Page 1
BayRS Version 14.00
Part No. 308645-14.00 Rev 00
September 1999
4401 Great America Parkway
Santa Clara, CA 95054
Configuring Traffic Filters and Protocol Prioritization
Page 2

Copyright © 1999 Nortel Networks
All rights reserved. Printed in the USA. September 1999.
The information in this document is subject to change without notice. The statements, configurations, technical data,
and recommendations in this document are believed to be accurate and reliable, but are presented without express or
implied warranty. Users must t ak e full re sponsib ility fo r th eir a pplic atio ns o f a ny products specified in this document.
The information in this document is proprietary to Nortel Networks NA Inc.
The software described in this document is furnished under a license agreement and may only be used in accordance
with the terms of that license. A summary of the Software License is included in this document.
Trademarks
NORTEL NETWORKS is a trademark of Nortel Networks.
Bay Networks, AN, BCN, BLN, BN, FRE, LN, Optivity and PPX are registered trademarks and Advanced Remote
Node, ANH, ARN, ASN, BayRS, BaySecure, BayStack, BayStream, BCC, and System 5000 are trademarks of Nortel
Networks.
Microsoft, MS, MS-DOS, Win32, Windows, and Windows NT are registered trademarks of Microsoft Cor poration.
All other trademarks and registered trademarks are t he property of their respective owners.
Restricted Rights Legend
Use, duplication, or disclosure by the United States Government is subject to restrictions as set forth in subparagraph
(c)(1)(ii) of the Rights in Technical Data and Computer Sof tware clause at DFARS 252.227-7013.
Notwithstanding any other license agreement that may pertain to, or accompany the delivery of, this computer
software, the rights of the United States Government regarding its use, reproduction, and disclosure are as set forth in
the Commercial Computer Software-Restricted Rights cl ause at FAR 52.227-19.
Statement of Conditions
In the interest of improvi ng internal design, operational fun c tion , an d/o r re lia bi lity, No rtel Ne tworks NA Inc. re se rv es
the right to make changes to the products described in this document without notice.
Nortel Networks NA Inc. does not assume any liability that may occur due to the use or application of the product(s)
or circuit layout(s) described herein.
Portions of the code in this software product may be Copyright © 1988, Regents of the University of California. All
rights reserved. Redistribution and use in source and binary forms of such portions are permitted, provided that the
above copyright notice and this paragraph are duplicated in all such forms and that any docu mentation, advertising
materials, and other materials related to such distribution and use acknowledge that su ch portions of the software were
developed by the University of California, Berkeley. The name of the University may not be used to endorse or
promote products derived from such portions of the software without specific prior written permission.
SUCH PORTIONS OF THE SOFTWARE ARE PROVIDED “AS IS” AND WITHOUT ANY EXPRESS OR
IMPLIED WARRANTIES, INCLUDING, WITHOUT LIMITATION, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE.
In addition, the program and information containe d herein are licensed only pursuant to a license agreement that
contains restrictions on use and disclosure (that may incorporate by reference certain limitations and notices imposed
by third parties).
ii
308645-14.00 Rev 00
Page 3

Nortel Networks NA Inc. Software License Agreement
NOTICE: Please carefully read this license agre ement before copying or using the accompanying software or
installing the hardware unit with pre-enabled software (each of which is referred to as “Software” in this Agreement).
BY COPYING OR USING THE SOFTWARE, YOU ACCEPT ALL OF THE TERMS AND CONDITIONS OF
THIS LICENSE AGREEMENT. THE TERMS EXPRESSED IN THIS AGREEMENT ARE THE ONLY TERMS
UNDER WHICH NORTEL NETWORKS WILL PERMIT YOU TO USE THE SOFTWARE. If you do not accept
these terms and conditions, return the product, unused and in the original shipping container, within 30 days of
purchase to obtain a credit for the full purchase price.
1. License Grant. Nortel Networks NA Inc. (“Nortel Networks”) grants the end user of the Software (“Licensee”) a
personal, nonex clusive, nontransferable license: a) to use the So ftwa re eithe r on a sing le com puter o r, if applicable, on
a single authorized device identified by host ID, for which it was originally acquired; b) to copy the Software solely
for backup purposes in support of authorized use of t he Software; and c) to use and copy the associated user manual
solely in support of authoriz ed use of th e Softwa re b y Licen see. Thi s license applies t o the So ftware o nly and d oes not
extend to Nortel Networks Agent software or other Nortel Networks software products. Nortel Networks Agent
software or other Nortel Networks software products are licensed for use under the terms of the applicable Nortel
Networks NA Inc. Software License Agreement that accompanies such software and upon payment by the end user of
the applicable license fees for such software.
2. Restrictions on use; reservation of rights. The Software and user manuals are protected und er copyright laws.
Nortel Networks and/or its licensors retain all title and ownership in both the Software and user manuals, including
any revisions made by Nortel Networks or its licensors. The copyright notice must be reproduced and included with
any copy of any portion of the Software or user manuals. Licensee may not modify, translate, decompile, disassemble,
use for any competitive analysis, reverse engineer, distribute, or create derivative works from the Software or user
manuals or any copy, in whole or in part. Except as expressly provided in this Agreement, Licensee may not copy or
transfer the Software or user manuals, in whole or in part. The Software and user manuals embody Nortel Networks’
and its licensors’ confidential and proprietary intellectual property. Licensee shall not sublicense, assign, or otherwise
disclose to any third party the Software, or any information about the operation, design, performance, or
implementation of the Software and user manuals that is confidential to Nortel Networks and its licensors; however,
Licensee may grant permission to its consultants, subcontractors, a nd agents to use the Softw are at Licensee’s facility,
provided they have agreed to use the Software only in accordance with the terms of this license.
3. Limited warranty . Nortel Networks warrants each item of Software, as delivered by Nortel Networks and properly
installed and operated on Nortel Networks hardware or other equipment it is originally licensed for, to function
substantially as described in its accompanying user manual during its warranty period, which begins on the date
Software is first shipped to Licensee. If an y item of S oftware f ails to so function d uring its w arranty period, as the sole
remedy Nortel Networks will at its discretion provide a suitable fix, patch, or workaround for the problem that may be
included in a future Software release. Nortel Networks further warrants to Licensee that the media on which the
Software is provided will be free from defec ts in materials and wo rkman ship under no rmal use for a peri od of 90 da ys
from the date Software is first shipped to Licensee. Nortel Networks will replace defective media at no charge if it is
returned to Nortel Netw orks during the warranty period along with proof of the date of ship ment. This warranty does
not apply if the media has been damaged as a result of accident, misuse, or abuse. The Licensee assumes all
responsibility for selection of the Software to achieve Licensee’s intended results and for the installation, use, and
results obtained from the Software. Nortel Networks does not warrant a) that the functions contained in the software
will meet the Licensee’s requirements, b) that the Software will operate in the hardware or software combinations that
the Licensee may select, c) that the operation of the Software will be uninterrupted or error free, or d) that all defects
in the operation of the Softw are will be corrected . Nortel Network s is not obligate d to remedy an y Software defect that
cannot be reproduced with the latest Software release. These warranties do not apply to the Software if it has been (i)
altered, except by Nortel Networks or in accordance with i ts instructions; (ii) used in conjunction with another
vendor’s product, resulting in the de fect; or (iii) damage d by improper environment, abuse, misuse, accident, or
negligence. THE FOREGOING WARRANTIES AND LIMITATIONS ARE EXCLUSIVE REMEDIES AND ARE
IN LIEU OF ALL OTHER WARRANTIES EXPRESS OR IMPLIED, INCLUDING WITHOUT LIMITATION ANY
WARRANTY OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. Licensee is responsible
308645-14.00 Rev 00
iii
Page 4

for the security of its own data and information and for maintaining adequate procedures apart from the Software to
reconstruct lost or altered files, data, or programs.
4. Limitation of liability. IN NO EVENT WILL NORTEL NETWORKS OR ITS LICENSORS BE LIABLE FOR
ANY COST OF SUBSTITUTE PROCUREMENT; SPECIAL, INDIRECT, INCIDENTAL, OR CONSEQUENTIAL
DAMAGES; OR ANY DAMAGES RESULTING FROM INACCURATE OR LOST DATA OR LOSS OF USE OR
PROFITS ARISING OUT OF OR IN CONNECTION WITH THE PERFORMANCE OF THE SOFTWARE, EVEN
IF NORTEL NETWORKS HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. IN NO EVENT
SHALL THE LIABILITY OF NORTEL NETWORKS RELA TING TO THE SOFTW ARE OR THIS AGREEMENT
EXCEED THE PRICE PAID TO NORTEL NETWORKS FOR THE SOFTWARE LICENSE.
5. Government Licensees. This provision applies to a ll Softwa re and docum entation acquired d irectly or i ndirectly by
or on behalf of the United States Government. The Software and documentation are commercial products, licensed on
the open market at market prices, and were developed entirely at private expense and without th e use of any U.S.
Government funds. The license to the U.S. Government is granted only with restricted rights, and use, duplication, or
disclosure by the U.S. Government is subject to the restrictions set forth in subparagraph (c)(1) of the Commercial
Computer Software––Restricte d Rig hts cla u se o f FAR 52.227-19 and the limita tions se t o ut in thi s licen se for civilian
agencies, and subparagraph (c)(1)(ii ) of the Rights in Technical Data and Computer Software clause of DFARS
252.227-7013, for agencies of t he Department of Defense or their successors, whichever is applicable.
6. Use of Software in the European Community. This provision applies to all Software acquired for use within the
European Community. If Licensee uses the Software within a country in the European Community, the Software
Directive enacted by the Council of European Communities Directive dated 14 May, 1991, will apply to the
examination of the Software to facilitate interoperability. Licensee agrees to notify Nortel Networks of any such
intended examination of the Software an d may procure support and assistance from Nortel Networks.
7. Term and termination. This license is effective until terminated; however, all of the restrictions with respect to
Nortel Networks’ copyright in the Software and user manuals will cease being effective at the date of expiration of the
Nortel Networks copyright; those restrictions relating to use and disclosure of Nortel Networks’ confidential
information shall continue in effect. Licensee may terminate this license at any time. The license will automatically
terminate if Licensee fails to comply with any of the terms and conditions of the license. Upon termination for any
reason, Licensee will immediat ely destroy or return to Nortel Networks the Software, user manuals, and all copies.
Nortel Networks is not liable to Licensee for damages in any form solely by reason of the termination of this license.
8. Export and Re-export. Licensee agrees not to export, directly or indirectly, the Software or related technical data
or information without first obtaining any required export licenses or other governmental approvals. Without limiting
the foregoing, Licensee, on behalf of itself and its subsidiaries and affiliates, agrees that it will not, without first
obtaining all export licenses and approvals required by the U.S. Government: (i) export, re-export, transfer, or divert
any such Software or technical data, or any direct product thereof, to any country to which such exports or re-exports
are restricte d or em b argoed under United States expo r t con tr o l la w s an d r egulations, or to any national or resident of
such restricted or embargoed countries; or (ii) provide the Software or related technical data or information to any
military end user or for any military end use, including the design, development, or production of any chemical,
nuclear, or biological weapons.
9. General. If any provision of this Agreement is held to be invalid or unenforceable by a court of competent
jurisdiction, the remainder of the provisions of this Agreement shall remain in full force and effect. This Agreement
will be governed by the laws of the state of California.
Should you have any questions concerning this Agreement, contact Nortel Networks, 4401 Great America Par kwa y,
P.O. Box 58 185, Santa Clara, California 95054-8185.
LICENSEE ACKNOWLEDGES THAT LICENSEE HAS READ THIS AGREEMENT, UNDERSTANDS IT, AND
AGREES TO BE BOUND BY ITS TERMS AND CONDITIONS. LICENSEE FURTHER AGREES THAT THIS
AGREEMENT IS THE ENTIRE AND EXCLUSIVE AGREEMENT BETWEEN NORTEL NETWORKS AND
LICENSEE, WHICH SUPERSEDES ALL PRIOR ORAL AND WRITTEN AGREEMENTS AND
COMMUNICATIONS BETWEEN THE PARTIES PERTAINING TO THE SUBJECT MATTER OF THIS
AGREEMENT. NO DIFFERENT OR ADDITIONAL TERMS WILL BE ENFORCEABLE AGAINST NORTEL
NETWORKS UNLESS NORTEL NETWORKS GIVES ITS EXPRESS WRITTEN CONSENT, INCLUDING AN
EXPRESS WAIVER OF THE TERMS OF THIS AGREEMENT.
iv
308645-14.00 Rev 00
Page 5
Contents
Preface
Before You Begin ............................................................................................................. xv
Text Conventions .............................................................................................................xvi
Acronyms ........................... .......................... .......................... ......................... ................xvii
Hard-Copy Technical Manuals ........ ...... ............................................. ....... ...... ................. xx
How to Get Help .............................................................................................................. xx
Chapter 1
Using Traffic Filters
What Are Traffic Filters? .................................................................................................1-1
Inbound Traffic Filters ...............................................................................................1-2
Outbound Traffic Filters ............................................................................................1-3
What Is Protocol Prioritization? ......................................................................................1-3
Filtering Strategies ...... ....... ............................................. ....... ...... ...................................1-4
Direct Traffic .............................................................................................................1-4
Drop or Accept Traffic ...............................................................................................1-4
Prioritize Traffic .........................................................................................................1-4
Combine Filters ........................................................................................................1-5
Build a Firewall .........................................................................................................1-5
Traffic Filter Components ................................................................................................1-6
Criteria .....................................................................................................................1-6
Predefined and User-Defined Criteria ...............................................................1-7
Ranges .............................. ................................. ................................ .................... 1 -11
Actions ...................................................................................................................1-11
Using Filter Templates ..................................................................................................1-13
Summary of Traffic Filter Support .................................................................................1-14
308645-14.00 Rev 00
v
Page 6

Chapter 2
Using Protocol Prioritization Queues
About Protocol Priorit izati on ........................................... ....... ...... ...... ....... ...... ....... ...... ...2-1
Priority Queuing .......................................................................................................2-2
The Dequeuing Process ...........................................................................................2-3
Bandwidth Allocation Algorithm .........................................................................2-4
Strict Dequeuing Algorithm ................................................................................2-7
Enabling Protocol Prioritization .......................................................................................2-9
Enabling Protocol Prioritization on an ATM Circuit .......................................................2-10
Tuning Protocol Prioritization ........................................................................................2-11
Tuning Concepts ....................................................................................................2-11
Percent of Bandwidth .......................................................................................2-11
Queue Size ......................................................................................................2-12
Latency ............................................................................................................2-14
Editing Protocol Prioritization Parameters ..............................................................2-15
Monitoring Protocol Prioritization Statistics ............................................................2-16
Chapter 3
Inbound Traffic Filter Criteria and Actions
Transparent Bridge Criteria and Actions .........................................................................3-2
Predefined Transparent Bridge Criteria ....................................................................3-3
User-Defined Transparent Bridge Criteria ................................................................3-4
Transparent Bridge Actions ......................................................................................3-4
Source Route Bridging Criteria and Actions ...................................................................3-5
Predefined SRB Criteria ...........................................................................................3-5
Specifying an SRB Criterion Range ..................................................................3-5
User-Defined SRB Criteri a .............................................. ...... ...................................3-6
SRB Actions .............................................................................................................3-6
DECnet Phase IV Criteria and Actions ...........................................................................3-7
Predefined DECnet Criteria .....................................................................................3-7
User-Defined DECnet Criteria ............................................................ ...... ....... ......... 3-7
DECnet Actions .............................. ....... ...... ....... ...... ....... .........................................3-7
DLSw Criteria and Actions .............................................................................................3-8
Predefined DLSw Criteria ........................................................................................3-8
User-Defined DLSw Criteri a ............................... ...... ....... ...... ...... ....... ...... ................3-8
DLSw Actions ...........................................................................................................3-8
vi
308645-14.00 Rev 00
Page 7
IP Criteria and Actions ....................................................................................................3-9
Predefined IP Criteria ...............................................................................................3-9
User-Defined IP Criter ia .... ....... ...... ....... ...... ....... ...... ....... .........................................3-9
IP Actions . ...... ...... ....... ...... ....... ...... ....... ............................................. ...... ....... .......3-1 0
IPX Criteria and Actio ns ................. ...... ....... ...... ....... ...... ............................................. .3-1 1
Predefined IPX Criteria ..........................................................................................3-11
User-Defined IPX Criteri a ........................................................................ ....... ...... .3-12
IPX Actions .............................................................................................................3-12
LLC2 Criteria and Actions ............................................................................................3-12
Predefined LLC2 Criteria .......................................................................................3-12
User-Defined LLC2 Criteri a ................................ ...... ....... ...... ...... ....... ...... .............. 3 -1 3
LLC2 Actions ..........................................................................................................3-13
OSI Criteria and Actions ...............................................................................................3-13
Predefined OSI Criteria ..........................................................................................3-13
User-Defined OSI Criter ia ........ ...... ....... ............................................. ...... ....... .......3-1 4
OSI Actions ............................................................................................................3-14
VINES Criteria and Actions ..........................................................................................3-14
Predefined VINES Criteria .....................................................................................3-14
User-Defined VINES Criteria ...................... ....... ...... ....... ...... ...... ....... ...... ....... ...... .3-1 5
VINES Actions ........................................................................................................3-15
XNS Criteria and Actio ns ...................... ....... ...... ....... ............................................. ...... .3-1 5
Predefined XNS Criteria .........................................................................................3-15
User-Defined XNS Criteri a .............................................. ...... .................................3-16
XNS Actions ...........................................................................................................3-16
Chapter 4
Outbound Traffic Filter Criteria and Actions
Selecting Predefined Cr ite r ia ....................... ...... ....... ...... ....... ...... ...................................4-2
Predefined Data Link Criteria ...................................................................................4-2
Predefined IP Criteria ...............................................................................................4-5
Specifying Criteria Common to IP and Data Link Headers ......................................4-6
Selecting User-Defined Cr iteria ............ ....... ...... ....... ...... ....... ...... ...... .............................4-7
Data Link Reference Points ......................................................................................4-7
IP Reference Points ....................... ....... ...... ............................................. ....... ...... ...4-9
Selecting Actions ................................................................... ...... ...... ...........................4-10
Filtering Actions .................................... ...... ............................................. ....... ...... .4-1 0
308645-14.00 Rev 00
vii
Page 8

