HP procurve switch 2600, procurve switch 2800, procurve switch 4100, procurve switch 6108 Access Security Manual
Page 1

hp procurve
switch 2600 series
switch 2800 series
switch 4100 series
switch 6108
access security guide
www.hp.com/go/hpprocurve
Page 2

Page 3
HP ProCurve
Switch 2600 Series
Switch 2800 Series
Switch 4100GL Series
Switch 6108
Access Security Guide
August 2003
Page 4
© Copyright 2001-2003 Hewlett-Packard Company, L..P. The information contained herein is subject to change without notice.
Publication Number
5990-6024
August 2003
Edition 1
Applicable Products
HP ProCurve Switch 2626 (J4900A)
HP ProCurve Switch 2650 (J4899A)
HP ProCurve Switch 2824 (J4903A)
HP ProCurve Switch 2848 (J4904A)
HP ProCurve Switch 4104GL (J4887A)
HP ProCurve Switch 4108GL (J4865A)
HP ProCurve Switch 6108 (J4902A)
Trademark Credits
Windows NT®, Windows®, and MS Windows® are US
registered trademarks of Microsoft Corporation.
Disclaimer
HEWLETT-PACKARD COMPANY MAKES NO WARRANTY
OF ANY KIND WITH REGARD TO THIS MATERIAL,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
WARRANTIES OF MERCHANTABILITY AND FITNESS
FOR A PARTICULAR PURPOSE. Hewlett-Packard shall not
be liable for errors contained herein or for incidental or
consequential damages in connection with the furnishing,
performance, or use of this material.
Hewlett-Packard Company shall not be liable for technical
or editorial errors or omissions contained herein. The
information is provided "as is" without warranty of any kind
and is subject to change without notice. The warranties for
Hewlett-Packard Company products are set forth in the
express limited warranty statements for such products.
Nothing herein should be construed as constituting an
additional warranty.
Hewlett-Packard assumes no responsibility for the use or
reliability of its software on equipment that is not furnished
by Hewlett-Packard.
Software Credits
SSH on HP ProCurve Switches is based on the OpenSSH
software toolkit. This product includes software developed
by the OpenSSH Project for use in the OpenSSH Toolkit. For
more information on OpenSSH, visit http://
www.openssh.com.
SSL on HP ProCurve Switches is based on the OpenSSL
software toolkit. This product includes software developed
by the OpenSSL Project for use in the OpenSSL Toolkit. For
more information on OpenSSL, visit
http://www.openssl.org.
This product includes cryptographic software written by
Eric Young (eay@cryptsoft.com)
This product includes software written by Tim Hudson
(tjh@cryptsoft.com)
Warranty
See the Customer Support/Warranty booklet included with
the product.
A copy of the specific warranty terms applicable to your
Hewlett-Packard products and replacement parts can be
obtained from your HP Sales and Service Office or
authorized dealer.
Hewlett-Packard Company€
8000 Foothills Boulevard, m/s 5551€
Roseville, California 95747-5551€
http://www.hp.com/go/hpprocurve
ii€
Page 5
Contents
1 Getting Started
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-1€
Introduction and Applicable Switches . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2€
About the Feature Descriptions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2€
Overview of Access Security Features . . . . . . . . . . . . . . . . . . . . . . . . . . 1-3€
Command Syntax Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5€
Simulating Display Output . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5€
Command Prompts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5€
Screen Simulations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-6€
Port Identity Convention for Examples . . . . . . . . . . . . . . . . . . . . . . . . . 1-6€
Related Publications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-6€
Getting Documentation From the Web . . . . . . . . . . . . . . . . . . . . . . . . . . 1-8€
Sources for More Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-9€
Need Only a Quick Start? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10€
To Set Up and Install the Switch in Your Network . . . . . . . . . . . . . . 1-10€
2 Configuring Username and Password Security
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-1€
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-2€
Configuring Local Password Security . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-4€
Menu: Setting Passwords . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-4€
CLI: Setting Passwords and Usernames . . . . . . . . . . . . . . . . . . . . . . . . . 2-5€
Web: Setting Passwords and Usernames . . . . . . . . . . . . . . . . . . . . . . . . 2-6€
iii
Page 6

3 TACACS+ Authentication
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-1€
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-2€
Terminology Used in TACACS Applications: . . . . . . . . . . . . . . . . . . . . 3-3€
General System Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-5€
General Authentication Setup Procedure . . . . . . . . . . . . . . . . . . . . . . . 3-5€
Configuring TACACS+ on the Switch . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-8€
BeforeYou Begin . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-8€
CLI Commands Described in this Section . . . . . . . . . . . . . . . . . . . . . . . 3-9€
Viewing the Switch’s Current Authentication Configuration . . . . . . . 3-9€
Viewing the Switch’s Current TACACS+ Server Contact €
Configuration
Configuring the Switch’s Authentication Methods . . . . . . . . . . . . . . . 3-11€
Configuring the Switch’s TACACS+ Server Access . . . . . . . . . . . . . . 3-15€
How Authentication Operates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-20€
General Authentication Process Using a TACACS+ Server . . . . . . . . 3-20€
Local Authentication Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22€
Using the Encryption Key . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-23€
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-10€
Controlling Web Browser Interface Access When Using
TACACS+ Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-24€
Messages Related to TACACS+ Operation . . . . . . . . . . . . . . . . . . . . . 3-25€
Operating Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-25€
4 RADIUS Authentication and Accounting
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-1€
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-2€
Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-3€
Switch Operating Rules for RADIUS . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-4€
General RADIUS Setup Procedure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-5€
iv
Page 7

Configuring the Switch for RADIUS Authentication . . . . . . . . . . . . . 4-6€
Outline of the Steps for Configuring RADIUS Authentication . . . . . . 4-6€
1. Configure Authentication for the Access Methods You Want €
RADIUS To Protect
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-8€
2. Configure the Switch To Access a RADIUS Server . . . . . . . . . . . . 4-10€
3. Configure the Switch’s Global RADIUS Parameters . . . . . . . . . . . 4-12€
Local Authentication Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-16€
Controlling Web Browser Interface Access When Using
RADIUS Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-17€
Configuring RADIUS Accounting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-17€
Operating Rules for RADIUS Accounting . . . . . . . . . . . . . . . . . . . . . . 4-19€
Steps for Configuring RADIUS Accounting . . . . . . . . . . . . . . . . . . . . . 4-19€
Viewing RADIUS Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-25€
General RADIUS Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-25€
RADIUS Authentication Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-27€
RADIUS Accounting Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-28€
Changing RADIUS-Server Access Order . . . . . . . . . . . . . . . . . . . . . . . 4-29€
Messages Related to RADIUS Operation . . . . . . . . . . . . . . . . . . . . . . . 4-31€
5 Configuring Secure Shell (SSH)
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-1€
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-2€
Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-4€
Prerequisite for Using SSH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-5€
Public Key Formats . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-5€
Steps for Configuring and Using SSH for Switch and Client
Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-6€
General Operating Rules and Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-8€
Configuring the Switch for SSH Operation . . . . . . . . . . . . . . . . . . . . . . 5-9€
1. Assigning a Local Login (Operator) and Enable (Manager) €
Password . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-9€
2. Generating the Switch’s Public and Private Key Pair . . . . . . . . . . 5-10€
3. Providing the Switch’s Public Key to Clients . . . . . . . . . . . . . . . . . . 5-12€
v
Page 8
4. Enabling SSH on the Switch and Anticipating SSH Client€
Contact Behavior . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-15€
5. Configuring the Switch for SSH Authentication . . . . . . . . . . . . . . . 5-18€
6. Use an SSH Client To Access the Switch . . . . . . . . . . . . . . . . . . . . . 5-21€
Further Information on SSH Client Public-Key Authentication . 5-21€
Messages Related to SSH Operation . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-27€
6 Configuring Secure Socket Layer (SSL)
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-1€
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-2€
Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-3€
Prerequisite for Using SSL . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-5€
Steps for Configuring and Using SSL for Switch and Client
Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-5€
General Operating Rules and Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-6€
Configuring the Switch for SSL Operation . . . . . . . . . . . . . . . . . . . . . . 6-7€
1. Assigning a Local Login (Operator) and Enable (Manager)€
Password
2. Generating the Switch’s Server Host Certificate . . . . . . . . . . . . . . . . 6-9€
3. Enabling SSL on the Switch and Anticipating SSL Browser€
Contact Behavior . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-17€
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-7€
vi
Common Errors in SSL setup . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-21€
7 Configuring Port-Based Access Control (802.1x)
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-1€
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-2€
Why Use Port-Based Access Control? . . . . . . . . . . . . . . . . . . . . . . . . . . 7-2€
General Features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-2€
How 802.1x Operates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-5€
Authenticator Operation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-5€
Switch-Port Supplicant Operation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-6€
Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-7€
General Operating Rules and Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-9€
Page 9

General Setup Procedure for Port-Based Access Control
(802.1x) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-11€
Do These Steps Before You Configure 802.1x Operation . . . . . . . . . 7-11€
Overview: Configuring 802.1x Authentication on the Switch . . . . . . 7-12€
Configuring Switch Ports as 802.1x Authenticators . . . . . . . . . . . . 7-14€
1. Enable 802.1x Authentication on Selected Ports . . . . . . . . . . . . . . 7-14€
3. Configure the 802.1x Authentication Method . . . . . . . . . . . . . . . . . 7-18€
4. Enter the RADIUS Host IP Address(es) . . . . . . . . . . . . . . . . . . . . . . 7-19€
5. Enable 802.1x Authentication on the Switch . . . . . . . . . . . . . . . . . . 7-19€
802.1x Open VLAN Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-20€
Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-20€
Use Models for 802.1x Open VLAN Modes . . . . . . . . . . . . . . . . . . . . . 7-21€
Operating Rules for Authorized-Client and Unauthorized-Client€
VLANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-24€
Setting Up and Configuring 802.1x Open VLAN Mode . . . . . . . . . . . . 7-26€
802.1x Open VLAN Operating Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-30€
Option For Authenticator Ports: Configure Port-Security To
Allow Only 802.1x Devices . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-31€
Configuring Switch Ports To Operate As Supplicants for 802.1x
Connections to Other Switches . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-33€
Displaying 802.1x Configuration, Statistics, and Counters . . . . . . 7-37€
Show Commands for Port-Access Authenticator . . . . . . . . . . . . . . . . 7-37€
Viewing 802.1x Open VLAN Mode Status . . . . . . . . . . . . . . . . . . . . . . . 7-39€
Show Commands for Port-Access Supplicant . . . . . . . . . . . . . . . . . . . 7-42€
How RADIUS/802.1x Authentication Affects VLAN Operation . . 7-43€
Messages Related to 802.1x Operation . . . . . . . . . . . . . . . . . . . . . . . . 7-47€
8 Configuring and Monitoring Port Security
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-1€
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-2€
Basic Operation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-2€
Blocking Unauthorized Traffic . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-3€
Trunk Group Exclusion . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-4€
Planning Port Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-5€
vii
Page 10

Port Security Command Options and Operation . . . . . . . . . . . . . . . . . 8-6€
Retention of Static MAC Addresses . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-10€
Displaying Current Port Security Settings . . . . . . . . . . . . . . . . . . . . . . 8-10€
Configuring Port Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-12€
Web: Displaying and Configuring Port Security Features . . . . . . . 8-17€
Reading Intrusion Alerts and Resetting Alert Flags . . . . . . . . . . . . 8-17€
Notice of Security Violations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-17€
How the Intrusion Log Operates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-18€
Keeping the Intrusion Log Current by Resetting Alert Flags . . . . . . . 8-19€
Using the Event Log To Find Intrusion Alerts . . . . . . . . . . . . . . . . . . . 8-24€
Web: Checking for Intrusions, Listing Intrusion Alerts, and €
Resetting Alert Flags
Operating Notes for Port Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-25€
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-24€
9 Traffic/Security Filters (HP ProCurve Switch 2824 and
2848)
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-1€
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-2€
Using Source-Port Filters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-4€
Operating Rules for Source-Port Filters . . . . . . . . . . . . . . . . . . . . . . . . . 9-4€
Configuring a Source-Port Filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-5€
Viewing a Source-Port Filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-7€
Filter Indexing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-8€
Editing a Source-Port Filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9-9€
10 Using Authorized IP Managers
Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-1€
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-2€
Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-3€
Access Levels . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-3€
viii
Page 11

Defining Authorized Management Stations . . . . . . . . . . . . . . . . . . . . 10-4€
Overview of IP Mask Operation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-4€
Menu: Viewing and Configuring IP Authorized Managers . . . . . . . . . 10-5€
CLI: Viewing and Configuring Authorized IP Managers . . . . . . . . . . . 10-6€
Web: Configuring IP Authorized Managers . . . . . . . . . . . . . . . . . . . . . 10-8€
Building IP Masks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-9€
Configuring One Station Per Authorized Manager IP Entry . . . . . . . 10-9€
Configuring Multiple Stations Per Authorized Manager IP Entry . . 10-10€
Additional Examples for Authorizing Multiple Stations . . . . . . . . . 10-12€
Operating Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10-12€
Index
ix
Page 12
— This page is intentionally unused. —
x€
Page 13

Getting Started€
Contents
Introduction and Applicable Switches . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2€
About the Feature Descriptions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2€
Overview of Access Security Features . . . . . . . . . . . . . . . . . . . . . . . . . . 1-3€
Command Syntax Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5€
Simulating Display Output . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5€
Command Prompts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5€
Screen Simulations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-6€
1
Port Identity Convention for Examples . . . . . . . . . . . . . . . . . . . . . . . . . 1-6€
Related Publications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-6€
Getting Documentation From the Web . . . . . . . . . . . . . . . . . . . . . . . . . . 1-8€
Sources for More Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-9€
Need Only a Quick Start? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10€
To Set Up and Install the Switch in Your Network . . . . . . . . . . . . . . 1-10€
1-1
Page 14

Getting Started
Introduction and Applicable Switches
Introduction and Applicable Switches
This guide describes how to use HP’s switch security features to protect
access to your HP ProCurveProCurve switch. This guide is intended for these
switch models:
■ HP ProCurve Switch 4100GL Series (4104GL, 4108GL)
■ HP ProCurve Switch 2800 Series (2824, 2848)
■ HP ProCurve Switch 2600 Series (2626, 2650)
■ HP ProCurve Switch 6108
The Product Documentation CD-ROM shipped with the switch includes this
guide. You can also download the latest version from the HP ProCurve
website. (Refer to
About the Feature Descriptions
“Getting Documentation From the Web” on page 1-8.)
In cases where a software feature is not available in all of the switch products
covered by this guide, the text specifically indicates which devices offer the
feature.
1-2
Page 15

