Page 1

WIRELESS
DUAL-BAND
ROUTER
USER MANUAL
MODEL 524988 (450N Gb)
MODEL 525268 (300N)
525268
INT-524988/525268-UM-0312-03
Page 2

Thank you for purchasing the INTELLINET NETWORK SOLUTIONS™ Wireless 300N
Dual-Band Router, Model 525268, or the Wireless 450N Dual-Band Gigabit Router,
Model 524988.
The latest in wireless networking, this Wireless Router serves multiple purposes —
an access point that provides both 2.4 GHz and 5 GHz wireless simultaneously, a
wireless bridge, a wireless repeater, a WDS repeater, a four-port router for your
hard-wired Ethernet devices, a rewall, and access and content control — and
brings it all together to maximize your high-speed Internet access.
Additional features:
• Dual-band operation that provides twice the bandwidth and less interference
• Up to 450 Mbps network link speed for 524988; up to 300 Mbps for 525268
• Model 524988 supports advanced 3T3R MIMO technology, signicantly
enhancing throughput and coverage range; 2T2R MIMO with Model 525268
• Supports WMM function to meet the multi-media data bandwidth requirement
• Supports Wi-Fi Protected Setup (WPS)
• Supports WEP and WPA/WPA2 (TKIP and AES) data encryption
• Supports Access Point, Station Infrastructure, Bridge Point-to-Point, Bridge
Point-to-Multi-Point, WDS and Universal Repeater modes
• DHCP server assigns IP addresses for all LAN users
• DHCP server supports static lease management
• Supports virtual server, port forwarding and DMZ (demilitarized zone)
• Supports DDNS (dynamic DNS)
• Supports UPnP (Universal Plug and Play)
• Integrated anti-DOS rewall
• QoS (Quality of Service) bandwidth management
• VPN Passthrough (PPTP, IPsec, L2TP)
• Easy Internet setup through WAN connection wizard
• Easy installation through Web-based user interface
• System status
• Security log
• Firmware upgradeable
• Complies with 5 GHz IEEE 802.11a/n standards and 2.4 GHz IEEE 802.11b/g/n
standards
• Three-Year Warranty
Package Contents
• Wireless 300N Dual-Band Router or Wireless 450N Dual-Band Gigabit Router
• Quick install guide, plus user manual on CD
• Power adapter and Ethernet Cat5 RJ45 cable: 1.0 m (3 ft.)
NOTE: Some screen images have been modied to t the format of this manual.
2
Page 3
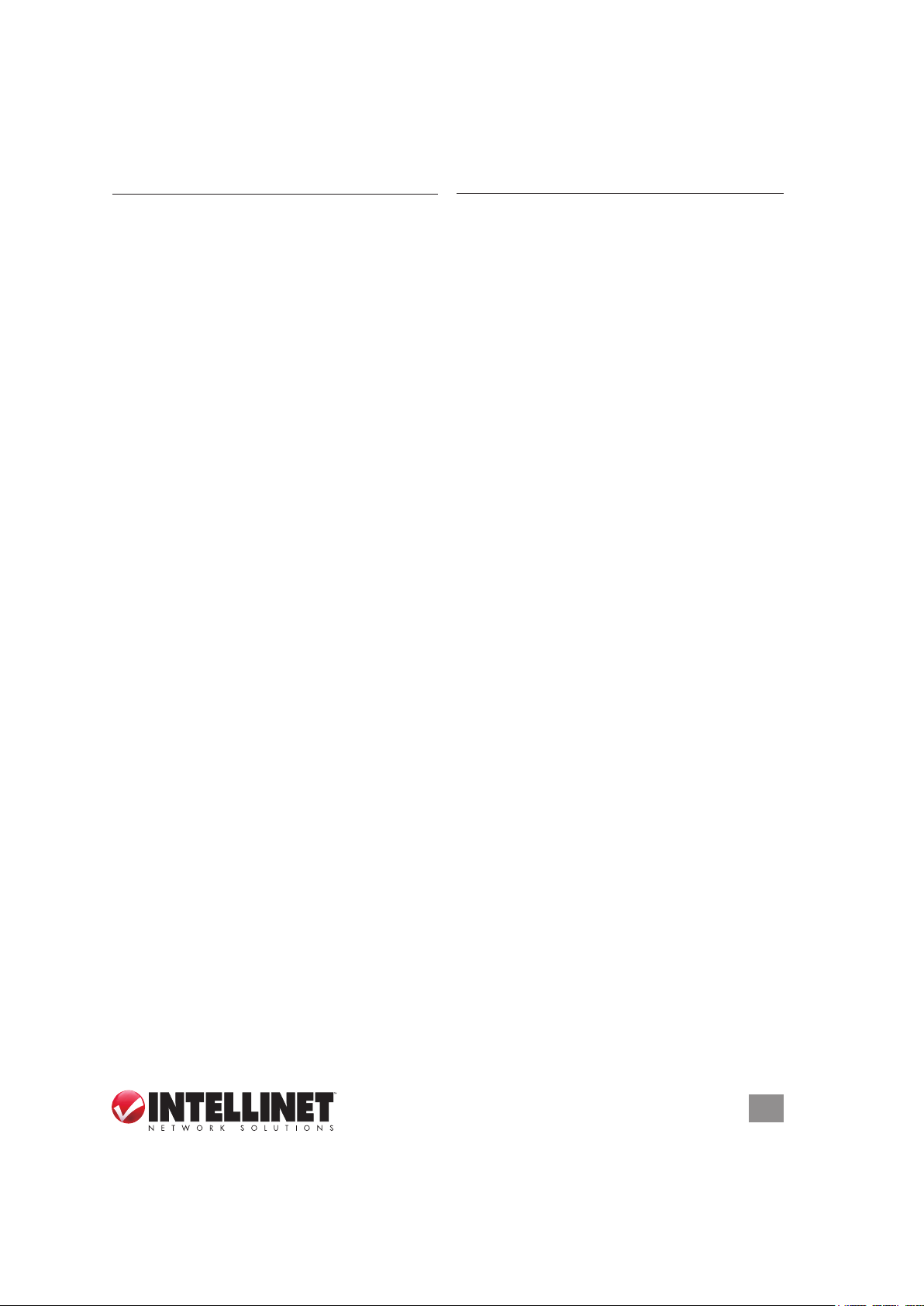
TABLE OF CONTENTS
section page section page
1 HARDWARE ...........................................5
1.1 Front Panel Display .......................... 5
1.2 Back Panel Display ..........................5
2 SYSTEM & NETWORK SETUP .............6
2.1 Connecting the Router .....................6
2.2 Obtaining an IP Address ..................6
2.2.1 Windows XP Setup .................... 7
2.2.2 Windows Vista/7 Setup .............. 9
2.2.3 Router IP Address Lookup .......10
2.3 Quick Setup ................................... 13
2.3.1 Cable Modem (Dynamic IP) ..... 14
2.3.2 Fixed IP xDSL (Static IP) ......... 15
2.3.3 PPPoE xDSL ...........................16
2.3.4 PPPTP xDSL ........................... 16
2.3.5 L2TP xDSL .............................. 18
2.3.6 Telstra BigPond ....................... 18
2.4 General Setup ................................ 19
2.4.1 Time Zone / Auto-Synch .......... 20
2.4.2 Changing Mngmt. Password ....20
2.4.3 Remote Management ..............21
2.5 WAN Setup ....................................22
2.5.1 Dynamic IP ..............................23
2.5.2 Static IP ...................................23
2.5.3 PPPoE ..................................... 24
2.5.4 PPPTP ..................................... 24
2.5.5 L2TP ........................................ 25
2.5.6 Telstra BigPond .......................26
2.5.7 DNS ......................................... 26
2.5.8 DDNS ......................................27
2.5.9 WISP .......................................28
2.6 LAN Conguration .........................29
2.6.1 LAN IP ..................................... 30
2.6.2 DHCP Server ...........................30
2.6.3 Static DHCP Leases Table ...... 31
2.7 WLAN Conguration ...................... 32
2.7.1 Basic Wireless Settings ........... 32
2.7.2 Advanced Wireless Settings .... 34
2.7.3 Wireless Security .....................36
2.7.4 Wireless Access Control .......... 39
2.7.5 WPS ........................................40
2.7.6 Security Tips ............................ 41
3 ADVANCED FUNCTIONS ....................43
3.1 QoS ................................................43
3.1.1 Basic QoS Settings ..................43
3.1.2 Adding a new QoS Rule ..........44
3.2 NAT ................................................ 45
3.2.1 Port Forwarding ....................... 46
3.2.2 Virtual Server ...........................47
3.2.3 Port Mapping ........................... 48
3.2.4 UPnP .......................................49
3.2.5 ALG .........................................50
3.3 Firewall ........................................... 50
3.3.1 Access Control ........................50
3.3.2 Add PC .................................... 52
3.3.3 URL Blocking ........................... 53
3.3.4 DoS Attack Prevention.............54
3.3.5 DMZ .........................................55
4 ADDITIONAL FUNCTIONS ..................57
4.1 S t at u s ............................................. 57
4.1.1 Internet Connections ...............57
4.1.2 Device Status ..........................58
4.1.3 System Log .............................. 58
4.1.4 Security Log ............................ 59
4.1.5 Active DHCP Client .................59
4.1.6 Statistics .................................. 59
4.2 Tools ..............................................60
4.2.1 Conguration Tools .................. 60
4.2.2 Firmware Upgrade ................... 61
4.2.3 Reset ....................................... 62
5 TROUBLESHOOTING .......................... 63
6 GLOSSARY ..........................................65
7 SPECIFICATIONS................................. 67
TABLE OF CONTENTS
3
Page 4

