Page 1
Wireless 11n ADSL Firewall Router
User Guide
WL-603
3CRWDR300A-73
3CRWDR300B-73
http://www.3Com.com/
Part No. 10015880 Rev. AA
Published June 2008
Page 2

3Com Corporation
350 Campus Drive,
Marlborough, MA
USA 01752-3064
Copyright © 2004, 2005, 2006, 2007, 2008, 3Com Corporation. All rights reserved. No part of this
documentation may be reproduced in any form or by any means or used to make any derivative work (such as
translation, transformation, or adaptation) without written permission from 3Com Corporation.
3Com Corporation reserves the right to revise this documentation and to make changes in content from time
to time without obligation on the part of 3Com Corporation to provide notification of such revision or change.
3Com Corporation provides this documentation without warranty, term, or condition of any kind, either
implied or expressed, including, but not limited to, the implied warranties, terms or conditions of
merchantability, satisfactory quality, and fitness for a particular purpose. 3Com may make improvements or
changes in the product(s) and/or the program(s) described in this documentation at any time.
If there is any software on removable media described in this documentation, it is furnished under a license
agreement included with the product as a separate document, in the hard copy documentation, or on the
removable media in a directory file named LICENSE.TXT or !LICENSE.TXT. If you are unable to locate a copy,
please contact 3Com and a copy will be provided to you.
UNITED STATES GOVERNMENT LEGEND
If you are a United States government agency, then this documentation and the software described herein are
provided to you subject to the following:
All technical data and computer software are commercial in nature and developed solely at private expense.
Software is delivered as “Commercial Computer Software” as defined in DFARS 252.227-7014 (June 1995) or
as a “commercial item” as defined in FAR 2.101(a) and as such is provided with only such rights as are
provided in 3Com’s standard commercial license for the Software. Technical data is provided with limited rights
only as provided in DFAR 252.227-7015 (Nov 1995) or FAR 52.227-14 (June 1987), whichever is applicable.
You agree not to remove or deface any portion of any legend provided on any licensed program or
documentation contained in, or delivered to you in conjunction with, this User Guide.
Unless otherwise indicated, 3Com registered trademarks are registered in the United States and may or may not
be registered in other countries.
3Com, and the 3Com logo are registered trademarks of 3Com Corporation.
Intel and Pentium are registered trademarks of Intel Corporation. Microsoft, MS-DOS, Windows, and Windows
NT are registered trademarks of Microsoft Corporation. Novell and NetWare are registered trademarks of
Novell, Inc. UNIX is a registered trademark in the United States and other countries, licensed exclusively
through X/Open Company, Ltd.
Netscape Navigator is a registered trademark of Netscape Communications.
JavaScript is a trademark of Sun Microsystems
Wi-Fi and the Wi-Fi logo are registered trademarks of the WI-Fi Alliance.
IEEE and 802 are trademarks of the Institute of Electrical and Electronics Engineers, Inc.
All other company and product names may be trademarks of the respective companies with which they are
associated.
ENVIRONMENTAL STATEMENT
It is the policy of 3Com Corporation to be environmentally-friendly in all operations. To uphold our policy, we
are committed to:
Establishing environmental performance standards that comply with national legislation and regulations.
Conserving energy, materials and natural resources in all operations.
Reducing the waste generated by all operations. Ensuring that all waste conforms to recognized environmental
standards. Maximizing the recyclable and reusable content of all products.
Ensuring that all products can be recycled, reused and disposed of safely.
Ensuring that all products are labelled according to recognized environmental standards.
Improving our environmental record on a continual basis.
End of Life Statement
3Com processes allow for the recovery, reclamation and safe disposal of all end-of-life electronic components.
Regulated Materials Statement
3Com products do not contain any hazardous or ozone-depleting material.
Environmental Statement about the Documentation
The documentation for this product is printed on paper that comes from sustainable, managed forests; it is
fully biodegradable and recyclable, and is completely chlorine-free. The varnish is environmentally-friendly, and
the inks are vegetable-based with a low heavy-metal content.
Page 3
CONTENTS
ABOUT THIS GUIDE
Naming Convention 7
Conventions 8
Feedback About This User Guide 9
Related Documentation 9
INTRODUCING THE ROUTER
Wireless 11n Cable/DSL Firewall Router 11
Router Advantages 13
Package Contents 13
Minimum System and Component Requirements 14
Physical Features 14
INSTALLING THE ROUTER
Introduction 19
Safety Information 19
Positioning the Router 19
Using the Rubber Feet 20
Wall Mounting 20
Powering Up the Router 21
Connecting the Router 21
SETTING UP YOUR COMPUTERS
Obtaining an IP Address Automatically 25
Windows 2000 25
Windows Vista 27
Windows XP 28
Macintosh 28
Page 4
Disabling PPPoE and PPTP Client Software 29
Disabling Web Proxy 29
RUNNING THE SETUP WIZARD
Accessing the Setup Wizard 31
Wizard Change Password 34
Wizard Time and Time Zone 34
Wizard Connection Type 35
Setup Wizard - LAN Settings 42
Wizard - Wireless Setting 43
Wizard - Configuration Summary 44
CONFIGURING THE ROUTER
Navigating Through the Router Configuration screens 45
Main Menu 45
Welcome Screen 45
Status 45
LAN Settings 46
LAN Settings 46
DHCP Clients List 47
Wireless Settings 49
Configuration 50
Encryption 51
WPS 56
Connection Control 57
Client List 58
WMM 59
WDS 60
Advanced 61
Internet Settings 62
WAN 62
DNS 69
Clone MAC address 70
Page 5

Firewall 71
SPI 71
Special Applications 75
Virtual Servers 76
DMZ 77
PC Privileges 78
Schedule Rule 80
URL Filter 81
Advanced 82
Security 82
VLAN 85
Static Routes 85
RIP 87
DDNS 89
SNMP 90
Syslog 91
Proxy ARP 92
QoS Settings 93
VPN 94
System Tools 98
Restart Router 98
Configuration 98
Upgrade 99
Time Zone 100
Ping 101
Traceroute 102
DNS Lookup 103
Status and Logs 104
Status 104
Routing Table 104
Logs 105
Traffic Statistics 105
Support/Feedback 106
Support 106
Feedback 106
Page 6
TROUBLESHOOTING
Basic Connection Checks 107
Browsing to the Router Configuration Screens 107
Connecting to the Internet 108
Forgotten Password and Reset to Factory Defaults 108
Wireless Networking 109
Recovering from Corrupted Software 111
Frequently Asked Questions 112
IP ADDRESSING
The Internet Protocol Suite 113
Managing the Router over the Network 113
IP Addresses and Subnet Masks 113
How does a Device Obtain an IP Address and Subnet Mask? 115
DHCP Addressing 115
Static Addressing 115
Auto-IP Addressing 115
TECHNICAL SPECIFICATIONS
3Com Wireless 11n Cable/DSL Firewall Router 117
Standards 118
SAFETY INFORMATION
END USER SOFTWARE LICENSE AGREEMENT
OBTAINING SUPPORT FOR YOUR PRODUCT
Page 7
GLOSSARY
REGULATORY NOTICES
INDEX
Page 8

Page 9
ABOUT THIS GUIDE
This guide describes how to install and configure the 3Com Wireless 11n
ADSL Firewall Router (3CRWDR300A-73, 3CRWDR300B-73).
This guide is intended for use by those responsible for installing and
setting up network equipment; consequently, it assumes a basic working
knowledge of LANs (Local Area Networks) and Internet Routers.
If a release note is shipped with the 3Com Wireless 11n ADSL Firewall
Router and contains information that differs from the information in this
guide, follow the information in the release note.
Most user guides and release notes are available in Adobe Acrobat
Reader Portable Document Format (PDF) on the 3Com World Wide Web
site:
http://www.3Com.com
Naming Convention Throughout this guide, the 3Com Wireless 11n ADSL Firewall Router is
referred to as the “Router”.
Category 3 and Category 5 Twisted Pair Cables are referred to as Twisted
Pair Cables throughout this guide.
Page 10
8 ABOUT THIS GUIDE
Conventions Ta bl e 1 and Tab l e 2 list conventions that are used throughout this guide.
Tab le 1 Notice Icons
Icon Notice Type Description
Information note Information that describes important features or
instructions.
Caution Information that alerts you to potential loss of data or
potential damage to an application, system, or device.
Warning Information that alerts you to potential personal
injury.
Tab le 2 Text Conventions
Convention Description
The words “enter”
and “type”
When you see the word “enter” in this guide, you must type
something, and then press Return or Enter. Do not press
Return or Enter when an instruction simply says “type.”
Keyboard key names If you must press two or more keys simultaneously, the key
names are linked with a plus sign (+). Example:
Press Ctrl+Alt+Del
Words in italics Italics are used to:
■ Emphasize a point.
■ Denote a new term at the place where it is defined in the
text.
■ Identify menu names, menu commands, and software
button names. Examples:
From the Help menu, select Contents.
Click OK.
Page 11
Feedback About This User Guide 9
Feedback About This User Guide
Related Documentation
Your suggestions are very important to us. They will help make our
documentation more useful to you. Please e-mail comments about this
document to 3Com at:
pddtechpubs_comments@3com.com
Please include the following information when commenting:
■ Document title
■ Document part number (on the title page)
■ Page number (if appropriate)
Example:
■ 3Com Wireless 11n ADSL Firewall Router User Guide
■ Part Number 10015880 Rev. AA
■ Page 24
Do not use this e-mail address for technical support questions. For
information about contacting Technical Support, please refer to
Appendix C
.
In addition to this guide, each Router document set includes one
Installation Guide. This guide contains the instructions you need to install
and configure your Router.
Page 12

10 ABOUT THIS GUIDE
Page 13
1
INTRODUCING THE ROUTER
Welcome to the world of networking with 3Com®. In the modern
business environment, communication and sharing information is crucial.
Computer networks have proved to be one of the fastest modes of
communication but, until recently, only large businesses could afford the
networking advantage.
Wireless 11n ADSL Firewall Router
The 3Com Wireless 11n ADSL Firewall Router is designed to provide a
cost-effective means of sharing a single broadband Internet connection
amongst several wired and wireless computers. The Router also provides
protection in the form of an electronic “firewall” preventing anyone
outside of your network from seeing your files or damaging your
computers. The Router can also prevent your users from accessing Web
sites which you find unsuitable.
Figure 1 shows an example network without a Router. In this network,
only one computer is connected to the Internet. This computer must
always be powered on for the other computers on the network to access
the Internet.
Page 14