Prioritizing Actions .................................................................................................4-11
Dial Service Actions ...............................................................................................4-11
Chapter 5
Specifying Common Criterion Ranges
Specifying MAC Address Ranges ...................................................................................5-2
SRB Source MAC Addresses ..................................................................................5-2
SRB Functional MAC Addresses .............................................................................5-3
Specifying VINES Address Ranges ................................................................................5-3
Specifying Source and Destination SAP Code Ranges .................................................5-4
Specifying Frame Relay NLPID Ranges .........................................................................5-5
Specifying PPP Protocol ID Ranges ...............................................................................5-5
Specifying TCP and UDP Port Ranges ..........................................................................5-6
Specifying Ethernet Type Ranges ..................................................................................5-7
Specifying IP Protocol ID and Type of Service Ranges ................................................5-10
Chapter 6
Applying Inbound Traffic Filters
Displaying the Inbound Traffic Filters Window ................................................................6-2
Preparing Inbound Traffic Filt er Tem plates ............................ ...... ...... ....... ...... ....... ...... ...6-3
Creating a Template .................................................................................................6-4
Customizing Templates ............................................................................................6-6
Copying a Te mplate .... ....... ...... ....... ...... ....... ...... ....... .........................................6-6
Editing a Template ...... ....... ...... ....... ...... ....... ............................................. ...... ...6-7
Creating an Inbound Traffic Filter ..................................................................................6-10
Editing an Inbound Traffic Filter ....................................................................................6-11
Enabling or Disabling an Inbound Traffic Filter .............................................................6-15
Deleting an Inbound Traffic Filter ..................................................................................6-16
Specifying User-Defined Criteria ..................................................................................6-17
Changing Inbound Traffic Filter Precedenc e ...... ....... ...... ............................................. .6-18
Chapter 7
Applying Outbound Traffic Filters
Displaying the Priority/Outbound Filters Window ...........................................................7-2
Preparing Outbound Traffic Filter Templates ..................................................................7-4
Creating a Template .................................................................................................7-4
Specifying Prioritization Length ................................................................................7-7
viii
308645-14.00 Rev 00
Page 9
Customizing Templates ............................................................................................7-9
Copying a Te mplate .... ....... ...... ....... ...... ....... ...... ....... .........................................7-9
Editing a Template ...... ....... ...... ....... ...... ....... ............................................. ...... .7-1 0
Creating an Outbound Traffic Filter ...............................................................................7-13
Editing an Outbound Traffic Filter ................................................................................7-14
Enabling or Disabling an Outbound Traffic Filter ..........................................................7-18
Deleting an Outbound Traffic Filter ...............................................................................7-19
Specifying User-Defined Criteria ..................................................................................7-20
Changing Outbound Traffic Filter Precedence ..............................................................7-21
Chapter 8
Configuring IP Inbound
Traffic Filters Using the BCC
IP Inbound Traffic Filter Concepts and Terminology .......................................................8-2
IP Traffic Filter Templates ................................... ...... ............................................. ...8-2
IP Inbound Traffic Filters ..........................................................................................8-3
Filter Precedence .....................................................................................................8-4
Filter Criteria and Actions .........................................................................................8-5
IP Filtering Actions ...... ....... ...... ....... ...... ....... ...... ....... ...... ...... .............................8-5
Extended and Nonextended Filtering Modes ...........................................................8-6
Creating an IP Traffic Filter Template ..............................................................................8-7
Creating an IP Inbound Traffic Filter ...............................................................................8-8
Specifying Match Criteria for IP Inbound Traffic Filters and Templates ..........................8-9
Specifying Source and Destination Networks As Match Criteria ...........................8-10
Specifying Source and Destination TCP and UDP Ports As Match Criteria ..........8-10
Specifying Protocol Identifiers As Match Criteria ...................................................8-13
Specifying the Type of Service (ToS) As Match Criteria .........................................8-15
Specifying TCP-Established Match Criteria ...........................................................8-15
Specifying User-Defined Criteria ............................................................................8-16
Specifying the Action of Inbound Traffic Filters and Templates ....................................8-16
Specifying the Log Action .......................................................................................8-19
Disabling and Reenabling IP Traffic Filters on an IP Interface ......................................8-20
Configuration Examples ...............................................................................................8-20
Creating an IP Traffic Filter Template .....................................................................8-20
Applying the Filter Template to an IP Traffic Filter ..................................................8-21
Creating a Traffic Filter Without Using a Filter Template ........................................8-22
308645-14.00 Rev 00
ix
Page 10

Appendix A
Site Manager Protocol Prioritization Parameters
Priority Interface Parameter Descriptions ...................................................................... A-2
Prioritization Length Parameters ................................................................................... A-7
Appendix B
Examples and Implementation Notes
Traffic Filter Example for Basic IP Network Security ...................................................... B-1
Inbound Traffic Filter Examples ..................................................................................... B-3
Protocol Prioritization Examples .................................................................................... B-7
Creating an Outbound Traffic Filter ......................................................................... B-7
Implementation Notes .................................................................................................. B-11
Filtering Outbound Frame Relay Traffic ....... ............................................. ....... ...... B -11
Filtering over a Dial Backup Line ........................................................................... B-11
Using a Drop-All Filter As a Firewall ..................................................................... B-12
Using Outbound Traffic Filters for LAN Protocols .................................................. B-13
Index
x
308645-14.00 Rev 00
Page 11
Figures
Figure 2-1. Protocol Prioritization Dequeuing ............................................................2-3
Figure 2-2. Bandwidth Allocation Algorithm ...............................................................2-6
Figure 2-3. Strict Dequeuing Algorithm ......................................................................2-8
Figure 2-4. Priority Queue Statistics for the Queue Size Example ...........................2-13
Figure 2-5. Reconfigured Priority Queue Statistics for the Queue Size Examples ..2-14
Figure 3-1. Header Reference Fields for Transparent Bridge Encapsulation Methods 3-2
Figure 4-1. Predefined Data Link Criteria for Outbound Traffic Filters .......................4-4
Figure 4-2. Predefined IP Criteria for Outbound Traffic Filters ...................................4-6
Figure 4-3. Data Link Reference Points in an SRB Packet Bridged over
Bay Networks Proprietary Frame Relay ...................................................4-8
Figure 4-4. Data Link Reference Points in an IEEE 802.2 LLC Header .....................4-8
Figure 4-5. IP Reference Points in an IP-Encapsulated SRB
Packet Bridged over PPP ........................................................................4-9
Figure 6-1. Inbound Traffic Filters Window .................................................................6-3
Figure 6-2. Filter Template Management Window ......................................................6-5
Figure 6-3. Create Template Window .........................................................................6-5
Figure 6-4. Edit Template Window .............................................................................6-8
Figure 6-5. Create Filter Window .............................................................................6-11
Figure 6-6. Edit Filters Window ................................................................................6-13
Figure 6-7. Add User-Defined Field Window ............................................................6-18
Figure 6-8. Filters Window Showing Filter Precedence ...........................................6-19
Figure 6-9. Change Precedence Window ............ ...... ....... .......................................6-20
Figure 6-10. Filters Window Showing New Order of Precedence ....................... ...... .6-2 0
Figure 7-1. Displaying the Priority/Outbound Filters Window .....................................7-3
Figure 7-2. Priority/Outbound Filters Window ............................................................7-3
Figure 7-3. Filter Template Management Window ......................................................7-6
Figure 7-4. Create Priority/Outbound Template Window ............................................7-6
Figure 7-5. Prioritization Length Window ...................................................................7-7
Figure 7-6. Edit Priority/Outbound Template Window ..............................................7-11
308645-14.00 Rev 00
xi
Page 12

Figure 7-7. Create Filter Window .............................................................................7-14
Figure 7-8. Edit Priority/Outbound Filters Window ...................................................7-16
Figure 7-9. Add User-Defined Field Window ............................................................7-21
Figure 7-10. Priority/Outbound Filters Window Showing Filter Precedence ..............7-22
Figure 7-11 . Change Precedence Window ......................................................... ...... .7-2 3
Figure 7-12. Priority/Outbound Filters Window Showing New Order
of Precedence ........................................................................................7-23
xii
308645-14.00 Rev 00
Page 13
Tables
Table 1-1. Predefined Inbound Traffic Filter Criteria .................................................1-8
Table 1-2. Predefined Outbound Traffic Filter Criteria ...............................................1-9
Table 1-3. Inbound Traffic Filter Actions ..................................................................1-12
Table 1-4. Outbound Traffic Filter Actions ...............................................................1-12
Table 1-5. Summary of Traffic Filter Support ..........................................................1-14
Table 3-1. Transparent Bridge Encapsulation Support .............................................3-3
Table 3-2. Predefined Criteria for Transparent Bridge Inbound Traffic Filters ...........3-3
Table 3-3. Predefined Criteria for SRB Inbound Traffic Filters ..................................3-5
Table 3-4. Predefined Criteria for DECnet Phase IV Inbound Traffic Filters .............3-7
Table 3-5. Predefined Criteria for DLSw Inbound Traffic Filters ................................3-8
Table 3-6. Predefined Criteria for IP Inbound Traffic Filters ......................................3-9
Table 3-7. User-Defined Criteria for IP Inbound Traffic Filters ................................3-10
Table 3-8. Predefined Criteria for IPX Inbound Traffic Filters ..................................3-11
Table 3-9. Predefined Criteria for LLC2 Inbound Traffic Filters ...............................3-12
Table 3-10. Predefined Criteria for OSI Inbound Traffic Filters .................................3-13
Table 3-11. Predefined Criteria for VINES Inbound Traffic Filters .............................3-14
Table 3-12. Predefined Criteria for XNS Inbound Traffic Filters ................................3-15
Table 4-1. Predefined Data Link Criteria for Outbound
Traffic Filters 4-2
Table 4-2. Predefined IP Criteria for Outbound Traffic Filters ...................................4-5
Table 4-3. Data Link Reference Points .....................................................................4-7
Table 4-4. IP Reference Points ................................................................................4-9
Table 5-1. Format for Specifying MAC Addresses ....................................................5-2
Table 5-2. Functional MAC Addresses .....................................................................5-3
Table 5-3. SAP Codes ........................................................................ ...... ....... .........5-4
Table 5-4. Fr a me Relay NLPIDs ...............................................................................5-5
Table 5-5. PPP Protocol IDs .................. ...... ....... ...... ....... ...... ...... ....... ...... ....... ...... ...5-5
Table 5-6. Source and Destination TCP Ports ..........................................................5-6
Table 5-7. Source and Destination UDP Ports ..........................................................5-6
308645-14.00 Rev 00
xiii
Page 14

Table 5-8. Ethernet Type Codes ...............................................................................5-7
Table 5-9. IP Protocol ID Codes .............................................................................5-10
Table 5-10. IP Type of Service Codes .......................................................................5-10
Table 6-1. Using the Edit Template Window .............................................................6-9
Table 6-2. Using the Edit Filters Window ................................................................6-14
Table 7-1. Using the Edit Priority/Outbound Template Window ..............................7-12
Table 7-2. Using the Edit Priority/Outbound Filters Window ...................................7-17
Table 8-1. TCP and UDP Match Criteria Parameters ............................................ .8-11
Table 8-2. Common TCP Ports ...............................................................................8-12
Table 8-3. Common UDP Ports ..............................................................................8-12
Table 8-4. Common Protocol IDs for IP Traffic ........................................................8-14
Table 8-5. Actions and Dependencies for Inbound IP Traffic Filters .......................8-17
Table B-1. Predefined Criteria, Ranges, and Actions for Sample Inbound Traffic Filters B-5
Table B-2. User-Defined Criteria and Ranges for Sample Inbound Traffic Filters .... B-6
Table B-3. Sample Criteria, Ranges, and Actions for Protocol Prioritization ............ B-9
xiv
308645-14.00 Rev 00
Page 15
This guide describes how to configure traffic filters and prioritize traffic on a
Nortel Networks
You can use Site Manager to configure traffic filters on a router. You can use the
Bay Command Console (BCC
Before You Begin
Before using this guide, you must complete the following procedures. For a new
router:
™
router.
Preface
™
) to configure IP inbound traffic filters on a router.
• Install the router (see the installation guide that came with your router).
• Connect the router to the network and create a pilot configuration file (see
Make sure that you are runni ng the lates t versio n of Nortel Netw orks BayRS
Site Manager software. For information about upgrading BayRS and Site
Manager, see the upgrading guide for your version of BayRS.
308645-14.00 Rev 00
Quick-Starti ng Router s , Conf igur ing BaySt ac k Remote Acc ess , or Connecting
ASN Routers to a Network).
™
and
xv
Page 16

Configuring Traffic Filters and Protocol Prioritization
Text Conventions
This guide uses the following text conventions:
angle brackets (< >) Indicate that you choose the text to enter based on the
description inside the brackets. Do not type the
brackets when entering the command.
Example: If the command syntax is:
ping
<
ip_address
ping 192.32.10.12
>, you enter:
bold text
Indicates command names and options and text that
you need to enter.
Example: Enter
show ip {alerts | routes
Example: Use the
dinfo
command.
}.
braces ({}) Indicate required elements in syntax descriptions
where there is more than one option. You must choose
only one of the options. Do not type the braces when
entering the command.
Example: If the command syntax is:
show ip {alerts | routes
show ip alerts or show ip routes
}
, you must enter either:
, but not both.
brackets ([ ]) Indicate optional elements in syntax descriptions. Do
not type the brackets when entering the command.
Example: If the command syntax is:
show ip interfaces [-alerts
show ip interfaces
or
]
, you can enter either:
show ip interfaces -alerts
.
ellipsis points (. . . ) Indicate that you repeat the last element of the
command as needed.
xvi
Example: If the command syntax is:
ethernet/2/1
ethernet/2/1
[<
parameter> <value
and as many parameter-value pairs as
needed.
. . .
>]
, you enter
308645-14.00 Rev 00
Page 17

Preface
italic text Indicates file and directory names, new terms, book
titles, and va riables in command syntax descriptions.
Where a variable is two or mor e words, the words are
connected by an underscore.
Example: If the command syntax is:
show at
valid_route
<
valid_route
>
is one variable and you substitute one value
for it.
screen text Indicates system output, for example, prompts and
system messages.
Acronyms
Example:
Set Trap Monitor Filters
separator ( > ) Shows menu paths.
Example: Protocols > I P ide nti fies the IP option on the
Protocols menu.
vertical line (
) Separates choices for command keywords and
|
arguments. Enter only one of the choices. Do not type
the vertical line when enteri ng the command.
Example: If the command syntax is:
show ip {alerts | routes
show ip alerts
or
}
, you enter either:
show ip routes
, but not both.
ANSI American National Standards Institute
APPN Advanced Peer-to-Peer Networking
ARP Address Resolution Protocol
ATM Asynchronous Transfer Mode
CCITT International Telegraph and Telephone Consultative
CLNP Connectionless Network Protocol
308645-14.00 Rev 00
Committee (now ITU-T)
xvii
Page 18

Configuring Traffic Filters and Protocol Prioritization
CSMA/CD carrier sense multiple access/collision detection
DE discard eligible
DLC data link control
DLCI data link connection identifier
DLCMI Data Link Control Management Interface
DLSw data link switching
DSAP destination service access point
FDDI Fiber Distributed Data Interface
FTP File Transfer Protocol
HDLC high-level data li nk control
HSSI high-speed serial interface
ICMP Internet Con trol Message Proto col
IP Internet P rotocol
IPX Internet Packet Exchange
ISDN Integrated Services Digital Ne twork
xviii
ISO Inte rnational Organization for Standardization
ITU-T International Telecommunications
Union–Telecommunications sector (formerly CCITT)
LAN local area network
LAT Local Area Transport
LLC Logical Link Control
LNM LAN Network Manager
MAC media access control
MCE1 multichannel E1
MCT1 multichannel T1
MSB most significant bit
NLPID network layer protocol ID
OSI Open Systems Interconnection
OSPF Open Shortest Path First (protocol)
308645-14.00 Rev 00
Page 19

