Page 1

880022..1111gg W
Wiirreelleessss LLAANN
CCaarrddbbuuss AAddaapptteerr
User Manual
Version: 1.0
(April, 2005)
Page 2

COPYRIGHT
Copyright © 2005/2006 by this company. All rights reserved. No part of this
publication may be reproduced, transmitted, transcribed, stored in a retrieval
system, or translated into any language or computer language, in any form or
by any means, electronic, mechanical, magnetic, optical, chemical, manual or
otherwise, without the prior written permission of this company
This company makes no representations or warranties, either expr essed or
implied, with respect to the contents hereof and specifically disclaims any
warranties, merchantability or fitness for any partic ular purpose. Any software
described in this manual is sold or licensed "as is". Should the programs
prove defective following their purchase, the buyer (and not this company, its
distributor, or its dealer) assumes the entire cost of all necessary servicing,
repair, and any incidental or consequential damages resulting from any defect
in the software. Further, this company reserves the right to revise this
publication and to make changes from time to time in the contents hereof
without obligation to notify any person of such revision or changes.
All brand and product names mentioned in this manual are trademarks and/or registered
trademarks of their respective holders.
Page 3

Federal Communication Commission
Interference Statement
This equipment has been tested and found to comply with the limits for a
Class B digital device, pursuant to Part 15 of FCC Rules. These limits are
designed to provide reasonable protection against harmful interference in a
residential installation. This equipment generates, uses, and can radiate radio
frequency energy and, if not installed and used in accordance with the
instructions, may cause harmful interference to radio communications.
However, there is no guarantee that interference will not occur in a particular
installation. If this equipment does cause harmful interference to radio or
television reception, which can be determined by turning the equipment off
and on, the user is encouraged to try to correct the interference by one or
more of the following measures:
1. Reorient or relocate the receiving antenna.
2. Increase the separation between the equipment and receiver.
3. Connect the equipment into an outlet on a circuit different from that to which the
receiver is connected.
4. Consult the dealer or an experienced radio technician for help.
FCC Caution
This device and its antenna(s) must not be co-located or operating in conjunction
with any other antenna or transmitter.
This device complies with Part 15 of the FCC Rules. Operat ion is subject to
the following two conditions: (1) this device may not cause harmful
interference, and (2) this device must accept any interference received,
including interference that may cause undesired operation.
Any changes or modifications not expressly approved by the party responsible
for compliance could void the authority to operate equipment.
Federal Communication Commission (FCC) Radiation Exposure Statement
This EUT is compliance with SAR for general population /uncontrolled exposure
limits in ANSI/IEEE C95.1-1999 and had been tested in accordance with the
measurement methods and procedures specified in OET Bulletin 65 Supplement C.
This equipment complies with FCC radiation exposure limits set forth for an
uncontrolled environment. In order to avoid the possibility of exceeding the FCC
radio frequency exposure limits, human proximity to the antenna shall not be
less than 1.5 cm during normal operation.
Page 4
R&TTE Compliance Statement
This equipment complies with all the requirements of DIRECTIVE 1999/5/CE
OF THE EUROPEAN PARLIAMENT AND THE COUNCIL of March 9, 1999 on
radio equipment and telecommunication terminal Equipment and the mutual
recognition of their conformity (R&TTE)
The R&TTE Directive repeals and replaces in the directive 98/13/EEC
(Telecommunications Terminal Equipment and Satellite Earth Station
Equipment) As of April 8, 2000.
Safety
This equipment is designed with the utmost care for the safety of those who
install and use it. However, special atte ntion must be paid to the dangers of
electric shock and static electricity when working with electrical equipment. All
guidelines of this and of the computer manufacture must therefore be allowed
at all times to ensure the safe use of the equipment.
EU Countries Intended for Use
The ETSI version of this device is intended for home and office use in Austria,
Belgium, Denmark, Finland, France, Germany, Greece, Ireland, Italy,
Luxembourg, the Netherlands, Portugal, Spain, Sweden, and the United
Kingdom.
The ETSI version of this device is also authorized for use in EFTA member
states: Iceland, Liechtenstein, Norway, and Switzerland.
EU Countries Not intended for use
None.
Page 5

