Page 1

© Copyright 2010 Fortinet Incorporated. All rights reserved.
Products mentioned in this document are trademarks or registered trademarks
of their respective holders.
Regulatory Compliance
FCC Class B Part 15 CSA/CUS
4 July 2010
Visit these links for more information and documentation for your Fortinet product.
• Technical Documentation - http://docs.fortinet.com
• Fortinet Knowledge Center - http://kb.fortinet.com
• Fortinet Technical Support - http://support.fortinet.com
• Training Services - http://campus.training.fortinet.com
Connecting
INTERNAL
DMZ
4
5
6
3
2
1
WAN 1 WAN 2POWER STATUS
HA ALARM
INTERNAL
DMZ
4
5
6
3
2
1
WAN 1 WAN 2POWER STATUS
HA ALARM
MODEM
(Not enabl ed
on th is mo del)
Power
LED
Statu s
LED
WAN
Inter faces
Inter nal
Inter face
DMZ
LED
CONSOLE
WAN 2 WAN 1
MODEM
DMZ
INTERNAL
12345
6
USBDC+12V
Power
Conne ction
RJ-45 Serial
Connection
USB
WAN2
WAN1
DMZ
Inter nal I nterf ace,
switc h con necto rs
1 to 6
Groun d
Cable Tie
Mount ing
Hole
CONSOLE
WAN 2 WAN 1
MODEM
DMZ
INTERNAL
Optio nal R S-232 ser ial c able conn ects to se rial port on m anagement comp uter
Strai ght-t hrough Et herne t
cable s con nect to I ntern et
Power cabl e connect s to power sup ply
Strai ght-t hrough
Ether net c ables con nect
to co mpute rs on int ernal network
Optio nal c onnection to
DMZ n etwor k
1 2 3 4 5
6
USB DC+12V
Cable Tie
FortiGate-30B
Tools and Documenation
Copyright 2009 Fo rtinet Inco rporated. All rights res erved.
Trademarks
QuickStart Guide
Welcome | Bienvenue | Willkommen | 歓迎 | Bienvenido | Benvenuto
INTERNAL
DMZ
4
5
6
3
2
1
WAN 1 WAN 2POWERSTATUS
HA ALARM
2 Moun ting Bracket s
Straig ht-through
Ethern et cable
AC Pow er Cable
RJ-45 to
DB-9 S erial Cable
Power Supply
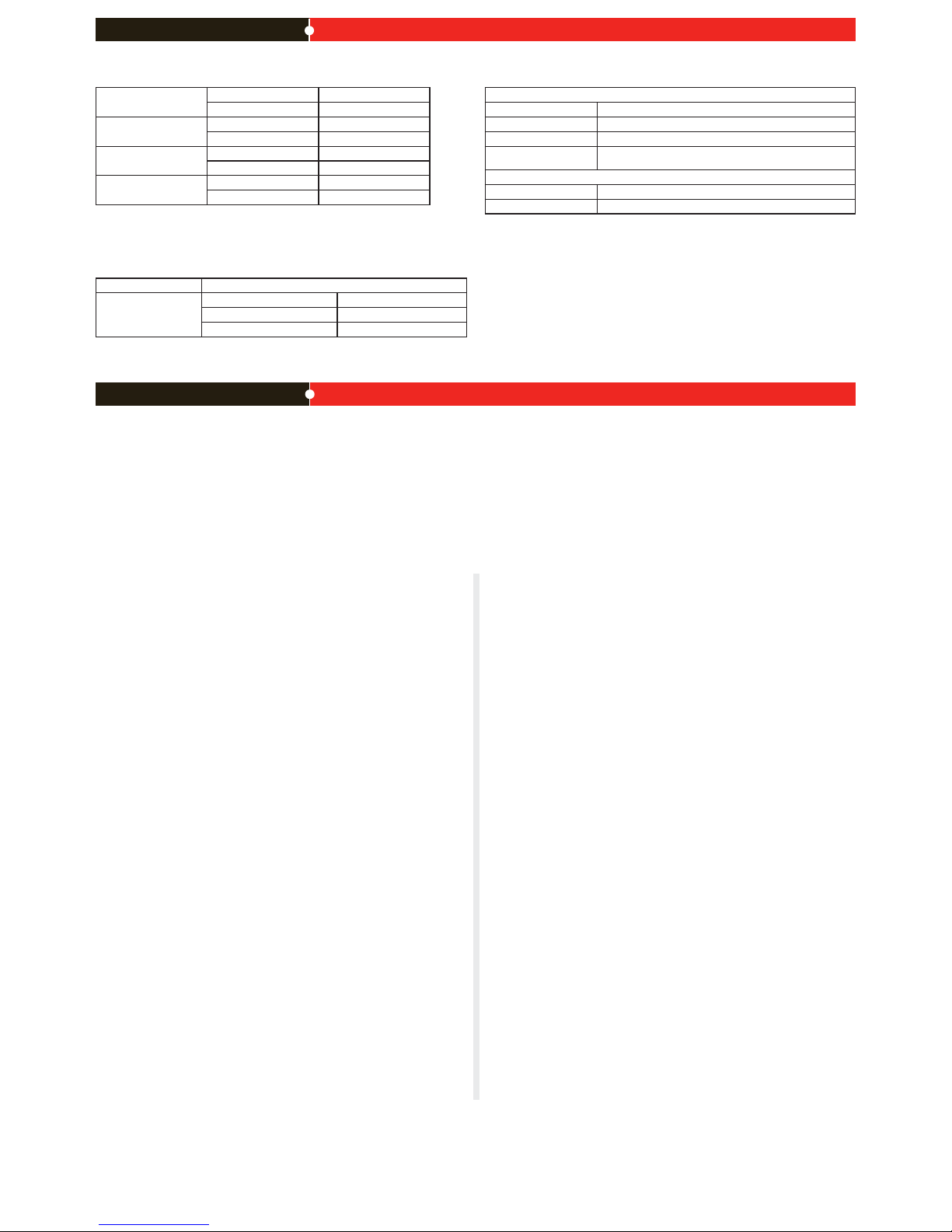
Interface Type Speed Protocol Description
Internal RJ-45 10/100 Base-T Ethernet A 6-port switch connection for up to six devices or the
internal network.
WAN1 and
WAN2
RJ-45 10/100/1000
Base-T
Ethernet Redundant connections to the Internet.
DMZ RJ-45 10/100 Base-T Ethernet Optional connection to a DMZ network or to other
FortiGate-80C units for high availability (HA).
Console RJ-45 9600 Bps
8/N/1
RS-232 Optional connection to the management computer. Pro-
vides access to the command line interface (CLI).
USB USB USB Two optional connections for the USB key, modem, or
backup operation.
Modem RJ-11 Not enabled for this model.
ExpressCard slot
ExpressCard/34,
ExpressCard/54
The Universal ExpressCard slot adds wireless communications.
Package Contents
FortiGate-80C
01-412-89805-20090615
QuickStart Guide
Web-based manager
The FortiGate web-based manager is an easy to use management tool.