Preface
PPP Point-to-Point Protocol
PRI primary rate interface
RIF routing information field
RII routing information indicator
RIP Routing Information Protocol
SAP service access point
SDLC Synchronous Data Link Control
SMDS switched multimegabit data service
SNA Systems Network Architecture
SNAP Subnetwork Access Protocol
SNMP Simple Network Management Protocol
SRB source routing bridge
SSAP source service access point
STP shielded twisted pair
TCP/IP Transmission Control Protocol/Internet Protocol
Telnet Telecommunication network
TFTP Trivial File Transfer Protocol
UDP User Datagram Protocol
UTP unshielded twisted pair
VINES Virtual Network Systems
WAN wide area network
XNS Xerox Network System
308645-14.00 Rev 00
xix
Page 20
Configuring Traffic Filters and Protocol Prioritization
Hard-Copy Technical Ma nua ls
You can print selected technical manuals and release notes free, directly from the
Internet. Go to support.baynetworks.com/library/tpubs/. Find the product for
which you need documentation. Then locate the specific category and model or
version for your hardw are or soft ware product . Usi ng Adobe Ac robat Re ader, you
can open the manuals and releas e notes, search for the sections you ne ed, and print
them on most standard printers. You can download Acrobat Reader free from the
Adobe Systems Web site, www.adobe.com.
You can purchase selected documentation sets, CDs, and technical publications
through the collateral catalog. The catalog is located on the World Wi de Web at
support.baynetworks.com/catalog.html and is divided into sections arranged
alphabetically:
• The “CD ROMs” section lists available CDs.
• The “Guides/Books” section lists books on technical topics.
• The “Technical Manuals” section lists available printed documentation sets.
How to Get Help
xx
If you purchased a service contract for your Nortel Networks product from a
distributor or authorized reseller, contact the technical support staff for that
distributor or reseller for assistance.
If you purchased a Nort el Net wor ks s ervice pr ogram, c ontact one of the f ollowing
Nortel Networks Technical Solutions Centers:
Technical Solutions Center Telephone Number
Billerica, MA 800-2LANWAN (800-252-6926)
Santa Clara, CA 800-2LANWAN (800-252-6926)
Valbonne, France 33-4-92-96-69-68
Sydney, Australia 61-2-9927-8800
Tokyo, Japan 81-3-5402-7041
308645-14.00 Rev 00
Page 21
Chapter 1
Using Traffic Filters
This chapter describes concepts and terms to help you understand and plan for
traffic filter configurations on Nortel Networks routers.
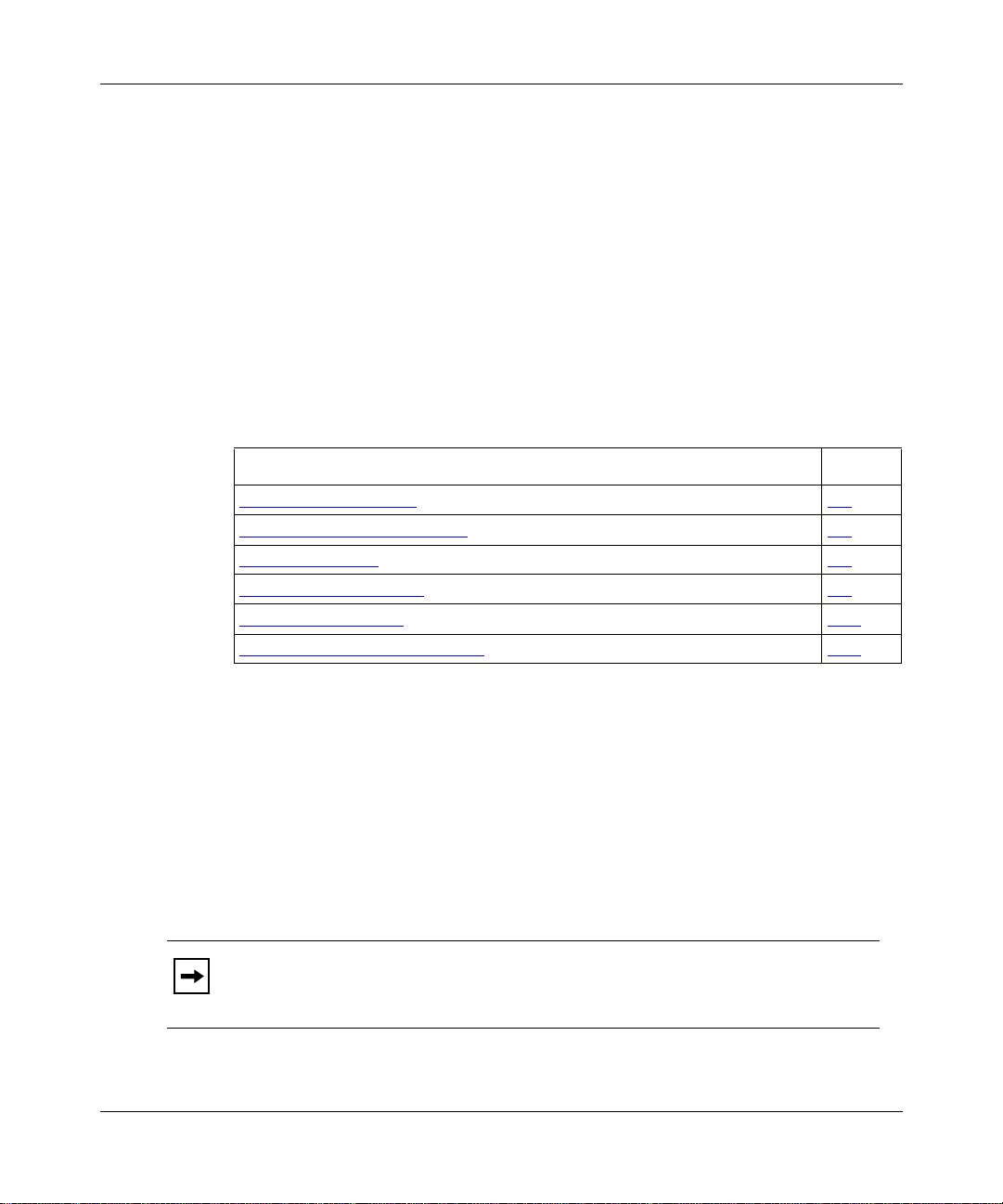
Topic Page
What Are Traffic Filters? 1-1
What Is Protocol Prioritization? 1-3
Filtering Strategies 1-4
Traffic Filter Components 1-6
Using Filter Templates 1-13
Summary of Traffic Filter Support 1-14
What Are Traffic Filters?
Traffic filters are router files that instruct an interface to selectively handle
specified network traffic (packets, frames, or datagrams). You determine which
packets receive special handling based on infor mation f ie lds in t he pack et header s.
Using traffic filters, you can reduce network congestion and control access to
network resources by blocking, forwarding, logging, or prioritizing specified
traffic on an interface.
Note:
Do not confuse traffic filters with other router filters. Traffic filters help
you manage customer traffic. Routing filters help you manage routing control
traffic (such as route table updates).
308645-14.00 Rev 00
1-1
Page 22

Configuring Traffic Filters and Protocol Prioritization
Nortel Networks routers support two types of traffic filters:
• Inbound traffic filters act on packets that the rout er is receiving.
• Outbound traffic filters act on packets t hat the router is forwardin g.
You can create traffic filters on the following router interfaces:
• Ethernet (10BASE-T and 100BASE-T)
• FDDI
• HSSI
•MCE1
•MCT1
• Synchronous
• Token ring
You can apply multiple traffic filters to a single interface. When more than one
filter applies to a packet, the order of filters determines the filtering result.
Inbound Traffic Filters
1-2
Inbound traffic filters act on packets arriving at a particular router interface. Most
sites use inbound traffic filters primaril y for secu rity, to restrict access to nodes in
a network.
When you configure inbound traffic filters, you specify a set of conditions that
apply to the traffic of a particular bridging or routing protocol. The Configuration
Manager supports inbound traffic filters for the following protocols:
• Transparent bridge (four encapsulation methods: Ethernet, 802.2 LLC, 802.2
LLC with SNAP, and Novell Proprietary)
• Native source route bridging (SRB)
•IP
•IPX
• XNS
•OSI
• DECnet Phase IV
•VINES
• DLSw
• LLC2 (APPN and LNM)
308645-14.00 Rev 00
Page 23

Chapter 3 provides protocol-specific information for designing inbound traffic
filters. Chapt er 6 explains ho w to use the Conf iguration Manager to apply inbound
traffic filters.
Outbound Traffic Filters
Outbound traffic filters act on packets that the router forwards to a local area
network (LAN) or wide area network (WAN) through a particular interface. Most
sites use outbound traffic filters to ensure timely delivery of critical data, or to
restrict traffic leaving the local network.
Outbound traffic filters are not based on a routing protocol, as are inbound traffic
filters. When you con fi gure outbo und traffic filters, you s pecify a s et of cond ition s
that apply to the following packet headers:
• Data link control (DLC) header
•IP header
To use outbound traffic filters, you must select Protocol Priority as one of the
configured prot ocols on an interface. Protocol Priority is enabled by default on
circuits configured with Frame Relay or PPP. Otherwise, you must enable
Protocol Priority the first time you configure outbound traffic filters on an
interface.
Using Traffic Filters
Chapter 4 provides information for designing outbound traffic filters. Chapter 7
explains how to use the Configuration Manager to enable Protocol Priority and
apply outbound traffic filters.
What Is Protocol Prioritization?
Protocol prioritization is an outbound traffic filter mechanism.
With Protocol Priority enabled on an interface, the router sorts traffic into
prioritized delivery queues (High, Normal, and Low), called priority queues.
Priority queues affect the sequence in which data leaves an interface; they do not
affect traffic as it arrives at the router. You use outbound traffic filters to specify
how traffic is sorted into priority queues. By default, all outbound traffic goes to
the Normal queue.
See Chapter 2 to learn more about priority queuing and dequeuing.
308645-14.00 Rev 00
1-3
Page 24
Configuring Traffic Filters and Protocol Prioritization
Filtering Strategies
This section recommends ways you might use traffic filters in a network. See
Appendix B for specific examples.
Direct Traffic
You can create traf f i c f i lter s that affect a particular protocol’s traffic. F or e xampl e,
you can forward all IP traffic to a next-hop address. You can also create traffic
filters th at affect certain locations on a b ridged network. F or example, if you want
all traffic from a node with a particular source MAC address (perhaps an
application server) to take precedence over other traffic, you can use protocol
prioritization to assign a high priority to any traffic with that source address.
Drop or Accept Traffic
You can configure a router interface to accept only specified traffic and drop all
other packets by configuring inbound traffic filters with specific accept criteria.
Or, to accept most traffic and drop only specified packets, you can configure
inbound traffic filters for the traffic you want to drop.
Note:
For example, to prevent all NetBIOS traffic from ente ring a particular LAN
segment, you can create an inbound traffic filter to drop all packets with a
destination or source SAP code of F0.
Prioritize Traffic
You can use protocol prioritization to expedite traffic coming from a particular
source or going to a particular destination.
When a router treats all packets equally, there is no way to ensure consistent
network services for users who are working with real-time applications. Bulk
transfer applications use too much of the available bandwidth and reduce
interactive response time. These problems are especially noticeable on low-speed
WAN interfaces.
1-4
Drop filters are generally more efficient than Accept filters.
308645-14.00 Rev 00
Page 25

You can also improve application response time and prevent session timeouts by
implementing protocol prioritization.
Combine Filters
On most interfaces, you can apply as many as 31 inbound and 31 outbound t ra ffic
filters for each protocol. You can configure IP interf aces to su pport as many as 127
inbound traffic filters.
As you add filters to an interface, the Configuration Manager numbers them
chronologically (Filter No. 1, Filter No. 2, Filter No. 3, and so on). The filter rule
number determines the filter’s precedence. Lower numbers have higher
precedence; Filter No. 1 has the highest precedence. If a packet matches two
filters, the filter with the high est precedence (lowest number) applies.
After you create traffic filters, you can change their precedence by reordering
them. See “Changing Inbound Traffic Filter Precedence” on page 6-18 (inbound
traffic filters) or “Changing Outbound Traffic Filter Precedence” on page 7-21
(outbound traffic filters).
Using Traffic Filters
Build a Firewall
If your filtering strategy involves blocking most or all inbound traffic (a firewall)
you can create a Drop-all filter for each protocol on the interface. That means for
each protocol you are filtering, you choose a filter criterion that appears in every
packet of the protocol (for example, a MAC address).
You can also create exceptions to the Drop-all filter by adding more-specific,
higher-precedence filters to allow only specified traffic on an interface. See
“Using a Drop-All Filter As a Firewall” on page B-12 for more information about
combining filters to accept certain traffic.
308645-14.00 Rev 00
1-5
Page 26

Configuring Traffic Filters and Protocol Prioritization
Traffic Filter Components
The Configuration Manager creates traffic filters from template files that contain
filtering information. Traffic filter templates consist of three components:
• Criteria
The portion of the incoming packet, frame, or datagram header to be
examined
•Ranges
Numeric values (often addresses) to be compared with the contents of
examined packets
• Actions
What happens to packets that match the criteria and ranges specified in a filter
To create a traffic filter, you apply a filter template to a particular router interface.
Table 1-5
filter criteria and actions supported on specific interfaces.
(at the end of this ch apter) summa rizes th e inbound an d outbound t raf fi c
Criteria
1-6
A f
ilter criterion is the portion of a packet, frame, or datagram header to be
examined. You can break down any packet into at least three components:
• The DLC (or data link) header. Examples of data link header types include:
-- Token ring (802.5)
-- Ethernet V.2 and IEEE 802.3
-- FDDI
-- PPP and Nortel Networks Standard
-- Frame Relay
• The upper-level protocol header. Examples of protocol header types include:
-- IP and TC P
-- Source route bridging (SRB)
-- DLSw
•User data
308645-14.00 Rev 00
Page 27

Using Traffic Filters
A traffic filter criterion is defined by a byte length and an offset from common bit
patterns (reference points) in the data link or protocol header. The criterion
includes the length of the filtered pattern and an offset from the known reference
point. The traffic filter us es thi s information to locate which portion of a packet t o
examine.
For bridged traffic, predefined criteria are part of the data link header. For routed
traffic, a predefined criterion can be part of the data link header or an upper-level
protocol header.
Inbound traffic filter criteria use reference points in the upper-level protocol
header. You select inbound criteria based on the protocol of the incoming traffic.
Outbound traffic filters use reference points in only the IP or DLSw protocol
headers. You select outbound criteria based on the WAN protocol configured on
the interface (transparent bridge, SRB, PPP, or Frame Relay).
Predefined and User-Defined Criteria
The Configuration Manager provides a selection of default filter criteria
(predefined criteria) for both inbound and outbound traffic filters. Predefined
criteria consist of predefined offsets and lengths from common reference points.
You can also def ine a c rite rion b ase d on bit patt ern s in a pack et hea der that are not
supported in predefined criteria (user-defined criteria). To apply user-defined
criteria, you specify the bit length and offset from a supported reference point.
Chapter 3 lists the supported reference points for inbound traffic filters. lists the
reference points for outbound traffic filters.
To fit your site’s traffic patterns, you can use a combination of predefined and
user-defined criteria in up to 32 traffic filters on each interface.
308645-14.00 Rev 00
1-7
Page 28
Configuring Traffic Filters and Protocol Prioritization
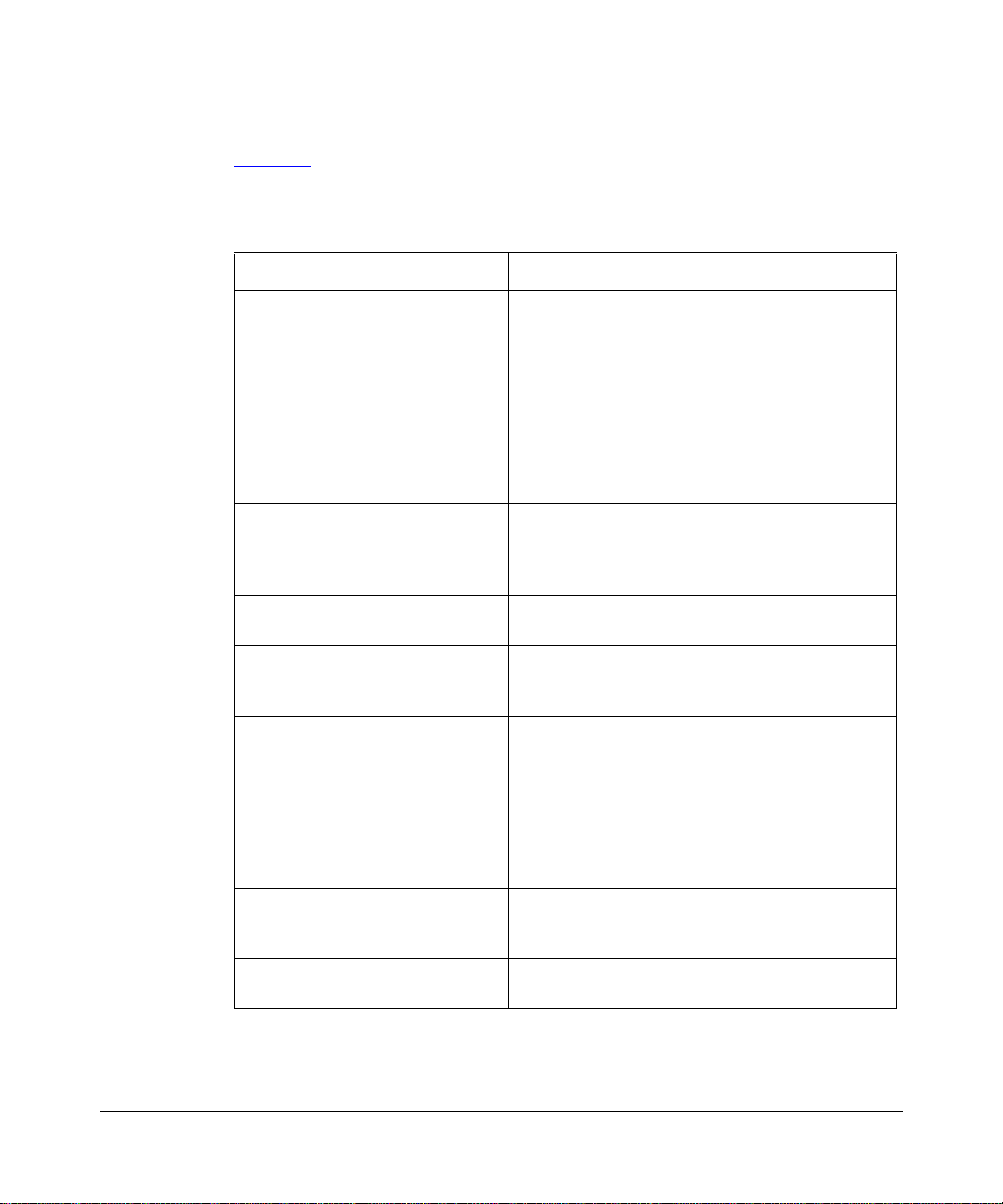
Predefined Criteria
Table 1-1 summarizes the predefined inbound traffic filter criteria for supported
protocols.
Table 1-1. Predefined Inbound Traffic Filter Criteria
Traffic Type Predefined Inbound Filter Criteria
Transparent bridge
(Four data link encapsulation
methods: Ethernet, 802.2 LLC,
Novell Proprietary, 802.2 LLC with
SNAP)
SRB
(Native only; IP-encapsulated SRB
is not supported)
DECnet Phase IV Area (Source or Destination)
DLSw MAC Address (Source or Destination)
IP Type of Service
IPX Network (Source or Destination)
OSI OSI Area (Source or Destination)
MAC Address (Source or Destination)
Ethernet Type
Novell
802.2 LLC Length
802.2 LLC DSAP
802.2 LLC SSAP
802.2 LLC Control
802.2 SNAP Length
802.2 SNAP Protocol ID
802.2 SNAP Ethernet Type
MAC Address (Source or Destination)
DSAP
SSAP
NetBIOS Name (Source or Destination)
Node (Source or Destination)
DSAP
SSAP
IP Address (Source or Destination)
UDP Port (Source and/or Destination)
TCP Port (Source and/or Destination)
UDP or TCP Source Port
UDP or TCP Destination Port
Established TCP Protocols
Protocol Type
Host Address (Source or Destination)
Socket (Source or Destination)
System ID (Source or Destination)
(continued)
1-8
308645-14.00 Rev 00
Page 29
Using Traffic Filters
Table 1-1. Predefined Inbound Traffic Filter Criteria
Traffic Type Predefined Inbound Filter Criteria
LLC2 MAC Address (Source or Destination)
DSAP
SSAP
VINES Protocol Type
VINES Address (Source or Destination)
XNS Network (Source or Destination)
Address (Source or Destination)
Socket (Source or Destination)
(continued )
Table 1-2 summarizes the predefined outbound traffic filter criteria for data link
and IP headers.
Note: See Configuring DLSw Services for information about criteria for
outbound traffic filters based on the DLSw header.
Table 1-2. Predefined Outbound Traffic Filter Criteria
Header Traffic Typ e Predefined Outbound Filter Criteria
IP header IP Type of Service
308645-14.00 Rev 00
Priority_IP Address (Source and/or
Destination)
UDP Port (Source and/or Destination)
TCP Port (Source and/or Destination)
Established TCP
Protocol Type
Native SRB SSAP
Destination Address
Source Address
PPP Protocol ID
Frame Relay 2-byte DLCI
3-byte DLCI
4-byte DLCI
NLPID
(continued)
1-9
Page 30
Configuring Traffic Filters and Protocol Prioritization
Table 1-2. Predefined Outbound Traffic Filter Criteria
Header Traffic Typ e Predefined Outbound Filter Criteria
Data link header Transparent bridge
(Data Link Type)
Native SRB SSAP
PPP Protocol ID
Frame Relay 2-byte DLCI
MAC Address (Source or Destination)
Ethernet Type
Novell
802.2 Length
802.2 DSAP
802.2 SSAP
802.2 Control
802.2 SNAP Length
802.2 SNAP Protocol ID
802.2 SNAP Ethernet Type
DSAP
3-byte DLCI
4-byte DLCI
NLPID
Ethernet Type
(continued)
User-Defined Criteria
1-10
To apply customized criter ia that use fields that are not represented i n a protocol’s
predefined criteria, you can create a user-defined criterion. You specify its
location in the packet header by specifying the following:
• Reference point
A known bit position in the packet header
• Offset
The first posit ion of the filtered bit pattern in relation to the reference point
(measured in bits)
• Length
The total bit length of the filtered pattern
308645-14.00 Rev 00
Page 31