12 CHAPTER 1: INTRODUCING THE ROUTER
Figure 1 Example Network Without a Router
When you use the Router in your network (Figure 2), it becomes your
connection to the Internet. Connections can be made directly to the
Router, or to an OfficeConnect Switch or Hub, expanding the number of
computers you can have in your network.
Figure 2 Example Network Using a Firewall Router
Page 15
Router Advantages The advantages of the Router include:
■ Shared Internet connection for both wired and wireless computers
■ High speed 802.11n wireless networking
■ No need for a dedicated, “always on” computer serving as your
Internet connection
■ Cross-platform operation for compatibility with Windows, Unix and
Macintosh computers
■ Easy-to-use, Web-based setup and configuration
■ Provides centralization of all network address settings (DHCP)
■ Acts as a Virtual server to enable remote access to Web, FTP, and other
services on your network
■ Security — Firewall protection against Internet hacker attacks and
encryption to protect wireless network traffic
Package Contents The Router kit includes the following items:
Router Advantages 13
■ One 3Com Wireless 11n ADSL Firewall Router
■ One power adapter for use with the Router
■ Four rubber feet
■ One Ethernet cable
■ One CD-ROM containing this User Guide, copies of the quick install
guide in various languages and the 3Com Detect application.
■ Installation guide
■ Support and Safety sheet
■ Warranty sheet
If any of these items are missing or damaged, please contact your retailer.
Page 16
14 CHAPTER 1: INTRODUCING THE ROUTER
Minimum System and Component Requirements
Your Router requires that the computer(s) and components in your
network be configured with at least the following:
■ A computer with an operating system that supports TCP/IP
networking protocols (for example Windows 2000/XP,/Vista, Unix,
Mac OS 8.5 or higher).
■ An Ethernet 10 Mbps or 10/100 Mbps or 10/100/1000 Mbps NIC for
each computer to be connected to the four-port switch on your
Router.
■ An 802.11b, 802.11g or 802.11n draft2.0 compliant wireless NIC.
■ An active ADSL subscription and connection.
■ A Web browser that supports JavaScript, such as Netscape 4.7 or
higher, Internet Explorer 6.0 or higher, or Mozilla 1.2.1 or higher, or
Apple’s Safari.
Physical Features The front panel of the Router contains a series of indicator lights (LEDs)
that help describe the state of various networking and connection
operations.
Figure 3 Router - Front Panel
Page 17
Physical Features 15
1 Power LED (Illuminated Logo)
White
The 3Com logo serves as power OK indicator. This LED will light if the
router is receiving power from the power adapter. If it is not lit check the
power adapter connections. Refer to Chapter 6 Troubleshooting
.
2 Alert LED
Amber
Fast flash during self test. If self test fails the LED will remain on.
Fast flash during software upgrade.
Fast flash for software reset to the factory defaults.
Fast flash for hardware reset to the factory defaults.
The LED is on for 2 seconds when the firewall detects a hacker attack.
3DSL
Blue
LED on indicates the Internet connection is on.
Fast flash means WAN port traffic activity.
4 Wireless LAN (WLAN) Status LED
Blue
If the LED is on it indicates that wireless networking is enabled. If the LED
is flashing, the link is OK and data is being transmitted or received. If the
LED is off, the Wireless LAN has been disabled in the Router, or there is a
problem. Refer to Chapter 6 Troubleshooting
.
5 LAN Status LEDs (4 indicators)
Blue
If the LED is on, the link between the port and the next piece of network
equipment is OK. If the LED is flashing, the link is OK and data is being
transmitted or received. If the LED is off, nothing is connected, or the
connected device is switched off, or there is a problem with the
connection (refer to Chapter 6 Troubleshooting
). The port will
automatically adjust to the correct speed and duplex.
6 WPS LED
LED on indicates the WPS function is active.
Page 18
16 CHAPTER 1: INTRODUCING THE ROUTER
The rear panel (Figure 4) of the Router contains one ADSL port, four LAN
ports, one WiFi on/off button, a reset button, one power adapter socket,
and one WPS button.
Figure 4 Router - Rear Panel
1 Wireless Antennae
The antennaes should be placed in a ‘V’ position when initially installed.
CAUTION: Do not force the antennae beyond their mechanical stops.
Rotating the antennae further may cause damage.
2ADSL Port
RJ-11 port, connect this port with the telephone socket.
3 Ethernet Ports (4 ports)
Using suitable RJ-45 cables, you can connect your Router to a computer,
or to any other piece of equipment that has an Ethernet connection (for
example, a hub or a switch). These ports have an automatic MDI/MDIX
feature, which means either straight-through or a crossover cable can be
used.
4 WiFi On/Off button
Use this button to turn on/turn off the wireless function. Press the button
for 3 seconds.
Page 19
Physical Features 17
5 Reset Button
If you want to reset your Router to factory default settings, or cannot
access the web management interface (for example, due to a lost
password), then you may use this button. Refer to Forgotten Password
and Reset to Factory Defaults on page 108 for further details.
6 Power Adapter Socket
Only use the power adapter that is supplied with this Router. Do not use
any other adapter.
7 WPS button
Press this button for 3 seconds when making WPS setup. Pushing the
WPS button will automatically enable WPS. Then initiate the WPS
procedure on the wireless NIC within two minutes. Refer to your wireless
NIC's documentation on this procedure. The wireless NIC will then be
securely added to your wireless network.
Page 20

18 CHAPTER 1: INTRODUCING THE ROUTER
Page 21
INSTALLING THE ROUTER
2
Introduction This chapter will guide you through a basic installation of the Router,
including:
■ Connecting the Router to the Internet.
■ Connecting the Router to your network.
■ Setting up your computers for networking with the Router.
Safety Information Please note the following:
Positioning the Router
WARNING: Please read the Safety Information
before you start.
VORSICHT: Bitte lesen Sie den Abschnitt Wichtige Sicherheitshinweise
sorgfältig durch, bevor Sie das Gerät einschalten.
AVERTISSEMENT: Veuillez lire attentivement la section Consignes
importantes de sécurité avant de mettre en route.
You should place the Router in a location that:
■ is conveniently located for connection to the telephone socket.
■ is centrally located to the wireless computers that will connect to the
Router. A suitable location might be on top of a high shelf or similar
furniture to optimize wireless connections to computers in both
horizontal and vertical directions, allowing wider coverage.
■ allows convenient connection to the computers that will be connected
to the four LAN ports on the rear panel, if desired.
■ allows easy viewing of the LED indicator lights, and access to the rear
panel connectors, if necessary.
section in Appendix C
Page 22
20 CHAPTER 2: INSTALLING THE ROUTER
When positioning your Router, ensure:
■ It is out of direct sunlight and away from sources of heat.
■ Cabling is away from power lines, fluorescent lighting fixtures, and
sources of electrical noise such as radios, transmitters and broadband
amplifiers.
■ Water or moisture cannot enter the case of the unit.
■ Air flow around the unit and through the vents in the side of the case
is not restricted. 3Com recommends you provide a minimum of
25 mm (1 in.) clearance.
Using the Rubber
Feet
Use the four self-adhesive rubber feet to prevent your Router from
moving around on your desk or when stacking with flat top units. Only
stick the feet to the marked areas at each corner of the underside of your
Router.
Please be careful when you put WL-603 on top of another unit, if the unit
underneath is hot, this may impact the reliability of WL-603.
Wall Mounting There are two slots on the underside of the Router that can be used for
wall mounting. The Router must be mounted with the LEDs facing
upwards.
When wall mounting the unit, ensure it is within reach of the power
outlet. When wall mounting the unit, ensure that the rubber feet are not
fixed.
Mounting
Instructions for
Cement Walls
To wall mount the unit:
1 Make two holes 100 mm (3.9 in.) apart and insert two nylon or similar
screw anchors that are suitable for the wall construction.
2 Fix two suitable screws into the anchors, leaving their heads 3 mm (0.12
in.) clear of the wall surface. The screws should be at least 30 mm (1.2
in.) long.
3 Remove any connections in the Router and locate it over the screw heads.
When in line, gently push the Router on to the wall and move it
downwards to secure.
Page 23

Powering Up the Router 21
Mounting
Instructions for
Wood Walls
Powering Up the Router
To wall mount the unit:
1 Make two holes 100 mm (3.9 in.) apart.
2 Fix two suitable screws directly into the wall, leaving their heads 3 mm
(0.12 in.) clear of the wall surface. The screws should be at least 20 mm
(0.75 in.) long.
3 Remove any connections in the Router and locate it over the screw heads.
When in line, gently push the Router on to the wall and move it
downwards to secure.
CAUTION: When making connections, be careful not to push the unit up
and off the wall.
To power up the Router:
1 Plug the power adapter into the power adapter socket located on the
back panel of the Router.
2 Plug the power adapter into a standard electrical wall socket.
Connecting the Router
The first step for installing your Router is to physically connect it to the
telephone socket and then connect it to a computer in order to be able to
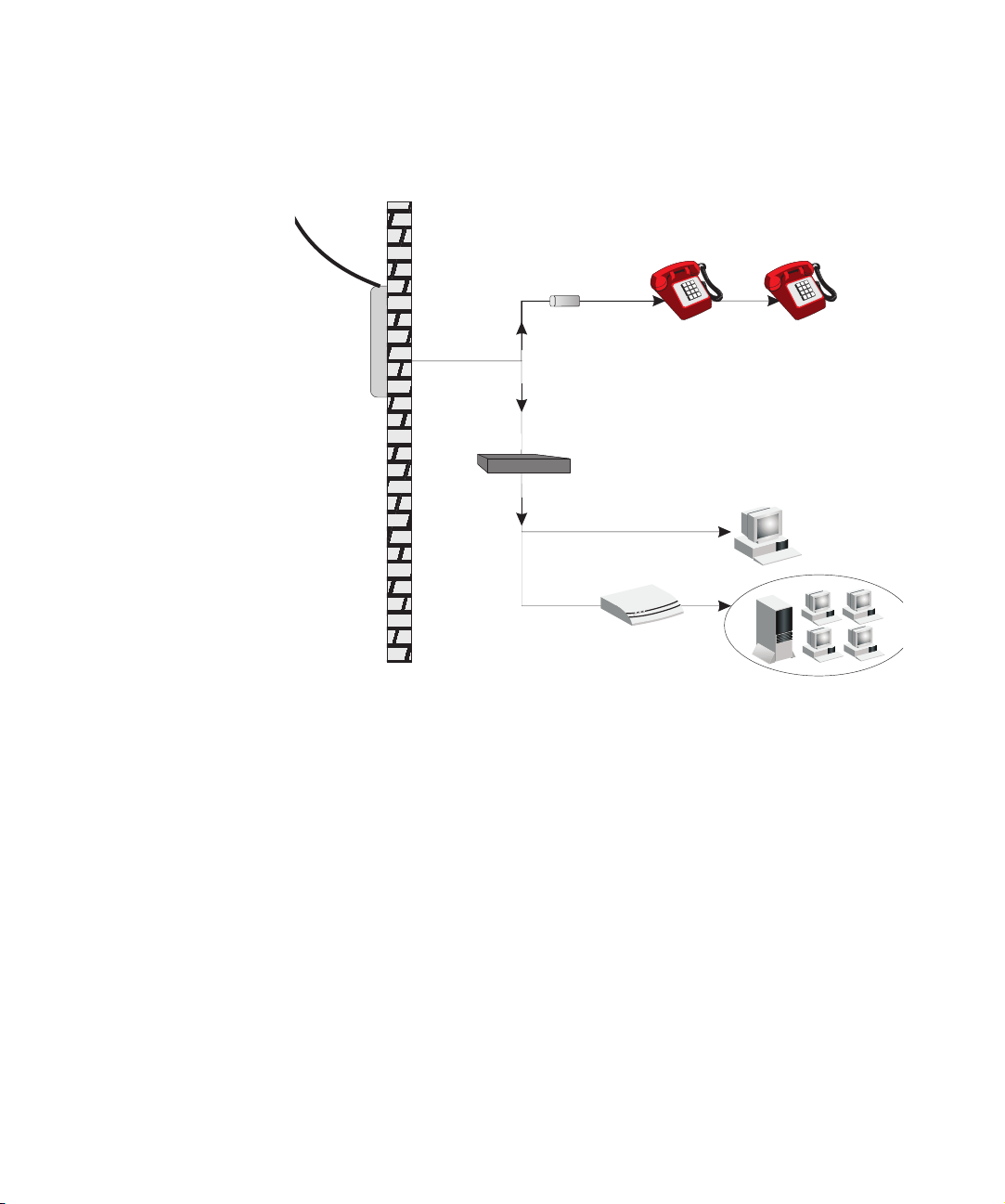
access the Internet. See Figure 5:
Page 24

