Page 1
Wireless
Broadband
Router
Model #: MI424-WR
Firmware Version: 4.0.16.1.45.120
User Manual
Ver 1.1
Solutions for the Digital Life
™
Page 2

Table of Contents
1 Introduction 1
Package Contents 1
Minimum System Requirements 2
Features 2
Getting to Know the Router 4
2 Connecting the Router 9
Setting Up the Router 9
Computer Network Configuration 13
Home Page 15
3 Configuring My Network Settings 17
Accessing My Network 17
Using My Network 18
4 Creating a Wireless Network 27
Overview 27
Wireless Status 28
Basic Security Settings 30
Advanced Security Settings 32
Configuring a Wireless Windows XP Client 40
Connecting a Wireless Windows XP Client 42
5 Using Network Connections 47
Network (Home/Office) 48
Ethernet Connection 53
Coax Connection 56
Broadband Ethernet Connection 59
Coax Broadband Connection 64
WAN PPPoE/WAN PPPoE 2 69
6 Configuring the Router’s Security 75
General 77
Access Control 79
Port Forwarding 82
DMZ (Demilitarized Zone) Host 83
Port Triggering 84
Remote Administration 86
Website Blocking 88
Static NAT 90
Advanced Filtering 91
Security Log 94
i
Page 3

Actiontec Wireless Broadband Router User Manual
iii
Table of Contents
7 Using Parental Controls 101
Activating Parental Controls 101
Creating a Filtering Policy 102
Advanced Options 106
Statistics 107
8 Using Advanced Settings 109
Firmware Upgrade 111
Firmware Restore 113
Configuration File 114
System Settings 115
Date and Time 120
Scheduler Rules 121
Routing 123
IP Address Distribution 125
Diagnostics 129
Restoring Default Settings 130
Reboot the Router 130
MAC Cloning 131
ARP (Address Resolution Protocol) Table 131
Users 132
QoS 133
Local Administration 133
Remote Administration 134
Dynamic DNS 134
DNS Server 136
Network Objects 138
Universal Plug and Play (UPnP) 139
Protocols 141
9 Monitoring the Router 143
Router Status 143
System Log 144
Connection Monitoring 145
Traffic Monitoring 146
10 Troubleshooting 147
A Quality of Service 151
Traffic Priority 151
Traffic Shaping 155
ii
ii
Page 4

Table of Contents
B Specifications 167
General 167
Wireless Operating Range 168
LED Indicators 168
Environmental 168
Notices 169
Regulatory Compliance Notices 169
Modifications 169
Limited Warranty 171
iii
Page 5

Actiontec Wireless Broadband Router User Manual
This page left intentionally blank.
iv
Page 6

Introduction
1
Thank you for purchasing the Actiontec Wireless Broadband Router. The Wireless
Broadband Router supports Multimedia over Coax Alliance (MoCA), a new net-
working standard that allows digital entertainment and information to be transmitted and distributed to multiple devices over coaxial cables. The Router also supports Ethernet and Wi-Fi networking, making it the most versatile router available.
If you want to take your home or office networking to the next level, the Actiontec
Wireless Broadband Router is sure to be one of the keys to your success.
Package Contents
s Actiontec Wireless Broadband Router
s Black Power cord
s Yellow cable (Ethernet, 6 ft.)
s White cable (Ethernet, 10 ft.)
s Quick Start Guide
s Installation Guide
s User Manual CD
s Wireless Networking Guide
1
Page 7
Actiontec Wireless Broadband Router User Manual
3
Chapter 1 Introduction
s Wall-mount template
s Vertical stand
s Warranty
Minimum System Requirements
s Computer with Ethernet capability
s Microsoft Windows 98SE, Me, 2000, or XP; Mac OS 9 or greater; Linux/
BSD, Unix
s Internet Explorer 5.0 or higher; Netscape Navigator 7.0 or higher
s TCP/IP network protocol installed on each computer
Features
s Supports multiple networking standards, including:
WAN - Ethernet and MoCA interfaces
LAN - 802.11g, 802.11b, Ethernet, and MoCA
s Integrated wired networking with 4-port 10/100 Mbps Ethernet switch
and MoCA
s Integrated wireless networking with 802.11g access point featuring:
802.11g enabled to support speeds up to 54 Mbps wirelessly
802.11b backward compatible, communicating with 802.11b wireless
products at speeds up to 11 Mbps
s Enterprise-level security, including :
Fully customizable firewall with Stateful Packet Inspection
Content filtering with URL-keyword based filtering, parental control,
customizable filtering policies per computer, and E-mail notification
Denial of service protection against IP spoofing attacks, intrusion and
scanning attacks, IP fragment overlap, ping of death, and fragmentation
attacks
Event logging
2
Page 8
Chapter 1 Introduction
Intrusion detection
MAC address filtering
NAT
DMZ hosting
Access control
Advanced wireless protection featuring WPA, WEP 64/128 bit encryp-
tion, 802.1x authentication, and MAC address filtering
ICSA certified
s Other Features
DHCP server option
DHCP server/PPPoE server auto-detection
DNS server
LAN IP and WAN IP address selection
MAC address cloning
Port forwarding
PPPoE support
QoS support (end to end layer 2/3) featuring Diffserv, 802.1p/q prioritization, configurable upstream/downstream traffic shaping, random early
detection and pass-through of WAN-side DSCPs, PHBs, and queuing to
LAN-side devices
Remote management and secured remote management using HTTPS
Reverse NAT
Static NAT
Static routing
Time zone support
VLAN multicast support
VPN IPSec (VPN passthrough only)
3
Page 9
Actiontec Wireless Broadband Router User Manual
5
Chapter 1 Introduction
1
2
3
4
MI424WR
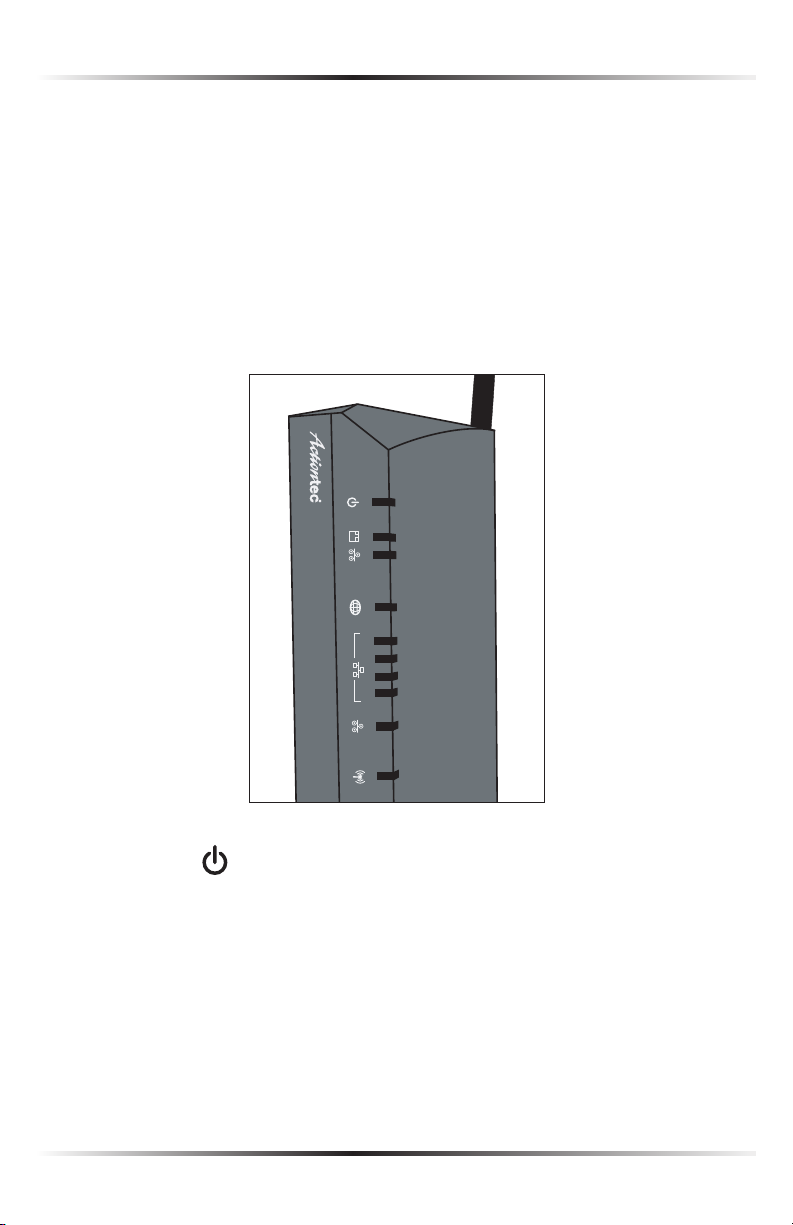
Getting to Know the Router
This section contains a quick description of the Router’s lights (LEDs), ports, etc.
The Router features several indicator lights on its front panel, and a series of ports
and switches on its rear panel.
Front Panel
The front panel of the Router features ten indicator lights: Power, Ethernet WAN,
Coax WAN, Internet, Ethernet LAN (4), Coax LAN, and Wireless.
Power Light
The Power light displays the Router’s current status. If the Power light glows
steadily green, the Router is receiving power and fully operational. When the
Power light flashes rapidly, the Router is initializing. If the Power light is not illuminated or glows red when the Power cord is plugged in and the Power switch is
turned on, the Router has suffered a critical error and technical support should
be contacted.
4
Page 10
Chapter 1 Introduction
Ethernet WAN Light
The Ethernet WAN light illuminates when the Router is connected to the
Internet via Ethernet. If flashing, data traffic is passing across the port.
Coax WAN Light
The Coax WAN light glows steadily or flashes when the Router is connected to
the Internet via coaxial cable.
Internet Light
When the Internet light glows steadily green, the Router is connected to the ISP
(Internet Service Provider). If it glows amber, there is a physical connection to
the ONT (Optical Network Terminator), but authentication has not taken place
(i.e., no IP address is present).
Ethernet LAN Lights (1, 2, 3, 4)
The Ethernet LAN lights illuminate when the Router is connected to a local
network via one or more of its Ethernet ports. If flashing, data traffic is passing
across the port(s).
Coax LAN Light
The Coax LAN light glows steadily or flashes when the Router is connected to a
local network via its Coax port.
Wireless Light
The Wireless light illuminates when the Router’s wireless access point is turned
on. If flashing, data traffic is passing across the wireless connection.
5
Page 11
Actiontec Wireless Broadband Router User Manual
7
Chapter 1 Introduction
1
Reset
2
3
4
1
00
1
00
Coax
ResetReset
On/Of
f
5VDC 3A
100
1
00
1
0
1
0
10
10
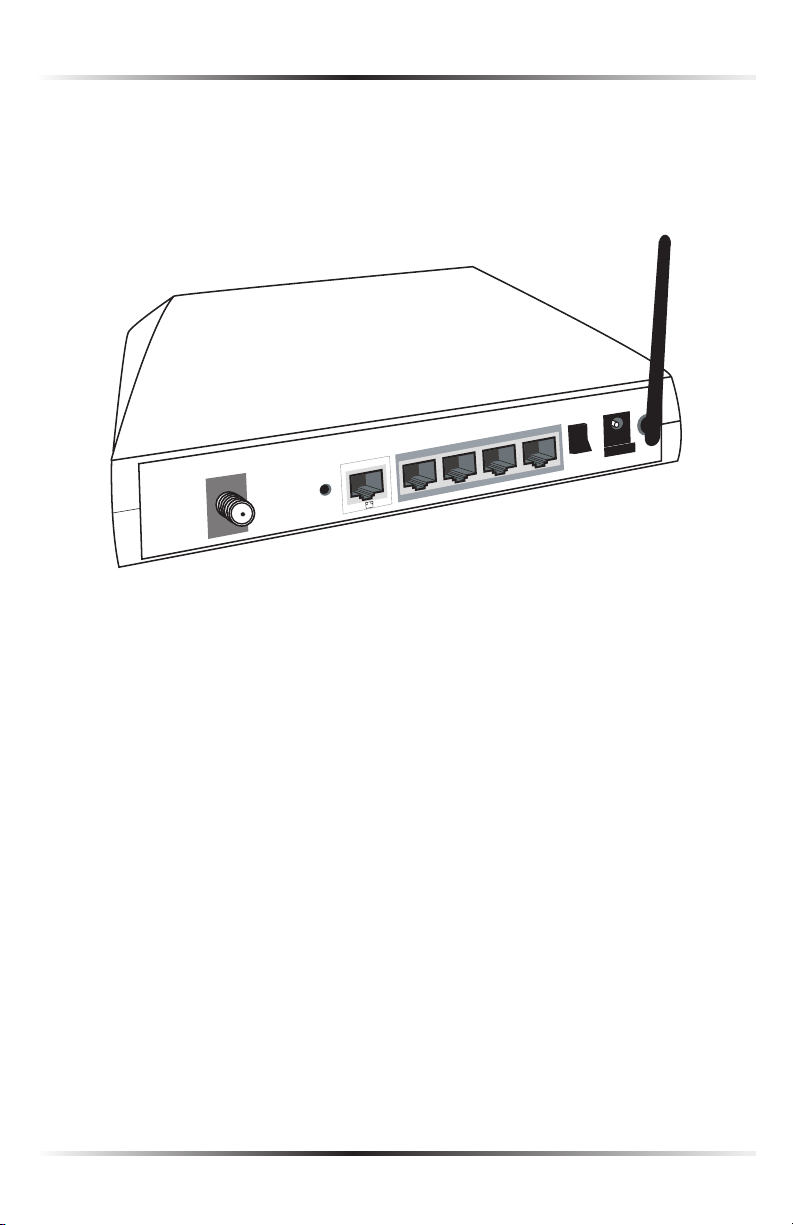
Rear Panel
The rear panel of the Router features seven ports (Coax, Ethernet WAN, Ethernet
LAN [4], and Power), as well as a Reset button and Power switch.
Coax Port
The Coax port connects the Router to the ISP or other devices using a coaxial
cable.
Reset Button
To restore the Router’s factory default settings, press and hold the Reset button
for approximately ten seconds. The reset process will start about ten seconds
after releasing the button. When the Router resets, all the lights on the front
panel turn off, and then some of the lights start flashing. The Router has completed its reset process when the Power light glows steadily green.
Caution: Do not unplug the Power cord from the Router dur-
M
ing the reset process. Doing so may result in the loss of the
Router’s configuration information. If this occurs, reset the
Router again.
6
Page 12

Chapter 1 Introduction
Ethernet WAN Port
The Ethernet WAN port connects the Router to the ISP using an Ethernet cable.
Ethernet LAN Ports (4)
The Ethernet LAN ports connect devices to the Router via Ethernet cables to cre-
ate a local area network (LAN). The Ethernet LAN ports are 10/100 Mbps auto-
sensing ports, and either a straight-through or crossover Ethernet cable can be
used when connecting devices to the ports.
Power Switch
The Power switch powers the Router on and off.
Power Port
The Power port connects the Router to an electrical wall outlet via the
Power cord.
7
Page 13