Ranges
Using Traffic Filters
For each traffic filter criterion, you also specify the valid r ange, a series of target
values that apply to the criterion. For most criteria, you specify an address range.
There must be at least one target value for each criterion. The range can be just
one value or a set of values.
You enter a minimum and a maximum value to specify the range. For a range of
only one value, you enter only the minimum value; the Configuration Manager
automatically uses that value for both the minimum and maximum value.
For examp le, if th e f i lter cr iter ia is MAC Source Address, you must specify whic h
addresses you want the filter to examine. If you specify 0x0000A2000001 as the
minimum range value and 0x0000A2000003 as the maximum range value, the
router checks for packets with a MAC source address between 0x0000A2000001
and 0x0000A2000003, inclusive.
Note:
Chapter 5 lists valid ranges for common traffic filter criteria and
explains how to specify some common address ranges.
Actions
The filter action determines what happens to packets that match a filter criterion’s
ranges. You can apply the following actions to any traffic filter:
• Accept
• Drop
•Log
308645-14.00 Rev 00
The router processes any packet that matches the filter criteria and ranges.
The router does n ot rou te any packet that matches the filter criteria and ranges.
For e v er y pack et tha t matc hes t he f ilt er cr iter ia an d r anges, the r out er s ends an
entry to the system Events log. You can specify the Log action in combination
with other actions.
1-11
Page 32

Configuring Traffic Filters and Protocol Prioritization
Note: Specify the Log action only to record abnormal events; otherwise, the
Events log will fill up with filtering messages, leaving no room for critical log
messages.
Table 1-3
lists additional protocol-specific actions for inbound traffic filters. See
Chapter 3 for more information.
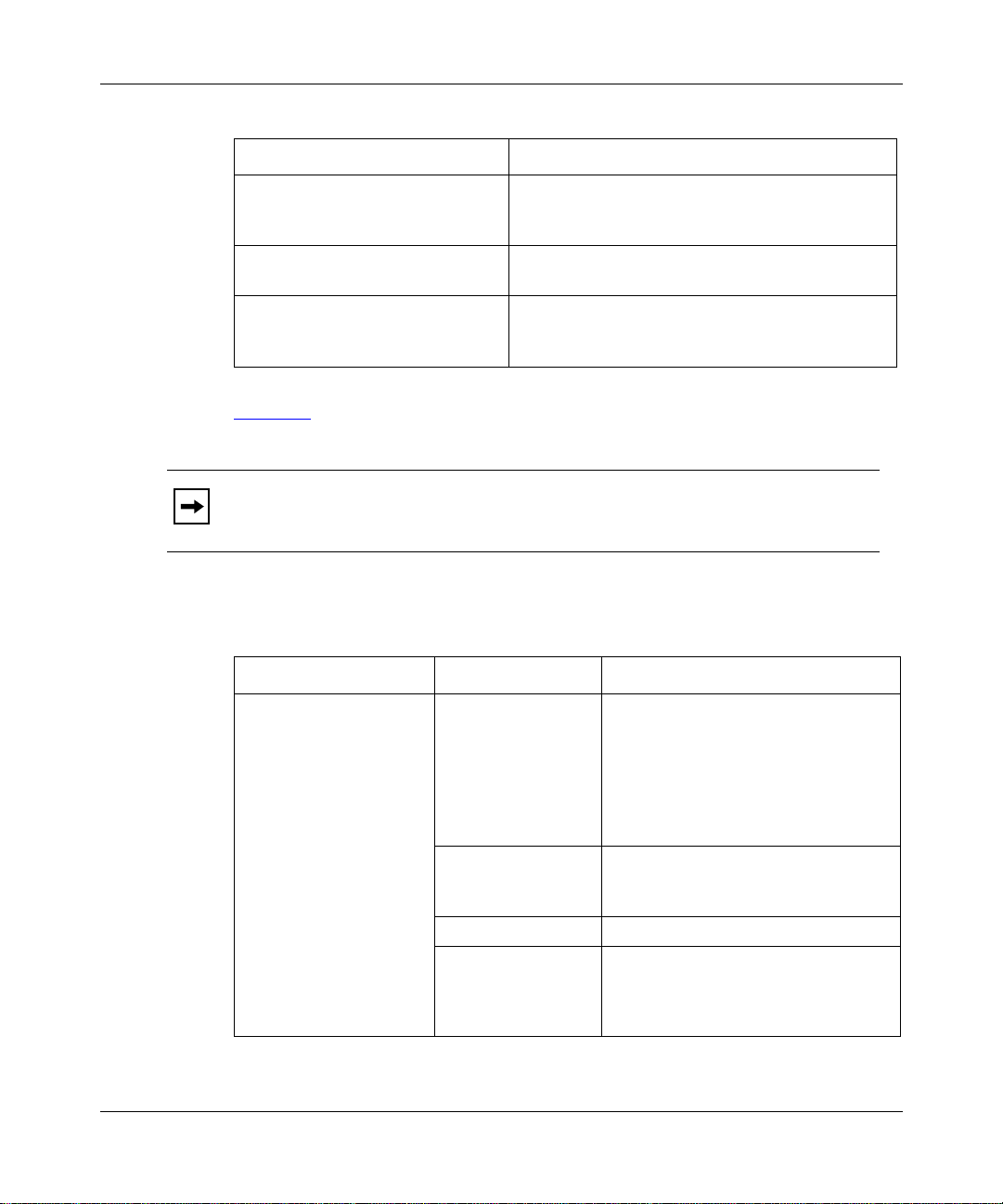
Table 1-3. Inbound Traffic Filter Actions
Protocol Inbound Traffic Filters
All protocols Drop
Accept
Log
Transparent bridge Flood
Forward to Circuit List
Native SRB Direct IP Explorers
Forward to Circuits
DLSw Forward to Peer
IP Forward to Next Hop
Drop If Next Hop Is Unreachable
Forward to IP Address
Forward to Next Hop Interface
Forward to First Up Next Hop Interface
Detailed Logging
Table 1-4
lists the actions for outbound traffic filters. See Chapter 4 for more
information.
1-12
Table 1-4. Outbound Traffic Filter Actions
Filtering Actions Prioritizing Actions*
Drop High Queue No Call
Accept Low Queue No Reset
Log Length
Detailed Log
* Outbound traffic filters with a prioritizing action are sometimes called
Dial Service Actions
priority filters.
308645-14.00 Rev 00
Page 33

Except for the log ac tions, in bound and out bound tra f fi c f ilter a ctions are mutually
exclusive; you can only apply one action to each filter.
Using Filter Templates
When you create traffic filters, it is important to understand the difference
between a traffic filter template and an actual traffic filter.
A traffic filter template is a reusable, predefined specification for a traffic filter.
Each template contains a complete filter specification (criterion, range, and
action) for one protocol, but is not associated with a specific interface or circuit.
You create an actual traffic filter when you use the Configuration Manager to
apply (sav e) a tr af f ic f ilt er template t o a conf igur ed router interf ace. You can apply
a single template to as many interfaces as you want, thus creating multiple filters
for that protocol.
When you want to add a filter to an interface, you have several options:
• If the re i s a t empl at e t ha t contains the e xa ct filtering instructions you w ant f or
this interface, apply that template to the interface.
Using Traffic Filters
• If there is a template that contains filtering instructions similar to what you
• If there is no template containing filtering instruc tions similar to what you
• If t here is an e xisti ng f ilter on the i nterf ace that conta ins inst ructions simil ar to
308645-14.00 Rev 00
want, copy, rename, and edit the template. Then, appl y the ne w template to the
appropriate interface.
want for this interface, you mu st create a temp late from scratch. Then, app ly
the new template to the appropriate interface.
what you want, edit the existing filter and s ave it.
1-13
Page 34

Configuring Traffic Filters and Protocol Prioritization
Summary of Traffic Filter Support
Table 1-5 summarizes the inbound and outbound traffic filter criteria and actions
supported on specific interfaces.
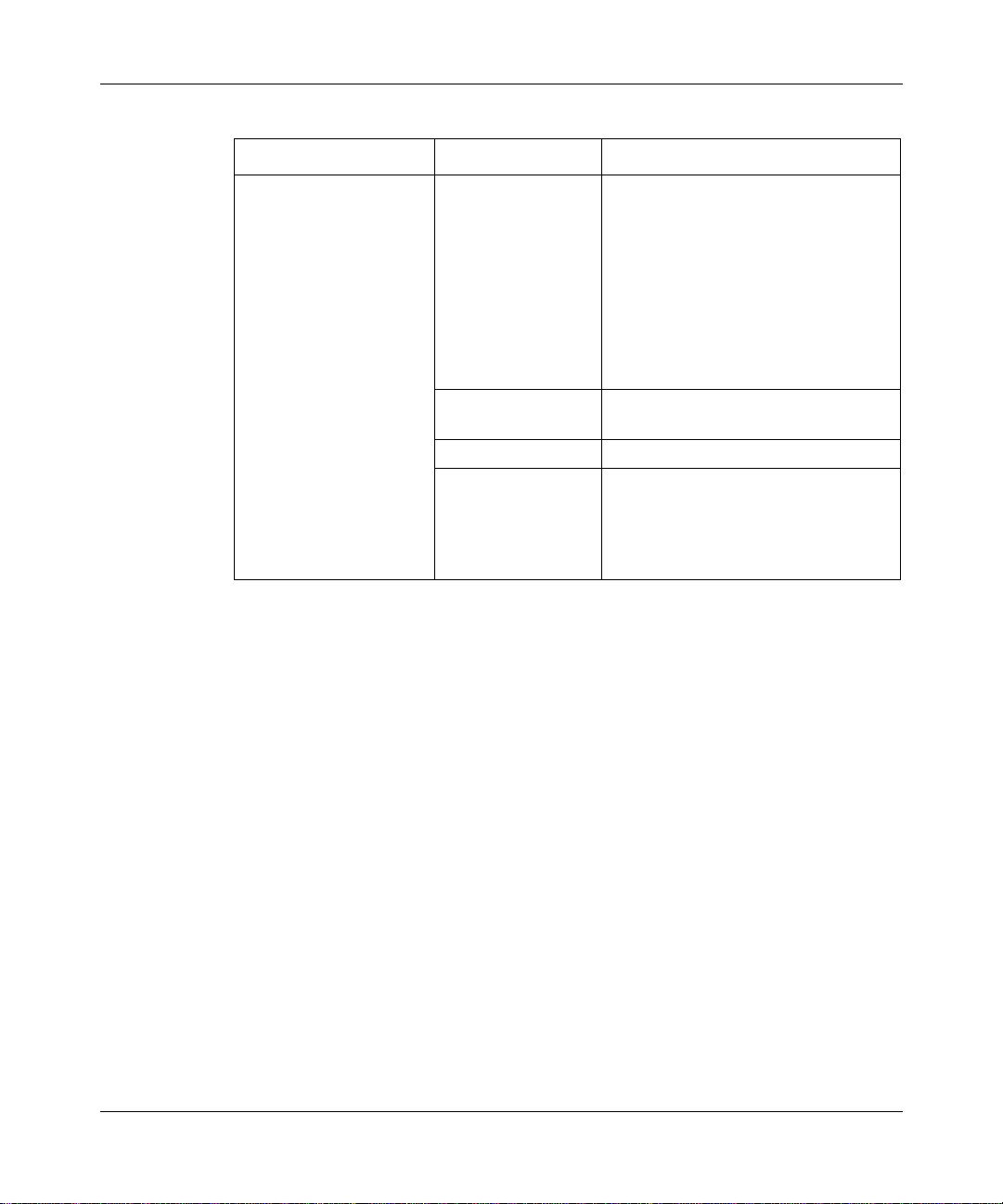
Table 1-5. Summary of Traffic Filter Support
Protocol Criteria Supported Filter Actions Supported
Network Interface Inbound Outbound Inbound Outbound
Ethernet
(10BASE-T or
100BASE-T)
FDDI Transparent bridge‡,
Token ring Transparent bridge‡,
HSSI Transparent bridge*,
MCE1 Transparent bridge,
MCT1 Transparent bridge,
Synchronous Transparent bridge*,
* Ethernet, 802.2 LLC, LLC with SNAP, and Novell encapsulations.
† Plus additional actions for transparent bridge, SRB, and IP filters (see Chapter 3).
‡ 802.2 LLC and LLC with SNAP encapsulations.
Transparent bridge*,
DECnet IV, DLSw, IP,
IPX, LLC2, OSI, SRB,
XNS, VINES
DECnet IV, DLSw, IP,
IPX, LLC2, OSI, SRB,
XNS, VINES
DECnet IV, DLSw, IP,
IPX, LLC2, OSI, SRB,
XNS, VINES
DECnet IV, DLSw, IP,
IPX, LLC2, OSI, SRB,
XNS, VINES
DECnet IV, DLSw, IP,
IPX, LLC2, OSI, SRB,
XNS, VINES
DECnet IV, DLSw, IP,
IPX, LLC2, OSI, SRB,
XNS, VINES
DECnet IV, DLSw, IP,
IPX, LLC2, OSI, SRB,
XNS, VINES
Transparent bridge,
IP, SRB
Transparent bridge,
IP, SRB
Transparent bridge,
IP, SRB
Transparent bridge,
Frame Relay, IP,
PPP, SRB
Transparent bridge,
Frame Relay, IP,
PPP, SRB
Transparent bridge,
Frame Relay, IP,
PPP, SRB
Transparent bridge,
Frame Relay, IP,
PPP, SRB
Accept, Drop,
Log †
Accept, Drop,
Log †
Accept, Drop,
Log †
Accept, Drop,
Log †
None Accept, Drop, Log,
None Accept, Drop, Log,
Accept, Drop,
Log †
Accept, Drop, Log
Accept, Drop, Log
Accept, Drop, Log
Accept, Drop, Log
High Queue, Low
Queue, Length, No
Call, No Reset
High Queue, Low
Queue, Length, No
Call, No Reset
Accept, Drop, Log ,
High Queue, Low
Queue, Length, No
Call, No Reset
1-14
308645-14.00 Rev 00
Page 35

Chapter 2
Using Protocol Prioritization Queues
This chapter desc ribes the pri orit y queues that yo u can i mple ment usi ng out boun d
traffic filters (protocol prioritization).
Topic Page
About Protocol Prioritization 2-1
Enabling Protocol Prioritization 2-9
Enabling Protocol Prioritization on an ATM Circuit 2-10
Tuning Protocol Prioritization 2-11
For instructions on using the Configuration Manager to create outbound traffic
filters, see Chapter 7.
About Protocol Prioritization
Site Manager supports protocol prioritization on synchronous (serial), HSSI,
MCE1, and MCT1 interfaces for the following WAN protocols:
• PPP
• Nortel Networks Standard PPP
• Frame Relay
Note:
The DLSw software also allows you to prioritize traffic within DLSw,
based on predefined or user-defined fields at the TCP level. For information
about these DLSw prioritization filters, see Configuring DLSw Services.
308645-14.00 Rev 00
2-1
Page 36

