Page 1

AVG 9 Internet Security
User Manual
Document rev ision 90.31 (15. 11. 2010)
Copyright AVG Technologies CZ, s.r.o. All rights reserved.
All other trademarks are the property of their respective owners.
This product uses RSA Data Security, Inc. MD5 Message-Digest Algorithm, Copyright (C) 1991-2, RSA Data
Security, Inc. C reated 1991.
This product uses code from C -SaCzech library, C opyright (c) 1996-2001 Jaromir Dolecek
(dolecek@ics.muni.cz).
This product uses compression library zlib, Copyright (c) 1995-2002 Jean-loup Gailly and Mark Adler.
This product uses compression library libbzip2, C opyright (c) 1996-2002 Julian R. Seward.
A V G 9 Internet Security © 2 010 C opyright AVG T ec hnologies CZ, s.r.o. A ll rights res erved. 1
Page 2

Contents
........................................................................................................................ 8
1. Introduction
........................................................................................................................ 9
2. AVG Installation Requirements
2.1 Operation Systems Supported
2.2 Minimum & Recommended HW Requirements
........................................................................................................................ 10
3. AVG Installation Options
........................................................................................................................ 11
4. AVG Download Manager
4.1 Language Selection
4.2 Connectivity Check
4.3 Proxy Settings
4.4 Downloading Installation Files
........................................................................................................................ 15
5. AVG Installation Process
5.1 Installation Launch
5.2 License Agreement
5.3 Checking System Status
5.4 Select Installation Type
5.5 Activate your AVG License
5.6 Custom Installation - Destination Folder
5.7 Custom Installation - Component Selection
5.8 AVG DataCenter
5.9 AVG Security Toolbar
5.10 Close down open applications
5.11 Installing AVG
5.12 Schedule regular scans and updates
5.13 Computer usage selection
5.14 Your computer Internet connection
5.15 AVG protection configuration is complete
.......................................................................................................... 9
.......................................................................................................... 9
.......................................................................................................... 11
.......................................................................................................... 12
.......................................................................................................... 13
.......................................................................................................... 14
.......................................................................................................... 15
.......................................................................................................... 16
.......................................................................................................... 16
.......................................................................................................... 17
.......................................................................................................... 17
.......................................................................................................... 18
.......................................................................................................... 19
.......................................................................................................... 20
.......................................................................................................... 21
.......................................................................................................... 21
.......................................................................................................... 22
.......................................................................................................... 23
.......................................................................................................... 23
.......................................................................................................... 24
.......................................................................................................... 25
........................................................................................................................ 26
6. After Installation
6.1 Scan optimization
6.2 Product Registration
6.3 Access to User Interfac e
6.4 Scanning of the whole computer
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 2
.......................................................................................................... 26
.......................................................................................................... 26
.......................................................................................................... 26
.......................................................................................................... 27
Page 3

6.5 Eicar Test
6.6 AVG Default Configuration
........................................................................................................................ 29
7. AVG User Interface
.......................................................................................................... 27
.......................................................................................................... 28
7.1 System Menu
7.1.1 File
7.1.2 Components
7.1.3 History
7.1.4 Tools
7.1.5 Help
7.2 Security Status Info
7.3 Quick Links
7.4 Components Overview
7.5 Statistics
7.6 System Tray Icon
........................................................................................................................ 38
8. AVG Components
8.1 Anti-Virus
8.1.1 Anti-Virus Principles
8.1.2 Anti-Virus Interface
8.2 Anti-Spyware
8.2.1 Anti-Spyware Principles
8.2.2 Anti-Spyware Interface
8.3 Anti-Spam
8.3.1 Anti-Spam Principles
8.3.2 Anti-Spam Interface
8.4 Anti-Rootkit
8.4.1 Anti-Rootkit Principles
8.4.2 Anti-Rootkit Interface
8.5 Remote Administration
8.6 System Tools
8.6.1 Processes
8.6.2 Network Connections
8.6.3 Autostart
8.6.4 Browser Extensions
8.6.5 LSP Viewer
8.7 Firewall
8.7.1 Firewall Principles
.......................................................................................................... 30
.......................................................................................................... 30
.......................................................................................................... 30
.......................................................................................................... 30
.......................................................................................................... 30
.......................................................................................................... 30
.......................................................................................................... 32
.......................................................................................................... 34
.......................................................................................................... 34
.......................................................................................................... 36
.......................................................................................................... 36
.......................................................................................................... 38
.......................................................................................................... 38
.......................................................................................................... 38
.......................................................................................................... 39
.......................................................................................................... 39
.......................................................................................................... 39
.......................................................................................................... 41
.......................................................................................................... 41
.......................................................................................................... 41
.......................................................................................................... 42
.......................................................................................................... 42
.......................................................................................................... 42
.......................................................................................................... 44
.......................................................................................................... 45
.......................................................................................................... 45
.......................................................................................................... 45
.......................................................................................................... 45
.......................................................................................................... 45
.......................................................................................................... 45
.......................................................................................................... 50
.......................................................................................................... 50
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 3
Page 4

8.7.2 Firewall Profiles
8.7.3 Firewall Interface
8.8 E-mail Scanner
8.8.1 E-mail Scanner Principles
8.8.2 E-mail Scanner Interface
8.8.3 E-mail Scanner Detection
8.9 ID Protection
8.9.1 ID Protection Principles
8.9.2 ID Protection Interface
8.10 License
8.11 Link Scanner
8.11.1 Link Sc anner Principles
8.11.2 Link Sc anner Interface
8.11.3 AVG Search-Shield
8.11.4 AVG Active Surf-Shield
8.12 Online Shield
8.12.1 Online Shield Principles
8.12.2 Online Shield Interface
8.12.3 Online Shield Detection
8.13 Resident Shield
8.13.1 Resident Shield Principles
8.13.2 Resident Shield Interface
8.13.3 Resident Shield Detec tion
8.14 Update Manager
8.14.1 Update Manager Principles
8.14.2 Update Manager Interfac e
.......................................................................................................... 50
.......................................................................................................... 50
.......................................................................................................... 55
.......................................................................................................... 55
.......................................................................................................... 55
.......................................................................................................... 55
.......................................................................................................... 59
.......................................................................................................... 59
.......................................................................................................... 59
.......................................................................................................... 61
.......................................................................................................... 62
.......................................................................................................... 62
.......................................................................................................... 62
.......................................................................................................... 62
.......................................................................................................... 62
.......................................................................................................... 65
.......................................................................................................... 65
.......................................................................................................... 65
.......................................................................................................... 65
.......................................................................................................... 71
.......................................................................................................... 71
.......................................................................................................... 71
.......................................................................................................... 71
.......................................................................................................... 75
.......................................................................................................... 75
.......................................................................................................... 75
........................................................................................................................ 78
9. AVG Security Toolbar
9.1 AVG Security Toolbar Interfac e
9.1.1 AVG logo button
9.1.2 AVG Secure Search powered searc h box
9.1.3 Page Status
9.1.4 AVG News
9.1.5 News
9.1.6 AVG Info
9.1.7 Delete history
9.1.8 E-mail Notifier
9.1.9 Weather Info
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 4
.......................................................................................................... 78
.......................................................................................................... 78
.......................................................................................................... 78
.......................................................................................................... 78
.......................................................................................................... 78
.......................................................................................................... 78
.......................................................................................................... 78
.......................................................................................................... 78
.......................................................................................................... 78
.......................................................................................................... 78
Page 5

9.1.10 Facebook
9.1.11 VeriSign Identity Protection
9.2 AVG Security Toolbar Options
9.2.1 Tab General
9.2.2 Tab Useful Buttons
9.2.3 Tab Security
9.2.4 Tab VIP
9.2.5 Tab Advanced Options
........................................................................................................................ 95
10. AVG Advanced Settings
.......................................................................................................... 78
.......................................................................................................... 78
.......................................................................................................... 89
.......................................................................................................... 89
.......................................................................................................... 89
.......................................................................................................... 89
.......................................................................................................... 89
.......................................................................................................... 89
10.1 Appearance
10.2 Sounds
10.3 Ignore Faulty Conditions
10.4 Identity Protection
10.4.1 Identity Protection Settings
10.4.2 Allowed List
10.5 Virus Vault
10.6 PUP Exceptions
10.7 Anti-Spam
10.7.1 Settings
10.7.2 Performance
10.7.3 RBL
10.7.4 Whitelist
10.7.5 Blacklist
10.7.6 Advanced Settings
10.8 Online Shield
10.8.1 Web Protection
10.8.2 Instant Messaging
10.9 Link Scanner
10.10 Scans
10.10.1 Sc an Whole Computer
10.10.2 Shell Extension Scan
10.10.3 Sc an Specific Files or Folders
10.10.4 Removable Device Scan
10.11 Schedules
10.11.1 Sc heduled Scan
10.11.2 Virus Database Update Schedule
10.11.3 Program Update Schedule
.......................................................................................................... 95
.......................................................................................................... 97
.......................................................................................................... 99
.......................................................................................................... 100
.......................................................................................................... 100
.......................................................................................................... 100
.......................................................................................................... 104
.......................................................................................................... 104
.......................................................................................................... 106
.......................................................................................................... 106
.......................................................................................................... 106
.......................................................................................................... 106
.......................................................................................................... 106
.......................................................................................................... 106
.......................................................................................................... 106
.......................................................................................................... 118
.......................................................................................................... 118
.......................................................................................................... 118
.......................................................................................................... 122
.......................................................................................................... 123
.......................................................................................................... 123
.......................................................................................................... 123
.......................................................................................................... 123
.......................................................................................................... 123
.......................................................................................................... 128
.......................................................................................................... 128
.......................................................................................................... 128
.......................................................................................................... 128
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 5
Page 6

.......................................................................................................... 128
10.11.4 Anti-Spam Update Schedule
10.12 E-mail Scanner
10.13 Resident Shield
10.14 Cache Server
10.15 Anti-Rootkit
10.16 Update
10.17 Remote Administration
.......................................................................................................... 139
.......................................................................................................... 139
10.12.1 Certification
.......................................................................................................... 139
10.12.2 Mail Filtering
.......................................................................................................... 139
10.12.3 Logs and Results
.......................................................................................................... 139
10.12.4 Servers
.......................................................................................................... 149
.......................................................................................................... 149
10.13.1 Advanced Settings
.......................................................................................................... 149
10.13.2 Direc tory Exludes
.......................................................................................................... 149
10.13.3 Exc luded Files
.......................................................................................................... 154
.......................................................................................................... 155
.......................................................................................................... 156
.......................................................................................................... 156
10.16.1 Proxy
.......................................................................................................... 156
10.16.2 Dial-up
.......................................................................................................... 156
10.16.3 URL
.......................................................................................................... 156
10.16.4 Manage
.......................................................................................................... 163
........................................................................................................................ 165
11. Firewall Settings
11.1 General
11.2 Security
11.3 Areas and Adapters Profiles
11.4 Logs
11.5 Profiles
........................................................................................................................ 180
12. AVG Scanning
12.1 Scanning Interface
12.2 Predefined Scans
12.3 Scanning in Windows Explorer
12.4 Command Line Sc anning
.......................................................................................................... 165
.......................................................................................................... 166
.......................................................................................................... 167
.......................................................................................................... 168
.......................................................................................................... 169
.......................................................................................................... 169
11.5.1 Profile Information
.......................................................................................................... 169
11.5.2 Defined Networks
.......................................................................................................... 169
11.5.3 Applications
.......................................................................................................... 169
11.5.4 System Services
.......................................................................................................... 180
.......................................................................................................... 181
.......................................................................................................... 181
12.2.1 Scan Whole Computer
.......................................................................................................... 181
12.2.2 Scan Specific Files or Folders
.......................................................................................................... 181
12.2.3 Anti-Rootkit Scan
.......................................................................................................... 189
.......................................................................................................... 190
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 6
Page 7

.......................................................................................................... 190
12.4.1 CMD Scan Parameters
12.5 Scan Sc heduling
12.6 Scan Results Overview
12.7 Scan Results Details
12.8 Virus Vault
........................................................................................................................ 213
13. AVG Updates
.......................................................................................................... 192
.......................................................................................................... 192
12.5.1 Schedule Settings
.......................................................................................................... 192
12.5.2 How to Scan
.......................................................................................................... 192
12.5.3 What to Scan
.......................................................................................................... 201
.......................................................................................................... 202
.......................................................................................................... 202
12.7.1 Results Overview Tab
.......................................................................................................... 202
12.7.2 Infections Tab
.......................................................................................................... 202
12.7.3 Spyware Tab
.......................................................................................................... 202
12.7.4 Warnings Tab
.......................................................................................................... 202
12.7.5 Rootkits Tab
.......................................................................................................... 202
12.7.6 Information Tab
.......................................................................................................... 210
13.1 Update Levels
13.2 Update Types
13.3 Update Process
........................................................................................................................ 215
14. Event History
........................................................................................................................ 216
15. FAQ and Technical Support
.......................................................................................................... 213
.......................................................................................................... 213
.......................................................................................................... 213
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 7
Page 8