Getting Started
Overview of Access Security Features
Overview of Access Security Features
■ Local Manager and Operator Passwords (page 2-1): Control
access and privileges for the CLI, menu, and web browser interfaces.
■ TACACS+ Authentication (page 3-1): Uses an authentication appli
cation on a server to allow or deny access to a switch.
■ RADIUS Authentication and Accounting (page 4-1): Like
TACACS+, uses an authentication application on a central server to
allow or deny access to the switch. RADIUS also provides accounting
services for sending data about user activity and system events to a
RADIUS server.
■ Secure Shell (SSH) Authentication (page 5-1): Provides
encrypted paths for remote access to switch management functions.
■ Secure Socket Layer (SSL) (page 6-1): Provides remote web access
to the switch via encrypted authentication paths between the switch
and management station clients capable of SSL/TLS operation.
■ Port-Based Access Control (802.1x) (page 7-1): On point-to-point
connections, enables the switch to allow or deny traffic between a
port and an 802.1x-aware device (supplicant) attempting to access the
switch. Also enables the switch to operate as a supplicant for connec
tions to other 802.1x-aware switches.
■ Port Security (page 8-1): Enables a switch port to maintain a unique
list of MAC addresses defining which specific devices are allowed to
access the network through that port. Also enables a port to detect,
prevent, and log access attempts by unauthorized devices.
■ Traffic/Security Filters (page 9-1 ): Source-Port filtering enhances
in-band security by enabling outbound destination ports on the switch
to forward or drop traffic from designated source ports (within the
same VLAN).
■ Authorized IP Managers (page 10-1): Allows access to the switch
by a networked device having an IP address previously configured in
the switch as "authorized".
HP recommends that you use local passwords together with your switch’s
other security features to provide a more comprehensive security fabric than
if you use only local passwords. For an overview, refer to
Table 1-1.
1-3
Page 16
Getting Started
Overview of Access Security Features
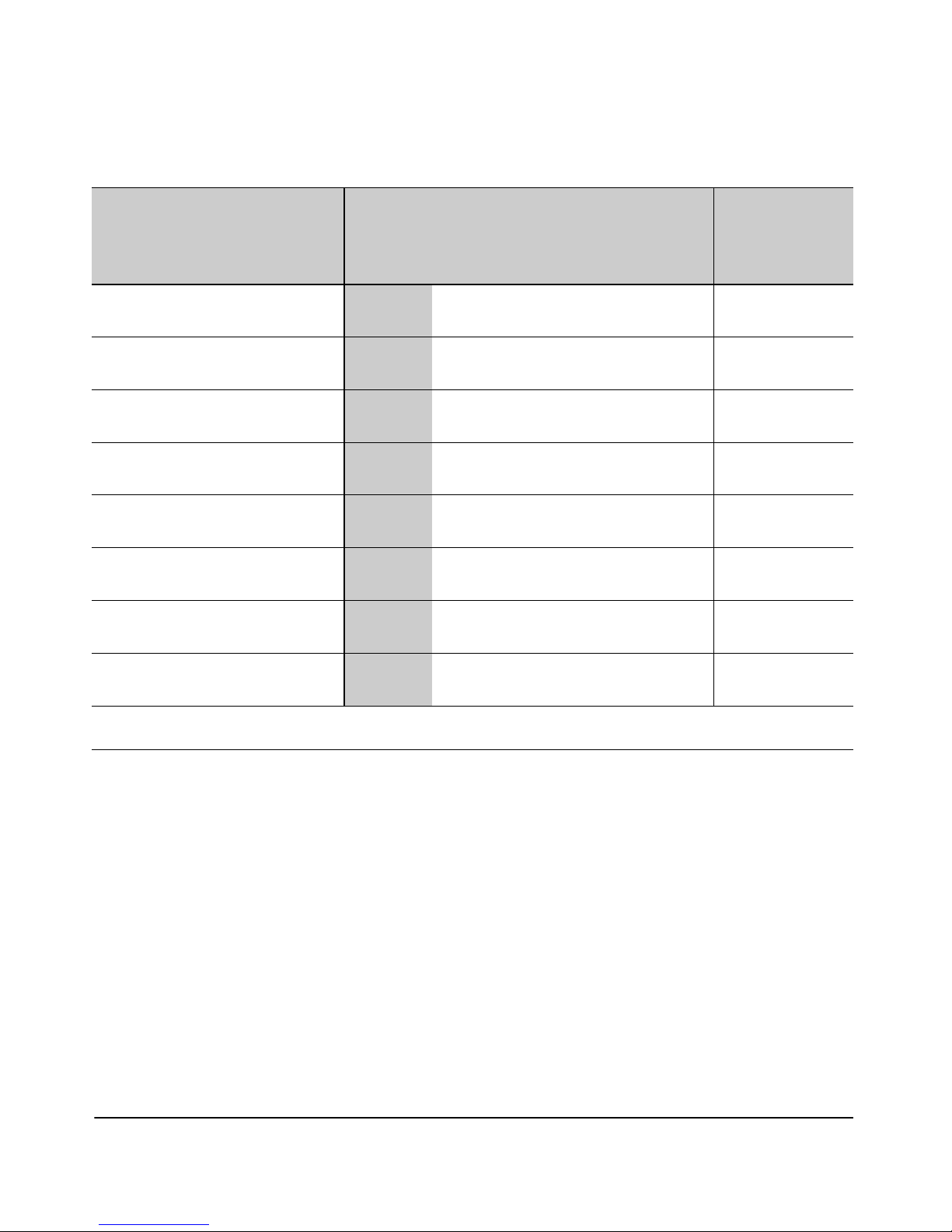
Table 1-1. Management Access Security Protection
Security Feature Offers Protection Against Unauthorized Client Access to
Local Manager and Operator
Usernames and Passwords
TACACS+
1
1
Switch Management Features
Connection Telnet SNMP
(Net Mgmt)
Web
Browser
SSH
Client
PtP: Yes No Yes Yes No
Remote: Yes No Yes Yes No
PtP: Yes No No Yes No
Offers Protection
Against
Unauthorized Client
Access to the
Network
Remote: Yes No No Yes No
RADIUS
1
PtP: Yes No No Yes No
Remote: Yes No No Yes No
SSH
Ptp: Yes No No Yes No
Remote: Yes No No Yes No
SSL
Ptp: No No Yes No No
Remote: No No Yes No No
Port-Based Access Control (802.1x)
PtP: Yes Yes Yes Yes Ye s
Remote: No No No No No
Port Security (MAC address)
PtP: Yes Yes Yes Yes Ye s
Remote: Yes Yes Yes Yes Ye s
Authorized IP Managers
PtP: Yes Yes Yes Yes No
Remote: Yes Yes Yes Yes No
1
The local Manager/Operator, TACACS+, and RADIUS options (direct connect or modem access) also offer protection
for serial port access.
There are two security areas to protect: access to the switch management
features and access to the network through the switch. The preceeding table
shows the type of protection each switch security feature offers.
1-4
Page 17

Getting Started
Command Syntax Conventions
Command Syntax Conventions
This guide uses the following conventions for command syntax and displays.
Syntax: aaa port-access authenticator < port-list >
[ control < authorized | auto | unauthorized >]
■ Vertical bars ( | ) separate alternative, mutually exclusive elements.
■ Square brackets ( [ ] ) indicate optional elements.
■ Braces ( < > ) enclose required elements.
■ Braces within square brackets ( [ < > ] ) indicate a required element
within an optional choice.
■ Boldface indicates use of a CLI command, part of a CLI command
syntax, or other displayed element in general text. For example:
“Use the copy tftp command to download the key from a TFTP server.”
■ Italics indicate variables for which you must supply a value when
executing the command. For example, in this command syntax, you
must provide one or more port numbers:
Syntax: aaa port-access authenticator < port-list >
Simulating Display Output
Command Prompts
In the default configuration, your switch’s CLI prompt includes the switch
model number, and appears similar to the following examples:
HP ProCurve Switch 4108#
HP ProCurve Switch 2650#
HP ProCurve Switch 6108#
To simplify recognition, this guide uses HPswitch to represent command
prompts for all models. That is:
HPswitch#
(You can use the hostname command to change the text in the CLI prompt.)
Commands or command output positioned to simulate displays of switch
information in a computer screen are printed in a monospace font, as shown
above.
1-5
Page 18

Getting Started
Port Identity Convention for Examples
Screen Simulations
Figures containing simulated screen text and command output appear similar
to this:
Figure 1-1.Example of a Figure Showing a Simulated Screen
In some cases, brief command-output sequences appear without figure iden
tification. For example:
HPswitch(config)# clear public-key
HPswitch(config)# show ip client-public-key
show_client_public_key: cannot stat keyfile
Port Identity Convention for Examples
This guide describes software applicable to both chassis-based and stackable
HP ProCurve switches. Where port identities are needed in an example, this
guide uses the chassis-based port identity system, such as "A1", "B3 - B5", "C7",
etc. However, unless otherwise noted, such examples apply equally to the
stackable switches, which typically use only numbers, such as "1", "3-5", "15",
etc. for port identities.
Related Publications
Product Notes and General Software Update Information. The
printed Read Me First shipped with your switch provides software update
information, product notes, and other information. For the latest version, refer
to
“Getting Documentation From the Web” on page 1-8.
Physical Installation and Initial Network Access. Use the Installation
and Getting Started Guide shipped with your switch to prepare for and
perform the physical installation. This guide also steps you through connect
ing the switch to your network and assigning IP addressing, as well as
describing the LED indications for correct operation and trouble analysis. A
1-6
Page 19

Getting Started
Related Publications
PDF version of this guide is also provided on the Product Documentation CDROM shipped with the switch. And you can download a copy from the HP
ProCurve website. (See
“Getting Documentation From the Web” on page 1-8.)
General Switch Management and Configuration. Use the Management
and Configuration Guide for information on:
■ Using the command line interface (CLI), Menu interface, and web
browser interface
■ Learning the operation and configuration of all switch software
features other than the access security features included in this guide
■ Troubleshooting software operation
HP provides a PDF version of this guide on the Product Documentation CDROM shipped with the switch. You can also download the latest copy from the
HP ProCurve website. (See
“Getting Documentation From the Web” on page
1-8.)
Release Notes. Release notes are posted on the HP ProCurve website and
provide information on new software updates:
■ New features and how to configure and use them
■ Software management, including downloading software to the switch
■ Software fixes addressed in current and previous releases
To view and download a copy of the latest release notes for your switch, see
“Getting Documentation From the Web” on page 1-8.
1-7
Page 20
Getting Started
Getting Documentation From the Web
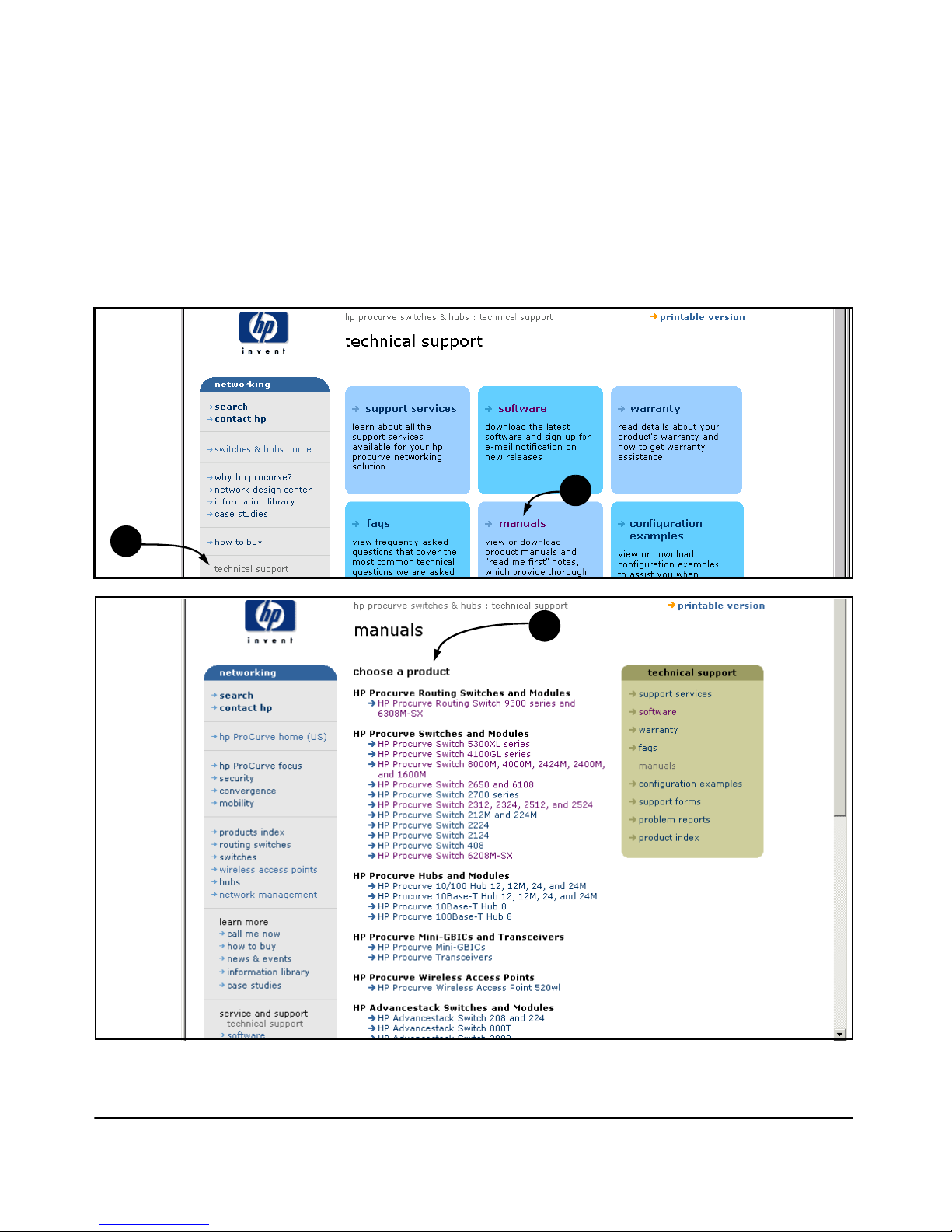
Getting Documentation From the Web
1. Go to the HP ProCurve website at http://www.hp.com/go/hpprocurve.
2. Click on technical support.
3. Click on manuals.
4. Click on the product for which you want to view or download a manual.
2
3
4
1-8
Page 21
Getting Started
Sources for More Information
Sources for More Information
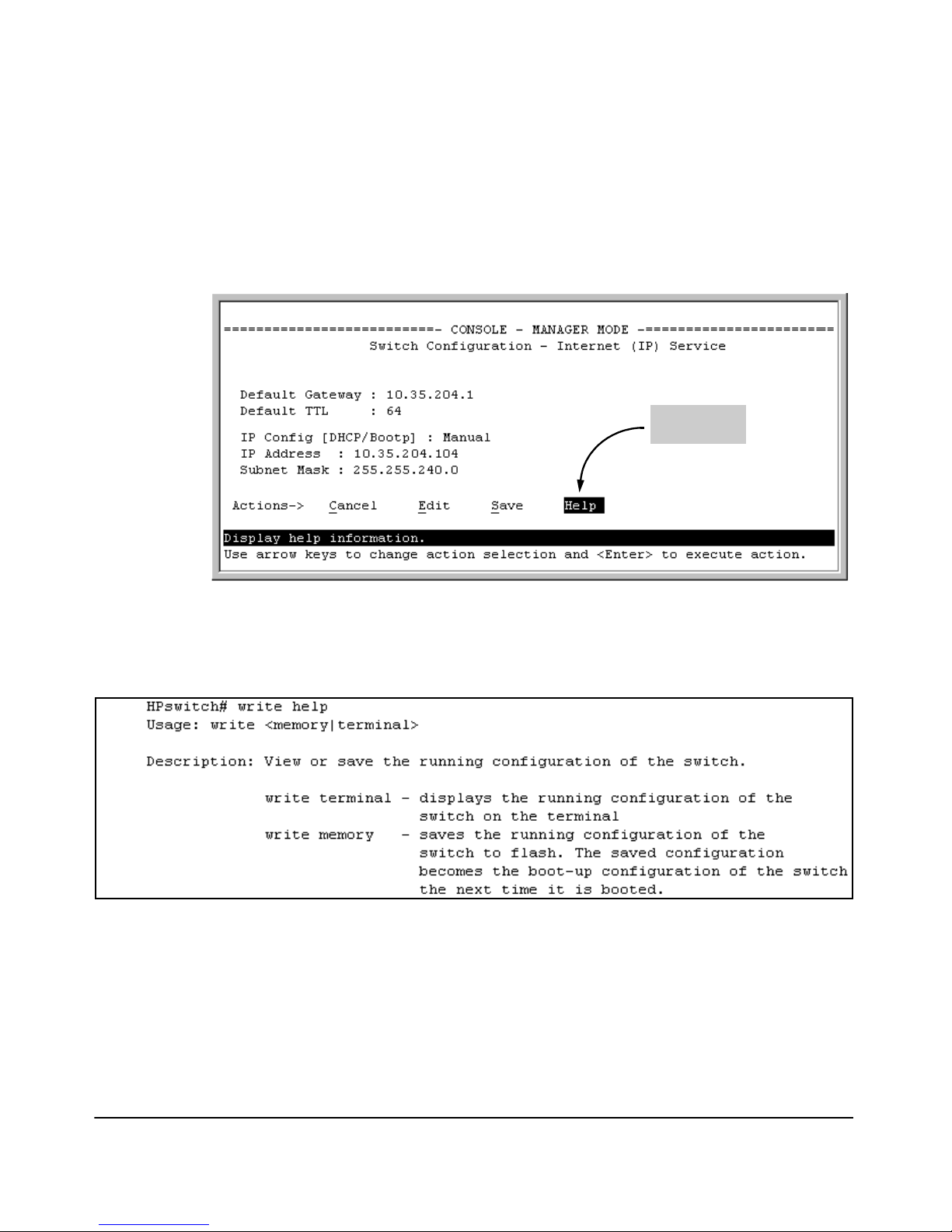
■ If you need information on specific parameters in the menu interface,
refer to the online help provided in the interface.
Online Help
for Menu
Figure 1-2. Where To Find Help in the Menu Interface
■ If you need information on a specific command in the CLI, type the
command name followed by “help”. For example:
Figure 1-3. How To Find Help in the CLI
■ If you need information on specific features in the HP Web Browser
Interface (hereafter referred to as the “web browser interface”), use
the online help available for the web browser interface. For more
information on web browser Help options, refer to the Management
and Configuration Guide for your switch.
1-9
Page 22

Getting Started
Need Only a Quick Start?
■ If you need further information on Hewlett-Packard switch tech
nology, visit the HP ProCurve website at:
http://www.hp.com/go/hpprocurve
Need Only a Quick Start?
IP Addressing. If you just want to give the switch an IP address, or if you
are not using VLANs, HP recommends that you use the Switch Setup screen
to quickly configure IP addressing. To do so, do one of the following:
■ Enter setup at the CLI Manager level prompt.
HPswitch# setup
■ In the Main Menu of the Menu interface, select
8. Run Setup
For more on using the Switch Setup screen, refer to the Installation and
Getting Started Guide you received with the switch.
To Set Up and Install the Switch in Your
Network
Use the Installation and Getting Started Guide for your switch model
(shipped with the switch) for the following:
■ Notes, cautions, and warnings related to installing and using the
switch and its related modules
■ Instructions for physically installing the switch in your network
■ Quickly assigning an IP address and subnet mask, set a Manager
password, and (optionally) configure other basic features.
1-10
Page 23