SAFETY GUIDELINES
For the protection of equipment users and connected devices, follow these safety
guidelines:
1. This router is designed for indoor use only; do not place this router outdoors.
2. Do not place or use this router in excessively hot or humid environments.
3. Do not yank any connected cables.
4. Firmly secure this device if it’s placed at any signicant height to prevent
damage or injury should it fall.
5. Router accessories such as the antenna and power supply should be considered
dangerous when handled by children under the age of 3. Keep this device out
of the reach of children.
6. The router will become hot when used for long time. This is normal and is not a
malfunction, but keep the router away from paper, cloth and other ammable
materials.
7. There are no user-serviceable parts inside the router. If the router is not working
properly, contact your dealer (place of purchase) and ask for help. Do not
disassemble the router, as doing so will void the warranty.
8. If the router falls into water while it’s powered on, do not pick it up with your
hands. Disconnect the power before you do anything, or contact an
experienced technician for help.
9. If you smell something strange, or if you see smoke coming from the router or
power supply, remove the power supply or switch the electrical power off
immediately and call the dealer for help.
4
SAFETY GUIDELINES
Page 5
1 HARDWARE
1.1 Front Panel Display
Shown: Model 524988
LED Status Description
POWER On Router is switched on and correctly powered.
2.4G / 5G On Indicates that the particular WLAN mode is active.
Off The WLAN mode is not active.
Flashing Wireless data is being received and/or transmitted.
WAN On The WAN port is connected to a cable or DSL modem.
Off No device is connected to the WAN port.
Flashing Data trafc on WAN port.
LNK/ACT On A device is connected to the LAN port.
(1-4) Off No device is connected to the LAN port.
Flashing Data trafc on LAN port.
1000M On A device is connected at Gigabit speed
Off A device is connected at either 10 or 100 Mbps.
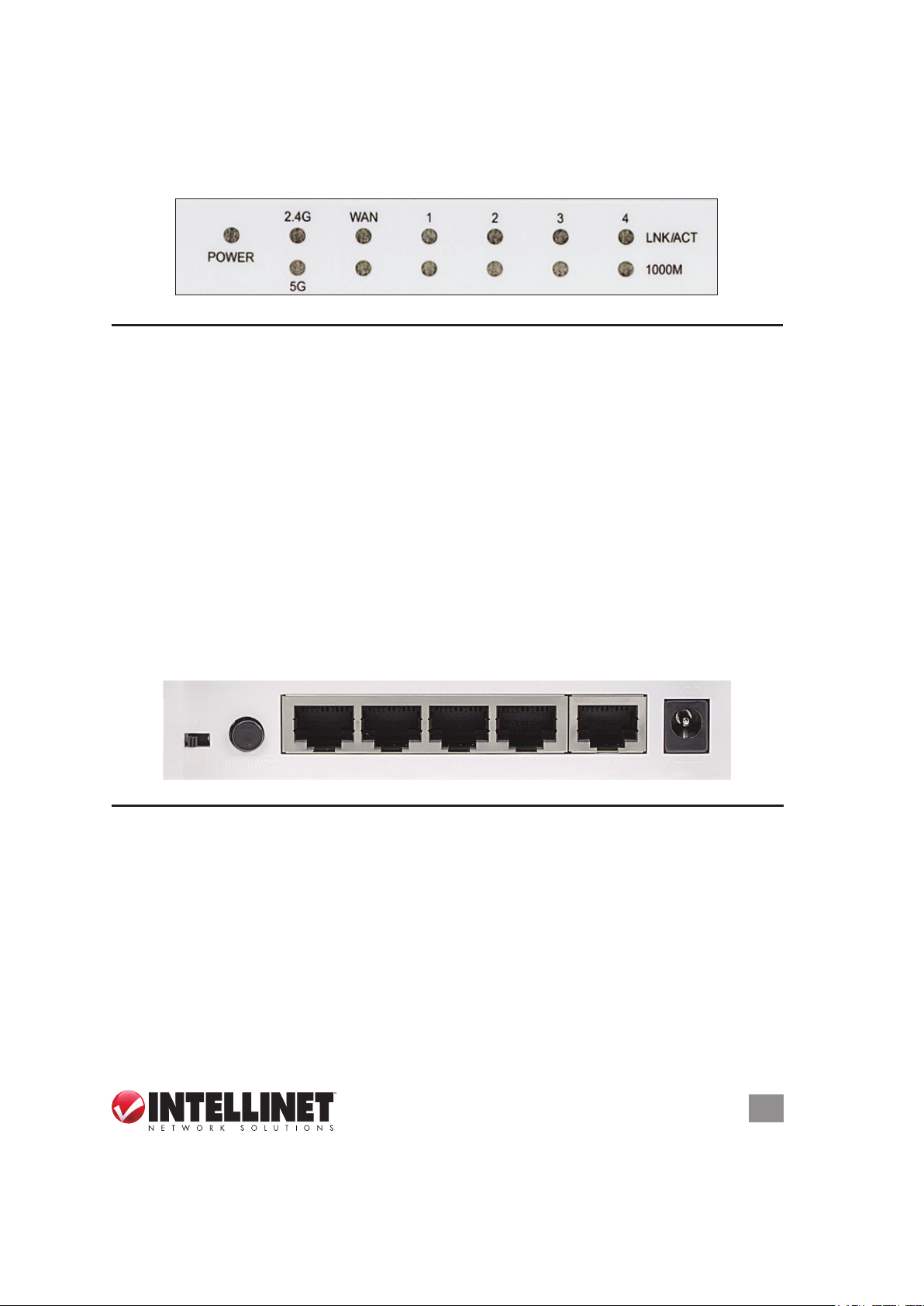
1.2 Back Panel Display
Shown: Model 525268
5VDC
Radio
ON/OFF
Re se t/WP S
4 3
2 1
WAN
Feature Description
Antennas All antennas are xed-dipole with 3 dBi of gain each.
Radio Activate or deactivate the wireless functions with this ON/OFF switch.
Reset/ Reset the router to factory default settings (clear all settings) or start the
WPS WPS function. Press and hold for 10 seconds to restore all settings to
factory defaults; press once for less than 5 seconds to start the 2.4GHz
WPS function; press twice for less than 5 seconds to start the 5GHz WPS.
1-4 Local Area Network (LAN) ports 1 to 4.
WAN Wide Area Network (WAN/Internet) port.
5 / 12 VDC Connects the A/C power adapter (Model 525268 = 5V DC; 524988 = 12V DC )
HARDWARE
.
5
Page 6
2 SYSTEM & NETWORK SETUP
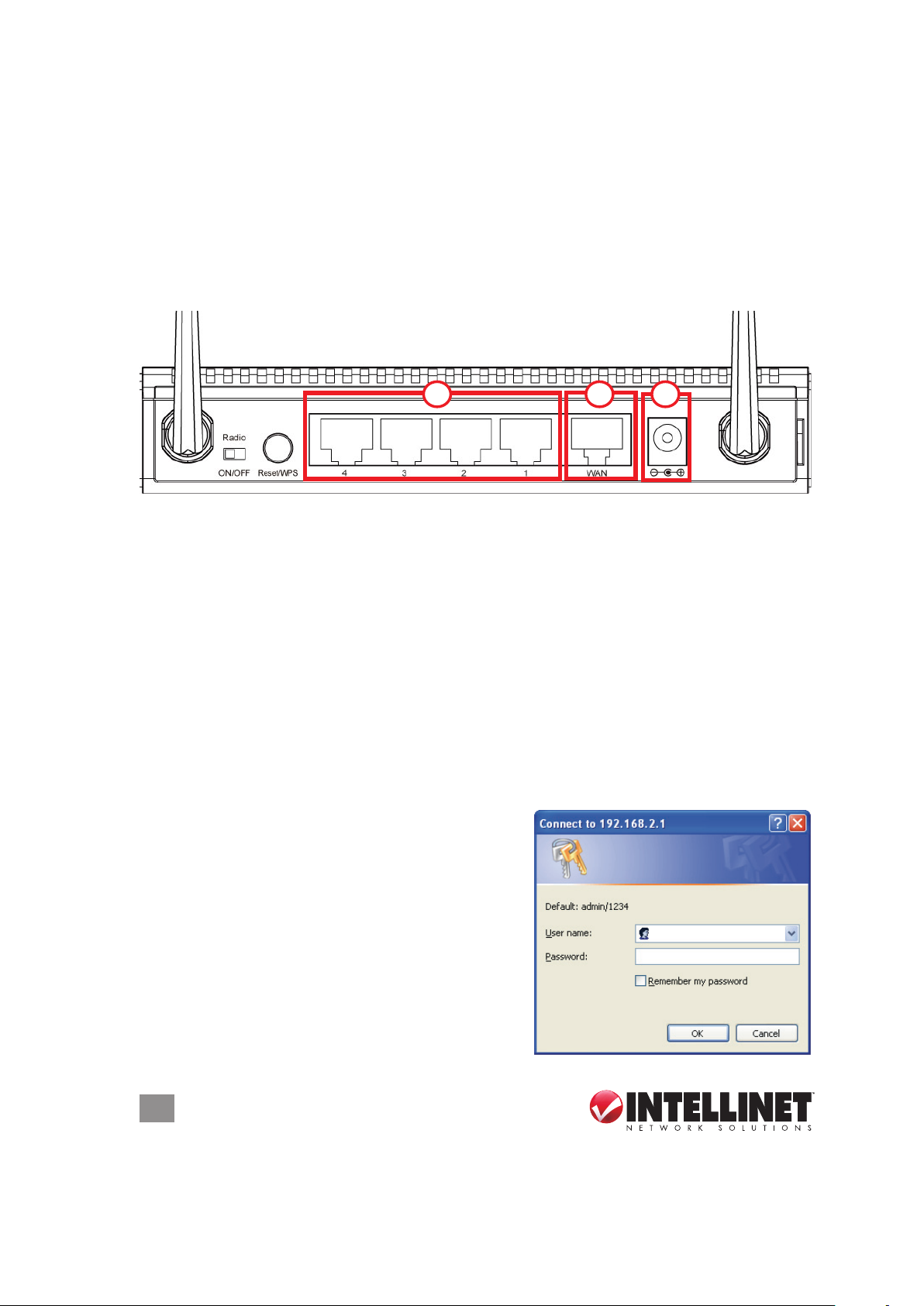
2.1 Connecting the Router
1. Connect your DSL or cable modem to the WAN port of the router using the
provided RJ45 Ethernet cable. NOTE: Standard modems provided by Internet
service providers come with at least one LAN/Ethernet port, which connects to
the WAN port of the router.
Depicted: Model 525268
312
2. Connect all your computers and network devices (network-enabled components
like game consoles, network media players, network storage units or LAN
switches) to the LAN ports (1-4) of the router.
3. Connect the A/C power adapter to the wall socket, then connect it to the power
jack of the router.
4. Check all LEDs on the front panel. The PWR LED should be on, and the WAN
and LAN LEDs should be on if the computer or network device connected to the
corresponding router port(s) is powered on and correctly connected.
2.2 Obtaining an IP Address
Before you can connect to the router and start conguration procedures, your
computer must be able to obtain an IP address automatically (that is, to use a
dynamic IP address). This is the default setup
for any standard Windows computer, and it
normally is not required to make any changes.
1. With your computer connected to a LAN
port on the router, activate the network
connection. Start your Web browser and
open http://192.168.2.1 to display a login
window (right).
2. Enter “admin” as the username and “1234” as
the password, then click “OK.”
6
SYSTEM & NETWORK SETUP
Page 7
NOTE: If this procedure is successful, skip the following subsections and proceed
to 2.3 Using Quick Setup. If the above procedure doesn’t result in your obtaining
an IP address, or if you know that your computer has a static IP address setup,
follow the steps in the appropriate subsection below.
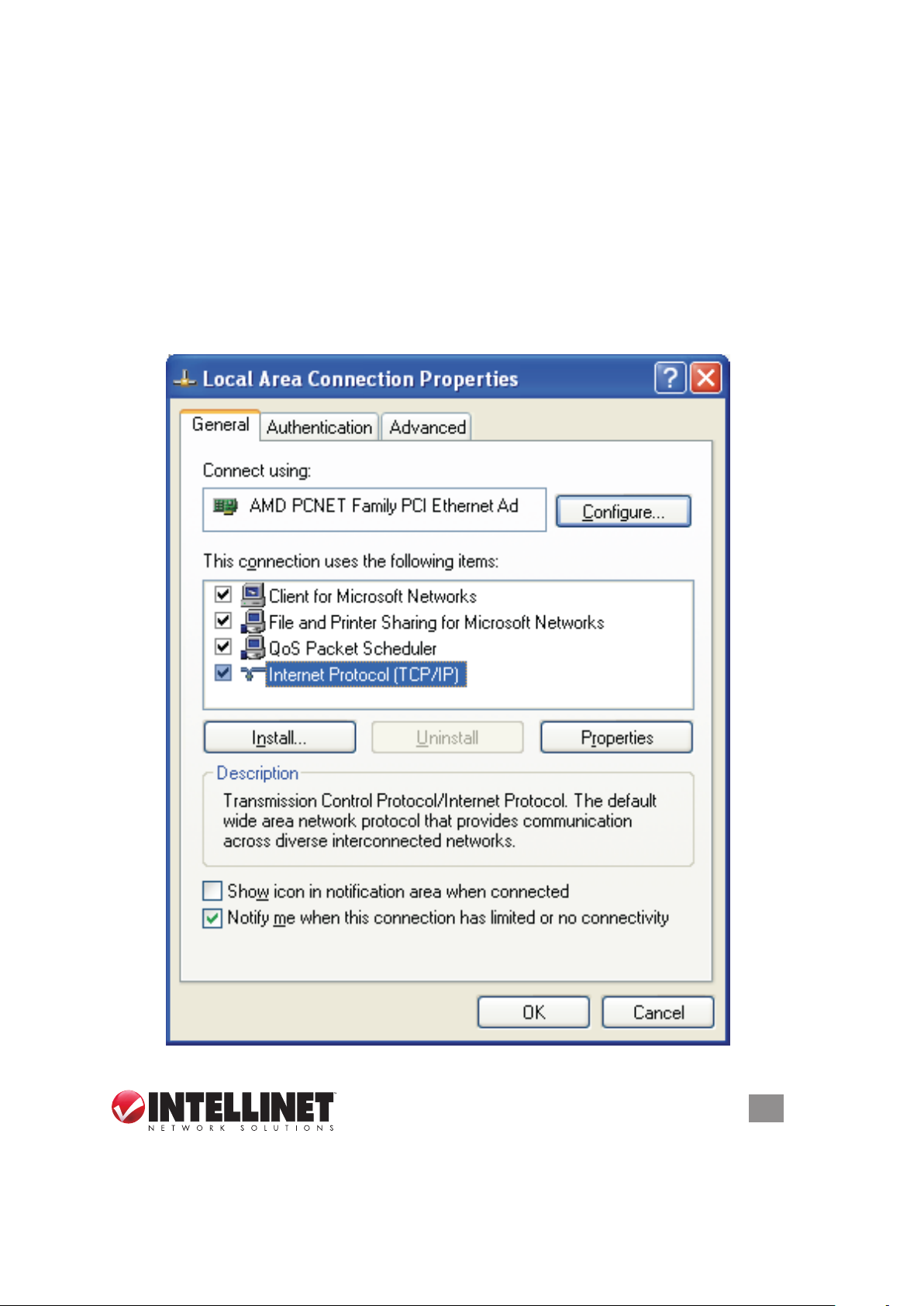
2.2.1 Windows XP IP Address Setup
1. Click “Start,” then go to the control panel. Double-click the Network & Internet
Connections icon, then click “Network Connections” and double-click “Local
Area Connection” to display the Local Area Connection Properties window.
Click “Properties.”
SYSTEM & NETWORK SETUP
7
Page 8
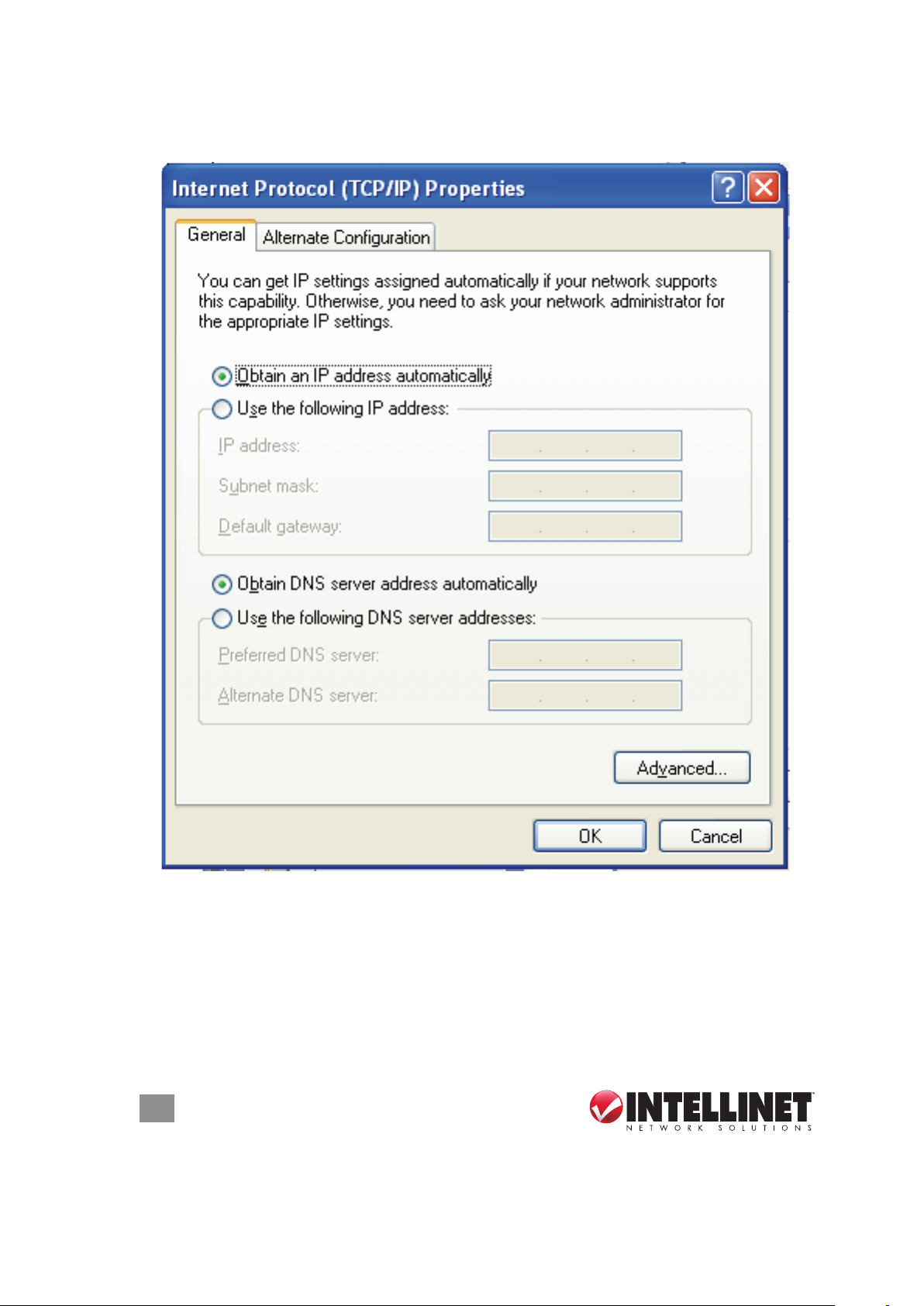
2. Select “Obtain an IP address automatically” and “Obtain DNS server address
automatically,” then click “OK.”
8
SYSTEM & NETWORK SETUP
Page 9
2.2.2 Windows Vista/7 IP Address Setup
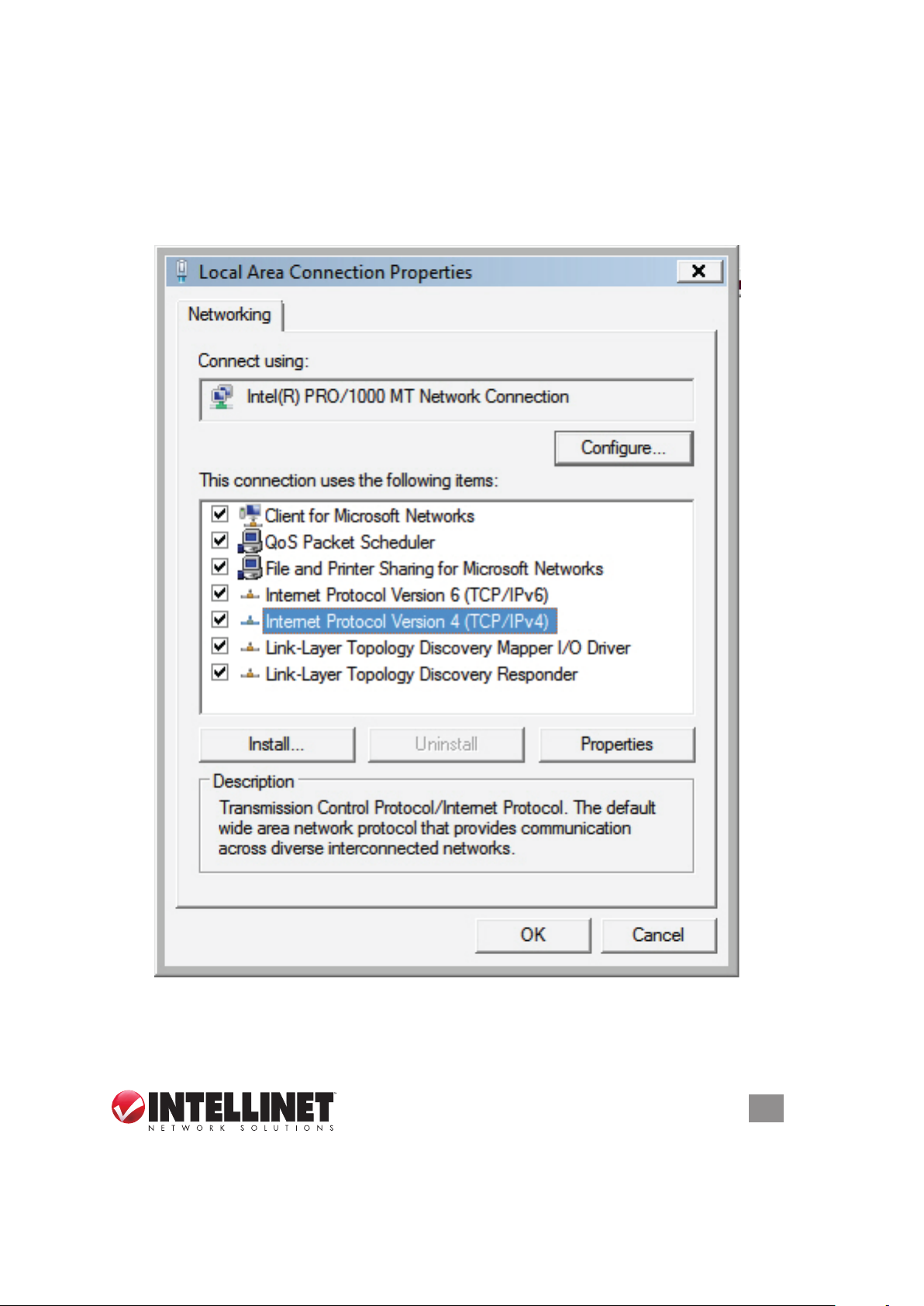
1. Click “Start,” then go to the control panel. Click “View Network Status and Tasks,”
then click “Manage Network Connections.” Right-click “Local Area Network,”
then select “Properties.” With the Local Area Connection Properties window
displayed, select “Internet Protocol Version 4 (TCP / IPv4),” and click “Properties.”
SYSTEM & NETWORK SETUP
9
Page 10
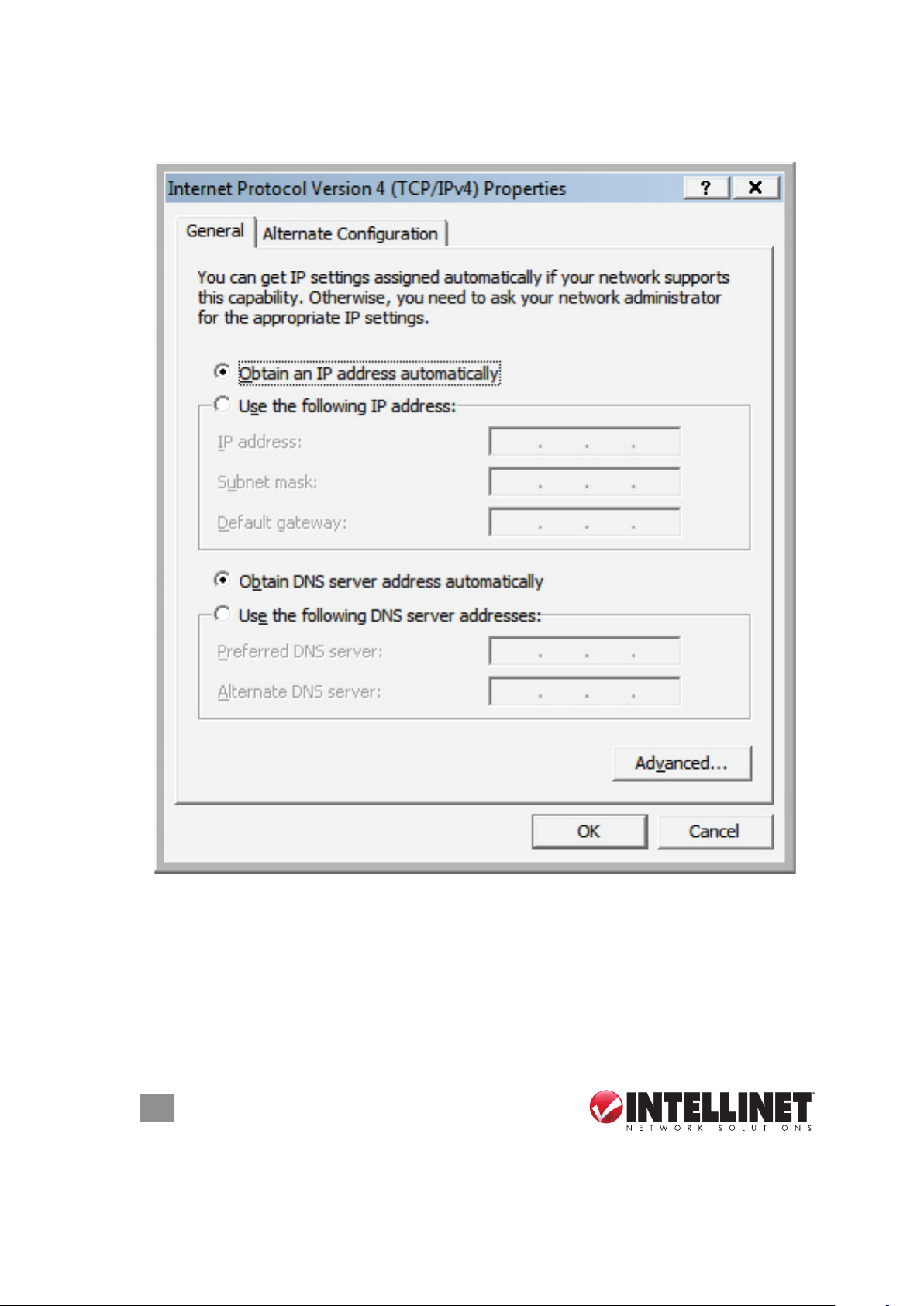
2. Select “Obtain an IP address automatically” and “Obtain DNS server address
automatically,” then click “OK.”
2.2.3 Router IP Address Lookup
1. After the IP address is set up, click “Start” at the bottom-left of the desktop, then
click “Run.”
10
SYSTEM & NETWORK SETUP
Page 11
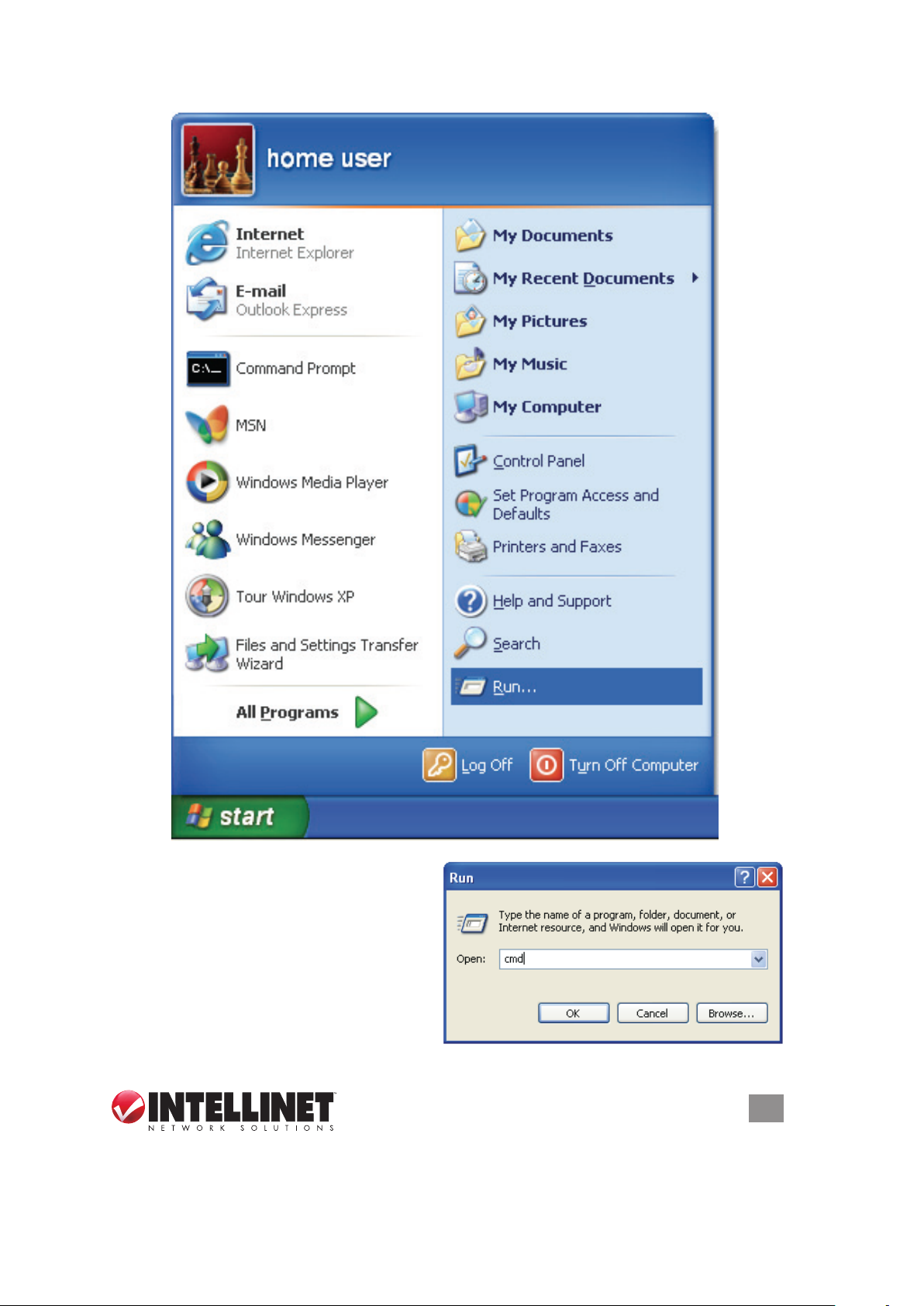
2. With the Run window displayed,
enter “cmd” in the “Open:” text eld,
then click “OK.”
SYSTEM & NETWORK SETUP
11
Page 12