Actiontec Wireless Broadband Router User Manual
This page left intentionally blank.
8
Page 14
Connecting the Router
Connecting a computer or local network to the Wireless Broadband Router is a
simple procedure, varying slightly depending on the computer’s operating system
but designed to seamlessly integrate the Router with the computer or local network. Moreover, addition configuration to access the GUI is not required when tak-
ing advantage of Universal Plug-and-Play support in Windows XP.
The Windows default network settings dictate that in most cases, the setup procedure described in the “Computer Network Configuration” will be unnecessary.
For example, the default DHCP setting in Windows 2000 is “client,” requiring no
further modification.
However, Actiontec advises following the setup procedure described below to verify all
communication parameters are valid and the physical cable connections are correct.
Setting Up the Router
There are three parts to setting up the Router: Connecting the Cables, Configuring
the Router, and Connecting Other Computers/Set Top Boxes.
Connecting the Cables
Note: If a different router was being used, disconnect it. Remove
☞
all router components, including power supplies and cables,
since they will not work with the Wireless Broadband Router.
2
1. Get the Router and black Power cord from the box.
2. Plug the black Power cord in the black port on the back of the Router and
then into a power outlet.
3. Turn the Router on.
4. Make sure the Power light on the front of the Router is glows steadily green.
5. Plug the yellow Ethernet cable from the box into one of the four yellow
Ethernet ports on the back of the Router.
9
Page 15
Actiontec Wireless Broadband Router User Manual
11
Chapter 2 Connecting the Router
6. Make sure the computer is powered on, then plug the other end of the yellow
Ethernet cable into an Ethernet port on the computer.
7. Make sure at least one of the Ethernet LAN lights on the front of the Router
glows steadily green. This may take a few moments.
8. The phone company previously installed a high-speed wall jack somewhere in
the house. Locate it and note its type (Ethernet or coaxial). If Ethernet, follow
steps 8a and 8b. If coaxial, follow steps 9a and 9b. Then, continue to step 10.
a) If connecting via Ethernet, get the white Ethernet cable from the box and
plug one end in the white port on the back of the Router.
b) Plug the other end of the white Ethernet cable into the high-speed
Ethernet jack.
9. a) If connecting via coaxial cable, get a coaxial cable and connect one end to
the red Coax port on the back of the Router.
b) Connect the other end of the coaxial cable to a coax jack.
10. Make sure the Ethernet WAN light (if connecting via Ethernet) or Coax WAN
light (if connecting via coaxial cable) on the front of the Router glows steadily
green. If connecting via coaxial cable, this may take a few minutes.
Note: If the Ethernet WAN light or Coax WAN light does not
☞
illuminate, make sure the cable (Ethernet or coaxial) is connected properly at both ends.
Configuring the Router
1. Open a web browser on the computer connected to the Router. In the
“Address” text box, type:
http://192.168.1.1
then press Enter on the keyboard.
10
Page 16
Chapter 2 Connecting the Router
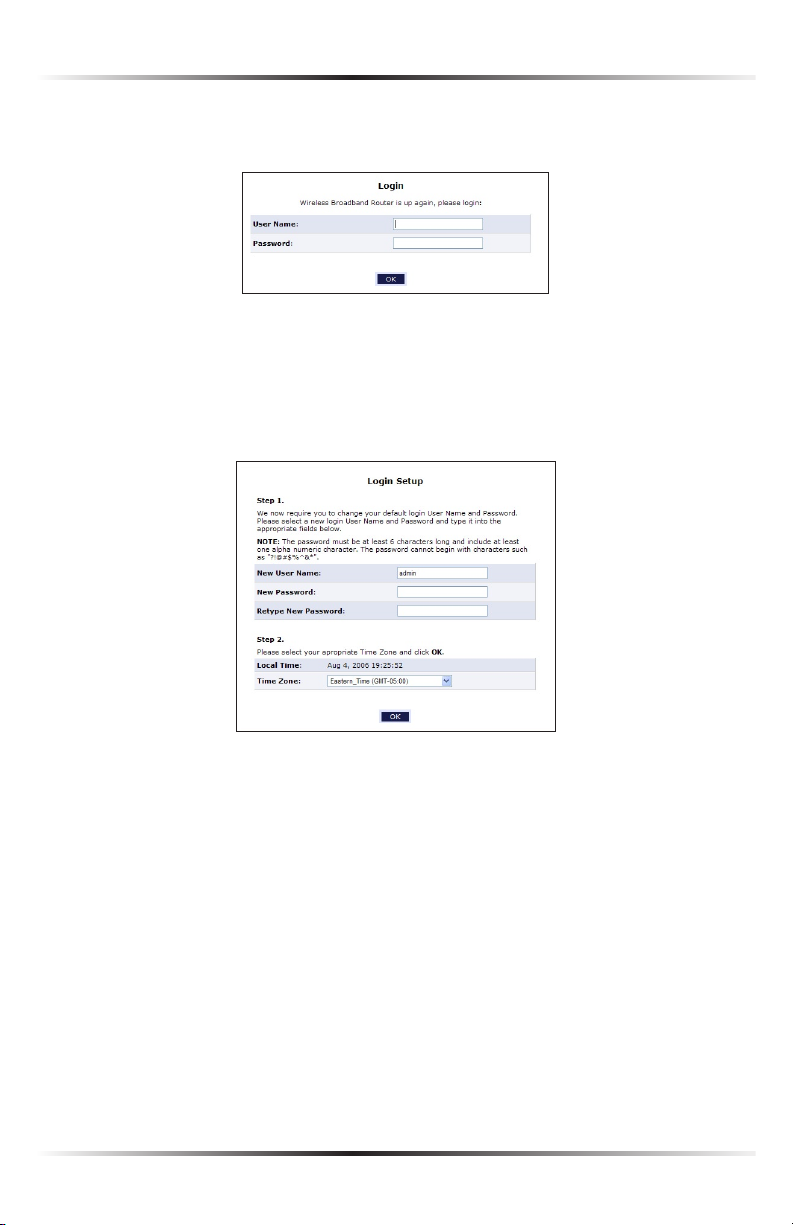
2. The “Login” screen appears. Enter the default user name (admin) and pass-
word (password) in the appropriate text boxes, then click OK.
3. The “Login Setup” screen appears. Select a new user name and password and
enter them in the appropriate text boxes (the password must be entered twice,
for validation purposes). Write the new user name and password down on a
piece of paper and keep it in a safe place, since they will be needed to access
the Router’s MegaControl Panel™ in the future.
4. In the bottom part of the screen, select the correct time zone from the “Time
Zone” drop-down list, then click OK at the bottom of the screen.
The Router is now configured.
11
Page 17

Actiontec Wireless Broadband Router User Manual
13
Chapter 2 Connecting the Router
Connecting Other Computers/Set Top Boxes
The Router can connect to other computers or set top boxes in three ways: via
Ethernet, via wireless connection, or via coaxial cable.
Ethernet
1. Get an Ethernet cable and plug one end into one of the open yellow
Ethernet ports on the back of the Router.
2. Plug the other end of the Ethernet cable into an Ethernet port on the computer.
3. Make sure the corresponding Ethernet LAN light on the front of the Router
glows steadily green.
4. Repeat these steps for each computer to be connected to the Router
via Ethernet.
Wireless
1. Make sure each computer to be connected wirelessly has built-in wireless or
an attached wireless adapter.
2. Make sure the computer uses the same ESSID and WEP key as the Router by
launching the computer’s wireless application
3. Enter the ESSID and WEP key found on the sticker on the bottom of the
Router in the computer’s wireless settings and click Save. Make sure to configure the computer to use 64/40-bit WEP encryption.
4. Make sure the changes were implemented by surfing the Internet from
the computer.
5. Repeat these steps for every other computer to be connected to the
Router wirelessly.
12
Page 18

Chapter 2 Connecting the Router
Coaxial
1. Make sure all set top boxes are turned off.
2. Disconnect any adapter currently connected to the coaxial jack in the room
where the Router is.
3. Connect one end of the coaxial cable to the coaxial wall jack, and the other
end to the red Coax port on the back of the Router.
4. Power up the set top box.
5. Make sure the Coax LAN light on the front of the Router glows steadily
green. This may take a few minutes. When it does, the set top box is connected to the Router.
Computer Network Conguration
Each network interface on the computer should either be configured with a statically defined IP address and DNS address, or instructed to automatically obtain an
IP address using the Network DHCP server. The Router is set up, by default, with an
active DHCP server, and Actiontec recommends leaving this setting as is.
Configuring Dynamic IP Addressing
To set up a computer to use dynamic IP addressing:
Windows XP
1. Select Network Connections in the Control Panel.
2. Right-click Ethernet Local Area Connection, then click Properties.
3. In the “General” tab, select Internet Protocol (TCP/IP), then click
Properties.
4. The “Internet Protocol (TCP/IP) Properties” window appears.
5. Click the “Obtain an IP address automatically” radio button.
6. Click the “Obtain DNS server address automatically” radio button.
7. Click OK in the “(TCP/IP) Properties” screen, then click OK in the “Local
Area Connection Properties” screen to save the settings.
13
Page 19
Actiontec Wireless Broadband Router User Manual
15
Chapter 2 Connecting the Router
Windows 2000
1. Select Network and Dialing Connections in the Control Panel.
2. Right-click on the Ethernet connection’s icon, then click Properties.
3. Select Internet Protocol (TCP/IP) component, then click Properties.
4. The “Internet Protocol (TCP/IP) Properties” window appears.
5. Click the “Obtain an IP address automatically” radio button.
6. Click the “Obtain DNS server address automatically” radio button.
Windows 98/Me
1. Select Network in the Control Panel.
2. Select the TCP/IP settings for the network card, then click Properties.
3. Click the “Obtain an IP address automatically” radio button in the “IP
Address” tab.
4. Click Disable DNS in the DNS configuration tab.
5. Click OK in the “TCP/IP Properties” screen.
6. Click OK in the “Network” screen to reboot and save the settings.
Windows NT
1. Click Network in the Control Panel. The “Network” window appears.
2. In the “Protocol” tab, select Internet Protocol (TCP/IP) then click
Properties.
3. In the “IP Address” tab, click the “Obtain an IP address automatically” radio
button.
4. In the “DNS” tab, verify no DNS server is defined in the “DNS Service Search
Order” text box and no suffix is defined in the “Domain Suffix Search
Order” text box.
14
Page 20
Chapter 2 Connecting the Router
Linux
1. Login into the system as a super-user, by entering “su” at the prompt.
2. Type “ifconfig” to display the network devices and allocated IPs.
3. Type “pump -i <dev>,” where <dev> is the network device name.
4. Type “ifconfig” again to view the newly allocated IP address.
5. Make sure no firewall is active on device <dev>.
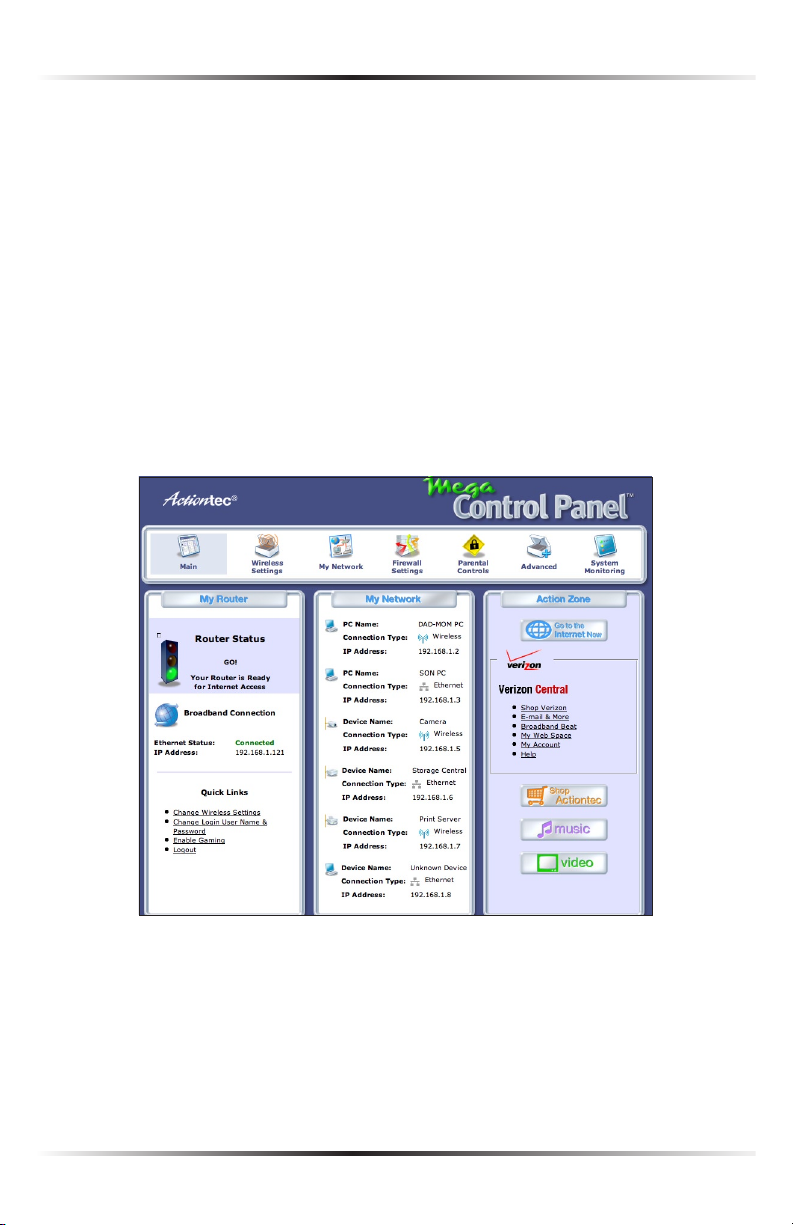
Home Page
After logging into the Router’s MegaControl Panel (see “Configuring the Router” at
the beginning of this chapter), the “Home” screen appears.
The Home screen has a “Main Menu” that occupies the top of the screen. Below
that, the screen is divided into three columns: “My Router,” “My Network,” and
“Action Zone.”
15
Page 21

Actiontec Wireless Broadband Router User Manual
Main Menu
The “Main Menu” contains links to all of the configuration options of the Router:
Wireless Setup (explained in chapter 4 of this manual), My Network (chapter 5),
Firewall (chapter 6), Parental Controls (chapter 7), Advanced (chapter 8), and
System Monitoring (chapter 9).
My Router
This section displays the status of the Router’s network and Internet connection.
A green light signifies the Router is connected; a yellow light means the Router is
attempting to connect; and a red light signifies the Router’s connection is down.
Broadband Connection
The “Broadband Connection” section of My Router displays the state of the
Router’s broadband connection (“Connected” or “Disconnected”) for the two
connection options (“Coax Status” and “Ethernet Status”), and the WAN IP
address of the broadband connection.
Quick Links
The “Quick Links” section of My Router contains a list of frequently accessed
settings, including “Change Wireless Settings,” “Change Login User Name &
Password,” “Enable Gaming,” and “Logout.”
My Network
The “My Network” section of the Home screen displays the connection type, name,
and IP address of all devices connected to the Router’s network. The icon associated
with the device will be displayed normally (signifying an active device) or shaded
(signifying the device has not been active for at least 60 seconds). The user can also
configure the basic settings of each device by clicking on its icon. These settings are
described in more detail in chapter 3, “Configuring My Network Settings.”
Action Zone
This section contains links to various Verizon Web sites, and other informational
links. Clicking on the icon above “Go to Internet Now” connects the user to the
home page configured on the user’s web browser.
16
Page 22
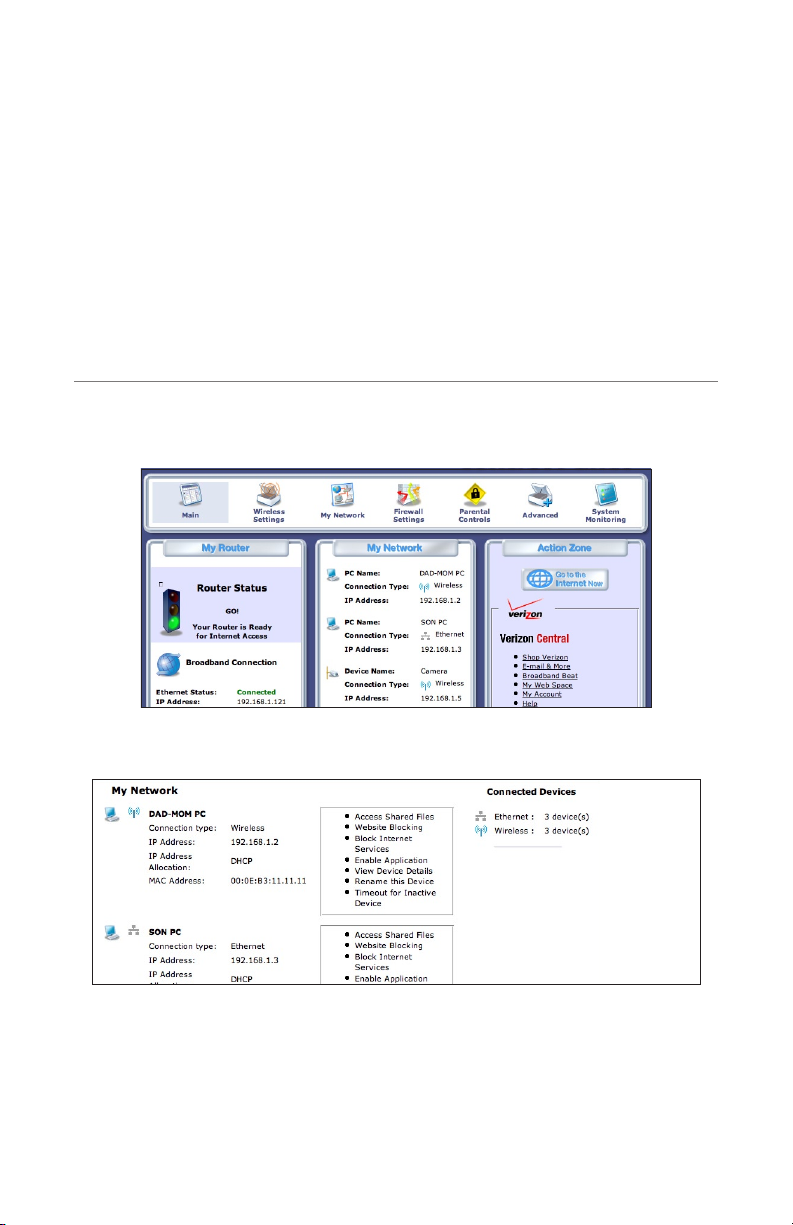
Configuring My Network Settings
Once the Wireless Broadband Router is physically connected and the MegaControl
Panel’s Home screen is displayed in a web browser, a list of the devices connected
to the Router’s network appears in the “My Network” section of the screen. From
here, some basic network settings can be configured.
Accessing My Network
To access My Network, click on the “My Network” icon in the Home screen.
The “My Network” screen appears:
3
On the far right side of the screen, in the “Connected Devices” section, is list of the
devices currently connected to the network, listed by connection type and number. The rest of the screen contains the “My Network” section, which displays each
device connected to the network, and a series of configuration settings.
17
Page 23

