Fortinet FortiGate 60B User Manual
I N S T A L L G U I D E
FortiGate-60B
FortiOS 3.0 MR6
www.fortinet.com

FortiGate-60B Install Guide
FortiOS 3.0 MR6 10 September 2008
01-30006-0446-20080910
© Copyright 2008 Fortinet, Inc. All rights reserved. No part of this publication including text, examples, diagrams or illustrations may be reproduced, transmitted, or translated in any form or by any means, electronic, mechanical, manual, optical or otherwise, for any purpose, without prior written permission of Fortinet, Inc.
Trademarks
Fortinet, FortiGate and FortiGuard are registered trademarks and Dynamic Threat Prevention System (DTPS), APSecure, FortiASIC, FortiBIOS, FortiBridge, FortiClient, FortiGate, FortiGate Unified Threat Management System, FortiGuard-Antispam, FortiGuard-Antivirus, FortiGuard-Intrusion, FortiGuard-Web, FortiLog, FortiAnalyzer, FortiManager, FortiOS, FortiPartner, FortiProtect, FortiReporter, FortiResponse, FortiShield, and FortiVoIP, are trademarks of Fortinet, Inc. in the United States and/or other countries. The names of actual companies and products mentioned herein may be the trademarks of their respective owners.
Regulatory compliance
FCC Class B Part 15 CSA/CUS
.
! Caution: Risk of Explosion if Battery is replaced by an Incorrect Type. Dispose of Used Batteries According to the Instructions.

Contents
Contents |
|
Contents.............................................................................................. |
3 |
Introduction ........................................................................................ |
7 |
Register your FortiGate unit............................................................................. |
7 |
About the FortiGate-60B ................................................................................... |
8 |
About this document......................................................................................... |
8 |
Document conventions.................................................................................. |
8 |
Typographic conventions .............................................................................. |
9 |
Further Reading................................................................................................. |
9 |
Fortinet Knowledge Center ......................................................................... |
10 |
Comments on Fortinet technical documentation......................................... |
10 |
Customer service and technical support ...................................................... |
10 |
Installing ........................................................................................... |
11 |
Environmental specifications......................................................................... |
11 |
Cautions and warnings ................................................................................... |
12 |
Grounding ................................................................................................... |
12 |
Rack mount instructions.............................................................................. |
12 |
Mounting ..................................................................................................... |
13 |
Plugging in the FortiGate................................................................................ |
13 |
Connecting to the network .......................................................................... |
13 |
Turning off the FortiGate unit......................................................................... |
13 |
Configuring....................................................................................... |
15 |
NAT vs. Transparent mode............................................................................. |
15 |
NAT mode ................................................................................................... |
15 |
Transparent mode....................................................................................... |
16 |
Connecting to the FortiGate unit.................................................................... |
16 |
Connecting to the web-based manager ...................................................... |
16 |
Connecting to the CLI ................................................................................. |
17 |
Configuring NAT mode ................................................................................... |
18 |
Using the web-based manager ................................................................... |
18 |
Configure the interfaces........................................................................ |
18 |
Configure a DNS server........................................................................ |
19 |
Adding a default route and gateway ..................................................... |
19 |
Adding firewall policies ......................................................................... |
20 |
Using the CLI .............................................................................................. |
21 |
Configure the interfaces........................................................................ |
21 |
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
01-30006-0446-20080910 |
3 |
Contents
Configure a DNS server ....................................................................... |
22 |
Adding a default route and gateway ..................................................... |
22 |
Adding firewall policies ......................................................................... |
23 |
Configuring Transparent mode...................................................................... |
23 |
Using the web-based manager ................................................................... |
24 |
Switching to Transparent mode............................................................ |
24 |
Configure a DNS server ....................................................................... |
24 |
Adding firewall policies ......................................................................... |
24 |
Using the CLI .............................................................................................. |
25 |
Switching to Transparent mode............................................................ |
25 |
Configure a DNS server ....................................................................... |
26 |
Adding firewall policies ......................................................................... |
26 |
Verify the configuration .................................................................................. |
27 |
Backing up the configuration......................................................................... |
27 |
Restoring a configuration............................................................................... |
28 |
Additional configuration................................................................................. |
28 |
Set the time and date.................................................................................. |
28 |