1. Introduction
This user manual provides comprehensive documentation for AVG 9 Internet Security
.
Congratulations on your purchase of AVG 9 Internet Security!
AVG 9 Internet Security is one of a range of award winning AVG products designed
to provide you with peace of mind and total security for your PC. As with all AVG
products AVG 9 Internet Security has been completely re-designed, from the ground
up, to deliver AVG’s renowned and accredited security protection in a new, more user
friendly and efficient way.
Your new AVG 9 Internet Security product has a streamlined interface combined with
more aggressive and faster scanning. More security features have been automated for
your convenience, and new ‘intelligent’ user options have been included so that you
can fit our security features to your way of life. No more compromising usability over
security!
AVG has been designed and developed to protect your computing and networking
activity. Enjoy the experience of full protection from AVG.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 8
Page 9
2. AVG Installation Requirements
2.1. Operation Systems Supported
AVG 9 Internet Security is intended to protect workstations with the following
operating systems:
· Windows 2000 Professional SP4 + Update Rollup 1
· Windows XP Home Edition SP2
· Windows XP Professional SP2
· Windows XP Professional x64 Edition SP1
· Windows Vista (x86 and x64, all editions)
· Windows 7 (x86 and x64, all editions)
(and possibly higher service packs for specific operating systems)
Note: The ID Protection component is not supported on Windows 2000 and XP x64.
On these operating systems you can install AVG 9 Internet Security but only without
the IDP component.
2.2. Minimum & Recommended HW Requirements
Minimum hardware requirements for AVG 9 Internet Security:
· Intel Pentium CPU 1,5 GHz
· 512 MB of RAM memory
· 390 MB of free hard drive space (for installation purposes)
Recommended hardware requirements for AVG 9 Internet Security:
· Intel Pentium CPU 1,8 GHz
· 512 MB of RAM memory
· 510 MB of free hard drive space (for installation purposes)
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 9
Page 10
3. AVG Installation Options
AVG can be installed either from the installation file available on your installation CD, or
you can download the latest installation file from AVG website (http://www.avg.com/).
Before you start installing AVG, we strongly recommend that you visit AVG
website (http://www.avg.com/) to check for a new installation file. This way
you can be sure to install the latest available version of AVG 9 Internet
Security.
We recommend you to try out our new AVG Download Manager tool that will
help you set up the installation file in your required language!
During the installation process you will be asked for your license/sales number. Please
make sure you have it available before starting the installation. The sales number can
be found on the CD packaging. If you purchased your copy of AVG on-line, your
license number will have been delivered to you via e-mail.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 10
Page 11
4. AVG Download Manager
AVG Download Manager is a simple tool that helps you select the proper installation file for the trial version of your AVG product. Based on your input data, the manager will select the spec ific product, license type, desired components, and language. Finally, AVG Download Manager will go on to download and launch the appropriate
installation process.
Warning: Please note that AVG Download Manager is not suitable for downloading of
network and SBS editions and only the following operating systems are supported:
Windows 2000 (SP4 + SRP roll-up), Windows XP, Windows Vista, and Windows 7.
AVG Download Manager is available for download at AVG website (http://www.avg.
com/). Following please find a brief desc ription of each single step you need to take
within the AVG Download Manager:
4.1. Language Selection
In this first step of AVG Download Manager select the installation language from the
roll-down menu. Note, that your language selection applies only to the installation
process; after the installation you will be able to change the language directly from
program settings. Then press the Next button to continue.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 11
Page 12
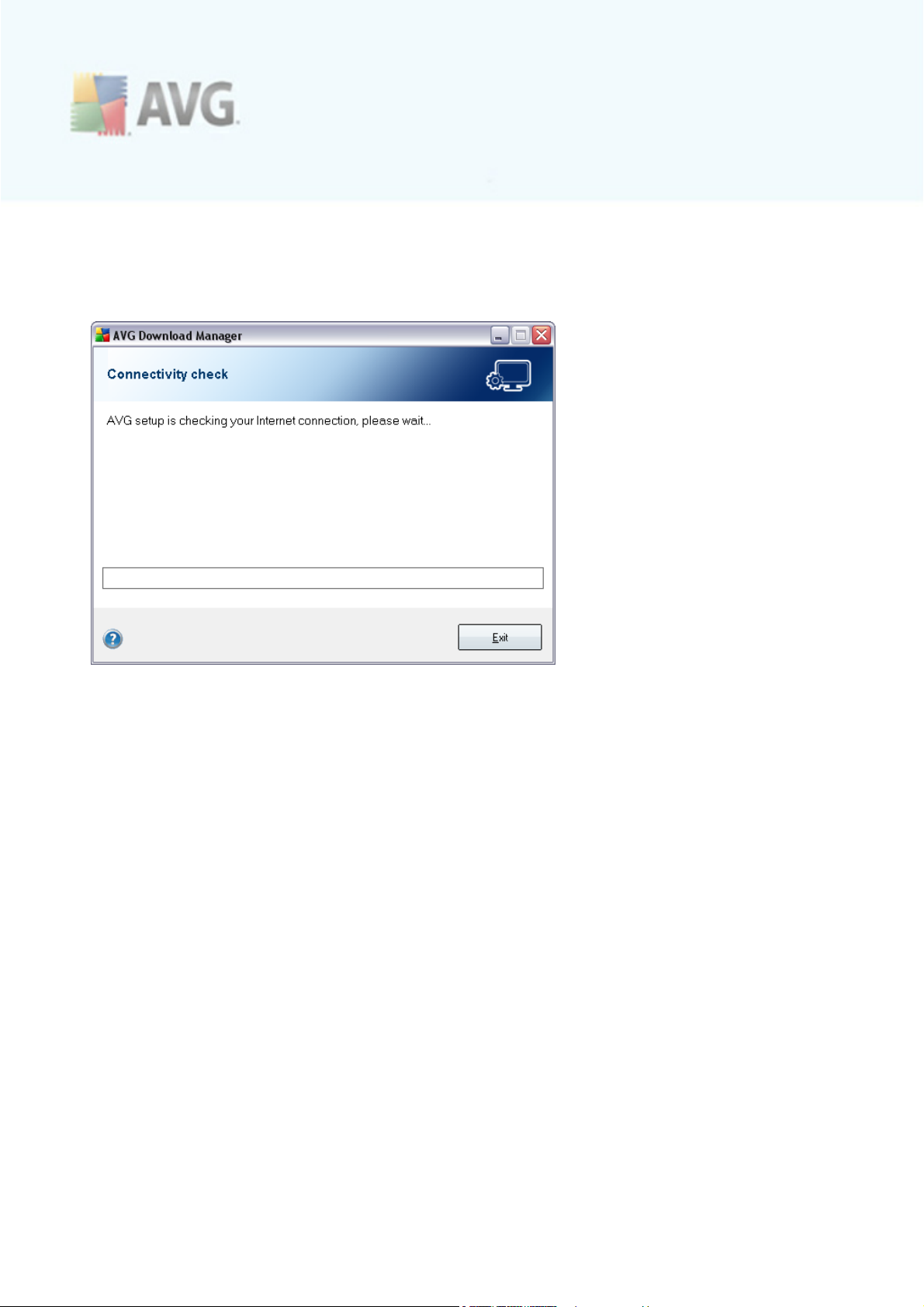
4.2. Connectivity Check
In the next step called Connectivity check, AVG Download Manager will attempt to
establish an Internet connection so that updates can be located.
You will not be allowed to advance the download process until the AVG Download
Manager is able to complete the connectivity test.
· If the test shows no connectivity, you will be informed about this status by
the following dialog - then make sure you are really connected to Internet, and
click the Retry button to continue:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 12
Page 13
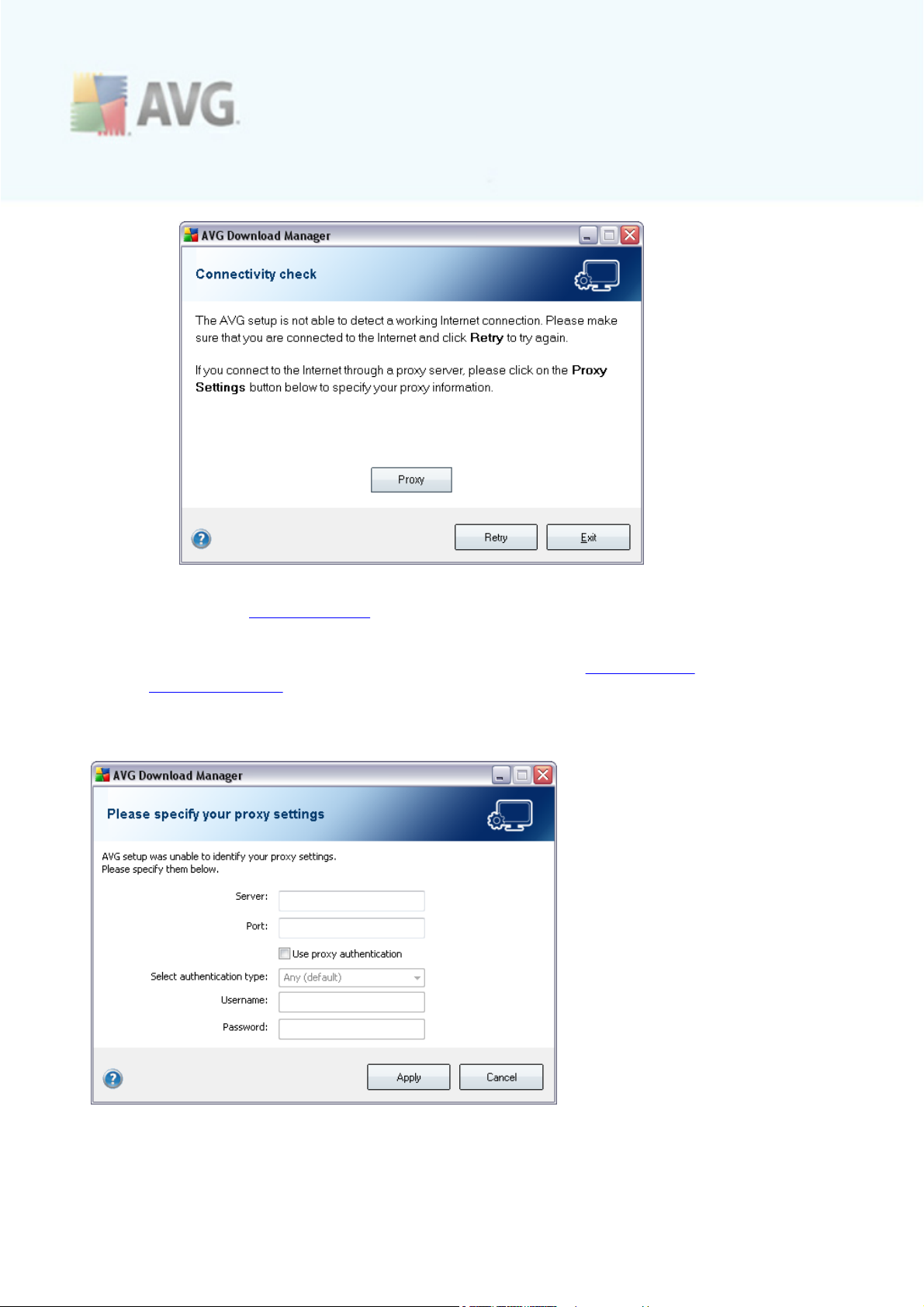
· If you are using a Proxy connection to the Internet, c lick the Proxy button to
specify your Proxy Settings.
· If the c heck has been succ essful, AVG Download Manager will go on
automatically and you will get redirected directly to the Downloading
installation files dialog.
4.3. Proxy Settings
If AVG Download Manager was not able to identify your Proxy settings you have to
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 13
Page 14
specify them manually. Please fill in the following data:
· Server - enter a valid proxy server name or IP address
· Port - provide the respective port number
· Use proxy authentication - if your proxy server requires authentication, tick
this c heck box.
· Select authentication - from the drop-down menu select the authentication
type. We strongly recommend that you keep to the default value (the proxy
server will then automatically c onvey its requirements to you). However, if
you are a skilled user, you can also choose Basic (required by some servers)
or NTLM (required by all ISA Servers) option. Then, enter a valid Username
and Password (optionally).
Confirm your settings by pressing the Apply button to follow to the next step of AVG
Download Manager.
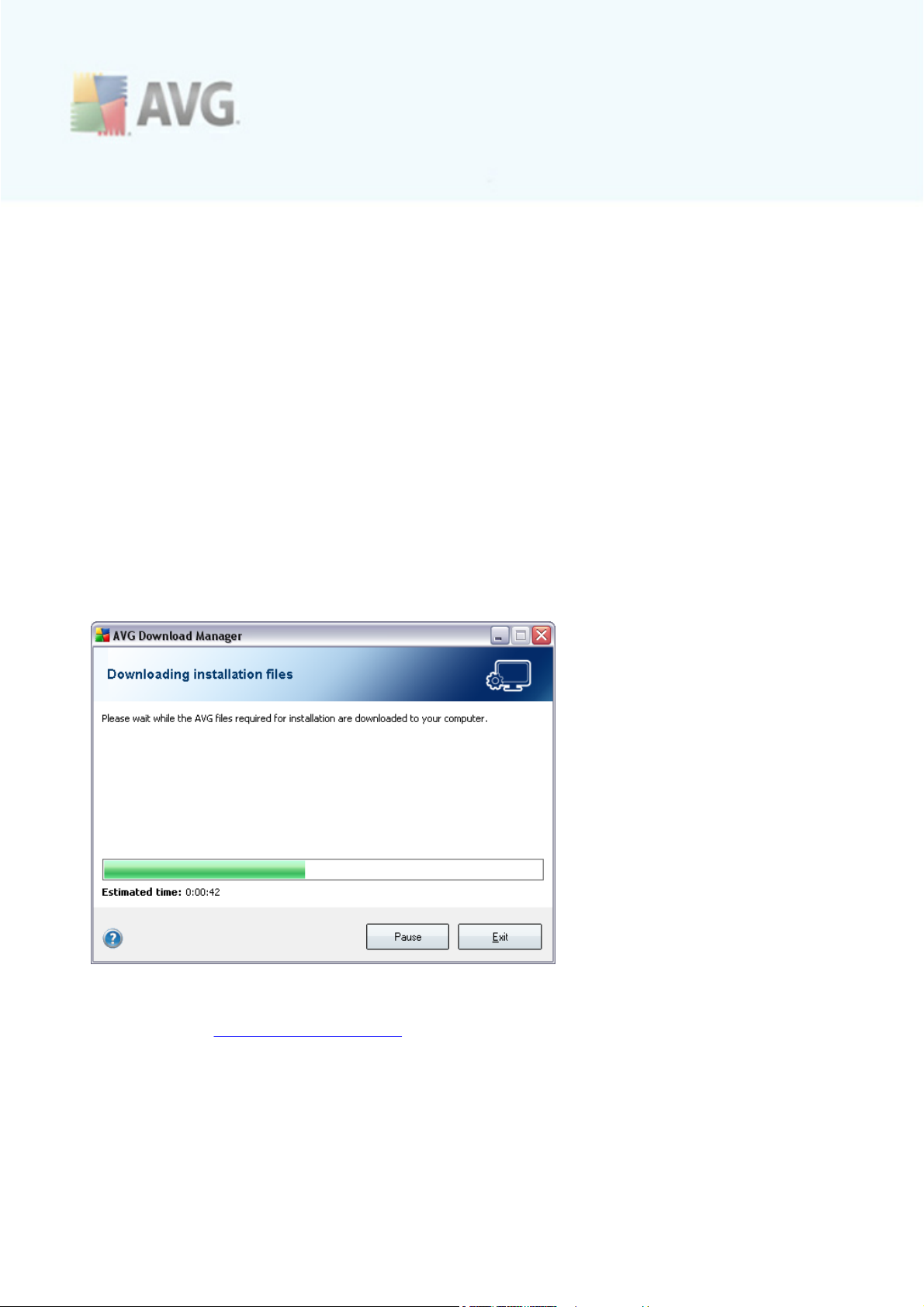
4.4. Downloading Installation Files
Now, you have provided all information needed for the AVG Download Manager to
start the installation package download, and launch the installation process. Further,
advance to the AVG Installation Process.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 14
Page 15
5. AVG Installation Process
To install AVG 9 Internet Security on your computer, you need to get the latest
installation file. You c an use the installation file from the CD that is a part of your box
edition but this file might be out-of-date. Therefore we recommended getting the
latest installation file online. You can download the file from AVG website (http://www.
avg.com/), the Support Center / Download section. Or, you can make use of our
new AVG Download Manager tool that helps you create and download the
installation package you need, and launch the installation process.
The installation is a sequence of dialog windows with a brief description of what do at
each step. In the following, we offer an explanation for each dialog window:
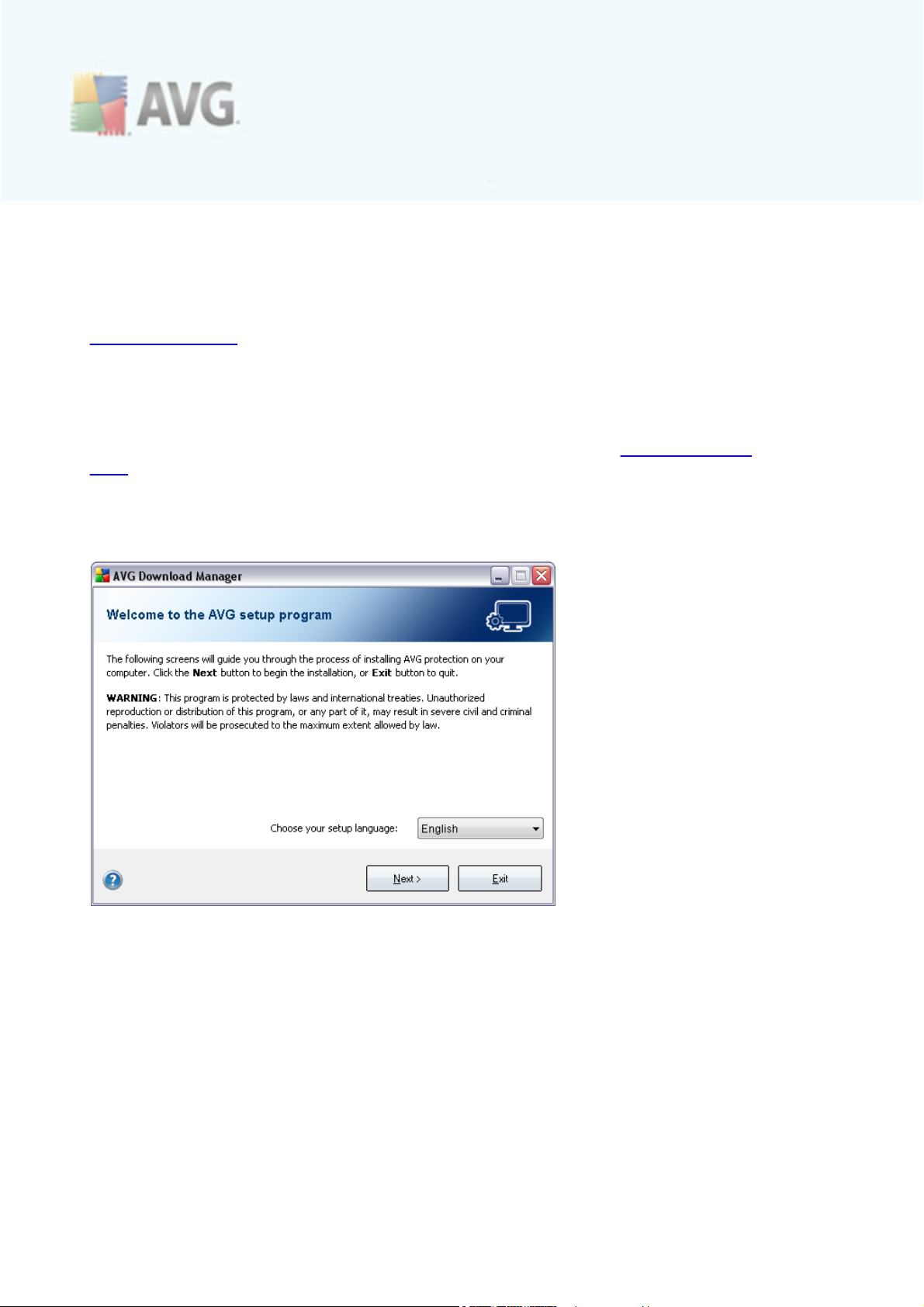
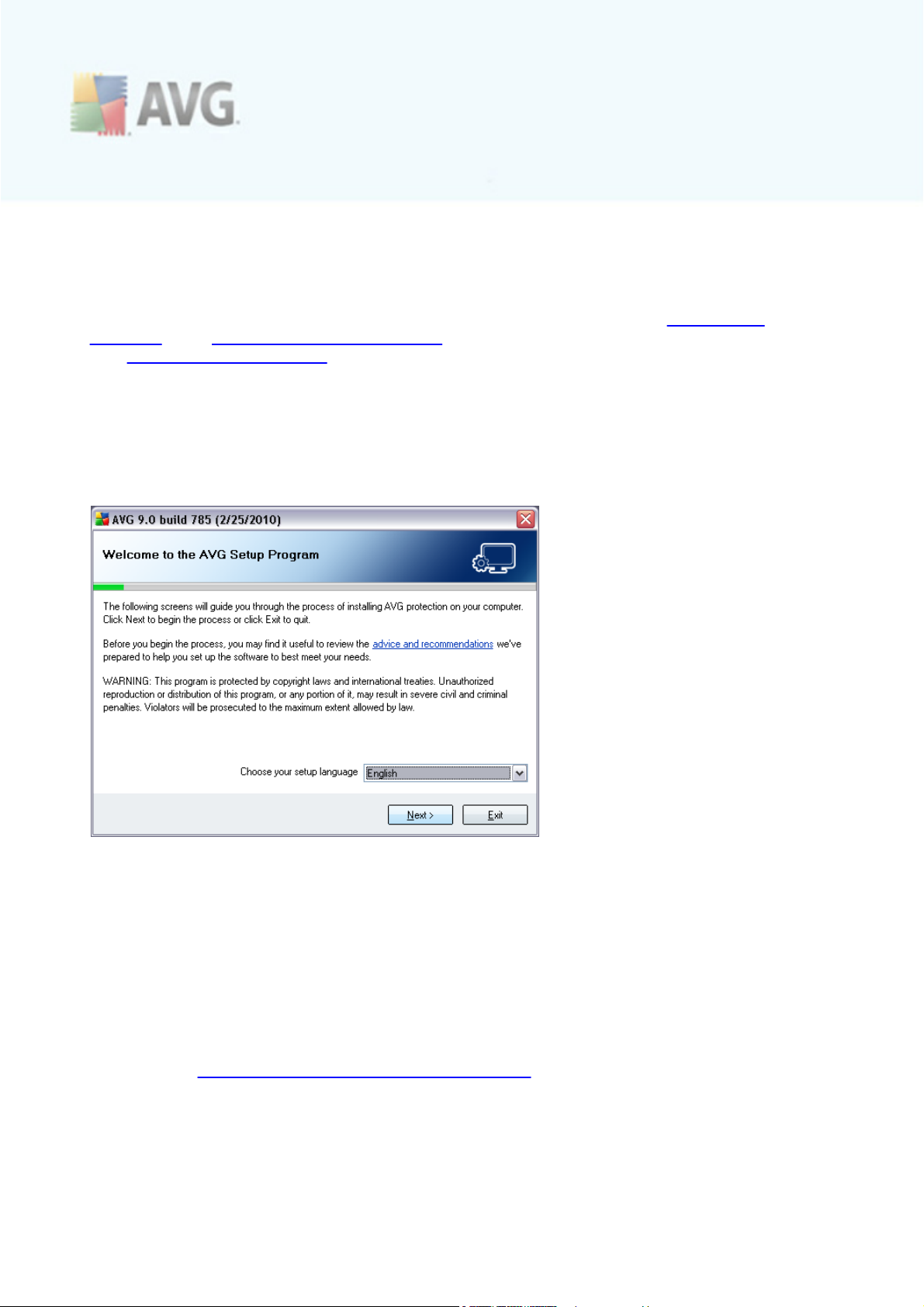
5.1. Installation Launch
The installation process starts with the Welcome to the AVG Setup Program
window. In here you select the language used for the installation process, and the
default language of AVG user interface. In the lower part of the dialog window find
the Choose your setup language item, and select the desired language from the
drop down menu. Then press the Next button to confirm and c ontinue to the next
dialog.
Attention: Here, you are selecting the language for the installation process. The
language you select will be installed as the default language for AVG user interface,
together with English that is installed automatically. If you want to have installed
other additional languages for the user interface, please define them within the setup
dialog named Custom Installation - Component Selection.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 15
Page 16
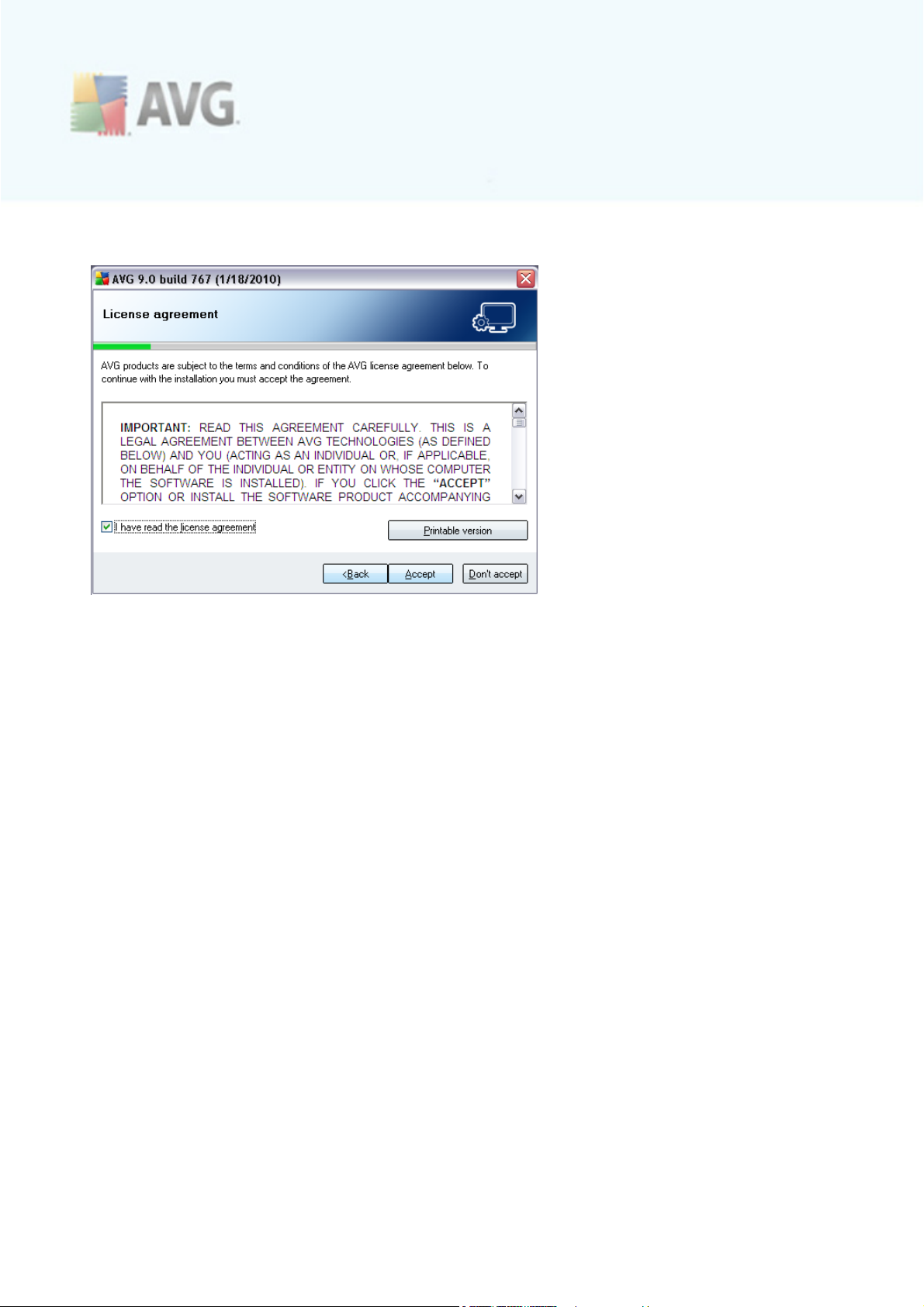
5.2. License Agreement
The License Agreement dialog provides the full wording of the AVG license
agreement. Please read it carefully and confirm that you have read, understood and
accept the agreement by marking the I have read license agreement chec k box and
pressing the Accept button.
If you do not agree with the license agreement press the Don't accept button, and
the installation process will be terminated immediately.
5.3. Checking System Status
Having confirmed the license agreement, you will be redirected to the Checking System Status dialog. This dialog does not require any intervention; your system is
being checked before the AVG installation can start. Please wait until the process has
finished, then continue automatically to the following dialog.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 16
Page 17
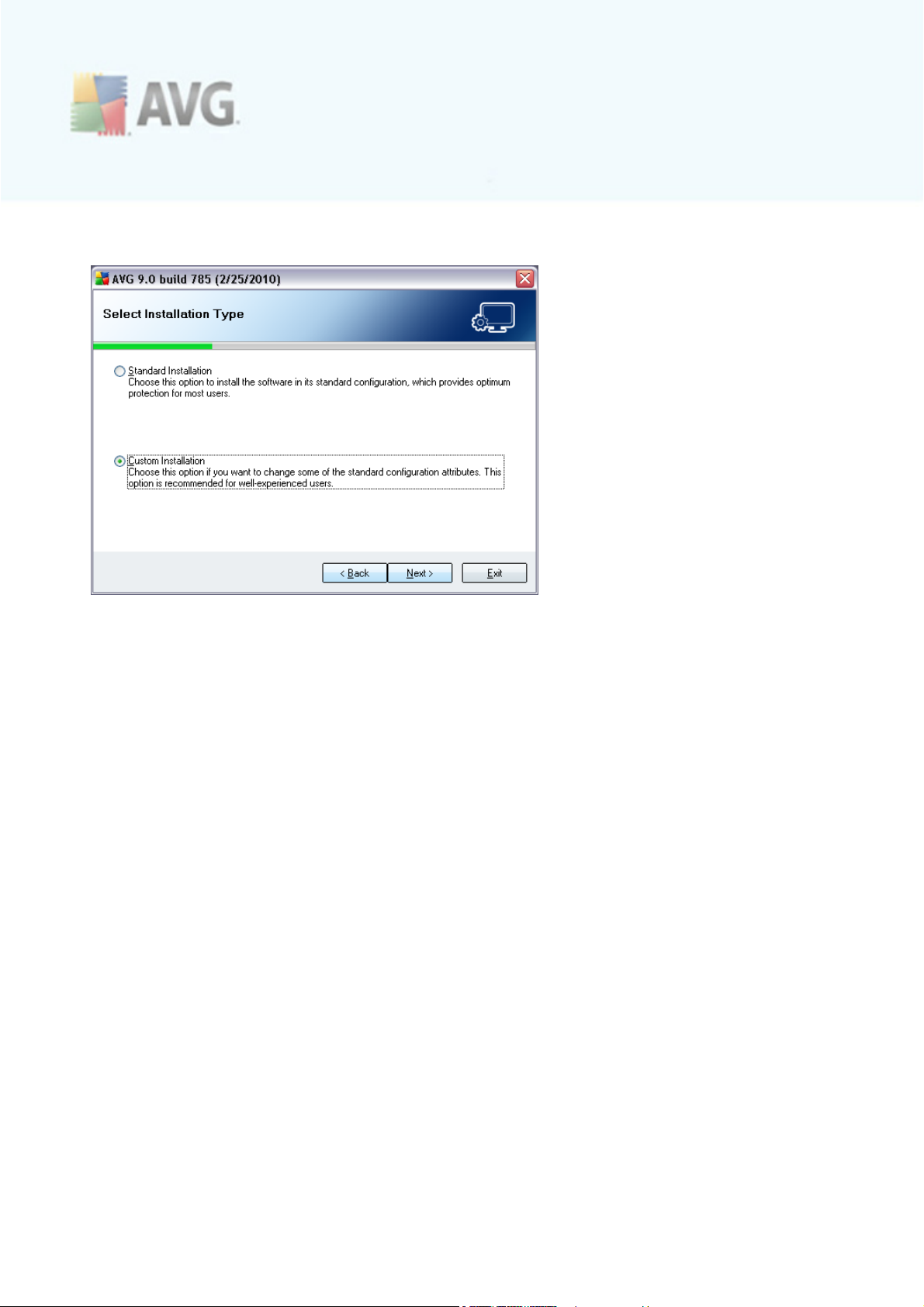
5.4. Select Installation Type
The Select Installation Type dialog offers the choice of two installation options: standard and custom installation.
For most users, it is highly recommended to keep to the standard installation that
installs AVG in fully automatic mode with settings predefined by the program vendor.
This configuration provides maximum sec urity combined with the optimal use of
resources. In the future, if the need arises to change the configuration, you will
always have the possibility to do so directly in the AVG application.
Custom installation should only be used by experienced users who have a valid
reason to install AVG with non-standard settings. E.g. to fit specific system
requirements.
5.5. Activate your AVG License
In the Activate your AVG License dialog you have to fill in your registration data.
Type in your name (User Name field) and the name of your organization (Company
Name field).
Then enter your license/sales number into the License Number text field. The sales
number can be found on the CD packaging in your AVG 9 Internet Security box. The
license number will be in the confirmation email that you received after purchasing
your AVG 9 Internet Security on-line. You must type in the number exactly as
shown. If the digital form of the license number is available (in the email), it is
recommended to use the copy and paste method to insert it.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 17
Page 18
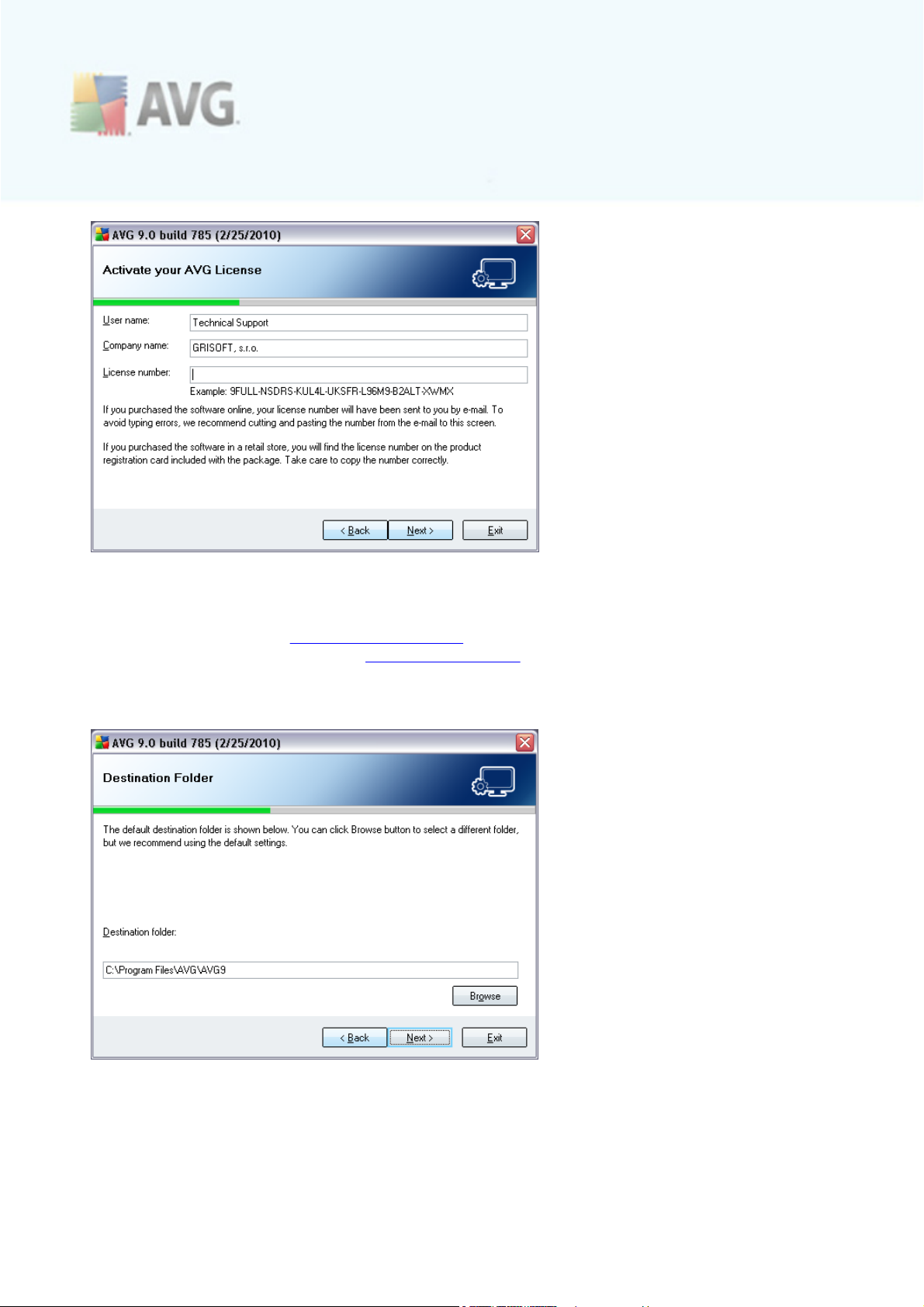
Press the Next button to continue the installation process.
If in the previous step you have selected the standard installation, you will be
redirected directly to the AVG Security Toolbar dialog. If custom installation was
selected you will continue with the Destination Folder dialog.
5.6. Custom Installation - Destination Folder
The Destination Folder dialog allows you to spec ify the location where AVG 9
Internet Security should be installed. By default, AVG will be installed to the program
files folder located on drive C:. In case the folder does not exist yet, you will be asked
in a new dialog to confirm you agree AVG creates this folder now.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 18
Page 19
If you want to change this location, use the Browse button to display the drive
structure, and select the respective folder.
Press the Next button to confirm.
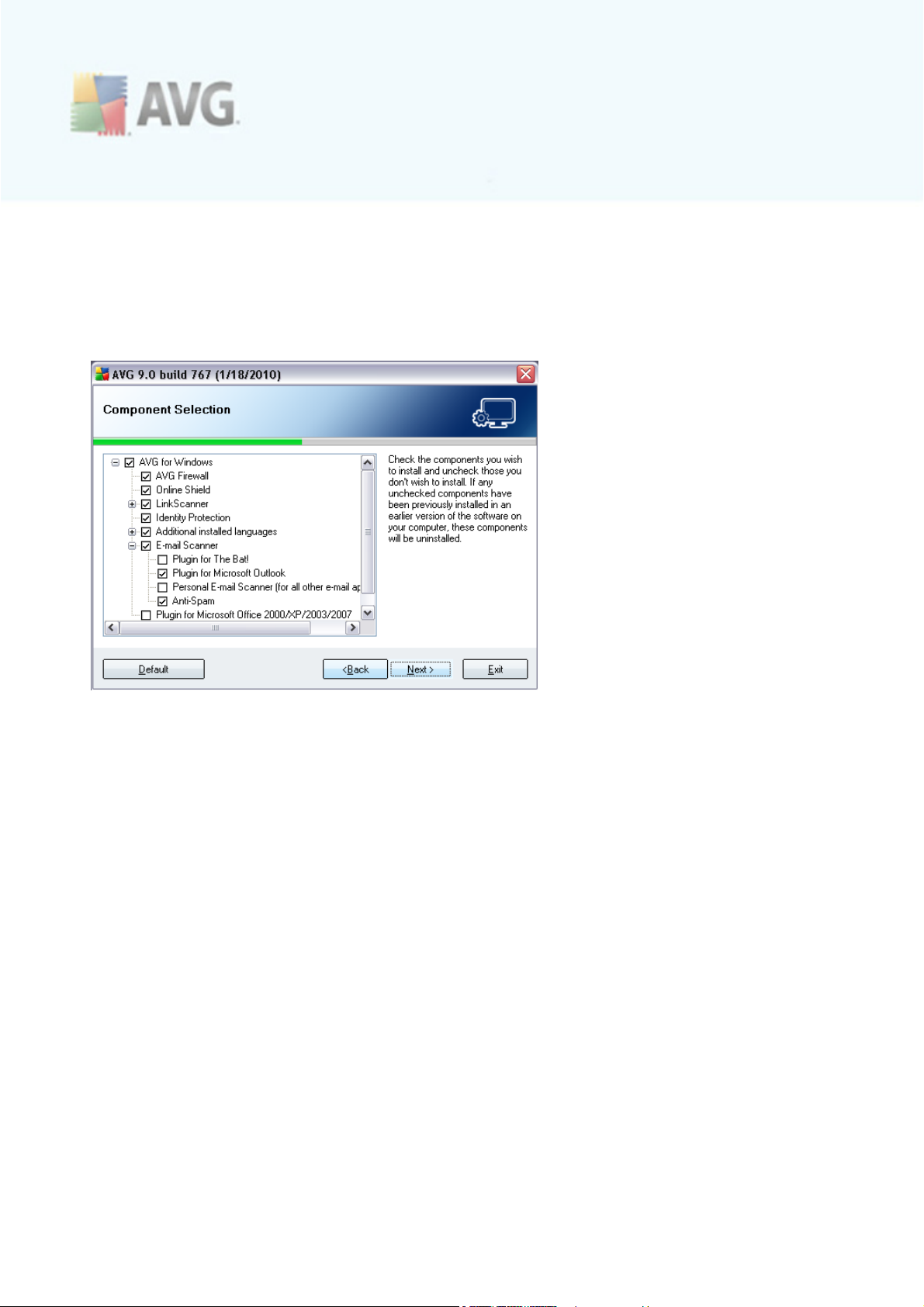
5.7. Custom Installation - Component Selection
The Component Selection dialog displays an overview of all AVG 9 Internet Security
components that can be installed. If the default settings do not suit you, you can
remove/add specific components.
However, you can only select from components that are included in your
purchased AVG edition. Only those components will be offered to be installed
within the Component Selection dialog!
· Language selection - within the list of components to be installed, you can
define which languages should be installed and further available for AVG user
interface. By default, English is installed always, and all other available
languages can be installed optionally. Unpack the Additional installed
languages item and then select the desired languages from the respective
menu.
· E-mail Scanner plug-ins - click the E-mail Scanner item to open and decide
on what plug-in is to be installed to guarantee your electronic mail security. By
default, the setup detects what is your currently installed e-mail client and
installs the respective plug-in. This is true for Plugin for Microsoft Outlook,
and Plugin for The Bat! In case none of these two e- mail clients is installed on
your computer, setup will assign Personal E-mail Scanner to be installed, and
this option covers all other e-mail clients (e.g. Qualcomm Eudora, etc.).
Optionally, you can mark the specific plug-ins for MS Outlook, and The Bat! to
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 19
Page 20
be installed as well. If your purchased license includes the Anti-Spam, it will
installed automatically as well.
· Remote Administration - if you plan to connect your computer to the AVG
Remote Administration later, please mark the respec tive item to be installed as
well.
Continue by pressing the Next button.
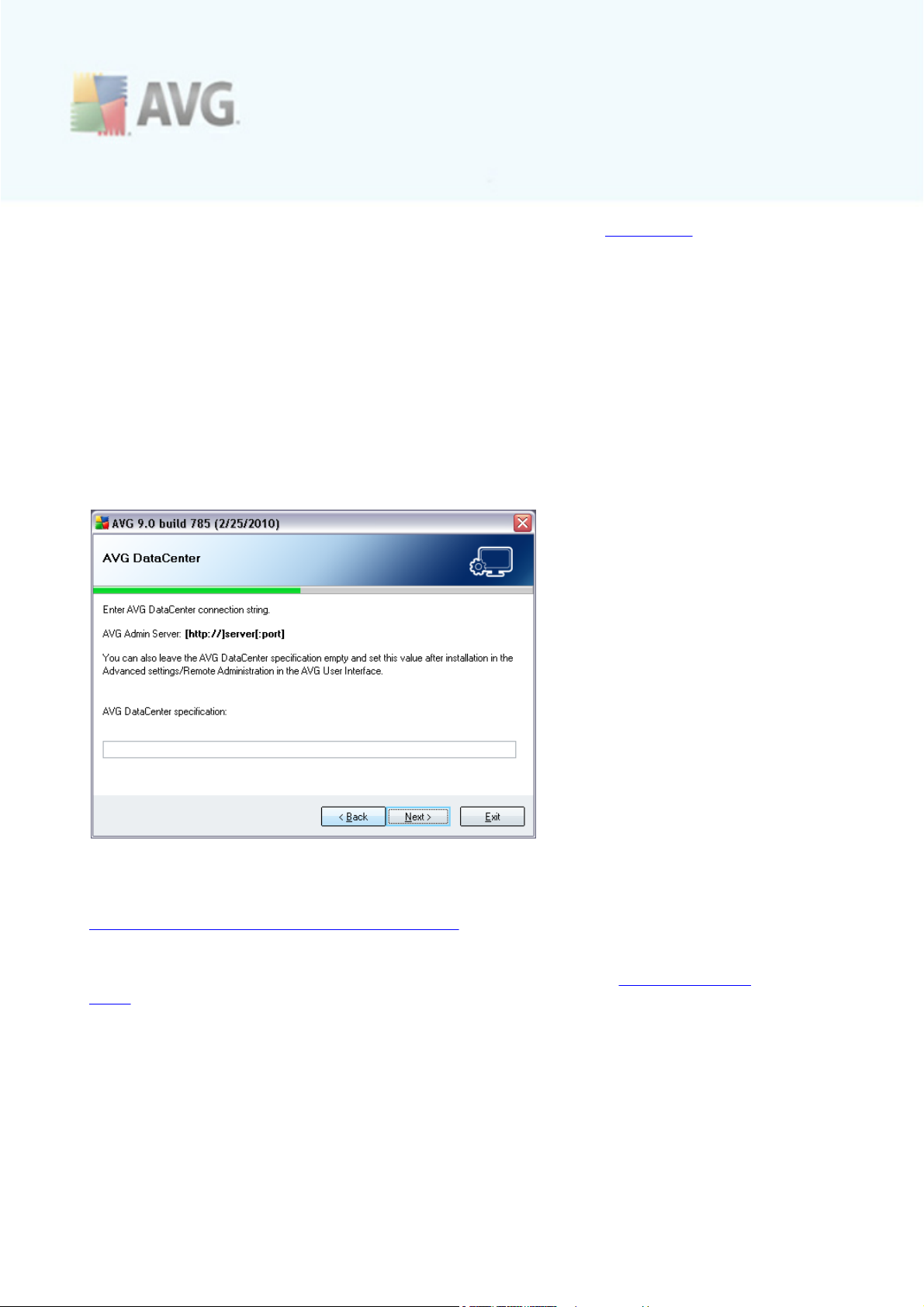
5.8. AVG DataCenter
If using AVG network license and in case in previous Custom Installation Component Selection dialog you have marked the Remote administration item to
be installed, it is nec essary to specify AVG DataCenter parameters:
Into the AVG DataCenter specification text field please provide the connection string
to AVG DataCenter in the form of server:port. If this information is not available at
the moment, leave the field blank and you can set the configuration later in within the
Advanced Settings / Remote Administration dialog.
Note: For detailed information on AVG Remote administration please consult AVG
Network Edition user manual; to be downloaded from AVG website (http://www.avg.
com/).
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 20
Page 21
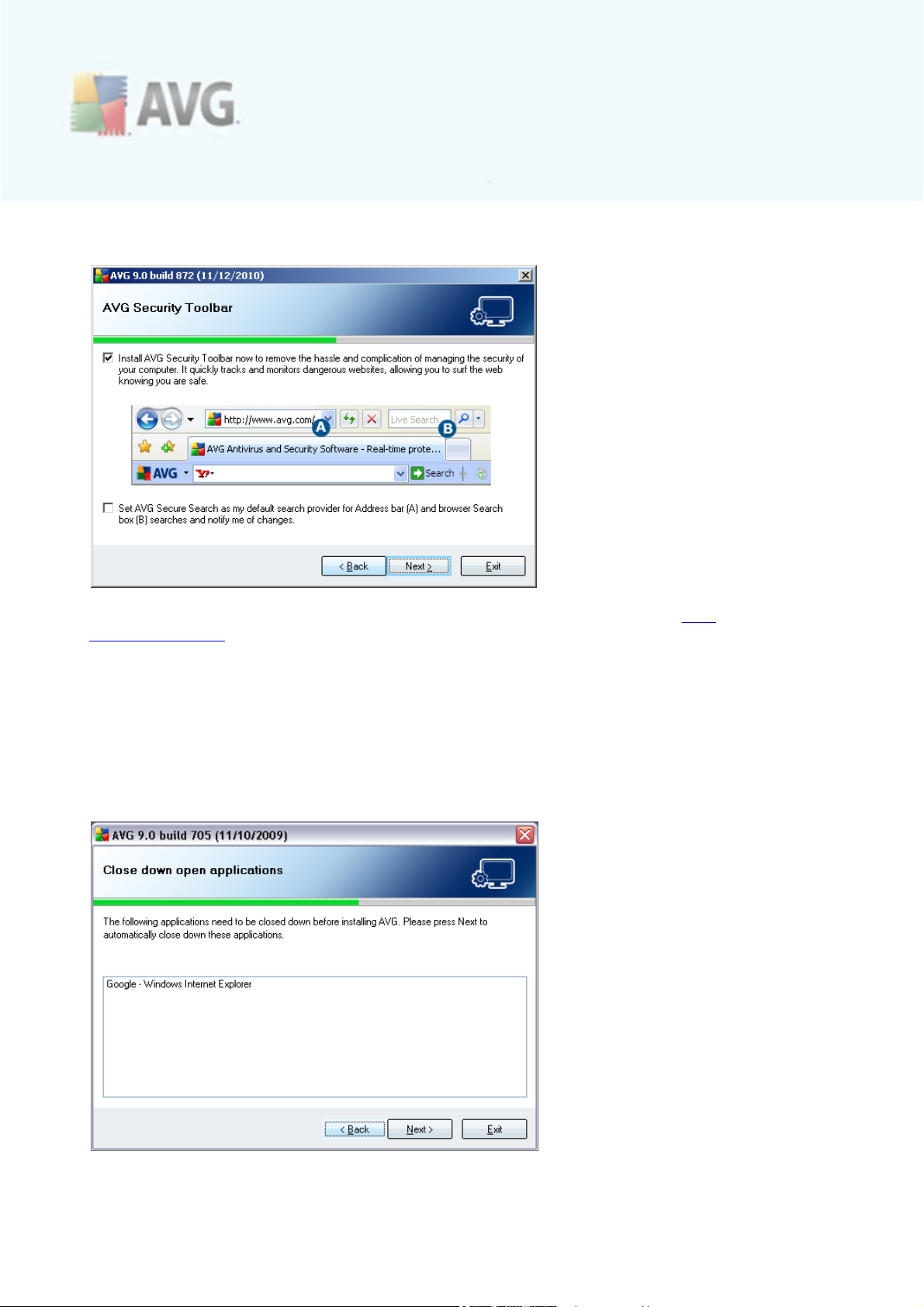
5.9. AVG Security Toolbar
In the AVG Security Toolbar dialog, dec ide whether you want to install the AVG
Security Toolbar. If you do not change the default settings, this component will be
installed automatically into your Internet browser (currently supported browsers are
Microsoft Internet Explorer v. 6.0 or higher, and Mozilla Firefox v. 3.0 or higher) and
to provide you with c omprehensive online protection while surfing the Internet.
Also, you have the option to decide whether you want to chose AVG Secure Search
as your default search provider. If so, please mark the respec tive chec k box.
5.10. Close down open applications
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 21
Page 22
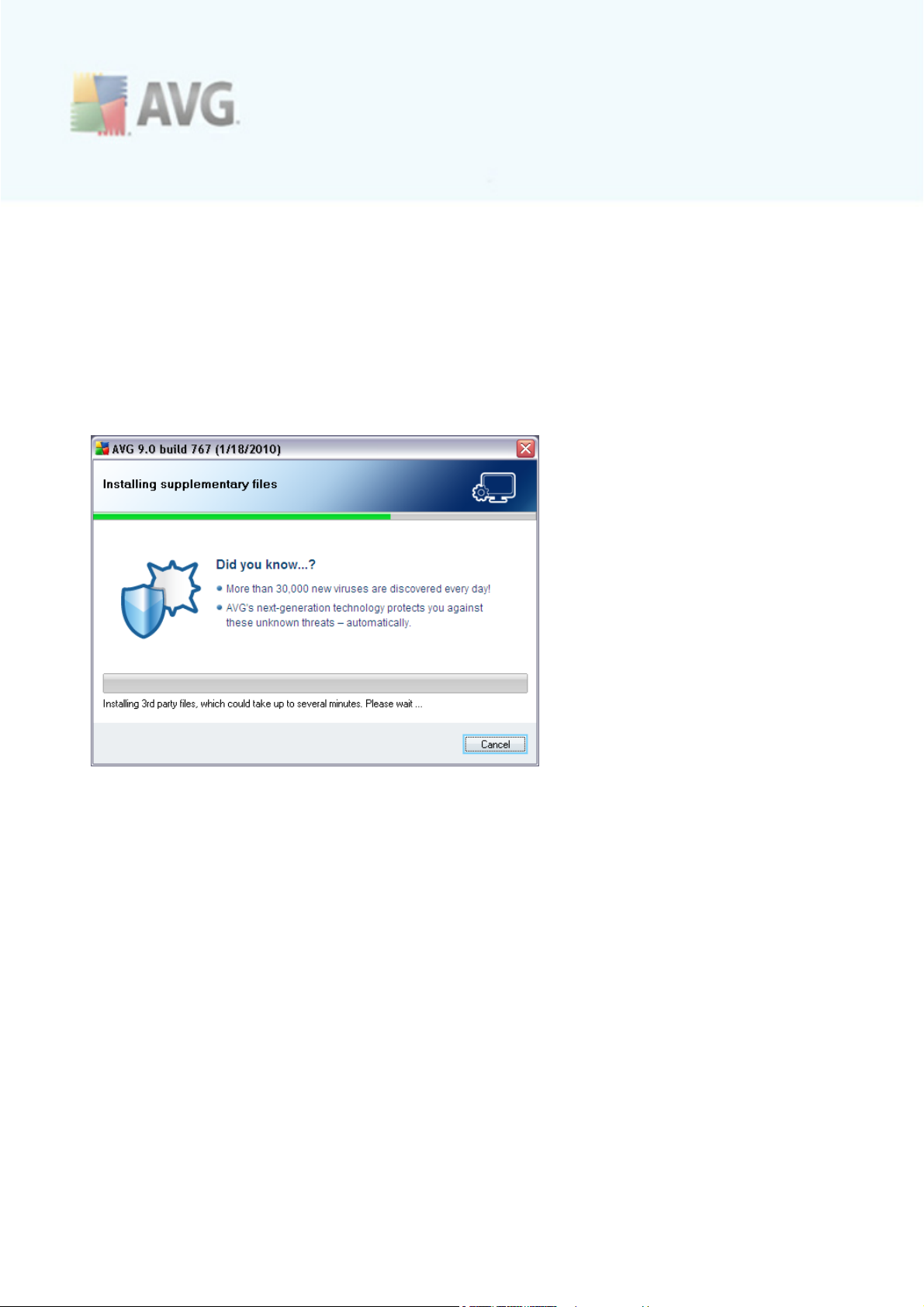
The Close down open applications dialog appears during the installation process only
in case there are some other clashing programs running on your computer at the
moment. Then, the list of programs that need to be closed in order to sucessfuly finish
the installation process will be provided. Press the Next button to c onfirm you agree
to close down the respective applications, and to c ontinue to the next step.
5.11. Installing AVG
The Installing AVG dialog shows the progress of the installation process, and does
not require any intervention:
After the installation process is finished, the virus database and program will be
updated automatically. Then, you will be redirected to the next dialog.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 22
Page 23
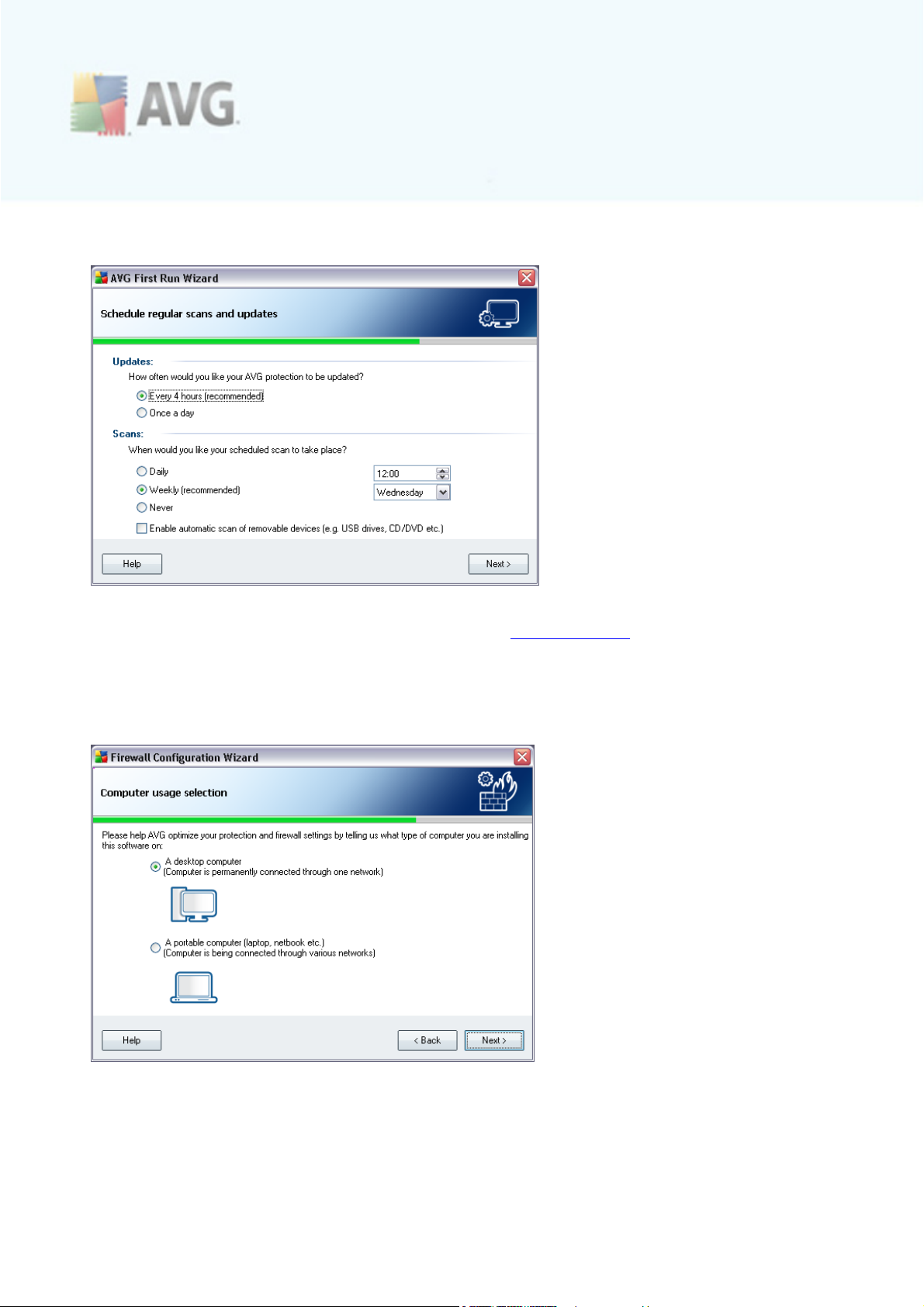
5.12. Schedule regular scans and updates
In the Schedule regular scans and updates dialog set up the interval for new update
files accessibility check-up, and define time when the scheduled scan should be
launched. It is recommended to keep the default values. Press the Next button to
continue.
5.13. Computer usage selection
In this dialog, the Firewall Configuration Wizard asks what type of computer you
use. For instance, your notebook, that connects to the Internet from many different
locations (airports, hotel rooms, etc.) requires security rules that are stricter than
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 23
Page 24
those of a computer in a domain (company network, etc.). Based on the selected
computer usage type the Firewall default rules will be defined with a different security
level.
You have two alternative options to select from:
· A desktop computer - having selected this option, you will be redirec ted to
the next dialog named Your computer internet connection
· A portable computer - with this option, you will go directly to the final step
of the installation process, AVG protection configuration is complete dialog
Confirm your selection by pressing the Next button and proceed to the next dialog.
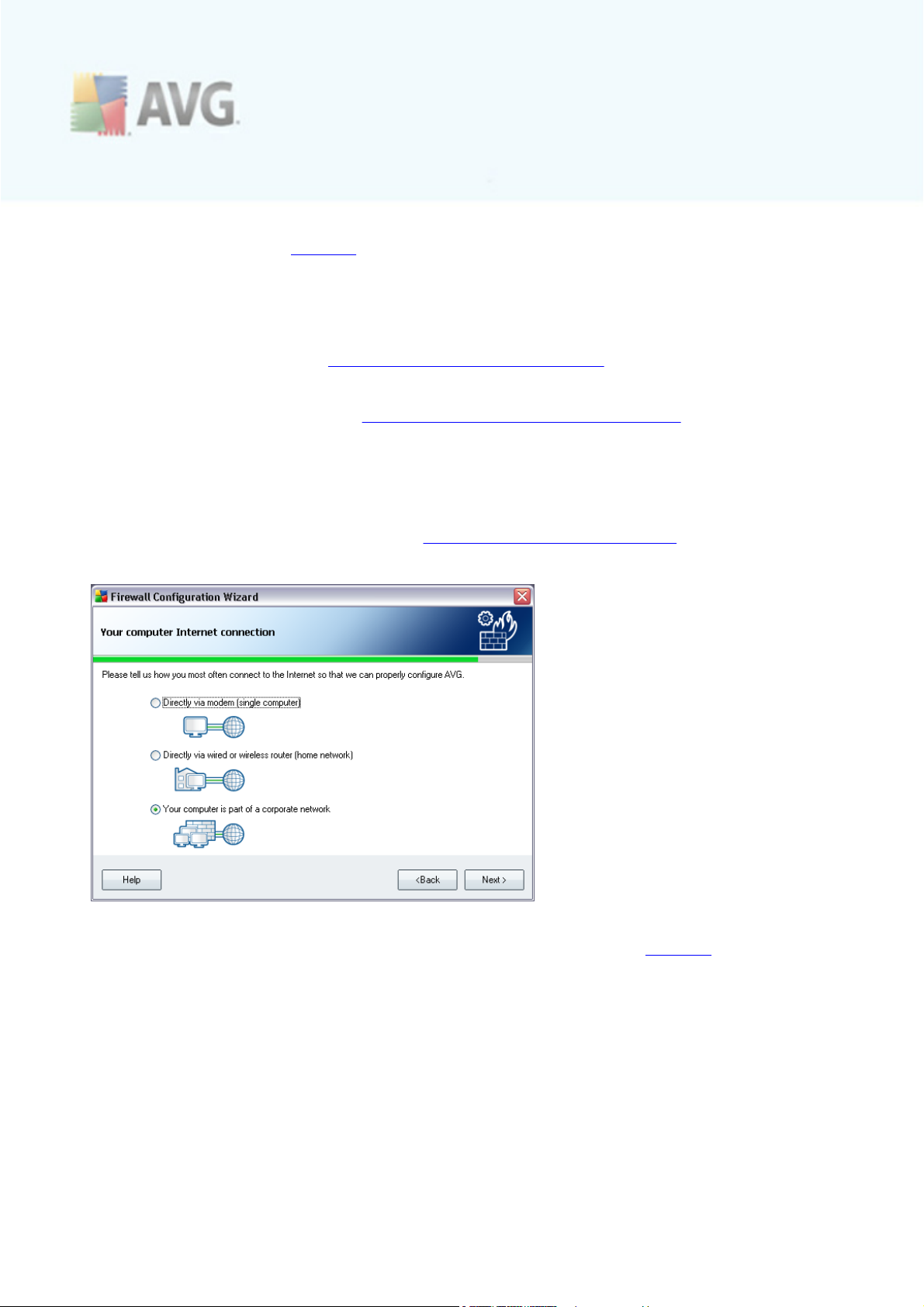
5.14. Your computer Internet connection
This dialog only appear if in the past step (Computer usage selection dialog) you have
selected the option of a desktop c omputer:
In this dialog, the Firewall Configuration Wizard asks how your computer is
connected to the Internet. Based on the selected connection type the Firewall
default rules will be defined with a different security level.
You have three alternative options to select from:
· Directly via modem
· Directly via wired or wireless router
· Your computer is a part of a corporate network
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 24
Page 25
Select the connection type that best describes your computer connection to the
Internet.
Confirm your selection by pressing the Next button and proceed to the next dialog.
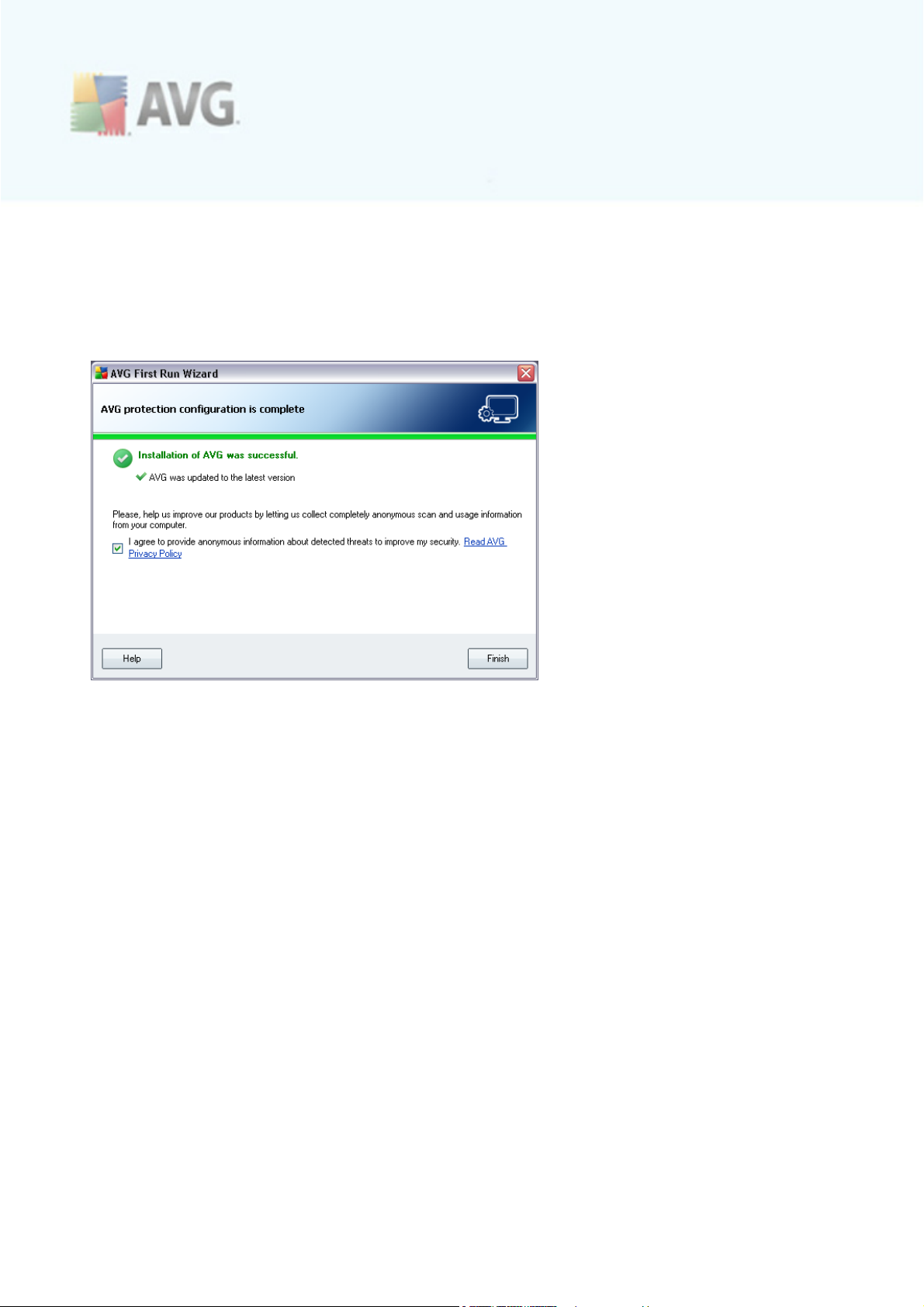
5.15. AVG protection configuration is complete
Now your AVG 9 Internet Security has been configured.
In this dialog you decide whether you want to activate the option of anonymous
reporting of exploits and bad sites to AVG virus lab. If so, please mark the I agree to
provide ANONYMOUS information about detected threats to improve my
security option.
Finally, press the Finish button.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 25
Page 26
6. After Installation
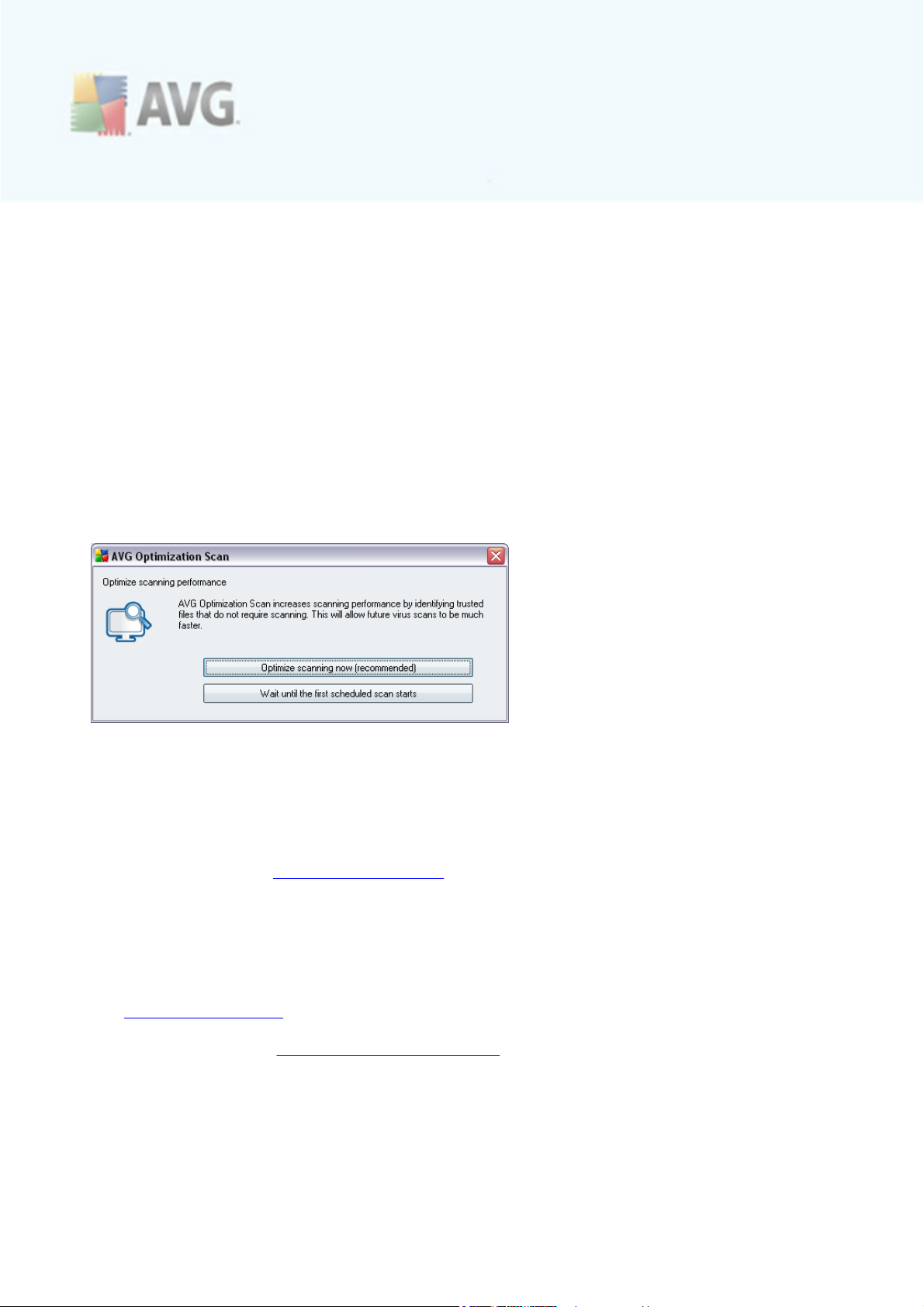
6.1. Scan optimization
The scanning optimization functionality searches the Windows and Program files
folders where it detec ts appropriate files (at the moment those are the *.exe, *.dll
and *.sys files) and saves the information on these files. With the next acc ess it will
no be necessary to scan these files automatically. The respective assigned files will
only be sc anned if AVG 9 Internet Security detects the files checksum change. If
there is no change to the file checksum, there is no need to scan the file again. This
approach reduces the the sc anning time significantly.
Once the installation process is over you will invited via a new dialog window to
optimize scanning:
We recommend to use this option and run the scanning optimization process by
pressing the Optimize scanning now button.
6.2. Product Registration
Having finished the AVG 9 Internet Security installation, please register you product
online on AVG website (http://www.avg.com/), Registration page (follow the
instruction provided directly in the page). After the registration you will be able to
gain full acc ess to your AVG User acc ount, the AVG Update newsletter, and other
services provided exclusively for registered users.
6.3. Access to User Interface
The AVG User Interface is ac cessible in several ways:
· double-click the AVG icon on the system tray
· double-click the AVG icon on the desktop
· from the menu Start/Programs/AVG 9.0/AVG User Interface
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 26
Page 27
· from AVG Security Toolbar via option Launch AVG
6.4. Scanning of the whole computer
There is a potential risk that a computer virus has been transmitted to your computer
prior to AVG 9 Internet Security installation. For this reason you should run a Scan of
the whole computer to make sure there are no infections on your PC.
For instructions on running a Scan of the whole computer please consult the
chapter AVG Scanning.
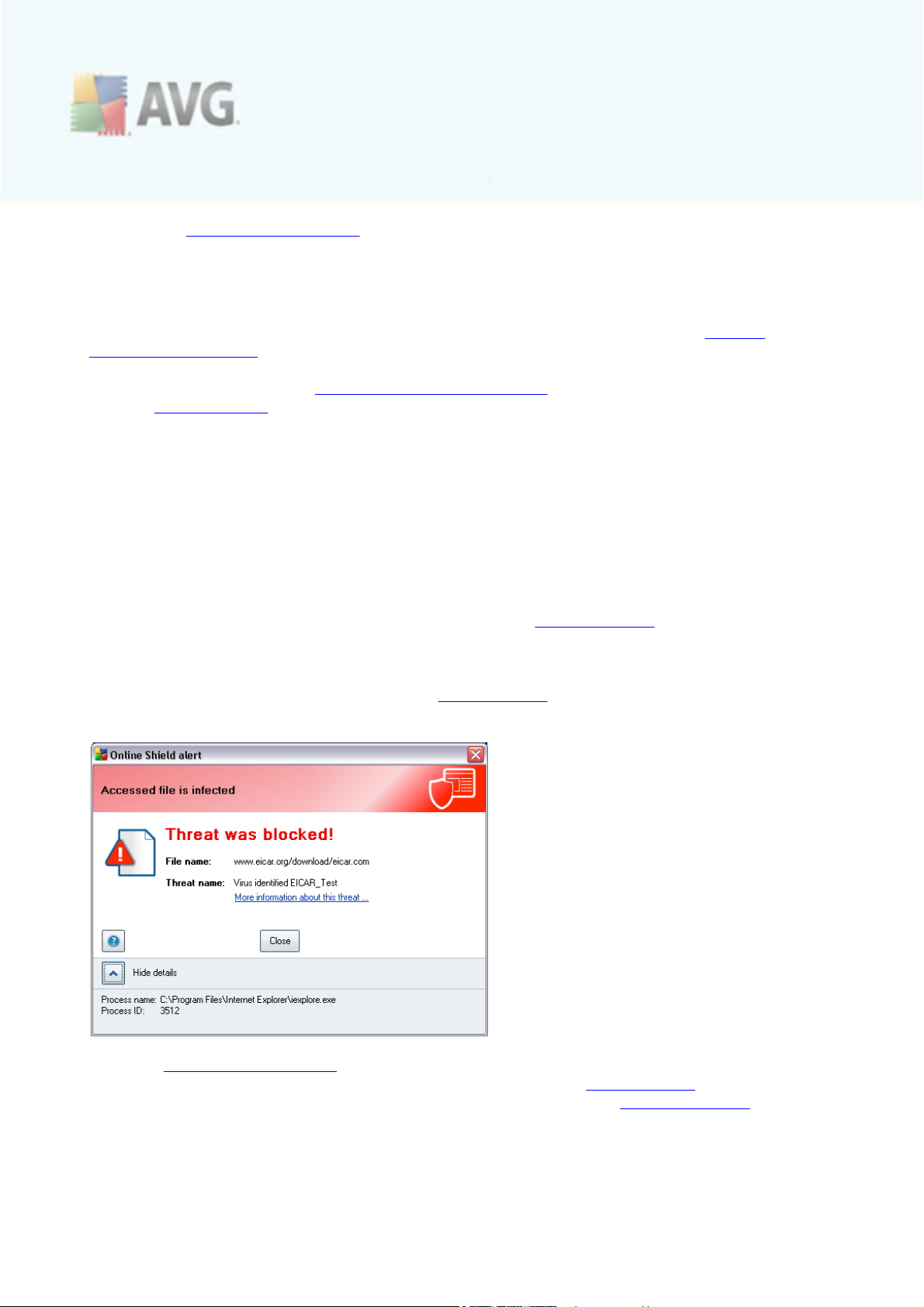
6.5. Eicar Test
To confirm that AVG 9 Internet Security has been installed correctly you can perform
the EICAR test.
The EICAR test is a standard and absolutely safe method used to test antivirus system
functioning. It is safe to pass around, because it is not an actual virus, and does not
include any fragments of viral code. Most products react to it as if it were a virus (
though they typically report it with an obvious name, such as "EICAR-AV-Test"). You
can download the EICAR virus from the EICAR website at www.eicar.com, and you will
also find all necessary EICAR test information there.
Try to download the eicar.com file, and save it on your local disk. Immediately after
you confirm downloading of the test file, the Online Shield will react to it with a
warning. This notice demonstrates that AVG is correctly installed on your computer.
From the http://www.eicar.com website you can also download the compressed
version of the EICAR 'virus' (e.g. in the form of eicar_com.zip). Online Shield allows
you to download this file and save it on your local disk but then the Resident Shield
detects the 'virus' as you try to unpack it. If AVG fails to identify the EICAR test file
as a virus, you should check the program configuration again!
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 27
Page 28
6.6. AVG Default Configuration
The default c onfiguration (i.e. how the applic ation is set up right after installation) of
AVG 9 Internet Security is set up by the software vendor so that all components
and functions are tuned up to achieve optimum performance.
Unless you have a real reason to do so, do not change the AVG configuration!
Changes to settings should only be performed by an experienced user.
Some minor editing of AVG components settings is accessible directly from the specific
component user interface. If you feel you need to change the AVG configuration to
better suit your your needs, go to AVG Advanced Settings: select the system menu
item Tools/Advanced settings and edit the AVG configuration in the newly opened
AVG Advanced Settings dialog.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 28
Page 29
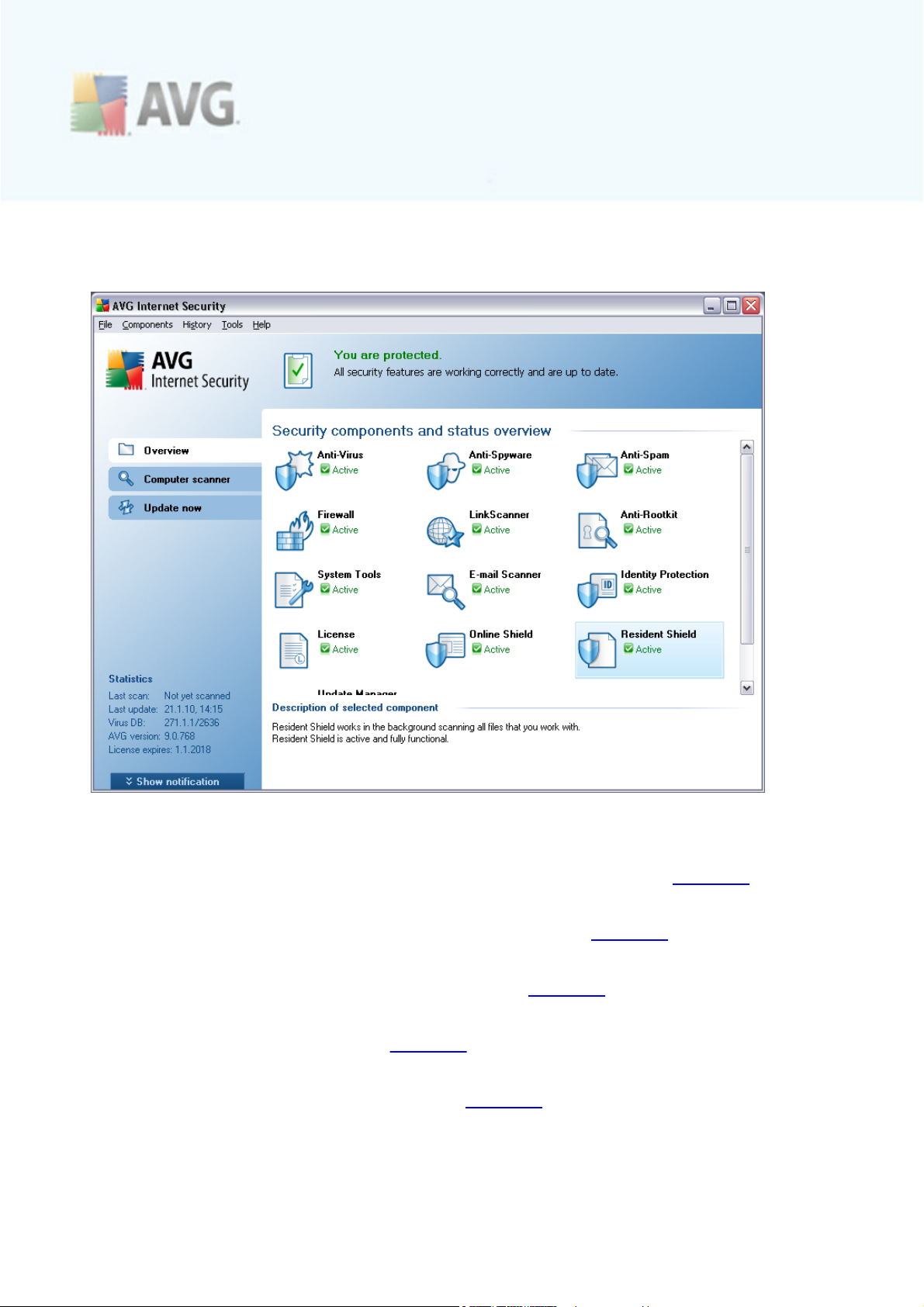
7. AVG User Interface
AVG 9 Internet Security open with the main window:
The main window is divided into several sections:
· System Menu (top system line in the window) is the standard navigation that
allows you to acc ess all AVG components, services, and features - details >>
· Security Status Info (upper section of the window) provides you with
information on the current status of your AVG program - details >>
· Quick Links (left section of the window) allow you to quickly ac cess the most
important and most frequently used AVG tasks - details >>
· Components Overview (central section of the window) offer an overview of
all installed AVG components - details >>
· Statistics (left bottom sec tion of the window) provide you with all statistical
data regarding the programs operation - details >>
· System Tray Icon (bottom right corner of the monitor, on the system tray)
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 29
Page 30
indicates the AVG current status - details >>
7.1. System Menu
The System menu is the standard navigation used in all Windows applic ations. It is located horizontally in the very top part of the AVG 9 Internet Security main window. Use the system menu to ac cess specific AVG components, feature, and services.
The system menu is divided into five main sec tions:
7.1.1. File
· Exit - closes the AVG 9 Internet Security's user interfac e. However, the AVG
application will continue running in the background and your computer will still
be protected!
7.1.2. Components
The Components item of the system menu includes links to all installed AVG components, opening their default dialog page in the user interface:
· System overview - switch to the default user interface dialog with the
overview of all installed components and their status
· Anti-Virus - opens the default page of the Anti-Virus component
· Anti-Rootkit - opens the default page of the Anti-Rootkit component
· Anti-Spyware - opens the default page of the Anti-Spyware c omponent
· Firewall - opens the default page of the Firewall component
· Link Scanner - opens the default page of the Link Scanner component
· Remote Administration - displayed only within AVG network editions in case
you have specified during the installation process you want to have this
component installed
· System Tools - opens the default page of the System Tools
· Anti-Spam - opens the default page of the Anti-Spam c omponent
· E-mail Scanner - opens the default page of the E-mail Scanner component
· ID Protection - opens the default page of the ID Protection component
· License - opens the default page of the License component
· Online Shield - opens the default page of the Online Shield component
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 30
Page 31