Actiontec Wireless Broadband Router User Manual
19
Chapter 3 Configuring My Network Settings
Using My Network
Various settings can be accessed for a particular device, as follows.
Access Device
For devices that can be accessed (such as Internet cameras and networked hard
drives), locate it in the My Network column, then click Access Devices to use the
device over the network.
Access Shared Files
To access the shared files on a particular device, locate the device in the My
Network column, then click Access Shared Files. A list of shared files appears on
the screen.
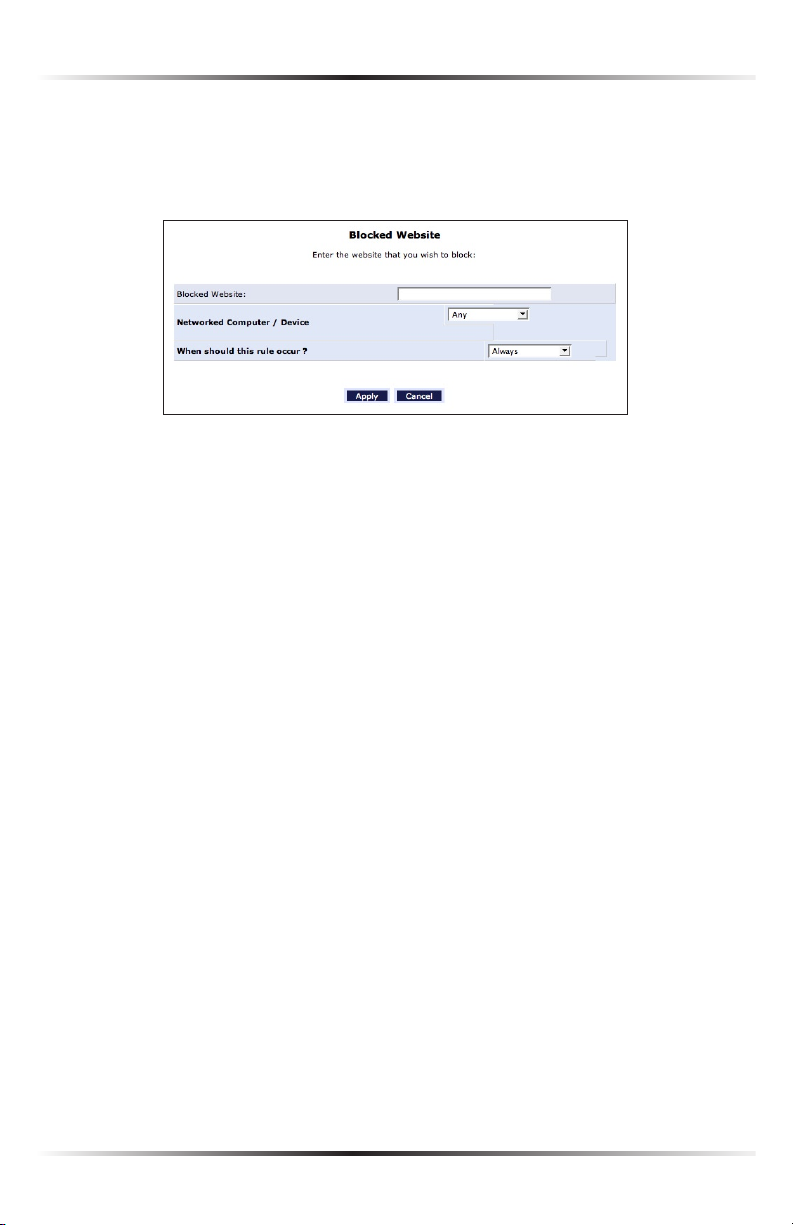
Website Blocking
Website blocking is used to prevent a device on the network from accessing particular websites on the Internet. To set up website blocking on a networked device,
locate the device in the My Network column, then click Website Blocking. The
“Website Blocking” screen appears.
1. Click in the “Enable Website Blocking” check box to enable web site blocking,
then click Add.
18
Page 24
Chapter 3 Configuring My Network Settings
2. The “Blocked Website” screen appears. Enter the website address (IP or URL)
to block on the network (all pages within the website will also be blocked). If
the website address has multiple IP addresses, the Router will resolve all additional addresses and automatically add them to the restrictions table.
3. To apply website blocking to a computer on the network, select it from the
“Networked Computer/Device” drop-down list.
4. If website blocking needs to be active all the time, select “Always” from the
“When should this rule occur?” drop-down list. If the rule will only be active at
certain times select “Specify Schedule” and click Add. Then, add a schedule rule
(for more details about schedule rules, see the “Advanced Settings” chapter of
this manual).
Note: Make sure the Router’s date and time settings for current
☞
time zone are set correctly for schedule rules to function properly.
5. Click Apply to add the website to the table. The previous screen appears while
the Router attempts to find the site. “Resolving...” appears in the “Status” column while the site is being located.
6. If the site is successfully located, “Resolved” appears in the Status column. If
not, “Hostname Resolution Failed” appears. Click Refresh to update the status
if necessary. If the Router fails to locate the website, do the following:
• Use a web browser to verify the website is available. If it is, the website
address was entered incorrectly.
• If the website is not available, return to the Website Blocking screen at a
later time and click Resolve Now to verify the website can be found and
blocked by the Router.
19
Page 25
Actiontec Wireless Broadband Router User Manual
21
Chapter 3 Configuring My Network Settings
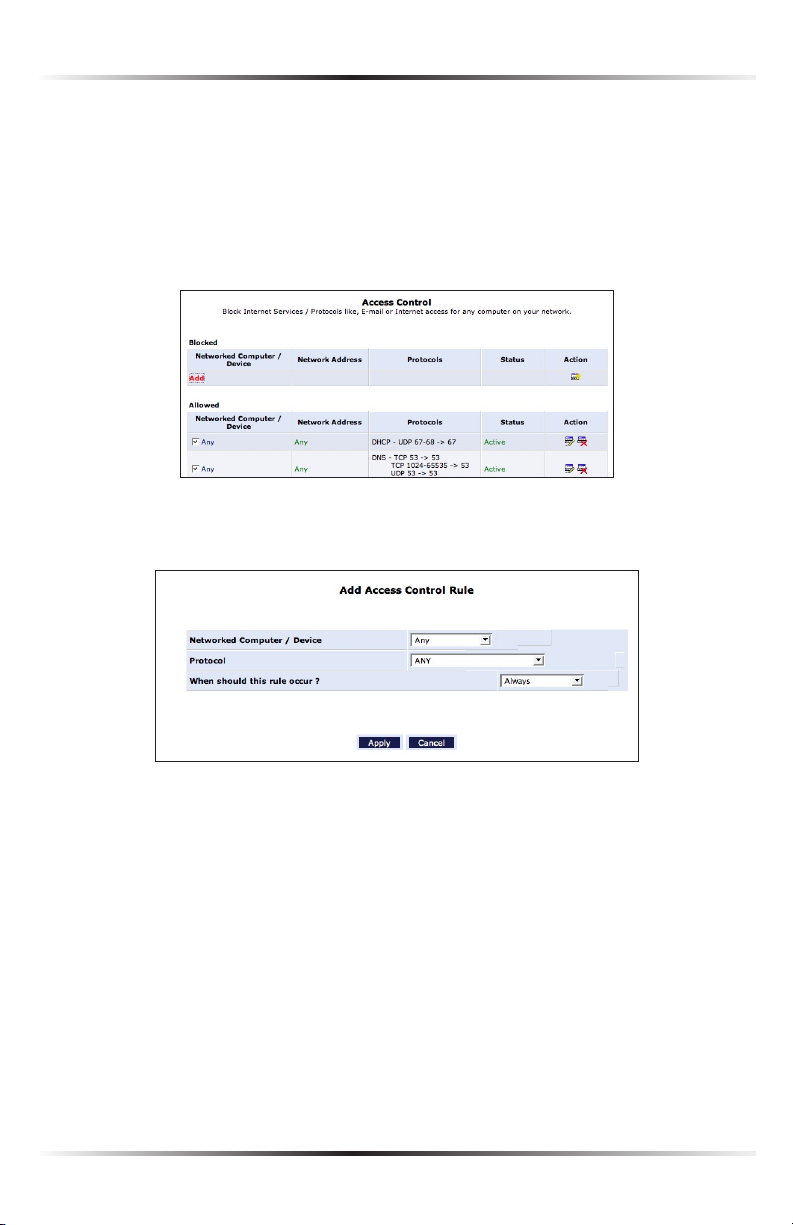
Block Internet Services
Internet services blocking is used to prevent a device on the network from accessing particular services on the Internet, such as receiving E-mail or downloading
from FTP sites. To set up Internet services blocking on a networked device, locate
the device in the My Network column, then click Block Internet Services. The
“Access Control” screen appears.
1. Click Add in the “Networked computer/Device” column. The “Add Access
Control Rule” screen appears.
2. If this access control rule applies to all networked devices, select “Any” from
the “Networked Computer/Device” list box. If this rule applies to certain
devices only, select “Specify Address” and click Add. Then, add a network
object (for more details about adding network objects, see the “Advanced
Settings” chapter of this manual).
3. Select the Internet protocol to be blocked from the “Protocol” drop-down list.
20
Page 26