Set the Administrator password .................................................................. |
28 |
Configure FortiGuard .................................................................................. |
29 |
Updating antivirus and IPS signatures ................................................. |
29 |
Advanced configuration.................................................................. |
31 |
Protection profiles........................................................................................... |
31 |
Firewall policies............................................................................................... |
32 |
Configuring firewall policies ........................................................................ |
33 |
Antivirus options............................................................................................. |
33 |
AntiSpam options............................................................................................ |
34 |
Web filtering..................................................................................................... |
35 |
Logging ............................................................................................................ |
36 |
Configuring the modem interface .................................................. |
37 |
Selecting a modem mode ............................................................................... |
37 |
Redundant mode ........................................................................................ |
37 |
Stand alone mode....................................................................................... |
38 |
Configuring modem settings.......................................................................... |
38 |
Configuring the modem using the CLI .......................................................... |
40 |
Syntax................................................................................................... |
40 |
Example................................................................................................ |
43 |
Adding a Ping Server ...................................................................................... |
44 |
Dead gateway detection ............................................................................. |
44 |
Adding firewall policies for modem connections......................................... |
45 |
Administrative access through the modem port.......................................... |
45 |
|
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
4 |
01-30006-0446-20080910 |

Contents
Configuring the PCMCIA modem card .......................................................... |
45 |
FortiGate Firmware .......................................................................... |
47 |
Downloading firmware .................................................................................... |
47 |
Using the web-based manager....................................................................... |
48 |
Upgrading the firmware............................................................................... |
48 |
Reverting to a previous version................................................................... |
48 |
Backup and Restore from a USB key ......................................................... |
49 |
Using the USB Auto-Install.......................................................................... |
49 |
Using the CLI.................................................................................................... |
50 |
Reverting to a previous version................................................................... |
51 |
Installing firmware from a system reboot using the CLI.............................. |
52 |
Restoring the previous configuration........................................................... |
54 |
Backup and Restore from a USB key ......................................................... |
54 |
Using the USB Auto-Install.......................................................................... |
55 |
Additional CLI Commands for a USB key ................................................... |
55 |
Testing new firmware before installing ......................................................... |
56 |
Index.................................................................................................. |
59 |
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
01-30006-0446-20080910 |
5 |
Contents
|
|
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
6 |
01-30006-0446-20080910 |
|

|
|
|
Introduction |
Register your FortiGate unit |
Introduction
Welcome and thank you for selecting Fortinet products for your real-time network protection.
The FortiGate Unified Threat Management System improves network security, reduces network misuse and abuse, and helps you use communications resources more efficiently without compromising the performance of your network. The FortiGate Unified Threat Management System are ICSA-certified for firewall, IPSec, and antivirus services.
The FortiGate Unified Threat Management Systemis a dedicated, easily managed security device that delivers a full suite of capabilities, which include:
•application-level services such as virus protection and content filtering
•network-level services such as firewall, intrusion detection, VPN and traffic shaping
The FortiGate Unified Threat Management System uses Fortinet’s Dynamic Threat Prevention System (DTPS™) technology, which leverages breakthroughs in chip design, networking, security and content analysis. The unique ASIC-based architecture analyzes content and behavior in real-time, enabling key applications to be deployed right at the network edge where they are most effective at protecting your networks.
Register your FortiGate unit
Register the FortiGate unit by visiting http://support.fortinet.com and select Product Registration.
To register, enter your contact information and the serial numbers of the FortiGate units that you or your organization have purchased. You can register multiple FortiGate units in a single session without re-entering your contact information.
By registering your FortiGate unit, you will receive updates to threat detection and prevention databases (Antivirus, Intrusion Detection, etc.) and will also ensure your access to technical support.
For more information, see the Fortinet Knowledge Centre article “Registration Frequently Asked Questions” (http://kc.forticare.com/default.asp?id=2071).
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
01-30006-0446-20080910 |
7 |

About the FortiGate-60B |
Introduction |
About the FortiGate-60B
The FortiGate-60B multi-threat security solution offers Small and Medium Business and SOHO/ROBO users enterprise-class protection against blended threats targeting 3G broadband, wireless LAN and wired infrastructure. The FortiGate-60B supports a wide array of wireless broadband PC Cards. The FortiGate-60B offers enterprise-class security for the SOHO/ROBO users and the flexibility needed for quick Point of Sales deployment.