· Resident Shield - opens the default page of the Resident Shield component
· Update Manager - opens the default page of the Update Manager
component
7.1.3. History
· Scan results - switches to the AVG testing interface, specifically to the Scan
Results Overview dialog
· Resident Shield Detection - open a dialog with an overview of threats
detected by Resident Shield
· E-mail Scanner Detection - open a dialog with an overview of mail messages
attachments detected as dangerous by the E-mail Scanner component
· Online Shield findings - open a dialog with an overview of threats detected
by Online Shield
· Virus Vault - opens the interface of the quarantine space (Virus Vault) to
where AVG removes all detected infections that cannot be healed automatically
for some reason. Inside this quarantine the infected files are isolated and your
computer's sec urity is guaranteed, and at the same time the infected files are
stored for possible future repair.
· Event History Log - opens the history log interface with an overview of all
logged AVG 9 Internet Security actions.
· Firewall - opens the Firewall settings interface on the Logs tab with a
detailed overview of all Firewall actions
7.1.4. Tools
· Scan computer - switches to the AVG scanning interfac e and launches a scan
of the whole c omputer
· Scan selected folder - switches to the AVG scanning interface and allows you
to define within the tree structure of your computer which files and folders
should be scanned
· Scan file - allows you to run an on-demand test over a single file selected from
the tree structure of your disk
· Update - automatically launches the update process of AVG 9 Internet
Security
· Update from directory - runs the update process from the update files
located in a specified folder on your local disk. However, this option is only
recommended as an emergency, e.g. in situations where there is no connection
to the Internet (for example, your computer is infected and disconnected
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 31
Page 32
from the Internet; your c omputer is connected to a network with no access
to the Internet, etc.). In the newly opened window select the folder where
you have previously placed the update file, and launch the update process.
· Advanced settings - opens the AVG advanced settings dialog where you
can edit the AVG 9 Internet Security configuration. Generally, it is
recommended to keep the default settings of the application as defined by the
software vendor.
· Firewall settings - open a standalone dialog for advanced configuration of
the Firewall component
7.1.5. Help
· Contents - opens the AVG help files
· Get Help Online - opens AVG website (http://www.avg.com/) at the
customer support center page
· Your AVG Web - opens AVG website (http://www.avg.com/)
· About Viruses and Threats - opens the online Virus Encyclopedia where you
can look up detailed information on the identified virus
· Reactivate - opens the Activate AVG dialog with the data you have entered
in the Personalize AVG dialog of the installation process. Within this dialog
you can enter your license number to either replace the sales number (the
number you have installed AVG with), or to replace the old license number (e.
g. when upgrading to a new AVG product).
· Register now - connects to the registration page of AVG website (http://
www.avg.com/). Please fill in your registration data; only customers who
register their AVG product can receive free technical support.
Note: If using the trial version of AVG 9 Internet Security, the latter two
items appear as Buy now and Activate, alowing you to buy the full version of
the program right away. For AVG 9 Internet Security installed with a sales
number, the items display as Register and Activate. For more information
please consult the License section of this documentation.
· About AVG - opens the Information dialog with five tabs providing data on
program name, program and virus database version, system info, license
agreement, and contact information of AVG Technologies CZ.
7.2. Security Status Info
The Security Status Info section is located in the upper part of the AVG main
window. Within this sec tion you will always find information on the current security
status of your AVG 9 Internet Security. Please see an overview of icons possibly
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 32
Page 33