Chapter 3 Configuring My Network Settings
4. If this rule will be active all the time, select “Always” from the “When should this
rule occur?” drop-down list. If the rule will only be active at certain times select
“Specify Schedule” and click Add. Then, add a schedule rule (for more details
about schedule rules, see the “Advanced Settings” chapter of this manual).
Note: Make sure the Router’s date and time settings for your time
☞
zone are set correctly for schedule rules to function properly.
5. Click Apply to save the changes. The Access Control screen will display a sum-
mary of the access control rule.
Note: To block a service that is not included in the list select
☞
“Specify Protocol” from the Protocol drop-down menu. The “Edit
Service” screen appears. Define the service, then click Apply. The
service will then be automatically added to the top section of the
“Add Access Control Rule” screen, and will be selectable.
The user may disable an access control and the service made available without
having to remove the service from the Access Control table. This may be useful to
make the service available only temporarily, with the expectation that the restriction will be reinstated later.
• To temporarily disable an access control clear the check box next to the network computer/device.
• To reinstate the restriction at a later time select the check box next to the
network computer/device.
• To remove an access restriction from the Access Control table click the
Remove button for the service. The service will be removed from the Access
Control table.
Note: When Web Filtering is enabled, HTTP services cannot be
☞
blocked by access control.
21
Page 27
Actiontec Wireless Broadband Router User Manual
23
Chapter 3 Configuring My Network Settings
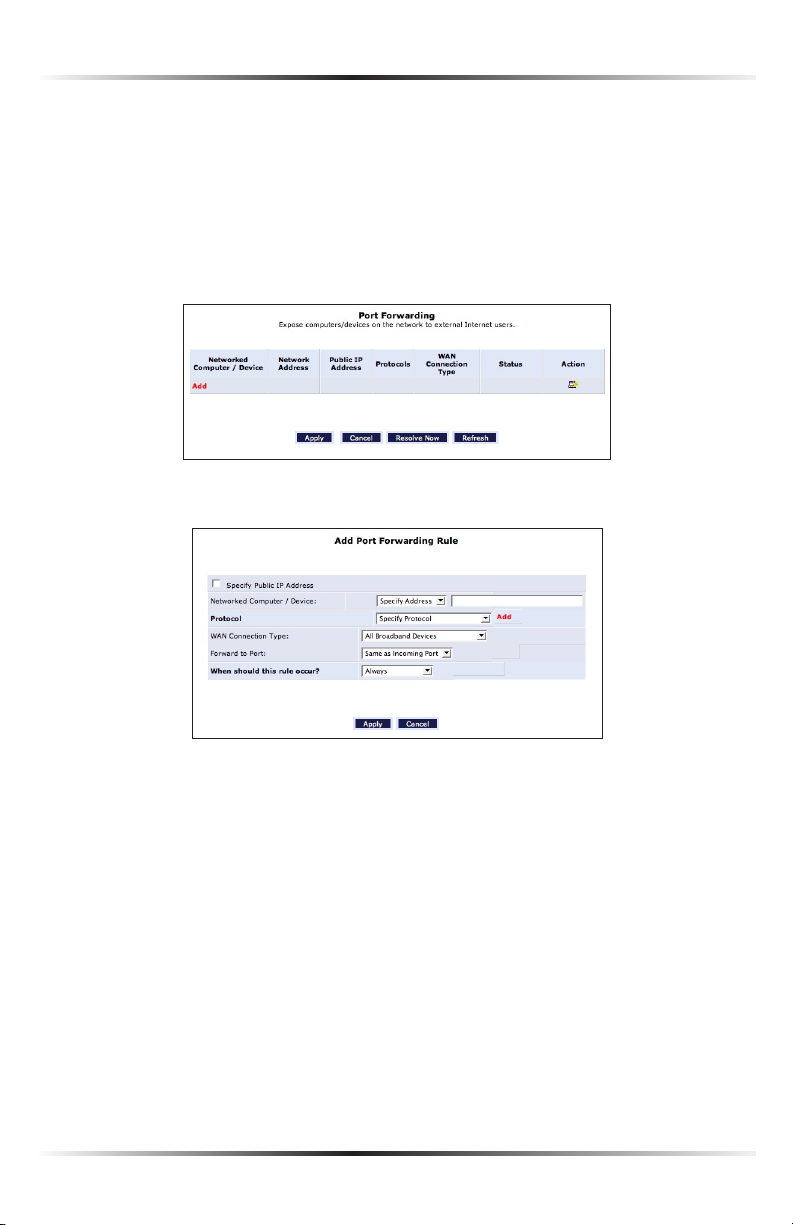
Enable Application
Activating “Enable Application” (also known as port forwarding) allows the network to be exposed to the Internet in certain limited and controlled ways, enabling
some applications to work from the local network (game, voice, and chat applications, for example), as well as allowing Internet access to servers in the network. To
set this up on a networked device, locate the device in the My Network column,
then click Enable Applications. The “Port Forwarding” screen appears.
1. Click Add. The “Add Port Forwarding Rule” screen appears.
2. Enter the local IP address or the host name of the computer providing the ser-
vice in the “Networked Computer/Device” text box. Note that only one local
network computer can be assigned to provide a specific service or application.
3. Select the Internet protocol to be provided from the “Protocol” drop-down
list.
4. To select a port to forward communications to (this is optional), select
“Specify” from the “Forward to Port” drop-down list, then, in the text box
that appears, enter the port number. If no port is identified, select “Same as
Incoming Port.”
5. If this port will be active all the time, select “Always” from the “When should this
rule occur?” drop-down list. If the rule will only be active at certain times select
“Specify Schedule” and click Add. Then, add a schedule rule (for more details
about schedule rules, see the “Advanced Settings” chapter of this manual).
22
Page 28
Chapter 3 Configuring My Network Settings
6. Click Apply to save the changes.
Note: Some applications, such as FTP, TFTP, PPTP, and H323,
☞
require the support of special specific Application Level Gateway
(ALG) modules to work inside the local network. Data packets
associated with these applications contain information that allows
them to be routed correctly. An ALG is needed to handle these
packets and ensure they reach their intended destinations. The
Router is equipped with a robust list of ALG modules, enabling
maximum functionality in the local network.
The ALG is automatically assigned based on the destination port.
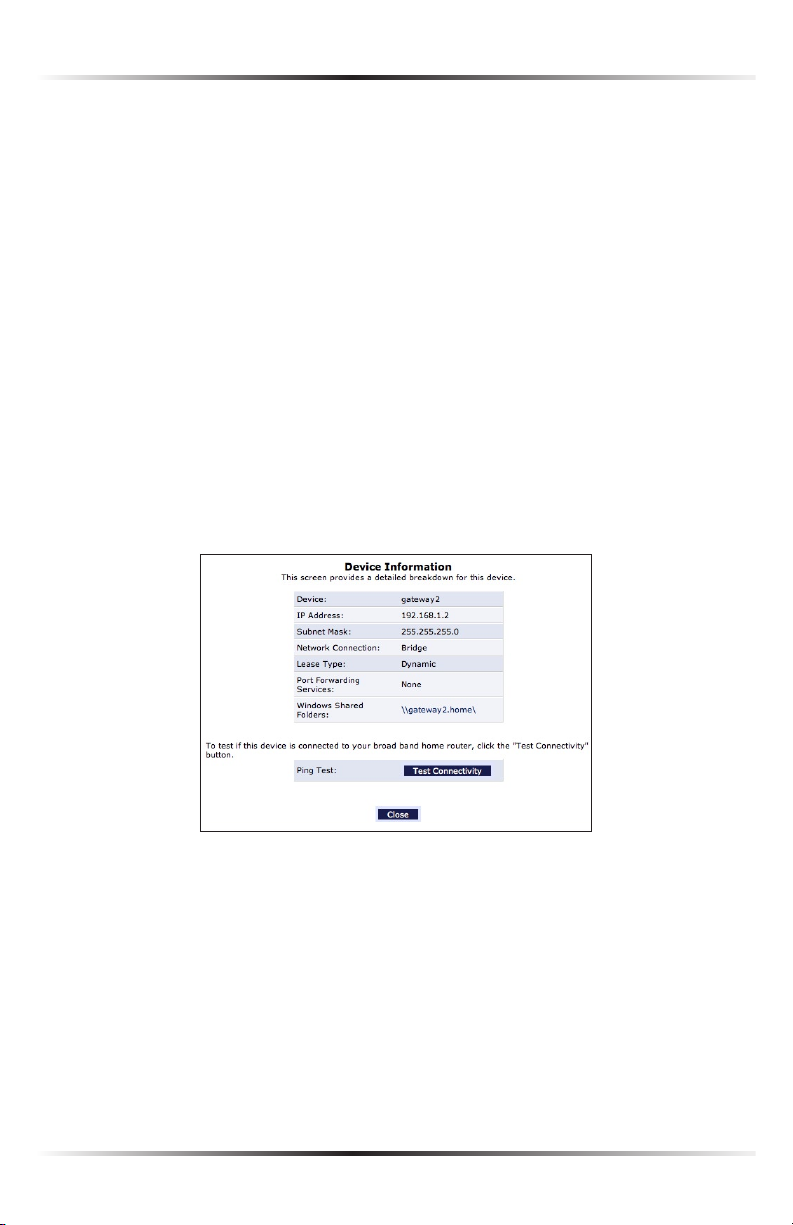
View Device Details
To view information about a networked device, or to test a device’s connection,
locate the device in the My Network column, then click View Device Details. The
“Device Information” screen appears.
23
Page 29
Actiontec Wireless Broadband Router User Manual
25
Chapter 3 Configuring My Network Settings
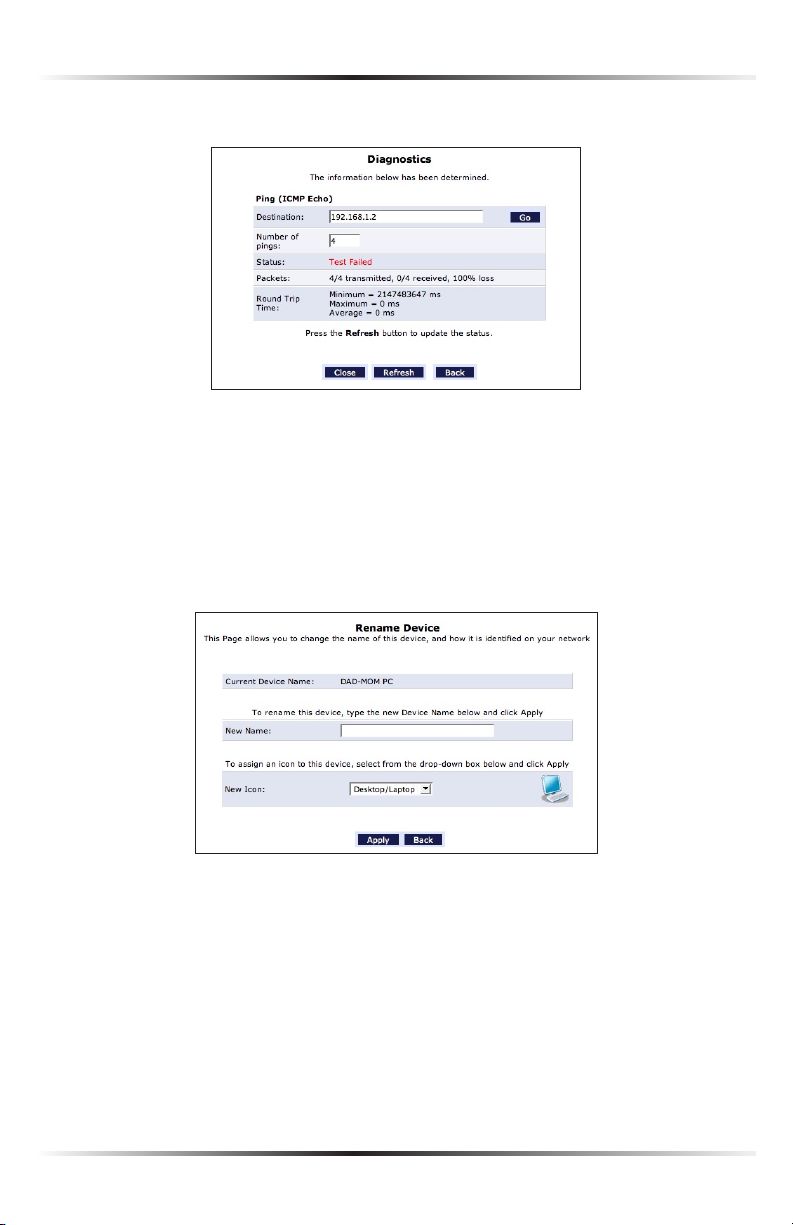
1. Click Test Connectivity. The “Diagnostics” screen appears.
2. Click Go. The Router runs a ping test, and the results are displayed in the
Diagnostics screen.
Rename This Device
To rename a networked device, locate the device in the My Network column, then
click Rename This Device. The “Rename Device” screen appears.
Enter the new name of the device in the “New Name” text box and, if needed, select
a new icon for the device from the “New Icon” drop-down list.
24
Page 30
Chapter 3 Configuring My Network Settings
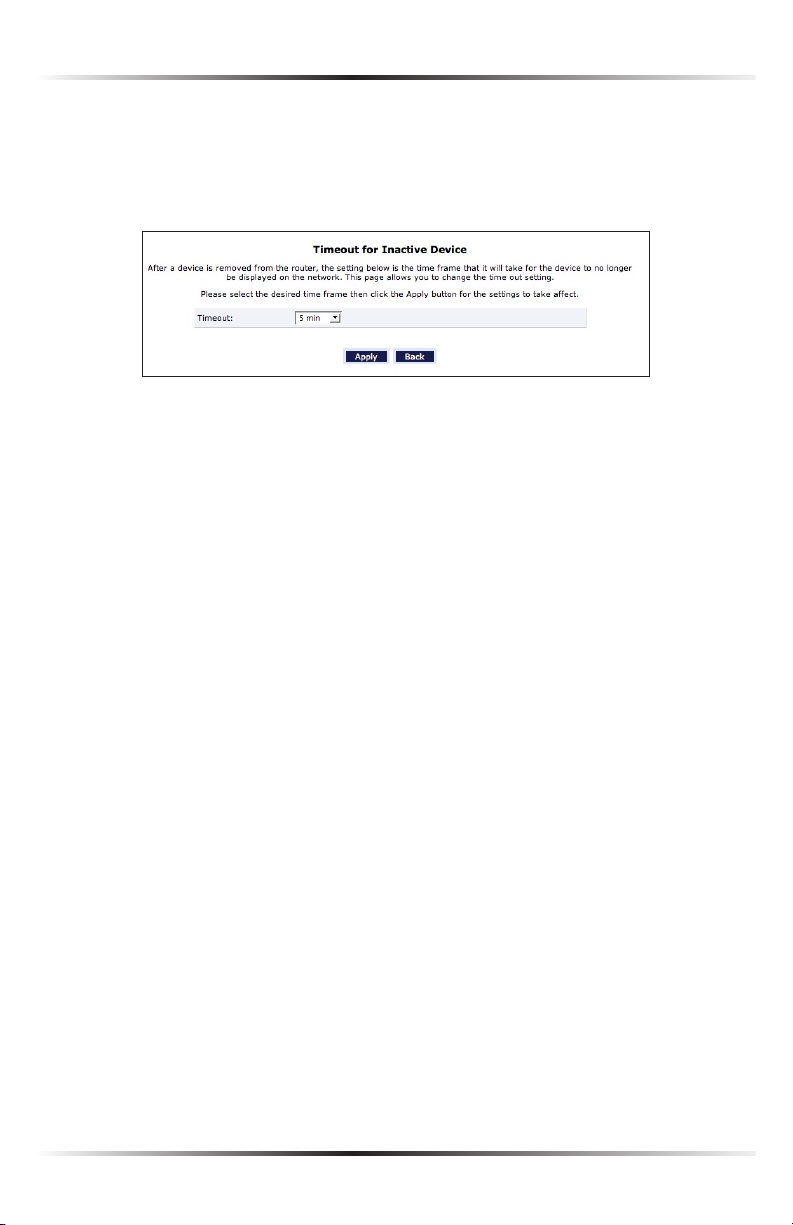
Timeout for Inactive Device
The amount of time a device continues to be displayed on the network after it has
been disconnected is configured in the “Timeout for Inactive Device” screen. To
display the screen, click Timeout for Inactive Device.
Select the timeout period from the “Timeout” drop-down list. After the device has
been disconnected for this amount of time, it will no longer be displayed in the
“My Network” column.
25
Page 31

Actiontec Wireless Broadband Router User Manual
This page left intentionally blank.
26
Page 32

Creating a Wireless Network
This chapter explains how to create a wireless network using the Wireless
Broadband Router, including accessing and configuring wireless security options.
Overview
The Wireless Broadband Router provides the user with wireless connectivity over
the 802.11b and g standards (the most common wireless standards). 802.11b has
a maximum data rate of 11 Mbps, while 802.11g has a maximum data rate of 54
Mbps. Both operate in the 2.4 GHz range.
The Router’s wireless feature is turned on, with wireless security activated, by default.
The level of security is 64/40-bit WEP, with a unique WEP key already entered. This
information is displayed on a sticker located on the bottom of the Router.
The Router integrates multiple layers of security. These include the IEEE 802.1x
port-based authentication protocol, RADIUS client, EAP-MD5, EAP-TLS, EAP-TTLS,
EAP-PEAP, Wired Equivalent Privacy (WEP), Wi-Fi Protected Access (WPA) and
firewall and VPN applications.
Connecting a Wireless Client
4
To connect a wireless client to the Router:
Note: The following procedure assumes the Router’s default wire-
☞
less settings are intact. If they have been changed, use the new ESSID
and wireless security settings. For more details, see the “Connecting
a Wireless Windows XP Client” section of this chapter.
1. In the wireless client’s configuration interface, enter the Router’s ESSID
(found on a sticker on the bottom of the Router’s case) in the appropriate
text box or field (this varies depending on the wireless client’s manufacturer).
2. Enter the Router’s WEP key (also found on the sticker on the bottom of the
Router’s case) in the wireless client’s configuration interface.
3. Save the changes and exit the wireless client’s configuration interface. The cli-
ent should now detect and join the Router’s wireless network. If not, check the
wireless client’s documentation, or contact its manufacturer.
27
Page 33

Actiontec Wireless Broadband Router User Manual
29
Chapter 4 Creating a Wireless Network
Wireless Status
Clicking on the “Wireless Settings” icon in the Home screen generates the “Wireless
Status” screen, which displays the current status of the wireless connection.
Radio Enabled
Displays whether the Router’s wireless radio is active.
SSID
The SSID (Service Set Identifier) is the network name shared among all devices
on a particular wireless network. The SSID must be identical for all devices on the
wireless network. It is case-sensitive and must not exceed 32 characters. Make sure
the SSID is the same for all devices to be connected to the wireless network. The
Router comes from the factory with an SSID already entered and displayed here.
The default SSID can also be found on a sticker on the bottom of the Router.
Channel
Displays the channel to which the wireless connection is currently set. All devices
on the wireless network must be on the same channel to function correctly.
Security Enabled
Displays what kind of security is active on the wireless connection, and the security
encryption key.
28
Page 34

Chapter 4 Creating a Wireless Network
SSID Broadcast
Displays whether the Router is broadcasting its SSID. If activated, the SSID of the
Router’s wireless network is broadcast wirelessly.
MAC Authentication
Displays whether the Router is using MAC (Media Access Control) address authen-
tication to allow wireless devices to join the network.
Wireless Mode
Displays the types of wireless device that can join the network. Options include
802.11b, 802.11g, or Mixed (allows both 802.11b- and 802.11g-equipped wireless
devices to join the network).
Packets Sent/Received
Displays the number of packets sent and received since the Router’s wireless capability was activated.
29
Page 35

Actiontec Wireless Broadband Router User Manual
31
Chapter 4 Creating a Wireless Network
Basic Security Settings
To configure the Router’s wireless network for basic security, select “Basic Security
Settings” from the menu on the left side of any Wireless Settings screen. The “Basic
Security Settings” screen appears.
1. Click the “On” radio button to activate the Router’s wireless radio.
2. Enter the name of the wireless network in the “SSID” text box.
3. Select the channel at which the Router’s wireless radio communicates by
selecting it from the “Channel” drop-down list.
4. Click the “WEP” radio button to activate WEP (Wired Equivalent Privacy)
security on the wireless network.
30
Page 36

