BDTIC www.BDTIC.com/ATMEL
1. Features
• One of a Family of Devices with User Memories from 1-Kbit to 8-Kbits
• 8-Kbit (1-Kbyte) EEPROM User Memory
– Eight 1-Kbit (128-byte) Zones
– Self-timed Write Cycle
– Single Byte or 16-byte Page Write Mode
– Programmable Access Rights for Each Zone
• 2-Kbit Configuration Zone
– 37-byte OTP Area for User-defined Codes
– 160-byte Area for User-defined Keys and Passwords
• High Security Features
– 64-bit Mutual Authentication Protocol (Under License of ELVA)
– Cryptographic Message Authentication Codes (MAC)
– Stream Encryption
– Four Key Sets for Authentication and Encryption
– Eight Sets of Two 24-bit Passwords
– Anti-Tearing Function
– Voltage and Frequency Monitors
• Smart Card Features
– ISO 7816 Class B (3V) Operation
– ISO 7816-3 Asynchronous T=0 Protocol (Gemplus® Patent)
– Multiple Zones, Key Sets and Passwords for Multi-application Use
– Synchronous 2-wire Serial Interface for Faster Device Initialization
– Programmable 8-byte Answer-To-Reset Register
– ISO 7816-2 Compliant Modules
• Embedded Application Features
– Low Voltage Supply: 2.7V – 3.6V
– Secure Nonvolatile Storage for Sensitive System or User Information
– 2-wire Serial Interface (TWI, 5V Compatible)
– 1.0 MHz Compatibility for Fast Operation
– Standard 8-lead Plastic Packages, Green compliant (exceeds RoHS)
– Same Pin Configuration as AT24CXXX Serial EEPROM in SOIC and PDIP Packages
• High Reliability
– Endurance: 100,000 Cycles
– Data Retention: 10 years
– ESD Protection: 2,000V min
CryptoMemory
AT88SC0808CA
Summary
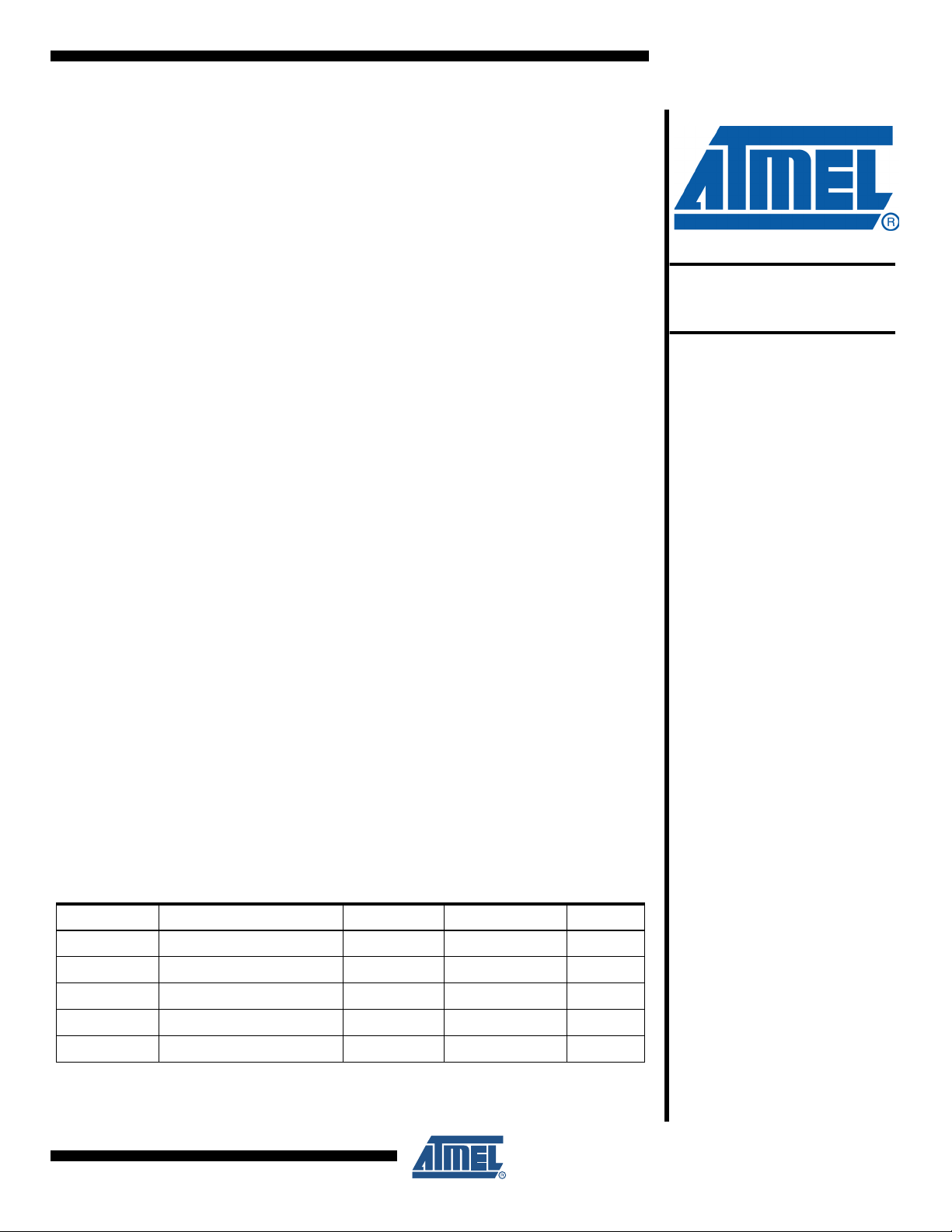
Table 1-1. Pads
Pad Description ISO Module “SOIC, PDIP” TSSOP
VCC Supply Voltage C1 8 8
GND Ground C5 4 1
SCL/CLK Serial Clock Input C3 6 6
SDA/IO Serial Data Input/Output C7 5 3
RST Reset Input C2 NC NC
5204BS–CRYPT–2/09
2. Description
1
2
3
4
8
7
6
5
Smart Card Module
VCC=C1
RST=C2
SCL/CLK=C3
NC=C4
C5=GND
C6=NC
C7=SDA/IO
C8=NC
8-lead SOIC, PDIP
NC
NC
NC
GND
VCC
NC
SCL
SDA
8-lead TSSOP
NC
1 8 VCC
NC
27NC
8-Lead TSSOP
NC
3 6 SCL
GND
45
SDA
The AT88SC0808CA member of the CryptoMemory® family is a high-performance secure
memory providing 8 Kbit of user memory with advanced security and cryptographic features built
