Page 1

USER’S GUIDE
VERSION 1.1
AUGUST 2011
DEFAULT LOGIN DETAILS
IP Address 192.168.0.1
Username admin
Password password
CVE-30360
Page 2

Page 3

3
ABOUT THIS USER’S GUIDE
ABOUT THIS USER’S GUIDE
INTENDED AUDIENCE
This manual is intended for people who want to configure the CVE-30360’s features
via its Graphical User Interface (GUI).
HOW TO USE THIS USER’S GUIDE
This manual contains information on each the CVE-30360’s GUI screens, and
describes how to use its various features.
Use the Introduction (page 15) to see an overview of the topics covered in this
manual.
Use the Table of Contents (page 7), List of Figures (page 11) and List of Tables
(page 13) to quickly find information about a particular GUI screen or topic.
Use the Index (page 95) to find information on a specific keyword.
Use the rest of this User’s Guide to see in-depth descriptions of the CVE-
30360’s features.
RELATED DOCUMENTATION
Quick Installation Guide: see this for information on getting your CVE-30360
up and running right away. It includes information on system requirements,
package contents, the installation procedure, and basic troubleshooting tips.
Online Help: each screen in the CVE-30360’s Graphical User Interface (GUI)
contains a Help button. Click this button to see additional information about
configuring the screen.
DOCUMENT CONVENTIONS
This User’s Guide uses various typographic conventions and styles to indicate
content type:
Page 4
4
HITRON CVE-30360 USER’S GUIDE
Bulleted paragraphs are used to list items, and to indicate options.
1 Numbered paragraphs indicate procedural steps.
NOTE: Notes provide additional information on a subject.
Product labels, field labels, field choices, etc. are in bold type. For example:
A mouse click in the Graphical User Interface (GUI) is denoted by a right angle
bracket ( > ). For example:
means that you should click Settings in the GUI, then Advanced settings.
A key stroke is denoted by square brackets and uppercase text. For example:
Warnings provide information about actions that could harm
you or your device.
Select UDP to use the User Datagram Protocol.
Click Settings > Advanced Settings.
Press [ENTER] to continue.
CUSTOMER SUPPORT
For technical assistance or other customer support issues, please consult your Hitron
representative.
ABOUT THIS USER’S GUIDE
Page 5
5
HITRON CVE-30360 USER’S GUIDE
Copyright 2011 Hitron Technologies. All rights reserved. All trademarks and
registered trademarks used are the properties of their respective owners.
DISCLAIMER: The information in this User’s Guide is accurate at the time of writing.
This User’s Guide is provided “as is” without express or implied warranty of any kind.
Neither Hitron Technologies nor its agents assume any liability for inaccuracies in this
User’s Guide, or losses incurred by use or misuse of the information in this User’s
Guide.
ABOUT THIS USER’S GUIDE
Page 6

6
HITRON CVE-30360 USER’S GUIDE
ABOUT THIS USER’S GUIDE
Page 7

7
TABLE OF CONTENTS
TABLE OF CONTENTS
About This User’s Guide..................................................................3
Table of Contents..............................................................................7
List of Figures .................................................................................11
List of Tables...................................................................................13
Introduction.....................................................................................15
1.1 CVE-30360 Overview .........................................................................15
1.1.1 Key Features .............................................................................16
1.2 Hardware Connections .......................................................................16
1.3 LEDs ..................................................................................................18
1.4 IP Address Setup ...............................................................................20
1.4.1 Manual IP Address Setup ..........................................................21
1.5 Logging into the CVE-30360 ..............................................................22
1.6 GUI Overview .....................................................................................23
1.7 Resetting the CVE-30360 ..................................................................23
Cable................................................................................................25
2.1 Cable Overview ..................................................................................25
2.1.1 DOCSIS .....................................................................................25
2.1.2 IP Addresses and Subnets ........................................................25
2.1.2.1 IP Address Format ............................................................25
2.1.2.2 IP Address Assignment .....................................................25
2.1.2.3 Subnets .............................................................................26
2.1.3 DHCP .........................................................................................27
2.1.4 DHCP Lease ..............................................................................28
2.1.5 MAC Addresses .........................................................................28
Page 8
8
HITRON CVE-30360 USER’S GUIDE
2.1.6 Routing Mode ............................................................................28
2.1.7 Configuration Files ....................................................................29
2.1.8 Downstream and Upstream Transmissions ..............................29
2.1.9 Cable Frequencies ....................................................................29
2.1.10 Modulation ...............................................................................29
2.1.11 TDMA, FDMA and SCDMA .....................................................30
2.2 The System Info Screen ....................................................................30
2.3 The Initialization Screen ....................................................................32
2.4 The Status Screen .............................................................................33
2.5 The Password Screen .......................................................................36
LAN .................................................................................................. 39
3.1 LAN Overview ....................................................................................39
3.1.1 Local Area Networks .................................................................39
3.1.2 LAN IP Addresses and Subnets ................................................39
3.1.3 Domain Suffix ............................................................................40
3.1.4 Debugging (Ping and Traceroute) .............................................40
3.2 The LAN IP Screen ............................................................................40
3.3 The Switch Setup Screen ..................................................................42
3.4 The Debug Screen .............................................................................43
3.5 The Backup Screen ...........................................................................44
Firewall ............................................................................................ 47
4.1 Firewall Overview ..............................................................................47
4.1.1 Firewall ......................................................................................47
4.1.2 Intrusion detection system .........................................................47
4.1.3 Ping ...........................................................................................47
4.1.4 MAC Filtering .............................................................................47
4.1.5 IP Filtering .................................................................................48
4.1.6 Port Forwarding .........................................................................48
4.1.7 Port Triggering ...........................................................................48
4.1.8 DMZ ...........................................................................................49
4.2 The Firewall Options Screen .............................................................49
4.3 The MAC Filtering Screen .................................................................50
4.4 The IP Filtering Screen ......................................................................53
4.4.1 Adding or Editing an IP Filtering Rule .......................................54
4.5 The Forwarding Screen .....................................................................56
4.5.1 Adding or Editing a Port Forwarding Rule .................................58
4.6 The Port Triggering Screen ...............................................................59
4.6.1 Adding or Editing a Port Triggering Rule ...................................61
TABLE OF CONTENTS
Page 9

9
HITRON CVE-30360 USER’S GUIDE
Parental Control..............................................................................63
5.1 Parental Control Overview .................................................................63
5.1.1 Website Blocking .......................................................................63
5.2 The Web Site Blocking Screen ..........................................................63
5.3 The Scheduling Screen ......................................................................65
5.4 The Local Logs Screen ......................................................................67
Wireless ...........................................................................................69
6.1 Wireless Basics ..................................................................................69
6.1.1 Wireless Standards ....................................................................70
6.1.2 Service Sets and SSIDs ............................................................70
6.1.3 Basic Wireless Security .............................................................71
6.2 Wireless Tutorials ...............................................................................71
6.2.1 Choosing a Security Method ......................................................71
6.2.2 Changing the Wireless Password ..............................................72
6.2.3 Changing the Network Name (SSID) .........................................73
6.2.4 Hiding the Network ....................................................................73
6.2.5 Improving the Wireless Network’s Performance ........................73
6.3 Advanced Wireless Networking .........................................................74
6.3.1 Advanced Wireless Security ......................................................74
6.3.2 Other Wireless Concepts ...........................................................75
6.3.2.1 WPS ..................................................................................75
6.3.2.2 WMM .................................................................................76
6.4 The Wireless Screens ........................................................................76
6.4.1 The Basic Screen ......................................................................76
6.4.2 The Security Screen ..................................................................78
6.4.3 The Access Control Screen .......................................................82
6.4.4 The WiFi Site Survey Screen .....................................................84
EMTA................................................................................................87
7.1 The Status Screen .............................................................................87
7.2 The DHCP Screen .............................................................................88
Troubleshooting..............................................................................91
Index.................................................................................................95
TABLE OF CONTENTS
Page 10

10
HITRON CVE-30360 USER’S GUIDE
TABLE OF CONTENTS
Page 11

11
LIST OF FIGURES
LIST OF FIGURES
FIGURE 1: Application Overview ........................................................................15
FIGURE 2: Hardware Connections .....................................................................17
FIGURE 3: LEDs .................................................................................................19
FIGURE 4: Login .................................................................................................22
FIGURE 5: GUI Overview ...................................................................................23
FIGURE 6: The Cable > System Info Screen .....................................................31
FIGURE 7: The Cable > Initialization Screen .....................................................33
FIGURE 8: The Cable > Status Screen ..............................................................34
FIGURE 9: The Cable > Password Screen ........................................................36
FIGURE 10: The LAN > LAN IP Screen .............................................................41
FIGURE 11: The LAN > Switch Setup Screen ....................................................43
FIGURE 12: The LAN > Debug Screen ..............................................................44
FIGURE 13: The LAN > Backup Screen .............................................................44
FIGURE 14: The Firewall > Firewall Options Screen .........................................49
FIGURE 15: The Firewall > MAC Filtering Screen .............................................51
FIGURE 16: The Firewall > IP Filtering Screen ..................................................53
FIGURE 17: The Firewall > IP Filtering > Add/Edit Screen ................................55
FIGURE 18: The Firewall > Forwarding Screen .................................................56
FIGURE 19: The Firewall > Forwarding > Add/Edit Screen ................................58
FIGURE 20: The Firewall > Port Triggering Screen ...........................................60
FIGURE 21: The Firewall > Port Triggering > Add/Edit Screen ..........................61
FIGURE 22: The Parent Control > Web Site Blocking Screen ...........................64
FIGURE 23: The Parent Control > Scheduling Screen .......................................66
FIGURE 24: The Parent Control > Local Logs Screen .......................................67
FIGURE 25: Example Wireless Network ............................................................70
FIGURE 26: The Wireless > Basic Screen .........................................................76
FIGURE 27: WPS PIN ........................................................................................77
FIGURE 28: The Wireless > Security Screen .....................................................79
FIGURE 29: The Wireless > Access Control ......................................................82
FIGURE 30: The Wireless > WiFi Site Survey Screen .......................................84
FIGURE 31: The EMTA > Status Screen ...........................................................87
Page 12
12
HITRON CVE-30360 USER’S GUIDE
FIGURE 32: The EMTA > DHCP Screen ...........................................................89
LIST OF FIGURES
Page 13

13
LIST OF TABLES
LIST OF TABLES
TABLE 1: Hardware Connections ......................................................................17
TABLE 2: LEDs ..................................................................................................19
TABLE 3: GUI Overview ....................................................................................23
TABLE 4: Private IP Address Ranges ...............................................................26
TABLE 5: IP Address: Decimal and Binary ........................................................27
TABLE 6: Subnet Mask: Decimal and Binary ....................................................27
TABLE 7: The Cable > System Info Screen ......................................................31
TABLE 8: The Cable > Status Screen ...............................................................34
TABLE 9: The Cable > Password Screen ..........................................................36
TABLE 10: The LAN > LAN IP Screen ..............................................................41
TABLE 11: The LAN > Switch Setup Screen .....................................................43
TABLE 12: The LAN > Debug Screen ...............................................................44
TABLE 13: The LAN > Backup Screen ..............................................................45
TABLE 14: The Firewall > Firewall Options Screen ...........................................50
TABLE 15: The Firewall > MAC Filtering Screen ...............................................51
TABLE 16: The Firewall > IP Filtering Screen ...................................................53
TABLE 17: The Firewall > IP Filtering > Add/Edit Screen ..................................55
TABLE 18: The Firewall > Forwarding Screen ..................................................56
TABLE 19: The Firewall > Forwarding > Add/Edit Screen .................................58
TABLE 20: The Firewall > Port Triggering Screen .............................................60
TABLE 21: The Firewall > Port Triggering > Add/Edit Screen ...........................62
TABLE 22: The Parent Control > Web Site Blocking Screen ............................64
TABLE 23: The Parent Control > Scheduling Screen ........................................66
TABLE 24: The Parental Control > Local Logs Screen .....................................67
TABLE 25: The Wireless > Basic Screen ..........................................................77
TABLE 26: The Wireless > Security Screen ......................................................79
TABLE 27: The Wireless > Access Control Screen ...........................................82
TABLE 28: The Wireless > WiFi Site Survey Screen ........................................84
TABLE 29: The EMTA > Status Screen .............................................................87
TABLE 30: The EMTA > DHCP Screen .............................................................89
Page 14
14
HITRON CVE-30360 USER’S GUIDE
LIST OF TABLES
Page 15

1
INTRODUCTION
This chapter introduces the CVE-30360 and its GUI (Graphical User Interface).
1.1 CVE-30360 OVERVIEW
Your CVE-30360 is a voice-enabled cable modem and wireless access point that
allows you to connect your computers, analog telephones, wireless devices, and
other network devices to one another, and to the Internet via the cable connection.
15
Computers with a wired connection to the CVE-30360 are on the Local Area Network
(LAN), computers with a wireless connection to the CVE-30360 are on the Wireless
Local Area Network (WLAN) and the CVE-30360 connects to the service provider
over the Wide Area Network (WAN).
FIGURE 1: Application Overview
INTRODUCTION
Page 16