Chapter 4 Creating a Wireless Network
5. Select a WEP security level from the “select a WEP Key” drop-down list
(options include “64/40 bit” or “128/104 bit”).
6. Enter the key code in the “Key Code” text box. Each character must be a letter
from A-F or a number from 0-9. If 64/40 bit was selected in step 5, enter 10
characters. If 128/104 was selected, enter 26 characters.
7. Write down the wireless settings displayed on the screen. Other wireless devic-
es wishing to join the Router’s wireless network must use these same settings
when configuring the device’s wireless networking scheme.
8. Click Apply to save the settings.
31
Page 37

Actiontec Wireless Broadband Router User Manual
33
Chapter 4 Creating a Wireless Network
Advanced Security Settings
To configure the Router’s advanced wireless network security settings, select
“Advanced Security Settings” from the menu on the left side of any Wireless
Settings screen. The “Advanced Security Settings” screen appears.
Note: The advanced settings should only be configured by experi-
☞
enced technical users.
Level 1 (Wireless Security)
This section is used to configure different types of wireless security. Select the type
of wireless security to apply to the wireless network by clicking the appropriate
radio button, then configure the security settings in the subsequent screens.
32
Page 38

Chapter 4 Creating a Wireless Network
WEP
If WEP was selected in the Advanced Security Settings screen, the “WEP Key”
screen appears.
1. Select the appropriate network authentication level from the drop-
down list. Options include Open System Authentication, Shared Key
Authentication, or Both.
2. Activate WEP key 1 by clicking the radio button next to “1” on the left side.
3. Select the length of key 1 by selecting “64/40 bit” or “128/104 bit” from the
appropriate drop-down list in the “Key Length” column.
4. Select the type of key from the appropriate drop-down list in the “Entry
Method” column. If “Hex” is selected, the key must be made up of hexadecimal digits. If “ASCII” is selected, the key can be made up of any characters.
5. Enter the key in the appropriate text box in the “Encryption Key” column.
If 64/40 bit was chosen in step 2, enter 10 characters. If 128/104 bit was chosen, enter 24 characters. Depending on what option was selected in step 3,
enter hexadecimal or ASCII characters.
6. Click Apply to save changes.
33
Page 39

Actiontec Wireless Broadband Router User Manual
35
Chapter 4 Creating a Wireless Network
802.1X WEP
If 802.1X WEP (Wired Equivalent Privacy) was selected, the “WEP+802.1x Radius
Settings” screen appears.
802.1x WEP is a robust security protocol that uses port control with dynamically
changing encryption keys automatically updated over the network. 802.11x WEP
uses a RADIUS (Remote Authentication Dial-in Service) server for authentication
purposes. This server must be physically connected to the Router. Also, the user
must enable the RADIUS client embedded in the Router (to do this, see chapter 9,
“Advanced Settings”).
1. Click in the “Enabled” check box to enable WEP+802.1x security.
2. Enter the RADIUS server IP address in the “Server IP” text boxes.
3. Enter the RADIUS server’s port number in the “Server Port” text box.
4. Enter the RADIUS server’s shared secret in the “Shared Secret” text box.
5. Click Apply to save changes.
34
Page 40

Chapter 4 Creating a Wireless Network
WPA
If WPA (Wi-Fi Protected Access) was selected, the “WPA Key”
screen appears.
1. Verify the authentication method selected is “Pre-Shared Key.”
2. Enter a phrase of at least eight characters in the “Pre-Shared Key” text box.
Verify that “ASCII” is selected in the associated drop-down list.
3. Select the proper encryption algorithm (TKIP or AES).
4. Click in the “Group Key Update Interval” check box to activate the group
key update interval, and set the interval time in the text box to the right.
5. Click Apply at the bottom of the screen to save changes.
Level 2 (SSID Broadcast)
This section is used to configure the Router’s SSID broadcast capabilities.
35
Page 41

Actiontec Wireless Broadband Router User Manual
37
Chapter 4 Creating a Wireless Network
Selecting “SSID Broadcast” generates the “SSID Broadcast” screen.
Click the “Enable” radio button to enable SSID broadcasting. If enabled, the SSID of
the Router’s wireless network will be broadcast wirelessly. To disable SSID broad-
casting, click the “Disable” radio button.
Level 3 (Limiting Access)
This section is used to limit access to the Router’s wireless network.
36
Page 42

Chapter 4 Creating a Wireless Network
Wireless MAC Authentication
Wireless MAC authentication allows the user to allow or deny access to the
Router’s wireless network by a particular device’s MAC address. Selecting
“Wireless MAC Authentication” from the Advanced Security Settings screen generates the “Wireless MAC Authentication” screen.
To set up wireless MAC authentication:
1. Click in the “Enable Access List” check box.
2. Select either “Accept all devices listed below” or “Deny all devices listed
below” by clicking the appropriate radio button. Selecting “Accept…” causes
all devices listed by MAC address to access the Router’s wireless network.
Selecting “Deny…” causes all listed devices to be denied access.
3. Enter the MAC address of a device in the “Client MAC address” text box.
4. Click Add.
5. Repeat steps 3 and 4 to add more devices to the list.
6. When finished listing devices, click Apply.
To remove a MAC address, select it from the “List” list box, then click Remove.
37
Page 43

Actiontec Wireless Broadband Router User Manual
39
Chapter 4 Creating a Wireless Network
802.11b/g Mode
This option allows the user to select the wireless communication standard compatible with the devices to be connected on the wireless network from the dropdown list. Options include 802.11b, 802.11g, or Mixed (allows both 802.11b
and 802.11g-equipped wireless devices to join the network).
Advanced Wireless Options
Clicking “Other Advanced Wireless Options” at the bottom of the Advanced
Security Settings screen generates the “Advanced Wireless Options” screen.
When should this rule occur?
Displays the time during which the rule is active. To configure schedule rules, see
chapter 9, “Advanced Settings.”
38
Page 44

Chapter 4 Creating a Wireless Network
Network
Select the type of connection being configured from this drop-down list
(options: Network [Home/Office], Broadband Connection, or DMZ).
MTU
MTU (Maximum Transmission Unit) specifies the largest packet size permit-
ted for Internet transmission. “Automatic” sets the MTU at 1500. Other choices
include “Automatic by DHCP,” which sets the MTU according to the DHCP connection, and “Manual,” which allows the user to set the MTU.
Transmission Rate
Select the wireless transmission rate from the drop-down list, or select “Auto”
to have the Router automatically select the best transmission rate. This setting
adjusts the bit rate of the Router’s wireless transmissions.
CTS Protection Mode
Activating CTS (Clear to Send) Protection Mode allows mixed 802.11b/g networks to operate at maximum efficiency. Select “Auto” from the drop-down list
to activate. Select “None” to deactivate .
Beacon Interval
Beacons are transmitted by the Router to help identify wireless networks. If beacons are transmitted too infrequently, networks may become hard to reach; if
too frequently, they become a resource waste. Enter the desired beacon interval
value (in milliseconds) in this text box.
DTIM Interval
Enter the DTIM (Delivery Traffic Indication Message) interval value (in mil-
liseconds) in this text box. A DTIM is a countdown mechanism for the Router,
informing wireless network clients of the next window for listening to broadcast
and multicast messages.
39
Page 45

Actiontec Wireless Broadband Router User Manual
41
Chapter 4 Creating a Wireless Network
Fragmentation Threshold
Setting the correct fragmentation threshold can increase the reliability of frame
transmissions on the wireless network. Enter the fragmentation threshold in this
text box.
RTS Threshold
Enter the RTS (Request to Send) threshold in this text box. This setting controls
what size data packet the low level RF protocol issues to an
RTS packet.
Configuring a Wireless Windows XP Client
If the computer has wireless capabilities and is running Windows XP, it will auto-
matically recognize this and create a wireless connection. View this connection
under Windows’ “Network Connections.”
Note: The following description and images are in accordance
☞
with Microsoft Windows XP, Version 2002, running Service Pack
2. If running another operating system, see the documentation
that came with the wireless adapter being used.
1. Click Network Connections in the Control Panel. The “Network
Connections” window appears.
40
Page 46

Chapter 4 Creating a Wireless Network
2. Double-click the wireless connection icon. The “Wireless Network
Connection” screen appears, displaying all available wireless networks in the
vicinity. If the Router is connected and active, the Router’s wireless connection
is displayed. Note that the connection’s status is “Not connected” and defined
as “Security-enabled wireless network (WPA)” in the figure below.
3. Click the connection once to mark it, then click Connect at the bottom of the
screen. After the connection is established, its status will change to “Connected.”
An icon appears in the notification area, announcing the successful initiation
of the wireless connection.
4. Test the connection by disabling all other connections in the Network
Connections window and browsing the Internet.
The Router’s wireless network can now be accessed from the configured computer. However, any other user with a wireless-equipped device can also access the
wireless network. To prevent this, secure the wireless network, as explained in the
“Wireless Security” section of this chapter.
41
Page 47

Actiontec Wireless Broadband Router User Manual
43
Chapter 4 Creating a Wireless Network
Connecting a Wireless Windows XP Client
This section assumes the Router is set up with WPA security.
1. Click Network Connections in the Control Panel. The “Network
Connections” window appears.
2. Double-click the wireless connection icon. The “Wireless Network
Connection” screen appears, displaying the Router’s wireless connection. Note
that the connection is defined as “Security-enabled wireless network (WPA).”
42
Page 48

Chapter 4 Creating a Wireless Network
3. Click the connection once to mark it, then click Connect at the bottom of
the screen. The following login window appears, asking for a “Network Key,”
which is the pre-shared key used when configuring the Router’s WPA security
(see the “WPA” section in this chapter).
4. Enter the pre-shared key in both text boxes and click Connect. After the con-
nection is established, its status will change to “Connected,” as shown below.
An icon appears in the notification area, announcing the successful initiation
of the wireless connection.
5. Test the connection by disabling all other connections in the Network
Connections window and surfing the Internet.
If the login window shown in step 3 does not appear and the connection attempt
fails, configure the connection manually:
1. Click the connection once to mark it and then click Change Advanced
Settings in the “Related Tasks” box on the left part of the window.
43
Page 49

Actiontec Wireless Broadband Router User Manual
45
Chapter 4 Creating a Wireless Network
2. The “Wireless Network Connection Properties” window appears. Select
Wireless Networks.
3. Click the connection to highlight it, then click Properties. The connection’s
“Properties Window” appears.
4. From the “Network Authentication” drop-down list, select WPA-PSK.
5. From the “Data Encryption” drop-down list, select TKIP.
44
Page 50

Chapter 4 Creating a Wireless Network
6. Enter the pre-shared key in both the “Network key” and the “Confirm net-
work key” text boxes.
7. Click OK, then OK again.
8. When attempting to connect to the wireless network, the login window
appears, pre-populated with the pre-shared key. Press Connect to connect.
Since the network is now secured, only users who know the pre-shared key will be
able to connect. The WPA security protocol is similar to securing network access
using a password.
45
Page 51

Actiontec Wireless Broadband Router User Manual
This page left intentionally blank.
46
Page 52

Using Network Connections
The Wireless Broadband Router supports various local area network (LAN) and wide
area network (WAN, on Internet) connections via Ethernet or coaxial cables. Network
connections is used to configure the various parameters of the Router’s network and
Internet connections, and create new connections.
Caution: The settings covered in this chapter should be config-
M
ured by experienced network technicians only.
To access the Router’s network connections, in the “My Network” screen,
click Network Connections from the menu on the left side. The “Network
Connections” screen appears.
5
Click Advanced to expand the screen and display all connection entries.
47
Page 53

Actiontec Wireless Broadband Router User Manual
49
Chapter 5 Using Network Connections
To select a connection, click on its name. The rest of this chapter describes the different network connections available on the Router, as well as the connection types
that can be created.
Network (Home/Office)
Select Network (Home/Office) in the Network Connections screen to generate
the “Network (Home/Office) Properties” screen. This screen displays a list of the
local network’s properties. The only modifications that can be made from this
screen are disabling the connection (by clicking Disable) or renaming the connection (by entering a new name in the “Rule Name” text box).
Note: When a network is disabled, its formerly underlying
☞
devices will not be able to get the DHCP address from the net-
work interface to which they were connected.
The Network (Home/Office) connection is used to combine several network
devices under one virtual network. For example, a home/office network can be
created for Ethernet and other network devices.
48
Page 54

Chapter 5 Using Network Connections
Configuring the Home/Office Network
Click Settings in the “Network (Home/Office) Properties” screen to generate the
“Configure Network (Home/Office)” screen.
General
The top part of the Configure Network (Home/Office) screen displays general
communication parameters. Actiontec recommends not changing the default
values in this section unless familiar with networking concepts.
Status Displays the connection status of the network.
When should this rule occur? Displays when the rule is active. To schedule rules,
see the “Advanced Settings” chapter.
Network Select the type of connection being configured from the drop-down list
(options: Broadband Connection, Network [Home/Office], or DMZ).
Connection Type Displays the type of connection.
Physical Address Displays the physical address of the network card used for the
network.
MTU MTU (Maximum Transmission Unit) specifies the largest packet size per-
mitted for Internet transmission. “Automatic” sets the MTU at 1500. Other choices include “Automatic by DHCP,” which sets the MTU according to the DHCP
connection, and “Manual,” which allows the MTU to be set manually.
49
Page 55

Actiontec Wireless Broadband Router User Manual
51
Chapter 5 Using Network Connections
Internet Protocol
This section has three options: No IP Address, Obtain an IP Address
Automatically, and Use the Following IP Address.
No IP Address Select this option if the connection will have no IP address. This is
useful if the connection operates under a bridge.
Obtain an IP Address Automatically Select this option if the network connection
is required by the ISP to obtain an IP address automatically. The server assigning
the IP address also assigns a subnet mask address, which can be overridden by
entering another subnet mask address.
Use the Following IP Address Select this option if the network connection uses a
permanent (static) IP address, then the IP address and subnet mask address.
Bridge
The “Bridge” section of the Configure Network (Home/Office) screen is used to
specify which networks can join the network bridge.
Note: When a network is disabled, its formerly underlying
☞
devices inherit the network’s DHCP settings. For example, the
removal of a network configured as DHCP client automatically
configures the devices formerly constituting the network as
DHCP clients, with the exact DHCP client configuration.
Click in the check box next to the particular network to specify it. Make sure
there are no loops in the network configuration, and apply these settings in case
the network consists of multiple switches, or other bridges apart from those created by the Router.
Status The “Status” column displays the connection status of a particular device.
50
Page 56

Chapter 5 Using Network Connections
STP Click in the device’s “STP” check box to enable Spanning Tree Protocol on
the device. This protocol provides path redundancy while preventing undesirable loops in the network.
Action The “Action” column contains an icon that, when clicked, generates the
configuration screen of the particular device.
DNS Server
Domain Name System (DNS) is the method by which website or domain names
are translated into IP addresses. Specify such an address manually, according to
the information provided by the ISP.
To manually configure DNS server addresses, select Use the Following DNS
Server Addresses. Specify up to two different DNS server addresses, one pri-
mary, the other secondary.
IP Address Distribution
The “IP Address Distribution” section of the Configure Network (Home/Office)
screen is used to configure the Router’s Dynamic Host Configuration Protocol
(DHCP) server parameters. DHCP automatically assigns IP addresses to net-
work devices. If enabled, make sure to configure the network devices as “DHCP
Clients.” There are three options in this section: Disabled, DHCP Server, and
DHCP Relay.
Disabled Select this option if statically assigning IP addresses to the network
devices.
DHCP Server To set up the network bridge to function as a DHCP server:
1. Select DHCP Server.
2. Enter the IP address at which the Router starts issuing addresses in the
“Start IP Address” text boxes. Since the Router’s default IP address is
192.168.1.1, the Start IP Address should be 192.168.1.2.
3. Enter the end of the IP address range used to automatically issue IP address-
es in the “End IP Address” text boxes. The “maximum” IP address that can
be entered here is 192.168.1.253.
51
Page 57