Configuring Username and Password Security
Contents
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-2€
Configuring Local Password Security . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-4€
Menu: Setting Passwords . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-4€
CLI: Setting Passwords and Usernames . . . . . . . . . . . . . . . . . . . . . . . . . 2-5€
Web: Setting Passwords and Usernames . . . . . . . . . . . . . . . . . . . . . . . . 2-6€
2
2-1
Page 24
Configuring Username and Password Security
Overview
Overview€
Feature Default Menu CLI Web
Set Usernames no user names set — — page 2-6
Set a Password no passwords set page 2-4 page 2-5 page 2-6
Delete Password n/a page 2-4 page 2-6 page 2-6
Protection
Console access includes both the menu interface and the CLI. There are two
levels of console access: Manager and Operator. For security, you can set a
password pair (username and password) on each of these levels.
Note Usernames are optional. Also, in the menu interface, you can configure
passwords, but not usernames. To configure usernames, use the CLI or the
web browser interface.
Level Actions Permitted
Manager: Access to all console interface areas.
This is the default level. That is, if a Manager password has not been set prior
to starting the current console session, then anyone having access to the
console can access any area of the console interface.
Operator: Access to the Status and Counters menu, the Event Log, and the CLI*, but no
Configuration capabilities.
On the Operator level, the configuration menus, Download OS, and Reboot
Switch options in the Main Menu are not available.
*Allows use of the ping, link-test, show, menu, exit, and logout commands, plus the enable
command if you can provide the Manager password.
To configure password security:
1. Set a Manager password pair (and an Operator password pair, if applicable
for your system).
2. Exit from the current console session. A Manager password pair will now
be needed for full access to the console.
2-2
Page 25
Configuring Username and Password Security
Overview
If you do steps 1 and 2, above, then the next time a console session is started€
for either the menu interface or the CLI, a prompt appears for a password.€
Assuming you have protected both the Manager and Operator levels, the level€
of access to the console interface will be determined by which password is €
entered in response to the prompt.€
If you set a Manager password, you may also want to configure the €
Inactivity Time parameter. (Refer to the Management and Configuration
Guide for your switch.) This causes the console session to end after the €
specified period of inactivity, thus giving you added security against unautho€
rized console access.€
Note The manager and operator passwords and (optional) usernames control
access to the menu interface, CLI, and web browser interface.
If you configure only a Manager password (with no Operator password), and
in a later session the Manager password is not entered correctly in response
to a prompt from the switch, then the switch does not allow management
access for that session.
If the switch has a password for both the Manager and Operator levels, and
neither is entered correctly in response to the switch’s password prompt, then
the switch does not allow management access for that session.
Passwords are case-sensitive.
Caution If the switch has neither a Manager nor an Operator password, anyone
having access to the switch through either Telnet, the serial port, or the web
browser interface can access the switch with full manager privileges. Also,
if you configure only an Operator password, entering the Operator password enables full manager privileges.
The rest of this section covers how to:
■ Set passwords
■ Delete passwords
■ Recover from a lost password
2-3
Page 26

Configuring Username and Password Security
Configuring Local Password Security
Configuring Local Password Security
Menu: Setting Passwords
As noted earlier in this section, usernames are optional. Configuring a username requires either the CLI or the web browser interface.
1. From the Main Menu select:
3. Console Passwords
Figure 2-1. The Set Password Screen
2. To set a new password:
a. Select Set Manager Password or Set Operator Password. You will then
be prompted with Enter new password.
b. Type a password of up to 16 ASCII characters with no spaces and
press
[Enter]. (Remember that passwords are case-sensitive.)
c. When prompted with Enter new password again, retype the new pass-
word and press
After you configure a password, if you subsequently start a new console
session, you will be prompted to enter the password. (If you use the CLI or
web browser interface to configure an optional username, the switch will
prompt you for the username, and then the password.)
To Delete Password Protection (Including Recovery from a Lost
Password): This procedure deletes all usernames (if configured) and pass-
words (Manager and Operator).
[Enter].
2-4
Page 27
Configuring Username and Password Security
Configuring Local Password Security
If you have physical access to the switch, press and hold the Clear button (on
the front of the switch) for a minimum of one second to clear all password
protection, then enter new passwords as described earlier in this chapter.
If you do not have physical access to the switch, you will need Manager-Level
access:
1. Enter the console at the Manager level.
2. Go to the Set Passwords screen as described above.
3. Select Delete Password Protection. You will then see the following prompt:
Continue Deletion of password protection? No
4. Press the Space bar to select Ye s, then press
5. Press
[Enter] to clear the Password Protection message.
[Enter].
To Recover from a Lost Manager Password: If you cannot start a console session at the Manager level because of a lost Manager password, you
can clear the password by getting physical access to the switch and pressing
and holding the Clear button for a minimum of one second. This action deletes
all passwords and usernames (Manager and Operator) used by both the
console and the web browser interface.
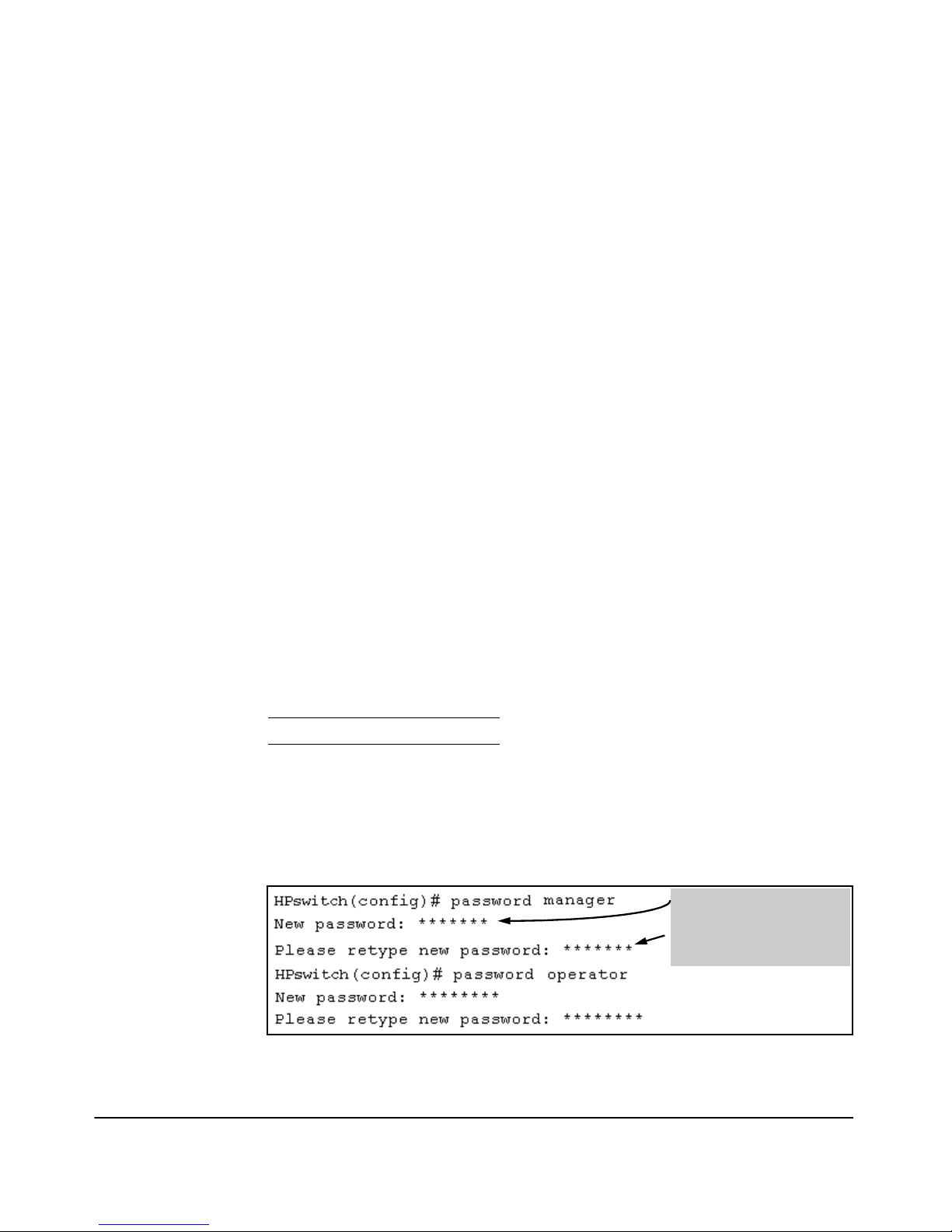
CLI: Setting Passwords and Usernames
Commands Used in This Section
password See below.
Configuring Manager and Operator Passwords.
Syntax:
[ no ] password <manager | operator > [ user-name ASCII-STR ]
[ no ] password < all >
Figure 2-2. Example of Configuring Manager and Operator Passwords
• Password entries appear
as asterisks.
• You must type the
password entry twice.
2-5
Page 28

Configuring Username and Password Security
Configuring Local Password Security
To Remove Password Protection. Removing password protection means
to eliminate password security. This command prompts you to verify that you
want to remove one or both passwords, then clears the indicated password(s).
(This command also clears the username associated with a password you are
removing.) For example, to remove the Operator password (and username, if
assigned) from the switch, you would do the following:
Press [Y] (for yes) and press [Enter].
Figure 2-3. Removing a Password and Associated Username from the Switch
The effect of executing the command in figure 2-3 is to remove password
protection from the Operator level. (This means that anyone who can access
the switch console can gain Operator access without having to enter a username or password.)
Web: Setting Passwords and Usernames
In the web browser interface you can enter passwords and (optional) usernames.
To Configure (or Remove) Usernames and Passwords in the Web
Browser Interface.
1. Click on the Security tab.
Click on
2. Do one of the following:
3. Implement the usernames and passwords by clicking on
To access the web-based help provided for the switch, click on
browser screen.
[Device Passwords].
• To set username and password protection, enter the usernames and
passwords you want in the appropriate fields.
• To remove username and password protection, leave the fields blank.
[Apply Changes].
[?] in the web
2-6
Page 29

TACACS+ Authentication
Contents
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-2€
Terminology Used in TACACS Applications . . . . . . . . . . . . . . . . . . . . . 3-3€
General System Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-5€
General Authentication Setup Procedure . . . . . . . . . . . . . . . . . . . . . . . 3-5€
Configuring TACACS+ on the Switch . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-8€
BeforeYou Begin . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-8€
CLI Commands Described in this Section . . . . . . . . . . . . . . . . . . . . . . . 3-9€
Viewing the Switch’s Current Authentication Configuration . . . . . . . 3-9€
Viewing the Switch’s Current TACACS+ Server Contact €
Configuration
Configuring the Switch’s Authentication Methods . . . . . . . . . . . . . . . 3-11€
Configuring the Switch’s TACACS+ Server Access . . . . . . . . . . . . . . 3-15€
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-10€
3
How Authentication Operates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-20€
General Authentication Process Using a TACACS+ Server . . . . . . . . 3-20€
Local Authentication Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22€
Using the Encryption Key . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-23€
Controlling Web Browser Interface Access When Using
TACACS+ Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-24€
Messages Related to TACACS+ Operation . . . . . . . . . . . . . . . . . . . . . 3-25€
Operating Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-25€
3-1
Page 30
TACACS+ Authentication
Overview
Overview€
Feature Default Menu CLI Web
view the switch’s authentication configuration n/a — page 3-9 —
view the switch’s TACACS+ server contact n/a — page —
configuration 3-10
configure the switch’s authentication methods disabled — page
3-11
configure the switch to contact TACACS+ server(s) disabled — page
3-15
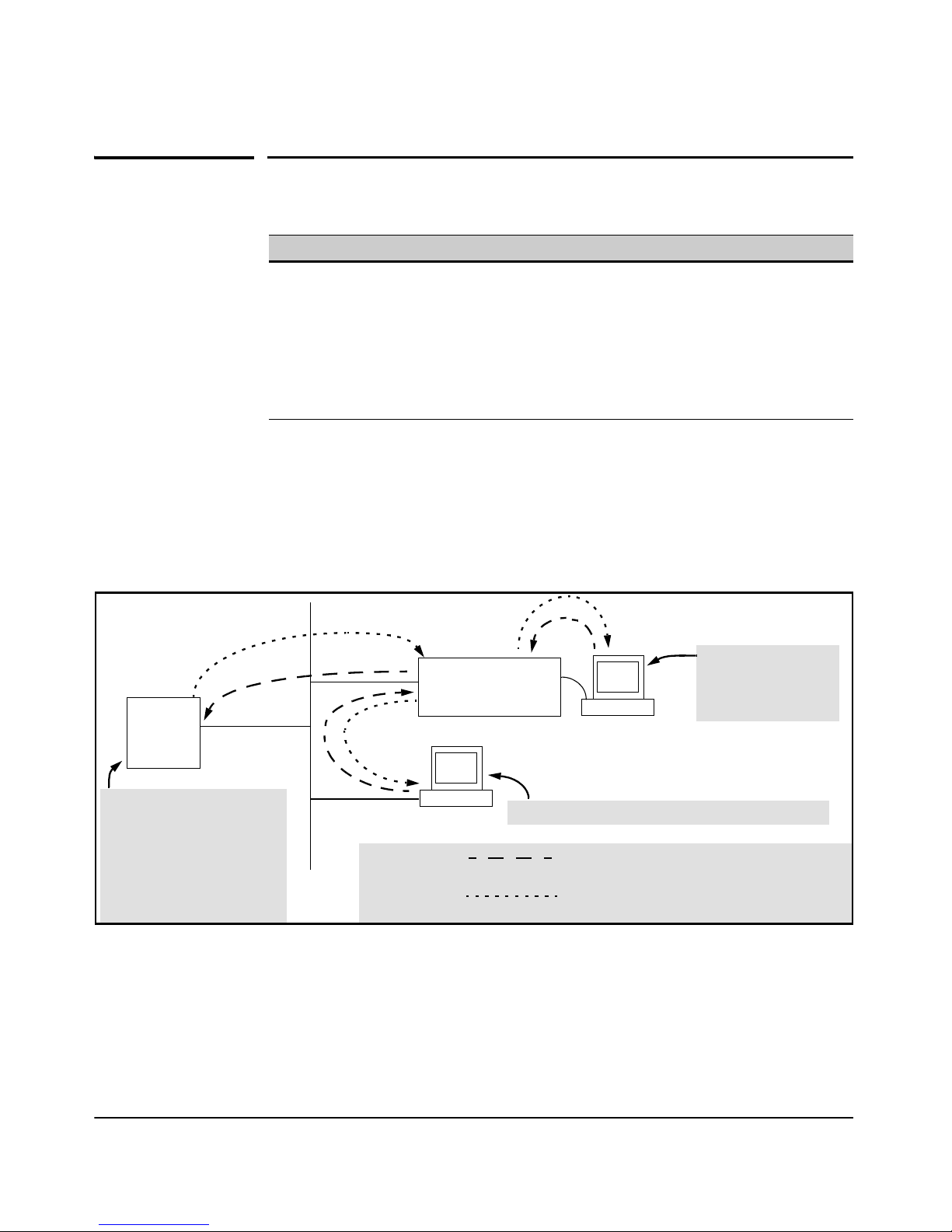
TACACS+ authentication enables you to use a central server to allow or deny
access to the switch (and other TACACS-aware devices) in your network. This
means that you can use a central database to create multiple unique username/
password sets with associated privilege levels for use by individuals who have
reason to access the switch from either the switch’s console port (local
access) or Telnet (remote access).
—
—
A3 or
B3
A2 or
Primary
TA CACS+
Server
B2
B4
B1
The switch passes the login
requests from terminals A and B
to the TACACS+ server for
authentication. The TACACS+
server determines whether to
allow access to the switch and
what privilege level to allow for
a given access request.
Access Request A1 - A4: Path for Request from
TACACS Server B1 - B4: Path for Request from
Response Terminal B (Through Telnet)
Figure 3-1. Example of TACACS+ Operation
TACACS+ in the switch manages authentication of logon attempts through
either the Console port or Telnet. TACACS+ uses an authentication hierarchy
consisting of (1) remote passwords assigned in a TACACS+ server and (2)
local passwords configured on the switch. That is, with TACACS+ configured,
the switch first tries to contact a designated TACACS+ server for authentica-
HP ProCurve Switch
Configured for
TACACS+ Operation
B
Terminal “B” Remotely Accessing The Switch Via Telnet
A1
A4
A
Terminal “A” Directly
Accessing the Switch
Via Switch’s Console
Port
Terminal A (Through Console Port)
3-2
Page 31

TACACS+ Authentication
Terminology Used in TACACS Applications:
tion services. If the switch fails to connect to any TACACS+ server, it defaults
to its own locally assigned passwords for authentication control if it has been
configured to do so. For both Console and Telnet access you can configure a
login (read-only) and an enable (read/write) privilege level access.
Notes The software does not support TACACS+ authorization or accounting
services.
TACACS+ does not affect web browser interface access. See “Controlling Web
Browser Interface Access” on page
3-24.
Terminology Used in TACACS
Applications:
■ NAS (Network Access Server): This is an industry term for a
TACACS-aware device that communicates with a TACACS server for
authentication services. Some other terms you may see in literature
describing TACACS operation are communication server, remote
access server, or terminal server. These terms apply when TACACS+
is enabled on the switch (that is, when the switch is TACACS-aware).
■ TACACS+ Server: The server or management station configured as
an access control server for TACACS-enabled devices. To use
TACACS+ with the switch and any other TACACS-capable devices in
your network, you must purchase, install, and configure a TACACS+
server application on a networked server or management station in
the network. The TACACS+ server application you install will provide
various options for access control and access notifications. For more
on the TACACS+ services available to you, see the documentation
provided with the TACACS+ server application you will use.
■ Authentication: The process for granting user access to a device
through entry of a user name and password and comparison of this
username/password pair with previously stored username/password
data. Authentication also grants levels of access, depending on the
privileges assigned to a user name and password pair by a system
administrator.
3-3
Page 32