22 CHAPTER 2: INSTALLING THE ROUTER
Figure 5 Connecting the Router
1 Run the provided telephone cable from the wall jack providing ADSL
service to the ADSL port on your Router. When inserting an ADSL RJ-11
plug, be sure the tab on the plug clicks into position to ensure that it is
properly seated. If you are using splitterless ADSL service, add low-pass
filters between the ADSL wall jack and your telephones. (These filters pass
voice signals through but filter data signals out.)
2 Then:
■ If you are using a full-rate (G.dmt) connection, your service provider
will attach the outside ADSL line to a data/voice splitter. In this case
you can connect your phones and computer directly to the splitter as
shown below (Figure 6):
or
■ If you are using a splitterless (G.lite) connection, then your service
provider will attach the outside ADSL line directly to your phone
system. In this case you can connect your phones and computer
directly to the incoming ADSL line, but you will have to add low-pass
filters to your phones as shown below (Figure 7)
Page 25
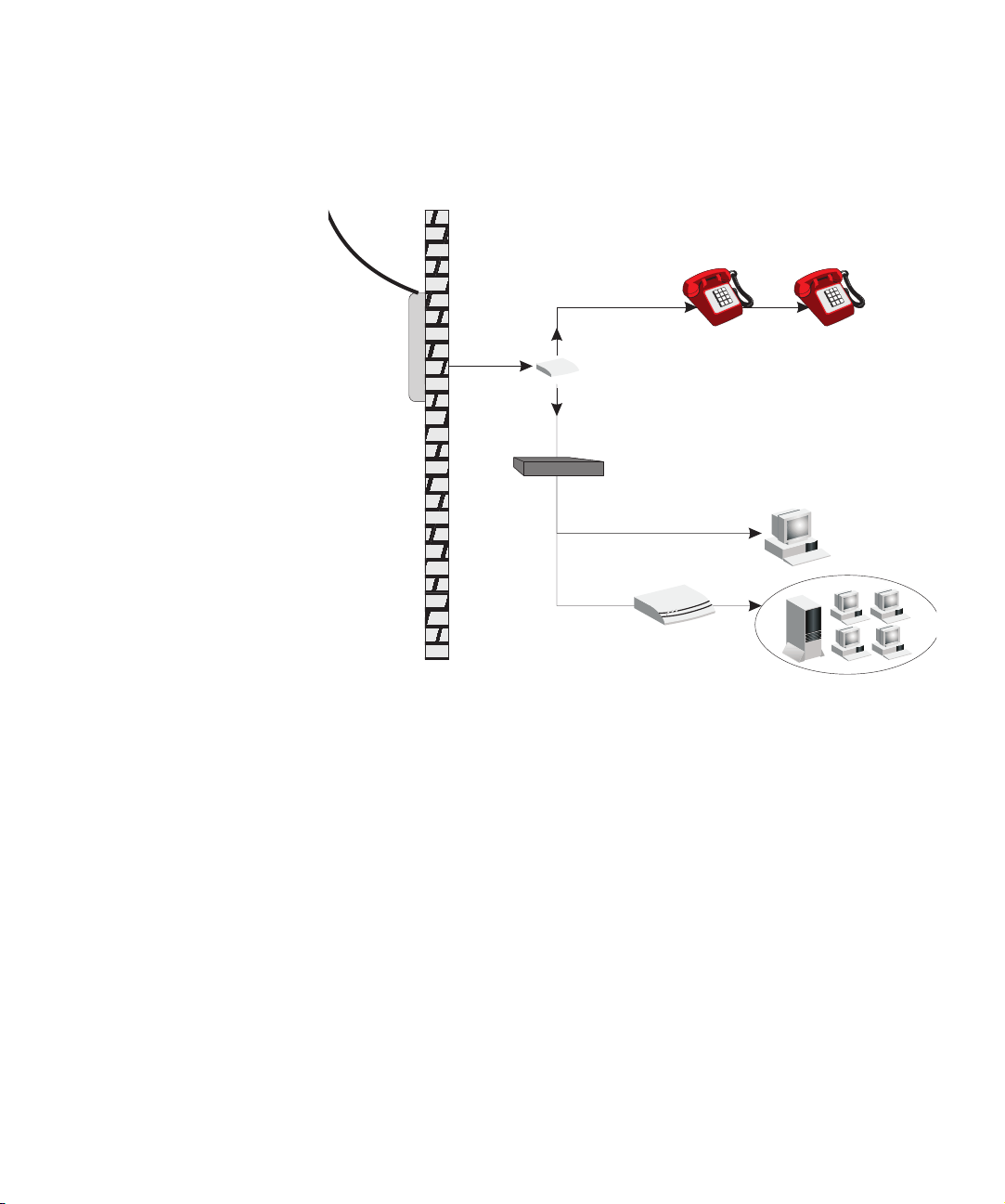
Figure 6 Installing with a splitter
Voice
Data
Residential
Connection
Point (NID)
Plain Old
Telephone
System (POTS)
or
Ethernet
hub or switch
Splitter
Router
Connecting the Router 23
Page 26
24 CHAPTER 2: INSTALLING THE ROUTER
Plain Old
Telephone
System (POTS)
Filter
or
Ethernet
hub or switch
Voice
& Data
Voice
& Data
Data
Voice
Residential
Connection
Point [Network
Interface
Device (NID)]
Router
Figure 7 Installing without a splitter
You have now completed the hardware installation of your Router. Next
you need to set up your computers so that they can make use of the
Router to communicate with the Internet.
3Com recommends that you perform the initial Router configuration
from a computer that is directly connected to one of the LAN ports.
If you configure the Router from a wireless computer, note that you may
lose contact with the Router if you change the wireless configuration.
To communicate wirelessly with your Router, your wireless NIC should be
set as follows:
■ Encryption — none
■ SSID — 3Com
■ Channel — 11
Page 27
3
Obtaining an IP Address Automatically
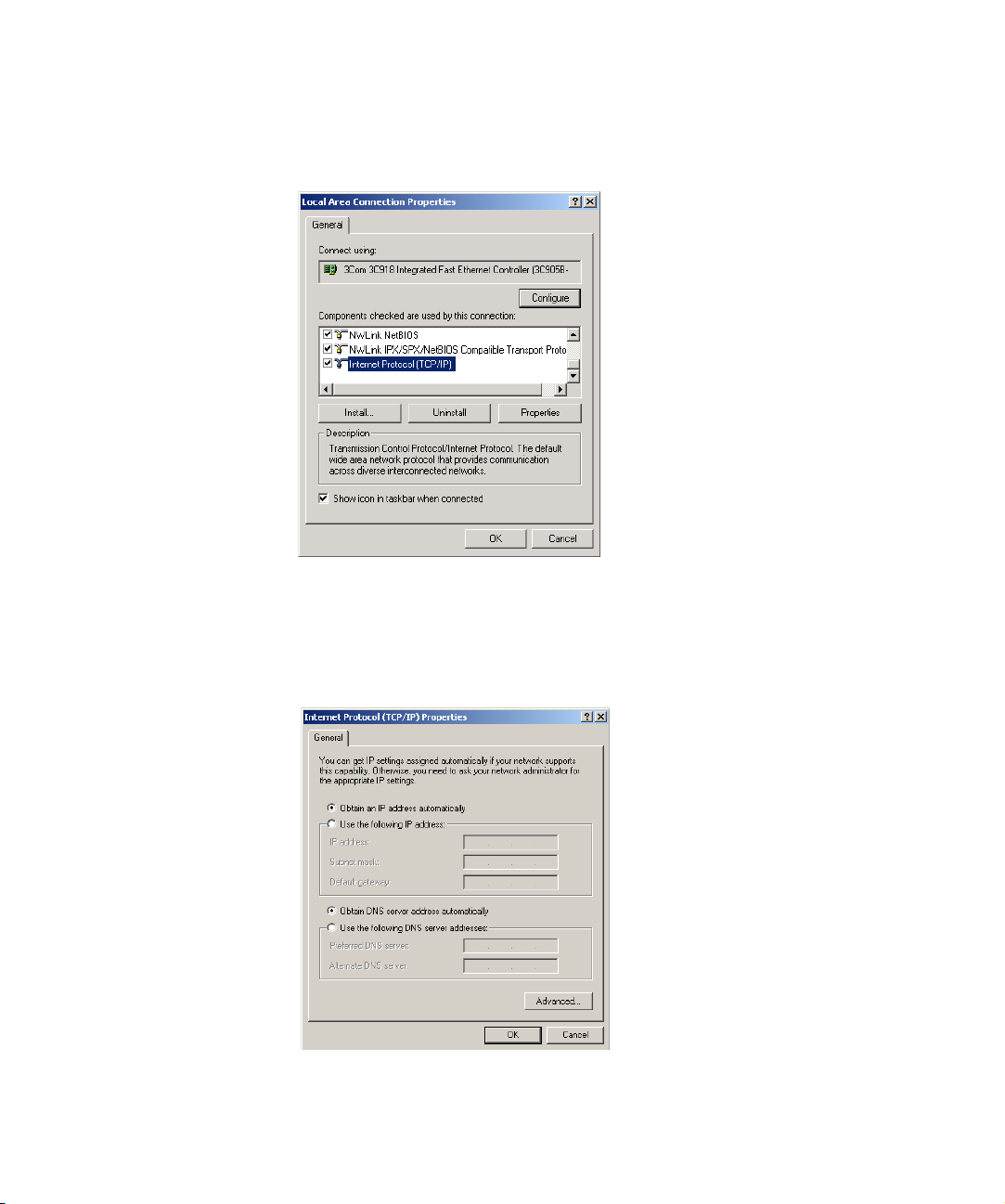
Windows 2000 If you are using a Windows 2000-based computer, use the following
SETTING UP YOUR COMPUTERS
The Router has the ability to dynamically allocate network addresses to
the computers on your network, using DHCP. However, your computers
need to be configured correctly for this to take place. To change the
configuration of your computers to allow this, follow the instructions in
this chapter.
procedure to change your TCP/IP settings:
1 From the Windows Start Menu, select Settings > Control Panel.
2 Double click on Network and Dial-Up Connections.
3 Double click on Local Area Connection.
4 Click on Properties.
5 A screen similar to Figure 8 should be displayed. Select Internet Protocol
TCP/IP and click on Properties.
Page 28
26 CHAPTER 3: SETTING UP YOUR COMPUTERS
Figure 8 Local Area Properties Screen
6 Ensure that the options Obtain an IP address automatically, and Obtain
DNS server address automatically are both selected as shown in Figure 9.
Click OK.
Figure 9 Internet Protocol (TCP/IP) Properties Screen
7 Restart your computer.
Page 29

Windows Vista
Obtaining an IP Address Automatically 27
1 From the Windows Start Menu, select Settings > Network.
2 Click on Organize. Select Properties.
3 Click on Manage network > Connections.
4 Double click Local Area Connection. Select Properties and click continue.
5 A screen similar to (Figure 10) should appear. Select Internet Protocol
Version 6,Version 4 (TCP/IPv6,v4) and click on Properties.
Figure 10 Local Area Connection Properties Screen
6 Ensure that the options Obtain an IPv6,v4 address automatically, and
Obtain DNS servers address automatically are both selected as shown in
(Figure 11). Click OK.
Figure 11 Internet Protocol Version 6 (TCP/IPv6) Properties Screen
Page 30