Actiontec Wireless Broadband Router User Manual
53
Chapter 5 Using Network Connections
4. Enter the subnet mask address in the “Subnet Mask” text boxes. The subnet
mask determines which portion of a destination LAN IP address is the network portion, and which portion is the host portion.
5. If Windows Internet Naming Service (WINS) is being used, enter the WINS
server address in the “WINS Server” text boxes.
6. Enter the amount of time a network device will be allowed to connect to
the Router with its currently issued dynamic IP address in the “Lease Time
in Minutes” text box.
7. Click in the “Provide Host Name If Not Specified by Client” check box to
have the Router automatically assign network devices with a host name, in
case a host name is not provided by the user.
DHCP Relay Select this option to have the Router function as a DHCP relay, and
enter the IP address in the screen that appears.
Routing
The Router can be configured to use static or dynamic routing. Dynamic routing automatically adjusts how packets travel on the network, while static routing
specifies a fixed routing path to neighboring destinations.
There are two options in the “Routing” section of the Configure Network
(Home/Office) screen: Basic or Advanced.
Basic Select this option for basic routing operation.
Advanced To set up the Router’s network bridge for advanced routing:
1. Select Advanced from the “Routing” drop-down menu.
2. Enter a device metric in the “Device Metric” text box. The device metric is
a value used by the Router to determine whether one route is superior to
another, considering parameters such as bandwidth and delay time.
3. Click in the “Default Route” check box to define this device as a the
default route.
4. Click in the “Multicast - IGMP Proxy Internal” check box to activate
multicasting.
52
Page 58

Chapter 5 Using Network Connections
Routing Table
Clicking New Route generates the “New Route” window, where a new route can
be configured.
Additional IP Addresses
Clicking New IP Address generates the “Additional IP Address Settings” screen,
where additional IP addresses can be created to access the Router via the
Network (Home/Office) connection.
Ethernet Connection
An Ethernet connection connects computers to the Router using Ethernet cables,
either directly or via network hubs and switches. Click Ethernet in the Network
Connections screen (if needed, click Advanced at the bottom of the screen to
reveal the “Ethernet” link below “Network [Home/Office]”) to generate the
“Ethernet Properties” screen. This screen displays a list of the connection’s properties. The only modifications that can be made from this screen are disabling the
connection (by clicking Disable) or renaming the connection (by entering a new
name in the “Rule Name” text box).
Note: If disabling the connection, the Router must be rebooted
☞
for the change to take effect.
53
Page 59

Actiontec Wireless Broadband Router User Manual
55
Chapter 5 Using Network Connections
Configuring the Ethernet Connection
Click Settings at the bottom-right of the Ethernet Properties screen to generate the
“Configure Ethernet” screen.
General
The top part of the Configure Ethernet screen displays general communication
parameters. Actiontec recommends not changing the default values in this section
unless familiar with networking concepts.
Status Displays the connection status of the Ethernet switch.
When should this rule occur? Displays when the rule is active. To schedule rules,
see the “Advanced Settings” chapter.
Network Select the type of connection being configured from the drop-down list
(Network [Home/Office], Broadband Connection, or DMZ).
Connection Type Displays the type of connection.
Physical Address Displays the physical address of the network card used for
the network.
54
Page 60

Chapter 5 Using Network Connections
MTU MTU (Maximum Transmission Unit) specifies the largest packet size per-
mitted for Internet transmission. “Automatic” sets the MTU at 1500. Other choices include “Automatic by DHCP,” which sets the MTU according to the DHCP
connection, and “Manual,” which allows the MTU to be set manually.
Additional IP Addresses
Clicking New IP Address generates the “Additional IP Address Settings” screen,
where additional IP addresses can be created to access the Router via the
Ethernet connection.
4 Ports Ethernet Switch
This section displays the connection status of the Router’s four Ethernet ports.
Clicking on a connection’s “Action” icon (in the column on the right) generates
the “Port VLANs” screen, where ingress and egress policies can be edited.
55
Page 61

Actiontec Wireless Broadband Router User Manual
57
Chapter 5 Using Network Connections
Coax Connection
A Coax connection connects devices (such as set-top boxes) to the Router using
a coaxial cable. Click Coax in the Network Connections screen (if needed, click
Advanced at the bottom of the screen to reveal the “Coax” link below “Network
[Home/Office]”) to generate the “Coax Properties” screen. This screen displays a
list of the connection’s properties. The only modifications that can be made from
this screen are disabling the connection (by clicking Disable) or renaming the
connection (by entering a new name in the “Name” text box).
Note: If disabling the connection, the Router must be rebooted
☞
for the change to take effect.
56
Page 62

Chapter 5 Using Network Connections
Configure Coax
Click Settings at the bottom-right of the Coax Properties screen generates the
“Configure Coax” screen.
General
The top part of the Configure Coax screen displays general communication
parameters. Actiontec recommends not changing the default values in this section unless familiar with networking concepts.
Status Displays the status of the coax connection.v
When should this rule occur? Displays when the rule is active. To schedule rules,
see the “Advanced Settings” chapter
Network Displays the type of network.
Connection Type Displays the type of connection.
Physical Address Displays the physical address of the network card used for the
network.
MTU MTU (Maximum Transmission Unit) specifies the largest packet size per-
mitted for Internet transmission. “Automatic” sets the MTU at 1500. Other choices include “Automatic by DHCP,” which sets the MTU according to the DHCP
connection, and “Manual,” which allows the MTU to be set manually.
57
Page 63

Actiontec Wireless Broadband Router User Manual
59
Chapter 5 Using Network Connections
Coax Link
Set up the coax link options in this section of the Configure Coax screen.
Options include Channel, Privacy, and Password.
Channel Select the Channel from the drop-down list (select from 1-6, or
“Automatic”).
Privacy Toggle “Privacy” by clicking in the “Enabled” check box. If Privacy is
activated, all devices connected via coaxial cable must use the same password.
Actiontec recommends leaving the Privacy option deactivated.
Password Enter the Coax Link password in this text box.
Additional IP Addresses
Clicking New IP Address generates the “Additional IP Address Settings” screen,
where additional IP addresses can be created to access the Router via the Coax
Link Ethernet connection.
Coax Connection Status
Click Go to LAN Coax Stats to generate the “Coax Connection Status” screen,
which gives an overview of all the devices connected to the Router via coaxial cable.
58
Page 64

Chapter 5 Using Network Connections
Broadband Ethernet Connection
A Broadband Ethernet connection connects the Router to the Internet using an
Ethernet cable. Click Broadband Connection (Ethernet) from the Network
Connections screen to generate the “Broadband Connection (Ethernet) Properties”
screen. This screen displays a list of the connection’s properties. The only modifications that can be made from this screen are disabling the connection (by clicking
Disable) or renaming the connection (by entering a new name in the “Rule Name”
text box).
Note: If disabling the connection, the Router must be rebooted
☞
for the change to take effect.
59
Page 65

Actiontec Wireless Broadband Router User Manual
61
Chapter 5 Using Network Connections
Configuring the Broadband Ethernet Connection
Click Settings at the bottom-right of the Broadband Connection (Ethernet) Properties
window to generate the “Configure Broadband Connection (Ethernet)” screen.
General
The top part of the screen displays general communication parameters. Actiontec
recommends not changing the default values in this section unless familiar with
networking concepts.
Status Displays the status of the Ethernet connection (“Down,” “Connected,”
etc.)
Schedule Displays when the rule is active. To configure rules, see the “Advanced
Settings” chapter.
Network Select the type of connection being configured from the drop-down list
(options: Network (Home/Office), Broadband Connection, or DMZ).
Connection Type Displays the type of connection. Since this is an Ethernet
Connection, “Ethernet” is displayed.
Physical Address Displays the physical address of the network card used for the
network.
60
Page 66

Chapter 5 Using Network Connections
MTU MTU (Maximum Transmission Unit) specifies the largest packet size per-
mitted for Internet transmission. “Automatic, sets the MTU at 1500. Other choices include “Automatic by DHCP,” which sets the MTU according to the DHCP
connection, and “Manual,” which allows the MTU to be set manually.
Internet Protocol
This section includes three options: No IP Address, Obtain an IP Address
Automatically, and Use the Following IP Address.
No IP Address Select this option if the connection has no IP address. This is use-
ful if the connection is operating under a bridge.
Obtain an IP Address Automatically Select this option if the ISP requires the con-
nection to obtain an IP address automatically. The server assigning the IP address
also assigns a subnet mask address, which can be overridden by clicking in the
“Override Subnet Mask” check box and entering another subnet mask address.
Additionally, the DHCP lease can be renewed and/or released by clicking on the
appropriate “DHCP Lease” button. The “Expires In” value displays how long until
the DHCP lease expires.
Use the Following IP Address Select this option if the connection uses a permanent (static) IP address. The ISP should provide this address, along with a subnet
mask address, default gateway address, and, optionally, primary and secondary
DNS server addresses.
DNS Server
The Domain Name System (DNS) is the method by which website or domain
names are translated into IP addresses. This connection can be configured to
automatically obtain a DNS server address, or such an address can be specified
manually, according to the information provided by the ISP.
To configure the connection to automatically obtain a DNS server address, select
Obtain DNS Server Address Automatically from the “DNS Server” drop-down
list. To manually configure DNS server addresses, select Use the Following DNS
Server Addresses. Specify up to two different DNS server addresses, one pri-
mary, the other secondary.
61
Page 67

Actiontec Wireless Broadband Router User Manual
63
Chapter 5 Using Network Connections
IP Address Distribution
The “IP Address Distribution” section of the Configure Broadband Connection
(Ethernet) screen is used to configure the Router’s Dynamic Host Configuration
Protocol (DHCP) server parameters. DHCP automatically assigns IP addresses
to network devices. If enabled, make sure to configure the network devices
as “DHCP Clients.” There are three options in this section: Disabled, DHCP
Server, and DHCP Relay.
Caution: Actiontec strongly recommends leaving this setting
M
at “Disabled.”
Disabled Select this option if statically assigning IP addresses to the network
devices.
DHCP Server To set up the Router to function as a DHCP server:
1. Select DHCP Server.
2. Enter the IP address at which the Router starts issuing addresses in the
“Start IP Address” text boxes. Since the Router’s default IP address is
192.168.1.1, the Start IP Address must be 192.168.1.2 or higher.
3. Enter the end of the IP address range used to automatically issue IP address-
es in the “End IP Address” text boxes.
4. Enter the subnet mask address in the “Subnet Mask” text boxes. The subnet
mask determines which portion of a destination LAN IP address is the network portion, and which portion is the host portion.
5. If a Windows Internet Naming Service (WINS) is being used, enter the
WINS server address in the “WINS Server” text boxes.
6. Enter the amount of time a network device will be allowed to connect to
the Router with its currently issued dynamic IP address in the “Lease Time
in Minutes” text box. Just before the time is up, the device’s user will need to
make a request to extend the lease or get a new IP address.
7. Click in the “Provide Host Name If Not Specified by Client” check box to
have the Router automatically assign network devices with a host name, in
case a host name is not provided by the user.
62
Page 68

Chapter 5 Using Network Connections
DHCP Relay Select this option to have the Router function as a DHCP relay, and
enter the IP address in the screen that appears.
To add a new product or product family, click New IP Range. This generates the
“DHCP Server Pool Settings” screen. Set the device name, IP range, and priority level
in the appropriate text boxes.
Routing
The Router can be configured to use static or dynamic routing. Dynamic routing automatically adjusts how packets travel on the network, while static routing
specifies a fixed routing path to neighboring destinations.
There are two options in the “Routing” section of the “Configure WAN Coax
Link Ethernet” screen: Basic or Advanced.
Basic Select this option for basic routing operation.
Advanced To set up the Router’s Broadband Ethernet connection for advanced
routing:
1. Select Advanced from the Routing drop-down menu.
2. Enter a device metric in the “Device Metric” text box. The device metric is
a value used by the Router to determine whether one route is superior to
another, considering parameters such as bandwidth and delay time.
3. Click in the “Default Route” check box to define this device as a the
default route.
4. Click in the “Multicast - IGMP Proxy Internal” check box to activate
multicasting.
63
Page 69

Actiontec Wireless Broadband Router User Manual
65
Chapter 5 Using Network Connections
Routing Table
Clicking New Route generates the “New Route” window, where a new route can
be configured.
Internet Connection Firewall
Click in the “Enabled” check box to activate the Router’s firewall on the connection.
Additional IP Addresses
Clicking New IP Address generates the “Additional IP Address Settings” screen, where
additional IP addresses can be created to access the Router via the connection.
Coax Broadband Connection
A Coax Broadband connection connects the Router to the Internet using a coaxial
cable. Click Broadband Connection (Coax) in the Network Connections screen
to generate the “Broadband Connection (Coax) Properties” screen. This screen displays a list of the connection’s properties. The only modifications that can be made
from this screen are disabling the connection (by clicking Disable) or renaming
the connection (by entering a new name in the “Name” text box).
Note: If disabling the connection, the Router must be rebooted
☞
for the change to take effect.
64
Page 70

Chapter 5 Using Network Connections
Configuring the Coax Broadband Connection
Click Settings at the bottom of the Broadband Connection (Coax) Properties
screen to generate the “Configure Broadband Connection (Coax)” screen.
General
The top part of the screen displays general communication parameters.
Actiontec recommends not changing the default values in this section unless
familiar with networking concepts.
Status Displays the status of the connection (“Down,” “Connected,” etc.).
When should this rule occur? Displays when the rule is active. To schedule rules,
see the “Advanced Settings” chapter.
Network Displays the type of network to which the link is connected. Since this
is a broadband connection (connected to the Internet), “Broadband Connection
is displayed.
Connection Type Displays the type of connection. Since this is a coaxial connection, “Coax” is displayed.
65
Page 71

Actiontec Wireless Broadband Router User Manual
67
Chapter 5 Using Network Connections
Physical Address Displays the physical address of the network card used for the
network.
MTU MTU (Maximum Transmission Unit) specifies the largest packet size
permitted for Internet transmission. “Automatic” sets the MTU at 1500. Other
choices include “Automatic by DHCP,” which sets the MTU according to the
DHCP connection, and “Manual,” which allows the MTU to be set manually.
Coax Link
Configure the coax link connection in this section of the screen.
Privacy Toggle “Privacy” by clicking in the “Enabled” check box. If Privacy is
activated, all devices connected via coaxial cable must use the same password.
Actiontec recommends leaving the Privacy option deactivated.
Password Enter the Coax Link password here.
WAN Coax Connection Speeds
This section displays the Router’s Tx and Rx speeds (in Mbps).
Internet Protocol
This section includes three options: No IP Address, Obtain an IP Address
Automatically, and Use the Following IP Address.
No IP Address Select this option if the connection has no IP address. This is use-
ful when the connection is operating under a bridge.
Obtain an IP Address Automatically Select this option if the ISP requires the con-
nection to obtain an IP address automatically. The server assigning the IP address
also assigns a subnet mask address, which can be overridden by clicking in the
“Override Subnet Mask” check box and entering another subnet mask address.
Additionally, the DHCP lease can be renewed and/or released by clicking on the
appropriate “DHCP Lease” button. The “Expires In” value displays how long
until the DHCP lease expires.
Use the Following IP Address Select if the WAN connection is configured using a
permanent (static) IP address. The ISP should provide this address, along with a
subnet mask address, default gateway address, and, optionally, primary and secondary DNS server addresses.
66
Page 72