3. Enter “ipcong,” then press <Enter>. The IP address displays, followed by the
default gateway. In the example below, the IP address of the router is
192.168. 2 .1.
NOTE: If the IP address of the gateway is not displayed, or if the address begins
with 169, recheck the network connection between your computer and the router,
and recheck each step of the network setup procedure.
4. Once your computer has obtained an IP address from the router, open your Web
browser and enter the IP address of the router into the address bar. When the
login window displays (see 2.2 above), enter the username (“admin”) and the
password (“1234”). Press “OK” to display the router’s Web management interface.
NOTE: If you can’t see the Web management interface and you’re being prompted
to enter the username and password again, it means you didn’t enter the correct
username and password. Retype the username and password. If you’re certain
that the username and password are correct, refer to 4-2 Troubleshooting to
perform a factory reset to set the password back to the default value.
TIP: This page (see 2.3 Quick Setup below) shows the four primary setting
categories: QuickSetup, General Setup, Status and Tools. You can jump to
another menu category directly by clicking the link at the top-right of each screen.
12
SYSTEM & NETWORK SETUP
Page 13
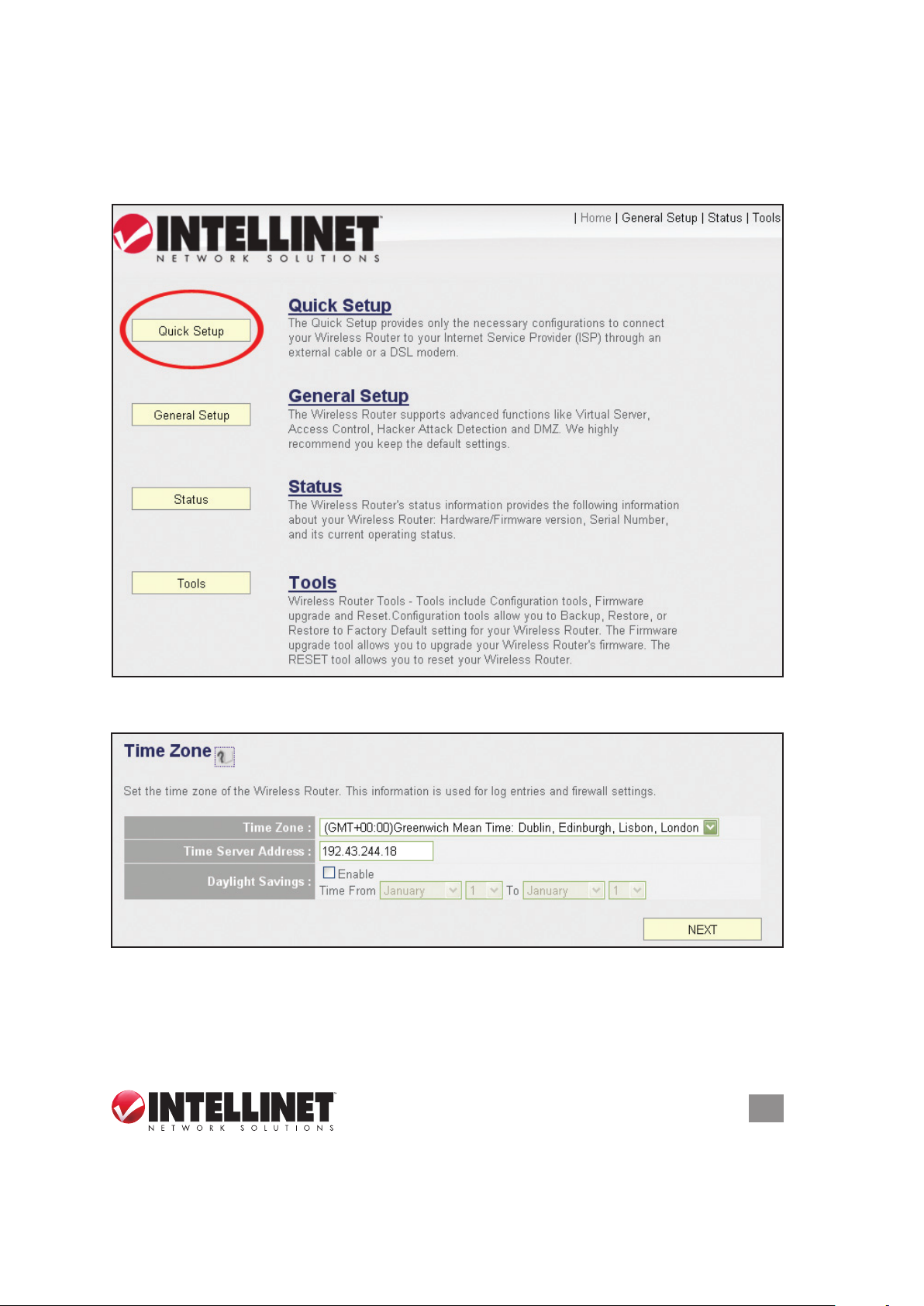
2.3 Quick Setup
The Quick Setup procedure lets you congure all the settings required for quick
Internet access.
.
The initial Quick Setup screen presents time settings.
Set Time Zone — Use the drop-down menu to select your time zone.
Time Server Address — Enter the IP address/hostname of the time server. This
isn’t normally required, but if the default time server (NTP) should go ofine, you
can obtain a new NTP server from the list at http://www.ntp.org.
SYSTEM & NETWORK SETUP
13
Page 14

Daylight Saving — If your locale uses Daylight Saving, activate “Enable Function”
and select the duration using the drop-down menus.
Click “Next” to continue to the next screen of the Quick Setup procedure, where
you select the broadband (Internet connection) type you use.
On all screens, click “Apply” (if such button appears at the bottom) to submit any
option or conguration changes. Click “Back” to return to the previous screen.
Click “Cancel” to undo any changes you’ve made on that screen. Click “Next” or
“OK” to proceed to the next screen.
There are six types of Internet connections available, as explained below: Cable
Modem, Fixed IP xDSL, PPPoE xDSL, PPTP xDSL, L2TP xDSL and Telstra
BigPond. Cable Modem and PPPoE xDSL are the most common, but if you’re not
sure which type of service you have, simply contact your Internet service provider
(ISP) to nd out. You won’t be able to connect to the Internet if you choose the
wrong type during the router setup. NOTE: DSL Internet service providers
normally operate using the PPPoE protocol; thus, PPPoE xDSL should be the
broadband type. However, in recent years more DSL ISPs provide customers with
DSL modems that handle the PPPoE portion of Internet access automatically. In
such cases, you need to select Cable Modem as your broadband type even if you
have a DSL service.
2.3.1 Setup Procedure for Cable Modem (Dynamic IP)
Host Name — Input the host name of your computer. This is optional, and is only
required if your service provider asks you to do so.
14
SYSTEM & NETWORK SETUP
Page 15

MAC address — Enter the MAC address of your computer here if your service
provider only permits a computer with a certain MAC address to access the
Internet. If you’re using a computer used to connect to the Internet via cable
modem, you can simply click “Clone Mac address” to ll in the MAC address
eld with the MAC address of your computer.
2.3.2 Setup Procedure for Fixed IP xDSL (Static IP)
IP address — Enter the IP address assigned by your ISP.
Subnet Mask — Enter the subnet mask assigned by your ISP.
DNS address — Enter the IP address of the DNS server provided by your ISP.
Service Provider Gateway Address — Enter the gateway IP address provided by
your ISP.
NOTE: You can choose this Internet connection method if your service provider
assigns a xed IP address (also know as a static address) to you, and doesn’t use
DHCP or PPPoE protocol. Contact your service provider for further information.
SYSTEM & NETWORK SETUP
15
Page 16
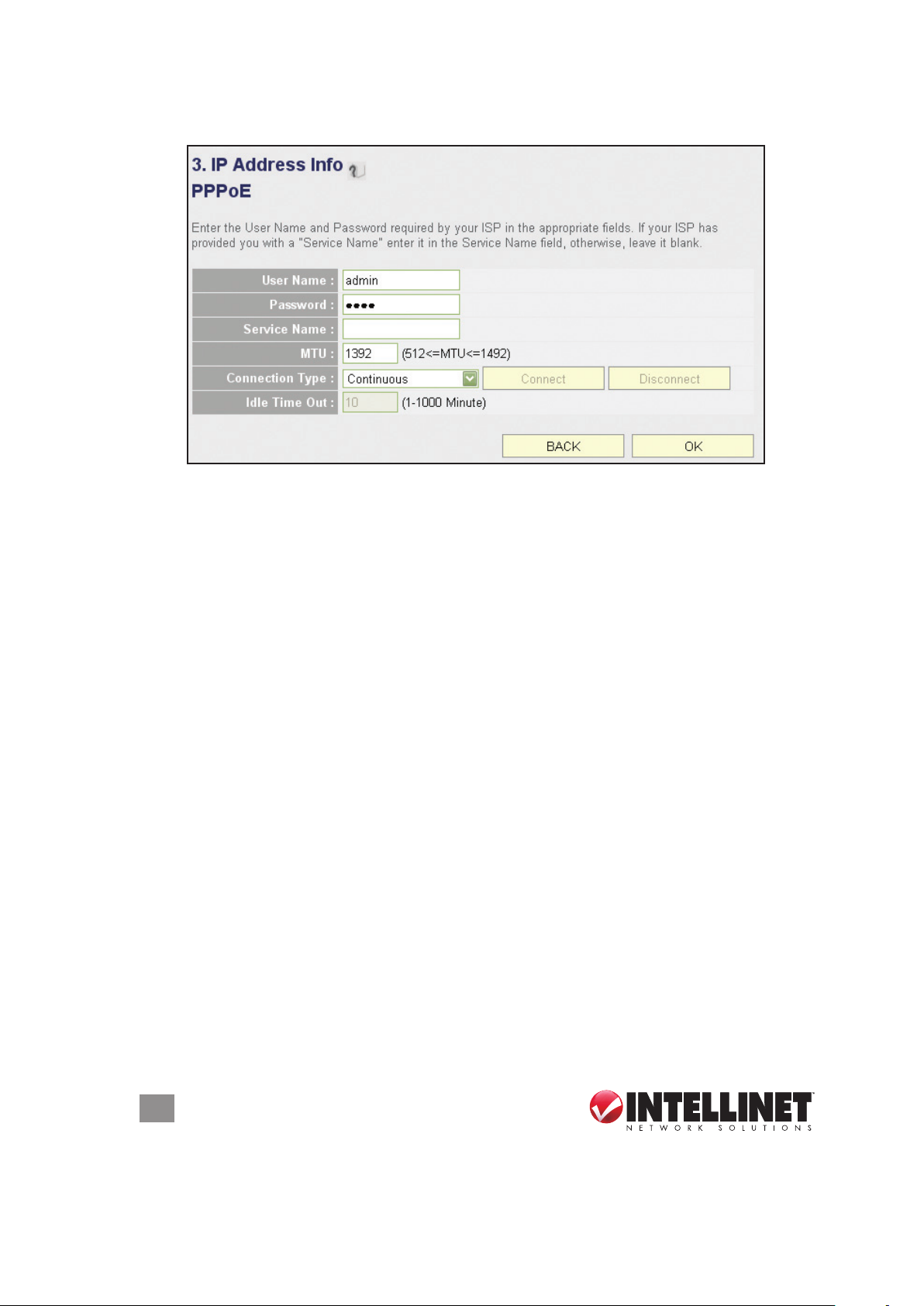
2.3.3 Setup Procedure for PPPoE xDSL
User Name — Enter the username assigned by your ISP.
Password — Enter the password assigned by your ISP.
Service Name — Provide a name for this Internet service. (optional)
MTU — Enter the MTU value of your network connection. NOTE: Use the default
value unless your ISP species otherwise.
Connection Type — Select one of the three connection types in the drop-down
menu:
• “Continuous” keeps the Internet connection alive and does not disconnect.
This is the preferred choice for always-on / at-rate Internet services.
• “Connect on Demand” only connects to the Internet when there’s a connect
attempt. This is the preferred choice for all users who have paid-per-minute
or per-transferred-data Internet service.
• “Manual” only connects to the Internet when “Connect” is selected, and
disconnects when “Disconnect” is selected.
Idle Time Out — Specify the time to shut down the Internet connection after no
Internet activity is detected. This option is only available when the connection
type is Connect on Demand.
2.3.4 Setup Procedure for PPTP xDSL
PPTP xDSL requires two groups of settings: the WAN interface settings (to set up
IP address) and PPTP settings (PPTP username and password).
In the WAN Interface Settings panel, select how you obtain an IP address from
your service provider: “Obtain an IP address automatically” or “Use the following
IP address” (i.e., a static IP address). The WAN interface settings must be
16
SYSTEM & NETWORK SETUP
Page 17