28 CHAPTER 3: SETTING UP YOUR COMPUTERS
Windows XP
1 From the Windows Start Menu, select Control Panel.
2 Click on Network and Internet Connections.
3 Click on the Network Connections icon.
4 Double click on LAN or High Speed Connection icon. A screen titled Local
Area Connection Status will appear.
5 Select Internet Protocol TCP/IP and click on Properties.
6 Ensure that the options Obtain an IP address automatically, and Obtain
DNS servers automatically are both selected. Click OK.
7 Restart your computer.
Macintosh If you are using a Macintosh computer, use the following procedure to
change your TCP/IP settings:
1 From the desktop, select Apple Menu, Control Panels, and TCP/IP.
2 In the TCP/IP control panel, set Connect Via: to Ethernet.
3 In the TCP/IP control panel, set Configure: to Using DHCP Server.
4 Close the TCP/IP dialog box, and save your changes.
5 Restart your computer.
Page 31
Disabling PPPoE and PPTP Client Software 29
Disabling PPPoE and PPTP Client Software
If you have PPPoE client software installed on your computer, you will
need to disable it. To do this:
1 From the Windows Start Menu, select Settings > Control Panel.
2 Double click on Internet Options.
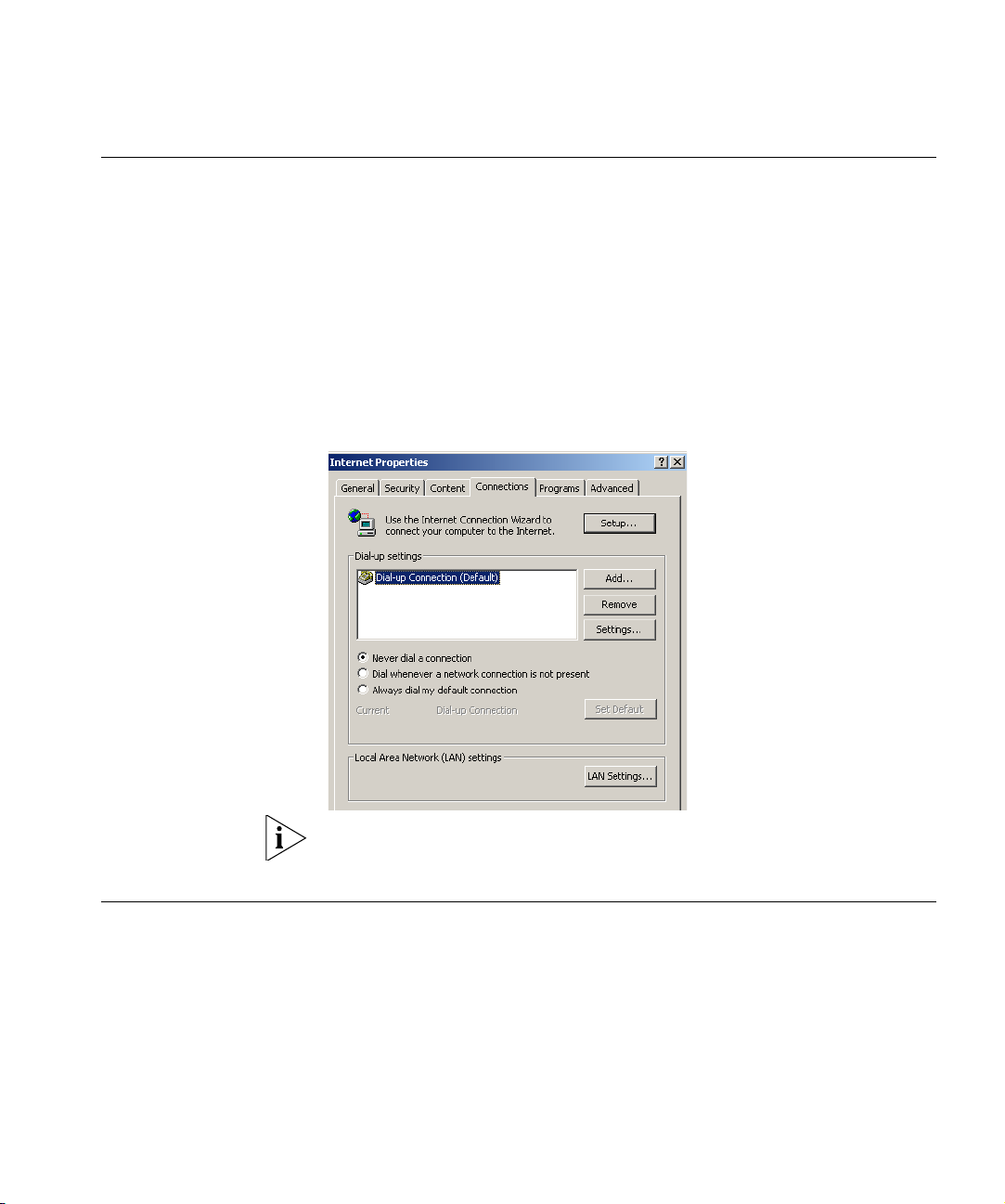
3 Select the Connections Tab. A screen similar to Figure 12 should be
displayed.
4 Select the Never dial a connection option.
Figure 12 Internet Properties Screen
Disabling Web Proxy
You may want to remove the PPPoE client software from your computer
to free resources, as it is not required for use with the Router.
Ensure that you do not have a web proxy enabled on your computer.
Go to the Control Panel and click on Internet Options. Select the
Connections tab and click LAN Settings at the bottom. Make sure that
the Use Proxy Server option is unchecked.
Page 32

30 CHAPTER 3: SETTING UP YOUR COMPUTERS
Page 33
4
RUNNING THE SETUP WIZARD
Accessing the Router using the 3Com Detect Application
Running the 3Com Detect Application
The 3Com Detect application works by automatically locating your
Router, establishing what IP address it is using and then launching your
default web browser to connect directly to it.
The application will only locate your Router if it is on the same subnet as
the PC on which the application is running. It will not be able to locate
your Router if there is another router between your PC and the Router.
The application is only designed to run on Windows operating systems.
The CD-ROM that comes with this Router contains, in addition to the
documentation, the 3Com Detect Application.
To use 3Com Detect to connect to the Web interface of your Router, do
the following:
On the computer that is connected to your Router (either directly or on a
network that is on the same subnet), insert the CD-ROM into its CD drive.
If you have autorun enabled, you will be presented with a menu showing
the contents of the CD-ROM. Select the 3Com Detect Application link to
install the utility. Follow the onscreen instructions.
If the auto-run program does not start, you should browse to your
CD-ROM drive, go to the /switch detect directory and double click on
setup.exe. Follow the prompts that will take you through the installation
process.
Once installed, the 3Com Detect Application can be accessed from the
Windows Start/Programs list.
When the 3Com Detect application starts, you will see the Welcome
Screen, see Figure 11.
Page 34

32 CHAPTER 4: RUNNING THE SETUP WIZARD
Figure 13 3Com Detect Application
If the computer has multiple network adapters, select the adapter that
connects the computer to the network or the Router, click Next.
You will then be offered the choice of searching the same subnet that
your PC is on for a connected Router (default), or specifying an IP range.
Note that specifying a large range may take some time for the search to
complete (see Figure 14 and Figure 15).
Figure 14 Discovery Screen - search the same subnet
Figure 15 Discovery Screen - search IP range
Once your Router has been located, you will see the list (see Figure 16).
Select the Router to which you want to connect and click Open. Your
default Web browser will launch and connect to the home page of the
Router, (seeFigure 18 ).
Page 35

Figure 16 Router List Screen
Accessing the Setup Wizard 33
Accessing the Setup Wizard
The Router setup program is Web-based, which means that it is accessed
through your Web browser (Netscape Navigator 4.7 or higher, Internet
Explorer 6.0 or higher, or Mozilla 1.2.1 or higher, or Apple’s Safari).
To use the Setup Wizard:
1 Ensure that you have at least one computer connected to the Router.
Refer to Chapter 2 for details on how to do this.
2 Launch your Web browser on the computer.
3 Enter the following URL in the location or address field of your browser:
http://192.168.1.1 (Figure 17). The Login screen displays.
Figure 17 Web Browser Location Field (Factory Default)
Page 36

34 CHAPTER 4: RUNNING THE SETUP WIZARD
4 To log in as an administrator, enter the password (the default password is
admin) in the System Password field and click Log in (see Figure 18).
Figure 18 Router Login Screen
5 When you have logged in,
■ if you are logging in for the first time, the Country Selection screen
will appear (see Figure 19). Please select the country form the
drop-down menu, and click Apply.
1. Note to US model owner: To comply with US FCC regulation, the
country selection function has been completely removed from all US
models. The above function is for non-US models only.
Figure 19 Country Selection Screen
The Wizard will then launch automatically (refer to Figure 22). You will be
guided step by step through a basic setup procedure.
■ if the Router has been configured previously, the Welcome screen will
appear (Figure 20). There are three tabs: Notice Board, Password and
Wizard.
Page 37

Accessing the Setup Wizard 35
Figure 20 Welcome Screen
■ Go to the Notice Board tab to see the current software information. To
view the Web help, click the Help button.
■ Go to the Password tab to change the password (Figure 21).
■ Go to the Wizard tab to do a quick setup of the Router (Figure 22).
The password screen allows you to change the current password and set
the login time limit to the Router’s management interface.
Figure 21 Password Screen
1 To change the current password, enter the password in the Current
Password field.
2 Enter the new password in the New Password field, and enter it again in
the Confirm New Password field.
Page 38

36 CHAPTER 4: RUNNING THE SETUP WIZARD
3 Enter the time period in Login Timeout to set a maximum period of time
for which the login session is maintained during inactivity (Default: 10
minutes).
Wizard -
Change Password
Wizard -
Time and Time Zone
To ensure the security of your Router, it is recommended that you choose
a new password - this should be a mix of letters and numbers, and not
easily guessed by others. To leave the current password unchanged, leave
the fields blank and click Next.
Figure 22 Change Password Screen
The Time and Time Zone screen allows you to set up the time for the
Router.
Figure 23 Time and Time Zone Screen
Page 39

Accessing the Setup Wizard 37
1 Select the correct base date and time.
2 If you want to automatically synchronize the Router with a public time
server, check the Enable box in the Using Time Server (NTP) field.
3 Select the time zone in the Set Time Zone drop-down menu.
4 Enter the time in the Synchronization Interval field.
5 Select the desired servers from the Time Server drop-down menu.
6 Check the Enable box in the Daylight Savings field, if daylight savings
applies to your area.
7 Click Next.
Wizard -
Connection Type
The Connection Type screen allows you to set up the Router for the type
of Internet connection you have. Before setting up your connection type,
have your account information from your ISP ready.
Figure 24 Connection Type Screen
Select a mode from the following:
■ PPPoE — PPP over Ethernet, providing routing for multiple PCs,
see page 39
■ PPPoA — PPP over ATM, providing routing for multiple PCs,
see page 40
■ Bridge Mode (for a single PC) — RFC1483 Bridged Mode, see page 41
■ Routing Mode over ATM — RFC1483 Routed Mode, for multiple PCs,
see page 42
Page 40

38 CHAPTER 4: RUNNING THE SETUP WIZARD
■ Dynamic/Fixed IP in 1483 Bridge Mode (For Multiple PCs) — see
page 43
and click Next.
For further information on selecting a mode see Internet Settings on
page 62.
Page 41

Accessing the Setup Wizard 39
PPPoE
PPPoE is often used for DSL connection. To set up the Router for use with
a PPPoE (PPP over Ethernet) connection, use the following procedure:
Figure 25 PPPoE Screen
1 Enter your user name in the Username field.
2 Enter your password in the Password field.
3 Re-type your password in the Retype Password field.
4 Enter your VPI and VCI information in the VPI/VCI fields.
5 Select the encapsulation type (LLC or VC MUX) in the Encapsulation
drop-down menu. This information should be provided to you by your ISP.
Check all of your settings, and then click Next.
The LAN Settings screen will then be displayed (refer to Figure 30).
Page 42

