this filter
Filter 5 in—Matches on traffic coming into the router
Filter 6 out—Matches on traffic going out of the router
NOTE: Send messages are logged to the bgpKeepAlives log when a message is added
to the send queue. A debug message is logged in to the bgpConnections log when
the message is actually passed to TCP.
bgpMessages
Description BGP protocol messages
Emergency None
Critical None
Warning Log Unknown message type received; invalid field in received message; notification
Notice Log Open message received or sent; update message received or sent; route-refresh
Alert None
Error None
message received or sent; invalid capability length in received ORF capability; invalid
capability value in received ORF capability; invalid ORF in received ORF capability;
ORF entries exceeded maximum limit in received prefix list
message received or sent; route-refresh-cisco message received or sent; received
ORF capability; received route refresh message with ORF entries
Info None
Debug Keepalive message received or sent (Full decode of message logged if verbosity is
high)
bgpMessages ■ 43
Page 68

JUNOSe 11.1.x System Event Logging Reference Guide
NOTE: Send messages are logged to the bgpMessages log when a message is added
to the send queue. A debug message is logged to the bgpConnections log when the
message is actually passed to TCP.
Filter 1 access-class—This filter is not currently supported
Filter 2 peer—See description of the bgpRoutes peer filter for information about this filter
Filter 3 route-map—This filter is not currently supported
Filter 4 router—See description of the bgpRoutes router filter for information about this filter
Filter 5 in—Matches on traffic coming into the router
Filter 6 out—Matches on traffic going out of the router
bgpNeighborChanges
Description BGP neighbor change
Emergency None
Alert None
Critical None
Error None
Warning Log None
Notice Log A peer has entered into or left the established state; reason for a session going idle
Info None
Debug None
Filter 1 access-class—This filter is not currently supported
Filter 2 peer—See description of the bgpRoutes peer filter for information about this filter
Filter 3 route-map—This filter is not currently supported
44 ■ bgpNeighborChanges
Page 69

Filter 4 router—See description of the bgpRoutes router filter for information about this filter
Filter 5 in—This filter is not currently supported
Filter 6 out—This filter is not currently supported
bgpNextHops
Description VPN and non-VPN BGP indirect next hops
Emergency None
Critical None
Chapter 4: B Commands
Alert None
Error Errors in BGP next hop events and state transitions
Warning Log None
Notice Log State transitions of BGP next hops
Info None
Debug BGP indirect next-hop events
Filter 1 access-class—This filter is not currently supported
Filter 2 peer—See description of the bgpRoutes peer filter for information about this filter
Filter 3 route-map—This filter is not currently supported
Filter 4 router—See description of the bgpRoutes router filter for information about this filter
Filter 5 in—Matches on traffic coming into the router
Filter 6 out—Matches on traffic going out of the router
bgpRoutes
Description BGP routing table updates
bgpNextHops ■ 45
Page 70

JUNOSe 11.1.x System Event Logging Reference Guide
Emergency None
Alert None
Critical None
Error None
Warning Log Failure to add, remove, or modify BGP route in IP forwarding table
Notice Log BGP route added to, removed from, or modified in the IP forwarding table; aggregate
route added to, removed from, or modified in Loc-RIB; network route added to,
removed from, or modified in Loc-RIB; best route for internal peers for a given prefix
became available; best route for internal peers for a given prefix is no longer available,
has changed, or has become available; best route for external peers for a given prefix
is no longer available, has changed, or has become available; MPLS base tunnel used
to reach an indirect next-hop came up or went down; MPLS stacked tunnel for label
came up; indirect next-hop became reachable or unreachable; direct next-hop for
an indirect next-hop changed; MPLS tunnel for Inter-AS label came up or went down;
route added to L2VPN instance; route deleted from L2VPN instance; route modified
for L2VPN instance; -VE device for multihomed local layer 2 site 1 changed from
peer to peer2
Info None
Debug Redistributed route added to, removed from, or modified in Loc-RIB; advertisement
for a given prefix received; withdraw for a given prefix received; local
route-target-filtering route added to or removed from prefix in addressFamily
Filter 1 access-class accessClassName [ route-map routeMapName routeMapOptions |
filtering-router filteringRouterName filteringRouterOptions | in | out ]
■ access-class—Logs events for traffic that matches a specific access class
■ accessClassName —Name of the access class for which you want to log events
■ route-map—Logs events for traffic that matches a specific route map
■ routeMapName—Name of route map for which you want to log events
■ routeMapOptions—In the following format—filtering-router filteringRouterName
filteringRouterOptions | in | out
■ filtering-router—Logs events only if the access class or route map are defined
on a specific virtual router
■ filteringRouterName—Virtual router where the access class or route map or both
are defined
■ filteringRouterOptions—in | out
■ in—Matches on traffic coming into the access class, route map, or virtual router
■ out—Matches on traffic sent out of the access class, route map, or virtual router
46 ■ bgpRoutes
Page 71

