
CAMÉRA RÉSEAU
Manuel d’utilisation
QND-8011
QND-8021

Caméra Réseau
Manuel d'utilisation
Droits d’auteur
Hanwha Techwin
©2019
Marque commerciale
Chaque marque déposée ci-dessus est enregistrée. Les noms de ce produit et d’autres marques de commerce mentionnées dans ce manuel sont les
marques déposées de leurs sociétés respectives.
Restriction
Le droit d’auteur de ce document est réservé. En aucun cas ce document ne doit être reproduit, distribué ou modifié, partiellement ou entièrement, sans
l’autorisation formelle.
Clause de non responsabilité
Hanwha Techwin
sera fournie à cet effet. L’utilisation de ce document et les résultats subséquents seront entièrement de la responsabilité de l’utilisateur.
Hanwha Techwin
La conception et les caractéristiques techniques sont susceptibles d’être modiées sans préavis.
L’ID initial de l’administrateur initi est “admin” et le mot de passe doit être déni lors de la première connexion.
Veuillez changer votre mot de passe tous les trois mois an de protéger les renseignements personnels sans risque et an de prévenir les
dommages du vol d’informations.
Veuillez prendre note que l’utilisateur est respondable de la sécurité et des autres problèmes causés par une mauvaise gestion du mot de passe.
fait de son mieux pour vérifi er l’intégrité et l’exactitude des contenus de ce document, mais aucune garantie formelle ne
se réserve le droit de modifi er les contenus de ce document sans avis préalable.
Co., Ltd. Tous droi ts réservés .

présentation
INSTRUCTIONS IMPORTANTES RELATIVES À LA SÉCURITÉ
1. Veuillez lire ces instructions.
2. Conservez ces instructions.
3. Prêtez attention à tous les avertissements.
4. Veuillez suivre toutes les instructions.
5. N’utilisez pas cet appareil à proximité de l’eau.
6. Nettoyez la zone contaminée sur la surface du produit avec un chiffon doux et sec ou un chiffon humide.
(Ne pas utiliser un détergent ou des produits cosmétiques contenant de l’alcool, des solvants et des
tensioactifs ou des produits contenant du pétrole, car ils peuvent déformer ou endommager le produit.)
7. N’obstruez pas les ouvertures de ventilation. Procédez à l’installation conformément aux instructions du
fabricant.
8. Ne pas installer l’appareil à proximité de sources de chaleur comme les radiateurs, les registres de chaleur et
les autres appareils (incluant les amplificateurs) produisant de la chaleur.
9. Veillez à vous conformer aux sécurités des prises de terre et polarisées. Une prise dite polarisée est composée
de deux fiches, une plus large que l’autre. Une prise de terre est composée de deux fiches et d’une troisième
fiche pour la terre. La troisième fiche, plus large que les deux autres, est fournie pour votre sécurité. Si la prise
qui vous est fournie ne correspond pas à votre prise murale, demandez à un électricien de remplacer la prise
obsolète.
10. Veillez à ce que personne ne marche ou se prenne les pieds dans le cordon d’alimentation et particulièrement
au niveau des fiches et des prises de courant et au niveau où ils se situent.
11. N’utilisez que des accessoires ou des produits additionnels spécifiés par le fabricant.
12. Utilisez uniquement un chariot, un socle, un trépied, un support ou une table
recommandés par le fabricant ou vendus avec l’appareil. Si vous utilisez un chariot,
déplacez le chariot transportant l’appareil avec précaution afin d’éviter les blessures que
pourrait entraîner un basculement accidentel.
13. Débranchez cet appareil en cas d'orage ou de non-utilisation prolongée.
14. Veuillez faire appel au personnel qualifié pour tous travaux de maintenance. Les travaux
de maintenance sont nécessaires si l’appareil a été endommagé de quelque manière que ce soit, comme
cordon d’alimentation endommagé, liquide répandu, objets tombés sur l’appareil, appareil exposé à la pluie et
à l’humidité, il ne fonctionne pas normalement ou est tombé par terre.
15. Ce produit est destiné à être alimenté par une unité d’alimentation répertoriée de « classe 2 » ou « LPS » et un
courant nominal de PoE (48 V), 0,11 A.
16. Ce produit est destiné à être alimenté par un courant isolé.
17. Si vous utilisez une force excessive lors de l’installation du produit, la caméra risque d’être endommagée et de
ne pas fonctionner correctement. Si vous installez le produit à l’aide d’outils non conformes, le produit risque
d’être endommagé.
18. Ne pas installer le produit dans un endroit où des substances chimiques ou des nuages d’huile existent ou
peuvent être générés. Comme les huiles comestibles telles que l’huile de soja peuvent endommager ou
déformer le produit, n’installez pas le produit dans la cuisine ou près de la table de cuisine.
Cela peut endommager le produit.
19. Lors de l’installation du produit, veillez à ne pas laisser la surface du produit se colorer avec une substance
chimique. Certains solvants chimiques tels que des produits de nettoyage ou des adhésifs peuvent causer de
graves dommages à la surface du produit.
20. Si vous installez / désassemblez le produit d’une manière qui n’a pas été recommandée, les fonctions /
performances de production peuvent ne pas être garanties.
Installez le produit en vous référant à “Installation et connexion” dans le manuel d’utilisation.
21. L’installation ou l’utilisation du produit dans l’eau peut causer des dommages importants au produit.
22. Bien qu’un changement rapide de température puisse entraîner la formation de givre à l’intérieur du dôme, la
vidéo ne posera aucun problème.
AVERTISSEMENT
AFIN DE RÉDUIRE LE RISQUE D’INCENDIE OU DE DÉCHARGE ÉLECTRIQUE, N’EXPOSEZ PAS
CET APPAREIL À LA PLUIE NI À L’HUMIDITÉ. NE PAS INSÉRER D’OBJET MÉTALLIQUE PAR
LES FENTES DE VENTILATION OU TOUTE AUTRE OUVERTURE SITUÉE SUR L’ÉQUIPEMENT.
Veillez à éviter toute projection de liquide sur l’appareil et ne placez jamais sur celui-ci des
●● PRÉSENTATION
récipients contenant des liquides, tels que des vases.
Pour éviter les blessures, cet appareil doit être fermement fixé au mur/plafond conformément aux
consignes d’installation.
ATTENTION
ATTENTION
RISQUE DE ECHOC ELECTRIQUE
NE PAS OUVRIR
ATTENTION
: POUR REDUIRE LES RISQUES DE CHOCS ELECTRIQUES,
NE RETIREZ PAS LE COUVERCLE (OU LA PARTIE ARRIERE) LES PIECES
INTERIEURES NE SONT PAS ACCESSIBLES A L’UTILISATEUR.
FAITES APPEL AU PERSONNEL DE MAINTENANCE QUALIFIE.
EXPLICATION DES SYMBOLES GRAPHIQUES
Le symbole de l’éclair se terminant par une flèche inscrit dans un triangle
équilatéral sensibilise l'utilisateur à la présence d’une « tension élevée » au sein
de l’unité, susceptible d’être suffisamment puissante pour présenter un risque de
décharge électrique.
Le symbole de point d'exclamation inscrit dans un triangle équilatéral sensibilise
l'utilisateur à la présence d'importantes instructions de fonctionnement et de
maintenance (entretien et réparation) dans la documentation accompagnant
l'appareil.
Français _3

présentation
Catégorie de classe
Un appareil appartenant à une catégorie de type CLASSE doit être connecté à la prise murale
secteur dotée d’une connexion de mise à la terre de protection.
Batterie
Les batteries (module batterie ou piles installées) ne doivent pas être exposées à des températures
excessives, telles que la chaleur du soleil, le feu ou toute autre source de même type.
La batterie ne peut pas être remplacée.
Appareil déconnecté
Débranchez la prise principale de l'appareil si celui-ci est défectueux. Contactez un réparateur
situé dans votre région.
Lorsque l'appareil est exploité hors des États-Unis, il est possible d'utiliser le code HAR
pour recourir aux services d'une agence agréée.
ATTENTION
Il existe un risque d’explosion si la batterie est remplacée par une autre de modèle incorrect.
Éliminez les batteries usagées conformément aux instructions.
Les instructions d'entretien sont fournies à l'intention d'un personnel qualifié exclusivement.
Pour réduire les risques de chocs électriques, ne procédez pas à des réparations autres que
celles qui sont indiquées dans les instructions de fonctionnement, à moins que vous ne soyez
qualifié pour ce faire.
Veuillez utiliser l’alimentation en entrée sur une seule caméra, les autres périphériques ne
doivent pas être connectés.
L’ITE ne doit être connecté que sur un réseau PoE sans routage vers l’alimentation
extérieure.
Veuillez lire attentivement les consignes de sécurité recommandées ci-après.
yNe placez pas cet appareil sur une surface inégale.
yN'installez pas l'appareil sur une surface où il pourrait être exposé à la lumière directe du
soleil ou situé à proximité d'un équipement de chauffage ou d'une zone exposée à un froid
extrême.
yNe placez pas cet appareil à proximité de matériaux conducteurs.
yN'essayez de réparer cet appareil vous-même.
yÉvitez de placer un verre d'eau sur ce produit.
yN'installez pas le produit à proximité de sources magnétiques.
yNe bloquez pas les ouvertures de ventilation.
yNe placez pas d'éléments lourds sur le produit.
yVeuillez porter des gants de protection lors de l’installation / retrait de la caméra.
La température élevée de la surface du produit peut causer une brûlure.
Le guide de l'utilisateur est un manuel d'instructions portant sur l'utilisation du produit.
La signification des indications fournies dans le manuel est comme suit.
yRéférence : Dans le cas de la fourniture d'informations pour aider à l'utilisation du produit.
yNotification : En cas de risques d'endommagement du produit et de blessures à l'utilisateur
provoqués par le non respect des instructions fournies.
Veuillez lire ce manuel et notamment les passages liés à la sécurité du produit, et gardez-le
en lieu sûr.
Dans certains environnements d’installation, les communications radio peuvent subir des
interférences.
Lorsque des interférences d’ondes électromagnétiques se produisent entre le produit et
l’appareil de communication radio, il est recommandé de garder une certaine distance entre les
deux ou de changer la direction de l’antenne de réception.
4_ présentation

SOMMAIRE
PRÉSENTATION
3
INSTALLATION ET CONNEXION
9
CONNEXION ET CONFIGURATION
RÉSEAU
12
3 Instructions Importantes Relatives à la
Sécurité
6 Caractéristiques du Produit
6 Spécifications PC Recommandées
6 Caractéristiques Recommandées Pour La
Carte Mémoire Micro SD/SDHC/SDXC
6 NAS — Indications du fabricant
7 Contenu
8 D’un Coup d’œil
9 Installation
10 Insertion/retrait d’une Carte Mémoire Micro
SD
11 Mise sous tension et mise en réseau
12 Connecter la Caméra Directement au
Réseau de Zone Locale
12 Connexion de la Caméra Directement à un
Modem DSL/Câble Basé Sur le Protocole
DHCP
13 Boutons Utilisés Sous IP Installer
13 Configuration de l’adresse IP Fixe
15 Configuration de l’adresse IP Dynamique
15 Configuration de la Redirection de la Plage
de Ports (Mappage de Ports)
16 Connexion à la Caméra Depuis Un
Ordinateur Local Partagé
16 Connexion à la Caméra Depuis Un
Ordinateur Distant Via Internet
VISIONNEUR WEB
17
ANNEXES
19
17 Connexion à la Caméra
18 Réglage du mot de passe
18 Login
18 Installation de la visionneuse Web de la
caméra
19 Spécifications
20 Vue du Produit
21 Résolution de Problèmes
22 Open Source Announcement
●● PRÉSENTATION
Français _5

présentation
CARACTÉRISTIQUES DU PRODUIT
• Indice d’étanchéité à la poussière et aux intempéries (IP42)
Protection contre les gouttes de liquide ménager et la poussière en cas d’utilisation domestique.
• Prend en charge des vidéos de 5 mégapixels de résolution
• Lecture en transit multiple
Cette caméra réseau peut afficher des vidéos en différentes qualités et résolutions simultanément, en utilisant
plusieurs CODEC.
• Compatible micro HDMI
• Surveillance basée sur navigateur Web
Utilisation du navigateur Web pour afficher l’image dans un environnement réseau local.
• Alarme
Lorsqu’un événement se produit, l’image correspondante est envoyée à l’adresse électronique enregistrée par un
utilisateur sur le serveur FTP ou enregistrée dans une carte micro SD ou NAS.
• Détection de sabotage
Détecte les tentatives de sabotage sur la surveillance vidéo.
• Fonction de détection des effets de flou
Détecte le phénomène de flou de la lentille de la caméra.
• Détection de mouvement
Détecte les mouvements depuis l’entrée vidéo de la caméra.
• Détection auto du réseau déconnecté
Détecte la déconnexion réseau avant le déclenchement de l’événement.
• Statistiques de comptage de personnes
Vous pouvez vérifier le nombre de personnes entrant dans la zone spécifiée grâce à l’analyse vidéo.
• Conformité ONVIF
Ce produit supporte l’ONVIF Profile S&G.
Pour obtenir de plus amples informations, consultez le site Web www.
onvif.org.
SPÉCIFICATIONS PC RECOMMANDÉES
• CPU : Intel(R) Core(TM) i7 3.4 GHz ou supérieur
• RAM : 8G ou supérieur
• Système d’exploitation pris en charge : Windows 7, 8.1, 10, Mac OS X 10.12, 10.13, 10.14
• Navigateur recommandé : Google Chrome
• Navigateurs pris en charge : MS Explorer11, MS Edge, Mozilla Firefox (Windows 64 bits uniquement), Apple
Safari (Mac OSX uniquement)
• VG
A : Carte graphique PCIe 256MB GDDR3 ou supérieure
Veuillez consulter l’annexe pour obtenir des informations détaillées sur le système d’exploitation et les navigateurs
vérifiés.
CARACTÉRISTIQUES RECOMMANDÉES POUR LA CARTE MÉMOIRE MICRO SD/SDHC/SDXC
• Capacité recommandée : 16 Go à 128 Go (type MLC)
• Fabricants recommandés : SanDisk, Transcend
• Type de produit : Haute endurance
• La compatibilité varie en fonction des fabricants et des types de cartes.
NAS — INDICATIONS DU FABRICANT
• Capacité recommandée : On recommande 200GO ou plus.
• Accès simultané : Un appareil NAS peut accepter un maximum de seize accès de caméra.
• Pour cette caméra-ci, il est recommandé d’utiliser un NAS respectant les indications suivantes.
Produits recommandés Grandeurs disponibles
QNAP NAS Le nombre maximum de caméras pouvant avoir accès simultanément est de 16.
NAS Synology Le nombre maximum de caméras pouvant avoir accès simultanément est de 16.
6_ présentation
Si vous utilisez de l’équipement NAS à des fins autres que de la sauvegarde vidéo, le nombre de caméras accessibles peut
`
J
diminuer.

CONTENU
Veuillez vérifier si votre caméra et l’ensemble de ses accessoires sont contenus dans l’emballage du produit.
(l’accessoire varie selon le pays de vente.)
Apparence Nom de l’élément Quantité Description
Accessoires en option pour l’installation
Pour faciliter l’installation, vous pouvez acheter les accessoires appropriés disponibles en option.
●● PRÉSENTATION
Caméra
Guide de prise en main rapide
(En option)
Carte de garantie
(En option)
Gabarit
Clé à ouverture fixe
(en forme de L)
1
1
1
1
1 Utilisé pour retirer et remplacer le couvercle du dôme
Guide d’installation du produit
Nom du modèle Montage mural
QND-8011/8021 SBP-120WMW
Français _7

présentation
D’UN COUP D’ŒIL
Apparence
Élément Description
Couvercle dôme
a
a
Couvercle du boîtier utilisé pour protéger l’objectif et l’unité principale.
Composants
a
RESET
b
Élément
Objectif Objectif de la caméra.
a
Compartiment de la carte
b
mémoire Micro SD
PoE Connector Relie le réseau et fournit l’alimentation à travers un câble Ethernet.
c
Bouton de réinitialisation
d
Port micro HDMI Raccordez à un moniteur avec un câble HDMI pour visionner ce que filme la caméra.
e
Compartiment de la carte mémoire Micro SD.
Le bouton permet de restaurer tous les réglages de la caméra sur leur valeur par défaut.
Appuyez dessus pendant 5 secondes pour relancer le système.
Si vous réinitialisez la caméra, les réglages réseau seront ajustés de sorte que le serveur
J
DHCP puisse être activé. En l’absence de serveur DHCP au sein du réseau, vous devez
lancer le programme d’installation IP Installer pour modifier les réglages réseau de base,
tels que l’adresse IP, le masque de sous-réseau, la passerelle, etc., avant de pouvoir vous
connecter au réseau.
dc e
8_ présentation

installation et connexion
INSTALLATION
Précautions à prendre avant l’installation
Assurez-vous de bien lire les instructions suivantes avant d’installer la caméra.
• Elle doit être installée sur une zone (plafond ou mur) qui peut supporter cinq fois le poids de la caméra, y
compris le support d’installation.
• L’utilisation de câbles recollés ou effilochés peut endommager le produit et provoquer un incendie.
• Pour des raisons de sécurité, ne laissez personne d’autre que vous sur le site de l’installation.
Ne lais
sez pas vos effets personnels sur le site, par mesure de précaution.
Démontage
Retirez le couvercle du dôme après avoir desserré les vis en les faisant
tourner dans le sens antihoraire avec la clé Allen fournie.
• Notez qu’il n’est pas nécessaire de desserrer la vis complètement.
Ne touchez pas la partie transparente du couvercle du dôme
`
J
une fois le film protecteur retiré.
Couvercle du dôme
Installation
1. Tenez compte de la direction à surveiller, attachez le gabarit et
percez des trous en suivant le gabarit.
Placez la marque < > imprimée sur la caméra en face de la zone à surveiller.
`
2. À l’aide de 2 vis taraudeuses, fixez la caméra à 2 trous percés avec
un gabarit.
3. Raccordez les bornes internes de la caméra avec les câbles
correspondants.
4. Réglez l’orientation de l’objectif selon la position souhaitée en vous
reportant à la section « Reglage de l’orientation de la camera de
surveillance ».
`
J
5. Couvrez le couvercle du dôme et serrez les vis dans le sens horaire
avec une clé Allen pour sécuriser le couvercle.
`Si nécessaire, retirez le cache du trou des câbles sur le côté du couvercle du
dôme.
(page 10)
Nous vous recommandons de ne pas toucher l’objectif de l’appareil car il a
été correctement mis au point durant le processus final de fabrication. Si c’est
le cas, l’objectif peut être flou ou taché par des substances étrangères.
●● INSTALLATION ET CONNEXION
`Montage mural (IP42)
Pour monter la caméra sur un mur, faites passer le câble LAN par le
bas, comme sur l’illustration, de sorte qu’il soit correctement protégé
des liquides et de la poussière.
Français _9