16
HITRON CVE-30360 USER’S GUIDE
1.1.1 KEY FEATURES
The CVE-30360 provides:
Internet connection to cable modem service via CATV port (F-type RF
connector)
Voice over IP (VoIP) connection to your voice service provider.
Local Area Network connection via four 10/100/1000 Mbps (megabits per
second) Ethernet ports
Dynamic Host Configuration Protocol (DHCP) for devices on the LAN
LAN troubleshooting tools (Ping and Traceroute)
IEEE 802.11b/g/n wireless MIMO (Multiple-In, Multiple-Out) networking, allowing
speeds of up to 300Mbps
Wireless security: WEP, WPA-PSK and WPA2-PSK encryption, Wifi Protected
Setup (WPS) push-button and PIN configuration and MAC filtering
Wired security: stateful inspection firewall with intrusion detection system, IP and
MAC filtering, port forwarding and port triggering, and De-Militarized Zone
(DMZ)
Parental control: scheduled website blocking and access logs
Settings backup and restore
Secure configuration interface, accessible by Web browser
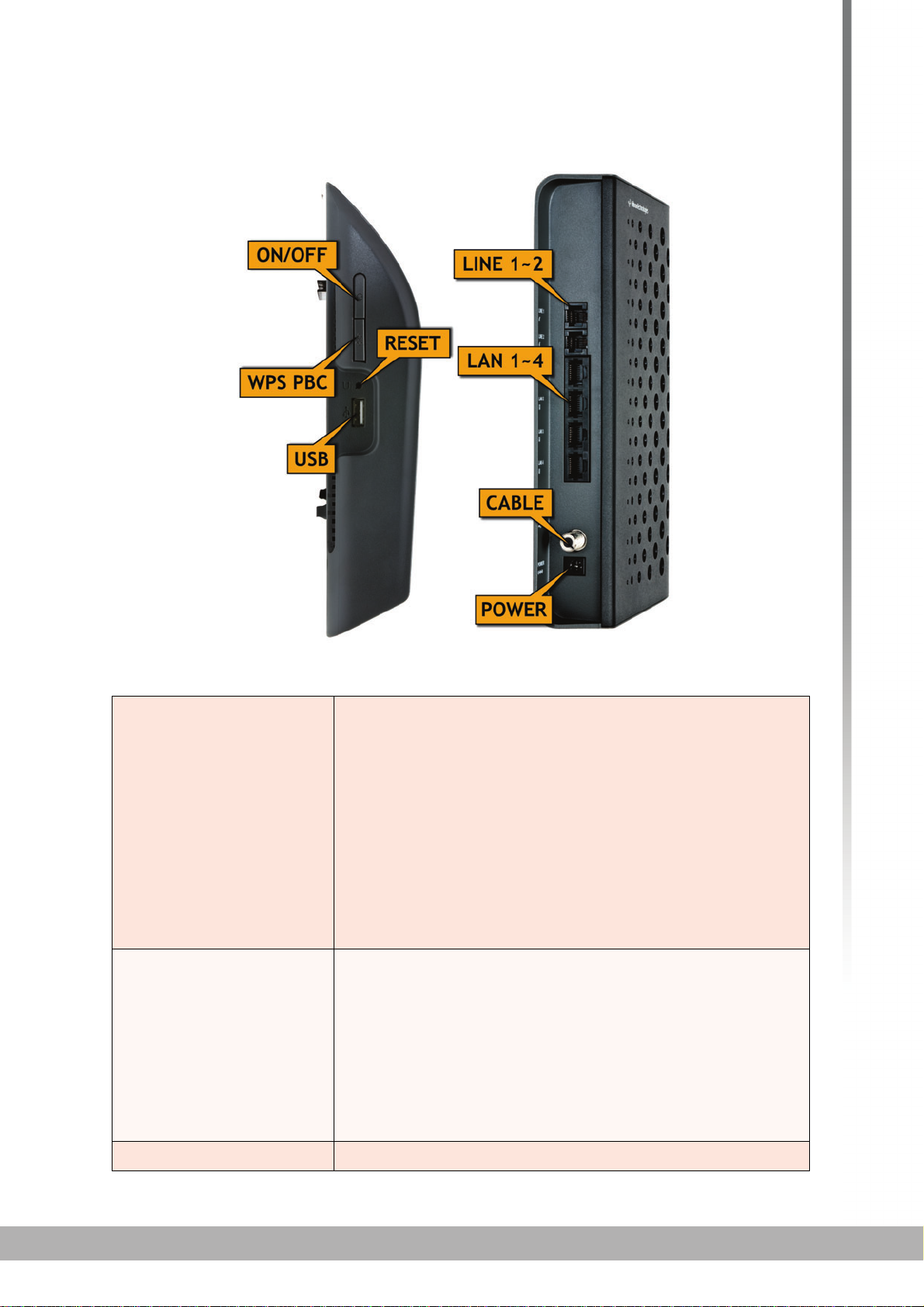
1.2 HARDWARE CONNECTIONS
This section describes the CVE-30360’s physical ports and buttons.
INTRODUCTION
Page 17
HITRON CVE-30360 USER’S GUIDE
FIGURE 2: Hardware Connections
17
TABLE 1: Hardware Connections
WIFI Use this button to turn the wireless network on or off,
and to begin the WiFi Protected Setup (WPS) PushButton Configuration (PBC) procedure (see WPS on
page 75 for more information.)
To turn the wireless network on or off, press the
button for between one and five seconds.
To begin the WPS PBC connection procedure, press
and hold the button for between five and ten
seconds. Press the PBC button on your wireless
clients in the coverage area within two minutes to
enable them to join the wireless network.
Reset Use this button to reboot or reset your CVE-30360.
Press the button and hold it for less than five
seconds to reboot the CVE-30360. The CVE-30360
restarts, using your existing settings.
Press the button and hold it for more than ten
seconds to delete all user-configured settings and
restart the CVE-30360 using its factory default
settings.
USB Insert USB disk to share files.
INTRODUCTION
Page 18
18
HITRON CVE-30360 USER’S GUIDE
TABLE 1: Hardware Connections
LAN1 Use these ports to connect your computers and other
LAN2
LAN3
LAN4
LINE 1 Use these ports to connect your analog phones for VoIP
LINE 2
CABLE Use this to connect to the Internet via an F-type RF
POWER Use this to connect to the 12v/2A power adapter that
network devices, using Category 5 or 6 Ethernet cables
with RJ45 connectors.
services, using cables with RJ11 connectors.
cable.
came with your CVE-30360.
NEVER use another power adapter with
your CVE-30360. Doing so could harm
your CVE-30360.
ON/OFF Use this button to turn your CVE-30360 on or off.
To turn the CVE-30360 on, press and hold the ON/
OFF button for less than 1 second.
To turn the CVE-30360 off, press and hold the ON/
OFF button for 1~2 seconds.
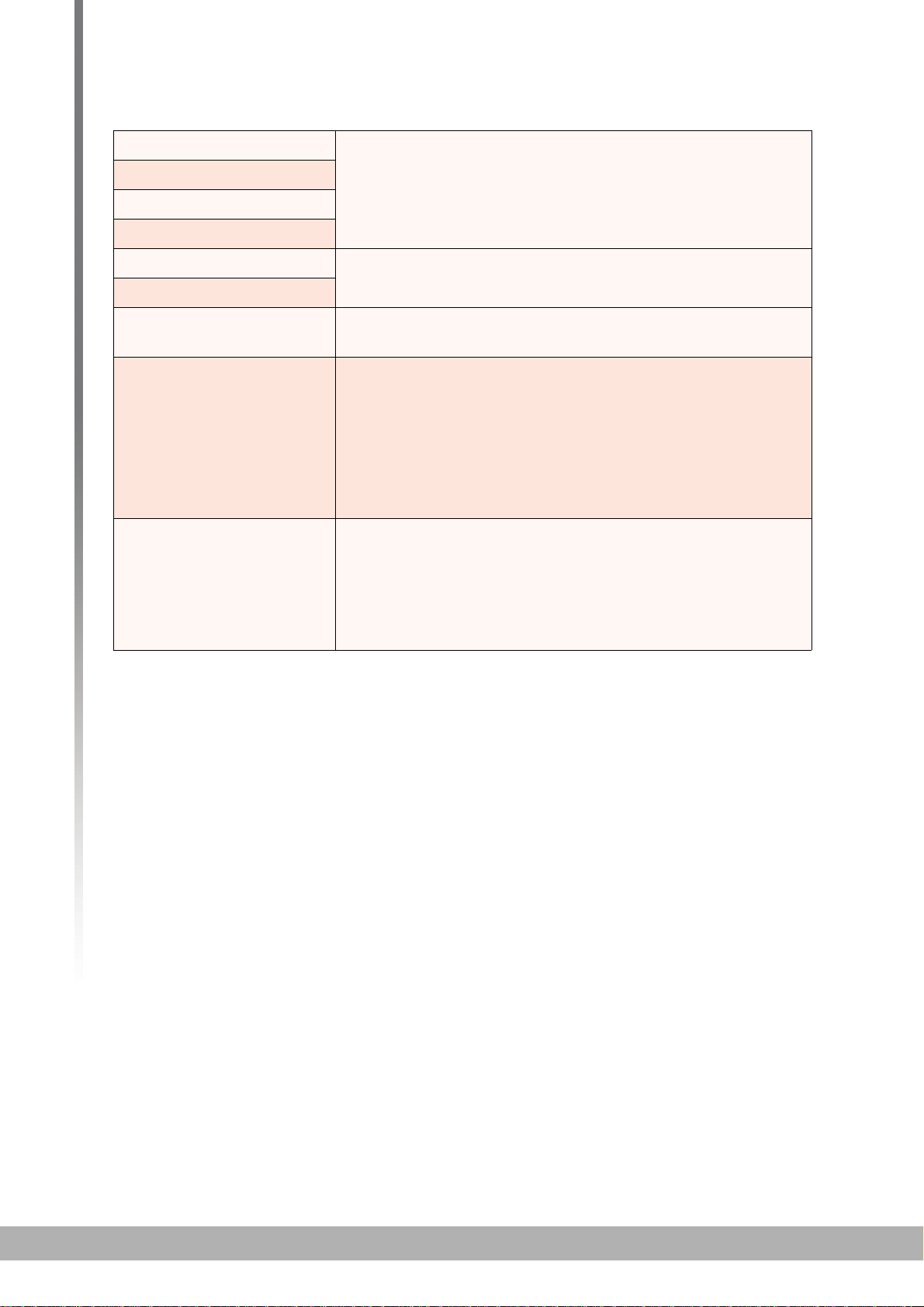
1.3 LEDS
This section describes the CVE-30360’s LEDs (lights).
INTRODUCTION
Page 19
HITRON CVE-30360 USER’S GUIDE
FIGURE 3: LEDs
19
TABLE 2: LEDs
LED STATUS DESCRIPTION
LINE 1
LINE 2
WIRELESS Off No data is being transmitted or received over the
USB On Valid USB connection status.
Off Your service plan does not include voice service.
NOTE: The number of LINE LEDs that light up
depends on your voice service plan.
Blinking A telephone is connected to the relevant Line port,
and is off-hook.
On Your service plan includes voice service.
NOTE: The number of LINE LEDs that light up
depends on your voice service plan.
wireless network.
Blinking Data is being transmitted or received over the
wireless network.
Off No USB is connected or invalid USB connection
status.
INTRODUCTION
Page 20
20
HITRON CVE-30360 USER’S GUIDE
TABLE 2: LEDs
ETH Off No device is connected to any LAN port.
Blinking A device is connected to a LAN port via a fast
Ethernet link, and is transmitting or receiving data.
On A device is connected to a LAN port via a fast
ethernet link, but is not transmitting or receiving
data.
Status Blinking The CVE-30360’s cable modem is registering with
the service provider.
On The CVE-30360’s cable modem has successfully
registered with the service provider.
US Blinking The CVE-30360 is searching for an upstream
frequency on the CATV connection.
On The CVE-30360 has successfully located and
locked onto an upstream frequency on the CATV
connection.
DS Blinking The CVE-30360 is searching for a downstream
frequency on the CATV connection.
On The CVE-30360 has successfully located and
locked onto a downstream frequency on the CATV
connection.
Power On The CVE-30360 is receiving power.
Off The CVE-30360 is not receiving power.
When you turn on the CVE-30360, the LEDs light up in the following order:
Power
US
DS
Status
The ETH 1~4 LEDs light up as soon as there is activity on the relevant port, the
LINE 1~2 ports light up if your service contract includes voice service (the
number of LEDs that lights up depends on your service plan), USB LED lights
up if your have valid USB connection, and the WIRELESS LED lights up once
the wireless network is ready.
1.4 IP ADDRESS SETUP
Before you log into the CVE-30360’s GUI, your computer’s IP address must be in the
same subnet as the CVE-30360. This allows your computer to communicate with the
CVE-30360.
NOTE: See IP Addresses and Subnets on page 25 for background information.
INTRODUCTION
Page 21

HITRON CVE-30360 USER’S GUIDE
The CVE-30360 has a built-in DHCP server that, when active, assigns IP addresses
to computers on the LAN. When the DHCP server is active, you can get an IP
address automatically. The DHCP server is active by default.
If your computer is configured to get an IP address automatically, or if you are not
sure, try to log in to the CVE-30360 (see Logging into the CVE-30360 on page 13).
If the login screen displays, your computer is already configured correctly.
If the login screen does not display, either the CVE-30360’s DHCP server is not
active or your computer is not configured correctly. Follow the procedure in
Manual IP Address Setup on page 12 and set your computer to get an IP
address automatically. Try to log in again. If you cannot log in, follow the manual
IP address setup procedure again, and set a specific IP address as shown. Try
to log in again.
NOTE: If you still cannot see the login screen, your CVE-30360’s IP settings may
have been changed from their defaults. If you do not know the CVE-30360’s
new address, you should return it to its factory defaults. See Resetting the
CVE-30360 on page 14. Bear in mind that ALL user-configured settings are
lost.
21
1.4.1 MANUAL IP ADDRESS SETUP
By default, your CVE-30360’s local IP address is 192.168.0.1. If your CVE-30360 is
using the default IP address, you should set your computer’s IP address to be
between 192.168.0.2 and 192.168.0.254.
NOTE: If your CVE-30360 DHCP server is active, set your computer to get an IP
address automatically in step 5. The CVE-30360 assigns an IP address to
your computer. The DHCP server is active by default.
Take the following steps to manually set up your computer’s IP address to connect to
the CVE-30360:
NOTE: This example uses Windows XP; the procedure for your operating system
may be different.
1 Click Start, then click Control Panel.
2 In the window that displays, double-click Network Connections.
3 Right-click your network connection (usually Local Area Connection) and click
Properties.
4 In the General tab’s This connection uses the following items list, scroll
down and select Internet Protocol (TCP/IP). Click Properties.
5 You can get an IP address automatically, or specify one manually:
INTRODUCTION
Page 22
22
HITRON CVE-30360 USER’S GUIDE
If your CVE-30360’s DHCP server is active, select Get an IP address
automatically.
If your CVE-30360’s DHCP server is not active, select Use the following IP
address. In the IP address field, enter a value between 192.168.0.2 and
192.168.0.254 (default). In the Subnet mask field, enter 255.255.255.0
(default).
NOTE: If your CVE-30360 is not using the default IP address, enter an IP address
and subnet mask that places your computer in the same subnet as the CVE-
30360.
6 Click OK. The Internet Protocol (TCP/IP) window closes. In the Local Area
Connection Properties window, click OK.
Your computer now obtains an IP address from the CVE-30360, or uses the IP
address that you specified, and can communicate with the CVE-30360.
1.5 LOGGING INTO THE CVE-30360
Take the following steps to log into the CVE-30360’s GUI.
NOTE: You can log into the CVE-30360’s GUI via the wireless interface. However, it
is strongly recommended that you configure the CVE-30360 via a wired
connection on the LAN.
1 Open a browser window.
2 Enter the CVE-30360’s IP address (default 192.168.0.1) in the URL bar. The
Login screen displays.
FIGURE 4: Login
3 Enter the Username and Password. The default login username is admin, and
the default password is password.
INTRODUCTION
Page 23
HITRON CVE-30360 USER’S GUIDE
NOTE: The Username and Password are case-sensitive; “admin” is not the same as
“Admin”.
4 Click Login. The System Info screen displays (see The System Info Screen on
page 30).
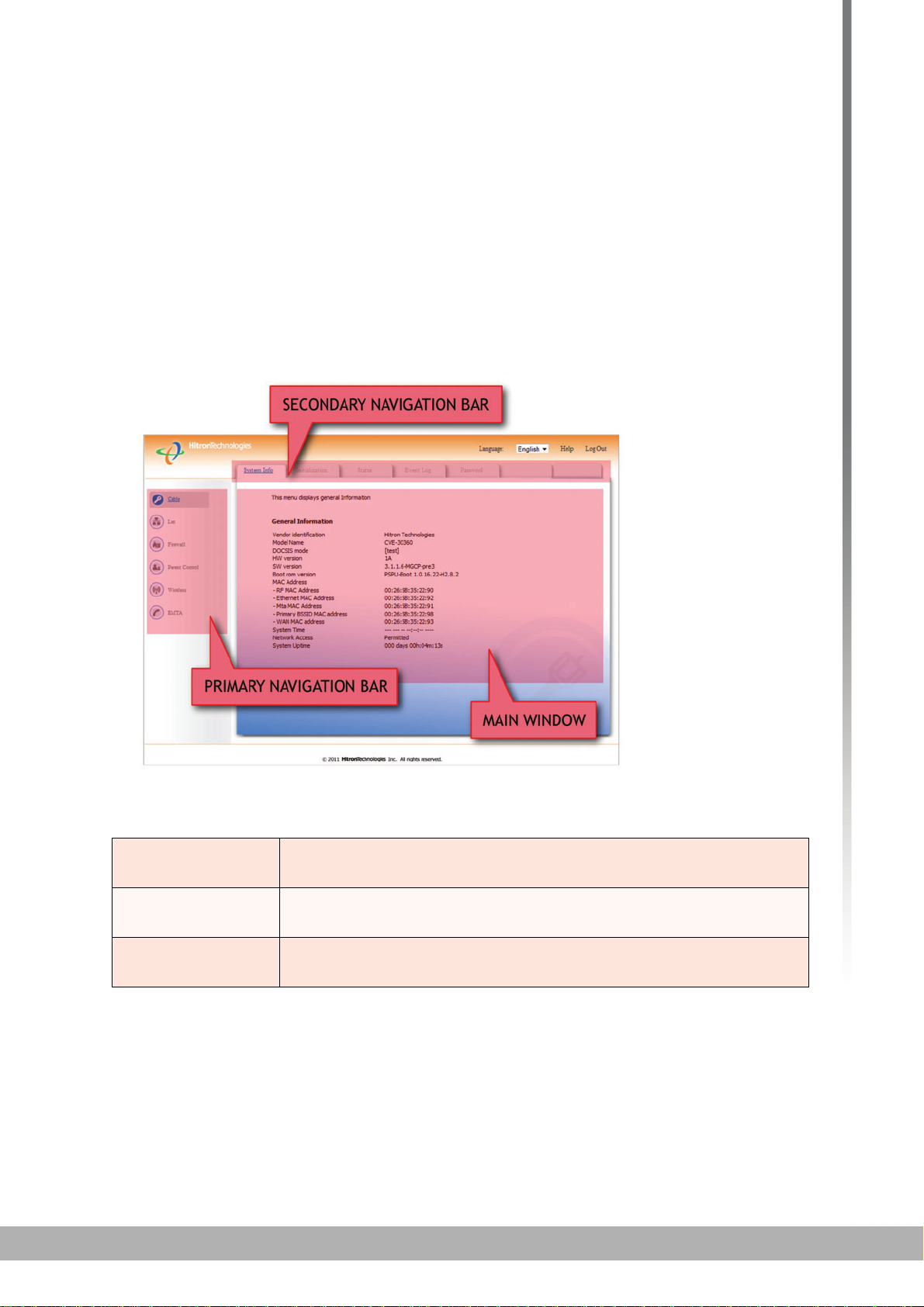
1.6 GUI OVERVIEW
This section describes the CVE-30360’s GUI.
FIGURE 5: GUI Overview
23
TABLE 3: GUI Overview
Primary
Navigation Bar
Secondary
Navigation Bar
Main Window Use this section to read information about your CVE-30360’s
Use this section to move from one part of the GUI to another.
Use this section to move from one related screen to another.
configuration, and make configuration changes.
1.7 RESETTING THE CVE-30360
When you reset the CVE-30360 to its factory defaults, all user-configured settings are
lost, and the CVE-30360 is returned to its initial configuration state.
There are two ways to reset the CVE-30360:
INTRODUCTION
Page 24