Chapter 5 Using Network Connections
DNS Server
Domain Name System (DNS) is the method by which website or domain names
are translated into IP addresses. The connection can be set to automatically
obtain a DNS server address, or an address can be set manually, according to
information provided by the ISP.
To configure the connection to automatically obtain a DNS server address, select
Obtain DNS Server Address Automatically from the “DNS Server” drop-down
list. To manually configure DNS server addresses, select Use the Following DNS
Server Addresses. Specify up to two different DNS server addresses, one pri-
mary, the other secondary.
IP Address Distribution
The “IP Address Distribution” section of the Configure Broadband Connection
(Coax) screen allows the user to configure the Router’s Dynamic Host
Configuration Protocol (DHCP) server parameters. The DHCP automatically
assigns IP addresses to network devices. If enabled, make sure to configure the
network devices as “DHCP Clients.” There are three options in this section:
Disabled, DHCP Server, and DHCP Relay.
Caution: Actiontec strongly recommends leaving this setting
M
at “Disabled.”
Disabled Select this option if statically assigning IP addresses to the network
devices.
DHCP Server To set up the WAN Coax Link Ethernet connection to function as a
DHCP server:
1. Select DHCP Server.
2. Enter the IP address at which the Router starts issuing addresses in the
“Start IP Address” text boxes. Since the Router’s default IP address is
192.168.1.1, the Start IP Address must be 192.168.1.2.
3. Enter the end of the IP address range used to automatically issue IP address-
es in the “End IP Address” text boxes.
4. Enter the subnet mask address in the “Subnet Mask” text boxes. The subnet
mask determines which portion of a destination LAN IP address is the network portion, and which portion is the host portion.
67
Page 73

Actiontec Wireless Broadband Router User Manual
69
Chapter 5 Using Network Connections
5. If a Windows Internet Naming Service (WINS) is being used, enter the
WINS server address in the “WINS Server” text boxes.
6. Enter the amount of time a network device will be allowed to connect to
the Router with its currently issued dynamic IP address in the “Lease Time
in Minutes” text box. Just before the time is up, the device’s user will need to
make a request to extend the lease or get a new IP address.
7. Click in the “Provide Host Name If Not Specified by Client” check box to
have the Router automatically assign network devices with a host name, in
case a host name is not provided by the user.
DHCP Relay Select this option to have the Router function as a DHCP relay, and
enter the IP address in the screen that appears.
Routing
The Router can be configured to use dynamic routing. Dynamic routing automatically adjusts how packets travel on the network There are two options in the
“Routing” section of the Configure Broadband Connection (Coax) screen: Basic
or Advanced.
Warning: Do not use static routing unless instructed to do so
M
by Verizon.
Basic Select this option for basic routing operation.
Advanced To set up the Router’s Coax broadband connection for advanced rout-
ing:
1. Select Advanced from the Routing drop-down list.
2. Enter a device metric in the “Device Metric” text box. The device metric is
a value used by the Router to determine whether one route is superior to
another, considering parameters such as bandwidth and delay time.
3. Click in the “Default Route” check box to define this device as the
default route.
4. Click in the “Multicast - IGMP Proxy Internal” check box to activate
multicasting.
68
Page 74

Chapter 5 Using Network Connections
Routing Table
Click New Route to generate the “New Route” window, where a new route can
be configured.
Additional IP Addresses
Click New IP Address to generate the “Additional IP Address Settings” screen, where
additional IP addresses can be created to access the Router via the connection.
WAN PPPoE/WAN PPPoE 2
WAN Point-to-Point Protocol over Ethernet (PPPoE) relies on two widely accepted
standards: Point-to-Point Protocol and Ethernet. PPPoE enables Ethernet net-
worked computers to exchange information with computers on the Internet. PPPoE
supports the protocol layers and authentication widely used in PPP and enables
a point-to-point connection to be established in the normally multipoint architecture of Ethernet. A discovery process in PPPoE determines the Ethernet MAC
address of the remote device in order to establish a session.
Click WAN PPPoE in the Network Connections screen to generate the “WAN
PPPoE Properties” screen. This screen displays a list of the connection’s proper-
ties. The only modifications that can be made from this screen are disabling the
connection (by clicking Disable) or renaming the connection (by entering a new
name in the “Name” text box).
69
Page 75

Actiontec Wireless Broadband Router User Manual
71
Chapter 5 Using Network Connections
Configuring the WAN PPPoE Connection
Click Settings in the WAN PPPoE Properties screen to generate the “Configure
WAN PPPoE” screen.
General
The top part of the Configure WAN PPPoE screen displays general communica-
tion parameters. Actiontec recommends not changing the default values in this
section unless familiar with networking concepts.
Status Displays the connection status of the WAN PPPoE connection. (“Down,”
“Disabled,” “Connected,” etc.)
When should this rule occur? Displays when the rule is active. To schedule rules,
see “Advanced Settings” chapter.
70
Page 76

Chapter 5 Using Network Connections
Network Select the type of connection being configured from the drop-down list
(Broadband Connection, Network (Home/Office), or DMZ).
Connection Type Displays the type of connection. Since this is PPPoE connection,
“PPPoE” is displayed.
MTU MTU (Maximum Transmission Unit) specifies the largest packet size
permitted for Internet transmission. “Automatic, sets the MTU at 1492. Other
choices include “Automatic,” which sets the MTU according to the connection to
the ISP, and “Manual,” which allows the MTU to be set manually.
Underlying Connection Specify the underlying connection above which the protocol initiates from the drop-down list, which displays all possible underlying devices.
PPP Configuration
Point-to-Point Protocol (PPP) is the most popular method for transporting
packets between the user and the ISP.
Service Name Specify the networking peer’s service name, if provided by the ISP,
in this text box.
On-Demand To use PPP on demand to initiate the point-to-point protocol session
only when packets are actually sent over the Internet, click in this check box. This
option should be active on a limited basis
Idle Time Before Hanging Up Enter the amount of idle time, in minutes, before the
PPP session automatically ends .
Time Between Reconnect Attempts In this text box, specify the duration between
PPP reconnect attempts, as provided by the ISP.
PPP Authentication
Point-to-Point Protocol (PPP) currently supports four authentication protocols: Password Authentication Protocol (PAP), Challenge Handshake
Authentication Protocol (CHAP), and Microsoft CHAP versions 1 and 2.
Select the authentication protocols the Router may use when negotiating with a
PPTP server in this section. Select all the protocols if no information is available
about the server’s authentication methods. Note that encryption is performed
only if Microsoft CHAP, Microsoft CHAP version 2, or both are selected.
Warning: The PPP Authentication settings should not be
M
changed unless instructed to do so by Verizon.
71
Page 77

Actiontec Wireless Broadband Router User Manual
73
Chapter 5 Using Network Connections
Login User Name Enter the user name (provided by the ISP) in this text box.
Login Password Enter the password (provided by the ISP) in this text box.
Support Unencrypted Password (PAP) Password Authentication Protocol (PAP)
is a simple, plain-text authentication scheme. The user name and password are
requested by the networking peer in plain-text. PAP, however, is not a secure
authentication protocol. Man-in-the-middle attacks can easily determine the
remote access client’s password. PAP offers no protection against replay attacks,
remote client impersonation, or remote server impersonation.
Support Challenge Handshake Authentication (CHAP) Click in this check box to
activate CHAP, a challenge-response authentication protocol that uses MD5 to
hash the response to a challenge. CHAP protects against replay attacks by using
an arbitrary challenge string per authentication attempt.
Support Microsoft CHAP Click in this check box if communicating with a peer
that uses Microsoft CHAP authentication protocol.
Support Microsoft CHAP Version 2 Select this check box if communicating with a
peer that uses Microsoft CHAP Version 2 authentication protocol.
PPP Compression
The PPP Compression Control Protocol (CCP) is responsible for configuring,
enabling, and disabling data compression algorithms on both ends of the pointto-point link. It is also used to signal a failure of the compression/ decompression mechanism in a reliable manner.
For each compression algorithm (BSD and Deflate), select one of the following
from the drop-down list:
Reject Selecting this option rejects PPP connections with peers that use the com-
pression algorithm. If Reject is activated, throughput may diminish.
Allow Selecting this option allows PPP connections with peers that use the com-
pression algorithm.
Require Selecting this option insures a connection with a peer using the compression algorithm.
72
Page 78

Chapter 5 Using Network Connections
Internet Protocol
Select one of the following Internet Protocol options from the “Internet
Protocol” drop-down list:
Obtain an IP Address Automatically This option is selected by default. Change only
if required by the ISP. The server that assigns the Router with an IP address also
assigns a subnet mask. Override the dynamically assigned subnet mask by selecting
the “Override Subnet Mask” and entering a different subnet mask.
Use the Following IP Address Select this option to configure the Router to use a
permanent (static) IP address. The ISP should provide this address.
DNS Server
The Domain Name System (DNS) is the method by which website or domain
names are translated into IP addresses. The Router can be configured to automatically obtain a DNS server address, or the address can be entered manually,
according to the information provided by the ISP.
To configure the connection to automatically obtain a DNS server address, select
Obtain DNS Server Address Automatically from the “DNS Server” drop-down
list. To manually configure DNS server addresses, select Use the Following DNS
Server Addresses from the “DNS Server” drop-down list. Up to two different
DNS server addresses can be entered (Primary and Secondary).
Routing
Select Advanced or Basic from the “Routing” drop-down list. If Advanced is
selected, additional options appear, as listed below.
Routing Mode Select one of the following Routing modes:
• Route - Select this option to cause the Router to act as a router between two
networks.
• NAT - Select this option to activate Network Address Translation (NAT),
which translates IP addresses to a valid, public address on the Internet. NAT
adds security, since the IP addresses of the devices on the network are not
transmitted over the Internet. In addition, NAT allows many addresses to
exist behind a single valid address. Use the NAT routing mode only if the
local network consists of a single device, or collisions may occur if more than
one device attempts to communicate using the same port.
73
Page 79

Actiontec Wireless Broadband Router User Manual
• NAPT - Select this option to activate NAPT (Network Address and Port
Translation), which refers to network address translation involving the
mapping of port numbers and allows multiple machines to share a single IP
address. Use NAPT if the local network contains multiple devices, a topol-
ogy that necessitates port translation in addition to address translation.
Device Metric The device metric is a value used by the Router to determine
whether one route is superior to another, considering parameters such as bandwidth, delay, and more.
Default Route Click in this check box to define the connection as a the default
route.
Multicast - IGMP Proxy Default Click in this check box to enable the Router to
issue IGMP (Internet Group Management Protocol) host messages on behalf of
hosts the Router discovers through standard IGMP interfaces. IGMP proxy enables
the routing of multicast packets according to the IGMP requests of local network
devices asking to join multicast groups.
Routing Table
Clicking New Route generates the “New Route” window, where a new route can
be configured.
Internet Connection Firewall
Click in the “Enabled” check box to activate the Router’s firewall on the WAN
PPPoE connection.
74
Page 80

Configuring the Router’s Security
The Wireless Broadband Router’s security suite includes comprehensive and robust
security services: Stateful Packet Inspection, a firewall, user authentication protocols, and password protection mechanisms. These features allow users to connect
their computers to the Internet and be protected from the security threats.
The Router’s firewall is the cornerstone of the Router’s security suite. It has been
exclusively tailored to the needs of the residential/office user and is pre-configured
to provide optimum security.
6
The firewall provides both the security and flexibility home and office users seek. It
provides a managed, professional level of network security while enabling the safe
use of interactive applications, such as Internet gaming and video-conferencing.
Additional features, including surfing restrictions and access control, can also be
configured locally through the Router’s MegaControl Panel, or remotely by a
service provider.
The firewall also supports advanced filtering, designed to allow comprehensive
control over the firewall’s behavior. Specific input and output rules can be defined,
the order of logically similar sets of rules can be controlled, and distinctions
between rules that apply to Internet and local network devices can be made.
75
Page 81

Actiontec Wireless Broadband Router User Manual
77
Chapter 6 Configuring the Router’s Security
This chapter covers these Security features:
• General - select the security level for the firewall.
• Access Control - restrict access from the local network to the Internet.
• Port Forwarding - enable access from the Internet to specified services
provided by computers on the local network.
• DMZ Host - configure a network host to receive all traffic arriving at the
Router which does not belong to a known session.
• Port Triggering - define port triggering entries to dynamically open the
firewall for some protocols or ports.
• Remote Administration - enable remote configuration of the Router from
any Internet-accessible computer.
• Website Blocking - block network access to a certain hosts or websites on
the Internet.
• Static NAT - allow multiple static NAT IP addresses to be designated to
devices on the network.
• Advanced Filtering - control the firewall’s settings and rules.
• Security Log - view and configure the security log.
76
Page 82

Chapter 6 Configuring the Router’s Security
General
The “General” screen is used to configure the Router’s basic security settings.
The firewall regulates the flow of data between the local network and the Internet.
Both incoming and outgoing data are inspected and then either accepted (allowed
to pass through the Router) or rejected (barred from passing through the Router)
according to a flexible and configurable set of rules. These rules are designed to
prevent unwanted intrusions from the outside, while allowing local network users
access to required Internet services.
The firewall rules specify what types of services available on the Internet can be
accessed from the local network and what types of services available in the local
network can be accessed from the Internet. Each request for a service the firewall
receives, whether originating in the Internet or from a computer in the local network, is checked against the firewall rules to determine whether the request should
be allowed to pass through the firewall. If the request is permitted to pass, all subsequent data associated with this request (a “session”) will also be allowed to pass,
regardless of its direction.
For example, when accessing a website on the Internet, a request is sent out to the
Internet for this site. When the request reaches the Router, the firewall identifies
the request type and origin (HTTP and a specific computer in the local network, in
this case). Unless the Router is configured to block requests of this type from this
computer, the firewall allows this request to pass out onto the Internet. When the
website is returned from the web server, the firewall will associate it with this session and allow it to pass, regardless of whether HTTP access from the Internet to
the local network is blocked or permitted.
77
Page 83

Actiontec Wireless Broadband Router User Manual
79
Chapter 6 Configuring the Router’s Security
Note that it is the origin of the request, not subsequent responses to this request,
which determines whether a session can be established or not.
The Router features three pre-defined security levels: Minimum, Typical, and
Maximum. The table below summarizes the behavior of the Router for each of the
three security levels.
Requests from the Internet
Security Level
Maximum
Security
Typical Security
Minimum
Security
These services include Telnet, FTP, HTTP, HTTPS, DNS, IMAP, POP3 and SMTP.
Note: Some applications (such as some Internet messengers and
☞
Peer-To-Peer client applications) tend to use these ports if they
cannot connect with their own default ports. When applying
this behavior, these applications will not be blocked outbound,
even at the Maximum Security level.
(incoming traffic)
Blocked - No access to local
network from Internet,
except as configured in the
Port Forwarding, DMZ host,
and Remote Access screens.
Blocked - No access to local
network from Internet,
except as configured in the
Port Forwarding, DMZ host,
and Remote Access screens.
Unrestricted - Permits full
access from Internet to local
network; all connection
attempts permitted.
Requests from the local
network (outgoing traffic)
Limited - Only commonly
used services, such as web
browsing and E-mail, are
permitted.
Unrestricted - All services
are permitted, except as
configured in the Access
Control screen.
Unrestricted - All services
are permitted, except as
configured in the Access
Control screen.
To configure the Router’s security settings:
1. From the General screen, select a security level by clicking the appropriate radio
button. Using the Minimum Security setting may expose the local network to
significant security risks, and thus should only be used for short periods of time.
78
Page 84

Chapter 6 Configuring the Router’s Security
2. Check the “Block IP Fragments” box to protect the local network from a com-
mon type of hacker attack that uses fragmented data packets to sabotage the
network. Note that VPN over IPSec and some UDP-based services make legiti-
mate use of IP fragments. IP fragments must be allowed to pass into the local
network to use these services.
3. Click Apply to save changes.
Access Control
Access control is used to block specific computers within the local network (or even
the whole network) from accessing certain services on the Internet. For example,
one computer can be prohibited from surfing the Internet, another computer from
transferring files using FTP, and the whole network from receiving incoming E-mail.
Access control defines restrictions on the types of requests that can pass from the
local network out to the Internet, and thus may block traffic flowing in both directions. In the E-mail example given above, computers in the local network can be
prevented from receiving E-mail by blocking their outgoing requests to POP3 serv-
ers on the Internet.
Access control also incorporates a list of preset services in the form of applications
and common port settings.
79
Page 85