installation et connexion
Réglage de l’orientation de la caméra de surveillance
Panoramique
Horizontale-Verticale
`Réglage de la direction de surveillance
Vous ne pouvez régler l’orientation de la caméra que lorsque celle-ci a été fixée au plafond.
La rotation de l’unité de la caméra vers la gauche ou la droite est appelée Panoramique, le réglage de
l’inclinaison est appelé Horizontale-Verticale et la rotation de l’objectif sur son axe est appelée Rotation.
- La plage effective du panoramique couvre un angle total de 350 degrés.
- La plage effective de la rotation couvre un angle total de 355 degrés.
- La plage effective de l’inclinaison couvre un angle total de 69 degrés.
L’image peut être recouverte par le boîtier de la caméra en fonction de l’angle.
`
J
`Méthodes de réglage
1. Après l’installation de la caméra, réglez l’angle de panoramique selon la direction de surveillance.
2. Réglez l’angle horizontal de manière à ce que l’image ne soit pas inversée.
3. Réglez l’angle d’inclinaison de sorte que la caméra soit face à l’objet à surveiller.
Rotation de l’objectif
INSERTION/RETRAIT D’UNE CARTE MÉMOIRE MICRO SD
Déconnectez le câble d’alimentation de la caméra avant d’y insérer la carte mémoire Micro SD.
`
J
N’insérez pas la carte mémoire Micro SD à l’envers et de force.
`
Autrement, vous risquez d’endommager la carte mémoire Micro SD.
En cas de pluie ou lorsque le taux d’humidité est élevé, l’insertion ou l’éjection d’une carte Micro SD n’est pas recommandée.
`
Insertion d’une carte mémoire Micro SD
1. Séparez le couvercle du dôme de la caméra.
2. Insérez une carte Micro SD en suivant la direction de la flèche du schéma.
10_ installation et connexion
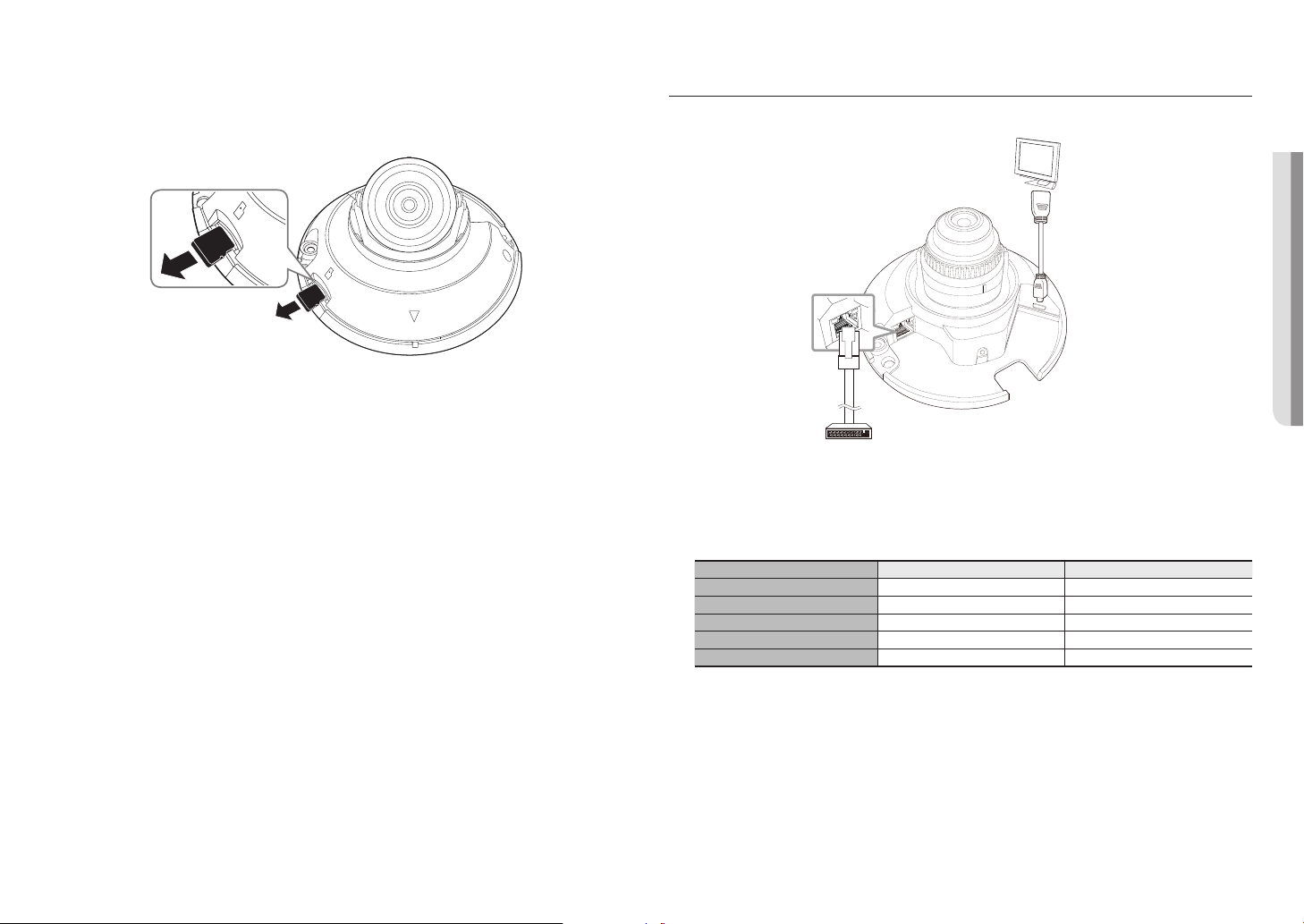
Retrait d’une carte mémoire Micro SD
Appuyer doucement vers le bas sur l'extrémité exposée de la carte mémoire comme indiqué dans le
diagramme pour éjecter la carte mémoire de la fente.
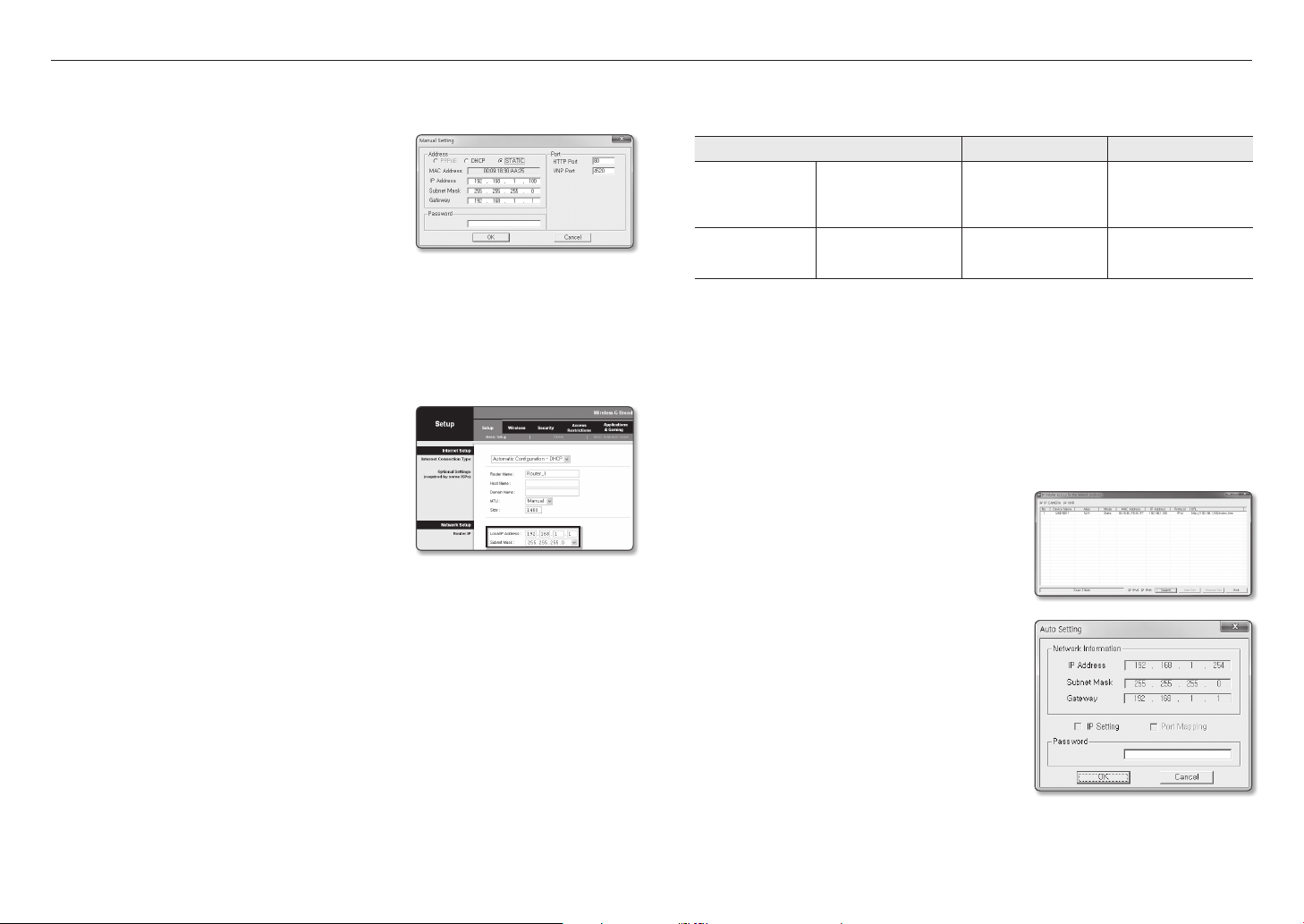
MISE SOUS TENSION ET MISE EN RÉSEAU
Connectez le périphérique PoE et les connecteurs PoE de la caméra.
Si vous exercez une pression excessive sur la carte mémoire Micro SD, celle-ci pourra s’éjecter du logement de manière
`
J
incontrôlable.
Avant de retirer votre carte mémoire Micro SD, éteignez la caméra ou allez à <Stockage>, éteignez l’appareil, puis appuyez
`
sur le bouton [Appliquer].
Si vous arrêtez la caméra ou retirez la carte mémoire Micro SD qui contient les données du produit, ces données peuvent
`
être perdues ou endommagées.
RESET
Périphérique PoE
Connectez-vous à un connecteur PoE de routeur PoE activé (alimentation électrique par câble Ethernet).
`
J
Utilisez un PoE (alimentation électrique par câble Ethernet) conforme aux protocoles IEEE802.3af.
`
Spécifications du câble réseau
Élément Contenus Remarque
Connecteur RJ45
Ethernet 10/100BASE-T 10/100 Mbps
Câble 5e catégorie
Distance max. 100 M Résistance CC ≤ 0,125 Ω / m
Support du PoE IEEE 802.3af
Moniteur
compatible HDMI
●● INSTALLATION ET CONNEXION
Si vous utilisez un câble différant des standards de catégorie 5e, la distance de transmission n’est pas garantie d’atteindre
`
M
les 100 m.
Français _11

connexion et configuration réseau
Vous pouvez configurer les paramétrages de réseau en fonction de vos configurations de réseau.
CONNECTER LA CAMÉRA DIRECTEMENT AU RÉSEAU DE ZONE LOCALE
Se connecte à la caméra à partir d'un PC local sur le LAN
1. Lancer un navigateur Internet sur le PC local.
2. Saisir l'adresse IP de la caméra dans la barre d'adresse du navigateur.
Caméra
INTERNET
Caméra
PC local
<Réseau local>
Un PC à distance dans une sortie Internet externe de réseau LAN peut ne pas pouvoir se connecter à la caméra installée
`
M
dans l'intranet si le renvoi de port n'est pas correctement configuré ou si un pare-feu est mis.
Dans ce cas, pour résoudre le problème, contacter votre administrateur de réseau.
Dans le programme d’installation IP, vous pouvez utiliser le mot de passe initial, “4321” pour définir l’adresse IP, le masque de
`
sous réseau, la passerelle, le port HTTP, le port VNP et le type d’IP. Après avoir changé l’interface réseau, pour une meilleure
sécurité, accédez au navigateur Web et modifiez le mot de passe.
Par défaut, l’adresse IP sera attribuée automatiquement depuis le serveur DHCP.
`
En l’absence de serveur DHCP disponible, l’adresse IP sera définie sur 192.168.1.100.
Pour changer l’adresse IP, utilisez le programme d'installation IP.
Pour obtenir de plus amples détails sur l’utilisation du programme d'installation IP, reportez-vous à la section « Configuration
de l’adresse IP Fixe ». (Page 13)
Ordinateur externe distant
Serveur DDNS
(Centre de données, COREE)
CONNEXION DE LA CAMÉRA DIRECTEMENT À UN MODEM DSL/CÂBLE BASÉ SUR LE PROTOCOLE DHCP
Modem DSL/Câble
Caméra
1. Connectez l’ordinateur utilisateur directement à la caméra réseau.
2. Exécutez le programme d'installation IP et changez l'adresse IP de la caméra afin d'utiliser le navigateur
Web sur votre poste pour la connexion à l'Internet.
3. Utilisez le navigateur Internet pour connecter le Web viewer.
4. Allez à la page [Configuration].
5. Allez sur [Réseau] – [DDNS], puis configurez les réglages DDNS.
6. Allez à [Basic] – [IP & Port], et définissez le type d’IP pour [DHCP].
7. Connectez la caméra, qui a été retirée de votre ordinateur, directement au modem.
8. Redémarrez la caméra.
Pour plus d’informations sur la configuration de DDNS, reportez-vous à l’aide en ligne de Web Viewer.
`
M
Pour plus d’informations sur la définition du format IP, reportez-vous à l’aide en ligne de Web Viewer.
`
INTERNET
Ordinateur externe distant
Serveur DDNS
(Centre de données, COREE)
12_ connexion et configuration réseau

BOUTONS UTILISÉS SOUS IP INSTALLER
a b c d e f g
h i
Élément Description
Device Name
a
Alias Cette fonction n’est pas appliquée pour le moment.
b
Mode Affiche <Static> ou <Dynamic> pour l’état de connexion réseau actuel.
c
MAC(Ethernet) Address
d
IP Address
e
Protocol
f
URL
g
IPv4 Recherche les caméras réglées sur IPv4.
h
Nom du modèle de la caméra connectée.
Cliquez sur la colonne pour trier la liste par nom de modèle.
Cependant, si vous cliquez dessus durant la recherche, celle-ci sera interrompue.
Adresse Ethernet de la caméra connectée.
Cliquez sur la colonne pour trier la liste par adresse Ethernet.
Cependant, si vous cliquez dessus durant la recherche, celle-ci sera interrompue.
Adresse IP.
Cliquez sur la colonne pour trier la liste par adresse IP.
Cependant, si vous cliquez dessus durant la recherche, celle-ci sera interrompue.
Réglage réseau de la caméra.
Le réglage par défaut est « IPv4 ».
Les caméras ayant un réglage en IPv6 affichent « IPv6 ».
Adresse URL du serveur DDNS autorisant l’accès à partir d’un système Internet externe.
Cependant, cette option sera remplacée par le réglage <IP Address> de la camera en cas
d’échec de l’enregistrement DDNS.
j k l m
Élément Description
IPv6
i
Search
j
Auto Set
k
Manual Set Vous devez configurer les réglages réseau manuellement.
l
Exit Quitte le programme IP Installer.
m
Utilisez la dernière version de du programme d’installation IP. Vous pouvez télécharger la version la plus récente du produit
`
M
sur le site Internet de Hanwha Techwin.
Si le système d’exploitation de support est Windows 8.1, il est recommandé d’utiliser le Gestionnaire de périphériques
`
Wisenet au lieu de l’IP Wisenet.
Le programme du gestionnaire de périphériques Wisenet peut être téléchargé en visitant le site Web de Hanwha Techwin
(http://www.hanwha-security.com) sous le menu <Guide technique> - <Outil en ligne>.
Recherche les caméras réglées sur IPv6.
Activé uniquement dans un environnement compatible IPv6.
Recherche les caméras actuellement connectées au réseau.
Cependant, ce bouton sera grisé si aucun des réglages IPv4 ou IPv6 n’est sélectionné.
Le programme d’installation IP configure automatiquement les réglages réseau.
●● CONNEXION ET CONFIGURATION RÉSEAU
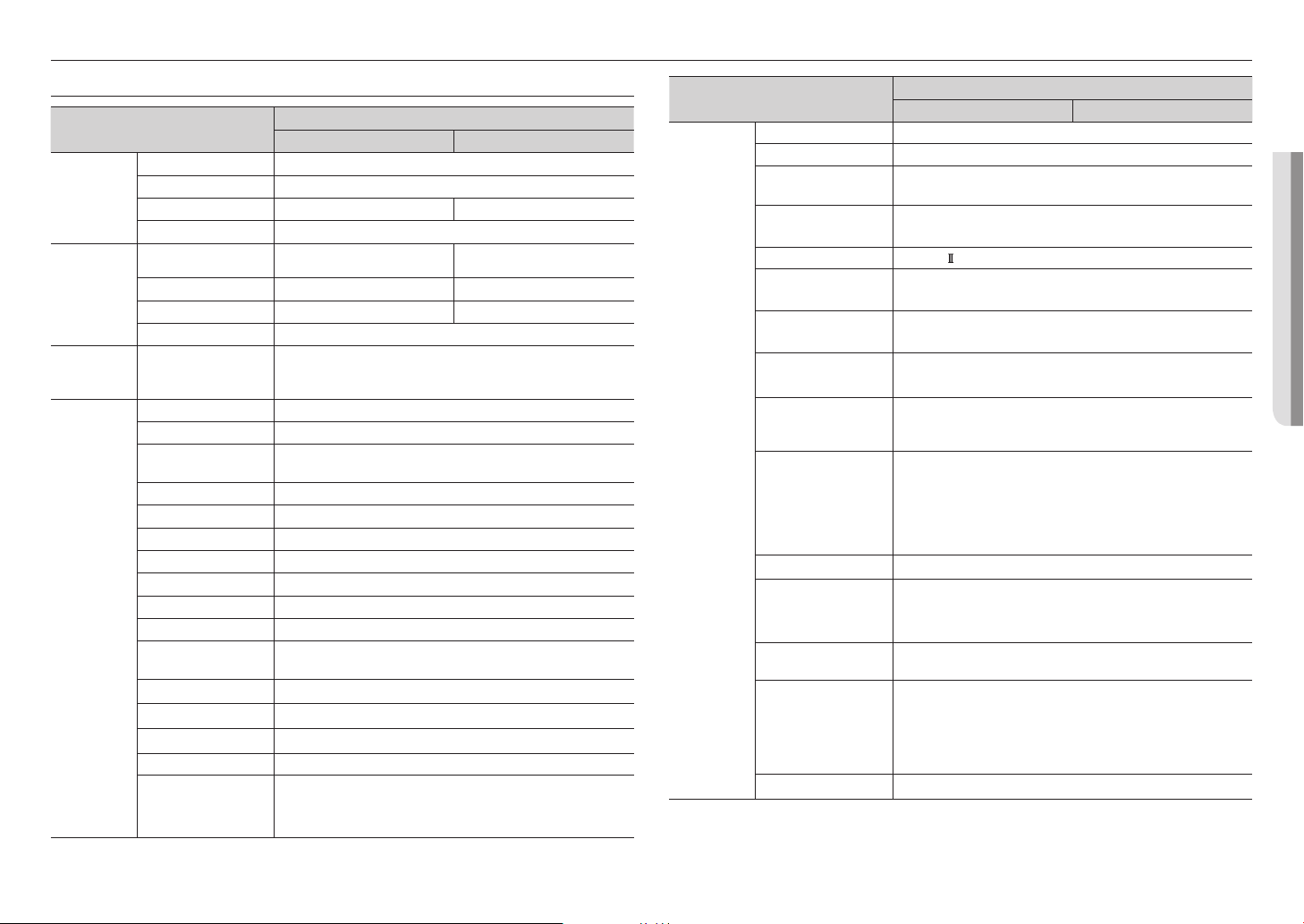
CONFIGURATION DE L’ADRESSE IP FIXE
Configuration réseau manuelle
Exécutez <IP Installer_v2.XX.exe> pour afficher la liste des résultats de la recherche de caméras.
Au démarrage initial, les deux options [Auto Set] et [Manual Set] sont grisées.
Pour les caméras trouvées ayant un réglage IPv6, ces boutons sont grisés car ces cameras ne prennent pas en charge cette
`
M
fonction.
1. Sélectionnez une caméra dans la liste de recherche.
Vérifiez l’adresse MAC de la caméra sur l’étiquette de la
caméra.
Les boutons [Auto Set] et [Manual Set] sont alors activés.
2. Cliquez sur [Manual Set].
La boîte de dialogue Manual Setting apparaît.
<IP Address>, <Subnet Mask>, <Gateway>, <HTTP
Port>, et <VNP Port> de la caméra sont affichés avec les
valeurs préréglées.
3. Renseignez les informations nécessaires dans la sous-fenêtre
<Address>.
• MAC (Ethernet) Address : L’adresse MAC imprimée sur
l’étiquette de la caméra est automatiquement affichée et ne
nécessite aucun réglage utilisateur.
Les paramètres liés à l’adresse IP ne peuvent être réglés que lorsque
`
M
DHCP n’est pas sélectionné.
Français _13
connexion et configuration réseau
Si vous n’utilisez pas de Routeur large bande
Pour le réglage des options <IP Address>, <Subnet Mask> et <Gateway>, contactez votre administrateur
réseau.
4.
Renseignez les informations nécessaires dans la sous-fenêtre
<Port>.
• HTTP Port : Permet d’accéder à la caméra à l’aide du
navigateur Internet, réglé par défaut sur 80.
• VNP Port : Permet de contrôler le transfert du signal vidéo,
réglé par défaut sur 4520.
5. Entrez le mot de passe.
Entrez le mot de passe du compte « admin » qui a été utilisé
pour accéder à la caméra.
Pour des raisons de sécurité, il est recommandé d’utiliser une combinaison de chiffres, de lettres majuscules et minuscules
`
J
et caractères spéciaux pour votre mot de passe.
Pour plus d’informations sur la modification du mot de passe, reportez-vous à l’aide en ligne de Web Viewer.
`
6. Cliquez sur [OK].
La configuration réseau manuelle est ainsi terminée.
Si vous utilisez un Routeur large bande
• IP Address : Entrez une adresse comprise dans la plage IP
fournie par le Routeur large bande.
ex.) 192.168.1.2~254, 192.168.0.2~254,
192.168.XXX.2~254
• Subnet Mask : La valeur de <Subnet Mask> du Routeur
large bande est identique à celle de l’option <Subnet Mask>
de la caméra.
• Gateway : La valeur de <Local IP Address> du Routeur
large bande est identique à celle de l’option <Gateway> de la
caméra.
Les réglages peuvent varier selon le modèle du Routeur large bande connecté.
`
M
Pour obtenir de plus amples informations à ce sujet, reportez-vous au guide d’utilisation du routeur applicable.
Pour plus d’informations sur la redirection de port du routeur large bande, reportez-vous à « Configuration de la Redirection
`
de la Plage de Ports (Mappage de Ports) ». (Page 15)
Si le Routeur large bande dispose de plusieurs caméras connectées
Configurez séparément les réglages IP et les réglages de port.
ex.)
Catégorie Caméra 1 Caméra 2
IP Address
Réglages IP
Réglages de port
Si l’option <HTTP Port> est réglée sur une valeur différente de 80, vous devrez indiquer le numéro du réglage <Port> dans la
`
M
barre d’adresse du navigateur Internet pour pouvoir accéder à la caméra.
ex.) http://IP address : HTTP Port
http://192.168.1.100:8080
Subnet Mask
Gateway
HTTP Port
VNP Port
192.168.1.100
255.255.255.0
192.168.1.1
8080
4520
192.168.1.101
255.255.255.0
192.168.1.1
8081
4521
Configuration réseau automatique
Exécutez <IP Installer_v2.XX.exe> pour afficher la liste des résultats de la recherche de caméras.
Au démarrage initial, les deux options [Auto Set] et [Manual Set] sont grisées.
Pour les caméras trouvées ayant un réglage IPv6, ces boutons sont grisés car ces cameras ne prennent pas en charge cette
`
M
fonction.
1.
Sélectionnez une caméra dans la liste de recherche.
Vérifiez l’adresse MAC de la caméra sur l’étiquette de la caméra.
Les boutons [Auto Set] et [Manual Set] sont alors activés.
2. Cliquez sur [Auto Set].
La boîte de dialogue Auto Setting apparaît.
Les options <IP Address>, <Subnet Mask> et <Gateway> sont
automatiquement réglées.
3. Entrez le mot de passe.
Entrez le mot de passe du compte « admin » qui a été utilisé
pour accéder à la caméra.
14_ connexion et configuration réseau
Pour des raisons de sécurité, il est recommandé d’utiliser une
`
J
combinaison de chiffres, de lettres majuscules et minuscules et
caractères spéciaux pour votre mot de passe.
Pour plus d’informations sur la modification du mot de passe,
`
reportez-vous à l’aide en ligne de Web Viewer.
4. Cliquez sur [OK].
La configuration réseau automatique est ainsi terminée.