correctly entered; otherwise, the Internet connection will fail even if the PPTP
settings are correct. Contact your ISP if you don’t know how you should ll in
these elds.
The PPTP Settings panel presents these options:
User Name — Enter the username assigned by your ISP.
Password — Enter the password provided by your ISP.
PPTP Gateway — Enter the IP address of PPTP gateway assigned by your ISP.
Connection ID — Enter the connection ID. (optional)
MTU — Enter the MTU value of your network connection. NOTE: Use the default
value unless your ISP species otherwise.
Connection Type — Select one of the three connection types in the drop-down
menu (see PPPoE above):
Idle Time Out — Specify the time to shut down the Internet connection after no
Internet activity is detected. This option is only available when the connection
type is Connect on Demand.
NOTE: Enable BEZEQ-ISRAEL only if you’re using that network provider.
SYSTEM & NETWORK SETUP
17
Page 18
2.3.5 Setup Procedure for L2TP xDSL
L2TP is another popular connection method for xDSL and other Internet connection
types, and all required setting items are the same as the PPTP connection (see
section 2.3.4 above).
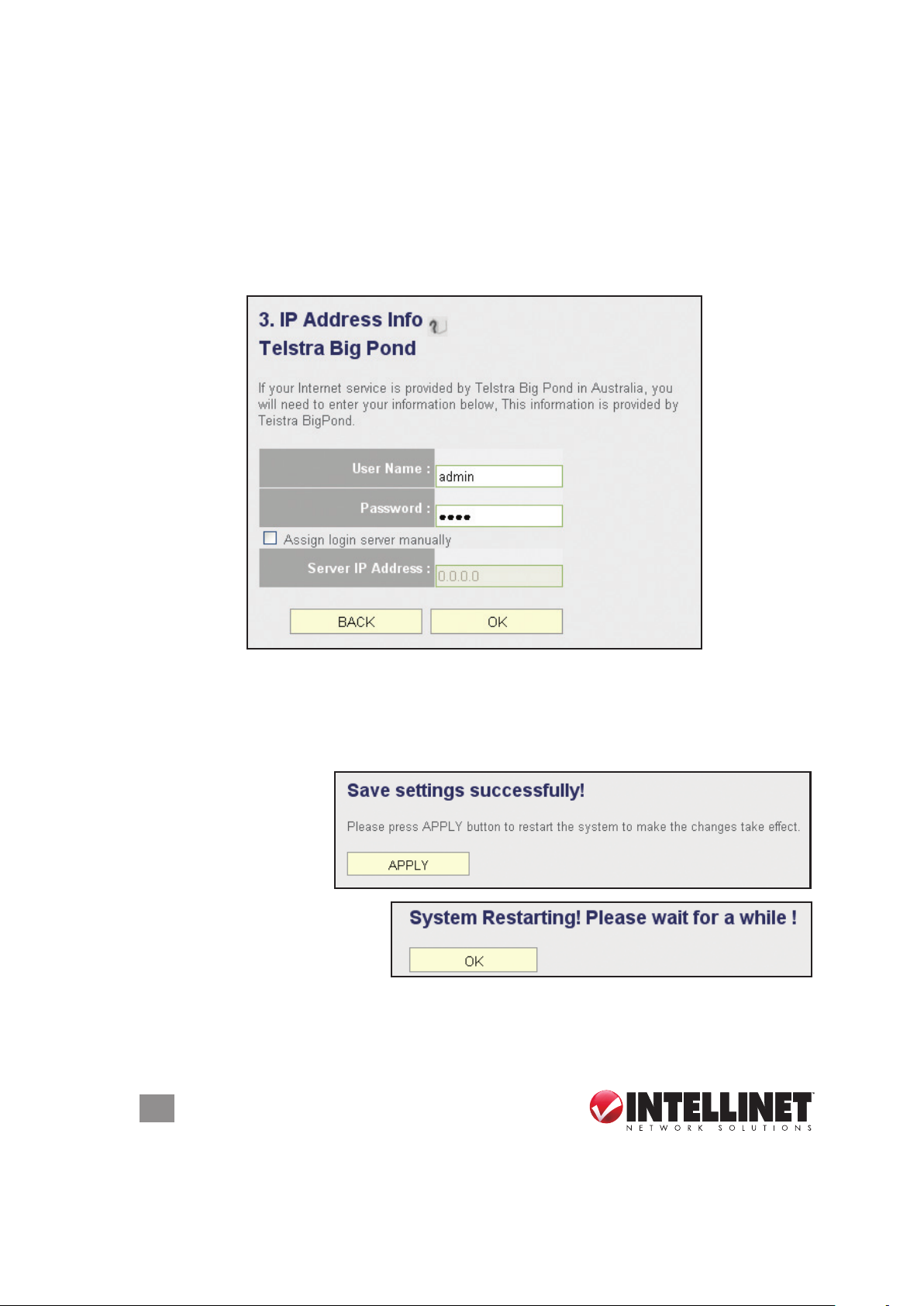
2.3.6 Setup Procedure for Telstra BigPond
This procedure is only for the Telstra BigPond network service in Australia.
User Name — Enter the username assigned by Telstra.
Password — Enter the password assigned by Telstra.
Assign login server manually — Select to choose the login server by yourself.
Server IP Address — Enter the IP address of the login server.
When all settings are
nished (and after you
click “OK”), you’ll see
this message (right) on
your Web browser.
Click “Apply” to restart the
router. You’ll see a second
restart message (right).
Wait for about 30 seconds, then click “OK.” You’ll be forwarded to the router’s Web
management interface. The router is now running with the new settings, and, if all
information entered is correct, you can now access the Internet.
18
SYSTEM & NETWORK SETUP
Page 19
NOTE TO DSL USERS
While PPPoE is the most common way to connect to DSL Internet service, it still
may be necessary to enable “Cable Modem” in the Broadband settings. Below are
examples for using Cable Modem instead of xDSL PPPoE, even if your Internet
service is a DSL service.
• Your ISP has given you a so-called “modem-router” instead of a simple modem.
• Your ISP has not given you a username and password for PPPoE login (implying
that it is not required).
• When your computer is connected directly to the modem, the computer obtains
an IP address which is in the private IP network range (192.168.xxx.yyy, 10.xxx.yyy,
172.16.xxx.yyy).
• You can connect to the Internet with your computer connected directly to the
modem without using a dialer program asking for a username and password.
• If attempts to utilize PPPoE xDSL fail repeatedly, you should activate “Cable
Modem” as a troubleshooting step.
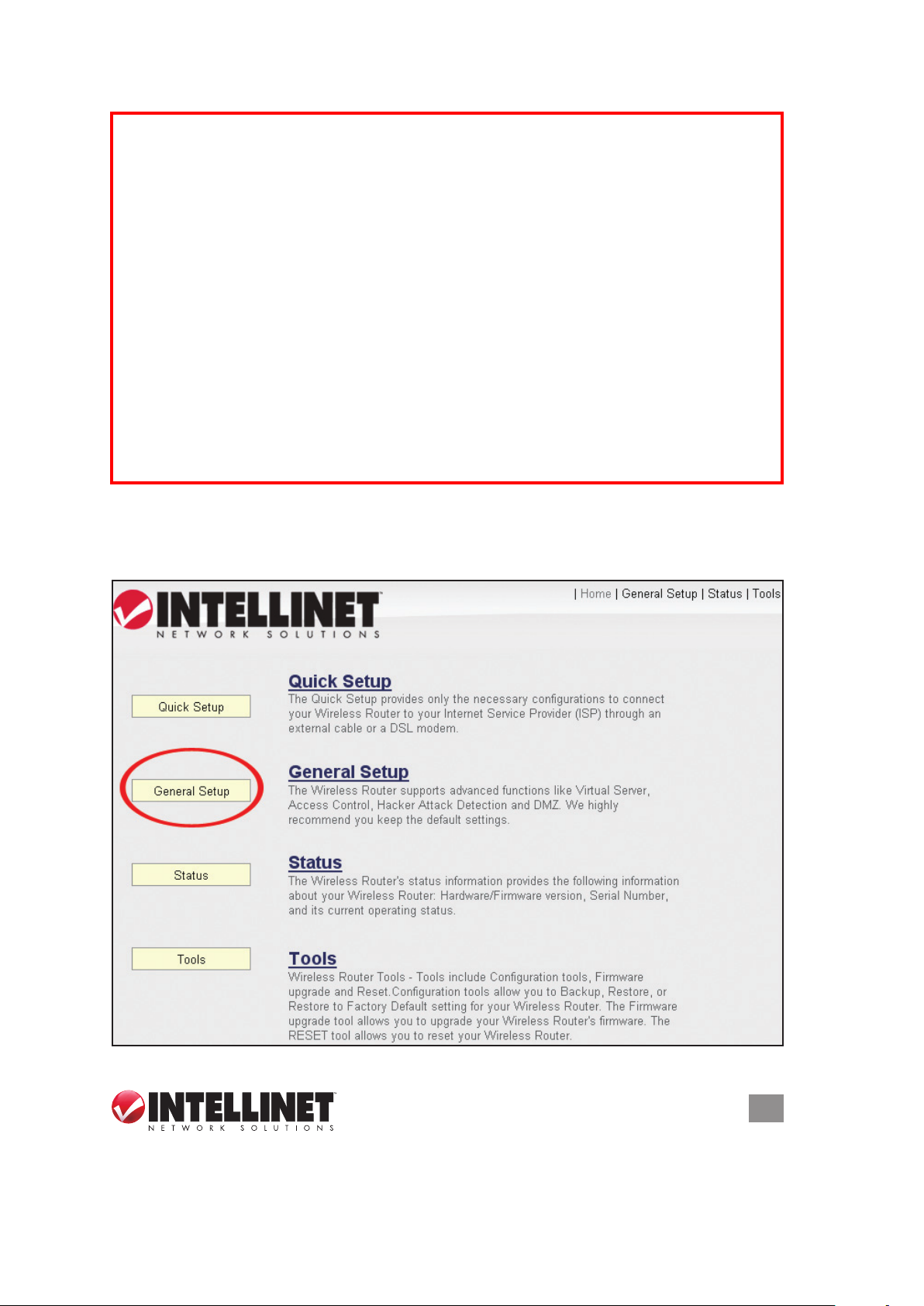
2.4 General Setup
This section explains how to change the time zone, password and remote
SYSTEM & NETWORK SETUP
19
Page 20
management settings. Start your Web browser and log on to the router’s Web
management interface by opening http://192.168.2.1, then click the “General Setup”
button on the left.
2.4.1 Time Zone and Time Auto-Synchronization
Click the “System” menu on the left of the Web management interface, then click
“Time Zone.” You’ll be prompted to select a time zone from the “Set time zone”
drop-down menu and enter the IP address or host name of the time server. If you
want to enable the Daylight Saving setting, check the “Enable Function” box and
set the duration of Daylight Saving.
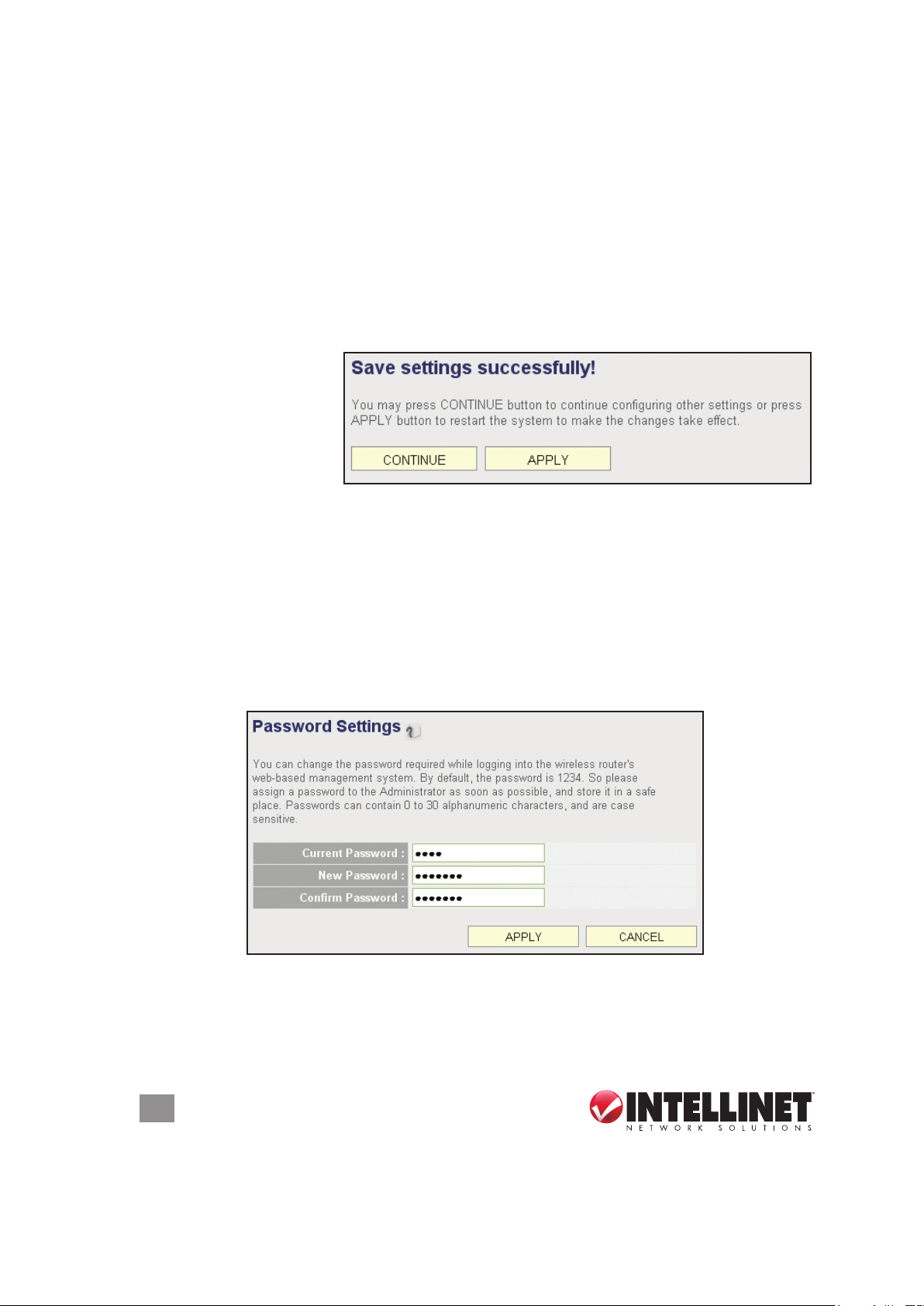
Click “Apply” and this
message will display.
Click “Continue” to save
the settings and make
additional changes;
click “Apply” to save the
settings and restart the router so the settings will take effect after it reboots.
2.4.2 Changing the Management Password
The default password of this router is 1234, and it’s displayed on the login prompt
when accessed from the Web browser. There’s a security risk if you don’t change
the default password, since everyone can see it. This is very important when you
have the wireless function enabled. To change the password, click the “System”
menu on the left of the Web management interface, then click “Password
Settings.”
Current Password — Enter the current password (for example, 1234).
New Password — Enter the new password.
Conrm Password — Enter the new password again.
20
SYSTEM & NETWORK SETUP
Page 21
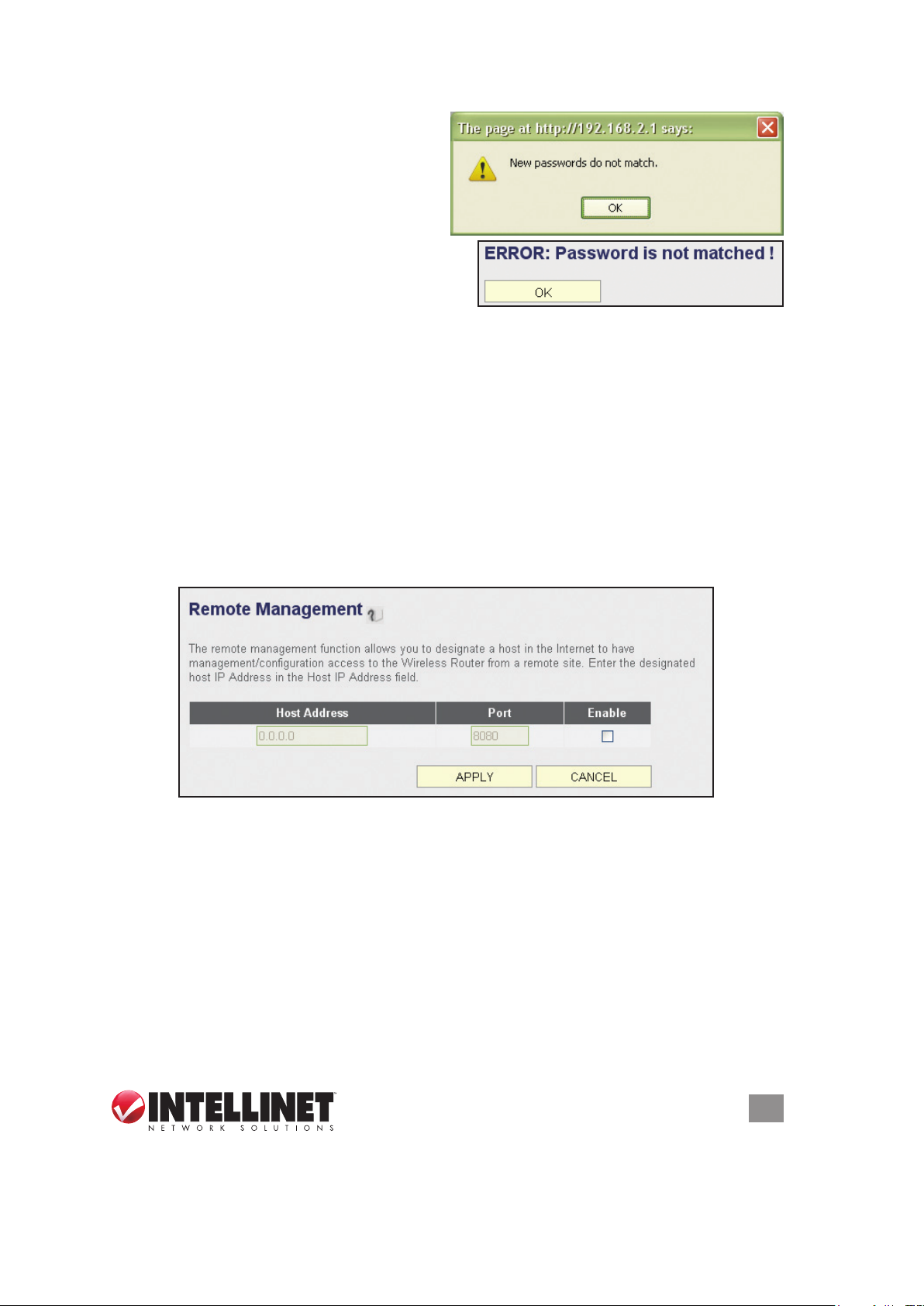
If the passwords entered in the “New
Password” and “Conrmed Password”
elds aren’t the same, you’ll see the
message at right. Re-enter the new
password.
If you see the error message at right, it
means the content in the “Current Password”
eld is wrong. Click “OK” to go back to the
previous menu, and try entering the current password again. If the current and
new passwords are correctly entered, click “Apply” and you’ll be prompted to log in
again. Enter the new password and enter “admin” for the username.
2.4.3 Remote Management
This router by default does not allow management access from the Internet to
prevent possible security risks (especially when you have dened a weak password
or didn’t change the default password). However, you can still manage this router
from a specic IP address by enabling the Remote Management function.
Click the “System” menu on the left of Web management interface, then click
“Remote Management.” The screen below will display on your Web browser.
Host Address — Enter the IP address of the remote host you want to initiate
management access..
Port — You can dene the port number through which this router should expect an
incoming request. If you’re providing a Web service (default port number is 80),
you should try to use another port number. You can use the default port setting
(8080) or something like 32245 or 1429 (any integer between 1 and 65534)..
Enabled — Select the eld to start the conguration.
Click “Apply,” then either click “Continue” to save the settings and make additional
changes or click “Apply” again to save the settings and restart the router so the
settings will take effect after it reboots.
SYSTEM & NETWORK SETUP
21
Page 22