FortiGate-60B offers a PC Card slot, dual WAN link support for redundant internet connections, a DMZ port and 6 built-in switch ports. The FortiGate-60B also offers an integrated analog modem for dial backup capability.
The FortiGate-60B is ideal for small businesses and enterprise remote offices where complete security including Firewall, IPSec and SSL VPN, Intrusion prevention, Antivirus, Web filtering and Antispam are needed.
The FortiGate-60B also supports wide range of 3G wireless PC Cards for instant Point of Sales deployment.
Figure 1: FortiGate-60B
|
|
1 |
INTERNAL |
5 |
|
|
3 |
||
POWER STATUS HA ALARM |
WAN 1 WAN 2 DMZ |
2 |
4 |
6 |
|
|






 B
B
About this document
This document explains how to install and configure your FortiGate unit onto your network. This document also includes how to install and upgrade new firmware versions on your FortiGate unit.
This document contains the following chapters:
•Installing – Describes setting up and powering on a FortiGate unit.
•Configuring – Provides an overview of the operating modes of the FortiGate unit and how to integrate the FortiGate unit into your network.
•Advanced configuration – Describes additional configuration you can perform on the FortiGate unit to enhance network protection, including antivirus, antispam, firewall configuration and logging.
•Configuring the modem interface – This chapter describes the modem interface configuration options. The FortiGate unit supports the modem interface only when running in NAT/Route mode.
•FortiGate Firmware – Describes how to install, update, restore and test firmware for the FortiGate device.
Document conventions
The following document conventions are used in this guide:
•In the examples, private IP addresses are used for both private and public IP addresses.
•Notes and Cautions are used to provide important information:
|
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
8 |
01-30006-0446-20080910 |
|
|
|
Introduction |
Further Reading |
Note: Highlights useful additional information.
Caution: Warns you about commands or procedures that could have unexpected or ! undesirable results including loss of data or damage to equipment.
Typographic conventions
FortiGate documentation uses the following typographical conventions:
Convention |
Example |
|
|
Keyboard input |
In the Gateway Name field, type a name for the remote VPN |
|
peer or client (for example, Central_Office_1). |
Code examples |
config sys global |
|
set ips-open enable |
|
end |
CLI command syntax |
config firewall policy |
|
edit id_integer |
|
set http_retry_count <retry_integer> |
|
set natip <address_ipv4mask> |
|
end |
Document names |
FortiGate Administration Guide |
|
|
Menu commands |
Go to VPN > IPSEC > Phase 1 and select Create New. |
|
|
Program output |
Welcome! |
Variables |
<address_ipv4> |
Further Reading
The most up-to-date publications and previous releases of Fortinet product documentation are available from the Fortinet Technical Documentation web site at http://docs.forticare.com.
The following FortiGate product documentation is available:
•FortiGate QuickStart Guide
Provides basic information about connecting and installing a FortiGate unit.
•FortiGate Administration Guide
Provides basic information about how to configure a FortiGate unit, including how to define FortiGate protection profiles and firewall policies; how to apply intrusion prevention, antivirus protection, web content filtering, and spam filtering; and how to configure a VPN.
•FortiGate online help
Provides a context-sensitive and searchable version of the Administration Guide in HTML format. You can access online help from the web-based manager as you work.
•FortiGate CLI Reference
Describes how to use the FortiGate CLI and contains a reference to all FortiGate CLI commands.
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
01-30006-0446-20080910 |
9 |
Customer service and technical support |
Introduction |
•FortiGate Log Message Reference
Available exclusively from the Fortinet Knowledge Center, the FortiGate Log Message Reference describes the structure of FortiGate log messages and provides information about the log messages that are generated by FortiGate units.
•FortiGate High Availability User Guide
Contains in-depth information about the high availability feature and the clustering protocol.
•FortiGate IPS User Guide
Describes how to configure the FortiGate Intrusion Prevention System settings and how the FortiGate IPS deals with some common attacks.
•FortiGate IPSec VPN User Guide
Provides step-by-step instructions for configuring IPSec VPNs using the web-based manager.
•FortiGate SSL VPN User Guide
Compares FortiGate IPSec VPN and FortiGate SSL VPN technology, and describes how to configure web-only mode and tunnel-mode SSL VPN access for remote users through the web-based manager.