in. The user memory is divided into eight 128-byte zones, each of which may be individually set
with different security access rights or effectively combined together to provide space for 1 to 8
data files. The AT88SC0808CA features an enhanced command set that allows direct communication with microcontroller hardware 2-Wire interface thereby allowing for faster firmware
development with reduced code space requirements.
3. Smart Card Applications
The AT88SC0808CA provides high security, low cost, and ease of implementation without the
need for a microprocessor operating system. The embedded cryptographic engine provides for
dynamic, symmetric-mutual authentication between the device and host, as well as performing
stream encryption for all data and passwords exchanged between the device and host. Up to
four unique key sets may be used for these operations. The AT88SC0808CA offers the ability to
communicate with virtually any smart card reader using the asynchronous T = 0 protocol (Gemplus Patent) defined in ISO 7816-3.
4. Embedded Applications
Through dynamic, symmetric-mutual authentication, data encryption, and the use of cryptographic Message Authentication Codes (MAC), the AT88SC0808CA provides a secure place for
storage of sensitive information within a system. With its tamper detection circuits, this information remains safe even under attack. A 2-wire serial interface running at speeds up to 1.0 MHz
provides fast and efficient communications with up to 15 individually addressable devices. The
AT88SC0808CA is available in industry standard 8-lead packages with the same familiar pin
configuration as AT24CXXX serial EEPROM devices.
2
Note: Does not apply to TSSOP Pinout.
AT88SC0808CA
5204BS–CRYPT–2/09
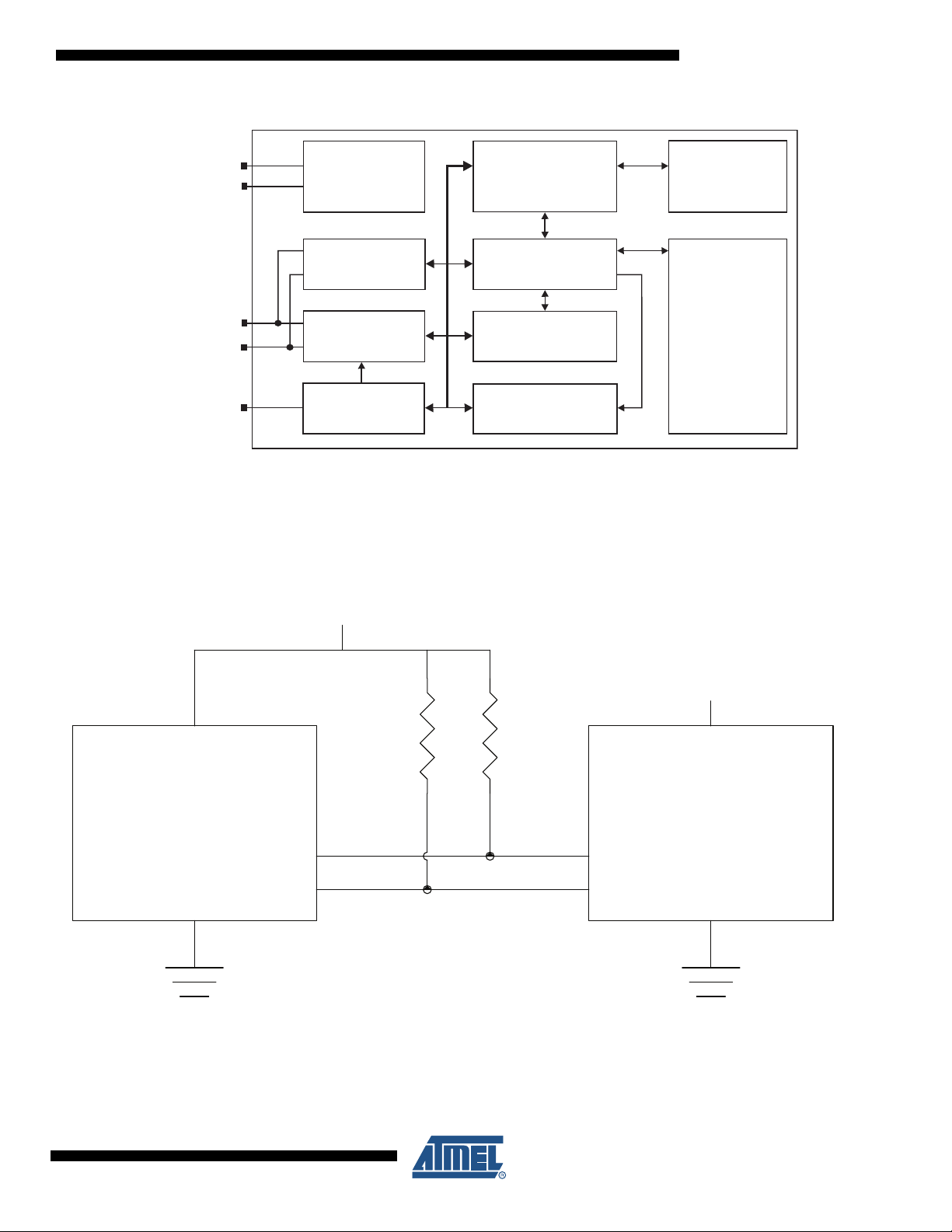
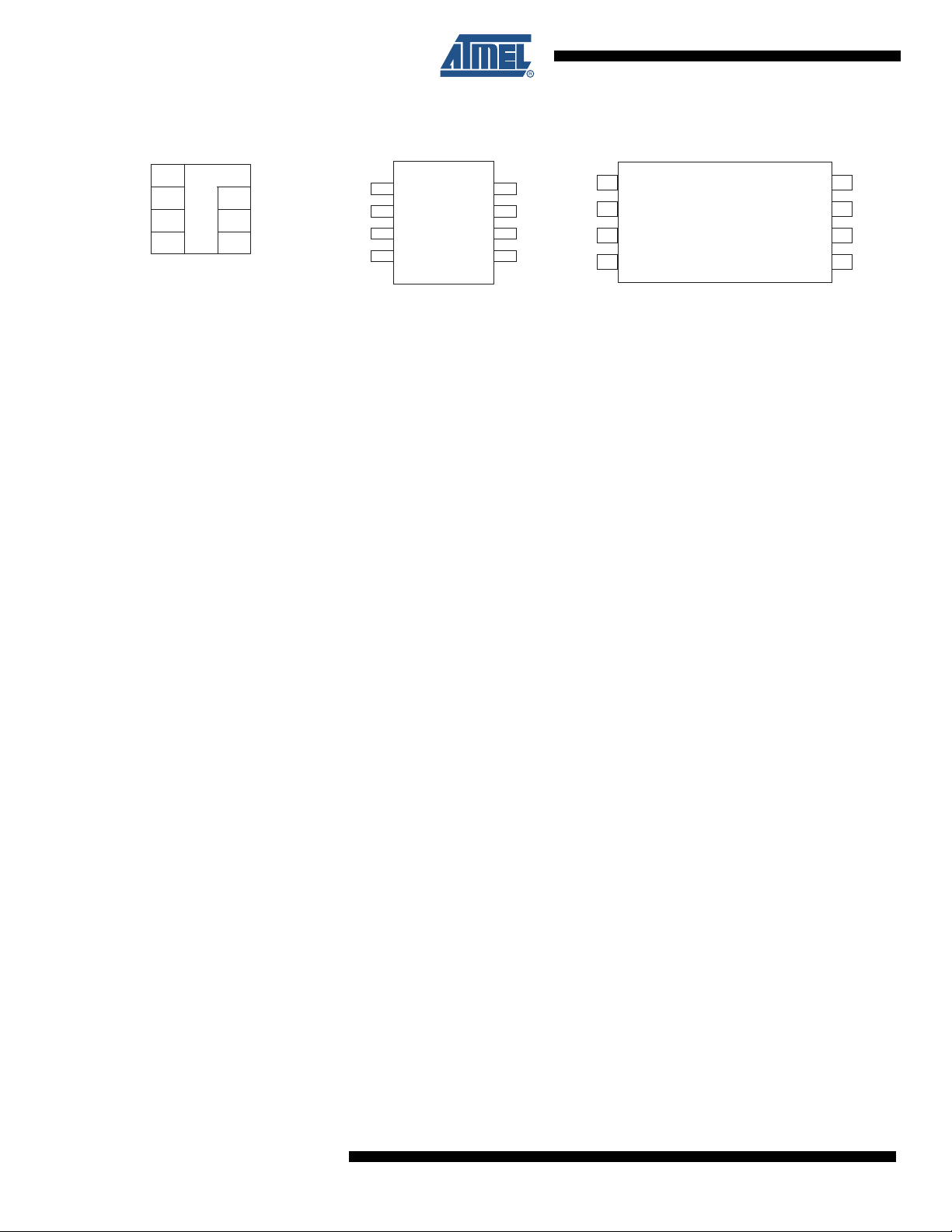
Figure 4-1. Block Diagram
Random
Generator
Authentication,
Encryption and
Certification Unit
EEPROM
Answer to Reset
Data Transf er
Password
Verification
Reset Block
Asynchronous
ISO Interface
Synchronous
Interface
Power
Management
VCC
GND
SCL/CLK
SDA/IO
RST
5. Connection Diagram
AT88SC0808CA
Figure 5-1. Connection Diagram
Microprocessor CryptoMemory
2.7v - 5.5v
2.7v - 3.6v
SDA
SCL
5204BS–CRYPT–2/09
3