CONTENTS
1 INTRODUCTION...................................................................... 1
1.1 F
1.2 S
1.3 P
EATURES..........................................................................................1
PECIFICATIONS .................................................................................. 1
ACKAGE CONTENTS ...........................................................................2
2 INSTALLATION PROCEDURE................................................. 3
3 CONFIGURATION UTILITY ................................................... 10
3.1 W
3.2 P
3.3 D
3.4 S
OVERWRIT ING AN EXISTING STATIC WEP KEY .............................................. 21
D
ISABLING STATIC WEP ............................................................................ 22
IRELESS CONNECTI ON STATUS ......................................................... 10
ROFILE MANAGEM ENT ...................................................................... 10
IAGNOSTICS.................................................................................... 12
ECURITY......................................................................................... 13
3.4.1 WPA Setting................................................................................................. 14
3.4.2 Using WPA Passphrase Security ................................................................... 20
3.4.3 Pre-Shared Encryption Keys .......................................................................... 20
4 TROUBLESHOOTING............................................................ 23
Page 6

1 Introduction
Thank you for purchasing the 802.11g Wireless LAN Carbus Adapter. This Adapter is
designed to comply with IEEE 802.11g Wireless LAN standard and easy to carry with the
Mini size. It is suitable for any Laptop or Desktop computers.
This adapter supports 64/128/152-bit WEP data encryption that protects your wireless
network from eavesdropping. It also supports WPA (Wi-Fi Protected Access) feature that
combines IEEE 802.1x and TKIP (Temporal Key Integrity Protocol) technologies. Client
users are required to authorize before accessing to APs or AP Routers, and the data
transmitted in the network is encrypted/decrypted by a dynamically changed secret k ey.
It supports the SuperG mode feature to enhance the da ta rate to reach to 108Mbps, it can
enhance the data rate when it connect with Super G product.
This adapter is with the versatile features; it is the best solution for you to build your
wireless network.
1.1 Features
• Complies with the IEEE 802.11b and IEEE 802.11g 2.4GHz standards.
• Up to 54Mbps high data transfer rate. ( 108M : Super G mode enabled)
• Support 64/128/152-bit WEP, WPA, IEEE 802.1x high level of security.
• Complies with IEEE 802.11d country roaming standard.
• Support the most popular operating system: Windows 98SE/Me/2000/XP.
• Supports Standard 32bit Cardbus interface.
• Portable and Compact-size design.
• Suitable for Any Notebook.
1.2 Specifications
• Standard: IEEE 802.11g/b
• Bus Type: 32-bit Cardbus
• Frequency Band: 2.4000~2.4835GHz (Industrial Scientific Medical Band)
• Modulation: OFDM with BPSK, QPSK, 16QAM, 64QAM (11g)
BPSK, QPSK, CCK (11b)
• Data Rate: 54/48/36/24/18/12/11/9/6/5.5/2/1Mbps auto fallback (108Mbps: Super G enabled)
• Security: 64/128/152-bit WEP Data Encryption, WPA , IEEE 802.1x
• Antenna: Internal Antenna
• Drivers: Windows 98SE/Me/2000/XP/2003 Server
• LED: Link, Activity
• Transmit Power: 16 ~18 dBm (Typical)
1
Page 7