NOTE: To manage this router from another computer on the Internet, you need to
input the IP address and port number of this router. If your Internet service provider
assigns you a static IP address, it will not be a problem; but if the IP address your
service provider assigns will vary every time you establish an Internet connection,
this will be a problem. Either ask your ISP to give you a static IP address, or use
a dynamic DNS service like DDNS. (See section 2.5.8 DDNS Client for details.)
NOTE: The default por t number the Web browser will use is 80. If the “Port” setting
on this page is not 80, you need to assign the port number in the address bar of
the Web browser manually. For example, if the IP address of this router is 1.2.3.4,
and the port number you set is 8888, you need to enter http://1.2.3.4:8888 in the
address bar of the Web browser.
2.5 Setting Up an Internet Connection (WAN Setup)
The Internet connection setup can be done by using the Quick Setup menu
described in section 2-3. However, you can set the WAN connections up by using
the WAN conguration menu. You can also program advanced functions like DDNS
(Dynamic DNS) here.
Click the “WAN” menu on the left of the Web management interface, then select
an Internet connection method based on the type of connection you’re using. You
can either click the connection method in the left-side menu or select it from the
main panel in the center (which requires that you then click “More Conguration”
to continue).
22
SYSTEM & NETWORK SETUP
Page 23
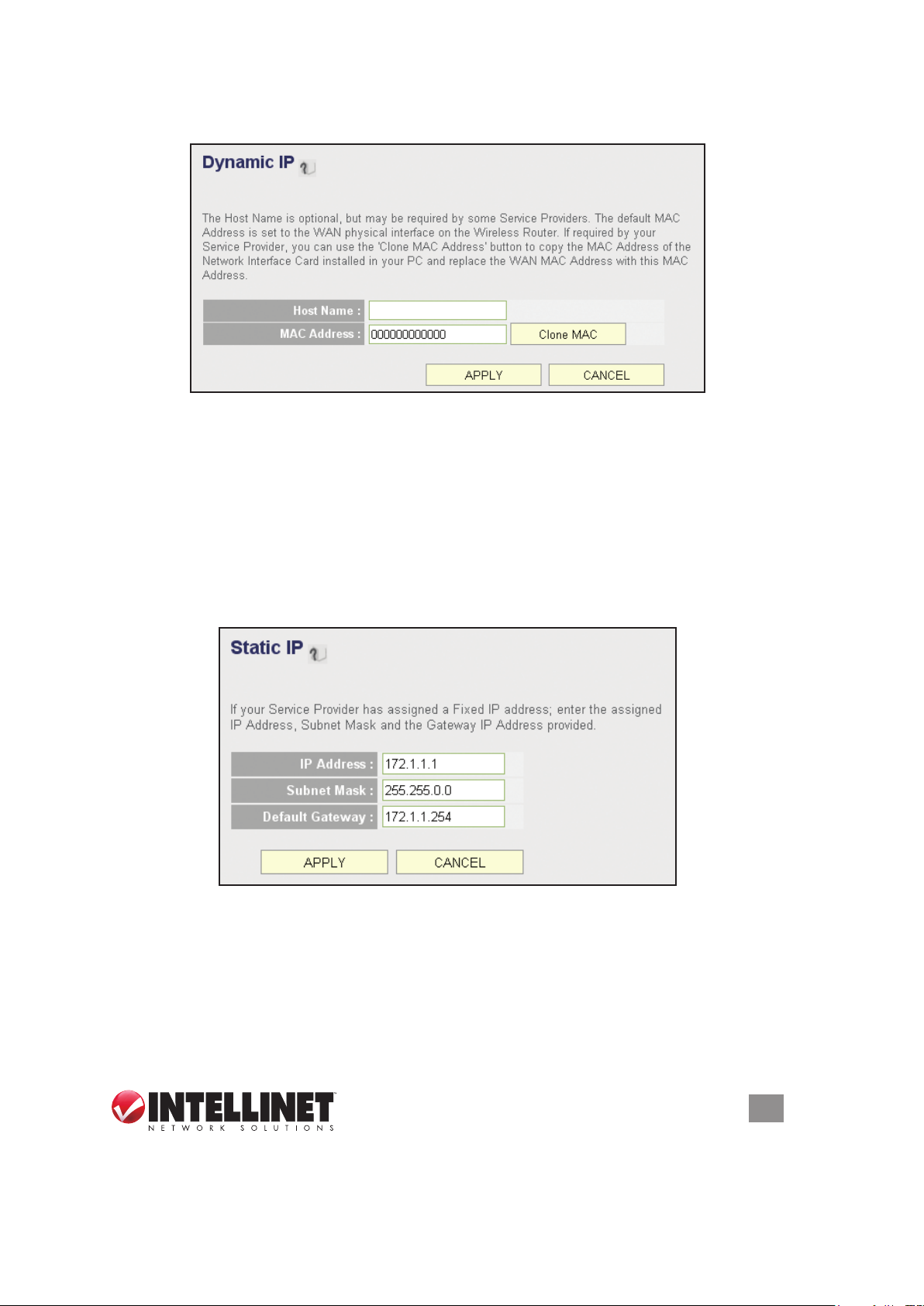
2.5.1 Setup Procedure for Dynamic IP
Host Name — Enter the host name of your computer. (This is optional and is only
required if your service provider asks you to do so.)
MAC Address — Enter the MAC address of your computer if your service provider
only permits a computer with a certain MAC address to access the Internet. If
you’re using the computer to connect to the Internet via cable modem, you can
simply click “Clone MAC” to ll the “MAC Address” eld with the MAC address
of your computer.
2.5.2 Setup Procedure for Static IP
IP Address — Enter the IP address assigned by your service provider.
Subnet Mask — Enter the subnet mask assigned by your service provider.
Default Gateway — Enter the IP address of the gateway server assigned by your
service provider.
SYSTEM & NETWORK SETUP
23
Page 24

2.5.3 Setup Procedure for PPPoE
User Name — Enter the username assigned by your Internet service provider.
Password — Enter the password assigned by your Internet service provider.
Service Name — Enter a name for this Internet service. (optional)
MTU — Enter the MTU value of your network connection. NOTE: Use the default
value unless your ISP species otherwise.
Connection Type — Select one of the three connection types in the drop-down menu:
• “Continuous” keeps the Internet connection alive and does not disconnect.
This is the preferred choice for always-on / at-rate Internet services.
• “Connect on Demand” only connects to the Internet when there’s a connect
attempt. This is the preferred choice for all users who have paid-per-minute
or per-transferred-data Internet service.
• “Manual” only connects to the Internet when “Connect” is selected, and
disconnects when “Disconnect” is selected.
Idle Time Out — Specify the time to shut down the Internet connection after no
Internet activity is detected. This option is only available when the connection
type is Connect on Demand.
2.5.4 Setup Procedure for PPTP
PPTP requires two groups of settings: the WAN interface settings (to set up the IP
address) and PPTP settings (PPTP username and password).
In the WAN Interface Settings panel, select how you obtain an IP address from
your service provider: “Obtain an IP address automatically” or “Use the following
IP address” (i.e., a static IP address). The WAN interface settings must be correctly
24
SYSTEM & NETWORK SETUP
Page 25

entered; otherwise, the Internet connection will fail even if the PPTP settings are
correct. Contact your ISP if you don’t know how you should ll in these elds.
The PPTP Settings panel presents these options:
User Name — Enter the username assigned by your ISP.
Password — Enter the password provided by your ISP.
PPTP Gateway — Enter the IP address of PPTP gateway assigned by your ISP.
Connection ID — Enter the connection ID. (optional)
MTU — Enter the MTU value of your network connection. NOTE: Use the default
value unless your ISP species otherwise.
Connection Type — Select one of the three connection types in the drop-down
menu (see PPPoE above):
Idle Time Out — Specify the time to shut down the Internet connection after no
Internet activity is detected. This option is only available when the connection
type is Connect on Demand.
NOTE: Enable BEZEQ-ISRAEL only if you’re using that network provider.
2.5.5 Setup Procedure for L2TP
L2TP settings are the same as the PPTP connection (see section 2.5.4 above).
SYSTEM & NETWORK SETUP
25
Page 26

2.5.6 Setup Procedure for Telstra BigPond
This procedure is only for the Telstra BigPond network service in Australia.
User Name — Enter the username assigned by Telstra.
Password — Enter the password assigned by Telstra.
Assign login server manually — Select to choose the login server by yourself.
Server IP Address — Enter the IP address of the login server.
2.5.7 Setup Procedure for DNS
If you select Dynamic IP or PPPoE as the Internet connection method, the ISP
typically assigns the DNS server information to the router. However, if you have a
26
SYSTEM & NETWORK SETUP
Page 27

preferred DNS server or use a static IP address, or if your service provider didn’t
assign the IP address of the DNS server for any reason, you can input the IP
address of the DNS server here.
Primary DNS — Enter the IP address of the DNS server provided by your ISP.
Secondary DNS — Enter the IP address of the secondary DNS server provided
by your ISP. (optional)
NOTE: Only an IP address can be entered here; do not use the hostname of the
DNS server! (Only numeric characters and periods are accepted; for example,
10.20.30.40 would be acceptable, but dns.serviceprovider.com would not be.)
2.5.8 Setup Procedure for DDNS
DDNS (Dynamic DNS) is an IP-to-hostname mapping service for Internet users who
don’t have a static (xed) IP address. It will be a problem when a user wants to
provide services to other users on the Internet because their IP addresses will vary
every time they connect, and they will not be able to know the IP address they’re
using at any certain time.
This router supports the DDNS service of several service providers; for example:
DynDNS (http://www.dyndns.org) and TZO (http://www.tzo.com). You can go to
one of these DDNS service provider’s Web sites and get a free DDNS account by
following their instructions.
Dynamic DNS — Select “Enable” or “Disable.”
Provider — Select your DDNS provider from the drop-down menu.
Domain Name — Enter the domain name you’ve obtained from the DDNS service
provider.
Account — Enter the user account of your DDNS registration.
Password/Key — Enter the DDNS service password or key.
SYSTEM & NETWORK SETUP
27
Page 28

2.5.9 Setup Procedure for WISP (Wireless ISP)
Wireless Internet service providers (WISPs) are Internet service providers with
networks built around wireless networking. Typically, WISPs are found in rural areas
with small populations, where cable and digital subscriber lines are not available.
The Intellinet Wireless 300N Dual-Band Router can receive a 2.4 or 5.0 GHz WiFibased WISP signal and can share it among the clients, which are connected locally,
pretty much the same way it does with cable or DSL connections. This function can
also be used if a wireless signal (from a wireless router, for example) is already
present in the location, but you want to create another network behind the Intellinet
Dual-Band Router. NOTE: If you do not understand any of this or if you don’t believe
you need to take advantage of this feature, you can safely skip to the next chapter.
Disable — By default, the WISP mode is deactivated until you enable it.
Enable — Click to enable the function. Select the wireless band and click “Site
Survey” to search for wireless signals that offer Internet service. In this mode, the
Intellinet Dual-Band Router uses its wireless function to pick up the wireless ISP
signal and, at the same time, allow wireless clients to connect and go online.
Enable (Station Mode Only) — This is similar to the “Enable” mode, with the
difference being that in “Station Mode Only” no wireless client can connect to the
Intellinet Dual-Band Router. The wireless function is used exclusively for the
wireless broadband (WISP) signal. Only stations that are connected to one of
the LAN ports can utilize the WISP connection.
SSID — Enter the name of the wireless network that you want to connect to, or
click “Site Survey” and let the router search all available networks for you and
enter the SSID automatically.
Channel Number — This is the radio frequency used to transmit and receive the
wireless signal. Enter it manually or click “Site Survey” and let the router search
all available networks for you and enter the channel number automatically.
28
SYSTEM & NETWORK SETUP
Page 29

Wireless Band — Check whether the WISP signal is found in either the 2.4 GHz or
5 GHz frequency range.
Site Survey — Click to display a wireless site survey table (not shown). It will list all
available access points nearby. Select the access point designated by your
wireless ISP in the table and click “Done.”
Security Settings — If the WISP signal encrypted, you need to enter the correct
information here. Refer to section 2.7.3 Wireless Security for details.
2.6 LAN Conguration
This section explains the IP address settings of the local network. Normally, there
is no need to make any changes here: The default values work ne for most
applications, and you could just go directly to section 2.7 WLAN Conguration.
There are two ways to assign IP addresses to computers: static IP address (set the
IP address for every computer manually) and dynamic IP address (the IP address
of computers will be assigned by the router automatically). It’s recommended for
most of the computers to use a dynamic IP address, as it will save a lot of time
when setting IP addresses for every computer, especially when there are a lot
of computers in your network. For servers and network devices that will provide
services to other computers and users that come from the Internet, a static IP
address should be used so other computers can locate the server.
SUGGESTIONS FOR AN IP ADDRESS NUMBERING PLAN
To dene an IP address plan for your network, here are some suggestions.
• A valid IP address has fo ur eld s: a.b.c .d. For m o st hom e and comp any users, it ’s
suggested to use 192.168.c.d, where c is an integer between 0 and 254, and d is
an integer between 1 and 254. This router is able to work with up to 253 clients, so
you can set the “d” eld of the router’s IP address as 1 or 254 (or any number
between 1 and 254), and pick a number between 0 and 254 for eld “c.”
• In most cases, you should use 255.255.255.0 as the subnet mask, which meets
the router’s capability of working with up to 253 clients.)
• For all servers and network devices that will provide services to other people (like
Internet service, print service and le service), use a static IP address. Give each
of them a unique number between 1 and 253, and maintain a list, so everyone
can locate those servers easily.
• For computers not dedicated to providing specic service to others, use a
dynamic IP address.
NOTE: Recommended setup values are provided in the sections that follow.
Click the “LAN” menu on the left of the Web management interface to see three
setup groups (explained below): LAN IP, DHCP Server, Static DHCP Leases Table.
SYSTEM & NETWORK SETUP
29
Page 30

2.6.1 LAN IP
IP address — Enter the IP address of this router.
Subnet Mask — Enter the subnet mask for this network.
802.1d Spanning Tree — Select “Enable” or “Disable” from the drop-down menu.
The Spanning Tree Protocol (STP) is a network protocol that ensures a loop-
free topology for any bridged Ethernet local area network. The basic function of
STP is to prevent bridge loops and ensuing broadcast radiation. Spanning tree
also allows a network design to include spare (redundant) links to provide
automatic backup paths if an active link fails, without the danger of bridge loops
or the need for manual enabling/disabling of these backup links. In larger
networks, this option should be enabled.
DHCP Server — Select “Enable” or “Disable” from the drop-down menu.
RECOMMENDED VALUES
IP Address: 192.168.2.1
Subnet Mask: 255.255.255.0
802.1d Spanning Tree: Disabled
DHCP Server: Enabled
2.6.2 DHCP Server
These settings are only available when “DHCP Server” in the LAN IP section is
enabled, but will also affect wireless clients.
Lease Time — Choose a lease time (the duration that every computer can keep a
specic IP address) for every IP address assigned by this router.
Start IP — Enter the start IP address of the IP range.
End IP — Enter the end IP address of the IP range.
Domain Name— Enter a domain name for your network. (optional)
NOTE: The number of the last eld (the “d” eld) of “End IP” must be greater than
30
SYSTEM & NETWORK SETUP
Page 31

“Start IP” and can’t be the same as the router’s IP address. Also, the rst three
elds of the IP address of “Start IP,” “End IP” and “IP Address” in the LAN IP
section (the “a,” “b” and “c” elds) should be the same.
Lease Time: Two Weeks (or “Forever” if
you have fewer than 20 computers)
RECOMMENDED VALUES
End IP: 192.168.2.200
Domain Name: (leave it blank)
Start IP: 192.168.2.100
2.6.3 Static DHCP Leases Table
This function allows you to assign a static IP address to a specic computer forever,
so you don’t need to set the IP address for a computer to enjoy the benet of using
a DHCP server. A maximum of 16 static IP addresses can be assigned here.
NOTE: If you set “Lease Time” to “Forever” in the DHCP Server section, you can
also assign an IP address to a specic computer permanently; however, you won’t
be able to assign a certain IP address to a specic computer, since IP addresses
will be assigned in random order this way.
Enable Static DHCP Leases — Select to enable; de-select to disable.
MAC Address — Enter the MAC address of the computer or network device (a
total of 12 characters, with numerals from 0 to 9 and characters from a to f,
such as 001122aabbcc).
IP Address — Enter the IP address you want to assign to this computer or device.
Click “Add” to include a MAC address and IP address pair into the Static DHCP
Leases table (below). Click “Clear” to remove characters entered in a text eld.
To delete a specic item, check the “Select” box of a MAC address and IP address
mapping, then click “Delete Selected.” To delete all mappings, click “Delete All.” To
deselect all mappings, click “Reset.”
SYSTEM & NETWORK SETUP
31
Page 32

2.7 Wireless LAN Conguration
If your computer, PDA, game console or other network device is equipped with a
wireless network interface, you can use the wireless function of this router to connect
to the Internet and share resources with other computers on your network. This
router contains two independently operating wireless units: one for the standard 2.4
GHz range; one for the 5 GHz range. Thus, you have two wireless conguration
options. Since the options of the 5 GHz setup are identical to those of the 2.4 GHz
setup, only the 2.4 GHz options are detailed here.
Furthermore, it’s strongly recommended that you use the built-in security functions
to protect your network from intruders. WPA/2 should be used whenever possible.
Click the “Wireless” menu on the left of the Web management interface to open
the wireless settings page. Remember to click “Apply” to save your settings.
2.7.1 Basic Wireless Settings
Mode — Select one of six options for the operational mode of the wireless radio:
• “Access Point” is the most common mode, in which the wireless router acts as
a bridge between 802.11b/g/n wireless devices and a wired Ethernet network,
and exchanges data between them. This is the most common way to use the
450N wireless router.
• “Station (Infrastructure)” allows you to connect the router to an Ethernet device
such as a TV and gaming console, effectively acting as the wireless network
adapter of the device to connect a wired Ethernet device to a wireless network.
Once Station mode is activated, the channel number selection disappears.
Click “Site Survey” and select the wireless network you want the router to
connect to. Click “Apply” to save the settings. NOTE: In Station mode, no
wireless client will be able to wirelessly connect to the device. Activate the
Universal Repeater mode (see below) to allow wireless clients to connect at the
same time.
• “AP Bridge (Point to Point)” lets you connect two wired Ethernet networks; for
example, if Network 1 and Network 2 are on opposite sides of a road, you can
32
SYSTEM & NETWORK SETUP
Page 33

use two of these wireless routers to connect the two networks. Both routers
need to be set to AP Bridge (Point to Point) mode: The screen will then display
a MAC Address 1 eld in which you enter the MAC address of the opposite
router, which you can obtain by clicking “Status” (top right) and “Device Status.”
You also need to set both routers to the same wireless channel in the Channel
Number eld. Finally, click “Security Settings” and set both devices up the
same way. NOTE: In Bridge mode, no wireless client will be able to wirelessly
connect to the device.
• “AP Bridge (Point to Multi-Point)” mode is very similar to the above-mentioned
Point-to-Point mode, except here you can have the router connecting up to four
different devices. The setup is the same, but you need to provide MAC
addresses for all other bridges you want to connect to (MAC Address 1 – 4).
NOTE: In Bridge mode, no wireless client will be able to wirelessly connect to
the device.
• “AP Bridge (WDS)” mode is quite similar to the Point to Multi-Point described
above in that it allows you to connect your wireless router to up to four other
wireless routers. However, whereas in bridge mode you can only use this
function to connect wired Ethernet networks (since in Bridge mode no wireless
client can connect to the wireless router), in WDS mode this limitation no longer
exists. WDS (Wireless Distribution System) is a system that enables the
wireless interconnection of access points in an IEEE 802.11 network. It allows
a wireless network to be expanded using multiple access points without the
traditional requirement for a wired backbone to link them. The downside is
two-fold: First, the performance of the wireless network suffers in WDS mode
quite signicantly; second, the setup is more complicated and interoperability
with different access points and routers cannot be guaranteed. The setup is
very much the same as the Point to Multi-Point Bridge mode; the only extra
information that needs to be provided is the SSID of the wireless network.
• “Universal Repeater” combines the rst two modes, Access Point and Station,
SYSTEM & NETWORK SETUP
33
Page 34

and increases the wireless coverage area by repeating an existing wireless
signal. Concerning the setup, you need click “Site Survey” and select the SSID
of the parent access point. (The SSID is the name of the wireless network the
router will be broadcasting. The Root AP SSID is the name of the network the
router is repeating.
Band — Select one of the options from the drop-down menu:
• “2.4 GHz (B)” only allows an 802.11b wireless network client to connect to this
router (maximum transfer rate of 11 Mbps).
• “2.4 GHz (N)” only allows an 802.11n wireless network client to connect to this
router (maximum transfer rate of 300 Mbps).
• “2.4 GHz (B+G)” only allows a802.11b and 802.11g wireless network clients to
connect to this router (maximum transfer rate of 11 Mbps for 802.11b clients;
maximum 54 Mbps for 802.11g clients).
• “2.4 GHz (G)” only allows an 802.11g wireless network client to connect to
this router (maximum transfer rate of 54 Mbps).
• “2.4 GHz (B+G+N)” allows 802.11b, 802.11g and 802.11n wireless network
clients to connect to this router (maximum transfer rate of 11 Mbps for 802.11b
clients; 54 Mbps for 802.11g clients; 300 Mbps for 802.11n clients.
NOTE: For optimal compatibility with wireless clients, select “2.4 GHz (B+G+N).”
ESSID — Enter the name for your wireless network. You may choose to use the
default value, but you can adjust the value to make identication in areas with
different wireless networks easier; e.g., to differentiate your wireless network from
that of your neighbors.
Channel Number — Select a channel: 1-13 for Europe; 1-11 for the U.S.
Associated Clients — Click “Show Active Clients” to see the status of all active
wireless stations connected to the access point.
You can try to change the channel number if you think the data transfer rate is too
slow. There could be interference from other wireless networks in the area using
the same channel, and the cross-talk between the two networks can reduce the
wireless data transfer rate. Ideally, you want to set your channel to a value which
leaves at least two channels spaced between the two networks.
Example: If your neighbor’s wireless network runs on channel 3, set your channel
to 6 or higher. Even a handheld phone in your household can cause interference
with the wireless signal, and changing the channel by two or three numbers often
resolves the problem.
2.7.2 Advanced Wireless Settings
Normally, there is no need to make any changes here. Unless you know that your
network requires special settings, you can proceed to 2.7.3 Wireless Security.
Fragment Threshold — Set the fragment threshold of the wireless radio. NOTE: If
34
SYSTEM & NETWORK SETUP
Page 35