Configuring Traffic Filters and Protocol Prioritization
While the router is operating, network traffic from various sources converges at
each WAN interface. Without protocol prioritization, the router transmits packets
in a first in, first out (FIFO) order.
With Protocol Priority enabled on an interface, the router sorts traffic into
prioritized delivery queues (High, Normal, and Low), called priority queues. The
router uses a dequeuing algo ri thm to empt y th e pri ori ty queues to transmit traffic.
Generally, the router tran smits higher-priority traffic first. Other configur able
values in the protocol prioritization scheme also affect the transmission of traffic.
T w o of these values are the maximum size of the queue (queue depth) and the line
delay (latency), described in “Tuning Protocol Prioritization” on page 2-11
Protocol prioritization is considered an outbound filter mechanism for these
reasons:
• You use outbound traffic filters to specify how traffic is prioritized.
• Priority queues affect the seque nce in which d ata leaves an interface; they do
not affect traffic as it arrives at the router.
Outbound traf fic filters include priorit izing actions for sp eci fy ing priority queues.
See “Prioritizing Actions” on page 4-11.
.
The following sections describe how the router prioritizes traffic into queues, and
the options for dequeuing:
• Priority Queuing
• The Dequeuing Process
Priority Queuing
With pr otocol prioritization enabled on an interface, the router sends each packet
leaving an inte rface to one of three priority queues:
• High queue
• Normal queu e
• Low queue
The router automatically queues packets that do not match a priority filter to the
Normal queue. To send traffic to the other queues, you create outbound traffic
filters that include a prioritizing action. These are called priority filters.
2-2
308645-14.00 Rev 00
Page 37

The Dequeuing Process
After queuing packe ts, the route r empties the priorit y queues b y sending the traf f ic
to the transmit queue using one of two dequeuing algorithms:
• Bandwidth Allocation Algorithm
• Strict Dequeuing Algorithm
By default, protocol priorit ization uses the bandwidt h allocat ion algori thm to send
traffic from the three priority queues to the transmit queue. You specify the active
dequeuing algorithm by setting the Prioritization Algorithm Type parameter, as
described in “Editing Protocol Prioritization Parameters
Using Protocol Prioritization Queues
” on page 2-15.
Figure 2-1
70% of bandwidth
illustrates the dequeuing process, with default configuration values.
High
queue
Normal
queue
20% of bandwidth
Dequeuing algorithm
(Default algorithm = bandwidth allocation)
Transmit
queue
(Default latency
= 250 ms)
Physical
interface
Low
queue
10% of bandwidth
TF0001A
Figure 2-1. Protocol Prioritization Dequeuing
308645-14.00 Rev 00
2-3
Page 38

Configuring Traffic Filters and Protocol Prioritization
Bandwidth Allocation Algorithm
The bandwidth allocation algorithm uses a configurable percentage of bandwidth
for each of the three priority queues to determine how to transmit queued traffic.
The default configuration is as follows:
• High queue -- 70% of bandwidth
• Normal queue -- 20% of bandwidth
• Low queue -- 10% of bandwidth
When the amount of traffic transmitted from a particular queue reaches the
configured percentage, the next-higher-priority queue begins to transmit traffic.
The amount of actual data transmitted depends on the clock speed of the circuit.
You can configure the clock speed on a synchronous interface by setting the
External Clock Speed parameter in the Configuration Manager Edit Sync
Parameters window. (See Configuring WAN Line Services.)
The bandwidth allocation algorithm works as follows:
1.
The transmit queue scans the High queue.
2-4
If there is no traffic in the High queue, the algorithm proceeds to step 3
2.
The router empties all packets from the High queue, up to the configured
bandwidth percent age , into the trans mit queue and then transmits the pack e ts.
The default bandwidth percentage for the High queue is 70 percent. If the
actual bandwidth use is less than the limit, the router empties the High queue
and proceeds to the Normal queue.
3.
The transmit queue scans the Normal queue.
If there is no traffic in the Normal queue, the algorithm proceeds to step 5
4.
The router empties all packets from the Normal queue, up to the configured
bandwidth percentage, into the transmit queue and then transmits the packets.
The default bandwidth percentage for the Normal queue is 20 percent. If the
actual bandwidth use is less than the limit, the router empties the Normal
queue and proceeds to the Low queue.
5.
The transmit queue scans the Low queue.
If there is no traffic in the Low queue, the algorithm returns to step 1
308645-14.00 Rev 00
.
.
.
Page 39

Using Protocol Prioritization Queues
6.
The router empties all packets from the Low queue, up to the configured
bandwidth percent age , into the trans mit queue and then transmits the pack e ts.
The default bandwidth percentage f or the Low queue is 10 percent. If the
actual bandwidth use is less than the limit, the router empties the Low queue.
7.
The algorithm returns to step 1.
Figure 2-2
illustrates the bandwidth allocation algorithm.
308645-14.00 Rev 00
2-5
Page 40

Configuring Traffic Filters and Protocol Prioritization
Scan the
High queue.
Are there
packets in the
High queue?
NO
Scan the
Normal queue.
Are there
packets in the
Normal queue?
NO
Scan the
Low queue.
YES
YES
Transmit all
packets, up to
the configured
bandwidth
percentage.
Transmit all
packets, up to
the configured
bandwidth
percentage.
2-6
Are there
packets in the
Low queue?
NO
YES
Transmit all
packets, up to
the configured
bandwidth
percentage.
Figure 2-2. Bandwidth Allocation Algorithm
TF0002A
308645-14.00 Rev 00
Page 41

Using Protocol Prioritization Queues
Strict Dequeuing Algorithm
Instead of the bandwi dth allocation algorit hm, you can configur e t he rout er to use
the strict de queuing algo rithm to send tr affic to the transmit queue.
Caution:
If the router uses the strict dequeuing algorithm and there is a great
deal of High queue traffic on the network, Normal and Low queue traffic may
never be transmitted.
The strict dequeuing algorithm works as follows:
1.
The transmit queue scans the High queue.
If there is no traffic in the High queue, the algorithm proceeds to step 4
2.
The router empties all packets from the High queue into the transmit queue,
.
up to the latency value or the maximum transmit queue size, and then
transmits the packets.
The transmit queue size is the maximum number of packets in the transmit
queue at one time. You cannot configure this number using Site Manager.
3.
If the latency value is reached, the transmi t queue return s to step 1, sc anning
and emptying traffic from the High queue.
If neither the latency value nor the maximum transmit queue size is reached,
the algorithm proceeds to step 4
4.
The transmit queue scans the Normal queue.
.
If there is no traffic in the Normal queue, the algorithm proceeds to step 7
.
5.
6.
7.
8.
9.
308645-14.00 Rev 00
The router empties all packets from the Normal queue, up to the latency value,
into the transmit queue and then transmits the packets.
If the latency value is reached, the transmi t queue return s to step 1, scanning
and emptying traffic from the High queue.
If the latency value is not reached, the algorithm proceeds to step 7
.
The transmit queue scans the Low queue.
If there is no traffic in the Low queue, the algorithm returns to step 1
.
The router empties all packets from the Low queue, up to the latency value,
into the transmit queue and then transmits the packets.
The algorithm returns to step 1, whether or not the latency value is reached.
2-7
Page 42

Configuring Traffic Filters and Protocol Prioritization
Figure 2-3 illustrates the strict dequeuing algorithm.
Scan the
High queue.
Are there
packets in the
High queue?
NO
Are there
packets in the
Normal queue?
NO
Are there
packets in the
Low queue?
YES
YES
YES
Transmit all packets.
Transmit all
packets, up to
the latency value.
Transmit all
packets, up to
the latency value.
Was the
maximum transmit
queue size
reached?
NO
Was the
latency value
NO
reached?
Was the
latency value
reached?
NO
YES
YES
YES
2-8
NO
TF0003A
Figure 2-3. Strict Dequeuing Algorithm
308645-14.00 Rev 00
Page 43

Enabling Protocol Prioritization
You use the Configuration Manager to configure protocol prioritization. To
configure priority queues with default value s, do the foll owing :
1.
Enable Protocol Priority on the cir cuit, as desc r ibed in this section.
2.
Apply outbound traffic filters with prioritizing actions to the circuit, as
described in Chapter 7.
Using Protocol Prioritization Queues
See “Tuning Protocol Prioritization
” on page 2-11 to learn how to customize the
way protocol prioritization works on a circuit.
To enable protocol prioritization:
Site Manager Procedure
You do this System responds
1. In the Configuration Manager window,
click on the circuit interface connector on
which you want to configure protocol
prioritization.
2. Click on
3. Look for Protocol Priority in the Protocols
scroll box.
Site Manager automatically enables protocol
prioritization for certain WAN protocols.
4. If Protocol Priority does not appear in the
Protocols scroll box, choose Protocols >
Add/Delete.
5. Scroll down the li st of protocols and select
Protocol Priority.
6. Click on OK. The Circuit Definition window opens.
Edit Circuit
. The Circuit Definition window opens; the
The Edit Connector window opens.
circuit you selected is highlighted.
If Protocol Priority appears in the
Protocols scroll bo x, protocol prioritizati on
is already enabled for this interface.
The Select Protocols window opens.
From the Circuit Definition window, you can do the following:
• Edit conf igurati on para meters, as describe d in “ Editi ng Protoco l Prioriti zation
• Configure an outbound traffic filter with a priority queue action, as described
308645-14.00 Rev 00
Parameters” on page 2-15.
in Chapter 7.
2-9
Page 44

Configuring Traffic Filters and Protocol Prioritization
Enabling Protocol Prioritization on an ATM Circuit
You can now set the priorities for the traffic sent across a HSSI and ATM line
interface using protocol prioritization.
You must manually start protocol prioritization on both a HSSI line interface and
an ATM circuit. However, the steps required to enable protocol prioritization for
ATM differ from the steps for all other circuit types. For ATM, you can use
protocol prioritization for IP traffic travelling over an ATM PVC.
To enable protocol prioritization for an ATM circuit:.
Site Manager Procedure
You do this System responds
1. In the Configuration Manager window,
click on the ATM1 connector on which y ou
want to configure protocol prioritization.
2. Click on
3. Click on
4. Click on
. The Edit ATM Connector window opens.
ATM
PVC Protocol Priority
Priority Interface
. The ATM PVC Protocol Priority window
. The ATM Priority Interface List window
The Select Connection Type window
opens.
opens.
opens.
From the ATM Priority List window, you can edit configuration parameters, as
described in Configuring ATM Services.
Note:
You cannot change the percent of bandwidth for the priority queues
when configuring protocol prioritization over ATM.
For more information about protocol prioritization and how to configure and
outbound traffic filter with a priority queue action, see Chapter 7.
2-10
308645-14.00 Rev 00
Page 45

Tuning Protocol Prioritization
When you enable Protocol Priority on a circuit, the router uses default values that
help determine ho w priori ty f ilters wo rk. These de faults ar e designed t o work well
for most configurations. However, you can customize (or tune) protocol
prioritization to maximize its impact on your network.
This section covers the following topics:
• Tuning Concepts
• Editing Protocol Prioritization Parameters
• Monitoring Protocol Prioritization Statistics
Tuning Concepts
How you tune protocol prioritization depends on whether you are using the
bandwidth allocation algorithm or strict dequeuing algorithm. (See “The
Dequeuing Process” on page 2-3.)
Using Protocol Prioritization Queues
To tune priority queuing with the bandwidth allocation algorithm, consider
adjusting the following configuration defaults:
• Percent of Bandwidth
• Queue Size
To tune priority queuing with the strict dequeuing algorithm, consider adjusting
the following configuration defaults:
• Queue Size
• Latency
Percent of Bandwidth
When using the bandwidth allocation algorithm, you can change the default
allocation of bandwidth for each of the three priority queues.
Queued traffic with large packets often require more than the default bandwidth
allocation. F or example, if statistics indicate that one int er face requires more t han
70 percent of bandwidth to properly transmit high-priority traffic, you can
increase the High Queue Size parameter and decrease the Normal or Low Queue
Size parameter.
308645-14.00 Rev 00
2-11
Page 46

Configuring Traffic Filters and Protocol Prioritization
If statistics indicate that the High queue does not have enough buffers,
Note:
consider reducing the amount of high-priority traffic. You should be selective
in assigning high-priority status. Too many traffic types with high-priority
status can defeat the purpose of protocol prioritization. With the strict
dequeuing algorithm, t oo much h igh-priori ty traf f ic can resul t in di scarding (or
clipping) normal- and low-priority traffic.
To configure the percent of bandwidth for the priority queues, you edit these
Configuration Manager parameters:
• High Queue Percent Bandwidth
• Normal Queue Percent Bandwidth
• Low Queue Percent Bandwidth
When changing bandwidt h allocati on, remember that t he percen t of band width for
the High queue, Normal queue, and Low queue must total 100 percent.
Queue Size
2-12
Queue size (or queue depth) is the configurable number of packets that each
priority queue can hold. The default value for bandwidth allocation is 20 packets,
regardless of p acket size.
The buffer size for priority queues is not configurable when using the
Note:
strict dequeuing algorithm.
When you set the queue size, you assign buffers (which hold the packets) to each
queue. A queue is full when it exceeds the buffer size. The router discards (clips)
traffic sent to a full queue.
To configure queue size, you edit these Configuration Manager parameters:
• High Queue Size
• Normal Queue Si ze
• Low Queue Size
• High Water Packets Clear
308645-14.00 Rev 00
Page 47

Using Protocol Prioritization Queues
Queue Size Example
Suppose that you use the default queue size (20 packets) for all three priority
queues. The statistics indicate that the Hi gh queue’ s Cl ipped Pack ets Count is 226,
and its High-Water Packets Mark is 20. This indicates that the High queue has
been full at least once and that the router has discarded 226 packets.
From this information, you can conclude that you have not assigned enough
buffers to the High queue for the amount of high-priority traffic on this interface.
To prevent additional high-priority traffic from being discarded, you can
reconfigure the size of the queues or reevaluate the amount of traffic assigned to
the High queue.
Reconfiguring Queue Size
Suppose that you now look at the statistics of the Normal and Low queues and
find that the Low queue has a Clipped Packets Count of zero and a High-Water
Packets Mark of 06 (Figure 2-4)
. Therefore, you can conclude that there have
never been more than six packets in the Low queue, and the router has not
discarded any low-priority packets.
Queue Size = 20
Clipped Packets Count = 226
High-Water Packets Mark = 20
20
10
0
Figure 2-4. Priority Queue Statistics for the Queue Size Example
In this case, you may choose to decrease the Low queue size to 10, and increase
the High queue size to 30 (Figure 2-5)
308645-14.00 Rev 00
High
Queue Size = 20
Clipped Packets Count = 0
High-Water Packets Mark = 10
20
10
0
Normal
.
Queue Size = 20
Clipped Packets Count = 0
High-Water Packets Mark = 06
20
10
0
Low
TF0004A
2-13
Page 48

Configuring Traffic Filters and Protocol Prioritization
Queue Size = 30
Clipped Packets Count = 0
High-Water Packets Mark = 20
30
20
10
Queue Size = 20
Clipped Packets Count = 0
High-Water Packets Mark = 10
20
10
Queue Size = 10
Clipped Packets Count = 0
High-Water Packets Mark = 06
10
0
High
0
Normal
0
Low
TF0005A
Figure 2-5. Reconfigured Priority Queue Statistics for the Queue Size
Examples
To see whether this reallocation solves the problem, reset the Clipped Packets
Count and High-Water Packets Mark counters using the Statistics Manager and
check them again later.
Latency
Line delay, or latency, indicates how many bits of normal- or low-priority traffic
the router can allocate to the transmit queue at any one time. The latency value is
the greatest time delay that a high-priority packet can experience.
Latency is based on the line speed of the attached media. The following formula
illustrates how the line speed, b its queued, and latency value are related:
Latency = Bits Queued / Line Speed (b/s)
The default value for latency is 250 milliseconds (ms). This value generally
ensures good throughput and maintains rapid terminal response (rapid echoing of
keystrokes and timely response to commands) over most media.
2-14
You can change the default latency value by setting the Max High Queue Latency
parameter. Keep in mind, however, that if you specify a higher l at ency value (thus
allowing more room on the transmit queue), throughput increases, but terminal
response time decreases. Nortel Networks recommends using the default value of
250 ms.
308645-14.00 Rev 00
Page 49

Editing Protocol Prioritization Parameters
To edit protocol prioritization parameters:
Site Manager Procedure
You do this System responds
Using Protocol Prioritization Queues
1. In the Circuit Definition window, choose
Protocols > Edit Protocol Priority > Interface.
2. Select the parameter you want to change.
To see additional parameters, use the scroll bar
on the right side of the window.
3. For a description of the parameter, click on
in the Site Manager window, or refer to
Help
the appropriate parameter description in
Appendix A:
•Enable
• High Queue Si ze
• Normal Queue Size
• Low Queue Size
• Max High Queue Latency
• High Water Packets Clear
• Pri oritization Algorithm Type
• High Queue Percent Bandwidth
• Normal Queue Percent Bandwidth
• Low Queue Percent Bandwi dth
• Discard Eligible Bit Low
• Discard Eligible Bit Normal
4. Click on
5. Select the value you want, then click on OK. The Values Selection window closes.
6. Click on OK when you are done setting
protocol prioritization para meters.
. The Valu es Selection window opens,
Values
The Edit Protocol Priority Interface
window opens.
listing valid values for the parameter.
The Edit Protocol Priority Interface
window now displ ays the new value.
You return to the Circuit Definition
window.
308645-14.00 Rev 00
2-15
Page 50

Configuring Traffic Filters and Protocol Prioritization
Monitoring Protocol Prioritization Statistics
To monitor and manage protocol prioritization, you use the Statistics Manager to
view statistics in the MIB object group
wfApplication.wfDatalink.wfProtocolPriorityGroup. For information about using
the Statistics Manager to view MIB objects and create custom screen reports, see
Configuring and Managing Routers with Site Manager.
To determine whether there are enough buffers in each priority queue for the
traffic flow on your network, use the St atistics Manager to examine the following
protocol prioritization statistics:
• High-Water Packets Mark
The greatest number of packets that have been in each queue.
• Clipped Packets Count
The number of pac ket s tha t have been discarded from eac h queue . ( The rout er
discards packets from priority queues that become full.)
Note:
To determine whether statistics reflect a transient event, you may want
to reset the statistics and check again later before chan ging the priority
queuing configur ation. You can reset the High-Water Packets Mark using the
Configuration Manager Edit Protocol Pri or it y I nt er f ac e window. You can reset
both the Clipped Packets Count and High-Water Packets Mark using the
Statistics Manager.
2-16
Generally, if a queue’s Clipped Packets Count is high and the High-Water Packets
Mark is close to its queue size, that queue does not have enough buffers.
308645-14.00 Rev 00
Page 51