• Dimension: 8(H) x 118(W) x 54(D) mm
• Temperature: 32~131°F (0 ~55°C)
• Humidity: 0-95% (NonCondensing)
• Certification: FCC, CE
1.3 Package Contents
Before you begin the installation, please check the items of your package. The package
should include the following items:
• One PC Card
• One CD (Driver/Utility/User’s Manual.)
• One Quick Guide
If any of the above items is missing, contact your supplier as soon as possible.
2
Page 8
2 Installation Procedure
Before you proceed with the installation, please notice following descriptions.
Note1: The following installation was operated in Windows XP. (Procedures are similar for
Windows 98SE/Me/2000/2003 Server.)
Note2: If you have installed the Wireless PC Card driver & utility before, please uninstall the
old version first.
This chapter describes using the Atheros installer to install the Atheros wireless
network adapter driver.
Installation
To install the ACU and device driver:
1. Insert the device into the computer, and insert the installation CD.
2. Open the InstallShield Wizard (setup.exe).
3. The Atheros Client Installation installer opens. Click Next.
4. The Atheros license agreement window appears. Read and accept the
agreement to continue. Click Next.
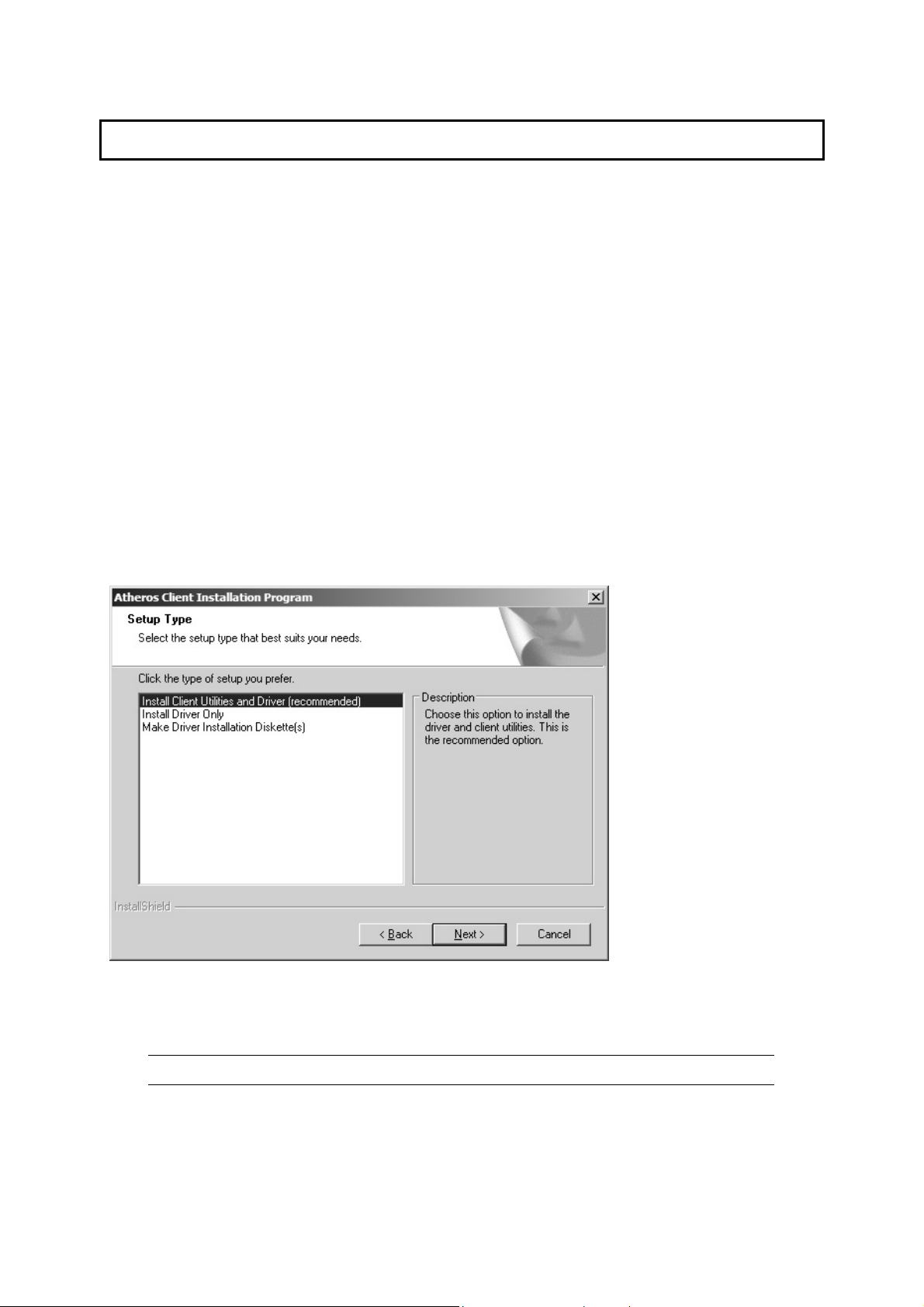
5. The Installation Program window appears with three setup options.
To install the client utilities and dr iver, select the appropriate installation type
(see Table (2-1) and click Next.