Use it to congure the administrator password, the interface and default gateway addresses,
and the DNS server addresses.
Requirements:
• An Ethernet connection between the FortiGate unit and management computer.
• A web browser such as FireFox or Internet Explorer on the management computer.
Command Line Interface (CLI)
The CLI is a full-featured management tool. Use it to congure the administrator password,
the interface addresses, the default gateway address, and the DNS server addresses. To
congure advanced settings, see the Tools and Documentation CD included with the
FortiGate unit.
Requirements:
• The RJ-45 to DB9 serial connection between the FortiGate unit and management computer.
• A terminal emulation application (HyperTerminal for Windows) on the management
computer.
Conguration Tools
LED State Description
Power
Green The FortiGate unit is on.
Off The FortiGate unit is off.
Status
Green Flashing The FortiGate unit is starting up.
Green The FortiGate unit is running normally.
Red Modem is in use and connected.
Internal, DMZ,
WAN1, WAN2
Green The correct cable is in use and the connected
equipment has power.
Green Flashing Network activity at this interface.
Off No link established.
HA Green The FortiGate unit being used in an HA cluster.
Alarm
Red A critical error has occurred.
Amber A minor error has occurred.
Off No errors detected.
Before you begin
If using the wall-mount kit, remove the rubber feet before attaching the wall mount brackets.
Connect the following to the FortiGate unit. Ensure the FortiGate unit is placed on a stable
surface.
• Insert a network cable to WAN1. Insert the other end to the router connected to the
Internet, or to the modem.
• Connect a network cable to the Internal port 1, 2, and 3.
• Insert the other end to a computer or switch.
• Connect the AC Power Cable to the Power Supply.
• Connect the Power Cord to a surge protected power bar or power supply.
• Insert the pointed end of the cable tie into the hole in the rear panel of the chassis to
anchor the cable tie to the chassis.
• Loop the loose end around the adapter cable and insert the loose end into the locking
latch.
• Pull the loose end to adjust the tightness of the loop around the adapter cable to prevent cable from being accidentally pulled out the FortiGate unit.
Optional
Insert the ExpressCard (not supplied) into the ExpressCard 3G slot.
Page 2
NAT/Route Mode
Internal IP: ____.____.____.____
Netmask: ____.____.____.____
WAN1 IP: ____.____.____.____
Netmask: ____.____.____.____
WAN2 IP: ____.____.____.____
Netmask: ____.____.____.____
DMZ IP: ____.____.____.____
Netmask: ____.____.____.____
The internal interface IP address and netmask must be valid for the internal network.