TACACS+ Authentication
Terminology Used in TACACS Applications:
• Local Authentication: This method uses username/password
pairs configured locally on the switch; one pair each for managerlevel and operator-level access to the switch. You can assign local
usernames and passwords through the CLI or web browser interface. (Using the menu interface you can assign a local password,
but not a username.) Because this method assigns passwords to
the switch instead of to individuals who access the switch, you
must distribute the password information on each switch to
everyone who needs to access the switch, and you must configure
and manage password protection on a per-switch basis. (For
more on local authentication, refer to
and Password Security” on page 2-1.)
• TACACS+ Authentication: This method enables you to use a
TACACS+ server in your network to assign a unique password,
user name, and privilege level to each individual or group who
needs access to one or more switches or other TACACS-aware
devices. This allows you to administer primary authentication
from a central server, and to do so with more options than you
have when using only local authentication. (You will still need to
use local authentication as a backup if your TACACS+ servers
become unavailable.) This means, for example, that you can use
a central TACACS+ server to grant, change, or deny access to a
specific individual on a specific switch instead of having to
change local user name and password assignments on the switch
itself, and then have to notify other users of the change.
“Configuring Username
3-4
Page 33

TACACS+ Authentication
General System Requirements
General System Requirements
To use TACACS+ authentication, you need the following:
■ A TACACS+ server application installed and configured on one or
more servers or management stations in your network. (There are
several TACACS+ software packages available.)
■ A switch configured for TACACS+ authentication, with access to one
or more TACACS+ servers.
Notes The effectiveness of TACACS+ security depends on correctly using your
TACACS+ server application. For this reason, HP recommends that you
thoroughly test all TACACS+ configurations used in your network.
TACACS-aware HP switches include the capability of configuring multiple
backup TACACS+ servers. HP recommends that you use a TACACS+ server
application that supports a redundant backup installation. This allows you to
configure the switch to use a backup TACACS+ server if it loses access to the
first-choice TACACS+ server.
TACACS+ does not affect web browser interface access. Refer to “Controlling
Web Browser Interface Access When Using TACACS+ Authentication” on
page 3-24.
General Authentication Setup Procedure
It is important to test the TACACS+ service before fully implementing it.
Depending on the process and parameter settings you use to set up and test
TACACS+ authentication in your network, you could accidentally lock all
users, including yourself, out of access to a switch. While recovery is simple,
it may pose an inconvenience that can be avoided.To prevent an unintentional
lockout on a switch, use a procedure that configures and tests TACACS+
protection for one access type (for example, Telnet access), while keeping the
3-5
Page 34

TACACS+ Authentication
General Authentication Setup Procedure
other access type (console, in this case) open in case the Telnet access fails
due to a configuration problem. The following procedure outlines a general
setup procedure.
Note If a complete access lockout occurs on the switch as a result of a TACACS+
configuration, see “Troubleshooting TACACS+ Operation” in the Troubleshooting chapter of the Management and Configuration Guide for your
switch.
1. Familiarize yourself with the requirements for configuring your
TACACS+ server application to respond to requests from a switch. (Refer
to the documentation provided with the TACACS+ server software.) This
includes knowing whether you need to configure an encryption key. (See
“Using the Encryption Key” on page 3-23.)
2. Determine the following:
• The IP address(es) of the TACACS+
server(s) you want the switch to use
for authentication. If you will use
more than one server, determine
which server is your first-choice for
authentication services.
• The encryption key, if any, for
allowing the switch to communicate
with the server. You can use either a
global key or a server-specific key,
depending on the encryption
configuration in the TACACS+
server(s).
• The number of log-in attempts you
will allow before closing a log-in
session. (Default: 3)
• The period you want the switch to
wait for a reply to an authentication
request before trying another
server.
• The username/password pairs you
want the TACACS+ server to use for
controlling access to the switch.
• The privilege level you want for
each username/password pair
administered by the TACACS+
server for controlling access to the
switch.
• The username/password pairs you
want to use for local authentication
(one pair each for Operator and
Manager levels).
3. Plan and enter the TACACS+ server configuration needed to support
TACACS+ operation for Telnet access (login and enable) to the switch.
This includes the username/password sets for logging in at the Operator
(read-only) privilege level and the sets for logging in at the Manager (read/
write) privilege level.
3-6
Page 35

TACACS+ Authentication
General Authentication Setup Procedure
Note on
Privilege Levels
When a TACACS+ server authenticates an access request from a switch,
it includes a privilege level code for the switch to use in determining which
privilege level to grant to the terminal requesting access. The switch
interprets a privilege level code of “15” as authorization for the Manager
(read/write) privilege level access. Privilege level codes of 14 and lower
result in Operator (read-only) access. Thus, when configuring the
TACACS+ server response to a request that includes a username/pass
word pair that should have Manager privileges, you must use a privilege
level of 15. For more on this topic, refer to the documentation you received
with your TACACS+ server application.
If you are a first-time user of the TACACS+ service, HP recommends that
you configure only the minimum feature set required by the TACACS+
application to provide service in your network environment. After you
have success with the minimum feature set, you may then want to try
additional features that the application offers.
4. Ensure that the switch has the correct local username and password for
Manager access. (If the switch cannot find any designated TACACS+
servers, the local manager and operator username/password pairs are
always used as the secondary access control method.)
Caution
You should ensure that the switch has a local Manager password. Otherwise, if authentication through a TACACS+ server fails for any reason,
then unauthorized access will be available through the console port or
Telnet.
5. Using a terminal device connected to the switch’s console port, configure
the switch for TACACS+ authentication only for telnet login access and
telnet enable access. At this stage, do not configure TACACS+ authenti
cation for console access to the switch, as you may need to use the
console for access if the configuration for the Telnet method needs
debugging.
6. Ensure that the switch is configured to operate on your network and can
communicate with your first-choice TACACS+ server. (At a minimum,
this requires IP addressing and a successful ping test from the switch to
the server.)
7. On a remote terminal device, use Telnet to attempt to access the switch.
If the attempt fails, use the console access to check the TACACS+
configuration on the switch. If you make changes in the switch configu
ration, check Telnet access again. If Telnet access still fails, check the
3-7
Page 36

TACACS+ Authentication
Configuring TACACS+ on the Switch
configuration in your TACACS+ server application for mis-configura
tions or missing data that could affect the server’s interoperation with
the switch.
8. After your testing shows that Telnet access using the TACACS+ server is
working properly, configure your TACACS+ server application for
console access. Then test the console access. If access problems occur,
check for and correct any problems in the switch configuration, and then
test console access again. If problems persist, check your TACACS+
server application for mis-configurations or missing data that could
affect the console access.
9. When you are confident that TACACS+ access through both Telnet and
the switch’s console operates properly, use the write memory command
to save the switch’s running-config file to flash memory.
Configuring TACACS+ on the Switch
BeforeYou Begin
If you are new to TACACS+ authentication, HP recommends that you read the
“General Authentication Setup Procedure” on page 3-5 and configure your
TACACS+ server(s) before configuring authentication on the switch.
The switch offers three command areas for TACACS+ operation:
■ show authentication and show tacacs: Displays the switch’s TACACS+
configuration and status.
■ aaa authentication: A command for configuring the switch’s authenti
cation methods
■ tacacs-server: A command for configuring the switch’s contact with
TACACS+ servers
3-8
Page 37

TACACS+ Authentication
Configuring TACACS+ on the Switch
CLI Commands Described in this Section
Command Page
show authentication
show tacacs
aaa authentication
console-
Telnet-
num-attempts <1-10 >-
tacacs-server
host < ip-addr >
key
timeout < 1-255 >
3-9
3-10
pages 3-11 through 3-14
pages 3-15 -
pages 3-15 -
3-19-
3-20-
Viewing the Switch’s Current Authentication
Configuration
This command lists the number of login attempts the switch allows in a single
login session, and the primary/secondary access methods configured for each
type of access.
Syntax:
show authentication
This example shows the default authentication configuration.
Figure 3-2. Example Listing of the Switch’s Authentication Configuration
Configuration for login and enable access
to the switch through the switch console
port.
Configuration for login and enable access
to the switch through Telnet.
3-9
Page 38

TACACS+ Authentication
Configuring TACACS+ on the Switch
Viewing the Switch’s Current TACACS+ Server Contact
Configuration
This command lists the timeout period, encryption key, and the IP addresses
of the first-choice and backup TACACS+ servers the switch can contact.
Syntax: show tacacs
For example, if the switch was configured for a first-choice and two backup
TACACS+ server addresses, the default timeout period, and paris-1 for a
(global) encryption key, show tacacs would produce a listing similar to the
following:
First-Choice
TACACS+ Server
Second-Choice
TACACS+ Server
Third-Choice
TACACS+ Server
Figure 3-3. Example of the Switch’s TACACS+ Configuration Listing
3-10
Page 39

TACACS+ Authentication
Configuring TACACS+ on the Switch
Configuring the Switch’s Authentication Methods
The aaa authentication command configures the access control for console
port and Telnet access to the switch. That is, for both access methods, aaa
authentication specifies whether to use a TACACS+ server or the switch’s local
authentication, or (for some secondary scenarios) no authentication (meaning
that if the primary method fails, authentication is denied). This command also
reconfigures the number of access attempts to allow in a session if the first
attempt uses an incorrect username/password pair.
Syntax: aaa authentication
< console | telnet >
Selects either console (serial port) or Telnet access for
configuration.
< enable | login >
Selects either the Manager (enable) or Operator (login)
access level.
< local | tacacs | radius >
Selects the type of security access:
local — Authenticates with the Manager and Operator
password you configure in the switch.
tacacs — Authenticates with a password and other
data configured on a TACACS+ server.
radius — Authenticates with a password and other
data configured on a RADIUS server. (Refer to
“RADIUS Authentication and Accounting” on page
4-1.)
[< local | none >]
If the primary authentication method fails, determines
whether to use the local password as a secondary method
or to disallow access.
aaa authentication num-attempts < 1-10 >
Specifies the maximum number of login attempts allowed in
the current session. Default: 3
3-11
Page 40

TACACS+ Authentication
Configuring TACACS+ on the Switch
Table 3-1. AAA Authentication Parameters
Name Default Range Function
console n/a n/a Specifies whether the command is configuring authentication for the console port
- or - or Telnet access method for the switch.
telnet
enable
- or login
local local n/a Specifies the primary method of authentication for the access method being
- or - configured.
tacacs local: Use the username/password pair configured locally in the switch for
local
- or -
none
num-attempts 3 1 - 10 In a given session, specifies how many tries at entering the correct username/
n/a n/a Specifies the privilege level for the access method being configured.
login: Operator (read-only) privileges
enable: Manager (read-write) privileges
the privilege level being configured
tacacs: Use a TACACS+ server.
none n/a Specifies the secondary (backup) type of authentication being configured.
local: The username/password pair configured locally in the switch for the
privilege level being configured
none: No secondary type of authentication for the specified
method/privilege path. (Available only if the primary method of
authentication for the access being configured is local.)
Note: If you do not specify this parameter in the command line, the switch
automatically assigns the secondary method as follows:
• If the primary method is
• If the primary method is
password pair are allowed before access is denied and the session terminated.
tacacs, the only secondary method is local.
local, the default secondary method is none.
3-12
As shown in the next table, login and enable access is always available locally
through a direct terminal connection to the switch’s console port. However,
for Telnet access, you can configure TACACS+ to deny access if a TACACS+
server goes down or otherwise becomes unavailable to the switch.
Page 41

Table 3-2. Primary/Secondary Authentication Table
TACACS+ Authentication
Configuring TACACS+ on the Switch
Access Method and
Privilege Level
Console — Login local none* Local username/password access only.
Console — Enable local none* Local username/password access only.
Telnet — Login local none* Local username/password access only.
Telnet — Enable local none* Local username/password access only.
*When “local” is the primary option, you can also select “local” as the secondary option. However, in this case, a
secondary “local” is meaningless because the switch has only one local level of username/password protection.
Authentication Options Effect on Access Attempts
Primary Secondary
tacacs local If Tacacs+ server unavailable, uses local username/password access.
tacacs local If Tacacs+ server unavailable, uses local username/password access.
tacacs local If Tacacs+ server unavailable, uses local username/password access.
tacacs none If Tacacs+ server unavailable, denies access.
tacacs local If Tacacs+ server unavailable, uses local username/password access.
tacacs none If Tacacs+ server unavailable, denies access.
Caution Regarding
the Use of Local for
Login Primary
Access
During local authentication (which uses passwords configured in the switch
instead of in a TACACS+ server), the switch grants read-only access if you
enter the Operator password, and read-write access if you enter the Manager
password. For example, if you configure authentication on the switch with
Telnet Login Primary as Local and Telnet Enable Primary as Tacacs, when you
attempt to Telnet to the switch, you will be prompted for a local password. If
you enter the switch’s local Manager password (or, if there is no local Manager
password configured in the switch) you can bypass the TACACS+ server
authentication for Telnet Enable Primary and go directly to read-write (Man
ager) access. Thus, for either the Telnet or console access method, configuring
Login Primary for Local authentication while configuring Enable Primary for
TACACS+ authentication is not recommended, as it defeats the purpose of
using the TACACS+ authentication. If you want Enable Primary log-in
attempts to go to a TACACS+ server, then you should configure both Login
Primary and Enable Primary for Tacacs authentication instead of configuring
Login Primary to Local authentication.
3-13
Page 42

TACACS+ Authentication
Configuring TACACS+ on the Switch
For example, here is a set of access options and the corresponding commands
to configure them:
Console Login (Operator or Read-Only) Access: Primary using TACACS+ server.
Secondary using Local.
HPswitch (config)# aaa authentication console login tacacs local
Console Enable (Manager or Read/Write) Access: Primary using TACACS+ server.
Secondary using Local.
HPswitch (config)# aaa authentication console enable tacacs local
Telnet Login (Operator or Read-Only) Access: Primary using TACACS+ server.
Secondary using Local.
HPswitch (config)# aaa authentication Telnet login tacacs local
Telnet Enable (Manager or Read/Write Access: Primary using TACACS+ server.
Secondary using Local.
HPswitch (config)# aaa authentication telnet enable tacacs local
Deny Access and Close the Session After Failure of Two Consecutive Username/Password Pairs:
HPswitch (config)# aaa authentication num-attempts 2
3-14
Page 43

TACACS+ Authentication
Configuring TACACS+ on the Switch
Configuring the Switch’s TACACS+ Server Access
The tacacs-server command configures these parameters:
■ The host IP address(es) for up to three TACACS+ servers; one first-
choice and up to two backups. Designating backup servers provides
for a continuation of authentication services in case the switch is
unable to contact the first-choice server.
■ An optional encryption key. This key helps to improve security, and
must match the encryption key used in your TACACS+ server appli
cation. In some applications, the term “secret key” or “secret” may be
used instead of “encryption key”. If you need only one encryption key
for the switch to use in all attempts to authenticate through a
TACACS+ server, configure a global key. However, if the switch is
configured to access multiple TACACS+ servers having different
encryption keys, you can configure the switch to use different encryp
tion keys for different TACACS+ servers.
■ The timeout value in seconds for attempts to contact a TACACS+
server. If the switch sends an authentication request, but does not
receive a response within the period specified by the timeout value,
the switch resends the request to the next server in its Server IP Addr
list, if any. If the switch still fails to receive a response from any
TACACS+ server, it reverts to whatever secondary authentication
method was configured using the aaa authentication command (local
or none; see
page 3-11.)
“Configuring the Switch’s Authentication Methods” on
Note As described under “General Authentication Setup Procedure” on page 3-5,
HP recommends that you configure, test, and troubleshoot authentication via
Telnet access before you configure authentication via console port access.
This helps to prevent accidentally locking yourself out of switch access due
to errors or problems in setting up authentication in either the switch or your
TACACS+ server.
3-15
Page 44