depicted in this section, and their meaning:
The green icon indicates that your AVG is fully functional. Your computer is
completely protected, up to date and all installed components are working
properly.
The orange icon warns that one or more components are incorrectly
configured and you should pay attention to their properties/settings. There is no
critical problem in AVG and you have probably decided to switch some
component off for some reason. You are still protected by AVG. However, please
pay attention to the problem component's settings! Its name will be provided in
the Security Status Info section.
This icon also appears if for some reason you have decided to ignore a
component's error status (the "Ignore component state" option is available from
the context menu opened by a right-click over the respective component's icon
in the component overview of the AVG main window). You may need to use this
option in a specific situation but it is strictly recommended to switch off the "
Ignore component state" option as soon as possible.
The red icon indicates that AVG is in critical status! One or more
components does not work properly and AVG cannot protect your computer.
Please pay immediate attention to fixing the reported problem. If you are not
able to fix the error yourself, contac t the AVG technical support team.
It is strongly recommended that you pay attention to Security Status Info and in
case the report indicates any problem, go ahead and try to solve it immediately.
Otherwise your computer is at risk!
Note: AVG status information can also be obtained at any moment from the system
tray icon.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 33
Page 34

7.3. Quick Links
Quick links (in the left section of the AVG User Interface) allow you to immediately access the most important and most frequently used AVG features:
· Overview - use this link to switc h from any currently opened AVG interface to
the default one with an overview of all installed components - see chapter
Components Overview >>
· Computer scanner - use this link to open the AVG scanning interfac e where
you can run tests directly, schedule scans, or edit their parameters - see
chapter AVG Scanning >>
· Update now - this link open the updating interface, and launches the AVG
update process immediately - see chapter AVG Updates >>
These links are accessible from the user interfac e at all times. Once you use a quick
link to run a specific process, the GUI will switch to a new dialog but the quick links
are still available. Moreover, the running process is further graphically depicted.
7.4. Components Overview
The Components Overview section is located in the central part of the AVG User
Interface. The sec tion is divided into two parts:
· Overview of all installed components consisting of a panel with the
component's icon and the information of whether the respective component is
active or inactive
· Description of a selected c omponent
Within the AVG 9 Internet Security the Components Overview section contains
information on the following components:
· Anti-Virus ensures that your computer is protected from viruses trying to
enter your computer - details >>
· Anti-Spyware ensures that your computer is protected from spyware and
adware - details >>
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 34
Page 35
· Anti-Spam c hecks all incoming e-mail messages and marks unwanted e-mails
as SPAM - details >>
· Firewall controls how your computer exchanges data with other computers on
the Internet or local network - details >>
· Link Scanner checks the search results displayed in your internet browser -
details >>
· Remote Administration is only displayed within AVG network editions in case
you have specified during the installation process you want to have this
component installed
· Anti-Rootkit detec ts programs and technologies trying to camouflage malware
- details >>
· System Tools offers a detailed summary of the AVG environment and
operating system information - details >>
· E-mail Scanner chec ks all incoming and outgoing mail for viruses - details >>
· ID Protection - anti-malware component focused on preventing identity
thieves from stealing your personal digital valuables - details >>
· License displays the license number, type and expiration date - details >>
· Online Shield scans all data being downloaded by a web browser - details >>
· Resident Shield runs in the bac kground and scans files as they are copied,
opened or saved - details >>
· Update Manager controls all AVG updates - details >>
Single-click any component's icon to highlight it within the components overview. At
the same time, the component's basic functionality description appears in the bottom
part of the user interfac e. Double-c lick the icon to open the c omponents own
interface with a list of basic statistical data.
Right-click you mouse over a component's icon to expand a c ontext menu: besides
opening the component's graphic interface you can also select to Ignore component
state. Select this option to express you are aware of the component's error state but
for some reason you wish to keep your AVG so and you do not want to be warned by
the system tray icon.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 35
Page 36
7.5. Statistics
The Statistics section is located in the left bottom part of the AVG User Interface. It
offers a list of information regarding the program's operation:
· Last scan - provides the date when the last scan was performed
· Last update - provides the date when the last update was launched
· Virus DB - informs you about the c urrently installed version of the virus
database
· AVG version - informs you about the AVG version installed (the number is in
the form of 9.0.xxx, where 9.0 is the product line version, and xxx stands for
the number of the build)
· License expires - provides the date of your AVG license expiration
7.6. System Tray Icon
System Tray Icon (on your Windows taskbar) indicates the c urrent status of your
AVG 9 Internet Security. It is visible at all times on your system tray, no matter
whether your AVG main window is opened or closed.
If in full color , the System Tray Icon indicates that all AVG components are ac tive
and fully functional. Also, AVG system tray icon can be displayed in full color if AVG is
in error state but you are fully aware of this situation and you have deliberately
decided to Ignore the component state.
An icon with an exclamation mark indicates a problem (inactive component, error
status, etc.). Double-click the System Tray Icon to open the main window and edit a
component.
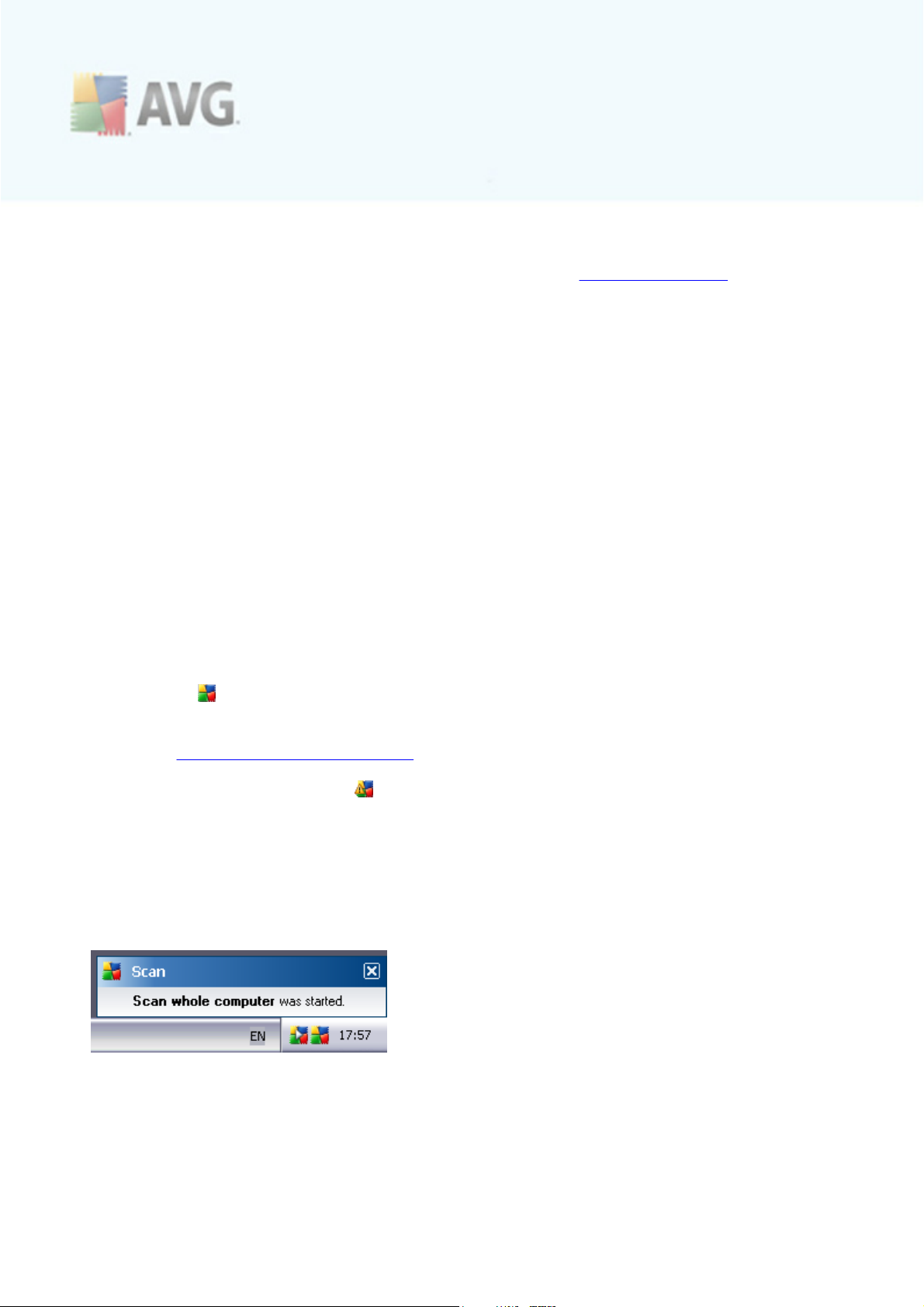
The system tray icon further informs on current AVG activities and possible status
changes in the program (e.g. automatic launch of a scheduled scan or update,
Firewall profile switch, a component's status c hange, error status occurrence, ...) via
a pop-up window opened from the AVG system tray icon:
The System Tray Icon can also be used as a quick link to access the AVG main window at any time - double click on the icon. By right-click on the System Tray Icon you open a brief context menu with the following options:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 36
Page 37

· Open AVG User Interface - click to open the AVG User Interface
· Scans - click to open the context menu of predefined scans (Scan Whole
Computer, Scan Specific Files or Folders, Anti-Rootkit scan) and select the
required scan, it will be launched immediately
· Firewall - c lick to open the context menu of Firewall settings options where
you can edit the major parameters:Firewall status (Firewall enabled/Firewall
disabled/Emergency mode), gaming mode switchingand Firewall profiles
· Update now - launches an immediate update
· Help - opens the help file on the start page
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 37
Page 38

8. AVG Components
8.1. Anti-Virus
8.1.1. Anti-Virus Principles
The antivirus software's sc anning engine scans all files and file activity (opening/
closing files, etc.) for known viruses. Any detected virus will be blocked from taking
any ac tion and will then be cleaned or quarantined. Most antivirus software also uses
heuristic scanning, where files are scanned for typical virus characteristics, so called
viral signatures. This means that the antivirus scanner can detect a new, unknown
virus, if the new virus contains some typical characteristics of existing viruses.
The important feature of antivirus protection is that no known virus can run on
the computer!
Where just a single technology might fall short of detecting or identifying a virus, AntiVirus combines several technologies to ensure that your computer is protected from
viruses:
· Scanning - searching for character strings that are characteristic of a given
virus
· Heuristic analysis - dynamic emulation of the scanned object’s instructions in a
virtual computer environment
· Generic detection - detection of instructions c haracteristic of the given virus/
group of viruses
AVG is also able to analyze and detect executable applic ations or DLL libraries that
could be potentially unwanted within the system. We call such threats Potentially
Unwanted Programs (various kinds of spyware, adware etc.). Furthermore, AVG scans
your system registry for suspicious entries, temporary Internet files and tracking
cookies, and allows you to treat all potentially harmful items in the same way as any
other infection.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 38
Page 39

8.1.2. Anti-Virus Interface
The Anti-Virus component's interface provides some basic information on the
component's functionality, information on the component's current status (Anti-Virus
component is active.), and a brief overview of Anti-Virus statistics:
· Infection definitions - number provides the count of viruses defined in the
up-to-date version of the virus database
· Latest database update - specifies when and at what time the virus
database was last updated
· Database version - defines the number of the currently installed virus
database version; and this number increases with every virus base update
There is just one operating button available within this component's interface (Back) -
press the button to return to the default AVG user interface (components overview).
8.2. Anti-Spyware
8.2.1. Anti-Spyware Principles
Spyware is usually defined as a type of malware, i.e. software, that gathers
information from a user's computer without the user's knowledge or consent. Some
spyware applications may also be installed on purpose and often contain
advertisements, window pop-ups or different types of unpleasant software.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 39
Page 40
Currently, the most common source of infection is websites with potentially dangerous
content. Other methods of transmission, such as via e-mail or transmission by worms
and viruses are also prevalent. The most important protection is to use an always-on
background scanner, Anti-Spyware, that works like a resident shield and scans your
applications in the background as you run them.
There is also the potential risk that malware has been transmitted to your computer
prior to AVG installation, or that you have neglected to keep your AVG 9 Internet
Security up-to-date with the latest database and program updates. For this reason,
AVG allows you to fully scan your computer for malware/spyware using the scanning
feature. It also detects sleeping and non-active malware, i.e. malware that has been
downloaded but not yet ac tivated.
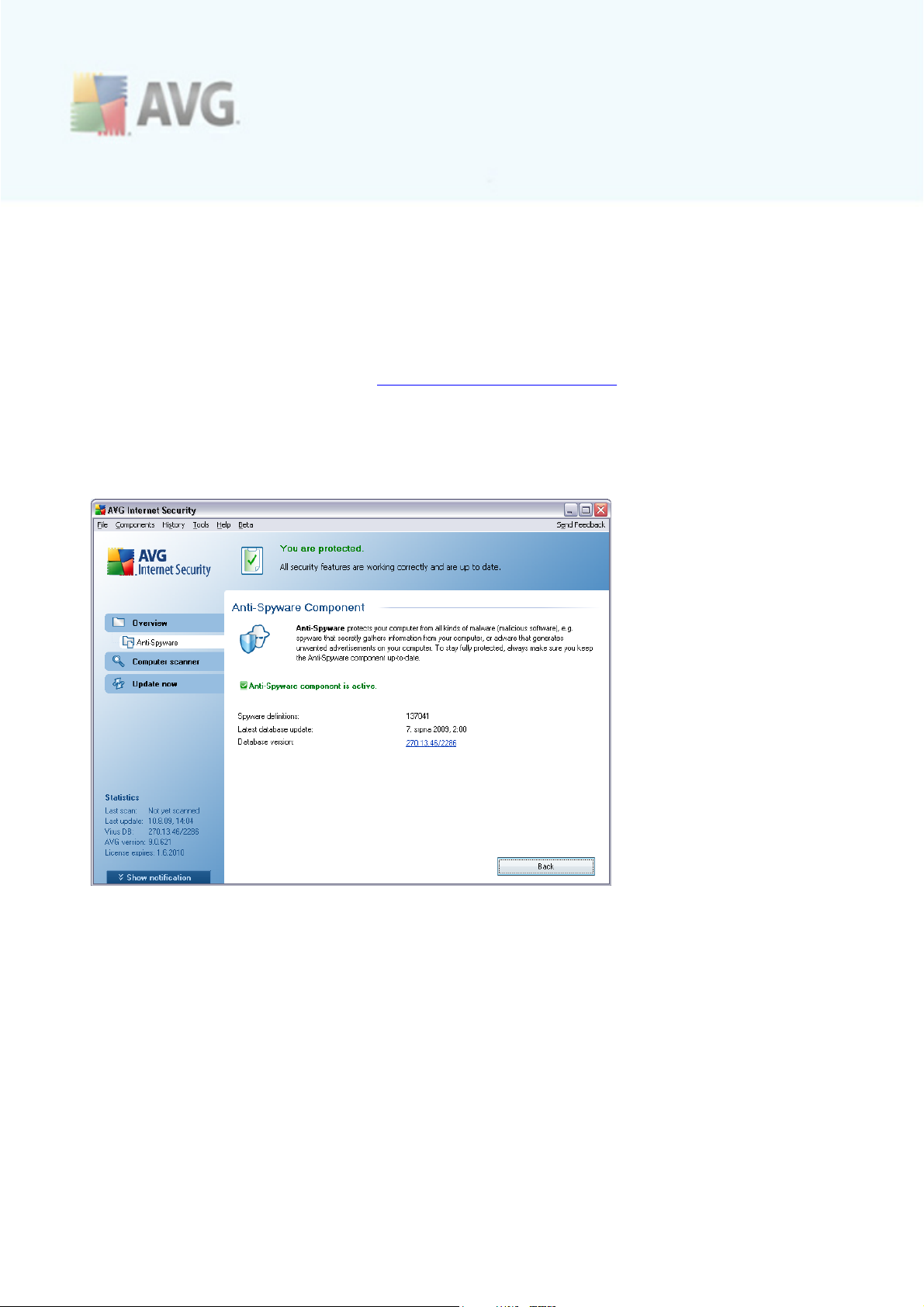
8.2.2. Anti-Spyware Interface
The Anti-Spyware component's interface provides a brief overview on the
component's functionality, information on the component's current status (Anti-
Spyware component is active.), and some Anti-Spyware statistics:
· Spyware definitions - number provides the count of spyware samples defined
in the latest spyware database version
· Latest database update - specifies when and at what time the spyware
database was updated
· Database version - defines the number of the latest spyware database
version; and this number increases with every virus base update
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 40
Page 41

There is just one operating button available within this component's interface (Back) -
press the button to return to the default AVG user interface (components overview).
8.3. Anti-Spam
Spam refers to unsolicited e-mail, mostly advertising a product or service that is mass
mailed to a huge number of e-mail addresses at a time, filling recipients’ mail boxes.
Spam does not refer to legitimate commercial e-mail for which consumers have given
their consent. Spam is not only annoying, but also can often be a source of sc ams,
viruses or offensive c ontent.
8.3.1. Anti-Spam Principles
AVG Anti-Spam checks all incoming e-mail messages and marks unwanted e-mails as
spam. AVG Anti-Spam can modify the subject of the email (that has been identified
as spam) by adding a special text string. Then you can then easily filter your emails in
your email client.
AVG Anti-Spam component uses several analyzing methods to process each e-mail
message, offering maximum possible protection against unwanted e-mail messages.
AVG Anti-Spam uses a regularly updated database for the detec tion of spam. It is
also possible to use RBL servers (public databases of "known spammer" email
addresses) and to manually add email addresses to your Whitelist (never mark as
spam) and Blacklist (always mark as spam).
8.3.2. Anti-Spam Interface
In the Anti-Spam component's dialog you will find a brief text describing the
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 41
Page 42

component's functionality, information on its current status (Anti-Spam component is
active.), and the following statistics:
· Database release - spec ifies when and at what time the spam database was
updated and published
· Spamcatcher version - defines the number of the latest version of the anti-
spam engine
There is just one operating button available within this component's interface (Back) -
press the button to return to the default AVG user interface (components overview).
Please note: The software vendor has set up all AVG components to give optimum
performance. Unless you have a real reason to do so, do not change the AVG
configuration. Any changes to settings should only be performed by an experienced
user. If you need to change AVG configuration, select the system menu item Tools /
Advanced settings and edit the AVG configuration in the newly opened AVG
Advanced Settings dialog.
8.4. Anti-Rootkit
A rootkit is a program designed to take fundamental control of a computer system,
without authorization by the system's owners and legitimate managers. Access to the
hardware is rarely required as a rootkit is intended to seize control of the operating
system running on the hardware. Typically, rootkits act to obscure their presence on
the system through subversion or evasion of standard operating system security
mechanisms. Often, they are also Trojans as well, thus fooling users into believing
they are safe to run on their systems. Tec hniques used to accomplish this can include
concealing running processes from monitoring programs, or hiding files or system data
from the operating system.
8.4.1. Anti-Rootkit Principles
AVG Anti-Rootkit is a specialized tool detecting and effec tively removing dangerous
rootkits, i.e. programs and technologies that can camouflage the presence of malicious
software on your computer. AVG Anti-Rootkit is able to detect rootkits based on a
predefined set of rules. Please note, that all rootkits are detec ted (not just the
infected). In case AVG Anti-Rootkit finds a rootkit, it does not necessarily mean the
rootkit is infected. Sometimes, rootkits are used as drivers or they are a part of
correct applications.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 42
Page 43

8.4.2. Anti-Rootkit Interface
The Anti-Rootkit user interface provides a brief description of the c omponent's
functionality, informs on the component's current status (Anti-Rootkit component is
active.) and also brings information on the last time the Anti-Rootkit test was
launched.
In the bottom part of the dialog you can find the Anti-Rootkit settings section where
you can set up some elementary functions of the rootkit presence sc anning. First,
mark up the respective check-boxes to specify objects that should be scanned:
· Scan applications
· Scan DLL libraries
· Scan drivers
Further you can pick the rootkit scanning mode:
· Quick rootkit scan - scans all running processes, loaded drivers and the
system folder (typically c:\Windows)
· Full rootkit scan - scans all running processes, loaded drivers, the system
folder (typically c :\Windows), plus all local disks (including the flash disk, but
excluding floppy disk/CD drives)
Control buttons available:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 43
Page 44
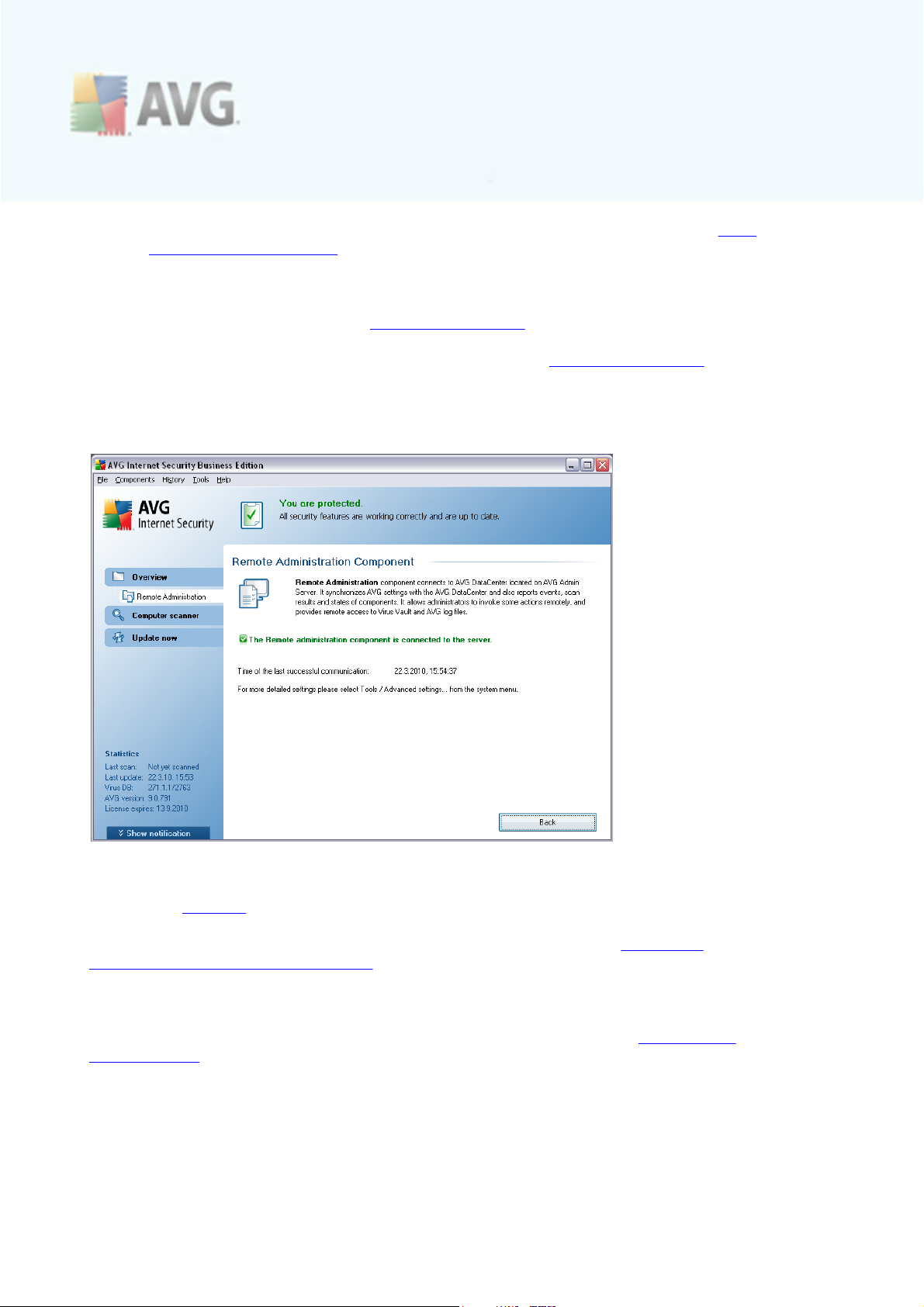
· Search for rootkits - since the rootkit scan is not an implicit part of the Scan
of the whole computer, you can run the rootkit scan directly from the Anti-
Rootkit interfac e using this button
· Save changes - press this button to save all changes made in this interface
and to return to the default AVG user interface (c omponents overview)
· Cancel - press this button to return to the default AVG user interface
(components overview) without having saved any changes you made
8.5. Remote Administration
The Remote Administration component only displays in the user interface of AVG 9 Internet Security in case you have installed the network edition of your product (see
component License). In the Remote Administration dialog you can find the
information on whether the component is active and connected to server. All settings
of the Remote Administration component is to be done within the Advanced
Settings / Remote Administration.
For detailed description of the c omponent's options and functionality within the AVG
Remote Administration system please refer to the spec ific documentation dedicated to
this topic exclusivety. This documentation is available for download at AVG website (
www.avg.com), in the Support center / Download / Documentation sec tion.
Control buttons
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 44
Page 45
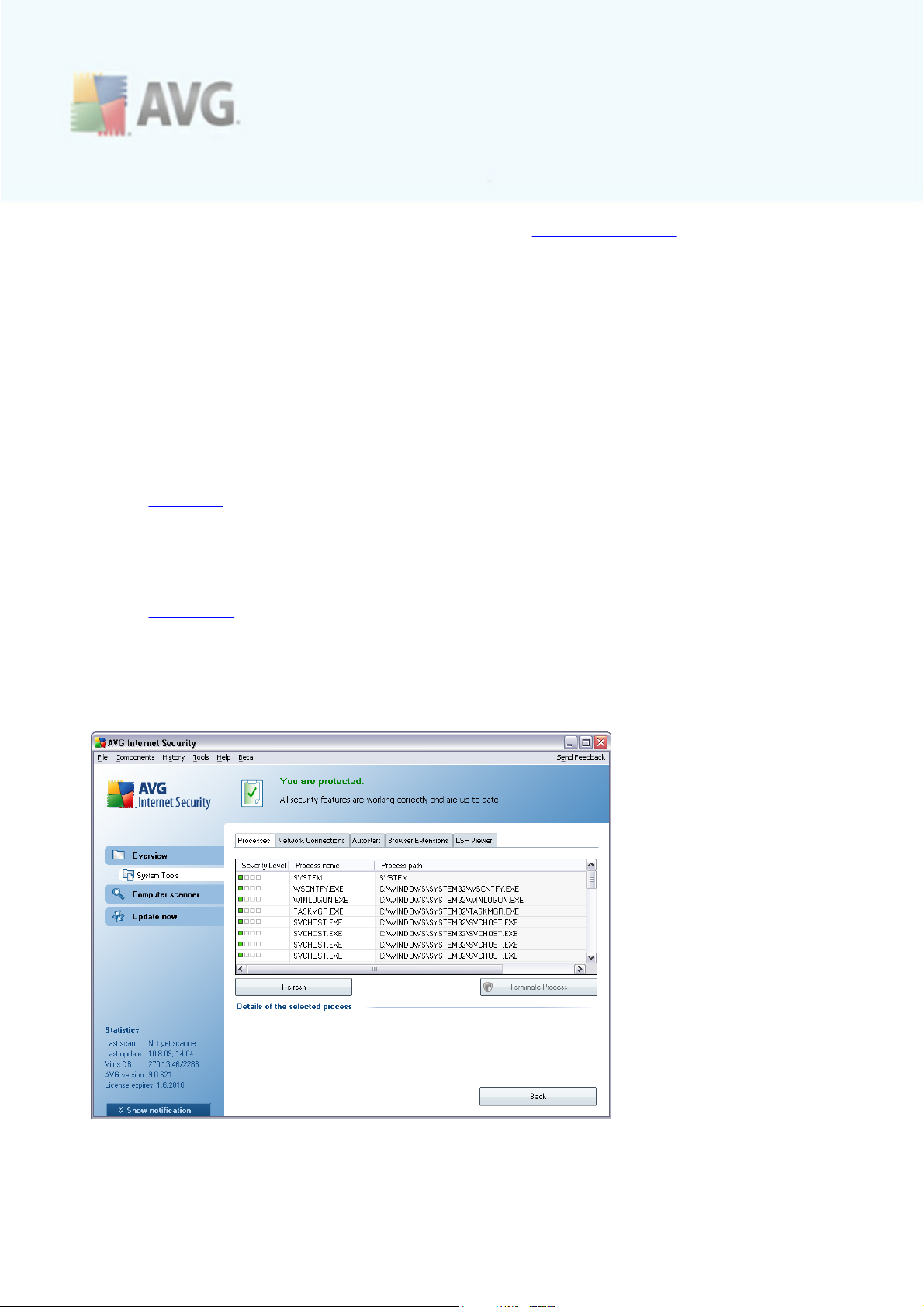
· Back - press this button to return to the default AVG user interface (
components overview).
8.6. System Tools
System Tools refer to tools offering a detailed summary of the AVG 9 Internet Security environment and the operating system. The component displays an overview
of:
· Processes - list of processes (i.e. running applications) that are currently
active on your computer
· Network connections - list of currently ac tive connections
· Autostart - list of all applications that are executed during Windows system
start-up
· Browser Extensions - list of plug-ins (i.e. applications) that are installed inside
your Internet browser
· LSP Viewer - list of Layered Service Providers (LSP)
Specific overviews can also be edited but this is only recommended for highly
experienced users!
8.6.1. Processes
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 45
Page 46
The Processes dialog contains a list of processes (i.e. running applications) that are
currently active on your computer. The list is divided into several columns:
· Severity Level – graphical identification of the respec tive process severity on
a four-levels scale from less important ( ) up to critical ( )
· Process name - name of the running process
· Path - physical path to the running process
· Window - if applicable, indicates application Window name
· Internet - indicates if the running process also connects to the Internet (Yes/
No)
· PID - process identification number is a unique Windows internal process
identifier
Control buttons
The control buttons available within the System Tools interface are as follows:
· Refresh - updates the list of processes according to the c urrent status
· Terminate Process - you can select one or more applic ations and then
terminate them by pressing this button. We strongly suggest not to
terminate any applications, unless you are absolutely sure that they
represent a real threat!
· Back - switches you bac k to the default AVG user interface (components
overview).
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 46
Page 47