Filter 2 peer peerIpAddress | peerIpv6Address
[ access-class accessClassName accessClassOptions |
route-map routeMapName routeMapOptions |
filtering-router filteringRouterName filteringRouterOptions | in | out ]
■ peer—Logs events for traffic that matches a specific peer
■ peerIpAddress—IP address of the peer for which you want to log events
■ peerIpv6Address—IPv6 address of the peer for which you want to log events
■ access-class—Logs events for traffic that matches a specific access class
■ accessClassName—Name of the access class for which you want to log events
■ accessClassOptions—In the following format—filtering-router filteringRouterName
filteringRouterOptions | in | out
■ route-map—Logs events for traffic that matches a specific route map
■ routeMapName—Name of route map for which you want to log events
■ routeMapOptions—In the following format—filtering-router filteringRouterName
filteringRouterOptions | in | out
Chapter 4: B Commands
■ filtering-router—Logs events only if the peer, access class or route map are
defined on a specific virtual router
■ filteringRouterName—Virtual router where the peer, access class or route map
or both are defined
■ filteringRouterOptions—in | out
■ in—Matches on traffic coming into the peer, access class, route map, or virtual
router
■ out—Matches on traffic sent out of the peer, access class, route map, or virtual
router
Filter 3 route-map routeMapName
[ filtering-router filteringRouterName filteringRouterOptions | in | out ]
■ route-map—Logs events for traffic that matches a specific route map
■ routeMapName—Name of route map for which you want to log events
■ filtering-router—Logs events only if the route map is defined on a specific virtual
router
■ filteringRouterName—Virtual router where the route map is defined
■ filteringRouterOptions—in | out
■ in—Matches on traffic coming into the route map or virtual router
■ out—Matches on traffic sent out of the route map or virtual router
Filter 4 router virtualRouterName [ access-class accessClassName accessClassOptions |
route-map routeMapName routeMapOptions |
filtering-router filteringRouterName filteringRouterOptions |
peer peerIpAddress peerOptions | in | out ]
bgpRoutes ■ 47
Page 72

JUNOSe 11.1.x System Event Logging Reference Guide
■ router—Logs events for traffic on a specific virtual router
■ virtualRouterName—Name of virtual router
■ access-class—Logs events for traffic that matches a specific access class on the
specified router
■ accessClassName—Name of the access class for which you want to log events
■ accessClassOptions—In the following format—route-map routeMapName
routeMapOptions | virtual-router virtualRouterName virtualRouterOptions | in |
out
■ route-map—Logs events for traffic that matches a specific route map
■ routeMapName—Name of route map for which you want to log events
■ routeMapOptions—In the following format—virtual-router virtualRouterName
virtualRouterOptions | in | out
■ filtering-router—Logs events only if the access class or route map is defined on
a specific virtual router
bridge
■ filteringRouterName—Virtual router where the access class or route map is defined
■ filteringRouterOptions—In the following format—in | out
■ peer—Logs events for traffic that matches a specific peer
■ peerIpAddress—Address of the peer for which you want to log events
■ peerOptions—In the following format—access-class accessClassName
accessClassOptions | filtering-router filteringRouterName filteringRouterOptions |
route-map routeMapName routeMapOptions | in | out
■ in—Matches on traffic coming into the virtual router, access class, or route map
■ out—Matches on traffic sent out of the virtual router, access class, or route map
Filter 5 in—Matches on traffic coming into the router
Filter 6 out—Matches on traffic going out of the router
Description Bridge group configuration
Emergency None
Alert None
Critical None
Error Bridge interface, learning, aging, and static MAC address errors
48 ■ bridge
Page 73