Table 2-1. Installer Installation Selections
Radio Button Description
Install Client
Utilities and
Driver
(recommended)
Installs the driver and client utilities. This is the recommends
option.
3
Page 9
Install Driver Only Installs only the driver without installing the client utilities.
Make Driver
Creates driver installation diskettes.
Installation
Diskette(s)
6. A prompt appears warning that the install requires the system to be rebooted
at the end of the installation process. Click Yes to continue.
7. Choose the setup directory. The default is C:\Program Files \ Atheros.
Click Next.
8. Choose the program folder for the start menu. The default is Atheros. Click
Next.
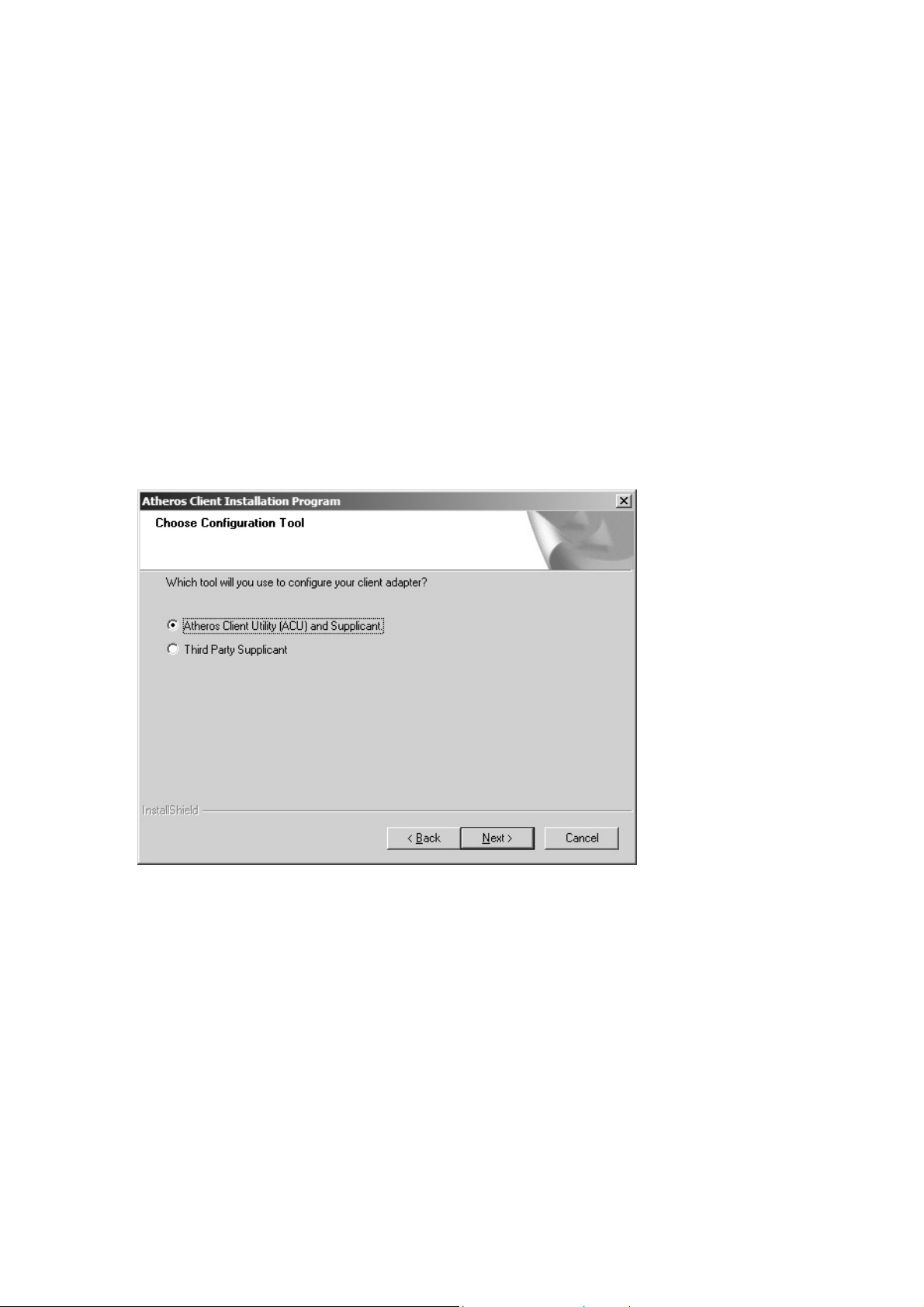
9. For a windows XP installation, the next screen defines the Windows Zero
Configuration. Windows XP Zero Configuration provides functionality to
automatically try to connect the station to available wireless networks. For
complete information on Windows Zero Configuration, see the Microsoft web
site.
10. In this installation, select the Atheros Client Utility and Supplicant.
Click Next. The installer automatically installs the driver.
11. Make sure that the USB device is inserted. If it i s not, insert it, then cancel
the found New Hardware Wizard if it appears. Proceed with the installation.
Click OK.
12. Windows may display a Windows Logo error for the USB bootloader. Click
Continue Anyway.
4
Page 10