8.6.2. Network Connections
The Network Connections dialog contains a list of currently ac tive connections. The
list is divided into the following columns:
· Application - name of the application related to the connection (with the
exception of Windows 2000 where the information is not available)
· Protocol - transmission protocol type used for the c onnection:
o
TCP - protocol used in conjunction with Internet Protocol (IP) to transmit
information over the Internet
o
UDP - alternative to TCP protoc ol
· Local address - IP address of the local computer and the port number used
· Remote address - IP address of the remote computer and the port number
connected to. If possible, it will also look up the host name of the remote
computer.
· State - indicates the most probable current state (Connected, Server should
close, Listen, Active c lose finished, Passive close, Active c lose)
To list only external connections, tick the Hide local connections checkbox in the
bottom section of the dialog under the list.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 47
Page 48

Control buttons
The control buttons available are:
· Terminate Connection - closes one or more connections selected in the list
· Terminate Process - closes one or more applications related to connections
selected in the list
· Back - switch back to the default AVG user interface (c omponents
overview).
Sometimes it is possible to terminate only applications that are currently in the
connected state. We strongly suggest not to terminate any connections, unless
you are absolutely sure that they represent a real threat!
8.6.3. Autostart
The Autostart dialog shows a list of all applications that are executed during Windows system start-up. Very often, several malware applications add themselves automatically to the start-up registry entry.
You can delete one or more entries by selecting them and pressing the Remove
selected button. The Back button switches you back to the default AVG user
interface (components overview).
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 48
Page 49
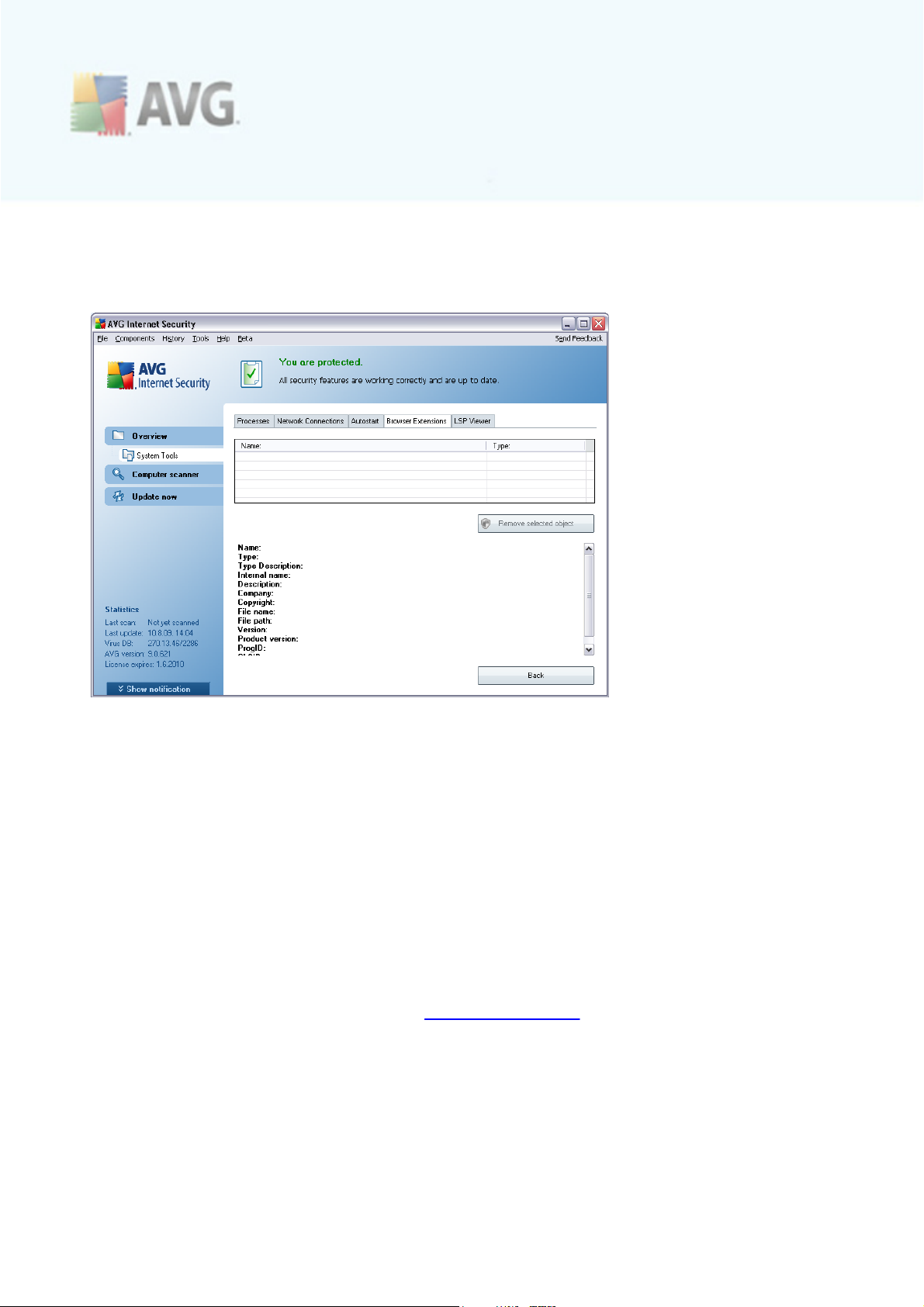
We strongly suggest not to delete any applications from the list, unless you are
absolutely sure that they represent a real threat!
8.6.4. Browser Extensions
The Browser Extensions dialog contains a list of plug-ins (i.e. applications) that are
installed inside your Internet browser. This list may contain regular applic ation plug-ins
as well as potential malware programs. Click on an object in the list to obtain detailed
information on the selected plug-in that will be displayed in the bottom section of the
dialog.
Control buttons
The control buttons available on the Browser Extension tab are:
· Remove selected object - removes the plug-in that is currently highlighted in the
list. We strongly suggest not to delete any plug-ins from the list, unless you
are absolutely sure that they represent a real threat!
· Back - switches you bac k to the default AVG user interface (components
overview)
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 49
Page 50
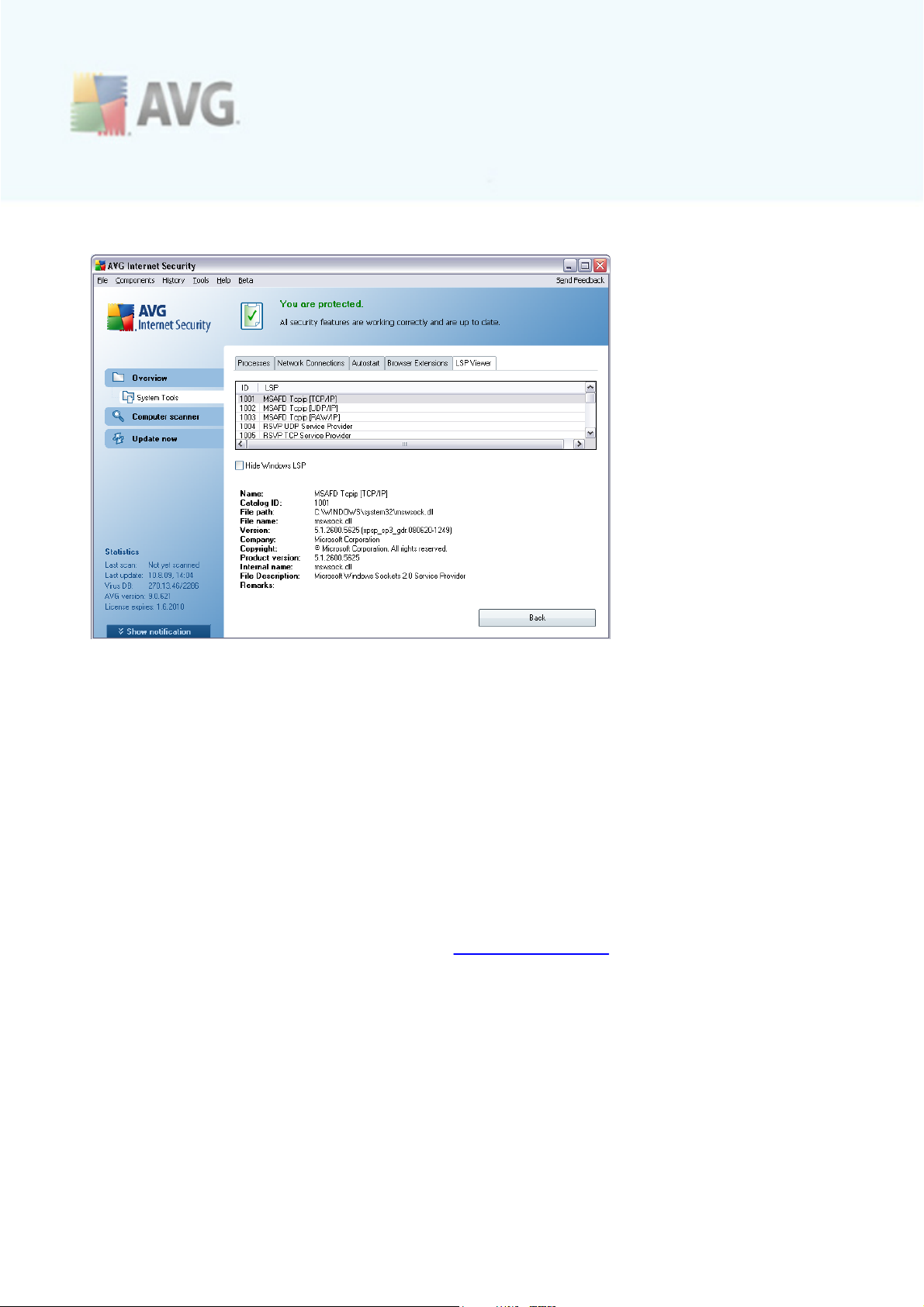
8.6.5. LSP Viewer
The LSP Viewer dialog shows a list of Layered Service Providers (LSP).
A Layered Service Provider (LSP) is a system driver linked into the networking
services of the Windows operating system. It has access to all data entering and
leaving the computer, including the ability to modify this data. Some LSPs are
necessary to allow Windows to c onnect you to other computers, including the
Internet. However, certain malware applications may also install themselves as an LSP,
thus having access to all data your computer transmits. Therefore, this review may
help you to c heck all possible LSP threats.
Under certain circumstances, it is also possible to repair broken LSPs (for example
when the file has been removed but the registry entries remain untouched). A new
button for fixing the issue is displayed once a repairable LSP is discovered.
To include Windows LSP in the list, uncheck the Hide Windows LSP checkbox. The
Back button switches you back to the default AVG user interface (components
overview).
8.7. Firewall
Firewall is a system that enforces an access control policy between two or more
networks by blocking/permitting traffic. Firewall contains a set of rules that protect
the internal network from attacks originating outside (typically from the Internet) and
controls all communication on every single network port. The communication is
evaluated ac cording to the defined rules, and then either allowed or forbidden. If
Firewall recognizes any intrusion attempts, it “blocks” the attempt and does not allow
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 50
Page 51
the intruder access to the computer.
Firewall is configured to allow or deny internal/external communication (both ways, in
or out) through defined ports, and for defined software applications. For example, the
firewall could be configured to only permit web data to flow in and out using Microsoft
Explorer. Any attempt to transmit web data by any other browser would be blocked.
Firewall protects your personally-identifiable information from being sent from your
computer without your permission. It controls how your computer exchanges data with
other computers on the Internet or local network. Within an organization, the firewall
also protects the single computer from attacks initiated by internal users on other
computers in the network.
Recommendation: Generally it is not recommended to use more than one firewall on
an individual computer. The security of the computer is not enhanced if you install
more firewalls. It is more probable that some conflicts between these two
applications will occur. Therefore we recommend that you use only one firewall on
your computer and deactivate all others, thus eliminating the risk of possible conflict
and any problems related to this.
8.7.1. Firewall Principles
In AVG, the Firewall component controls all traffic on every network port of your
computer. Based on the defined rules, the Firewall evaluates applications that are
either running on your computer (and want to connect to the Internet/local network),
or applications that approach your computer from outside trying to connect to your
PC. For eac h of these applications the Firewall then either allows or forbids the
communication on the network ports. By default, if the application is unknown (i.e. has
no defined Firewall rules), the Firewall will ask you if you wish to allow or block the
communication attempt.
Note: AVG Firewall is not intended for server platforms!
What AVG Firewall can do:
· Allow or block communication attempts of known applications automatically, or
ask you for confirmation
· Use complete profiles with predefined rules, according to your needs
· Switc h profiles automatically when connecting to various networks, or using
various network adapters
8.7.2. Firewall Profiles
The Firewall allows you to define specific security rules based on whether your
computer is located in a domain, or it is a standalone computer, or even a notebook.
Each of these options requires a different level of protection, and the levels are
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 51
Page 52
covered by the respective profiles. In short, a Firewall profile is a specific
configuration of Firewall component, and you can use a number of such predefined
configurations.
Available profiles
· Allow all - a Firewall system profile that has been pre-set by the
manufac turer and is always present. When this profile is activated, all network
communication is allowed and no safety policy rules are applied, as if the
Firewall protec tion was switched off (i.e. all applications are allowed but
packets are still being chec ked - to completely disable any filtering you need
to disable Firewall). This system profile cannot be duplicated, deleted, and its
settings cannot be modified.
· Block all - a Firewall system profile that has been pre-set by the
manufac turer and is always present. When this profile is activated, all network
communication is blocked, and the c omputer is neither accessible from outer
networks, nor can communicate outside. This system profile cannot be
duplicated, deleted, and its settings cannot be modified.
· Custom profiles:
o
Directly connected to the Internet – suitable for common desktop
home computers c onnected directly to the Internet or notebooks
connecting to the Internet outside the safe company network. Select
this option if you connecting from home, or you are in a small company
network with no c entral control. Also, select this option when traveling
and connecting with your notebook from various unknown and possibly
dangerous places (internet café, hotel room etc.). More restrictive rules
will be c reated, as it is assumed that these computers have no additional
protection and therefore require the maximum protection.
o
Computer in domain – suitable for computers in a local network, e.g.
school or corporate network. It is assumed that the network is protected
by some additional measures so that the security level can be lower than
for a standalone computer.
o
Small home or office network – suitable for computers in a small
network, e.g. at home or in a small business, typically only several
computers c onnected together, without a "central" administrator.
Profile switching
The profile switc hing feature allows the Firewall to switch automatically to the
defined profile when using a certain network adapter, or when connected to a certain
type of network. If no profile has been assigned to a network area yet, then upon
next connection to that area, the Firewall will display a dialog asking you to assign a
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 52
Page 53

profile.
You can assign profiles to all local network interfac es or areas and specify further
settings in the Areas and Adapters Profiles dialog, where you can also disable the
feature if you do not wish to use it (then, for any kind of connection, the default
profile will be used).
Typically, users who have a notebook and use various types of c onnection will find
this feature useful. If you have a desktop c omputer, and only ever use one type of
connection (e.g. cable connection to the Internet), you do not have to bother with
profile switching as most likely you will never use it.
8.7.3. Firewall Interface
The Firewall's interface provides some basic information on the component's
functionality, and a brief overview of Firewall statistics:
· Firewall has been enabled for - time elapsed since Firewall was last launched
· Blocked packets - number of blocked packets from the entire amount of
packets chec ked
· Overall packets - number of all packets checked during the Firewall run
Basic component configuration
· Select Firewall profile - from the roll-down menu select one of the defined
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 53
Page 54
profiles - two profiles are available at all times (the default profiles named
Allow all and Block all), other profiles were added manually by profile editing in
the Profiles dialog in Firewall Settings.
· Enable gaming mode - Check this option to ensure that when running full-
screen applications (games, PowerPoint presentations etc.), the Firewall will
not display dialogs asking you whether you want to allow or block
communication for unknown applic ations. In case an unknown application tries
to communicate over the network at that time, the Firewall will allow or block
the attempt automatically acc ording to settings in the c urrent profile. With the
gaming mode on, all scheduled tasks (scans, updates) are postponed till the
application is closed.
· Firewall status:
o
Firewall enabled - select this option to allow communication to those
applications that are assigned as 'allowed' in the set of rules defined
within selected Firewall profile
o
Firewall disabled - this option switches Firewall off completely, all
network traffic is allowed but not checked!
o
Emergency mode (block all internet traffic) - select this option to
block all traffic on every single network port; Firewall is still running but
all network traffic is stopped
Please note: The software vendor has set up all AVG components to give optimum
performance. Unless you have a real reason to do so, do not change the AVG
configuration. Any changes to settings should only be performed by an experienced
user. If you need to change Firewall configuration, select the system menu item
Tools/Firewall settings and edit the Firewall configuration in the newly opened
Firewall Settings dialog.
Control buttons
· Configuration wizard - press the button to switch to the respective dialog (
used within installation process) called Computer Usage Selection where you
can specify the Firewall component configuration
· Save changes - press this button to save and apply any c hanges made in this
dialog
· Cancel - press this button to return to the default AVG user interface (
components overview)
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 54
Page 55
8.8. E-mail Scanner
One of the most common sources of viruses and trojans is via e-mail. Phishing and
spam make e-mail an even greater source of risks. Free e-mail accounts are more likely
to receive such malicious e-mails (as they rarely employ anti-spam technology), and
home users rely quite heavily on such e-mail. Also home users, surfing unknown sites
and filling in online forms with personal data (such as their e-mail address) increase
exposure to attacks via e-mail. Companies usually use corporate e-mail accounts and
employ anti-spam filters etc, to reduce the risk.
8.8.1. E-mail Scanner Principles
Personal E-mail Scanner scans incoming/outgoing e-mails automatically. You can use
it with e-mail clients that do not have their own plug-in in AVG (but can be also used
to scan e-mail messages for e-mail clients that AVG supports with a specific plug-in, i.
e. Microsoft Outlook, and The Bat). Primarily, it is to be used with e-mail applications
like Outlook Express, Mozilla, Incredimail, etc.
During AVG installation AVG there are automatic servers created for e-mail control:
one for checking incoming e-mails and the sec ond one for checking outgoing e-mails.
Using these two servers e-mails are automatically chec ked on ports 110 and 25 (
standard ports for sending/rec eiving e-mails).
E-mail Scanner works as an interface between e-mail client and e-mail servers on the Internet.
· Incoming mail: While receiving a message from the server, the E-mail
Scanner component tests it for viruses, removes infected attachments, and
adds certification. When detected, viruses are quarantined in Virus Vault
immediately. Then the message is passed to the e-mail client.
· Outgoing mail: Message is sent from e-mail client to E-mail Sc anner; it tests
the message and its attachments for viruses and then sends the message to
the SMTP server (scanning of outgoing e-mails is disabled by default, and can
be set up manually).
Note: AVG E-mail Scanner is not intended for server platforms!
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 55
Page 56

8.8.2. E-mail Scanner Interface
In the E-mail Scanner c omponent's dialog you can find a brief text describing the
component's functionality, information on its current status (E-mail Scanner is active.
), and the following statistics:
· Total e-mails scanned - how many e-mail messages were scanned since the
E-mail Scanner was last launched (if needed, this value can be reset; e.g. for
statistic purposes - Reset value)
· Threats found and blocked - provides the number of infections detected in e-
mail messages since the last E-mail Scanner launch
· Installed e-mail protection - information about a specific e-mail protection
plug-in referring to your default installed e-mail c lient
Basic component configuration
In the bottom part of the dialog you can find the sec tion named E-mail Scanner
settings where you can edit some elementary features of the component's
functionality:
· Scan incoming messages - c heck the item to specify that all e-mails deliver
ed to your account should be scanned for viruses. By default, this item is on,
and it is recommended not to change this setting!
· Scan outgoing messages - check the item to confirm all e-mail sent from
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 56
Page 57

your account should be scanned for viruses. By default, this item is off.
· Display notification icon while E-mail is being scanned - check the item to
confirm you want to be informed via notification dialog displayed over the AVG
icon on the system tray during the scanning of your mail via E-mail Scanner
component. By default, this item is on, and it is recommended not to change
this setting!
The advanced c onfiguration of the E-mail Scanner component is accessible via the
Tools/Advanced settings item of the system menu; however advanced
configuration is recommended for experienced users only!
Please note: The software vendor has set up all AVG components to give optimum
performance. Unless you have a real reason to do so, do not change the AVG
configuration. Any changes to settings should only be performed by an experienced
user. If you need to change AVG configuration, select the system menu item Tools /
Advanced settings and edit the AVG configuration in the newly opened AVG
Advanced Settings dialog.
Control buttons
The control buttons available within the E-mail Scanner interface are as follows:
· Save changes - press this button to save and apply any c hanges made in this
dialog
· Cancel - press this button to return to the default AVG user interface
(components overview)
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 57
Page 58

8.8.3. E-mail Scanner Detection
In the E-mail Scanner detection dialog (acc essible via system menu option History / E-mail Sc anner detection) you will be able to see a list of all findings detected by the
E-mail Scanner component. For eac h detec ted object the following information is
provided:
· Infection- description (possibly even name) of the detected object
· Object - object location
· Result - action performed with the detected object
· Detection time - date and time the suspicious object was detected
· Object Type - type of the detected object
In the bottom part of the dialog, under the list, you will find information on total
number of detected objects listed above. Further you can export the entire list of
detected objects in a file (Export list to file) and delete all entries on detected
objects (Empty list).
Control buttons
The control buttons available within the E-mail Scanner detection interface are as
follows:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 58
Page 59

· Refresh list - updates the list of detected threats
· Back - switches you bac k to the previously displayed dialog
8.9. ID Protection
AVG Identity Protection is an anti-malware product that is foc used on preventing
identity thieves from stealing your passwords, bank account details, credit card
numbers and other personal digital valuables from all kinds of malicious software (
malware) that target your PC. It makes sure that all programs running on your PC are
operating correctly. AVG Identity Protection spots and blocks suspicious behavior on
a continuous basis and protects your computer from all new malware.
8.9.1. ID Protection Principles
AVG Identity Protection is an anti-malware component that protec ts you from all
kinds of malware (spyware, bots, identity theft, ...) using behavioral technologies and
provide zero day protection for new viruses. As malware gets sophisticated and comes
in a form of normal programs that can open up your PC to the remote attacker for
identity theft, AVG Identity Protection secures you from these new execution based
malware. It is a complimentary protection to AVG Anti-Virus that protec ts you from
file based and known viruses using signature mechanism and sc anning.
We strongly recommend you have the both AVG Anti-Virus and AVG Identity
Protection components installed, in order to have complete protection for your
PC.
8.9.2. ID Protection Interface
The Identity Protection component interface provides a brief description of the
component's basic functionality, its status (AVG Identity Protection is active and fully
functional.) and some statistical data:
· Malware items removed - gives the number of applications detected as
malware, and removed
· Processes monitored - number of currently running applications that are
being monitored by IDP
· Behaviors monitored - number of specific ac tions running within the
monitored applications
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 59
Page 60

Basic component configuration
In the bottom part of the dialog you will find the Identity Protection settings section
where you can edit some elementary features of the component's functionality:
· Identity Protection is active - (on by default): check to activate the IDP
component, and to open further editing options.
In some cases, Identity Protection may report that some legitimate file is
suspicious or dangerous. Since Identity Protection detects threats based on
their behavior, this usually oc curs when some program tries to monitor key
presses, install other programs or a new driver is installed on the computer.
Therefore please select one of the following options spec ifying Identity
Protection component's behavior in case of a suspicious activity detection:
o
Always prompt - if an application is detected as malware, you will be
asked whether it should be blocked (this option is on by default and it is
recommended not to change it unless you have a real reason to do so)
o
Automatically quarantine detected threats - all applic ations detected
as malware will be blocked automatically
o
Automatically quarantine known threats - only those applications that
are with absolute certainty detec ted as malware will be blocked
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 60
Page 61

Control buttons
The control buttons available within the Identity Protection interface are as follows:
· Save changes - press this button to save and apply any c hanges made in this
dialog
· Cancel - press this button to return to the default AVG user interface
(components overview)
8.10. License
In the Licence component interface you will find a brief text describing the
component's functionality, information on its current status (License component is
active.), and the following information:
· License number - provides the shortened form of your license number (for
security reasons the last four symbols are missing). When entering your
license number, you have to be absolutely precise and type it exactly as
shown. Therefore we strongly recommend to always use "copy & paste"
method for any manipulation with the license number.
· License type - specifies the product type installed.
· License expires - this date determines the period of validity of your lic ense. If
you want to go on using AVG 9 Internet Security after this date you have to
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 61
Page 62

renew your license. The license renewal can be performed online on AVG
website.
· Number of seats - how many workstations on which you are entitled to install
your AVG 9 Internet Security.
Control buttons
· Register - connects to the registration page of AVG website (http://www.
avg.com/). Please fill in your registration data; only customers who register
their AVG product can receive free technical support.
· Re-activate - opens the Activate AVG dialog with the data you have entered
in the Personalize AVG dialog of the installation process. Within this dialog
you can enter your license number to either replace the sales number (the
number you have installed AVG with), or to replace the old license number (e.
g. when upgrading to a new AVG product).
Note: If using the trial version of AVG 9 Internet Security, the buttons appear
as Buy now and Activate, alowing you to buy the full version of the program
right away. For AVG 9 Internet Security installed with a sales number, the
buttons display as Register and Activate.
· Back - press this button to return to the default AVG user interface
(components overview).
8.11. Link Scanner
8.11.1. Link Scanner Principles
The LinkScanner component provides protection against websites, that are designed
to install malware into your computer via the web browser or its plugins. The
LinkScanner technology consists of two features, AVG Search-Shield and AVG
Active Surf-Shield:
· AVG Search Shield contains list of websites (URL addresses) which are known
to be dangerous. When searching with Google, Yahoo!, WebHledani, Yandex,
Baidu, Bing, AOL, AltaVista, EarthLink, Ask, Seznam, eBay, Twitter, Digg, or
SlashDot, all results of the search are checked ac cording to this list and a
verdict icon is shown (for Yahoo! search results only "exploited website"
verdict icons are shown).
· AVG Active Surf-Shield scans the contents of the websites you are visiting,
regardless of the websites address. Even if some website is not detected by
AVG Search Shield (e.g. when a new malicious website is created, or when a
previously clean website now contains some malware), it will be detected and
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 62
Page 63

blocked by AVG Active Surf-Shield once you try to visit it.
Note: AVG Link Scanner is not intended for server platforms!
8.11.2. Link Scanner Interface
The LinkScanner component consists of two parts that you can switch on/off in the
LinkScanner component interfac e:
The LinkScanner component interface provides a brief description of the component's
functionality and information on its current status (LinkScanner component is active.).
Further, you can find the information on the latest LinkScanner database version
number (LinkScanner Version).
In the bottom part of the dialog you can edit several options:
· Enable AVG Search-Shield - (on by default): advisory notifying icons on
searches performed with Google, Yahoo!, WebHledani, Yandex, Baidu, Bing,
AOL, AltaVista, EarthLink, Ask, Seznam, eBay, Twitter, Digg, or SlashDot:
having checked ahead the content of sites returned by the search engine.
· Enable AVG Active Surf-Shield - (on by default): active (real-time)
protection against exploitive sites as they are accessed. Known malicious site
connections and their exploitive c ontent is blocked as they are accessed by
the user via a web browser (or any other application that uses HTTP).
· Enable reporting of detected threats to AVG - mark this item to allow back
reporting of exploits and bad sites found by users either via Safe Surf or Safe
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 63
Page 64
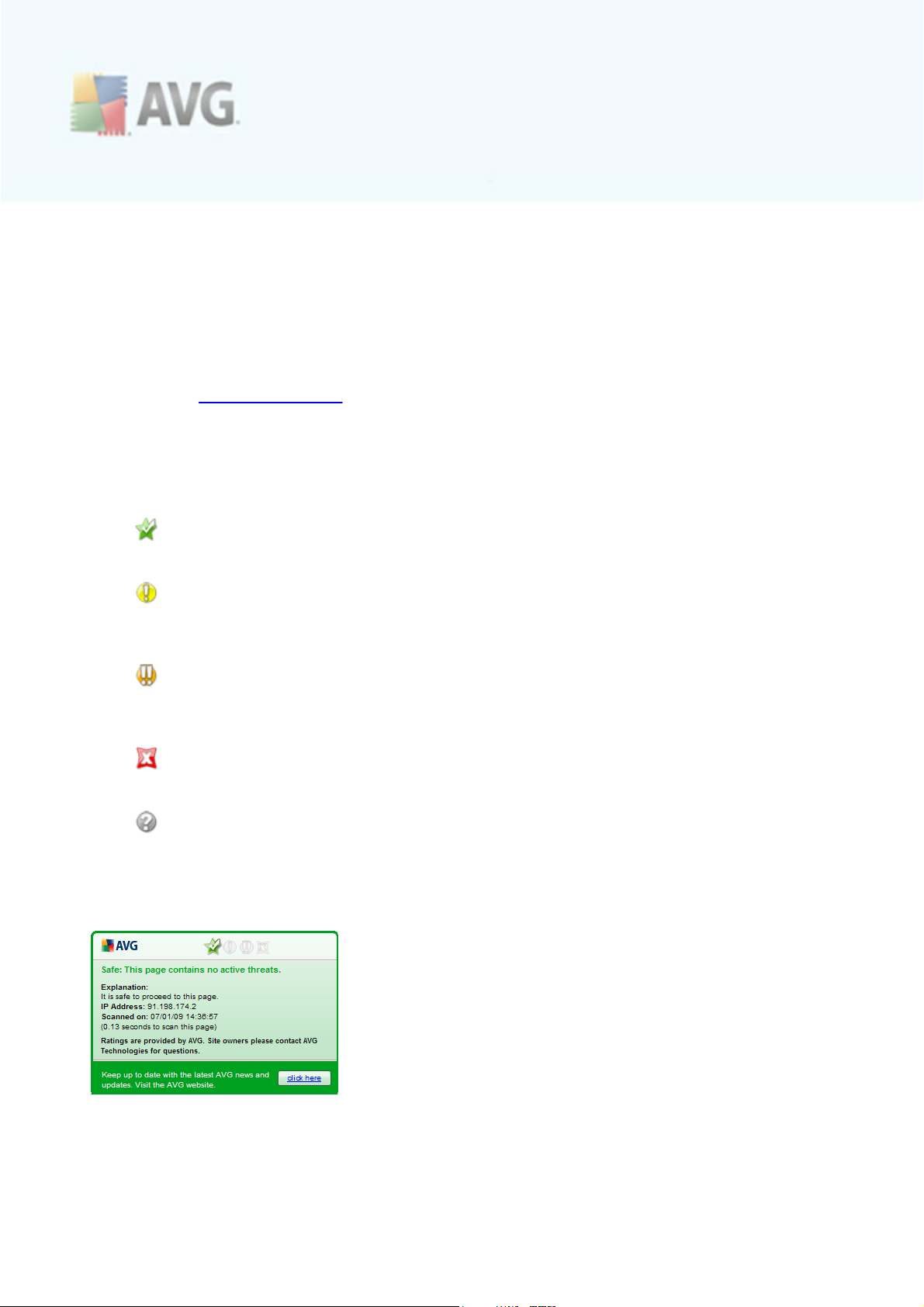
Search to feed the database collecting information on malicious activity on the
web.
8.11.3. AVG Search-Shield
When searching Internet with the AVG Search-Shield on, all search results returned
from the most popular search engines (Google, Yahoo!, WebHledani, Yandex, Baidu,
Bing, AOL, AltaVista, EarthLink, Ask, Seznam, eBay, Twitter, Digg, and SlashDot) are
evaluated for dangerous or suspicious links. By checking these links and marking the
bad links, the AVG Link Scanner warns you before you click on dangerous or
suspicious links, so you can ensure you only go to safe websites.
While a link is being evaluated on the search results page, you will see a graphic sign
next to the link informing that the link verification is in progress. When the evaluation
is complete, the respec tive informative icon will be displayed:
The linked page is safe (with Yahoo! search engine this icon will not be
displayed!).
The linked page does not contain threats but is somewhat suspicious (
questionable in origin or motive, therefore not recommended for e-shopping
etc.).
The linked page can be either safe itself, but containing further links to
positively dangerous pages; or suspicious in code, though not directly employing
any threats at the moment.
The linked page contains active threats! For your own safety, you will not be
allowed to visit this page.
The linked page is not accessible, and so could not be scanned.
Hovering over an individual rating icon will display details about the particular link in
question. Information include additional details of the threat (if any), the IP address of
the link and when the page was scanned by AVG:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 64
Page 65