Warning Log Bridge resources (maximum interfaces, memory exhaustion)
Notice Log Bridge group interface location availability, operation status, and MTU changes
bridgeEngine
Description Bridge engine configuration
Chapter 4: B Commands
Info Bridge group state changes (start, shutdown); bridge interface, learning, aging, and
static MAC address modifications
Debug Verbose bridge interface, learning, aging, and static MAC address configuration and
status
Filter None
Emergency None
Warning Log Bridge engine resources (maximum interfaces, memory exhaustion)
Notice Log Slot status; bridge interface location availability
bridgingMgr
Alert None
Critical None
Error Bridge engine, bridge agent, and bridge interface errors
Info Bridge engine and bridge agent state changes (create, start, stop delete); bridge
engine, bridge agent, and bridge interface modifications
Debug Verbose bridge engine, bridge agent, and bridge interface configuration and status
Filter None
Description Bridging manager configuration
Emergency None
Alert None
bridgeEngine ■ 49
Page 74

JUNOSe 11.1.x System Event Logging Reference Guide
Critical None
Error Bridge mode, bridge group, and subscriber policy errors
Warning Log Bridging manager resources (maximum bridge groups, maximum subscriber policies,
memory exhaustion)
Notice Log None
Info Bridging manager operation state changes (init, start, shutdown); bridge mode, bridge
group, and subscriber policy modifications
Debug Verbose bridge mode, bridge group, and subscriber policy configuration and status
Filter None
bulkStats
Warning Log Operational failures, such as failed transfer–reverting to secondary receiver, file full,
Description Bulk statistics collector
Emergency None
Alert None
Critical None
Error None
file creation failure, file deletion failure
Notice Log File full or file nearly full conditions, preparing to send an SNMP trap
Info Status of user configuration commands
Debug Tracks performance progress of bulkstats application
Filter None
50 ■ bulkStats
Page 75

Chapter 5
C Commands
■ cacGeneral on page 51
■ cacIntf on page 52
■ cliCommand on page 52
■ cliGeneral on page 53
■ connectionManager on page 53
■ cops on page 54
■ copsPr on page 54
■ coreDump on page 55
■ ctreeLog on page 56
cacGeneral
Description CAC general purpose
Emergency None
Alert None
Critical None
Error None
Warning Log Unusual conditions in IGP/CAC interaction
Notice Log None
Info None
Debug General debugging info
Filter None
cacGeneral ■ 51
Page 76

JUNOSe 11.1.x System Event Logging Reference Guide
cacIntf
Description CAC interface events
Emergency None
Alert None
Critical None
Error None
Warning Log Unusual or failure situations in interface processing
Notice Log None
cliCommand
Description CLI commands
Info None
Debug Interface level debugging info
Filter interface interfaceType interfaceSpecifier
■ interface—Logs events for a specific interface
■ interfaceType—Type of interface on which you want to log events
■ interfaceSpecifier—Location of interface in the appropriate format
NOTE: For information about interface types and specifiers, see Interface Types and
Specifiers in JUNOSe Command Reference Guide.
Emergency None
Alert None
Critical None
Error None
52 ■ cacIntf
Page 77

Warning Log None
cliGeneral
Description CLI general log
Chapter 5: C Commands
Notice Log All successful CLI configuration commands
Info All unsuccessful CLI configuration commands; all nonconfiguration commands
Debug None
Filter None
Emergency None
Alert None
Critical None
Error None
Warning Log CLI command mode from prior release no longer exists; the overridden privilege
Notice Log None
Info None
Debug None
Filter None
connectionManager
Description Logging various conditions in the component that manages the chassis fabric.
level command will be discarded
Emergency None
Alert None
Critical 10G and 5G SRP modules only—Detection that the FPGAs have not been loaded
(results in an SRP [and chassis] reset)
cliGeneral ■ 53
Page 78