The installer continues installation.
13. Windows may display a Windows Logo error for the WLAN driver. Click Click
Continue Anyway.
The installer continues installation.
14. Click OK at the prompt to reboot and complete the installation.
5
Page 11

Installing the Atheros Wireless Network
Adapter
To install the driver an d the Atheros Client Utility, see “To install the ACU and
device driver:” on page 2-1.
To install the Devic e Driver separate ly:
1. Insert the device into the computer: The Found New Hardware Wizard opens.
Choose advanced installation and click Next.
2. Choose Search for driver in these locat ions. The driver is located in the
NDIS5x directory.
3. Windows may display a Win dows Logo error for th e bootloader. C lick Continue
Anyway.
6
Page 12

The installer continues installation.
4. Click Finish to close the Found New Hardware Wizard and complete installation
of the USB device bootloader.
5. The Found New Hardware Wizard opens to install software for the device. Click
Next to continue.
6. Choose Search for driver in these locations. The driver is located in the
NDIS5x directory.
7. Windows may display a Windows Logo error for the WLAN dr iver. Click
Continue Anyway.
7
Page 13

The installer continues installation.
8. Click Finish to close the Found New Hardware Wizard and complete installation
of the Atheros Network Adapter.
Use the ACU to configure the device drive r. The ACU provides extens ive online
help to aid in configuring the device. Access the ACU by right-clicking the tray
icon and choosing Atheros Client Utility.
III. Using the Configuration Utility
To setup the adapter, double-click the icon in the system tray.
For Windows XP, there is a “Windows Zero Configuration Tool” by default for you to setup
wireless clients. If you want to use the Utility of the adapter, please follow one of the ways
as below.
8
Page 14

A. Double-click the icon.
B. Click “Advance”.
C. Uncheck “Use Windows to
configure my wireless
network settings”.
9
Page 15

3 Configuration Utility
The Client Utility is a user-mode utility designed to edit and add profiles for, as w ell as
display and diagnostics
3.1 Wireless Connection Status
When you open the Configuration Utility, the system will scan all the channels to find all the
access points/stations within the accessible range of your card and automatically connect to
the wireless device with the highest signal strength. From the screen, you may know all the
infomration about the wireless connection.
pertaining to a selected wireless adapter.
3.2 Profile Management
10
Page 16

Parameter Description
New To add a new configuration profile, click New on the Profile
Management tab. To modify a configuration profile, select the
configuration from the Profile list and click the Modify butto n.
Modify
In the Atheros Client Utility, access the General tab by clicking New or
Modify on the Profile Management tab.
Edit the fields in the General tab to configure the configuration
profile. Make sure to also edit the Security
and Advanced tabs.
Remove Select the profile to remove fr om the list of configuration profiles .
Import
1. From the Profile Management tab , click the Impo rt button.
The Import Profile window appears.
2.
Browse to the directory where the profile is located.
Highlight the profile name.
3.
4.
Click Open. The imported profile appears in the profiles
list.
Export
1. From the Profile Management tab, highligh t the profile to
export.
Click the Export button. The Export Profile window
2.
appears.
3.
Browse to the directory to export the profile to.
Click Save. The profile is exported to the specified
4.
11
Page 17

Order Profiles
location.
Including a profile in the auto selection feature allows the w ireless
adapter to automatically select that profile from the list of profiles
and use it to connect to the network.
3.3 Diagnostics
The client utility includes a number of tools to display current diagnostics and s tatus
information.
Parameter Description
Adapter Information The Adapter Information button contains general information
about the network interface card (the wireless network adapter)
and the network driver interface specification (NDIS) driver.
Advanced Statistics
The Diagnostics tab of the Atheros Client Utility provides buttons
used to retrieve receive and transmit statistics. The Diagnostics
tab does not require any configuration
12
Page 18

3.4 Security
This Chapter describes setting up security using the Atheros Client Utility(ACU).
While using the Atheros wireless network adapter, encryption data can protect its
as it is transmitted through the wireless network .
Radio Button Description
WPA
WPA
Passphrase
Enables the use of Wi-Fi Protected Access (WPA).
Choosing WPA opens the WPA EAP drop-down menu. The
options include:
• EAP-TLS
• EAP-TTLS
• PEAP (EAP-GTC)
• PEAP (EAP-MSCHAP V2)
• LEAP
Enables WPA Passphrase security.
Click on the Configure button and fill in the WPA Passphrase.
802.1x
Enables 802.1x security. This option requires IT administration.
Choosing 802.1x opens the 802.1x EAP type drop-down
menu. The options include:
• EAP-TLS
• EAP-TTLS
• PEAP (EAP-GTC)
13
Page 19

• PEAP (EAP-MSCHAP V2)
• LEAP
If the access point that the wireless adapter is associating to has
WEP set to Optional and the client has WEP enabled, make sure
that Allow Association to Mixed Cells is checked on the Security
Tab to allow association.
Pre-Shared
Key(Static
WEP)
Enables the use of pre-shared keys that are defined on both the
access point and the station.
To define pre-shared encryption keys, choose the Pre-Shared Key
radio button and click the Configure button to fill in the Define
Pre-Shared Keys window.
If the access point that the wireless adapter is associating to has
WEP set to Optional and the client has WEP enabled, make sure
that Allow Association to Mixed Cells is checked on the Security
Tab to allow association.
None
No security (not recommended).
3.4.1 WPA Setting
Using EAP-TLS Security
To use EAP-TLS security In the Atheros Client Utility, access the Security tab in the Profile
Management window.
14
Page 20