General settings
Administrator password:
Network Settings: Default Gateway: ____.____.____.____
Primary DNS Server: ____.____.____.____
Secondary DNS Server: ____.____.____.____
A default gateway is required for the FortiGate unit to route connections to the Internet.
Factory default settings
NAT/Route mode
Internal interface 192.168.1.99
WAN1 interface 192.168.100.99
WAN2 interface 192.168.101.99
DHCP server on Internal
interface
192.168.1.110 – 192.168.1.210
Administrative account settings
User name admin
Password (none)
To reset the FortiGate unit to the factory defaults, in the CLI type the command
execute factoryreset
Collecting Information
Conguring
Refer to the Tools and Documentation CD for information on how to control trafc, and how to congure HA, antivirus protection, FortiGuard, Web content ltering, Spam ltering, intrusion
prevention (IPS), and virtual private networking (VPN).
NAT/Route mode
You would typically use NAT/Route mode when the FortiGate unit is deployed as a gateway between
private and public networks. In its default NAT/Route mode conguration, the unit functions as a rewall.
Firewall policies control communications through the FortiGate unit.
Transparent mode
You would typically use the FortiGate unit in Transparent mode on a private network behind an existing
rewall or behind a router. In its default Transparent mode conguration, the unit functions as a rewall.
Web-based Manager
1. Connect the FortiGate MGMT1 interface to a management computer Ethernet interface. Use a crossover Ethernet cable to connect the devices directly. Use straight-through Ethernet cables to connect
the devices through a hub or switch.
2. Congure the management computer to be on the same subnet as the MGMT1 interface of the
FortiGate unit. To do this, change the IP address of the management computer to 192.168.1.2 and
the netmask to 255.255.255.0.
3. To access the FortiGate web-based manager, start a web browser and type the address
http://192.168.1.99
4. Type admin in the Name eld and click Login.
NAT/Route mode
To change the administrator password
1. Go to System > Admin > Administrators.
2. Select Change Password for the admin administrator and enter a new password.
To congure interfaces
1. Go to System > Network > Interface.
2. Select the edit icon for each interface to congure.
3. Set the addressing mode for the interface. (See the online help for information.)
• For manual addressing, enter the IP address and netmask for the interface.
• For DHCP addressing, select DHCP and any required settings.
• For PPPoE addressing, select PPPoE, and enter the username and password and any other
required settings.
To congure the Primary and Secondary DNS server IP addresses
1. Go to System > Network > Options, enter the Primary and Secondary DNS IP addresses that you
recorded above and select Apply.
To congure a Default Gateway
1. Go to Router > Static and select Edit icon for the static route.
2. Set Gateway to the Default Gateway IP address you recorded above and select OK.
Transparent mode
To switch from NAT/route mode to transparent mode
1. Go to System > Cong > Operation Mode and select Transparent.
2. Set the Management IP/Netmask to 192.168.1.99/24.
3. Set a default Gateway and select Apply.
To change the administrator password
1. Go to System > Admin > Administrators.
2. Select Change Password for the admin administrator and enter a new password.
To change the management interface
1. Go to System > Cong > Operation Mode.
2. Enter the Management IP address and netmask that you recorded above and select Apply.
To congure the Primary and Secondary DNS server IP addresses
1. Go to System > Network > Options, enter the Primary and Secondary DNS IP addresses that you
recorded above and select Apply.
Command Line Interface
1. Use the RJ-45 to DB9 serial cable to connect the FortiGate Console port to the management computer serial port.
2. Start a terminal emulation program (HyperTerminal) on the management computer. Use these settings: Baud Rate (bps) 9600, Data bits 8, Parity None, Stop bits 1, and Flow Control None.
3. At the Login: prompt, type admin and press Enter twice (no password required).
NAT/Route mode
1. Congure the FortiGate MGMT1 interface.
cong system interface
edit MGMT1
set ip <intf_ip>/<netmask_ip>
end
2. Repeat to congure each interface, for example, to congure the Port 1 interface.
cong system interface
edit port1
...
3. Congure the primary and secondary DNS server IP addresses.
cong system dns
set primary <dns-server_ip>
set secondary <dns-server_ip>
end
4. Congure the default gateway.
cong router static
edit 1
set gateway <gateway_ip>
end
Transparent Mode
1. Change from NAT/Route mode to Transparent mode and congure the Management IP address.
cong system settings
set opmode transparent
set manageip <mng_ip>/<netmask>
set gateway <gateway_ip>
end
2. Congure the DNS server IP address.
cong system dns
set primary <dns-server_ip>
set secondary <dns-server_ip>
end
 Loading...
Loading...