•FortiGate PPTP VPN User Guide
Explains how to configure a PPTP VPN using the web-based manager.
•FortiGate Certificate Management User Guide
Contains procedures for managing digital certificates including generating certificate requests, installing signed certificates, importing CA root certificates and certificate revocation lists, and backing up and restoring installed certificates and private keys.
•FortiGate VLANs and VDOMs User Guide
•Describes how to configure VLANs and VDOMS in both NAT/Route and Transparent mode. Includes detailed examples.
Fortinet Knowledge Center
The Knowledge Center contains troubleshooting and how-to articles, FAQs, technical notes, and more. Visit the Fortinet Knowledge Center at http://kc.forticare.com.
Comments on Fortinet technical documentation
Please send information about any errors or omissions in this document, or any Fortinet technical documentation, to techdoc@fortinet.com.
Customer service and technical support
Fortinet Technical Support provides services designed to make sure that your Fortinet systems install quickly, configure easily, and operate reliably in your network.
Please visit the Fortinet Technical Support web site at http://support.fortinet.com to learn about the technical support services that Fortinet provides.
|
|
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
|
|
|
|
|
|
|
|
10 |
01-30006-0446-20080910 |
|

|
|
|
Installing |
Environmental specifications |
Installing
This chapter describes installing your FortiGate unit in your server room, environmental specifications and how to mount the FortiGate in a rack if applicable.
This chapter contains the following topics:
•Environmental specifications
•Cautions and warnings
•Plugging in the FortiGate
•Plugging in the FortiGate
•Turning off the FortiGate unit
Environmental specifications
•Operating temperature: 32 to 104°F (0 to 40°C)
If you install the FortiGate unit in a closed or multi-unit rack assembly, the operating ambient temperature of the rack environment may be greater than room ambient temperature. Therefore, make sure to install the equipment in an environment compatible with the manufacturer's maximum rated ambient temperature.
•Storage temperature: -13 to 158°F (-25 to 70°C)
•Humidity: 5 to 90% non-condensing
•Air flow - For rack installation, make sure that the amount of air flow required for safe operation of the equipment is not compromised.
•For free-standing installation, make sure that the appliance has at least 1.5 in. (3.75 cm) of clearance on each side to allow for adequate air flow and cooling.
This device complies with part FCC Class A, Part 15, UL/CUL, C Tick, CE and VCCI. Operation is subject to the following two conditions:
•This device may not cause harmful interference, and
•This device must accept any interference received, including interference that may cause undesired operation.
This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses and can radiate radio frequency energy and, if not installed and used in accordance with the instructions, may cause harmful interference to radio communications. However, there is no guarantee that interference will not occur in a particular installation. If this equipment does cause harmful interference to radio or television reception, which can be determined by turning the equipment off and on, the user is encouraged to try to correct the interference by one or more of the following measures:
•Reorient or relocate the receiving antenna.
•Increase the separation between the equipment and receiver.
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
01-30006-0446-20080910 |
11 |
Cautions and warnings |
Installing |
•Connect the equipment into an outlet on a circuit different from that to which the receiver is connected.
•Consult the dealer or an experienced radio/TV technician for help.
The equipment compliance with FCC radiation exposure limit set forth for uncontrolled Environment.
Cautions and warnings
Review the following cautions before installing your FortiGate unit.
!
!
Grounding
Caution: Risk of Explosion if battery is replaced by an incorrect type. Dispose of used batteries according to the instructions
Caution: To reduce the risk of fire, use only No. 26 AWG or larger UL Listed or CSA Certified Telecommunication Line Cord.
•Ensure the FortiGate unit is connected and properly grounded to a lightning and surge protector. WAN or LAN connections that enter the premises from outside the building should be connected to an Ethernet CAT5 (10/100 Mb/s) surge protector.
•Shielded Twisted Pair (STP) Ethernet cables should be used whenever possible rather than Unshielded Twisted Pair (UTP).
•Do not connect or disconnect cables during lightning activity to avoid damage to the FortiGate unit or personal injury.
Rack mount instructions
Elevated Operating Ambient - If installed in a closed or multi-unit rack assembly, the operating ambient temperature of the rack environment may be greater than room ambient. Therefore, consideration should be given to installing the equipment in an environment compatible with the maximum ambient temperature (Tma) specified by the manufacturer.