1. On the Security tab, cho ose the WPA radio button.
OR: On the Security tab, choose the 802.1x radio button.
2.
Choose EAP-TLS from the drop-down menu.
Enabling EAP-TLS security:
To use EAP-TLS security, the machine must already have the EAP-TLS certificates
downloaded onto it. Check with the IT manager.
If EAP-TLS is supported, choose EAP-TLS from the drop-down menu on the right,
1.
then click the Configure button.
Select the appropriate certificate authority from the list. The server/domain name
2.
and the login name are filled in automatically from the certificate in formation. Click
OK.
Click OK.
3.
4.
Activate the profile.
Using EAP-TTLS Security
To use EAP security In the Atheros Client Utility, access the Security tab in the Profile
Management window.
On the Security tab, choose the WPA radio bu tton.
1.
OR: On the Security tab, choose the 802.1x radio button.
Choose EAP-TTLS from the drop-down menu.
2.
Enabling EAP-TTLS security:
To use EAP-TTLS security, the machine must already have the EAP-TTLS certificates
downloaded onto it. Check with the IT manager.
15
Page 21

1. If EAP-TTLS is supported, choose EAP-T TLS from the drop-down menu on the right,
then click the Configure button.
2.
Select the appropriate certificate from the drop-down list and click OK.
Specify a user name for EAP authentication:
3.
o Check Use Windows User Name to use the Windows user name as the EAP
user name.
o OR: Enter a EAP user name in the User Name field to use a separate user
name and password and start the EAP authentication process.
4.
Click Advanced and:
o Leave the server name field blank for the client to accept a certifica te from
any server with a certificate signed by the authority listed in the Network
Certificate Authority drop-down list. (recommended)
o Enter the domain name of the server from which the client will accept a
certificate.
o Change the login name if needed.
Click OK.
5.
Enable the profile.
6.
Using PEAP-GTC Security
To use PEAP-GTC security In the Atheros Client Utility, access the Security tab in the
Profile Management window.
On the Security tab, choose the WPA radio bu tton.
1.
OR: On the Security tab, choose the 802.1x radio button.
Choose PEAP (EAP-GTC) from the drop-down menu.
2.
To use PEAP (EAP-GTC) security, the server must have WPA-PEAP certificates, and the
server properties must already be set. Check with the IT manager.
1. Click the Configure button.
16
Page 22

2. Select the appropriate network certi ficate authority from the drop-down list.
Specify a user name for inner PEAP tunnel authentication:
3.
o Check Use Windows User Name to use the Windows user name as the PEAP
user name.
o OR: Enter a PEAP user name in the User Name field to use a separate user
name and start the PEAP authentication process.
Choose Token or Static Password, depending on the user database.
4.
Note that Token uses a hardware token device or the Secure Computin g SofToken
program (version 1.3 or later) to obtain and enter a one-time password during
authentication.
5.
Click Advanced and:
o Leave the server name field blank for the client to accept a certifica te from
any server with a certificate signed by the authority listed in the Network
Certificate Authority drop-down list. (recommended)
o Enter the domain name of the server from which the client will accept a
certificate.
The login name used for PEAP tunnel authentication, fills in automatically as PEAPxxxxxxxxxxxx, where xxxxxxxxxxxx is the computer's MAC address. Change the
login name if needed.
Click OK.
6.
Enable the profile.
7.
Using PEAP-MSCHAP V2 Security
To use PEAP-MSCHAP V2 security In the Atheros Client Utility, access the Securit y tab in
the Profile Management window.
On the Security tab, choose the WPA radio bu tton.
1.
OR: On the Security tab, choose the 802.1x radio button.
2. Choose PEAP (EAP-MSCHAP V2) from the drop-down menu.
To use PEAP (EAP-MSCHAP V2) security, the server must have WPA-PEAP certificates,
and the server properties must already be set. Check with the IT manager.
17
Page 23