40 CHAPTER 4: RUNNING THE SETUP WIZARD
PPPoA
To set up the Router for use with a PPP over ATM (PPPoA) connection, use
the following procedure:
Figure 26 PPPoA Screen
1 Enter your user name in the Username field.
2 Enter your password in the Password field.
3 Re-type your password in the Retype Password field.
4 Enter your VPI and VCI information in the VPI/VCI fields.
5 Select the encapsulation type (LLC or VC MUX) in the Encapsulation
drop-down menu. This information should be provided to you by your ISP.
Check all of your settings, and then click Next.
The LAN Settings screen will then be displayed (refer to Figure 30).
Page 43

Accessing the Setup Wizard 41
Bridge Mode (for a single PC)
To set up the Router for use with an RFC1483 bridged connection, use
the following procedure:
Figure 27 Bridged Mode Screen
1 Enter your VPI and VCI information in the VPI/VCI fields.
2 Select the encapsulation type (LLC or VC MUX) in the Encapsulation
drop-down menu. This information should be provided to you by your ISP.
Check all of your settings, and then click Next.
The LAN Settings screen will then be displayed (refer to Figure 30).
Page 44

42 CHAPTER 4: RUNNING THE SETUP WIZARD
Routing Mode over ATM
To set up the Router for use with an RFC1483 routed connection, use the
following procedure:
Figure 28 Routing mode over ATM Screen
1 Enter your Internet IP address in the WAN IP field.
2 Enter the subnet mask in the Subnet Mask field.
3 Enter the default gateway IP address in the Default Gateway field.
4 Enter the DNS address in the DNS field.
5 Enter your VPI and VCI information in the VPI/VCI fields.
6 Select the encapsulation type (LLC or VC MUX) in the Encapsulation
drop-down menu. This information should be provided to you by your ISP.
Check all of your settings, and then click Next.
The LAN Settings screen will then be displayed (refer to Figure 30).
Page 45

Accessing the Setup Wizard 43
Dynamic/Fixed IP in 1483 Bridge Mode (For Multiple PCs)
For bridge mode to work, you need to assign an IP address to the Router.
You can either configure the Router to obtain an IP address automatically
from a DHCP server or assign a fixed or static IP address to it.
Figure 29 Dynamic/Fixed IP for Bridge Mode Screen
■ To obtain an IP address automatically from a DHCP server: check the
Get WAN IP By DCHP checkbox, and then click Next.
■ To assign a fixed IP address:
1 Enter your IP address in the WAN IP field.
2 Enter the subnet mask in the Subnet Mask field.
3 Enter the default gateway IP address in the Default Gateway field.
4 Enter the DNS address in the DNS field.
5 Enter your VPI and VCI information in the VPI/VCI fields.
6 Select the encapsulation type (LLC or VC MUX) in the Encapsulation
drop-down menu. This information should be provided to you by your ISP.
Check all of your settings, and then click Next.
The LAN Settings screen will then be displayed (refer to Figure 30).
Page 46

44 CHAPTER 4: RUNNING THE SETUP WIZARD
Setup Wizard - LAN
Settings
The LAN Settings screen allows you to set the default IP address and
DHCP client IP range for the Router.
Figure 30 The LAN Settings Screen
1 To change the Router’s default IP address, enter the new IP address in the
IP Address field, and then enter the subnet mask in the Subnet Mask
field.
2 Check the Enable DHCP Server box to enable the DHCP function.
3 Enter the client IP address range in the IP Pool Start Address and IP Pool
End Address fields. You can also click Auto IP Range to automatically set
the starting and ending IP address: 192.168.1.2 ~ 192.168.1.254.
4 Click Next. The Wireless Settings screen will appear (refer to Figure 31).
Page 47

Accessing the Setup Wizard 45
Wizard - Wireless
Setting
The Wireless Settings screen allows you to set up the SSID and radio
channel used for the wireless connection.
Figure 31 Wireless Setting Screen
1 Select the channel you want to use from the Channel drop-down menu.
2 Specify the SSID to be used by your wireless network in the SSID field. If
there are other wireless networks in your area, you should give your
wireless network an unique name.
3 Select the Security Mode from the drop-down menu. Five options
available:
■ Disabled: in this mode, wireless transmissions will not be
encrypted, and will be visible to everyone. However, when setting
up or debugging wireless networks, it is often useful to use this
security mode.
■ 64-bit WEP, see page 46
■ 128-bit WEP, see page 47
■ WPA-PSK (no server), this mode includes WPA and WPA2,
see page 48
■ WPA (with Radius Server), this mode includes WPA and WPA2,
see page 49
Page 48

46 CHAPTER 4: RUNNING THE SETUP WIZARD
64-bit WEP
WEP is the basic mechanism to transmit your data securely over the
wireless network. Matching encryption keys must be setup on your
Router and wireless client devices to use WEP.
Figure 32 64-bit WEP Screen
Security Mode is 64-bit WEP. You can enter the 64-bit WEP key manually:
■ enter the WEP key as 5 pairs of hex digits (0-9, A-F).
Or you can generate the 64-bit WEP key automatically:
■ enter a memorable passphrase in the Passphrase box, and then click
Generate to generate the hex keys from the passphrase.
For 64-bit WEP, you can enter up to four keys, in the fields Key 1 to Key 4.
The radio button on the left hand side selects the key that is used in
transmitting data.
Note that all four WEP keys on each device of the same wireless network
must be identical.
Click Next.
Page 49

Accessing the Setup Wizard 47
128-bit WEP
WEP is the basic mechanism to transmit your data securely over the
wireless network. Matching encryption keys must be set up on your
Router and wireless client devices to use WEP.
Figure 33 128-bit WEP
Security Mode is 128-bit WEP. You can enter the 128-bit WEP key
manually:
■ enter your WEP key as 13 pairs of hex digits (0-9, A-F).
Or you can generate the 128-bit WEP key automatically:
■ enter a memorable passphrase in the Passphrase box, and then click
Generate to generate the hex keys from the passphrase.
Note that the WEP keys on each device of the same wireless network
must be identical. And In 128-bit WEP mode, only one WEP key can be
specified.
Click Next.
Page 50

48 CHAPTER 4: RUNNING THE SETUP WIZARD
WPA-PSK (no server)
WPA (Wi-Fi Protected Access) provides dynamic key changes and
constitutes the best security solution. If your network does not have a
RADIUS server. Select the no server option. Note that in home and very
small office deployments, PSK is typically used.
Figure 34 WPA-PSK no server Screen
1 Select WPA-PSK (no server) from the WPA drop-down menu.
2 Select WPA mode from the drop-down menu, three modes are
supported: WPA, WPA2, and Mixed mode.
3 Select Encryption technique from the drop-down menu, four options are
available: TKIP, AES, Auto for WPA AES for WPA2, and AES for both WPA
and WPA2.
4 Enter the pre-shared key in the Pre-shared Key (PSK) field. The pre-shared
key is a password, in the form of a word, phrase or series of letters and
numbers. The key must be between 8 and 63 characters long and can
include spaces and symbols. Each client that connects to the network
must use the same key.
5 If you want the key that you enter to be shown on the screen as a series
of asterisks (*), then check the Hide PSK checkbox.
6 Click Next.
Page 51

Accessing the Setup Wizard 49
WPA with Radius Server
WPA (Wi-Fi Protected Access) provides dynamic key changes and
constitutes the best security solution. This function requires that a
RADIUS server is running on the network.
Figure 35 WPA with Radius Server Screen
1 Select WPA with RADIUS server from the Security Mode drop-down
menu.
2 Select WPA mode from the drop-down menu, three modes are
supported: WPA, WPA2, and Mixed mode.
3 Select Encryption technique from the drop-down menu, four options are
available: TKIP, AES, Auto for WPA AES for WPA2, and AES for both WPA
and WPA2.
4 Enter the IP address of the RADIUS server on your network into the
RADIUS Server field.
5 Enter the Radius Port number that the RADIUS server is operating on.
6 Enter the key for the RADIUS server in the Radius Key field.
7 By default, the WPA keys are changed every hour, but if you want to
change this setting, you can do so by specifying the rotation time in the
Re-key Interval field.
8 Click Next.
Page 52

50 CHAPTER 4: RUNNING THE SETUP WIZARD
Wizard -
Configuration
Summary
When you have completed the Setup Wizard, a configuration summary
will appear. Verify the configuration information of the Router and then
click Apply to save your settings. 3Com recommends that you print out
this page for your records.
Figure 36 Configuration Summary Screen
Your Router is now configured and ready for use.
See Chapter 5 for a further detailed description of the Router
configuration.
Page 53

5
CONFIGURING THE ROUTER
Navigating Through the Router Configuration screens
Main Menu The main menu is located on the left side, as shown in Figure 30. When
Welcome Screen The Welcome screen shows the current software information.
Status
This chapter describes all the screens available through the Router
configuration screens, and is provided as a reference. To get to the
configuration screens, enter the Router’s default IP in the location bar of
your browser. The default IP is http://192.168.1.1.
However, if you changed the Router LAN IP address during initial
configuration, use the new IP address instead. Enter your password to
login to the management interface. (The default password is admin).
you click on an item from the main menu, the corresponding screen will
then appear in the center.
Figure 30 Welcome Screen
Page 54

46 CHAPTER 5: CONFIGURING THE ROUTER
LAN Settings Your Router is equipped with a DHCP server that will automatically assign
IP addresses to each computer on your network. The factory default
settings for the DHCP server will work with most applications. If you need
to make changes to the settings, you can do so.
The LAN settings screen allows you to:
■ Change the default IP address of the Router. The default IP is
192.168.1.1
■ Change the Subnet Mask. The default setting is 255.255.255.0
■ Enable/Disable the DHCP Server Function. The default is “Enable”.
■ Specify the Starting and Ending IP Pool address. The default is
Starting: 2 / Ending: 254.
■ Specify the IP address Lease Time. The default is One day.
■ Specify a local Domain Name. This field is optional.
■ Specify the IP address of 3Com NBX call processor.
The Router will also provide a list of all client computers connected to the
Router.
LAN Settings The LAN Settings screen is used to specify the LAN IP address of your
Router, and to configure the DHCP server.
Figure 31 LAN Settings Screen
Page 55

LAN Settings 47
1 Enter the Router’s IP Address and Subnet Mask in the appropriate fields.
The default IP address is 192.168.1.1.
2 If you want to use the Router as a DHCP Server, check Enable in the DHCP
Server field.
3 Enter the IP address range in the IP Pool Start Address and IP Pool End
Address fields.
4 Specify the DHCP Lease time by selecting the required value from the
Lease Time drop-down menu. The lease time is the length of time the
DHCP server will reserve the IP address for each computer.
5 Specify the Local Domain Name for your network (this step is optional).
6 Enter the IP address of the NBX Call Processor in the 3Com NBX Call
Processor field (this step is optional).
7 Check all of your settings, and then click Apply.
DHCP Clients List The DHCP Clients List provides details on the devices that have received IP
addresses from the Router. The list is only created when the Router is set
up as a DHCP server. A maximum of 253 clients can be connected to the
Router.
Figure 32 DHCP Clients List Screen
For each device that is connected to the LAN, the following information is
displayed:
■ IP address — The Internet Protocol (IP) address issued to the client
machine.
Page 56

48 CHAPTER 5: CONFIGURING THE ROUTER
■ Host Name — The client machine’s host name, if configured.
■ MAC Address — The Media Access Control (MAC) address of the
client’s network card.
■ Client Type — Whether the client is connected to the Router by wired
or wireless connection.
■ Check the Fix checkbox to permanently fix the IP address.
■ Click Release to release the displayed IP address.
■ Click Add to allocate an IP address to a MAC address. Enter the
required details and click Apply to save your settings.
The DHCP server will give out addresses to both wired and wireless
clients.
Page 57