CONFIGURATION DE L’ADRESSE IP DYNAMIQUE
Configuration de l’environnement IP Dynamique
• Exemple d’environnement IP Dynamique
- Routeur large bande, disposant de caméras connectées, affecté à une adresse IP par le serveur DHCP
- En cas de connexion directe de la caméra au modem via les protocoles DHCP
- Adresses IP affectées par le serveur DHCP interne via le réseau LAN
Vérification de l'adresse IP Dynamique
1. Exécutez le programme IP Installer sur l’ordinateur local de
l’utilisateur.
Les cameras attribuées avec l’adresse <Dynamic IP> sont
indiquées dans la liste.
2. Sélectionnez une caméra parmi les résultats de la recherche.
3. Cliquez sur le bouton [Manual Set] et vérifiez l’adresse
<Dynamic IP> de la caméra.
Si vous désélectionnez <DHCP>, vous pourrez modifier la
valeur de l’option IP en la réglant sur <Static>.
CONFIGURATION DE LA REDIRECTION DE LA PLAGE DE PORTS (MAPPAGE DE PORTS)
Si vous avez installé un Routeur large bande muni d'une caméra connectée, vous devrez régler la redirection de la plage
de ports sur le Routeur large bande de sorte qu'un ordinateur distant puisse accéder à la caméra qui y est installée.
Redirection manuelle de la plage de ports
1.
Depuis le menu Setup du Routeur large bande, sélectionnez
<Applications & Gaming> - <Port Range Forward>.
Pour le réglage de la redirection de la plage de ports sur
un Routeur large bande tiers, reportez-vous au manuel
d’utilisation du Routeur large bande concerné.
2. Sélectionnez <TCP> et <UDP Port> pour chacune des
cameras connectées au Routeur large bande.
Le nombre de ports à configurer sur le routeur IP doit
être réglé en fonction du nombre de ports indiqué dans
<Configuration> - <Basic> - <IP & Port> sur le visualiseur
Web de la caméra.
3.
Une fois terminé, cliquez sur [Save Settings].
Vos réglages seront ainsi sauvegardés.
Les instructions des exemples ci-dessus sont basées sur le Routeur large bande de CISCO.
`
M
Les réglages peuvent varier selon le modèle du Routeur large bande connecté.
`
Pour obtenir de plus amples informations à ce sujet, reportez-vous au guide d’utilisation du routeur applicable.
Réglage de la redirection de la plage de ports pour plusieurs caméras en réseau
• Vous pouvez définir une règle de redirection de port sur le périphérique du Routeur large bande via sa
page Web de configuration.
• Un utilisateur peut modifier chaque port à l’aide de l’écran de réglage de la caméra.
Lorsque la Caméra 1 et la Caméra 2 sont connectées à un routeur :
Utilisateur Internet
Début Fin Protocole Adresse IP
3000 3000 TCP/UDP 192.168.1.100
3001 3001 TCP/UDP 192.168.1.101
4520 4520 TCP/UDP 192.168.1.100
4521 4521 TCP/UDP 192.168.1.101
8080 8080 TCP/UDP 192.168.1.100
8081 8081 TCP/UDP 192.168.1.101
`
M
Routeur large bande
La redirection de port peut être réalisée sans paramétrage supplémentaire du routeur si celui-ci supporte la fonction UPnP.
Après avoir raccordé la caméra réseau, réglez <Connexion rapide> de <Wisenet DDNS> sur <Active> dans le menu
« Configuration Réseau DDNS ».
Caméra 1 (192.168.1.100)
Caméra 2 (192.168.1.101)
Port HTTP 8080
Port Périph. 4520
Port RTSP 3000
Port HTTP 8081
Port Périph. 4521
Port RTSP 3001
●● CONNEXION ET CONFIGURATION RÉSEAU
Français _15

connexion et configuration réseau
CONNEXION À LA CAMÉRA DEPUIS UN ORDINATEUR LOCAL PARTAGÉ
1.
Exécutez le programme d’installation IP.
Le système recherche les caméras connectées et en affiche
la liste.
2. Double-cliquez sur une caméra pour y accéder.
Le navigateur Internet démarre et se connecte à la caméra.
Vous pouvez aussi accéder à la caméra en tapant l’adresse IP de la
`
M
caméra trouvée dans la barre d’adresse du navigateur Internet.
CONNEXION À LA CAMÉRA DEPUIS UN ORDINATEUR DISTANT VIA INTERNET
L'utilisation du programme d’installation IP sur un ordinateur à distance n’appartenant pas à la grappe du réseau
du Routeur large bande n'est pas autorisé, les utilisateurs peuvent accéder aux caméras au sein du réseau du
Routeur large bande en utilisant l’adresse URL DDNS de la caméra.
1. Avant de pouvoir accéder à une caméra depuis le réseau du Routeur large bande, vous devez régler la
redirection des plages de port du Routeur large bande.
2. Depuis l'ordinateur distant, lancez le navigateur Internet et tapez l’adresse URL DDNS de la camera ou
l’adresse IP du Routeur large bande dans la barre d’adresse.
ex.) http://ddns.hanwha-security.com/ID
Pour plus d’informations sur l’enregistrement du DDNS, reportez-vous au guide de configuration du réseau.
`
M
16_ connexion et configuration réseau

visionneur web
CONNEXION À LA CAMÉRA
Normalement, vous devez procéder comme suit
1. Lancez le navigateur Internet.
Tapez l’adresse IP de la caméra dans la barre d’adresse.
2.
ex.) • Adresse IP (IPv4) : 192.168.1.100
http://192.168.1.100
- la boîte de dialogue de connexion devrait apparaître.
Adresse IP (IPv6) : 2001:230:abcd:ffff:0000:0000:ffff:1111
•
http://[2001:230:abcd:ffff:0000:0000:ffff:1111]
dialogue de connexion devrait apparaître.
Si le numéro de port HTTP est différent de 80
1. Lancez le navigateur Internet.
2. Tapez l’adresse IP et le numéro de port HTTP de la caméra dans la barre d’adresse.
ex.) Adresse IP: 192.168.1.100:
http://192.168.1.100:
HTTP
8080 - la boîte de dialogue de connexion devrait apparaître.
Numéro de port (
Utilisation de l’adresse URL
1. Lancez le navigateur Internet.
2. Tapez l’adresse URL DDNS de la caméra dans la barre d’adresse.
ex.) Adresse URL : http://ddns.hanwha-security.com/ID
- la boîte de dialogue de connexion devrait apparaître.
La connexion réseau est désactivée dans un environnement uniquement LAN.
`
J
Se connecter via UPnP
1. Exécutez le système client ou d’exploitation afin de supporter le protocole UPnP.
2. Cliquez sur le nom de la caméra aux fins de recherche.
Dans le système d’exploitation Windows, cliquez sur le nom de la caméra recherchée dans le menu
réseau.
- La fenêtre de connexion s’affiche.
- la boîte de
8080
)
Se connecter via Bonjour
1. Exécutez le système client ou d’exploitation afin de supporter le protocole Bonjour.
2. Cliquez sur le nom de la caméra pour recherche.
Sur le système d’exploitation Mac, cliquer sur le nom de la caméra lance la recherche depuis l’onglet
Bonjour de Safari.
- La fenêtre de connexion s’affiche.
●● VISIONNEUR WEB
Vérification de l'adresse DDNS
Si la caméra est connectée directement à un modem câble ou à un modem DSL basé sur DHCP, l’adresse
IP change chaque fois qu’elle tente de se connecter au FAI (la société à laquelle vous vous êtes abonné).
Le cas échéant, vous ne serez pas informé du changement d'adresse IP par le serveur DDNS.
Une fois que vous enregistrez un périphérique dynamique basé sur IP sur le serveur <DDNS>, vous pouvez
facilement vérifier l’adresse IP modifiée lorsque vous essayez d’accéder au périphérique.
http://ddns.hanwha-security.com et enregistrez tout d’abord votre périphérique puis réglez <Réseau> <DDNS> de Web Viewer sur <Wisenet DDNS>. Renseignez également le champ <ID produit> avec la
donnée utilisée pour l’enregistrement DDNS.
Français _17

visionneur web
RÉGLAGE DU MOT DE PASSE
Lorsque vous accédez au produit pour la première fois, vous devez
enregistrer le mot de passe de connexion.
Lorsque la fenêtre « Confirm new password » apparaît, saisissez le
nouveau mot de passe.
Pour un nouveau mot de passe de 8 à 9 chiffres, vous devez
`
J
utiliser au moins trois des éléments suivants : lettres majuscules /
minuscules, chiffres et caractères spéciaux. Pour un mot de passe
de 10 à 15 chiffres, vous devez utiliser au moins deux des types
mentionnés.
Les caractères spéciaux qui sont autorisés. : ~`!@#$%^*()_-+=|{}
-
[].?/
Pour plus de sécurité, il n’est pas recommandé de répéter les mêmes caractères ou entrées clavier consécutives pour vos
`
mots de passe.
Si vous avez perdu votre mot de passe, vous pouvez appuyer sur le bouton [RESET] pour initialiser le produit. Veuillez donc
`
ne pas perdre votre mot de passe en utilisant un bloc-notes ou bien mémorisez-le.
LOGIN
Lorsque vous accédez à la caméra, la fenêtre de connexion apparaît.
Saisissez l’identifiant utilisateur et le mot de passe pour accéder à la caméra.
1. Entrez « admin » dans la zone de saisie de texte <User
Name>.
L’identifiant de l’administrateur « admin » est fixe et ne peut
être modifié.
2.
Saisissez le mot de passe dans le champ de saisie <Password>.
3. Cliquez sur [OK].
Si vous vous êtes connecté avec succès, vous verrez l’écran
Live Viewer s’afficher.
Lorsque vous accédez à la visionneuse web de la caméra, accordez une attention particulière à la sécurité en vérifiant si les
`
J
données d’image sont cryptées.
INSTALLATION DE LA VISIONNEUSE WEB DE LA CAMÉRA
1. Cliquez sur l’îcone [Configuration ( )].
2. La fenêtre de configuration apparaît.
3. Vous pouvez configurer les paramètres pour les informations de base de la caméra, la vidéo, l’audio, le
réseau, l’événement, l’analyse et le système sur le réseau.
4. Cliquez sur <Aide (
)> pour voir les descriptions détaillées de chaque fonction.
Si vous sélectionnez l’option « Remember my credentials » après avoir entré votre saisie, vous serez automatiquement
`
M
connecté sans être invité à entrer vos informations de connexion à votre prochaine connexion.
Pour une qualité vidéo optimale, passez en affichage 100 %. La réduction du format de l’image peut couper l’image sur les bords.
`
18_ visionneur web
annexes
SPÉCIFICATIONS
Éléments
Système imageur 1/2,8” 5MP CMOS
Vidéo
Objectif
Panoramique /
Inclinaison /
Rotation
Opérationnel
Nombre de pixels réels
Luminosité minimale Couleur : 0,15 Lux (F2.0, 1/30 sec) Couleur : 0,15 Lux (F1.6, 1/30 sec)
Sortie vidéo HDMI: 1080p@30/25 fps (60/50 Hz)
Longueur focale
(facteur zoom)
Ouverture relative maxi F2.0 F1.6
Champ de vision angulaire
Contrôle de la mise au point
Plage panoramique /
inclinaison / rotation
Titre de caméra Affichage jusqu’à 85 caractères
Jour et Nuit Auto (Électrique)
Compensation de
rétroéclairage
Large gamme dynamique 120dB
Réduction du bruit numérique SSNR
Détection mouvement 4ea, zones polygonales
Masque de confidentialité 6ea, zones rectangulaires
Contrôle du gain Assistance
Balance Blancs ATW / AWC / Manuel / Intérieur / Extérieur
LDC Assistance
Vitesse d’obturateur
électronique
Rotation vidéo Retourner, Miroir, Corridor (90˚ / 270˚)
Analyse Détection des effets de flou, détection de mouvement, sabotage
Business Intelligence Comptage de personnes
Déclenchements d’alarme Analyse, Déconnexion réseau
Événements d'alarme
Éléments
Description
QND-8011 QND-8021
2592(H) x 1944(V)
Focale fixe 2,8mm Focale fixe 4mm
H: 104,4°/ V: 76,7°/ D: 136,1° H: 80,1°/ V: 58,0°/ D: 105,8°
Fixe
0˚~350˚ / 0˚~69˚ / 0˚~355˚
BLC, WDR, SSDR
Minimum / Maximum / Anti scintillement (1/5~1/12,000 sec)
yTélétransmission de fichiers via FTP, E-mail
yNotification par e-mail
yEnregistrement SD/SDHC/SDXC ou NAS lors des déclenchements d’événements
Réseau
Ethernet RJ-45 (10/100BASE-T)
Format de compression vidéo H.265/H.264 : format principal/haute qualité, MJPEG
Résolution
Vitesse d’enregistrement
max.
Smart Codec WiseStream
Réglage de la qualité vidéo
Méthode de contrôle du débit
binaire
Diffusion
Protocole
Sécurité
Edge storage Micro SD/SDHC/SDXC 1 fentes 128 Go
Interface de programmation
de l’application
Langue de la page Web
Web Viewer
Mémoire 512 MB RAM, 256 MB Flash
2592 x 1944, 1920 x 1080, 1280 x 960, 1280 x 720, 800 x 600, 800 x 448,
720 x 576, 720 x 480, 640 x 480, 640 x 360
H.265/H.264 : Max. 30fps/25fps (60 Hz/50 Hz)
MJPEG : Max. 15fps/12fps (60 Hz/50 Hz)
H.264/H.265 : Contrôle du niveau de débit binaire cible
MJPEG : Contrôle du niveau de qualité
H.264/H.265 : CBR ou VBR
Motion JPEG : VBR
Unicast (6 utilisateurs) / Multicast
Diffusion multiple (jusqu’à 3 profils)
IPv4, IPv6, TCP/IP, UDP/IP, RTP(UDP), RTP(TCP), RTCP, RTSP, NTP, HTTP, HTTPS,
SSL/TLS, DHCP, FTP, SMTP, ICMP, IGMP, SNMPv1/v2c/v3(MIB-2), ARP, DNS, DDNS,
QoS, UPnP, Bonjour, LLDP
Authentification de l'identifiant HTTPS(SSL)
Authentification de l'identifiant en abrégé
Filtrage de l’adresse IP
Journal d’accès des utilisateurs
Authentification 802.1X (EAP-TLS, EAP-LEAP)
ONVIF Profile S/G/T
SUNAPI(HTTP API)
Plate-forme ouverte Wisenet
Anglais, Coréen, Français, Allemand, Espagnol, Italien, Chinois, Russe, Japonais,
Suédois, Portugais, Tchèque, Polonais, Turc, Néerlandais, Hongrois, Grec
Système d’exploitation pris en charge : Windows 7, 8.1, 10, Mac OS X 10.12,
10.13, 10.14
Navigateur recommandé : Google Chrome
Navigateurs pris en charge : MS Explore11, MS Edge, Mozilla Firefox(supporté
uniquement sur Window 64bit), Apple Safari(supporté uniquement sur Mac OS X)
QND-8011 QND-8021
Description
●● ANNEXES
Français _19
annexes
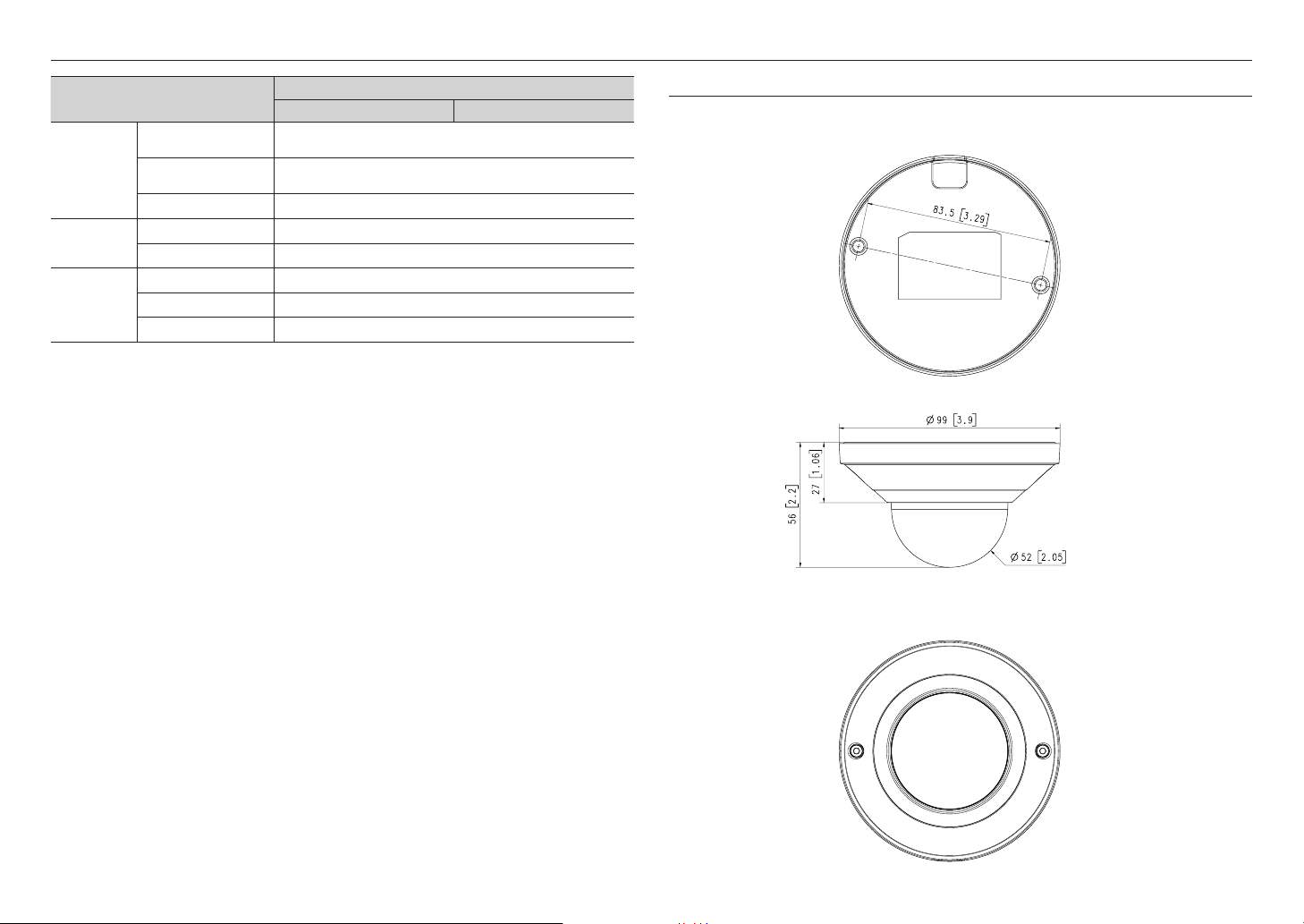
Environnemental
Électrique
Mécanique
Éléments
Température / Humidité de
fonctionnement
Température / Humidité de
stockage
Certification IP42, IK08
Tension d’entrée PoE(IEEE802.3af, Class2)
Consommation d’énergie PoE: Max 5 W, typique 4 W
Couleur / Matériau Blanc/Plastique
Code RAL RAL9003
Dimensions/poids du produit Ø99 x 56 mm(Ø3,9 x 2,2”), 165 g
-10°C ~ +40°C (-14°F ~ +104°F) / Moins de 90 % d’humidité relative
-30°C ~ +60°C (-22°F ~ +140°F) / Moins de 90 % d’humidité relative
QND-8011 QND-8021
Description
VUE DU PRODUIT
Unité : mm [pouce]
20_ annexes