1.
Click the Configure button.
Select the appropriate certificate from the drop-down list.
2.
Specify a user name for inner PEAP tunnel authentication:
3.
o Check Use Windows User Name to use the Windows user name as the PEAP
user name.
o OR: Enter a PEAP user name in the User Name field to use a separate user
name and start the PEAP authentication process.
Click Advanced and:
4.
o Leave the server name field blank for the client to accept a certifica te from
any server with a certificate signed by the authority listed in the Network
Certificate Authority drop-down list. (recommended)
o Enter the domain name of the server from which the client will accept a
certificate.
o The login name used for PEAP tunnel authentication, fills in automatically as
PEAP-xxxxxxxxxxxx, where xxxxxxxxxxxx is the computer's MAC
address. Change the login name if needed.
Click OK.
5.
6.
Enable the profile.
Using LEAP Security
To use security In the Atheros Client Utility, access the Security tab in the Profile
Management window.
LEAP security requires that all infrastructure devices (e.g. access points and servers) are
configured for LEAP authentication. Check with the IT manager.
Configuring LEAP:
18
Page 24

• On the Security tab, choose the WPA radio button. Choose WPA-LEAP from the
drop-down menu.
• OR: On the Security tab, choose the 802.1x radio button. Choose LEAP from the
drop-down menu.
Click the Configure button.
1.
2. Specify a user name and password:
Select to Use Temporary User Name and Password by choosing the ra dio button:
o Check Use Windows User Name to use the Windows user name as the LEAP
user name.
o OR: Check Manually Prompt for LEAP User Name and Password to manually
login and start the LEAP authentication process.
Select to Use Saved User Name and Password by choosing the radio button:
o Specify the LEAP user name, password, and domain to save and use.
3.
Enter the user name and password.
Confirm the password.
4.
Specify a domain name:
5.
o Check the Include Windows Logon Domain with User Name setting to pass
the Windows login domain and user name to the RADIUS server. (default)
o OR: Enter a specific domain name.
6. If desired, check No Network Connection Unless User Is Logged In to force the
wireless adapter to disassociate after logging off.
Enter the LEAP authentication timeout time (between 30 an d 500 seconds) to specify
7.
how long LEAP should wait before declaring authentication failed, and sending an
error message. The default is 90 seconds.
19
Page 25

8. Click OK.
Enable the profile.
9.
3.4.2 Using WPA Passphrase Security
To use WPA Passphrase security In the Atheros Client Utility, access the Security tab in the
Profile Management window.
On the Security tab, choose the WPA Passphrase radio button.
1.
Click on the Configure button.
2.
Fill in the WPA Passphrase.
3.
4.
Click OK.
3.4.3 Pre-Shared Encryption Keys
Defining pre-shared encryption keys:
1. Click the Define Pre-Shared Keys radio bu tton on the Security tab.
2.
Click on Configure.
3. Fill in the fields in the Define Pre-Shared Keys dialog box:
20
Page 26

Key Button Description
Key Entry Determines the entry method for an encryption key:
hexadecimal (0-9, A-F), or ASCII text (all keyboard characters
except spaces).
Encryption Keys Selects the default encryption keys used. Only allows the
selection for a shared First, Second, Third, or Fourth key
whose corresponding field has been completed.
WEP Keys (1-4)
Defines a set of shared encryption keys for network
configuration security. At least one Shared Key field must be
populated to enable security using a shared key.
Click on the radio button to set the key as the default
encryption key.
WEP Key Size
Defines the size for each encryption key. The options include:
o 64- bit (enter 10 digits for hexadecimal, 5 ASCII
characters)
o 128- bit (enter 26 digits for hexadecimal, 13
digits for ASCII)
152-bit (enter 32 digits hexadecimal, 16 digits for ASCII)
4. Click OK for the changes to take effect.
Overwriting an Existing Static WEP Key
1. Click the Define Pre-Shared Keys radio bu tton on the Security tab.
Click on Configure.
2.
3. In the window, all existing static WEP keys are displayed as asterisks for security
reasons. Click in the field of the existing static WEP key to overwrite.
Delete the asterisks in that field.
4.
21
Page 27

5. Enter a new key.
Make sure to select the Transmit Key button to the left of this key is selected for the
6.
key to transmit packets.
Click OK.
7.
Disabling Static WEP
• To disable static WEP for a particular profile, choose None on the Profile
Management tab and click OK.
• OR: Select any other security option on the Profile Management tab to automatically
disable static WEP.
22
Page 28