JUNOSe 11.1.x System Event Logging Reference Guide
Error 10G and 5G SRP modules only—That there is not enough bandwidth for a particular
board in the system, that connections could not be added in the fabric due to resource
limitations (such as memory), that a board was just removed and the resource will
not be needed when this condition is detected momentarily, or that a connection
cannot be closed or a multicast destination cannot be dropped.
Warning Log Cannot connect to a particular source or destination address (board may have just
been removed)
Notice Log A connection that previously could not be closed has now closed; a multicast
destination that previously could not be dropped has now been dropped
Info Various logs to indicate events and transitions for low level diagnosis
Debug Various logs to indicate events and transitions for low level diagnosis
cops
Filter None
Description Common Open Policy Service (COPS) protocol
Emergency None
Alert None
Critical None
Error COPS message with bad header, version, length, or client
Warning Log Unexpected socket event
Notice Log COPS layer enabled or disabled; socket remotely closed
Info None
Debug COPS session instantiation or removal; COPS connection or socket creation or
deletion; keepalive value
Filter None
copsPr
Description COPS-PR general log
54 ■ cops
Page 79

Chapter 5: C Commands
Emergency None
Alert None
Critical None
Error Error decoding COPS-PR messages received from the SDX program
Warning Log Outstanding COPS-PR pool allocations while attempting to shut down SSC client;
temporary resource allocations while sending COPS-PR messages to SDX program
Notice Log None
Info None
coreDump
Warning Log Core dump configuration changes due to core dump monitor; core dump monitor
Debug None
Filter None
Description Core dump events
Emergency None
Alert None
Critical None
Error Connection errors; file open errors; write failures; core dump failures; transfer errors
memory allocation errors
Notice Log Successful line card core dump; core dump attempts; core dump progression; core
dump monitor checks; core dump monitor transfer completions; core dump monitor
dump file deletion
Info None
Debug lcLoader creation; dump request receipt; core dump monitor start; core dump monitor
stop
Filter None
coreDump ■ 55
Page 80

JUNOSe 11.1.x System Event Logging Reference Guide
ctreeLog
Description For internal maintenance of IP routes
Emergency None
Alert None
Critical None
Error Failure in insertion, deletion, and update of IP routes in internal data structure used
to maintain the routes
Warning Log None
Notice Log None
Info None
Debug Creation or deletion of an internal data structure
Filter None
56 ■ ctreeLog
Page 81

Chapter 6
D Commands
■ dcm on page 58
■ dcmEngineGeneral on page 58
■ debounceEvents on page 59
■ debounceGeneral on page 59
■ dhcpCapture on page 60
■ dhcpExternal on page 60
■ dhcpExternalEngine on page 61
■ dhcpGeneral on page 61
■ dhcpIssuLog on page 62
■ dhcpLocalClients on page 63
■ dhcpLocalGeneral on page 63
■ dhcpLocalHighAvailability on page 64
■ dhcpLocalPool on page 64
■ dhcpLocalProtocol on page 65
■ dhcpOfferLog on page 66
■ dhcpPbeGeneral on page 66
■ dhcpProxyGeneral on page 67
■ dhcpRelayGeneral on page 67
■ dhcpRelayNvWriterGeneral on page 68
■ dhcpv6Client on page 68
■ dhcpv6DemuxGeneral on page 69
■ dhcpv6LsGeneral on page 69
■ dismanEventMgr on page 70
■ dnsGeneralLog on page 71
■ dosProtection on page 71
■ ds1 on page 72
■ ds3 on page 72
■ dvmrpGeneral on page 73
■ dvmrpGracefulRestart on page 74
■ 57
Page 82