RÉSOLUTION DE PROBLÈMES
PROBLÈME SOLUTION
yDans la fenêtre d'authentification contextuelle affichée lors de l'accès initial à https, cliquez
Aucune vidéo n’est affichée lors de
l’accès libre au visualiseur Web de
plug-in sur Safari via HTTPS.
Je n'ai pas accès à la caméra à partir
d'un navigateur Internet.
Le visionneur a été déconnecté
pendant le suivi.
Aucune vidéo ne s’affiche lorsque
l’utilisateur vient d’accéder au
visualiseur Web ou qu’il se connecte
directement avec le client.
La caméra connectée au réseau n'est
pas détectée dans le programme
d'installateur IP.
Chevauchement d'images.
Aucune image n'apparaît.
sur "Afficher certificat d'authentification" et sélectionnez l'option "Toujours faire confiance
lors de la connexion à l'adresse IP du visualiseur Web désigné".
ySi le visualiseur Web ne peut toujours pas lire une vidéo après avoir sélectionné "Suivant"
dans la fenêtre de message ci-dessous, appuyez sur la touche de commande + Q pour
quitter le navigateur Safari puis recommencez et suivez les procédures indiquées ci-dessus.
yVérifier pour s'assurer que les paramètres de réseau de la caméra sont appropriés.
yVérifier pour assurer que tous les câbles de réseau ont été correctement connectés.
ySi elle est connectée en utilisant DHCP, vérifier que la caméra peut acquérir des adresses
IP dynamiques sans aucun problème.
ySi la caméra est connectée à un Routeur large bande, vérifier que le renvoi de port est
configuré correctement.
yLes visionneurs connectés se déconnectent à tout changement apporté à la caméra ou aux
configurations de réseau.
yVérifier toutes les connexions de réseau.
yLe nombre maximum de profils disponibles est de 3.
La connexion peut être perdue si vous utilisez 4 ou plusieurs profils.
Exemple : Si vous accédez aux profils MJPEG, H264 et H265 puis essayez un profil différent,
la connexion sera perdue.
yDésactiver les paramètres de pare-feu sur votre PC et chercher de nouveau la caméra.
yVérifier si une ou plusieurs caméras sont configurée à une adresse multidiffusion unique au
lieu d'adresses différentes. Si une adresse unique est utilisée pour des caméras multiples,
les images peuvent se chevaucher.
ySi la méthode de transmission est configurée sur multidiffusion, vérifier s'il y a un routeur qui
prend en charge la multidiffusion dans le LAN sur lequel la caméra est connectée.
PROBLÈME SOLUTION
<Détection mvt> de l’<Analyse> est
réglé sur <Activer>, mais je ne reçois
pas de notification par e-mail même
quand un événement d’analyse s’est
produit.
Impossible d’effectuer un
enregistrement sur la carte mémoire
Micro SD.
La carte mémoire Micro SD est
insérée mais la caméra ne fonctionne
pas correctement.
Impossible d’enregistrer sur le
système NAS.
Un rapport mentionne que le réglage
du système NAS a échoué.
yVérifiez les réglages selon la séquence suivante :
A. Vérifiez les réglages <Date et heure>.
B. L’option <Détection mvt> doit être réglée sur <Activer>.
C. Vérifiez si l'option <E-mail> du menu <Config. évén.> est cochée avant utilisation.
yVérifiez que la carte mémoire n’est pas défectueuse.
yVérifiez si la carte mémoire est insérée dans le bon sens. Le fonctionnement des cartes
mémoire formatées sur d’autres appareils n’est pas garanti sur cette caméra.
yFormatez la carte mémoire à nouveau sous le menu
<Stockage>
.
yAssurez-vous que l’information enregistrée dans le système NAS soit correcte.
yL’adresse IP du NAS est valide.
yID/mot de passe du NAS est valide.
yAssurez-vous de pouvoir accéder au dossier désigné comme dossier principal en utilisant le
ID du NAS.
yLes items SMB/CIFS du NAS ne sont pas cochés.
yL’adresse IP du NAS et celle de la caméra ont le même format.
Ex) La valeur initiale du masque de sous-réseau du NAS et de la caméra est 255.255.255.0.
Si l’adresse IP est 192.168.20.32, alors l’adresse IP du NAS devrait être quelque part dans
192.168.20.1~192.168.20.255.
yVérifiez si vous avez tenté d’y accéder sous un autre nom d’utilisateur sans formater le
principal dossier utilisé ou sauvegardé.
yAssurez-vous d’avoir utilisé l’équipement NAS recommandé.
<Configuration> <Événement>
●● ANNEXES
Français _21

OPEN SOURCE ANNOUNCEMENT
GPL/LGPL software license
The software included in this product contains copyrighted software that is licensed under the GPL/LGPL. You may obtain the complete Corresponding
Source code from us for a period of three years after our last shipment of this product by sending email to help.cctv@hanwha.com
If you want to obtain the complete Corresponding Source code in the physical medium such as CD-ROM, the cost of physically performing source
distribution might be charged.
GPL SW
Component Name License URL
Base Kernel
Busybox
iproute2-4.3.0
iptables-1.4.21
ethtool-4.2
mtd-1.5.2
mii-diag-2.11
rp-pppoe-3.11
wpa_supplicant-2.5
bash-4.3.30
zeroconf
LGPL SW
Component Name License URL
gLibc
Inetutils
neon-0.29.6
GPL 2.0
GPL 2.0
GPL 2.0
GPL 2.0
GPL 2.0
GPL 2.0
GPL 2.0
GPL 2.0
GPL 2.0
GPL 3.0
GPL 2.0
LGPL 2.0
LGPL 3.0
LGPL 2.0 http://www.webdav.org/neon/
http://www.busybox.net/downloads/snapshots
http://ftp.netfilter.org/pub/iptables
ftp://ftp.infradead.org/pub/mtd-utils
http://www.roaringpenguin.com/pppoe/
GNU GENERAL PUBLIC LICENSE
Version 2, June 1991
Copyright (C)1989, 1991 Free Software Foundation, Inc. 51 Franklin Street,Fifth Floor, Boston, MA 02110-1301, USA
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
Preamble
The licenses for most software are designed to take away your freedom to share and change it. By contrast, the GNU General Public License is intended to
guarantee your freedom to share and change free software-- to make sure the software is free for all its users. This General Public License applies to most of the
Free Software Foundation’s software and to any other program whose authors commit to using it. (Some other Free Software Foundation software is covered
by the GNU Lesser General Public License instead.) You can apply it to your programs, too. When we speak of free software, we are referring to freedom, not
price. Our General Public Licenses are designed to make sure that you have the freedom to distribute copies of free software (and charge for this service if you
wish), that you receive source code or can get it if you want it, that you can change the software or use pieces of it in new free programs ; and that you know
you can do these things.
To protect your rights, we need to make restrictions that forbid anyone to deny you these rights or to ask you to surrender the rights. These restrictions translate
to certain responsibilities for you if you distribute copies of the software, or if you modify it.
For example, if you distribute copies of such a program, whether gratis or for a fee, you must give the recipients all the rights that you have.
You must make sure that they, too, receive or can get the source code. And you must show them these terms so they know their rights. We protect your rights
with two steps :
(1)copyright the software, and (2)offer you this license which gives you legal permission to copy, distribute and/or modify the software. Also, for each author’s
protection and ours, we want to make certain that everyone understands that there is no warranty for this free software. If the software is modified by someone
else and passed on, we want its recipients to know that what they have is not the original, so that any problems introduced by others will not reflect on the
original authors’ reputations.
Finally, any free program is threatened constantly by software patents. We wish to avoid the danger that redistributors of a free program will individually obtain
patent licenses, in effect making the program proprietary. To prevent this, we have made it clear that any patent must be licensed for everyone’s free use or not
licensed at all. The precise terms and conditions for copying, distribution and modification follow.
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
Version 2, June 1991 Copyright (C) 1989, 1991 Free Software Foundation, Inc. 51 Franklin S
0. This License applies to any program or other work which contains a notice placed by the copyright holder saying it may be distributed under the terms of this
General Public License.
The “Program”, below, refers to any such program or work, and a “work based on the Program” means either the Program or any derivative work under
copyright law : that is to say, a work containing the Program or a portion of it, either verbatim or with modifications and/or translated into another language.
(Hereinafter, translation is included without limitation in the term “modification”.) Each licensee is addressed as “you”.
Activities other than copying, distribution and modification are not covered by this License ; they are outside its scope. The act of running the Program is not
restricted, and the output from the Program is covered only if its contents constitute a work based on the Program (independent of having been made by
running the Program). Whether that is true depends on what the Program does.
1. You may copy and distribute verbatim copies of the Program’s source code as you receive it, in any medium, provided that you conspicuously and
appropriately publish on each copy an appropriate copyright notice and disclaimer of warranty; keep intact all the notices that refer to this License and to the
absence of any warranty ; and give any other recipients of the Program a copy of this License along with the Program.
You may charge a fee for the physical act of transferring a copy, and you may at your option offer warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Program or any portion of it, thus forming a work based on the Program, and copy and distribute such
modifications or work under the terms of Section 1 above, provided that you also meet all of these conditions :
a) You must cause the modified files to carry prominent notices stating that you changed the files and the date of any change.
b) You must cause any work that you distribute or publish, that in whole or in part contains or is derived from the Program or any part thereof, to be licensed
as a whole at no charge to all third parties under the terms of this License.
c) If the modified program normally reads commands interactively when run,you must cause it, when started running for such interactive use in the most
ordinary way, to print or display an announcement including an appropriate copyright notice and a notice that there is no warranty (or else, saying that
you provide a warranty) and that users may redistribute the program under these conditions, and telling the user how to view a copy of this License.
(Exception:if the Program itself is interactive but does not normally print such an announcement, your work based on the Program is not required to print
an announcement.)
These requirements apply to the modified work as a whole. If identifiable sections of that work are not derived from the Program, and can be reasonably
considered independent and separate works in themselves, then this License, and its terms, do not apply to those sections when you distribute them as separate
works. But when you distribute the same sections as part of a whole which is a work based on the Program, the distribution of the whole must be on the terms of
this License, whose permissions for other licensees extend to the entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest your rights to work written entirely by you ; rather, the intent is to exercise the right to control the
distribution of derivative or collective works based on the Program. In addition, mere aggregation of another work not based on the Program with the Program
(or with a work based on the Program)on a volume of a storage or distribution medium does not bring the other work under the scope of this License.
3. You may copy and distribute the Program (or a work based on it, under Section 2)in object code or executable form under the terms of Sections 1 and 2
above provided that you also do one of the following :
a) Accompany it with the complete corresponding machine-readable source code, which must be distributed under the terms of Sections 1 and 2 above on
a medium customarily used for software interchange ; or,
b) Accompany it with a written offer, valid for at least three years, to give any third party, for a charge no more than your cost of physically performing source
distribution, a complete machinereadable copy of the corresponding source code, to be distributed under the terms of Sections 1 and 2 above on a medium
customarily used for software interchange ; or,
c) Accompany it with the information you received as to the offer to distribute corresponding source code. (This alternative is allowed only for noncommercial
distribution and only if you received the program in object code or executable form with such an offer, in accord with Subsection b above.) The source code
for a work means the preferred form of the work for making modifications to it. For an executable work, complete source code means all the source code for
all modules it contains, plus any associated interface definition files, plus the scripts used to control compilation and installation of the executable. However,
as a special exception, the source code distributed need not include anything that is normally distributed (in either source or binary form) with the major

components (compiler, kernel, and so on) of the operating system on which the executable runs, unless that component itself accompanies the executable.
If distribution of executable or object code is made by offering access to copy from a designated place, then offering equivalent access to copy the source
code from the same place counts as distribution of the source code, even though third parties are not compelled to copy the source along with the object
code.
4. You may not copy, modify, sublicense, or distribute the Program except as expressly provided under this License. Any attempt otherwise to copy, modify,
sublicense or distribute the Program is void, and will automatically terminate your rights under this License.
However, parties who have received copies, or rights, from you under this License will not have their licenses terminatedso long as such parties remain in full
compliance.
5. You are not required to accept this License, since you have not signed it. However, nothing else grants you permission to modify or distribute the Program or
its derivative works.
These actions are prohibited by law if you do not accept this License.Therefore, by modifying or distributing the Program (or any work based on the Program), you
indicate your acceptance of this License to do so, and all its terms and conditions for copying, distributing or modifying the Program or works based on it.
6. Each time you redistribute the Program (or any work based on the Program), the recipient automatically receives a license from the original licensor to copy,
distribute or modify the Program subject to these terms and conditions. You may not impose any further restrictions on the recipients’ exercise of the rights
granted herein. You are not responsible for enforcing compliance by third parties to this License.
7. If, as a consequence of a court judgment or allegation of patent infringement or for any other reason (not limited to patent issues), conditions are imposed on
you (whether by court order, agreement or otherwise)that contradict the conditions of this License, they do not excuse you from the conditions of this License.
If you cannot distribute so as to satisfy simultaneously your obligations under this License and any other pertinent obligations, then as a consequence you
may not distribute the Program at all.
For example, if a patent license would not permit royaltyfree redistribution of the Program by all those who receive copies directly or indirectly through you, then
the only way you could satisfy both it and this License would be to refrain entirely from distribution of the Program.
If any portion of this section is held invalid or unenforceable under any particular circumstance, the balance of the section is intended to apply and the section as
a whole is intended to apply in other circumstances. It is not the purpose of this section to induce you to infringe any patents or other property right claims or to
contest validity of any such claims; this section has the sole purpose of protecting the integrity of the free software distribution system, which is implemented by
public license practices. Many people have made generous contributions to the wide range of software distributed through that system in reliance on consistent
application of that system ; it is up to the author/donor to decide if he or she is willing to distribute software through any other system and a licensee cannot
impose that choice. This section is intended to make thoroughly clear what is believed to be a consequence of the rest of this License.
8. If the distribution and/or use of the Program is restricted in certain countries either by patents or by copyrighted interfaces, the original copyright holder who
places the Program under this License may add an explicit geographical distribution limitation excluding those countries,so that distribution is permitted only
in or among countries not thus excluded. In such case, this License incorporates the limitation as if written in the body of this License.
9. The Free Software Foundation may publish revised and/or new versions of the General Public License from time to time. Such new versions will be similar
in spirit to the present version, but may differ in detail to address new problems or concerns. Each version is given a distinguishing version number. If the
Program specifies a version number of this License which applies to it and “any later version”, you have the option of following the terms and conditions either
of that version or of any later version published by the Free Software Foundation. If the Program does not specify a version number of this License, you may
choose any version ever published by the Free Software Foundation.
10. If you wish to incorporate parts of the Program into other free programs whose distribution conditions are different, write to the author to ask for permission.
For software which is copyrighted by the Free Software Foundation,write to the Free Software Foundation ; we sometimes make exceptions for this. Our
decision will be guided by the two goals of preserving the free status of all derivatives of our free software and of promoting the sharing and reuse of software
generally.
NO WARRANTY
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM
“ASIS” WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS
WITH YOU. SHOULD THE PROGRAMPROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY
WHO MAY MODIFY AND/OR REDISTRIBUTE DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING
OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE
OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH
HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New Programs If you develop a new program, and you want it to be of the greatest possible use to the public, the best way
to achieve this is to make it free software which everyone can redistribute and change under these terms. To do so, attach the following notices to the program.
It is safest to attach them to the start of each source file to most effectively convey the exclusion of warranty ; and each file should have at least the “copyright”
line and a pointer to where the full notice is found.one line to give the program’s name and an idea of what it does.
Copyright (C)yyyy name of author
This program is free software ; you can redistribute it and/or modify it under the terms of the GNU General Public License as published by the Free Software
Foundation ; either version 2 of the License, or (at your option)any later version.
This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY ; without even the implied warranty of MERCHANTABILITY or
FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License for more details.
You should have received a copy of the GNU General Public License along with this program ; if not, write to the Free Software Foundation, Inc.,51 Franklin
Street, Fifth Floor, Boston, MA 02110-1301, USA.
Also add information on how to contact you by electronic and paper mail. If the program is interactive, make it output a short notice like this when it starts in an
interactive mode :
Gnomovision version 69, Copyright (C) year name of author Gnomovision comes with ABSOLUTELY NO WARRANTY ; for details type ‘show w’. This is free software,
and you are welcome to redistribute it under certain conditions ; type ‘show c’ for details.
The hypothetical commands ‘show w’ and ‘show c’ should show the appropriate parts of the General Public License. Of course, the commands you use may
be called something other than ‘show w’ and ‘show c’ ; they could even be mouse-clicks or menu items-- whatever suits your program.
You should also get your employer (if you work as a programmer)or your school, if any, to sign a “copyright disclaimer” for the program,if necessary. Here is a
sample ; alter the names:
Yoyodyne, Inc.,hereby disclaims all copyright interest in the program ‘Gnomovision’ (which makes passes at compilers) written by James Hacker. signature of
Ty Coon, 1 April 1989 Ty Coon, President of Vice This General Public License does not permit incorporating your program into proprietary programs. If your
program is a subroutine library, you may consider it more useful to permit linking proprietary applications with the library. If this is Lwihcaetn ysoeu want to do,
use the GNU Lesser General Public instead of this License.
GNU GENERAL PUBLIC LICENSE
Version 3, 29 June 2007
Copyright (C) 2007 Free Software Foundation, Inc. <http://fsf.org/>
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
Preamble
The GNU General Public License is a free, copyleft license for software and other kinds of works. The licenses for most software and other practical works are
designed to take away your freedom to share and change the works. By contrast, the GNU General Public License is intended to guarantee your freedom to
share and change all versions of a program-- to make sure it remains free software for all its users.
We, the Free Software Foundation, use the GNU General Public License for most of our software; it applies also to any other work released this way by its
authors.
You can apply it to your programs, too. When we speak of free software, we are referring to freedom, not price. Our General Public Licenses are designed to
make sure that you have the freedom to distribute copies of free software (and charge for them if you wish), that you receive source code or can get it if you
want it, that you can change the software or use pieces of it in new free programs, and that you know you can do these things.
To protect your rights, we need to prevent others from denying you these rights or asking you to surrender the rights. Therefore, you have certain responsibilities
if you distribute copies of the software, or if you modify it: responsibilities to respect the freedom of others. For example, if you distribute copies of such a
program, whether gratis or for a fee, you must pass on to the recipients the same freedoms that you received. You must make sure that they, too, receive
or can get the source code. And you must show them these terms so they know their rights. Developers that use the GNU GPL protect your rights with two
steps: (1) assert copyright on the software, and (2) offer you this License giving you legal permission to copy, distribute and/or modify it. For the developers’ and
authors’ protection, the GPL clearly explains that there is no arranty for this free software. For both users’ and authors’ sake, the GPL requires that modified
versions be marked as changed, so that their problems will not be attributed erroneously to authors of previous versions. Some devices are designed to deny
users access to install or run modified versions of the software inside them, although the manufacturer can do so. This is fundamentally incompatible with the
aim of protecting users’ freedom to change the software. The systematic pattern of such abuse occurs in the area of products for individuals to use, which is
precisely where it is most unacceptable. Therefore, we have designed this version of the GPL to prohibit the practice for those products. If such problems arise
substantially in other domains, we stand ready to extend this provision to those domains in future versions of the GPL, as needed to protect the freedom of
users.
Finally, every program is threatened constantly by software patents. States should not allow patents to restrict development and use of software on generalpurpose omputers, but in those that do, we wish to avoid the special anger that patents applied to a free program could make it ffectively proprietary. To prevent
this, the GPL assures that atents cannot be used to render the program non-free. he precise terms and conditions for copying, distribution and modification
follow.
TERMS AND CONDITIONS
0. Definitions.
“This License” refers to version 3 of the GNU General Public License.
Copyright” also means copyright-like laws that apply to other kinds of works, such as semiconductor masks. “The Program” refers to any copyrightable work
licensed under this License. Each licensee is addressed as “you”. “Licensees” and “recipients” may be individuals or organizations.
To “modify” a work means to copy from or adapt all or part of the work in a fashion requiring copyright permission, other than the making of an exact copy. The
resulting work is called a “modified version” of the earlier work or a work “based on” the earlier work.
A “covered work” means either the unmodified Program or a work based on the Program.
To “propagate” a work means to do anything with it that, without permission, would make you directly or secondarily liable for infringement under applicable
copyright law, except executing it on a computer or modifying a private copy.
Propagation includes copying, distribution (with or without modification), making available to the public, and in some countries other activities as well.
To “convey” a work means any kind of propagation that enables other parties to make or receive copies. Mere interaction with a user through a computer
network, with no transfer of a copy, is not conveying. An interactive user interface displays “Appropriate Legal Notices” to the extent that it includes a convenient
and prominently visible feature that (1) displays an appropriate copyright notice, and (2) tells the user that there is no warranty for the work (except to the extent
that warranties are provided), that licensees may convey the work under this License, and how to view a copy of this License. If the interface presents a list of
user commands or options, such as a menu, a prominent item in the list meets this criterion.
1. Source Code.
The “source code” for a work means the preferred form of the work for making modifications to it. “Object code” means any non-source form of a work.
A “Standard Interface” means an interface that either is an official standard defined by a recognized standards body, or, in the case of interfaces specified for a
particular programming language, one that is widely used among developers working in that language.
The “System Libraries” of an executable work include anything, other than the work as a whole, that (a) is included in the normal form of packaging a Major
Component, but which is not part of that Major Component, and (b) serves only to enable use of the work with that Major Component, or to implement a
Standard Interface for which an implementation is available to the public in source code form. A “Major Component”, in this context, means a major essential
component (kernel, window system, and so on) of the specific operating system (if any) on which the executable work runs, or a compiler used to produce the
work, or an object code interpreter used to run it.
The “Corresponding Source” for a work in object code form means all the source code needed to generate, install, and (for an executable work) run the object
code and to modify the work, including scripts to control those activities.
However, it does not include the work’s System Libraries, or generalpurpose tools or generally available free programs which are used unmodified in performing
those activities but which are not part of the work. For example, Corresponding Source includes interface definition files associated with source files for the
work, and the source code for shared libraries and dynamically linked subprograms that the work is specifically designed to require, such as by intimate data
communication or control flow between those subprograms and other parts of the work.
The Corresponding Source need not include anything that users can regenerate automatically from other parts of the Corresponding Source. The Corresponding
Source for a work in source code form is that same work.