Reduced Air Flow - Installation of the equipment in a rack should be such that the amount of air flow required for safe operation of the equipment is not compromised.
Mechanical Loading - Mounting of the equipment in the rack should be such that a hazardous condition is not achieved due to uneven mechanical loading.
Circuit Overloading - Consideration should be given to the connection of the equipment to the supply circuit and the effect that overloading of the circuits might have on overcurrent protection and supply wiring. Appropriate consideration of equipment nameplate ratings should be used when addressing this concern.
Reliable Earthing - Reliable earthing of rack-mounted equipment should be maintained.
Particular attention should be given to supply connections other than direct connections to the branch circuit (e.g. use of power strips).
|
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
12 |
01-30006-0446-20080910 |

|
|
|
Installing |
Plugging in the FortiGate |
Mounting
If required to fit into a rack unit, remove the rubber feet from the bottom of the FortiGate unit.
Adhere the rubber feet included in the package to the underside of the FortiGate unit, near the corners of the device.
Place the FortiGate unit on any flat, stable surface. Ensure the unit has sufficient clearance on each side to ensure adequate airflow for cooling.
Plugging in the FortiGate
Use the following steps to connect the power supply to the FortiGate unit.
To power on the FortiGate unit
1Connect the AC adapter to the power connection at the back of the FortiGate unit.
2Connect the AC adapter to the power cable.
3Connect the power cable to a power outlet.
The FortiGate unit starts and the Power and Status LEDs light up. The Status LEDs flash while the FortiGate unit starts up, and remain lit when the system is running.
Connecting to the network
Using the supplied Ethernet cable, connect one end of the cable to your router or modem, whatever the connection is to the Internet. Connect the other end to the FortiGate unit. Connect to either the External, WAN port, or port 1. Connect additional cable to the Internal port or port 2 and your internal hub or switch.
Turning off the FortiGate unit
Always shut down the FortiGate operating system properly before turning off the power switch to avoid potential hardware problems.
To power off the FortiGate unit
1From the web-based manager, go to System > Status.
2In the Unit Operation display, select Shutdown, or from the CLI enter: execute shutdown
3Disconnect the power cables from the power supply.
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
01-30006-0446-20080910 |
13 |
Turning off the FortiGate unit |
Installing |
|||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
14 |
01-30006-0446-20080910 |
|
|
Configuring |
NAT vs. Transparent mode |
Configuring
This section provides an overview of the operating modes of the FortiGate unit, NAT/Route and Transparent, and how to configure the FortiGate unit for each mode. There are two ways you can configure the FortiGate unit, using the web-based manager or the command line interface (CLI). This section will step through using both methods. Use whichever you are most comfortable with.
This section includes the following topics:
•NAT vs. Transparent mode
•Connecting to the FortiGate unit
•Verify the configuration
•Backing up the configuration
•Additional configuration
NAT vs. Transparent mode
The FortiGate unit can run in two different modes, depending on your network infrastructure and requirements. You have a choice between NAT/Route mode and Transparent mode. Both include the same robust network security features such as antispam, antivirus, VPN and firewall policies.