TACACS+ Authentication
Configuring TACACS+ on the Switch
Note on
Encryption Keys
Syntax: tacacs-server host < ip-addr >
Adds a TACACS+ server and optionally assigns a server-specific
encryption key
[no] tacacs-server host < ip-addr >
Removes a TACACS+ server assignment (including its serverspecific encryption key, if any).
tacacs-server key <key-string>
Enters the optional global encryption key.
[no] tacacs-server key
Removes the optional global encryption key. (Does not affect any
server-specific encryption key assignments.)
tacacs-server timeout < 1-255 >
Changes the wait period for a TACACS server response. (Default:
5 seconds.)
.
[key < key-string >]
Encryption keys configured in the switch must exactly match the encryption
keys configured in TACACS+ servers the switch will attempt to use for
authentication.
If you configure a global encryption key, the switch uses it only with servers
for which you have not also configured a server-specific key. Thus, a global
key is more useful where the TACACS+ servers you are using all have an
identical key, and server-specific keys are necessary where different
TACACS+ servers have different keys.
If TACACS+ server “X” does not have an encryption key assigned for the
switch, then configuring either a global encryption key or a server-specific key
in the switch for server “X” will block authentication support from server “X”.
3-16
Page 45
TACACS+ Authentication
Configuring TACACS+ on the Switch
Table 3-3. Details on Configuring TACACS Servers and Keys
Name Default Range
tacacs-server host <ip-addr> none n/a
This command specifies the IP address of a device running a TACACS+ server application. Optionally, it can also specify
the unique, per-server encryption key to use when each assigned server has its own, unique key. For more on the
encryption key, see “Using the Encryption Key” on page 3-23 and the documentation provided with your TACACS+ server
application.
You can enter up to three IP addresses; one first-choice and two (optional) backups (one second-choice and one thirdchoice).
Use show tacacs to view the current IP address list.
If the first-choice TACACS+ server fails to respond to a request, the switch tries the second address, if any, in the show
tacacs list. If the second address also fails, then the switch tries the third address, if any.
(See figure 3-3, “Example of the Switch’s TACACS+ Configuration Listing” on 3-10.)
The priority (first-choice, second-choice, and third-choice) of a TACACS+ server in the switch’s TACACS+ configuration
depends on the order in which you enter the server IP addresses:
1.When there are no TACACS+ servers configured, entering a server IP address makes that server the first-choice
TACACS+ server.
2.When there is one TACACS+ serves already configured, entering another server IP address makes that server the
second-choice (backup) TACACS+ server.
3.When there are two TACACS+ servers already configured, entering another server IP address makes that server
the third-choice (backup) TACACS+ server.
• The above position assignments are fixed. Thus, if you remove one server and replace it with another, the new server
assumes the priority position that the removed server had. For example, suppose you configured three servers, A, B,
and C, configured in order:
First-Choice:A
Second-Choice:B
Third-Choice: C
• If you removed server B and then entered server X, the TACACS+ server order of priority would be:
First-Choice:A
Second-Choice:X
Third-Choice: C
• If there are two or more vacant slots in the TACACS+ server priority list and you enter a new IP address, the new
address will take the vacant slot with the highest priority. Thus, if A, B, and C are configured as above and you (1)
remove A and B, and (2) enter X and Y (in that order), then the new TACACS+ server priority list would be X, Y, and C.
• The easiest way to change the order of the TACACS+ servers in the priority list is to remove all server addresses in
the list and then re-enter them in order, with the new first-choice server address first, and so on.
To add a new address to the list when there are already three addresses present, you must first remove one of the currently
listed addresses.
See also “General Authentication Process Using a TACACS+ Server” on page 3-20.
3-17
Page 46

TACACS+ Authentication
Configuring TACACS+ on the Switch
Name Default Range
[ key <key-string> ] none (null) n/a
Specifies the optional, global “encryption key” that is also assigned in the TACACS+ server(s) that the switch will access
for authentication. This option is subordinate to any “per-server” encryption keys you assign, and applies only to
accessing TACACS+ servers for which you have not given the switch a “per-server” key. (See the host <ip-addr> [key
<key-string> entry at the beginning of this table.)
For more on the encryption key, see “Using the Encryption Key” on page 3-23 and the documentation provided with your
TACACS+ server application.
timeout <1 - 255> 5 sec 1 - 255 sec
Specifies how long the switch waits for a TACACS+ server to respond to an authentication request. If the switch does
not detect a response within the timeout period, it initiates a new request to the next TACACS+ server in the list. If all
TACACS+ servers in the list fail to respond within the timeout period, the switch uses either local authentication (if
configured) or denies access (if none configured for local authentication).
Adding, Removing, or Changing the Priority of a TACACS+ Server.
Suppose that the switch was already configured to use TACACS+ servers at
10.28.227.10 and 10.28.227.15. In this case, 10.28.227.15 was entered first, and
so is listed as the first-choice server:
First-Choice TACACS+ Server
Figure 3-4. Example of the Switch with Two TACACS+ Server Addresses Configured
To move the “first-choice” status from the “15” server to the “10” server, use
the
no tacacs-server host <ip-addr> command to delete both servers, then use
tacacs-server host <ip-addr> to re-enter the “10” server first, then the “15” server.
The servers would then be listed with the new “first-choice” server, that is:
3-18
Page 47

TACACS+ Authentication
Configuring TACACS+ on the Switch
The “10” server is now the “first-choice” TACACS+ authentication device.
Figure 3-5. Example of the Switch After Assigning a Different “First-Choice” Server
To remove the 10.28.227.15 device as a TACACS+ server, you would use this
command:
HPswitch(config)# no tacacs-server host 10.28.227.15
Configuring an Encryption Key. Use an encryption key in the switch if the
switch will be requesting authentication from a TACACS+ server that also uses
an encryption key. (If the server expects a key, but the switch either does not
provide one, or provides an incorrect key, then the authentication attempt will
fail.) Use a global encryption key if the same key applies to all TACACS+
servers the switch may use for authentication attempts. Use a per-server
encryption key if different servers the switch may use will have different keys.
(For more details on encryption keys, see
“Using the Encryption Key” on page
3-23.)
To configure
north01 as a global encryption key:
HPswitch(config) tacacs-server key north01
To configure
north01 as a per-server encryption key:
HPswitch(config)# tacacs-server host 10.28.227.63 key
north01
An encryption key can contain up to 100 characters, without spaces, and is
likely to be case-sensitive in most TACACS+ server applications.
To delete a global encryption key from the switch, use this command:
HPswitch(config)# no tacacs-server key
3-19
Page 48

TACACS+ Authentication
How Authentication Operates
To delete a per-server encryption key in the switch, re-enter the tacacs-server
host command without the key parameter. For example, if you have
north01
configured as the encryption key for a TACACS+ server with an IP address of
10.28.227.104 and you want to eliminate the key, you would use this command:
HPswitch(config)# tacacs-server host 10.28.227.104
Note The show tacacs command lists the global encryption key, if configured.
However, to view any configured per-server encryption keys, you must use
show config or show config running (if you have made TACACS+ configuration
changes without executing
Configuring the Timeout Period. The timeout period specifies how long
the switch waits for a response to an authentication request from a TACACS+
server before either sending a new request to the next server in the switch’s
Server IP Address list or using the local authentication option. For example,
to change the timeout period from 5 seconds (the default) to 3 seconds:
HPswitch(config)# tacacs-server timeout 3
write mem).
First-Choice
TACACS+ Server
Second-Choice
TACACS+ Server
(Optional)
Third-Choice
TACACS+ Server
(Optional)
How Authentication Operates
General Authentication Process Using a TACACS+
Server
Authentication through a TACACS+ server operates generally as described
below. For specific operating details, refer to the documentation you received
with your TACACS+ server application.
Terminal “A” Directly Accessing This
Switch Via Switch’s Console Port
HP Switch
Configured for
TACACS+ Operation
HP Switch Configured
for TACACS+ Operation
A
Terminal “B” Remotely
Accessing This Switch Via Telnet
B
Figure 3-6. Using a TACACS+ Server for Authentication
3-20
Page 49

TACACS+ Authentication
How Authentication Operates
Using figure 3-6, above, after either switch detects an operator’s logon request
from a remote or directly connected terminal, the following events occur:
1. The switch queries the first-choice TACACS+ server for authentication
of the request.
• If the switch does not receive a response from the first-choice
TACACS+ server, it attempts to query a secondary server. If the
switch does not receive a response from any TACACS+ server,
then it uses its own local username/password pairs to authenti
cate the logon request. (See
“Local Authentication Process” on
page 3-22.)
• If a TACACS+ server recognizes the switch, it forwards a user-
name prompt to the requesting terminal via the switch.
2. When the requesting terminal responds to the prompt with a username,
the switch forwards it to the TACACS+ server.
3. After the server receives the username input, the requesting terminal
receives a password prompt from the server via the switch.
4. When the requesting terminal responds to the prompt with a password,
the switch forwards it to the TACACS+ server and one of the following
actions occurs:
• If the username/password pair received from the requesting
terminal matches a username/password pair previously stored in
the server, then the server passes access permission through the
switch to the terminal.
• If the username/password pair entered at the requesting terminal
does not match a username/password pair previously stored in
the server, access is denied. In this case, the terminal is again
prompted to enter a username and repeat steps
2 through 4. In
the default configuration, the switch allows up to three attempts
to authenticate a login session. If the requesting terminal
exhausts the attempt limit without a successful TACACS+
authentication, the login session is terminated and the operator
at the requesting terminal must initiate a new session before
trying again.
3-21
Page 50

TACACS+ Authentication
How Authentication Operates
Local Authentication Process
When the switch is configured to use TACACS+, it reverts to local authentica
tion only if one of these two conditions exists:
■ “Local” is the authentication option for the access method being used.
■ TACACS+ is the primary authentication mode for the access method
(For a listing of authentication options, see table 3-2, “Primary/Secondary
Authentication Table” on 3-13.)
For local authentication, the switch uses the operator-level and manager-level
username/password set(s) previously configured locally on the switch. (These
are the usernames and passwords you can configure using the CLI password
command, the web browser interface, or the menu interface—which enables
only local password configuration).
being used. However, the switch was unable to connect to any
TACACS+ servers (or no servers were configured) and Local is the
secondary authentication mode being used.
■ If the operator at the requesting terminal correctly enters the user-
name/password pair for either access level, access is granted.
■ If the username/password pair entered at the requesting terminal does
not match either username/password pair previously configured
locally in the switch, access is denied. In this case, the terminal is
again prompted to enter a username/password pair. In the default
configuration, the switch allows up to three attempts. If the requesting
terminal exhausts the attempt limit without a successful authentica
tion, the login session is terminated and the operator at the requesting
terminal must initiate a new session before trying again.
Note The switch’s menu allows you to configure only the local Operator and
Manager passwords, and not any usernames. In this case, all prompts for local
authentication will request only a local password. However, if you use the CLI
or the web browser interface to configure usernames for local access, you will
see a prompt for both a local username and a local password during local
authentication.
3-22
Page 51

TACACS+ Authentication
How Authentication Operates
Using the Encryption Key
General Operation
When used, the encryption key (sometimes termed “key”, “secret key”, or
“secret”) helps to prevent unauthorized intruders on the network from reading
username and password information in TACACS+ packets moving between
the switch and a TACACS+ server. At the TACACS+ server, a key may include
both of the following:
■ Global key: A general key assignment in the TACACS+ server appli
cation that applies to all TACACS-aware devices for which an indi
vidual key has not been configured.
■ Server-Specific key: A unique key assignment in the TACACS+
server application that applies to a specific TACACS-aware device.
Note Configure a key in the switch only if the TACACS+ server application has this
exact same key configured for the switch. That is, if the key parameter in
switch “X” does not exactly match the key setting for switch “X” in the
TACACS+ server application, then communication between the switch and
the TACACS+ server will fail.
Thus, on the TACACS+ server side, you have a choice as to how to implement
a key. On the switch side, it is necessary only to enter the key parameter so
that it exactly matches its counterpart in the server. For information on how
to configure a general or individual key in the TACACS+ server, refer to the
documentation you received with the application.
Encryption Options in the Switch
When configured, the encryption key causes the switch to encrypt the
TACACS+ packets it sends to the server. When left at “null”, the TACACS+
packets are sent in clear text. The encryption key (or just “key”) you configure
in the switch must be identical to the encryption key configured in the
corresponding TACACS+ server. If the key is the same for all TACACS+
servers the switch will use for authentication, then configure a global key in
the switch. If the key is different for one or more of these servers, use “serverspecific” keys in the switch. (If you configure both a global key and one or
more per-server keys, the per-server keys will override the global key for the
specified servers.)
3-23
Page 52

TACACS+ Authentication
Controlling Web Browser Interface Access When Using TACACS+ Authentication
For example, you would use the next command to configure a global encryp
tion key in the switch to match a key entered as
TACACS+ servers. (That is, both servers use the same key for your switch.)
Note that you do not need the server IP addresses to configure a global key in
the switch:
HPswitch(config)# tacacs-server key north40campus
Suppose that you subsequently add a third TACACS+ server (with an IP
address of 10.28.227.87) that has
this key is different than the one used for the two servers in the previous
example, you will need to assign a server-specific key in the switch that applies
only to the designated server:
HPswitch(config)# tacacs-server host 10.28.227.87 key
south10campus
south10campus for an encryption key. Because
north40campus in two target
With both of the above keys configured in the switch, the
overrides the
TACACS+ server having the 10.28.227.87 address.
north40campus key only when the switch tries to access the
south10campus key
Controlling Web Browser Interface
Access When Using TACACS+
Authentication
Configuring the switch for TACACS+ authentication does not affect web
browser interface access. To prevent unauthorized access through the web
browser interface, do one or more of the following:
■ Configure local authentication (a Manager user name and password
and, optionally, an Operator user name and password) on the switch.
■ Configure the switch’s Authorized IP Manager feature to allow web
browser access only from authorized management stations. (The
Authorized IP Manager feature does not interfere with TACACS+
operation.)
■ Disable web browser access to the switch by going to the System
Information screen in the Menu interface and configuring the
Agent Enabled
3-24
Web
parameter to No.
Page 53

TACACS+ Authentication
Messages Related to TACACS+ Operation
Messages Related to TACACS+
Operation
The switch generates the CLI messages listed below. However, you may see
other messages generated in your TACACS+ server application. For informa
tion on such messages, refer to the documentation you received with the
application.
CLI Message Meaning
Connecting to Tacacs server The switch is attempting to contact the TACACS+ server identified in the switch’s tacacs-
server
Connecting to secondary The switch was not able to contact the first-choice TACACS+ server, and is now
Tacacs server attempting to contact the next (secondary) TACACS+ server identified in the switch’s
tacacs-server configuration.
configuration as the first-choice (or only) TACACS+ server.
Invalid password The system does not recognize the username or the password or both. Depending on the
authentication method (tacacs or local), either the TACACS+ server application did not
recognize the username/password pair or the username/password pair did not match the
username/password pair configured in the switch.
No Tacacs servers The switch has not been able to contact any designated TACACS+ servers. If this message
is followed by the Username prompt, the switch is attempting local authentication.responding
Not legal combination of
authentication methods
Record already exists When resulting from a
For console access, if you select tacacs as the primary authentication method, you must
select local as the secondary authentication method. This prevents you from being locked
out of the switch if all designated TACACS+ servers are inaccessible to the switch.
tacacs-server host <ip addr> command, indicates an attempt to
enter a duplicate TACACS+ server IP address.
Operating Notes
■ If you configure Authorized IP Managers on the switch, it is not
necessary to include any devices used as TACACS+ servers in the
authorized manager list. That is, authentication traffic between a
TACACS+ server and the switch is not subject to Authorized IP
Manager controls configured on the switch. Also, the switch does not
attempt TACACS+ authentication for a management station that the
Authorized IP Manager list excludes because, independent of
TACACS+, the switch already denies access to such stations.
3-25
Page 54

TACACS+ Authentication
Operating Notes
■ When TACACS+ is not enabled on the switch—or when the switch’s
only designated TACACS+ servers are not accessible— setting a local
Operator password without also setting a local Manager password
does not protect the switch from manager-level access by unautho
rized persons.)
3-26
Page 55

RADIUS Authentication and Accounting
Contents
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-2€
Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-3€
Switch Operating Rules for RADIUS . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-4€
General RADIUS Setup Procedure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-5€
Configuring the Switch for RADIUS Authentication . . . . . . . . . . . . . 4-6€
Outline of the Steps for Configuring RADIUS Authentication . . . . . . 4-6€
1. Configure Authentication for the Access Methods You Want €
RADIUS To Protect . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-8€
2. Configure the Switch To Access a RADIUS Server . . . . . . . . . . . . 4-10€
3. Configure the Switch’s Global RADIUS Parameters . . . . . . . . . . . 4-12€
4
Local Authentication Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-16€
Controlling Web Browser Interface Access When Using
RADIUS Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-17€
Configuring RADIUS Accounting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-17€
Operating Rules for RADIUS Accounting . . . . . . . . . . . . . . . . . . . . . . 4-19€
Steps for Configuring RADIUS Accounting . . . . . . . . . . . . . . . . . . . . . 4-19€
Viewing RADIUS Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-25€
General RADIUS Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-25€
RADIUS Authentication Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-27€
RADIUS Accounting Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-28€
Changing RADIUS-Server Access Order . . . . . . . . . . . . . . . . . . . . . . . 4-29€
Messages Related to RADIUS Operation . . . . . . . . . . . . . . . . . . . . . . . 4-31€
4-1
Page 56

RADIUS Authentication and Accounting
Overview
Overview€
Feature Default Menu CLI Web
Configuring RADIUS Authentication None n/a 4-6 n/a
Configuring RADIUS Accounting None n/a 4-17 n/a
Viewing RADIUS Statistics n/a n/a
RADIUS (Remote Authentication Dial-In User Service) enables you to use
up to three servers (one primary server and one or two backups) and maintain
separate authentication and accounting for each RADIUS server employed.
For authentication, this allows a different password for each user instead of
having to rely on maintaining and distributing switch-specific passwords to
all users. For accounting, this can help you track network resource usage.
4-25 n/a
Authentication. You can use RADIUS to verify user identity for the follow
ing types of primary password access to the HP switch:
■ Serial port (Console)
■ Telnet
■ SSH
■ Port-Access
Note The switch does not support RADIUS security for SNMP (network manage
ment) access or web browser interface access. For steps to block unautho
rized access through the web browser interface, see
Browser Interface Access When Using RADIUS Authentication” on page 4-17.
Accounting. RADIUS accounting on the switch collects resource consump
tion data and forwards it to the RADIUS server. This data can be used for trend
analysis, capacity planning, billing, auditing, and cost analysis.
“Controlling Web
4-2
Page 57