2. Basic Permissions.
All rights granted under this License are granted for the term of copyright on the Program, and are irrevocable provided the stated conditions are met. This
License explicitly affirms your unlimited permission to run the unmodified Program. The output from running a covered work is covered by this License only if the
output, given its content, constitutes a covered work. This License acknowledges your rights of fair use or other equivalent, as provided by copyright law.
You may make, run and propagate covered works that you do not convey, without conditions so long as your license otherwise remains in force. You may convey
covered works to others for the sole purpose of having them make modifications exclusively for you, or provide you with facilities for running those works, provided
that you comply with the terms of this License in conveying all material for which you do not control copyright. Those thus making or running the covered works for
you must do so exclusively on your behalf, under your direction and control, on terms that prohibit them from making any copies of your copyrighted material outside
their relationship with you. Conveying under any other circumstances is permitted solely under the conditions stated below. Sublicensing is not allowed; section 10
makes it unnecessary.
3. Protecting Users’ Legal Rights From anti-Circumvention Law.
No covered work shall be deemed part of an effective technological measure under any applicable law fulfilling obligations under article 11 of the WIPO copyright
treaty adopted on 20 December 1996, or similar laws prohibiting or restricting circumvention of such measures.
When you convey a covered work, you waive any legal power to forbid circumvention of technological measures to the extent such circumvention is effected by
exercising rights under this License with respect to the covered work, and you disclaim any intention to limit operation or modification of the work as a means of
enforcing, against the work’s users, your or third parties’ legal rights to forbid circumvention of technological measures.
4. Conveying Verbatim Copies.
You may convey verbatim copies of the Program’s source code as you receive it, in any medium, provided that you conspicuously and appropriately publish on
each copy an appropriate copyright notice; keep intact all notices stating that this License and any non-permissive terms added in accord with section 7 apply
to the code; keep intact all notices of the absence of any warranty; and give all recipients a copy of this License along with the Program. You may charge any
price or no price for each copy that you convey, and you may offer support or warranty protection for a fee.
5. Conveying Modified Source Versions.
You may convey a work based on the Program, or the modifications to produce it from the Program, in the form of source code under the terms of section 4,
provided that you also meet all of these conditions:
a) The work must carry prominent notices stating that you modified it, and giving a relevant date.
b) The work must carry prominent notices stating that it is released under this License and any conditions added under section 7. This requirement modifies
the requirement in section 4 to “keep intact all notices”.
c) You must license the entire work, as a whole, under this License to anyone who comes into possession of a copy. This License will therefore apply, along
with any applicable section 7 additional terms, to the whole of the work, and all its parts, regardless of how they are packaged. This License gives no
permission to license the work in any other way, but it does not invalidate such permission if you have separately received it.
d) If the work has interactive user interfaces, each must display Appropriate Legal Notices; however, if the Program has interactive interfaces that do not
display Appropriate Legal Notices, your work need not make them do so. A compilation of a covered work with other separate and independent works,
which are not by their nature extensions of the covered work, and which are not combined with it such as to form a larger program, in or on a volume of
a storage or distribution medium, is called an “aggregate” if the compilation and its resulting copyright are not used to limit the access or legal rights of
the compilation’s users beyond what the individual works permit. Inclusion of a covered work in an aggregate does not cause this License to apply to the
other parts of the aggregate.
6. Conveying Non-Source Forms.
You may convey a covered work in object code form under the terms of sections 4 and 5, provided that you also convey the machine-readable Corresponding
Source under the terms of this License, in one of these ways:
a) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied by the Corresponding Source
fixed on a durable physical medium customarily used for software interchange.
b) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied by a written offer, valid for at least
three years and valid for as long as you offer spare parts or customer support for that product model, to give anyone who possesses the object code
either (1) a copy of the Corresponding Source for all the software in the product that is covered by this License, on a durable physical medium customarily
used for software interchange, for a price no more than your reasonable cost of physically performing this conveying of source, or (2) access to copy the
Corresponding Source from a network server at no charge.
c) Convey individual copies of the object code with a copy of the written offer to provide the corresponding Source. This alternative is allowed only
occasionally and noncommercially, and only if you received the object code with such an offer, in accord with subsection 6b.
d) Convey the object code by offering access from a designated place (gratis or for a charge), and offer equivalent access to the Corresponding Source
in the same way through the same place at no further charge. You need not require recipients to copy the Corresponding Source along with the object
code. If the place to copy the object code is a network server, the Corresponding Source may be on a different server (operated by you or a third party)
that supports equivalent copying facilities, provided you maintain clear directions next to the object code saying where to find the Corresponding Source.
Regardless of what server hosts the Corresponding Source, you remain obligated to ensure that it is available for as long as needed to satisfy these
requirements.
e) Convey the object code using peer-to-peer transmission, provided you inform other peers where the object code and Corresponding Source of the
work are being offered to the general public at no charge under subsection 6d. A separable portion of the object code, whose source code is excluded
from the Corresponding Source as a System Library, need not be included in conveying the object code work. A “User Product” is either (1) a “consumer
product”, which means any tangible personal property which is normally used for personal, family, or household purposes, or (2) anything designed or
sold for incorporation into a dwelling. In determining whether a product is a consumer product, doubtful cases shall be resolved in favor of coverage. For
a particular product received by a particular user, “normally used” refers to a typical or common use of that class of product, regardless of the status of
the particular user or of the way in which the particular user actually uses, or expects or is expected to use, the product. A product is a consumer product
regardless of whether the product has substantial commercial, industrial or non-consumer uses, unless such uses represent the only significant mode of
use of the product.
“Installation Information” for a User Product means any methods, procedures, authorization keys, or other information required to install and execute modified
versions of a covered work in that User Product from a modified version of its Corresponding Source. The information must suffice to ensure that the continued
functioning of the modified object code is in no case prevented or interfered with solely because modification has been made. If you convey an object code
work under this section in, or with, or specifically for use in, a User Product, and the conveying occurs as part of a transaction in which the right of possession
and use of the User Product is transferred to the recipient in perpetuity or for a fixed term (regardless of how the transaction is characterized), the Corresponding
Source conveyed under this section must be accompanied by the Installation Information. But this requirement does not apply if neither you nor any third party
retains the ability to install modified object code on the User Product (for example, the work has been installed in ROM).
The requirement to provide Installation Information does not include a requirement to continue to provide support service, warranty, or updates for a work that
has been modified or installed by the recipient, or for the User Product in which it has been modified or installed. Access to a network may be denied when
the modification itself materially and adversely affects the operation of the network or violates the rules and protocols for communication across the network.
Corresponding Source conveyed, and Installation Information provided, in accord with this section must be in a format that is publicly documented (and with an
implementation available to the public in source code form), and must require no special password or key for unpacking, reading or copying.
7. Additional Terms.
“Additional permissions” are terms that supplement the terms of this License by making exceptions from one or more of its conditions. Additional permissions
that are applicable to the entire Program shall be treated as though they were included in this License, to the extent that they are valid under applicable law. If
additional permissions apply only to part of the Program, that part may be used separately under those permissions, but the entire Program remains governed
by this License without regard to the additional permissions. When you convey a copy of a covered work, you may at your option remove any additional
permissions from that copy, or from any part of it. (Additional permissions may be written to require their own removal in certain cases when you modify the
work.) You may place additional permissions on material, added by you to a covered work, for which you have or can give appropriate copyright permission.
Notwithstanding any other provision of this License, for material you add to a covered work, you may (if authorized by the copyright holders of that material)
supplement the terms of this License with terms:
a) Disclaiming warranty or limiting liability differently from the terms of sections 15 and 16 of this License; or
b) Requiring preservation of specified reasonable legal notices or author attributions in that material or in the Appropriate Legal Notices displayed by works
containing it; or
c) Prohibiting misrepresentation of the origin of that material, or requiring that modified versions of such material be marked in reasonable ways as different
from the original version; or
d) Limiting the use for publicity purposes of names of licensors or authors of the material; or
e) Declining to grant rights under trademark law for use of some trade names, trademarks, or service marks; or
f) Requiring indemnification of licensors and authors of that material by anyone who conveys the material (or modified versions of it) with contractual
assumptions of liability to the recipient, for any liability that these contractual assumptions directly impose on those licensors and authors. All other
non-permissive additional terms are considered “further restrictions” within the meaning of section 10. If the Program as you received it, or any part of it,
contains a notice stating that it is governed by this License along with a term that is a further restriction, you may remove that term. If a license document
contains a further restriction but permits relicensing or conveying under this License, you may add to a covered work material governed by the terms
of that license document, provided that the further restriction does not survive such relicensing or conveying. If you add terms to a covered work in
accord with this section, you must place, in the relevant source files, a statement of the additional terms that apply to those files, or a notice indicating
where to find the applicable terms. Additional terms, permissive or non-permissive, may be stated in the form of a separately written license, or stated as
exceptions; the above requirements apply either way.
8. Termination.
You may not propagate or modify a covered work except as expressly provided under this License. Any attempt otherwise to propagate or modify it is void, and
will automatically terminate your rights under this License (including any patent licenses granted under the third paragraph of section 11).
However, if you cease all violation of this License, then your license from a particular copyright holder is reinstated (a) provisionally, unless and until the copyright
holder explicitly and finally terminates your license, and (b) permanently, if the copyright holder fails to notify you of the violation by some reasonable means prior
to 60 days after the cessation. Moreover, your license from a particular copyright holder is reinstated permanently if the copyright holder notifies you ofthe violation
by some reasonable means, this is the first time you have received notice of violation of this License (for any work) from that copyright holder, and you cure the
violation prior to 30 days after your receipt of the notice. Termination of your rights under this section does not terminate the licenses of parties who have received
copies or rights from you under this License. If your rights have been terminated and not permanently reinstated, you do not qualify to receive new licenses for the
same material under section 10.
9. Acceptance Not Required for Having Copies.
You are not required to accept this License in order to receive or run a copy of the Program. Ancillary propagation of a covered work occurring solely as a
consequence of using peer-to-peer transmission to receive a copy likewise does not require acceptance. However, nothing other than this License grants you
permission to propagate or modify any covered work. These actions infringe copyright if you do not accept this License. Therefore, by modifying or propagating
a covered work, you indicate your acceptance of this License to do so.
10. Automatic Licensing of Downstream Recipients.
Each time you convey a covered work, the recipient automatically receives a license from the original licensors, to run, modify and propagate that work, subject
to this License. You are not responsible for enforcing compliance by third parties with this License. An “entity transaction” is a transaction transferring control
of an organization, or substantially all assets of one, or subdividing an organization, or merging organizations. If propagation of a covered work results from
an entity transaction, each party to that transaction who receives a copy of the work also receives whatever licenses to the work the party’s predecessor in
interest had or could give under the previous paragraph, plus a right to possession of the Corresponding Source of the work from the predecessor in interest, if
the predecessor has it or can get it with reasonable efforts. You may not impose any further restrictions on the exercise of the rights granted or affirmed under
this License. For example, you may not impose a license fee, royalty, or other charge for exercise of rights granted under this License, and you may not initiate
litigation (including a cross-claim or counterclaim in a lawsuit) alleging that any patent claim is infringed by making, using, selling, offering for sale, or importing
the Program or any portion of it.
11. Patents.
A “contributor” is a copyright holder who authorizes use under this License of the Program or a work on which the Program is based. The work thus licensed
is called the contributor’s “contributor version”. A contributor’s “essential patent claims” are all patent claims owned or controlled by the contributor, whether
already acquired or hereafter acquired, that would be infringed by some manner, permitted by this License, of making, using, or selling its contributor version,
but do not include claims that would be infringed only as a consequence of further modification of the contributor version. For purposes of this definition, “control”
includes the right to grant patent sublicenses in a manner consistent with the requirements of this License. Each contributor grants you a non-exclusive,
worldwide, royaltyfree patent license under the contributor’s essential patent claims, to make, use, sell, offer for sale, import and otherwise run, modify and
propagate the contents of its contributor version.
In the following three paragraphs, a “patent license” is any express agreement or commitment, however denominated, not to enforce a patent (such as an
express permission to practice a patent or covenant not to sue for patent infringement). To “grant” such a patent license to a party means to make such an
agreement or commitment not to enforce a patent against the party. If you convey a covered work, knowingly relying on a patent license, and the Corresponding
Source of the work is not available for anyone to copy, free of charge and under the terms of this License, through a publicly available network server or other
readily accessible means, then you must either (1) cause the Corresponding Source to be so available, or (2) arrange to deprive yourself of the benefit of the
patent license for this particular work, or (3) arrange, in a manner consistent with the requirements of this License, to extend the patent license to downstream
recipients. “Knowingly relying” means you have actual knowledge that, but for the patent license, your conveying the covered work in a country, or your
recipient’s use of the covered work in a country, would infringe one or more identifiable patents in that country that you have reason to believe are valid. If,
pursuant to or in connection with a single transaction or arrangement, you convey, or propagate by procuring conveyance of, a covered work, and grant a