JUNOSe 11.1.x System Event Logging Reference Guide
■ dvmrpMcastTable on page 75
■ dvmrpProbeRcv on page 75
■ dvmrpProbeSent on page 76
■ dvmrpRtTable on page 76
dcm
Description Dynamic Configuration Manager
Emergency None
Alert None
Critical None
Error None
Warning Log None
Notice Log None
Info None
Debug Schedule engine event; status of dynamic interface creation; receipt of teardown
Filter None
dcmEngineGeneral
Description DCM engine general
Emergency None
Alert None
signal for a dynamic interface; no interface adapter to propagate teardown; creation
of dynamic PPP interface failed; creation of dynamic PPPoE interface failed
Critical None
Error None
Warning Log None
58 ■ dcm
Page 83

Notice Log None
Info None
Debug Giving notify credits to line module; receipt of request buffer from line module;
Filter None
debounceEvents
Description Events causing changes to the upper-layer link status based on Ethernet debounce
Chapter 6: D Commands
starting line module communication session; Ack/Nack dynamic interface creation
request
configuration
Emergency None
Alert Debounce preempted; link stabilized to operational up or down status
Critical None
Error None
Warning Log None
Notice Log Events causing finite state machine transitions
Info Events not causing finite state machine transitions
Debug None
Filter None
debounceGeneral
Description Ethernet debounce configuration status log
Emergency None
Alert None
Critical None
debounceEvents ■ 59
Page 84

JUNOSe 11.1.x System Event Logging Reference Guide
Error Error in enabling or disabling the debounce timer on the Ethernet interface
Warning Log None
Notice Log Debounce timer enabled or disabled on the Ethernet interface
Info None
Debug None
Filter None
dhcpCapture
Description DHCP packet capture
Emergency None
Alert None
Critical None
Error Configuration errors
Warning Log Processing errors (resource exhaustion)
Notice Log None
Info Logged DHCP packets, configured by the ip dhcp-capture command (specify high
verbosity for detail)
Debug Configuration change details; DHCP discover, offer, request, decline, and ACK/NAK
packets on a per-interface basis
Filter None
dhcpExternal
Description DHCP external
Emergency None
Alert None
60 ■ dhcpCapture
Page 85

Critical None
Error Configuration errors; client processing errors (invalid data)
Warning Log Client processing errors (resource exhaustion)
Notice Log Configuration changes
Info None
Debug Configuration change details; client events
Filter None
Chapter 6: D Commands
dhcpExternalEngine
Description DHCP external engine
Emergency None
Alert None
Critical None
Error Configuration errors; client processing errors (invalid data)
Warning Log None
Notice Log None
Info System events (line cards online/offline)
Debug Configuration change details; client events
Filter None
dhcpGeneral
Description DHCP general
Emergency None
dhcpExternalEngine ■ 61
Page 86

JUNOSe 11.1.x System Event Logging Reference Guide
Alert Rvn8
Critical None
Error None
Warning Log None
Notice Log None
Info None
Debug DHCP message received
Filter None
dhcpIssuLog
Description DHCP ISSU information
Emergency None
Warning Log Buffering capacity exceeded between DHCP engine and the driver/ISSU shadow
Notice Log None
Alert None
Critical None
Error Error recreating DHCP ISSU IC shadow and its data structures, followed by an ISSU
halt
driver
Info None
Debug Normal operation: packet processing events, creation and deletion of DHCP common
objects during ISSU
Filter None
62 ■ dhcpIssuLog
Page 87

dhcpLocalClients
Description DHCP local server clients
Emergency None
Alert None
Critical None
Error Cannot find the client’s interface; cannot find the client to expire the lease or remove
Chapter 6: D Commands
it from the database; trying to expire client’s lease or remove it from database with
bad IP address; requested MAC address does not match the available address; cannot
allocate SDX subscriber information
Warning Log Cannot find the DHCP instance for the client with an expired lease; cannot find the
Notice Log None
Info None
Debug Removing stale offers to clients and stale clients; adding and removing clients;
Filter None
dhcpLocalGeneral
Description General DHCP local server
Emergency None
Alert None
DHCP instance to release the client IP address; secondary DNS without primary DNS
configured, using DHCP values; secondary NetBIOS Name Server (NBNS) without
primary NBNS configured, using DHCP values
expiring client’s lease; client’s transactions with DHCP local server
Critical None
Error Memory allocation failure; cannot find interface location for the UID
Warning Log No DHCP instance to process the received packet; hard limits reached; packet
discarded due to no resources
dhcpLocalClients ■ 63
Page 88