6. Pin Descriptions
6.1 Supply Voltage (VCC)
The VCC input is a 2.7V to 3.6V positive voltage supplied by the host.
6.2 Clock (SCL/CLK)
When using the asynchronous T = 0 protocol, the CLK (SCL) input provides the device with a
carrier frequency f. The nominal length of one bit emitted on I/O is defined as an “elementary
time unit” (ETU) and is equal to 372/f.
When using the synchronous protocol, data clocking is done on the positive edge of the clock
when writing to the device and on the negative edge of the clock when reading from the device.
6.3 Reset (RST)
The AT88SC0808CA provides an ISO 7816-3 compliant asynchronous Answer-To-Reset (ATR)
sequence. Upon activation of the reset sequence, the device outputs bytes contained in the 64bit Answer-To-Reset register. An internal pull-up on the RST input pad allows the device to operate in synchronous mode without bonding RST. The AT88SC0808CA does not support an
Answer-To-Reset sequence in the synchronous mode of operation.
6.4 Serial Data (SDA/IO)
The SDA/IO pin is bidirectional for serial data transfer. This pin is open-drain driven and may be
wired with any number of other open-drain or open-collector devices. An external pull-up resistor
should be connected between SDA/IO and VCC. The value of this resistor and the system
capacitance loading the SDA/IO bus will determine the rise time of SDA/IO. This rise time will
determine the maximum frequency during read operations. Low value pull-up resistors will allow
higher frequency operations while drawing higher average power supply current. SDA/IO information applies to both asynchronous and synchronous protocols.
4
AT88SC0808CA
5204BS–CRYPT–2/09
AT88SC0808CA
7. Absolute Maximum Ratings
Stresses beyond those listed under “Absolute Maximum Ratings” may cause permanent damage to the device. This is a
stress rating only and functional operation of the device at these or any other conditions beyond those indicated in the operational sections of this specification is not implied. Exposure to absolute maximum rating conditions for extended periods of
time may affect device reliability.
Absolute Maximum Ratings