24
HITRON CVE-30360 USER’S GUIDE
Press the RESET button on the CVE-30360, and hold it in for ten seconds or
longer.
Click LAN > Backup. In the screen that displays, click the Factory Reset
button.
The CVE-30360 turns off and on again, using its factory default settings.
NOTE: Depending on your CVE-30360’s previous configuration, you may need to re-
configure your computer’s IP settings; see IP Address Setup on page 11.
INTRODUCTION
Page 25

25
CABLE
2
CABLE
This chapter describes the screens that display when you click Cable in the toolbar.
2.1 CABLE OVERVIEW
This section describes some of the concepts related to the Cable screens.
2.1.1 DOCSIS
The Data Over Cable Service Interface Specification (DOCSIS) is a
telecommunications standard that defines the provision of data services) Internet
access) over a traditional cable TV (CATV) network.
Your CVE-30360 supports DOCSIS version 3.0.
2.1.2 IP ADDRESSES AND SUBNETS
Every computer on the Internet must have a unique Internet Protocol (IP) address.
The IP address works much like a street address, in that it identifies a specific
location to which information is transmitted. No two computers on a network can have
the same IP address.
2.1.2.1 IP ADDRESS FORMAT
IP addresses consist of four octets (8-bit numerical values) and are usually
represented in decimal notation, for example 192.168.1.1. In decimal notation, this
means that each octet has a minimum value of 0 and a maximum value of 255.
An IP address carries two basic pieces of information: the “network number” (the
address of the network as a whole, analogous to a street name) and the “host ID”
(analogous to a house number) which identifies the specific computer (or other
network device).
2.1.2.2 IP ADDRESS ASSIGNMENT
IP addresses can come from three places:
The Internet Assigned Numbers Agency (IANA)
Page 26
26
HITRON CVE-30360 USER’S GUIDE
Your Internet Service Provider
You (or your network devices)
IANA is responsible for IP address allocation on a global scale, and your ISP assigns
IP addresses to its customers. You should never attempt to define your own IP
addresses on a public network, but you are free to do so on a private network.
In the case of the CVE-30360:
The public network (Wide Area Network or WAN) is the link between the cable
(CATV) connector and your Internet Service Provider. Your CVE-30360’s IP
address on this network is assigned by your service provider.
The private network (in routing mode - see Routing Mode on page 28) is your
Local Area Network (LAN) and Wireless Local Area Network (WLAN), if
enabled. You are free to assign IP addresses to computers on the LAN and
WLAN manually, or to allow the CVE-30360 to assign them automatically via
DHCP (Dynamic Host Configuration Protocol). IANA has reserved the following
blocks of IP addresses to be used for private networks only:
TABLE 4: Private IP Address Ranges
FROM... ...TO
10.0.0.0 10.255.255.255
172.16.0.0 172.31.255.255
192.168.0.0 192.168.255.255
If you assign addresses manually, they must be within the CVE-30360’s LAN
subnet.
2.1.2.3 SUBNETS
A subnet (short for sub-network) is, as the name suggests, a separate section of a
network, distinct from the main network of which it is a part. A subnet may contain all
of the computers at one corporate local office, for example, while the main network
includes several offices.
In order to define the extent of a subn
a subnet mask is used. This “masks” the part of the IP address that refers to the main
network, leaving the part of the IP address that refers to the sub-network.
Each subnet mask has 32 bits (binary digits), as does each IP address:
et, and to differentiate it from the main network,
A binary value of 1 in the subnet mask indicates that the corresponding bit in the
IP address is part of the main network.
A binary value of 0 in the subnet mask indicates that the corresponding bit in the
IP address is part of the sub-network.
CABLE
Page 27
27
HITRON CVE-30360 USER’S GUIDE
For example, the following table shows the IP address of a computer (192.168.1.1)
expressed in decimal and binary (each cell in the table indicates one octet):
TABLE 5: IP Address: Decimal and Binary
192 168 0 1
11000000 10101000 00000000 00000001
The following table shows a subnet mask that “masks” the first twenty-four bits of the
IP address, in both its decimal and binary notation.
TABLE 6: Subnet Mask: Decimal and Binary
255 255 255 0
11111111 11111111 11111111 00000000
This shows that in this subnet, the first three octets (192.168.1, in the example IP
address) define the main network, and the final octet (1, in the example IP address)
defines the computer’s address on the subnet.
The decimal and binary notations give us the two common ways to write a subnet
mask:
Decimal: the subnet mask is written in the same fashion as the IP address:
255.255.255.0, for example.
Binary: the subnet mask is indicated after the IP address (preceded by a forward
slash), specifying the number of binary digits that it masks. The subnet mask
255.255.255.0 masks the first twenty-four bits of the IP address, so it would be
written as follows: 192.168.1.1/24.
2.1.3 DHCP
The Dynamic Host Configuration Protocol, or DHCP, defines the process by which IP
addresses can be assigned to computers and other networking devices
automatically, from another device on the network. This device is known as a DHCP
server, and provides addresses to all the DHCP client devices.
In order to receive an IP address via DHCP, a computer must first request one from
the DHCP server (this is a broadcast request, meaning that it is sent out to the whole
network, rather than just one IP address). The DHCP server hears the requests, and
responds by assigning an IP address to the computer that requested it.
If a computer is not configured to request an IP address via DHCP, you must
configure an IP address manually if you want to access other computers and devices
on the network. See IP Address Setup on page 20 for more information.
By default, the CVE-30360 is a DHCP client on the WAN (the CATV connection). It
broadcasts an IP address over the cable network, and receives one from the service
provider. By default, the CVE-30360 is a DHCP server on the LAN; it provides IP
addresses to computers on the LAN which request them.
CABLE
Page 28
28
HITRON CVE-30360 USER’S GUIDE
2.1.4 DHCP LEASE
“DHCP lease” refers to the length of time for which a DHCP server allows a DHCP
client to use an IP address. Usually, a DHCP client will request a DHCP lease
renewal before the lease time is up, and can continue to use the IP address for an
additional period. However, if the client does not request a renewal, the DHCP server
stops allowing the client to use the IP address.
This is done to prevent IP addresses from being used up by computers that no longer
require them, since the pool of available IP addresses is finite.
2.1.5 MAC ADDRESSES
Every network device possesses a Media Access Control (MAC) address. This is a
unique alphanumeric code, given to the device at the factory, which in most cases
cannot be changed (although some devices are capable of “MAC spoofing”, where
they impersonate another device’s MAC address).
MAC addresses are the most reliable way of identifying network devices, since IP
addresses tend to change over time (whether manually altered, or updated via
DHCP).
Each MAC address displays as six groups of two hexadecimal digits separated by
colons (or, occasionally, dashes) for example 00:AA:FF:1A:B5:74.
NOTE: Each group of two hexadecimal digits is known as an “octet”, since it
represents eight bits.
Bear in mind that a MAC address does not precisely represent a computer on your
network (or elsewhere), it represents a network device, which may be part of a
computer (or other device). For example, if a single computer has an Ethernet card
(to connect to your CVE-30360 via one of the LAN ports) and also has a wireless
card (to connect to your CVE-30360 over the wireless interface) the MAC addresses
of the two cards will be different. In the case of the CVE-30360, each internal module
(cable modem module, Ethernet module, wireless module, etc.) possesses its own
MAC address.
2.1.6 ROUTING MODE
When your CVE-30360 is in routing mode, it acts as a gateway for computers on the
LAN to access the Internet. The service provider assigns an IP address to the CVE30360 on the WAN, and all traffic for LAN computers is sent to that IP address. The
CVE-30360 assigns private IP addresses to LAN computers (when DHCP is active),
and transmits the relevant traffic to each private IP address.
NOTE: When DHCP is not active on the CVE-30360 in routing mode, each computer
on the LAN must be assigned an IP address in the CVE-30360’s subnet
manually.
CABLE
Page 29

29
HITRON CVE-30360 USER’S GUIDE
When the CVE-30360 is not in routing mode, the service provider assigns an IP
address to each computer connected to the CVE-30360 directly. The CVE-30360
does not perform any routing operations, and traffic flows between the computers and
the service provider.
Routing mode is not user-configurable; it is specified by the service provider in the
CVE-30360’s configuration file.
2.1.7 CONFIGURATION FILES
The CVE-30360’s configuration (or config) file is a document that the CVE-30360
obtains automatically over the Internet from the service provider’s server, which
specifies the settings that the CVE-30360 should use. It contains a variety of settings
that are not present in the user-configurable Graphical User Interface (GUI) and can
be specified only by the service provider.
2.1.8 DOWNSTREAM AND UPSTREAM TRANSMISSIONS
The terms “downstream” and “upstream” refer to data traffic flows, and indicate the
direction in which the traffic is traveling. “Downstream” refers to traffic from the
service provider to the CVE-30360, and “upstream” refers to traffic from the CVE30360 to the service provider.
2.1.9 CABLE FREQUENCIES
Just like radio transmissions, data transmissions over the cable network must exist
on different frequencies in order to avoid interference between signals.
The data traffic band is separate from the TV band, and each data channel is
separate from other data channels.
2.1.10 MODULATION
Transmissions over the cable network are based on a strong, high frequency periodic
waveform known as the “carrier wave.” This carrier wave is so called because it
“carries” the data signal. The data signal itself is defined by variations in the carrier
wave. The process of varying the carrier wave (in order to carry data signal
information) is known as “modulation.” The data signal is thus known as the
“modulating signal.”
Cable transmissions use a variety of methods to perform modulation (and the
“decoding” of the received signal, or “demodulation”). The modulation methods
defined in DOCSIS 3 are as follows:
QPSK: Quadrature Phase-Shift Keying
QAM: Quadrature Amplitude Modulation
QAM TCM: Trellis modulated Quadrature Amplitude Modulation
CABLE
Page 30
30
HITRON CVE-30360 USER’S GUIDE
In many cases, a number precedes the modulation type (for example 16 QAM). This
number refers to the complexity of modulation. The higher the number, the more data
can be encoded in each symbol.
NOTE: In modulated signals, each distinct modulated character (for example, each
audible tone produced by a modem for transmission over telephone lines) is
known as a symbol.
Since more information can be represented by a single character, a higher number
indicates a higher data transfer rate.
2.1.11 TDMA, FDMA AND SCDMA
Time Division Multiple Access (TDMA), Frequency Division Multiple Access (FDMA)
and Synchronous Code Division Multiple Access (SCDMA) are channel access
methods that allow multiple users to share the same frequency channel.
TDMA allows multiple users to share the same frequency channel by splitting
transmissions by time. Each user is allocated a number of time slots, and
transmits during those time slots.
FDMA allows multiple users to share the same frequency channel by assigning a
frequency band within the existing channel to each user.
SCDMA allows multiple users to share the same frequency channel by assigning
a unique orthogonal code to each user.
2.2 THE SYSTEM INFO SCREEN
Use this screen to see general information about your CVE-30360’s hardware, its
software, and its connection to the Internet.
NOTE: Most of the information that displays in this screen is for troubleshooting
purposes only. However, you may need to use the MAC Address information
when setting up your network.
Click Cable > System Info. The following screen displays.
CABLE
Page 31

31
HITRON CVE-30360 USER’S GUIDE
FIGURE 6: The Cable > System Info Screen
The following table describes the labels in this screen.
TABLE 7: The Cable > System Info Screen
General Information
Vendor
Identification
Model Name This displays the device’s model name (CVE-30360).
DOCSIS Mode This displays the version of the Data Over Cable Service
HW Version This displays the version number of the CVE-30360’s
SW Version This displays the version number of the software that
Boot ROM Version This displays the version number of the program that
MAC Address
RF MAC Address This displays the Media Access Control (MAC) address of
This displays the name of the company that supplied the
CVE-30360.
Interface Specification (DOCSIS) standard to which the
CVE-30360 complies.
physical hardware.
controls the CVE-30360.
controls the CVE-30360’s boot procedure (in which the
main software is loaded).
the CVE-30360’s RF module. This is the module that
connects to the Internet through the CATV connection.
Ethernet MAC
Address
WAN MAC Address
(in Routing Mode
This displays the Media Access Control (MAC) address of
the CVE-30360’s Ethernet module. This is the module to
which you connect through the LAN ports.
This displays the Media Access Control (MAC) address of
the module that connects to the Internet through the CATV
connection when the CVE-30360 is in routing mode.
CABLE
Page 32

32
HITRON CVE-30360 USER’S GUIDE
TABLE 7: The Cable > System Info Screen (continued)
Primary BSSID
MAC Address
System Time This displays the current date and time.
System Uptime This displays the number of days, hours, minutes and
Network Access This field displays when you are connected to your service
This displays the Media Access Control (MAC) address of
the CVE-30360’s Basic Service Set IDentifier (BSSID).
This is the MAC address of the wireless module to which
wireless clients connect.
NOTE: You may have additional BSSIDs, depending on
your contract with your service provider.
seconds since the CVE-30360 was last switched on or
rebooted.
provider, and shows whether or not your service provider
allows you to access the Internet over the CATV
connection.
Permitted displays if you can access the Internet.
Denied displays if you cannot access the Internet.
2.3 THE INITIALIZATION SCREEN
This screen displays the steps successfully taken to connect to the Internet over the
CATV connection.
Use this screen for troubleshooting purposes to ensure that the CVE-30360 has
successfully connected to the Internet; if an error has occurred you can identify the
stage at which the failure occurred.
NOTE: This screen displays when you first log in to the CVE-30360.
Click Cable > Initialization. The following screen displays.
CABLE
Page 33

33
HITRON CVE-30360 USER’S GUIDE
FIGURE 7: The Cable > Initialization Screen
For each step:
Process displays when the CVE-30360 is attempting to complete a connection
step.
Success displays when the CVE-30360 has completed a connection step.
2.4 THE STATUS SCREEN
Use this screen to discover information about:
The nature of the upstream and downstream connection between the CVE-
30360 and the device to which it is connected through the CATV interface.
IP details of the CVE-30360’s WAN connection.
You can also configure the CVE-30360’s downstream center frequency.
Click Cable > Sta
tus. The following screen displays.
CABLE
Page 34

34
HITRON CVE-30360 USER’S GUIDE
FIGURE 8: The Cable > Status Screen
The following table describes the labels in this screen.
TABLE 8: The Cable > St atus Screen
Network Access This displays whether or not your service provider allows
you to access the Internet over the CATV connection.
Permitted displays if you can access the Internet.
Denied displays if you cannot access the Internet.
Downstream
NOTE: The downstream signal is the signal transmitted to the CVE-30360.
CABLE
Page 35

35
HITRON CVE-30360 USER’S GUIDE
TABLE 8: The Cable > Status Screen (continued)
Frequency to Tune to This displays the current center frequency in Hertz (Hz)
over which data is transmitted to the CVE-30360 over
the CATV interface. This is the frequency to which the
CVE-30360 is locked in; it will only scan for another
frequency if this frequency becomes unavailable.
If you want the CVE-30360 to attempt to connect at a
different frequency, enter it in the field and click Apply.
NOTE: Do not change the frequency unless you have a
good reason to do so.
Scanning Start
Frequency
Channel Frequency This displays the actual frequency of each downstream
Modulation This displays the type of modulation that each
Signal Strength This displays the power of the signal of each
Signal Noise Ratio This displays the Signal to Noise Ratio (SNR) of each
Upstream
NOTE: The upstream signal is the signal transmitted from the CVE-30360.
Channel ID This displays the ID number of each channel on which
Upstream Frequency This displays the frequency in Herz (Hz) of each
This displays the frequency in Hertz (Hz) at which the
CVE-30360 begins scanning for a connection over the
CATV interface (if a frequency is not already locked in).
data channel to which the CVE-30360 is connected.
downstream channel uses. Possible modulation types
downstream data channel to which the CVE-30360 is
connected, in dBmV (decibels above/below 1 millivolt).
downstream data channel to which the CVE-30360 is
connected, in dB (decibels).
the upstream signal is transmitted.
upstream data channel to which the CVE-30360 is
connected.
Upstream Bandwidth This displays the bandwidth of each upstream data
channel to which the CVE-30360 is connected (in Hertz).
SCDMA Mode This displays the Synchronous Code Division Multiple
Access (SCDMA) mode of each channel on which the
upstream signal is transmitted.
Transmission Signal
Strength
Cable Modem IP Information
IP Address This displays the CVE-30360’s WAN IP address. This IP
Subnet Mask This displays the CVE-30360’s WAN subnet mask.
This displays the transmitted power of the signal of each
upstream data channel to which the CVE-30360 is
connected, in dBmV (decibels above/below 1 millivolt).
address is automatically assigned to the CVE-30360
CABLE
Page 36