JUNOSe 11.1.x System Event Logging Reference Guide
Notice Log DHCP local server not configured; client’s session failed to start
Info Client per-interface limit exceeded; client per-interface exceeded condition abated
Debug Any log message that indicates the status of the general operation of the DHCP local
server; NVS actions; grace period lease state; configuration changes
Filter None
NOTE: This category replaces the dhcpLocalServerGeneral category.
dhcpLocalHighAvailability
Description DHCP local high availability
Emergency None
Alert None
Critical None
Error Out of resources errors; nonrecoverable software errors during client restoration or
mirroring, pool creation/modification; recoverable software errors during modification
of existing client
Warning Log Recoverable software errors during client, server or pool configuration; out of
resources on new client, server, or pool configuration; timer configuration problems
Notice Log Normal recovery following SRP switch
Info None
Debug Normal client, server, pool processing
Filter None
dhcpLocalPool
Description DHCP local address pool, including normal, linked, and shared pools
Emergency None
64 ■ dhcpLocalHighAvailability
Page 89

Chapter 6: D Commands
Alert Local pool IP address is exhausted (address limit violation)
Critical Higher limit of address pool utilization reached
Error None
Warning Log Lower limit of address pool utilization reached; invalid DHCP local address pool
attributes
Notice Log None
Info None
Debug DHCP local address pool resolution; address allocation
Filter None
dhcpLocalProtocol
Description DHCP local server protocol
Emergency None
Alert None
Critical None
Error Cannot find interface; remote client bind add failed; client failed to decline IP address;
Warning Log AAA not responding; SDX program not responding; rediscovering with no IP address
client failed to decline a null offered IP address; delete remote client entry failed
allocated; a renewal is received on the line module for an unknown client; secondary
DNS without primary DNS configured, using DHCP values; secondary NetBIOS Name
Server (NBNS) without primary NBNS configured, using DHCP values; duplicate MAC
address detected
Notice Log None
Info None
Debug Received packet; transmit packet; authentication status; DHCP local server state
transitions
Filter interface interfaceType interfaceSpecifier
dhcpLocalProtocol ■ 65
Page 90

JUNOSe 11.1.x System Event Logging Reference Guide
■ interface—Logs events for a specific interface
■ interfaceType—Type of interface for which you want to log events
■ interfaceSpecifier—Location of interface in the appropriate format
NOTE: For information about interface types and specifiers, see Interface Types and
Specifiers in JUNOSe Command Reference Guide.
dhcpOfferLog
Description DHCP offer selection process log
Emergency None
Alert None
Critical None
Error None
Warning Log None
Notice Log None
Info None
Debug Status of the offer selection process
Filter None
dhcpPbeGeneral
Description DHCP Proxy Backend Log
Emergency None
Alert None
Critical None
Error Heap exhaustion
66 ■ dhcpOfferLog
Page 91

Warning Log Failure to send a DHCP message to a client
Notice Log Failure to restore client after reboot or interface change; failure to allocate memory
Info None
Debug Status of task and DHCP operations
Filter None
dhcpProxyGeneral
Description DHCP Proxy general
Chapter 6: D Commands
from task-controlled pools
Emergency None
Alert None
Critical None
Error None
Warning Log None
Notice Log None
Info None
Debug Control flow and key events
Filter None
dhcpRelayGeneral
Description DHCP Relay general
Emergency None
Alert None
Critical None
dhcpProxyGeneral ■ 67
Page 92