Operating Temperature..................................... -40⋅C to +85⋅C
Storage Temperature .......................................... −65
⋅C to +150⋅C
Voltage on Any Pin
with Respect to Ground.................................... −0.7 to Vcc +0.7V
Maximum Operating Voltage............................................. 6.0V
DC Output Current........................................................ 5.0 mA
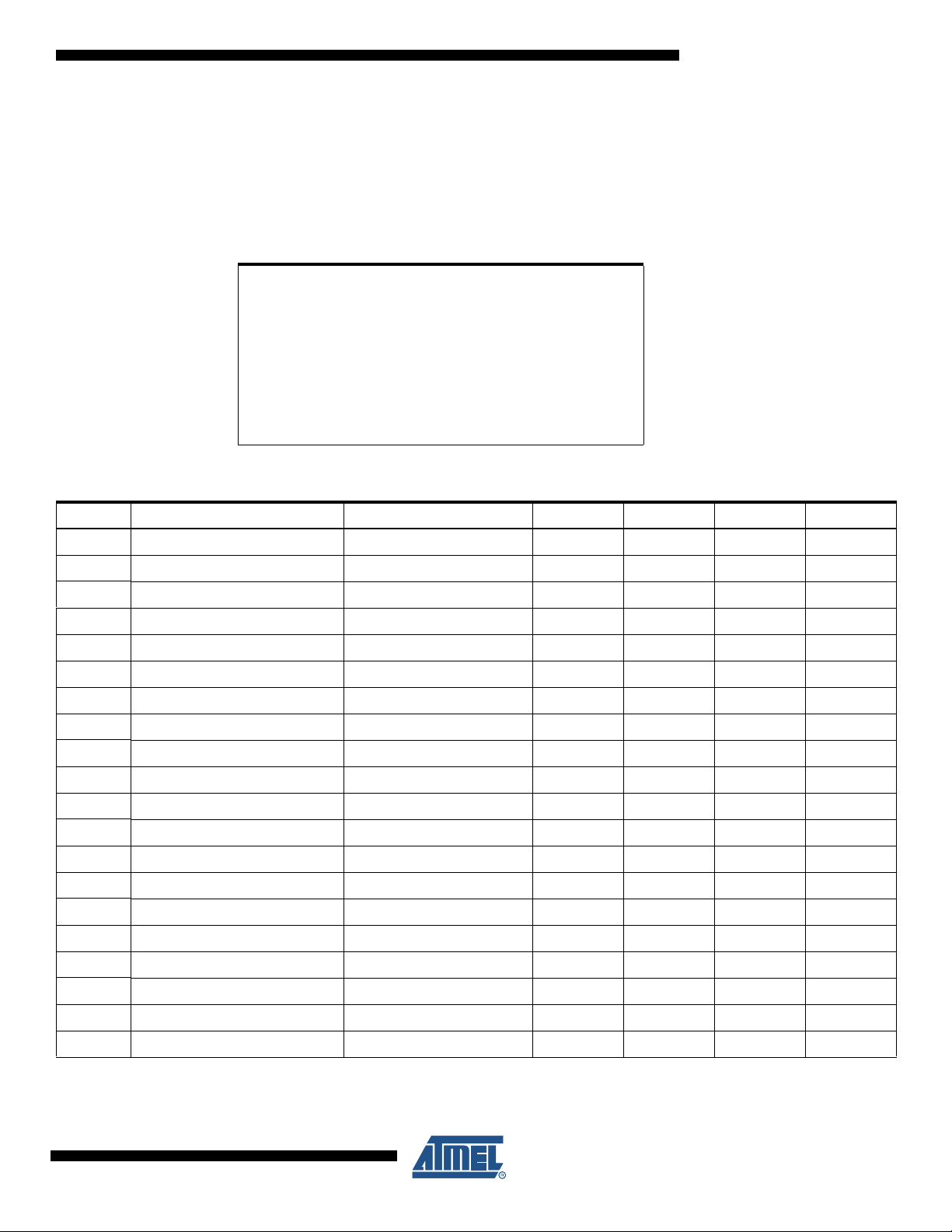
Table 7-1. DC Characteristics
Applicable over recommended operating range from VCC = +2.7 to 3.6V, T
= -40⋅C to +85⋅C (unless otherwise noted)
AC
Symbol Parameter Test Condition Min Typ Max Units
(1)
V
CC
I
CC
I
CC
I
CC
I
CC
I
SB
V
IL
V
IL
V
IL
(1)
V
IH
(1)
V
IH
(1)
V
IH
I
IL
I
IL
I
IL
I
IH
I
IH
I
IH
V
OH
V
OL
Supply Voltage 2.7 3.6 V
Supply Current Async READ at 3.57MHz 5 mA
Supply Current Async WRITE at 3.57MHz 5 mA
Supply Current Synch READ at 1MHz 5 mA
Supply Current Synch WRITE at 1MHz 5 mA
Standby Current VIN = VCC or GND 100 uA
SDA/IO Input Low Voltage 0 VCC x 0.2 V
CLK Input Low Voltage 0 VCC x 0.2 V
RST Input Low Voltage 0 VCC x 0.2 V
SDA/IO Input High Voltage VCC x 0.7 5.5 V
SCL/CLK Input High Voltage VCC x 0.7 5.5 V
RST Input High Voltage VCC x 0.7 5.5 V
SDA/IO Input Low Current 0 < VIL < VCC x 0.15 15 uA
SCL/CLK Input Low Current 0 < VIL < VCC x 0.15 15 uA
RST Input Low Current 0 < VIL < VCC x 0.15 50 uA
SDA/IO Input High Current VCC x 0.7 < VIH < VCC 20 uA
SCL/CLK Input High Current VCC x 0.7 < VIH < VCC 100 uA
RST Input High Current VCC x 0.7 < VIH < VCC 150 uA
SDA/IO Output High Voltage 20K ohm external pull-up VCC x 0.7 VCC V
SDA/IO Output Low Voltage IOL = 1mA 0 VCC x 0.15 V
5204BS–CRYPT–2/09
5
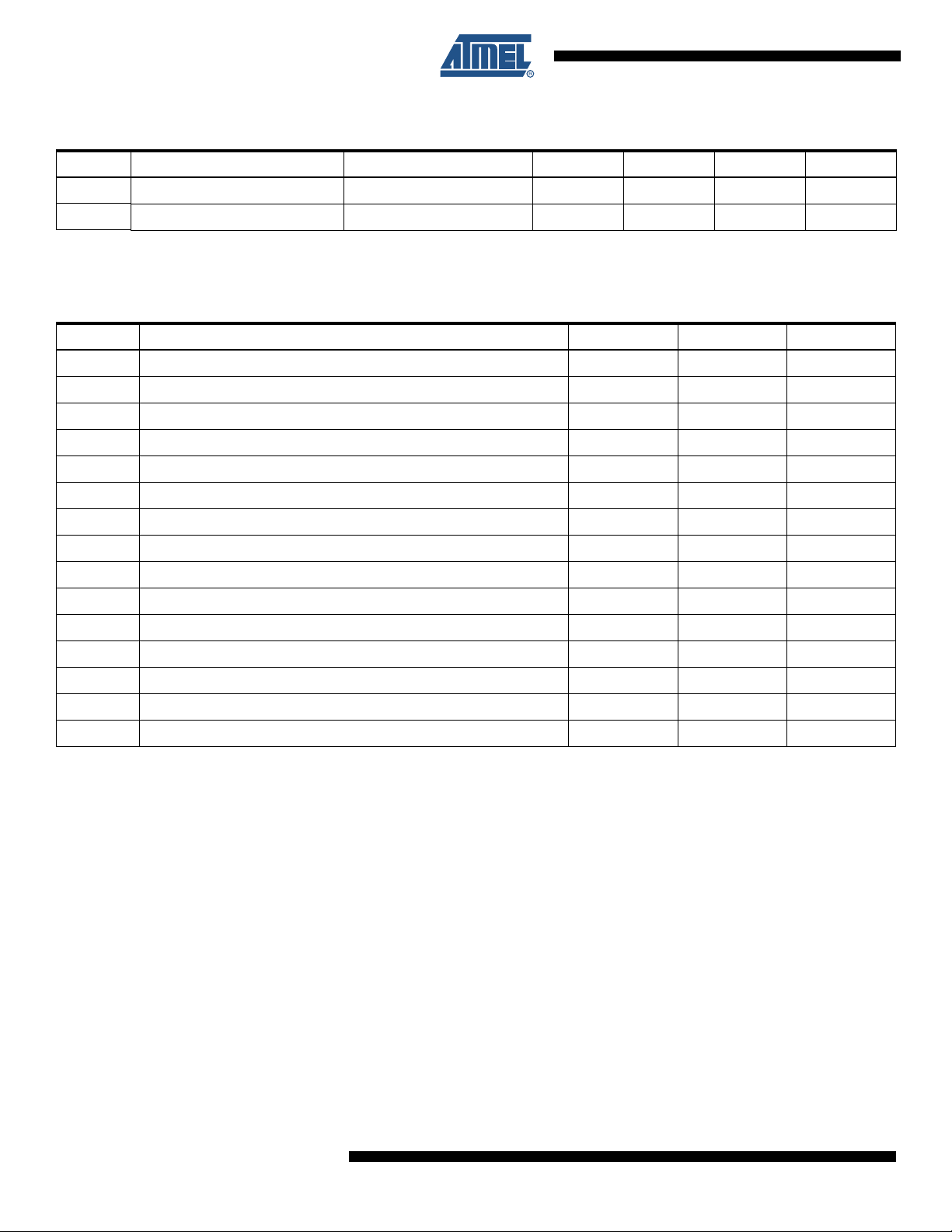
Table 7-1. DC Characteristics (Continued)
Applicable over recommended operating range from VCC = +2.7 to 3.6V, T
= -40⋅C to +85⋅C (unless otherwise noted)
AC
Symbol Parameter Test Condition Min Typ Max Units
I
OH
I
OL
Note: 1. To prevent Latch Up Conditions from occurring during Power Up of the AT88SC0808CA, V
SDA/IO Output High Current VOH 20 uA
SDA/IO Output Low Current VOL 10 mA
must be turned on before
applying V
. For Powering Down, VIH must be removed before turning VCC off.
IH