Wireless Settings 49
Wireless Settings The Wireless Settings screens allow you to configure the settings for the
wireless connections.
You can enable or disable the wireless connection for your LAN. When
disabled, no wireless PCs can gain access to either the Internet or other
PCs on your wired or wireless LAN through this Router.
Figure 33 Wireless Settings Screen
There are 8 tabs available:
■ Configuration
■ Encryption
■ WPS
■ Connection Control
■ Client List
■ WMM
■ WDS
■ Advanced
Page 58

50 CHAPTER 5: CONFIGURING THE ROUTER
Configuration The Wireless Configuration Screen allows you to turn on/ turn off the
wireless function, and set up basic wireless settings.
Figure 34 Wireless Configuration Screen
To enable the wireless function:
1 Check Enable Wireless Networking checkbox.
2 Select the wireless channel you want to use from the Channel drop-down
menu.
3 Select the Extension Channel.
4 Specify the SSID to be used by your wireless network in the SSID field. If
there are other wireless networks in your area, you should give your
wireless network an unique name.
5 Enable or disable SSID Broadcast.
A feature of many wireless network adapters is that a computer's SSID
can be set to ANY, which means it looks randomly for any existing
wireless network. The available networks are then displayed in a site
survey, and your computer can select a network. If you disable this SSID
broadcast function, you can block this random search, and set the
computer's SSID to a specific network (for example, WLAN). This
increases network security. If you decide to enable SSID Broadcast, ensure
that you know the name of your network first.
6 Select whether your Router will operate in 11b mode only, 11g mode
only, 11n mode only, or mixed mode from the Wireless Mode drop-down
menu.
7 Bandwidth: select the bandwidth to use.
Page 59

Wireless Settings 51
8 Select to turn on/off the Protected Mode function.
9 Click Apply.
Encryption This feature prevents any non-authorized party from reading or changing
your data over the wireless network.
Figure 35 Encryption Screen
Select the wireless security mode that you want to use from the
drop-down menu, and click Apply. There are five selections:
■ Disabled
■ 64-bit WEP (see page 52)
■ 128-bit WEP (see page 53)
■ WPA-PSK (no server) (see page 54)
■ WPA (with RADIUS Server) (see page 55)
Disabled
In this mode, wireless transmissions will not be encrypted, and will be
visible to everyone. However, when setting up or debugging wireless
networks, it is often useful to use this security mode.
Page 60

52 CHAPTER 5: CONFIGURING THE ROUTER
64-bit WEP
WEP is the basic mechanism to transmit your data securely over the
wireless network. Matching encryption keys must be setup on your
Router and wireless client devices to use WEP.
Figure 36 64-bit WEP Screen
To setup 64-bit WEP:
1 You can enter the 64-bit WEP key manually:
■ enter the WEP key as 5 pairs of hex digits (0-9, A-F).
Or you can generate the 64-bit WEP key automatically:
■ enter a memorable passphrase in the Passphrase field, and then
click Generate to generate the hex keys from the passphrase.
For 64-bit WEP, you can enter up to four keys, in the fields Key 1 to Key 4.
The radio button on the left hand side selects the key that is used in
transmitting data.
Note that all four WEP keys on each device in the wireless network must
be identical.
2 Click Apply.
Page 61

Wireless Settings 53
128-bit WEP
WEP is the basic mechanism to transmit your data securely over the
wireless network. Matching encryption keys must be set up on your
Router and wireless client devices to use WEP.
Figure 37 128-bit WEP Screen
To setup 128-bit WEP:
1 You can enter the 128-bit WEP key manually:
■ enter your WEP key as 13 pairs of hex digits (0-9, A-F).
Or you can generate the 128-bit WEP key automatically:
■ enter a memorable passphrase in the Passphrase field, and then
click Generate to generate the hex keys from the passphrase.
The WEP keys on each device on the wireless network must be identical.
In 128-bit WEP mode, only one WEP key can be specified.
2 Click Apply.
Page 62

54 CHAPTER 5: CONFIGURING THE ROUTER
WPA-PSK (no server)
WPA (Wi-Fi Protected Access) provides dynamic key changes and
constitutes the best security solution. If your network does not have a
RADIUS server. Select the no server option.
Figure 38 WPA-PSK (no server) Screen
1 Select WPA-PSK (no server) from the WPA drop-down menu.
2 Select WPA mode from the drop-down menu, three modes are
supported: WPA, WPA2, and Mixed mode.
3 Select Encryption technique from the drop-down menu, four options are
available: TKIP, AES, Auto for WPA AES for WPA2, and AES for both WPA
and WPA2.
4 Enter the pre-shared key in the Pre-shared Key (PSK) field. The pre-shared
key is a password, in the form of a word, phrase or series of letters and
numbers. The key must be between 8 and 63 characters long and can
include spaces and symbols. Each client that connects to the network
must use the same key.
5 If you want the key that you enter to be shown on the screen as a series
of asterisks (*), then check the Hide PSK checkbox.
6 Click Apply.
Page 63

Wireless Settings 55
WPA (with RADIUS Server)
WPA (Wi-Fi Protected Access) provides dynamic key changes and
constitutes the best security solution. This function requires that a
RADIUS server is running on the network.
Figure 39 WPA (with RADIUS Server) Screen
1 Select WPA with RADIUS server from the Security Mode drop-down
menu.
2 Select WPA mode from the drop-down menu, three modes are
supported: WPA, WPA2, and Mixed mode.
3 Select Encryption technique from the drop-down menu, four options are
available: TKIP, AES, Auto for WPA AES for WPA2, and AES for both WPA
and WPA2.
4 Enter the IP address of the RADIUS server on your network into the
RADIUS Server field.
5 Enter the port number that the RADIUS server is operating on in the
RADIUS Port field.
6 Enter the key for the RADIUS server in the RADIUS Key field.
7 By default, the WPA keys are changed every hour, but if you want to
change this setting, you can do so by specifying the required time in the
Re-key Interval field.
8 Click Apply.
Page 64

56 CHAPTER 5: CONFIGURING THE ROUTER
WPS Wireless Provisioning Services (WPS) is a standard for easy and secure
establishment of a wireless home network, created by the Wi-Fi Alliance.
3Com Wireless 11n Cable/DSL firewall Router supports the PIN method.
Check the Enable WPS Function box. The WPS-PIN field will appear.
Figure 40 WPS Screen
Enter the PIN code in the WPS-PIN field. And then click Apply.
Page 65

Wireless Settings 57
Connection Control This feature is used to filter the clients based on their MAC addresses.
Check the Enable MAC Address Filtering checkbox, the Connection
Control screen will appear.
Figure 41 Connection Control Screen
There are two options available in the Access rule for registered MAC
address field:
■ if you click Allow, this means only the MAC addresses registered here
in the list will be allowed to access the Router via wireless link.
■ if you click Deny, this means the registered MAC addresses will not be
able to access the Router via wireless link.
Use the MAC Address Filtering List to quickly copy the MAC addresses of
the current wireless clients into the list table. You can define up to 32
MAC addresses to the list.
You can click Clear to delete the current entry in the list.
Page 66

58 CHAPTER 5: CONFIGURING THE ROUTER
Client List You can view the list of all wireless clients that are connected to the
Router.
Figure 42 Client List Screen
Click Refresh to update the list.
Page 67

Wireless Settings 59
WMM Wireless Multimedia (WMM) mode, which supports devices that meet the
802.11E QBSS standard. WMM uses traffic priority based on the four
ACs; Voice, Video, Best Effort, and Background. The higher the AC
priority, the higher the probability that data is transmitted.
Check the Enable WMM Function box, the WMM parameters table will
appear.
Figure 43 WMM Screen
The following table explains the four access categories:
Access Category WMM
Designation
AC_BE (AC0) Best Effort Normal priority, medium
AC_BK (AC1) Background Lowest priority. Data with no
AC_VI (AC2) Video High priority, minimum
AC_VO (AC3) Voice Highest priority, minimum
Description
delay and throughput. Data
only affected by long delays.
Data from applications or
devices that lack QoS
capabilities.
delay or throughput
requirements, such as bulk
data transfers.
delay. Time-sensitive data
such as streaming video.
delay. Time-sensitive data
such as VoIP (Voice over IP)
calls.
802.1D
Tags
0, 3
2, 1
5, 4
7, 6
Page 68

60 CHAPTER 5: CONFIGURING THE ROUTER
WDS The Router supports WDS (Wireless Distribution System). WDS enables
one or more Access Points to rebroadcast received signals to extend
range and reach, though this can affect the overall throughput of data.
Figure 44 Wireless WDS Settings Screen
1 Check the Enable WDS Function checkbox.
2 To refresh the list of available access points, click Rescan Wireless
Networking.
3 Click Add to add the MAC address of the AP to the list, the add WDS
screen will appear (refer to Figure 45).
Figure 45 Add WDS screen
Enter the MAC address(es) of one or more access points in the AP MAC
Address table, and click Apply.
Page 69

Wireless Settings 61
Advanced The Advanced screen allows you to configure detailed settings for your
wireless connection.
Figure 46 Wireless Advanced Setting Screen
There are six parameters that you can configure:
■ Beacon Interval: this represents the amount of time between beacon
transmissions.
■ DTIM Interval: A DTIM (Delivery Traffic Indication Message) is a
countdown mechanism used to inform your wireless clients of the
next window for listening to broadcast and multicast messages.
■ Fragmentation Threshold: this is the maximum size for directed data
packets transmitted. The use of fragmentation can increase the
reliability of frame transmissions. Because of sending smaller frames,
collisions are much less likely to occur.
■ RTS Threshold: RTS stands for Request to Send, this parameter
controls what size data packet the low level RF protocol issues to an
RTS packet.
■ CTS Protection Mode: CTS stands for Clear to Send. CTS Protection
Mode boosts the Router’s ability to intercept 802.11b/ 802.11g
transmissions. Conversely, CTS Protection Mode decreases
performance. Leave this feature disabled unless you encounter severe
communication difficulties between the Router and your wireless
clients.
■ AP Isolation Mode: AP Isolation is a function to prevent wireless clients
connected with the device from communicating with one another.
Page 70

62 CHAPTER 5: CONFIGURING THE ROUTER
Internet Settings You can configure the settings for your WAN port connection.
WAN This feature is used to configure the parameters for your Internet
connection. The information necessary to complete these screens should
be obtained from your ISP. Check with your ISP first to find out what type
of connection you should choose.
Figure 47 WAN Screen
You should see the first entry already contains information that’s been
configured using the Wizard in the initial setup. If you want to change
that information or set up other connection, click Edit.
There are seven options available for the connection mode:
■ Disable — To disable the Internet connection function (see page 63)
■ Bridge Mode — RFC1483 Bridged Mode, (see page 63)
■ Dynamic IP — Using DHCP for WAN connection (see page 64)
■ Static IP — Using fixed IP for WAN connection (see page 65)
■ PPPoE — PPP over Ethernet, providing routing for multiple PCs (see
page 66)
■ PPTP — Point-to-Point Tunneling Protocol (see page 67)
■ L2TP — Layer 2 Tunneling Protocol (see page 68)
Page 71

Internet Settings 63
Disable
Selecting this option means that you do not want your Router to connect
to the Internet.
Figure 48 Disable Internet Connection Screen
Bridge Mode
If your ISP limits access to the Internet to specific computers, this means
that traffic to/from these computers only will be forwarded. In this case,
Bridge Mode is used to connect to the ISP. The ISP will generally give one
Internet account and limit only one computer to access the Internet.
Check with your ISP to determine if this mode is used for your Internet
connection.
Figure 49 Bridge Mode Screen
Enter the IP address and Subnet mask information.
Page 72