JUNOSe 11.1.x System Event Logging Reference Guide
Error None
Warning Log None
Notice Log Warm start recovery problems (high availability and unified ISSU)
Info None
Debug Control flow and key events, packets that are transmitted using the layer 2 unicast
feature, status and changes to DHCP relay agent information option and suboptions
Filter None
dhcpRelayNvWriterGeneral
Description DHCP host route preservation
Emergency None
Alert None
Critical None
Error Out of memory conditions
Warning Log Unexpected unified ISSU signal, removing all NVS and routing table entries at startup,
removing routing table entries at startup due to inconsistencies
Notice Log Removing or adding entries on start up due to inconsistencies
Info None
Debug Receiving unified ISSU signal, construction of the writer, saving to NVS, removing
router, removing routes, adding routes
Filter None
dhcpv6Client
Description DHCPv6 internal test client events
Emergency None
68 ■ dhcpRelayNvWriterGeneral
Page 93

Alert None
Critical None
Error Problems communicating with IPv6; invalid message types received; out-of-memory
conditions; serious DHCPv6 protocol state errors; internal errors
Warning Log Minor DHCPv6 protocol errors
Notice Log None
Info None
Debug None
Chapter 6: D Commands
Filter None
dhcpv6DemuxGeneral
Description DHCPv6 packet demultiplexer events
Emergency None
Alert None
Critical None
Error UDP transmit errors, out-of-memory conditions, internal errors
Warning Log Invalid DHCPv6 packet type received
Notice Log None
Info None
Debug None
Filter None
dhcpv6LsGeneral
Description DHCPv6 local server events
dhcpv6DemuxGeneral ■ 69
Page 94

JUNOSe 11.1.x System Event Logging Reference Guide
Emergency None
Alert None
Critical None
Error Failure to create server (bad router or out of memory)
Warning Log Attempt to remove a nonexistent server
Notice Log Failure to create server (IPv6 not licensed); cold/warm restart of DHCPv6 local server;
before/after restoring client bindings;
Info None
Debug Server bind, creation, deletion, unbind, and restoration of bindings post warm SRP
Filter None
dismanEventMgr
Description Distributed management event manager
Emergency None
Alert None
Critical None
Error Configuration errors; Sampling, testing and setting errors
Warning Log Limit maximums reached
Notice Log Trigger values reached
switchover
Info Application started; traps activated; sampling information provided
Debug None
Filter None
70 ■ dismanEventMgr
Page 95

dnsGeneralLog
Description DNS general
Emergency None
Alert None
Critical None
Error None
Warning Log Failure to post a message to DNS about the query response from DNS server
Chapter 6: D Commands
Notice Log None
Debug Dump DNS response packet; trace DNS query submission; trace DNS response parsing
dosProtection
Description DoS general
Emergency None
Critical Suspicious control flows exceed threshold for specific line module; possible distributed
Info None
and processing; trace dropped queries if router is shutting down or DNS disabled in
virtual router; trace DNS cache cleanup
Filter None
Alert None
DoS attack
Error Control flow changed to suspicious.
Warning Log Flow table overflow, protocol (or priority) has transitioned to suspicious
Notice Log Suspicious control flow returned to nonsuspicious protocol (or priority) has transitioned
from suspicious
dnsGeneralLog ■ 71
Page 96

JUNOSe 11.1.x System Event Logging Reference Guide
Info Suspicious control flow deleted
Debug None
Filter None
ds1
Description DS1 layer
Emergency None
Alert None
Critical None
ds3
Error None
Warning Log Interface creation or binding failure
Notice Log Failure to bring line module application online; dropped interface state change
notification due to lack of resources; discarded stale line module notification
Info Dropped interface state change notification for unknown or removed interface
Debug None
Filter None
Description DS3 layer
Emergency None
Alert None
Critical None
Error None
Warning Log Failure to create or bind interface
72 ■ ds1
Page 97