patent license to some of the parties receiving the covered work authorizing them to use, propagate, modify or convey a specific copy of the covered work,
then the patent license you grant is automatically extended to all recipients of the covered work and works based on it. A patent license is “discriminatory” if it
does not include within the scope of its coverage, prohibits the exercise of, or is conditioned on the non-exercise of one or more of the rights that are specifically
granted under this License. You may not convey a covered work if you are a party to an arrangement with a third party that is in the business of distributing
software, under which you make payment to the third party based on the extent of your activity of conveying the work, and under which the third party grants,
to any of the parties who would receive the covered work from you, a discriminatory patent license
in connection with copies of the covered work conveyedby you (or copies made from those copies), or
(a)
(b) primarily for and in connection with specific products or compilations that contain the covered work, unless you entered into that arrangement, or that patent
license was granted, prior to 28 March 2007. Nothing in this License shall be construed as excluding or limiting any implied license or other defenses to
infringement that may otherwise be available to you under applicable patent law.
12. No Surrender of Others’ Freedom.
If conditions are imposed on you (whether by court order, agreement or otherwise) that contradict the conditions of this License, they do not excuse you from
the conditions of thisLicense. If you cannot convey a covered work so as to satisfy simultaneously your obligations under this License and any other pertinent
obligations, then as a consequence you may not convey it at all. For example, if you agree to terms that obligate you to collect a royalty for further conveying
from those to whom you convey the Program, the only way you could satisfy both those terms and this License would be to refrain entirely from conveying the
Program.
13. Use with the GNU Affero General Public License.
Notwithstanding any other provision of this License, you have permission to link or combine any covered work with a work licensed under version 3 of the GNU
Affero General Public License into a single combined work, and to convey the resulting work. The terms of this License will continue to apply to the part which is
the covered work, but the special requirements of the GNU Affero General Public License, section 13, concerning interaction through a network will apply to the
combination as such.
14. Revised Versions of this License.
The Free Software Foundation may publish revised and/ or new versions of the GNU General Public License from time to time. Such new versions will be similar
in spirit to the present version, but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Program specifies that a certain numbered version of the GNU General Public License “or any later
version” applies to it, you have the option of following the terms and conditions either of that numbered version or of any later version published by the Free
Software Foundation. If the Program does not specify a version number of the GNU General Public License, you may choose any version ever published by the
Free Software Foundation. If the Program specifies that a proxy can decide which future versions of the GNU General Public License can be used, that proxy’s
public statement of acceptance of a version permanently authorizes you to choose that version for the Program. Later license versions may give you additional
or different permissions. However, no additional obligations are imposed on any author or copyright holder as a result of your choosing to follow a later version.
15. Disclaimer of Warranty.
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING
THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM “AS IS” WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR
IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE
ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME
THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
16. Limitation of Liability.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO
MODIFIES AND/OR CONVEYS THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL,
INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO
LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO
OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
17. Interpretation of Sections 15 and 16.
If the disclaimer of warranty and limitation of liability provided above cannot be given local legal effect according to their terms, reviewing courts shall apply
local law that most closely approximates an absolute waiver of all civil liability in connection with the Program, unless a warranty or assumption of liability
accompanies a copy of the Program in return for a fee.
OpenSSL Combined License
The OpenSSL toolkit stays under a dual license, i.e. both the conditions of the OpenSSL License and the original SSLeay license apply to the toolkit.
See below for the actual license texts. Actually both licenses are BSD-style Open Source licenses. In case of any license issues related to OpenSSL please
contact openssl-core@openssl.org.
Component Name License URL
openssl-1.0.2e OpenSSL Combined License http://www.openssl.org/source
Copyright (c) 1998-2011 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or
other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following acknowledgment: "This product includes software developed
by the OpenSSL Projectfor use in the OpenSSL Toolkit. (http://www.openssl.org/)"
4. The names "OpenSSL Toolkit" and "OpenSSL Project" must not be used to endorse or promote products derived from this software without prior written
permission. For written permission, please contact openssl-core@openssl.org.
5. Products derived from this software may not be called "OpenSSL" nor may "OpenSSL" appear in their names without prior written permission of the
OpenSSL Project.
6. Redistributions of any form whatsoever must retain the following acknowledgment: "This product includes software developed by the OpenSSL Project for
use in the OpenSSL Toolkit (http://www.openssl.org/)"
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT ``AS IS'' AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED
TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE
OpenSSL PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR
BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING
NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young(eay@cryptsoft.com). This product includes software written by Tim Hudson (tjh@cryptsoft.com).
Original SSLeay License
Copyright (C) 1995-1998 Eric Young (eay@cryptsoft.com) All rights reserved.
This package is an SSL implementation written by Eric Young (eay@cryptsoft.com).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as the following conditions are aheared to. The following conditions apply to all code found
in this distribution, be it the RC4, RSA, lhash, DES, etc., code; not just the SSL code. The SSL documentation included with this distribution is covered by the
same copyright terms except that the holder is Tim Hudson (tjh@cryptsoft.com).
Copyright remains Eric Young's, and as such any Copyright notices in the code are not to be removed. If this package is used in a product, Eric Young should
be given attribution as the author of the parts of the library used. This can be in the form of a textual message at program startup or in documentation (online
or textual) provided with the package. Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following
conditions are met:
1. Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or
other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following acknowledgement: "This product includes cryptographic
software written by Eric Young (eay@cryptsoft.com)" The word 'cryptographic' can be left out if the rouines from the library being used are not cryptographic
related :-).
4. If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you must include an acknowledgement: "This
product includes software written by Tim Hudson (tjh@cryptsoft. com)"
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG ``AS IS'' AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR
CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT
LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The licence and distribution terms for any publically available version or derivative of this code cannot be changed. i.e. this code cannot simply be copied and
put under another distribution licence [including the GNU Public Licence.]
BSD License
Some software components of this product incorporate source code covered under the BSD license as follows.
Component Name License URL
net-snmp-5.7.3
pcre-8.38
libcap-1.7.4
lighttpd-1.4.35
MiniUPnP Project Client
pppd-2.4.7
lighttpd is a secure, fast, compliant, and very flexible webserver that has been optimized for high-performance environments. It has a very low memory footprint
compared to other webservers and takes care of cpuload. Its advanced feature-set (FastCGI, CGI, Auth, Output-Compression, URL-Rewriting and many more)
make lighttpd the perfect webserver-software for every server that suffers load problems. Simple Network Management Protocol (SNMP) is an Internetstandard
protocol for managing devices on IP networks. It is used mostly in network management systems to monitor the devices attached to the network for conditions
that need administrative attention. Net-SNMP is a suite of applications used to implement SNMP v1, SNMP v2c and SNMP v3 using both IPv4 and IPv6. For
more additional information, send email to help.cctv@hanwha.com.
Copyright (C) 2004, Kneschke, incremental
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met :
- Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or
other materials provided with the distribution.
- Neither the name of the ‘incremental’ nor the names of its contributors may be used to endorse or promote products derived from this software without
specific prior written permission.
BSD
BSD
BSD 2.0
BSD 2.0
BSD 2.0
BSD 2.0
http://www.net-snmp.org/about/license.html
http://www.kernel.org/pub/linux/libs/security/linux-privs/libcap2
http://www.opensource.org/licenses/bsd-license.html
http://opensource.org/licenses/BSD-3-Clause

THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR
PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE.
Copyright (c) 1998-2001 University College London
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, is permitted provided that the following conditions are met :
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or
other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following acknowledgement: This product includes software developed
by the Computer Science Department at University College London.
4. Neither the name of the University nor of the Department may be used to endorse or promote products derived from this software without specific prior
written permission.
THIS SOFTWARE IS PROVIDED BY THE AUTHORS AND CONTRIBUTORS ``AS IS’’ AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT
NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSEARE DISCLAIMED. IN NO EVENT
SHALL THE AUTHORS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR
BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING
NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Copyright (c) 1988, 1989, 1990, 1991, 1993, 1994, 1995, 1996 The Regents of the University of California.
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or
other materials provided with the distribution.
3. Neither the name of the Regents of the University of California nor the names of its contributors may be used to endorse or promote products derived from
this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR
PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE.
Copyright (c) 2006, Creative Labs Inc
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or
other materials provided with the distribution.
3. Neither the name of the Creative Labs nor the names of its contributors may be used to endorse or promote products derived from this software without
specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR
PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE.
Copyright (c) 2005-2012, Thomas BERNARD
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or
other materials provided with the distribution.
3. Neither the name of Thomas BERNARD nor the names of its contributors may be used to endorse or promote products derived from this software without
specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR
PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE.
Various copyrights apply to this package, listed in various separate parts below. Please make sure that you read all the parts.
Part 1: CMU/UCD copyright notice: (BSD like)
Copyright 1989, 1991, 1992 by Carnegie Mellon University Derivative Work - 1996, 1998-2000
Copyright 1996, 1998-2000 The Regents of the University of California
All Rights Reserved
Permission to use, copy, modify and distribute this software and its documentation for any purpose and without fee is hereby granted, provided that the above
copyright notice appears in all copies and that both that copyright notice and this permission notice appear in supporting documentation, and that the name
of CMU and The Regents of the University of California not be used in advertising or publicity pertaining to distribution of the software without specific written
permission.
CMU AND THE REGENTS OF THE UNIVERSITY OF CALIFORNIA DISCLAIM ALL WARRANTIES WITH REGARD TO THIS SOFTWARE, INCLUDING ALL
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS. IN NO EVENT SHALL CMU OR THE REGENTS OF THE UNIVERSITY OF CALIFORNIA BE
LIABLE FOR ANY SPECIAL, INDIRECT OR CONSEQUENTIAL DAMAGES OR ANY DAMAGES WHATSOEVER RESULTING FROM THE LOSS OF USE, DATA
OR PROFITS, WHETHER IN AN ACTION OF CONTRACT, NEGLIGENCE OR OTHER TORTIOUS ACTION, ARISING OUT OF OR IN CONNECTION WITH THE
USE OR PERFORMANCE OF THIS SOFTWARE.
Part 2 : Networks Associates Technology, Inc copyright notice (BSD)
Copyright (c) 2001-2003, Networks Associates Technology, Inc
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: yy Redistributions
of source code must retain the above copyright notice, this list of conditions and the following disclaimer. yy Redistributions in binary form must reproduce the
above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. yy Neither
the name of the Networks Associates Technology, Inc nor the names of its contributors may be used to endorse or promote products derived from this software
without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY,
OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA,
OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE.
Part 3: Cambridge Broadband Ltd. copyrightnotice (BSD)
Portions of this code are copyright (c) 2001-2003, Cambridge Broadband Ltd.
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: yy Redistributions
of source code must retain the above copyright notice, this list of conditions and the following disclaimer. yy Redistributions in binary form must reproduce the
above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. yy The
name of Cambridge Broadband Ltd. may not be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDER “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO,
THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT
HOLDER BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY
THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE
USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Part 4: Sun Microsystems, Inc. copyright notice
(BSD)
Copyright (c) 2003 Sun Microsystems, Inc., 4150 Network
Circle, Santa Clara, California 95054, U.S.A.
All rights reserved.
Use is subject to license terms below. This distribution may include materials developed by third parties. Sun, Sun Microsystems, the Sun logo and Solaris
are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. Redistribution and use in source and binary forms, with or
without modification, are permitted provided that the following conditions are met: yy Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer. yy Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution. yy Neither the name of the Sun Microsystems, Inc. nor the
names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY,
OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA,
OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE.
Part 5: Sparta, Inc copyright notice (BSD)
Copyright (c) 2003-2009, Sparta, Inc
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: yy Redistributions
of source code must retain the above copyright notice, this list of conditions and the following disclaimer. yy Redistributions in binary form must reproduce the
above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. yy Neither
the name of Sparta, Inc nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written
permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY,
OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA,
OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE.
Part 6: Cisco/BUPTNIC copyright notice (BSD)
Copyright (c) 2004, Cisco, Inc and Information Network
Center of Beijing University of Posts and Telecommunications.
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: yy Redistributions
of source code must retain the above copyright notice, this list of conditions and the following disclaimer. yy Redistributions in binary form must reproduce the
above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. yy Neither
the name of Cisco, Inc, Beijing University of Posts and Telecommunications, nor the names of their contributors may be used to endorse or promote products
derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY,
OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA,
OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE.
Part 7: Fabasoft R&D Software Software GmbH & Co KG copyright Notice (BSD)
Copyright (c) Fabasoft R&D Software GmbH & Co KG, 2003oss@fabasoft.com
Author: Bernhard Penz
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: yy Redistributions
of source code must retain the above copyright notice, this list of conditions and the following disclaimer. yy Redistributions in binary form must reproduce the
above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. yy The
name of Fabasoft R&D Software GmbH & Co KG or any of its subsidiaries, brand or product names may not be used to endorse or promote products derived
from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDER “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED
TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE
COPYRIGHT HOLDER BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING,
BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR
OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Part 8: Apple Inc. copyright notice (BSD)
Copyright (c) 2007 Apple Inc.
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or
other materials provided with the distribution. 3. Neither the name of Apple Inc. (“Apple”) nor the names of its contributors may be used to endorse or promote
products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY APPLE AND ITS CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT
LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL APPLE OR ITSCONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES
(INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING
NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Part 9: ScienceLogic, LLC copyright notice(BSD)
Copyright (c) 2009, ScienceLogic, LLC
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions aremet: yy Redistributions
of source code must retain the above copyright notice, this list of conditions and the following disclaimer. yy Redistributions in binary form must reproduce the
above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. yy Neither
the name of ScienceLogic, LLC nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior
written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY,
OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA,
OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE
The MIT License
Some software components of this product incorporate source code covered under the MIT license as follows
MIT License 2.0
- Acewidget, bettermeans, jquery-ui, libxml, libxml2, Mesa3D-MesaLib,mwEmbed,OpenGL Samples Pack, Wide Studio, xorg-server, dropbear-2012.55,
ncurses-5.7
Copyright (c) 2011, The Dojo Foundation
Copyright 2010, AUTHORS.txt (http://jqueryui.com/about)
Dual licensed under the MIT or GPL Version 2 licenses.
- http://jquery.org/license
- http://docs.jquery.com/UI/Widget
Copyright Daniel Veillard
Copyright Igor Zlatovic <igor@zlatkovic.com>
Copyright Aleksey Sanin
Copyright Gary Pennington <Gary.Pennington@uk.sun.com>
Copyright Alfred Mickautsch <alfred@mickautsch.de>
Copyright Bjorn Reese <bjorn.reese@systematic.dk>
Copyright Joel W. Reed
Copyright William Brack <wbrack@mmm.com.hk>
Copyright (c) 2007-2010 The Khronos Group Inc.
Copyright Atish Kumar Patra
Copyright (c) 2006 Free Software Foundation, Inc.
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the "Software"), to deal in the
Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software,
and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES
OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT
HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING
FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
Mozilla Public License
Since we, at Hanwha Techwin, used the Mozilla Firefox component without modifying the source code according to the MOZILLA Public license 1.1, we
are not obliged to provide the source code of the corresponding component.
• Version 1.1
1. Definitions.
1.0.1. "Commercial Use" means distribution or otherwise making the Covered Code available to a third party.
1.1. "Contributor" means each entity that creates or contributes to the creation of Modifications.
"Contributor Version" means the combination of the Original Code, prior Modifications used by a Contributor, and the Modifications made by that particular Contributor.
1.2.
1.3. "Covered Code" means the Original Code or Modifications or the combination of the Original Code and Modifications, in each case including portions thereof.
1.4. "Electronic Distribution Mechanism" means a mechanism generally accepted in the software development community for the electronic transfer of data.
1.5. "Executable" means Covered Code in any form other than Source Code.
1.6. "Initial Developer" means the individual or entity identified as the Initial Developer in the Source Code notice required by Exhibit A.
1.7. "Larger Work" means a work which combines Covered Code or portions thereof with code not governed by the terms of this License.
1.8. "License" means this document.
1.8.1. "Licensable" means having the right to grant, to the maximum extent possible, whether at the time of the initial grant or subsequently acquired, any and all of the
rights conveyed herein.
1.9. "Modifications" means any addition to or deletion from the substance or structure of either the Original Code or any previous Modifications. When Covered Code is
released as a series of files, a Modification is:
A. Any addition to or deletion from the contents of a file containing Original Code or previous Modifications.
B. Any new file that contains any part of the Original Code or previous Modifications.
1.10. "Original Code" means Source Code of computer software code which is described in the Source Code notice required by Exhibit A as Original Code, and which,
at the time of its release under this License is not already Covered Code governed by this License.
1.10.1. "Patent Claims" means any patent claim(s), now owned or hereafter acquired, including without limitation, method, process, and apparatus claims, in any patent
Licensable by grantor.