64 CHAPTER 5: CONFIGURING THE ROUTER
Dynamic IP
You can configure the Router to obtain an IP address automatically from a
DHCP server.
Figure 50 Dynamic IP Screen
1 Select Dynamic IP from the Internet sharing protocol drop-down menu.
2 If the ISP requires you to input a Host Name, type it in the Host Name
field.
3 Click Apply.
Page 73

Internet Settings 65
Static IP
If your Service Provider has assigned a fixed IP address, enter the assigned
IP address information on the screen.
Figure 51 Static IP Screen
1 Select Static IP from the Internet sharing protocol drop-down menu.
2 Enter your IP address in the IP address assigned by your service provider
field.
3 Enter the subnet mask in the Subnet Mask field.
4 Enter the default gateway IP address in the Service Provider Gateway
Address field.
5 Enter DNS IP address.
6 If there is a secondary DNS, enter the IP address.
7 Click Apply.
Page 74
66 CHAPTER 5: CONFIGURING THE ROUTER
PPPoE
PPP over Ethernet, provides routing for multiple PCs. To configure this
function correctly, you should obtain the information from your ISP.
Figure 52 PPPoE Settings Screen
1 Select PPPoE from the Internet sharing protocol drop-down menu.
2 Enter the user name assigned to you by your ISP in the Username field.
And enter the password assigned to you by your ISP in the Password field.
Re-enter your password in the Retype Password field.
3 The Service Name field is optional.
4 Enter the MTU value in the MTU field. Do not make changes to this
setting, unless your ISP specifically requires a different setting other than
1492.
5 If you want your Router to automatically disconnect from the Internet
after a period of inactivity, specify a time in the Idle Timeout field. (Enter a
value of 0 to disable this timeout). Check the Auto Reconnect After
Timeout box to automatically re-establish the connection as soon as you
attempt to access the Internet again.
6 Click Apply.
Page 75

Internet Settings 67
PPTP
If your ISP uses PPTP as the Internet connection protocol, setup the details
on this screen.
Figure 53 PPTP Screen
1 Select PPTP from the Internet sharing protocol drop-down menu.
2 Enter the PPTP Server information.
3 Enter the user ID in the User ID field. And enter the password assigned to
you by your ISP in the Password field. Re-enter your password in the
Retype Password field.
4 If you want your Router to automatically disconnect from the Internet
after a period of inactivity, specify a time in the Idle Timeout field. (Enter a
value of 0 to disable this timeout).
5 If you receive the IP address from your ISP via DHCP function, check the
Get IP By DHCP box.
6 If no DHCP function is used, then enter the IP Address, Subnet Mask, and
Default Gateway information.
7 Click Apply.
Page 76

68 CHAPTER 5: CONFIGURING THE ROUTER
L2TP
If your ISP uses L2TP as the Internet connection protocol, setup the details
on this screen.
Figure 54 L2TP Connection Screen
1 Select L2TP from the Internet sharing protocol drop-down menu.
2 Enter the L2TP Server information.
3 Enter the User ID and Password required by your ISP.
4 Retype the password.
5 Enter the maximum Idle Timeout for the Internet connection. After this
time has been exceeded the connection will be terminated.
6 Check the Get IP By DHCP box to receive IP address from your ISP’s DHCP
function. If this box is not checked, enter the IP address, Subnet mask,
and Default Gateway information.
7 Click Apply.
Page 77

Internet Settings 69
DNS Domain Name Service (or Server) is an Internet service that translates
domain names into IP addresses. Because domain names are alphabetic,
they're easier to remember. The Internet however, is really based on IP
addresses. Every time you use a domain name, a DNS service must
translate the name into the corresponding IP address. For example, the
domain name www.example.com might translate to 198.105.232.4.
Check with your ISP for information on this screen.
Figure 55 DNS Screen
If the DNS information is automatically provided by your ISP every time
you connect to it, check the Automatic from ISP checkbox.
If your ISP provided you with specific DNS addresses to use, enter them
into the appropriate fields on this screen and click Apply.
Many ISPs do not require you to enter this information into the Router. If
you are using a Static IP connection type, you may need to enter a
specific DNS address and secondary DNS address for your connection to
work properly. If your connection type is Dynamic or PPPoE, it is likely that
you do not have to enter a DNS address.
Page 78

70 CHAPTER 5: CONFIGURING THE ROUTER
Clone MAC address To configure the Hostname and Clone MAC Address information for your
Router, select Internet Settings, then go to the Clone MAC address tab.
The Hostname and MAC Address screen displays.
Figure 56 Hostname and Clone MAC Address Screen
1 Some ISPs require a host name. If your ISP has this requirement, enter the
host name in the Host Name field.
2 Three different ways to configure the WAN MAC Address:
■ If your ISP requires an assigned MAC address, enter the values in the
WAN MAC address field.
or
■ If the computer that you are using is the one that was previously
connected directly to the cable modem, click Clone.
or
■ To reset the MAC Address to the default, click Reset MAC.
3 Click Apply to save the settings.
Page 79

Firewall 71
Firewall This section is for configuration settings of the Router’s firewall function.
Your Router is equipped with a firewall that will protect your network
from a wide array of common hacker attacks including Ping of Death
(PoD) and Denial of Service (DoS) attacks. You can turn the firewall
function off if needed. Turning off the firewall protection will not leave
your network completely vulnerable to hacker attacks, but 3Com
recommends that you leave the firewall enabled whenever possible.
SPI Stateful Packet Inspection (SPI) - The Intrusion Detection Feature of the
Router limits access for incoming traffic at the WAN port.
This feature is called a "stateful" packet inspection, because it examines
the contents of the packet to determine the state of the communications;
i.e., it ensures that the stated destination computer has previously
requested the current communication. This is a way of ensuring that all
communications are initiated by the recipient computer and are taking
place only with sources that are known and trusted from previous
interactions. In addition to being more rigorous in their inspection of
packets, stateful inspection firewalls also close off ports until connection
to the specific port is requested.
Figure 57 Firewall Screen
Page 80

72 CHAPTER 5: CONFIGURING THE ROUTER
To enable the firewall function:
1 Select the level of protection (High, Medium, or Low) that you desire from
the Firewall level drop-down menu.
2 Click Apply.
■ For low and medium levels of firewall protection, refer to Figure 58.
■ For high level of firewall protection, refer to Figure 59.
Figure 58 Low and Medium Level Firewall Protection Screen
When abnormal network activity occurs, an alerting email will be sent out
to you. Enter the following information to receive the email:
■ Your E-mail Address
■ SMTP Server Address
■ User name
■ Password
Page 81

Firewall 73
Figure 59 High Level Firewall Protection Screen
If you select high level of protection, you will need to configure additional
parameters for the firewall.
■ Fragmentation half-open wait - Configures the number of seconds
that a packet state structure remains active. When the timeout value
expires, the Router drops the un-assembled packet, freeing that
structure for use by another packet.
■ TCP SYN wait - Defines how long the software will wait for a TCP
session to synchronize before dropping the session.
■ TCP FIN wait - Specifies how long a TCP session will be maintained
after the firewall detects a FIN packet.
■ TCP connection idle timeout - The length of time for which a TCP
session will be managed if there is no activity.
■ UDP session idle timeout - The length of time for which a UDP session
will be managed if there is no activity.
■ H.323 data channel idle timeout - The length of time for which an
H.323 session will be managed if there is no activity.
Page 82

74 CHAPTER 5: CONFIGURING THE ROUTER
■ Total incomplete TCP/UDP sessions HIGH - Defines the rate of new
unestablished sessions that will cause the software to start deleting
half-open sessions.
■ Total incomplete TCP/UDP sessions LOW - Defines the rate of new
unestablished sessions that will cause the software to stop deleting
half-open sessions.
■ Incomplete TCP/UDP sessions (per min) HIGH - Maximum number of
allowed incomplete TCP/UDP sessions per minute.
■ Incomplete TCP/UDP sessions (per min) LOW - Minimum number of
allowed incomplete TCP/UDP sessions per minute.
■ Maximum incomplete TCP/UDP sessions number from same host -
Maximum number of incomplete TCP/UDP sessions from the same
host.
■ Incomplete TCP/UDP sessions detect sensitive time period - Length of
time before an incomplete TCP/UDP session is detected as incomplete.
■ Maximum half-open fragmentation packet number from same host -
Maximum number of half-open fragmentation packets from the same
host.
■ Half-open fragmentation detect sensitive time period - Length of time
before a half-open fragmentation session is detected as half-open.
■ Flooding cracker block time - Length of time from detecting a flood
attack to blocking the attack.
Page 83

Firewall 75
Special Applications Special Applications let you choose specific ports to be open for specific
applications to work properly with the Network Address Translation (NAT)
feature of the Router.
Figure 60 Special Applications Screen
A list of popular applications has been included to choose from. Select
the application from the Popular Applications drop-down menu. Then
select the row that you want to copy the settings to from the Copy To
drop-down menu, and click Copy To. The settings will be transferred to
the row that you specified. Click Apply to save the setting for that
application.
If your application is not listed, you will need to check with the
application vendor to determine which ports need to be configured. You
can manually enter the port information into the Router. To manually
enter the port information:
1 Specify the trigger port (the one used by the application when it is
initialized) in the Trigger Port column, and specify whether the trigger is
TCP or UDP.
2 Specify the Public Ports used by the application, that will need to be
opened up in the firewall for the application to work properly. Also
specify whether these ports are TCP or UDP.
3 Check the Enabled checkbox, then click Apply.
Page 84

76 CHAPTER 5: CONFIGURING THE ROUTER
Virtual Servers The Virtual servers feature allows you to route external (Internet) calls for
services such as a web server (port 80), FTP server (Port 21), or other
applications through your Router to your internal network. Since your
internal computers are protected by a firewall, machines from the
Internet cannot get to them because they cannot be 'seen'.
If you need to configure the Virtual Server function for a specific
application, you will need to contact the application vendor to find out
which port settings you need.
The maximum number of virtual servers that can be configured is 20.
Figure 61 Virtual Servers Screen
A list of popular servers has been included to choose from. Select the
server from the Popular servers drop-down menu. Then click Add, your
selection will be added to the table.
If the server that you want to use is not listed in the drop-down menu,
you can manually add the virtual server to the table. To manually
configure your virtual servers:
1 Enter the IP address, and the description in the spaces provided for the
internal machine.
2 Select the protocol type (TCP, UDP, or both TCP and UDP) from the
drop-down menu.
Page 85

Firewall 77
3 Specify the public port that will be seen by clients on the Internet, and the
LAN port which the traffic will be routed to.
4 You can enable or disable each Virtual Server entry by checking or
unchecking the appropriate Enabled checkbox.
5 Click Apply to save the changes for each Virtual Server entry.
DMZ If you have a client PC that cannot run an Internet application properly
from behind the firewall, you can open the client up to unrestricted
two-way Internet access. This may be necessary if the NAT feature is
causing problems with an application such as a game or video
conferencing application.
Figure 62 DMZ Screen
Use this feature on a temporary basis. The computer in the DMZ is not
protected from hacker attacks.
Check the Enable DMZ box, the IP Address of Virtual DMZ Host will
appear.
1 Enter the last digits of the LAN IP address in the Client PC IP Address field.
Enter the IP address (if known) that will be accessing the DMZ PC into the
Public IP Address field, so that only the computer on the Internet at this
address can access the DMZ PC without firewall protection. If the IP
address is not known, or if more than one PC on the Internet will need to
access the DMZ PC, then set the Public IP Address to 0.0.0.0.
2 Click Apply.
Page 86