VeriSign Seal
Besides the above listed AVG Search Shield verdict icons, you can also see the
VeriSign icon in your browser. However, this icon display refers only to pages
websites that participate in the Verisign Seal project. In such a case, the VeriSign
icon will be displayed next to any link in the search results list, or next to the
sponsored links. For instance, if the website is considered safe, you will see the
VeriSign icon next to the green AVG Search Shield icon. If the site is considered
potentially dangerous, you will be informed via the AVG verdic t icon only.
The VeriSign icons are supported in the following search engines: Altavista, AOL, Ask,
Baidu, Bing, Earthlink, Google, Seznam, Webhledani, Yandex, and Yahoo!
8.11.4. AVG Active Surf-Shield
This powerful protection will block malicious c ontent of any webpage you try to open,
and prevent it from being downloaded to your computer. With this feature enabled,
clicking a link or typing in a URL to a dangerous site will automatically block you from
opening the web page thus protecting you from inadvertently being infected. It is
important to remember that exploited web pages can infect your computer simply by
visiting the affected site, for this reason when you request a dangerous webpage
containing exploits or other serious threats, the AVG Link Scanner will not allow your
browser to display it.
If you do encounter a malicious web site, within your web browser the AVG Link
Scanner will warn you with a screen similar to:
Entering such web site is highly risky and it cannot be recommended!
8.12. Online Shield
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 65
Page 66

8.12.1. Online Shield Principles
Online Shield is a type of a real time resident protec tion; it scans the content of
visited web pages (and possible files included in them) even before these are displayed
in your web browser or downloaded to your computer.
Online Shield detects that the page you are about to visit includes some dangerous
javascript, and prevents the page from being displayed. Also, it recognizes malware
contained in a page and stops its downloading immediately so that it never gets to
your computer.
Note: AVG Online Shield is not intended for server platforms!
8.12.2. Online Shield Interface
The Online Shield component's interface desc ribes the behavior of this type of
protection. Further you can find information on the component's current status (Online
Shield is active and fully functional.). In the bottom part of the dialog you will then
find the elementary editing options of this c omponent's functionality.
Basic component configuration
First of all, you have the option to immediately switch on/off the Online Shield by
checking the Enable Online Shield item. This option is enabled by default, and the
Online Shield component is active. However, if you do not have a good reason to
change this settings, we recommend to keep the component active. If the item is
checked, and the Online Shield is running, more c onfiguration options are available
and editable on two tabs:
· Web - you can edit the component's configuration regarding the scan of the
website c ontent. The editing interface allows you to configure the following
elementary options:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 66
Page 67
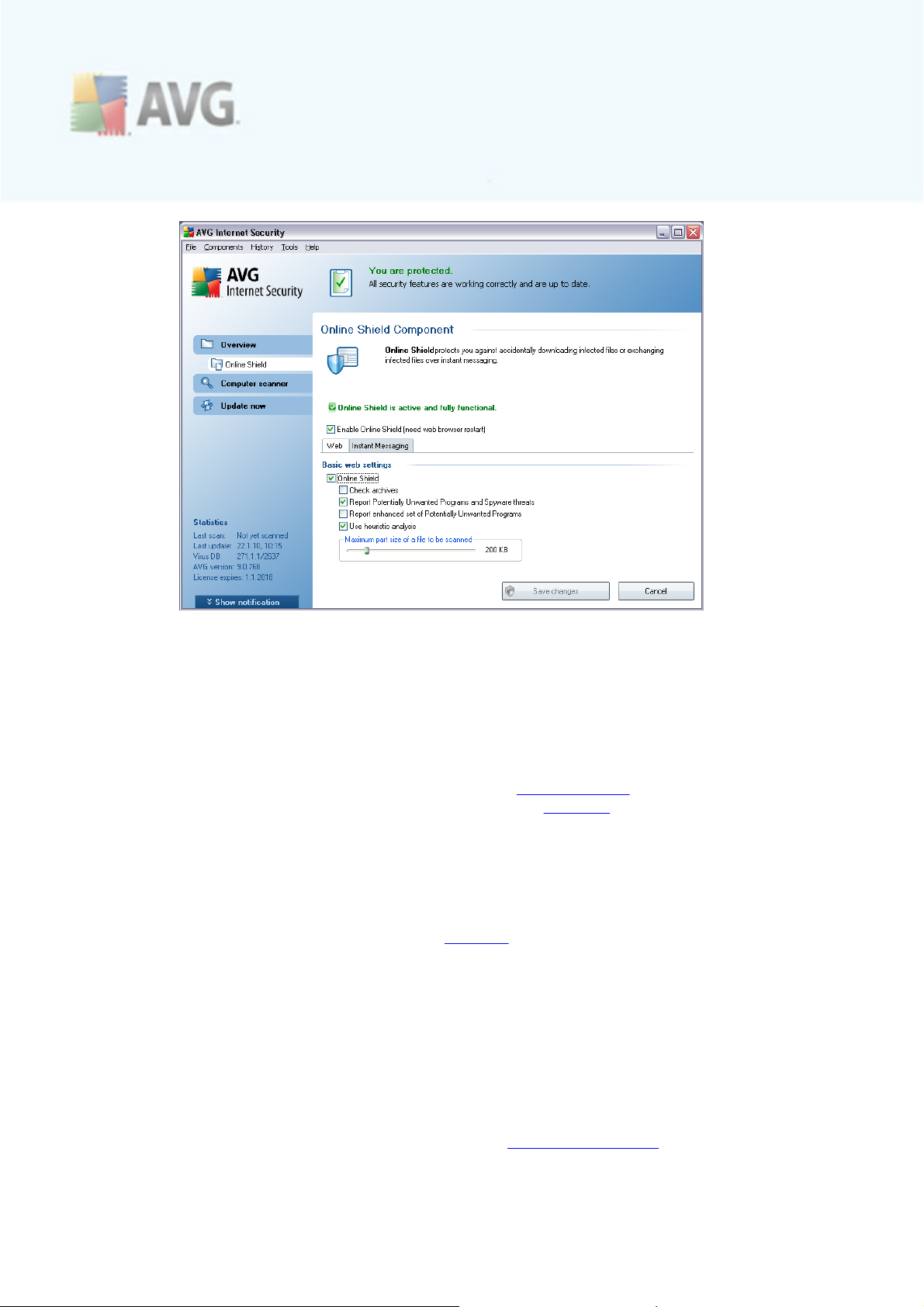
o
Online Shield - this option confirms that the Online Shield should
perform scanning of the www pages content. Provided this option is on (
by default), you can further switch on/off these items:
Ø Check archives - scan the content of archives possibly included in
the www page to be displayed
Ø Report Potentially Unwanted Programs and Spyware threats - (
on by default): chec k to activate the Anti-Spyware engine, and
scan for spyware as well as for viruses. Spyware represents a
questionable malware category: even though it usually represents a
security risk, some of these programs can be installed intentionally.
We recommend to keep this feature activated as it increases your
computer security.
Ø Report enhanced set of Potentially Unwanted Programs - mark to
detect extended package of spyware: programs that are perfectly ok
and harmless when acquired from the manufacturer directly, but can
be misused for malicious purposes later. This is an additional measure
that increases your computer security even more, however it can
possibly block legal programs, and is therefore switched off by
default.
Ø Use heuristic analysis - scan the content of the page to be
displayed using the heuristic analysis method, i.e. simulation and
evaluation of the scanned object's instructions in a virtual computer
environment. Therefore, it can even detec t malicious code not yet
described in the virus database (see Anti-Virus Principles).
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 67
Page 68

Ø Maximum file size to be scanned - if included files are present in
the displayed page you can also scan their content even before these
are downloaded to your computer. However, sc anning of large files
takes quite some time and the web page download might be slowed
significantly. You can use the slide bar to specify the maximum size of
a file that is still to be scanned with Online Shield. Even if the
downloaded file is bigger than specified, and therefore will not be
scanned with Online Shield, you are still protected: in case the file is
infected, the Resident Shield will detect it immediately.
· Instant Messaging - allows you to edit the components settings referring to
instant messaging (e.g. ICQ, MSN Messenger, Yahoo ...) sc anning.
o
Instant Messaging protec tion - check this item if you wish that the
Online Shield verifies the on-line communication is virus free. Provided
this option is on, you c an further specify which instant messaging
application you want to c ontrol - currently AVG 9 Internet Security
supports the ICQ, MSN, and Yahoo applications.
Please note: The software vendor has set up all AVG components to give optimum
performance. Unless you have a real reason to do so, do not change the AVG
configuration. Any changes to settings should only be performed by an experienced
user. If you need to change AVG configuration, select the system menu item Tools /
Advanced settings and edit the AVG configuration in the newly opened AVG
Advanced Settings dialog.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 68
Page 69

Control buttons
The control buttons available within the Online Shield interface are as follows:
· Save changes - press this button to save and apply any c hanges made in this
dialog
· Cancel - press this button to return to the default AVG user interface (
components overview)
8.12.3. Online Shield Detection
Online Shield scans the content of visited web pages and possible files included in
them even before these are displayed in your web browser or downloaded to your
computer. If a threat is detected, you will be warned immediately with the following
dialog:
Within this warning dialog you will find data on the file that was detected and assigned
as infected (File name), the name of the recognized infection (Threat name), and a
link to the Virus encyclopedia where you can find detailed information on the
detected infection (if known). The dialog provides the following buttons:
· Show/Hide details - click the Show details button to open a new section in
the bottom part of the dialog; here you c an find information on the process
running while the infection was detec ted, and the process' identification. The
Hide details button ten closes the newly opened section of the dialog.
· Close - click the button to close the warning dialog.
The suspec t web page will not be opened, and the threat detection will be logged in
the list of Online Shield findings - this overview of detected threats is accessible
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 69
Page 70
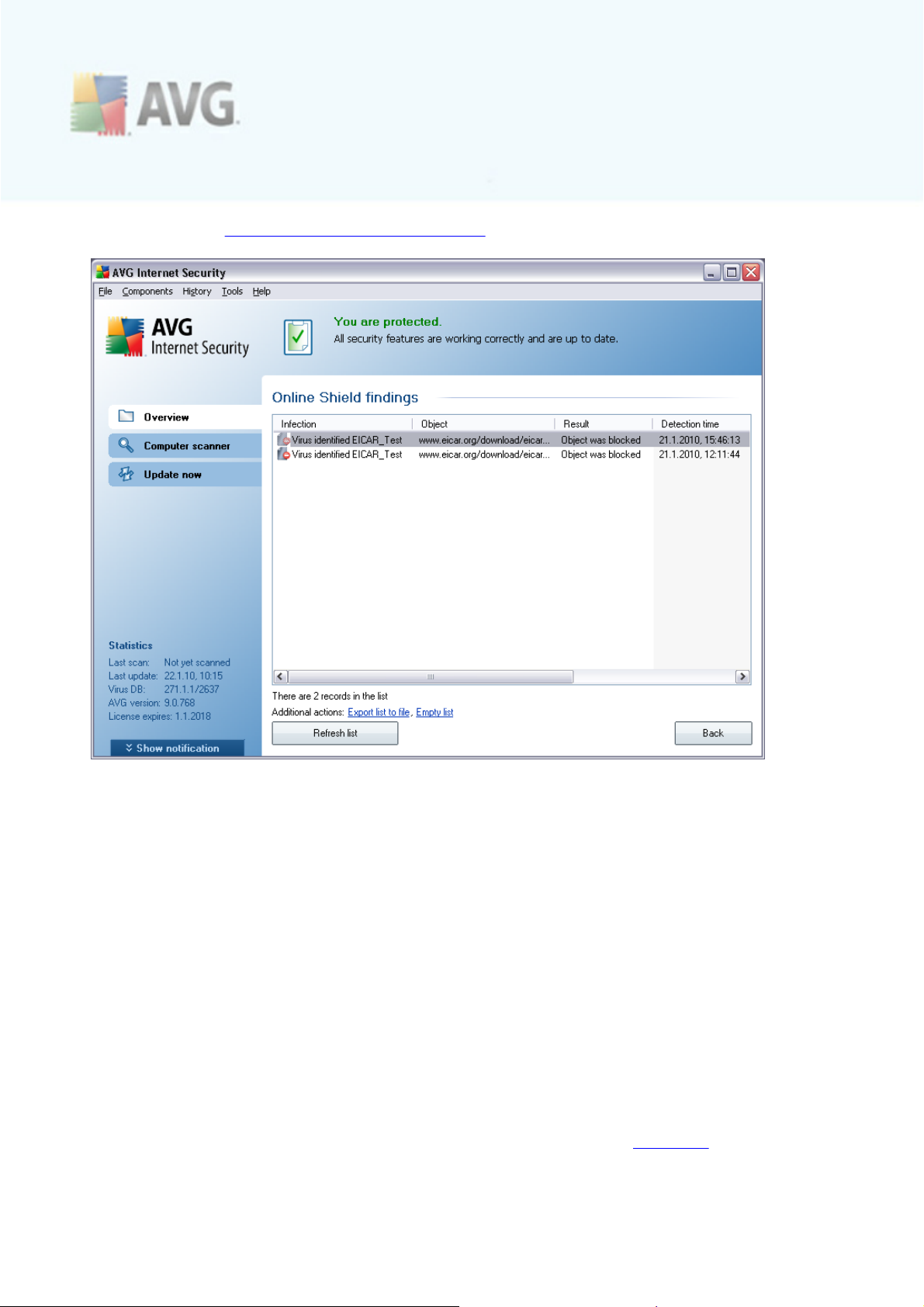
via system menu History / Online Shield findings.
For each detec ted object the following information is provided:
· Infection- description (possibly even name) of the detected object
· Object - object source (web page)
· Result - action performed with the detected object
· Detection time - date and time the threat was detected and blocked
· Object Type - type of the detected object
· Process - what action was performed to c all out the potentially dangerous
object so that it could be detected
In the bottom part of the dialog, under the list, you will find information on total
number of detected objects listed above. Further you can export the entire list of
detected objects in a file (Export list to file) and delete all entries on detected
objects (Empty list). The Refresh list button will update the list of finding detected
by Online Shield. The Back button switches you back to the default AVG user
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 70
Page 71
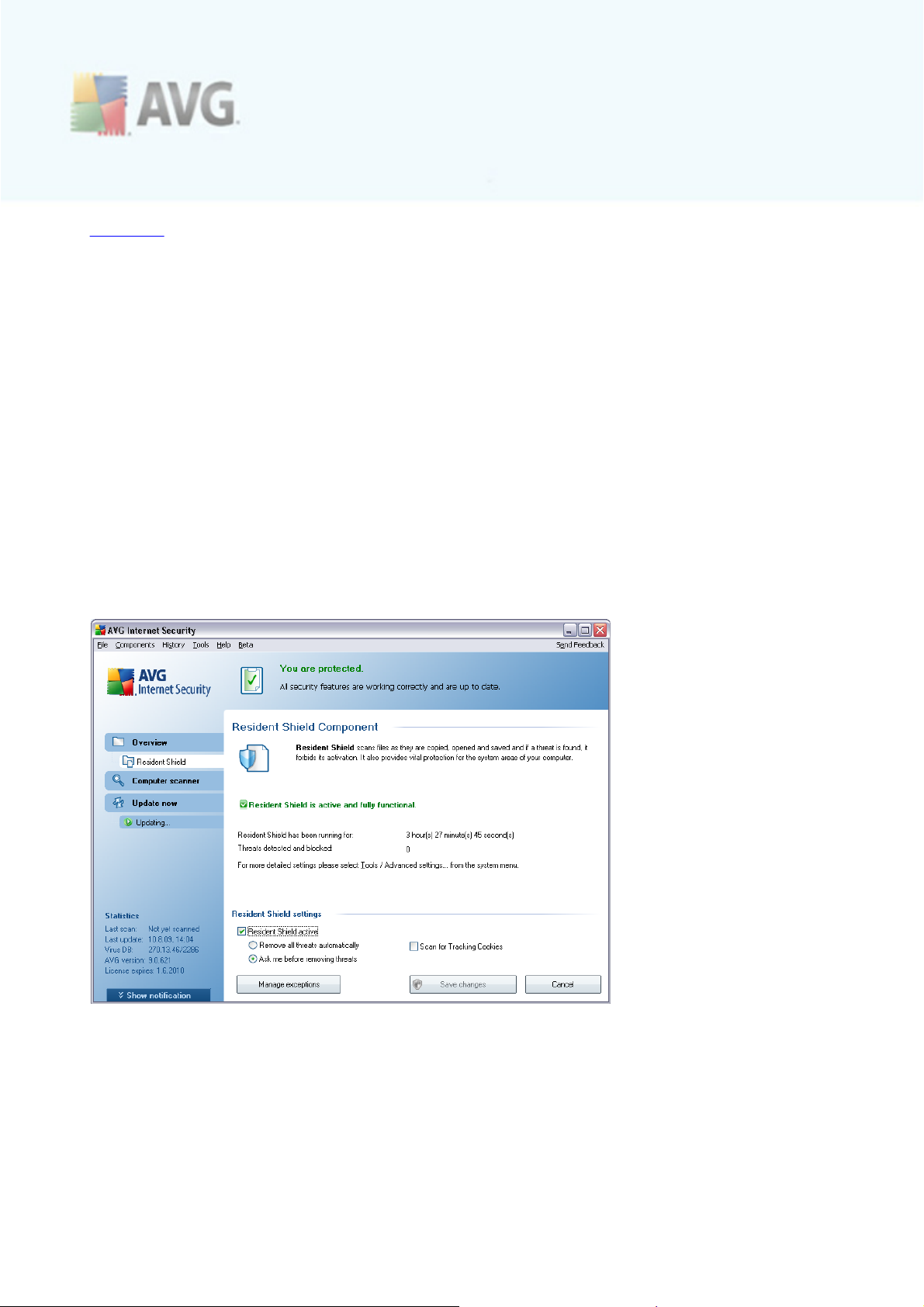
interface (components overview).
8.13. Resident Shield
8.13.1. Resident Shield Principles
The Resident Shield component gives your computer c ontinuous protection. It sc ans
every single file that is being opened, saved, or copied, and guards the system areas
of the computer. When Resident Shield discovers a virus in a file that is accessed, it
stops the operation currently being performed and does not allow the virus to activate
itself. Normally, you do not even notice the process, as it runs "in the background",
and you only get notified when threats are found; at the same time, Resident Shield
blocks ac tivation of the threat and removes it. Resident Shield is being loaded in the
memory of your computer during system startup.
Warning: Resident Shield is loaded in the memory of your computer during
startup, and it is vital that you keep it switched on at all times!
8.13.2. Resident Shield Interface
Besides an overview of the most important statistical data and the information on the component's current status (Resident Shield is active and fully functional), the Resident Shield interface offers some elementary component settings options, too. The statistics is as follows:
· Resident Shield has been running for - provides the time since the latest
component's launch
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 71
Page 72

· Threats detected and blocked - number of detected infections that were
prevented from being run/opened (if needed, this value can be reset; e.g. for
statistic purposes - Reset value)
Basic component configuration
In the bottom part of the dialog window you will find the section called Resident
Shield settings where you can edit some basic settings of the component's
functionality (detailed configuration, as with all other c omponents, is available via the
Tools/Advanced settings item of the system menu).
The Resident Shield is active option allows you to easily switch on/off resident
protection. By default, the function is on. With resident protection on you can further
decide how the possibly detected infections should be treated (removed):
o
either automatically (Remove all threats automatically)
o
or only after the user's approval (Ask me before removing threats)
This choice has no impact on the security level, and it only reflects your preferences.
In both c ases, you can still select whether you want to Scan for tracking cookies. In
specific cases you can switc h this option on to ac hieve maximum security levels,
however it is switc hed off by default. (cookies = parcels of text sent by a server to a
web browser and then sent back unchanged by the browser each time it accesses
that server. HTTP cookies are used for authenticating, tracking, and maintaining
specific information about users, such as site preferences or the contents of their
electronic shopping carts).
Please note: The software vendor has set up all AVG components to give optimum
performance. Unless you have a real reason to do so, do not change the AVG
configuration. Any changes to settings should only be performed by an experienced
user. If you need to change AVG configuration, select the system menu item Tools /
Advanced settings and edit the AVG configuration in the newly opened AVG
Advanced Settings dialog.
Control buttons
The control buttons available within the Resident Shield interface are as follows:
· Manage exceptions - opens the Resident Shield - Directory Excludes dialog
where you can define folders and files that should be left out from the
Resident Shield scanning
· Save changes - press this button to save and apply any c hanges made in this
dialog
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 72
Page 73
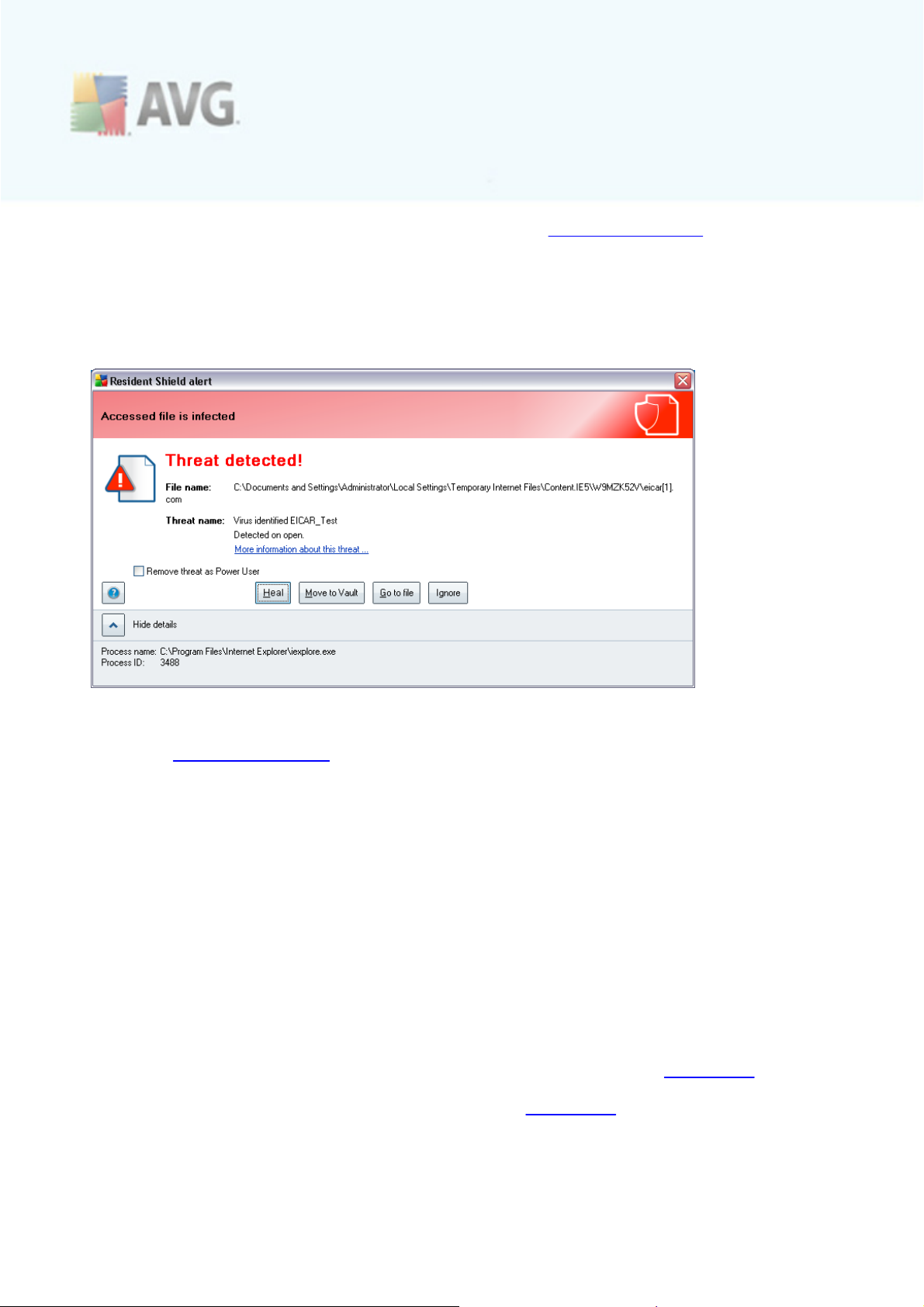
· Cancel - press this button to return to the default AVG user interface
(components overview)
8.13.3. Resident Shield Detection
Resident Shield scans files as they are copied, opened or saved. When a virus or any
kind of threat is detected, you will be warned immediately via the following dialog:
Within this warning dialog you will find data on the file that was detected and assigned
as infected (File name), the name of the recognized infection (Threat name), and a
link to the Virus encyclopedia where you can find detailed information on the
detected infection (if known). The dialog provides the following buttons:
· Show/Hide details - click the Show details button to open a new section in
the bottom part of the dialog; here you c an find information on the process
running while the infection was detec ted, and the process' identification. The
Hide details button ten closes the newly opened section of the dialog.
Further, you have to decide what action should be taken now:
· Remove threat as Power User - check the box if you suppose that you
might not have sufficient rights to remove the threat as a common user. Power
Users have extensive access rights, and if the threat is located in a certain
system folder, you might need to use this checkbox to successfully remove it.
· Heal - this button only appears if the detec ted infection can be healed. Then,
it removes it from the file, and restores the file to the original state. If the file
itself is a virus, use this function to delete it (i.e. removed to the Virus Vault)
· Move to Vault - the virus will be moved to AVG Virus Vault
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 73
Page 74

· Go to file - this option redirects you to the exact location of the suspicious
object (opens new Windows Explorer window)
· Ignore - we strictly recommend NOT TO use this option unless you have a
very good reason to do so!
· Show/Hide details - this button with alternative option gives a name and full
path to the file, name of the detected infection, and details about the process
(running application) during which the threat was detected
The entire overview of all threats detected by Resident Shield can be found in the
Resident Shield detection dialog accessible from system menu option History /
Resident Shield detection:
The Resident Shield detection offers an overview of objects that were detected by
the Resident Shield, evaluated as dangerous and either cured or moved to the Virus
Vault. For each detected object the following information is provided:
· Infection- description (possibly even name) of the detected object
· Object - object location
· Result - action performed with the detected object
· Detection time - date and time the object was detec ted
· Object Type - type of the detected object
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 74
Page 75