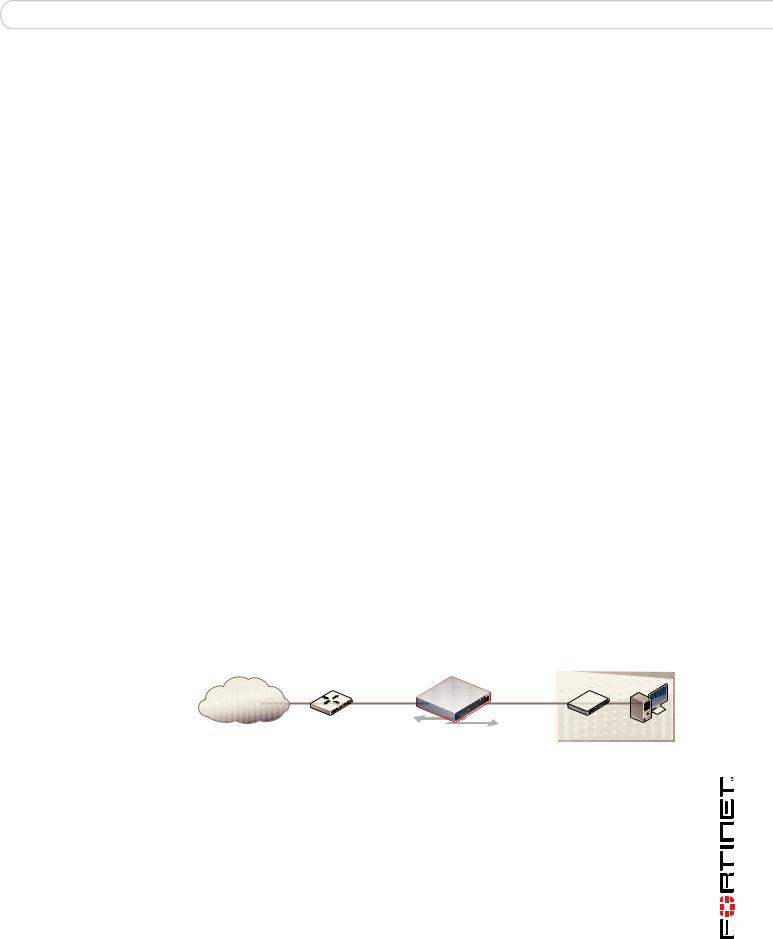
NAT mode
In NAT/Route mode, the FortiGate unit is visible to the network. Like a router, all its interfaces are on different subnets.
In NAT mode, each port is on a different subnet, enabling you to have a single IP address available to the public Internet. The FortiGate unit performs network address translation before it sends and receives the packet to the destination network.
In Route mode, there is no address translation.
Figure 2: FortiGate unit in NAT mode
Internet |
204.23.1.5 |
192.168.1.99 |
|
|
Router
NAT mode policies controlling traffic between internal and external networks.
Internal network
192.168.1.20
You typically use NAT/Route mode when the FortiGate unit is operating as a gateway between private and public networks. In this configuration, you would create NAT mode firewall policies to control traffic flowing between the internal, private network and the external, public network, usually the Internet.
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
01-30006-0446-20080910 |
15 |
Connecting to the FortiGate unit |
Configuring |
Transparent mode
In Transparent mode, the FortiGate unit is invisible to the network. Similar to a network bridge, all FortiGate interfaces must be on the same subnet. You only have to configure a management IP address to make configuration changes. The management IP address is also used for antivirus and attack definition updates.
Figure 3: FortiGate unit in Transparent mode
|
|
|
|
10.10.10.1 |
|
|
|
|
Management IP |
|
Gateway to public network |
|
Internal Network |
|
|
|
|
||
Internet |
204.23.1.2 |
10.10.10.2 |
External |
Internal |
|
|
Router |
|
10.10.10.3 |
|
|
|
Transparent mode policies |
|
|
|
|
controlling traffic between |
|
|
|
|
internal and external networks. |
|
You typically use the FortiGate unit in Transparent mode on a private network behind an existing firewall or behind a router. The FortiGate unit performs firewall functions, IPSec VPN, virus scanning, IPS web filtering, and Spam filtering.
Connecting to the FortiGate unit
To configure, maintain and administer the FortiGate unit, you need to connect to it.
There are two methods for these tasks:
•using the web-based manger, a GUI interface using a current web browser such as FireFox or Internet Explorer.
•using the command line interface (CLI), a command line interface similar to DOS or UNIX commands using an SSH terminal or Telnet terminal.
Connecting to the web-based manager
To connect to the web-based manager, you require:
•a computer with an Ethernet connection
•Microsoft Internet Explorer version 6.0 or higher or any recent version of the most popular web browser
•an Ethernet cable.
To connect to the web-based manager
1Set the IP address of the management computer to the static IP address 192.168.1.2 with a netmask of 255.255.255.0.
2Using the Ethernet cable, connect the internal interface of the FortiGate unit to the computer Ethernet connection.
3Start your browser and enter the address https://192.168.1.99. (remember to include the “s” in https://).
|
|
|
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
16 |
01-30006-0446-20080910 |
||
|
|
Configuring |
Connecting to the FortiGate unit |
To support a secure HTTPS authentication method, the FortiGate unit ships with a self-signed security certificate, which is offered to remote clients whenever they initiate a HTTPS connection to the FortiGate unit. When you connect, the FortiGate unit displays two security warnings in a browser.