Chapter 3
Inbound Traffic Filter Criteria and Actions
You create inbound traffic filters using templates that consist of protocol-specific
filter crit er ia , ra nges , and act ion s. To define a n inb ound traff i c filter template, you
need to know the specific criteria and action s that Site Manager suppo r ts for the
applicable protocol.
This chapter lists the following for supported bridging and routing protocols:
• Predefined inbound traffic filter criteria and actions
• Reference points for specifying user-defined criteria
Topic Page
Transparent Bridge Criteria and Actions 3-2
Source Route Bridging Criteria and Actions 3-5
DECnet Phase IV Criteria and Actions 3-7
DLSw Criteria and Actions 3-8
IP Criteria and Actions 3-9
IPX Criteria and Actions 3-11
LLC2 Criteria and Actions 3-12
OSI Criteria and Actions 3-13
VINES Criteria and Actions 3-14
XNS Criteria and Actions 3-15
For an overview of traffic filters, templates, and the ir criteria, ranges, and actions,
see Chapter 1. For instructions on using Site Manager to create inbound traffic
filters, see Chapter 6.
308645-14.00 Rev 00
3-1
Page 52

Configuring Traffic Filters and Protocol Prioritization
Transparent Bridge Criteria and Actions
Transp arent bridge tra f fi c fi lters su pport se v eral encapsula tion methods and media
types. You filter inbound transparent bridge frames based on the contents of the
header fields for one of the four supported encapsulation methods:
•Ethernet
• IEEE 802.2 LLC
• IEEE 802.2 LLC with SNAP
• Novell Proprietary
Figure 3-1
illustrates the header reference fields for each encapsulation method.
Ethernet Header
MAC
Destination
48-bit MAC destination address
48-bit MAC source address
16-bit length/type is TYPE (>1518)
MAC
Source
Length/
Type
IEEE 802.2 LLC Header
MAC MAC
Destination
48-bit MAC destination address
48-bit MAC source address
16-bit length/type is LENGTH (<1519)
8-bit DSAP
8-bit SSAP
8-bit Control
Source
Length/
Type
DSAP SSAP Control
IEEE 802.2 LLC with SNAP Encapsulation
MAC
Source
Length/
Type
DSAP
SSAP
Control
Org.
MAC
Destination
48-bit MAC destination address
48-bit MAC source address
16-bit length/type is LENGTH (<1519)
DSAP/SSAP/Control is 0xAAAA03
24-bit Organization Code
16-bit Ethernet Type
Novell Proprietary Encapsulation
MAC
Destination
48-bit MAC destination address
48-bit MAC source address
16-bit length/type is LENGTH (<1519)
Next 16 bits are all ones (part of IPX header)
MAC
Source
Length/
Type
FF FF
Ethernet
TypeCode
TF0007A
Figure 3-1. Header Reference Fields for Transparent Bridge Encapsulation Methods
Table 3-1 indic at es which encapsu lati on methods are support ed for spe cif i c route r
interfaces.
3-2
308645-14.00 Rev 00
Page 53

Inbound Traffic Filter Criteria and Actions
Table 3-1. Transparent Bridge Encapsulation Support
Encapsulation Method
Router Interface
Ethernet/802.3 (XCVR) Yes Yes Yes Yes
FDDI (FDDI) No Yes Yes No
Token ring (TOKEN) No Yes Yes No
Synchronous (COM) Yes Yes Yes Yes
Ethernet 802.2 LLC LLC with SNAP Novell
Predefined Transparent Bridge Criteria
Each transparent b ri dge encapsulation met hod has specific, pr ede fined criteria for
filtering fram es. These pre defined criteria are based on an offset to a header
reference field (Figure 3-1
predefined criteria for each encapsulation method, and the reference field, offset,
and length for each criterion.
Table 3-2. Predefined Criteria for Transparent Bridge Inbound Traffic
Filters
Encapsulation
Method Criterion Name
All MAC Source Address MAC 0 48
MAC Destina tio n Addr es s MAC 48 48
Ethernet Ethernet Type MAC 96 16
802.2 LLC Length
(Ethernet/802.3 and PPP only)
SSAP DATA_LINK 0 8
DSAP DATA_LINK 8 8
Control DATA_LINK 16 8
802.2 LLC with
SNAP
Novell Novell MAC 112 16
Length MAC 96 16
Organization Code (Protoco l ID) DAT A_LI NK 24 24
Ethernet Type DATA_LINK 48 16
) and are a specified length. Table 3-2 lists the
Reference
Field
MAC 96 16
Offset
(bits)
Length
(bits)
308645-14.00 Rev 00
3-3
Page 54

Configuring Traffic Filters and Protocol Prioritization
User-Defined Transparent Bridge Criteria
You can create bridge traffic filters with user-defined criteria by specifying an
offset and length to these supported reference fi elds:
Reference Field Description
MAC Points to the first byte of the MAC Destination Address
DATA_LINK Points to the first byte of the DATA_LINK reference field
Transparent Bridge Actions
In addition to the Accept, Drop, and Log actions that are common to all inbound
traffic filters, there are two transparent bridge actions:
• Flood
Specifies that any frame that matches the filter will be forwarded to all
transparent bridge cir cuits, except fo r the circuit from which it was received
• Forward to Circuit List
3-4
Specifies that any frame that matches the filter will be forwarded to the
specified circuits
Note:
The circuit names th at you spec ify for the F orw ard to Ci rcuits a ction ar e
case-sensitive. For example, if the circuit name is E21, but you type
e21
, the
filter will not be saved.
You can specify the Log action wit h any of the ot her acti ons. Ho we ver, you should
specify the Log action only to recor d abnormal events; otherwise, the Events log
will fill up with filtering messages, leaving no room for critical log messages.
308645-14.00 Rev 00
Page 55

Inbound Traffic Filter Criteria and Actions
Source Route Bridging Criteria and Actions
You filter inbound source route bridging (SRB) traffic based on specified bit
patterns in the native SRB frame header. IP-encapsulated SRB traffic filters are
not supported.
SRB filters affect both explorer and routed frames. However, filters that include
Next Ring as a criteri on af fect only route d frames because the Ne xt Ring refe rence
field does not appear in explorer frames. See Configuring Bridging Services for
information about explorer and routed frames.
Note:
The router applies SRB filters after it processes a packet. The router
receives the packet on the incoming interface and updates the routing
information field (RIF). The filters that you configure then act on the updated
RIF.
Predefined SRB Criteria
Table 3-3 lists the predefined criteria for SRB inbound traffic filters, and the
reference field, offset, and length for each SRB criterion.
Table 3-3. Predefined Criteria for SRB Inbound Traffic Filters
Criterion Name Reference Field Offset (bits) Length (bits)
Next Ring NEXT_RING 0 12
Destination MAC Address HEADER_START 0 48
Source MAC Address HEADER_START 48 48
DSAP DATA_LINK 0 8
SSAP DATA_LINK 8 8
Destination NetBIOS Name DATA_LINK 120 120
Source NetBIOS Name DATA_LINK 248 120
Specifying an SRB Criterion Range
If you create an SRB filter that includes a Source or Destination NetBIOS Name
criterion, you type the NetBIOS name as the ASCII equivalent of the first 15
characters of the name. If the name has fewer than 15 characters, use ASCII
spaces (0x20) to ensure that the name has exactly 15 characters.
308645-14.00 Rev 00
3-5
Page 56

Configuring Traffic Filters and Protocol Prioritization
See Chapter 5 for information about specifying SAP and MAC address criteria.
User-Defined SRB Criteria
In addition to the predefined filter criteria, you can create SRB inbound traffic
filters with user-defined criteria by specifying an offset and length to these
reference fields in the SRB h eader:
Reference Field Description
NEXT_RING Points to the first byte of the NEXT_RING reference field
HEADER_START Points to the first byte of the Destination MAC Address
DATA_LINK Points to the first byte of the DATA_LINK reference field
SRB Actions
In addition to the Accept, Drop, and Log actions common to all inbound traffic
filters, there are two SRB actions:
• Direct IP Explorers
3-6
Specifies that any explorer frame that matches the filter will be sent to some
number of IP addresses. You must specify these IP addresses.
For this action to work, IP encapsulation must be configured on the filter’s
interface. If IP encapsulation is not configured and a frame matches the filter,
the frame will be flooded as if no filter exists.
• Forward to Circuits
Specifies that any frame that matches the filter will be forwarded to some
number of circuits on the same router. You must specify these circuits.
Note:
The circuit names th at you spec ify for the F orw ard to Ci rcuits a ction ar e
case-sensitive. For example, if the circuit name is E21, but you type
e21
, the
filter will not be saved.
You can specify the Log action wit h any of the ot her acti ons. Ho we ver, you should
specify the Log action only to recor d abnormal events; otherwise, the Events log
will fill up with filtering messages, leaving no room for critical log messages.
308645-14.00 Rev 00
Page 57

Inbound Traffic Filter Criteria and Actions
DECnet Phase IV Criteria and Actions
You can filter inbound DECnet Phase IV traffic based on specified bit patterns in
the DECnet header.
Predefined DECnet Criteria
Table 3-4 lists the predefined criteria for DECnet Phase IV inbound traffic filters,
and the reference field, offset, and length for each criterion.
Table 3-4. Predefined Criteria for DECnet Phase IV Inbound Traffic
Filters
Criterion Name Reference Field Offset Length
Destination Area DEC4_BASE 0 6
Destination Node DEC4_BASE 6 10
Source Area DEC4_BASE 16 6
Source Node DEC4_BASE 22 10
User-Defined DECnet Criteria
In addition to the predef ined DECnet Phase IV fi lter cri teria, you can cre ate traf f ic
filters with user-defined criteria by specifying an offset and length to this
reference field in the DECnet header:
Reference Field Description
DEC4_BASE Points to the first by te in the header
DECnet Actions
The DECnet Phase IV filtering actions are Accept, Drop, and Log.
308645-14.00 Rev 00
3-7
Page 58

Configuring Traffic Filters and Protocol Prioritization
DLSw Criteria and Actions
You can filter inbound DLSw traffic based on specified bit patterns in the DLSw
header, as defined in RFC 1434.
Predefined DLSw Criteria
Table 3-5 lists the predefined criteria for DLSw inbound traffic filters, and the
reference field, offset, and length for each criterion.
Table 3-5. Predefined Criteria for DLSw Inbound Traffic Filters
Criterion Name Reference Field Offset Length
Destination MAC Address DLS_BASE 192 48
Source MAC Address DLS_BASE 240 48
DSAP DLS_BASE 296 8
SSAP DLS_BASE 288 8
User-Defined DLSw Criteria
In addition to the predefined DLSw filter criteria, you can create inbound traffic
filters with user-defined criteria by specifying an offset and length to these
reference fields in the DLSw header:
Reference Field Description
DLS_CTRL_START Points to the start of the DLSw header
DLS_DATA_START Points to the start of the DLSw data
DLSw Actions
The DLSw filtering actions are as follows:
• Drop, Log -- Common to all inbound traffic filters
• Forward to Peer -- Any frame that matches the filter will be sent to the
3-8
specified DLSw circuits
308645-14.00 Rev 00
Page 59

IP Criteria and Actions
You can filter IP inbound traffic based on specified bit patterns in one of the
following headers in an IP datagram:
• The IP header
• The header of the upper-level protocol (TCP or UDP, for example)
Predefined IP Criteria
Table 3-6 lists the predefined criteria for IP inbound traffic filters, and the
reference field, offset, and length for each criterion.
Table 3-6. Predefined Criteria for IP Inbound Traffic Filters
Criterion Name Reference Field Offset Length
Type of Service HEADER_START 8 8
Protocol ID HEADER_START 72 8
IP Source Address HEADER_START 96 32
IP Destination Address HEADER_START 128 32
UDP or TCP Source Port HEADER_END 0 16
UDP or TCP Destination Port HEADER_END 16 16
Established TCP*
* Allows filtering on the ACK and RESET bits in the TCP header. You do not specify a range for this
criterion
.
Inbound Traffic Filter Criteria and Actions
HEADER_END 107 3
User-Defined IP Criteria
In addition to the pre def in ed f i lter crit eria, yo u can c reate IP inbound traffic filters
with user-defined criteria by specifying an offset and length to these reference
fields in the IP header (Table 3-7
308645-14.00 Rev 00
).
3-9
Page 60

Configuring Traffic Filters and Protocol Prioritization
Table 3-7. User-Defined Criteria for IP Inbound Traffic Filters
Reference Field Description
HEADER_START Points to the first byte of the Type of Service (ToS)
HEADER_END Points to the last byte of the IP Destination Address
When specifying the user-defined criterion length, use 8 bits whenever possible.
IP inbound traffic filter criteria with a length of 1 bit work onl y when alig ned on a
byte (word) boundary. Lengths from 2 through 7 bits do not work.
IP Actions
In addition to the Accept, Drop, and Log actions common to all inbound traffic
filters, there are the following IP actions:
• Forward to Next Hop
Specifies that any frame that matches the filter will be forwarded to the
next-hop router. You must specify the IP address of the ne xt - hop router. If the
next-hop router is not reachable, any packets matching the filter will be
forwarded normally u nless y ou also specif y Drop If Ne xt Hop Is Unreach able.
3-10
If you specify 255.255.255.255 as the next hop, any frame that matches this
filter will be forwarded normally.
• Drop If Next Hop Is Unreachable
This action is val id only whe n Forward to Next Hop is in use. It specifies th at
if the next-hop address specified is unreachable, the frame is dropped.
• Forward to IP Address
Specifies that any frame that matches the filter will be forwarded to a single
address in a list of specified IP addresses. The destination address of the
original packet changes to the specified IP address.
• Forward to Next Hop Interfaces
Specifies that any frame that matches the filter will be duplicated and
forwarded to a group of next-hop IP addresses that you specify. If none of the
next-hop interfaces is active, the router forwards packets that match the filter
to the packet desti nati on addre ss (unl ess you also sp ecify Drop If Ne xt Hop I s
Unreachable).
308645-14.00 Rev 00
Page 61

• Forward to First Up Next Hop Interface
Specifies that any frame that matches the filter will be forwarded to a
specified next-hop router or to a network connected to the router. If the
specified hop is not reachable, the filter tries all addresses on the next-hop
interfaces list using ARP messages. If none of the next-hop interfaces is
reachable, the router forwards packets that match the filter to the packet
destination address (unless you also specify Drop If Next Hop Is
Unreachable).
• Detailed Logging
For every packet that matches the filter criteria and ranges, the filter adds an
entry containing IP header information to the system Events log.
IPX Criteria and Actions
You filter inbound IPX traffic based on specified bit patterns in the IPX header.
Predefined IPX Criteria
Inbound Traffic Filter Criteria and Actions
Table 3-8 lists the predefined criteria for IPX inbound traffic filters, and the
reference field, offset, and length for each criterion.
Table 3-8. Predefined Criteria for IPX Inbound Traffic Filters
Criterion Name Reference Field Offset Length
Destination Network IPX_BASE 48 32
Destination Address IPX_BASE 80 48
Destination Socket IPX_BASE 128 16
Source Network IPX_BASE 144 32
Source Address IPX_BASE 176 48
Source Socket IPX_BASE 224 16
308645-14.00 Rev 00
3-11
Page 62

Configuring Traffic Filters and Protocol Prioritization
User-Defined IPX Criteria
In addition to the predefined filter criteria, you can create traffic filters with
user-def ined cri teria b y specifying an offse t and lengt h to this refer ence fi eld in the
IPX header:
Reference Field Description
IPX_BASE Points to the first byte in the IPX header
IPX Actions
The IPX filtering actions are Accept, Drop, and Log.
LLC2 Criteria and Actions
You can filter inbound LLC2 traffic based on specified bit patterns in the LLC2
header.
Adding an IBM protocol to a cir cuit auto maticall y adds LLC2 . LLC2 traf f ic f ilt ers
apply to LLC2 routed over Frame Relay (also known as native SNA over Frame
Relay) and to any protocol running over LLC2, including Advanced Peer-to-Peer
Networking (APPN) and LAN Network Manager (LNM).
Predefined LLC2 Criteria
Table 3-9 lists the predefined criteria for LLC2 inbound traffic filters, and the
reference field, offset, and length for each criterion.
Table 3-9. Predefined Criteria for LLC2 Inbound Traffic Filters
Criterion Name Reference Field Offset Length
Destination MAC Address LLC2_DEST_MAC 0 48
Source MAC Address LLC2 _SOURCE_MAC 48 48
DSAP LLC2_DSAP 0 8
SSAP LLC2_SSAP 8 8
3-12
308645-14.00 Rev 00
Page 63

User-Defined LLC2 Criteria
In addition to the predefined LLC2 criteria, you can create traffic filters with
user-defined criteria by specifying an offset and length to these reference fields in
the LLC2 header:
Reference Field Description
LLC2_DEST_MAC Points to the first byte of the Destination MAC Address
LLC2_DSAP Points to the first byte of the Destination SAP (DSAP)
LLC2 Actions
The LLC2 filtering actions are Accept, Drop, and Log.
OSI Criteria and Actions
You can configure OSI inbound tr af fic filters based on specified bi t patterns in the
Connectionless Network Protocol (CLNP) header.
Inbound Traffic Filter Criteria and Actions
Predefined OSI Criteria
Table 3-2 lists the predefined criteria for OSI inbound traffic filters, and the
reference field, offset, and length for each criterion.
Table 3-10. Predefined Criteria for OSI Inbound Traffic Filters
Criterion Name Reference Field Offset Length
Destination Area OSI_DEST 0 16
Destination System ID OSI_DEST 16 48
Source Area OSI_SRC 0 16
Source System ID OSI_SRC 16 48
308645-14.00 Rev 00
3-13
Page 64