Actiontec Wireless Broadband Router User Manual
81
Chapter 6 Configuring the Router’s Security
Allow or Restrict Services
To view and allow/restrict these services:
1. Select Access Control from the left side of any Security screen. The “Access
Control” screen appears.
Note: The “Allowed” section is only visible when the firewall is
☞
set to “Maximum.”
2. Click Add. The “Add Access Control Rule” screen appears.
Note: To block a service, click Add in the “Blocked” section of
☞
the Access Control screen. To allow outgoing traffic, click Add
in the “Allowed” section of the screen.
80
Page 86

Chapter 6 Configuring the Router’s Security
3. If this access control rule applies to all networked devices, select “Any” from
the “Networked Computer/Device” list box. If this rule applies to certain
devices only, select “Specify Address” and click Add. Then, create and add
a network object (for more details about adding network objects, see the
“Advanced Settings” chapter of this manual).
4. Select the Internet protocol to be allowed or blocked from the “Protocol”
drop-down list.
5. If the rule will be active all the time, select Always from the “When should this
rule occur?” drop-down list. If the rule will only be active at certain times, select
Specify Schedule and click Add. Then, add a schedule rule (for more details
about schedule rules, see the “Advanced Settings” chapter of this manual).
6. Click Apply to save the changes. The Access Control screen will display a sum-
mary of the new access control rule.
Note: To block a service not included in the list, select Specify
☞
Protocol from the Protocol drop-down menu. The “Edit
Service” screen appears. Define the service, then click OK. The
service will then be automatically added to the top section of the
“Add Access Control Rule” screen, and will be selectable.
An access control can be disabled and the service made available without having
to remove the service from the Access Control table. This may be useful to make
the service available temporarily, with the expectation that the restriction will be
reinstated later.
• To temporarily disable an access control, clear the check box next to the service name.
• To reinstate the restriction at a later time, select the check box next to the
service name.
• To remove an access restriction from the Access Control table, click Remove
for the service. The service will be removed from the Access Control table.
81
Page 87

Actiontec Wireless Broadband Router User Manual
83
Chapter 6 Configuring the Router’s Security
Port Forwarding
In its default state, the Router blocks all external users from connecting to or
communicating with the network, making it safe from hackers who may try to
intrude on the network and damage it. However, the network can be exposed to
the Internet in certain limited and controlled ways to enable some applications to
work from the local network (game, voice, and chat applications, for example) and
to enable Internet access to servers in the network. Port forwarding (sometimes
referred to as local servers) supports both of these functions.
To grant Internet users access to servers inside the local network, each service provided, as well as the computer providing it, must be identified. To do this:
1. Select Port Forwarding from the left side of any Security screen. The “Port
Forwarding” screen appears.
2. Click Add. The “Add Port Forwarding Rule” screen appears.
3. Enter the local IP address or the host name of the computer providing the
service in the “Networked Computer/Device” text box, or select them from the
drop-down list. Note that only one local network computer can be assigned to
provide a specific service or application.
82
Page 88

Chapter 6 Configuring the Router’s Security
4. Select the Internet protocol to be provided from the “Protocol” drop-down
list. To see all options, select All Services.
5. Select a WAN connection type from the “WAN Connection Type” drop-down
list. Actiontec recommends selecting All Broadband Devices.
6. To select a port to forward communications to (this is optional), select Specify
from the “Forward to Port” drop-down list, then, in the text box that appears,
enter the port number. If no port is identified, select Same as Incoming Port.
7. If this port will be active all the time, select Always from the “When should this
rule occur?” drop-down list. If the rule will only be active at certain times, select
Specify Schedule and click Add. Then, add a schedule rule (for more details
about schedule rules, see the “Advanced Settings” chapter of this manual).
8. Click Apply to save the changes.
How many computers can use a service or play a game simultaneously? Well, the
answer may be a bit confusing. All the computers on the network can behave as
clients and use a specific service simultaneously. Being a client means the computer within the network initiates the connection; for example, a computer on the
network can open an FTP connection with an FTP server on the Internet. But only
one computer on the network can operate as a server and respond to requests from
computers on the Internet (outside the local network).
DMZ (Demilitarized Zone) Host
The DMZ host feature allows one device on the network to operate outside the fire-
wall. Designate a DMZ host:
• To use an Internet service, such as an online game or video-conferencing
program, not present in the Port Forwarding list and for which no port
range information is available.
• To expose one computer to all services without restriction or security.
Warning: A DMZ host is not protected by the firewall and may be
M
vulnerable to attack. Designating a DMZ host may also put other
computers in the local network at risk. When designating a DMZ
host, consider the security implications and protect it if necessary.
83
Page 89

Actiontec Wireless Broadband Router User Manual
85
Chapter 6 Configuring the Router’s Security
To designate a local computer as a DMZ host:
1. Select DMZ Host from the left side of any Security screen. The “DMZ Host”
screen appears.
2. Click in the “DMZ Host IP Address” check box, then enter the IP address of the
computer to be designated as a DMZ host. Note that only one network computer can be a DMZ host at any time.
3. Click Apply.
Click in the “DMZ Host IP Address” check box again to disable the DMZ host.
Port Triggering
Port triggering can be used for dynamic port forwarding configuration. By setting
port triggering rules, inbound traffic is allowed to arrive at a specific network host
using ports different than those used for the outbound traffic. The outbound traffic triggers which ports inbound traffic is directed.
For example, a gaming server is accessed using UDP protocol on port 2222. The
gaming server responds by connecting the user using UDP on port 3333 when
starting gaming sessions. In this case, port triggering must be used, since it conflicts with the following default firewall settings:
• The firewall blocks inbound traffic by default.
• The server replies to the Router’s IP, and the connection is not sent back to
the host, since it is not part of a session.
To resolve the conflict, a port triggering entry must be defined, which allows
inbound traffic on UDP port 3333, only after a network host generated traffic to
UDP port 2222. This results in accepting the inbound traffic from the gaming
server, and sending it back to the network host which originated the outgoing traffic to UDP port 2222.
84
Page 90

Chapter 6 Configuring the Router’s Security
To use port triggering:
1. Select Port Triggering from the left side of any Security screen. The “Port
Triggering” screen appears.
2. Select either “Specify Protocol” or “Show All Services” from the drop-down list
next to “Add.”
3. Click Add. An “Edit Service” screen appears.
4. Specify the port triggering entries by clicking New Trigger Ports and New
Opened Ports and entering the protocol and protocol number in the succeeding screens. For example, to set up port triggering for the scenario laid out on
the previous page, the service ports would be set to UDP and 2222, while the
opened ports would be set to UDP and 3333.
85
Page 91

Actiontec Wireless Broadband Router User Manual
87
Chapter 6 Configuring the Router’s Security
Remote Administration
The Router can be accessed and controlled not only from within the local network,
but also from the Internet using remote adminstration.
To access, select Remote Administration from the left side of any Security screen.
The “Remote Administration” screen appears.
Telnet
Telnet is used to create a command-line session and gain access to all system settings and parameters using a text-based terminal. Select the Telnet port to be used
by clicking in the appropriate check box, then click Apply.
86
Page 92

Chapter 6 Configuring the Router’s Security
MegaControl Panel
MegaControl Panel is used to obtain access to the Router’s MegaControl Panel and
gain access to all settings and parameters,using a web browser. Both secure (HTTPS)
and non-secure (HTTP) access is available. Select the port to be used by clicking in
the appropriate text box, then click Apply.
Note: Telnet and MegaControl Panel remote administration
☞
access may be used to modify or disable firewall settings. Local
IP addresses and other settings can also be changed, making
it difficult or impossible to access the Router from the local
network. Therefore, remote adminstration access to Telnet or
MegaControl Panel services should be activated only when
absolutely necessary.
Diagnostic Tools
Diagnostic Tools are used for troubleshooting and remote system management by a
user or the ISP.
Note: Encrypted remote administration is performed using a
☞
secure SSL connection, and requires an SSL certificate. When
accessing the Router for the first time using encrypted remote
administration, a warning appears regarding certificate authentication because the Router’s SSL certificate is self-generated. When
encountering this message under these circumstances, ignore it
and continue. Even though this message appears, the self-generated certificate is safe, and provides a secure SSL connection.
87
Page 93

Actiontec Wireless Broadband Router User Manual
89
Chapter 6 Configuring the Router’s Security
Website Blocking
The Router can be configured to block specific websites, preventing access to them
from computers on the local network. Restrictions can also be applied to a comprehensive, automatically updated table of sites to which access is not recommended. To view the table of websites currently being blocked, select Website Blocking
in any Security screen. To activate website blocking, click in the “Enable Website
Blocking” check box.
To add a new website to the table:
1. Click Add. The “Blocked Website” screen appears.
2. Enter the website’s address (IP or URL). All pages within the website will also be
blocked. If the website address has multiple IP addresses, the Router will resolve
all additional addresses and automatically add them to the restrictions table.
3. To apply website blocking to a single computer or group of computers on the
network, select them from the “Networked Computer/Device” drop-down list.
88
Page 94

Chapter 6 Configuring the Router’s Security
4. If website blocking needs to be active all the time, select Always from the “When
should this rule occur?” drop-down list. If the rule will only be active at certain
times, select Specify Schedule and click Add. Then, add a schedule rule (for more
details about schedule rules, see the “Advanced Settings” chapter of this manual).
Note: Make sure the Router’s date and time are set correctly for
☞
the local time zone.
5. Click Apply to add the website to the table. The previous screen appears while
the Router attempts to find the site. “Resolving...” appears in the “Status” column while the website is being located.
6. If the site is successfully located, “Resolved” appears in the Status column. If
not, “Hostname Resolution Failed” appears. Click Refresh to update the status,
if necessary. If the Router fails to locate the website, do the following:
• Use a web browser to verify the website is available. If it is, the website
address was entered incorrectly. See “Modifying a Website Address,” below.
• If the website is not available, return to the Website Blocking screen at a
later time and click Resolve Now to verify the website can be found and is
blocked by the Router.
Modifying a Website Address
To modify a website address currently in the table:
1. Click the appropriate icon in the “Action” column. The “Blocked Website”
screen appears.
2. Modify the website address, group, and schedule as necessary. Omit the
“http://” at the beginning and the “/” at the end of the address.
3. Click Apply to save changes.
89
Page 95

Actiontec Wireless Broadband Router User Manual
91
Chapter 6 Configuring the Router’s Security
Static NAT
This option allows multiple public addresses to be designated to devices on the
network. Static NAT allows devices behind a firewall and configured with private IP
addresses appear to have public IP addresses on the Internet. This allows an internal host, such as a web server, to have an unregistered (private) IP address and still
be reachable over the Internet. To do this:
1. Select Static NAT from any Security screen. The “Static NAT” screen appears.
2. Click Add. The “Add Static NAT” screen appears.
3. Enter the name of the computer to be used as the local host, or, to enter a
specific IP address, select Specify Address from the “Networked Computer/
Device” drop-down list and enter the IP address in the box on the right.
4. Enter a public IP address assigned by the ISP in the “Public IP Address”
text box.
5. Select a connection from the “WAN Connection Type” drop-down list.
6. Select the protocol that needs to be accessible from the public IP address by
clicking in the check box next to “Enable Port Forwarding for Static NAT,” then
selecting a protocol from the drop-down menu. Use “Any” to pass all data. Click
Apply, and Apply again.
Repeat these steps to add more static IP addresses from the network.
90
Page 96

Chapter 6 Configuring the Router’s Security
Advanced Filtering
Advanced filtering is designed to allow comprehensive control over the firewall’s
behavior. Specific input and output rules can be defined, the order of logically
similar sets of rules controlled, and distinctions made between rules that apply to
Internet and local network devices.
To access, select Advanced Filtering from any Security screen. The “Advanced
Filtering” screen appears.
Two sets of rules can be configured: input rules and output rules. Each set of rules
comprises three subsets: initial rules, network devices rules, and final rules. These
subsets determine the sequence by which the rules will be applied. Following is a
description of the set ordering for inbound and outbound packets.
91
Page 97

Actiontec Wireless Broadband Router User Manual
93
Chapter 6 Configuring the Router’s Security
Inbound Packets - Input Rule Sets
• Initial rules
• All rules defined for the network device on which the packet is
• Local servers rules from the local server tab in the security screen
• Rules to accept all the packets on a device in case the firewall check
box “Internet Connection Firewall” in the connection settings screen is
unchecked
• Remote administration rules from the remote administration tab
• DMZ host rules from the DMZ tab
• Final rules
Outbound Packets - Output Rules Sets
• Initial rules
• All rules defined for the network device on which the packet is
• Rules to accept all the packets on a device in case the firewall check
box “Internet Connection Firewall” in the connection settings screen is
unchecked
• IP/hostname filtering rules and access control rules from the tabs in the
security screen
• Final rules
There are numerous rules automatically inserted by the firewall in order to provide
improved security and block harmful attacks.
92
Page 98

Chapter 6 Configuring the Router’s Security
To configure advanced filtering rules, click Add next to the rule title. The “Add
Advanced Filter” screen appears.
To add an advanced filtering rule, define the following rule parameters:
Matching
To apply a firewall rule, a match must be made between IP addresses or ranges
and ports. Use the “Source Address” and “Destination Address” drop-down lists to
define the coupling of source and destination traffic. Port matching will be defined
when selecting protocols. For example, if the FTP protocol is selected, port 21 will be
checked for matching traffic flow between the defined source and destination IPs.
Operation
This is where the action the rule will take is defined. Select one of the following
radio buttons:
• Drop - Deny access to packets that match the source and destination IP
addresses and protocol ports defined in “Matching.”
• Reject - Deny access to packets that match the source and destination IP
addresses and protocol ports defined in upper section of the screen, and
send an ICMP error or a TCP reset to the origination peer.
93
Page 99

Actiontec Wireless Broadband Router User Manual
95
Chapter 6 Configuring the Router’s Security
• Accept - Allow access to packets that match the source and destination IP
addresses and protocol ports defined in upper section of the screen. The
data transfer session will be handled using Stateful Packet Inspection (SPI).
• Accept Packet - Allow access to packets that match the source and destination IP addresses and protocol ports defined in upper section of the
screen. The data transfer session will not be handled using Stateful Packet
Inspection (SPI), so other packets that match this rule will not be automati-
cally allowed access. This setting is useful when creating rules that allow
broadcasting.
Logging
Click in this check box to add entries relating to this rule to the security log.
Scheduler (When should this rule occur?)
If advanced filtering needs to be active all the time, select “Always” from the “When
should this rule occur?” drop-down list. If the rule will only be active at certain times
select Specify Schedule and click Add. Then, add a schedule rule (for more details
about schedule rules, see the “Advanced Settings” chapter of this manual)
Security Log
The security log displays a list of firewall-related events, including attempts to
establish inbound and outbound connections, attempts to authenticate at an
administrative interface (MegaControl Panel or Telnet terminal), firewall configuration, and system start-up.
To access the security log, select Security Log from any Security screen. The
“Security Log” screen appears.
94
Page 100

Chapter 6 Configuring the Router’s Security
Time
The time (based on the Router’s date and time settings) the event occurred.
Event
There are five kinds of events listed in the system log:
• Inbound Traffic - a result of an incoming packet
• Outbound Traffic - a result of an outgoing packet.
• Firewall Setup - configuration message
• WBM Login - a user logged in to WBM
• CLI Login - a user logged in to the command line interface via Telnet
Event-Type
Displays a textual description of the event.
Details
The “Details” column displays more information about the packet or the event,
such as protocol, IP addresses, ports, etc. The following are the available event types
that can be recorded in the security log:
• Firewall internal - from the firewall internal mechanism, in case this eventtype is recorded, an accompanying explanation will be added.
• Firewall status changed - the firewall changed status from up to down or
the vice versa, as specified in the event type description.
• STP packet - an STP (Spanning Tree Protocol) packet has been accepted/
rejected.
• Illegal packet options - the options field in the packet’s header is either illegal or forbidden.
• Fragmented packet - a fragment has been rejected.
• WinNuke protection - a WinNuke attack has been blocked.
95
 Loading...
Loading...