36
HITRON CVE-30360 USER’S GUIDE
TABLE 8: The Cable > Status Screen (continued)
Gateway IP This displays the IP address of the device to which the
CVE-30360 is connected over the CATV interface.
DHCP Lease Time This displays the time that elapses before your device’s
IP address lease expires, and a new IP address is
assigned to it by the DHCP server.
System Time This displays the current date and time.
2.5 THE PASSWORD SCREEN
Use this screen to change the password with which you log in to the CVE-30360.
NOTE: If you forget your password, you will need to reset the CVE-30360 to its
factory defaults.
Click Cable > Password. The following screen displays.
FIGURE 9: The Cable > Password Screen
The following table describes the labels in this screen.
TABLE 9: The Cable > Password Screen
Enter Current Password Enter the password with which you currently log into the
CVE-30360
Enter New Password Enter and re-enter the password you want to use to log
Re-Enter New Password
into the CVE-30360.
Password Idle Time Enter the number of minutes of inactivity after which you
should be automatically logged out of the CVE-30360.
Once this period elapses, you will need to log in again.
Apply Click this to save your changes to the fields in this
screen.
CABLE
Page 37

37
HITRON CVE-30360 USER’S GUIDE
TABLE 9: The Cable > Password Screen (continued)
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
CABLE
Page 38

38
HITRON CVE-30360 USER’S GUIDE
CABLE
Page 39

39
LAN
3
LAN
This chapter describes the screens that display when you click LAN in the toolbar.
3.1 LAN OVERVIEW
This section describes some of the concepts related to the LAN screens.
3.1.1 LOCAL AREA NETWORKS
A Local Area Network (LAN) is a network of computers and other devices that usually
occupies a small physical area (a single building, for example). Your CVE-30360’s
LAN consists of all the computers and other networking devices connected to the
LAN 1~4 ports. This is your private network (in routing mode - see Routing Mode on
page 28).
The LAN is a separate network from the Wide Area Network (WAN). In the case of
the CVE-30360, the WAN refers to all computers and other devices available on the
cable (CATV) connection.
By default, computers on the WAN cannot identify individual computers on the LAN;
they can see only the CVE-30360. The CVE-30360 handles routing to and from
individual computers on the LAN.
3.1.2 LAN IP ADDRESSES AND SUBNETS
IP addresses on the LAN are controlled either by the CVE-30360’s built-in DHCP
server (see DHCP on page 27), or by you (when you manually assign IP addresses
to your computers).
For more information about IP addresses and subnets in general, see IP Addresses
and Subnets on page 25.
Page 40

40
HITRON CVE-30360 USER’S GUIDE
3.1.3 DOMAIN SUFFIX
A domain is a location on a network, for instance example.com. On the Internet,
domain names are mapped to the IP addresses to which they should refer by the
Domain Name System. This allows you to enter “www.example.com” into your
browser and reach the correct place on the Internet even if the IP address of the
website’s server has changed.
Similarly, the CVE-30360 allows you to define a Domain Suffix to the LAN. When
you enter the domain suffix into your browser, you can reach the CVE-30360 no
matter what IP address it has on the LAN.
3.1.4 DEBUGGING (PING AND TRACEROUTE)
The CVE-30360 provides a couple of tools to allow you to perform network
diagnostics on the LAN:
Ping: this tool allows you to enter an IP address and see if a computer (or other
network device) responds with that address on the network. The name comes
from the pulse that submarine SONAR emits when scanning for underwater
objects, since the process is rather similar. You can use this tool to see if an IP
address is in use, or to discover if a device (whose IP address you know) is
working properly.
Traceroute: this tool allows you to see the route taken by data packets to get
from the CVE-30360 to the destination you specify. You can use this tool to
solve routing problems, or identify firewalls that may be blocking your access to
a computer or service.
3.2 THE LAN IP SCREEN
Use this screen to:
Configure the CVE-30360’s LAN IP address, subnet mask and domain suffix
Configure the CVE-30360’s internal DHCP server
See information about the network devices connected to the CVE-30360 on the
LAN.
Click LAN > LAN IP. The following screen displays.
LAN
Page 41

41
HITRON CVE-30360 USER’S GUIDE
FIGURE 10: The LAN > LAN IP Screen
The following table describes the labels in this screen.
TABLE 10: The LAN > LAN IP Screen
WAN Information
WAN Address This field displays the CVE-30360’s IP address on the
WAN (Wide Area Network) interface.
Subnet Mask This field displays the CVE-30360’s WAN subnet mask.
Gateway Address This field displays the address of the device on the WAN
to which the CVE-30360 is connected.
DNS Server This field displays the Domain Name Servers that the
CVE-30360 uses to resolve domain names into IP
addresses.
Private LAN IP Setting
IP Address Use this field to define the IP address of the CVE-30360
on the LAN.
Subnet Mask Use this field to define the LAN subnet. Use dotted
decimal notation (for example, 255.255.255.0).
LAN
Page 42

42
HITRON CVE-30360 USER’S GUIDE
TABLE 10: The LAN > LAN IP Screen (continued)
Domain Suffix Use this field to define the domain that you can enter into a
Web browser (instead of an IP address) to reach the CVE30360 on the LAN.
NOTE: The Domain Suffix is hitronhub.home by default.
Private LAN DHCP Setting
Enable LAN DHCP Select this if you want the CVE-30360 to provide IP
addresses to network devices on the LAN automatically.
Deselect this if you already have a DHCP server on your
LAN, or if you wish to assign IP addresses to your
computers and other network devices manually.
Lease Time Use this field to define the time after which the CVE-30360
renews the IP addresses of all the network devices
connected to the CVE-30360 on the LAN (when DHCP is
enabled).
DHCP Start IP Use this field to specify the IP address at which the CVE-
30360 begins assigning IP addresses to devices on the
LAN (when DHCP is enabled).
DHCP End IP Use this field to specify the IP address at which the CVE-
30360 stops assigning IP addresses to devices on the
LAN (when DHCP is enabled).
NOTE: Devices requesting IP addresses once the DHCP
pool is exhausted are not assigned an IP address.
Host Name This displays the name of each network device connected
on the LAN.
IP Address This displays the IP address of each network device
connected on the LAN.
MAC Address This displays the Media Access Control (MAC) address of
each network device connected on the LAN.
Type This displays whether the device’s IP address was
assigned by DHCP (DHCP-IP), or self-assigned.
Interface This displays whether the device is connected on the LAN
(Ethernet) or the WLAN (Wireless(x), where x denotes
the wireless mode; b, g or n).
Apply Click this to save your changes to the fields in this screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this screen.
3.3 THE SWITCH SETUP SCREEN
Use this screen to see information about the data rate and flow of each of the CVE30360’s LAN ports, and to activate or deactivate each port.
LAN
Page 43

43
HITRON CVE-30360 USER’S GUIDE
Click LAN > Switch Setup. The following screen displays.
FIGURE 11: The LAN > Switch Setup Screen
The following table describes the labels in this screen.
TABLE 11: The LAN > Switch Setup Screen
Port This displays the LAN port number.
Speed This displays the maximum achievable data speed in
megabits per second (MBPS).
Duplex
Active
Apply Click this to save your changes to the fields in this
Cancel Click this to return the fields in this screen to their last-
Help Click this to see information about the fields in this
This displays Full when data can flow inbetween the
CVE-30360 and the connected device in both
directions simultaneously.
This displays Half when data can flow inbetween the
CVE-30360 and the connected device in only one
direction at a time.
Select a Port’s checkbox to enable communications
between the CVE-30360 and devices connected to
the port.
Deselect a Port’s checkbox if you do not want to
exchange data between the CVE-30360 and devices
connected to the port.
screen.
saved values without saving your changes.
screen.
3.4 THE DEBUG SCREEN
Use this screen to perform ping and traceroute tests on IP addresses or URLs.
Click LAN > Debug. The following screen displays.
LAN
Page 44

44
HITRON CVE-30360 USER’S GUIDE
FIGURE 12: The LAN > Debug Screen
The following table describes the labels in this screen.
TABLE 12: The LAN > Debug Screen
IP/URL Enter the IP address or URL that you want to test.
Method Select the type of test that you want to run on the IP/
URL that you specified.
Run Click this to perform the test.
Help Click this to see information about the fields in this
screen.
3.5 THE BACKUP SCREEN
Use this screen to back up your CVE-30360’s settings to your computer, to load
settings from a backup you created earlier, to reboot your CVE-30360, or to return it
to its factory default settings.
Click LAN > Backup. The following screen displays.
FIGURE 13: The LAN > Backup Screen
LAN
Page 45

45
HITRON CVE-30360 USER’S GUIDE
The following table describes the labels in this screen.
TABLE 13: The LAN > Backup Screen
Backup/Restore Setting
Backup Settings
Locally
Restore Settings
Locally
Reboot/Factory Reset
Reboot Click this to restart your CVE-30360.
Factory Reset Click this to return your CVE-30360 to its factory default
Help Click this to see information about the fields in this
Click this to create a backup of all your CVE-30360’s
settings on your computer.
Use these fields to return your CVE-30360’s settings to
those specified in a backup that you created earlier.
Click Choose to select a backup, then click Restore to
return your CVE-30360’s settings to those specified in
the backup.
settings.
NOTE: When you do this, all your user-configured
settings are lost, and cannot be retrieved.
screen.
LAN
Page 46

46
HITRON CVE-30360 USER’S GUIDE
LAN
Page 47

47
FIREWALL
4
FIREWALL
This chapter describes the screens that display when you click Firewall in the
toolbar.
4.1 FIREWALL OVERVIEW
This section describes some of the concepts related to the Firewall screens.
4.1.1 FIREWALL
The term “firewall” comes from a construction technique designed to prevent the
spread of fire from one room to another. Similarly, your CVE-30360’s firewall
prevents intrusion attempts and other undesirable activity originating from the WAN,
keeping the computers on your LAN safe. You can also use filtering techniques to
specify the computers and other devices you want to allow on the LAN, and prevent
certain traffic from going from the LAN to the WAN.
4.1.2 INTRUSION DETECTION SYSTEM
An intrusion detection system monitors network activity, looking for policy violations,
and malicious or suspicious activity.
4.1.3 PING
The CVE-30360 allows you to use the ping utility on the LAN (in the LAN > Debug
screen) and also on the WAN (in the Firewall > Firewall Options screen). For more
information, see Debugging (Ping and Traceroute) on page 40.
4.1.4 MAC FILTERING
Every networking device has a unique Media Access Control (MAC) address that
identifies it on the network. When you enable MAC address filtering on the CVE30360’s firewall, you can set up a list of MAC addresses, and then specify whether
you want to:
Page 48

48
HITRON CVE-30360 USER’S GUIDE
Deny the devices on the list access to the CVE-30360 and the network (in which
case all other devices can access the network)
or
Allow the devices on the list to access the network (in which case no other
devices can access the network)
4.1.5 IP FILTERING
IP filtering allows you to prevent computers on the LAN from sending certain types of
data to the WAN. You can use this to prevent unwanted outgoing communications.
Specify the IP address of the computer on the LAN from which you want to prevent
communications, and specify the port range of the communications you want to
prevent. The CVE-30360 discards outgoing data packets that match the criteria you
specified.
4.1.6 PORT FORWARDING
Port forwarding allows a computer on your LAN to receive specific communications
from the WAN. Typically, this is used to allow certain applications (such as gaming)
through the firewall, for a specific computer on the LAN. Port forwarding is also
commonly used for running a public HTTP server from a private network.
You can set up a port forwarding rule for each application for which you want to open
ports in the firewall. When the CVE-30360 receives incoming traffic from the WAN
with a destination port that matches a port forwarding rule, it forwards the traffic to the
LAN IP address and port number specified in the port forwarding rule.
NOTE: For information on the ports you need to open for a particular application,
consult that application’s documentation.
NOTE: This feature is not available when the DS-lite function is enabled.
4.1.7 PORT TRIGGERING
Port triggering is a means of automating port forwarding. The CVE-30360 scans
outgoing traffic (from the LAN to the WAN) to see if any of the traffic’s destination
ports match those specified in the port triggering rules you configure. If any of the
ports match, the CVE-30360 automatically opens the incoming ports specified in the
rule, in anticipation of incoming traffic.
NOTE: This feature is not available when the DS-lite function is enabled.
FIREWALL
Page 49
49
HITRON CVE-30360 USER’S GUIDE
4.1.8 DMZ
In networking, the De-Militarized Zone (DMZ) is a part of your LAN that has been
isolated from the rest of the LAN, and opened up to the WAN. The term comes from
the military designation for a piece of territory, usually located between two opposing
forces, that is isolated from both and occupied by neither.
NOTE: This feature is not available when the DS-lite function is enabled.
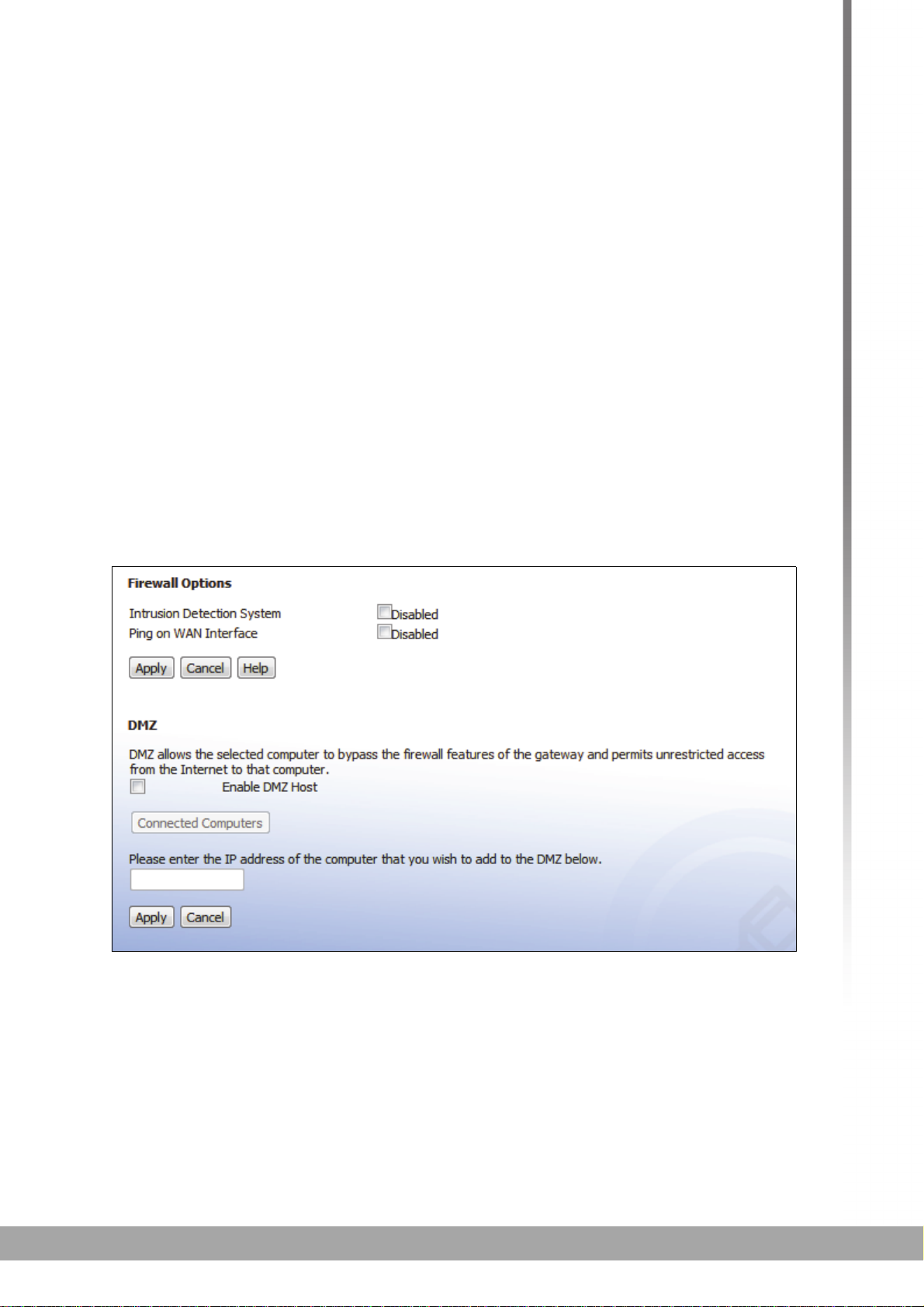
4.2 THE FIREWALL OPTIONS SCREEN
Use this screen to turn firewall features on or off, and to configure your network’s
Demilitarized Zone (DMZ). You can enable or disable the CVE-30360’s intrusion
detection system, and allow or prevent responses to ICMP requests from the WAN.
NOTE: Only one device can be on the DMZ at a time.
Click Firewall > Firewall Options. The following screen displays.
FIGURE 14: The Firewall > Firewall Options Screen
FIREWALL
Page 50