· Process - what action was performed to c all out the potentially dangerous
object so that it could be detected
In the bottom part of the dialog, under the list, you will find information on total
number of detected objects listed above. Further you can export the entire list of
detected objects in a file (Export list to file) and delete all entries on detected
objects (Empty list). The Refresh list button will update the list of finding detected
by Resident Shield. The Back button switches you back to the default AVG user
interface (components overview).
8.14. Update Manager
8.14.1. Update Manager Principles
No security software can guarantee true protection from various types of threats
unless it is regularly updated! Virus writers are always looking for new flaws that they
can exploit in both software and operating systems. New viruses, new malware, new
hacking attacks appear daily. For this reason, software vendors are continually issuing
updates and security patches, to fix any security holes that are discovered.
It is crucial to update your AVG regularly!
The Update Manager helps you to control regular updating. Within this component you can schedule automatic downloads of update files either from the Internet, or the local network. Essential virus definition updates should be daily if possible. Less urgent
program updates can be weekly.
Note: Please pay attention to the AVG Updates chapter for more information on
update types and levels!
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 75
Page 76
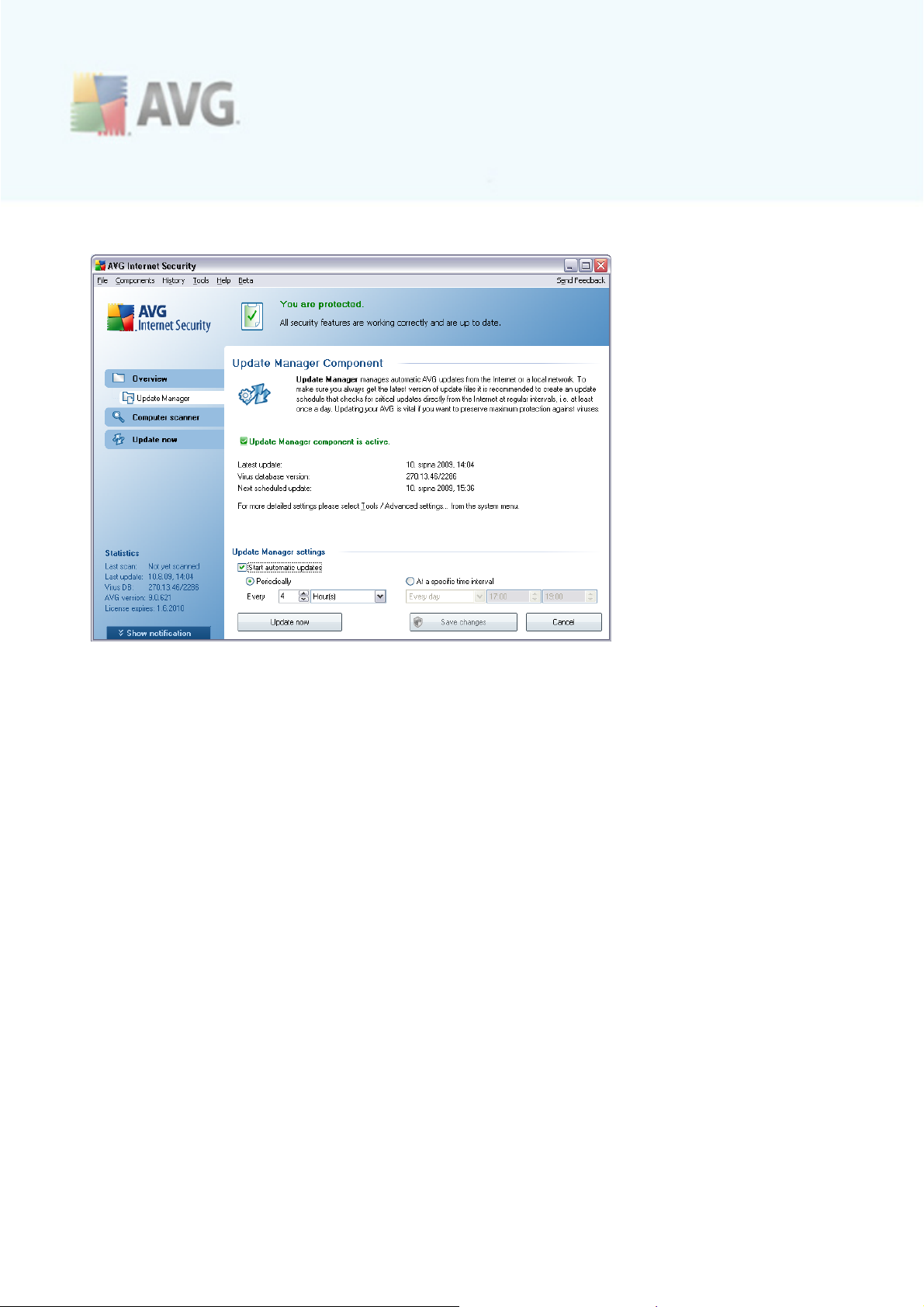
8.14.2. Update Manager Interface
The Update Manager's interface displays information about the c omponent's
functionality and its current status (Update manager is active.), and provides the
relevant statistical data:
· Latest update - specifies when and at what time the database was updated
· Virus database version - defines the number of the currently installed virus
database version; and this number increases with every virus base update
· Next scheduled update - spec ifies when and at what time the database is
scheduled to be updated again
Basic component configuration
In the bottom part of the dialog you can find the Update Manager settings section
where you can perform some changes to the rules of the update process launch. You
can define whether you wish the update files to be downloaded automatically (Start
automatic updates) or just on demand. By default, the Start automatic updates
option is switched on and we recommend to keep it that way! Regular download of
the latest update files is crucial for proper functionality of any security software!
Further you can define when the update should be launched:
o
Periodically - define the time interval
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 76
Page 77

o
At a specific time - define the exact day time the update should be launched
By default, the update is set for every 4 hours. It is highly recommended to keep this
setting unless you have a true reason to change it!
Please note: The software vendor has set up all AVG components to give optimum
performance. Unless you have a real reason to do so, do not change the AVG
configuration. Any changes to settings should only be performed by an experienced
user. If you need to change AVG configuration, select the system menu item Tools /
Advanced settings and edit the AVG configuration in the newly opened AVG
Advanced Settings dialog.
Control buttons
The control buttons available within the Update Manager interface are as follows:
· Update now - launches an immediate update on demand
· Save changes - press this button to save and apply any c hanges made in this
dialog
· Cancel - press this button to return to the default AVG user interface
(components overview)
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 77
Page 78

9. AVG Security Toolbar
AVG Security Toolbar is a new tool which works together with the AVG LinkScanner
component. AVG Security Toolbar can be used to control AVG LinkScanner functions
and to adjust its behavior.
If you select to install the toolbar during the installation of AVG 9 Internet Security,
it will be added into your web browser (Internet Explorer and/or Mozilla Firefox)
automatically.
Note: In case you are using some alternative Internet browser (e.g Avant Browser)
you can meet unexpected behavior.
9.1. AVG Security Toolbar Interface
The AVG Security Toolbar is designed to work with MS Internet Explorer (version
6.0 or higher) and Mozilla Firefox (version 3.0 or higher). Once you have decided you
want to install AVG Security Toolbar (during the AVG installation process you were
asked to decide whether or not you wish to install the component), the component
will be located in your web browser just under the address bar:
The AVG Security Toolbar consists of the following:
9.1.1. AVG logo button
This button provides access to general toolbar items. Click the logo button to get
redirected to AVG website. Clicking the pointer next to the AVG icon will open the
following:
· Toolbar Info - link to the AVG Security Toolbar home page with detailed
information on the toolbar's protection
· Launch AVG 9.0 - opens the AVG 9 Internet Security user interface
· Options - opens a configuration dialog where you can adjust your AVG
Security Toolbar settings to suit your needs - see the following chapter AVG
Security Toolbar Options
· Delete History - allows you within AVG Security Toolbar delete complete
history, or separately to delete search history, delete browser history, delete
download history and delete cookies.
· Update - checks for new updates for your AVG Security Toolbar
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 78
Page 79

· Help - provides options to open the help file, contact AVG technical support,
send your product related feedback, or view the details of the current version
of the toolbar
9.1.2. AVG Secure Search powered search box
AVG Secure Search powered search box is easy and safe way to search the web using
AVG Secure Search search. Enter a word or phrase into the search box press the
Search button, or the Enter key, to start the search on the AVG Secure Search
server directly, no matter what page is currently displayed. The search box also lists
your search history. Searches done through the search box are analyzed using the
AVG Search-Shield protection.
Alternatively, within the search field you can switc h to Wikipedia, or some other
specific search service - see picture:
9.1.3. Page Status
Directly in the toolbar, this button displays the evaluation of the currently displayed
web page base on criteria of the AVG Active Surf-Shield component:
· The linked page is safe
· Page is somewhat suspicious.
· Page containing links to positively dangerous pages.
· The linked page contains active threats! For your own safety, you will not
be allowed to visit this page.
· The page is not accessible, and so could not be scanned.
Clic k the button to open an information panel with detailed data on the specific web
page.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 79
Page 80
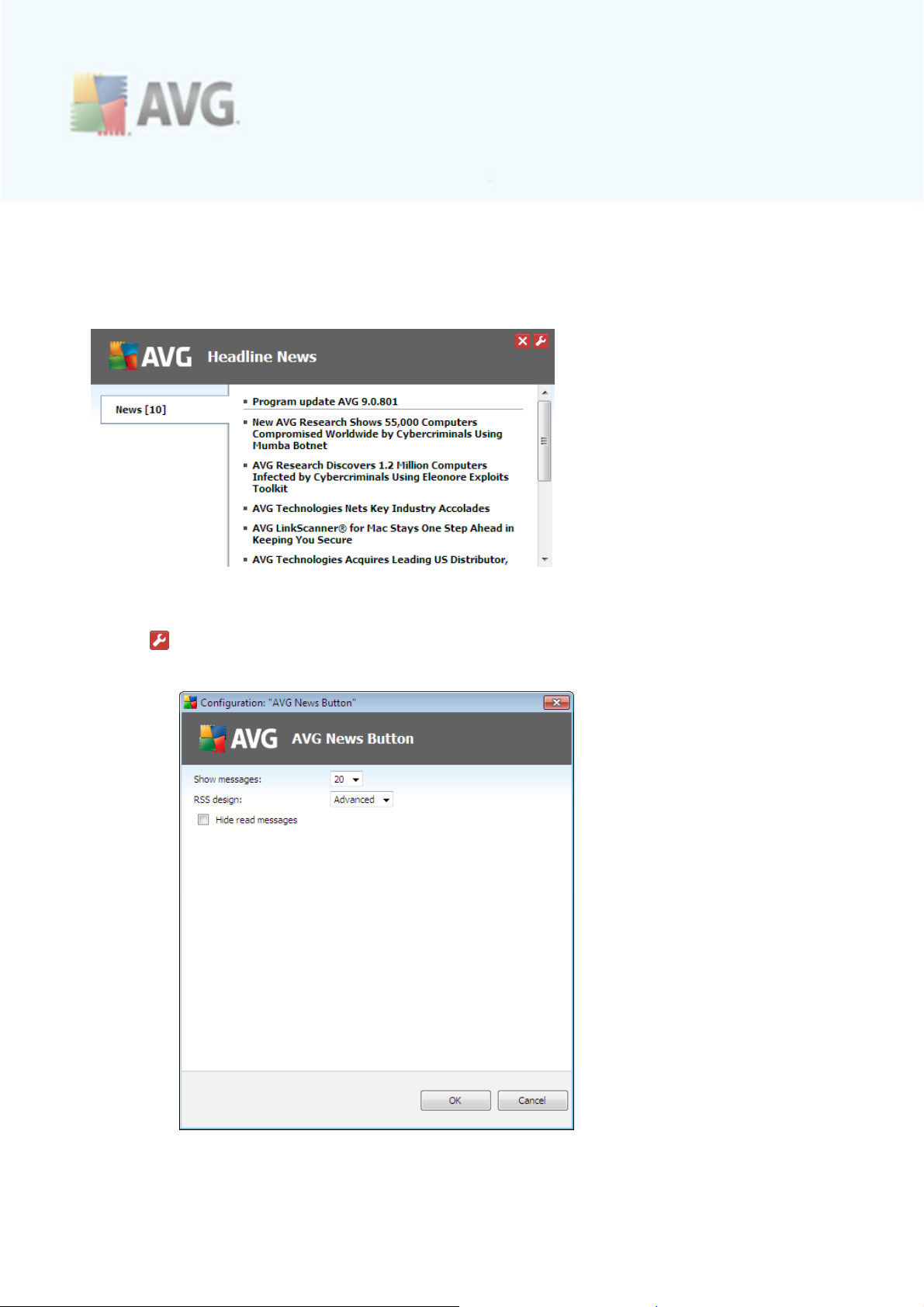
9.1.4. AVG News
Directly from within the AVG Security Toolbar, this button opens an overview of the
latest Headline news related to AVG, both news from the press and c ompany press
release:
In the right upper corner you can see two red control buttons:
· - the button opens the editing dialog where you can specify parameters of
the AVG News button displayed within the AVG Security Toolbar:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 80
Page 81
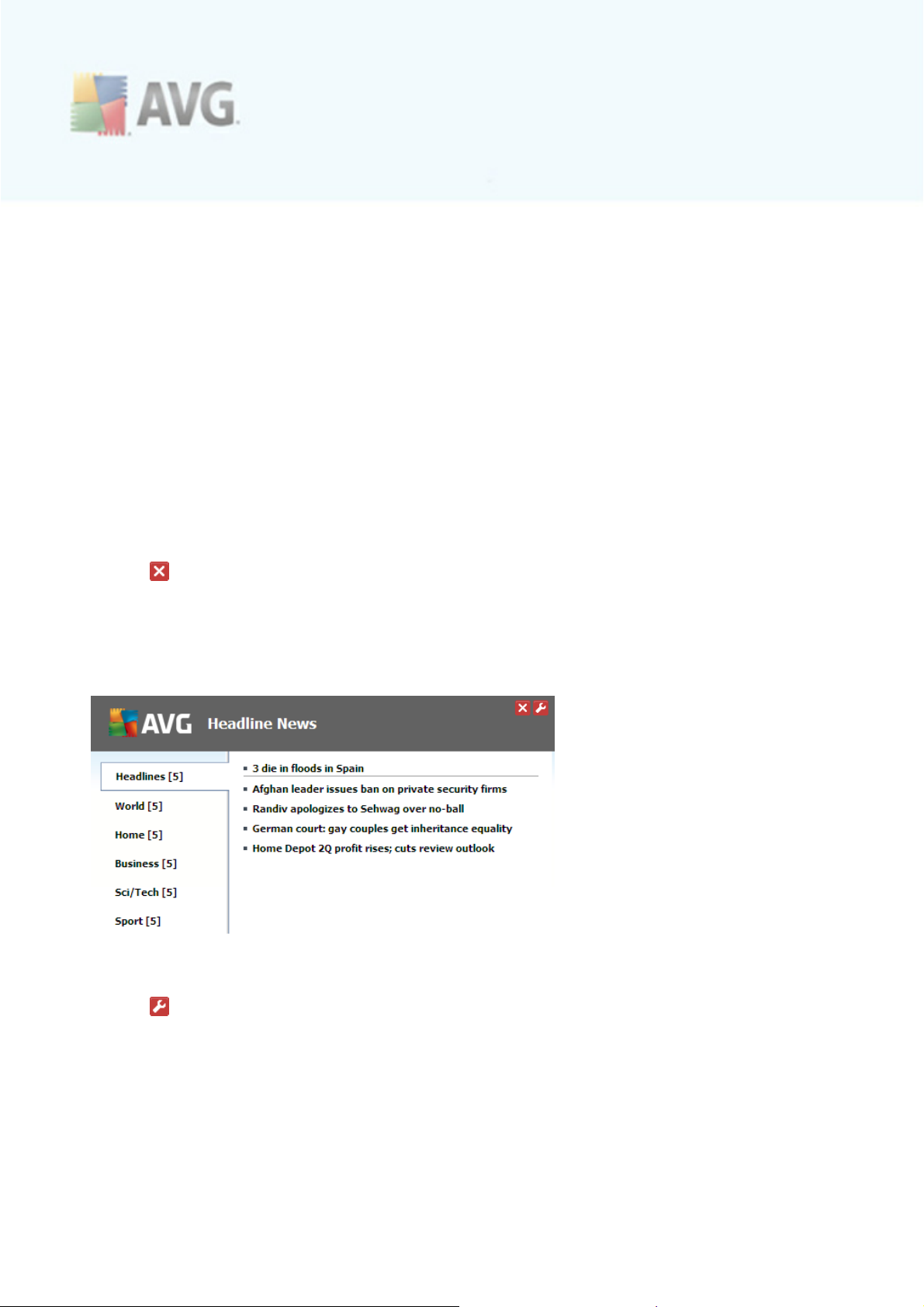
o
Button name - you have the option to change the button name as it will
be displayed within AVG Security Toolbar
o
Show messages - change the desired number of messages that are to
be displayed at a time
o
RSS design - select between Advanced/Basic mode of the current
display of the news overview (by default, the Advanced mode is selected
- see picture above)
o
Hide read messages - mark this item to confirm that each read
message should not be displayed any longer, so that new messages c an
be supplied
o
Button shows - in this field you can select the respective news
categories that you want to have displayed in your news overview
within AVG Security Toolbar
· - click this button to close the currently opened news overview
9.1.5. News
Similarly, directly from within the AVG Security Toolbar, this button opens an
overview of the latest news from selected media divided into several sections:
In the right upper corner you can see two red control buttons:
· - the button opens the editing dialog where you can specify parameters of
the News button displayed within the AVG Security Toolbar:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 81
Page 82

· - click this button to close the currently opened news overview
9.1.6. AVG Info
The button provides links to important security information related to AVG 9 Internet
Security:
· Toolbar Info - link to the AVG Security Toolbar home page with detailed
information on the toolbar's protection
· About Threats - opens the AVG website at page providing most important
data on top threats, virus removal recommendations, AVG update information,
access to Virus database and more relevant info
· AVG News - opens the web page providing the latest AVG related press
release
· Current Threat Level - opens the virus lab web page with a graphical display
of the current threat level on the web
· Virus Encyclopedia - opens the Virus database page where you can search
the spec ific viruses by name and get detailed information on each one
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 82
Page 83

9.1.7. Delete history
Using this button you can delete the history of your browser just like via the AVG logo
-> Delete history option.
9.1.8. E-mail Notifier
The E-mail Notifier button allows you to activate the option of being informed about
newly arrived e-mail messages directly in the AVG Security Toolbar interface. The
button opens the following editing dialog where you can define parameters of your email account and the e-mail display rules. Please follow the instructions in the dialog:
· Account type - Specify the protocol type your e-mail account uses. You can select
among the following alternatives: Gmail, POP3, or select the server name from the
drop down menu within the Other item (at the moment, you can use this option if
your account is on Yahoo! Mail or Hotmail). If you are not sure what e-mail server
type your account uses, try to find the information from your e-mail provider, or
your internet service provider.
· Login - In the section below provide the exact form of your e-mail address, and the
respective password. Keep the Auto Login option marked so that you do not have to
fill in the data repeatedly.
· Test account - Use this button to test the entered details.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 83
Page 84

· Reset Settings - Quickly removes the above entered e-mail address details.
· Check for new e-mails every ... minutes - Define the time interval to be used to
check for new e-mail messages (in the range of 5-120 minutes), and specify
whether and how you want to be informed about the new message arrival.
· Allow new e-mail alerts - Uncheck this to disable visual notifications of new e-mail
messages arrival.
o
Play a sound when new e-mails arrive - Uncheck this to disable sound
notifications of new e-mail messages arrival.
o
Close notification window after 5 seconds - Check this to
automatically close the visual notification window of new e-mail
messages arrival after 5 seconds.
9.1.9. Weather Info
The Weather button displays the information on the current temperature (updated
every 3-6 hours) in your selected destination directly within the AVG Security
Toolbar interface. Click the button to open a new info panel with detailed weather
overview:
Following find the editing options:
· Change location - click the Change location text to display a new dialog
called Search for your location. Fill in the name of your desired location into
the text field, and confirm by clicking the Search button. Next, within the list
of all locations of the same name select the destination you are looking for.
Finally, the info panel will be displayed again providing the weather information
for the selected location.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 84
Page 85
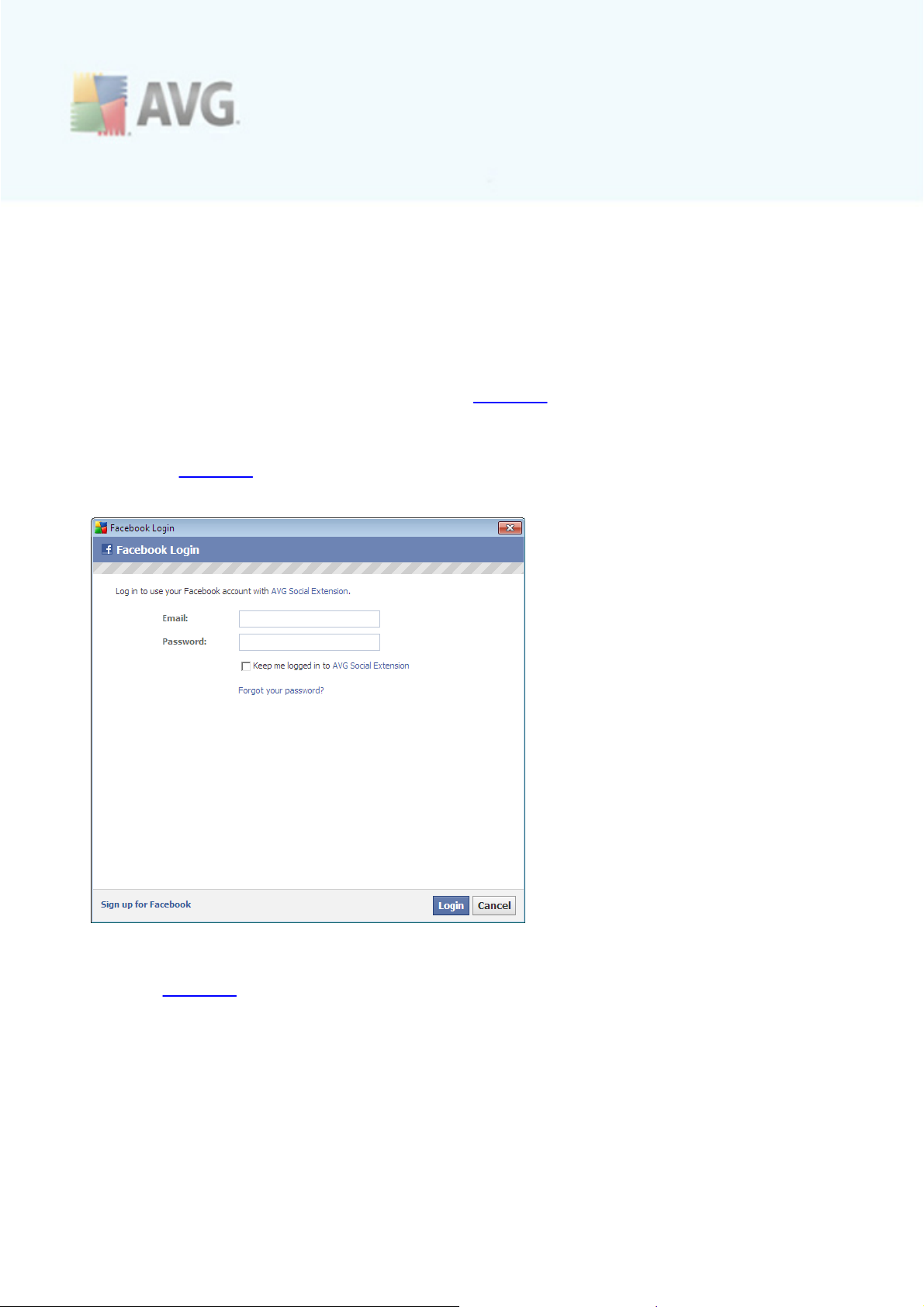
· Fahrenheit / Celsius converter - in the upper right-hand corner of the info
panel you can chose between the Fahrenheit and Celsius scales. Based on
your selection, the temperature information will be further provided in the
selected scale.
· Full Forecast - if interested in full and detailed forecast, use the Full Forecast link
to get to a specialized weather website.
9.1.10. Facebook
The Facebook button allows you connect to the Facebook social network from the AVG Security Toolbar directly. Click the button, and the login invitation appears;click
again to open the Facebook login dialog. In the dialog provide your acc ess data, that
means your e-mail address and password, and press the Connect button. If you do
not have a Facebook account yet, you can create one directly using the Sign up for
Facebook link:
Further, go to the following Facebook dialog where you will be invited to allow the
AVG Social Extension application. This application functionality is essential for the
toolbar - Fac ebook connection, therefore it is recommended to allow its functioning.
Press the Allow Status Updates button to confirm:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 85
Page 86
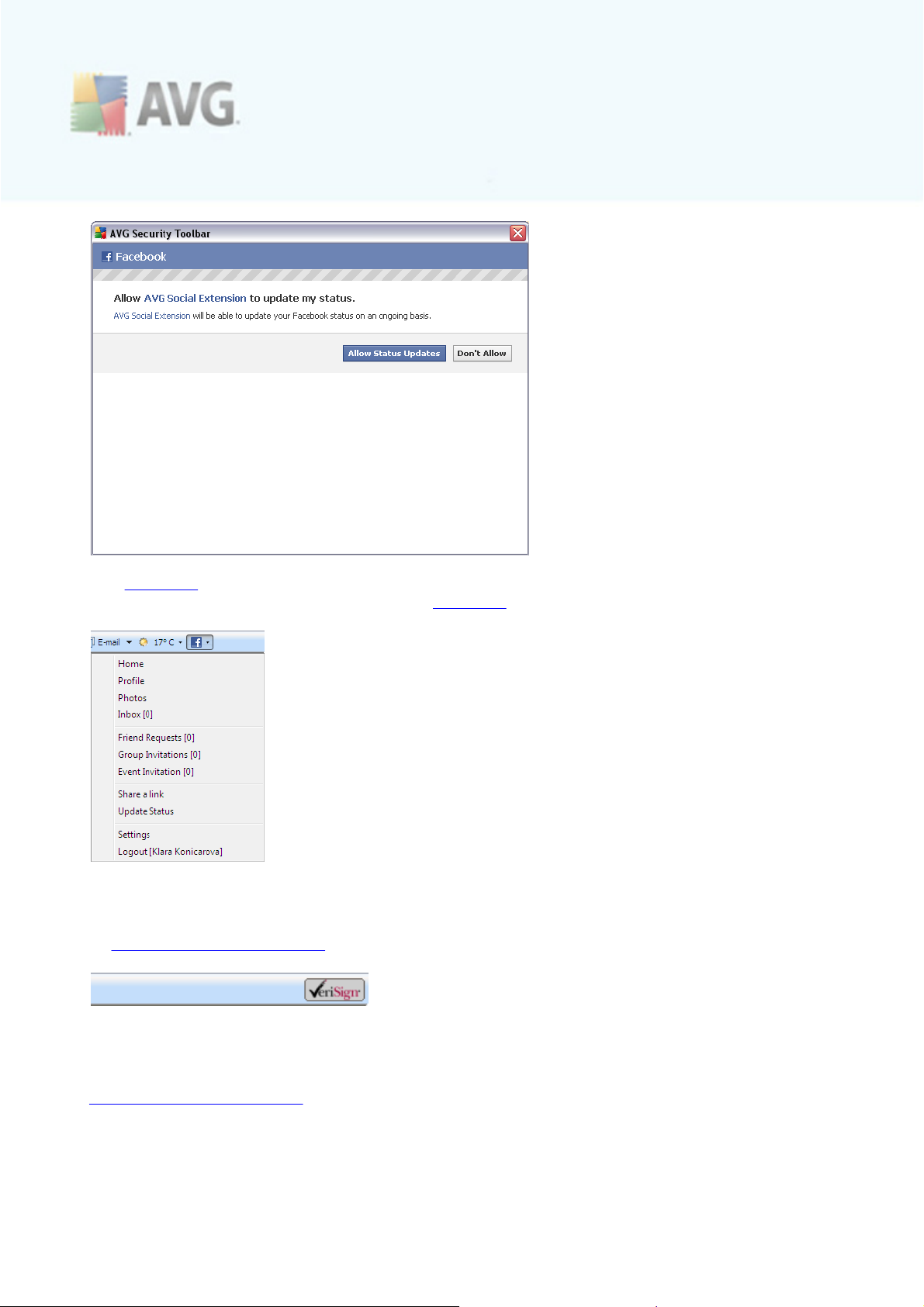
The Facebook connection has been activated. The Facebook button within AVG
Security Toolbaru now offers the standard Facebook menu options:
9.1.11. VeriSign Identity Protection
On the right side of AVG Security Toolbar you c an see the VeriSign button referring
to VeriSign Identity Protection:
VeriSign Identity Protection principles
VeriSign Identity Protection (VIP) helps protect your accounts and your identity by
requiring a unique security c ode, in addition to your user name and password, to
access your online acc ounts. VIP is based on so called two-factor authentication
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 86
Page 87
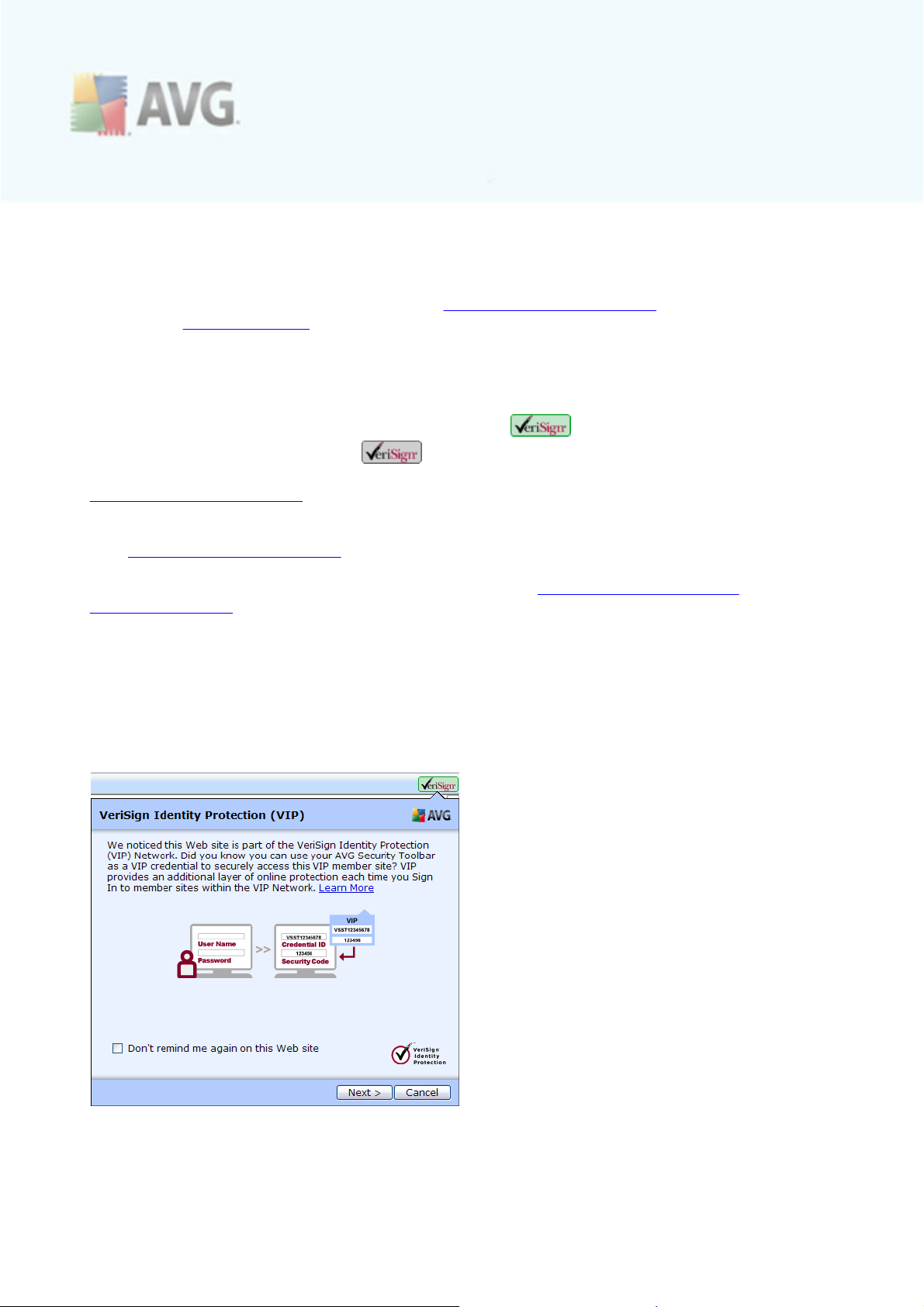
which combines something you know (such as your username and password) with
something unique that only you can generate instantaneously before logging to a site
(a security c ode in this case) to verify an identity or to verify a transaction.
Recommended: For detailed information on VeriSign Identity Protection please
consult the VeriSign website.
VeriSign Identity Protection member websites
The VeriSign button is displayed either in green color (for all recognized VIP
member website), or in gray color (for all non-VIP member sites or VIP
member sites that the Toolbar does not recognize). This basically means that the
VeriSign Identity Protection can only be ac tivated on websites that are members of
the VIP programme (VIP member sites, VIP network). A VIP member site is a website
maintained by a company that offers an additional layer of protec tion to their users
with VeriSign Identity Protection.
For overview of currently registered websites please visit https://vipmobile.verisign.
com/wheretouse.v.
How it works?
When you visit a website that is a VIP member, VeriSign Identity Protection within
AVG Security Toolbar will recognize the site, and inform you about this fact by
displaying the following info panel:
Within this website, you can apply the VeriSign Identity Protection, and use the
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 87
Page 88