The first warning prompts you to accept and optionally install the FortiGate unit’s self-signed security certificate. If you do not accept the certificate, the FortiGate unit refuses the connection. If you accept the certificate, the FortiGate login page appears. The credentials entered are encrypted before they are sent to the FortiGate unit. If you choose to accept the certificate permanently, the warning is not displayed again.
Just before the FortiGate login page is displayed, a second warning informs you that the FortiGate certificate distinguished name differs from the original request. This warning occurs because the FortiGate unit redirects the connection. This is an informational message. Select OK to continue logging in.
4 Type admin in the Name field and select Login.
Connecting to the CLI
To connect to the FortiGate CLI you require:
•a computer with an available communications port
•a serial cable, either a RJ-45 to DB-9 or null modem cable, whichever was included in your FortiGate package
•terminal emulation software such as HyperTerminal for Microsoft Windows
Note: The following procedure uses Microsoft Windows HypterTerminal software. You can apply these steps to any terminal emulation program.
To connect to the CLI
1Connect the serial cable to the communications port of your computer and to the FortiGate console port.
2Start HyperTerminal, enter a name for the connection and select OK.
3Configure HyperTerminal to connect directly to the communications port on your computer and select OK.
4Select the following port settings and select OK:
Bits per second |
9600 |
Data bits |
8 |
Parity |
None |
Stop bits |
1 |
Flow control |
None |
5Press Enter to connect to the FortiGate CLI.
6When the login prompt appears, type admin and press Enter twice.
Type ? to list available commands. For information about how to use the CLI, see the FortiGate CLI Reference.
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
01-30006-0446-20080910 |
17 |
Configuring NAT mode |
Configuring |
Configuring NAT mode
Configuring NAT mode involves defining interface addresses and default routes, and simple firewall policies. You can use the web-based manager or the CLI to configure the FortiGate unit in NAT/Route mode.
Using the web-based manager
After connecting to the web-based manager, you can use the following procedures to complete the basic configuration of the FortiGate unit. Ensure you read the section “Connecting to the web-based manager” on page 16 before beginning.
Configure the interfaces
When shipped, the FortiGate unit has a default address of 192.168.1.99 and a netmask of 255.255.255.0. for either the Port 1 or Internal interface. You need to configure this and other ports for use on your network.
To configure interfaces
1Go to System > Network > Interface.
2Select the edit icon for an interface.
3Set the Addressing Mode for the interface.
•For Manual addressing, enter the IP address and netmask for the interface.
•For DHCP addressing, select DHCP and complete the following:
Distance |
Enter the administrative distance, between 1 and 255 for the |
|
default gateway retrieved from the DHCP server. The |
|
administrative distance specifies the relative priority of a route |
|
when there are multiple routes to the same destination. A |
|
lower administrative distance indicates a more preferred route. |
Retrieve default gateway from server
Override internal DNS
Enable to retrieve a default gateway IP address from the DHCP server. The default gateway is added to the static routing table.
Enable to use the DNS addresses retrieved from the DHCP server instead of the DNS server IP addresses on the DNS page on System > Network > Options. On FortiGate-100 units and lower, you should also enable Obtain DNS server address automatically in System > Network > Options.
•For PPPoE addressing, select PPPoE, and complete the following:
|
|
Username |
Enter the username for the PPPoE server. This may have |
|
|
|
been provided by your ISP. |
|
|
Password |
Enter the password for the PPPoE server for the above user |
|
|
|
name. |
|
|
Unnumbered |
Specify the IP address for the interface. If your ISP has |
|
|
|
assigned you a block of IP addresses, use one of these IP |
|
|
|
addresses. Alternatively, you can use, or borrow, the IP |
|
|
|
address of a configured interface on the router. You may need |
|
|
|
to do this to minimize the number of unique IP addresses |
|
|
|
within your network. |
|
|
|
If you are borrowing an IP address remember the interface |
|
|
|
must be enabled, or up to function correctly. |
|
|
Initial Disc Timeout |
Initial discovery timeout in seconds. The time to wait before |
|
|
|
starting to retry a PPPoE discovery. To disable the discovery |
|
|
|
timeout, set the value to 0. |
|
|
|
|
|
|
|
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
18 |
01-30006-0446-20080910 |
|
|
|
Configuring |
Configuring NAT mode |
Initial PADT Timeout |
Initial PPPoE Active Discovery Terminate (PADT) timeout in |
|
seconds. Use this timeout to shut down the PPPoE session if it |
|
is idle for this number of seconds. Your ISP must support |
|
PADT. To disable the PADT timeout, set the value to 0. |
Distance |
Enter the administrative distance, between 1 and 255 for the |
|
default gateway retrieved from the DHCP server. The |
|
administrative distance specifies the relative priority of a route |
|
when there are multiple routes to the same destination. A |
|
lower administrative distance indicates a more preferred route. |
Retrieve default gateway Enable to retrieve a default gateway IP address from the |
|
from server |
DHCP server. The default gateway is added to the static |
|
routing table. |
Override internal DNS |
Enable to use the DNS addresses retrieved from the DHCP |
|
server instead of the DNS server IP addresses on the DNS |
|
page on System > Network > Options. On FortiGate-100 |
|
units and lower, you should also enable Obtain DNS server |
|
address automatically in System > Network > Options. |
4Select OK.