1.11. "Source Code" means the preferred form of the Covered Code for making modifications to it, including all modules it contains, plus any associated interface
definition files, scripts used to control compilation and installation of an Executable, or source code differential comparisons against either the Original Code or another
well known, available Covered Code of the Contributor’s choice. The Source Code can be in a compressed or archival form, provided the appropriate decompression or
de-archiving software is widely available for no charge.
1.12. "You’’ (or "Your") means an individual or a legal entity exercising rights under, and complying with all of the terms of, this License or a future version of this License
issued under Section 6.1. For legal entities, "You’’ includes any entity which controls, is controlled by, or is under common control with You. For purposes of this
definition, "control’’ means (a) the power, direct or indirect, to cause the direction or management of such entity, whether by contract or otherwise, or (b) ownership of
more than fifty percent (50%) of the outstanding shares or beneficial ownership of such entity.
2. Source Code License.
2.1. The Initial Developer Grant. The Initial Developer hereby grants You a world-wide, royalty-free, non-exclusive license, subject to third party intellectual property
claims:
(a) under intellectual property rights (other than patent or trademark) Licensable by Initial Developer to use, reproduce, modify, display, perform, sublicense and
distribute the Original Code (or portions thereof) with or without Modifications, and/or as part of a Larger Work; and
(b) under Patents Claims infringed by the making, using or selling of Original Code, to make, have made, use, practice, sell, and offer for sale, and/or otherwise
dispose of the Original Code (or portions thereof).
(c) the licenses granted in this Section 2.1(a) and (b) are effective on the date Initial Developer first distributes Original Code under the terms of this License.
(d) Notwithstanding Section 2.1(b) above, no patent license is granted: 1) for code that You delete from the Original Code; 2) separate from the Original Code; or
3) for infringements caused by: i) the modification of the Original Code or ii) the combination of the Original Code with other software or devices.
2.2. Contributor Grant. Subject to third party intellectual property claims, each Contributor hereby grants You a world-wide, royalty-free, non-exclusive license
(a) under intellectual property rights (other than patent or trademark) Licensable by Contributor, to use, reproduce, modify, display, perform, sublicense and
distribute the Modifications created by such Contributor (or portions thereof) either on an unmodified basis, with other Modifications, as Covered Code and/
or as part of a Larger Work; and
(b) under Patent Claims infringed by the making, using, or selling of Modifications made by that Contributor either alone and/or in combination with its
Contributor Version (or portions of such combination), to make, use, sell, offer for sale, have made, and/or otherwise dispose of: 1) Modifications made by
that Contributor (or portions thereof); and 2) the combination of Modifications made by that Contributor with its Contributor Version (or portions of such
combination).
(c) the licenses granted in Sections 2.2(a) and 2.2(b) are effective on the date Contributor first makes Commercial Use of the Covered Code.
(d) Notwithstanding Section 2.2(b) above, no patent license is granted: 1) for any code that Contributor has deleted from the Contributor Version; 2) separate from the
Contributor Version; 3) for infringements caused by: i) third party modifications of Contributor Version or ii) the combination of Modifications made by that Contributor
with other software (except as part of the Contributor Version) or other devices; or 4) under Patent Claims infringed by Covered Code in the absence of Modifications
made by that Contributor.
3. Distribution Obligations.
3.1. Application of License. The Modifications which You create or to which You contribute are governed by the terms of this License, including without limitation Section
2.2. The Source Code version of Covered Code may be distributed only under the terms of this License or a future version of this License released under Section 6.1,
and You must include a copy of this License with every copy of the Source Code You distribute. You may not offer or impose any terms on any Source Code version that
alters or restricts the applicable version of this License or the recipients’ rights hereunder. However, You may include an additional document offering the additional rights
described in Section 3.5.
3.2. Availability of Source Code. Any Modification which You create or to which You contribute must be made available in Source Code form under the terms of this
License either on the same media as an Executable version or via an accepted Electronic Distribution Mechanism to anyone to whom you made an Executable version
available; and if made available via Electronic Distribution Mechanism, must remain available for at least twelve (12) months after the date it initially became available, or
at least six (6) months after a subsequent version of that particular Modification has been made available to such recipients. You are responsible for ensuring that the
Source Code version remains available even if the Electronic Distribution Mechanism is maintained by a third party.
3.3. Description of Modifications. You must cause all Covered Code to which You contribute to contain a file documenting the changes You made to create that Covered
Code and the date of any change. You must include a prominent statement that the Modification is derived, directly or indirectly, from Original Code provided by the Initial
Developer and including the name of the Initial Developer in (a) the Source Code, and (b) in any notice in an Executable version or related documentation in which You
describe the origin or ownership of the Covered Code.
3.4. Intellectual Property Matters
(a) Third Party Claims. If Contributor has knowledge that a license under a third party’s intellectual property rights is required to exercise the rights granted by such
Contributor under Sections 2.1 or 2.2, Contributor must include a text file with the Source Code distribution titled "LEGAL’’ which describes the claim and the party
making the claim in sufficient detail that a recipient will know whom to contact. If Contributor obtains such knowledge after the Modification is made available as
described in Section 3.2, Contributor shall promptly modify the LEGAL file in all copies Contributor makes available thereafter and shall take other steps (such as
notifying appropriate mailing lists or newsgroups) reasonably calculated to inform those who received the Covered Code that new knowledge has been obtained.
(b) Contributor APIs. If Contributor’s Modifications include an application programming interface and Contributor has knowledge of patent licenses which are reasonably
necessary to implement that API, Contributor must also include this information in the LEGAL file.
(c) Representations.
Contributor represents that, except as disclosed pursuant to Section 3.4(a) above, Contributor believes that Contributor’s Modifications are Contributor’s original
creation(s) and/or Contributor has sufficient rights to grant the rights conveyed by this License.
3.5. Required Notices. You must duplicate the notice in Exhibit A in each file of the Source Code. If it is not possible to put such notice in a particular Source Code file
due to its structure, then You must include such notice in a location (such as a relevant directory) where a user would be likely to look for such a notice. If You created
one or more Modification(s) You may add your name as a Contributor to the notice described in Exhibit A. You must also duplicate this License in any documentation for
the Source Code where You describe recipients’ rights or ownership rights relating to Covered Code. You may choose to offer, and to charge a fee for, warranty, support,
indemnity or liability obligations to one or more recipients of Covered Code. However, You may do so only on Your own behalf, and not on behalf of the Initial Developer
or any Contributor. You must make it absolutely clear than any such warranty, support, indemnity or liability obligation is offered by You alone, and You hereby agree to
indemnify the Initial Developer and every Contributor for any liability incurred by the Initial Developer or such Contributor as a result of warranty, support, indemnity or
liability terms You offer.
3.6. Distribution of Executable Versions. You may distribute Covered Code in Executable form only if the requirements of Section 3.1-3.5 have been met for that Covered
Code, and if You include a notice stating that the Source Code version of the Covered Code is available under the terms of this License, including a description of how
and where You have fulfilled the obligations of Section 3.2. The notice must be conspicuously included in any notice in an Executable version, related documentation or
collateral in which You describe recipients’ rights relating to the Covered Code. You may distribute the Executable version of Covered Code or ownership rights under
a license of Your choice, which may contain terms different from this License, provided that You are in compliance with the terms of this License and that the license
for the Executable version does not attempt to limit or alter the recipient’s rights in the Source Code version from the rights set forth in this License. If You distribute
the Executable version under a different license You must make it absolutely clear that any terms which differ from this License are offered by You alone, not by the
Initial Developer or any Contributor. You hereby agree to indemnify the Initial Developer and every Contributor for any liability incurred by the Initial Developer or such
Contributor as a result of any such terms You offer.
3.7. Larger Works. You may create a Larger Work by combining Covered Code with other code not governed by the terms of this License and distribute the Larger Work
as a single product. In such a case, You must make sure the requirements of this License are fulfilled for the Covered Code.
4. Inability to Comply Due to Statute or Regulation.
If it is impossible for You to comply with any of the terms of this License with respect to some or all of the Covered Code due to statute, judicial order, or regulation then
You must: (a) comply with the terms of this License to the maximum extent possible; and (b) describe the limitations and the code they affect. Such description must
be included in the LEGAL file described in Section 3.4 and must be included with all distributions of the Source Code. Except to the extent prohibited by statute or
regulation, such description must be sufficiently detailed for a recipient of ordinary skill to be able to understand it.
5. Application of this License.
This License applies to code to which the Initial Developer has attached the notice in Exhibit A and to related Covered Code.
6. Versions of the License.
6.1. New Versions. Netscape Communications Corporation (‘’Netscape’’) may publish revised and/or new versions of the License from time to time. Each version will be
given a distinguishing version number.
6.2. Effect of New Versions. Once Covered Code has been published under a particular version of the License, You may always continue to use it under the terms of that
version. You may also choose to use such Covered Code under the terms of any subsequent version of the License published by Netscape. No one other than Netscape
has the right to modify the terms applicable to Covered Code created under this License.
6.3. Derivative Works. If You create or use a modified version of this License (which you may only do in order to apply it to code which is not already Covered Code
governed by this License), You must (a) rename Your license so that the phrases "Mozilla", "MOZILLAPL", "MOZPL", "Netscape", "MPL", "NPL" or any confusingly similar
phrase do not appear in your license (except to note that your license differs from this License) and (b) otherwise make it clear that Your version of the license contains
terms which differ from the Mozilla Public License and Netscape Public License. (Filling in the name of the Initial Developer, Original Code or Contributor in the notice
described in Exhibit A shall not of themselves be deemed to be modifications of this License.)
7. DISCLAIMER OF WARRANTY.
COVERED CODE IS PROVIDED UNDER THIS LICENSE ON AN "AS IS’’ BASIS, WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING,
WITHOUT LIMITATION, WARRANTIES THAT THE COVERED CODE IS FREE OF DEFECTS, MERCHANTABLE, FIT FOR A PARTICULAR PURPOSE OR NONINFRINGING. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE COVERED CODE IS WITH YOU. SHOULD ANY COVERED CODE PROVE
DEFECTIVE IN ANY RESPECT, YOU (NOT THE INITIAL DEVELOPER OR ANY OTHER CONTRIBUTOR) ASSUME THE COST OF ANY NECESSARY SERVICING,
REPAIR OR CORRECTION. THIS DISCLAIMER OF WARRANTY CONSTITUTES AN ESSENTIAL PART OF THIS LICENSE. NO USE OF ANY COVERED CODE IS
AUTHORIZED HEREUNDER EXCEPT UNDER THIS DISCLAIMER.
8. TERMINATION.
8.1. This License and the rights granted hereunder will terminate automatically if You fail to comply with terms herein and fail to cure such breach within 30 days of
becoming aware of the breach. All sublicenses to the Covered Code which are properly granted shall survive any termination of this License. Provisions which, by their
nature, must remain in effect beyond the termination of this License shall survive.
8.2. If You initiate litigation by asserting a patent infringement claim (excluding declatory judgment actions) against Initial Developer or a Contributor (the Initial Developer
or Contributor against whom You file such action is referred to as "Participant") alleging that:
(a) such Participant’s Contributor Version directly or indirectly infringes any patent, then any and all rights granted by such Participant to You under Sections 2.1 and/
or 2.2 of this License shall, upon 60 days notice from Participant terminate prospectively, unless if within 60 days after receipt of notice You either: (i) agree in writing
to pay Participant a mutually agreeable reasonable royalty for Your past and future use of Modifications made by such Participant, or (ii) withdraw Your litigation claim
with respect to the Contributor Version against such Participant. If within 60 days of notice, a reasonable royalty and payment arrangement are not mutually agreed
upon in writing by the parties or the litigation claim is not withdrawn, the rights granted by Participant to You under Sections 2.1 and/or 2.2 automatically terminate at
the expiration of the 60 day notice period specified above.
(b) any software, hardware, or device, other than such Participant’s Contributor Version, directly or indirectly infringes any patent, then any rights granted to You by such
Participant under Sections 2.1(b) and 2.2(b) are revoked effective as of the date You first made, used, sold, distributed, or had made, Modifications made by that
Participant.
8.3. If You assert a patent infringement claim against Participant alleging that such Participant’s Contributor Version directly or indirectly infringes any patent where
such claim is resolved (such as by license or settlement) prior to the initiation of patent infringement litigation, then the reasonable value of the licenses granted by such
Participant under Sections 2.1 or 2.2 shall be taken into account in determining the amount or value of any payment or license.
8.4. In the event of termination under Sections 8.1 or 8.2 above, all end user license agreements (excluding distributors and resellers) which have been validly granted by
You or any distributor hereunder prior to termination shall survive termination.
9. LIMITATION OF LIABILITY.
UNDER NO CIRCUMSTANCES AND UNDER NO LEGAL THEORY, WHETHER TORT (INCLUDING NEGLIGENCE), CONTRACT, OR OTHERWISE, SHALL YOU, THE
INITIAL DEVELOPER, ANY OTHER CONTRIBUTOR, OR ANY DISTRIBUTOR OF COVERED CODE, OR ANY SUPPLIER OF ANY OF SUCH PARTIES, BE LIABLE TO
ANY PERSON FOR ANY INDIRECT, SPECIAL, INCIDENTAL, OR CONSEQUENTIAL DAMAGES OF ANY CHARACTER INCLUDING, WITHOUT LIMITATION, DAMAGES
FOR LOSS OF GOODWILL, WORK STOPPAGE, COMPUTER FAILURE OR MALFUNCTION, OR ANY AND ALL OTHER COMMERCIAL DAMAGES OR LOSSES, EVEN
IF SUCH PARTY SHALL HAVE BEEN INFORMED OF THE POSSIBILITY OF SUCH DAMAGES. THIS LIMITATION OF LIABILITY SHALL NOT APPLY TO LIABILITY
FOR DEATH OR PERSONAL INJURY RESULTING FROM SUCH PARTY’S NEGLIGENCE TO THE EXTENT APPLICABLE LAW PROHIBITS SUCH LIMITATION. SOME
JURISDICTIONS DO NOT ALLOW THE EXCLUSION OR LIMITATION OF INCIDENTAL OR CONSEQUENTIAL DAMAGES, SO THIS EXCLUSION AND LIMITATION MAY
NOT APPLY TO YOU. 10. U.S. GOVERNMENT END USERS.
The Covered Code is a "commercial item," as that term is defined in 48 C.F.R. 2.101 (Oct. 1995), consisting of "commercial computer software" and "commercial
computer software documentation," as such terms are used in 48 C.F.R. 12.212 (Sept. 1995). Consistent with 48 C.F.R. 12.212 and 48 C.F.R. 227.7202-1 through
227.7202-4 (June 1995), all U.S. Government End Users acquire Covered Code with only those rights set forth herein.
11. MISCELLANEOUS.
This License represents the complete agreement concerning subject matter hereof. If any provision of this License is held to be unenforceable, such provision shall
be reformed only to the extent necessary to make it enforceable. This License shall be governed by California law provisions (except to the extent applicable law, if
any, provides otherwise), excluding its conflictof-law provisions. With respect to disputes in which at least one party is a citizen of, or an entity chartered or registered
to do business in the United States of America, any litigation relating to this License shall be subject to the jurisdiction of the Federal Courts of the Northern District of
California, with venue lying in Santa Clara County, California, with the losing party responsible for costs, including without limitation, court costs and reasonable attorneys’
fees and expenses. The application of the United Nations Convention on Contracts for the International Sale of Goods is expressly excluded. Any law or regulation which
provides that the language of a contract shall be construed against the drafter shall not apply to this License.
12. RESPONSIBILITY FOR CLAIMS.
As between Initial Developer and the Contributors, each party is responsible for claims and damages arising, directly or indirectly, out of its utilization of rights under
this License and You agree to work with Initial Developer and Contributors to distribute such responsibility on an equitable basis. Nothing herein is intended or shall be
deemed to constitute any admission of liability.
13. MULTIPLE-LICENSED CODE.
Initial Developer may designate portions of the Covered Code as Multiple-Licensed. Multiple-Licensedmeans that the Initial Developer permits you to utilize portions of
the Covered Code under Your choice of the MPL or the alternative licenses, if any, specified by the Initial Developer in the file described in Exhibit A.
EXHIBIT A -Mozilla Public License.
The contents of this file are subject to the Mozilla Public License Version 1.1 (the "License"); you may not use this file except in compliance with the License. You may
obtain a copy of the License at http://www.mozilla.org/MPL/Software distributed under the License is distributed on an "AS IS" basis, WITHOUT WARRANTY OF ANY
KIND, either express or implied. See the License for the specific language governing rights and limitations under the License.
The Original Code is ___________________________________.
The Initial Developer of the Original Code is ________________________. Portions created by ______________________ are Copyright (C) ______
_______________________. All Rights Reserved.
Contributor(s): ______________________________________.
Alternatively, the contents of this file may be used under the terms of the _____ license (the [___] License), in which case the provisions of [______] License are applicable
instead of those above. If you wish to allow use of your version of this file only under the terms of the [____] License and not to allow others to use your version of this file
under the MPL, indicate your decision by deleting the provisions above and replace them with the notice and other provisions required by the [___] License. If you do not
delete the provisions above, a recipient may use your version of this file under either the MPL or the [___] License."
[NOTE: The text of this Exhibit A may differ slightly from the text of the notices in the Source Code files of the Original Code. You should use the text of this Exhibit A
rather than the text found in the Original Code Source Code for Your Modifications
The Independent JPEG Group’s JPEG Software
The software included in this product contains copyrighted software that is licensed under the JPEG license.
• JPEG license
- Code project . Generating Outline OpenGL, Libjpeg
This distribution contains the sixth public release of the Independent JPEG Group’s free JPEG software. You are welcome to redistribute this software and to use it for
any purpose, subject to the conditions under LEGAL ISSUES, below.
Serious users of this software (particularly those incorporating it into larger programs) should contact IJG at jpeg-info@uunet.uu.net to be added to our electronic mailing
list. Mailing list members are notified of updates and have a chance to participate in technical discussions, etc.
This software is the work of Tom Lane, Philip Gladstone, Jim Boucher, Lee Crocker, Julian Minguillon, Luis Ortiz, George Phillips, Davide Rossi, Guido Vollbeding, Ge’
Weijers, and other members of the Independent JPEG Group.
IJG is not affiliated with the official ISO JPEG standards committee.
LEGAL ISSUES
============
In plain English:
We don’t promise that this software works. (But if you find any bugs, please let us know!)
1.
2. You can use this software for whatever you want. You don’t have to pay us.
3. You may not pretend that you wrote this software. If you use it in a program, you must acknowledge somewhere in your documentation that you’ve used the
IJG code.
In legalese:
The authors make NO WARRANTY or representation, either express or implied, with respect to this software, its quality, accuracy, merchantability, or fitness for
a particular purpose. This software is provided "AS IS", and you, its user, assume the entire risk as to its quality and accuracy.
This software is copyright (C) 1991-1998, Thomas G. Lane. All Rights Reserved except as specified below.
Permission is hereby granted to use, copy, modify, and distribute this software (or portions thereof) for any purpose, without fee, subject to these conditions:
(1) If any part of the source code for this software is distributed, then this README file must be included, with this copyright and no-warranty notice unaltered;
and any additions, deletions, or changes to the original files must be clearly indicated in accompanying documentation.
(2) If only executable code is distributed, then the accompanying documentation must state that "this software is based in part on the work of the Independent
JPEG Group".
(3) Permission for use of this software is granted only if the user accepts full responsibility for any undesirable consequences; the authors accept NO LIABILITY
for damages of any kind.
These conditions apply to any software derived from or based on the IJG code, not just to the unmodified library. If you use our work, you ought to acknowledge
us.
Permission is NOT granted for the use of any IJG author’s name or company name in advertising or publicity relating to this software or products derived from it.
This software may be referred to only as "the Independent JPEG Group’s software".
We specifically permit and encourage the use of this software as the basis of commercial products, provided that all warranty or liability claims are assumed by
the product vendor.
ansi2knr.c is included in this distribution by permission of L. Peter Deutsch, sole proprietor of its copyright holder, Aladdin Enterprises of Menlo Park, CA.
ansi2knr.c is NOT covered by the above copyright and conditions, but instead by the usual distribution terms of the Free Software Foundation; principally, that
you must include source code if you redistribute it. (See the file ansi2knr.c for full details.) However, since ansi2knr. c is not needed as part of any program
generated from the IJG code, this does not limit you more than the foregoing paragraphs do.
The Unix configuration script "configure" was produced with GNU Autoconf. It is copyright by the Free Software Foundation but is freely distributable. The same
holds for its supporting scripts (config.guess, config.sub, ltconfig, ltmain. sh). Another support script, install-sh, is copyright by M.I.T. but is also freely distributable.
It appears that the arithmetic coding option of the JPEG spec is covered by patents owned by IBM, AT&T, and Mitsubishi. Hence arithmetic coding cannot legally
be used without obtaining one or more licenses. For this reason, support for arithmetic coding has been removed from the free JPEG software. (Since arithmetic
coding provides only a marginal gain over the unpatented Huffman mode, it is unlikely that very many implementations will support it.) So far as we are aware,
there are no patent restrictions on the remaining code.
The IJG distribution formerly included code to read and write GIF files. To avoid entanglement with the Unisys LZW patent, GIF reading support has been removed
altogether, and the GIF writer has been simplified to produce "uncompressed GIFs". This technique does not use the LZW algorithm; the resulting GIF files are
larger than usual, but are readable by all standard GIF decoders.
We are required to state that
"The Graphics Interchange Format(c) is the Copyright property of CompuServe Incorporated. GIF(sm) is a Service Mark property of CompuServe Incorporated."
T-Kernel License
- This Product uses the Source Code of T-Kernel under T-License granted by the T-Engine Forum(www.t-engine.org)
T-License [License Agreement for Source Code of T-Kernel]
established by T-Engine Forum
on January 23, 2004
revised on June 17, 2004
revised on December 21, 2006
revised on March 24, 2009
Article 1. Scope of License Agreement
1. This License Agreement sets forth copyrights and the terms and conditions of use applicable to the source code of T-Kernel distributed by T-Engine Forum
and any derivative work created therefrom.
Article 2. Definition
1. "T-Kernel" means a real-time operating system controlled and distributed by T-Engine Forum on behalf of the copyright holder thereof.
2. "Source Code" means a source program, including related comments and documentations, for the T-Kernel and the Ported Source Code defined in Article 2.8
which is registered with T-Engine Forum.
3. "Hardware-dependent Part" means the part of the Source Code which depends on hardware and needs to be changed when the Source Code is ported and
operated on the target hardware, and is designated and separated as such part.
4. "Compiler-dependent Part" means the part of the Source Code which depends on compiler and needs to be changed when the Source Code is ported and
operated on the target hardware, and is designated and separated as such part.
5. "Header File" means the part of the Source Code which contains definitions necessary to develop application programs.
6. "T-Engine Hardware" means the hardware which is manufactured in accordance with the T-Engine Hardware specifications or the μT-Engine Hardware
specifications issued by T-Engine Forum, and registered with T-Engine Forum.
7. "Similar Hardware to T-Engine Hardware" means any hardware (including software which emulates hardware) other than that defined in Article 2.6 above, on
which the T-Kernel can be operated.
8. "Ported Source Code" means a source program produced from the Source Code by modifying only its Hardwaredependent Part and/or Compiler-dependent
Part to enable it to be operated on the T-Engine Hardware or the Similar Hardware to T-Engine Hardware. The Ported Source Code which is registered with
T-Engine Forum shall be included in the Source Code.
9. "Modified Source Code" means a source program modified from the Source Code for the purpose of improving its performance, increasing or decreasing its
function, and the like. The Ported Source Code shall not be included in the Modified Source Code.
10. "Binary Code" means an executable code form which is created by compiling programs, which include all or part of the Source Code or the Modified Source
Code.
11. "Derivative Work" means the Modified Source Code or the Binary Code.
12. "Embedded Product" means any product which operates with executable code form of the Source Code, the Modified Source Code or the Binary Code
loaded on its hardware.
13. "End User" means a consumer who uses the Embedded Product.
14. "System Developer" means any person who develops the Embedded Product by itself or has a third party develop the same, and provides, whether with or
without payment, the End User with the Embedded Product.
15. "Distributor of Modification" means any person who produces the Modified Source Code and, whether with or without payment, distributes the same to any
third party.