you aren’t sure what this should be set to, leave it as the default value of 2346.
RTS Threshold — Set the RTS (return to sender) threshold of the wireless radio.
NOTE: If unsure what this should be set to, leave it as the default value: 2347.
Beacon Interval — Set the beacon interval of the wireless radio. NOTE: If you
aren’t sure what this should be set to, leave it as the default value of 100.
DTIM Period — Set the DTIM (delivery trafc indication message) period of the
wireless radio. NOTE: If you aren’t sure what this should be set to, leave it as the
default value of 3.
Data Rate — Set the wireless data transfer rate to a specic value. Since most
wireless devices will negotiate with each other and pick a proper data transfer
rate automatically, it’s not necessary to change this value unless you know what
will happen after modication.
N Data Rate — Same as above, but only for 802.11n clients.
Channel Width — Set the channel width of the wireless radio. NOTE: If you aren’t
sure what this should be set to, leave it as the default setting (“Auto 20/40 MHz”).
Preamble Type — Set the preamble type. NOTE: If you aren’t sure what this should
be set to, leave it as the default setting (“Short Preamble”).
Broadcast ESSID — Decide if the wireless router will broadcast its own ESSID. You
can hide the ESSID of your wireless router (select “Disable”) so only people who
know the ESSID of your wireless router can connect to it.
CTS Protect — Enabling this function reduces the chance of radio signal collisions
SYSTEM & NETWORK SETUP
35
Page 36

between 802.11b and 802.11g/n wireless access points. NOTE: The recommended
setting is either “Auto” or “Always.”
Tx Power — Set the output power of the wireless radio. Unless you’re using this
router in a really big space, you may not need to set this to “100%.”
WMM — Set WMM (Wi-Fi Multimedia, which enhances the data transfer
performance of multimedia content sent over a wireless network) to “Enable” or
leave it as the default (“Disable”).
2.7.3 Wireless Security
Unlike the Advanced Wireless Settings options, these settings are critical: If not done
properly, freeloaders can use your Internet connection without your knowledge
and hackers could gain access to your network and steal vital data such as credit
card information or bank records. Click the “Security Settings” menu on the left of
the Web management interface to select one of the four encryption methods from
the drop-down menu (see image below).
2.7.3.1 Disable Wireless Security
When you select this mode, data encryption is disabled and every wireless device
in proximity will be able to connect your wireless router if no other security measure
is enabled (like using MAC address access control disabling ESSID broadcast).
NOTE: Only use this option when you want to allow everyone to use your wireless
router and you don’t care if someone reads the data you transfer over the network
without your consent.
2.7.3.2 Wired Equivalent Privacy (WEP)
WEP encryption is an outdated method to secure your network, as it doesn’t meet
the security standards of modern data encryption. Thus, it’s not recommended that
you use WEP,unless you use WLAN adapters or WLAN networking devices that
don’t support WPA/WPA2 encryption. If your WLAN card supports WPA/WPA2,
you can proceed to section 2.7.3.3 Wi-Fi Protected Access (WPA).
Key Length — There are two types of WEP key length: 64-bit and 128-bit. Selecting
“128-bit” is safer than “64-bit,” but will reduce some data transfer performance.
Key Format — There are two types of key format: ASCII and hexadecimal, or “hex.”
To improve the security level, don’t use words found in a dictionary or that are too
easily remembered. Wireless clients will remember the WEP key, so you only
need to input the WEP key for a wireless client once. It’s worth using a complicated
WEP key to improve the security level. Once you enter your WEP key and save the
settings, all wireless clients will need to enter that identical character conguration
in order to gain access to your wireless network. NOTE: 128-bit encryption and
ASCII key format are recommended.
36
SYSTEM & NETWORK SETUP
Page 37

When you select a key format, the number of characters in the key will be displayed.
For example, if you select “64-bit” as the key length and “Hex” as the key format,
you’ll see the message to the right of “Key Format” is “Hex (10 characters),” which
means the length of the WEP key is 10 characters.
Default Tx Key — You can set up to four sets of WEP keys, and designate one as
the default here. NOTE: If unsure which one you should use, select “Key 1.”
Encryption Key 1-4 — Enter WEP key characters here. The number of characters
must be the same as the number displayed n the “Key Format” eld. You can
use any alphanumerical characters (0-9, a-z and A-Z) if you select “ASCII” for
the key format. If you select “Hex” as key the format, you can use 0-9, a-f and
A-F. You must enter at least one encryption key here; if you enter multiple WEP
keys, they should not be same.
Enable 802.1x Authentication — IEEE 802.1x is an authentication protocol. Every
user must use a valid account to log in to this router before accessing the wireless
LAN. The authentication is processed by a RADIUS server. This mode
authenticates the user by IEEE 802.1x, but it does not encrypt the data during
communication. If there is a RADIUS server in your environment, enable this
function. Check this box and another sub-menu will appear:
RADIUS Server IP address — Enter the IP address of the RADIUS server.
RADIUS Server Port — Enter the port number of the RADIUS server.
RADIUS Server Password — Enter the password of the RADIUS server.
SYSTEM & NETWORK SETUP
37
Page 38

2.7.3.3 Wi-Fi Protected Access (WPA) Pre-Shared Key
WPA Unicast Cipher Suite — Once you select one of the three ciper options —
“WPA (TKIP),” “WPA2 (AES)” or “WPA2 Mixed” — make sure your wireless
clients support it.
Pre-shared Key Format — Select the type of pre-shared key from the drop-down
menu: “Passphrase” (8 or more alphanumerical characters, up to 63) or “Hex”
(64 characters of 0-9 and a-f).
Pre-shared Key — Enter the WPA passphrase. NOTE: As mentioned earlier, try to
avoid common terms or character combinations.
Some wireless devices (especially those manufactured before 2003) only support
the WEP or WPA (TKIP) cipher. A driver upgrade would be needed for them to be
able to use WPA and WPA2 encryption.
2.7.3.4 WPA RADIUS
If you have a RADIUS server, this router can work with it and provide even safer
wireless authentication.
WPA Unicast Cipher Suite — Once you select one of the three ciper options —
38
SYSTEM & NETWORK SETUP
Page 39

“WPA (TKIP),” “WPA2 (AES)” or “WPA2 Mixed” — make sure your wireless
clients support it.
RADIUS Server IP address — Enter the IP address of the RADIUS server.
RADIUS Server Port — Enter the port number of the RADIUS server.
RADIUS Server Password — Enter the password of the RADIUS server.
2.7.4 Wireless Access Control
This function helps to prevent unauthorized users from connecting to your router:
Only those wireless devices that have the MAC address you assign here can gain
access. The MAC address is a unique hardware identication number that every
network adapter carries. You can use this function in combination with data
encryption (WPA, WPA2 or WEP) to create an additional layer of security for your
wireless network.
Up to 20 MAC addresses can be assigned using this function. Click the “Wireless”
menu on the left of the Web management interface, then click “Access Control.”
NOTE: As explained below, all allowed MAC address will display in the MAC
Address Filtering table.
Delete — To delete a specic MAC address entry, check the “Select” box of the
MAC address you want to delete, then click “Delete Selected.” (You can select
more than one MAC address at a time.)
Delete All — Click to delete all MAC addresses listed.
SYSTEM & NETWORK SETUP
39
Page 40

Enable Access Control — Select to enforce MAC address ltering. The router will
not lter the MAC addresses of wireless clients if this is left unchecked.
MAC Address — Enter the MAC addresses of your wireless devices here without
special characters. If the MAC address label of your wireless device indicates
“aa-bb-cc-dd-ee-ff” or “aa:bb:cc:dd:ee:ff,” just enter “aabbccddeeff” (without the
quote marks).
Comment — This is optional and can be left blank, but it’s recommended that you
enter something (such as “My Desktop,” as shown) that will help you identify an
address later.
Add — Click to add the MAC address and associated comment to the MAC Address
Filtering table.
Clear — Click to remove whatever you entered in the “MAC Address” or “Comment”
elds.
2.7.5 Wi-Fi Protected Setup (WPS)
Wi-Fi Protected Setup (WPS) is the simplest way to build a connection between
wireless network clients and this router. You don’t need to select an encryption
mode and input a long encryption passphrase every time you need to set up a
wireless client: You only need to press a button on a wireless device/client and
this wireless router, and the WPS will do the rest for you.
40
SYSTEM & NETWORK SETUP
Page 41

This router supports two types of WPS: Push-Button Conguration (PBC) and PIN
code. To use PBC, you need to push a specic button on the wireless client to start
the WPS mode and switch this router to WPS mode. You can push the Reset/WPS
button of this router, or click “Start PBC” in the Web conguration interface to do
this. To use PIN code, you need to know the PIN code of the wireless client and
switch it to WPS mode, then provide the PIN code of the wireless client you want
to connect to this wireless router.
Click the “Wireless” menu on the left of the Web management interface, then click
“WPS.”
Enable WPS Settings — Check the box to enable the function; uncheck to disable.
Enable WPS Proxy — Check the box to enable the function; uncheck to disable.
When enabled, it allows another access point to serve as an “intermediary” device
for the connection between wireless network clients and the router.
WPS Status — “Congured” is displayed if the wireless security (encryption) function
of this wireless router is properly set. “Not congured” is shown if the WPS
function has not been congured correctly.
PinCode Self — This is the WPS PIN code of this wireless router, which is useful
when you need to build a wireless connection by WPS with other WPS-enabled
wireless devices.
SSID — As it denes this router.
Authentication Mode — If you don’t enable the security function of the router before
WPS is activated, the router will auto-set the security to WPA (AES) and generate
a set of passphrase keys for WPS connection.
Passphrase Key — As it was congured.
Cong Mode — There are “Registrar” and “Enrollee” modes as options for the WPS
connection. When “Registrar” is enabled, wireless clients will follow the router’s
wireless settings for a WPS connection. When “Enrolle” mode is enabled, the
router will follow the wireless settings of wireless client for a WPS connection.
Congure by Push Button — Click “Start PBC” to start a Push-Button-style WPS
setup procedure. This wireless router will wait for WPS requests from wireless
clients for two minutes. The WLAN LED on the wireless router will be on for two
minutes when this wireless router is waiting for an incoming WPS request.
Congure by Client PinCode — Enter the PIN code of the wireless client you want
to connect, and click “Start PIN.” The WLAN LED on the wireless router will be
on when this wireless router is waiting for an incoming WPS request.
2.7.6 Security Tips for Wireless Networks
Below are ve reminders that will help you maintain a higher level of security for
your wireless network.
• Never use simple words for the WPA/WEP encryption passphrase. A good
SYSTEM & NETWORK SETUP
41
Page 42

password cannot be found in the dictionary and consists of a combination of
characters, symbols and numbers. You should also refrain from using passwords
that carry a personal meaning — names of pets, names or birthdays of a spouse,
and such — as these can easily be guessed by unauthorized users.
• Use WPA versus WEP whenever possible: WPA encryption and (even more so)
WPA2 encryption are much stronger. If your wireless network adapters support
WPA or WPA2, you should abandon WEP entirely.
• You can hide the ESSID of this router by setting the “Broadcast ESSID” option
(refer to section 2.7.2.Advanced Wireless Settings) to “Disable.” Once this
option is disabled, the router will no longer broadcast the SSID; thus, wireless
clients in the area will not be able to see the wireless network in the list of
available WLAN networks. Keep in mind that hiding the SSID will make it more
difcult for wireless clients to join the network — and that is basically the idea.
Instead of selecting the wireless network from the list, the user now must
manually enter the wireless SSID, which will be difcult without knowing what it
is. While this option offers additional protection, you should never rely on this
mechanism as your only means of protection. A WPA encryption key is still
highly recommended. Hiding the SSID of your access point is simply one
additional step you can take.
• Use the Access Control function (section 2.7.4) so people who are not on your
list will not be able to connect to your network. If you don’t have guest trafc, you
normally know which computers access your network, and you can specically
allow those computers and deny all the others.
• Utilizing all three mechanisms (encryption, no SSID broadcast and MAC address
ltering) offers the best protection against unauthorized access.
42
SYSTEM & NETWORK SETUP
Page 43

3 ADVANCED FUNCTIONS
3.1 Quality of Service (QoS)
Quality of service provides an efcient way for computers on the network to share
the Internet bandwidth with a promised quality of Internet service. Without QoS,
all computers and devices on the network compete with each other to get Internet
bandwidth, and some applications which require guaranteed bandwidth (like video
streaming and network telephone) are affected negatively, resulting in an interruption
of video/audio transfers. QoS allows you to limit the maximum bandwidth or grant
a guaranteed bandwidth for a specic computer or network service port.
3.1.1 Basic QoS Settings
Click “QoS” on the left of the Web management interface.
Enable QoS— Check to enable the function; uncheck if you prefer not to enforce
QoS bandwidth limitations.
Total Download Bandwidth — You can set the limit of total download bandwidth in
kilobits. To disable the download bandwidth limitation, enter “0.”
Total Upload Bandwidth — You can set the limit of total upload bandwidth in kilobits.
To disable the upload bandwidth limitation, enter “0.” NOTE: Both Total Download
and Total Upload bandwidths should be specied according to the maximum
ADVANCED FUNCTIONS
43
Page 44

performance of your Internet service. If you’re not sure about these numbers,
contact your ISP. QoS can only be effective if accurate information is provided.
Current QoS Table — All existing QoS rules are shown here.
Add — Click to add new QoS rules (see section 3.1.2 Adding a New QoS Rule).
Edit — To modify the content of a specic rule, check the “Select” box of that rule,
then click “Edit.” NOTE: Only one rule should be selected at a time. If you didn’t
select a rule before clicking “Edit,” you’ll be prompted to add a new rule.
Delete — You can select one or more rules to delete by checking the “Select” box of
the rule(s) you want to delete, then clicking “Delete.” If the QoS table is empty, this
button is inaccessible.
Delete All — Click to delete all rules in the QoS table. If the QoS table is empty,
this button is inaccessible.
Move Up — Click to raise the priority of the selected QoS rule.
Move Down — Click to lower the priority of the selected QoS rule.
3.1.2 Adding a New QoS Rule
After you click “Add” on the QoS screen, you’ll have these options.
Rule Name — Enter a name for the QoS rule (up to 15 alphanumerical characters;
e.g, “VoIP Phone”).
Bandwidth — Set the bandwidth amount of the QoS rule. You need to select the
data direction of this rule (Upload or Download) and the speed of the bandwidth
limitation in kbps, then select the type of QoS: “Guarantee” (guaranteed usable
bandwidth for this rule) or “Max” (set the maximum bandwidth for the application
allowed by this rule).
44
ADVANCED FUNCTIONS
Page 45

Local IP Address — Specify the local (source) IP address that will be affected by
this rule. Enter the starting IP address in the left eld, and enter the end address
in the right eld to dene a range of IP addresses; or just enter the IP address in
the left eld to dene a single IP address.
Local Port Range — Enter the range of local (source) port numbers that should be
affected by this rule. To apply this rule on ports 80 to 90, enter “80-90”; to apply
this rule only to a single port, just enter the port number, such as “80.”
Remote IP Address — Specify the remote (destination) IP address that should be
affected by this rule. Enter the starting IP address in the left eld, and enter the
end address in the right eld to dene a range of IP addresses; or just enter the
IP address in the left eld to dene a single IP address.
Remote Port Range — Enter the range of remote (destination) port numbers that
should be affected by this rule. To apply this rule on ports 80 to 90, enter “80-90”;
to apply this rule only to a single port, just enter the port number, such as “80.”
If the remote (destination) IP address and/or port number is universal, just leave
it blank.
Trafc Type — Select the trafc type of this rule from the drop-down menu: “None,”
“SMTP,” “HTTP,” “POP3” or “FTP.” To make this rule an IP address-based rule
(to apply the limitation on all trafc from/to the specied IP address or port
number), select “None.”
Protocol — Select the protocol type of this rulefrom the drop-down menu: “TCP” or
“UDP.” If you don’t know what protocol your application uses, try “TCP” rst and
switch to “UDP” if this rule doesn’t seem to work.
Click “Save” to add the new rule. It will appear in the current QoS table. Should an
error message show up after you click “Save,” you can try again, but xing the
problem rst and then clicking “Save” will have a better chance of working.
To erase all values you’ve entered, click “Reset.”
3.2 Network Address Translation (NAT)
Network Address Translation (NAT, also known as Network Masquerading, Native
Address Translation or IP Masquerading) is a technique of transceiving network
trafc through a router that involves re-writing the source and/or destination IP
addresses and usually the TCP/UDP port numbers of IP packets as they pass
through. Checksums (both IP and TCP/UDP) must also be rewritten to take account
of the changes. Most systems using NAT do so in order to enable multiple hosts
on a private network to access the Internet using a single public IP address (see
gateway). Many network administrators nd NAT a convenient technique and use
it widely. Simply put: The router’s NAT function allows the connection of multiple
computers to one Internet line.
ADVANCED FUNCTIONS
45
Page 46