50
HITRON CVE-30360 USER’S GUIDE
The following table describes the labels in this screen.
TABLE 14: The Firewall > Firewall Options Screen
Intrusion Detection
System
Select this to turn the intrusion detection system off.
Deselect this to turn the intrusion detection system
on.
Ping on WAN Interface
Enable DMZ Host Use this field to turn the DMZ on or off.
Connected Computers Click this to see a list of the computers currently
[...] IP Address [...] Enter the IP address of the computer that you want to
Apply Click this to save your changes to the fields in this
Cancel Click this to return the fields in this screen to their last-
Help Click this to see information about the fields in this
Select this to prevent responses to ICMP requests
originating from the WAN.
Select this to allow responses to ICMP requests
originating from the WAN.
Select the checkbox to enable the DMZ.
Deselect the checkbox to disable the DMZ.
Computers that were previously in the DMZ are now
on the LAN.
connected to the CVE-30360 on the LAN.
add to the DMZ.
screen.
saved values without saving your changes.
screen.
4.3 THE MAC FILTERING SCREEN
Use this screen to configure Media Access Control (MAC) address filtering on the
LAN.
NOTE: To configure MAC address filtering on the wireless network, see The Access
Control Screen on page 82.
You can set the CVE-30360 to allow only certain devices to access the CVE-30360
and the network, or to deny certain devices access.
NOTE: To see a list of all the computers connected to the CVE-30360 on the LAN,
click the Connected Computers button in the Firewall > IP Filtering,
Forwarding, Port Triggering or Firewall Options screens.
Click Firewall > MAC Filtering. The following screen displays.
FIREWALL
Page 51

51
HITRON CVE-30360 USER’S GUIDE
FIGURE 15: The Firewall > MAC Filtering Screen
The following table describes the labels in this screen.
TABLE 15: The Firewall > MAC Filtering Screen
MAC Filter Options
MAC Filter Options Use this field to control whether the CVE-30360 performs
MAC filtering.
Select Allow-All to turn MAC filtering off. All devices
may access the CVE-30360 and the network.
Select Allow to permit only devices with the MAC
addresses you set up in the Allow Table to access the
CVE-30360 and the network. All other devices are
denied access.
Select Deny to permit all devices except those with the
MAC addresses you set up in the Deny Table to
access the CVE-30360 and the network. The specified
devices are denied access.
Allow Table (up to 16 Items)
FIREWALL
Page 52

52
HITRON CVE-30360 USER’S GUIDE
TABLE 15: The Firewall > MAC Filtering Screen (continued)
# This displays the index number assigned to the permitted
device.
Device Name This displays the name you gave to the permitted device.
MAC Address This displays the MAC address of the permitted device.
Delete Select a permitted device’s radio button ( ) and click this
to remove the device from the list. The device may no
longer access the CVE-30360 and the network.
NOTE: Make sure you do not delete your management
computer from the list; if you do so, you will need
to log back in from another computer, or reset the
CVE-30360.
Deny Table (up to 16 Items)
Device Name This displays the name you gave to the denied device.
MAC Address This displays the MAC address of the denied device.
Delete Select a denied device’s radio button ( ) and click this to
remove the device from the list. The device may now
access the CVE-30360 and the network.
Auto-Learned LAN Devices
Device Name This displays the name of each network device that has
connected to the CVE-30360 on the LAN.
MAC Address This displays the MAC address of each network device
that has connected to the CVE-30360 on the LAN.
Type Use this field to specify the list to which you want to add
the device.
Select Allow to add the device to the Allow Table.
Select Deny to add the device to the Deny Table.
Manually-Added LAN Devices
Device Name Enter the name to associate with a network device that
you want to permit or deny access to the CVE-30360 and
the network.
NOTE: This name is arbitrary, and does not affect
functionality in any way.
MAC Address Specify the MAC address of the network device that you
want to permit or deny access to the CVE-30360 and the
network.
Type Use this field to specify the list to which you want to add
the device.
Select Allow to add the device to the Allow Table.
Select Deny to add the device to the Deny Table.
FIREWALL
Page 53

53
HITRON CVE-30360 USER’S GUIDE
TABLE 15: The Firewall > MAC Filtering Screen (continued)
Add Click this to add the device to the list you specified.
Cancel Click this to clear the Manually-Added LAN Devices
fields.
Apply Click this to save your changes to the fields in this screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this screen.
4.4 THE IP FILTERING SCREEN
Use this screen to configure IP filtering. You can turn IP filtering on or off and
configure new and existing IP filtering rules.
Click Firewall > IP Filtering. The following screen displays.
FIGURE 16: The Firewall > IP Filtering Screen
The following table describes the labels in this screen.
TABLE 16: The Firewall > IP Filtering Screen
All IP Filtering Rules Use this to turn IP filtering on or off.
Deselect the checkbox to enable IP filtering.
Select the checkbox to disable IP filtering (default).
NOTE: You can add, edit or delete IP filtering rules only
when this checkbox is deselected.
Select Select an IP filtering rule’s radio button ( ) before
clicking Edit or Delete.
# This displays the arbitrary identification number
assigned to the IP filtering rule.
Application Name This displays the arbitrary name you assigned to the
rule when you create it.
FIREWALL
Page 54

54
HITRON CVE-30360 USER’S GUIDE
TABLE 16: The Firewall > IP Filtering Screen (continued)
Port Range This displays the start and end values of the ports to
which communications from the specified IP addresses
is not permitted.
Protocol This displays the type of communications that are not
permitted:
TCP displays if communications via the
Transmission Control Protocol are not permitted.
UDP displays if communications via the User
Datagram Protocol are not permitted.
TCP/UDP displays if communications via the
Transmission Control Protocol and the User
Datagram Protocol are not permitted.
IP Address Range This displays the start and end IP address from which
communications to the specified ports are not permitted.
Enable Use this field to turn each IP filtering rule on or off.
Select this checkbox to enable the IP filtering rule.
Deselect this checkbox to disable the IP filtering rule.
Add New Click this to define a new IP filtering rule. See Adding or
Editing an IP Filtering Rule on page 54 for information
on the screen that displays.
Edit Select an IP filtering rule’s radio button ( ) and click
this to make changes to the rule. See Adding or Editing
an IP Filtering Rule on page 54 for information on the
screen that displays.
Delete Select an IP filtering rule’s radio button ( ) and click
this to remove the rule. The deleted rule’s information
cannot be retrieved.
Apply Click this to save your changes to the fields in this
screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
4.4.1 ADDING OR EDITING AN IP FILTERING RULE
To add a new IP filtering rule, click Add in the Firewall > IP Filtering screen.
To edit an existing IP filtering rule, select the rule’s radio button ( ) in the
Firewall > IP Filtering screen and click the Edit button.
The following screen displays.
FIREWALL
Page 55

55
HITRON CVE-30360 USER’S GUIDE
FIGURE 17: The Firewall > IP Filtering > Add/Edit Screen
The following table describes the labels in this screen.
TABLE 17: The Firewall > IP Filtering > Add/Edit Screen
Application Name Enter a name for the application that you want to block.
NOTE: This name is arbitrary, and does not affect
functionality in any way.
Port Range Use these fields to specify the target port range to which
communication should be blocked.
Enter the start port number in the first field, and the end
port number in the second field.
To specify only a single port, enter its number in both
fields.
Protocol Use this field to specify whether the CVE-30360 should
block communication via:
Transmission Control Protocol (TCP)
User Datagram Protocol (UDP)
Both TCP and UDP.
NOTE: If in doubt, leave this field at its default (Both).
IP Address Range Use these fields to specify the range of local computers’
IP addresses from which communications should be
blocked.
Enter the start IP address in the first field, and the end IP
address in the second.
To specify only a single IP address, enter it in both fields.
Connected Computers Click this to see a list of the computers currently
connected to the CVE-30360 on the LAN.
Back Click this to return to the Firewall > IP filtering screen
without saving your changes to the IP filtering rule.
Apply Click this to save your changes to the fields in this
screen.
FIREWALL
Page 56
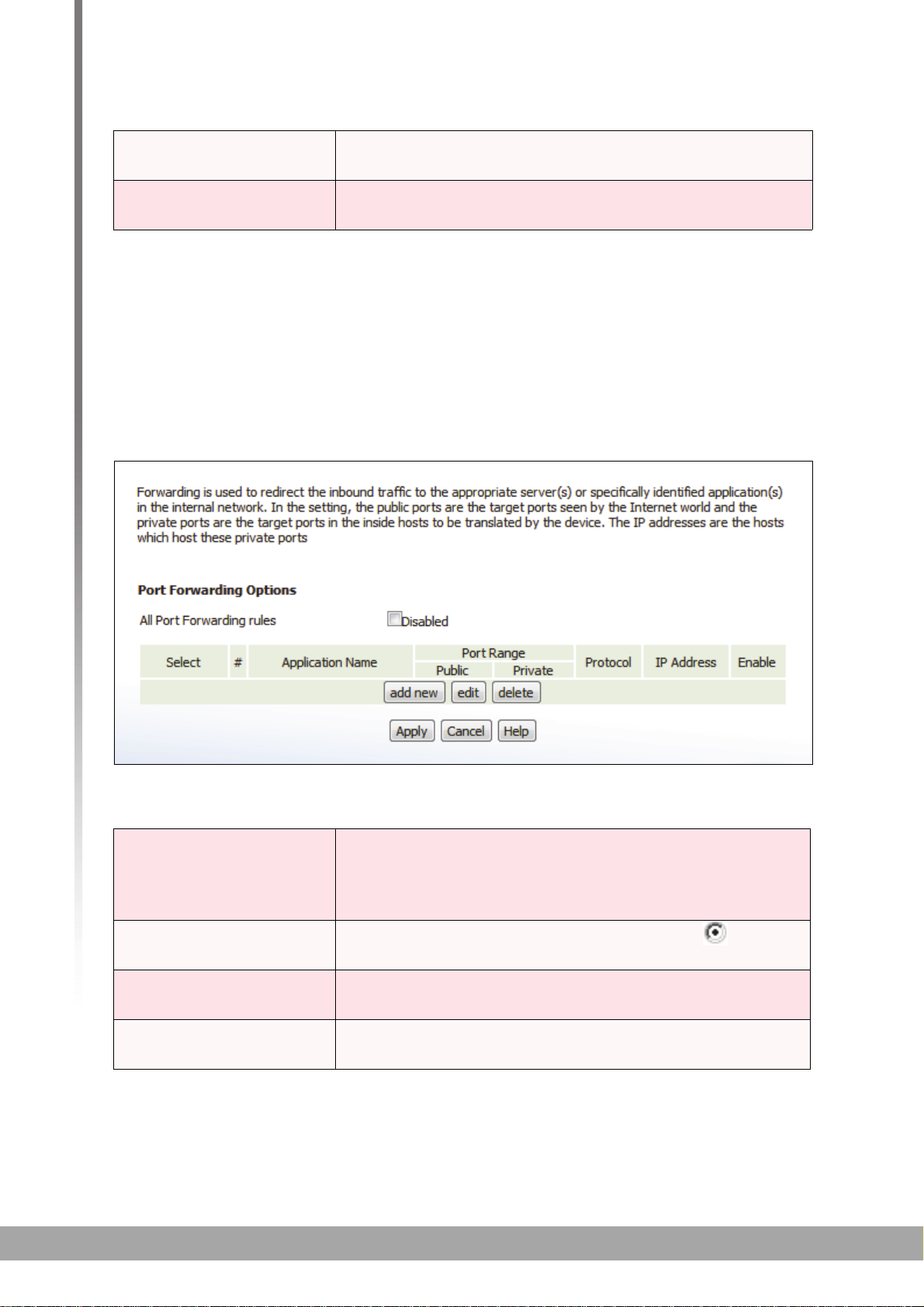
56
HITRON CVE-30360 USER’S GUIDE
TABLE 17: The Firewall > IP Filtering > Add/Edit Screen
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
4.5 THE FORWARDING SCREEN
Use this screen to configure port forwarding between computers on the WAN and
computers on the LAN. You can turn port forwarding on or off and configure new and
existing port forwarding rules.
Click Firewall > Forwarding. The following screen displays.
FIGURE 18: The Firewall > Forwarding Screen
The following table describes the labels in this screen.
TABLE 18: The Firewall > Forwarding Screen
All Port Forwarding Rules Use this field to turn port forwarding on or off.
Select the checkbox to enable port forwarding.
Deselect the checkbox to disable port forwarding.
Select Select a port forwarding rule’s radio button ( ) before
clicking Edit or Delete.
# This displays the arbitrary identification number
assigned to the port forwarding rule.
Application Name This displays the arbitrary name you assigned to the rule
when you created it.
FIREWALL
Page 57

57
HITRON CVE-30360 USER’S GUIDE
TABLE 18: The Firewall > Forwarding Screen (continued)
Port Range These fields display the ports to which the rule applies:
The Public field displays the incoming port range.
These are the ports on which the CVE-30360
received traffic from the originating host on the WAN.
The Private field displays the port range to which the
CVE-30360 forwards traffic to the device on the LAN.
Protocol This field displays the protocol or protocols to which this
rule applies:
Transmission Control Protocol (TCP)
User Datagram Protocol (UDP)
Transmission Control Protocol and User Datagram
Protocol (TCP/UDP)
Generic Routing Encapsulation (GRE)
Encapsulating Security Protocol (ESP)
IP Address This displays the IP address of the computer on the LAN
to which traffic conforming to the Public Port Range
and Protocol conditions is forwarded.
Enable Use this field to turn each port forwarding rule on or off.
Select this checkbox to enable the port forwarding
rule.
Deselect this checkbox to disable the port forwarding
rule.
Add New Click this to define a new port forwarding rule. See
Adding or Editing a Port Forwarding Rule on page 58 for
information on the screen that displays.
Edit Select a port forwarding rule’s radio button ( ) and
click this to make changes to the rule. See Adding or
Editing a Port Forwarding Rule on page 58 for
information on the screen that displays.
Delete Select a port forwarding rule’s radio button ( ) and
click this to remove the rule. The deleted rule’s
information cannot be retrieved.
Apply Click this to save your changes to the fields in this
screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
FIREWALL
Page 58

58
HITRON CVE-30360 USER’S GUIDE
4.5.1 ADDING OR EDITING A PORT FORWARDING RULE
To add a new port forwarding rule, click Add in the Firewall > Forwarding
screen.
To edit an existing port forwarding rule, select the rule’s radio button ( ) in the
Firewall > Forwarding screen and click the Edit button.
The following screen displays.
FIGURE 19: The Firewall > Forwarding > Add/Edit Screen
The following table describes the labels in this screen.
TABLE 19: The Firewall > Forwarding > Add/Edit Screen
Application Name Enter a name for the application for which you want to
create the rule.
NOTE: This name is arbitrary, and does not affect
functionality in any way.
Public Port Range Use these fields to specify the incoming port range.
These are the ports on which the CVE-30360 received
traffic from the originating host on the WAN.
Enter the start port number in the first field, and the end
port number in the second field.
To specify only a single port, enter its number in both
fields.
Private Port Range Use these fields to specify the ports to which the
received traffic should be forwarded.
Enter the start port number in the first field. The number
of ports must match that specified in the Public Port
Range, so the CVE-30360 completes the second field
automatically.
FIREWALL
Page 59

59
HITRON CVE-30360 USER’S GUIDE
TABLE 19: The Firewall > Forwarding > Add/Edit Screen
Protocol Use this field to specify whether the CVE-30360 should
forward traffic via:
Transmission Control Protocol (TCP)
User Datagram Protocol (UDP)
Transmission Control Protocol and User Datagram
Protocol (TCP/UDP)
Generic Routing Encapsulation (GRE)
Encapsulating Security Protocol (ESP)
NOTE: If in doubt, leave this field at its default (TCP/
UDP).
IP Address Use this field to enter the IP address of the computer on
the LAN to which you want to forward the traffic.
Connected Computers Click this to see a list of the computers currently
connected to the CVE-30360 on the LAN.
Back Click this to return to the Firewall > Forwarding screen
without saving your changes to the port forwarding rule.
Apply Click this to save your changes to the fields in this
screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
4.6 THE PORT TRIGGERING SCREEN
Use this screen to configure port triggering. You can turn port triggering on or off and
configure new and existing port triggering rules.
Click Firewall > Port Triggering. The following screen displays.
FIREWALL
Page 60

60
HITRON CVE-30360 USER’S GUIDE
FIGURE 20: The Firewall > Port Triggering Screen
The following table describes the labels in this screen.
TABLE 20: The Firewall > Port Triggering Screen
All Port Triggering Rules Use this field to turn port triggering on or off.
Select the checkbox to enable port triggering.
Deselect the checkbox to disable port triggering.
Select Select a port triggering rule’s radio button ( ) before
clicking Edit or Delete.
# This displays the arbitrary identification number
assigned to the port triggering rule.
Application Name This displays the arbitrary name you assigned to the
rule when you created it.
Port Range These fields display the ports to which the rule applies:
The Trigger field displays the range of outgoing
ports. When the CVE-30360 detects activity
(outgoing traffic) on these ports from computers on
the LAN, it automatically opens the Target ports.
The Target field displays the range of triggered
ports. These ports are opened automatically when
the CVE-30360 detects activity on the Trigger ports
from computers on the LAN.
Protocol This displays the protocol of the port triggering rule.
Timeout (ms) This displays the time (in milliseconds) after the CVE-
30360 opens the Target ports that it should close them.
Enable Use this field to turn each port triggering rule on or off.
Select this checkbox to enable the port triggering
rule.
Deselect this checkbox to disable the port triggering
rule.
FIREWALL
Page 61