16. "Patch for Modification" means a difference, program, system, or the like in order to create the Modified Source Code from the Source Code or the Binary
Code thereof.
17. "Vicarious Execution of Patch Processing" means vicarious execution service to create the Modified Source Code applying the Patch for Modification to the
Source Code or the Binary Code thereof.
18. "Source Code User" means a person who uses the Source Code.
19. "Distribution" means any of the following acts:
1. to transmit a work to a large number of specific persons through the Internet communication, broadcasting, and the like;
2. to transmit a work to the general public through the Internet communication, broadcasting, and the like automatically in response to a request from the
public; and
3. to distribute a copy of a work to the general public or a large number of specific persons.
Article 3. Copyright
1. The copyrights of the Source Code shall be owned by Ken Sakamura.
Article 4. License of Source Code
1. As provided for in this Article, T-Engine Forum shall provide, and grant a license to use, the Source Code free of charge to any person who has taken the
necessary procedure for registration as prescribed by T-Engine Forum and agreed to the T-License.
2. The Source Code shall be distributed exclusively by T-Engine Forum. Any person who obtains the Source Code under Article 4.1 above shall not make any
re-Distribution of the Source Code.
3. In accordance with the license granted under Article 4.1 above, the Source Code User may perform the following acts:
1. to copy and/or modify the Source Code provided by T-Engine Forum hereunder for its own research, development and the like.
2. to run the Source Code provided by T-Engine Forum hereunder for its own research, development and the like.
3. to run the Source Code modified in accordance with the provision of Article 4.3 (1) above for its own research, development and the like.
4. to distribute the Binary Code created from the Source Code provided by T-Engine Forum hereunder or from the Source Code modified in accordance with
the provision of Article 4.3 (1) above.
4. In accordance with the license granted under Article 4.1 above, the System Developer may perform the following acts:
1. to perform any and all acts set forth in the Article 4.3 above.
2. to develop and manufacture the Embedded Product containing the Binary Code, and, whether with or without payment, provide the End User with the same
and make the Binary Code available to the End User on the Embedded Product.
5. The Source Code User and the System Developer shall be obligated to give a notice that the Source Code is used, in such a way as separately specified by
T-Engine Forum, when they use the Source Code or the Binary Code, or make the Binary Code available for the End User on the Embedded Product.
Article 5. Distribution of Modified Source Code
1. Any of A- members of T-Engine Forum may become the Distributor of Modification by obtaining the approval of T-Engine Forum through the registration
procedure as prescribed by the Forum provided that only the department of the A- member which has taken the registration procedure may distribute the
Modified Source Code in such a way as provided for in this Article as long as it holds the Amembership.
2. The Distributor of Modification may create the Modified Source Code based on the Source Code provided by T-Engine Forum and the Patch for Modification
to be applied to create such Modified Source Code from the Source Code.
3. The Distributor of Modification shall, prior to the distribution, inform T-Engine Forum of and register a name and description of the Modified Source Code in
such a way as specified by T-Engine Forum.
4. The Distributor of Modification shall determine the name of the Modified Source Code subject to the rules separately established by T-Engine Forum and
publish an appropriate notice as required by the rules on the Patch for Modification and the Modified Source Code.
5. The Distributor of Modification may distribute the Modified Source Code to a third party, whether with or without payment, provided that the Distributor of
Modification shall take the necessary measures to prohibit the third party from making the re-Distribution of the Modified Source Code.
6. Developer with the Patch for Modification. Provided, however, that the Distributor of Modification shall be obligated to confirm that the System Developer is
the Source Code User duly licensed under Article 4.1.
7. The Distributor of Modification may perform the Vicarious Execution of Patch Processing for the System Developer.
8. The System Developer shall not distribute the Modified Source Code in further modified form to any third party as a stand-alone software product.
9. The System Developer may, under the same obligation as imposed in Article 4.5, make the Embedded Product available for the End User through use of the
Patch for Modification distributed by the Distributor of Modification or the Derivative Works obtained through the Vicarious Execution of Patch Processing.
Article 6. Distribution and Registration of the Ported Source Code
1. The Source Code User and the System Developer may, whether with or without charge, distribute to any third party only the following parts of the Ported
Source Code on the T-Engine Hardware or the Similar Hardware to T-Engine Hardware:
1. The Hardware-dependent Part and/or Compiler-dependent Part; provided that the Source Code User and the System Developer shall inform T-Engine Forum
of, and T-Engine Forum may publish, a method for distributing said Part(s) to third parties.
2. The Header File; provided that the Header File shall be distributed together with the Binary Code of the Ported Source Code.
2. Any member of T-Engine Forum may request T-Engine Forum to register and distribute, as an original source code for T-Kernel, the Ported Source Code on
the T-Engine Hardware or the Similar Hardware to T-Engine Hardware.
3. Any member of T-Engine Forum who requests the distribution mentioned in the preceding paragraph shall accede to the following conditions:
1. The member shall confirm that the object hardware is the T-Engine Hardware or the Similar Hardware to T-Engine Hardware.
2. The member shall provide T-Engine Forum with a complete set of operational environment for the object hardware and T-Kernel free of charge when
requesting the distribution.
3. The member shall submit test results of the Ported Source Code to T-Engine Forum when requesting the distribution.
4. In the event that T-Engine Forum accepts the request mentioned in Article 6.2, T-Engine Forum shall register and distribute the Ported Source Code as the
Source Code for T-Kernel. Provided, however, that the Ported Source Code may be treated in the same way as the Modified Source Code until the time of
registration hereunder.
5. The provision set forth in Article 3 shall apply to the Ported Source Code registered in accordance with this Article.
Article 7. Use for Other Purpose
1. Any use of the Source Code, the Modified Source Code or the Ported Source Code other than those stipulated in Articles 4, 5 and 6 shall be subject to the
prior approval of T-Engine Forum.
Article 8. Limited Warranty
1. T-Engine Forum and the copyright holder of the Source Code warrant that the Source Code does not infringe third party’s copyrights. Provided, however, that
T-Engine Forum and the copyright holder of the Source Code make no warranty as to the Hardware-dependent Part and/or Compiler- dependent Part set forth
in Article 6.2 in the Ported Source Code by any third party.
2. Neither T-Engine Forum nor the copyright holder of the Source Code warrants that the Source Code will fit for any particular purpose of the Source Code
User.
3. Neither T-Engine Forum nor the copyright holder of the Source Code warrants that the Source Code does not infringe any third party’s industrial property
rights. In no event shall T-Engine Forum and the copyright holder of the Source Code be liable for any dispute which may arise between the Source Code User
and a third party in connection with the third party’s industrial property rights.
Article 9. Indemnity
1. Neither T-Engine Forum nor the copyright holder of the Source Code shall be liable for any damages (including, but not limited to, damages resulting from
loss of profit, business interruption, loss of business information or any other pecuniary damage) arising out of use or impossibility of use of the Source Code,
even if T-Engine Forum and the copyright holder have been informed of the possibility of such damages.
Article 10. Breach of Agreement
1. In case that T-Engine Forum considers that this License Agreement is breached or that the popularization of T-Kernel is obstructed, T-Engine Forum shall take
measures to correct such breach or such obstruction, take measures on the ground of copyright infringement, or take any other necessary measures against
the breaching person or the obstructing person, regardless of whether or not the said person is a member of T-Engine Forum.
2. In case of breach of this License Agreement by a member of T-Engine Forum, T-Engine Forum may take appropriate measures against the member; for
example, the member is disqualified from membership, depending on what kind of breach has been committed by it.
3. Any legal dispute which may arise in relation to any breach of this License Agreement shall be subject to the exclusive jurisdiction of the Tokyo District Court.
Article 11. Governing Law and Language
1. This License Agreement shall be governed by and interpreted under the laws of Japan.
2. This License Agreement is executed in both Japanese text and English text provided that the Japanese text shall govern the interpretation and performance
of this License Agreement.
Apache License 2.0
Component Name License URL
mDNSResponder_bonjour Apache License 2.0 http://www.apache.org/licenses/LICENSE-2.0
TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION
1. Definitions.
"License" shall mean the terms and conditions for use, reproduction, and distribution as defined by Sections 1 through 9 of this document.
"Licensor" shall mean the copyright owner or entity authorized by the copyright owner that is granting the License.
"Legal Entity" shall mean the union of the acting entity and all other entities that control, are controlled by, or are under common control with that entity. For the
purposes of this definition, "control" means (i) the power, direct or indirect, to cause the direction or management of such entity, whether by contract or otherwise, or (ii)
ownership of fifty percent (50%) or more of the outstanding shares, or (iii) beneficial ownership of such entity.
"You" (or "Your") shall mean an individual or Legal Entity exercising permissions granted by this License. "Source" form shall mean the preferred form for making
modifications, including but not limited to software source code, documentation source, and configuration files.
"Object" form shall mean any form resulting from mechanical transformation or translation of a Source form, including but not limited to compiled object code,
generated documentation, and conversions to other media types.
"Work" shall mean the work of authorship, whether in Source or Object form, made available under the License, as indicated by a copyright notice that is included in
or attached to the work (an example is provided in the Appendix below).
"Derivative Works" shall mean any work, whether in Source or Object form, that is based on (or derived from) the Work and for which the editorial revisions,
annotations, elaborations, or other modifications represent, as a whole, an original work of authorship. For the purposes of this License, Derivative Works shall not
include works that remain separable from, or merely link (or bind by name) to the interfaces of, the Work and Derivative Works thereof.
"Contribution" shall mean any work of authorship, including the original version of the Work and any modifications or additions to that Work or Derivative Works
thereof, that is intentionally submitted to Licensor for inclusion in the Work by the copyright owner or by an individual or Legal Entity authorized to submit on behalf
of the copyright owner. For the purposes of this definition, "submitted" means any form of electronic, verbal, or written communication sent to the Licensor or its
representatives, including but not limited to communication on electronic mailing lists, source code control systems, and issue tracking systems that are managed
by, or on behalf of, the Licensor for the purpose of discussing and improving the Work, but excluding communication that is conspicuously marked or otherwise
designated in writing by the copyright owner as "Not a Contribution." "Contributor" shall mean Licensor and any individual or Legal Entity on behalf of whom a
Contribution has been received by Licensor and subsequently incorporated within the Work.
2. Grant of Copyright License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-
charge, royalty-free, irrevocable copyright license to reproduce, prepare Derivative Works of, publicly display, publicly perform, sublicense, and distribute the Work and
such Derivative Works in Source or Object form.
3. Grant of Patent License. Subject to the terms and conditions of this License, each Contributor hereby grants to You a perpetual, worldwide, non-exclusive, no-charge,
royaltyfree, irrevocable (except as stated in this section) patent license to make, have made, use, offer to sell, sell, import, and otherwise transfer the Work, where
such license applies only to those patent claims licensable by such Contributor that are necessarily infringed by their Contribution(s) alone or by combination of their
Contribution(s) with the Work to which such Contribution(s) was submitted. If You institute patent litigation against any entity (including a crossclaim or counterclaim in
a lawsuit) alleging that the Work or a Contribution incorporated within the Work constitutes direct or contributory patent infringement, then any patent licenses granted
to You under this License for that Work shall terminate as of the date such litigation is filed.
4. Redistribution. You may reproduce and distribute copies of the Work or Derivative Works thereof in any medium, with or without modifications, and in Source or Object
form, provided that You meet the following conditions:
(a) You must give any other recipients of the Work or Derivative Works a copy of this License; and
(b) You must cause any modified files to carry prominent notices stating that You changed the files; and
(c) You must retain, in the Source form of any Derivative Works that You distribute, all copyright, patent, trademark, and attribution notices from the Source form of the
Work, excluding those notices that do not pertain to any part of the Derivative Works; and
(d) If the Work includes a "NOTICE" text file as part of its distribution, then any Derivative Works that You distribute must include a readable copy of the attribution
notices contained within such NOTICE file, excluding those notices that do not pertain to any part of the Derivative Works, in at least one of the following places:
within a NOTICE text file distributed as part of the Derivative Works; within the Source form or documentation, if provided along with the Derivative Works; or,
within a display generated by the Derivative Works, if and wherever such third-party notices normally appear. The contents of the NOTICE file are for informational
purposes only and do not modify the License. You may add Your own attribution notices within Derivative Works that You distribute, alongside or as an addendum
to the NOTICE text from the Work, provided that such additional attribution notices cannot be construed as modifying the License.
You may add Your own copyright statement to Your modifications and may provide additional or different license terms and conditions for use, reproduction, or
distribution of Your modifications, or for any such Derivative Works as a whole, provided Your use, reproduction, and distribution of the Work otherwise complies with the
conditions stated in this License.
5. Submission of Contributions. Unless You explicitly state otherwise, any Contribution intentionally submitted for inclusion in the Work by You to the Licensor shall be
under the terms and conditions of this License, without any additional terms or conditions. Notwithstanding the above, nothing herein shall supersede or modify the
terms of any separate license agreement you may have executed with Licensor regarding such Contributions.
6. Trademarks. This License does not grant permission to use the trade names, trademarks, service marks, or product names of the Licensor, except as required for
reasonable and customary use in describing the origin of the Work and reproducing the content of the NOTICE file.
7. Disclaimer of Warranty. Unless required by applicable law or agreed to in writing, Licensor provides the Work (and eachContributor provides its Contributions) on an
"AS IS" BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied, including, without limitation, any warranties or conditions of
TITLE, NONINFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A PARTICULAR PURPOSE. You are solely responsible for determining the appropriateness of
using or redistributing the Work and assume any risks associated with Your exercise of permissions under this License.
8. Limitation of Liability. In no event and under no legal theory, whether in tort (including negligence), contract, or otherwise, unless required by applicable law (such as
deliberate and grossly negligent acts) or agreed to in writing, shall any Contributor be liable to You for damages, including any direct, indirect, special, incidental, or
consequential damages of any character arising as a result of this License or out of the use or inability to use the Work (including but not limited to damages for loss
of goodwill, work stoppage, computer failure or malfunction, or any and all other commercial damages or losses), even if such Contributor has been advised of the
possibility of such damages.
9. Accepting Warranty or Additional Liability. While redistributing the Work or Derivative Works thereof, You may choose to offer, and charge a fee for, acceptance of
support, warranty, indemnity, or other liability obligations and/or rights consistent with this License. However, in accepting such obligations, You may act only on Your
own behalf and on Your sole responsibility, not on behalf of any other Contributor, and only if You agree to indemnify, defend, and hold each Contributor harmless for
any liability incurred by, or claims asserted against, such Contributor by reason of your accepting any such warranty or additional liability.
END OF TERMS AND CONDITIONS
APPENDIX: How to apply the Apache License to your work.
To apply the Apache License to your work, attach the following boilerplate notice, with the fields enclosed by brackets "[]" replaced with your own identifying information.
(Don't include the brackets!) The text should be enclosed in the appropriate comment syntax for the file format. We also recommend that a file or class name and
description of purpose be included on the same "printed page" as the copyright notice for easier identification within third-party archives.
Copyright [yyyy] [name of copyright owner]
Licensed under the Apache License, Version 2.0 (the "License"); you may not use this file except in compliance with the License. You may obtain a copy of the License
at http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software distributed under the License is distributed on an "AS IS" BASIS, WITHOUT WARRANTIES OR
CONDITIONS OF ANY KIND, either express or implied. See the License for the specific language governing permissions and limitations under the License.
BZip2 License
This program, "bzip2", the associated library "libbzip2", and all documentation, are copyright (C) 1996-2007 Julian R Seward. All rights reserved.
Component Name License URL
bzip2-1.0.6 Bzip2 http://www.bzip.org/
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
2. The origin of this software must not be misrepresented; you must not claim that you wrote the original software. If you use this software in a product, an
acknowledgment in the product documentation would be appreciated but is not required.
3. Altered source versions must be plainly marked as such, and must not be misrepresented as being the original software.
4. The name of the author may not be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE AUTHOR ``AS IS'' AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR
BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND
ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY
OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Julian Seward, jseward@bzip.org
bzip2/libbzip2 version 1.0.5 of 10 December 2007
University of Illinois / NCSA Open Source License
Copyright (c) 1999-2007, The Board of Trustees of the University of Illinois All Rights Reserved.
Component Name License
iperf-2.0.5 University of Illinois / NCSA Open Source
Iperf performance test
Mark Gates
Ajay Tirumala
Jim Ferguson
Jon Dugan
Feng Qin
Kevin Gibbs
John Estabrook
National Laboratory for Applied Network Research
National Center for Supercomputing Applications
University of Illinois at Urbana-Champaign
http://www.ncsa.uiuc.edu
Permission is hereby granted, free of charge, to any person obtaining a copy of this software (Iperf) and associated documentation files (the "Software"), to deal
in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the
Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimers.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimers in the documentation and/or other
materials provided with the distribution.
Neither the names of the University of Illinois, NCSA, nor the names of its contributors may be used to endorse or promote products derived from this Software
without specific prior written permission. THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING
BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL
THE CONTIBUTORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT,
TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.

PHP 3.01 License
The PHP License, version 3.01 Copyright (c) 1999 - 2010 The PHP Group. All rights reserved.
Component Name License URL
php-5.2.17 PHP 3.01 http://www.php.net/distributions
Redistribution and use in source and binary forms, with or without modification, is permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or
other materials provided with the distribution.
3. The name "PHP" must not be used to endorse or promote products derived from this software without prior written permission. For written permission,
please contact group@php.net.
4. Products derived from this software may not be called "PHP", nor may "PHP" appear in their name, without prior written permission from group@php.net.
You may indicate that your software works in conjunction with PHP by saying "Foo for PHP" instead of calling it "PHP Foo" or "phpfoo"
5. The PHP Group may publish revised and/or new versions of the license from time to time. Each version will be given a distinguishing version number. Once
covered code has been published under a particular version of the license, you may always continue to use it under the terms of that version. You may also
choose to use such covered code under the terms of any subsequent version of the license published by the PHP Group. No one other than the PHP Group
has the right to modify the terms applicable to covered code created under this License.
6. Redistributions of any form whatsoever must retain the following acknowledgment: "This product includes PHP software, freely available from <http://www.
php.net/software/>".
THIS SOFTWARE IS PROVIDED BY THE PHP DEVELOPMENT TEAM ``AS IS'' AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT
NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL THE PHP DEVELOPMENT TEAM OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR
PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR
TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY
OF SUCH DAMAGE.
This software consists of voluntary contributions made by many individuals on behalf of the PHP Group. The PHP Group can be contacted via Email at group@
php.net.
For more information on the PHP Group and the PHP project, please see <http://www.php.net>. PHP includes the Zend Engine, freely available at <http://www.
zend.com>.
zlib / libpng License
This software is provided 'as-is', without any express or implied warranty. In no event will the authors be held liable for any damages arising from the use of
this software.
Component Name License URL
zlib-1.2.8 zlib / libpng http://zlib.net/
Copyright (C) 1995-2010 Jean-loup Gailly and Mark Adler
Permission is granted to anyone to use this software for any purpose, including commercial applications, and to alter it and redistribute it freely, subject to the
following restrictions:
1. The origin of this software must not be misrepresented; you must not claim that you wrote the original software. If you use this software in a product, an
acknowledgment in the product documentation would be appreciated but is not required.
2. Altered source versions must be plainly marked as such, and must not be misrepresented as being the original software.
3. This notice may not be removed or altered from any source distribution.
Jean-loup Gailly Mark Adler
jloup@gzip.org madler@alumni.caltech.edu
The data format used by the zlib library is described by RFCs (Request for Comments) 1950 to 1952 in the files http://www.ietf.org/rfc/rfc1950.txt (zlib format),
rfc1951.txt (deflate format) and rfc1952.txt (gzip format).
Cet équipement a été testé et se conforme aux limites relatives à un appareil numérique de classe
A, conformément à la partie 15 des Réglementations FCC. Ces limites sont élaborées pour fournir
un degré raisonnable de protection contre les interférences dangereuses si l’équipement fonctionne
dans un environnement commercial.
Cet équipement génère, utilise et peut produire une énergie à radio fréquence, s’il n’est pas installé
et utilisé selon le manuel d’instruction, il peut causer des interférences nuisibles aux communications
radiophoniques.
Le fonctionnement de cet équipement au sein d’une zone résidentielle peut provoquer des
interférences dangereuses, dans ce cas l’utilisateur est sommé de corriger l’ interférence à ses
propres frais.
Hanwha Techwin se soucie de l’environnement à toutes les phases de fabrication du produit et s’engage à tout
mettre en oeuvre pour offrir à ses clients des produits plus respectueux de l’environnement.
La marque Eco représente l'engagement de Hanwha Techwin à créer des produits respectueux de l'environnement
et indique que le produit est conforme à la Directive RoHS de l’Union européenne.
Les bons gestes de mise au rebut de ce produit (Déchets d’équipements électriques et électroniques)
(Applicable dans les pays de l’Union Européenne et dans d’autres pays européens pratiquant le tri sélectif)
Ce symbole sur le produit, ses accessoires ou sa documentation indique que ni le produit, ni ses accessoires
électroniques usagés (chargeur, casque audio, câble USB, etc.) ne peuvent être jetés avec les autres déchets
ménagers. La mise au rebut incontrôlée des déchets présentant des risques environnementaux et de santé
publique, veuillez séparer vos produits et accessoires usagés des autres déchets. Vous favoriserez ainsi le
recyclage de la matière qui les compose dans le cadre d’un développement durable.
Les particuliers sont invités à contacter le magasin leur ayant vendu le produit ou à se renseigner auprès des
autorités locales pour connaître les procédures et les points de collecte de ces produits en vue de leur recyclage.
Les entreprises et professionnels sont invités à contacter leurs fournisseurs et à consulter les conditions de leur
contrat de vente. Ce produit et ses accessoires ne peuvent être jetés avec les autres déchets professionnels et
commerciaux.
Elimination des batteries de ce produit
(Applicable aux pays de l’Union européenne et aux autres pays européens dans lesquels des systèmes de collecte
sélective sont mis en place.)
Le symbole sur la batterie, le manuel ou l’emballage indique que les batteries de ce produit ne doivent pas être éliminées en fin de vie
avec les autres déchets ménagers. L’indication éventuelle des symboles chimiques Hg, Cd ou Pb signifie que la batterie contient des
quantités de mercure, de cadmium ou de plomb supérieures aux niveaux de référence stipulés dans la directive CE 2006/66. Si les
batteries ne sont pas correctement éliminées, ces substances peuvent porter préjudice à la santé humaine ou à l’environnement.
Afin de protéger les ressources naturelles et d’encourager la réutilisation du matériel, veillez à séparer les batteries des autres types de
déchets et à les recycler via votre système local de collecte gratuite des batteries.

 Loading...
Loading...