4 Troubleshooting
This chapter provides solutions to problems usually encountered during the installation and
operation of the adapter.
1. What is the IEEE 802.11g standar d?
802.11g is the new IEEE standard for high-speed wireless LAN communications that
provides for up to 54 Mbps data rate in the 2.4 GHz band. 802.11g is quickly becoming
the next mainstream wireless LAN technology for the home, office and public ne tworks.
802.11g defines the use of the same OFDM modulation technique specified in IEEE
802.11a for the 5 GHz frequency band and applies it in the same 2.4 GH z frequency
band as IEEE 802.11b. The 802.11g standard requires backward compatibility with
802.11b.
The standard specifically calls for:
A. A new physical layer for the 802.11 Medium Access Control (MAC) in th e 2.4 GHz
frequency band, known as the extended rate PHY (ERP). Th e ERP adds OFDM as
a mandatory new coding scheme for 6, 12 and 24 Mbps (mandatory speeds), and
18, 36, 48 and 54 Mbps (optional speeds). The ERP includes the modulation
schemes found in 802.11b including CCK for 11 and 5.5 Mbps and Barker code
modulation for 2 and 1 Mbps.
B. A protection mechanism called RTS/ CTS that governs how 802.11g devices and
802.11b devices interoperate.
2. What is the IEEE 802.11b standar d?
The IEEE 802.11b Wireless LAN standard subcommittee, which formulates the
standard for the industry. The objective is to enable wireless LAN hardware from
different manufactures to communicate.
3. What does IEEE 802.11 feature support?
The product supports the following IEEE 802.11 functions:
CSMA/CA plus Acknowledge Protocol
Multi-Channel Roaming
Automatic Rate Selection
RTS/CTS Feature
Fragmentation
Power Management
4. What is Ad-hoc?
An Ad-hoc integrated wireless LAN is a group of computers, each has a Wireless LAN
adapter, Connected as an independent wireless LAN. Ad hoc wireless LAN is
applicable at a departmental scale for a branch or SOHO operation.
23
Page 29

5. What is Infrastructure?
An integrated wireless and wireless and wired LAN is called an Infrastructure
configuration. Infrastructure is applicable to enterprise scale for wireless access to
central database, or wireless application for mobile workers.
6. What is BSS ID?
A specific Ad hoc LAN is called a Basic Service Set (BSS). Computers in a BSS must
be configured with the same BSS ID.
7. What is WEP?
WEP is Wired Equivalent Privacy, a data privacy mechanism based on a 40 bit shared
key algorithm, as described in the IEEE 802 .11 standard.
8. What is TKIP?
TKIP is a quick-fix method to quickly overcome the inherent weaknesses in WEP
security, especially the reuse of encryption keys. TKIP is involved in the IEEE 802.11i
WLAN security standard, and the specification might be officially released by early
2003.
9. What is AES?
AES (Advanced Encryption Standard), a chip-based security, has been developed to
ensure the highest degree of security and authenticity for digital information , wherever
and however communicated or stored, while making more efficient use of hardware
and/or software than previous encryption standards. It is also included in IEEE 802.11i
standard. Compare with AES, TKIP is a temporary protocol for replacing WEP security
until manufacturers implement AES at the hardware level.
10. Can Wireless products support printer sharing?
Wireless products perform the same function as LAN products. Therefore, Wireless
products can work with Netware, Windows 2000, or other LAN operating systems to
support printer or file sharing.
11. Would the information be intercepted while transmitting on air?
WLAN features two-fold protection in security. On the hardware side, as with Direct
Sequence Spread Spectrum technology, it has the inherent security feature of
scrambling. On the software side, WLAN series offer the encryption function (WEP) to
enhance security and Access Control. Users can set it up depending upon their needs.
24
Page 30

12. What is DSSS?What is FHSS?And w hat are their differences?
Frequency-hopping spread-spectrum (FHSS) uses a narrowband carrier that changes
frequency in a pattern that is known to both transmitter and receiver. Properly
synchronized, the net effect is to maintain a single logical ch annel. To an unintended
receiver, FHSS appears to be short-duration impulse noise. Direct-sequence spreadspectrum (DSSS) generates a redundant bit pattern for eac h bit to be transmitted . This
bit pattern is called a chip (or chipping code). The longer the chip is, the greater the
probability that the original data can be recovered. Even if one or more bits in the chip
are damaged during transmission, statistical techniques embedded in the radio can
recover the original data without-the need for retransmission. To an unintended
receiver, DSSS appears as low power wideband noise and is rejected (ignored) by
most narrowband receivers.
13. What is Spread Spectrum?
Spread Spectrum technology is a wideband radio frequency technique developed by
the military for use in reliable, secure, mission-critical communication systems. It is
designed to trade off bandwidth efficiency for reliability, integrity, and security. In other
words, more bandwidth is consumed than in the case of narrowband transmission, but
the trade off produces a signal that is, in effect, louder and thus easier to detect,
provided that the receiver knows the parameters of the spread-spectrum signal being
broadcast. If a receiver is not tuned to the right frequency, a spread –spectrum signal
looks like background noise. There are two main alternatives, Direct Sequence Spread
Spectrum (DSSS) and Frequency Hopping Spread Spectrum (FHSS).
25
 Loading...
Loading...