61
HITRON CVE-30360 USER’S GUIDE
TABLE 20: The Firewall > Port Triggering Screen
Add New Click this to define a new port triggering rule. See
Adding or Editing a Port Triggering Rule on page 61 for
information on the screen that displays.
Edit Select a port triggering rule’s radio button ( ) and click
this to make changes to the rule. See Adding or Editing
a Port Triggering Rule on page 61 for information on the
screen that displays.
Delete Select a port triggering rule’s radio button ( ) and click
this to remove the rule. The deleted rule’s information
cannot be retrieved.
Apply Click this to save your changes to the fields in this
screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
4.6.1 ADDING OR EDITING A PORT TRIGGERING RULE
To add a new port triggering rule, click Add in the Firewall > Port Triggering
screen.
To edit an existing port triggering rule, select the rule’s radio button ( ) in the
Firewall > Port Triggering screen and click the Edit button.
The following screen displays.
FIGURE 21: The Firewall > Port Triggering > Add/Edit Screen
FIREWALL
Page 62

62
HITRON CVE-30360 USER’S GUIDE
The following table describes the labels in this screen.
TABLE 21: The Firewall > Port Triggering > Add/Edit Screen
Application Name Enter a name for the application for which you want to
create the rule.
NOTE: This name is arbitrary, and does not affect
functionality in any way.
Trigger Port Range Use these fields to specify the trigger ports. When the
CVE-30360 detects activity on any of these ports
originating from a computer on the LAN, it automatically
opens the Target ports in expectation of incoming traffic.
Enter the start port number in the first field, and the end
port number in the second field.
To specify only a single port, enter its number in both
fields.
Target Port Range Use these fields to specify the target ports. The CVE-
30360 opens these ports in expectation of incoming
traffic whenever it detects activity on any of the Trigger
ports. The incoming traffic is forwarded to these ports on
the computer connected to the LAN.
Enter the start port number in the first field, and the end
port number in the second field.
To specify only a single port, enter its number in both
fields.
Protocol Use this field to specify whether the CVE-30360 should
activate this trigger when it detects activity via:
Transmission Control Protocol (TCP)
User Datagram Protocol (UDP)
Transmission Control Protocol and User Datagram
Protocol (Both)
NOTE: If in doubt, leave this field at its default (Both).
Timeout (ms) Enter the time (in milliseconds) after the CVE-30360
opens the Target ports that it should close them.
Connected Computers Click this to see a list of the computers currently
connected to the CVE-30360 on the LAN.
Back Click this to return to the Firewall > Forwarding screen
without saving your changes to the port forwarding rule.
Apply Click this to save your changes to the fields in this
screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
FIREWALL
Page 63

63
PARENTAL CONTROL
5
PARENTAL CONTROL
This chapter describes the screens that display when you click Parent Control in the
toolbar.
5.1 PARENTAL CONTROL OVERVIEW
This section describes some of the concepts related to the Parent Control screens.
5.1.1 WEBSITE BLOCKING
The Parent Control screens allow you to block access from computers on the LAN to
certain websites, or websites whose URLs (website addresses) contain the keywords
you specify.
You can also specify “trusted” computers, which should be exempted from website
blocking, and you can schedule website blocking so that it is only in effect at certain
times (evenings and weekends, for example).
5.2 THE WEB SITE BLOCKING SCREEN
Use this screen to block access from the LAN to certain websites. You can also
specify trusted computers, which are not subject to the blocking filter.
NOTE: To apply the blocking filter only at certain times, use the Parent Control >
Scheduling screen.
Click Parent Control > Web Site Blocking. The following screen displays.
Page 64

64
HITRON CVE-30360 USER’S GUIDE
FIGURE 22: The Parent Control > Web Site Blocking Screen
The following table describes the labels in this screen.
TABLE 22: The Parent Control > Web Site Blocking Screen
Web Site Blocking Options
Enable Web Site
Blocking
New Key Word/URL
Blocking
Use this field to turn web site blocking on or off.
Select the checkbox to enable web site blocking.
Deselect the checkbox to disable web site blocking.
Use these fields to configure the websites to which users
on the LAN are denied access:
Enter a URL (for example, “www.example.com”) to
block access to that website only.
Enter a keyword (for example, “example”) to block
access to all websites that contain the keyword in
their URL (for example, “www.example.com”,
“www.example.org”, “www.someotherwebsite.com/
example” and so forth).
Click Add to add the URL or keyword to the Blocked
Key Words/URLs list.
PARENTAL CONTROL
Page 65

65
HITRON CVE-30360 USER’S GUIDE
TABLE 22: The Parent Control > Web Site Blocking Screen (continued)
Blocked Key Words/
URLs
Trusted Computers
This displays the list of websites and keywords to which
users on the LAN are denied access.
Select a URL or keyword and click Remove to delete
it from the list.
Click Clear List to delete all the URLs and keywords
from the list.
New Computer MAC
Address
Trusted Computer
List
Connected
Computers
Remove Select a computer’s MAC address from the Connected
Clear List Click this to delete all the computers’ MAC addresses
Apply Click this to save your changes to the fields in this
Cancel Click this to return the fields in this screen to their last-
Help Click this to see information about the fields in this
Enter a computer’s Media Access Control (MAC)
address and click Add to include it in the trusted
computer list.
This displays a list of the computers which are exempt
from the website blocking filter, identified by their MAC
addresses.
Click this to see a list of the computers that are currently
connected to the CVE-30360.
Computers list and click this to delete it from the list.
from the list.
screen.
saved values without saving your changes.
screen.
5.3 THE SCHEDULING SCREEN
Use this screen to control when the website blocking filter should be in effect.
NOTE: To configure the website blocking filter, use the Parent Control > Web Site
Blocking screen.
Click Parent Control > Scheduling. The following screen displays.
PARENTAL CONTROL
Page 66

66
HITRON CVE-30360 USER’S GUIDE
FIGURE 23: The Parent Control > Scheduling Screen
The following table describes the labels in this screen.
TABLE 23: The Parent Control > Scheduling Screen
Days of the Week Select the days of the week on which you want the
website blocking filter to be in effect.
Time of Day Use these fields to control the time that the website
blocking filter should be in effect:
Select All Day to apply the website blocking filter at
all times.
To apply the website blocking filter only at certain
times of day, deselect All Day. Use the Start fields
to define the time that the filter should come into
effect, and use the End fields to define the time that
the filter should cease being in effect.
Apply Click this to save your changes to the fields in this
screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
PARENTAL CONTROL
Page 67

67
HITRON CVE-30360 USER’S GUIDE
5.4 THE LOCAL LOGS SCREEN
Use this screen to see information about events that have triggered the website
blocking filter.
Click Parent Control > Local Logs. The following screen displays.
FIGURE 24: The Parent Control > Local Logs Screen
The following table describes the labels in this screen.
TABLE 24: The Parental Control > Local Logs Screen
WAN Activity This field displays information about website blocking
filter events in the following format:
Date (DD/MM/YY)
Time (HH:MM:SS)
IP Address
Event type
Clear Click this to remove the log events. Deleted information
cannot be retrieved.
Refresh Logs Click this to reload the information in the WAN Activity
list. Events that have occurred since you last refreshed
the list display.
PARENTAL CONTROL
Page 68

68
HITRON CVE-30360 USER’S GUIDE
PARENTAL CONTROL
Page 69

69
WIRELESS
6
WIRELESS
This chapter provides an introduction to wireless networking, describes some
common wireless network setup procedures, and documents the screens that display
when you click Wireless in the toolbar. It contains the following sections:
Wireless Basics on page 69: this section describes how wireless networks work
and are secured.
Wireless Tutorials on page 71: this section describes how to perform some
common wireless network configuration tasks using your CVE-30360.
Advanced Wireless Networking on page 74: this section provides more in-depth
information.
If you are just interested in setting up your wireless network in a standard
configuration you do not need to read this section.
The Wireless Screens on page 76: this section provides detailed information on
each of the CVE-30360’s wireless screens.
Use this section as a reference to find out about a particular screen or field.
6.1 WIRELESS BASICS
This section describes how wireless networks and wireless security work.
Your CVE-30360’s wireless network is part of the Local Area Network (LAN), known
as the Wireless LAN (WLAN). The WLAN is a network of radio links between the
CVE-30360 and the other computers and devices that connect to it.
In the following figure, the wireless network is the part in the circle. The laptop and the
PC are called “wireless clients” and connect to the CVE-30360, which is called the
“access point” or “AP”. The wireless clients can use the AP to access other devices
(such as the printer) or the Internet.
Page 70

70
HITRON CVE-30360 USER’S GUIDE
FIGURE 25: Example Wireless Network
6.1.1 WIRELESS STANDARDS
The way in which wireless devices communicate with one another is standardized by
the Institute of Electrical and Electronics Engineers (IEEE). The IEEE standards
pertaining to wireless LANs are identified by their 802.11 designation. There are a
variety of WLAN standards, but the CVE-30360 supports the following (in order of
adoption - old to new - and data transfer speeds - low to high):
IEEE 802.11b
IEEE 802.11g
IEEE 802.11n
6.1.2 SERVICE SETS AND SSIDS
Each wireless network, including all the devices that comprise it, is known as a
“Service Set”.
Each Service Set is identified by a Service Set IDentifier (SSID). This is the name of
the network. Wireless clients must know the SSID in order to be able to connect to
the AP.
You can configure the CVE-30360 to broadcast the SSID (in which case, any client
who scans the airwaves can discover the SSID), or to “hide” the SSID (in which case
it is not broadcast, and only users who already know the SSID can connect). See
Hiding the Network on page 73 for more information.
WIRELESS
Page 71

71
HITRON CVE-30360 USER’S GUIDE
6.1.3 BASIC WIRELESS SECURITY
Radio is inherently an insecure medium, since it can be intercepted by anybody in the
coverage area with a radio receiver. Therefore, a variety of techniques exist in an
attempt to secure it.
These techniques control authentication (identifying who should be allowed to join the
network) and encryption (signal scrambling so that only authenticated users can
decode the transmitted data). The sophistication of each security method varies, as
does its effectiveness.
The CVE-30360 supports the following wireless security protocols (in order of
effectiveness):
Least secure
Most secure
For more information on these security protocols, see Advanced Wireless Security on
page 74.
No security
WEP
WPA-PSK
WPA2-PSK
6.2 WIRELESS TUTORIALS
This section walks you through some of the more common wireless networking tasks.
NOTE: For basic wireless network setup, please see the Quick Installation Guide that
came with your CVE-30360.
These tasks include:
Choosing a Security Method on page 71
Changing the Wireless Password on page 72
Changing the Network Name (SSID) on page 73
Hiding the Network on page 73
Improving the Wireless Network’s Performance on page 73
6.2.1 CHOOSING A SECURITY METHOD
The security method that you choose to use for your wireless network depends upon
the security methods supported by the devices on the network (the CVE-30360, your
PC, your laptop, and so on).
Not all devices support the same security methods, so you must find out what
security methods each of the supports, and choose a method that they all support.
WIRELESS
Page 72
72
HITRON CVE-30360 USER’S GUIDE
You should choose the best security method available; see Basic Wireless Security
on page 71 for a list of methods the CVE-30360 supports, in order of effectiveness.
In order to find out which security methods your other wireless devices support, you
can:
Look at the wireless device and see if it has a label listing the methods
supported.
Look at any documentation or packaging that came with the device.
Go into the device’s configuration utility and look for a list of supported methods.
This is often displayed as a drop-down list from which you can select an option.
Go to the device’s manufacturer’s website and look for an information page that
lists the device’s specifications.
If you want to use WPS (see WPS on page 75) all the wireless clients must also
support WPS. There are two ways to determine if this is the case (in addition to those
described above):
Look at the wireless device and see if it has a physical button labeled “WPS” or
something similar, a wireless “wave” icon (something like ), or the “Wi-Fi
Protected Setup” logo. If any of these are the case, the device probably supports
the WPS PBC (“Push-Button Configuration”) method.
Go into the wireless device’s configuration utility and look for a “WPS” or “Wi-Fi
Protected Setup” screen. This screen should let you know whether the device
supports WPS PBC method, the WPS PIN method, or both (some devices have
a PBC button in their configuration utilities, in addition to or instead of a physical
button).
Once you have chosen a security method, you can select it on the CVE-30360 in the
Wireless > Security screen’s Security Mode field (see The Security Screen on
page 78).
6.2.2 CHANGING THE WIRELESS PASSWORD
Only wireless clients with the correct password can access the network. It’s a good
idea to change your wireless network’s password every so often, if you think
someone knows it who shouldn’t, or if there’s suspicious activity on your network.
You should change the password on the CVE-30360, then change the password on
each of your wireless clients.
The procedure for changing the password on the CVE-30360 depends on the
security method your network is using.
If you are using the WPS PBC (“Push-Button Configuration”) security method,
where you press a button on the CVE-30360 and the other wireless devices,
which connect automatically, just run the WPS PBC process again; see the
Quick Installation Guide that came with your CVE-30360 for more information on
how to do this.
WIRELESS
Page 73

73
HITRON CVE-30360 USER’S GUIDE
If you are using the WPS PIN security, where you have a WPS password that
you enter into each device on the network, go to the Wireless > Basic screen
and click the PIN button. In the screen that displays, enter the WPS PIN that you
want to use for the CVE-30360, or the WPS PIN of the client device you want to
add to the network.
If you are using WEP, go to the Wireless > Security screen. Use the WEP
Settings section to define the key(s) you want to use. Click Apply when you
have finished.
If you are using WPA-PSK or WPA2-PSK, go to the Wireless > Security
screen. In the WPA_Personal section, enter the new password in the Pre-
Shared Key field. Click Apply when you have finished.
Whichever security method you are using, when you change the password on the
CVE-30360, the other devices will not be able to connect to the network until you
change their passwords as well.
The way in which you change the password on the client devices differs according to
manufacturer and model. In general, you will need to log in to the device’s
configuration utility and perform a similar procedure to the one you just performed on
the CVE-30360, unless you are using the WPS PBC method, in which case you must
press the button within two minutes of pressing the button on the CVE-30360.
NOTE: If you are using WPS PBC, bear in mind that any device that also supports
WPS can connect to the CVE-30360 during the connection period. It is
therefore not an ideal method to use in public places, or if you suspect
someone is attempting to gain unauthorized access to the network.
6.2.3 CHANGING THE NETWORK NAME (SSID)
To change your wireless network’s SSID (the name that displays when you scan for
wireless networks on your wireless client), go to the Wireless > Basic screen. Enter
the new network name in the SSID Name field and click Apply.
NOTE: Since the SSID is required to connect to a network, you will need to re-
connect your wireless client devices to the new SSID.
6.2.4 HIDING THE NETWORK
There are various reasons that you might not want your network to be visible to
people scanning for available networks. To do this, go to the Wireless > Basic
screen. Select the Hidden checkbox and click Apply.
6.2.5 IMPROVING THE WIRELESS NETWORK’S
PERFORMANCE
There are two main factors that affect how well your wireless devices can
communicate:
WIRELESS
Page 74

74
HITRON CVE-30360 USER’S GUIDE
1 Interference from physical objects
2 Radio Frequency (RF) interference
To minimize interference from physical objects:
Move the CVE-30360 away from walls, heavy furniture, other massive or
metallic objects like refrigerators, and so forth.
Install the CVE-30360 in a higher location.
To minimize RF interference:
Move the CVE-30360 away from sources of RF energy such as wireless
telephone base stations, microwaves, and so forth.
Conduct a wireless site audit to see if other wireless networks are interfering with
yours. If so, you can change the wireless channel to one that isn’t so congested.
To conduct a site audit on the CVE-30360, go to the Wireless > WiFi Site
Survey screen. Click Scan. The screen that displays shows the wireless
networks in the area, the Ch field shows the channel they are using, and the
Signal (%) field shows how strongly the CVE-30360 is receiving their signal
(bear in mind that the strength of a network at the CVE-30360’s location is not
necessarily the same as at your wireless client’s location; it may be much
stronger there).
If there are a lot of networks or a very strong network using a single channel or a
group of channels, you can change the CVE-30360’s channel to one further
away from the congested channel. To do this on the CVE-30360, go to the
Wireless > Basic screen and choose an option from the Channel list. You
should choose a channel as far away from the congested area as possible;
ideally a difference of five channels is desirable.
Depending on their configuration, you may also then need to change the channel
on your wireless client devices.
6.3 ADVANCED WIRELESS NETWORKING
This section provides more technical information about wireless networks.
NOTE: If you are just setting up your wireless network in a standard configuration
(covered in Wireless Tutorials on page 71) you do not need to read this
section.
6.3.1 ADVANCED WIRELESS SECURITY
This section describes the CVE-30360’s supported security protocols in greater
detail.
WIRELESS
Page 75