Notice Log Failure to bring line module application online; dropped interface state change
Debug None
dvmrpGeneral
Description DVMRP general
Emergency None
Chapter 6: D Commands
notification due to lack of resources; discarded stale line module notification
Info Dropped interface state change notification for unknown or removed interface
Filter None
Alert None
Critical None
Error Memory allocation errors; bad parameters (internal errors); designated forwarder
errors (two for same interface, DoNotForward by no designated forwarder); processing
prune errors; graft errors; internal errors; catastrophic RT table errors; management
interaction errors; NVS errors
Warning Log Unable to add local route; routeHogCheck; routeLimit
Notice Log Route expiration; pruneProcessing (send or receive); graftAck processing; source
group (SG) state information; deletion of an output interface; nbrQuickDelete;
nbrReset; nbrTimeOut; error adding neighbor on Route Report Reception
Info Designated forwarder election information; sending graft; timer expired for
MulticastEntry; attempting to log duplicate accept filter; external route deleted or
added
Debug Local address creation or deletion; information about accept filters; dvmrpInterface
creation or deletion; sgTimeout information; noMoreOifs info; sg creation information;
multicastForwarding enabled or disabled; DvmrpInit; dvmrpEnable/Disable;
rpfCallback
Filter 1 interface interfaceType interfaceSpecifier
■ interface—Logs events for a specific interface
■ interfaceType—Type of interface for which you want to log events
■ interfaceSpecifier—Location of interface in the appropriate format
dvmrpGeneral ■ 73
Page 98

JUNOSe 11.1.x System Event Logging Reference Guide
NOTE: For information about interface types and specifiers, see Interface Types and
Specifiers in JUNOSe Command Reference Guide.
Filter 2 router virtualRouterName [ interface interfaceType interfaceSpecifier ]
■ router—Logs events for a specific virtual router
■ virtualRouterName—Name of virtual router for which you want to log events
■ interface—Logs events on a specific interface on the virtual router
■ interfaceType—Type of interface for which you want to log events
■ interfaceSpecifier—Location of interface in the appropriate format
NOTE: For information about interface types and specifiers, see Interface Types and
Specifiers in JUNOSe Command Reference Guide.
dvmrpGracefulRestart
Description DVMRP graceful restart
Emergency None
Alert None
Critical None
Error None
Warning Log None
Notice Log DVMRP graceful restart complete
Info None
Debug None
Filter None
74 ■ dvmrpGracefulRestart
Page 99

dvmrpMcastTable
Description DVMRP multicast table messages
Emergency None
Alert None
Critical None
Error Error removing MulticastEntry; adding duplicate MulticastEntry; adding nonexistent
Chapter 6: D Commands
MulticastEntry; attempting to send prune to nonexistent neighbor; error deleting
MulticastEntry; error adding outgoing interfaces
Warning Log Deleting MulticastEntry with no SG state found; attempting to create MulticastEntry,
Notice Log Creating MulticastEntry
Info rePruning; delOif; add outgoing interface; not adding outgoing interface for some
Debug None
Filter 1 interface—See description of the dvmrpGeneral interface filter for information about
Filter 2 router—See description of the dvmrpGeneral router filter for information about this
dvmrpProbeRcv
Description DVMRP probe received
Emergency None
but unable to do so
reason; creating sgoiflist; pruneDelayCallback; prune; deleting MulticastEntry
this filter
filter
Alert None
Critical None
Error None
Warning Log None
dvmrpMcastTable ■ 75
Page 100

JUNOSe 11.1.x System Event Logging Reference Guide
Notice Log procProbe new neighbor
Info None
Debug Processing probe (verified has our address in packet); display probe
Filter 1 interface—See description of the dvmrpGeneral interface filter for information about
this filter
Filter 2 router—See description of the dvmrpGeneral router filter for information about this
filter
dvmrpProbeSent
Description DVMRP probe sent
Emergency None
Alert None
Critical None
Error None
Warning Log None
Notice Log None
Info None
Debug Send probe
Filter 1 interface—See description of the dvmrpGeneral interface filter for information about
this filter
Filter 2 router—See description of the dvmrpGeneral router filter for information about this
filter
dvmrpRtTable
Description DVMRP Routing Table
Emergency None
76 ■ dvmrpProbeSent
 Loading...
Loading...