RADIUS Authentication and Accounting
Terminology
Terminology
CHAP (Challenge-Handshake Authentication Protocol): A challengeresponse authentication protocol that uses the Message Digest 5 (MD5)
hashing scheme to encrypt a response to a challenge from a RADIUS server.
EAP (Extensible Authentication Protocol): A general PPP authentication
protocol that supports multiple authentication mechanisms. A specific
authentication mechanism is known as an EAP type, such as MD5-Challenge,
Generic Token Card, and TLS (Transport Level Security).
Host: See RADIUS Server.
NAS (Network Access Server): In this case, an HP switch configured for
RADIUS security operation.
RADIUS (Remote Authentication Dial In User Service):
RADIUS Client: The device that passes user information to designated
RADIUS servers.
RADIUS Host: See RADIUS server.
RADIUS Server: A server running the RADIUS application you are using on
your network. This server receives user connection requests from the switch,
authenticates users, and then returns all necessary information to the switch.
For the HP switch, a RADIUS server can also perform accounting functions.
Sometimes termed a RADIUS host.
Shared Secret Key: A text value used for encrypting data in RADIUS packets.
Both the RADIUS client and the RADIUS server have a copy of the key, and
the key is never transmitted across the network.
4-3
Page 58
RADIUS Authentication and Accounting
Switch Operating Rules for RADIUS
Switch Operating Rules for RADIUS
■ You must have at least one RADIUS server accessible to the switch.
■ The switch supports authentication and accounting using up to three
RADIUS servers. The switch accesses the servers in the order in
which they are listed by show radius (page
not respond, the switch tries the next one, and so-on. (To change the
order in which the switch accesses RADIUS servers, refer to
“Changing RADIUS-Server Access Order” on page 4-29.)
■ You can select RADIUS as the primary authentication method for each
type of access. (Only one primary and one secondary access method
is allowed for each access type.)
■ In the HP switch, EAP RADIUS uses MD5 and TLS to encrypt a
response to a challenge from a RADIUS server.
4-25). If the first server does
4-4
Page 59

RADIUS Authentication and Accounting
General RADIUS Setup Procedure
General RADIUS Setup Procedure
Preparation:
1. Configure one to three RADIUS servers to support the switch. (That is,
one primary server and one or two backups.) Refer to the documentation
provided with the RADIUS server application.
2. Before configuring the switch, collect the information outlined below.
Table 4-1. Preparation for Configuring RADIUS on the Switch
• Determine the access methods (console, Telnet, Port-Access, and/or SSH) for which you want RADIUS as the primary
authentication method. Consider both Operator (login) and Manager (enable) levels, as well as which secondary
authentication methods to use (local or none) if the RADIUS authentication fails or does not respond.
Console access
requires Local as
secondary method to
prevent lockout if the
primary RADIUS
access fails due to loss
of RADIUS server
access or other
problems with the
server.
Figure 4-1. Example of Possible RADIUS Access Assignments
• Determine the IP address(es) of the RADIUS server(s) you want to support the switch. (You can configure the switch
for up to three RADIUS servers.)
• If you need to replace the default UDP destination port (1812) the switch uses for authentication requests to a specific
RADIUS server, select it before beginning the configuration process.
• If you need to replace the default UDP destination port (1813) the switch uses for accounting requests to a specific
Radius server, select it before beginning the configuration process.
• Determine whether you can use one, global encryption key for all RADIUS servers or if unique keys will be required
for specific servers. With multiple RADIUS servers, if one key applies to two or more of these servers, then you can
configure this key as the global encryption key. For any server whose key differs from the global key you are using,
you must configure that key in the same command that you use to designate that server’s IP address to the switch.
• Determine an acceptable timeout period for the switch to wait for a server to respond to a request. HP recommends
that you begin with the default (five seconds).
• Determine how many times you want the switch to try contacting a RADIUS server before trying another RADIUS
server or quitting. (This depends on how many RADIUS servers you have configured the switch to access.)
• Determine whether you want to bypass a RADIUS server that fails to respond to requests for service. To shorten
authentication time, you can set a bypass period in the range of 1 to 1440 minutes for non-responsive servers. This
requires that you have multiple RADIUS servers accessible for service requests.
4-5
Page 60

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
Configuring the Switch for RADIUS
Authentication
RADIUS Authentication Commands Page
aaa authentication 4-8
< console | telnet | ssh > < enable | login > radius 4-8
[no] radius-server host < IP-address > 4-10
[auth-port < port-number >] 4-10
[acct-port < port-number >] 4-10, 4-20
[key < server-specific key-string >] 4-10
[no] radius-server key < global key-string > 4-12
radius-server timeout < 1 - 15> 4-12
radius-server retransmit < 1 - 5 > 4-12
[no] radius-server dead-time < 1 - 1440 > 4-14
show radius 4-25
[< host < ip-address>] 4-25
show authentication 4-27
show radius authentication 4-27
< local | none > 4-8
Outline of the Steps for Configuring RADIUS
Authentication
There are three main steps to configuring RADIUS authentication:
1. Configure RADIUS authentication for controlling access through one or
more of the following
• Serial port
• Telnet
• SSH
• Port-Access (802.1x)
2. Configure the switch for accessing one or more RADIUS servers (one
primary server and up to two backup servers):
4-6
Page 61

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
Note This step assumes you have already configured the RADIUS server(s) to
support the switch. Refer to the documentation provided with the
RADIUS server documentation.)
• Server IP address
• (Optional) UDP destination port for authentication requests (default:
1812; recommended)
• (Optional) UDP destination port for accounting requests (default:
1813; recommended)
• (Optional) encryption key for use during authentication sessions with
a RADIUS server. This key overrides the global encryption key you
can also configure on the switch, and must match the encryption key
used on the specified RADIUS server. (Default: null)
3. Configure the global RADIUS parameters.
• Server Key: This key must match the encryption key used on the
RADIUS servers the switch contacts for authentication and account
ing services unless you configure one or more per-server keys.
(Default: null.)
• Timeout Period: The timeout period the switch waits for a RADIUS
server to reply. (Default: 5 seconds; range: 1 to 15 seconds.)
• Retransmit Attempts: The number of retries when there is no server
response to a RADIUS authentication request. (Default: 3; range of 1
to 5.)
• Server Dead-Time: The period during which the switch will not send
new authentication requests to a RADIUS server that has failed to
respond to a previous request. This avoids a wait for a request to time
out on a server that is unavailable. If you want to use this feature,
select a dead-time period of 1 to 1440 minutes. (Default: 0—disabled;
range: 1 - 1440 minutes.) If your first-choice server was initially
unavailable, but then becomes available before the dead-time expires,
you can nullify the dead-time by resetting it to zero and then trying to
log on again. As an alternative, you can reboot the switch, (thus
resetting the dead-time counter to assume the server is available) and
then try to log on again.
• Number of Login Attempts: This is actually an aaa authentication
command. It controls how many times in one session a RADIUS client
(as well as clients using other forms of access) can try to log in with
the correct username and password. (Default: Three times per ses
sion.)
(For RADIUS accounting features, refer to “Configuring RADIUS Accounting”
on page 4-17.)
4-7
Page 62

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
1. Configure Authentication for the Access Methods You
Want RADIUS To Protect
This section describes how to configure the switch for RADIUS authentication
through the following access methods:
■ Console: Either direct serial-port connection or modem connection.
■ Telnet: Inbound Telnet must be enabled (the default).
■ SSH: To employ RADIUS for SSH access, you must first configure the
switch for SSH operation. Refer to “Configuring Secure Shell (SSH)”
on page 5-1.
You can also use RADIUS for Port-Based Access authentication. Refer to
“Configuring Port-Based Access Control (802.1x)” on page 7-1.
You can configure RADIUS as the primary password authentication method
for the above access methods. You will also need to select either local or none
as a secondary, or backup, method. Note that for console access, if you
configure radius (or tacacs) for primary authentication, you must configure
local for the secondary method. This prevents the possibility of being com
pletely locked out of the switch in the event that all primary access methods
fail.
4-8
Syntax: aaa authentication < console | telnet | ssh > < enable | login > < radius >
Configures RADIUS as the primary password authentication
method for console, Telnet, and/or SSH. (The default primary
< enable | login > authentication is local.)
[< local | none >]
Provides options for secondary authentication
(default: none). Note that for console access, secondary
authentication must be local if primary access is not
local. This prevents you from being completely locked
out of the switch in the event of a failure in other access
methods.
Page 63

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
For example, suppose you have already configured local passwords on the
switch, but want to use RADIUS to protect primary Telnet and SSH access
without allowing a secondary Telnet or SSH access option (which would be
the switch’s local passwords):
The switch now
allows Telnet and
SSH authentication
only through
Figure 4-2. Example Configuration for RADIUS Authentication
Note In the above example, if you configure the Login Primary method as local
instead of radius (and local passwords are configured on the switch), then you
can gain access to either the Operator or Manager level without encountering
the RADIUS authentication specified for Enable Primary. Refer to
Authentication Process” on page 4-16.
“Local
4-9
Page 64

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
2. Configure the Switch To Access a RADIUS Server
This section describes how to configure the switch to interact with a RADIUS
server for both authentication and accounting services.
Note If you want to configure RADIUS accounting on the switch, go to page 4-17:
“Configuring RADIUS Accounting” instead of continuing here.
Syntax: [no] radius-server host < ip-address >
Adds a server to the RADIUS configuration or (with no)
deletes a server from the configuration. You can configure
up to three RADIUS server addresses. The switch uses the
first server it successfully accesses. (Refer to “Changing
the RADIUS Server Access Order” on page
[auth-port < port-number >]
4-29.)
Optional. Changes the UDP destination port for authenti
cation requests to the specified RADIUS server (host). If
you do not use this option with the radius-server host
command, the switch automatically assigns the default
authentication port number. The auth-port number must
match its server counterpart. (Default: 1812)
[acct-port < port-number >]
Optional. Changes the UDP destination port for account
ing requests to the specified RADIUS server. If you do not
use this option with the radius-server host command, the
switch automatically assigns the default accounting port
number. The acct-port number must match its server coun
terpart.(Default: 1813)
[key < key-string >]
Optional. Specifies an encryption key for use during
authentication (or accounting) sessions with the specified
server. This key must match the encryption key used on
the RADIUS server. Use this command only if the specified
server requires a different encryption key than configured
for the global encryption key.
4-10
no radius-server host < ip-address > key
Use the no form of the command to remove the key for a
specified server.
Page 65

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
For example, suppose you have configured the switch as shown in figure 4-3
and you now need to make the following changes:
1. Change the encryption key for the server at 10.33.18.127 to “source0127”.
2. Add a RADIUS server with an IP address of 10.33.18.119 and a serverspecific encryption key of “source0119”.
Figure 4-3. Sample Configuration for RADIUS Server Before Changing the Key and
Adding Another Server
To make the changes listed prior to figure 4-3, you would do the following:
Changes the key
for the existing
server to
“source0127”
Adds the new
RADIUS server
with its required
“source0119” key.
Lists the switch’s
new RADIUS
server
configuration.
Compare this with
Figure 4-4. Sample Configuration for RADIUS Server After Changing the Key and Adding Another Server
To change the order in which the switch accesses RADIUS servers, refer to
“Changing RADIUS-Server Access Order” on page 4-29.
4-11
Page 66

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
3. Configure the Switch’s Global RADIUS Parameters
You can configure the switch for the following global RADIUS parameters:
■ Number of login attempts: In a given session, specifies how many
tries at entering the correct username and password pair are allowed
before access is denied and the session terminated. (This is a general
aaa authentication parameter and is not specific to RADIUS.)
■ Global server key: The server key the switch will use for contacts
with all RADIUS servers for which there is not a server-specific key
configured by radius-server host < ip-address > key < key-string >. This
key is optional if you configure a server-specific key for each RADIUS
server entered in the switch. (Refer to
Access a RADIUS Server” on page 4-10.)
■ Server timeout: Defines the time period in seconds for authentica
tion attempts. If the timeout period expires before a response is
received, the attempt fails.
“2. Configure the Switch To
■ Server dead time: Specifies the time in minutes during which the
switch avoids requesting authentication from a server that has not
responded to previous requests.
■ Retransmit attempts: If the first attempt to contact a RADIUS
server fails, specifies how many retries you want the switch to attempt
on that server.
4-12
Page 67

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
Syntax: aaa authentication num-attempts < 1 - 10 >
Specifies how many tries for entering the correct username and password before shutting down the session
due to input errors. (Default: 3; Range: 1 - 10).
[no] radius-server
key < global-key-string >
Specifies the global encryption key the switch uses with
servers for which the switch does not have a serverspecific key assignment. This key is optional if all
RADIUS server addresses configured in the switch
include a server-specific encryption key. (Default:
Null.)
dead-time < 1 - 1440 >
Optional. Specifies the time in minutes during which
the switch will not attempt to use a RADIUS server that
has not responded to an earlier authentication attempt.
(Default: 0; Range: 1 - 1440 minutes)
radius-server timeout < 1 - 15 >
Specifies the maximum time the switch waits for a
response to an authentication request before counting
the attempt as a failure. (Default: 3 seconds; Range: 1
- 15 seconds)
radius-server retransmit < 1 - 5 >
If a RADIUS server fails to respond to an authentication request, specifies how many retries to attempt
before closing the session. Default: 3; Range: 1 - 5)
Note Where the switch has multiple RADIUS servers configured to support authen
tication requests, if the first server fails to respond, then the switch tries the
next server in the list, and so-on. If none of the servers respond, then the switch
attempts to use the secondary authentication method configured for the type
of access being attempted (console, Telnet, or SSH). If this occurs, refer to
“RADIUS-Related Problems” in the Troubleshooting chapter of the Manage
ment and Configuration Guide for your switch.
4-13
Page 68

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
For example, suppose that your switch is configured to use three RADIUS
servers for authenticating access through Telnet and SSH. Two of these servers
use the same encryption key. In this case your plan is to configure the switch
with the following global authentication parameters:
■ Allow only two tries to correctly enter username and password.
■ Use the global encryption key to support the two servers that use the
same key. (For this example, assume that you did not configure these
two servers with a server-specific key.)
■ Use a dead-time of five minutes for a server that fails to respond to
an authentication request.
■ Allow three seconds for request timeouts.
■ Allow two retries following a request that did not receive a response.
Figure 4-5. Example of Global Configuration Exercise for RADIUS Authentication
4-14
Page 69

RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
After two attempts failing due
to username or password
entry errors, the switch will
terminate the session.
Global RADIUS parameters
from figure 4-5.
Server-specific encryption key
for the RADIUS server that will
not use the global encryption
key.
Figure 4-6. Listings of Global RADIUS Parameters Configured In Figure 4-5
These two servers will use the
global encryption key.
4-15€
Page 70

RADIUS Authentication and Accounting
Local Authentication Process
Local Authentication Process
When the switch is configured to use RADIUS, it reverts to local authentication
only if one of these two conditions exists:
■ “Local” is the authentication option for the access method being used.
■ The switch has been configured to query one or more RADIUS servers
for a primary authentication request, but has not received a response,
and local is the configured secondary option.
For local authentication, the switch uses the Operator-level and Manager-level
username/password set(s) previously configured locally on the switch. (These
are the usernames and passwords you can configure using the CLI password
command, the web browser interface, or the menu interface—which enables
only local password configuration).
■ If the operator at the requesting terminal correctly enters the user-
name/password pair for either access level (Operator or Manager),
access is granted on the basis of which username/password pair was
used. For example, suppose you configure Telnet primary access for
RADIUS and Telnet secondary access for local. If a RADIUS access
attempt fails, then you can still get access to either the Operator or
Manager level of the switch by entering the correct username/pass
word pair for the level you want to enter.
■ If the username/password pair entered at the requesting terminal does
not match either local username/password pair previously configured
in the switch, access is denied. In this case, the terminal is again
prompted to enter a username/password pair. In the default configu
ration, the switch allows up to three attempts. If the requesting
terminal exhausts the attempt limit without a successful authentica
tion, the login session is terminated and the operator at the requesting
terminal must initiate a new session before trying again.
4-16
Page 71

RADIUS Authentication and Accounting
Controlling Web Browser Interface Access When Using RADIUS Authentication
Controlling Web Browser Interface
Access When Using RADIUS
Authentication
Configuring the switch for RADIUS authentication does not affect web
browser interface access. To prevent unauthorized access through the web
browser interface, do one or more of the following:
■ Configure local authentication (a Manager user name and password
and, optionally, an Operator user name and password) on the switch.
■ Configure the switch’s Authorized IP Manager feature to allow web
browser access only from authorized management stations. (The
Authorized IP Manager feature does not interfere with TACACS+
operation.)
■ Disable web browser access to the switch.
Configuring RADIUS Accounting€
RADIUS Accounting Commands Page
[no] radius-server host < ip-address > 4-20
[acct-port < port-number >] 4-20
[key < key-string >] 4-20
[no] aaa accounting < exec | network | system > 4-23
< start-stop | stop-only> radius
[no] aaa accounting update
periodic < 1 - 525600 > (in minutes)
[no] aaa accounting suppress null-username 4-24
show accounting 4-28
show accounting sessions 4-29
show radius accounting 4-28
4-24
4-17
Page 72