CC
Table 7-2. AC Characteristics
Applicable over recommended operating range from VCC = +2.7 to 3.6V, TAC = -40°C to +85°C, CL = 30pF (unless otherwise noted)
Parameter Min Max Units
f
Async Clock Frequency 1 4 MHz
CLK
Synch Clock Frequency 0 1 MHz
f
CLK
Clock Duty cycle 40 60 %
tR “Rise Time - SDA/IO, RST” 1 uS
t
F
t
Rise Time - SCL/CLK 9% x period uS
R
t
F
t
AA
t
HD.STA
t
SU.STA
t
HD.DAT
t
SU.DAT
t
SU.STO
t
DH
t
WR
“Fall Time - SDA/IO, RST” 1 uS
Fall Time - SCL/CLK 9% x period uS
Clock Low to Data Out Valid 250 nS
Start Hold Time 200 nS
Start Set-up Time 200 nS
Data In Hold Time 10 nS
Data In Set-up Time 100 nS
Stop Set-up Time 200 nS
Data Out Hold Time 20 nS
Write Cycle Time 5mS
6
AT88SC0808CA
5204BS–CRYPT–2/09
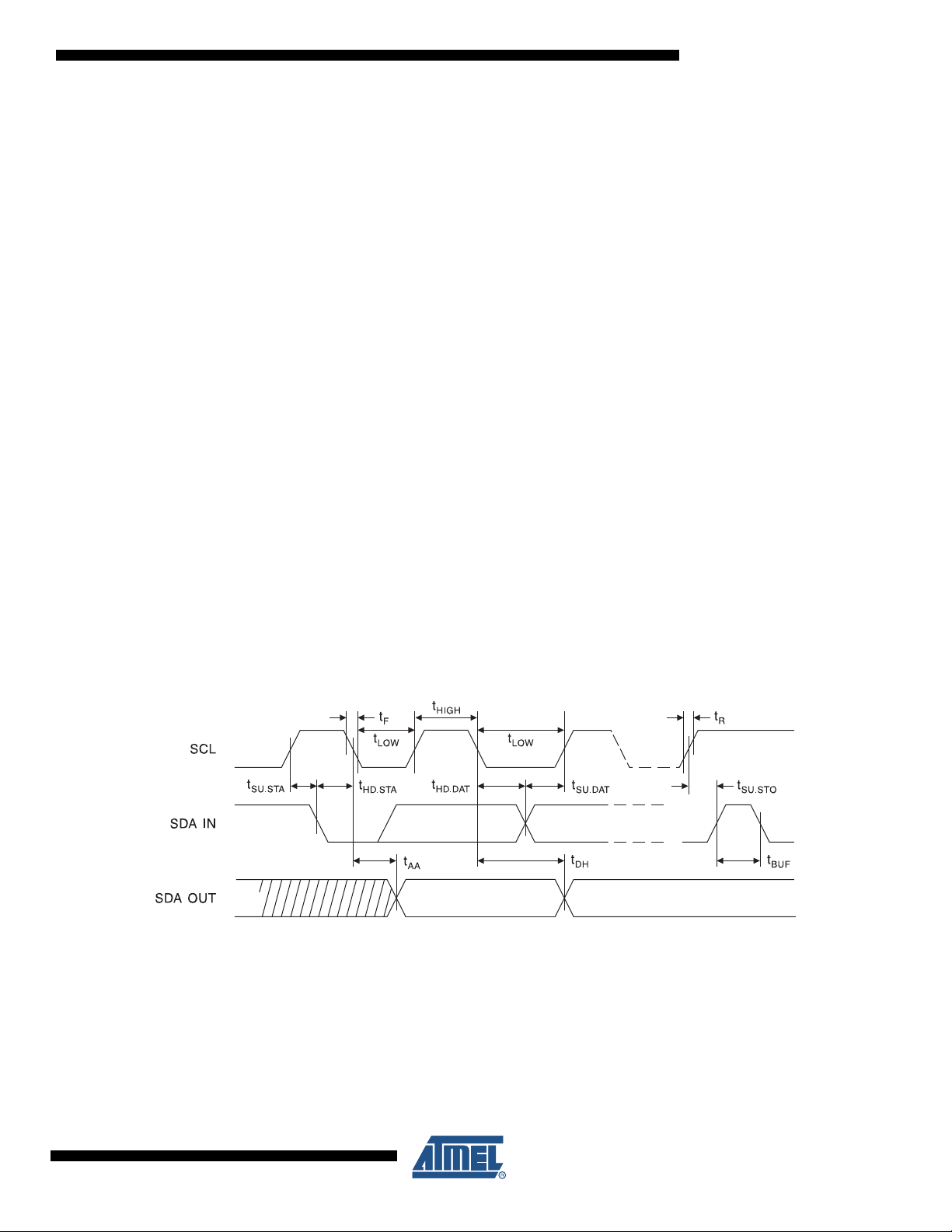
8. Device Operations for Synchronous Protocols
8.1 Clock and Data Transitions
The SDA pin is normally pulled high with an external device. Data on the SDA pin may change
only during SCL low time periods (see Figure 8-3 on page 8). Data changes during SCL high
periods will indicate a start or stop condition as defined below.
8.1.1 Start Condition
A high-to-low transition of SDA with SCL high defines a START condition which must precede all
commands (see Figure 8-4 on page 8).
8.1.2 Stop Condition
A low-to-high transition of SDA with SCL high defines a STOP condition. After a read sequence,
the STOP condition will place the EEPROM in a standby power mode (see Figure 8-4 on page
8).
8.1.3 ACKNOWLEDGE
All addresses and data words are serially transmitted to and from the EEPROM in 8-bit words.
The EEPROM sends a zero to acknowledge that it has received each word. This happens during the ninth clock cycle (see Figure 8-5 on page 9).
AT88SC0808CA
8.2 Memory Reset
After an interruption in communication due protocol errors, power loss or any reason, perform
"Acknowledge Polling" to properly recover from the condition. Acknowledge polling consists of
sending a start condition followed by a valid CryptoMemory command byte and determining if
the device responded with an ACKNOWLEDGE.
Figure 8-1. Bus Time for 2-Wire Serial Communications. SCL: Serial Clock, SDA: Serial Data I/O
5204BS–CRYPT–2/09
7