Click the “NAT” menu on the left of the Web management interface. NAT is enabled
by default, and there is normally no need to change this.
3.2.1 Port Forwarding
With this function, you can tell the router to forward incoming connections bound to
a specic port or port range to an IP address on your local network. Many online
games, game consoles with Internet service, remote access applications and
special network devices such as network cameras require you to open and forward
ports, often referred to as port mapping.
With port forwarding, the external and internal ports are always the same. If you
need to redirect an incoming request on public port A to internal port B, you need
to use the Virtual Server function (see section 3.2.2 Virtual Server).
Enable Port Forwarding — Check to enable this function; uncheck to disable.
Private IP — Enter the IP address of the computer on the local network that provides
Internet service.
Computer Name — With all the computers connected to the router listed in this
drop-down menu, you can select a name without checking its IP address.
46
ADVANCED FUNCTIONS
Page 47
Type — Select the type of connection from the drop-down menu: “TCP,” “UDP” or
“Both.” If you’re not sure which to use, select “Both.”
Port Range — Enter the starting port number in the left eld and enter the ending
port number in the right eld. To redirect a single port number, just enter the port
number in the left eld.
Comment — Enter text to describe this mapping, using up to 16 alphanumerical
characters; e.g., “camera web port.”
Add — Add the mapping to the Current Port Forwarding Table.
Reset — Click to remove all entries.
Current Port Forwarding Table — Shows all existing port forwarding rules (port
mapping).
Delete — Select a port forwarding mapping by checking the “Select” box of the
mapping, then clicking “Delete.” If there’s no existing mapping, this button will be
grayed out.
Delete All — Click to delete all existing port mappings.
Reset — Click to unselect all mappings.
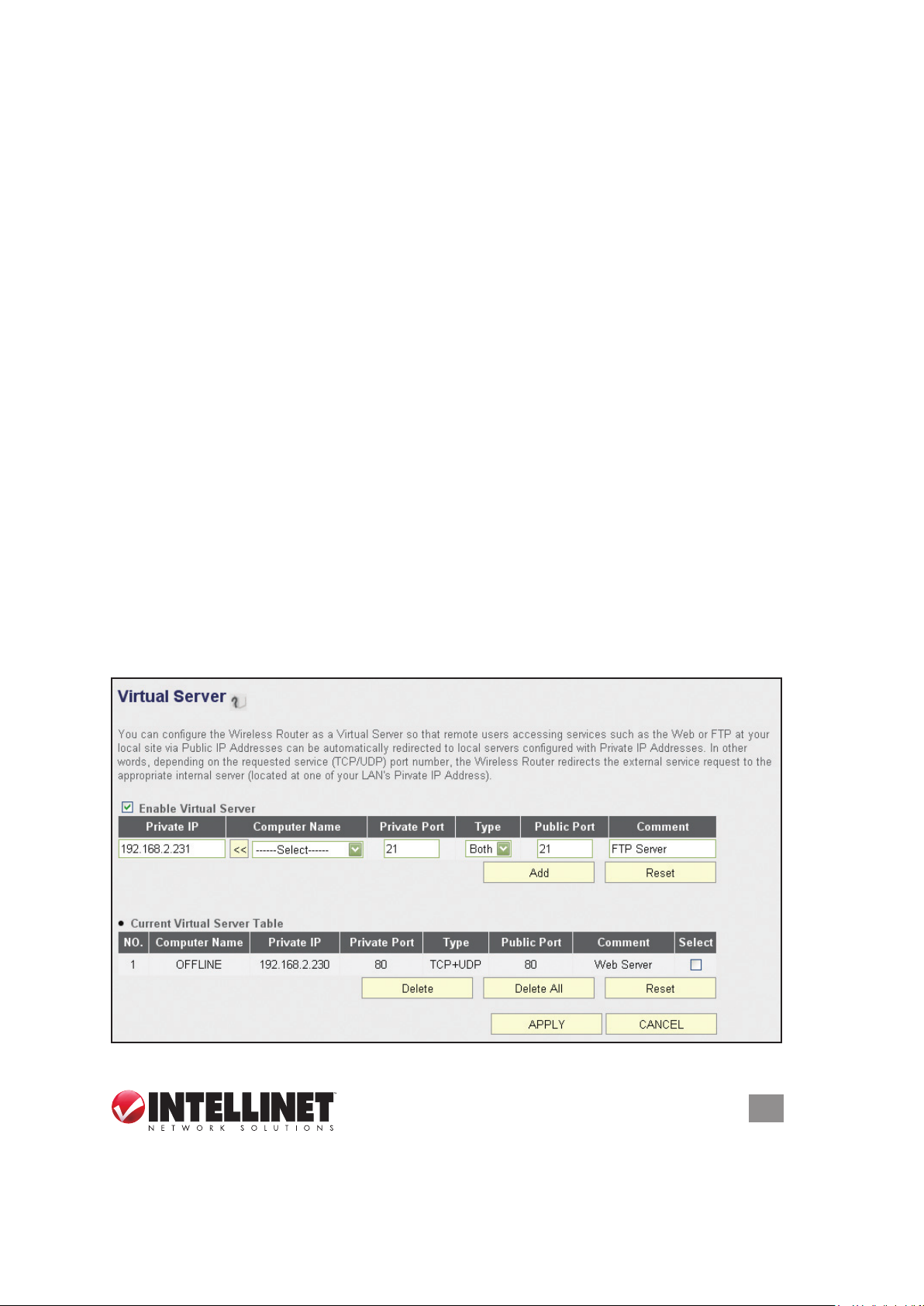
3.2.2 Virtual Server
This function is very similar to Port Forwarding. The difference is that Virtual Server
only allows you to specify one port. On the other hand, it enables you to redirect
a public port to a different private port (e.g., public port 80 redirects to private port
85). This makes Virtual Server the obvious choice for hosting public Web services
(such as a Web server) on a computer connected to one of the LAN ports on the
router.
ADVANCED FUNCTIONS
47
Page 48

Enable Virtual Server — Check to enable this function; uncheck to disable.
Private IP — Enter the IP address of the computer on the local network that provides
Internet service.
Computer Name — With all the computers connected to the router listed in this
drop-down menu, you can select a name without checking its IP address.
Private Port — Enter the port number of the IP address that provides Internet
service.
Type — Select the type of connection from the drop-down menu: “TCP,” “UDP” or
“Both.” If you’re not sure which to use, select “Both.”
Public Port — Select the port number of Internet IP address that will be redirected
to the port number of the local IP address dened above.
Comment — Enter text to describe this mapping, using up to 16 alphanumerical
characters; e.g., “FTP Server.”
Add — Add the mapping to the Virtual Server Table.
Reset — Click to remove all entries.
Current Virtual Server Table — Shows all existing virtual server mappings.
Delete — Select a virtual server mapping by checking the “Select” box of the
mapping, then clicking “Delete.” If there’s no existing mapping, this button will be
grayed out.
Delete All — Click to delete all existing virtual server mappings.
Reset — Click to unselect all mappings.
3.2.3 Port Mapping for Special Applications
Some applications require more than one connection a time. This function allows
these applications to work when they won’t work with simple NAT rules.
Enable Special Applications — Check to enable this function; uncheck to disable.
IP Address — Enter the IP address of the computer where you want to open the
ports.
Computer Name — With all the computers connected to the router listed in this
drop-down menu, you can select a name without checking its IP address.
TCP Port to Open — This is the outgoing (outbound) range of TCP port numbers
for this particular application.
UDP Port to Open — This is the outgoing (outbound) range of UDP port numbers
for this particular application.
Comment — Enter a description for this setting.
Popular Applications — The drop-down menu lists some popular applications that
require multiple connections. To save one to the Current Trigger-Port Table,
select it and click “Add.”
Add — Click to add a selection to the Current Trigger-Port Table.
Reset — Click to remove all entries.
48
ADVANCED FUNCTIONS
Page 49

Current Trigger-Port Table — All the settings for the specifal applications are listed
here.
Delete — To remove a Special Application setting from the Current Trigger-Port
Table, select the setting and click “Delete.”
Delete All — Click to delete all existing specifal application settings.
3.2.4 UPnP
This function enables network auto-conguration for peer-to-peer communications.
With this function, network devices will be able to communicate with other UPnP-
enabled devices directly and learn about other devices. Many network devices and
applications rely on UPnP function nowadays.
UPnP Module — There is nothing to congure for UPnP. Just select “Enable” or
“Disable.”
3.2.5 ALG
Application Layer Gateway (ALG) is a special function of this router. It includes
many preset routing rules for numerous applications (as shown below) that require
special support to work with the NAT architecture. Check “Enable” next to the
listing and click “Apply.”
ADVANCED FUNCTIONS
49
Page 50

3.3 Firewall
In addition to the NAT feature, this router provides rewall functionality to block
malicious intruders from accessing the computers on your local network. Click the
“Firewall” menu on the left of the Web management interface.
Firewall Module — Check to enable this function; uncheck to disable.
3.3.1 Access Control
This function allows or denies computers with a specic MAC address — or a
specic IP address, protocol or port — access to the network.
Enable MAC Filtering — Check this box to enable MAC address-based ltering,
and select “Deny” or “Allow” to determine the behavior of the MAC ltering table.
If you select “Deny,” all MAC addresses listed in the ltering table will be denied
access to the network; if you select “Allow,” only MAC addresses listed in the
50
ADVANCED FUNCTIONS
Page 51

ltering table will be able to connect to the network, and all other network devices
will be rejected.
Client PC MAC address — Enter the MAC address of the computer or network
device. Dashes (–) or colons ( : ) are not required. For example, if the MAC
address label of your device reads “aa-bb-cc-dd-ee-ff” or “aa:bb:cc:dd:ee:ff,” just
enter “aabbccddeeff” (without the quote marks).
Computer Name — With all the computers connected to the router listed in this
drop-down menu, you can select a name without checking its IP address.
Comment — Enter up to 16 alphanumerical characters to identify the MAC address,
such as “Room 2A Computer.” This is optional, and you can leave it blank.
Add — Click to add the MAC address and associated comment to the MAC address
ltering table.
Reset — Click to remove all entries (in either panel).
Current MAC Filtering Table — All existing MAC addresses in the ltering table.
Delete — You can select one or more MAC addresses to delete by checking the
“Select” box of those you want to delete, then clicking “Delete.”
Delete All — Click to delete all MAC addresses listed.
Enable IP Filtering — Check this box to enable IP address-based ltering, and
select “Deny” or “Allow” to determine the behavior of the IP ltering table. If you
select “Deny,” all IP addresses listed in the ltering table will be denied access
to the network; if you select “Allow,” only IP addresses listed in the ltering table
will be able to connect to the network; all other network devices will be rejected.
Add PC — Click to add a new IP address to the IP ltering table. Up to 20
addresses can be added. (Refer to section 3. 3 .1.1 Add PC below.)
Delete — You can select one or more IP addresses to delete by checking the “Select”
box of those you want to delete, then clicking “Delete.”
Delete All — Click to delete all IP addresses listed.
ADVANCED FUNCTIONS
51
Page 52

3.3.2 Add PC
Clicking “Add PC” on the Access Control screen will display this page.
Client PC Description — Enter up to 16 alphanumerical characters to describe this
IP address.
Client PC IP Address — Enter the starting IP address in the left eld and the end
IP address in the right eld to dene a range of IP addresses, or just input the IP
address in the left eld to dene a single IP address.
Client PC Service — Select all services you want to allow or deny through this IP
address.
52
ADVANCED FUNCTIONS
Page 53

Protocol — If the service you need is not listed, you can create a new service
yourself. Select “TCP” or “UDP” from the drop-down menu and follow the Port
Range instructions below. If you’re not sure which Protocol to use, select “Both.”
Port Range — Enter the port range of the new service. To specify ports 80 to 90,
enter “80-90”; to apply this rule to a single port, just enter the port number.
Add — Click to save the settings. You’ll be re-directed to the previous menu, and
the rule you just set will appear in the IP Filtering Table.
Reset — Click to remove all entries.
3.3.3 URL Blocking
To prevent computers in the local network from accessing certain Web sites, you
can dene the Web sites, IP addresses or keywords here. This function is useful
for parents and company managers: The former can protect children from
inappropriate contents on the Internet; the latter can protect employees from
losing their jobs.
You can block full Web site URLs, such as “www.microsoft.com”; IP addresses,
such as “207.46.232.182”; or just a part of a URL. For example, if you enter the
keyword “downloads,” the computer can connect to “www.microsoft.com” but not
“www.microsoft.com/downloads.”
Enable URL Blocking — Check to enable this function; uncheck to disable.
URL/Keyword — Enter the URL (host name or IP address of a Web site, such as
“http://www.blocked-site.com” or “http://11.22.33.44”), or a keyword contained in
a URL (like “pornography,” “sex,” “banner advertisement,” etc).
ADVANCED FUNCTIONS
53
Page 54

Add — Click to add the URL/keyword to the URL/Keyword Filtering Table.
Reset — Click to remove all entries in the “URL/Keyword” text eld.
Current URL Blocking Table — All existing URL/keywords in the ltering table.
Delete — Select a URL/keyword by checking the “Select” box of the entry, then
clicking “Delete.”
Delete All — Click to delete all existing URL/keyword entries.
3.3.4 DoS Attack Prevention
A denial-of-service (DoS) attack is an attempt to make a computer resource
unavailable to its intended users. DoS attacks generally consist of the concerted,
malevolent efforts of a person or persons to prevent an Internet site or service from
functioning efciently or at all, temporarily or indenitely. One common method of
attack involves saturating the target (victim) machine, in this case the router, with
external communications requests, such that it cannot respond to legitimate trafc
or responds so slowly as to be rendered effectively unavailable.
This router has a built-in DoS attack prevention mechanism to prevent DoS attacks
from succeeding. Activating all options is recommended.
Ping of Death — Ping of Death is a
special packet, and it will cause certain
computers to stop responding. Check
this box and the router will lter out this
kind of packet.
Discard Ping From WAN — Ping is a
common and useful tool for knowing the
connection status of a specied remote
network device, but some malicious
intruder could try to ll your network bandwidth with a lot of PING request data
packets to make your Internet connection become very slow — even unusable.
Check this box and the router will ignore all inbound PING requests. NOTE:
Unfortunately, when you activate this function, you will not be able to ping your
own router from the Internet, either.
Port Scan — An intruder could try to use a port scanner to determine how many
ports of your Internet IP address are open, through which they can collect a lot
of valuable information. Check this box and the router will block all trafc that’s
involved in trying to scan your Internet IP address.
Sync Flood — Another kind of attack, this one uses a lot of fake connection requests
to consume the memory of your server, rendering it unusable. Check this box
and the router will lter this kind of trafc out.
Advanced Settings — Click to set advanced settings of the DoS prevention method
listed above. (See section 3.3.4.1 DoS – Advanced Settings below.)
54
ADVANCED FUNCTIONS
Page 55

3.3.4.1 DoS – Advanced Settings
Clicking “Advanced Settings” on the rst DoS Module screen will display this page.
Ping of Death — Set the threshold of when this DoS prevention mechanism will be
activated. Check the box for Ping of Death and enter the frequency of threshold
(how many packets per second, minute or hour). You can also enter the “Burst”
value: When this number of Ping of Death packets is received within a very
short timeframe, this DoS prevention mechanism will be activated.
Discard Ping From WAN — Check the box to activate this mechanism.
Port Scan — A number of port scan methods are listed here. Check one or more
DoS attack methods you want to prevent.
Sync Flood — As with Ping of Death, you can set the threshold for when this DoS
prevention mechanism will be activated.
3.3.5 Demilitarized Zone (DMZ)
With NAT and the rewall, this router protects all connected computers in your local
network. Sometimes, however, you may want to expose a computer or network
device to the Internet intentionally for various reasons; e.g., troubleshooting of
network problems. Placing a computer in the DMZ puts it at great risk because the
protection mechanisms of the router no longer apply.
So, unless you know what you are doing, you should not use this function at all.
Enable DMZ — Check to enable this function; uncheck to disable.
Public IP — Select “Dynamic IP” or “Static IP.” If you select “Dynamic IP,” you need
to select an Internet connection session from the drop-down menu; if you select
“Static IP,” enter the IP address that you want to map to a specic private IP
address.
Client PC IP Address — Enter the private IP address that the Internet IP address
will be mapped to. That is the computer you want to bypass the rewall and NAT.
ADVANCED FUNCTIONS
55
Page 56

Computer Name — With all the computers connected to the router listed in this
drop-down menu, you can select a name without checking its IP address.
Add — Click to add the public IP address and associated private IP address to the
DMZ table.
Reset — Click to remove all entries (in either panel).
Current DMZ Table — All existing public/private IP address mappings.
Delete — Select one or more DMZ entries to delete by checking the “Select” box of
those you want to delete, then clicking “Delete.”
Delete All — Click to delete all DMZ entries.
56
ADVANCED FUNCTIONS
Page 57

4 ADDITIONAL FUNCTIONS/FEATURES
4 .1 Sta tus
This screen and the submenus that can be accessed from here show information
about the rmware version of the router, the Internet connection, IP address
information, log les and more. Click the “Status” link at the upper-right corner of
the Web management interface.
In case you experience technical difculties with the router and need to contact
technical support, you should write down the Boot Code Version and Runtime Code
Version shown on your screen (which may vary from the example shown here). It
is very likely that you would be asked to provide these numbers by the technical
support representative.
4.1.1 Internet Connection
ADDITIONAL FUNCTIONS
57
Page 58

This screen shows IP address information the router has obtained. If you experience
problems with your Internet connection, open this page and check the contents.
Values for IP address, default gateway and primary DNS should always be lled.
If they’re missing, it indicates that there is a connection problem preventing the
router from accessing the Internet.
4.1.2 Device Status
This screen shows information about the wireless conguration as well as the
LAN conguration, including information about the encryption and IP address
settings of the router.
4.1.3 System Log
All important system events are logged here.
58
ADDITIONAL FUNCTIONS
Page 59

Save — Click to save the current event log to a text le.
Clear — Click to delete all event log messages displayed.
Refresh — Click to refresh the view to display the most current event log messages.
4.1.4 Security Log
Save — Click to save the current event log to a text le.
Clear — Click to delete all event log messages displayed.
Refresh — Click to refresh the view to display the most current event log messages.
4.1.5 Active DHCP Client
If you’re using the DHCP server function of this router, you can use this function to
check all active DHCP leases issued by this router.
4.1.6 Statistics
Statistics of the wireless LAN, wired LAN and WAN interface of the router are
shown on this screen.
ADDITIONAL FUNCTIONS
59
Page 60

Refresh — Click to display the latest information. NOTE: The information is
accumulative and is only reset after the router is restarted.
4.2 Tools
This screen and the submenus that can be accessed from here provide options
and information helpful in managing les and router information. Click the “Tools”
link at the upper-right corner of the Web management interface.
4.2.1 Conguration Tools
This screen lets you back up the conguration of the router to a le so you can
reload it at a later time. You can save different congurations, each with unique
settings, and reload them as needed.
Backup Settings — Click “Save...” and you’ll be prompted to download the
conguration as a le (the default lename is “default.bin”). Remember to save it
as another lename each time you back up for easier retrieval of information..
60
ADDITIONAL FUNCTIONS
Page 61

Restore Settings — Click “Browse…” to select a saved conguration le from your
computer, then click “Upload” to transfer the conguration le to the router. After
the conguration is uploaded, the router’s current conguration will be replaced
by the le you just uploaded.
Restore to Factory Default — Click to reset all settings of the router to the factory
default values.
4.2.2 Firmware Upgrade
The rmware of the router is like the operating system on your computer. Firmware
upgrades for this router may be available at www.intellinet-network.com. If you
experience technical difculties, you should rst check if any updated rmware is
available for the router and install it using this rmware upgrade function.
Next — Click to proceed to the upgrade procedure screen.
Browse — Click to locate the rmware le you’ve downloaded. If the le is in Zip
(compressed archive) format, you need to uncompress it prior to the upgrade.
Apply — Click to start the rmware upgrade process.
Never interrupt the upgrade process by closing the Web browser or by physically
disconnecting your computer from the router. If the upgrade process is interrupted
by a network problem or a power failure, the router will cease to function. Damages
resulting from improperly performed rmware upgrades are excluded from the
product warranty!
ADDITIONAL FUNCTIONS
61
Page 62

4.2.3 Reset
This screen lets you restart the router without disconnecting the power from the
unit. A restart (or system reset) may be necessary if the router responds slowly, if
your Internet connection speed has dropped or if the router behaves in an unusual
manner.
Apply — Click to reset the router. It will be operational again after a few minutes.
NOTE: This function does not change any settings you have made. It simply restarts
(reboots) the router — just as Start / Shut Down / Restart reboots your computer —
freeing up memory and system resources for more stable operation.
62
ADDITIONAL FUNCTIONS
Page 63