RADIUS Authentication and Accounting
Configuring RADIUS Accounting
Note This section assumes you have already:
■ Configured RADIUS authentication on the switch for one or more
access methods
■ Configured one or more RADIUS servers to support the switch
If you have not already done so, refer to “General RADIUS Setup Procedure”
on page 4-5 before continuing here.
RADIUS accounting collects data about user activity and system events and
sends it to a RADIUS server when specified events occur on the switch, such
as a logoff or a reboot. The switch supports three types of accounting services:
■ Network accounting: Provides records containing the information
listed below on clients directly connected to the switch and operating
under Port-Based Access Control (802.1x):
• Acct-Session-Id
• Acct-Status-Type
• Acct-Terminate-Cause
• Acct-Authentic
• Acct-Delay-Time
• Acct-Input-Packets
• Acct-Output-Packets
• Acct-Input-Octets
• Nas-Port
• Acct-Output-Octets
• Acct-Session-Time
• Username
• Service-Type
• NAS-IP-Address
• NAS-Identifier
• Called-Station-Id
(For 802.1x information for the switch, refer to “Configuring Port-Based
Access Control (802.1x)” on page 7-1.)
■ Exec accounting: Provides records holding the information listed
below about login sessions (console, Telnet, and SSH) on the switch:
• Acct-Session-Id
• Acct-Status-Type
• Acct-Terminate-Cause
• Acct-Authentic
■ System accounting: Provides records containing the information
• Acct-Delay-Time
• Acct-Session-Time
• Username
• Service-Type
• NAS-IP-Address
• NAS-Identifier
• Calling-Station-Id
listed below when system events occur on the switch, including
system reset, system boot, and enabling or disabling of system
accounting.
• Acct-Session-Id
• Acct-Status-Type
• Acct-Terminate-Cause
• Acct-Authentic
4-18
• Acct-Delay-Time
• Username
• Service-Type
• NAS-IP-Address
• NAS-Identifier
• Calling-Station-Id
Page 73

RADIUS Authentication and Accounting
Configuring RADIUS Accounting
The switch forwards the accounting information it collects to the designated
RADIUS server, where the information is formatted, stored, and managed by
the server. For more information on this aspect of RADIUS accounting, refer
to the documentation provided with your RADIUS server.
Operating Rules for RADIUS Accounting
■ You can configure up to three types of accounting to run simulta
neously: exec, system, and network.
■ RADIUS servers used for accounting are also used for authentication.
■ The switch must be configured to access at least one RADIUS server.
■ RADIUS servers are accessed in the order in which their IP addresses
were configured in the switch. Use show radius to view the order. As
long as the first server is accessible and responding to authentication
requests from the switch, a second or third server will not be
accessed. (For more on this topic, refer to
Access Order” on page 4-29.)
“Changing RADIUS-Server
■ If access to a RADIUS server fails during a session, but after the client
has been authenticated, the switch continues to assume the server is
available to receive accounting data. Thus, if server access fails during
a session, it will not receive accounting data transmitted from the
switch.
Steps for Configuring RADIUS Accounting
1. Configure the switch for accessing a RADIUS server.
You can configure a list of up to three RADIUS servers (one primary, two
backup). The switch operates on the assumption that a server can operate
in both accounting and authentication mode. (Refer to the documentation
for your RADIUS server application.)
• Use the same radius-server host command that you would use to
configure RADIUS authentication. Refer to “2. Configure the Switch
To Access a RADIUS Server” on page 4-10.
• Provide the following:
– A RADIUS server IP address.
– Optional—a UDP destination port for authentication requests.
Otherwise the switch assigns the default UDP port (1812; recom
mended).
4-19
Page 74

RADIUS Authentication and Accounting
Configuring RADIUS Accounting
– Optional—if you are also configuring the switch for RADIUS
2. Configure accounting types and the controls for sending reports to the
RADIUS server.
• Accounting types: exec (page 4-18), network (page 4-18), or system
(page
• Trigger for sending accounting reports to a RADIUS server: At
session start and stop or only at session stop
3. (Optional) Configure session blocking and interim updating options
• Updating: Periodically update the accounting data for sessions-in-
progress
• Suppress accounting: Block the accounting session for any
unknown user with no username access to the switch
authentication, and need a unique encryption key for use during
authentication sessions with the RADIUS server you are desig
nating, configure a server-specific key. This key overrides the
global encryption key you can also configure on the switch, and
must match the encryption key used on the specified RADIUS
server. For more information, refer to the key < key-string > param
eter on page
4-10. (Default: null)
4-18)
1. Configure the Switch To Access a RADIUS Server
Before you configure the actual accounting parameters, you should first
configure the switch to use a RADIUS server. This is the same as the process
described on page
yet configured the switch to use a RADIUS server, your server data has
changed, or you need to specify a non-default UDP destination port for
accounting requests. Note that switch operation expects a RADIUS server to
accommodate both authentication and accounting.
4-10. You need to repeat this step here only if you have not
4-20
Page 75

Syntax: [no] radius-server host < ip-address >
Adds a server to the RADIUS configuration or (with no)
deletes a server from the configuration.
[acct-port < port-number >]
Optional. Changes the UDP destination port for
accounting requests to the specified RADIUS server. If
you do not use this option, the switch automatically
assigns the default accounting port number. (Default:
1813)
[key < key-string >]
Optional. Specifies an encryption key for use during
accounting or authentication sessions with the specified server. This key must match the encryption key
used on the RADIUS server. Use this command only if
the specified server requires a different encryption key
than configured for the global encryption key.
RADIUS Authentication and Accounting
Configuring RADIUS Accounting
(For a more complete description of the radius-server command and its
options, turn to page
4-10.)
For example, suppose you want to the switch to use the RADIUS server
described below for both authentication and accounting purposes.
■ IP address: 10.33.18.151
■ A non-default UDP port number of 1750 for accounting.
For this example, assume that all other RADIUS authentication parameters
for accessing this server are acceptable at their default settings, and that
RADIUS is already configured as an authentication method for one or more
types of access to the switch (Telnet, Console, etc.).
4-21
Page 76

RADIUS Authentication and Accounting
Configuring RADIUS Accounting
Because the radius-server command
includes an acct-port element with a nondefault 1750, the switch assigns this value to
the accounting port UDP port numbers.
Because auth-port was not included in the
command, the authentication UDP port is set
to the default 1812.
Figure 4-7. Example of Configuring for a RADIUS Server with a Non-Default Accounting UDP Port Number
The radius-server command as shown in figure 4-7, above, configures the
switch to use a RADIUS server at IP address 10.33.18.151, with a (non-default)
UDP accounting port of 1750, and a server-specific key of “source0151”.
2. Configure Accounting Types and the Controls for Sending
Reports to the RADIUS Server
Select the Accounting Type(s):
■ Exec: Use exec if you want to collect accounting information on login
sessions on the switch via the console, Telnet, or SSH. (See also
“Accounting” on page 4-2.)
■ System: Use system if you want to collect accounting data when:
• A system boot or reload occurs
• System accounting is turned on or off
Note that there is no time span associated with using the system option. It
simply causes the switch to transmit whatever accounting data it cur
rently has when one of the above events occurs.
■ Network: Use Network if you want to collect accounting information
on 802.1x port-based-access users connected to the physical ports on
the switch to access the network. (See also
For information on this feature, refer to
Access Control (802.1x)” on page 7-1.
“Accounting” on page 2.)
“Configuring Port-Based
Determine how you want the switch to send accounting data to a RADIUS
server:
4-22
Page 77

RADIUS Authentication and Accounting
Configuring RADIUS Accounting
■ Start-Stop:
• Send a start record accounting notice at the beginning of the account
ing session and a stop record notice at the end of the session. Both
notices include the latest data the switch has collected for the
requested accounting type (Network, Exec, or System).
• Do not wait for an acknowledgement.
The system option (page 4-22) ignores start-stop because the switch sends
the accumulated data only when there is a reboot, reload, or accounting
on/off event.
■ Stop-Only:
• Send a stop record accounting notice at the end of the accounting
session. The notice includes the latest data the switch has collected
for the requested accounting type (Network, Exec, or System).
• Do not wait for an acknowledgment.
The system option (page 4-22) always delivers stop-only operation because
the switch sends the accumulated data only when there is a reboot, reload,
or accounting on/off event.
Syntax: [no] aaa accounting < exec | network | system > < start-stop | stop-only >
radius
Configures RADIUS accounting type and how data will be
sent to the RADIUS server.
For example, to configure RADIUS accounting on the switch with start-stop
for exec functions and stop-only for system functions:
Figure 4-8. Example of Configuring Accounting Types
Configures exec and system
accounting and controls.
Summarizes the switch’s
accounting configuration.
Exec and System accounting are
active. (Assumes the switch is
configured to access a reachable
4-23
Page 78

RADIUS Authentication and Accounting
Configuring RADIUS Accounting
3. (Optional) Configure Session Blocking and Interim
Updating Options
These optional parameters give you additional control over accounting data.
■ Updates: In addition to using a Start-Stop or Stop-Only trigger, you
can optionally configure the switch to send periodic accounting
record updates to a RADIUS server.
■ Suppress: The switch can suppress accounting for an unknown user
having no username.
Syntax: [no] aaa accounting update periodic < 1 - 525600 >
Sets the accounting update period for all accounting sessions on the switch. (The no form disables the update
function and resets the value to zero.) (Default: zero; disabled)
Syntax: [no] aaa accounting suppress null-username
Disables accounting for unknown users having no username. (Default: suppression disabled)
To continue the example in figure 4-8, suppose that you wanted the switch to:
■ Send updates every 10 minutes on in-progress accounting sessions.
■ Block accounting for unknown users (no username).
• Update Period
• Suppress Unknown User
Figure 4-9. Example of Optional Accounting Update Period and Accounting Suppression on Unknown User
4-24
Page 79

RADIUS Authentication and Accounting
Viewing RADIUS Statistics
General RADIUS Statistics
Syntax: show radius [host < ip-addr >]
Shows general RADIUS configuration, including the server
IP addresses. Optional form shows data for a specific
RADIUS host. To use show radius, the server’s IP address must
be configured in the switch, which. requires prior use of the
radius-server host command. (See
Accounting” on page 4-17.)
Viewing RADIUS Statistics
“Configuring RADIUS
Figure 4-10. Example of General RADIUS Information from Show Radius Command
Figure 4-11. RADIUS Server Information From the Show Radius Host Command
4-25
Page 80

RADIUS Authentication and Accounting
Viewing RADIUS Statistics
Table 4-2. Values for Show Radius Host Output (Figure 4-11)
Term Definition
Round Trip Time The time interval between the most recent Accounting-Response and the Accounting-
Request that matched it from this RADIUS accounting server.
Pending Requests The number of RADIUS Accounting-Request packets sent to this server that have not yet
timed out or received a response. This variable is incremented when an accounting-Request
is sent and decremented due to receipt of an Accounting-Response, a timeout or a
retransmission.
Retransmissions The number of RADIUS Accounting-Request packets retransmitted to this RADIUS
accounting server. Retransmissions include retries where the Identifier and Acct-Delay have
been updated, as well as those in which they remain the same.
Timeouts The number of accounting timeouts to this server. After a timeout the client may retry to the
same server, send to a different server, or give up. A retry to the same server is counted as
a retransmit as well as a timeout. A send to a different server is counted as an AccountingRequest as well as a timeout.
Malformed Responses The number of malformed RADIUS Accounting-Response packets received from this server.
Malformed packets include packets with an invalid length. Bad authenticators and unknown
types are not included as malformed accounting responses.
Bad Authenticators The number of RADIUS Accounting-Response packets which contained invalid
authenticators received from this server.
Unknown Types The number of RADIUS packets of unknown type which were received from this server on
the accounting port.
Packets Dropped The number of RADIUS packets which were received from this server on the accounting port
and dropped for some other reason.
Access Requests
Accounting Requests The number of RADIUS Accounting-Request packets sent. This does not include
Access Challenges The number of RADIUS Access-Challenge packets (valid or invalid) received from this server.
Access Accepts The number of RADIUS Access-Accept packets (valid or invalid) received from this server.
Access Rejects The number of RADIUS Access-Reject packets (valid or invalid) received from this server.
Responses The number of RADIUS packets received on the accounting port from this server.
The number of RADIUS Access-Requests the switch has sent since it was last rebooted.
(Does not include retransmissions.)
retransmissions.
4-26
Page 81

RADIUS Authentication and Accounting
RADIUS Authentication Statistics
Syntax: show authentication
Displays the primary and secondary authentication methods configured for the Console, Telnet, Port-Access (802.1x),
and SSH methods of accessing the switch. Also displays the
number of access attempts currently allowed in a session.
show radius authentication
Displays NAS identifier and data on the configured RADIUS
server and the switch’s interactions with this server.
(Requires prior use of the radius-server host command to
configure a RADIUS server IP address in the switch. See
“Configuring RADIUS Accounting” on page 4-17.)
Viewing RADIUS Statistics
Figure 4-12. Example of Login Attempt and Primary/Secondary Authentication
Information from the Show Authentication Command
Figure 4-13. Example of RADIUS Authentication Information from a Specific Server
4-27
Page 82

RADIUS Authentication and Accounting
Viewing RADIUS Statistics
RADIUS Accounting Statistics
Syntax: show accounting
show radius accounting
show accounting sessions
Lists configured accounting interval, “Empty User” suppression status, accounting types, methods, and modes.
Lists accounting statistics for the RADIUS server(s) configured in the switch (using the radius-server host command).
Lists the accounting sessions currently active on the switch.
4-28
Figure 4-14. Listing the Accounting Configuration in the Switch
Figure 4-15. Example of RADIUS Accounting Information for a Specific Server
Page 83

RADIUS Authentication and Accounting
Changing RADIUS-Server Access Order
Figure 4-16. Example Listing of Active RADIUS Accounting Sessions on the Switch
Changing RADIUS-Server Access Order
The switch tries to access RADIUS servers according to the order in which
their IP addresses are listed by the show radius command. Also, when you add
a new server IP address, it is placed in the highest empty position in the list.
Adding or deleting a RADIUS server IP address leaves an empty position, but
does not change the position of any other server addresses in the list. For
example if you initially configure three server addresses, they are listed in the
order in which you entered them. However, if you subsequently remove the
second server address in the list and add a new server address, the new
address will be placed second in the list.
Thus, to move a server address up in the list, you must delete it from the list,
ensure that the position to which you want to move it is vacant, and then reenter it. For example, suppose you have already configured the following three
RADIUS server IP addresses in the switch:
RADIUS server IP addresses listed in the order
in which the switch will try to access them. In this
case, the server at IP address 10.10.10.1 is first.
Note: If the switch successfully accesses the
first server, it does not try to access any other
servers in the list, even if the client is denied
access by the first server.
Figure 4-17. Search Order for Accessing a RADIUS Server
4-29
Page 84

RADIUS Authentication and Accounting
Changing RADIUS-Server Access Order
To exchange the positions of the addresses so that the server at 10.10.10.003
will be the first choice and the server at 10.10.10.001 will be the last, you would
do the following:
1. Delete 10.10.10.003 from the list. This opens the third (lowest) position in
the list.
2. Delete 10.10.10.001 from the list. This opens the first (highest) position in
the list.
3. Re-enter 10.10.10.003. Because the switch places a newly entered address
in the highest-available position, this address becomes first in the list.
4. Re-enter 10.10.10.001. Because the only position open is the third position,
this address becomes last in the list.
Removes the “003” and “001” addresses from
the RADIUS server list.
Figure 4-18. Example of New RADIUS Server Search Order
Inserts the “003” address in the first position in
the RADIUS server list, and inserts the “001”
address in the last position in the list.
Shows the new order in which the switch
searches for a RADIUS server.
4-30
Page 85

Messages Related to RADIUS Operation€
Message Meaning
Can’t reach RADIUS server < x.x.x.x >.
No server(s) responding.
Not legal combination of
authentication methods.
A designated RADIUS server is not responding to an
authentication request. Try pinging the server to
determine whether it is accessible to the switch. If the
server is accessible, then verify that the switch is using
the correct encryption key and that the server is correctly
configured to receive an authentication request from the
switch.
The switch is configured for and attempting RADIUS
authentication, however it is not receiving a response
from a RADIUS server. Ensure that the switch is
configured to access at least one RADIUS server. (Use
show radius.) If you also see the message
reach RADIUS server < x.x.x.x >
the suggestions listed for that message.
Indicates an attempt to configure local as both the
primary and secondary authentication methods. If local
is the primary method, then none must be the secondary
method.
RADIUS Authentication and Accounting
Messages Related to RADIUS Operation
Can’t
, try
4-31
Page 86

RADIUS Authentication and Accounting
Messages Related to RADIUS Operation
— This page is intentionally unused. —
4-32€
Page 87

Configuring Secure Shell (SSH)€
Contents
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-2€
Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-4€
Prerequisite for Using SSH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-5€
Public Key Formats . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-5€
Steps for Configuring and Using SSH for Switch and Client
Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-6€
General Operating Rules and Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-8€
5
Configuring the Switch for SSH Operation . . . . . . . . . . . . . . . . . . . . . . 5-9€
1. Assigning a Local Login (Operator) and Enable (Manager) €
Password
2. Generating the Switch’s Public and Private Key Pair . . . . . . . . . . 5-10€
3. Providing the Switch’s Public Key to Clients . . . . . . . . . . . . . . . . . . 5-12€
4. Enabling SSH on the Switch and Anticipating SSH Client€
Contact Behavior
5. Configuring the Switch for SSH Authentication . . . . . . . . . . . . . . . 5-18€
6. Use an SSH Client To Access the Switch . . . . . . . . . . . . . . . . . . . . . 5-21€
Further Information on SSH Client Public-Key Authentication . 5-21€
Messages Related to SSH Operation . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-27€
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-9€
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-15€
5-1
Page 88