Figure 8-2. Write Cycle Timing. SCL: Serial Clock, SDA: Serial Data I/O
CONDITION
S
S
DATA
CHANGE
ALLOWED
CL
DA
WORDn
Figure 8-3. Data Validity
8th BIT
Note: The Write Cycle time twr is the time from a valid stop condition of a write sequence to the end of
the internal clear/write cycle.
ACK
STOP
(1)
t
WR
START
CONDITION
Figure 8-4. START and STOP Definitions
8
AT88SC0808CA
5204BS–CRYPT–2/09

Figure 8-5. Output Acknowledge
AT88SC0808CA
5204BS–CRYPT–2/09
9

9. Device Architecture
9.1 User Zones
The EEPROM user memory is divided into 8 zones of 1 Kbits each. Multiple zones allow for storage of different types of data or files in different zones. Access to user zones is permitted only
after meeting proper security requirements. These security requirements are user definable in
the configuration memory during device personalization. If the same security requirements are
selected for multiple zones, then these zones may effectively be accessed as one larger zone.
Figure 9-1. User Zone
ZONE $0 $1 $2 $3 $4 $5 $6 $7
$00
User 0
User 1 $00
--
-
--
User 6 $78
User 7
- 128 Bytes
-
$78
$00
- 128 Bytes
-
$78
10
AT88SC0808CA
5204BS–CRYPT–2/09

AT88SC0808CA
10. Control Logic
Access to the user zones occur only through the control logic built into the device. This logic is
configurable through access registers, key registers and keys programmed into the configuration
memory during device personalization. Also implemented in the control logic is a cryptographic
engine for performing the various higher-level security functions of the device.
11. Configuration Memory
The configuration memory consists of 2048 bits of EEPROM memory used for storage of passwords, keys, codes, and also used for definition of security access rights for the user zones.
Access rights to the configuration memory are defined in the control logic and are not alterable
by the user after completion of personalization.
Figure 11-1. Configuration Memory
$0 $1 $2 $3 $4 $5 $6 $7
$00 Answer To Reset
$08 Fab Code MTZ Card Manufacturer Code
$10 Lot History Code Read Only
$18 DCR Identification Number Nc
$20 AR0 PR0 AR1 PR1 AR2 PR2 AR3 PR3
$28 AR4 PR4 AR5 PR5 AR6 PR6 AR7 PR7
$30
$38
$40
$48
$50
$58
$60
$68
$70
$78
$80
$88
$90
$98
$A0
$A8
$B0 PAC Write 0 PAC Read 0
$B8 PAC Write 1 PAC Read 1
$C0 PAC Write 2 PAC Read 2
$C8 PAC Write 3 PAC Read 3
$D0 PAC Write 4 PAC Read 4
$D8 PAC Write 5 PAC Read 5
$E0 PAC Write 6 PAC Read 6
$E8 PAC Write 7 PAC Read 7
$F0
$F8
For Authentication and Encryption use Cryptography
For Authentication and Encryption use Secret
Reserved
Issuer Code
Reserved Forbidden
Identification
Access Control
Password
5204BS–CRYPT–2/09
11

11.1 Security Fuses
There are three fuses on the device that must be blown during the device personalization process. Each fuse locks certain portions of the configuration zone as OTP (One-Time
Programmable) memory. Fuses are designed for the module manufacturer, card manufacturer
and card issuer and should be blown in sequence, although all programming of the device and
blowing of the fuses may be performed at one final step.
12. Communication Security Modes
Communications between the device and host operate in three basic modes. Standard mode is
the default mode for the device after power-up. Authentication mode is activated by a successful
authentication sequence. Encryption mode is activated by a successful encryption activation following a successful authentication.
Table 12-1. Communication Security Modes
Mode Configuration Data User Data Passwords Data Integrity Check
Standard Clear Clear Clear MDC
Authentication Clear Clear Encrypted MAC
Encryption Clear Encrypted Encrypted MAC
Note: 1. Configuration data include viewable areas of the Configuration Zone except the passwords:
MDC: Modification Detection Code.
MAC: Message Authentication Code.
(1)
13. Security Options
13.1 Anti-Tearing
In the event of a power loss during a write cycle, the integrity of the device’s stored data is recoverable. This function is optional: the host may choose to activate the anti-tearing function,
depending on application requirements. When anti-tearing is active, write commands take longer
to execute, since more write cycles are required to complete them, and data is limited to a maximum of eight bytes for each write request.
Data is written first into a buffer zone in EEPROM instead of the intended destination address,
but with the same access conditions. The data is then written in the required location. If this second write cycle is interrupted due to a power loss, the device will automatically recover the data
from the system buffer zone at the next power-up. Non-volatile buffering of the data is done
automatically by the device.
12
During power-up in applications using Anti-Tearing, the host is required to perform ACK polling
in the event that the device needs to carry out the data recovery process.
AT88SC0808CA
5204BS–CRYPT–2/09