75
HITRON CVE-30360 USER’S GUIDE
WEP (the Wired Equivalency Protocol): this protocol uses a series of “keys” or
data strings to authenticate the wireless client with the AP, and to encrypt data
sent over the wireless link. WEP is a deprecated protocol, and should only be
used when it is the only security standard supported by the wireless clients.
WEP provides only a nominal level of security, since widely-available software
exists that can break it in a matter of minutes.
WPA-PSK (WiFi Protected Access - Pre-Shared Key): WPA was created to
solve the inadequacies of WEP. There are two types of WPA: the “enterprise”
version (known simply as WPA) requires the use of a central authentication
database server, whereas the “personal” version (supported by the CVE-30360)
allows users to authenticate using a “pre-shared key” or password instead.
While WPA provides good security, it is still vulnerable to “brute force”
password-guessing attempts (in which an attacker simply barrages the AP with
join requests using different passwords), so for optimal security it is advised that
you use a random password of thirteen characters or more, containing no
“dictionary” words.
WPA2-PSK: WPA2 is an improvement on WPA. The primary difference is that
WPA uses the Temporal Key Integrity Protocol (TKIP) encryption standard
(which has been shown to have certain possible weaknesses), whereas WPA2
uses the stronger Advanced Encryption Standard (AES) in the Counter mode
with Cipher block chaining Message authentication code Protocol (CCMP),
which has received the US government’s seal of approval for communications
up to the Top Secret security level. Since WPA2-PSK uses the same pre-shared
key mechanism as WPA-PSK, the same caveat against using insecure or
simple passwords applies.
6.3.2 OTHER WIRELESS CONCEPTS
This section provides information on wireless-related topics not covered in previous
sections.
6.3.2.1 WPS
WiFi-Protected Setup (WPS) is a standardized method of allowing wireless devices
to quickly and easily join wireless networks, while maintaining a good level of
security. The CVE-30360 provides two methods of WPS authentication:
Push-Button Configuration (PBC): when the user presses the PBC button on
the AP (either a physical button, or a virtual button in the GUI), any user of a
wireless client that supports WPS can press the corresponding PBC button on
the client within two minutes to join the network.
Personal Identification Number (PIN) Configuration: all WPS-capable
devices possess a PIN (usually to be found printed on a sticker on the device’s
housing). When you configure another device to use the same PIN, the two
devices authenticate with one another.
Once authenticated, devices that have joined a network via WPS use the WPA2
security standard.
WIRELESS
Page 76

76
HITRON CVE-30360 USER’S GUIDE
6.3.2.2 WMM
WiFi MultiMedia (WMM) is a Quality of Service (QoS) enhancement that allows
prioritization of certain types of data over the wireless network. WMM provides four
data type classifications (in priority order; highest to lowest):
Voice
Video
Best effort
Background
If you wish to improve the performance of voice and video (at the expense of other,
less time-sensitive applications such as Internet browsing and FTP transfers), you
can enable WMM. You can also edit the WMM QoS parameters, but are disadvised
to do so unless you have an extremely good reason to make the changes.
6.4 THE WIRELESS SCREENS
This section describes each of the screens that display when you click Wireless in
the toolbar.
6.4.1 THE BASIC SCREEN
Use this screen to configure your CVE-30360’s basic wireless settings. You can turn
the wireless module on or off, select the wireless mode and channel, run WPS and
configure the wireless network’s SSID.
Click Wireless > Basic. The following screen displays.
FIGURE 26: The Wireless > Basic Screen
WIRELESS
Page 77

77
HITRON CVE-30360 USER’S GUIDE
The following table describes the labels in this screen.
TABLE 25: The Wireless > Basic Screen
Wireless Basic Settings
Wireless ON/OFF Use this field to turn the wireless network on or off.
Select ENABLE to turn the wireless network on.
Deselect DISABLE to turn the wireless network off.
Wireless Mode Select the type of wireless network that you want to use:
11B/G Mixed: use IEEE 802.11b and 802.11n
11B Only: use IEEE 802.11b
11G Only: use IEEE 802.11g
11N Only: use IEEE 802.11n
11G/N Mixed: use IEEE 802.11g and 802.11N
11B/G/N Mixed: use IEEE 802.11b, 802.11g and
802.11N
NOTE: Only wireless clients that support the network
protocol you select can connect to the wireless
network. If in doubt, use 11B/G/N (default).
Channel Select the wireless channel that you want to use, or
select Auto to have the CVE-30360 select the optimum
channel to use.
NOTE: Use the Auto setting unless you have a specific
reason to do otherwise.
Run WPS Use these buttons to run Wifi Protected Setup (WPS):
Click the PBC button to begin the Push-Button
Configuration process. You must then press the PBC
button on your client wireless devices within two
minutes in order to register them on your wireless
network.
Click the PIN button to begin the PIN configuration
process. In the screen that displays, enter the WPS
PIN that you want to use for the CVE-30360, or the
WPS PIN of the client device you want to add to the
network.
FIGURE 27: WPS PIN
WIRELESS
Page 78

78
HITRON CVE-30360 USER’S GUIDE
TABLE 25: The Wireless > Basic Screen (continued)
SSID Setting This displays Primary SSID.
NOTE: You may have additional BSSIDs, depending on
your contract with your service provider.
SSID Name Enter the name that you want to use for your wireless
network. This is the name that identifies your network,
and to which wireless clients connect.
NOTE: It is suggested that you change the SSID from its
default, for security reasons.
Hidden Use this field to make your network visible or invisible to
other wireless devices.
Select the checkbox if you do not want the CVE-
30360 to broadcast the network name (SSID) to all
wireless devices in the coverage area. Anyone who
wants to connect to the network must know the
SSID.
Deselect the checkbox if you want your network
name (SSID) to be public. Anyone with a wireless
device in the coverage area can discover the SSID,
and attempt to connect to the network.
In Service This field controls whether or not the SSID is in
operation.
NOTE: At the time of writing, this field is not user-
configurable.
WMM Mode Select the checkbox if you want to apply Wifi MultiMedia
(WMM) Quality of Service (QoS) settings to this SSID.
6.4.2 THE SECURITY SCREEN
Use this screen to configure authentication and encryption on your wireless network.
NOTE: It is strongly recommended that you set up security on your network;
otherwise, anyone in the radio coverage area can access your network.
Click Wireless > Security. The following screen displays.
WIRELESS
Page 79

79
HITRON CVE-30360 USER’S GUIDE
FIGURE 28: The Wireless > Security Screen
The following table describes the labels in this screen.
TABLE 26: The Wireless > Security Screen
Wireless Security
SSID Select the SSID for which you want to configure
security.
NOTE: At the time of writing, only one SSID is available.
Security Mode Select the type of security that you want to use.
Select None to use no security. Anyone in the
coverage area can enter your network.
Select WEP to use the Wired Equivalent Privacy
security protocol.
Select WPA-Personal to use the WiFi Protected
Access (Personal) security protocol.
NOTE: Due to inherent security vulnerabilities, it is
suggested that you use WEP only if it is the only
security protocol your wireless clients support.
Under almost all circumstances, you should use
WPA-Personal.
WIRELESS
Page 80

80
HITRON CVE-30360 USER’S GUIDE
TABLE 26: The Wireless > Security Screen (continued)
WEP Settings
NOTE: These fields are only configurable when you select WEP from the Security
Mode list.
WEP Key Length Use this field to specify the length of the security key
used to allow wireless devices to join the network. The
longer the key, the more secure it is.
Select 64-bit to use a ten-digit security key.
Select 128-bit to use a twenty-six-digit security key.
WEP Key 1~4 Use these fields to define the security keys that all
wireless devices on the network must use to join the
network.
The CVE-30360 supports up to four WEP keys, of which
you can select one as the default. You should input the
same four keys, in the same order, in your network’s
wireless clients. Your CVE-30360 and your wireless
clients can use different default keys, as long as all four
keys are present and in the same order. If your wireless
client supports only a single WEP key, use the CVE30360’s default key.
Enter the keys in hexadecimal format (using the digits
0~9 and the letters A~F).
Default WEP Key Select the number of the security key that you want the
CVE-30360 to use as its default authentication key for
transmissions.
Authentication Select the authentication mode that you want to use:
Select Open System to allow wireless clients to
authenticate (identify themselves) to the CVE-30360
before presenting their security credentials (WEP
keys).
Select Shared Key to use the WEP key in the
authentication process. When a client wants to
associate, the CVE-30360 sends an unencrypted
challenge message. The client must use the WEP
key to encrypt the challenge message and return it to
the CVE-30360, which then decrypts the message
and compares the result with its original message.
Open System authentication is the more secure of the
two authentication types, since while the Shared Key
system appears more robust, it is possible to derive
secure data by capturing the challenge messages.
Select Automatic to have the CVE-30360 choose
the authentication method.
WIRELESS
Page 81

81
HITRON CVE-30360 USER’S GUIDE
TABLE 26: The Wireless > Security Screen (continued)
WPA_Personal
NOTE: These fields are only configurable when you select WPA-Personal from the
Security Mode list.
WPA Mode Select the type of WPA security that you want to use:
Select WPA-PSK to use Wifi Protected Access (PreShared Key) mode
Select WPA2-PSK to use Wifi Protected Access 2
(Pre-Shared Key) mode
Select Auto (WPA-PSK or WPA2-PSK) to allow
clients operating in either mode to connect to the
CVE-30360.
Cipher Type Select the type of encryption that you want to use:
Select TKIP to use the Temporal Key Integrity
Protocol.
Select AES to use the Advanced Encryption
Standard.
Select TKIP and AES to allow clients using either
encryption type to connect to the CVE-30360.
Group Key Update
Interval
Pre-Shared Key Enter the pre-shared key that you want to use for your
Pre-Authentication Use this field to allow pre-authentication (Enable) in
Apply Click this to save your changes to the fields in this
Enter the frequency (in seconds) with which you want
the CVE-30360 to create new pre-shared keys, and
issue them to the wireless client.
wireless network. You will need to enter this key into
your wireless clients in order to allow them to connect to
the network.
WPA2, or deny pre-authentication requests (Disable).
In preauthentication, a WPA2 wireless client can
perform authentication with other wireless access points
in its range when it is still connected to its current
wireless access point. This allows mobile wireless
clients to connect to new access points more quickly,
permitting more efficient roaming.
screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
WIRELESS
Page 82
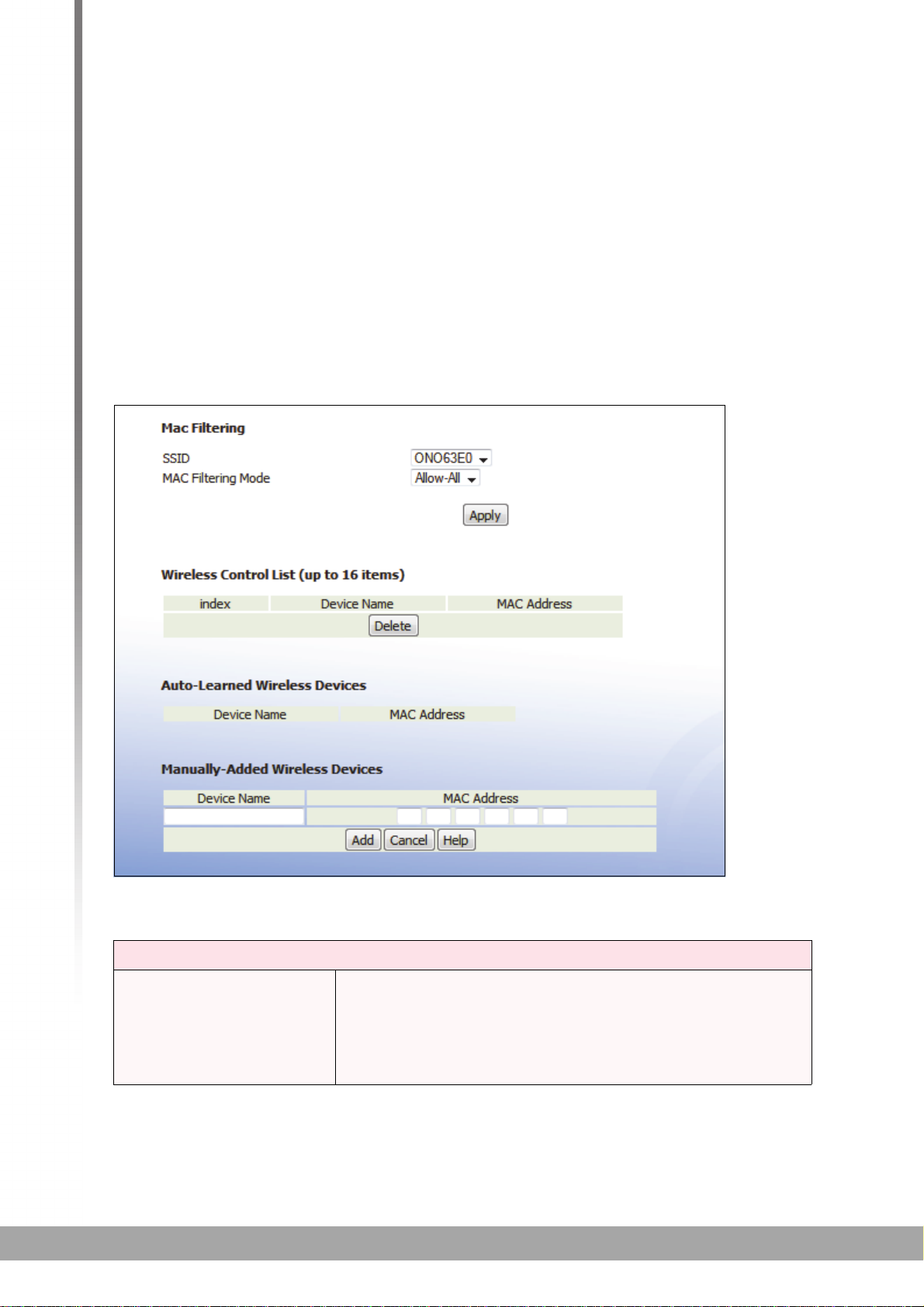
82
HITRON CVE-30360 USER’S GUIDE
6.4.3 THE ACCESS CONTROL SCREEN
Use this screen to configure Media Access Control (MAC) address filtering on the
wireless network.
NOTE: To configure MAC address filtering on the wired LAN, see The MAC Filtering
Screen on page 50.
You can set the CVE-30360 to allow only certain devices to access the CVE-30360
and the network wirelessly, or to deny certain devices access.
Click Wireless > Access Control. The following screen displays.
FIGURE 29: The Wireless > Access Control
The following table describes the labels in this screen.
TABLE 27: The Wireless > Access Control Screen
MAC Filtering
SSID Select the SSID for which you want to configure wireless
access control.
NOTE: At the time of writing, the CVE-30360 supports a
single SSID.
WIRELESS
Page 83

83
HITRON CVE-30360 USER’S GUIDE
TABLE 27: The Wireless > Access Control Screen (continued)
MAC Filtering Mode Use this field to control whether the CVE-30360
performs MAC filtering on the wireless network.
Select Allow-All to turn MAC filtering off. All devices
may access the CVE-30360 and the network
wirelessly.
Select Allow to permit only devices with the MAC
addresses you set up in the Wireless Control List to
access the CVE-30360 and the network wirelessly.
All other devices are denied access.
Select Deny to permit all devices except those with
the MAC addresses you set up in the Wireless
Control List to access the CVE-30360 and the
network wirelessly. The specified devices are denied
access.
Apply Click this to save your changes in the MAC filtering
section.
Wireless Control List (up to 16 Items)
# Index This displays the index number assigned to the
permitted or denied wireless device.
Device Name This displays the name you gave to the permitted or
denied wireless device.
MAC Address This displays the MAC address of the permitted or
denied wireless device.
Delete Select a permitted or denied wireless device’s radio
button ( ) and click this to remove the device from the
list. The device may no longer access the CVE-30360
and the network.
Auto-Learned Wireless Devices
Device Name This displays the name of each network device that has
connected to the CVE-30360 on the wireless network.
MAC Address This displays the MAC address of each network device
that has connected to the CVE-30360 on the wireless
network.
Manually-Added Wireless Devices
Device Name Enter the name to associate with a network device that
you want to permit or deny access to the CVE-30360
and the network wirelessly.
NOTE: This name is arbitrary, and does not affect
functionality in any way.
MAC Address Specify the MAC address of the network device that you
want to permit or deny access to the CVE-30360 and the
network wirelessly.
WIRELESS
Page 84