Configuring Traffic Filters and Protocol Prioritization
User-Defined OSI Criteria
In addition to the predefined OSI filter criteria, you can create traffic filters with
user-defined criteria by specifying an offset and length to these reference fields in
the CLNP header:
Reference Field Description
OSI_BASE Points to the first byte of the CLNP header
OSI_DEST Points to the last two bytes of the OSI_DEST reference field
OSI_SRC Points to the last two bytes of the OSI_SRC reference field
OSI Actions
The OSI filtering actions are Accept, Drop, and Log.
VINES Criteria and Actions
You can filter inb ound VINES traffic based on specified b it pat terns in the VINES
header.
Predefined VINES Criteria
Table 3-11 lists the predefined criteria for VINES inbound traffic filters, and the
reference field, offset, and length for each criterion.
Table 3-11. Predefined Criteria for VINES Inbound Traffic Filter s
Criterion Name Reference Field Offset Length
Protocol Type VINES_BASE 40 8
Destination Address VINES_BASE 48 48
Source Address VINES_BASE 96 48
3-14
308645-14.00 Rev 00
Page 65

User-Defined VINES Criteria
In addition to the predefined VINES filter criteria, you can create traffic filters
with user-de fined criteria by specifying an offset and length to this reference field
in the VINES h eader:
Reference Field Description
VINES_BASE Points to the first byte in the VINES header
VINES Actions
The VINES filtering actions are Accept, Drop, and Log.
XNS Criteria and Actions
You can filter inbound XNS traffic based on specified bit patterns in the XNS
header.
Inbound Traffic Filter Criteria and Actions
Predefined XNS Criteria
Table 3-12 lists the predefined criteria for XNS inbound traffic filters, and the
reference field, offset, and length for each criterion.
Table 3-12. Predefined Criteria for XNS Inbound Traffic Filters
Criterion Name Reference Field Offset Length
Destination Network XNS_BASE 48 32
Destination Address XNS_BASE 80 48
Destination Socket XNS_BASE 128 16
Source Network XNS_BASE 144 32
Source Address XNS_BASE 176 48
Source Socket XNS_BASE 224 16
308645-14.00 Rev 00
3-15
Page 66

Configuring Traffic Filters and Protocol Prioritization
User-Defined XNS Criteria
In addition to the predefined filter criteria, you can create traffic filters with
user-def ined cri teria b y specifying an offse t and lengt h to this refer ence fi eld in the
XNS header:
Reference Field Description
XNS_BASE Points to the first byte in the XNS header
XNS Actions
The XNS filtering actions are Accept, Drop, and Log.
3-16
308645-14.00 Rev 00
Page 67

Chapter 4
Outbound Traffic Filter Criteria and Actions
You create outbound traffic filters using templates that consist of criteria, ranges,
and actions. To define a template, you need to know the specific criteria and
actions that Site Manager supports for outbound traffic filters.
This chapter lists the following:
• Predefined outbound traffic filter criteria and actions
• Reference points for user-defined criteria
Topic Page
Selecting Predefined Criteria
Selecting User-Defined Criteria 4-7
Selecting Actions 4-10
For an overview of traffic filters, templates, and the ir criteria, ranges, and actions,
see Chapter 1. For instructions on using Site Manager to create outbound traffic
filters, see Chapter 7.
Note:
DLSw Services.
308645-14.00 Rev 00
4-2
For information about DLSw outbound traffic filters, see Configuring
4-1
Page 68

Configuring Traffic Filters and Protocol Prioritization
Selecting Predefined Criteria
Outbound traffic filter criteria are based on the data link header or IP header.
• For bridged traffic, you use predefined criteria based on the data link header.
• For IP-routed traffic, you use predefined criteria based on the IP header.
• For most WAN and LAN routing protocols, you can use predefined criteria
based on either the data link header or the IP header.
• F or Net BIOS, SNA, and other DLSw-encapsulated traffic, you use predef ined
outbound traffic filter criteria based on the DLSw protocol header. For
information about DLSw outbound traffic filters, see Configuring DLSw
Services.
This section covers the following topics:
• Predefined Data Link Criteria
• Predefined IP Criteria
• Specifying Criteria Common to IP and Data Link He aders
Predefined Data Link Criteria
You can configure outbound traffic filters based on the predefined data link
criteria listed in Table 4-1
Table 4-1. Predefined Data Link Criteria for Outbound
Traffic Fi lt ers
Packet Component Predefined Criteria
Data link header
(Data Link Type)
.
MAC Source Address
MAC Destination Address
Ethernet Type
Novell
802.2 Length
802.2 DSAP
802.2 SSAP
802.2 Control
802.2 SNAP Length
802.2 SNAP Protocol ID
802.2 SNAP Ethernet Type (Ethertype)
(continued)
4-2
308645-14.00 Rev 00
Page 69

Outbound Traffic Filter Criteria and Actions
Table 4-1. Predefined Data Link Criteria for Outbound
Traffic Fi lt ers
Packet Component Predefined Criteria
SRB DSAP
PPP Protocol ID
Frame Relay 2-byte DLCI
(continued)
SSAP
3-byte DLCI
4-byte DLCI
NLPID
Ethernet Type (Ethertype)
Figure 4-1 shows the Configuration Manager menu path for specifying these
criteria. See Chapter 7 for detailed instructions on creating outbound filters.
308645-14.00 Rev 00
4-3
Page 70

Configuring Traffic Filters and Protocol Prioritization
4-4
Figure 4-1. Predefined Data Link Criteria for Outbound Traffic Filters
308645-14.00 Rev 00
Page 71

Predefined IP Criteria
You configure outbound traffic filters for routing protocols based on the
predefined criteria listed in Table 4-2
Table 4-2. Predefined IP Criteria for Outbound Traffic Filters
Packet Type or Component Predefined Criteria
IP header Type of Service
SRB MAC Destination Address
PPP Protocol ID
Frame Relay 2-byte DLCI
Outbound Traffic Filter Criteria and Actions
.
IP Source Address
IP Destination Address
Both Source Address
UDP Source Port
UDP Destination Port
TCP Source Port
TCP Destination Port
TCP
TCP
Established TCP P o rt
Protocol
MAC Source Address
SSAP
DSAP
3-byte DLCI
4-byte DLCI
NLPID
UDP Source Port
or
UDP Destination Port
or
Destination Address
and
You can assign as many as 31 outbound traffic filters with IP criteria to an
interface. Figure 4-2
these criteria. See Chap ter 7 f or detailed instructions on using Configuration
Manager to create outbound traffic filters.
308645-14.00 Rev 00
shows the Configuration Manager menu path for specifying
4-5
Page 72

Configuring Traffic Filters and Protocol Prioritization
Figure 4-2. Predefined IP Criteria for Outbound Traffic Filters
Specifying Criteria Common to IP and Data Link Headers
Several predefined outbound traffic filter criteria are common to both the IP and
data link headers, such as the PPP Protocol ID, SRB SSAP/DSAP, and Frame
Relay DLCI and NLPID criteria.
T o config ure outbound tra ff ic f ilters f or IP-rout ed packets , alwa ys select IP ins tead
of Datalink when choosing the criterion. If you create a filter using a data link
criterion to ide ntify an IP-r outed packet (for ex ample, using t he Ethertype r ange of
0x0800 or the Protocol ID of 0x0021), the filter does not work because the router
code recognizes the IP-routed packet and expects IP filter rules.
4-6
308645-14.00 Rev 00
Page 73

To configure criteria for both IP and data link reference points, you create two
filters: one with the IP criterion and the other with the Datalink criterion. For
example, if you want to prioritize Frame Relay traffic with data link connection
identifier (DLCI) 400 in the High que ue, create f ilter s for both the IP and Datalink
DLCI criterion, using a range value of 400.
Selecting User-Defined Criteria
To create a filter wit h a us er-defined criterion, you specify the of fset and length to
a supported reference point in the data link or IP packet header. This section
describes the following reference points for specifying user-defined outbound
traffic filter criteria:
• Data Link Reference Points
• IP Reference Points
Data Link Reference Points
Table 4-3 defines the reference points in the data link header from which you can
build user-defined criterion
Outbound Traffic Filter Criteria and Actions
Table 4-3. Data Link Reference Points
Reference Point Definition
MAC Points to the high-order byte of the destination address
DATA_LINK Points to the first byte following the length/type criteria
DL_HEADER_START Points to the beginning of the header (beginning of the
DL_HEADER_END Points to the first byte following the DLCI in a Frame Relay
DL_FR_MPE Points to the NLPID (Frame Relay packets only)
DL_SR_START Points to the beginning of the SRB packet, which is the
DL_SR_DATA_LINK Points to the first byte following the RIF
Figures 4-3
a packet.
308645-14.00 Rev 00
packet) for PPP and Frame Relay packets
packet, and the first byte following the protocol ID in a PPP
packet
high-order byte of the destination address
and 4-4 show examples of where these reference points are locat ed in
4-7
Page 74

Configuring Traffic Filters and Protocol Prioritization
DL_HEADER_START
DL_HEADER_END
DL_FR_MPE
DLCI OX03 00 00 80 00 80 C2 00 07 DA SA LENGTH DSAP SSAP
DL_SR_START DL_SR_DATA_LINK
03
00 00 A2 8101
DA SA RIF DSAP SSAP
MAC DATA_LINK
Figure 4-3. Data Link Reference Points in an SRB Packet Bridged over
Bay Networks Proprietary Frame Relay
TF0008A
4-8
MAC
TYPE
DATA_LINK
DSAPMAC SAMAC DA LENGTH
SSAP
CONTROL
TF0009A
Figure 4-4. Data Link Reference Points in an IEEE 802.2 LLC Header
308645-14.00 Rev 00
Page 75

IP Reference Points
Table 4-4 defines the reference points in the IP header from which you can build
user-defined criterion. Figure 4-5
points are located in a packet.
Table 4-4. IP Reference Points
Reference Point Definition
HEADER_START Points to the first byte in the IP header
HEADER_END Points to the first byte following the IP header
IP_WAN_HEADER_START Points to the beginning of the header (beginning
IP_WAN_HEADER_END Points to the first byte following the DLCI in a
IP_SR_START Points to the beginning of the SRB packet, which
IP_SR_DATA_LINK Points to the first byte following the RIF
Outbound Traffic Filter Criteria and Actions
shows an example of where those reference
of the packet) for PPP and Frame Relay packets
Frame Relay packet, and the first byte following
the protocol ID in a PPP packet
is the high-order byte of the destination address
IP_WAN_HEADER_START
IP_WAN_HEADER_END
FF
HEADER_START
00000003 4521
HEADER_END
IP_SR_START
0x3000UDP
IP_SR_DATA_LINK
DA SP RIF
DSAP
SSAP CONTROL
TF0010A
Figure 4-5. IP Reference Points in an IP-Encapsulated SRB Packet Bridged over PPP
308645-14.00 Rev 00
4-9
Page 76

Configuring Traffic Filters and Protocol Prioritization
Selecting Actions
For outbound traffic filters, you can specify different types of actions:
• Filtering Actions
• Prioritizing Actions
• Dial Service Actions
Filtering Actions
You can apply the following actions to an outbound traffic filter:
• Accept
The router processes any packet that matches the filter criteria and ranges.
•Drop
The router does n ot rou te any packet that matches the filter criteria and ranges.
•Log
For e v er y pack et tha t matc hes t he f ilt er cr iter ia an d r anges, the r out er s ends an
entry to the system Events log. You can specify the Log action in combination
with other actions.
4-10
• Detailed Log
For every packet that matches the filter criteria and ranges, the router adds a
more-detailed entry to the system Events log, containing IP header
information.
Note:
Specify the Log actions to record abnormal events only; otherwise, the
Events log will fill up with filtering messages, leaving no room for critical log
messages.
308645-14.00 Rev 00
Page 77

Prioritizing Actions
You can apply the following actions to outbound traffic filters for WAN protocols:
• High
Directs packets that match the filter criteria and ranges to the High queue
•Low
Directs packets that match the filter criteria and ranges to the Low queue
• Length
Uses the length of packets to determine the priority queue
Outbound traffic filters with a prioritizing action are called priority filters.
Note:
You can apply prioritizing actions only to MCE1, MCT1, and
synchronous interfaces. The Configuration Manager does not support priority
filters on the LAN interfaces.
See Chapter 2 for detailed information about protocol prioritization.
Outbound Traffic Filter Criteria and Actions
Dial Service Actions
You can apply the following actions to outbound traffic filters for interfaces
configured as dial-up lines:
•No Call
Packets tha t match the fil ter crit eria and rang es are dropped and do not init iate
a dial connection. (By default, packets transmitted on dial-on-demand lines
always trigger the router to establish a connection.)
• No Reset
Packets that match the filter criteria and ranges are processed but do not reset
the inactivity timer.
Note:
Although No Call and No Reset are available when creating any
outbound traffic filter, these actions are useful only on dial-up interfaces such
as synchronous modem lines or MCT1 interfaces configured with ISDN PRI.
308645-14.00 Rev 00
4-11
Page 78

Configuring Traffic Filters and Protocol Prioritization
You can use the dial service actions to configure outbound traffic filters that
specify or reduce the type of traffic that initiates dial connections.
For example, you can use dial service actions to configure a dial-on-demand
interface to exchange IP RIP and IPX RIP/SAP routing updates only when the
router initiates connections for data transmission. This reduction in update-only
traffic, called dial optimized routing, prevents unnecessary connections and
reduces line costs.
See Configuring Dial Services for information about dial services such as
dial-on-demand and dial optimized routing.
4-12
308645-14.00 Rev 00
Page 79

Chapter 5
Specifying Common Criterion Ranges
For every inbound or outbound traffic filter criterion, you must specify a valid
range -- a series of target values appropriate for the criterion. For many criteria,
you specify an address range.
This chapter expl ains how to specify common address ranges and lists valid
ranges.
Topic Page
Specifying MAC Address Ranges 5-2
Specifying VINES Address Ranges 5-3
Specifying Source and Destination SAP Code Ranges 5-4
Specifying Frame Relay NLPID Ranges 5-5
Specifying PPP Protocol ID Ranges 5-5
Specifying TCP and UDP Port Ranges 5-6
Specifying Ethernet Type Ranges 5-7
Specifying IP Protocol ID and Type of Service Ranges 5-10
308645-14.00 Rev 00
5-1
Page 80

Configuring Traffic Filters and Protocol Prioritization
Specifying MAC Address Ranges
When you create a traffic filter that includes a Source or Destination MAC
Address criterion, you specify the MAC address range in either canonical format
or most significant bit (MSB) format. Table 5-1
Table 5-1. Format for Specifying MAC Addresses
Address Type Address Format
PPP MSB
Bay Networks Standard Frame Relay Canonical
Bay Networks Proprietary PPP Canonical
Token ring MSB*
Ethernet Canonical
* For example, to drop the address 0x123456789ABC, specify the filter range in bit-swapped
format: 0x482C6A1E593D.
The following sections provide information about specifying SRB source MAC
addresses and functional MAC addresses.
lists the MAC address formats.
SRB Source MAC Addresses
Consider the following when specifying source MAC addresses for SRB traffic
filters:
• Set the MSB to 1 by addin g the First Bit Set MAC Address
(0x800000000000) to the source MAC address.
For example, to filter token ring packets with the source MAC address of
0x400037450440, first add 0x800000000000. Then, specify the result,
0xC00037450440, as the criteria range.
• If you use a sniffer to analyze packets for their source MAC address, keep in
mind that the routing information indicator (RII) is set to 1 if the routing
information field (RIF) is present, and is set to 0 if there is no RIF.
Bit 0 (the 0x80 bit) of byte 0 (the leftmost byte) is the RII bit, which indicates
the presence of the RIF b it. For exa mp le, a sniffer decodes LAA with the first
byte of 40 as 0x400031740001. If the RIF bit is set, the hexadecimal value of
the packet is 0xC00031740001.
5-2
308645-14.00 Rev 00
Page 81

SRB Functional MAC Addresses
Functional MA C addr esses a re destinat ion MA C addresse s that alw ays conform to
the following rules:
• Byte 0 = 0xC0
• Byte 1 = 0x00
• The first half of byte 2 = 0x0 to 0x7
Specifying Common Criterion Ranges
Table 5-2
Table 5-2. Functional MAC Addresses
Function Name MAC Address (MSB) Identifying Bit Ethernet Address
Active Monitor 0xC000 0000 0001 Byte 5, bit 7 0x030000000080
Ring Parameter
Server
Ring Error
Monitor
Configuration
Report Server
NetBIOS 0xC000 0000 0080 Byte 5, bit 0 0x030000000001
Bridge 0xC000 0000 0100 Byte 4, bit 7 0x030000008000
LAN Manager 0xC000 0000 2000 Byte 4, bit 2 0x030000000400
User-defined 0xC000 0008 0000 to
lists some common functional MAC addresses.
0xC000 0000 0002 Byte 5, bit 6 0x030000000040
0xC000 0000 0008 Byte 5, bit 4 0x030000000010
0xC000 0000 0010 Byte 5, bit 3 0x030000000008
0xC000 4000 0000
Specifying VINES Address Ranges
You specify VINES server address ranges in hexadecimal format. For example, if
the address of a VINES server is
and specify the filter criteria range as
a2482c.0001
0xa2482c0001
Byte 3, bits 0-4;
Byte 2, bits 1-7
0x030000100000 to
0x030002000000
, convert the value to hexadecimal
.
You can obtain a VINES server address as follows:
• From a sniffer trace
• By using the Technician Interface to obtain the value of the
308645-14.00 Rev 00
wfVinesIfEntry.wfVinesIfAdr MIB object
5-3
Page 82