AT88SC0808CA
13.2 Write Lock
If a user zone is configured in the write lock mode, the lowest address byte of an 8-byte page
constitutes a write access byte for the bytes of that page. For example, the write lock byte at
$080 controls the bytes from $081 to $087.
Table 13-1. Write Lock Example
Address $0 $1 $2 $3 $4 $5 $6 $7
$080 11011001 xxxx xxxx xxxx xxxx xxxx xxxx xxxx xxxx xxxx xxxx xxxx xxxx xxxx xxxx
locked locked locked
The Write-Lock byte itself may be locked by writing its least significant (rightmost) bit to “0”.
Moreover, when write lock mode is activated, the write lock byte can only be programmed – that
is, bits written to “0” cannot return to “1”.
In the write lock configuration, write operations are limited to writing only one byte at a time.
Attempts to write more than one byte will result in writing of just the first byte into the device.
13.3 Password Verification
Passwords may be used to protect READ and/or WRITE access of any user zone. When a valid
password is presented, it is memorized and active until power is turned off, unless a new password is presented or RST becomes active. There are eight password sets that may be used to
protect any user zone. Only one password is active at a time.
Presenting the correct WRITE password also grants READ access privileges.
13.4 Authentication Protocol
The access to a user zone may be protected by an authentication protocol. Any one of four keys
may be selected to use with a user zone.
Authentication success is memorized and active as long as the chip is powered, unless a new
authentication is initialized or RST becomes active. If the new authentication request is not validated, the card loses its previous authentication which must be presented again to gain access.
Only the latest request is memorized.
5204BS–CRYPT–2/09
13

Figure 13-1. Password and Authentication Operations
CS
VERIFY CS
Write DATA
VERIFY RPW
DATA
Checksum (CS) VERIFY CS
Note: Authentication and password verification may be attempted at any time and in any order. Exceeding corresponding authentica-
tion or password attempts trial limit renders subsequent authentication or password verification attempts futile.
13.5 Cryptographic Message Authentication Codes
AT88SC0808CA implements a data validity check function in the standard, authentication or
encryption modes of operation.
In the standard mode, data validity check is done through a Modification Detection Code (MDC),
in which the host may read an MDC from the device in order to verify that the data sent was
received correctly.
In authentication and encryption modes, the data validity check becomes more powerful since it
provides a bidirectional data integrity check and data origin authentication capability in the form
of a Message Authentication Codes (MAC). Only the host/device that carried out a valid authentication is capable of computing a valid MAC. While operating in the authentication or encryption
modes, the use of MAC is required. For an ingoing command, if the device calculates a MAC different from the MAC transmitted by the host, not only is the command abandoned but the
security privilege is revoked. A new authentication and/or encryption activation will be required
to reactivate the MAC.
14
AT88SC0808CA
5204BS–CRYPT–2/09

13.6 Encryption
The data exchanged between the device and the host during read, write and verify password
commands may be encrypted to ensure data confidentiality.
The issuer may choose to require encryption for a user zone by settings made in the configuration memory. Any one of four keys may be selected for use with a user zone. In this case,
activation of the encryption mode is required in order to read/write data in the zone and only
encrypted data will be transmitted. Even if not required, the host may still elect to activate
encryption provided the proper keys are known.
13.7 Supervisor Mode
Enabling this feature allows the holder of one specific password to gain full access to all eight
password sets, including the ability to change passwords.
13.8 Modify Forbidden
No write access is allowed in a user zone protected with this feature at any time. The user zone
must be written during device personalization prior to blowing the security fuses.
AT88SC0808CA
13.9 Program Only
For a user zones protected by this feature, data can only be programmed (bits change from a “1”
to a “0”), but not erased (bits change from a “0” to a “1”).
14. Protocol Selection
The AT88SC0808CA supports two different communication protocols.
Smartcard Applications:
Smartcard applications use ISO 7816-B protocol in asynchronous T = 0 mode for compatibility
and interoperability with industry standard smartcard readers.
Embedded Applications:
A 2-wire serial interface provides fast and efficient connectivity with other logic devices or microcontrollers.
The power-up sequence determines establishes the communication protocol for use within that
power cycle. Protocol selection is allowed only during power-up.
14.1 Synchronous 2-Wire Serial Interface
The synchronous mode is the default mode after power up. This is due to the presence of an
internal pull-up on RST. For embedded applications using CryptoMemory in standard plastic
packages, this is the only available communication protocol.
5204BS–CRYPT–2/09
Power-up VCC, RST goes high also.
After stable VCC, SCL(CLK) and SDA(I/O) may be driven.
15

Once synchronous mode has been selected, it is not possible to switch to asynchronous mode
V
cc
I/O-SDA
RST
CLK-SCL
1
2
3
45
V
cc
I/O-SDA
RST
CLK-SCL
AT R
without first powering off the device.
Figure 14-1. Synchronous 2-Wire Protocol
Note: Five clock pulses must be sent before the first command is issued.
14.2 Asynchronous T = 0 Protocol
This power-up sequence complies to ISO 7816-3 for a cold reset in smart card applications.
VCC goes high; RST, I/O (SDA) and CLK (SCL) are low.
Set I/O (SDA) in receive mode.
Provide a clock signal to CLK (SCL).
RST goes high after 400 clock cycles.
The device will respond with a 64-bit ATR code, including historical bytes to indicate the memory
density within the CryptoMemory family.
Once asynchronous mode has been selected, it is not possible to switch to synchronous mode
without first powering off the device.
Figure 14-2. Asynchronous T = 0 Protocol (Gemplus Patent)
15. Initial Device Programming
Enabling the security features of CryptoMemory requires prior personalization. Personalization
entails setting up of desired access rights by zones, passwords and key values, programming
these values into the configuration memory with verification using simple WRITE and READ
commands, and then blowing fuses to lock this information in place.
16
Gaining access to the configuration memory requires successful presentation of a secure (or
transport) code. The initial signature of the secure (transport) code for the AT88SC0808CA
AT88SC0808CA
5204BS–CRYPT–2/09