84
HITRON CVE-30360 USER’S GUIDE
TABLE 27: The Wireless > Access Control Screen (continued)
Add Click this to save your changes to the fields in this
screen.
Cancel Click this to return the fields in this screen to their last-
saved values without saving your changes.
Help Click this to see information about the fields in this
screen.
6.4.4 THE WIFI SITE SURVEY SCREEN
Use this screen to view information about the wireless networks within the CVE30360’s coverage area.
Click Wireless > WiFi Site Survey. The following screen displays.
FIGURE 30: The Wireless > WiFi Site Survey Screen
The following table describes the labels in this screen.
TABLE 28: The Wireless > WiFi Site Survey Screen
Survey Results
ch This field displays the number of the radio channel that
the target wireless network is using.
SSID This field displays the Service Set IDentifier of the target
wireless network.
BSSID This field displays the Basic Service Set IDentifier of the
target wireless network. This is usually the Media
Access Control (MAC) address of the target network
device.
Security This field displays the type of security that the target
wireless network is using.
Signal (%) This field displays the signal strength of the target
wireless network, as received by the CVE-30360, as a
percentage fro 0 (no reception) to 100 (perfect
reception)
W-mode This field displays the wireless network standard (for
instance, 11n) that the target wireless network is using.
WIRELESS
Page 85

85
HITRON CVE-30360 USER’S GUIDE
TABLE 28: The Wireless > WiFi Site Survey Screen (continued)
ExtCH For IEEE 802.11n networks that support 40MHz
wireless transmissions, this field displays whether the
network uses channel bonding, and specifies whether
the extension channel is above or below the primary
control channel.
NOTE: Channel bonding allows an access point to
increase data throughput by using two wireless
channels simultaneously, instead of a single
channel. When you use channel bonding, you
have a primary control channel, and an
extension channel. The extension channel may
be either directly above the control channel, or
directly below.
For IEEE 802.11n networks using channel bonding,
where the extension channel is above the main
channel, ABOVE displays.
For IEEE 802.11n networks using channel bonding,
where the extension channel is above the main
channel, BELOW displays.
For networks that do not use channel bonding,
NONE displays.
Nt This field displays whether the network is using
infrastructure mode, or ad-hoc mode.
NOTE: In infrastructure mode, wireless devices connect
to a central Access Point (AP), which usually
connects to the Internet or another network via a
wired connection. In ad-hoc mode, wireless
devices connect to one another, as peers.
WPS DPID This field displays whether the target network is using
WiFi Protected Setup (WPS) or not. If the target network
is using WPS, this field displays whether it is using PIN
mode, or Push-Button Configuration (PBC) mode.
If the target network is not using WPS, NO displays.
If the target network is using WPS, and allows
wireless devices to connect using the PIN mode, PIN
displays.
If the target network is using WPS, and allows
wireless devices to connect using the push-button
mode, PBC displays.
NOTE: See WPS on page 75 for more information on
WPS, and the difference between PIN and PBC
modes.
WIRELESS
Page 86

86
HITRON CVE-30360 USER’S GUIDE
WIRELESS
Page 87

87
EMTA
7
EMTA
This chapter describes the screens that display when you click EMTA in the toolbar.
These screens display information about the CVE-30360’s embedded Multimedia
Terminal Adapter module.
NOTE: The fields in these screens are read-only, and are provided for
troubleshooting purposes only.
7.1 THE STATUS SCREEN
Use this screen to see general information about the eMTA module.
Click EMTA > Status. The following screen displays.
FIGURE 31: The EMTA > Status Screen
The following table describes the labels in this screen.
TABLE 29: The EMTA > Status Screen
Startup Procedure
Telephony DHCP This field displays the status of the remote telephony
DHCP server.
Telephony Security This displays the type of security used for voice calls
through the CVE-30360.
Page 88

88
HITRON CVE-30360 USER’S GUIDE
TABLE 29: The EMTA > Status Screen (continued)
Telephony TFTP This field displays the status of the remote telephony
TFTP server.
Telephony Call
Server Registration
Telephony
Registration
Complete
SIP Registration Status
SIP Registration
Timer
MTA Line State
Line 1 These fields display the current status of each phone
Line 2
This field displays the status of the connection between
each of the CVE-30360’s phone lines and the remote
call server.
This field displays the overall status of voice call
registration.
This field displays the number of seconds after which the
CVE-30360 re-registers with the SIP (Session Initiation
Protocol) server. This field does not display when the
CVE-30360 is not connected to a SIP server.
connected to the CVE-30360.
These fields do not display when a phone is not
connected to the relevant port.
7.2 THE DHCP SCREEN
Use this screen to see information about the MTA module’s connections to the
service provider.
Click EMTA > DHCP. The following screen displays.
EMTA
Page 89

89
HITRON CVE-30360 USER’S GUIDE
FIGURE 32: The EMTA > DHCP Screen
The following table describes the labels in this screen.
TABLE 30: The EMTA > DHCP Screen
Address Information
MTA MAC Address This field displays the Media Access Control (MAC)
address of the Media Terminal Adapter (MTA) module.
MTA IP Address This field displays the IP address of the MTA module.
Lease Parameters
FQDN This displays the Fully-Qualified Domain Name of the
DHCP server from which the MTA module derives its IP
address and subnet mask.
IP Address/Submask This displays the MTA module’s IP address and subnet
mask, derived by DHCP.
Gateway This displays the IP address of the MTA module’s
gateway on the WAN.
Primary DNS This displays the IP address of the MTA module’s
primary Domain Name System (DNS) server.
Secondary DNS This displays the IP address of the MTA module’s
secondary DNS server.
Lease Timers
EMTA
Page 90

90
HITRON CVE-30360 USER’S GUIDE
TABLE 30: The EMTA > DHCP Screen (continued)
Lease Time
Remaining
This displays the amount of time for which the MTA
module’s current DHCP lease is valid.
Rebind Time
Remaining
Renew Time
Remaining
Packet Cable DHCP Option 122
NOTE: DHCP Option 122 is defined in RFC 3495.
SNMP Entity (SubOption 3)
Kerberos Realm (SubOption 6)
Provisioning Timer (SubOption 8)
This displays the amount of time until the MTA module
attempts to obtain another IP address from another
DHCP server, should lease renewal fail.
This displays the amount of time until the MTA module
attempts to renew its DHCP lease with the current
DHCP server.
This displays the Telephony Service Provider’s
provisioning server address.
This displays the TSP’s Kerberos realm name.
This displays the TSP’s provisioning timer value.
EMTA
Page 91

91
TROUBLESHOOTING
8
TROUBLESHOOTING
Use this section to solve common problems with the CVE-30360 and your network.
Problem: None of the LEDs Turn On
The CVE-30360 is not receiving power, or there is a fault with the device.
1 Ensure that you are using the correct power adaptor.
Problem: One of the LEDs does not Display as Expected
Using a power adaptor other than the one that came with your
CVE-30360 can damage the CVE-30360.
2 Ensure that the power adaptor is connected to the CVE-30360 and the wall
socket (or other power source) correctly.
3 Ensure that the power source is functioning correctly. Replace any broken fuses
or reset any tripped circuit breakers.
4 Disconnect and re-connect the power adaptor to the power source and the CVE-
30360.
5 If none of the above steps solve the problem, consult your vendor.
1 Ensure that you understand the LED’s normal behavior (see LEDs on page 18).
2 Ensure that the CVE-30360’s hardware is connected correctly; see the Quick
Installation Guide.
3 Disconnect and re-connect the power adaptor to the CVE-30360.
4 If none of the above steps solve the problem, consult your vendor.
Page 92

92
HITRON CVE-30360 USER’S GUIDE
Problem: I Forgot the CVE-30360’s IP Address
1 The CVE-30360’s default LAN IP address is 192.168.0.1.
2 You can locate the CVE-30360’s GUI by entering the LAN domain suffix into
your browser’s address bar (on a computer connected to the LAN). The default
LAN domain suffix is hitronhub.home. See The LAN IP Screen on page 40 for
more information.
3 Depending on your operating system and your network, you may be able to find
the CVE-30360’s IP address by looking up your computer’s default gateway. To
do this on (most) Windows machines, click Start > Run, enter “cmd”, and then
enter “ipconfig”. Get the IP address of the Default Gateway, and enter it in your
browser’s address bar.
4 If you still cannot access the CVE-30360, you need to reset the CVE-30360.
See Resetting the CVE-30360 on page 23. All user-configured data is lost, and
the CVE-30360 is returned to its default settings. If you previously backed-up a
more recent version your CVE-30360’s settings, you can now upload them to
the CVE-30360; see The Backup Screen on page 44.
Problem: I Forgot the CVE-30360’s Admin Username or Password
1 The default username is admin, and the default password is password.
2 If the default username and password do not work, you need to reset the CVE-
30360 back to its factory defaults. See Resetting the CVE-30360 on page 23. All
user-configured data is lost, and the CVE-30360 is returned to its default
settings. If you previously backed-up a more recent version your CVE-30360’s
settings, you can now upload them to the CVE-30360; see The Backup Screen
on page 44.
Problem: I Cannot Access the CVE-30360 or the Internet
1 Ensure that you are using the correct IP address for the CVE-30360.
2 Check your network’s hardware connections, and that the CVE-30360’s LEDs
display correctly (see LEDs on page 18).
3 Make sure that your computer is on the same subnet as the CVE-30360; see IP
Address Setup on page 20.
4 If you are attempting to connect over the wireless network, there may be a
problem with the wireless connection. Connect via a LAN port instead.
5 If the above steps do not work, you need to reset the CVE-30360. See Resetting
the CVE-30360 on page 23. All user-configured data is lost, and the CVE-30360
is returned to its default settings. If you previously backed-up a more recent
TROUBLESHOOTING
Page 93

93
HITRON CVE-30360 USER’S GUIDE
version your CVE-30360’s settings, you can now upload them to the CVE30360; see The Backup Screen on page 44.
6 If the problem persists, contact your vendor.
Problem: I Cannot Access the Internet and the DS and US LEDs
Keep Blinking
Your service provider may have disabled your Internet access; check the Cable >
System Info screen’s Network Access field (see The System Info Screen on page
30).
Problem: I Cannot Connect My Wireless Device
1 Ensure that your wireless client device is functioning properly, and is configured
correctly. See the wireless client’s documentation if unsure.
2 Ensure that the wireless client is within the CVE-30360’s radio coverage area.
Bear in mind that physical obstructions (walls, floors, trees, etc.) and electrical
interference (other radio transmitters, microwave ovens, etc) reduce your CVE30360’s signal quality and coverage area.
3 Ensure that the CVE-30360 and the wireless client are set to use the same
wireless mode and SSID (see The Basic Screen on page 76) and security
settings (see The Security Screen on page 78).
4 Re-enter any security credentials (WEP keys, WPA(2)-PSK password, or WPS
PIN).
5 If you are using WPS’s PBC (push-button configuration) feature, ensure that you
are pressing the button on the CVE-30360 and the button on the wireless client
within two minutes of one another.
TROUBLESHOOTING
Page 94

94
FCC Statement <Part 15B 15.105>This equipment has been tested and found to comply with
the limits for a Class B digital device, pursuant to Part 15 of the FCC Rules. These limits are
designed to provide reasonable protection against harmful interference in a residential
installation. This equipment generates, uses and can radiate radio frequency energy and, if
not installed and used in accordance with the instructions, may cause harmful interference
to radio communications. However, there is no guarantee that interference will not occur in
a particular installation. If this equipment does cause harmful interference to radio or
television reception, which can be determined by turning the equipment off and on, the
user is encouraged to try to correct the interference by one of the following measures: Reorient or relocate the receiving antenna. - Increase the separation between the
equipment and receiver. - Connect the equipment into an outlet on a circuit different from
that to which the receiver is connected. - Consult the dealer or an experienced radio/TV
technician for help.
This device complies with Part 15 of the FCC Rules. Operation is subject to the following
two conditions:
1. This device may not cause harmful interference and
2. This device must accept any interference received, including interference that may cause
undesired operation.
This equipment complies with FCC RF radiation exposure limits set forth for an uncontrolled
environment.
This equipment should be installed and operated with a minimum distance of 20cm
between the radiator and your
body.
HITRON CVE-30360 USER’S GUIDE
TROUBLESHOOTING
Page 95

95
INDEX
HITRON CVE-30360 USER’S GUIDE
INDEX
Numbers
802.11b/g/n 16, 70, 77
A
access control 82
access logs 16
access point 15
accounts, login 22
address, IP 20
address, IP, local 21
AP 15
attached network devices 33
authentication 80
B
backup 44
backup and restore 16
bar, navigation 23
buttons 16
cable connection status 32
cable modem 15
CATV 16, 25, 26
cipher type 81
configuration file 29
connection process 33
connection status, cable 32
conventions, document 3
customer support 4
D
debugging 40, 43
default 44
default IP address 21
default username and password 22
defaults 36, 44
De-Militarized Zone 49, 62
DHCP 16, 20, 21, 27, 42, 88
DHCP lease 28
diagnostics 40
DMZ 49, 62
DMZ De-Militarized Zone 16
DNS 40
DOCSIS 25
document conventions 3
Domain Name System 40
domain suffix 40
downstream transmission 29
DS 20
C
cable connection 15
Page 96

96
INDEX
HITRON CVE-30360 USER’S GUIDE
E
eMTA 87
ETH 19
Ethernet 16
Ethernet cables 18
Ethernet port 21
F
factory defaults 36, 44
factory reset 17, 23
fast Ethernet 16
FDMA 30
firewall 47
forwarding, port 16, 48, 56
frequencies, cable 29
F-type RF connector 16
I
IANA 25
ICMP 49
IEEE 802.11b/g/n 16, 70
interface, user 15
intrusion detection 16, 47, 49
IP address 20, 21, 25, 39, 92
IP address lease 28
IP address renewal 28
IP address setup 20, 21
IP address, default 21
IP address, format 25
IP address, local 21
IP filtering 16, 48, 53
ISP 26
K
G
Graphical User Interface 15
graphical user interface 15
GUI 15, 23
GUI overview 23
H
hardware 16
host ID 25
keyword blocking 64
L
LAN 15, 39, 69
LAN 1~4 18
LAN IP 40
LEDs 18, 91, 93
lights 18
Line 1~2 19
Local Area Network 15
local IP address 21
local logs 67
logging in 22
login accounts 22
login screen 20
logs, access 16
logs, local 67
Page 97

97
INDEX
HITRON CVE-30360 USER’S GUIDE
M
MAC address 28
MAC address filtering 82
MAC filtering 16, 47, 50
main window 23
Media Access Control address 28
MIMO 16
modem 15
modulation 29
Multiple-In, Multiple-Out 16
N
navigation 23
navigation bar 23
network devices, attached 33
network diagnostics 40
network number 25
network, local 15
network, wide area 15
network, wireless 15
PBC configuration 75
PIN configuration 16, 75
ping 16, 40, 43, 47, 49
port forwarding 16, 48, 56
port triggering 16, 59
port, Ethernet 21
ports 16
Power 18
pre-authentication 81
pre-shared key 81
private IP address 26
push-button configuration 16
Q
QAM 29
QAM TCM 29
QoS 76
QPSK 29
R
O
open system authentication 80
overview, GUI 23
P
parental control 16, 63
password 36, 92
password and username 22
radio coverage 78
radio links 69
reboot 44
reset 17, 23
restore and backup 16
RF connector 16
RJ45 connectors 18
routing mode 26, 28, 39
rule, IP filtering 54
rule, port forwarding 58
Page 98

98
INDEX
HITRON CVE-30360 USER’S GUIDE
S
SCDMA 30
scheduled website blocking 16
scheduling 65
security 78, 79
security, wireless 16
service set 70
settings backup and restore 16
shared key authentication 80
SSID 70, 76
Status 20
status 33
status, cable connection 32
subnet 20, 21, 25, 39
subnet, IP 20
support, customer 4
switch setup 42
T
TCP/IP 21
TDMA 30
traceroute 16, 40, 43
triggering, port 16, 59
trusted computers 63
U
V
voice-enabled cable modem 15
VoIP (Voice over IP) 16
W
WAN 15, 26
WAN connection 33
website blocking 63
website blocking, scheduled 16
WEP 16, 71
Wide Area Network 15
Wifi MultiMedia 76
Wifi Protected Setup 16, 75
window, main 23
Windows XP 21
wired security 16
wireless 69
wireless access point 15
wireless connection 93
Wireless Local Area Network 15
wireless networking standards 70
wireless security 16, 71, 78, 79
wireless settings, basic 76
WLAN 15, 69
WMM 76
WPA2 75
WPA2-PSK 16, 71
WPA-PSK 16, 71
WPS 16, 75, 76, 79
WPS PBC 17
upstream transmission 29
URL blocking 64
US 20
user interface 15
username 92
username and password 22
X
XP, Windows 21
 Loading...
Loading...