AVG Security Toolbar VeriSign button to view your VIP credential. VIP credential is
a unique identifier consisting of 12 alphanumeric characters. This identification is to be
used while you register at any VIP member site where you have an online account.
Your VIP credential is unique to each installation of the AVG Security Toolbar and so
if you have multiple toolbars installed on different computers you will need to register
each toolbar to the member sites you would like to use.
To gain your VIP credential, click Next to continue to the following dialog:
After you register your VIP credential at the VIP member site, the next time you enter
the site, your VIP credential ID will be recognized automatically - the following dialog
will pop-up displaying your registered VIP credential, and a specific sec urity code. For
your protection, the sec urity code is valid within a limited timeframe. A new sec urity
code is dynamically generated by the VIP c redential every 30 seconds:
To succ essfully login to the VIP member site, you will be required to input your login
name, password and the security code generated by AVG Security Toolbar.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 88
Page 89
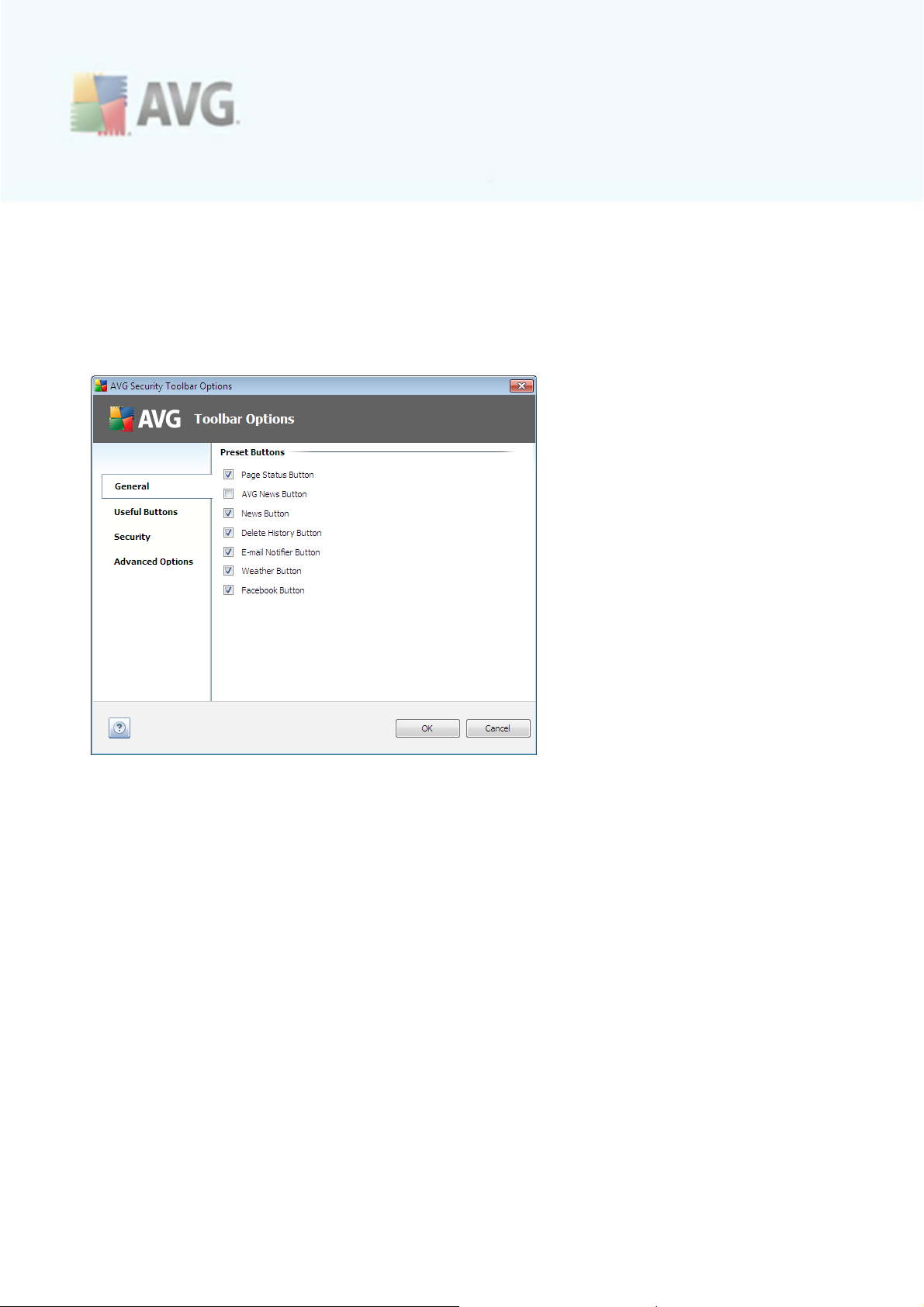
9.2. AVG Security Toolbar Options
All AVG Security Toolbar parameters configuration is accessible directly within the
AVG Security Toolbar panel. The editing interface opens via the AVG / Options toolbar
menu item in a new dialog called Toolbar Options divided into four sections:
9.2.1. Tab General
On this tab you c an specify toolbar control buttons that should be displayed or hidden
within the AVG Security Toolbar panel. Mark any option in case you want to have
displayed the respective button. Further find described the functionality of each of the
toolbar buttons:
· Page Status Button - the button offers the possibility of having displayed the
information on the currently opened page security status within AVG Security
Toolbar
· AVG News Button - the button opens a web page providing the latest AVG
related press release
· News Button - the button provides a structured overview of current news
from the daily press
· AVG Info Button - the button offers information on AVG toolbar, on current
threats and the internet threat level, opens the virus encyc lopedia, and
provides more AVG products related news
· Delete History Button - this button allows you to Delete complete history, or
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 89
Page 90

Delete search history, Delete browser history, Delete download history, or
Delete cookies directly from the AVG Security Toolbar panel
· E-mail Notifier Button - the button allows you to have displayed your newly
arrived e-mail messages within the AVG Security Toolbar interface
· Weather Button - the button offers an immediate information on the weather
situation in a selected location
· Facebook Button - the button offers a direct connection to the Facebook
social network
9.2.2. Tab Useful Buttons
The Useful Buttons tab allows you to select applications from a list and have their
icon displayed in the toolbar interface. The icon then serves as a quick link enabling to
launch the respective application immediately.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 90
Page 91
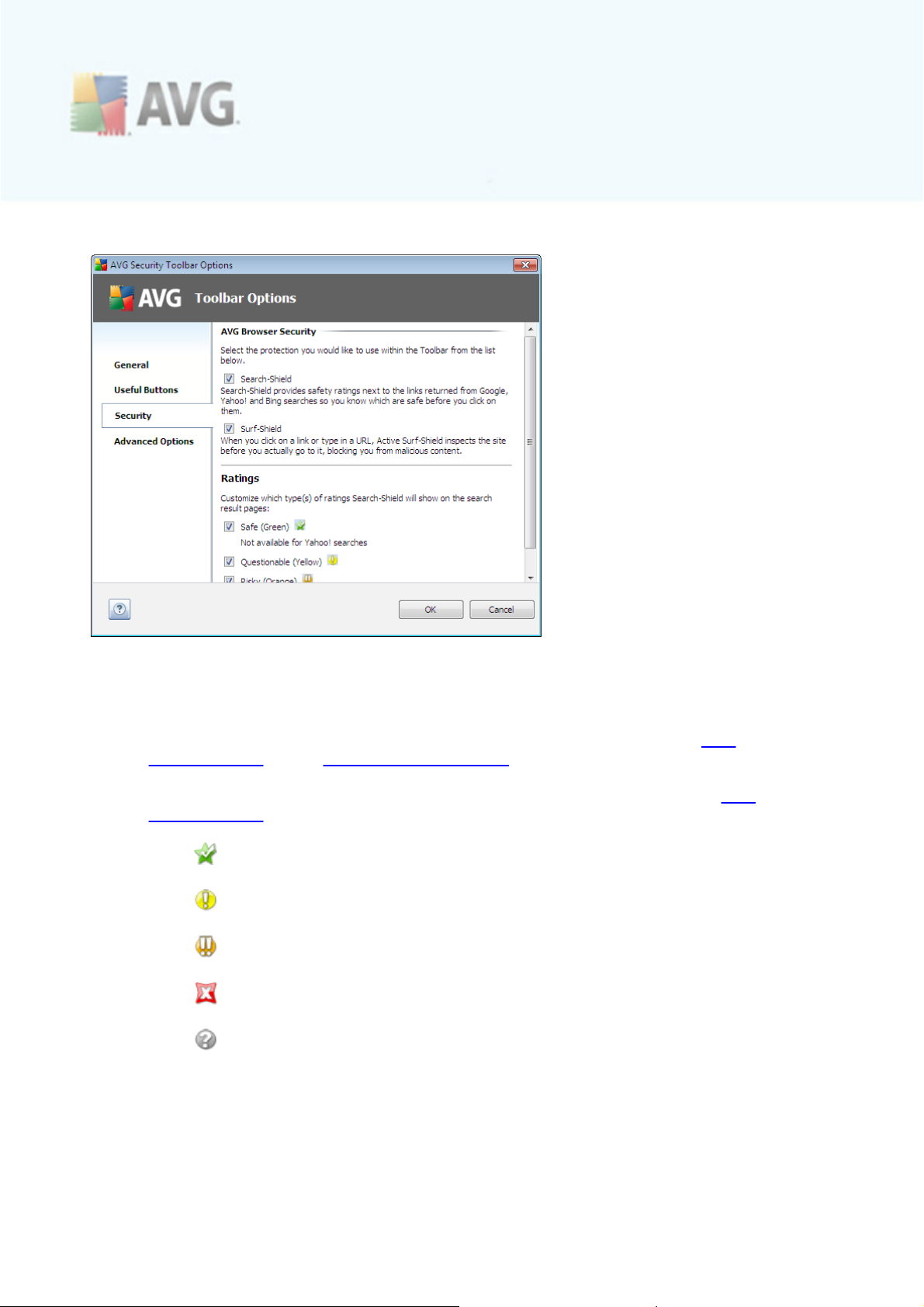
9.2.3. Tab Security
The Security tab is divided into two sections, AVG Browser Security and Ratings,
where you can mark specific check-boxes to assign AVG Security Toolbar
functionality you want to use:
· AVG Browser Security - check this item to activate or switch-off the AVG
Search-Shield and/or AVG Active Surf-Shield service
· Ratings - select graphical symbols used for search results ratings by the AVG
Search-Shield component that you want to use:
o
page is safe
o
page is somewhat suspicious
o
page containing links to positively dangerous pages
o
page contains active threats
o
page is not accessible, and so could not be scanned
Mark the respec tive option to c onfirm you want to be informed about this
specific threat level. However, display of the red mark assigned to pages
containing active and dangerous threats cannot be switched-off. Again, it is
recommended to keep the default configuration set by the program vendor
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 91
Page 92
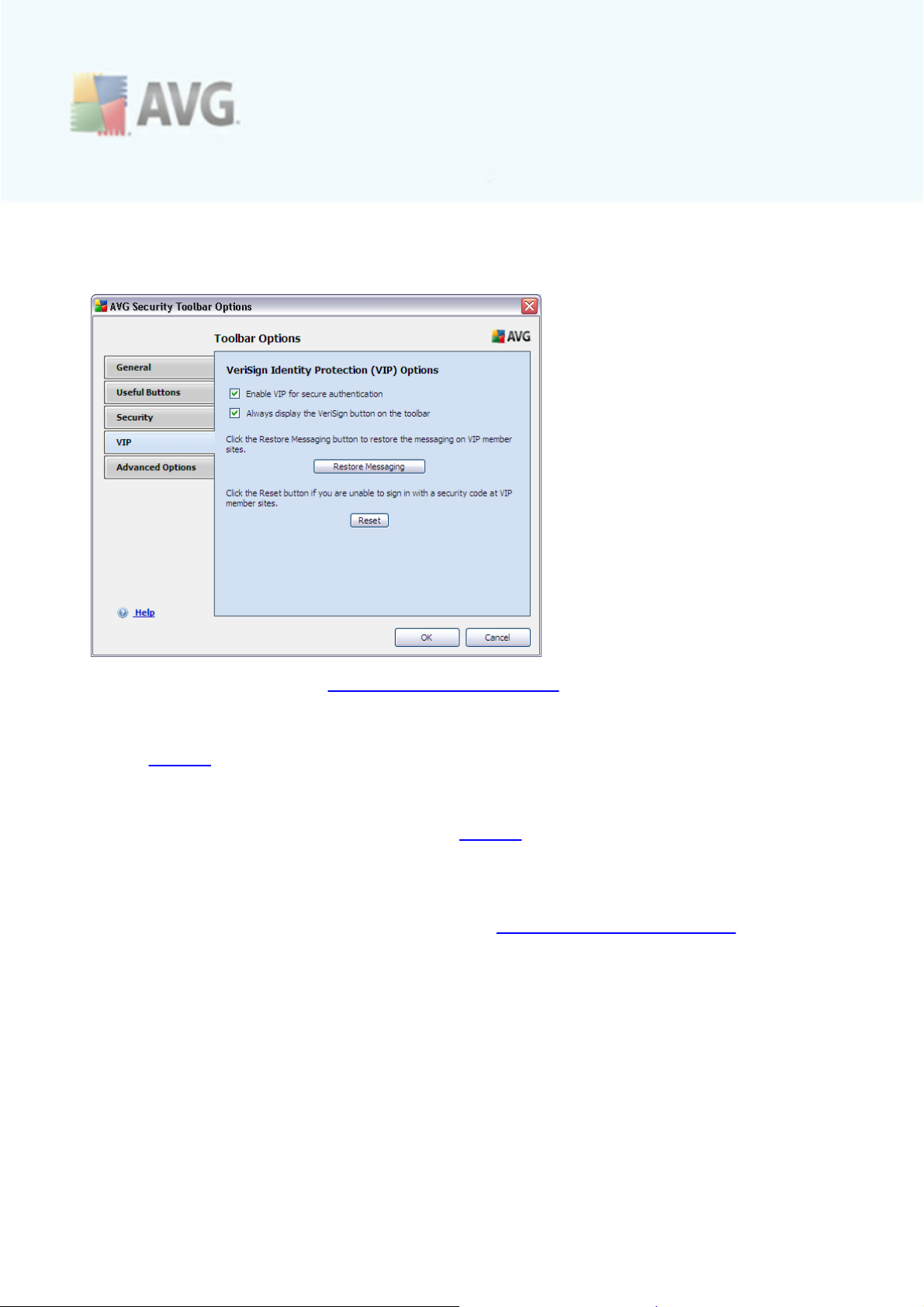
unless you have a real reason to change it.
9.2.4. Tab VIP
This tab allows you to set the VeriSign Identity Protection parameters. First dec ide
whether the following options should be allowed:
· Enable VIP for secure authentication - mark this option to activate the
VeriSign protection.
· Always display the VeriSign button on the toolbar - this option is only
activated in case you marked the previous Enable VIP for secure
authentication option. If chec ked, the VeriSign logo appears on the AVG
Security Toolbar. Other wise, the logo will be hidden.
Next, these two control buttons are available:
· Restore Messaging - when navigating to a registered member VIP website
you will be automatically informed about this fact by the following info panel:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 92
Page 93

In the bottom section of the panel you can see and activate the Don't remind
me again in this Web site option - if marked, the next time you enter the
specific website, the info panel will not be displayed again. However, if in the
future you dec ide to change this settings, and you will want to restore displaying
the member site info for all VIP websites, press the Restore Messaging button
to get back to the default settings for all registered domains.
· Reset - use this button in case the time synchronization on client and server
fails (for instance, when switc hing to daylight saving time, etc.); then you can
press the button to re-activate and synchronize the VIP protec tion.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 93
Page 94

9.2.5. Tab Advanced Options
On the Advanced Options tab first select what search engine you want to use as
default. You have the choice of AVG Secure Search, Baidu, WebHledani, Yandex and
Yahoo!. Having changed the default search engine, please restart your internet
browser for the change to take effect.
Further, you can activate or switch-off further specific AVG Security Toolbar settings
(the listed caption refers to the default AVG Secure Search settings):
· Set and keep AVG Secure Search as the search provider for Address bar -
if marked, this option allows you to type a search keyword directly into the
address bar into your Internet browser and the Google service will be used
automatically to search for relevant websites.
· Let AVG make suggestion on browser navigation errors (404/DNS) - if
when searching the web you run into a non-existing page, or a page that
cannot be displayed (404 error), you will be automatically redirected to a web
page that allows you to select from an overview of alternative topic-related
pages.
· Set and keep AVG Secure Search as the default search provider - Google is
the default search engine for web search within AVG Security Toolbar, and
activating this option it can also become your web browser default search
engine.
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 94
Page 95

10. AVG Advanced Settings
The advanced c onfiguration dialog of AVG 9 Internet Security opens in a new
window named Advanced AVG Settings. The window is divided into two sections: the
left part offers a tree-arranged navigation to the program configuration options. Select
the component you want to change the configuration of (or its specific part) to open
the editing dialog in the right-hand section of the window.
10.1. Appearance
The first item of the navigation tree, Appearance, refers to the general settings of
the AVG user interface and a few elementary options of the application's behavior:
Language selection
In the Language selection section you can chose your desired language from the
drop-down menu; the language will then be used for the entire AVG user interface.
The drop-down menu only offers those languages you have previously selected to be
installed during the installation process (see chapter Custom Installation - Component
Selection) plus English (that is installed by default). However, to finish switching the
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 95
Page 96
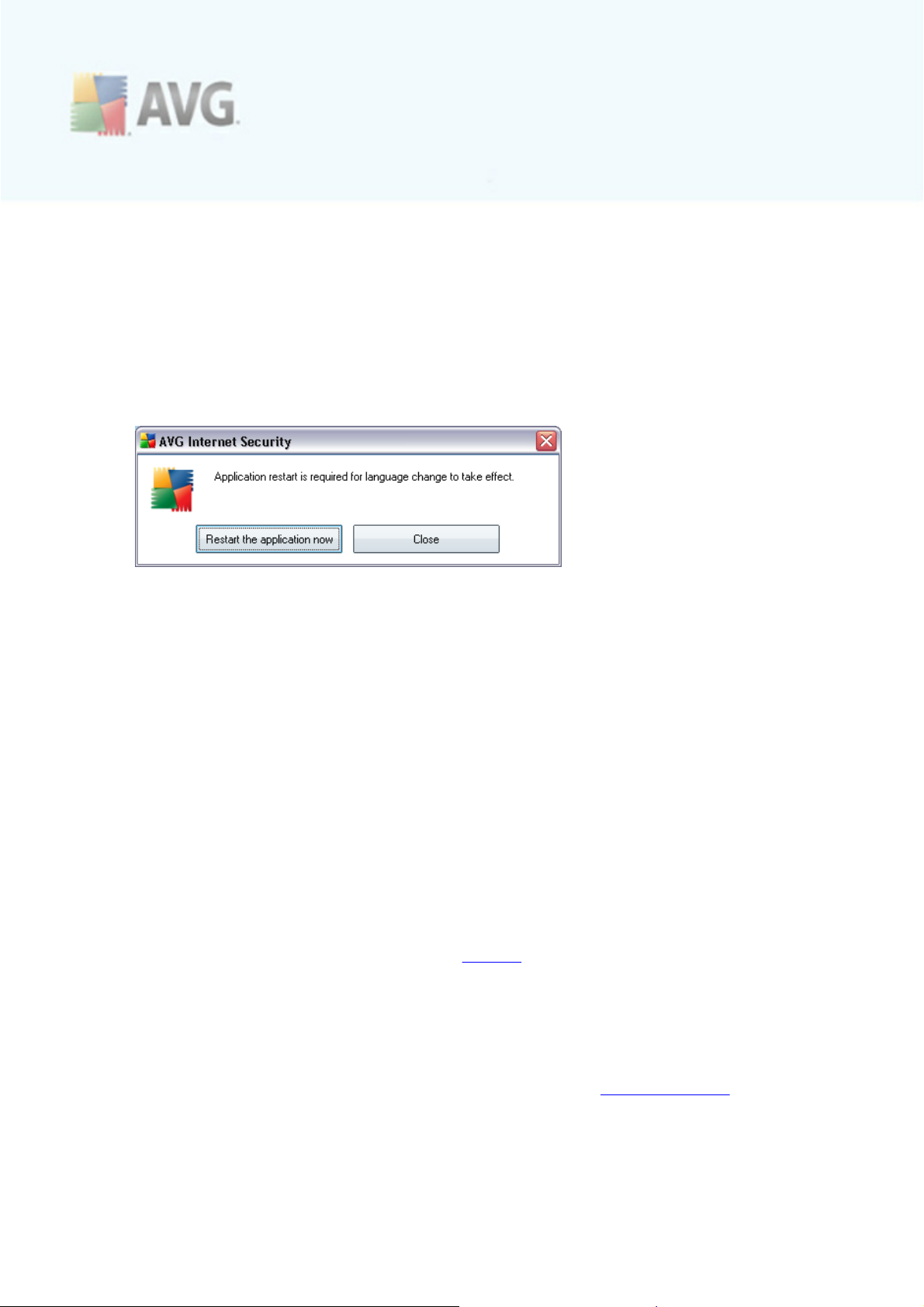
application to another language you have to restart the user interface; follow these
steps:
· Select the desired language of the application and confirm your selection by
pressing the Apply button (right-hand bottom corner)
· Press the OK button confirm
· New dialog window pops-up informing you the language change of AVG user
interface requires the application restart:
Balloon tray notifications
Within this section you can suppress display of system tray balloon notifications on
the status of the application. By default, the balloon notifications are allowed to be
displayed, and it is recommended to keep this configuration! The balloon notifications
typically inform on some AVG component's status change, and you should pay
attention to them!
However, if for some reason you decide you do not wish these notifications to be
displayed, or you would like only certain notifications (related to a specific AVG
component) to be displayed, you can define and specify your preferences by
checking/unchec king the following options:
· Display system tray notifications - by default, this item is checked (
switched on), and notifications are displayed. Uncheck this item to c ompletely
turn off the display of all balloon notifications. When turned on, you c an
further select what specific notifications should be displayed:
o
Display tray notifications about update - dec ide whether information
regarding AVG update process launch, progress, and finalization should be
displayed;
o
Display components state change notifications - decide whether
information regarding component's activity/inactivity or its possible
problem should be displayed. When reporting a component's fault status,
this option equals to the informative function of the system tray icon
(color changing) reporting a problem in any AVG component;
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 96
Page 97
o
Display Resident Shield related tray notifications - decide whether
information regarding file saving, copying, and opening processes should
be displayed or suppressed (this configuration only demonstrates if the
Resident Shield Auto-heal option is on);
o
Display tray notifications about scanning - decide whether
information upon automatic launch of the scheduled scan, its progress
and results should be displayed;
o
Display Firewall related tray notifications - decide whether
information concerning Firewall status and processes, e.g. component's
activation/deactivation warnings, possible traffic blocking etc. should be
displayed;
o
Display E-mail Scanner related tray notifications - decide whether
information upon scanning of all incoming and outgoing e-mail messages
should be displayed.
Gaming mode
This AVG function is designed for full-screen applic ations where possible AVG
information ballons (displayed e.g. when a scheduled scan is started) would be
disturbing (they c ould minimize the application or corrupt its graphics). To avoid this
situation, keep the check box for the Enable gaming mode when a full-screen
application is executed option marked (default setting).
10.2. Sounds
Within the Sounds dialog you can specify whether you want to be informed about
specific AVG actions by a sound notification. If so, check the Enable sound events
option (off by default) to activate the list of AVG actions:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 97
Page 98

Then, select the respec tive event from the list and browse (Browse) your disk for an
appropriate sound you want to assign to this event. To listen to the selected sound,
highlight the event in the list and push the Play button. Use the Delete button to
remove the sound assigned to a spec ific event.
Note: Only *.wav sounds are supported!
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 98
Page 99
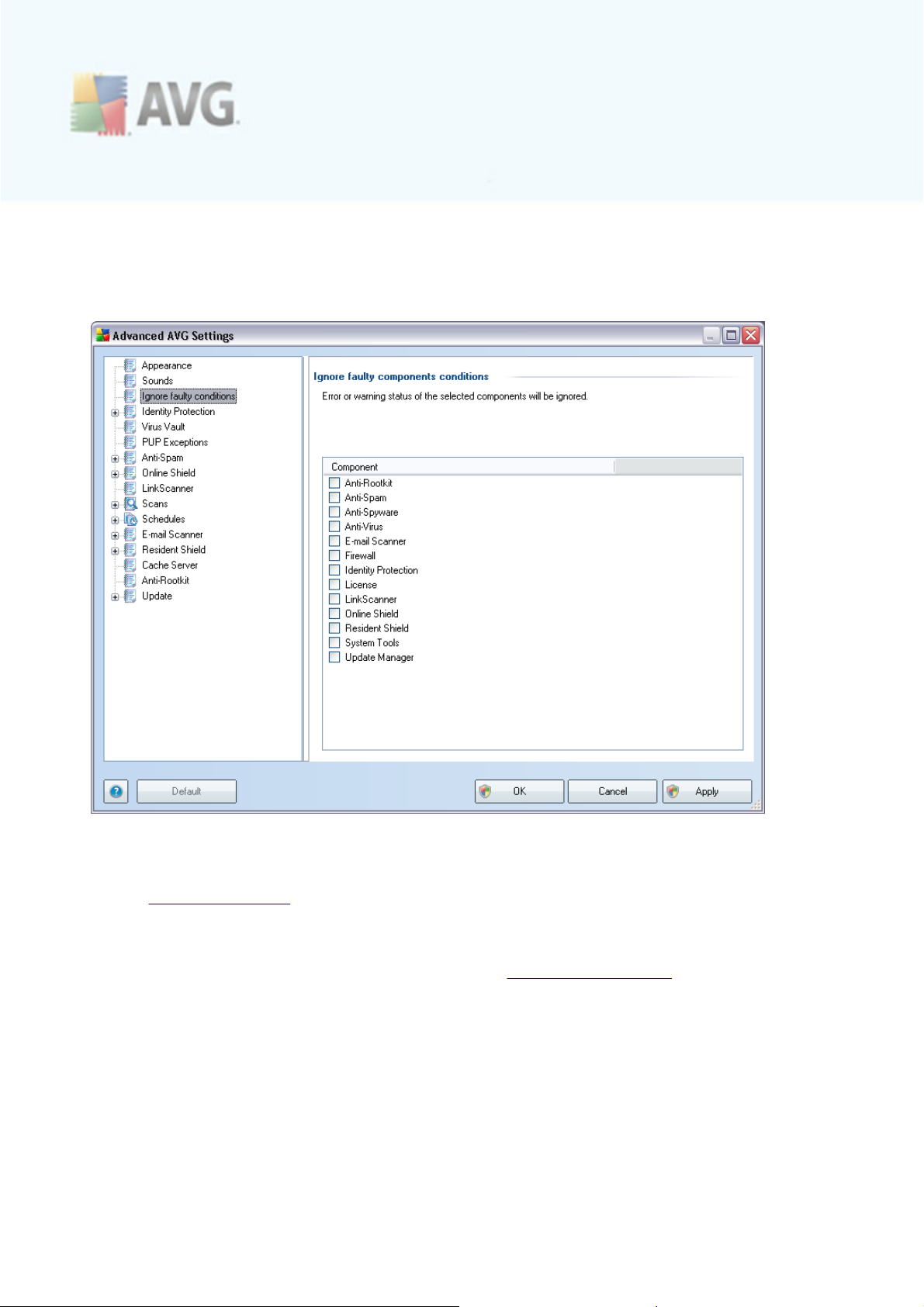
10.3. Ignore Faulty Conditions
In the Ignore faulty components conditions dialog you can tick those c omponents
that you do not want to get informed about:
By default, no c omponent is selected in this list. It means that if any component get
to an error status, you will be informed about it immediately via:
· system tray icon - while all parts of AVG are working properly, the icon is
displayed in four colors; however, if an error occurs, the icon appears with a
yellow exclamation mark,
· text description of the existing problem in the Security Status Info sec tion of
the AVG main window
There might be a situation that for some reason you need to switc h a component off
temporarily (this is not recommended, you should try to keep all components
permanently on and in default configuration, but it may be happen). In that case the
system tray icon automatically reports the component's error status. However, in this
very case we cannot talk about an actual error since you have deliberately induced it
yourself, and you are aware of the potential risk. At the same time, once being
displayed in grey color, the icon cannot actually report any possible further error that
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 99
Page 100
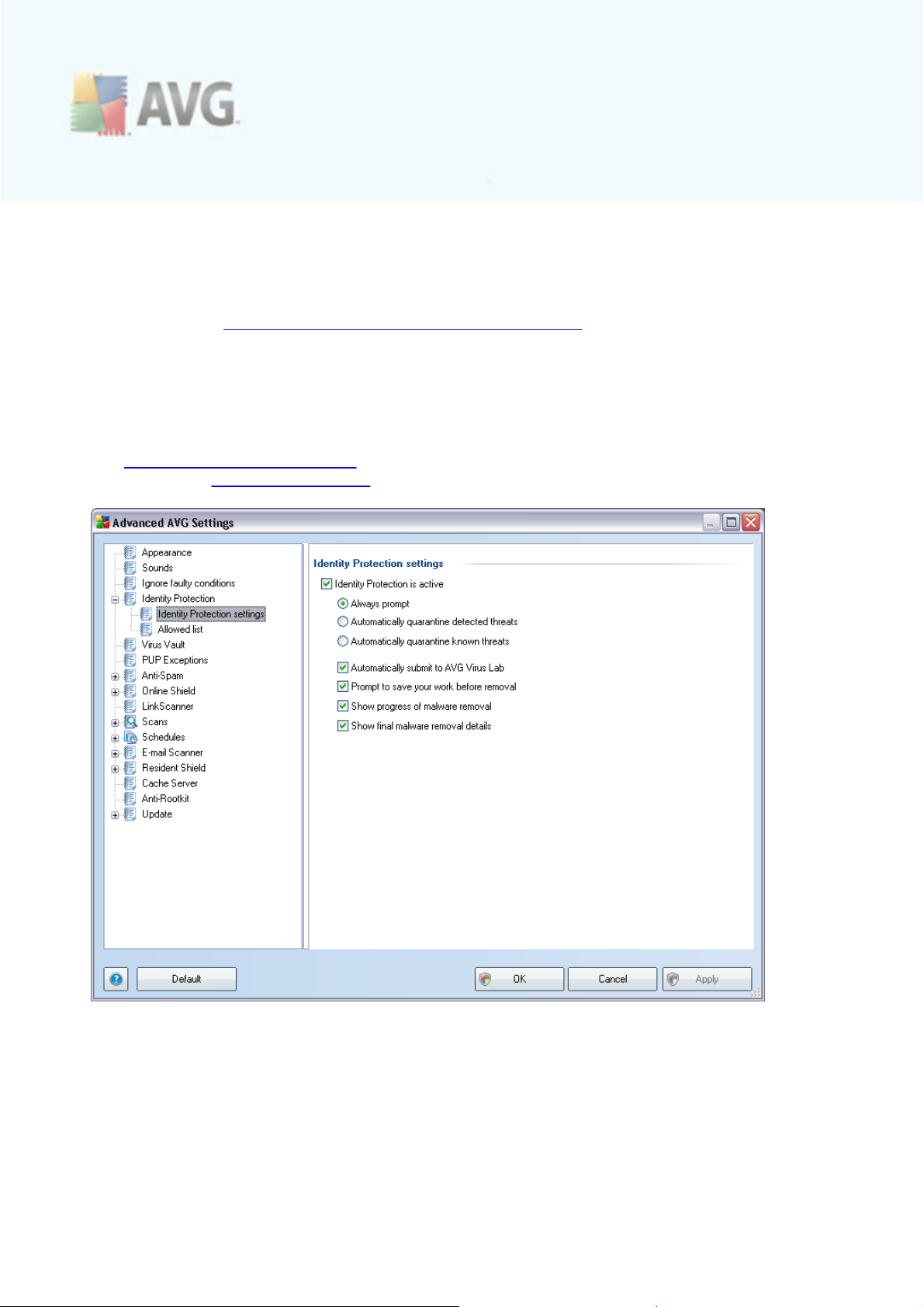
might appear.
For this situation, within the above dialog you can select components that may be in
an error state (or switched off) and you do not wish to get informed about it. The
same option of Ignoring component state is also available for specific components
directly from the c omponents overview in the AVG main window.
10.4. Identity Protection
10.4.1. Identity Protection Settings
The Identity Protection settings dialog allows you to switch on/off the elementary features of the Identity Protection component:
Identity Protection is active (on by default) – uncheck to turn off the Identity
Protection component.
We strongly recommend not to do this unless you have to!
When the Identity Protection is activated, you can specify what to do when a threat
is detected:
A V G 9 Internet Sec urity © 2 0 10 C opyright A V G T e c hnologies C Z, s.r.o. A ll rights re s e rv ed. 10 0
 Loading...
Loading...