AT88SC0808CA
device is $22 E8 3F. This is the same as the WRITE 7 password. The user may elect to change
the signature of the secure code anytime after successful presentation.
After writing and verifying data in the configuration memory, the security fuses MUST be blown
to lock this information in the device. For additional information on personalizing CryptoMemory,
please see the application notes Programming CryptoMemory for Embedded Applications and
Initializing CryptoMemory for Smart Card Applications from the product page at
www.atmel.com/products/securemem.
16. Ordering Information
Ordering Code Package Voltage Range Temperature Range
AT88SC0808CA-MJ
AT88SC0808CA-MP
AT88SC0808CA-PU
AT88SC0808CA-SU
AT88SC0808CA-TU
M2 – J Module
M2 – P Module
8P3
8S1
8A2
2.7V–3.6V Commercial (0°C to 70°C)
2.7V–3.6V
Green compliant (exceeds RoHS)/Industrial
(−40°C to 85°C)
AT88SC0808CA-WI 7 mil wafer 2.7V–3.6V Industrial (−40°C to 85°C)
Package Type
M2 – J Module M2 ISO 7816 Smart Card Module
M2 – P Module M2 ISO 7816 Smart Card Module with Atmel® Logo
8P3 8-lead, 0.300” Wide, Plastic Dual Inline Package (PDIP)
8S1 8-lead, 0.150” Wide, Plastic Gull Wing Small Outline Package (JEDEC SOIC)
8A2 8-lead, 4.4mm Body, Plastic Thin Shrink Small Outline Package (TSSOP)
Note: Formal drawings may be obtained from an Atmel sales office.
(1)
Description
5204BS–CRYPT–2/09
17

17. Packaging Information
Module Size: M2
Dimension*: 12.6 x 11.4 [mm]
Glob Top: Square - 8.8 x 8.8 [mm]
Thickness: 0.58 [mm]
Pitch: 14.25 mm
Ordering Code: MP
Module Size: M2
Dimension*: 12.6 x 11.4 [mm]
Glob Top: Round - 8.5 [mm]
Thickness: 0.58 [mm]
Pitch: 14.25 mm
∅
Ordering Code: MJ
*Note: The module dimensions listed refer to the dimensions of the exposed metal contact area. The actual dimensions
of the module after excise or punching from the carrier tape are generally 0.4 mm greater in both directions
(i.e., a punched M2 module will yield 13.0 x 11.8 mm).
Module Size: M2
Dimension*: 12.6 x 11.4 [mm]
Glob Top: Square - 8.8 x 8.8 [mm]
Thickness: 0.58 [mm]
Pitch: 14.25 mm
Ordering Code: MP
Module Size: M2
Dimension*: 12.6 x 11.4 [mm]
Glob Top: Round - 8.5 [mm]
Thickness: 0.58 [mm]
Pitch: 14.25 mm
∅
Ordering Code: MJ
*Note: The module dimensions listed refer to the dimensions of the exposed metal contact area. The actual dimensions
of the module after excise or punching from the carrier tape are generally 0.4 mm greater in both directions
(i.e., a punched M2 module will yield 13.0 x 11.8 mm).
Note: The module dimensions listed refer to the dimensions of the exposed metal contact area. The actual dimensions of the module
after excise or punching from the carrier tape are generally 0.4 mm greater in both directions (i.e., a punched M2 module will
yield 13.0 x 11.8 mm).
18
AT88SC0808CA
5204BS–CRYPT–2/09

18. Ordering Code: SU
1150 E. Cheyenne Mtn. Blvd.
Colorado Springs, CO 80906
TITLE
DRAWING NO.
R
REV.
Note:
3/17/05
8S1, 8-lead (0.150" Wide Body), Plastic Gull Wing
Small Outline (JEDEC SOIC)
8S1 C
COMMON DIMENSIONS
(Unit of Measure = mm)
SYMBOL
MIN
NOM
MAX
NOTE
A1 0.10 – 0.25
These drawings are for general information only. Refer to JEDEC Drawing MS-012, Variation AA for proper dimensions, tolerances, datums, etc.
A 1.35 – 1.75
b 0.31 – 0.51
C 0.17 – 0.25
D 4.80 – 5.05
E1 3.81 – 3.99
E 5.79 – 6.20
e 1.27 BSC
L 0.40 – 1.27
θ 0° – 8°
ØØ
EE
11
NN
TOP VIEWTOP VIEW
CC
E1E1
END VIEW
AA
bb
LL
A1A1
ee
DD
SIDE VIEWSIDE VIEW
18.1 8-lead SOIC
AT88SC0808CA
5204BS–CRYPT–2/09
19

19. Ordering Code: PU
2325 Orchard Parkway
San Jose, CA 95131
TITLE
DRAWING NO.
R
REV.
8P3, 8-lead, 0.300" Wide Body, Plastic Dual
In-line Package (PDIP)
01/09/02
8P3
B
Notes: 1. This drawing is for general information only; refer to JEDEC Drawing MS-001, Variation BA for additional information.
2. Dimensions A and L are measured with the package seated in JEDEC seating plane Gauge GS-3.
3. D, D1 and E1 dimensions do not include mold Flash or protrusions. Mold Flash or protrusions shall not exceed 0.010 inch.
4. E and eA measured with the leads constrained to be perpendicular to datum.
5. Pointed or rounded lead tips are preferred to ease insertion.
6. b2 and b3 maximum dimensions do not include Dambar protrusions. Dambar protrusions shall not exceed 0.010 (0.25 mm).
COMMON DIMENSIONS
(Unit of Measure = inches)
SYMBOL
MIN
NOM
MAX
NOTE
D
D1
E
E1
e
L
b2
b
A2 A
1
N
eA
c
b3
4 PLCS
A 0.210 2
A2 0.115 0.130 0.195
b 0.014 0.018 0.022 5
b2 0.045 0.060 0.070 6
b3 0.030 0.039 0.045 6
c 0.008 0.010 0.014
D 0.355 0.365 0.400 3
D1 0.005 3
E 0.300 0.310 0.325 4
E1 0.240 0.250 0.280 3
e 0.100 BSC
eA 0.300 BSC 4
L 0.115 0.130 0.150 2
Top View
Side View
End View
19.1 8-lead PDIP
20
AT88SC0808CA
5204BS–CRYPT–2/09

19.2 8-lead TSSOP
AT88SC0808CA
5204BS–CRYPT–2/09
21

20. Revision History
Table 20-1. Revision History
Doc. Rev. Date Comments
5204BS 2/2009 Connection Diagram inserted; DC Characteristics table updated.
5204AS 7/2008 Initial document release.
22
AT88SC0808CA
5204BS–CRYPT–2/09
 Loading...
Loading...