Configuring Traffic Filters and Protocol Prioritization
Specifying Source and Destina tion SAP Code Ranges
Table 5-3 lists some common SAP codes. The SAP code consists of a 7-bit SAP
address and a 1-bit Command/Response field.
Table 5-3. SAP Codes
SAP Code Description
00-01*
02 Individual Sublayer Management
03 Group Sublayer Management
04-05, 08-09, 0C-0D SNA
06 IP
0E Proway Network Management
10 Novell and SDLC Link Servers
20, 34, EC CLNP ISO OSI
42 BPDU
7E X.25 over 802.2 LLC2
80 XNS
86 Nestar
8E Active Station List
98 ARP
AA SNAP
BC Banyan VIP
E0 Novell IPX
F0 IBM NetBIOS
F4, F5 LAN Network Manager
F8 Remote Program Load
FC IBM RPL
FE ISO Network Layer
FF LLC Broadcast
* The Command/Response bit makes the 0x00 byte look like 0x01.
XID or TEST
5-4
Use these val ues to specif y a range for an y Sou rce or Destin ation SAP traf fic filter
criteria.
308645-14.00 Rev 00
Page 83

Specifying Common Criterion Ranges
Specifying Frame Relay NLPID Ranges
Table 5-4 lists some common Frame Relay network layer protocol ID (NLPID)
values. You use these values to specify ranges for NLPID criteria in an outbound
traffic filter.
Table 5-4. Frame Relay NLPIDs
NLPID (0x) Description
CC*
81, 82, 83 OSI
80 SNAP
* Use this value only to specify ranges for the criterion selected by choosing
Criteria > Add > IP > Frame Relay > NLPID on the Create Priority/Outbound
Template window. Do not use a data link criterion to specify IP traffic.
IP
Specifying PPP Protocol ID Ranges
Table 5-5 lists some common PPP protocol ID values. See RFC 1700 for a
complete list. You use these values to specify ranges for Protocol ID criteria in an
outbound traffic filter.
Tabl e 5-5 . PP P Proto c o l I Ds
Protocol ID (0x) Description
0021*
0023 OSI
0033 Stream Protocol (ST2)
* Use this value only to specify ranges for the criterion selected by choosing
Criteria > Add > IP > PPP > Protocol ID on the Create Priority/Outbound
Template window. Do not use a data link criterion to specify IP traffic.
IP
308645-14.00 Rev 00
5-5
Page 84

Configuring Traffic Filters and Protocol Prioritization
Specifying TCP and U DP Port Ranges
Table 5-6 lists some common TCP port v al ues t o use when speci fying TCP sour ce
or destination port ranges in inbound or outbound IP traffic filters.
Table 5-6. Source and Destination TCP Ports
Description TCP Port
FTP 20, 21
Telnet 23
SMTP 25
DNS 53
Gopher 70
World Wide Web http 80 to 84
DLSw Read P o rt 2065
DLSw Write Po rt 2067
5-6
Table 5-7
lists some common UDP port values to use when specifying UDP
source or destination port ranges in inbound or outbound IP traffic filters.
Table 5-7. Source and Destination UDP Ports
Description UDP Port
DNS 53
TFTP 69
SNMP 161
SNMPTRAP 162
308645-14.00 Rev 00
Page 85

Specifying Ethernet T y pe Ranges
Table 5-8 lists some common Ethernet Type codes to use when specifying
Ethertype ranges in inbound or outbound traffic filters. See RFC 1700 for a
complete list.
Table 5-8. Ethernet Type Codes
Description
Bay Networks Synchronous Pass-Through 80FF
Bay Networks Source Route Traffic (non-Token Ring media) 8101
Bay Networks Breath of Life Packet (BofL) 8102
Bay Networks Transparent Bridge Traffic on Token Ring 8103
Bridged Ethernet over RFC 1490 Frame Relay 0007
Bridged Token Ring over RFC 1490 Frame Relay 0009
Bridged FDDI over RFC 1490 Frame Relay 000A
Bridged PDUs over RFC 1490 Frame Relay 000B
802.3 Length Field 0000-05EE
802.5 Length Field 0000-05FF
Xerox PUP 0101-01FF, 0200, 0201
Nixdorf 0400
XNS (IDP) 0600
XNS (Address Translation) 0601
IP 0800
X.25 0801
CHAOSnet 0804
X.25 Level 3 0805
ARP 0806
XNS 0807
Symbolix 081C
Xyplex 0888-088A
UB Debugger 0900
XNS Address Translation 0A00-0A01
Specifying Common Criterion Ranges
Ethernet Type or
Ethertype Code (0x)
(continued)
308645-14.00 Rev 00
5-7
Page 86

Configuring Traffic Filters and Protocol Prioritization
Table 5-8. Ethernet Type Codes
Description
Banyan VINES 0BAD
DEC 6000-6009
DEC MOP 6001-6002
DRP 6003
DEC LAT 6004
LAVC 6007
3COM 6010-6014
UB Download 7000
UB NUI 7001
UB Boot Broadcast 7002
Proteon 7030
Cabletron 7034
Cronous 8003-8004
HP Probe 8005
Nestar 8006
Excelan 8010
Silicon Graphics 8013, 8014, 8015
HP Apollo Native Ethernet 8019
RARP 8035
DEC BPDU 8038
DEC 8039-8042
DEC Encryption 803D
DEC LAN Traffic Monitor 803F
DEC NetBIOS Emulator 8040
AT&T 8046-8047
Compugraphic 8069
Vitalink Management 807D-8080
Xyplex 8088-808A
Kinetics Ether-talk 809B
(continued)
Ethernet Type or
Ethertype Code (0x)
(continued)
5-8
308645-14.00 Rev 00
Page 87

Specifying Common Criterion Ranges
Table 5-8. Ethernet Type Codes
Description
Spider 809F
Nixdorf 80A3
Siemens 80A4-80B3
Pacer Software 80C6
Applitek 80C7
Intergraph 80C8-80CC
Harris 3M 80CD-80CE
IBM SNA 80D5
Retix Bridge Management 80F2
AARP 80F3
Shiva 80F4
HP Apollo 80F7
Symbolics 8107-8109
Waterloo Software 8130
IPX over Frame Relay 8137
Novell 8137-8138
DEC MOP 9000
XNS Bridge Comm Management 9001
3Com 9002-9003
(continued)
Ethernet Type or
Ethertype Code (0x)
308645-14.00 Rev 00
5-9
Page 88

Configuring Traffic Filters and Protocol Prioritization
Specifying IP Protocol ID and Type of Service Ranges
The Internet Protocol version 4 (IPv4) specifies an 8-bit Protocol field to identify
the next-level protocol. Table 5-9
traffic. Table 5-10
Table 5-9. IP Protocol ID Codes
Description Protocol ID Code (decimal)
ICMP (Internet Control Message Packets) 1
IGP (Interior Gateway Protocol) 9
RSVP (Reservation Protocol) 46
VINES 83
OSPF 89
Table 5-10. IP Type of Service Codes
Description Type of Service Code
Network Control 111
Internetwork Control 110
CRITIC/ECP 101
Flash Override 100
Flash 011
Immediate 010
Priority 001
Routine 000
lists IP Type of Service codes. See RFC 1700 for information.
lists some common Protocol ID codes for IP
5-10
You use these codes to specify ranges for Protocol or Type of Service criteria in
inbound or outbound IP traffic filters. Select these criteria as follows:
• For an inbound traffic filter -- In either the Create IP Template or Edit IP
Filters window, choose Criteria > Add > IP > Type of Service
Protocol ID.
|
• For an outbound traffic filter -- In either the Create Priority/Outbound
Template window or Edit Priority/Outbound Filters window, choose
Criteria > Add > IP > IP > Type of Service
Protocol.
|
308645-14.00 Rev 00
Page 89

Chapter 6
Applying Inbound Traffic Filters
This chapter describes how to use the Configuration Manager to configure
inbound traffic filters.
Topic Page
Displaying the Inbound Traffic Filters Window 6-2
Preparing Inbound Traffic Filter Templates 6-3
Creating an Inbound Traffic Filter 6-10
Editing an Inbound Traffic Filter 6-11
Enabling or Disabling an Inbound Traffic Filter 6-15
Deleting an Inbound Traffic Filter 6-16
Specifying User-Defined Criteria 6-17
Changing Inbound Traffic Filter Precedence 6-18
To complete the procedures in this chapter, you must be familiar with
protocol-specific filtering criteria and actions. Se e Chapter 3 for this information.
308645-14.00 Rev 00
6-1
Page 90

Configuring Traffic Filters and Protocol Prioritization
Displaying the Inbound Traffic Filters Window
T o apply inbound t raf f ic fi lters t o a part icular interf ace , you f irst displa y the Fil ters
window for the protocol you are filtering.
To display the Filters window for all protocols except DLSw:
Site Manager Procedure
You do this System responds
1. Display the Co nfi gur ation Manager
window .
2. Click on the c irc uit int erface connector (for
example,
3. Click on
4. Choose Protocols > Edit
Filters.
The menu path to the Filters window is
protocol specific.
COM1, XCVR2
Edit Circuit
).
. The Circuit Definition window opens; the
protocol
> Traffic
The Edit Connector window opens.
circuit you selected is highlighted.
The Filters windo w for the selected circuit
and protocol opens (Figure 6-1)
.
6-2
To display the Filters window for DLSw:
Site Manager Procedure
You do this System responds
1. Display the Co nfi gur ation Manager
window .
2. Choose Protocols > DLSw > Traffic Filters
(Inbound).
The DLS Filters window opens.
Although the Filters window is protocol specific, you use it the same way for all
protocols. Figure 6-1
shows the Bridge Filters window.
308645-14.00 Rev 00
Page 91

Figure 6-1. Inbound Traffic Filters Window
Preparing Inbound Traffic Filter Templates
Applying Inbound Traffic Filters
To add an inbound traffic filter to a router interface, you apply a protocol-specific
traffic filter template to the circuit. However, you do not alway s need to create a
template; often, you can begin with an existing template. This section describes
how to prepare an inbound traffic filter template by:
• Creating a Template
• Customizing Templates
See “Creating an Inbound Traffic Filter
filter by applying (saving) a filter template to an interface.
308645-14.00 Rev 00
” on page 6-10 to learn how to create the
6-3
Page 92

Configuring Traffic Filters and Protocol Prioritization
Creating a Template
To create an inbound traffic filter template:
Site Manager Procedure
You do this System responds
1. Display the Filters window (Figure 6-1)
“Displaying the Inbound Traffic Filters Window.”
2. Click on
3. Click on
4. Specify a name for the new template in the Filter
Name field.
Use a descriptive name. For example, the name
Drop_Telnet
Telnet session requests from remote nodes.
5. Choose Criteria > Add >
See Chapter 3 for information about the criteria for
your protocol. Each filter template can use only one
criterion.
6. Specify a range for the selected criterion. To
specify a hexadecimal number, use the prefix 0x.
You must specify at least one range. If the range
consists of just one value, specify that value in the
Minimum value field. See Chapter 5 for information
about common traffic filter ranges.
7. Click on OK. The Add Range window closes. The criterion and
8. To add more ranges, choos e Range > Add. Then,
repeat steps 6 and 7.
Template
Create
suggests the crit erion and a ction to drop
. The Filter Te mplate Management window opens
. The Create Template window for the prot ocol opens
criterion
. See
(Figure 6-2)
(Figure 6-3).
.
The Add Range window opens.
range appear in the Filter Information field of the
Create Template window.
.
You can add up to 100 ranges for each criterion.
9. Choose Action > Ad d >
10. C lick on OK. The Filter Temp late Managem ent window opens
6-4
action
.
(Figure 6-2). The template appears in the templates
list.
308645-14.00 Rev 00
Page 93

Applying Inbound Traffic Filters
Figure 6-2. Filter Template Management Window
Figure 6-3. Create Template Window
308645-14.00 Rev 00
6-5
Page 94

Configuring Traffic Filters and Protocol Prioritization
Customizing Templates
There are two ways to customize a filter temp late:
• Copy an existing template , rename it, and then edit it.
This preserv es the origi nal templa te and creat es an e nt irely ne w t empla te wit h
the same criteria and actions. You can t hen modify the n ew temp late to suit
your needs.
• Edit an existing template.
If you do not need to preserve the original template, you can edit it without
first cop yi ng and renaming it. (Changing a template does not affect interfaces
to which the template has already been applied.)
Note:
You can also edit or copy a template using a text editor. The
Configuration Manager stores all templates in the file template.flt.
Copying a Template
To du plicate an existing template:
6-6
Site Manager Procedure
You do this System responds
1. Display the Filters window (Figure 6-1)
See “Displaying the Inbound Traffic
Filters Window.”
2. Click on
3. Select a template.
4. Click on
5. Specify a name for the new template.
Be sure to use a name that refl ects its
contents.
6. Click on OK. The Filter Template Management window
Template
Copy
. The Filter Template Management window
. The Copy Filter Template window opens.
.
opens (Figure 6-2).
opens. The new template appears in the
templates list.
308645-14.00 Rev 00
Page 95

Applying Inbound Traffic Filters
Editing a Template
After you create or copy a template, edit it as follows:
Site Manager Procedure
You do this System responds
1. Select a template in the Filter Template
Management window.
2. Click on
3. Add or delete predefined criteria,
ranges, and actions (Table 6-1).
4. Click on OK. The Filter Template Management window
5. Click on
. The Edit Template window for the protoco l
Edit
opens (Figure 6-4)
opens (Figure 6-2).
. The Filters window opens (Figure 6-1)
Done
.
.
Table 6-1
actions in the Edit Template window (Figure 6-4)
describes how to add, delete, or modify predefined criteria, ranges, and
.
To add a user-defined criterion, see “Specifying User-Defined Criteria
page 6-17
.
” on
308645-14.00 Rev 00
6-7
Page 96

Configuring Traffic Filters and Protocol Prioritization
6-8
Figure 6-4. Edit Template Window
308645-14.00 Rev 00
Page 97

Table 6-1. Using the Edit Template Window
Task Site Manager Procedure Notes
Applying Inbound Traffic Filters
Add a
criterion
Delete a
criterion
Add a
range
Modify a
range
Delete a
range
Add an
action
Delete
an action
Save the
template
1. Choose Criteria > Add >
Range window opens.
2. Type a range in the Minimum value and
Maximum value fields, then click on OK.
1. Select the criterion to delete in the Filter
Information field.
2. Click on
opens.
3. Click on
1. Select the criterion in the Filte r Information field. You can add up to 100 ranges. If th e range
2. Click on
3. Type a range in the Minimum value and
Maximum value fields, then click on OK.
1. Select the range to modify in the Filter
Information field.
2. Click on
3. Type new values in the Range Min and Range
Max fields.
1. Select the range to delete in the Filter
Information field.
2. Click on
opens.
3. Click on
1. Choose Action > Add >
1. Select an action in the Filter Information field. You must specify at least one action in a
2. Click on
opens.
3. Click on
1. Click on OK. The Filter Template Management
window opens.
. The Delete Criteria window
Delete
.
Delete
. The Add Range window opens.
Add
.
Modify
. The Delete Range window
Delete
.
Delete
. The Delete Action window
Delete
.
Delete
criterion
action
. The Add
. With the exception of the Log action, each
A template can have only one criterion.
You must specify at least one range in a
template.
A template must ha ve a criterion. Specify a
new criterion after deleting one.
consists of a single v alue , type the v alu e in
the Minimum value field only. Use the
prefix 0x to specify a h e xadec imal num ber.
Zero is not a valid entry.
Ranges are listed below the criterion in the
Filter Information field. Selected ranges
appear in the Range Min and Range Max
fields at the bottom of the Edit Template
window.
You must specify at least one range for
each criterion.
template has only one action.
template.
Be sure you have specified:
• Only one criterion
• Only one action
• 1-100 ranges
308645-14.00 Rev 00
6-9
Page 98

Configuring Traffic Filters and Protocol Prioritization
Creating an Inbound Traff ic Filter
You create an inbound traffic filter by applying a filter template to an interface.
Note:
You should create the filters on an interface in order of precede nce. The
first filter you create has the highest precedence and a rule number of 1.
Subsequent filters that you create have lower precedence. For more
information, see “Changing Inbound Traffic Filter Precedence
To create an inbound traffic filter:
Site Manager Procedure
You do this System responds
” on page 6-18.
1. Display the Filters window (Figure 6-1)
See “Displaying the Inbound Traffic Filters
Window” on page 6-2.
2. Click on
3. Select a circuit in the Interfaces field.
4. Select a template in the Templates field.
If the Templates field is empty, complete the
steps in “Preparing Inbound Traffic Filter
Templa tes” on page 6-3.
5. In the Filter Name field, specify a name for
the new filter.
It can be helpful to include the circuit name to
differentiate the template from the filter. For
example, specify
name of a filter that drops inbound Telnet
traffic on the synchronous circuit S42.
6. Click on OK. The Filters window opens.
. The Create Filter window opens
Create
Drop_T elnet_S42
.
(Figure 6-5).
as the
6-10
308645-14.00 Rev 00
Page 99

Applying Inbound Traffic Filters
Figure 6-5. Create Filter Window
Editing an Inbound Traffic Filter
After you apply an inbound traffic filter to an interface, you can edit its criterion,
ranges, or action. If you used a template that you edited to suit your needs, you
may not need to make further edits.
When you customize a filter, you have the following options:
• Add or delete pre defined criteria
• Add or delete user-defined criteria
• Add or delete actions
• Add, modify, or delete ranges
To add a user-defined criterion, see “Specifying User-Defined Criteria” later in
this chapter.
308645-14.00 Rev 00
6-11
Page 100

Configuring Traffic Filters and Protocol Prioritization
To add predefined criteria, ranges, and actions, or delete any criterion, range, or
action:
Site Manager Procedure
You do this System responds
1. Display the Filters window (Figure 6-1)
See “Displaying the Inbound Traffic Filters
Window” on page 6-2.
2. Select a filter.
3. Click on
4. Add or delete predefined criteria, ranges,
and actions (Table 6-2).
5. Click on OK. The Filters window opens.
Table 6-2
. The Edit Filters window opens
Edit
describes how to add, delete, or modify predefined criteria, ranges, and
actions in the Edit Filters window (Figure 6-6)
.
(Figure 6-6)
.
.
6-12
308645-14.00 Rev 00
 Loading...
Loading...