5Repeat this procedure for each interface as required.
Note: If you change the IP address of the interface you are connecting to, you must connect through a web browser again using the new address. Browse to https:// followed by the new IP address of the interface. If the new IP address of the interface is on a different subnet, you may have to change the IP address of your computer to the same subnet.
Configure a DNS server
A DNS server is a service that converts symbolic node names to IP addresses. A domain name server (DNS server) implements the protocol. In simple terms, it acts as a phone book for the Internet. A DNS server matches domain names with the computer IP address. This enables you to use readable locations, such as fortinet.com when browsing the Internet.
DNS server IP addresses are typically provided by your internet service provider.
To configure DNS server settings
1Go to System > Network > Options.
2Enter the IP address of the primary DNS server.
3Enter the IP address of the secondary DNS server.
4Select Apply.
Adding a default route and gateway
A route provides the FortiGate unit with the information it needs to forward a packet to a particular destination. A static route causes packets to be forwarded to a destination other than the default gateway. You define static routes manually. Static routes control traffic exiting the FortiGate unit-you can specify through which interface the packet will leave and to which device the packet should be routed.
In the factory default configuration, entry number 1 in the Static Route list is associated with a destination address of 0.0.0.0/0.0.0.0, which means any/all destinations. This route is called the "static default route". If no other routes are present in the routing table and a packet needs to be forwarded beyond the FortiGate unit, the factory configured static default route causes the FortiGate unit to forward the packet to the default gateway.
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
01-30006-0446-20080910 |
19 |
Configuring NAT mode |
Configuring |
For an initial configuration, you must edit the factory configured static default route to specify a different default gateway for the FortiGate unit. This will enable the flow of data through the FortiGate unit.
For details on adding additional static routes, see the FortiGate Administration Guide.
To modify the default gateway
1Go to Router > Static.
2Select Edit for the default route
3In the Gateway field, type the IP address of the next-hop router where outbound traffic is directed.
4If the FortiGate unit reaches the next-hop router through a different interface (compared to the interface that is currently selected in the Device field), select the name of the interface from the Device field.
5Select OK.
Adding firewall policies
Firewall policies enable traffic to flow through the FortiGate interfaces. Firewall policies define how the FortiGate unit processes the packets in a communication session. You can configure the firewall policies to allow only specific traffic, users and specific times when traffic is allowed.
For the initial installation, a single firewall policy that enables all traffic through will enable you to verify your configuration is working. On lower-end units such a default firewall policy is already in place. For the higher end FortiGate units, you will need to add a firewall policy.
The following steps add two policies that allows all traffic through the FortiGate unit, to enable you to continue testing the configuration on the network.
To add an outgoing traffic firewall policy
1Go to Firewall > Policy.
2Select Create New.
3Set the following and select OK.
Source Interface |
Select the port connected to the network. |
Source Address |
All |
Destination Interface Select the port connected to the Internet.
Destination Address All
Schedule |
always |
Service |
Any |
Action |
Accept |
To add an incoming traffic firewall policy
1Go to Firewall > Policy.
2Select Create New.
|
|
|
FortiGate-60B FortiOS 3.0 MR6 Install Guide |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
20 |
01-30006-0446-20080910 |
||
 Loading...
Loading...