78 CHAPTER 5: CONFIGURING THE ROUTER
PC Privileges The Router can be configured to restrict access to the Internet, email or
other network services at specific days and times. Restriction can be set
for a single computer, a range of computers, or multiple computers.
You can define the traffic type permitted or not-permitted to the Internet.
Figure 63 PC Privileges Screen
1 Select one option from filtering function:
■ All PCs have access to the Internet: selecting this mode means that all
clients have full access to Internet.
■ PCs access authorised services only:
2 Click Add PC (refer to Figure 64).
To edit or delete specific existing filtering rules, click on Edit or Delete for
the appropriate filtering rule.
Page 87

Firewall 79
Figure 64 PC Privileges Add PC Screen
1 Enter a description in the Client PC Description field, and the IP address or
IP address range into the Client PC IP Address fields.
2 To bypass the URL Filter and Content Filter, check the corresponding
Bypass checkbox.
If you check the two options: Bypass URL Filter, and Bypass Content Filter,
then the Web sites and keywords defined in this screen will not be filtered
out.
3 Select the services to be blocked. A list of popular services is listed on this
screen, to block a particular service, check the appropriate Blocking
checkbox.
If the service to be restricted is not listed here, you can enter a custom
range of ports at the bottom of the screen, under User Defined Blocked
Ports.
4 If you want the restriction to apply only at certain times, select the
schedule rule to apply from the Schedule Rule drop-down menu.
Note that schedule rules are defined on the Schedule Rules screen
(see page 80).
5 Click Apply to add the settings.
Page 88

80 CHAPTER 5: CONFIGURING THE ROUTER
Schedule Rule The Router can be configured to restrict access to the Internet, email or
other network services at specific days and times. Define the time in this
screen, and define the rules in the PC Privileges screen (see page 78).
Figure 65 Schedule Rule Screen
1 Click Add Rule to add a schedule rule (refer to Figure 66).
Figure 66 Add Schedule Rule Screen
2 Enter a name and comment for the schedule rule in the Name and
Comment fields.
3 Specify the schedule rules for the required days and times - note that all
times should be in 24 hour format.
4 Click Apply.
Page 89

Firewall 81
URL Filter To configure the URL filter feature, use the table on the URL Filter screen
to specify the Web sites (www.somesite.com) and/or keywords you want
to filter on your network.
For example, entering a keyword of xxx would block access to any URL
that contains the string xxx.
Figure 67 URL Filter Screen
1 Check the Enable URL Filtering Function checkbox. The rule table will
appear.
2 Enter the URL address or keywords in the URL/Keyword field.
3 Select Denied or Allowed from the Mode drop-down menu.
To complete this configuration, you will need to create or modify the
filtering rule in the PC Privileges screen (see page 78).
From the PC Privileges Add PC screen (Figure 64), if you check the two
options: Bypass URL Filter, and Bypass Content Filter, then the Web sites
and keywords defined in this screen will not be filtered out.
Page 90

82 CHAPTER 5: CONFIGURING THE ROUTER
Advanced The Advanced section allows you to set additional parameter details for
the Router. You can configure:
■ Security
■ VLAN
■ Static Routes
■ RIP
■ DDNS
■ SNMP
■ Syslog
■ Proxy Arp
■ QoS Settings
Security Use the Security screen to set the advanced security settings for the
Router.
Figure 68 Security Screen
Page 91

Advanced 83
■ NAT — Before you enable NAT (Network Address Translation), make
sure you have changed the administrator password. NAT is the
method by which the Router shares the single IP address assigned by
your ISP with the computers on your network.
This function should only be disabled by advanced users, and if your
ISP assigns you multiple IP addresses or you need NAT disabled for an
advanced system configuration. If you have a single IP address and
you turn NAT off, the computers on your network will not be able to
access the Internet. Other problems may also occur.
■ IPSEC NAT-T Pass-through — NAT-T (NAT Traversal) is an Internet
Draft proposed to IETF in order to help the problems associated
with passing IPsec traffic through NAT Routers. For NAT-T to work,
both ends of the connection need to support this function. Ensure
that you select NAT-T only if it is needed as it will reduce LAN-WAN
throughput. This Router supports NAT-T draft 2 implementation.
■ Universal Plug and Play — This is a technology that offers seamless
operation of voice messaging, video messaging, games, and other
applications that are Universal Plug and Play compliant. Some
applications require the Router's firewall to be configured in a specific
way to operate properly. This usually requires opening TCP and UDP
ports and in some instances setting trigger ports. An application that
is Universal Plug and Play compliant has the ability to communicate
with the Router, basically "telling" the Router which way it needs the
firewall configured. The Router ships with the Universal Plug and Play
feature disabled. If you are using any applications that are Universal
Plug and Play compliant, and want to take advantage of the Universal
Plug and Play features, you can enable this feature. Simply check the
Enable Universal Plug and Play checkbox. Click Apply to save the
change.
■ WAN Ping Blocking — Computer hackers use what is known as
"Pinging" to find potential victims on the Internet. By pinging a
specific IP address and receiving a response from the IP address, a
hacker can determine that something of interest might be there.
The Router can be set up so it will not respond to an Internet Control
Message Protocol (ICMP) Ping from the outside. This heightens the
level of security of your Router. To turn off the ping response, check
Block ICMP Ping and click Apply; the Router will not respond to an
ICMP ping from the Internet.
Page 92

84 CHAPTER 5: CONFIGURING THE ROUTER
■ MSS Clamping — You might not be able to browse some Web sites or
to send email messages that contain attachments from an Internet
Connection Sharing client computer if your outbound connection is
through a Windows XP-based Internet Connection Sharing host
computer that uses Point-to-Point Protocol over Ethernet (PPPoE).
This issue may occur if the Windows XP-based Internet Connection
Sharing host computer uses a smaller Maximum Transmission Unit
(MTU) size on the WAN interface (the PPPoE connection to the
Internet) than it uses on the private interface (the Ethernet connection
to the Internet Connection Sharing client). If a packet is larger than
the MTU size on the WAN interface, the client sends an Internet
Control Message Protocol (ICMP) error to the external server to
request that the server negotiate the TCP Maximum Segment Size
(MSS). However, this message may be blocked by some firewalls.
When this occurs, the packet is dropped. To allow the message to go
through the firewall, enable MSS Clamping. MSS clamping will make
Internet Connection Sharing set the MSS value low enough to match
the external interface.
■ Remote Administration — This feature allows you to make changes to
your Router’s settings from anywhere on the Internet. Four options are
available:
■ If you do not want to use this feature, select Disable Remote
Administration.
■ Select Enable administration from a single Internet Host, and enter
the IP address, to allow only one computer to use the remote
administration. This is more secure, as only the specified IP address
will be able to manage the Router.
■ Select Enable administration from a whole Subnet Internet Host,
and enter the IP address and subnet mask, to allow PCs from that
specific subnet group to use the remote administration.
■ Select Enable administration from any Internet Host, this allows
any computer to access the Router remotely.
Before you enable this function, ensure that you have set the
Administration Password.
Page 93

VLAN The VLAN screen allows you to setup VLAN groups.
Figure 69 VLAN Screen
Static Routes You can configure static routes in this screen.
Advanced 85
Figure 70 Static Routes Screen
To add a static route entry to the table, click Add (see Figure 71).
To change an existing entry, click Edit. To delete an entry, click Delete.
Page 94
86 CHAPTER 5: CONFIGURING THE ROUTER
Figure 71 Add Static Route Screen
Enter the following information:
■ Index — the index of the entry.
■ Network Address — the network address of the static route.
■ Subnet Mask — the subnet mask of the route.
A network address of 0.0.0.0 and a subnet mask of 0.0.0.0 indicates the
default route.
■ Gateway — the router used to route data to the network specified by
the network address.
■ Interface — select the interface.
After you have finished making changes to the table, click Apply.
Page 95

Advanced 87
RIP RIP (Routing Information Protocol) - RIP allows the network administrator
to set up routing information on one RIP-enabled device and send that
information to all RIP-enabled devices on the network.
Figure 72 RIP Parameter Screen
You can set up RIP independently on both LAN and WAN interfaces.
1 Check the Enable RIP checkbox.
2 Check the Enable Auto summary checkbox. Auto summarization sends
simplified routing data to other RIP-enabled devices rather than full
routing data.
3 Select the Operation Mode:
■ Disable — RIP is not enabled for the WAN or LAN interface.
■ Enable — RIP is enabled for the WAN or LAN interface. The router will
transmit RIP update information to other RIP-enabled devices.
■ Silent — RIP is enabled, however the Router only receives RIP update
messages, it will not transmit any messages itself.
4 In the Version field, select 1 or 2.
3Com recommends that you only use RIPv1 if there is an existing
RIP-enabled device on your network that does not support RIPv2. In all
other cases, you should use RIPv2.
Page 96

88 CHAPTER 5: CONFIGURING THE ROUTER
5 Use the Poison Reverse drop-down menu to enable or disable Poison
Reverse on the Router. Enabling Poison Reverse on your Router allows it
to indicate to other RIP-enabled devices that they have both routes that
point to each other, preventing data loops.
6 Use the Authentication Required field to choose the mode of
authentication:
■ None — Switches off authentication on the specified interface.
■ Password — An unencrypted text password that needs to be set on all
RIP-enabled devices connected to this Router. RIP information is not
shared between devices whose passwords do not match.
7 In the Password field, enter the required password.
8 Click Apply.
Page 97

Advanced 89
DDNS The Router provides a list of dynamic DNS providers for you to choose
from. Dynamic Domain Name Server (DDNS) enables you to map a static
domain name to a dynamic IP address.
Before you set up DDNS, you must obtain an account, password or key
and static domain name from your DDNS provider.
The Router supports five DDNS providers:
■ DynDNS.org
■ TZO.com
■ Dt DNS.com
■ No-IP.com
■ Zoneedit.com
Figure 73 Dynamic Domain Name Server (DDNS) Screen
1 Check Enable DDNS.
2 Select the provider, and then enter the necessary information provided by
your DDNS provider.
3 Click Apply.
Page 98

90 CHAPTER 5: CONFIGURING THE ROUTER
SNMP SNMP (Simple Network Management Protocol) allows remote
management of your Router by a PC that has an SNMP management
agent installed.
Check the Enable SNMP box, the table will appear.
Figure 74 SNMP Screen
To Configure SNMP Community:
1 In the Community column, enter the name of the SNMP communication
channel. Your SNMP management agent needs to be configured with this
name so that it can communicate with your Router.
2 In the Access column, select Read to allow the management agent to
collect data (for example, bandwidth usage) from your Router. Select
Write to allow the management agent to change the configuration of
your Router.
3 Check the appropriate Valid checkbox to enable the communication
channel.
Page 99

Advanced 91
You can configure your Router to send status messages to the SNMP
management agent if a problem occurs on the network. To configure
SNMP traps:
1 In the IP Address field, enter the IP address of the PC to which you want
your Router to send status messages.
2 In the Community field, enter the name of the SNMP communication
channel to which you want your Router to send status messages.
3 Set the Version field to match the version of trap messaging that your
SNMP management agent supports. The Router supports V1 and V2c
trap messaging.
Syslog Using third party syslog software, this Syslog Server tool will automatically
download the Router log to the specified server IP address.
Figure 75 Syslog Server Screen
1 Check the Enable Syslog Server checkbox.
2 Enter the Server LAN IP Address in the space provided.
3 Click Apply.
Page 100

92 CHAPTER 5: CONFIGURING THE ROUTER
Proxy ARP Proxy ARP is the technique in which one host, usually a Router, answers
ARP requests intended for another machine. By “faking” its identity, the
Router accepts responsibility for routing packets to the “real” or intended
destination. This heightens the security for your network.
Figure 76 Proxy ARP Screen
1 Check the Enable ProxyARP box.
2 Enter the corresponding IP address in the IP Address From and IP Address
To fields.
3 Click Apply.
 Loading...
Loading...