5 TROUBLESHOOTING
This section helps you troubleshoot problems you may be experiencing with the
router. Before you contact your dealer for help, you should perform the following
troubleshooting steps as they apply to your situation.
The router is not responding when I want to access it with the Web browser.
• Check the power connection and the connection of the network cable. All cords
and cables should be correctly and rmly inserted into the router.
• If all LEDs on the router are off, check the status of the A/C power adapter, and
make sure it’s correctly plugged into your power outlet.
• Verify the IP address you connect to. The router’s default IP address is
192.168.2.1, but you may have changed it.
• Are you using a MAC or an IP address lter? Try to connect to the router with
another computer and see if it works; if not, restore the router’s factory default
settings by pressing the Reset button on the back panel of the router for at least
10 seconds.
• Set your computer to obtain an IP address automatically (DHCP) and check if
your computer gets an IP address.
• If you did a rmware upgrade before the problem started, contact your dealer
for assistance.
I can’t get connected to the Internet.
• Go to Status / Internet Connection and check the Internet connection status.
• Be patient — sometimes the Internet is just slow.
• Connect a computer directly to the DSL or cable modem to see if you can
access the Internet that way. If you can, check the WAN connection settings of
the router to make sure they are set up correctly.
• Check the PPPoE / L2TP / PPTP user ID and password again.
• Call your Internet service provider and ask if there’s something wrong with their
service.
• If you just can’t connect to one or more websites but you can still use other
Internet services, check the URL/keyword lter to make sure that you are not
trying to access a blocked website.
• Restart your modem and the router.
• Reset the device provided by your Internet service provider.
• Try to use an IP address instead of a hostname. If you can use an IP address to
communicate with a remote server but can’t use a hostname, check the DNS
settings.
TROUBLESHOOTING
63
Page 64

My wireless notebook cannot see or connect to the wireless network.
• Check if Broadcast ESSID is off. Remember that you need to input the ESSID
on your wireless client manually if the ESSID broadcast is disabled.
• Check that you’ve securely attached the antenna(s).
• Make sure that you’re not too far away from the router.
I can’t log on to the Web management interface: The password is wrong.
• Make sure you’re connecting to the correct IP address of the router.
• The password is case-sensitive. Make sure the Caps Lock feature isn’t on.
• If you’ve simply forgotten your password, do a hardware reset using the Reset
button on the back panel of the router.
The router becomes hot.
• It’s normal for the router to heat up during operation, and this is usually nothing
to worry about. If, however, the router gets too hot to touch, or if you smell
something burning or see smoke coming from the router or A/C power adapter,
immediately disconnect the router and adapter from the utility power — making
sure it’s safe to do this — and call your dealer for help.
The date and time of all the event logs are wrong.
• Adjust the internal clock of the router.
64
TROUBLESHOOTING
Page 65

6 GLOSSARY
Default Gateway (Router): Every non-router IP device needs to congure a default
gateway’s IP address. When the device sends out an IP packet, if the destination is
not on the same network, the device has to send the packet to its default gateway,
which will then send it out toward the destination.
DHCP: Dynamic Host Conguration Protocol. This protocol automatically gives
every computer on your home network an IP address.
DNS Server IP Address: DNS stands for Domain Name System, which allows
Internet servers to have a domain name (such as www.Broadbandrouter.com) and
one or more IP addresses (such as 192.34.45.8). A DNS server keeps a database
of Internet servers and their respective domain names and IP addresses, so that
when a domain name is requested (as in typing “Broadbandrouter.com” into your
Internet browser), the user is sent to the proper IP address. The DNS server IP
address used by the computers on your home network is the location of the DNS
server your ISP has assigned to you.
DSL Modem: DSL stands for Digital Subscriber Line. A DSL modem uses your
existing phone lines to transmit data at high speeds.
Idle Timeout: Idle Timeout is designed so that after there is no trafc to the
Internet for a pre-congured amount of time, the connection will be disconnected.
IP Address and Network (Subnet) Mask: An Internet Protocol address consists
of a series of four numbers separated by periods, which identies a single, unique
Internet computer host in an IP network. Example: 192.168.2.1 consists of two
portions: the IP network address and the host identier. The IP address is a 32-bit
binary pattern that can be represented as four cascaded decimal numbers separated
by “.”: aaa.aaa.aaa.aaa, where each “aaa” can be anything from 000 to 255; or as
four cascaded binary numbers separated by “.”: bbbbbbbb.bbbbbbbb.bbbbbbbb.
bbbbbbbb, where each “b” can either be 0 or 1. A network mask is also a 32-bit
binary pattern, and consists of consecutive leading 1’s followed by consecutive
trail i n g 0 ’s, su c h as 11111111.11111111.11111111.00 0 00 0 00. Ther e f o r e , so me t im es
a network mask can also be described simply as “x” number of leading 1’s. When
both are represented side by side in their binary forms, all bits in the IP address
that correspond to 1’s in the network mask become part of the IP network address,
and the remaining bits correspond to the host ID. For example, if the IP address
for a device is, in its binary form, 11011001.10110000.10010000.00000111, and if
its net wo rk mask is 11111111.11111111.111100 0 0.00 0 000 0 0 it means t h e de v i ce’s
network address is 11011001.10110000.10010000.00000000, and its host ID is
00000000.00000000.00000000.00000111. This is a convenient and efcient method
for routers to route IP packets to their destination.
GLOSSARY
65
Page 66

ISP: Internet Service Provider. An ISP is a business that provides connectivity to
the Internet for individuals and other businesses or organizations.
LAN: Local Area Network. A LAN is a group of computers and devices connected
together in a relatively small area (such as a house or an ofce). Your home network
is considered a LAN.
MAC Address: MAC stands for Media Access Control. A MAC address is the
hardware address of a device connected to a network, and is a unique identier for
a device with an Ethernet interface. It is composed of two parts: three bytes of data
that corresponds to the Manufacturer ID (unique for each manufacturer), and three
bytes that are often used as the product’s serial number.
NAT: Network Address Translation. This process allows all of the computers on your
home network to use one IP address. Using the broadband router’s NAT capability,
you can access the Internet from any computer on your home network without
having to purchase more IP addresses from your ISP.
PPPoE: Point-to-Point Protocol over Ethernet. Point-to-Point Protocol is a secure
data transmission method originally created for dial-up connections; PPPoE is for
Ethernet connections. PPPoE relies on two widely accepted standards, Ethernet
and the Point-to-Point Protocol. It is a communications protocol for transmitting
information over Ethernet between different manufacturers.
Protocol: A protocol is a set of rules for interaction agreed upon between multiple
parties so that when they interface with each other based on such a protocol, the
interpretation of their behavior is well-dened and can be made objectively, without
confusion or misunderstanding.
Router: A router is an intelligent network device that forwards packets between
different networks based on network layer address information such as IP addresses.
Subnet Mask: A subnet mask, which may be a part of the TCP/IP information
provided by your ISP, is a set of four numbers (e.g., 255.255.255.0) congured like
an IP address. It’s used to create IP address numbers used only within a particular
network (as opposed to valid IP address numbers recognized by the Internet,
which must be assigned by InterNIC).
TCP/IP, UDP: Transmission Control Protocol/Internet Protocol and Unreliable
Datagram Protocol are the standard protocols for data transmission over the Internet.
Both TCP and UDP are transport layer protocols. TCP performs proper error
detection and error recovery, and thus is reliable. UDP, on the other hand, is not
reliable. They both run on top of the IP (Internet Protocol), a network layer protocol.
WAN: A Wide Area Network connects computers located in geographically
separate areas (e.g., different buildings, cities, countries). The Internet is a wide
area network.
66
GLOSSARY
Page 67

7 SPECIFICATIONS
Model 524988 450N
Standards
• IEEE 802.1d (Spanning Tree Protocol)
• IEEE 802.11a (54 Mbps Wireless LAN)
• IEEE 802.11b (11 Mbps Wireless LAN)
• IEEE 802.11g (54 Mbps Wireless LAN)
• IEEE 802.11n (450 Mbps Wireless LAN)
• IEEE 802.3 (10Base-T Ethernet)
• IEEE 802.3u (100Base-TX Fast Ethernet)
• IEEE 802.3ab (Gigabit Ethernet) on Model 524988
General
• LAN ports: 4 RJ45 10/100/1000 Mbps data ports
• LAN ports with Auto MDI/MDI-X
• WAN port: 10/100/1000 Mbps RJ45 connector
• LAN to WAN throughput: 275 Mbps
• PPPoE throughput: 163 Mbps
• 500 MHz MIPS CPU
• Flash: 8 MB
• Memory: 64 MB DDR2 RAM
• Certications: FCC Class B, CE, RoHS
Router
• Supported WAN connection types:
- Dynamic IP (DHCP for cable service)
- Static IP
- PPPoE (for DSL)
- PPTP
- BigPond (Australia)
• Protocols:
- CSMA/CA
- CSMA/CD
- TCP/IP
- UDP
- ICMP
- PPPoE
- NTP
- NAT (network address translation)
SPECIFICATIONS
67
Page 68

- DHCP
- DNS
• NAT:
- Virtual server
- Port forwarding
- Special applications (port trigger)
• Firewall:
- Access control based on MAC address
- URL lter
- DMZ (demilitarized zone)
• Supports UPnP (Universal Plug and Play)
• Supports DHCP (client/server)
• Supports PPPoE (DSL), DHCP (cable) and static IP
• VPN passthrough: PPTP, IPsec, L2TP
Wireless 5.0 GHz
• Chipset: Ralink RT3883
• Link speed: up to 450 Mbps
• Modulation technologies:
- 802.11a/n: Orthogonal Frequency Division Multiplexing (OFDM): BPSK, QPSK,
16QAM, 64QAM
• Channels:
- USA & Canada: 36, 40, 44, 48, 149, 153, 157, 161, 165
- Europe: 36, 40, 44, 48, 52, 56, 60, 64, 100, 104, 108, 112, 116, 120, 124, 128,
132, 136, 140
• Output power:
- 11n (450 Mbps): 20 MHz: 14 dBm; 40 MHz: 14 dBm (±1.5 dBm)
- 11a (54 Mbps): 14 dBm (± 1.5 dBm)
• Receiver sensitivity:
- 11n (450 Mbps): 20 MHz: -66 dBm; 40 MHz: -64 dBm (±2 dBm)
- 11a (54 Mbps): -68 dBm (±2 dBm)
Wireless 2.4 GHz
• Chipset: Ralink RT3092
• Link speed: up to 300 Mbps
• Modulation technologies:
- 802.11b: Direct Sequence Spread Spectrum (DSSS): DBPSK, DQPSK, CCK
- 802.11g: Orthogonal Frequency Division Multiplexing (OFDM): BPSK, QPSK,
16QAM, 64QAM
- 802.11n: Orthogonal Frequency Division Multiplexing (OFDM): BPSK, QPSK,
16QAM, 64QAM
68
SPECIFICATIONS
Page 69

• Channels:
- USA & Canada: 11 channels
- Europe: 13 channels
• Output power:
- 11n (300 Mbps): 20 MHz: 17 dBm; 40 MHz: 16 dBm (±1.5 dBm)
- 11g (54 Mbps): 17 dBm (±1.5 dBm)
- 11b (11 Mbps): 18 dBm (±1.5 dBm)
• Receiver sensitivity:
- 11n (300 Mbps): 20 MHz: -66 dBm; 40 MHz: -64 dBm (±2 dBm)
- 11g (54 Mbps): -70 dBm (±2 dBm)
- 11b (11 Mbps): -84 dBm (±2 dBm)
Wireless 2.4 + 5.0 GHz
• Wireless security:
- WEP encryption (64/128 bit)
- WPA TKIP
- WPA2 AES
- WPA2 mixed
- WPA RADIUS
- Client access control through media access control (MAC) lter
• Antennas:
- 3 xed-dipole antennas with 3 dBi gain each
- 2.4 GHz/300 Mbps: 2T2R MIMO mode (2 transmitter, 2 receiver)
- 5 GHz/450 Mbps: 3T3R MIMO mode (3 transmitter, 3 receiver)
Environmental
• Dimensions: 195 (W) x 127 (L) x 35 (H) mm (7.6 x 5.0 x 1.4 in.)
• Weight: 1.0 kg (2.2 lbs.)
• Operating temperature: 0 – 50°C (32 – 122°F)
• Operating humidity: 10 – 90% RH, non-condensing
• Storage temperature: -20 – 60°C (4 – 149°F)
Power
• External power adapter: 12 V DC, 1.25 A
• Power consumption: 10.5 Watts max.
SPECIFICATIONS
69
Page 70

Model 525268 300N
Standards
• IEEE 802.1d (Spanning Tree Protocol)
• IEEE 802.11a (54 Mbps Wireless LAN)
• IEEE 802.11b (11 Mbps Wireless LAN)
• IEEE 802.11g (54 Mbps Wireless LAN)
• IEEE 802.11n (450 Mbps Wireless LAN)
• IEEE 802.3 (10Base-T Ethernet)
• IEEE 802.3u (100Base-TX Fast Ethernet)
General
• LAN ports: 4 RJ45 10/100 Mbps data ports
• LAN ports with Auto MDI/MDI-X
• WAN port: 10/100 Mbps RJ45 connector
• Chipset: Ralink RT3352 + RT3572
• Flash: 4 MB
• Memory: 32 MB DDR2 RAM
• Certications: FCC Class B, CE, RoHS
Router
• Supported WAN connection types:
- Dynamic IP (DHCP for cable service)
- Static IP
- PPPoE (for DSL)
- PPTP
- BigPond (Australia)
• Protocols:
- CSMA/CA
- CSMA/CD
- TCP/IP
- UDP
- ICMP
- PPPoE
- NTP
- NAT (network address translation)
- DHCP
- DNS
• NAT:
- Virtual server
- Port forwarding
70
SPECIFICATIONS
Page 71

- Special applications (port trigger)
• Firewall:
- Access control based on MAC address
- URL lter
- DMZ (demilitarized zone)
• Supports UPnP (Universal Plug and Play)
• Supports DHCP (client/server)
• Supports PPPoE (DSL), DHCP (cable) and static IP
• VPN passthrough: PPTP, IPsec, L2TP
Wireless 5.0 GHz
• Link Speed: up to 300 Mbps
• Modulation technologies:
- 802.11a/n: Orthogonal Frequency Division Multiplexing (OFDM): BPSK, QPSK,
16QAM, 64QAM
• Channels:
- USA & Canada: 36, 40, 44, 48, 149, 153, 157, 161, 165
- Europe: 36, 40, 44, 48, 52, 56, 60, 64, 100, 104, 108, 112, 116, 120, 124, 128,
132, 136, 140
• Output power:
- 11n (300 Mbps): 11 dBm (±1.5 dBm)
- 11a (54 Mbps): 11 dBm (± 1.5 dBm)
Wireless 2.4 GHz
• Link Speed: up to 300 Mbps
• Modulation technologies:
- 802.11b: Direct Sequence Spread Spectrum (DSSS): DBPSK, DQPSK, CCK
- 802.11g: Orthogonal Frequency Division Multiplexing (OFDM): BPSK, QPSK,
16QAM, 64QAM
- 802.11n: Orthogonal Frequency Division Multiplexing (OFDM): BPSK, QPSK,
16QAM, 64QAM
• Channels:
- USA & Canada: 11 channels
- Europe: 13 channels
• Output power:
- 11n (300 Mbps): 13 dBm (±1.5 dBm)
- 11g (54 Mbps): 14 dBm (±1.5 dBm)
- 11b (11 Mbps): 16 dBm (±1.5 dBm)
Wireless 2.4 + 5.0 GHz
• Wireless security:
- WEP encryption (64/128 bit)
SPECIFICATIONS
71
Page 72

- WPA TKIP
- WPA2 AES
- WPA2 mixed
- WPA RADIUS
- Client access control through media access control (MAC) lter
• Antennas:
- 2 xed-dipole antennas with 3 dBi gain each
- 2.4 GHz/300 Mbps: 2T2R MIMO mode (2 transmitter, 2 receiver)
- 5 GHz/300 Mbps: 2T2R MIMO mode (2 transmitter, 2 receiver)
Environmental
• Dimensions: 157 (W) x 127 (L) x 30 (H) mm (6.2 x 5.0 x 1.2 in.)
• Weight: 0.8 kg (1.7 lbs.)
• Operating temperature: 0 – 50°C (32 – 122°F)
• Operating humidity: 10 – 90% RH, non-condensing
• Storage temperature: -20 – 60°C (4 – 149°F)
Power
• External power adapter: 5 V DC, 2 A
WASTE ELECTRICAL & ELECTRONIC EQUIPMENT
Disposal of Electric and Electronic Equipment
(applicable in the European Union and other European countries with separate collection systems)
This symbol on the product or its packaging indicates that this product shall not be
treated as household waste. Instead, it should be taken to an applicable
collection point for the recycling of electrical and electronic equipment.
By ensuring this product is disposed of correctly, you will help prevent
potential negative consequences to the environment and human health,
which could otherwise be caused by inappropriate waste handling of this product.
If your equipment contains easily removable batteries or accumulators, dispose of
these separately according to your local requirements. The recycling of materials
will help to conserve natural resources. For more detailed information about
recycling of this product, contact your local city ofce, your household waste
disposal service or the shop where you purchased this product. In countries
outside of the EU: If you wish to discard this product, contact your local authorities
and ask for the correct manner of disposal.
72
SPECIFICATIONS
Page 73

COMPLIANCE STATEMENTS
FCC Class B
This equipment has been tested and found to comply with the limits for a Class B
digital device, pursuant to Part 15 of Federal Communications Commission (FCC)
Rules. These limits are designed to provide reasonable protection against harmful
interference in a residential installation. This equipment generates, uses and can
radiate radio frequency energy and, if not installed and used in accordance with
the instructions, may cause harmful interference to radio communications. However,
there is no guarantee that interference will not occur in a particular installation. If
this equipment does cause harmful interference to radio or television reception,
which can be determined by turning the equipment off and on, the user is encouraged
to try to correct the interference by one or more of the following measures:
• Reorient or relocate the receiving antenna.
• Increase the separation between the equipment and the receiver.
• Connect the equipment to an outlet on a circuit different from the receiver.
• Consult the dealer or an experienced radio/TV technician for help.
FCC Radiation Exposure Statement
This equipment complies with FCC radiation exposure set forth for an uncontrolled
environment. To avoid the possibility of exceeding FCC radio frequency exposure
limits, human proximity to the antenna shall not be less than 20 cm (8 inches)
during normal operation. The antenna(s) used for this transmitter must not be
co-located or operating in conjunction with any other antenna or transmitter. The
equipment version marketed in the U.S. is restricted to usage of channels 1-11.
CE / R&TTE
This device complies with the requirements of R&TTE Directive 1999/5/EC.
The ETSI version of this device is intended for home and ofce use in Austria,
Belgium, Denmark, Finland, France, Germany, Greece, Ireland, Italy, Luxembourg,
the Netherlands, Portugal, Spain, Sweden and the United Kingdom, and is also
authorized for use in EFTA member states Iceland, Liechtenstein, Norway and
Switzerland.
73
Page 74

74
Page 75

INTELLINET NETWORK SOLUTIONS™ offers a complete line
of active and passive networking products.
Ask your local computer dealer for more information or visit
www.intellinet-network.com.
© IC INTRACOM. All rights reserved.
INTELLINET is a trademark of IC INTRACOM, registered in the U.S. and other countries.
 Loading...
Loading...