Configuring Secure Shell (SSH)
Overview
Overview€
Feature Default Menu CLI Web
Generating a public/private key pair on the switch No n/a page 5-10 n/a
Using the switch’s public key n/a n/a page 5-12 n/a
Enabling SSH Disabled n/a page 5-15 n/a
Enabling client public-key authentication Disabled n/a pages 5-19, n/a
Enabling user authentication Disabled n/a page 5-18 n/a
The HP switches covered in this guide use Secure Shell version 1 or 2 (SSHv1
or SSHv2) to provide remote access to management functions on the switches
via encrypted paths between the switch and management station clients
capable of SSH operation.
5-21
SSH provides Telnet-like functions but, unlike Telnet, SSH provides encrypted,
authenticated transactions. The authentication types include:
■ Client public-key authentication
■ Switch SSH and user password authentication
Client Public Key Authentication (Login/Operator Level) with User
Password Authentication (Enable/Manager Level). This option uses
one or more public keys (from clients) that must be stored on the switch. Only
a client with a private key that matches a stored public key can gain access
to the switch. (The same private key can be stored on one or more clients.)
1. Switch-to-Client SSH authentication.
HP
Switch
(SSH
Server)
2. Client-to-Switch (login rsa) authentication
3.User-to-Switch (enable password) authentication
options:
– Local
–TACACS+
–RADIUS
–None
Figure 5-1. Client Public Key Authentication Model
SSH
Client
Work-
Station
5-2
Page 89

Configuring Secure Shell (SSH)
Overview
Note SSH in the HP Procurve is based on the OpenSSH software toolkit. For more
information on OpenSSH, visit http://www.openssh.com
Switch SSH and User Password Authentication . This option is a subset
of the client public-key authentication show in figure 5-1. It occurs if the switch
has SSH enabled but does not have login access (login public-key) configured
to authenticate the client’s key. As in figure
5-1, the switch authenticates itself
to SSH clients. Users on SSH clients then authenticate themselves to the
switch (login and/or enable levels) by providing passwords stored locally on
the switch or on a TACACS+ or RADIUS server. However, the client does not
use a key to authenticate itself to the switch.
.
SSH
Client
Work-
Station
HP
Switch
(SSH
Server)
1. Switch-to-Client SSH
2. User-to-Switch (login password and
enable password authentication)
options:
– Local
– TACACS+
Figure 5-2. Switch/User Authentication
SSH on the HP ProCurve switches covered in this guide supports these data
encryption methods:
■ 3DES (168-bit)
■ DES (56-bit)
Note The HP ProCurve switches covered in this guide use the RSA algorithm for
internally generated keys (v1/v2 shared host key & v1 server key). However,
HP ProCurve switches support both RSA and DSA/DSS keys for client authen
tication. All references to either a public or private key mean keys generated
using these algorithms unless otherwise noted
5-3
Page 90

Configuring Secure Shell (SSH)
Terminology
Terminology
■ SSH Server: An HP ProCurve switch with SSH enabled.
■ Key Pair: A pair of keys generated by the switch or an SSH client
■ PEM (Privacy Enhanced Mode): Refers to an ASCII-formatted
■ Private Key: An internally generated key used in the authentication
application. Each pair includes a public key, that can be read by
anyone and a private key, that is held internally in the switch or by a
client.
client public-key that has been encoded for portability and efficiency.
SSHv2 client public-keys are typically stored in the PEM format. See
figures
5-3 and 5-4 for examples of PEM-encoded ASCII and non-
encoded ASCII keys.
process. A private key generated by the switch is not accessible for
viewing or copying. A private key generated by an SSH client applica
tion is typically stored in a file on the client device and, together with
its public key counterpart, can be copied and stored on multiple
devices.
■ Public Key: An internally generated counterpart to a private key. A
device’s public key is used to authenticate the device to other devices.
■ Enable Level: Manager privileges on the switch.
■ Login Level: Operator privileges on the switch.
■ Local password or username: A Manager-level or Operator-level
password configured in the switch.
■ SSH Enabled: (1) A public/private key pair has been generated on
the switch (crypto key generate ssh [rsa]) and (2) SSH is enabled (ip
ssh). (You can generate a key pair without enabling SSH, but you
cannot enable SSH without first generating a key pair. See
“2. Gener
ating the Switch’s Public and Private Key Pair” on page 5-10 and “4.
Enabling SSH on the Switch and Anticipating SSH Client Contact
Behavior” on page 5-15.)
5-4
Page 91

Configuring Secure Shell (SSH)
Prerequisite for Using SSH
Prerequisite for Using SSH
Before using the switch as an SSH server, you must install a publicly or
commercially available SSH client application on the computer(s) you use for
management access to the switch. If you want client public-key authentication
(page
5-2), then the client program must have the capability to generate or
import keys.
Public Key Formats
Any client application you use for client public-key authentication with the
switch must have the capability export public keys. The switch can accept
keys in the PEM-Encoded ASCII Format or in the Non-Encoded ASCII format.
Comment
describing public
key identity.
Beginning of actual SSHv2
public key in PEM-Encoded
ASCII format.
Figure 5-3. Example of Public Key in PEM-Encoded ASCII Format Common for SSHv2 Clients
Bit
Size
Exponent <e>
Modulus <n>
Figure 5-4. Example of Public Key in Non-Encoded ASCII Format (Common for SSHv1 Client Applications)
5-5
Page 92

Configuring Secure Shell (SSH)
Steps for Configuring and Using SSH for Switch and Client Authentication
Steps for Configuring and Using SSH for
Switch and Client Authentication
For two-way authentication between the switch and an SSH client, you must
use the login (Operator) level.
Table 5-1. SSH Options
Switch
Access
Level
Operator
(Login)
Level
Manager
(Enable)
Level
1
For ssh login public-key, the switch uses client public-key authentication instead of the switch password options for
primary authentication.
Primary SSH
Authentication
ssh login rsa Yes Ye s
ssh login Local Yes No Yes local or none
ssh login TACACS Yes No Yes local or none
ssh login RADIUS Yes No Yes local or none
ssh enable local Yes No Yes local or none
ssh enable tacacs Yes No Yes local or none
ssh enable radius Yes No Yes local or none
Authenticate
Switch Public Key
to SSH Clients?
Authenticate
Client Public Key
to the Switch?
1
Primary Switch
Password
Authentication
1
No
Secondary Switch
Password
Authentication
local or none
The general steps for configuring SSH include:
A. Client Preparation
1. Install an SSH client application on a management station you want
to use for access to the switch. (Refer to the documentation provided
with your SSH client application.)
2. Optional—If you want the switch to authenticate a client public-key
on the client:
a. Either generate a public/private key pair on the client computer
(if your client application allows) or import a client key pair that
you have generated using another SSH application.
b. Copy the client public key into an ASCII file on a TFTP server
accessible to the switch and download the client public key file to
the switch. (The client public key file can hold up to ten client
keys.) This topic is covered under
“To Create a Client-Public-Key
Text File” on page 5-23.
5-6
Page 93

Configuring Secure Shell (SSH)
Steps for Configuring and Using SSH for Switch and Client Authentication
B. Switch Preparation
1. Assign a login (Operator) and enable (Manager) password on the
switch (page
5-9).
2. Generate a public/private key pair on the switch (page 5-10).
You need to do this only once. The key remains in the switch even if
you reset the switch to its factory-default configuration. (You can
remove or replace this key pair, if necessary.)
3. Copy the switch’s public key to the SSH clients you want to access
the switch (page
5-12).
4. Enable SSH on the switch (page 5-15).
5. Configure the primary and secondary authentication methods you
want the switch to use. In all cases, the switch will use its host-publickey to authenticate itself when initiating an SSH session with a client.
• SSH Login (Operator) options:
– Option A:
Primary: Local, TACACS+, or RADIUS password
Secondary: Local password or none
– Option B:
Primary: Client public-key authentication (login public-
key — page 5-21)€
Secondary: Local password or none€
Note that if you want the switch to perform client public-key
authentication, you must configure the switch with Option B.
• SSH Enable (Manager) options:
Primary: Local, TACACS+, or RADIUS
Secondary: Local password or none
6. Use your SSH client to access the switch using the switch’s IP address
or DNS name (if allowed by your SSH client application). Refer to the
documentation provided with the client application.
5-7
Page 94

Configuring Secure Shell (SSH)
General Operating Rules and Notes
General Operating Rules and Notes
■ Public keys generated on an SSH client must be exportable to the
switch. The switch can only store ten keys client key pairs.
■ The switch’s own public/private key pair and the (optional) client
public key file are stored in the switch’s flash memory and are not
affected by reboots or the erase startup-config command.
■ Once you generate a key pair on the switch you should avoid re-
generating the key pair without a compelling reason. Otherwise, you
will have to re-introduce the switch’s public key on all management
stations (clients) you previously set up for SSH access to the switch.
In some situations this can temporarily allow security breaches.
■ On HP ProCurve switches that support stacking, when stacking is
enabled, SSH provides security only between an SSH client and the
stack manager. Communications between the stack commander and
stack members is not secure.
■ The switch does not support outbound SSH sessions. Thus, if you
Telnet from an SSH-secure switch to another SSH-secure switch, the
session is not secure.
5-8
Page 95

Configuring Secure Shell (SSH)
Configuring the Switch for SSH Operation
Configuring the Switch for SSH
Operation
SSH-Related Commands in This Section Page
show ip ssh 5-17
show crypto client-public-key [keylist-str] [< babble | fingerprint >] 5-24
show crypto host-public-key [< babble | fingerprint >]
show authentication
crypto key < generate | zeroize > ssh [rsa]
ip ssh
key-size < 512 | 768 | 1024 >
port < 1 - 65535|default >
timeout < 5 - 120 >
version <1 | 2 | 1-or-2 >
aaa authentication ssh
login < local | tacacs | radius | public-key >
< local | none >
enable < tacacs | radius | local >
< local | none >
copy tftp pub-key-file <tftp server IP> <public key file>
clear crypto client-public-key [keylist-str]
5-14
5-21
5-11
5-16
5-16
5-16
5-16
5-16
5-18, 5-20
5-18
5-18
5-18
5-24
5-25
1. Assigning a Local Login (Operator) and Enable
(Manager) Password
At a minimum, HP recommends that you always assign at least a Manager
password to the switch. Otherwise, under some circumstances, anyone with
Telnet, web, or serial port access could modify the switch’s configuration.
To Configure Local Passwords. You can configure both the Operator and
Manager password with one command.
Syntax:password < manager | operator | all >
5-9
Page 96

Configuring Secure Shell (SSH)
Configuring the Switch for SSH Operation
Figure 5-5. Example of Configuring Local Passwords
2. Generating the Switch’s Public and Private Key Pair
You must generate a public and private host key pair on the switch. The switch
uses this key pair, along with a dynamically generated session key pair to
negotiate an encryption method and session with an SSH client trying to
connect to the switch.
The host key pair is stored in the switch’s flash memory, and only the public
key in this pair is readable. The public key should be added to a "known hosts"
file (for example, $HOME/.ssh/known_hosts on UNIX systems) on the
SSH clients which should have access to the switch. Some SSH client appli
cations automatically add the switch’s public key to a "known hosts" file. Other
SSH applications require you to manually create a known hosts file and place
the switch’s public key in the file. (Refer to the documentation for your SSH
client application.)
(The session key pair mentioned above is not visible on the switch. It is a
temporary, internally generated pair used for a particular switch/client ses
sion, and then discarded.)
5-10
Page 97

Configuring Secure Shell (SSH)
Configuring the Switch for SSH Operation
Notes When you generate a host key pair on the switch, the switch places the key
pair in flash memory (and not in the running-config file). Also, the switch
maintains the key pair across reboots, including power cycles. You should
consider this key pair to be "permanent"; that is, avoid re-generating the key
pair without a compelling reason. Otherwise, you will have to re-introduce the
switch’s public key on all management stations you have set up for SSH access
to the switch using the earlier pair.
Removing (zeroing) the switch’s public/private key pair renders the switch
unable to engage in SSH operation and automatically disables IP SSH on the
switch. (To verify whether SSH is enabled, execute show ip ssh.) However, any
active SSH sessions will continue to run, unless explicitly terminated with the
CLI kill command.
To Generate or Erase the Switch’s Public/Private RSA Host Key Pair.
Because the host key pair is stored in flash instead of the running-config file,
it is not necessary to use write memory to save the key pair. Erasing the key
pair automatically disables SSH.
Syntax: crypto key generate ssh [rsa]
Generates a public/private key pair for the switch. If a
switch key pair already exists, replaces it with a new
key pair. (See the Note, above.)
crypto key zeroize ssh [rsa]
Erases the switch’s public/private key pair and disables SSH operation.
show crypto host-public-key
Displays switch’s public key. Displays the version 1
and version 2 views of the key.
[ babble ]
Displays hashes of the switch’s public key in
phonetic format. (See “Displaying the Public
Key” on page 5-14.)
[ fingerprint ]
Displays fingerprints of the switch’s public key
in hexadecimal format. (See “Displaying the
Public Key” on page
5-14.)
5-11
Page 98

Configuring Secure Shell (SSH)
Configuring the Switch for SSH Operation
For example, to generate and display a new key:
Host Public
Key for the
Switch
Version 1 and Version 2 Views
of Same Host Public Key
Figure 5-6. Example of Generating a Public/Private Host Key Pair for the Switch
The 'show crypto host-public-key' displays data in two different formats
because your client may store it in either of these formats after learning the
key. If you wish to compare the switch key to the key as stored in your client's
known-hosts file, note that the formatting and comments need not match. For
version 1 keys, the three numeric values bit size, exponent <e>, and modulus
<n> must match; for PEM keys, only the PEM-encoded string itself must
match.
Notes "Zeroizing" the switch’s key automatically disables SSH (sets ip ssh to no).
Thus, if you zeroize the key and then generate a new key, you must also reenable SSH with the ip ssh command before the switch can resume SSH
operation.
3. Providing the Switch’s Public Key to Clients
When an SSH client contacts the switch for the first time, the client will
challenge the connection unless you have already copied the key into the
client’s "known host" file. Copying the switch’s key in this way reduces the
chance that an unauthorized device can pose as the switch to learn your access
passwords. The most secure way to acquire the switch’s public key for
5-12
Page 99

Configuring Secure Shell (SSH)
Configuring the Switch for SSH Operation
distribution to clients is to use a direct, serial connection between the switch
and a management device (laptop, PC, or UNIX workstation), as described
below.
The public key generated by the switch consists of three parts, separated by
one blank space each:
Bit Size
Exponent <e>
Modulus <n>
896 35 427199470766077426366625060579924214851527933248752021855126493
2934075407047828604329304580321402733049991670046707698543529734853020
0176777055355544556880992231580238056056245444224389955500310200336191
3610469786020092436232649374294060627777506601747146563337525446401
Figure 5-7. Example of a Public Key Generated by the Switch
(The generated public key on the switch is always 896 bits.)
With a direct serial connection from a management station to the switch:
1. Use a terminal application such as HyperTerminal to display the switch’s
public key with the show crypto host-public-key command (figure 5-6).
2. Bring up the SSH client’s "known host" file in a text editor such as Notepad
as straight ASCII text, and copy the switch’s public key into the file.
3. Ensure that there are no changes in breaks in the text string. (A public
key must be an unbroken ASCII string. Line breaks are not allowed
Changes in the line breaks will corrupt the Key.) For example, if you are
using Windows® Notepad, ensure that
W
ord Wrap (in the Edit menu) is
disabled, and that the key text appears on a single line.
Figure 5-8. Example of a Correctly Formatted Public Key
5-13
Page 100

Configuring Secure Shell (SSH)
Configuring the Switch for SSH Operation
4. Add any data required by your SSH client application. For example Before
saving the key to an SSH client’s "known hosts" file you may have to insert
the switch’s IP address:
Inserted
IP
Address
Bit
Size
Exponent <e>
Modulus <n>
Figure 5-9. Example of a Switch Public Key Edited To Include the Switch’s IP Address
For more on this topic, refer to the documentation provided with your SSH
client application.
Displaying the Public Key. The switch provides three options for display
ing its public key. This is helpful if you need to visually verify that the public
key the switch is using for authenticating itself to a client matches the copy
of this key in the client’s "known hosts" file:
■ Non-encoded ASCII numeric string: Requires a client ability to
display the keys in the “known hosts” file in the ASCII format. This
method is tedious and error-prone due to the length of the keys. (See
figure
■ Phonetic hash: Outputs the key as a relatively short series of alpha
5-8 on page 5-13.)
betic character groups. Requires a client ability to convert the key to
this format.
■ Hexadecimal hash: Outputs the key as a relatively short series of
hexadecimal numbers. Requires a parallel client ability.
For example, on the switch, you would generate the phonetic and hexadecimal
versions of the switch’s public key in figure
5-14
5-8 as follows:
 Loading...
Loading...